| URL: | https://objects.githubusercontent.com/github-production-release-asset-2e65be/589087848/d82b96e2-e79a-4fa4-b59e-a44a25ae31de?X-Amz-Algorithm=AWS4-HMAC-SHA256&X-Amz-Credential=releaseassetproduction%2F20250323%2Fus-east-1%2Fs3%2Faws4_request&X-Amz-Date=20250323T222048Z&X-Amz-Expires=300&X-Amz-Signature=f8ac7a348246f60d6f7490c4de6fd558422a91a5c21c87299056c742349e9875&X-Amz-SignedHeaders=host&response-content-disposition=attachment%3B%20filename%3DMod.Menu.zip&response-content-type=application%2Foctet-stream |
| Full analysis: | https://app.any.run/tasks/2710a51c-17bb-4d51-81a5-3d6612e84f75 |
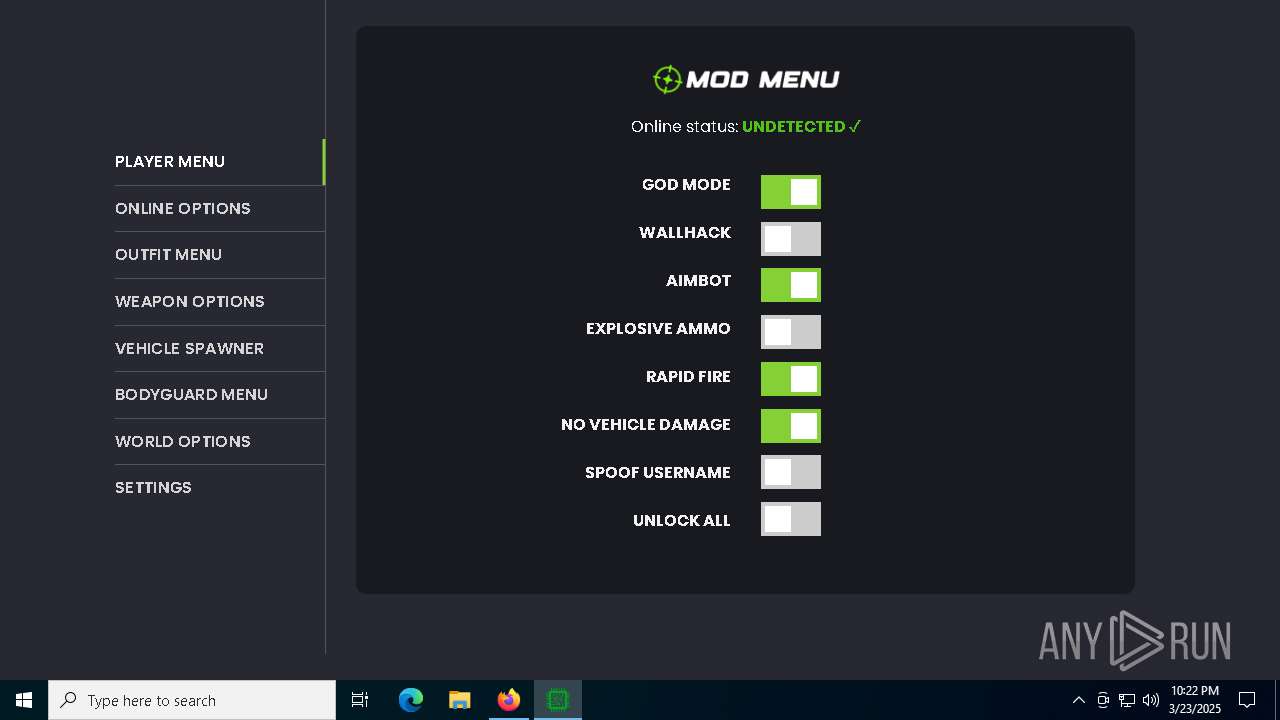
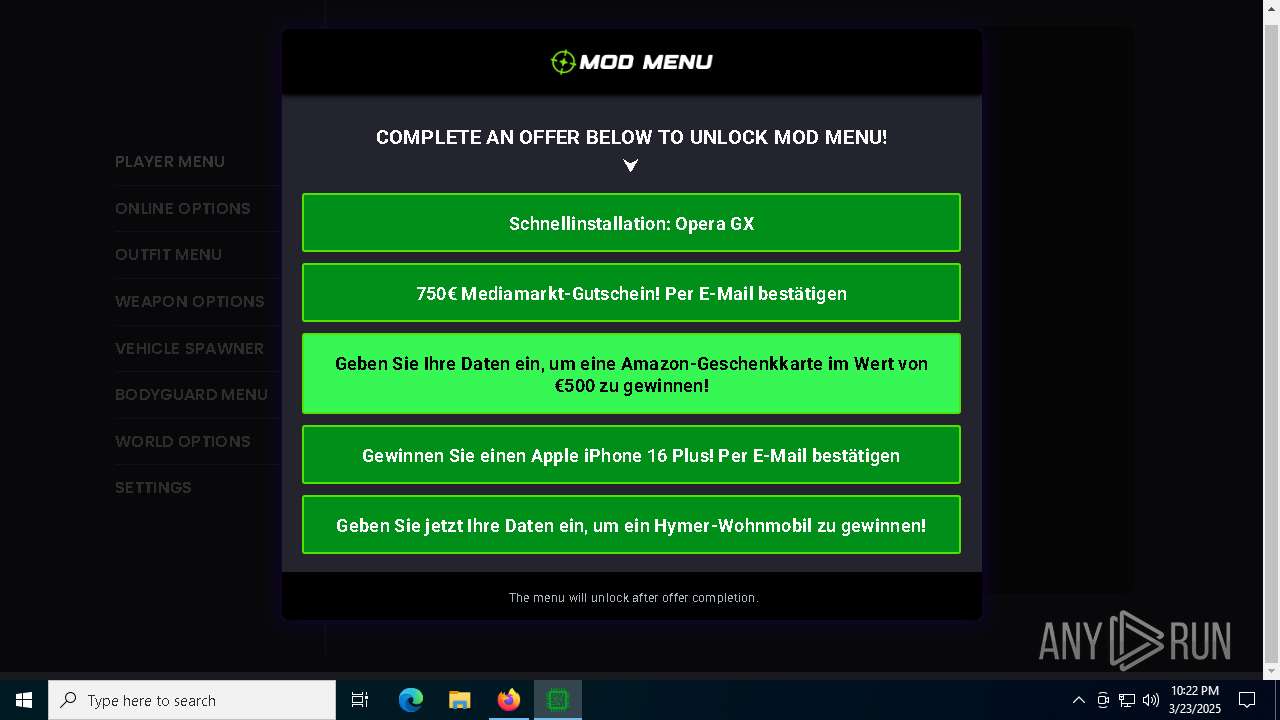
| Verdict: | Malicious activity |
| Analysis date: | March 23, 2025, 22:21:40 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | D9D507090AC3EC3F30B713E675D54880 |
| SHA1: | 086A2075C5CDE569ED86498811C2E9652F7425BE |
| SHA256: | BD22D8AD8AC36ADFACF24D2B38EA00D4BA1A558D7AAE96B7FF64796F95D081BB |
| SSDEEP: | 12:28aMGmb+OmyLvttSmU9AAh2mAivU+HnCTUtLVnAIn:23MGmySNU9Hh2hoqUtxAIn |
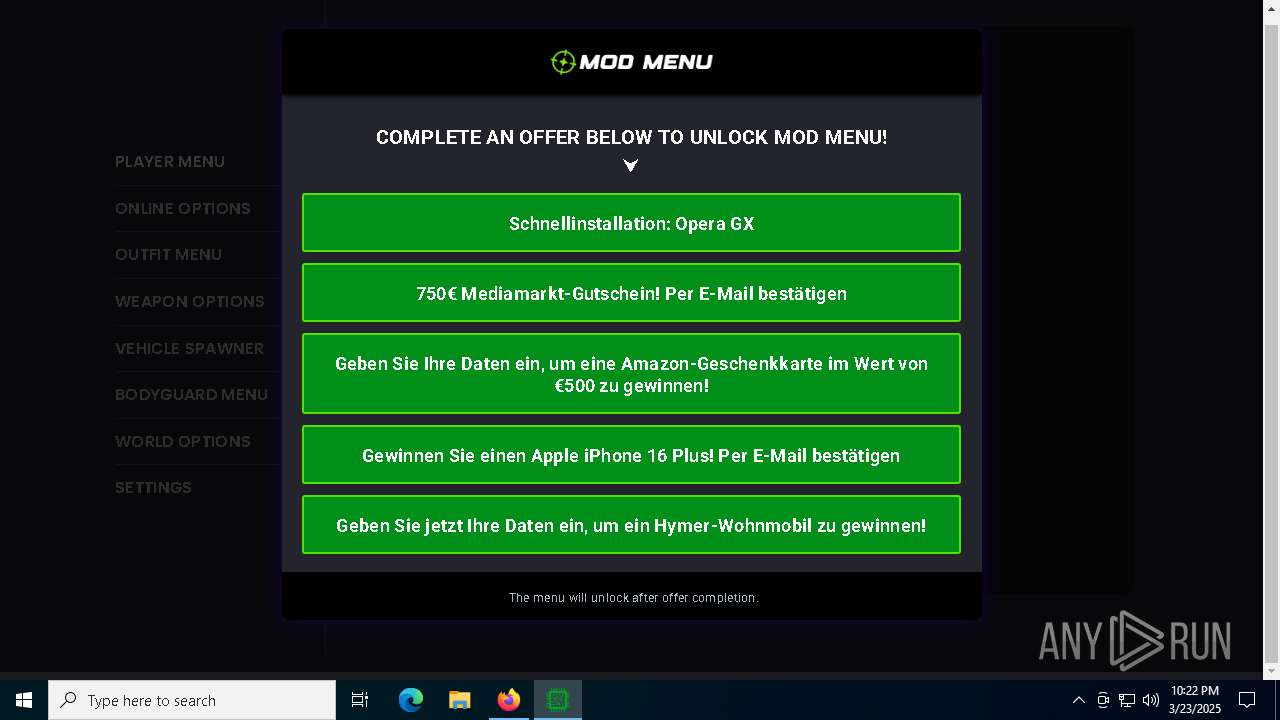
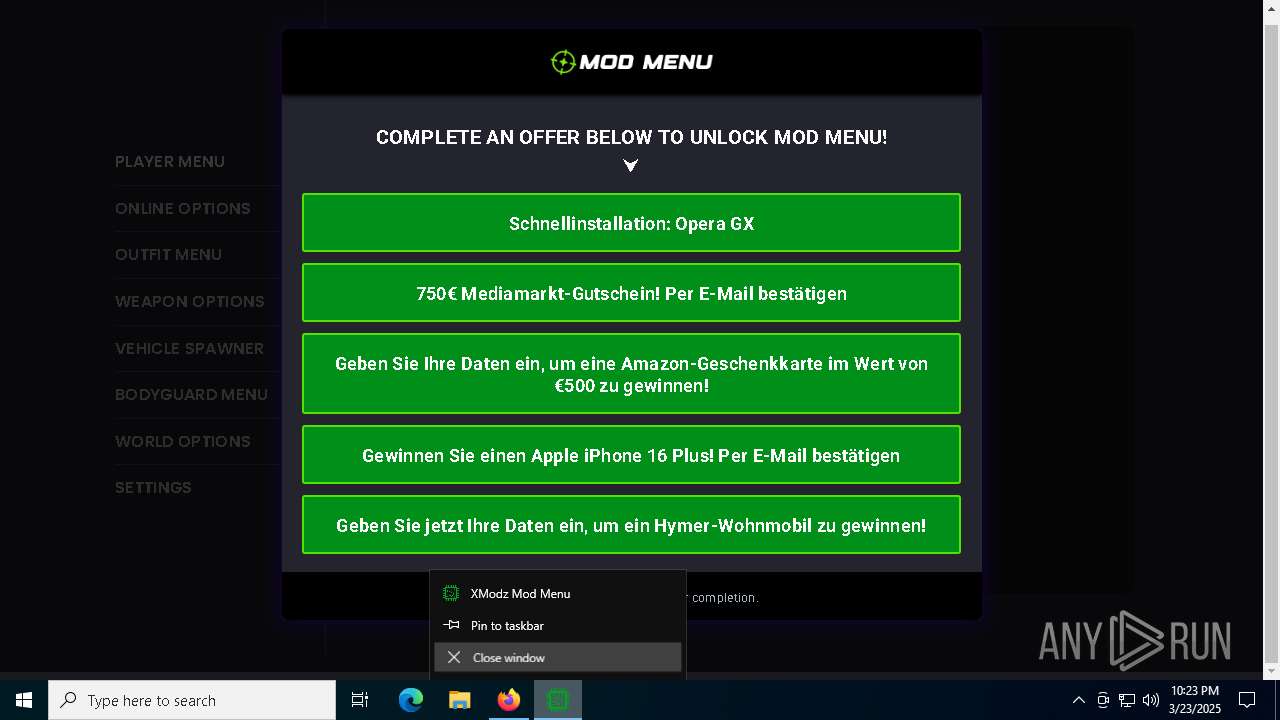
MALICIOUS
Changes the autorun value in the registry
- Mod Menu.exe (PID: 2772)
SUSPICIOUS
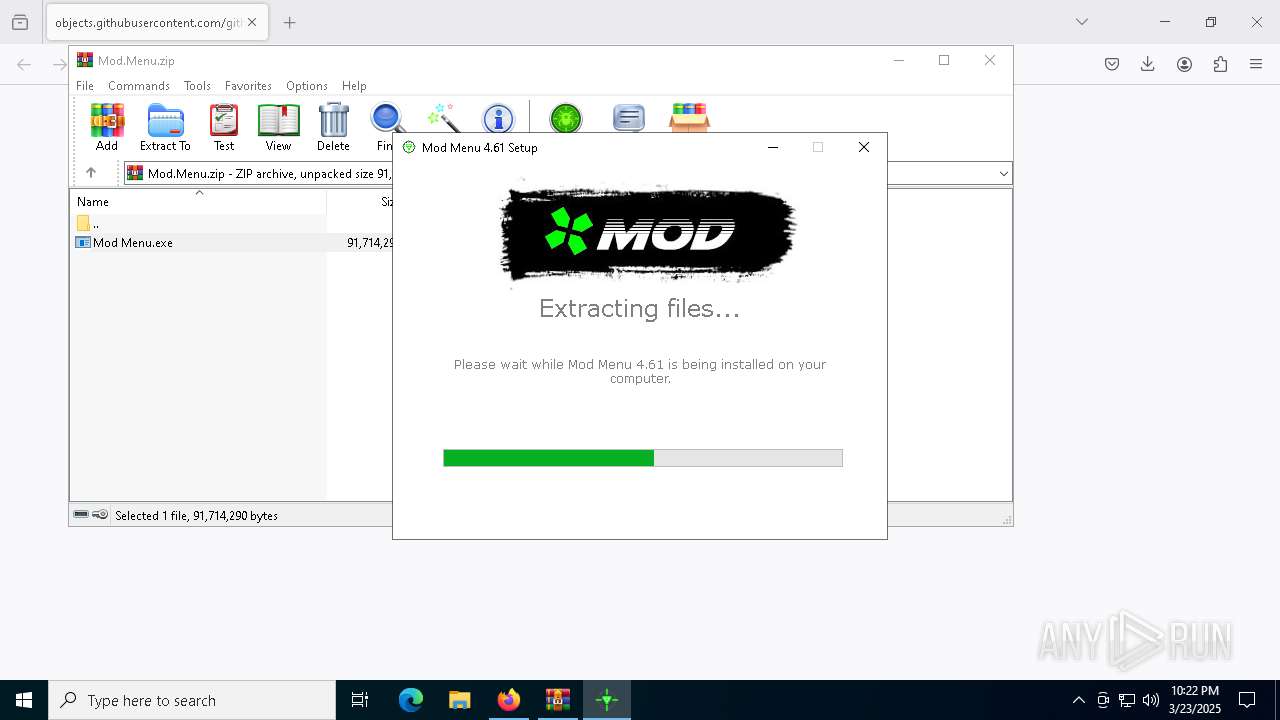
Executable content was dropped or overwritten
- Mod Menu.exe (PID: 2772)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 5400)
- Mod Menu.exe (PID: 2772)
- ShellExperienceHost.exe (PID: 5200)
Process drops legitimate windows executable
- Mod Menu.exe (PID: 2772)
Application launched itself
- XModz Mod Menu.exe (PID: 6040)
INFO
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 1096)
- slui.exe (PID: 8100)
- XModz Mod Menu.exe (PID: 6040)
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 8076)
- BackgroundTransferHost.exe (PID: 5384)
- BackgroundTransferHost.exe (PID: 5776)
- BackgroundTransferHost.exe (PID: 1096)
- BackgroundTransferHost.exe (PID: 8136)
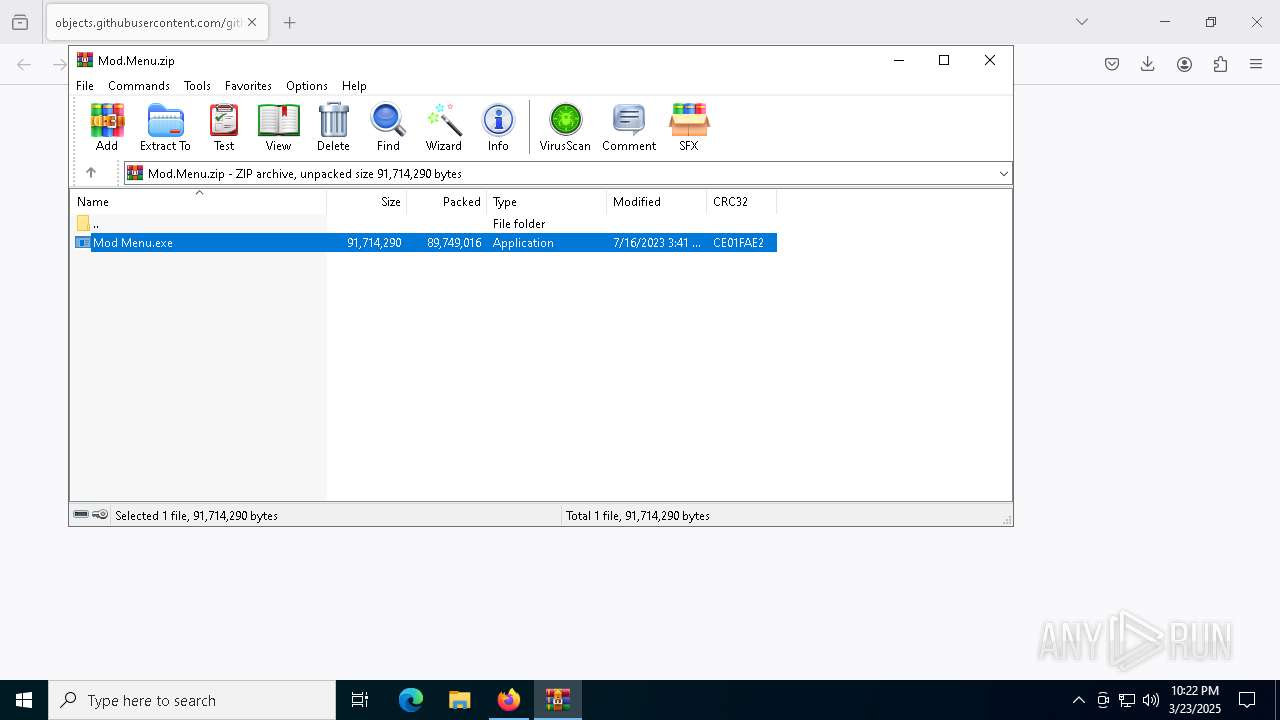
Manual execution by a user
- WinRAR.exe (PID: 5400)
Create files in a temporary directory
- Mod Menu.exe (PID: 2772)
- XModz Mod Menu.exe (PID: 6040)
Checks supported languages
- Mod Menu.exe (PID: 2772)
- XModz Mod Menu.exe (PID: 6040)
- XModz Mod Menu.exe (PID: 7836)
- XModz Mod Menu.exe (PID: 5116)
- XModz Mod Menu.exe (PID: 3100)
- XModz Mod Menu.exe (PID: 3968)
- ShellExperienceHost.exe (PID: 5200)
Reads the computer name
- Mod Menu.exe (PID: 2772)
- XModz Mod Menu.exe (PID: 6040)
- XModz Mod Menu.exe (PID: 7836)
- XModz Mod Menu.exe (PID: 5116)
- ShellExperienceHost.exe (PID: 5200)
Creates files or folders in the user directory
- Mod Menu.exe (PID: 2772)
- BackgroundTransferHost.exe (PID: 1096)
- XModz Mod Menu.exe (PID: 5116)
- XModz Mod Menu.exe (PID: 6040)
Autorun file from Downloads
- firefox.exe (PID: 6048)
Application launched itself
- firefox.exe (PID: 6048)
- firefox.exe (PID: 4628)
The sample compiled with english language support
- firefox.exe (PID: 6048)
- Mod Menu.exe (PID: 2772)
Checks proxy server information
- BackgroundTransferHost.exe (PID: 1096)
- XModz Mod Menu.exe (PID: 6040)
Process checks computer location settings
- Mod Menu.exe (PID: 2772)
- XModz Mod Menu.exe (PID: 3100)
- XModz Mod Menu.exe (PID: 3968)
- XModz Mod Menu.exe (PID: 6040)
Reads product name
- XModz Mod Menu.exe (PID: 6040)
- XModz Mod Menu.exe (PID: 3100)
Reads Environment values
- XModz Mod Menu.exe (PID: 6040)
- XModz Mod Menu.exe (PID: 3100)
Reads the machine GUID from the registry
- XModz Mod Menu.exe (PID: 6040)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
161
Monitored processes
27
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1096 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
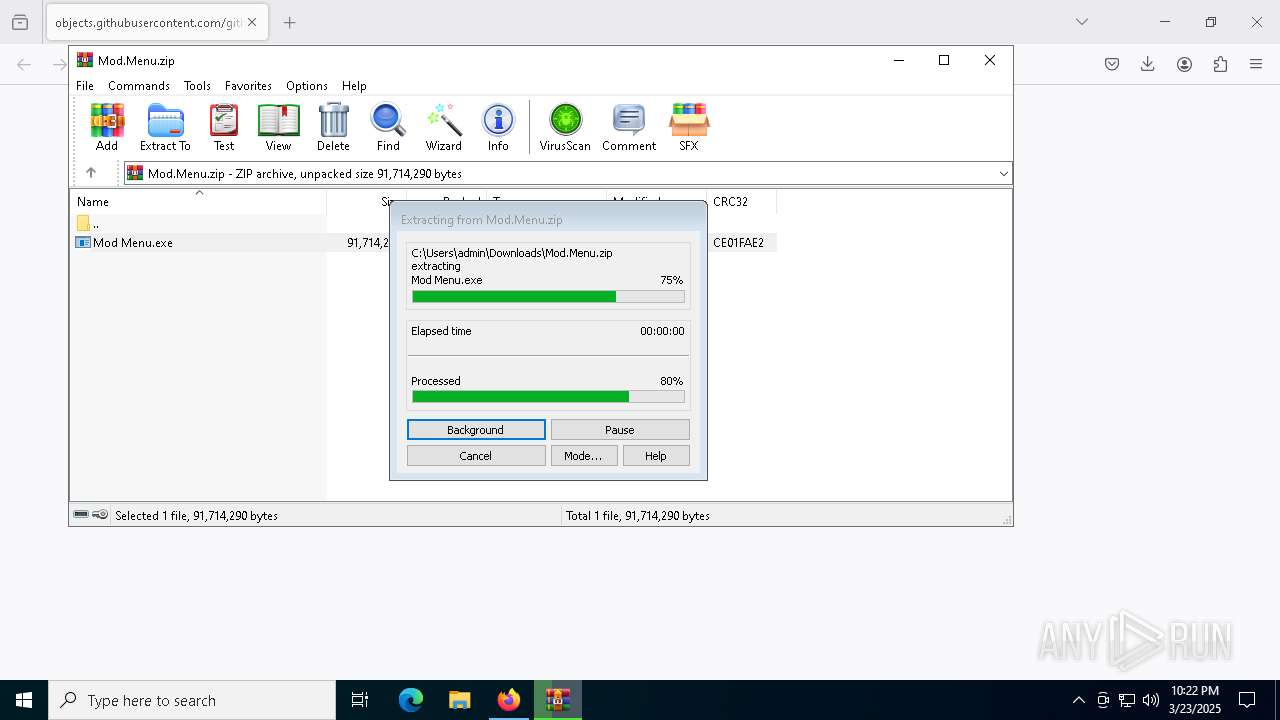
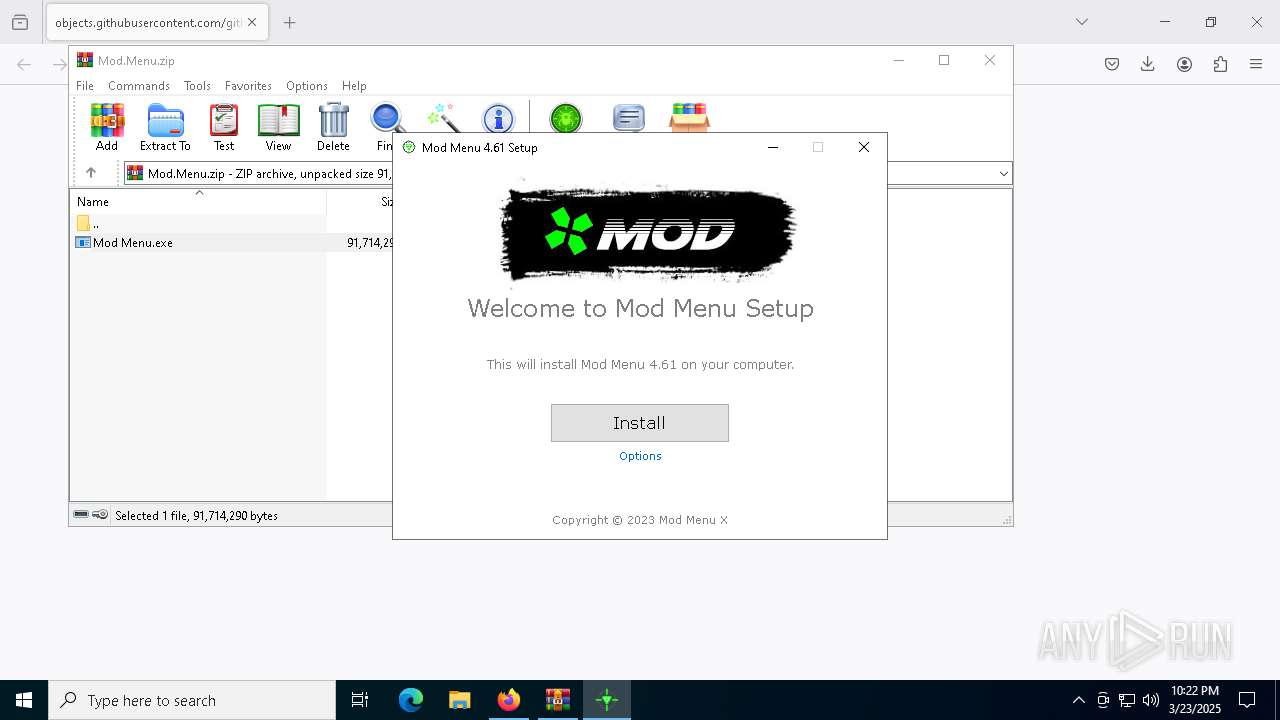
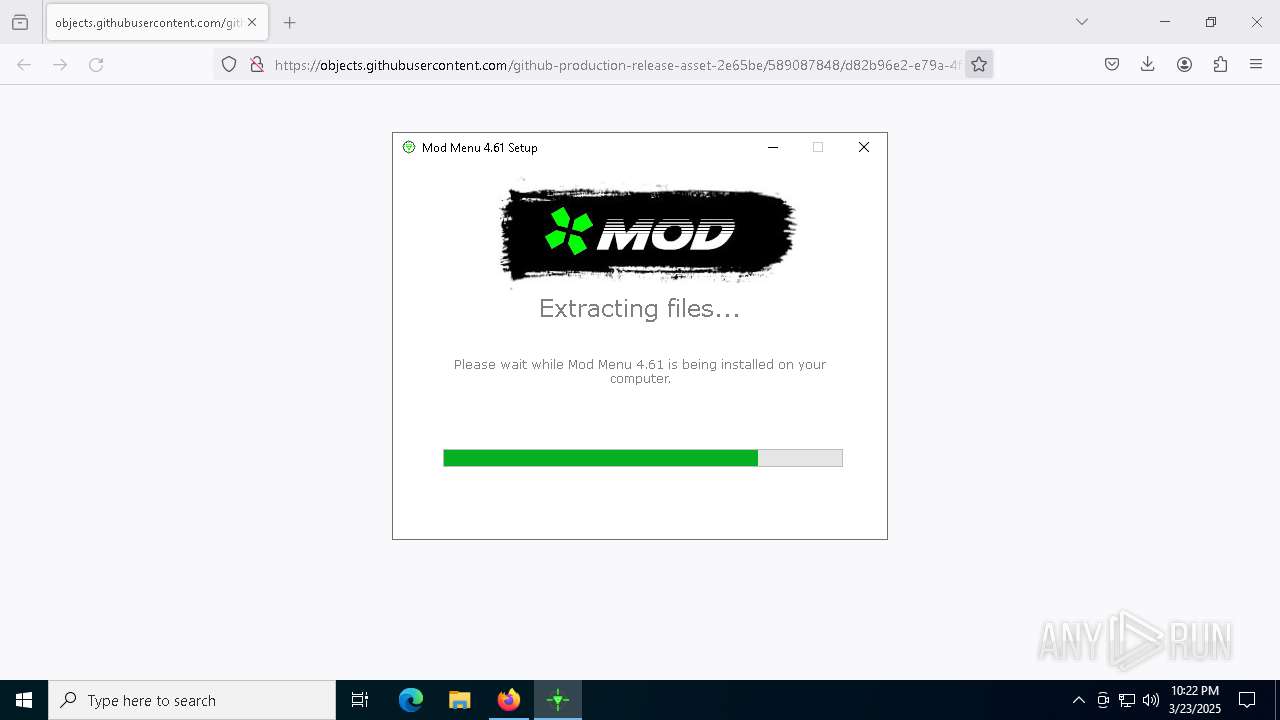
| 2772 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa5400.34652\Mod Menu.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa5400.34652\Mod Menu.exe | WinRAR.exe | ||||||||||||
User: admin Company: Unknown Integrity Level: MEDIUM Description: Installation Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3100 | "C:\Users\admin\AppData\Roaming\Mod Menu\XModz Mod Menu.exe" --type=renderer --user-data-dir="C:\Users\admin\AppData\Roaming\xmodz-mod-menu-nativefier-e5a4a8" --app-user-model-id=xmodz-mod-menu-nativefier-e5a4a8 --app-path="C:\Users\admin\AppData\Roaming\Mod Menu\resources\app" --no-sandbox --no-zygote --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --mojo-platform-channel-handle=2392 --field-trial-handle=1684,i,2829524807744710991,556066541725815152,131072 --disable-features=SpareRendererForSitePerProcess,WinRetrieveSuggestionsOnlyOnDemand /prefetch:1 | C:\Users\admin\AppData\Roaming\Mod Menu\XModz Mod Menu.exe | — | XModz Mod Menu.exe | |||||||||||
User: admin Company: Jia Hao Integrity Level: MEDIUM Description: XModz Mod Menu Exit code: 0 Version: 1.0.0 Modules
| |||||||||||||||
| 3968 | "C:\Users\admin\AppData\Roaming\Mod Menu\XModz Mod Menu.exe" --type=renderer --user-data-dir="C:\Users\admin\AppData\Roaming\xmodz-mod-menu-nativefier-e5a4a8" --app-user-model-id=xmodz-mod-menu-nativefier-e5a4a8 --app-path="C:\Users\admin\AppData\Roaming\Mod Menu\resources\app" --enable-sandbox --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=3244 --field-trial-handle=1684,i,2829524807744710991,556066541725815152,131072 --disable-features=SpareRendererForSitePerProcess,WinRetrieveSuggestionsOnlyOnDemand /prefetch:1 | C:\Users\admin\AppData\Roaming\Mod Menu\XModz Mod Menu.exe | — | XModz Mod Menu.exe | |||||||||||
User: admin Company: Jia Hao Integrity Level: LOW Description: XModz Mod Menu Exit code: 0 Version: 1.0.0 Modules
| |||||||||||||||
| 4628 | "C:\Program Files\Mozilla Firefox\firefox.exe" "https://objects.githubusercontent.com/github-production-release-asset-2e65be/589087848/d82b96e2-e79a-4fa4-b59e-a44a25ae31de?X-Amz-Algorithm=AWS4-HMAC-SHA256&X-Amz-Credential=releaseassetproduction%2F20250323%2Fus-east-1%2Fs3%2Faws4_request&X-Amz-Date=20250323T222048Z&X-Amz-Expires=300&X-Amz-Signature=f8ac7a348246f60d6f7490c4de6fd558422a91a5c21c87299056c742349e9875&X-Amz-SignedHeaders=host&response-content-disposition=attachment%3B%20filename%3DMod.Menu.zip&response-content-type=application%2Foctet-stream" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 5116 | "C:\Users\admin\AppData\Roaming\Mod Menu\XModz Mod Menu.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --user-data-dir="C:\Users\admin\AppData\Roaming\xmodz-mod-menu-nativefier-e5a4a8" --mojo-platform-channel-handle=2024 --field-trial-handle=1684,i,2829524807744710991,556066541725815152,131072 --disable-features=SpareRendererForSitePerProcess,WinRetrieveSuggestionsOnlyOnDemand /prefetch:8 | C:\Users\admin\AppData\Roaming\Mod Menu\XModz Mod Menu.exe | XModz Mod Menu.exe | ||||||||||||
User: admin Company: Jia Hao Integrity Level: MEDIUM Description: XModz Mod Menu Exit code: 0 Version: 1.0.0 Modules
| |||||||||||||||
| 5200 | "C:\WINDOWS\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe" -ServerName:App.AppXtk181tbxbce2qsex02s8tw7hfxa9xb3t.mca | C:\Windows\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Shell Experience Host Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5384 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
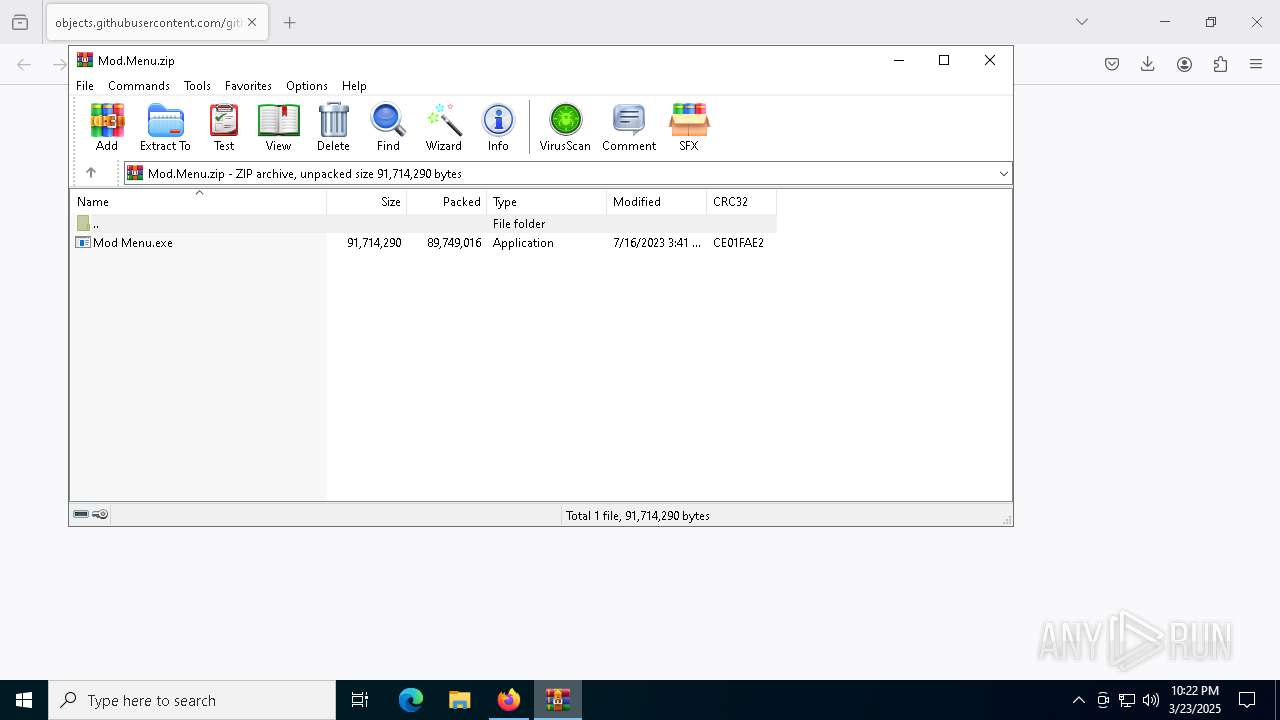
| 5400 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\Mod.Menu.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 5776 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
23 722
Read events
23 667
Write events
37
Delete events
18
Modification events
| (PID) Process: | (6048) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (8136) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (8136) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (8136) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1096) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1096) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1096) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (5776) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (5776) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (5776) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
7
Suspicious files
276
Text files
36
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6048 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 6048 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json.tmp | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 6048 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cookies.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 6048 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\SiteSecurityServiceState.bin | binary | |
MD5:25D2A5B2CB1F7E76705CD2C9599F41B0 | SHA256:A515B758BB23998FD3615F7271DD0AB4133F689EFFF944287AE7A0B42C371F10 | |||
| 6048 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-child-current.bin | binary | |
MD5:C95DDC2B1A525D1A243E4C294DA2F326 | SHA256:3A5919E086BFB31E36110CF636D2D5109EB51F2C410B107F126126AB25D67363 | |||
| 6048 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 6048 | firefox.exe | C:\Users\admin\Downloads\Mod.H4oK2ad_.Menu.zip.part | — | |
MD5:— | SHA256:— | |||
| 6048 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\urlCache-current.bin | binary | |
MD5:297E88D7CEB26E549254EC875649F4EB | SHA256:8B75D4FB1845BAA06122888D11F6B65E6A36B140C54A72CC13DF390FD7C95702 | |||
| 6048 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 6048 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
25
TCP/UDP connections
87
DNS requests
118
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6048 | firefox.exe | POST | 200 | 142.250.184.227:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
6048 | firefox.exe | POST | 200 | 142.250.184.227:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
1760 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1760 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6048 | firefox.exe | POST | 200 | 2.16.168.113:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
6048 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
6048 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.16.168.124:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6048 | firefox.exe | POST | 200 | 2.16.168.113:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
6048 | firefox.exe | POST | 200 | 142.250.184.227:80 | http://o.pki.goog/s/wr3/cgo | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 2.16.168.124:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6048 | firefox.exe | 185.199.109.133:443 | objects.githubusercontent.com | FASTLY | US | whitelisted |
6048 | firefox.exe | 142.250.186.106:443 | safebrowsing.googleapis.com | — | — | whitelisted |
6048 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
6048 | firefox.exe | 95.101.54.107:80 | r11.o.lencr.org | Akamai International B.V. | DE | whitelisted |
6048 | firefox.exe | 34.117.188.166:443 | contile.services.mozilla.com | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
objects.githubusercontent.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
example.org |
| whitelisted |
ipv4only.arpa |
| whitelisted |
spocs.getpocket.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Misc activity | ET INFO DNS Query to Cloudflare Page Developer Domain (pages .dev) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Pages platform for frontend developers to collaborate and deploy websites (pages .dev) |
5116 | XModz Mod Menu.exe | Misc activity | ET INFO Observed Cloudflare Page Developer Domain (pages .dev in TLS SNI) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |