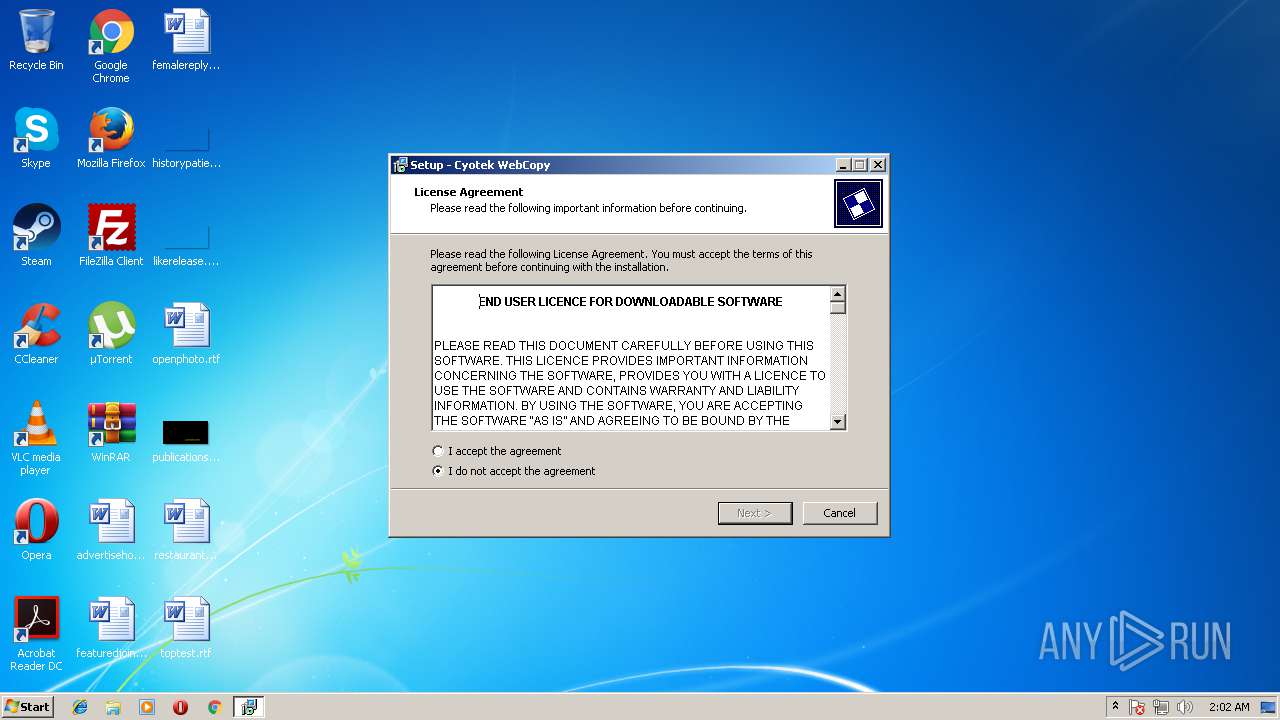
| File name: | setup-cyowcopy-1.5.0-build-516.exe |
| Full analysis: | https://app.any.run/tasks/0c0a4d14-1f7f-40d6-a191-f2863abd62f0 |
| Verdict: | Malicious activity |
| Analysis date: | August 19, 2018, 01:02:32 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | D50AE8D1FB8A404AEBA381821A246CAC |
| SHA1: | 84D74804B40FF643606959A5320FB1B31CCA1033 |
| SHA256: | BCE4D850EA31BC5A539810096A960BC13DA6B4155E3AE88F1C836ECF1641857D |
| SSDEEP: | 98304:mB6QKVFErqBS+N0eCaGh+4mTUoR/j5BQYptlhrZLlwlqLxjc:m1KVFErqBS+NBo+Zj/jbQYXlhhlGqLxY |
MALICIOUS
Loads dropped or rewritten executable
- mscorsvw.exe (PID: 1704)
- mscorsvw.exe (PID: 3392)
- mscorsvw.exe (PID: 3340)
- mscorsvw.exe (PID: 2360)
- mscorsvw.exe (PID: 2364)
- mscorsvw.exe (PID: 3384)
- mscorsvw.exe (PID: 1592)
- mscorsvw.exe (PID: 2784)
- mscorsvw.exe (PID: 1100)
- mscorsvw.exe (PID: 592)
- mscorsvw.exe (PID: 2492)
- mscorsvw.exe (PID: 2672)
- mscorsvw.exe (PID: 3140)
- mscorsvw.exe (PID: 3064)
- mscorsvw.exe (PID: 3972)
- mscorsvw.exe (PID: 2160)
- mscorsvw.exe (PID: 3460)
- mscorsvw.exe (PID: 1660)
- mscorsvw.exe (PID: 3016)
- mscorsvw.exe (PID: 1940)
- mscorsvw.exe (PID: 3124)
- mscorsvw.exe (PID: 2160)
- mscorsvw.exe (PID: 2428)
- mscorsvw.exe (PID: 3752)
- mscorsvw.exe (PID: 3508)
- mscorsvw.exe (PID: 1932)
- mscorsvw.exe (PID: 2084)
- mscorsvw.exe (PID: 2224)
- mscorsvw.exe (PID: 2596)
- mscorsvw.exe (PID: 3208)
- mscorsvw.exe (PID: 3312)
- mscorsvw.exe (PID: 1648)
- mscorsvw.exe (PID: 3612)
- mscorsvw.exe (PID: 2344)
- mscorsvw.exe (PID: 1572)
- mscorsvw.exe (PID: 1484)
- mscorsvw.exe (PID: 1616)
- mscorsvw.exe (PID: 3440)
- mscorsvw.exe (PID: 1732)
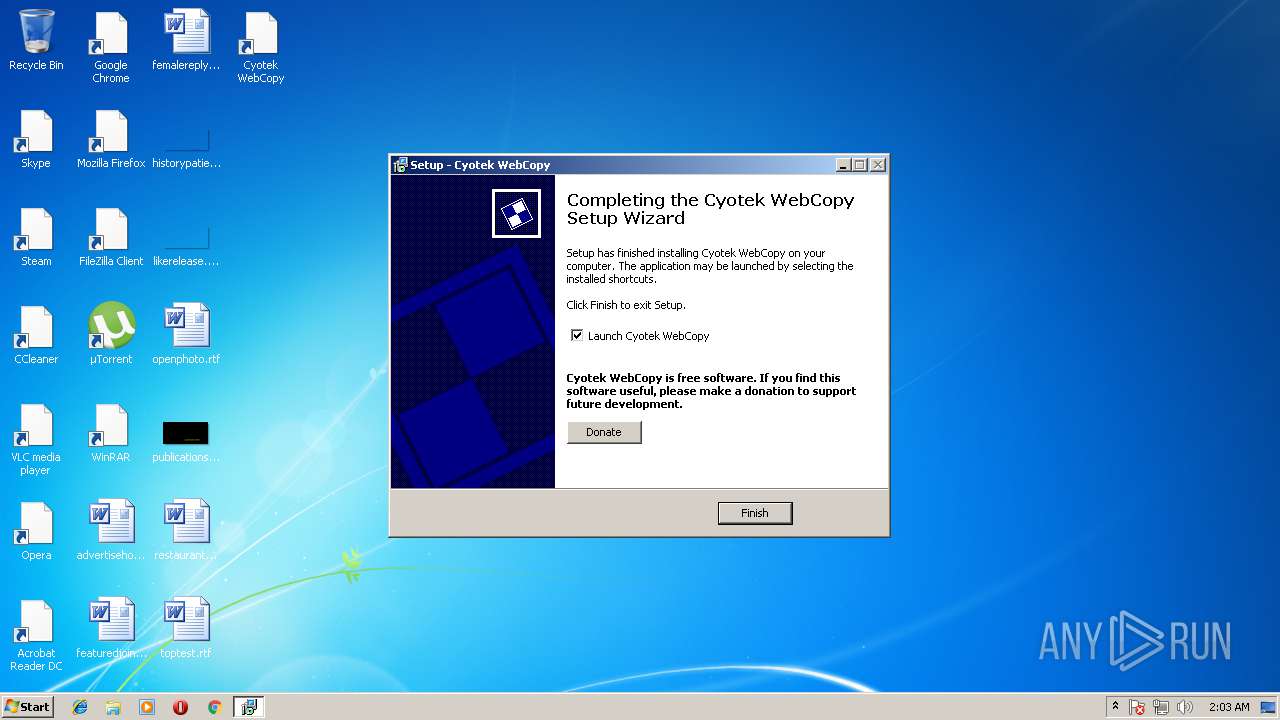
- cyowcopy.exe (PID: 4068)
Application was dropped or rewritten from another process
- cyowcopy.exe (PID: 4068)
SUSPICIOUS
Reads the Windows organization settings
- setup-cyowcopy-1.5.0-build-516.tmp (PID: 2472)
Modifies the open verb of a shell class
- setup-cyowcopy-1.5.0-build-516.tmp (PID: 2472)
Reads Windows owner settings
- setup-cyowcopy-1.5.0-build-516.tmp (PID: 2472)
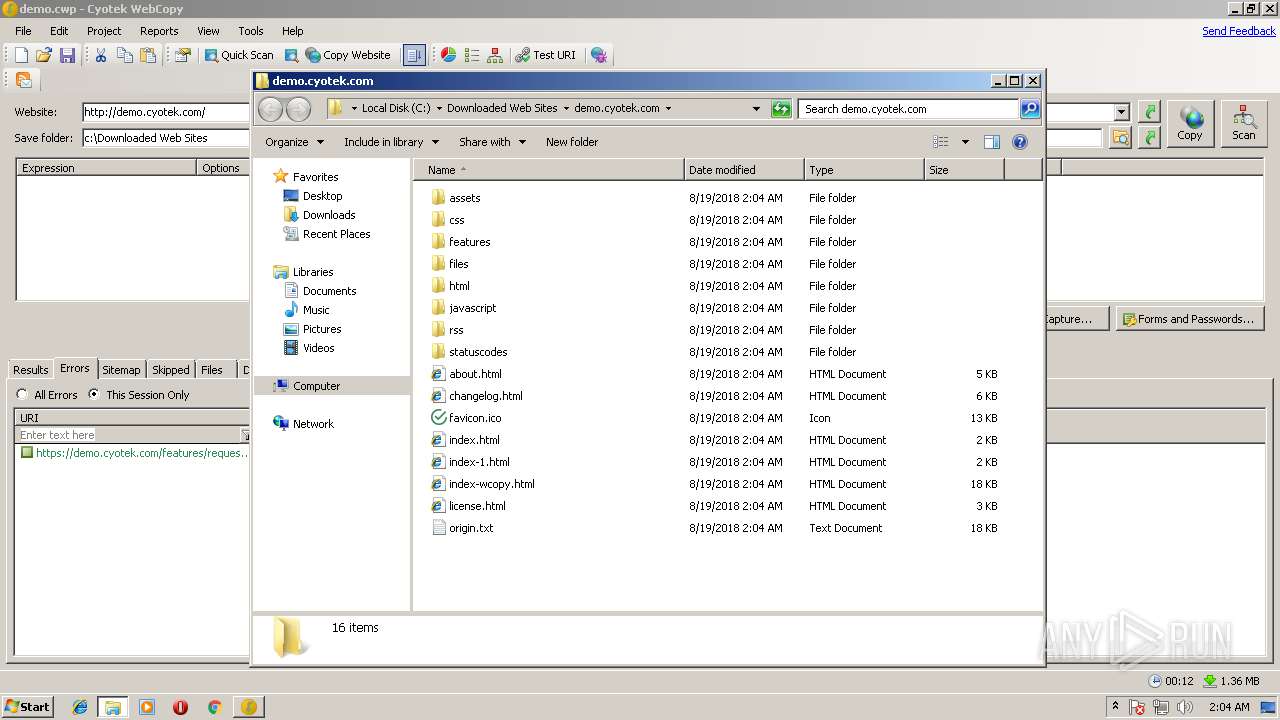
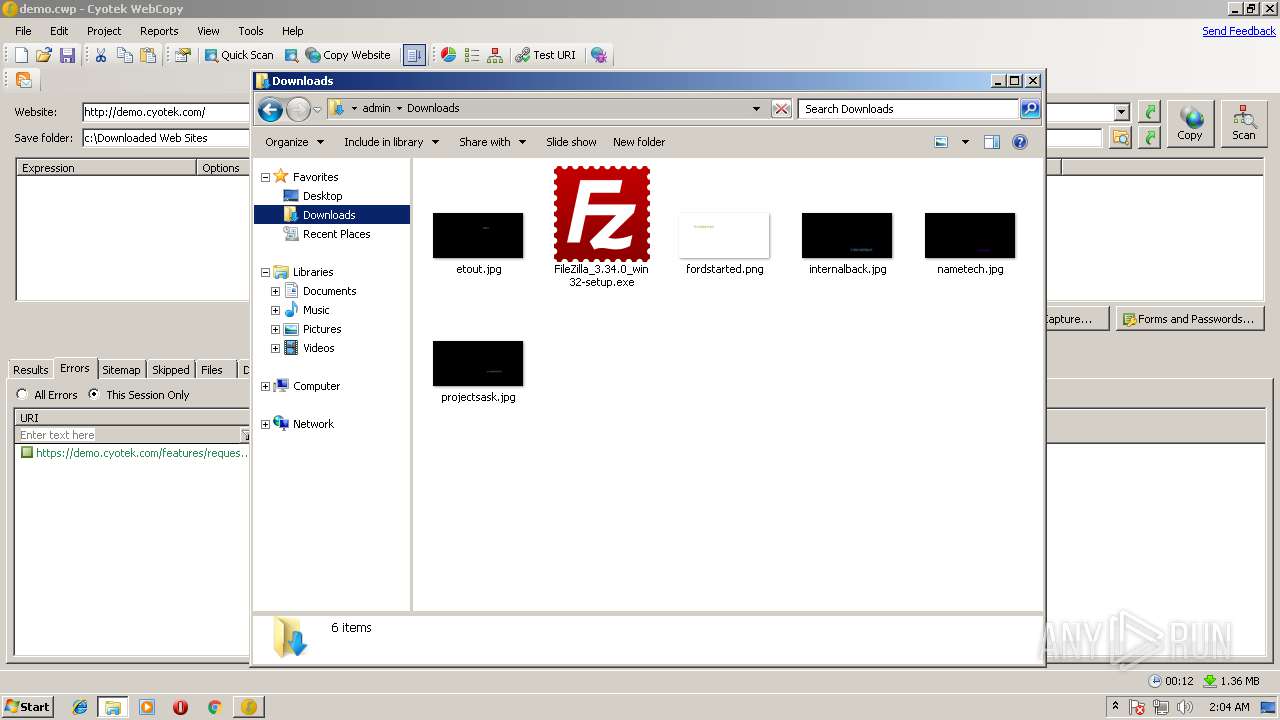
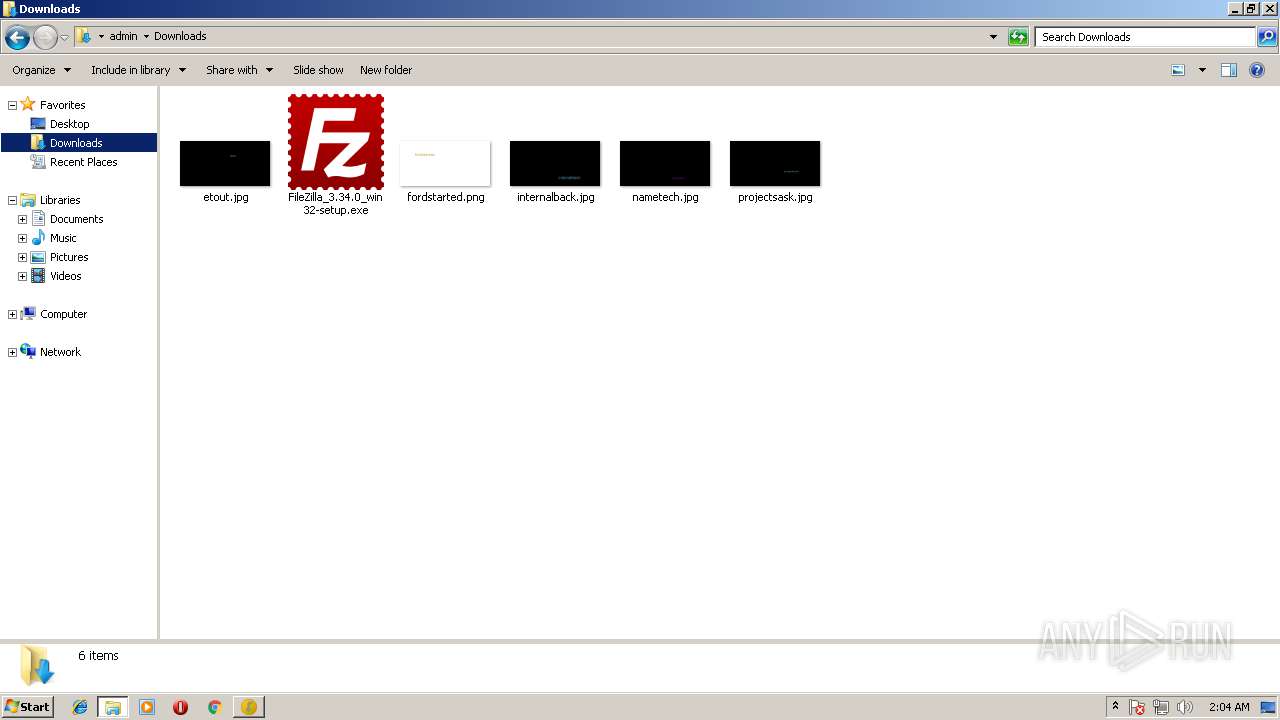
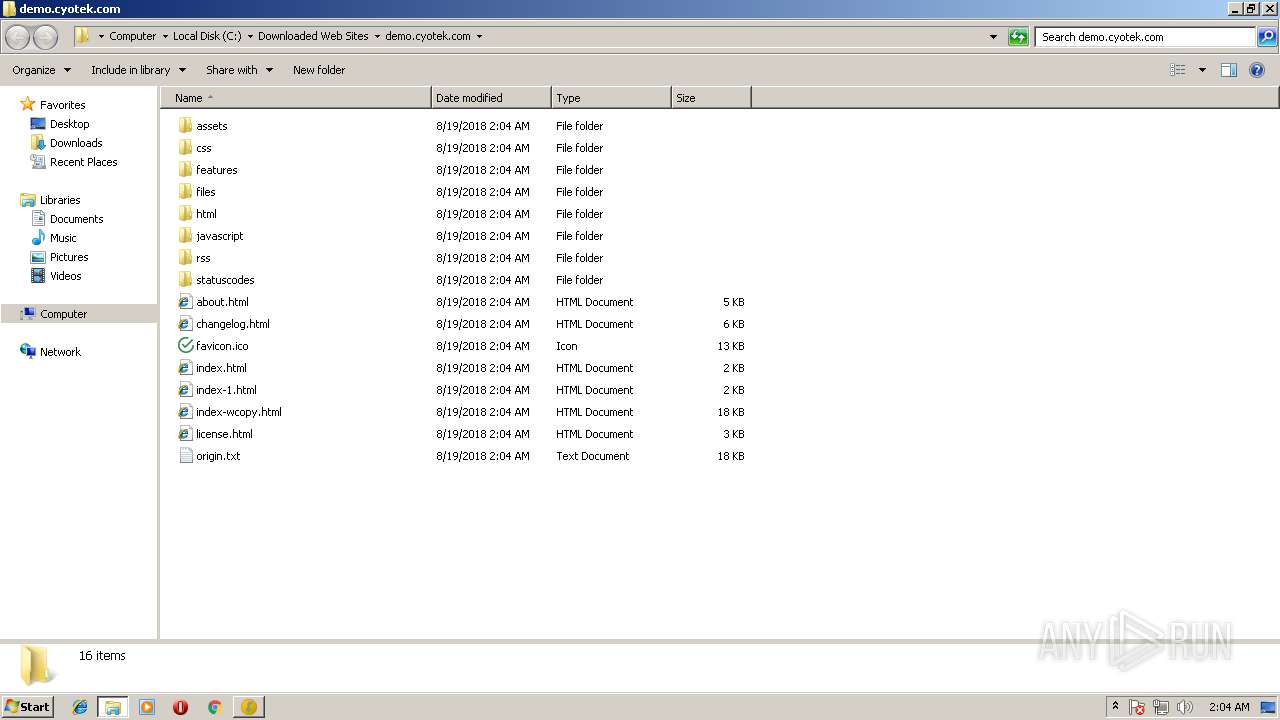
Creates files in the user directory
- setup-cyowcopy-1.5.0-build-516.tmp (PID: 2472)
- cyowcopy.exe (PID: 4068)
Executable content was dropped or overwritten
- setup-cyowcopy-1.5.0-build-516.exe (PID: 384)
- setup-cyowcopy-1.5.0-build-516.tmp (PID: 2472)
- setup-cyowcopy-1.5.0-build-516.exe (PID: 3924)
- mscorsvw.exe (PID: 1704)
- mscorsvw.exe (PID: 2360)
- mscorsvw.exe (PID: 2364)
- mscorsvw.exe (PID: 3340)
- mscorsvw.exe (PID: 1100)
- mscorsvw.exe (PID: 2784)
- mscorsvw.exe (PID: 592)
- mscorsvw.exe (PID: 3384)
- mscorsvw.exe (PID: 1592)
- mscorsvw.exe (PID: 3064)
- mscorsvw.exe (PID: 3140)
- mscorsvw.exe (PID: 3972)
- mscorsvw.exe (PID: 2672)
- mscorsvw.exe (PID: 2492)
- mscorsvw.exe (PID: 2160)
- mscorsvw.exe (PID: 3460)
- mscorsvw.exe (PID: 1660)
- mscorsvw.exe (PID: 1616)
- mscorsvw.exe (PID: 1940)
- mscorsvw.exe (PID: 3124)
- mscorsvw.exe (PID: 3016)
- mscorsvw.exe (PID: 2160)
- mscorsvw.exe (PID: 3508)
- mscorsvw.exe (PID: 2428)
- mscorsvw.exe (PID: 3752)
- mscorsvw.exe (PID: 2224)
- mscorsvw.exe (PID: 1932)
- mscorsvw.exe (PID: 2344)
- mscorsvw.exe (PID: 3208)
- mscorsvw.exe (PID: 2596)
- mscorsvw.exe (PID: 2084)
- mscorsvw.exe (PID: 3612)
- mscorsvw.exe (PID: 1484)
- mscorsvw.exe (PID: 1648)
- mscorsvw.exe (PID: 1732)
Creates files in the Windows directory
- ngen.exe (PID: 3112)
- mscorsvw.exe (PID: 1704)
- mscorsvw.exe (PID: 2360)
- mscorsvw.exe (PID: 2364)
- mscorsvw.exe (PID: 3340)
- mscorsvw.exe (PID: 3384)
- mscorsvw.exe (PID: 1100)
- mscorsvw.exe (PID: 592)
- mscorsvw.exe (PID: 2784)
- mscorsvw.exe (PID: 3064)
- mscorsvw.exe (PID: 3140)
- mscorsvw.exe (PID: 3972)
- mscorsvw.exe (PID: 2672)
- mscorsvw.exe (PID: 2160)
- mscorsvw.exe (PID: 3460)
- mscorsvw.exe (PID: 1660)
- mscorsvw.exe (PID: 1616)
- mscorsvw.exe (PID: 2492)
- mscorsvw.exe (PID: 3016)
- mscorsvw.exe (PID: 3124)
- mscorsvw.exe (PID: 1940)
- mscorsvw.exe (PID: 2160)
- mscorsvw.exe (PID: 3508)
- mscorsvw.exe (PID: 1932)
- mscorsvw.exe (PID: 2428)
- mscorsvw.exe (PID: 2224)
- mscorsvw.exe (PID: 2084)
- mscorsvw.exe (PID: 2596)
- mscorsvw.exe (PID: 3752)
- ngen.exe (PID: 3244)
- mscorsvw.exe (PID: 1648)
- mscorsvw.exe (PID: 2344)
- mscorsvw.exe (PID: 3208)
- mscorsvw.exe (PID: 3612)
- ngen.exe (PID: 1872)
- mscorsvw.exe (PID: 1484)
- ngen.exe (PID: 2576)
- mscorsvw.exe (PID: 1732)
- mscorsvw.exe (PID: 1592)
Removes files from Windows directory
- mscorsvw.exe (PID: 1704)
- mscorsvw.exe (PID: 2360)
- mscorsvw.exe (PID: 2364)
- mscorsvw.exe (PID: 3340)
- mscorsvw.exe (PID: 1100)
- mscorsvw.exe (PID: 2784)
- mscorsvw.exe (PID: 3384)
- mscorsvw.exe (PID: 1592)
- mscorsvw.exe (PID: 3064)
- mscorsvw.exe (PID: 3140)
- mscorsvw.exe (PID: 3972)
- mscorsvw.exe (PID: 2672)
- mscorsvw.exe (PID: 592)
- mscorsvw.exe (PID: 2492)
- mscorsvw.exe (PID: 2160)
- mscorsvw.exe (PID: 3460)
- mscorsvw.exe (PID: 1660)
- mscorsvw.exe (PID: 1940)
- mscorsvw.exe (PID: 3124)
- mscorsvw.exe (PID: 1616)
- mscorsvw.exe (PID: 3016)
- mscorsvw.exe (PID: 2160)
- mscorsvw.exe (PID: 2428)
- mscorsvw.exe (PID: 3508)
- mscorsvw.exe (PID: 3752)
- mscorsvw.exe (PID: 2224)
- mscorsvw.exe (PID: 1932)
- mscorsvw.exe (PID: 2344)
- mscorsvw.exe (PID: 3208)
- mscorsvw.exe (PID: 2596)
- mscorsvw.exe (PID: 2084)
- mscorsvw.exe (PID: 3612)
- mscorsvw.exe (PID: 1484)
- mscorsvw.exe (PID: 1648)
- mscorsvw.exe (PID: 1732)
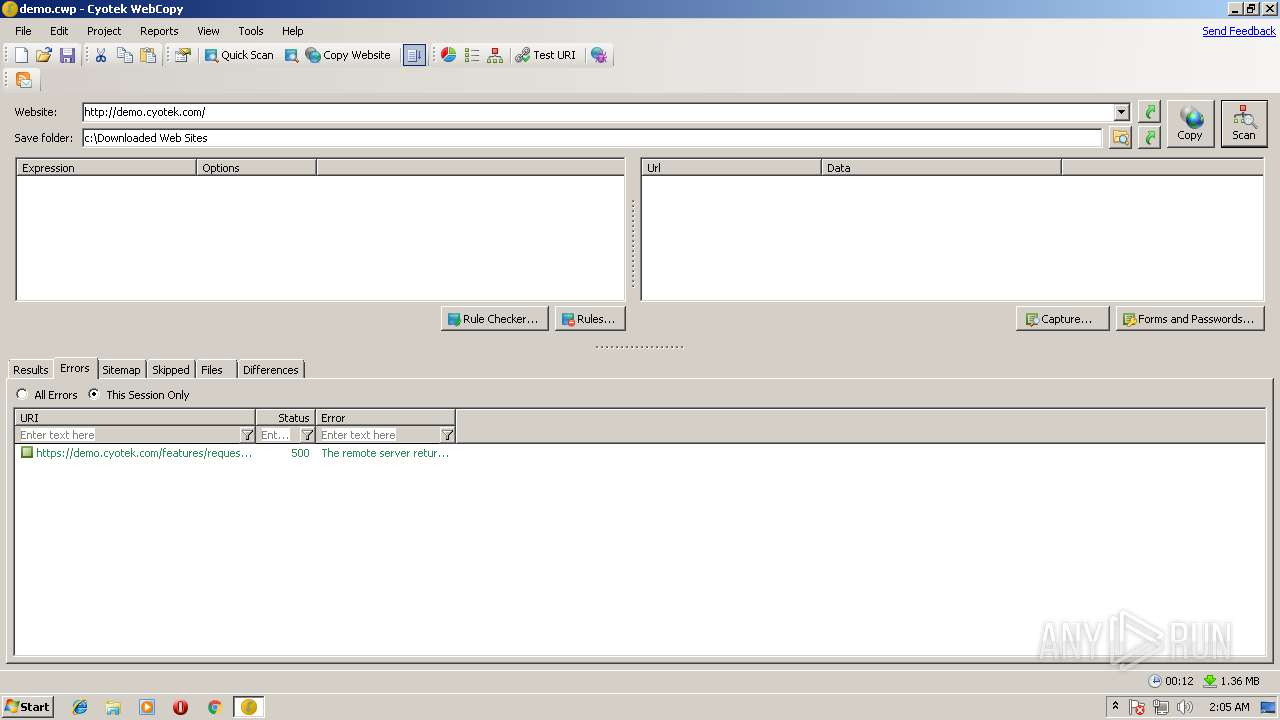
Changes IE settings (feature browser emulation)
- cyowcopy.exe (PID: 4068)
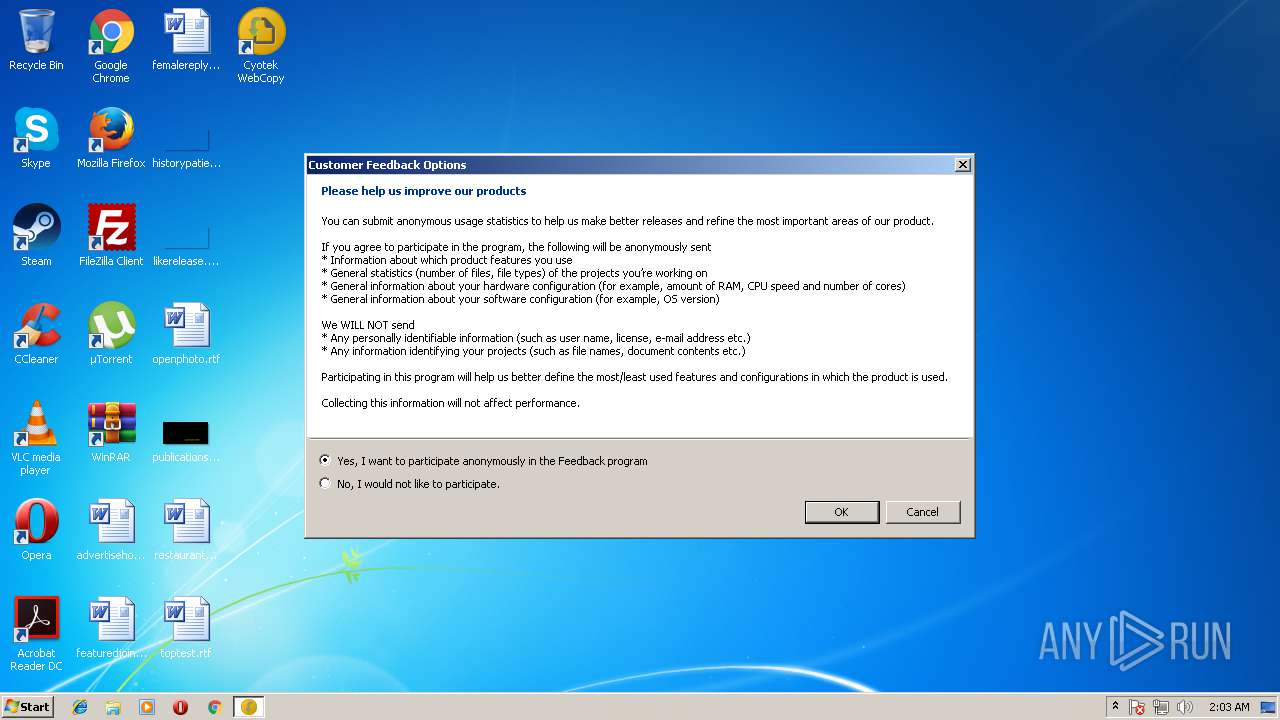
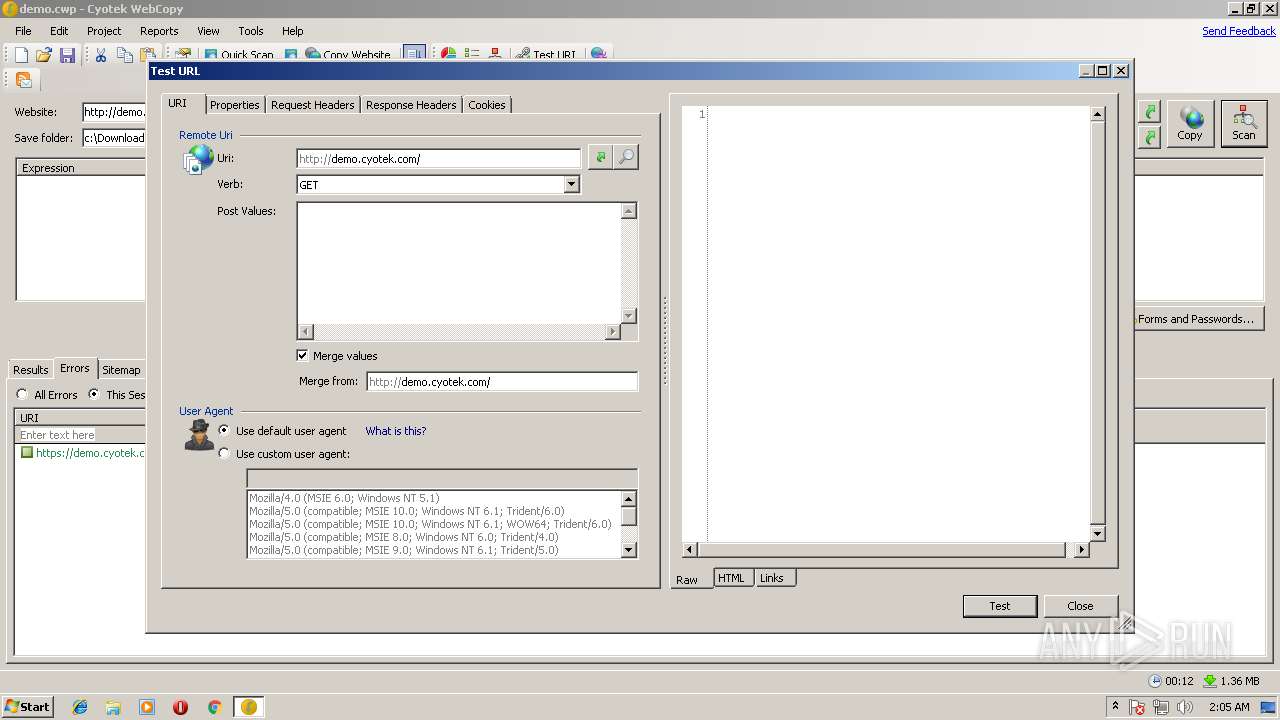
Reads internet explorer settings
- cyowcopy.exe (PID: 4068)
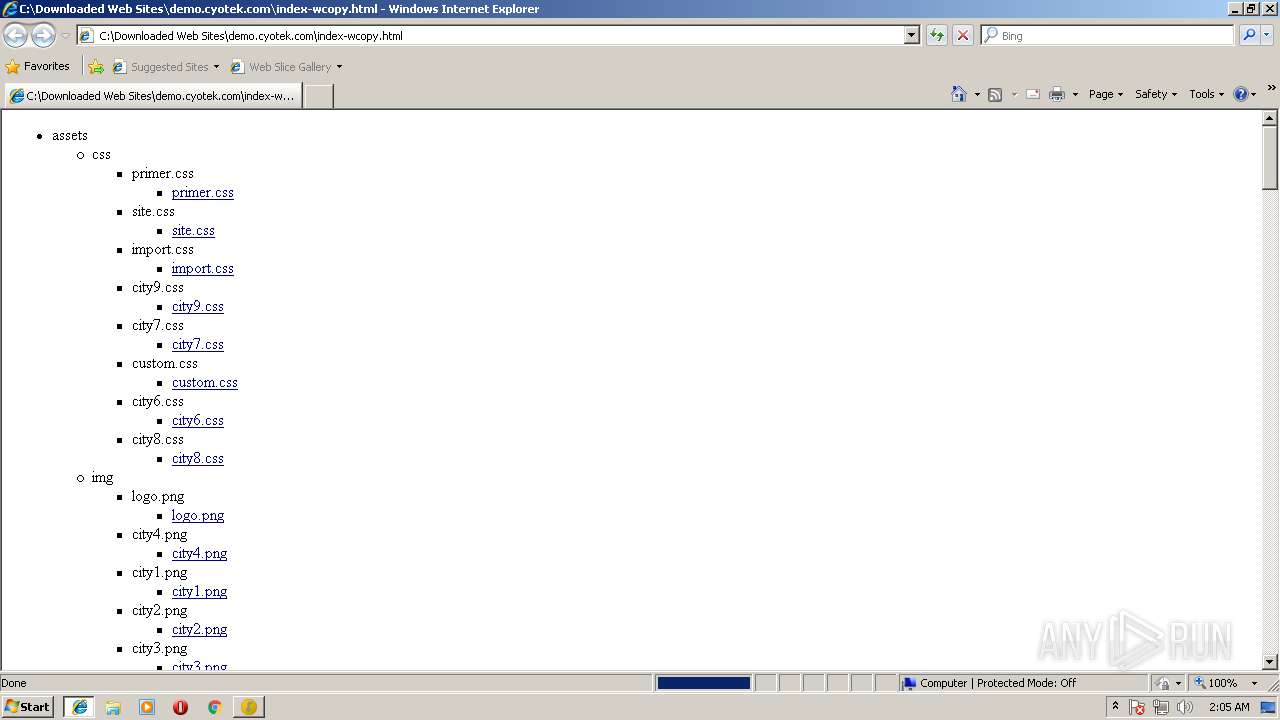
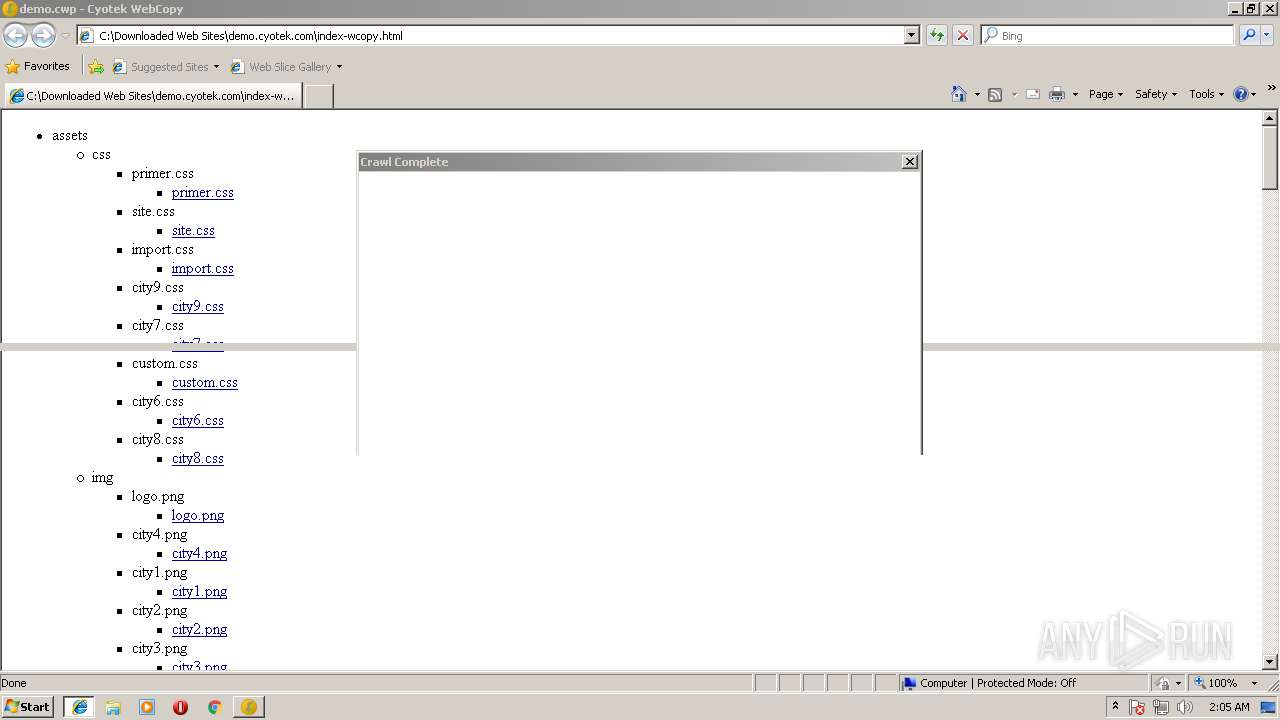
Starts Internet Explorer
- cyowcopy.exe (PID: 4068)
Reads Internet Cache Settings
- cyowcopy.exe (PID: 4068)
INFO
Dropped object may contain URL's
- ngen.exe (PID: 3112)
- setup-cyowcopy-1.5.0-build-516.tmp (PID: 2472)
- mscorsvw.exe (PID: 1100)
- mscorsvw.exe (PID: 2784)
- mscorsvw.exe (PID: 3508)
- ngen.exe (PID: 3244)
- ngen.exe (PID: 1872)
- ngen.exe (PID: 2576)
- cyowcopy.exe (PID: 4068)
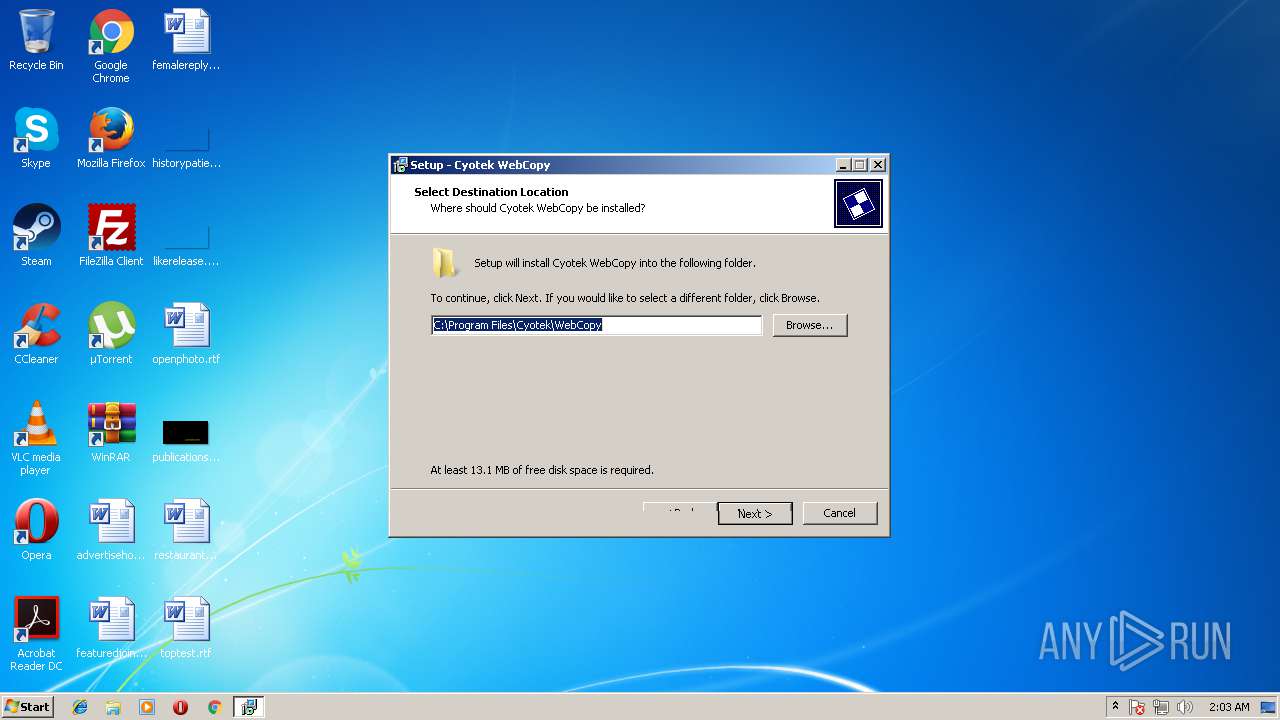
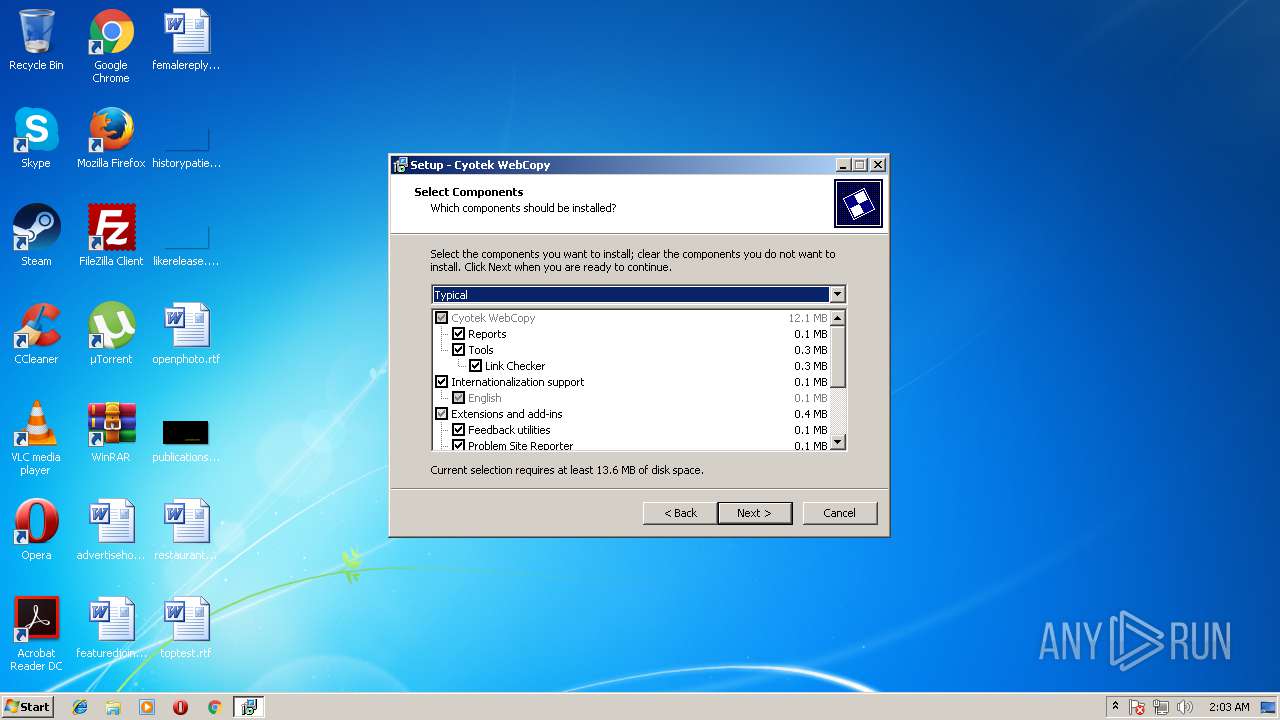
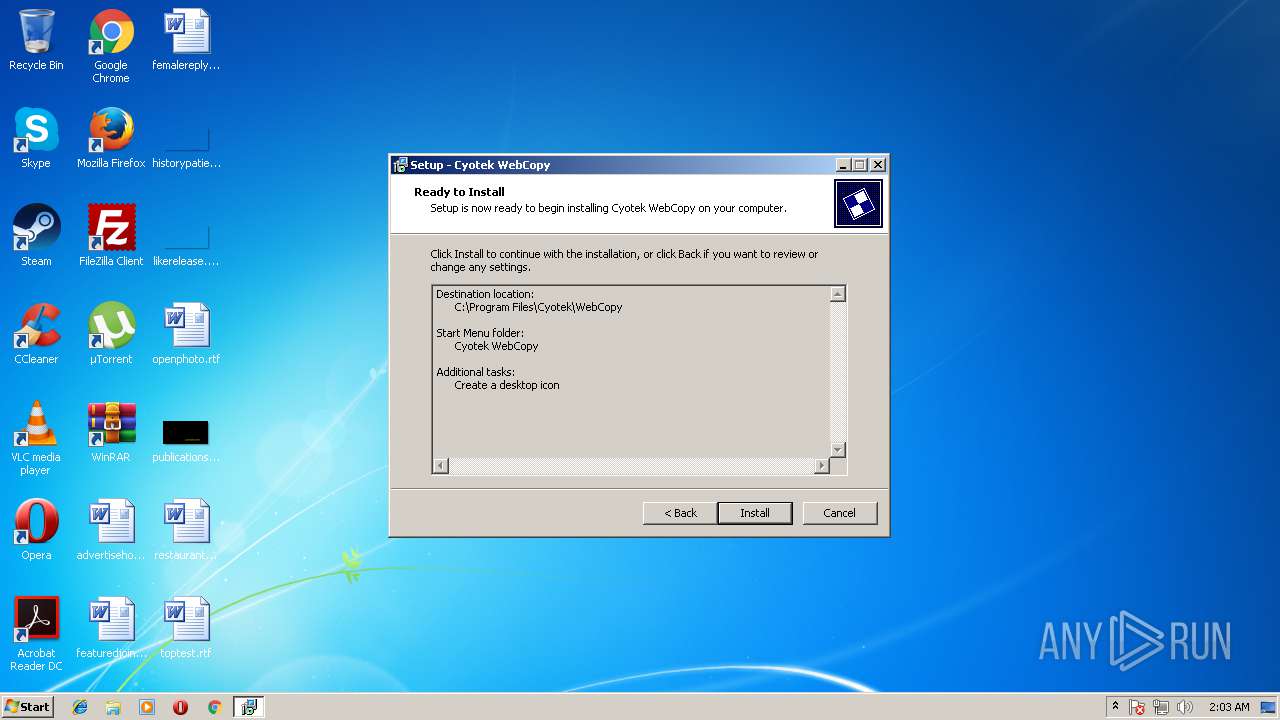
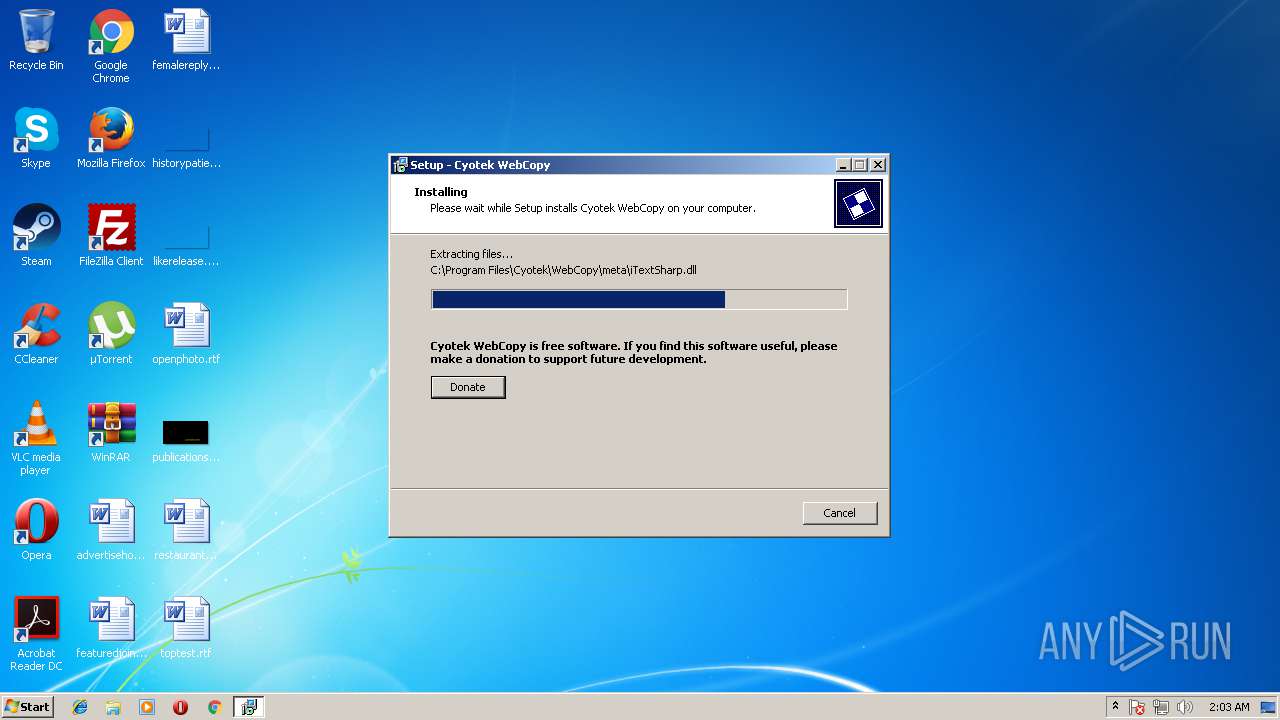
Creates files in the program directory
- setup-cyowcopy-1.5.0-build-516.tmp (PID: 2472)
Loads dropped or rewritten executable
- setup-cyowcopy-1.5.0-build-516.tmp (PID: 2472)
Application was dropped or rewritten from another process
- setup-cyowcopy-1.5.0-build-516.tmp (PID: 2472)
- setup-cyowcopy-1.5.0-build-516.tmp (PID: 3348)
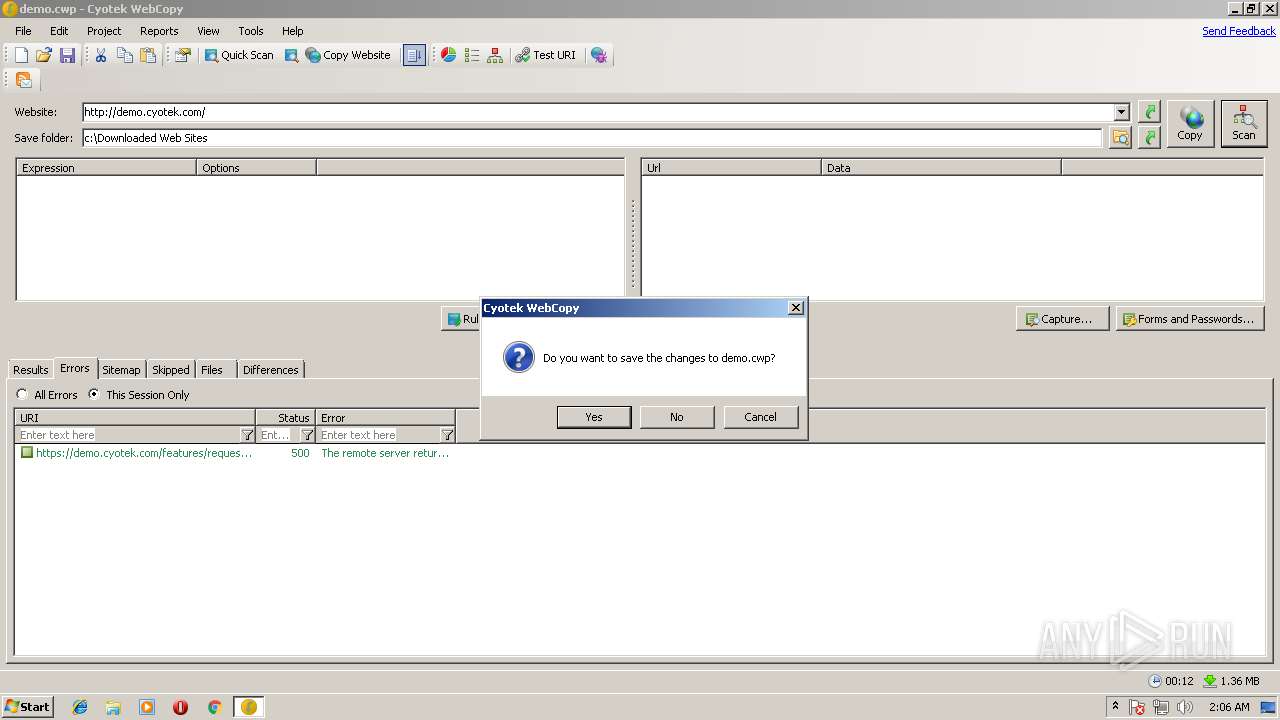
Creates a software uninstall entry
- setup-cyowcopy-1.5.0-build-516.tmp (PID: 2472)
Reads internet explorer settings
- iexplore.exe (PID: 3968)
Changes internet zones settings
- iexplore.exe (PID: 2940)
Reads settings of System Certificates
- cyowcopy.exe (PID: 4068)
Application launched itself
- iexplore.exe (PID: 2940)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Delphi generic (45.2) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (20.9) |
| .exe | | | Win32 Executable (generic) (14.3) |
| .exe | | | Win16/32 Executable Delphi generic (6.6) |
| .exe | | | Generic Win/DOS Executable (6.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:04:06 16:39:04+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 66560 |
| InitializedDataSize: | 53760 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x117dc |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.5.0.516 |
| ProductVersionNumber: | 1.5.0.516 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
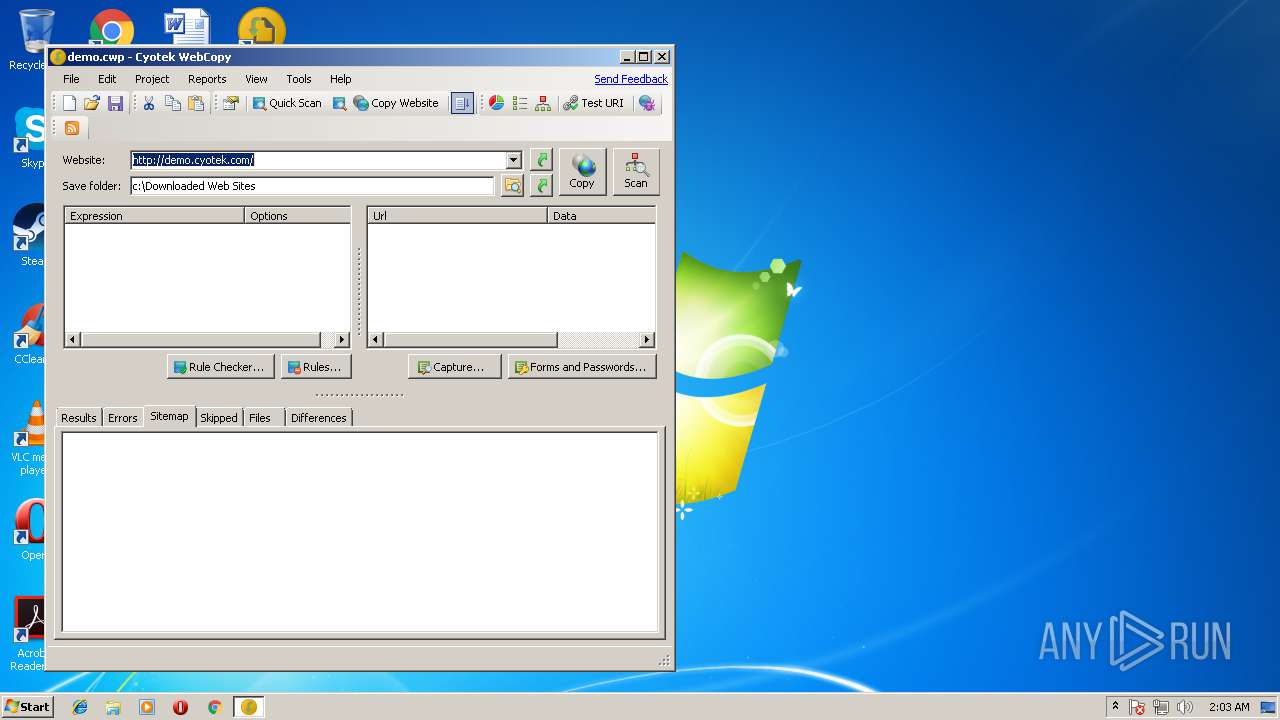
| CompanyName: | Cyotek Ltd |
| FileDescription: | Cyotek WebCopy |
| FileVersion: | 1.5.0.516 |
| LegalCopyright: | Copyright © 2010-2018 Cyotek Ltd. All Rights Reserved. |
| ProductName: | Cyotek WebCopy |
| ProductVersion: | 1.5.0.516 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 06-Apr-2016 14:39:04 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | Cyotek Ltd |
| FileDescription: | Cyotek WebCopy |
| FileVersion: | 1.5.0.516 |
| LegalCopyright: | Copyright © 2010-2018 Cyotek Ltd. All Rights Reserved. |
| ProductName: | Cyotek WebCopy |
| ProductVersion: | 1.5.0.516 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 06-Apr-2016 14:39:04 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000F244 | 0x0000F400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.37521 |
.itext | 0x00011000 | 0x00000F64 | 0x00001000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.7322 |
.data | 0x00012000 | 0x00000C88 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.29672 |
.bss | 0x00013000 | 0x000056BC | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00019000 | 0x00000E04 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.59781 |
.tls | 0x0001A000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0001B000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.204488 |
.rsrc | 0x0001C000 | 0x0000B200 | 0x0000B200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.14644 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.13965 | 1580 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.47151 | 1384 | UNKNOWN | Dutch - Netherlands | RT_ICON |
3 | 3.91708 | 744 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4 | 3.91366 | 2216 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4091 | 2.56031 | 104 | UNKNOWN | UNKNOWN | RT_STRING |
4092 | 3.25287 | 212 | UNKNOWN | UNKNOWN | RT_STRING |
4093 | 3.26919 | 164 | UNKNOWN | UNKNOWN | RT_STRING |
4094 | 3.33268 | 684 | UNKNOWN | UNKNOWN | RT_STRING |
4095 | 3.34579 | 844 | UNKNOWN | UNKNOWN | RT_STRING |
4096 | 3.28057 | 660 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
96
Monitored processes
54
Malicious processes
47
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 384 | "C:\Users\admin\AppData\Local\Temp\setup-cyowcopy-1.5.0-build-516.exe" /SPAWNWND=$2401BC /NOTIFYWND=$2F016A | C:\Users\admin\AppData\Local\Temp\setup-cyowcopy-1.5.0-build-516.exe | setup-cyowcopy-1.5.0-build-516.tmp | ||||||||||||
User: admin Company: Cyotek Ltd Integrity Level: HIGH Description: Cyotek WebCopy Exit code: 0 Version: 1.5.0.516 Modules
| |||||||||||||||
| 592 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe -StartupEvent 224 -InterruptEvent 0 -NGENProcess 208 -Pipe 210 -Comment "NGen Worker Process" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe | ngen.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: .NET Runtime Optimization Service Exit code: 0 Version: 4.6.1055.0 built by: NETFXREL2 Modules
| |||||||||||||||
| 1100 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe -StartupEvent 21c -InterruptEvent 0 -NGENProcess 194 -Pipe 108 -Comment "NGen Worker Process" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe | ngen.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: .NET Runtime Optimization Service Exit code: 0 Version: 4.6.1055.0 built by: NETFXREL2 Modules
| |||||||||||||||
| 1484 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe -StartupEvent 16c -InterruptEvent 0 -NGENProcess 110 -Pipe 108 -Comment "NGen Worker Process" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe | ngen.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: .NET Runtime Optimization Service Exit code: 0 Version: 4.6.1055.0 built by: NETFXREL2 Modules
| |||||||||||||||
| 1572 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe -StartupEvent 108 -InterruptEvent 0 -NGENProcess f8 -Pipe 104 -Comment "NGen Worker Process" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe | — | ngen.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: .NET Runtime Optimization Service Exit code: 0 Version: 4.6.1055.0 built by: NETFXREL2 Modules
| |||||||||||||||
| 1592 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe -StartupEvent 1d8 -InterruptEvent 0 -NGENProcess 1d0 -Pipe 198 -Comment "NGen Worker Process" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe | ngen.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: .NET Runtime Optimization Service Exit code: 0 Version: 4.6.1055.0 built by: NETFXREL2 Modules
| |||||||||||||||
| 1616 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe -StartupEvent 1d0 -InterruptEvent 0 -NGENProcess 224 -Pipe 21c -Comment "NGen Worker Process" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe | ngen.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: .NET Runtime Optimization Service Exit code: 0 Version: 4.6.1055.0 built by: NETFXREL2 Modules
| |||||||||||||||
| 1648 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe -StartupEvent 190 -InterruptEvent 0 -NGENProcess 174 -Pipe 18c -Comment "NGen Worker Process" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe | ngen.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: .NET Runtime Optimization Service Exit code: 0 Version: 4.6.1055.0 built by: NETFXREL2 Modules
| |||||||||||||||
| 1660 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe -StartupEvent 208 -InterruptEvent 0 -NGENProcess 1fc -Pipe 22c -Comment "NGen Worker Process" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe | ngen.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: .NET Runtime Optimization Service Exit code: 0 Version: 4.6.1055.0 built by: NETFXREL2 Modules
| |||||||||||||||
| 1704 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe -StartupEvent 1b0 -InterruptEvent 0 -NGENProcess 188 -Pipe 1ac -Comment "NGen Worker Process" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe | ngen.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: .NET Runtime Optimization Service Exit code: 0 Version: 4.6.1055.0 built by: NETFXREL2 Modules
| |||||||||||||||
Total events
5 030
Read events
4 690
Write events
332
Delete events
8
Modification events
| (PID) Process: | (2472) setup-cyowcopy-1.5.0-build-516.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: A8090000960B685E5837D401 | |||
| (PID) Process: | (2472) setup-cyowcopy-1.5.0-build-516.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: E176BB70E9892110CB3586AC90EBDFA05FEBB25A77EBFDB2CB996361A5BEBC37 | |||
| (PID) Process: | (2472) setup-cyowcopy-1.5.0-build-516.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (2472) setup-cyowcopy-1.5.0-build-516.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFiles0000 |
Value: C:\Program Files\Cyotek\WebCopy\Cyotek.ExceptionHandler.dll | |||
| (PID) Process: | (2472) setup-cyowcopy-1.5.0-build-516.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFilesHash |
Value: EAC13139E2037D8DF1777CFF5515A29185F086E23888832C38DBB6D9A6E8F060 | |||
| (PID) Process: | (2472) setup-cyowcopy-1.5.0-build-516.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\App Paths\cyowcopy.exe |
| Operation: | write | Name: | |
Value: C:\Program Files\Cyotek\WebCopy\cyowcopy.exe | |||
| (PID) Process: | (2472) setup-cyowcopy-1.5.0-build-516.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\App Paths\cyowcopy.exe |
| Operation: | write | Name: | Path |
Value: C:\Program Files\Cyotek\WebCopy | |||
| (PID) Process: | (2472) setup-cyowcopy-1.5.0-build-516.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\App Paths\wcopy.exe |
| Operation: | write | Name: | |
Value: C:\Program Files\Cyotek\WebCopy\wcopy.exe | |||
| (PID) Process: | (2472) setup-cyowcopy-1.5.0-build-516.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\App Paths\wcopy.exe |
| Operation: | write | Name: | Path |
Value: C:\Program Files\Cyotek\WebCopy | |||
| (PID) Process: | (2472) setup-cyowcopy-1.5.0-build-516.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\App Paths\lnkchk.exe |
| Operation: | write | Name: | |
Value: C:\Program Files\Cyotek\WebCopy\lnkchk.exe | |||
Executable files
94
Suspicious files
21
Text files
252
Unknown types
43
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2472 | setup-cyowcopy-1.5.0-build-516.tmp | C:\Program Files\Cyotek\WebCopy\is-9AIFL.tmp | — | |
MD5:— | SHA256:— | |||
| 2472 | setup-cyowcopy-1.5.0-build-516.tmp | C:\Program Files\Cyotek\WebCopy\is-EP1F5.tmp | — | |
MD5:— | SHA256:— | |||
| 2472 | setup-cyowcopy-1.5.0-build-516.tmp | C:\Program Files\Cyotek\WebCopy\is-1J4OT.tmp | — | |
MD5:— | SHA256:— | |||
| 2472 | setup-cyowcopy-1.5.0-build-516.tmp | C:\Program Files\Cyotek\WebCopy\is-U2N71.tmp | — | |
MD5:— | SHA256:— | |||
| 2472 | setup-cyowcopy-1.5.0-build-516.tmp | C:\Program Files\Cyotek\WebCopy\is-NN4VP.tmp | — | |
MD5:— | SHA256:— | |||
| 2472 | setup-cyowcopy-1.5.0-build-516.tmp | C:\Program Files\Cyotek\WebCopy\is-NO9MS.tmp | — | |
MD5:— | SHA256:— | |||
| 2472 | setup-cyowcopy-1.5.0-build-516.tmp | C:\Program Files\Cyotek\WebCopy\is-688IJ.tmp | — | |
MD5:— | SHA256:— | |||
| 2472 | setup-cyowcopy-1.5.0-build-516.tmp | C:\Program Files\Cyotek\WebCopy\is-9RF6E.tmp | — | |
MD5:— | SHA256:— | |||
| 2472 | setup-cyowcopy-1.5.0-build-516.tmp | C:\Program Files\Cyotek\WebCopy\is-CTLNU.tmp | — | |
MD5:— | SHA256:— | |||
| 2472 | setup-cyowcopy-1.5.0-build-516.tmp | C:\Program Files\Cyotek\WebCopy\is-99PMM.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
12
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
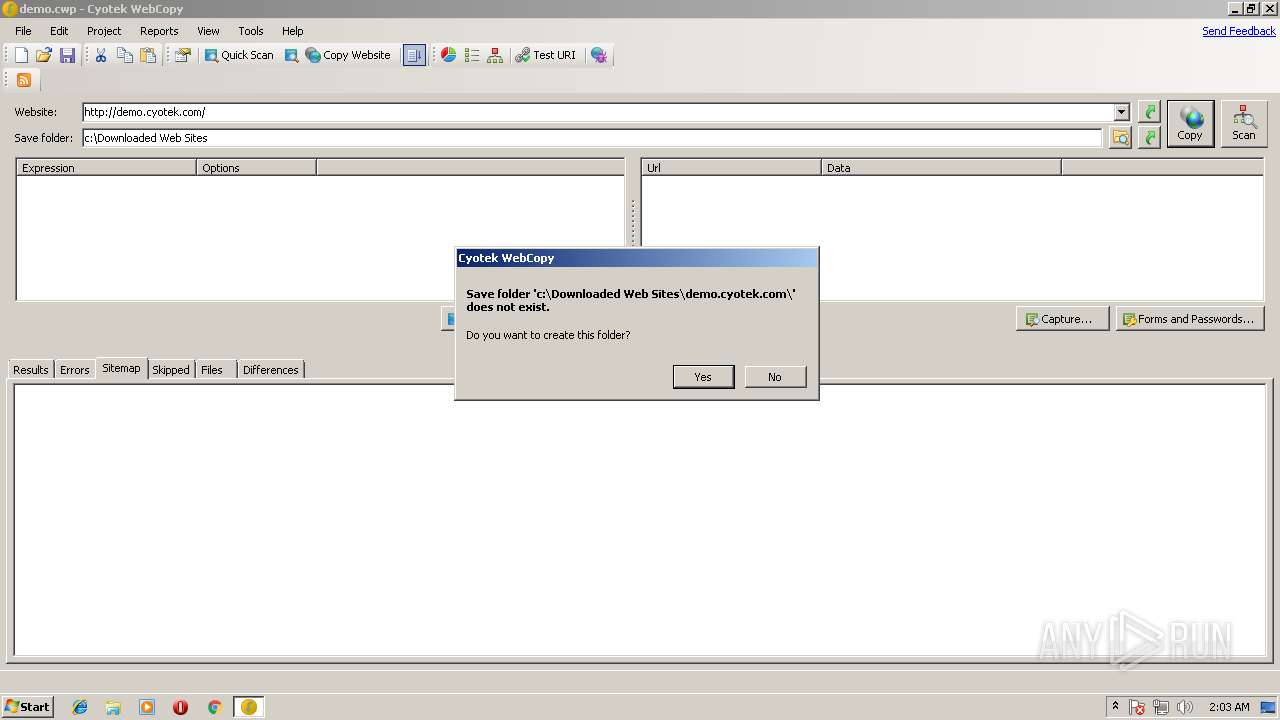
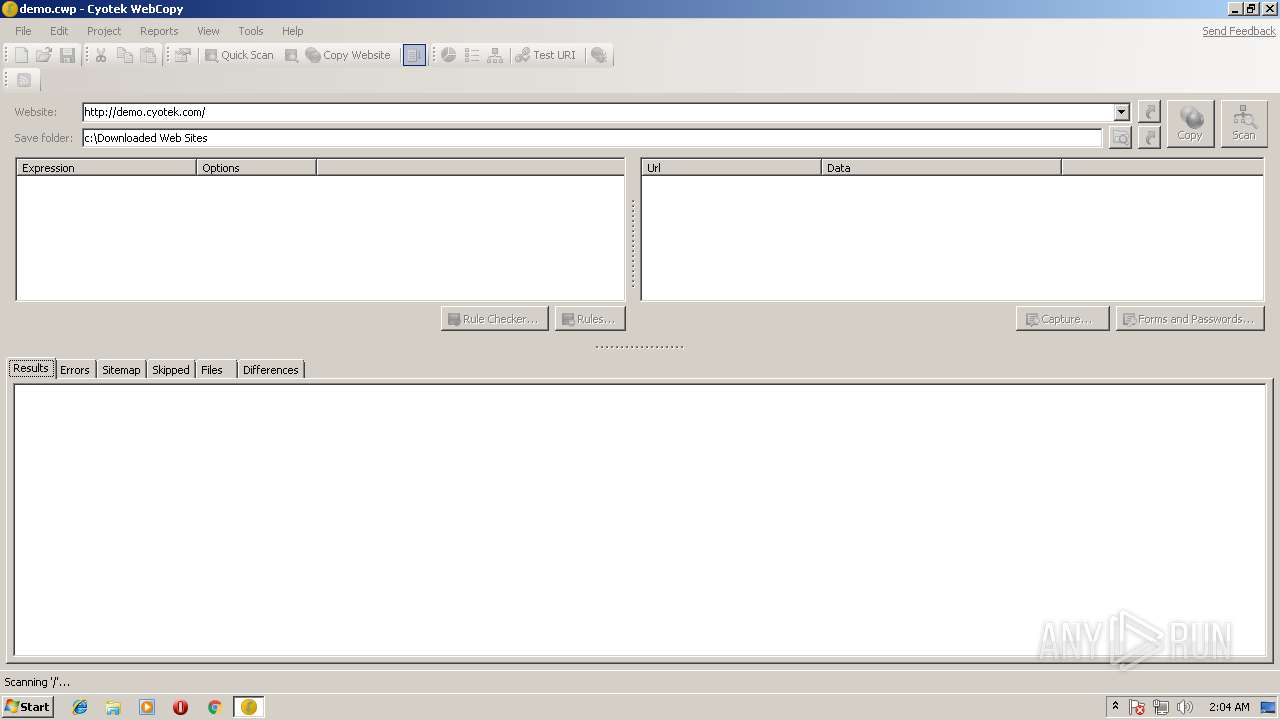
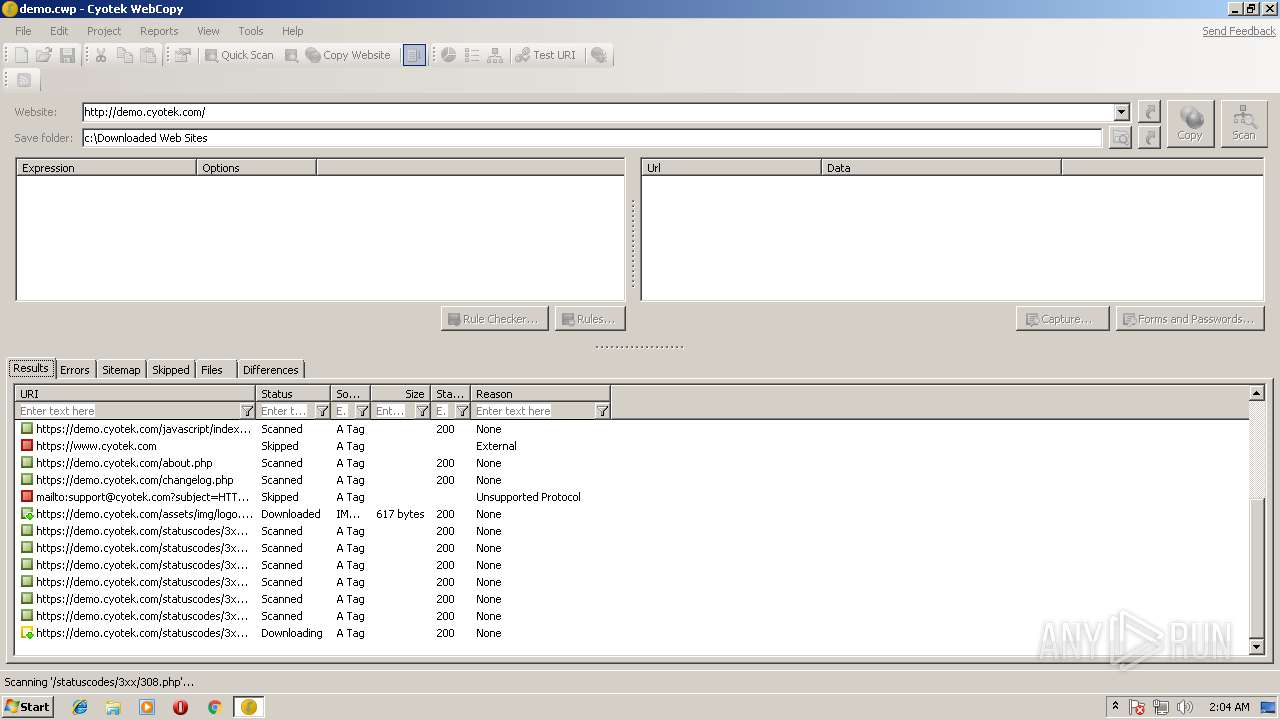
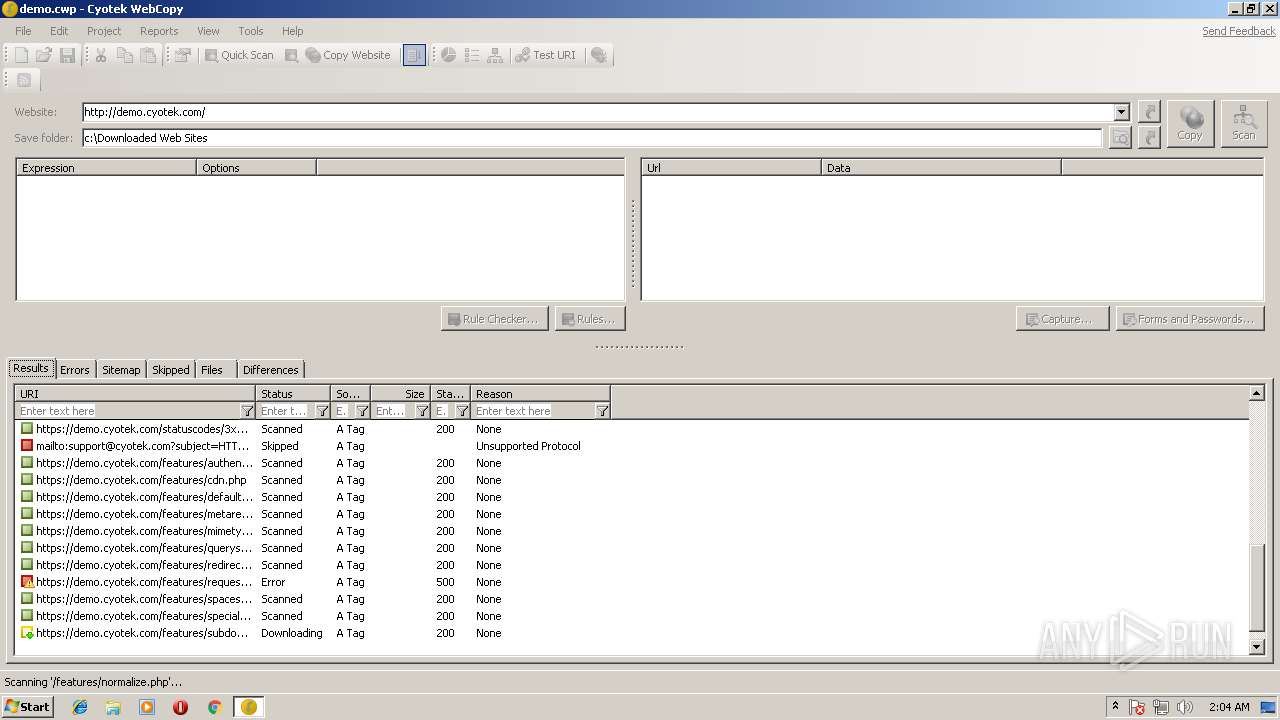
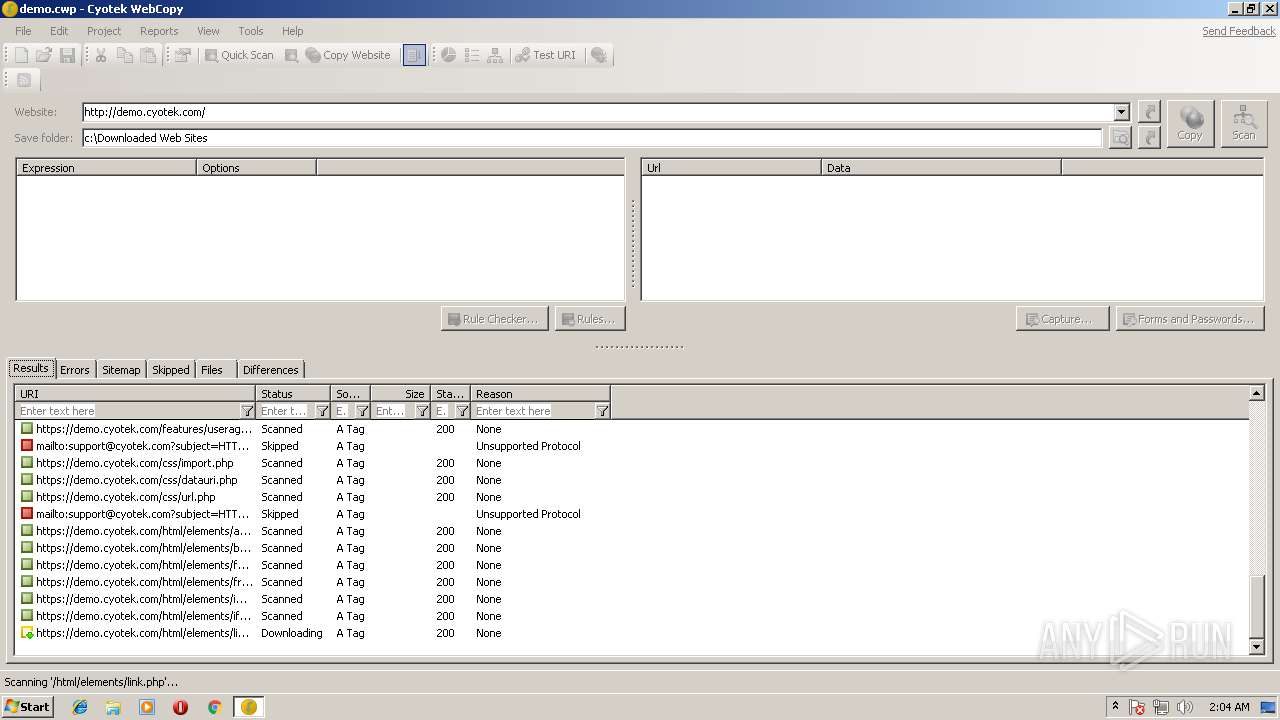
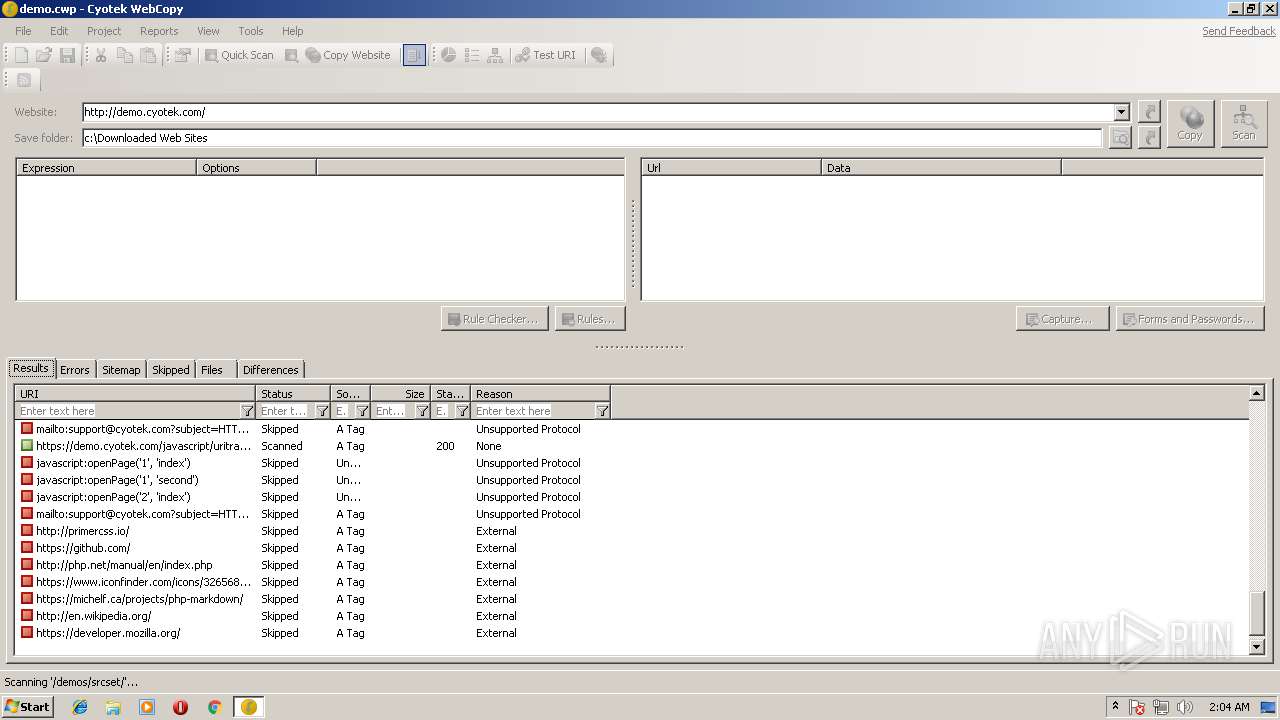
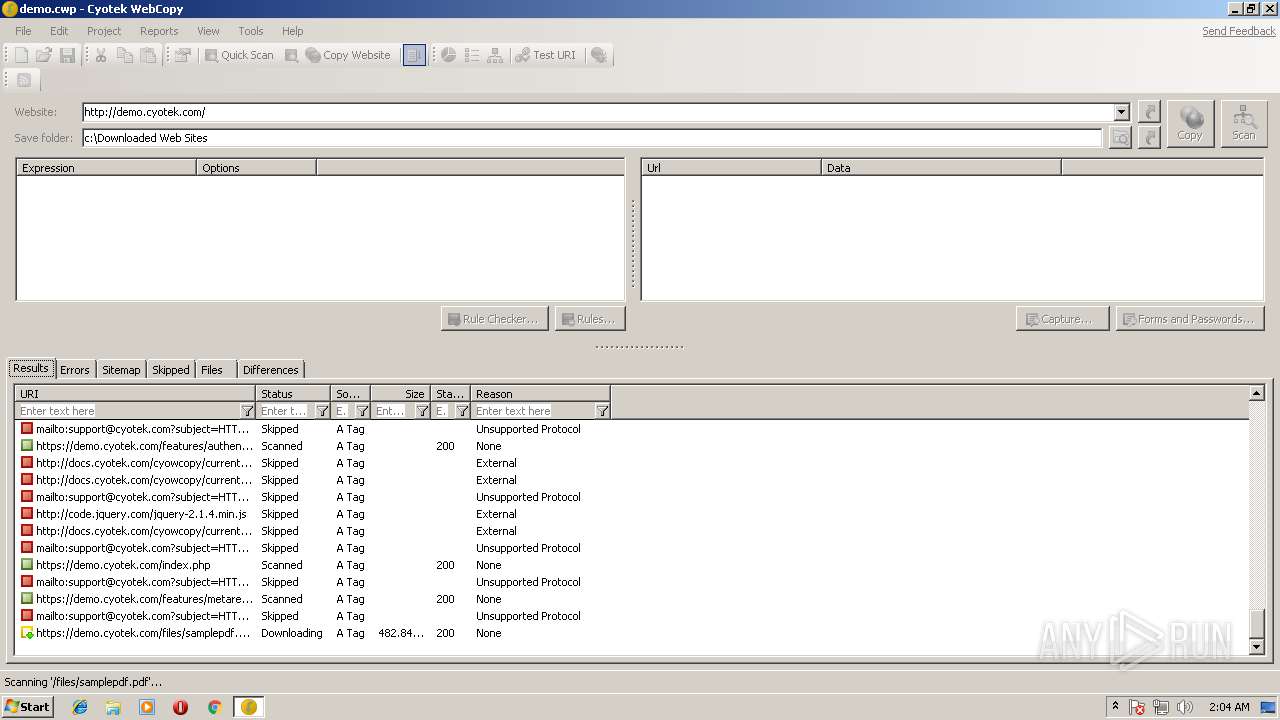
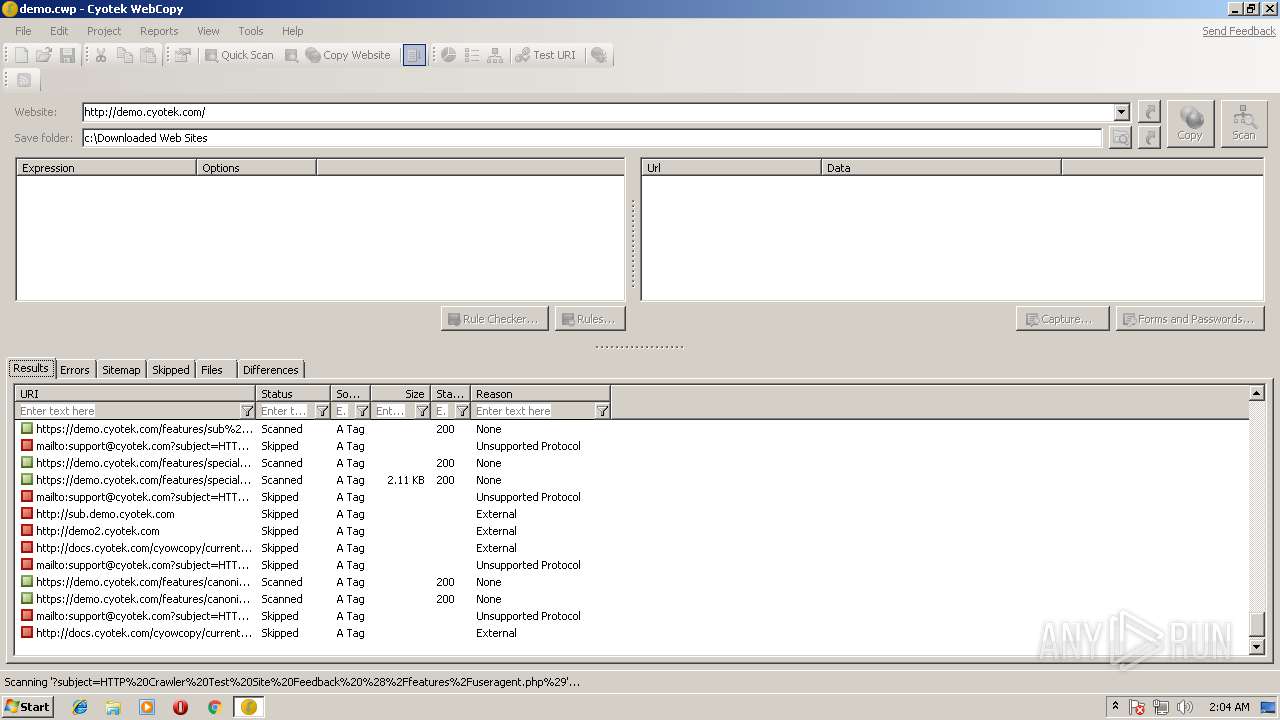
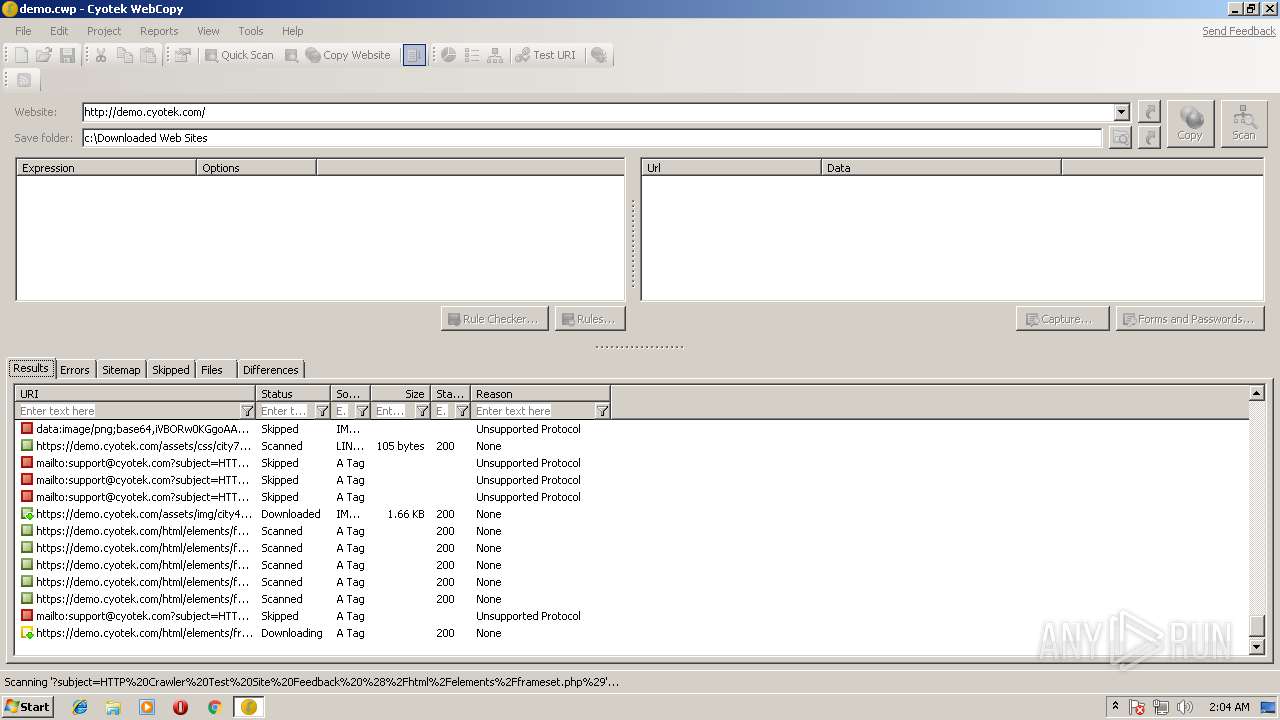
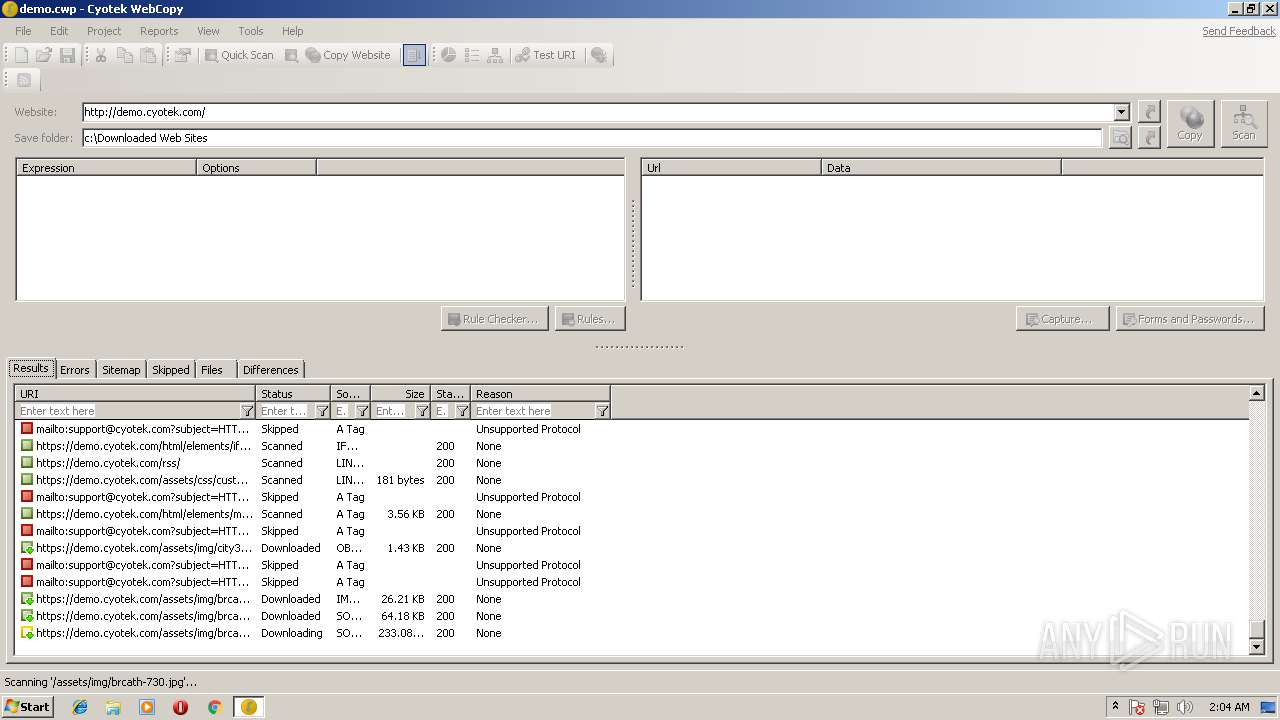
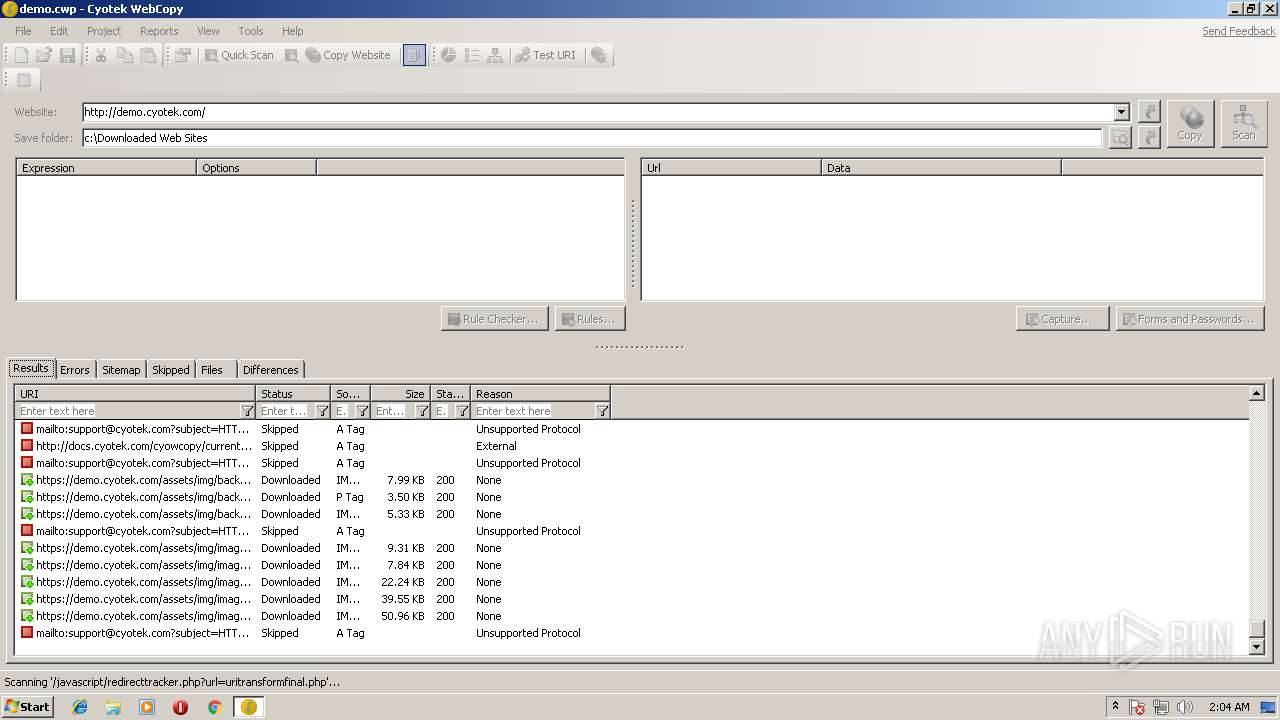
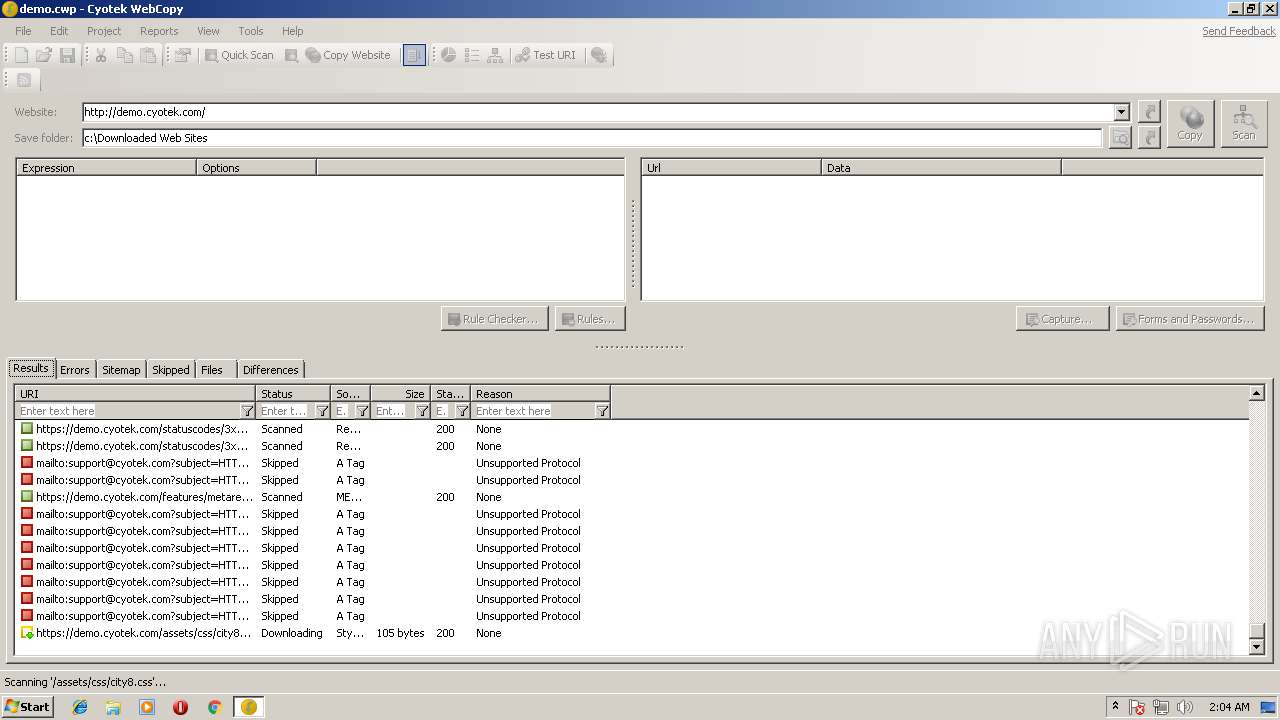
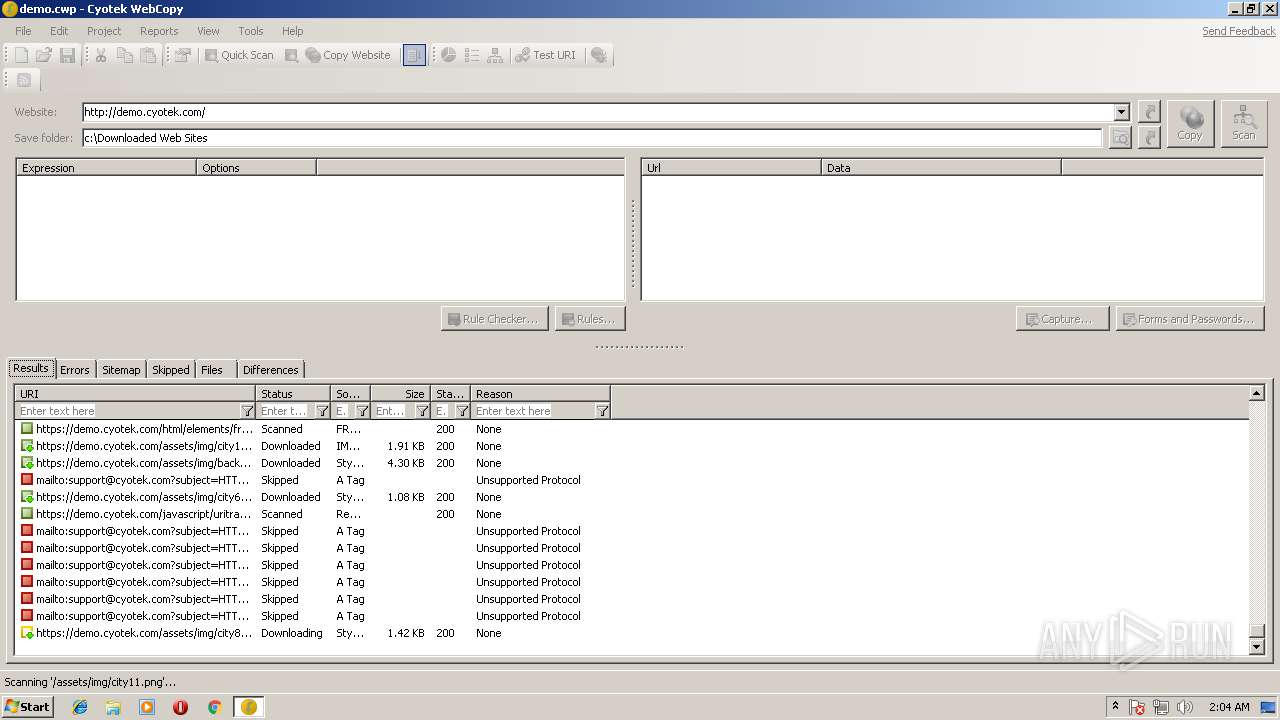
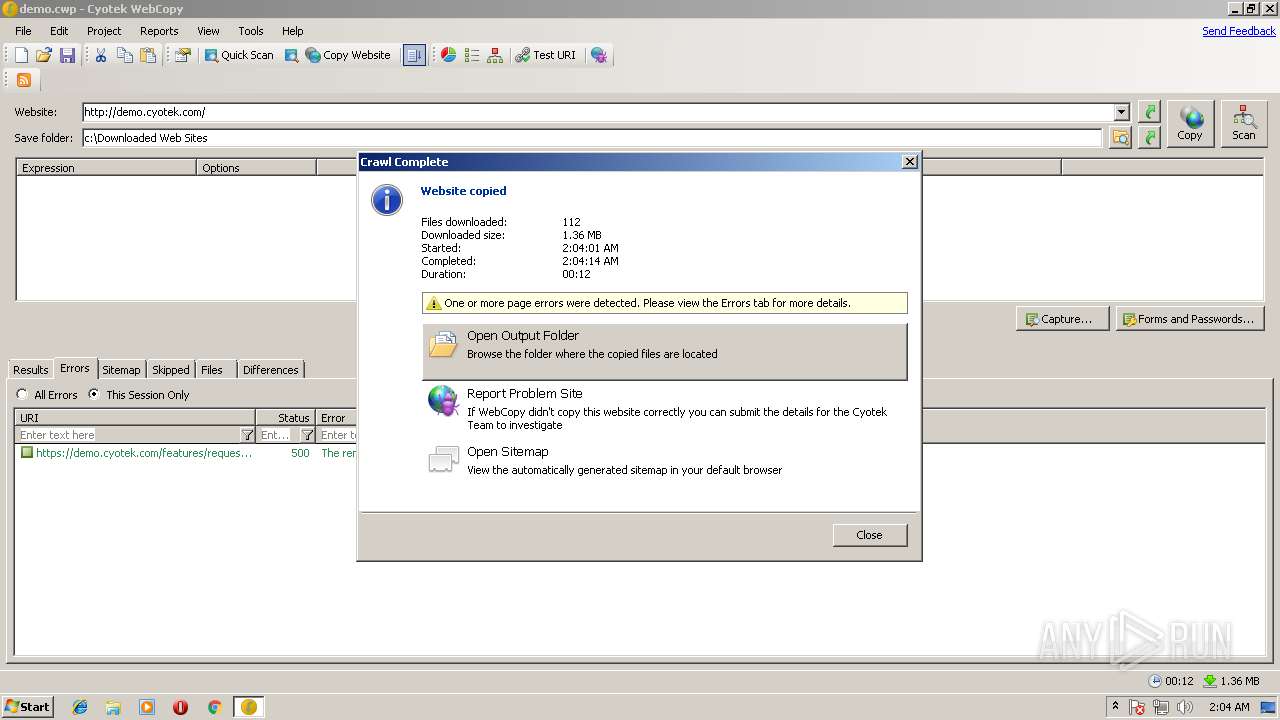
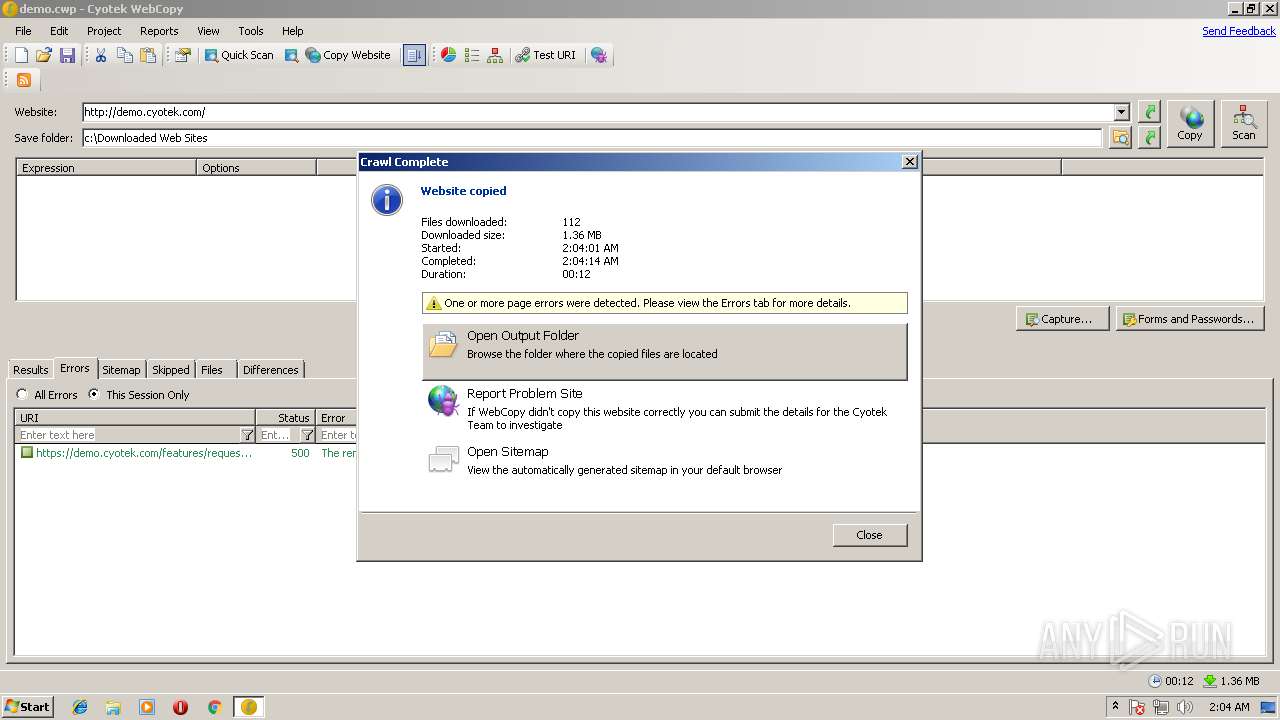
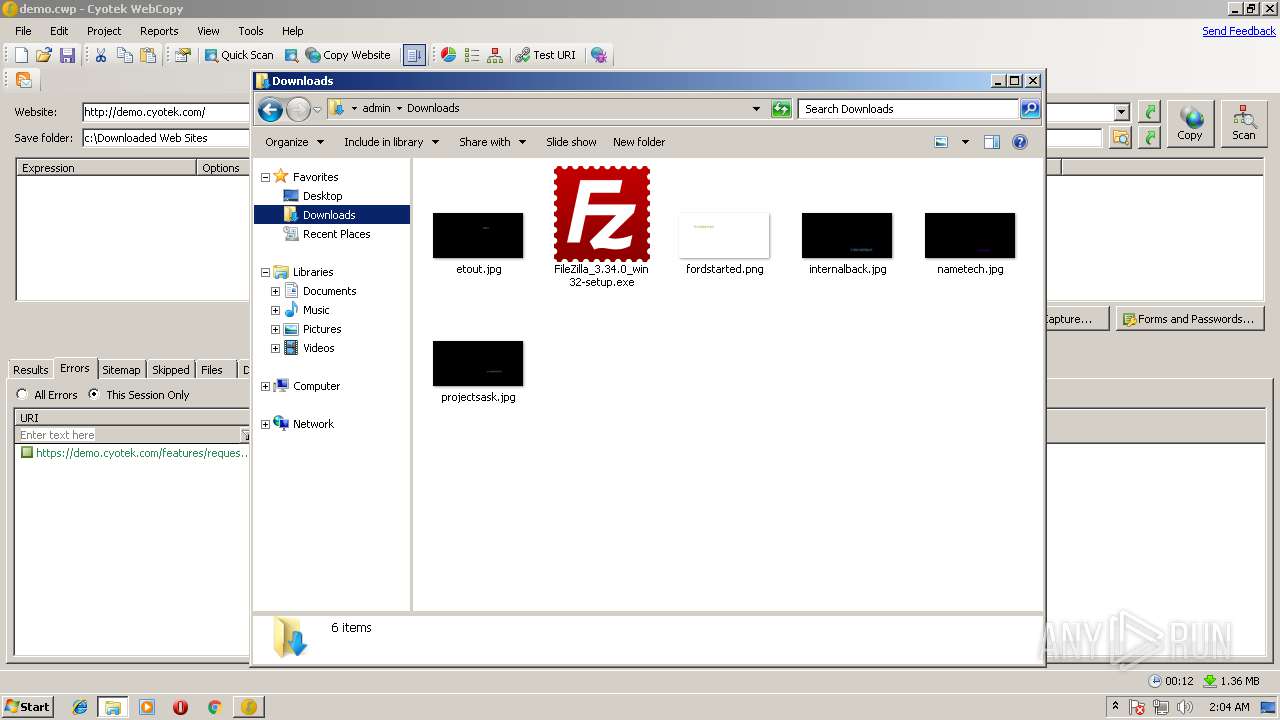
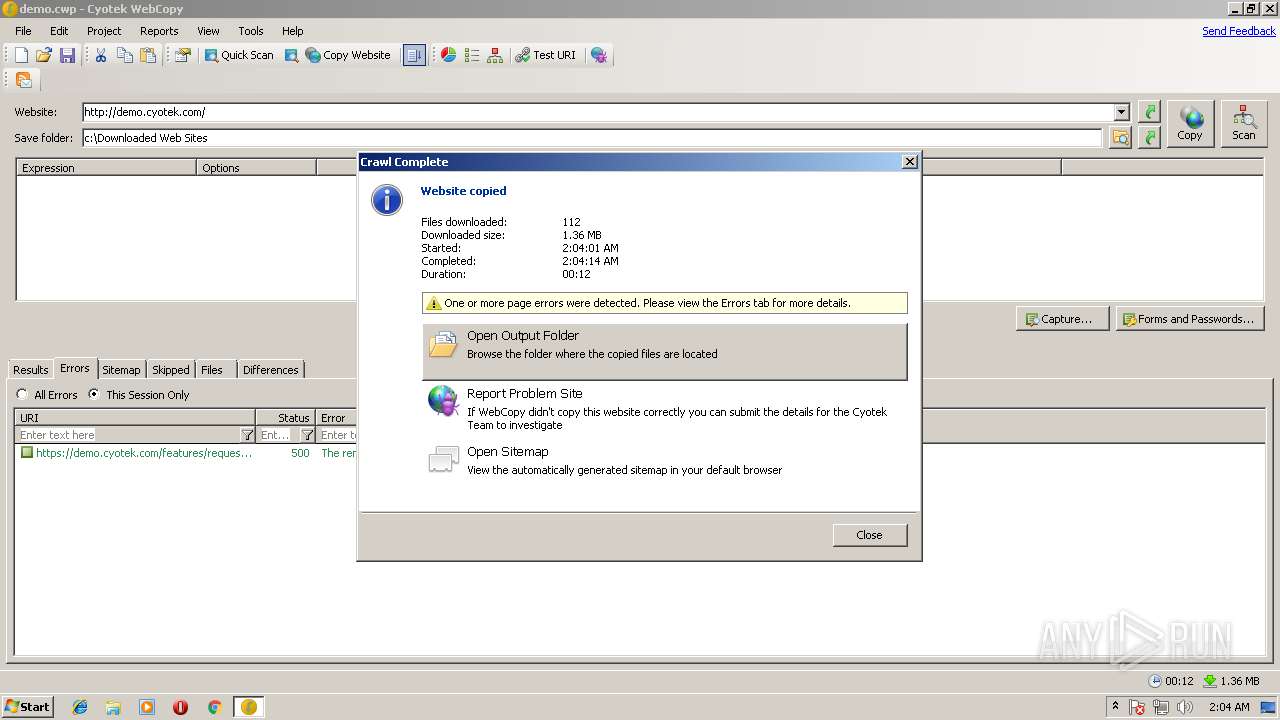
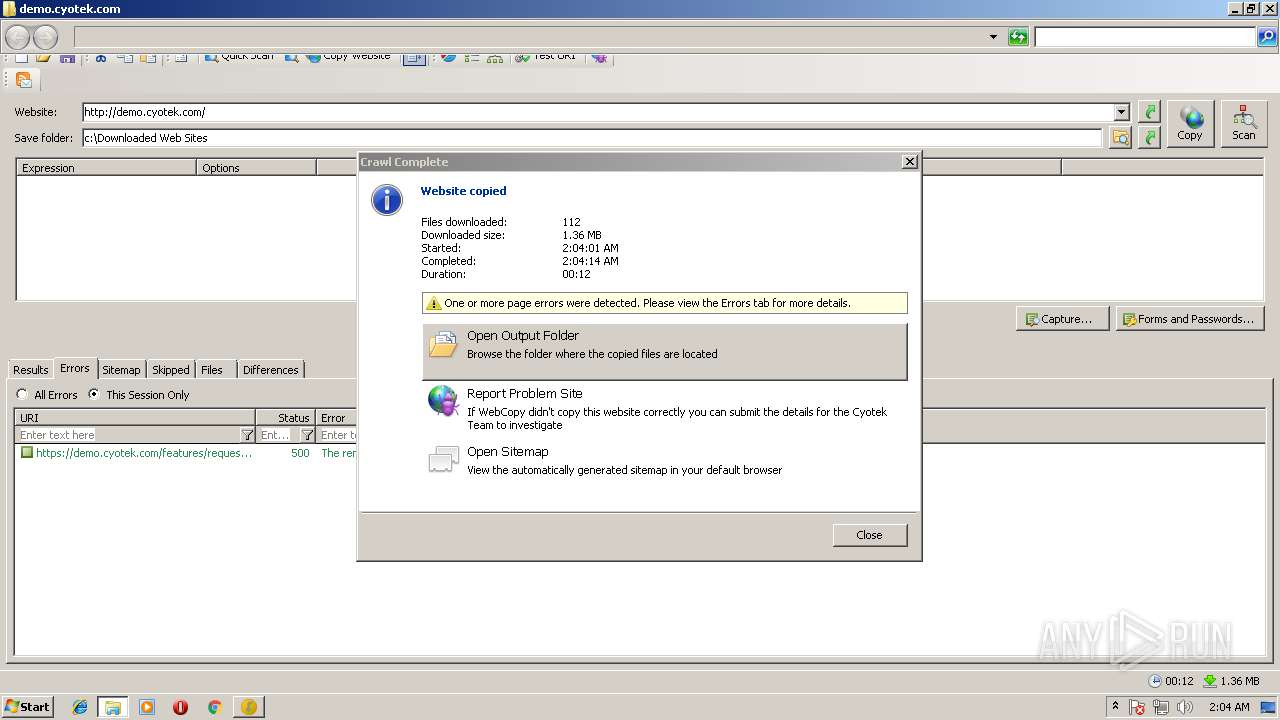
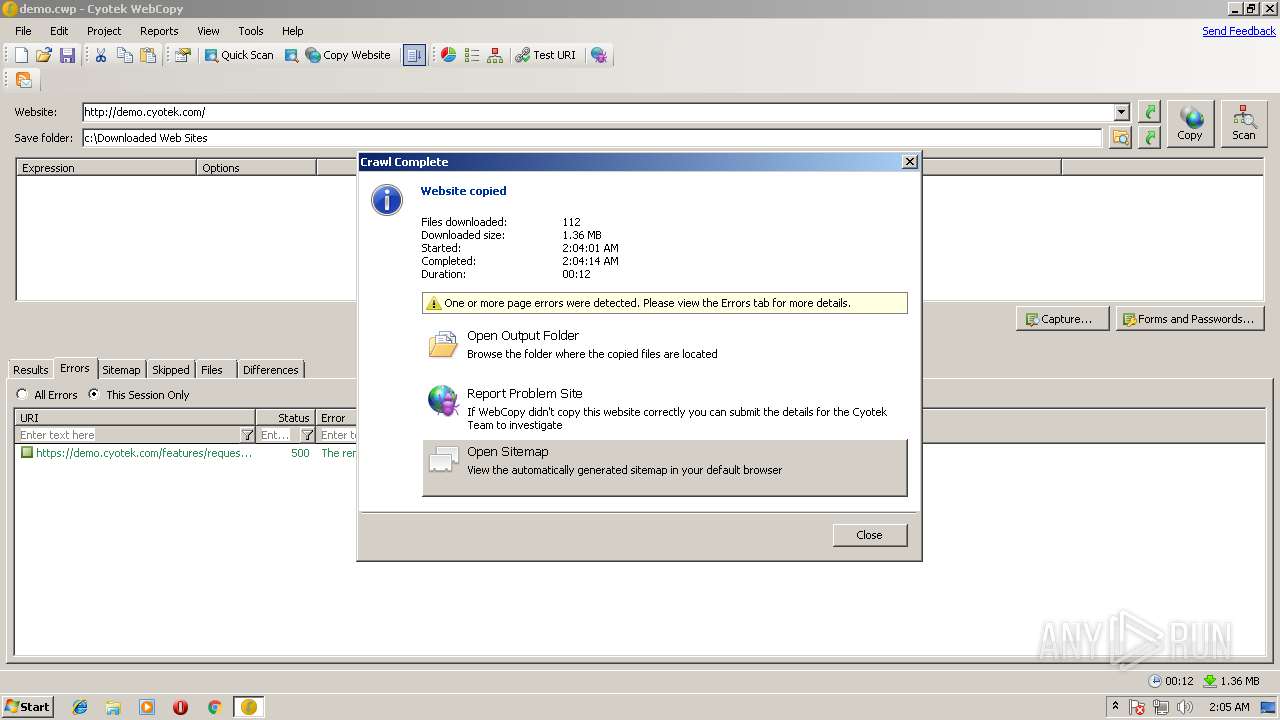
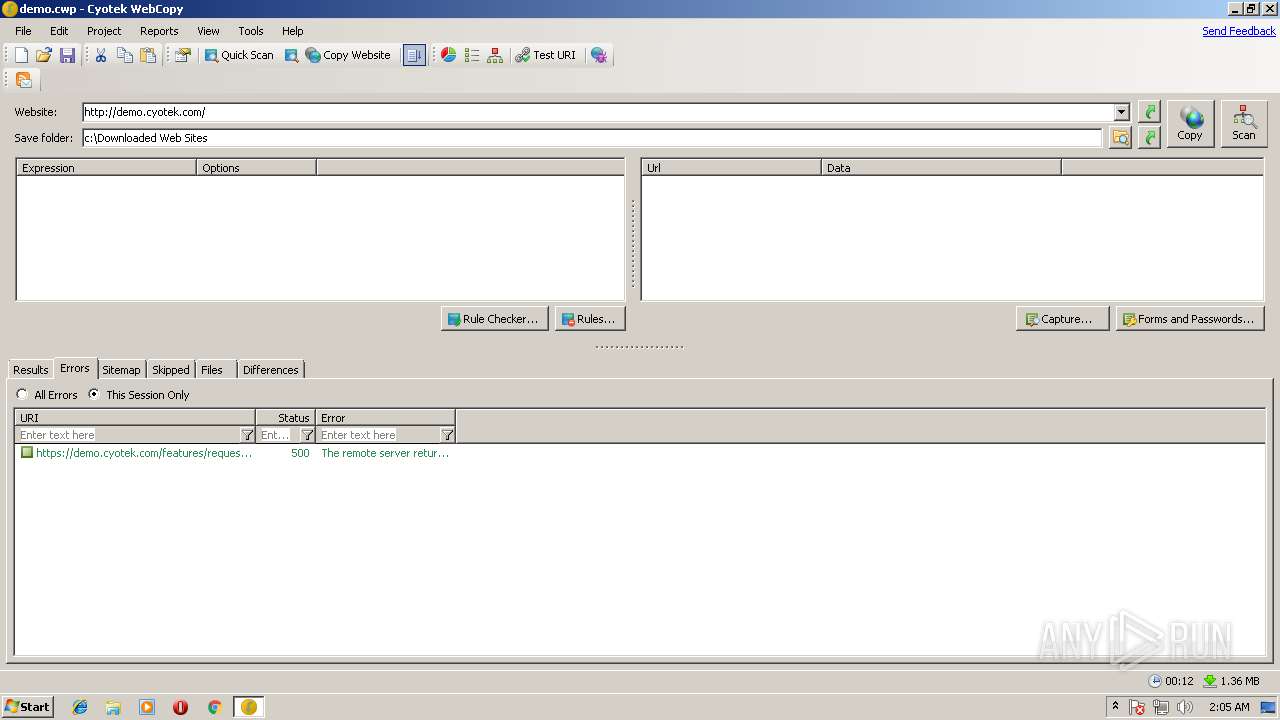
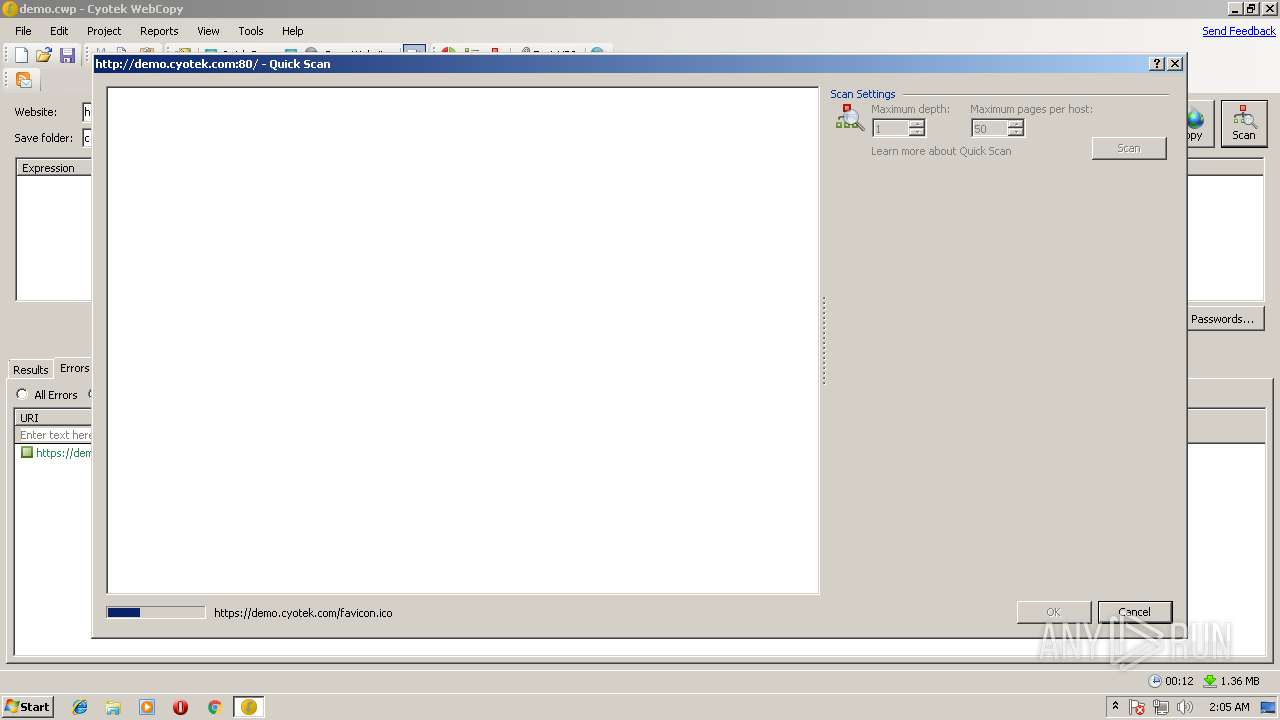
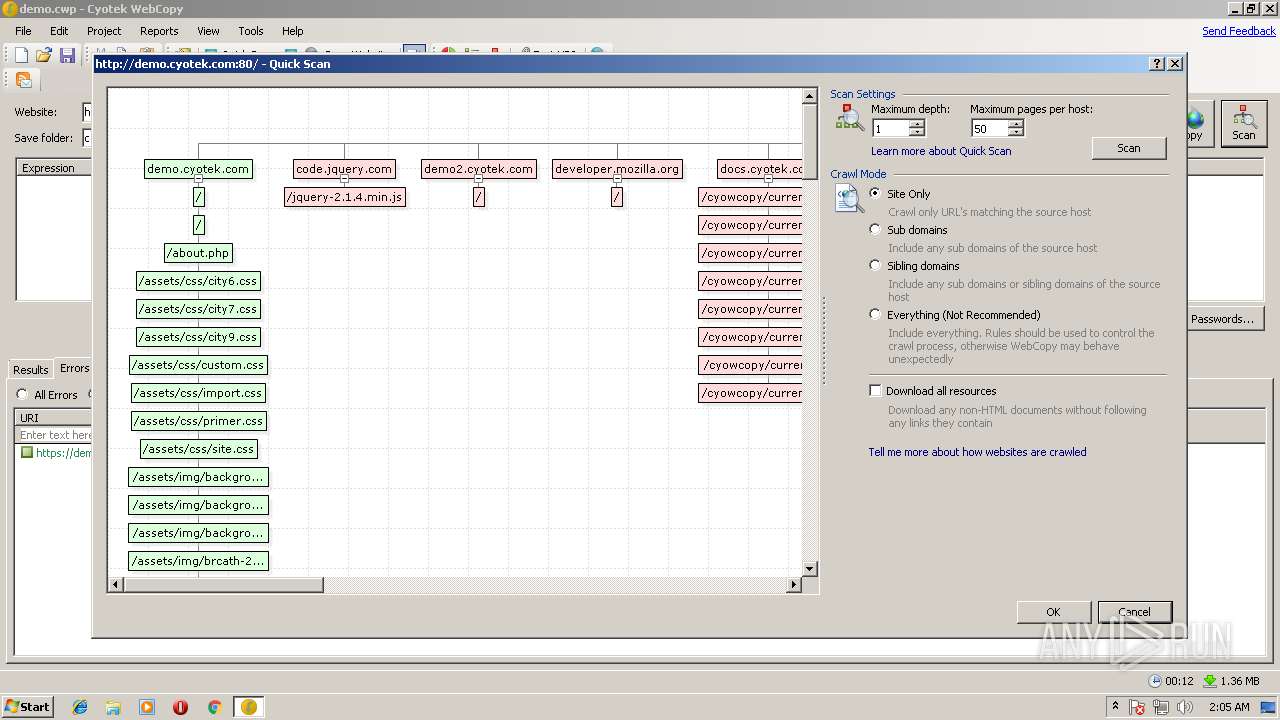
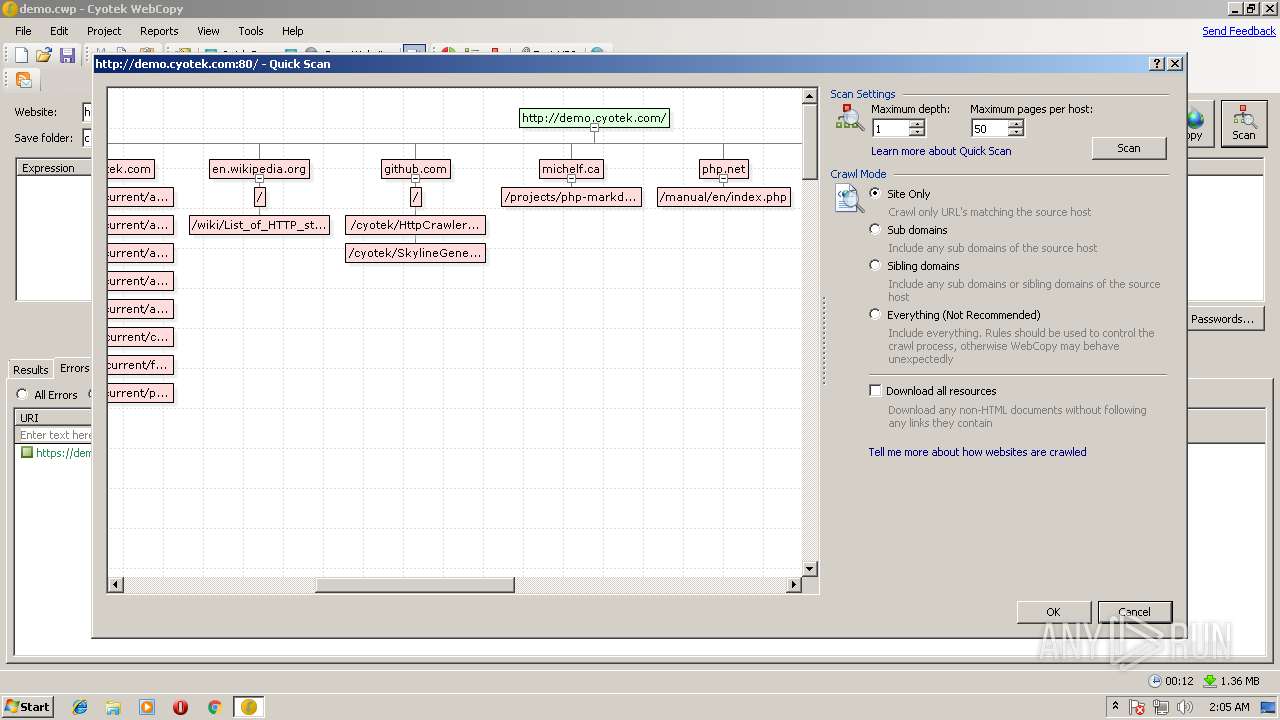
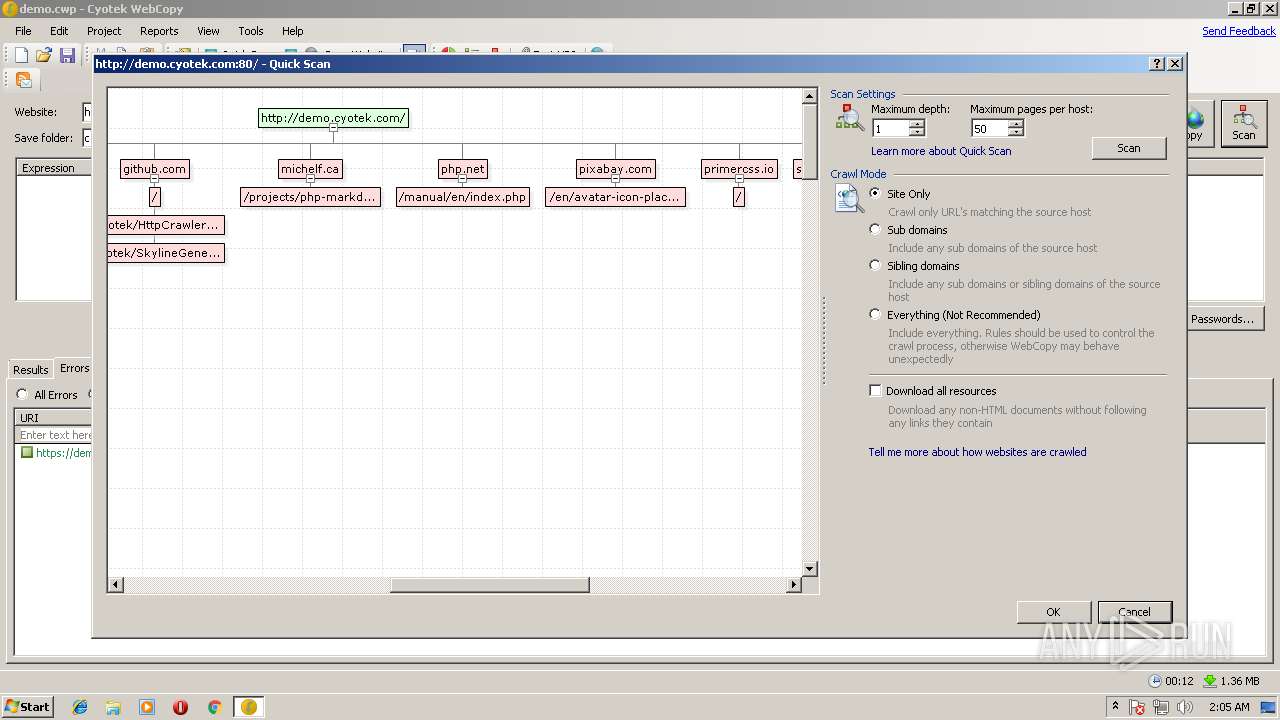
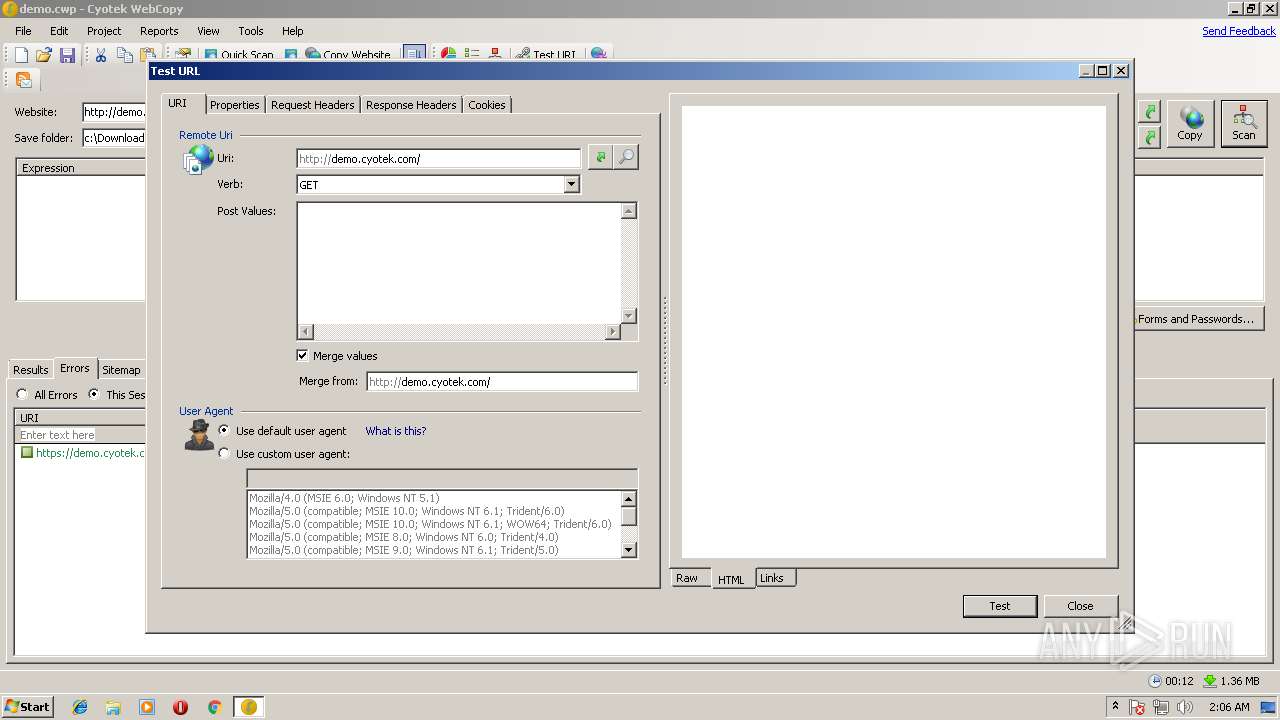
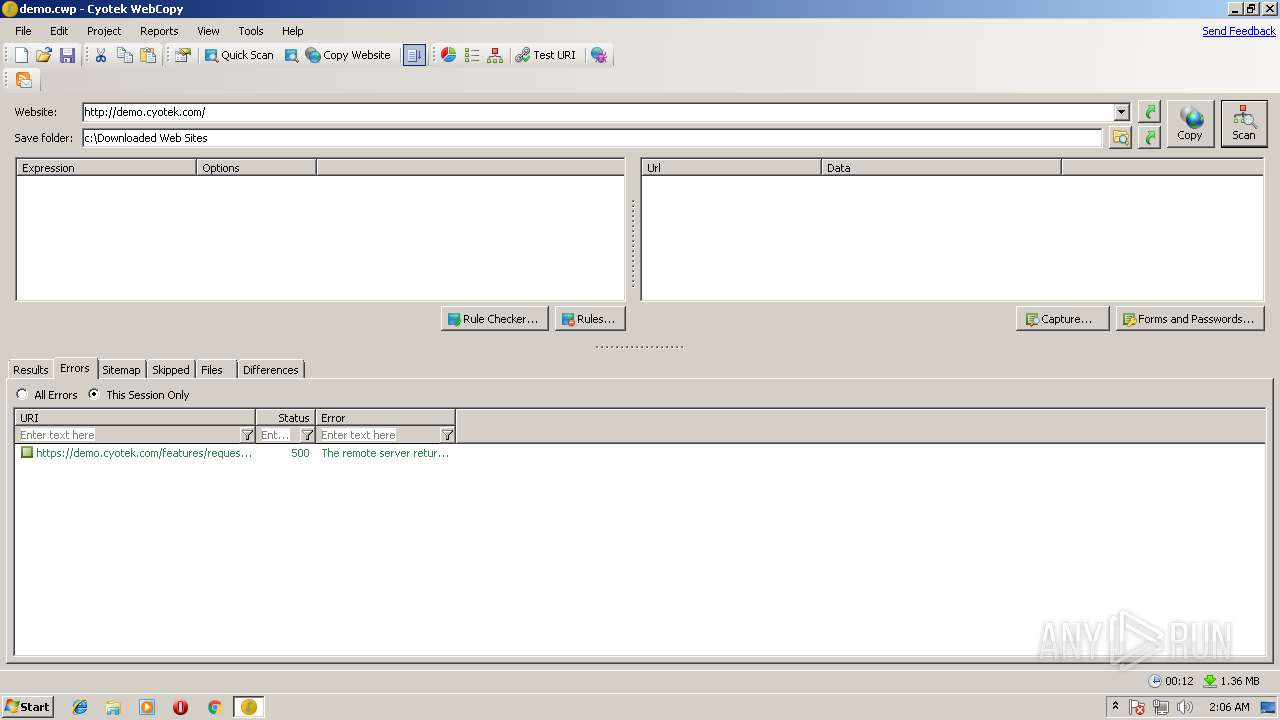
4068 | cyowcopy.exe | HEAD | 301 | 217.194.210.72:80 | http://demo.cyotek.com/ | GB | — | — | unknown |
4068 | cyowcopy.exe | GET | 301 | 217.194.210.66:80 | http://www.cyotek.com/products/rss/cyowcopy?titlesOnly=true | GB | html | 183 b | whitelisted |
4068 | cyowcopy.exe | GET | 200 | 192.35.177.64:80 | http://apps.identrust.com/roots/dstrootcax3.p7c | US | cat | 893 b | shared |
4068 | cyowcopy.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 52.8 Kb | whitelisted |
2940 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
4068 | cyowcopy.exe | HEAD | 301 | 217.194.210.72:80 | http://demo.cyotek.com/ | GB | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4068 | cyowcopy.exe | 217.194.210.66:443 | www.cyotek.com | iomart Cloud Services Limited. | GB | unknown |
4068 | cyowcopy.exe | 192.35.177.64:80 | apps.identrust.com | IdenTrust | US | malicious |
4068 | cyowcopy.exe | 93.184.221.240:80 | www.download.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
4068 | cyowcopy.exe | 217.194.210.72:80 | demo.cyotek.com | iomart Cloud Services Limited. | GB | unknown |
4068 | cyowcopy.exe | 217.194.210.72:443 | demo.cyotek.com | iomart Cloud Services Limited. | GB | unknown |
4068 | cyowcopy.exe | 217.194.210.66:80 | www.cyotek.com | iomart Cloud Services Limited. | GB | unknown |
2940 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.cyotek.com |
| unknown |
apps.identrust.com |
| shared |
www.download.windowsupdate.com |
| whitelisted |
demo.cyotek.com |
| unknown |
www.bing.com |
| whitelisted |