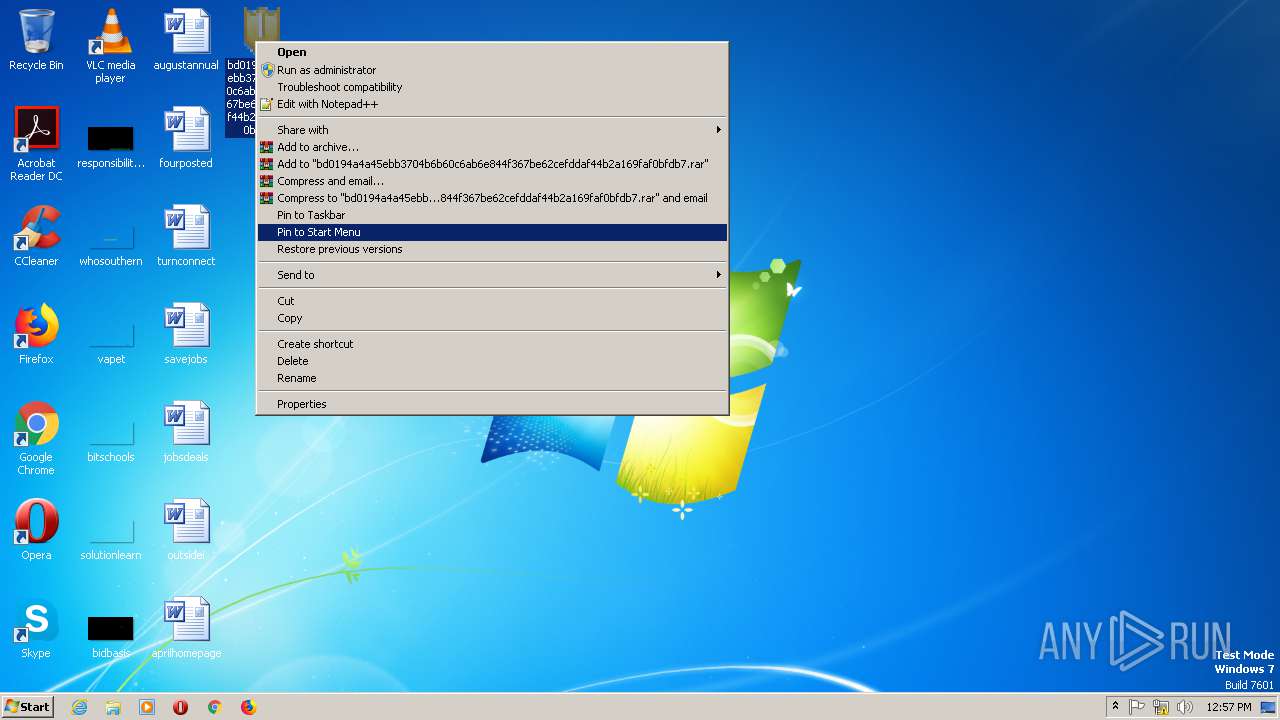
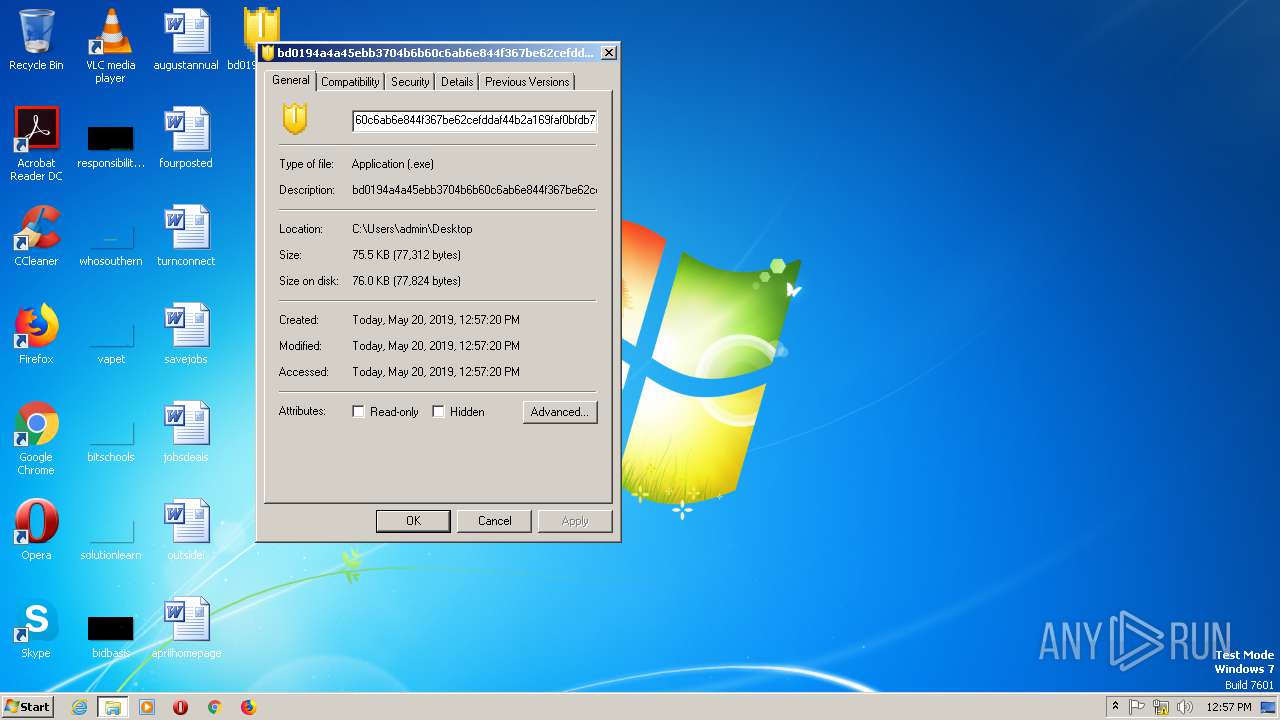
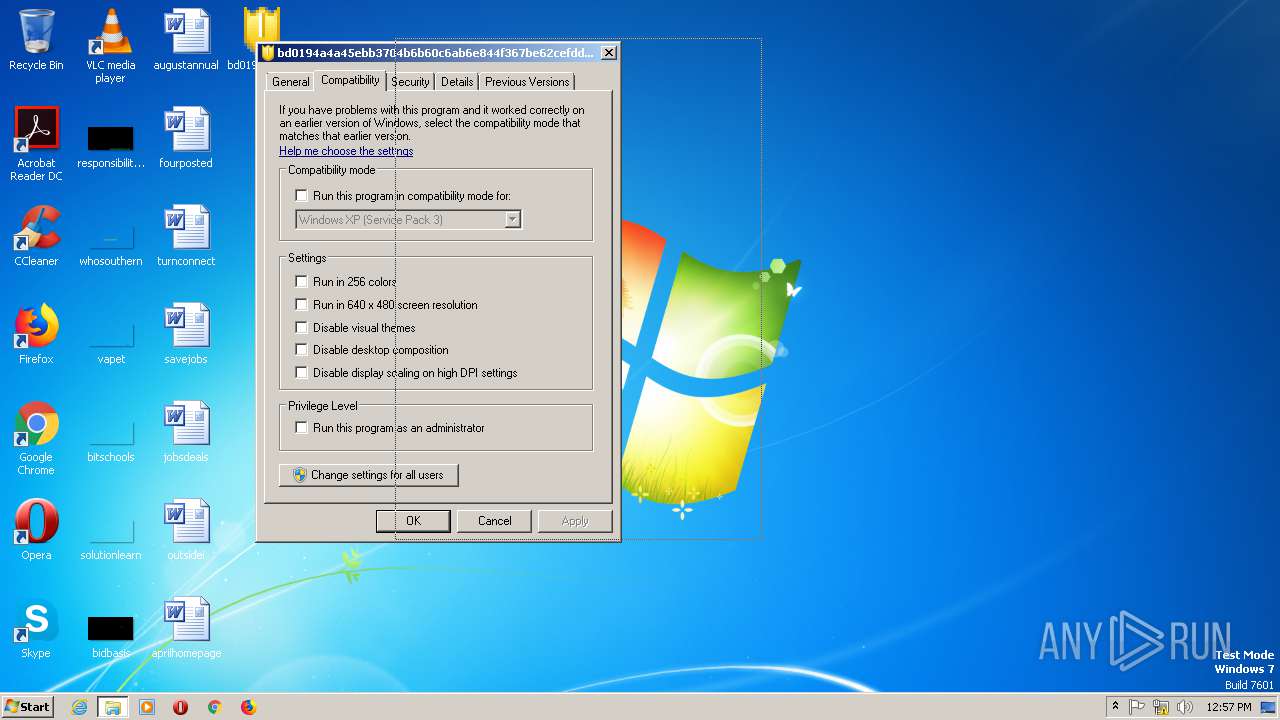
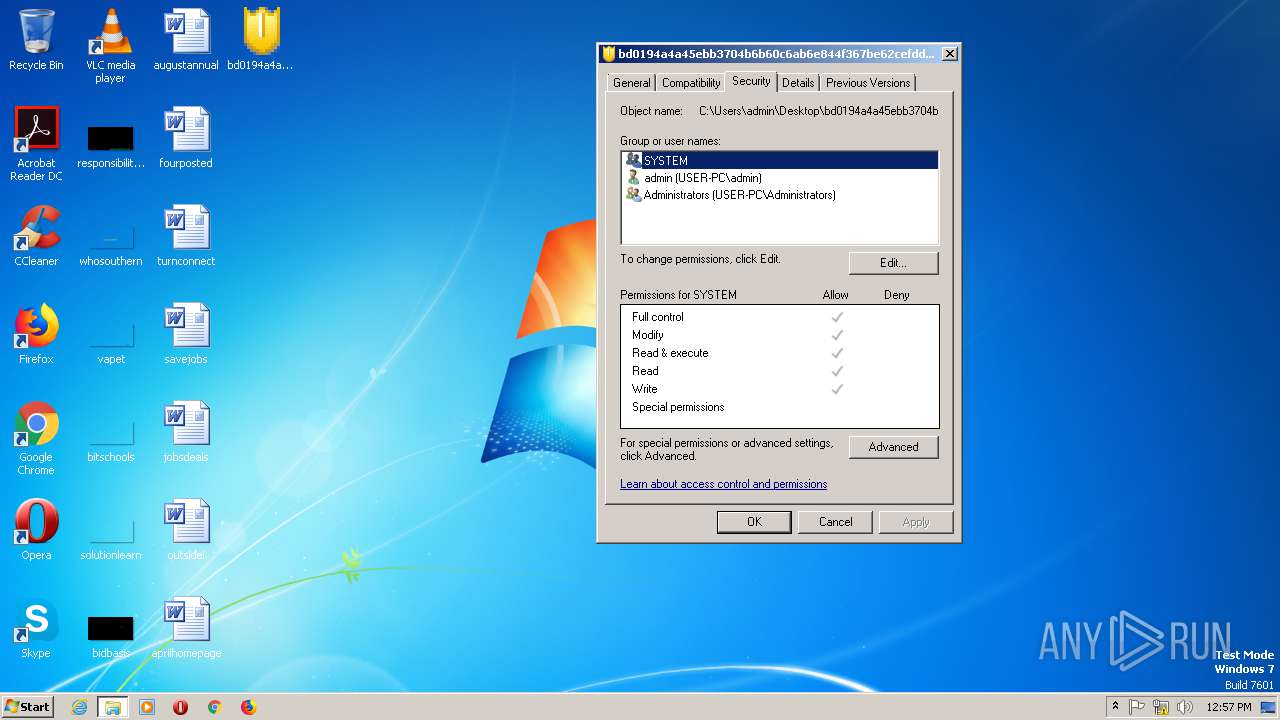
| File name: | bd0194a4a45ebb3704b6b60c6ab6e844f367be62cefddaf44b2a169faf0bfdb7.exe |
| Full analysis: | https://app.any.run/tasks/09d4cd50-c952-4b25-8b28-0e6bbcf893e4 |
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2019, 12:56:55 |
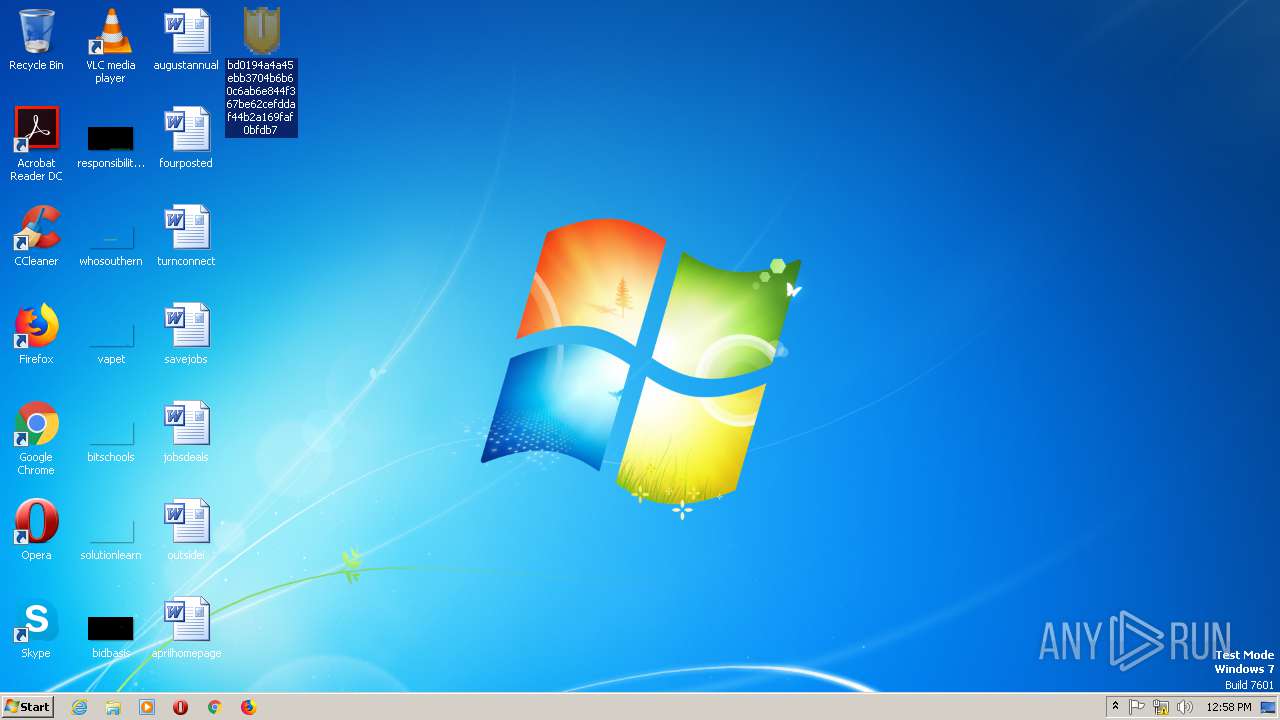
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 8C35B67FD989043499A4F71E9056CD25 |
| SHA1: | D556798D27C6F9A54127DE72C1219B47EBD9E26D |
| SHA256: | BD0194A4A45EBB3704B6B60C6AB6E844F367BE62CEFDDAF44B2A169FAF0BFDB7 |
| SSDEEP: | 1536:dtLr9uqykPyM+5VesYMQ/JQitpB+DDLBnek:dZr1+5VBgQitvaxnek |
MALICIOUS
Changes the autorun value in the registry
- bd0194a4a45ebb3704b6b60c6ab6e844f367be62cefddaf44b2a169faf0bfdb7.exe (PID: 980)
Disables Windows System Restore
- winsvcs.exe (PID: 580)
Changes Security Center notification settings
- winsvcs.exe (PID: 580)
Connects to CnC server
- winsvcs.exe (PID: 580)
SUSPICIOUS
Executable content was dropped or overwritten
- bd0194a4a45ebb3704b6b60c6ab6e844f367be62cefddaf44b2a169faf0bfdb7.exe (PID: 980)
- winsvcs.exe (PID: 580)
Starts itself from another location
- bd0194a4a45ebb3704b6b60c6ab6e844f367be62cefddaf44b2a169faf0bfdb7.exe (PID: 980)
Creates files in the user directory
- winsvcs.exe (PID: 580)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:11:04 06:33:13+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 26624 |
| InitializedDataSize: | 52736 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1735 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
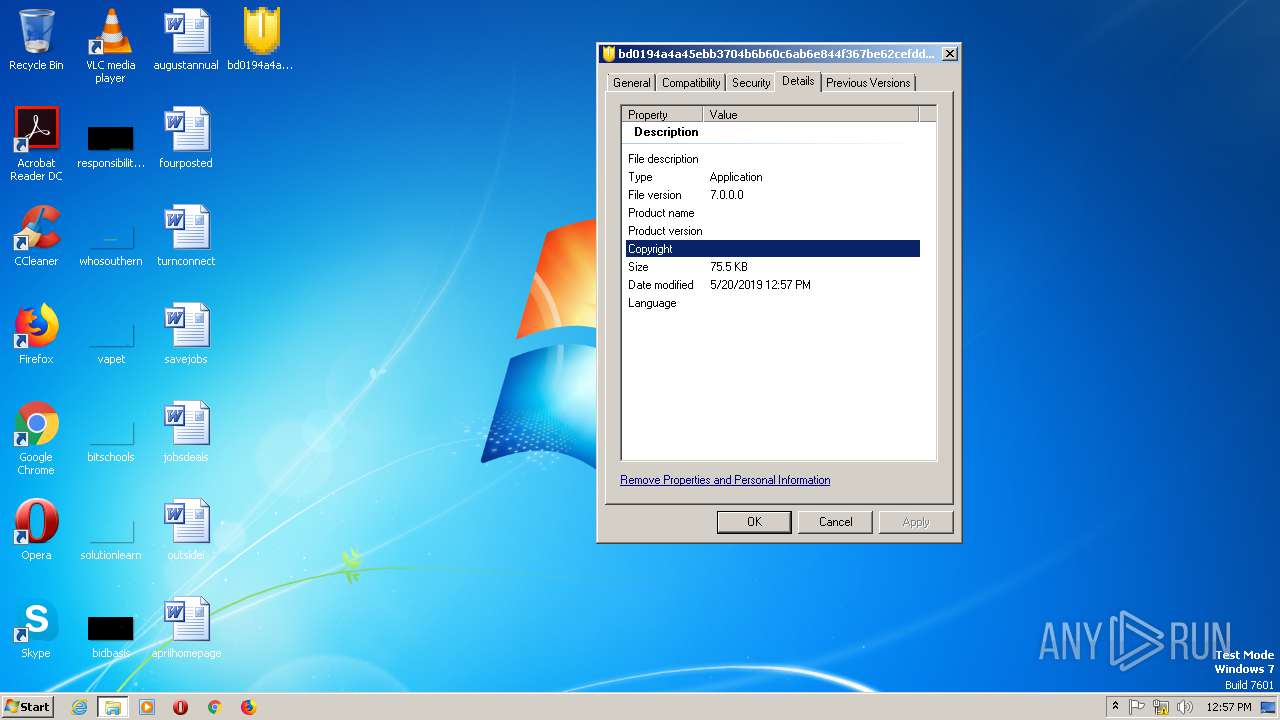
| FileVersionNumber: | 7.0.0.0 |
| ProductVersionNumber: | 3.0.0.0 |
| FileFlagsMask: | 0x004f |
| FileFlags: | (none) |
| FileOS: | Unknown (0x40534) |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Unknown (457A) |
| CharacterSet: | Unknown (A56B) |
| InternalName: | jjoru.enu |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 04-Nov-2017 05:33:13 |
| Detected languages: |
|
| InternalName: | jjoru.enu |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 04-Nov-2017 05:33:13 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000067B0 | 0x00006800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.63091 |
.rdata | 0x00008000 | 0x00001EF7 | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.34623 |
.data | 0x0000A000 | 0x0000A4DC | 0x00008C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.88585 |
.rsrc | 0x00015000 | 0x000007FC | 0x00000800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.31236 |
.reloc | 0x00016000 | 0x00000D46 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 4.2031 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 2.94045 | 236 | UNKNOWN | French - France | RT_VERSION |
101 | 2.99443 | 274 | UNKNOWN | French - France | RT_DIALOG |
128 | 1.91924 | 20 | UNKNOWN | French - France | RT_GROUP_ICON |
366 | 2 | 8 | UNKNOWN | French - France | RT_ACCELERATOR |
Imports
KERNEL32.dll |
USER32.dll |
ole32.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
_MyFunc1@4 | 1 | 0x00001230 |
Total processes
32
Monitored processes
2
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 580 | C:\Users\admin\4960650049563030\winsvcs.exe | C:\Users\admin\4960650049563030\winsvcs.exe | bd0194a4a45ebb3704b6b60c6ab6e844f367be62cefddaf44b2a169faf0bfdb7.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 980 | "C:\Users\admin\Desktop\bd0194a4a45ebb3704b6b60c6ab6e844f367be62cefddaf44b2a169faf0bfdb7.exe" | C:\Users\admin\Desktop\bd0194a4a45ebb3704b6b60c6ab6e844f367be62cefddaf44b2a169faf0bfdb7.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
34
Read events
11
Write events
23
Delete events
0
Modification events
| (PID) Process: | (980) bd0194a4a45ebb3704b6b60c6ab6e844f367be62cefddaf44b2a169faf0bfdb7.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Microsoft Windows Services |
Value: C:\Users\admin\4960650049563030\winsvcs.exe | |||
| (PID) Process: | (980) bd0194a4a45ebb3704b6b60c6ab6e844f367be62cefddaf44b2a169faf0bfdb7.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Microsoft Windows Services |
Value: C:\Users\admin\4960650049563030\winsvcs.exe | |||
| (PID) Process: | (580) winsvcs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Security Center |
| Operation: | write | Name: | AntiVirusOverride |
Value: 1 | |||
| (PID) Process: | (580) winsvcs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Security Center |
| Operation: | write | Name: | UpdatesOverride |
Value: 1 | |||
| (PID) Process: | (580) winsvcs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Security Center |
| Operation: | write | Name: | FirewallOverride |
Value: 1 | |||
| (PID) Process: | (580) winsvcs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Security Center |
| Operation: | write | Name: | AntiVirusDisableNotify |
Value: 1 | |||
| (PID) Process: | (580) winsvcs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Security Center |
| Operation: | write | Name: | UpdatesDisableNotify |
Value: 1 | |||
| (PID) Process: | (580) winsvcs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Security Center |
| Operation: | write | Name: | AutoUpdateDisableNotify |
Value: 1 | |||
| (PID) Process: | (580) winsvcs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Security Center |
| Operation: | write | Name: | FirewallDisableNotify |
Value: 1 | |||
| (PID) Process: | (580) winsvcs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Windows NT\CurrentVersion\SystemRestore |
| Operation: | write | Name: | DisableSR |
Value: 1 | |||
Executable files
2
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 980 | bd0194a4a45ebb3704b6b60c6ab6e844f367be62cefddaf44b2a169faf0bfdb7.exe | C:\Users\admin\4960650049563030\winsvcs.exe | executable | |
MD5:— | SHA256:— | |||
| 580 | winsvcs.exe | C:\Users\admin\AppData\Local\Temp\Windows Archive Manager.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
4
DNS requests
83
Threats
16
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
580 | winsvcs.exe | GET | — | 71.209.210.140:80 | http://ssofhoseuegsgrfnu.ru/tldr.php?newinf=1 | US | — | — | malicious |
580 | winsvcs.exe | GET | — | 92.63.197.48:80 | http://92.63.197.48/tldr.php?newinf=1 | RU | — | — | malicious |
580 | winsvcs.exe | GET | — | 92.63.197.48:80 | http://slpsrgpsrhojifdij.ru/tldr.php?newinf=1 | RU | — | — | malicious |
580 | winsvcs.exe | GET | 404 | 208.100.26.251:80 | http://ssofhoseuegsgrfnj.in/tldr.php?newinf=1 | US | html | 178 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
580 | winsvcs.exe | 71.209.210.140:80 | ssofhoseuegsgrfnu.ru | Qwest Communications Company, LLC | US | malicious |
580 | winsvcs.exe | 92.63.197.48:80 | slpsrgpsrhojifdij.ru | — | RU | malicious |
580 | winsvcs.exe | 208.100.26.251:80 | ssofhoseuegsgrfnj.in | Steadfast | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ssofhoseuegsgrfnu.ru |
| malicious |
slpsrgpsrhojifdij.ru |
| malicious |
aiiaiafrzrueuedur.ru |
| malicious |
fuaiuebndieufeufu.ru |
| unknown |
eiifngjfksisiufjf.ru |
| unknown |
eoroooskfogihisrg.ru |
| malicious |
noeuaoenriusfiruu.ru |
| malicious |
iuirshriuisruruuf.ru |
| malicious |
afeifieuuufufufuf.ru |
| malicious |
srndndubsbsifurfd.ru |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
368 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
368 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
368 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
368 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
368 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
368 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
368 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
368 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
368 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
368 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |