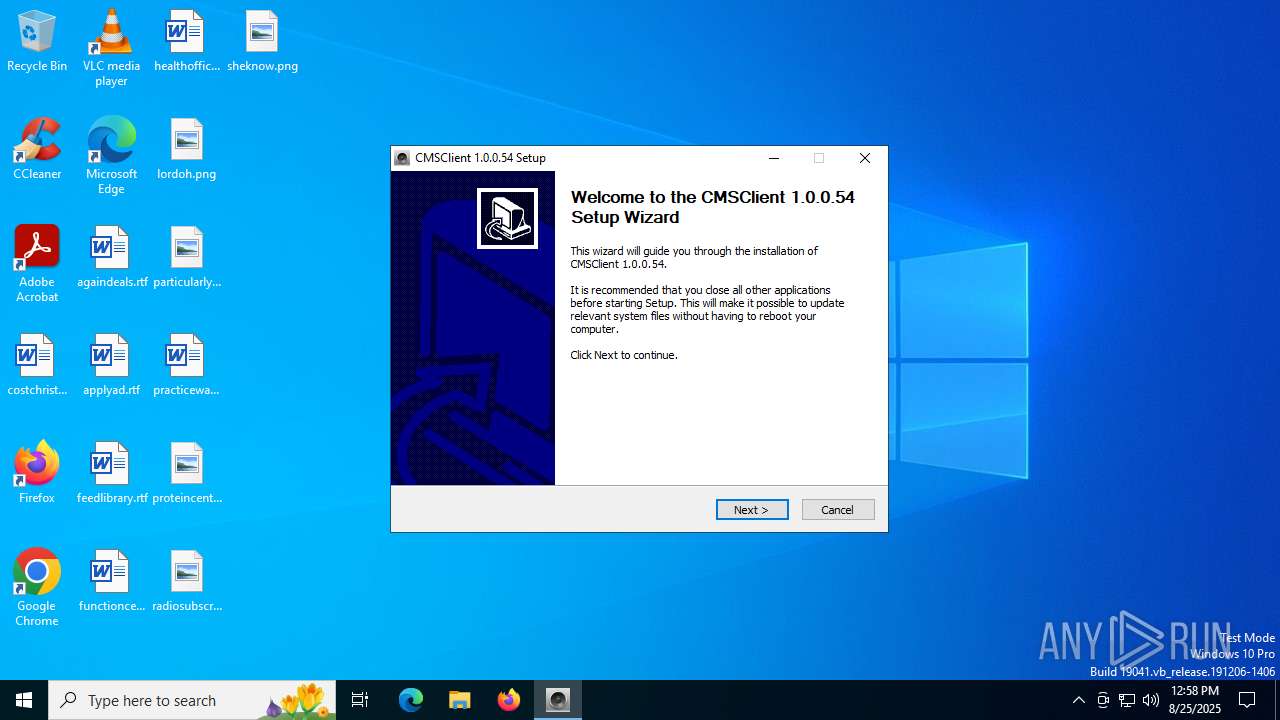
| File name: | CMSSetup_1.0.0.54.exe |
| Full analysis: | https://app.any.run/tasks/93a0b6b8-431a-4ab1-aed9-3a3f70b90703 |
| Verdict: | Malicious activity |
| Analysis date: | August 25, 2025, 12:58:05 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive, 5 sections |
| MD5: | 2671218C049621EF4FF8C4B5D9676185 |
| SHA1: | 346227900D7F985C911BD2C32320D823307F04F4 |
| SHA256: | BD1B02CE03C799DFE234FA3A57108A0908E5DC077EE5DE297C8E8387FC859CED |
| SSDEEP: | 98304:o3RKcUA4+X7quBjJDwMYYNTVK/+E0XgazTa+m75jGajfaBDyq5UpiJc9okXL8IA0:+X9sq/779h1rUtfufD6j |
MALICIOUS
No malicious indicators.SUSPICIOUS
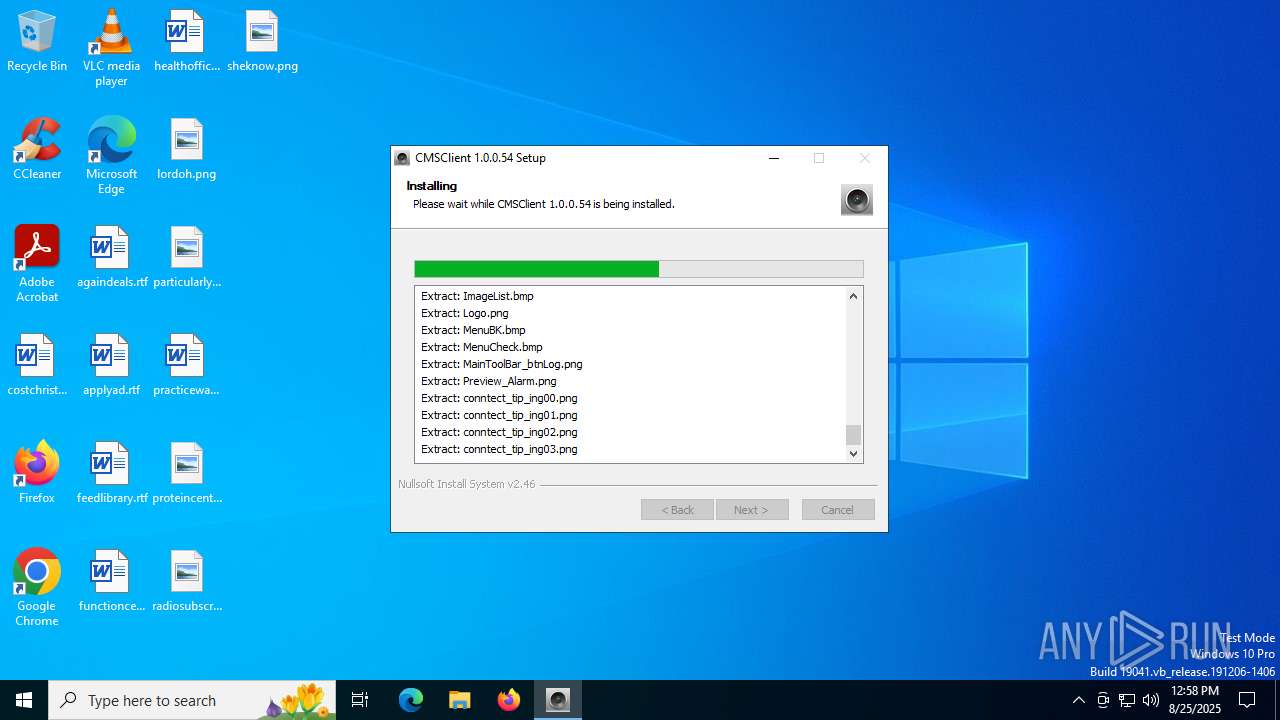
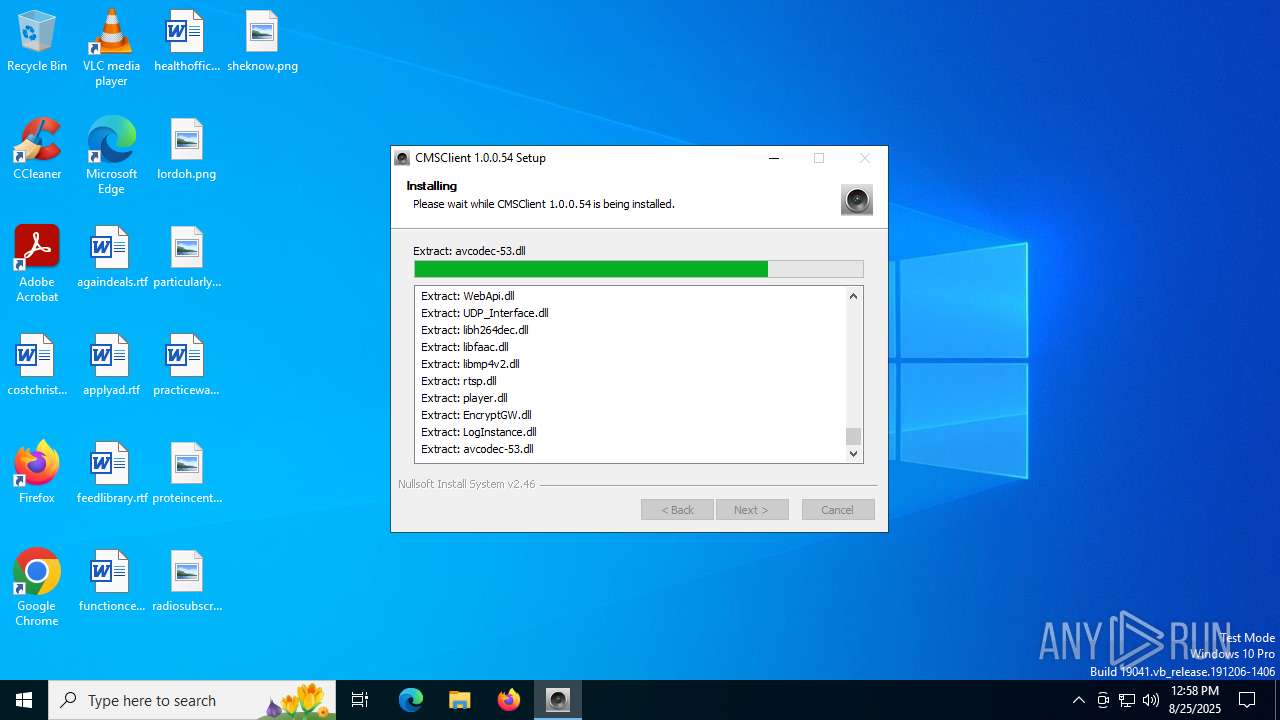
Executable content was dropped or overwritten
- CMSSetup_1.0.0.54.exe (PID: 2128)
Process drops SQLite DLL files
- CMSSetup_1.0.0.54.exe (PID: 2128)
There is functionality for taking screenshot (YARA)
- CMSSetup_1.0.0.54.exe (PID: 2128)
