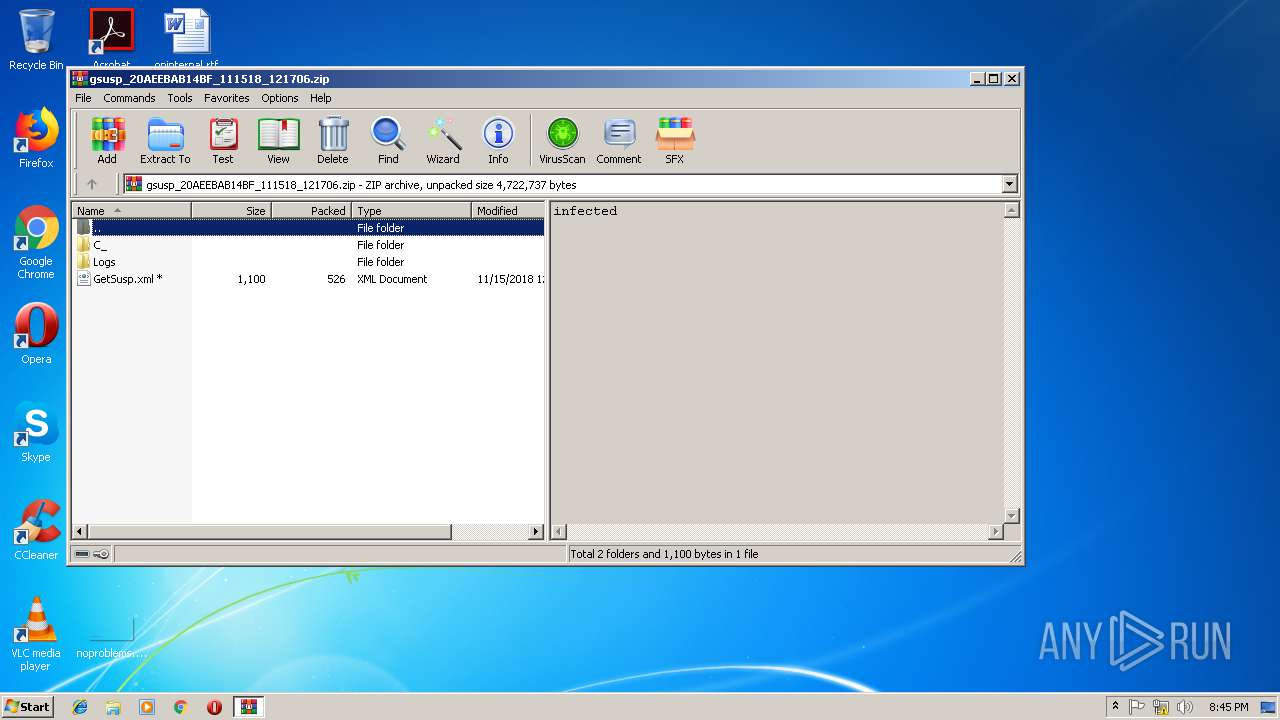
| File name: | gsusp_20AEEBAB14BF_111518_121706.zip |
| Full analysis: | https://app.any.run/tasks/fd00c548-2310-49f4-8b92-3e102f7544cc |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | November 15, 2018, 20:45:19 |
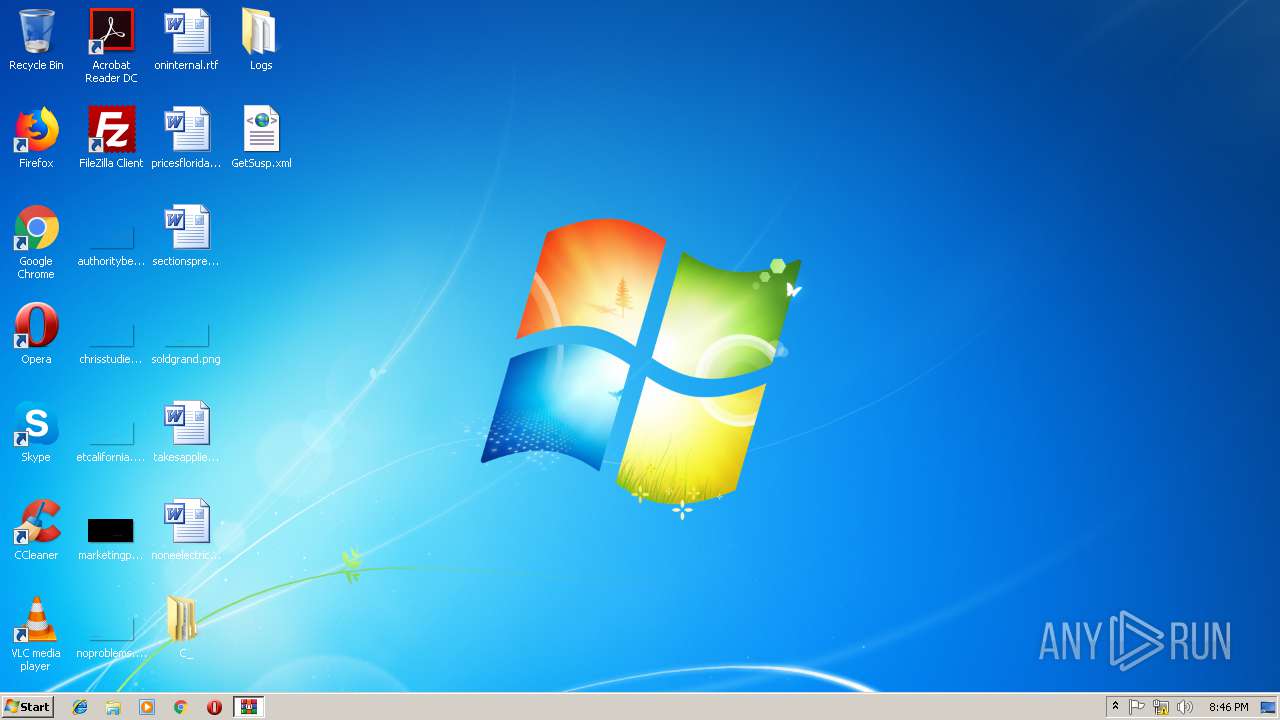
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 6B27E7A040C01A638B7F402A2E382402 |
| SHA1: | 14FA44E5F9F3792738A949E09FD59AA2A0E61396 |
| SHA256: | BD1F245C20083B7D497E935E666AD34D76C4D42C1A73B2CF834C6AEF8370B334 |
| SSDEEP: | 12288:O7oy8fp32woxlJS1vR5EiqZAg62kiJ1Nrhq+YLuDniH1eXzodeh7CWco+ZmuIbdW:rGTzJKfwAHR8rhq+YLk9RZuZba0hDMDk |
MALICIOUS
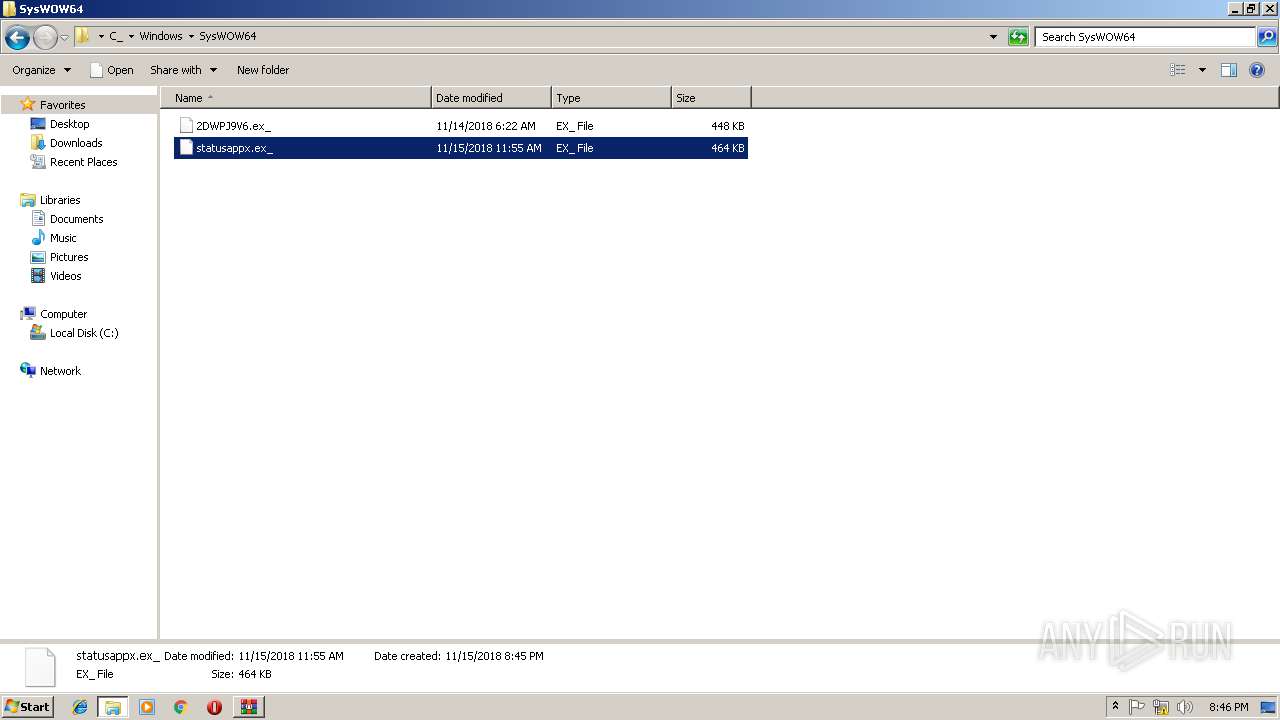
Application was dropped or rewritten from another process
- statusappx.exe (PID: 2612)
- statusappx.exe (PID: 3636)
- lpiograd.exe (PID: 3968)
- lpiograd.exe (PID: 2816)
Emotet process was detected
- lpiograd.exe (PID: 3968)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3264)
- statusappx.exe (PID: 2612)
Starts itself from another location
- statusappx.exe (PID: 2612)
Connects to unusual port
- lpiograd.exe (PID: 2816)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0003 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2018:11:08 11:33:14 |
| ZipCRC: | 0x9ead2682 |
| ZipCompressedSize: | 492049 |
| ZipUncompressedSize: | 2156385 |
| ZipFileName: | C_\Users\wilrod524\AppData\Local\IBM\DD\DownloadDirectorLauncher.ex_ |
Total processes
40
Monitored processes
6
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
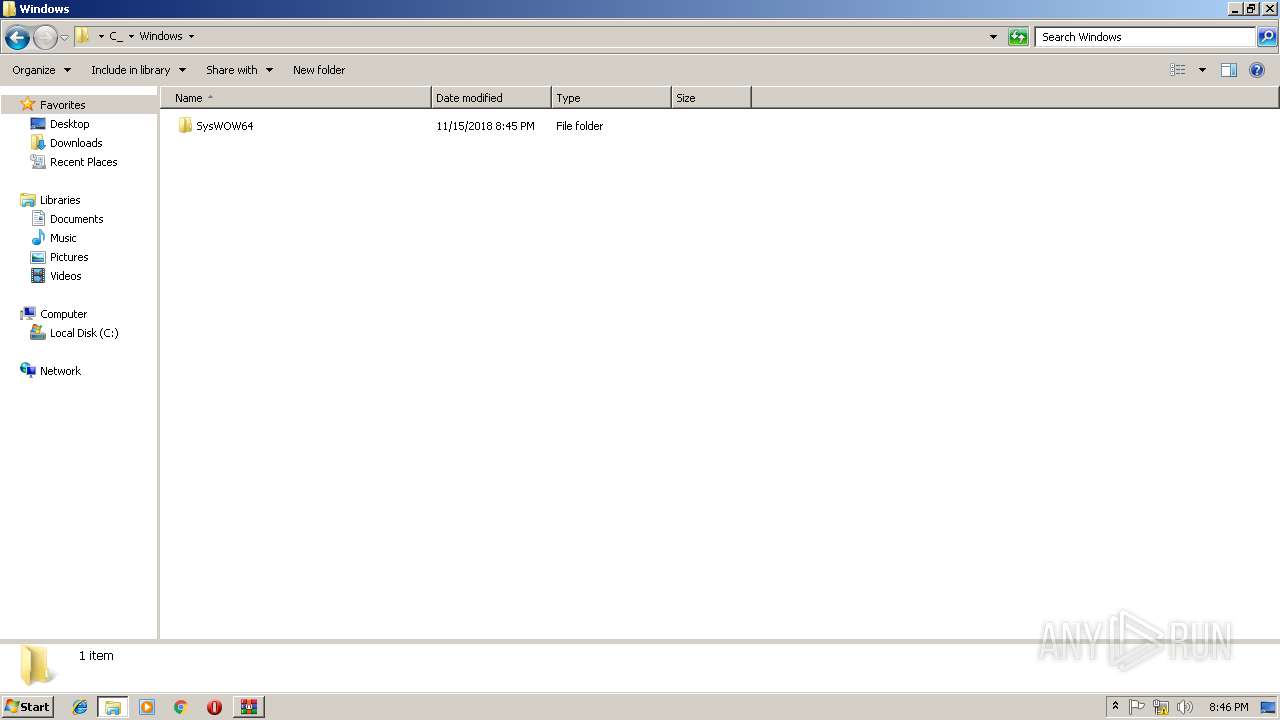
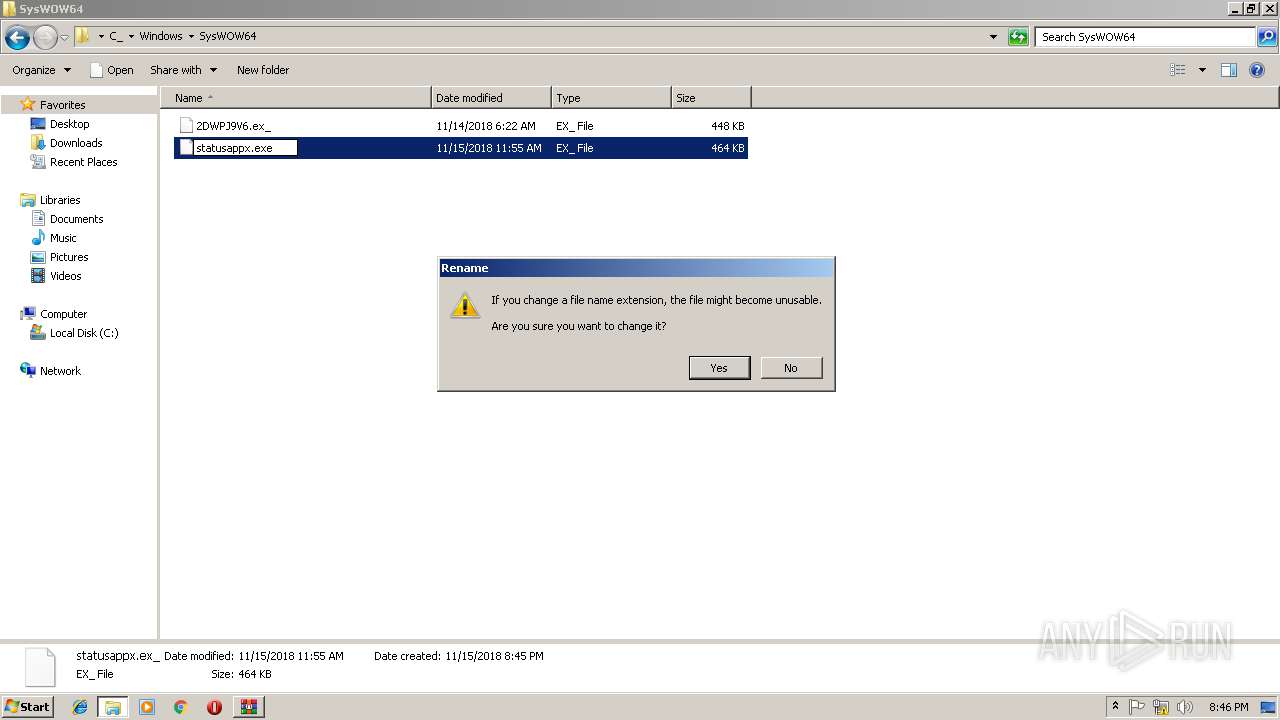
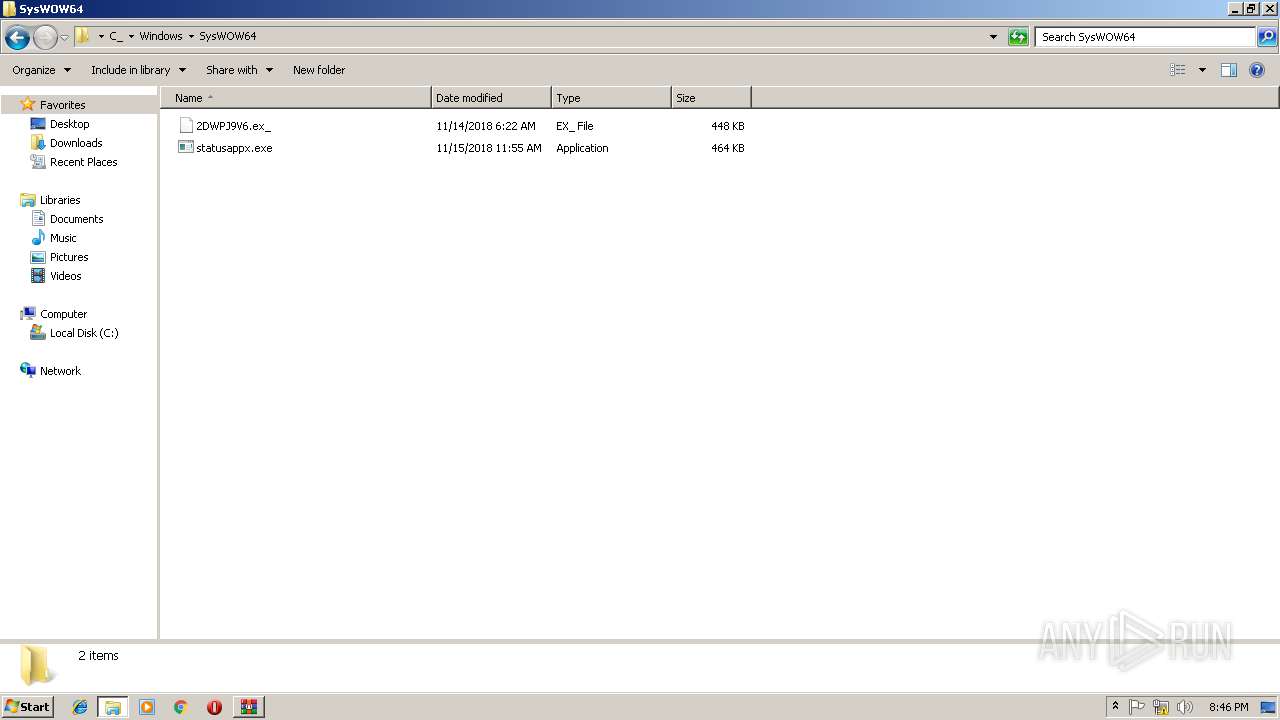
| 2612 | "C:\Users\admin\Desktop\C_\Windows\SysWOW64\statusappx.exe" | C:\Users\admin\Desktop\C_\Windows\SysWOW64\statusappx.exe | statusappx.exe | ||||||||||||
User: admin Company: Microsoft Corpora Integrity Level: MEDIUM Description: Microsoft SQL Exit code: 0 Version: 3.00. Modules
| |||||||||||||||
| 2816 | "C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe | lpiograd.exe | ||||||||||||
User: admin Company: Microsoft Corpora Integrity Level: MEDIUM Description: Microsoft SQL Exit code: 0 Version: 3.00. Modules
| |||||||||||||||
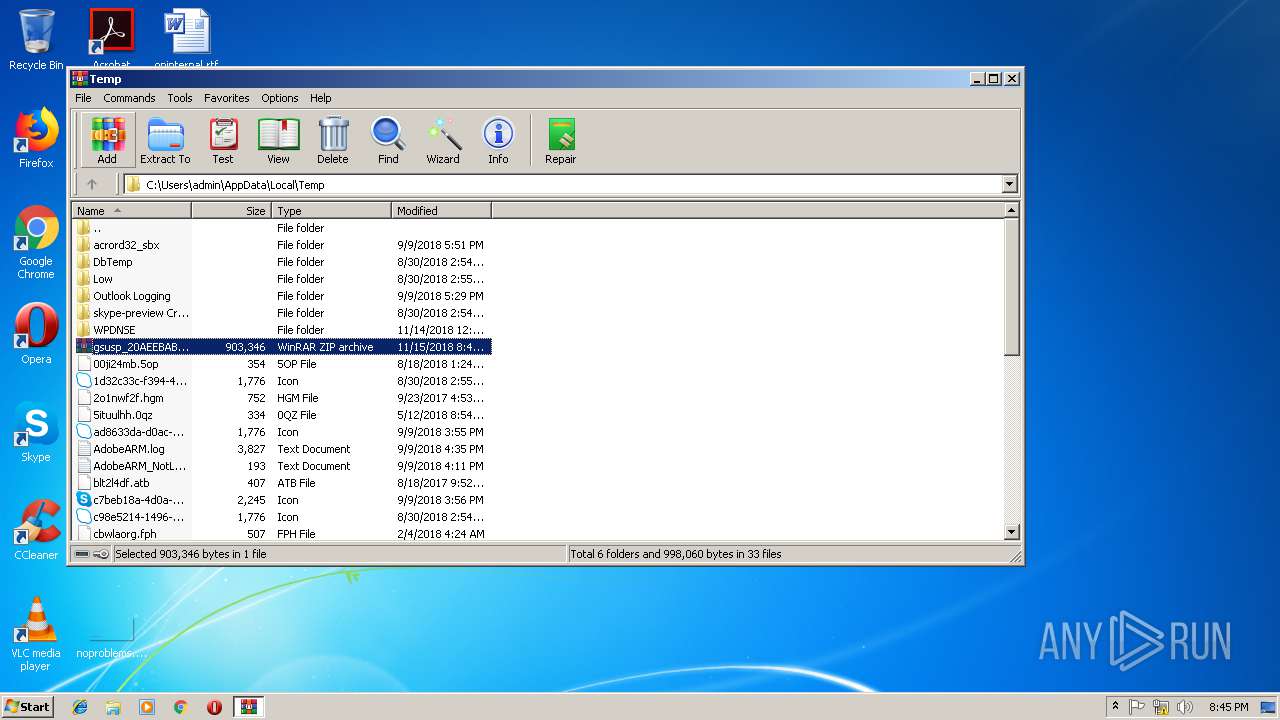
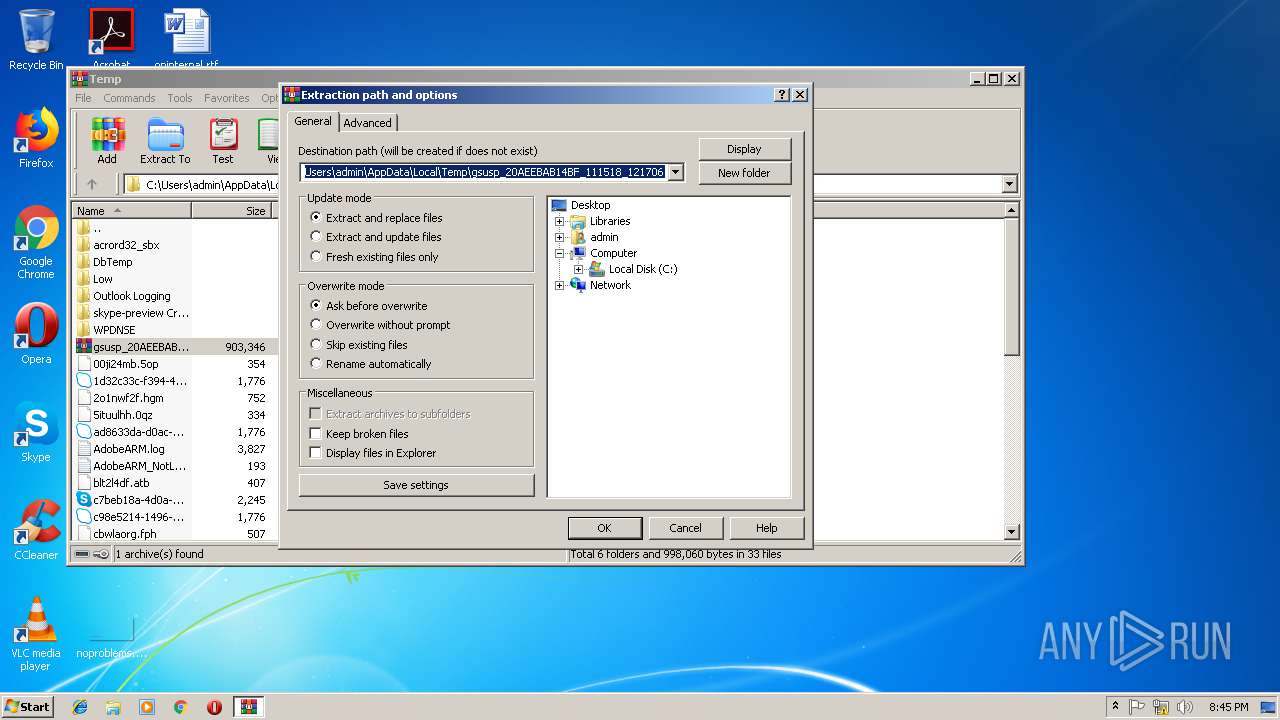
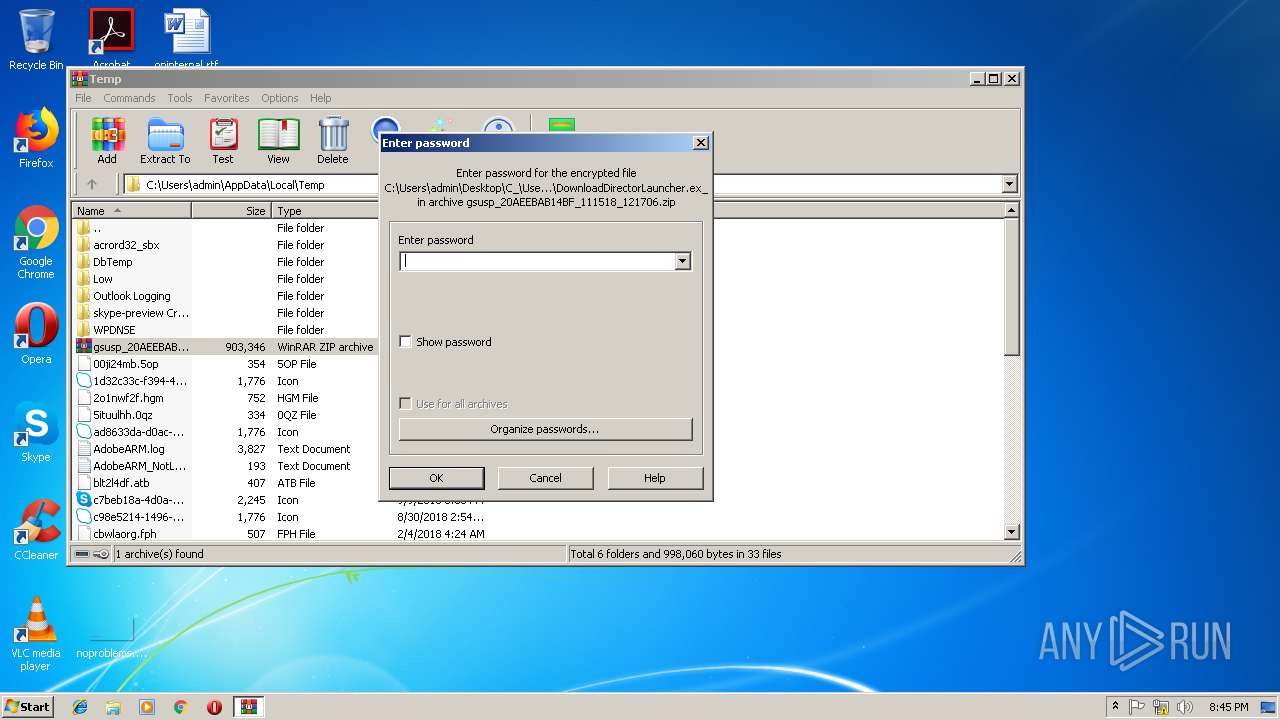
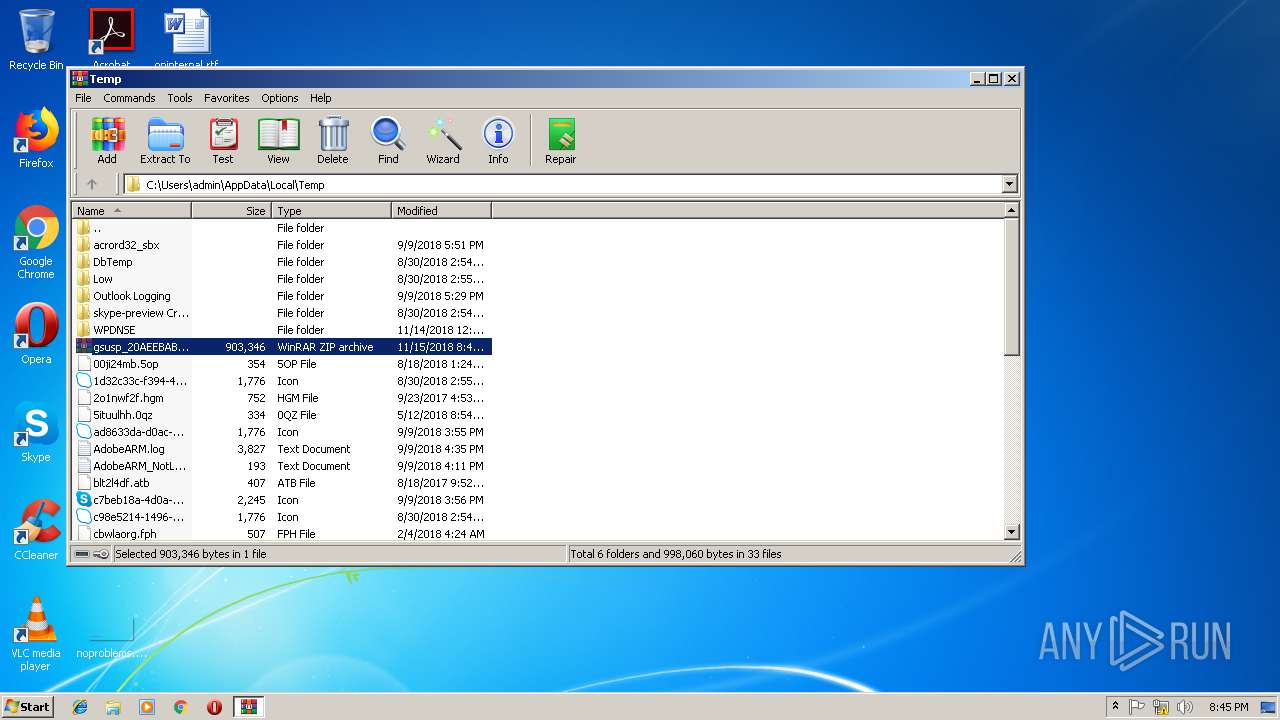
| 3264 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\gsusp_20AEEBAB14BF_111518_121706.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3636 | "C:\Users\admin\Desktop\C_\Windows\SysWOW64\statusappx.exe" | C:\Users\admin\Desktop\C_\Windows\SysWOW64\statusappx.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corpora Integrity Level: MEDIUM Description: Microsoft SQL Exit code: 0 Version: 3.00. Modules
| |||||||||||||||
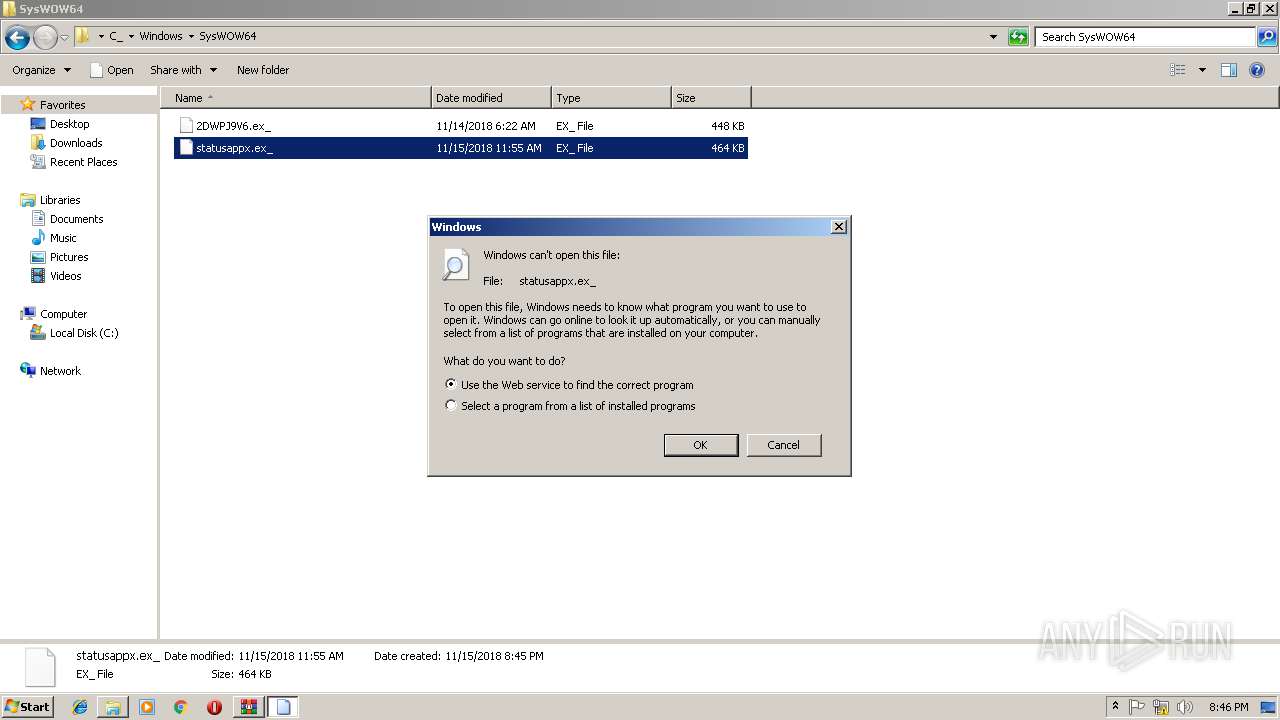
| 3820 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\Desktop\C_\Windows\SysWOW64\statusappx.ex_ | C:\Windows\system32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3968 | "C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe | statusappx.exe | ||||||||||||
User: admin Company: Microsoft Corpora Integrity Level: MEDIUM Description: Microsoft SQL Exit code: 0 Version: 3.00. Modules
| |||||||||||||||
Total events
520
Read events
486
Write events
34
Delete events
0
Modification events
| (PID) Process: | (3264) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3264) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3264) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3264) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\gsusp_20AEEBAB14BF_111518_121706.zip | |||
| (PID) Process: | (3264) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3264) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3264) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3264) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3264) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Comment |
| Operation: | write | Name: | LeftBorder |
Value: 476 | |||
| (PID) Process: | (3264) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
Executable files
6
Suspicious files
0
Text files
8
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
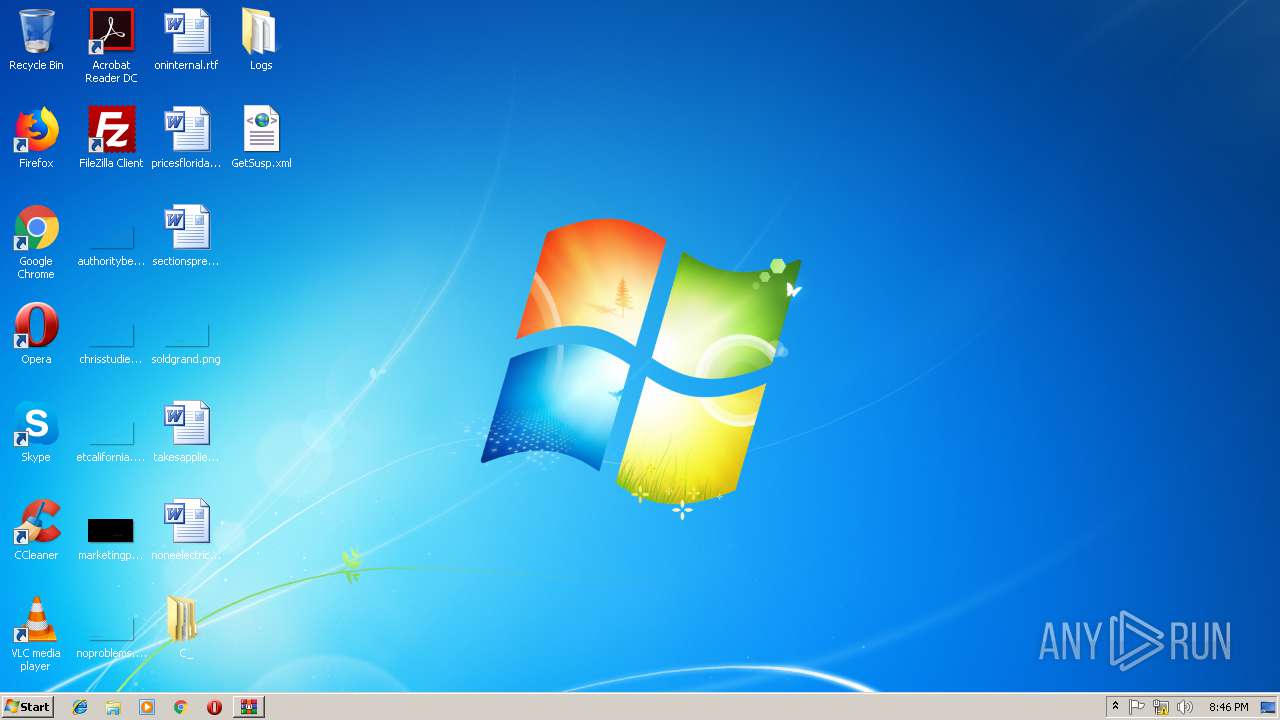
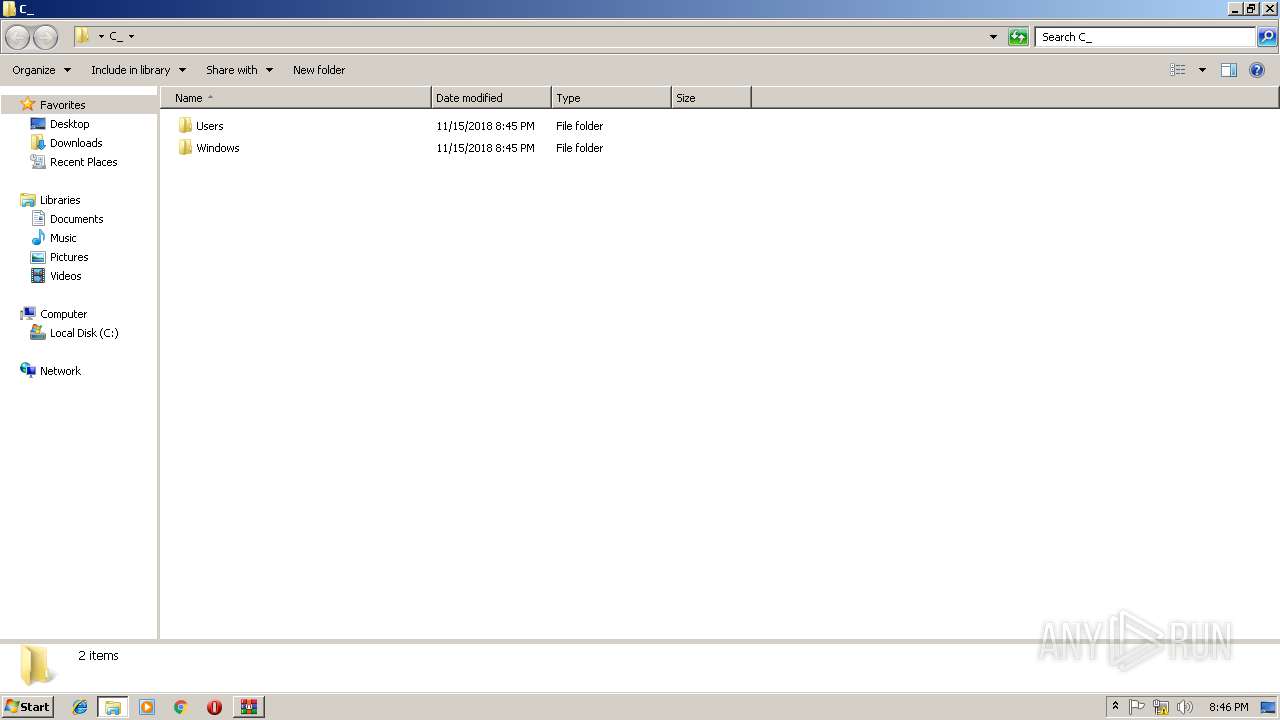
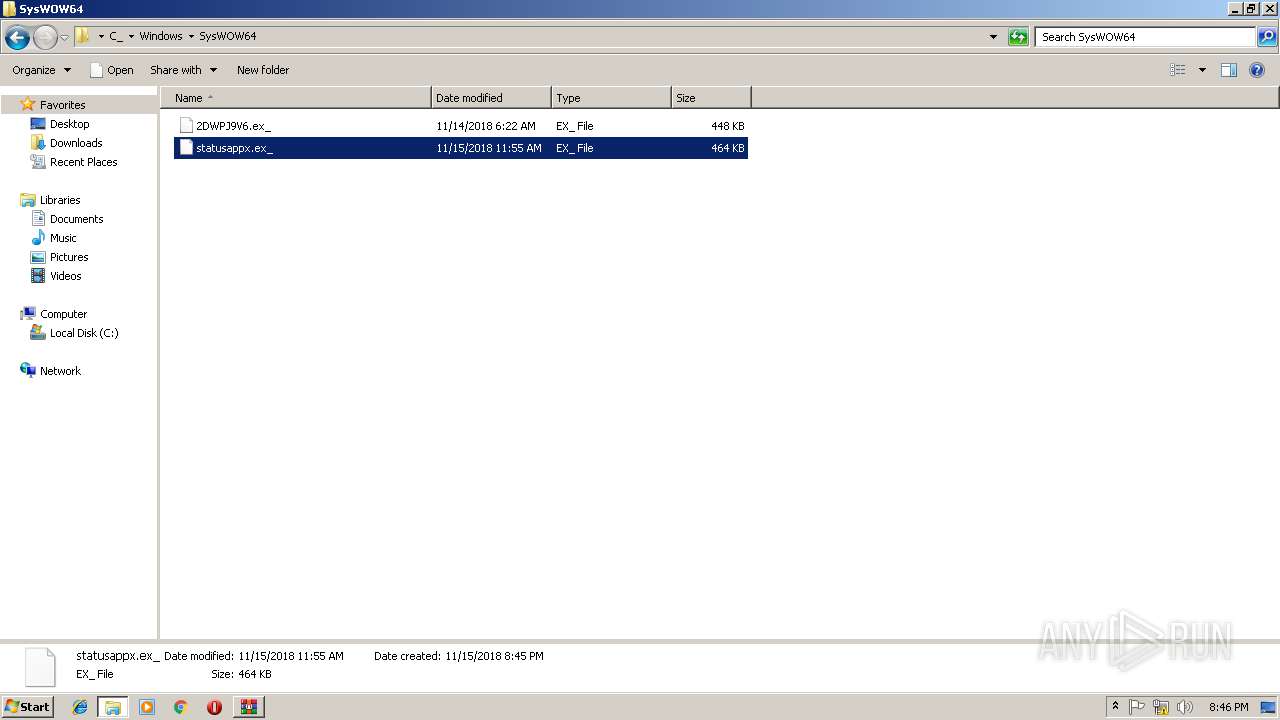
| 3264 | WinRAR.exe | C:\Users\admin\Desktop\C_\Windows\SysWOW64\2DWPJ9V6.ex_ | executable | |
MD5:— | SHA256:— | |||
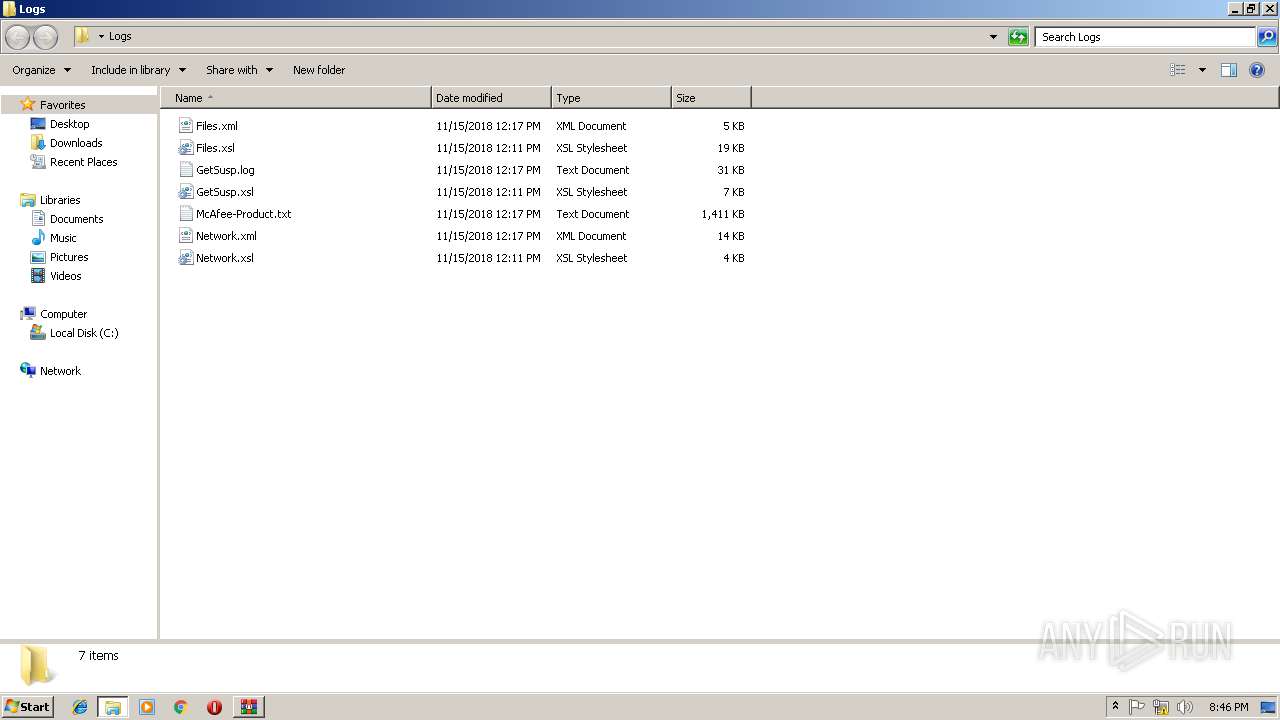
| 3264 | WinRAR.exe | C:\Users\admin\Desktop\Logs\Files.xml | xml | |
MD5:— | SHA256:— | |||
| 3264 | WinRAR.exe | C:\Users\admin\Desktop\Logs\McAfee-Product.txt | text | |
MD5:— | SHA256:— | |||
| 3264 | WinRAR.exe | C:\Users\admin\Desktop\Logs\Network.xsl | xml | |
MD5:— | SHA256:— | |||
| 3264 | WinRAR.exe | C:\Users\admin\Desktop\Logs\Files.xsl | xml | |
MD5:— | SHA256:— | |||
| 3264 | WinRAR.exe | C:\Users\admin\Desktop\Logs\Network.xml | xml | |
MD5:— | SHA256:— | |||
| 3264 | WinRAR.exe | C:\Users\admin\Desktop\Logs\GetSusp.xsl | xml | |
MD5:— | SHA256:— | |||
| 3264 | WinRAR.exe | C:\Users\admin\Desktop\Logs\GetSusp.log | text | |
MD5:— | SHA256:— | |||
| 3264 | WinRAR.exe | C:\Users\admin\Desktop\C_\Users\wilrod524\AppData\Local\Microsoft\VisualStudio\15.0_0cebdecf\3082\ResourceCache.dl_ | executable | |
MD5:— | SHA256:— | |||
| 3264 | WinRAR.exe | C:\Users\admin\Desktop\C_\Users\wilrod524\Desktop\McAfee-10.160.0.24\gsusp_B56B3429DE2B_111518_084824\C_\Users\wilrod524\source\repos\RevisarBloqueos\RevisarBloqueos\bin\Debug\RevisarBloqueos.ex_ | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
0
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2816 | lpiograd.exe | GET | — | 177.242.156.119:80 | http://177.242.156.119/ | MX | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2816 | lpiograd.exe | 50.78.167.65:7080 | — | Comcast Cable Communications, LLC | US | malicious |
2816 | lpiograd.exe | 177.242.156.119:80 | — | SERVICIO Y EQUIPO EN TELEFONÍA INTERNET Y TV S.A. DE C.V. | MX | malicious |