- CMSClient.exe (PID: 1964)
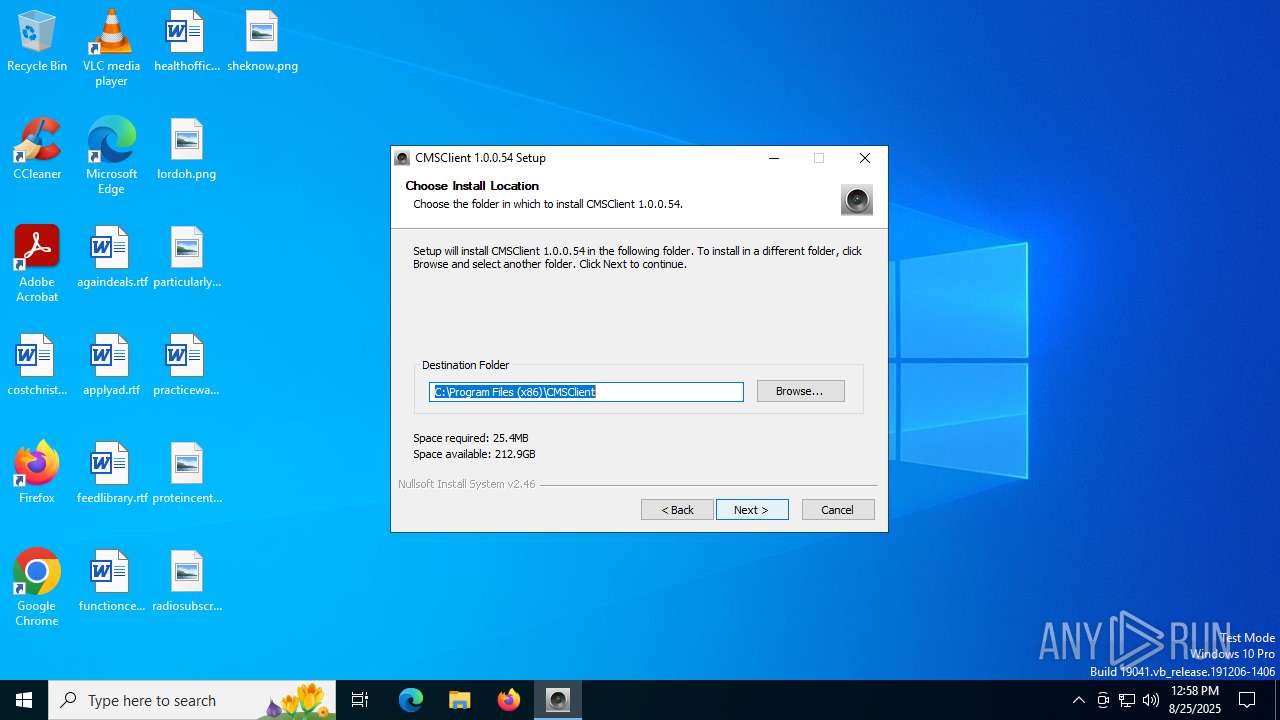
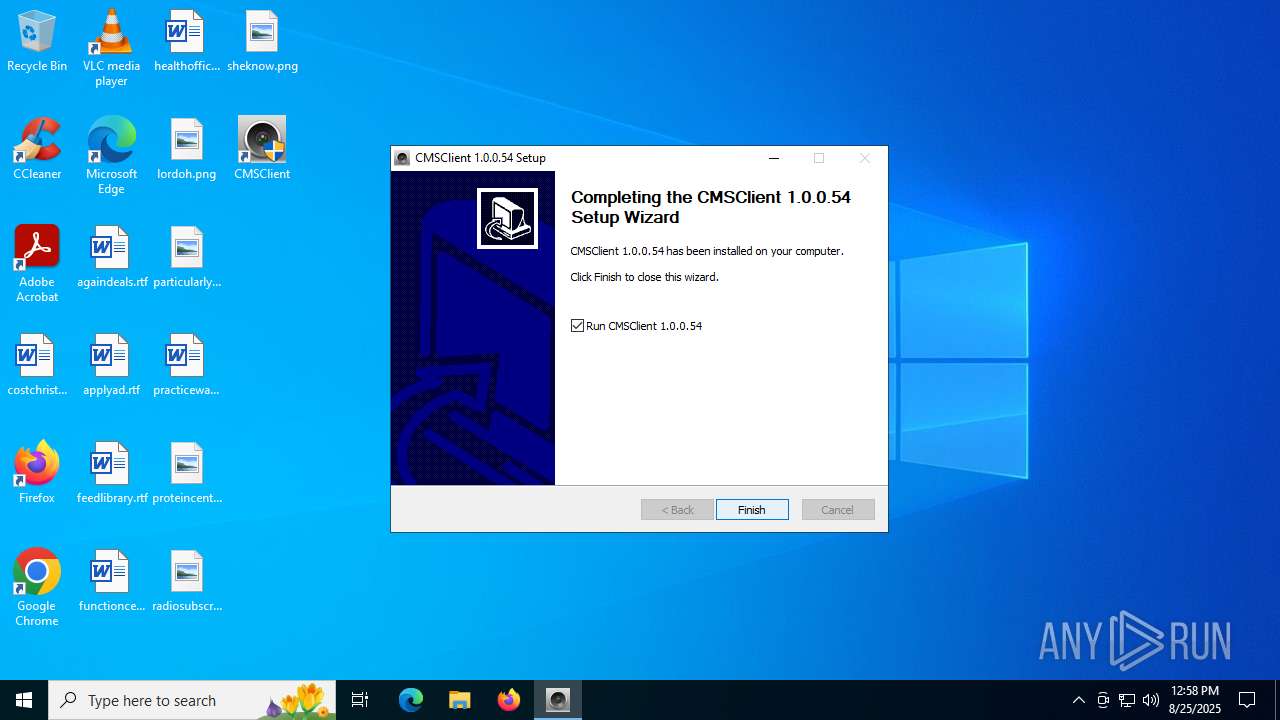
Creates a software uninstall entry
- CMSSetup_1.0.0.54.exe (PID: 2128)
- CMSClient.exe (PID: 1964)
The process drops C-runtime libraries
- CMSSetup_1.0.0.54.exe (PID: 2128)
Process drops legitimate windows executable
- CMSSetup_1.0.0.54.exe (PID: 2128)
Searches for installed software
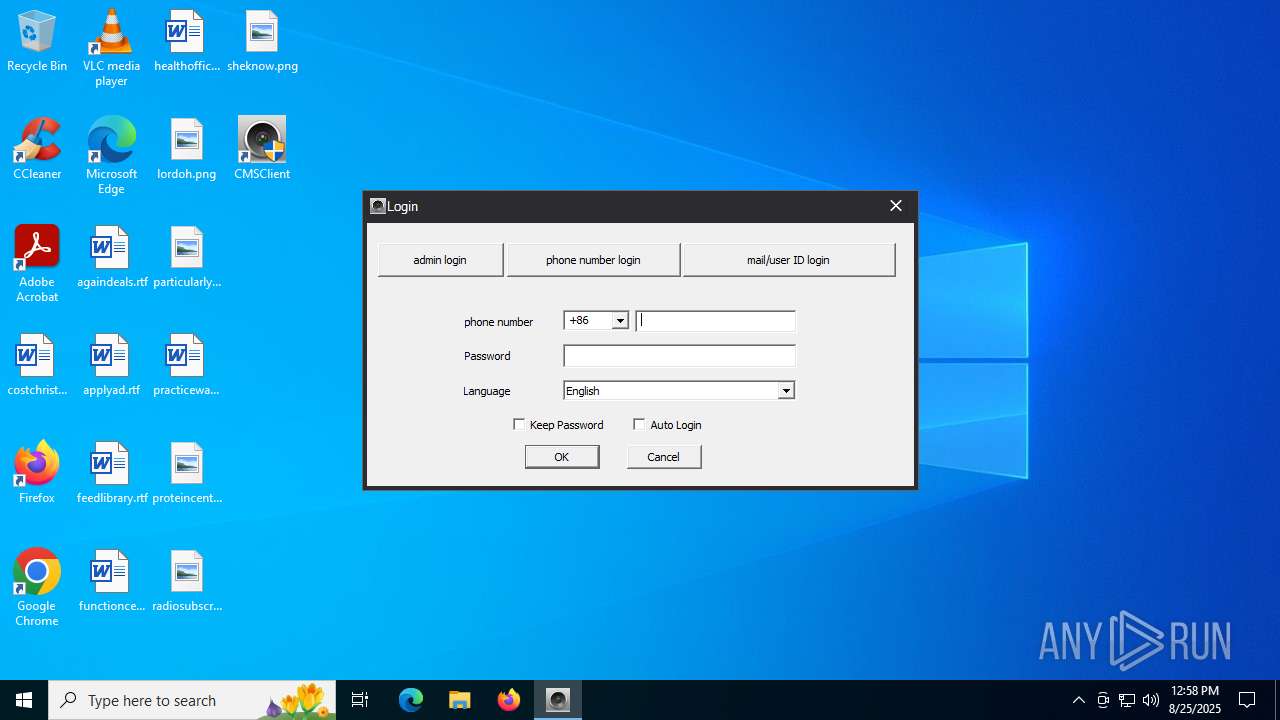
- CMSClient.exe (PID: 1964)
INFO
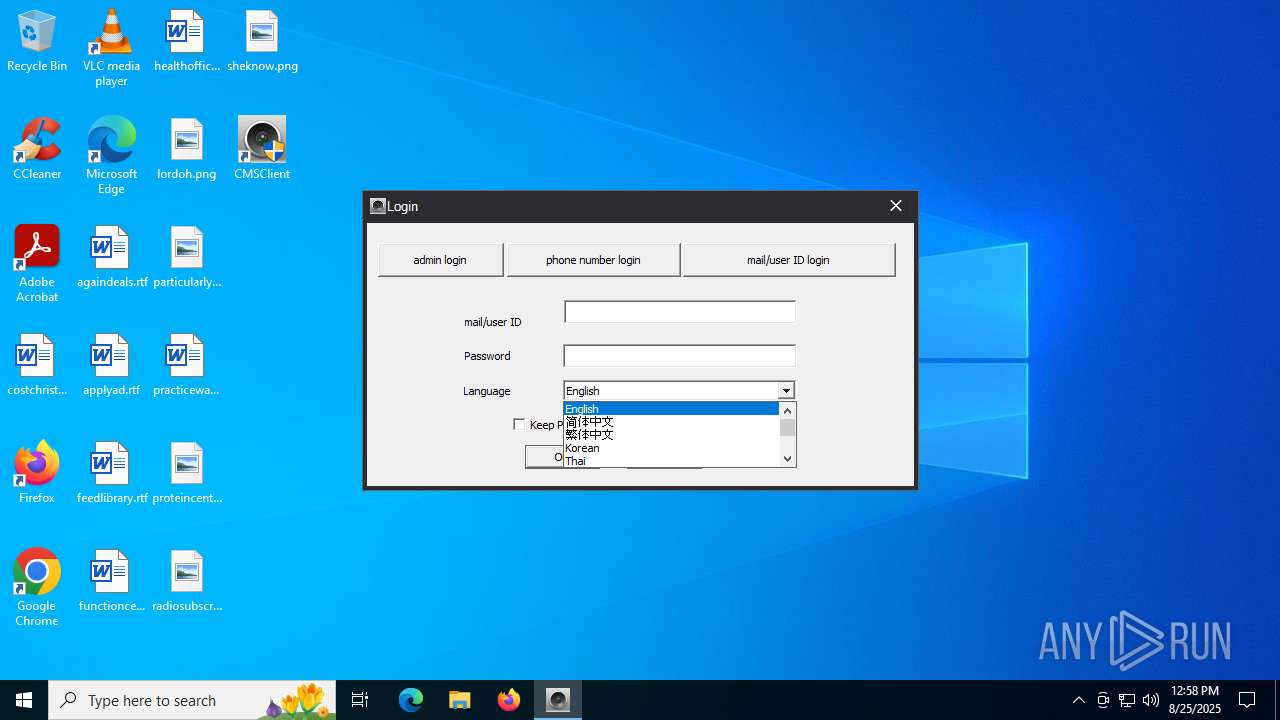
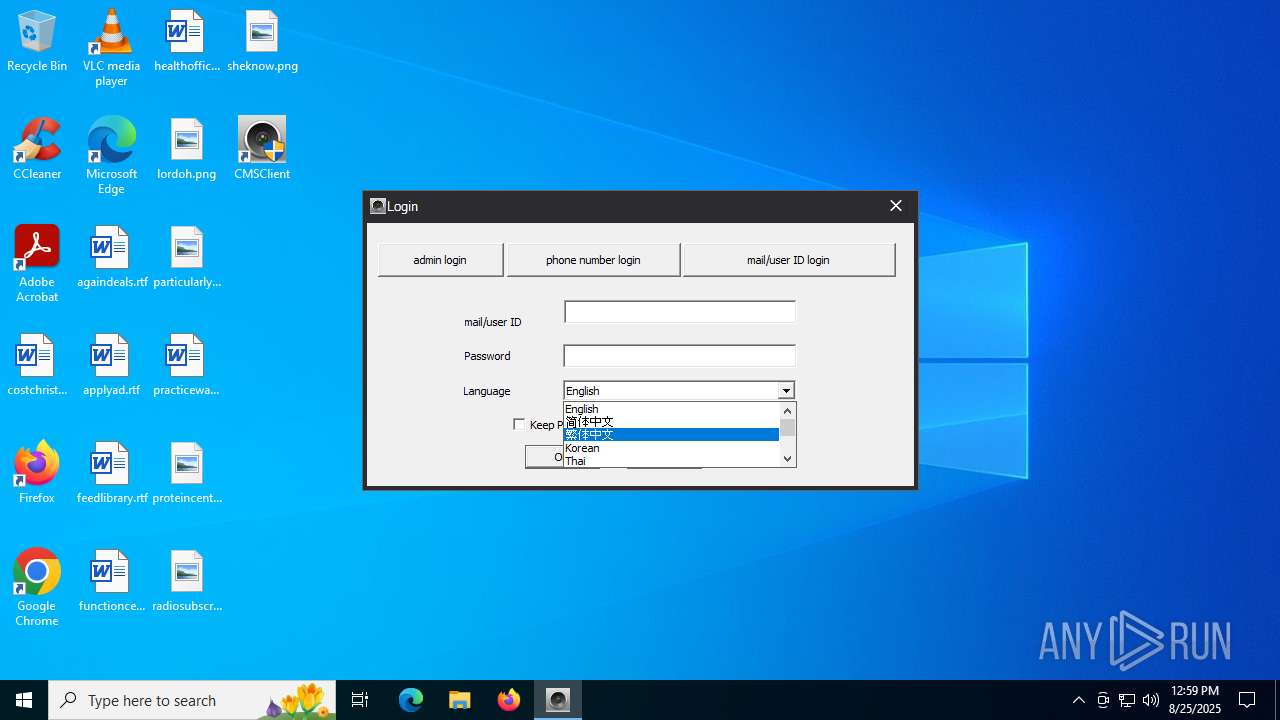
Checks supported languages
- CMSSetup_1.0.0.54.exe (PID: 2128)
- CMSClient.exe (PID: 1964)
Reads the computer name
- CMSSetup_1.0.0.54.exe (PID: 2128)
- CMSClient.exe (PID: 1964)
Create files in a temporary directory
- CMSSetup_1.0.0.54.exe (PID: 2128)
The sample compiled with chinese language support
- CMSSetup_1.0.0.54.exe (PID: 2128)
The sample compiled with english language support
- CMSSetup_1.0.0.54.exe (PID: 2128)
Creates files in the program directory
- CMSClient.exe (PID: 1964)
- CMSSetup_1.0.0.54.exe (PID: 2128)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (94.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.5) |
| .exe | | | Generic Win/DOS Executable (0.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:12:05 22:50:46+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 23552 |
| InitializedDataSize: | 119808 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x323c |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
140
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1964 | "C:\Program Files (x86)\CMSClient\CMSClient.exe" | C:\Program Files (x86)\CMSClient\CMSClient.exe | CMSSetup_1.0.0.54.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: CMS Version: 1.0.0.47 Modules
| |||||||||||||||
| 2128 | "C:\Users\admin\AppData\Local\Temp\CMSSetup_1.0.0.54.exe" | C:\Users\admin\AppData\Local\Temp\CMSSetup_1.0.0.54.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 4072 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4748 | "C:\Users\admin\AppData\Local\Temp\CMSSetup_1.0.0.54.exe" | C:\Users\admin\AppData\Local\Temp\CMSSetup_1.0.0.54.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
Total events
631
Read events
624
Write events
7
Delete events
0
Modification events
| (PID) Process: | (2128) CMSSetup_1.0.0.54.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\CMSClient |
| Operation: | write | Name: | DisplayName |
Value: CMSClient 1.0.0.54 | |||
| (PID) Process: | (2128) CMSSetup_1.0.0.54.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\CMSClient |
| Operation: | write | Name: | UninstallString |
Value: C:\Program Files (x86)\CMSClient\uninst.exe | |||
| (PID) Process: | (2128) CMSSetup_1.0.0.54.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\CMSClient |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Program Files (x86)\CMSClient\CMSClient.exe | |||
| (PID) Process: | (2128) CMSSetup_1.0.0.54.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\CMSClient |
| Operation: | write | Name: | DisplayVersion |
Value: 1.0.0.54 | |||
| (PID) Process: | (2128) CMSSetup_1.0.0.54.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\CMSClient |
| Operation: | write | Name: | NSIS:StartMenuDir |
Value: CMSClient | |||
| (PID) Process: | (2128) CMSSetup_1.0.0.54.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\CMSClient |
| Operation: | write | Name: | NSIS:Language |
Value: 1033 | |||
| (PID) Process: | (1964) CMSClient.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\CMSClient |
| Operation: | write | Name: | FeatureCode |
Value: f4c581582aba5d19133424cfd5b5fa8d | |||
Executable files
29
Suspicious files
17
Text files
89
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2128 | CMSSetup_1.0.0.54.exe | C:\Users\admin\AppData\Local\Temp\nseCADE.tmp\LangDLL.dll | executable | |
MD5:9384F4007C492D4FA040924F31C00166 | SHA256:60A964095AF1BE79F6A99B22212FEFE2D16F5A0AFD7E707D14394E4143E3F4F5 | |||
| 2128 | CMSSetup_1.0.0.54.exe | C:\Users\admin\AppData\Local\Temp\nseCADE.tmp\modern-wizard.bmp | image | |
MD5:CBE40FD2B1EC96DAEDC65DA172D90022 | SHA256:3AD2DC318056D0A2024AF1804EA741146CFC18CC404649A44610CBF8B2056CF2 | |||
| 2128 | CMSSetup_1.0.0.54.exe | C:\Program Files (x86)\CMSClient\Language\Thai.xml | xml | |
MD5:53A97FD89D68BDC2178A5DCC6D935007 | SHA256:FEF63408D5F66DB0C1A218FFA554AC76984ADC3963F5B9B115BAD45650A3CE90 | |||
| 2128 | CMSSetup_1.0.0.54.exe | C:\Program Files (x86)\CMSClient\Image\slider_Thumb2.bmp | image | |
MD5:232A8BDE1A5B7009B112DFF734A1C156 | SHA256:AEC6224552276BFD455C73D2992D0F3F10609FE161B0576170E0420A66CBAFA2 | |||
| 2128 | CMSSetup_1.0.0.54.exe | C:\Program Files (x86)\CMSClient\Buzzer\buzzer1.wav | binary | |
MD5:C2C0D5058284FC3F250C8CD11C3F967C | SHA256:BE6A82E9DFD6DA6EACFB77B4301FBD6F1ED85AF053F8785784BE65097611B0FB | |||
| 2128 | CMSSetup_1.0.0.54.exe | C:\Program Files (x86)\CMSClient\Buzzer\buzzer2.wav | binary | |
MD5:28EB56F2A972A6DFD69722665025442D | SHA256:9AA3B36A3C0C3E01D4E7DD17190A1773D4BB41993C0DDA7C11E3DF3418C49A72 | |||
| 2128 | CMSSetup_1.0.0.54.exe | C:\Program Files (x86)\CMSClient\Buzzer\buzzer3.wav | binary | |
MD5:177EAD3E1F9EC18A297F3D97761D86CA | SHA256:D74B57046A487612EFF988345DBAB9AB5B7AE4879CEE5E1BD1FBD9F7BFF2380A | |||
| 2128 | CMSSetup_1.0.0.54.exe | C:\Program Files (x86)\CMSClient\Image\splash.png | image | |
MD5:85125E61BFBE30E4AED16E286590159A | SHA256:CBD9ABD3BE4419FFD699B527879F44D234861AB6BF1A73EF5AC5C78E1B5CBB04 | |||
| 2128 | CMSSetup_1.0.0.54.exe | C:\Program Files (x86)\CMSClient\Language\Chinese Simplified.xml | xml | |
MD5:D54B8985E871ADE291EA5B99D37CE07C | SHA256:49E87AAA56151D5D3427550C37BD83424FB8FD5ECD3E57B75CA3465D15D540B6 | |||
| 2128 | CMSSetup_1.0.0.54.exe | C:\Program Files (x86)\CMSClient\Language\English.xml | xml | |
MD5:25B73381997F9CC60DAB7213C3BD8DB1 | SHA256:D8146D28F48827BD2D9C397A11E122E4A80348B45412CC5AD40667F0A672BB73 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
21
DNS requests
16
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 23.216.77.20:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4912 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6452 | SIHClient.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6452 | SIHClient.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5944 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4196 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 23.216.77.20:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 69.192.161.161:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 255.255.255.255:8899 | — | — | — | unknown |
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |