| File name: | Release.exe |
| Full analysis: | https://app.any.run/tasks/77efd3ce-4fcc-4b51-8c1a-f4608e375c70 |
| Verdict: | Malicious activity |
| Analysis date: | April 24, 2019, 00:17:03 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | B4D43B1BA8A82249EEBD02FCA8D60C71 |
| SHA1: | 4358507897499E77CFDA0A811ABECE927A7C97DA |
| SHA256: | BCC7B1F96EDE9AD181FBB7E28F61AA0CFD48BC718926B5D0A06D79457E508F3B |
| SSDEEP: | 24576:yJlh9bDtPUiRHPSQ7BP5xqrR/1jNGdWRwhwO7UzzylxDLjpqCA:yJ/U7Q9P5xGedWRwhw6uzUxDLjpy |
MALICIOUS
Application was dropped or rewritten from another process
- ARM.exe (PID: 2980)
Loads dropped or rewritten executable
- ARM.exe (PID: 2980)
Actions looks like stealing of personal data
- ARM.exe (PID: 2980)
SUSPICIOUS
Executable content was dropped or overwritten
- Release.exe (PID: 2848)
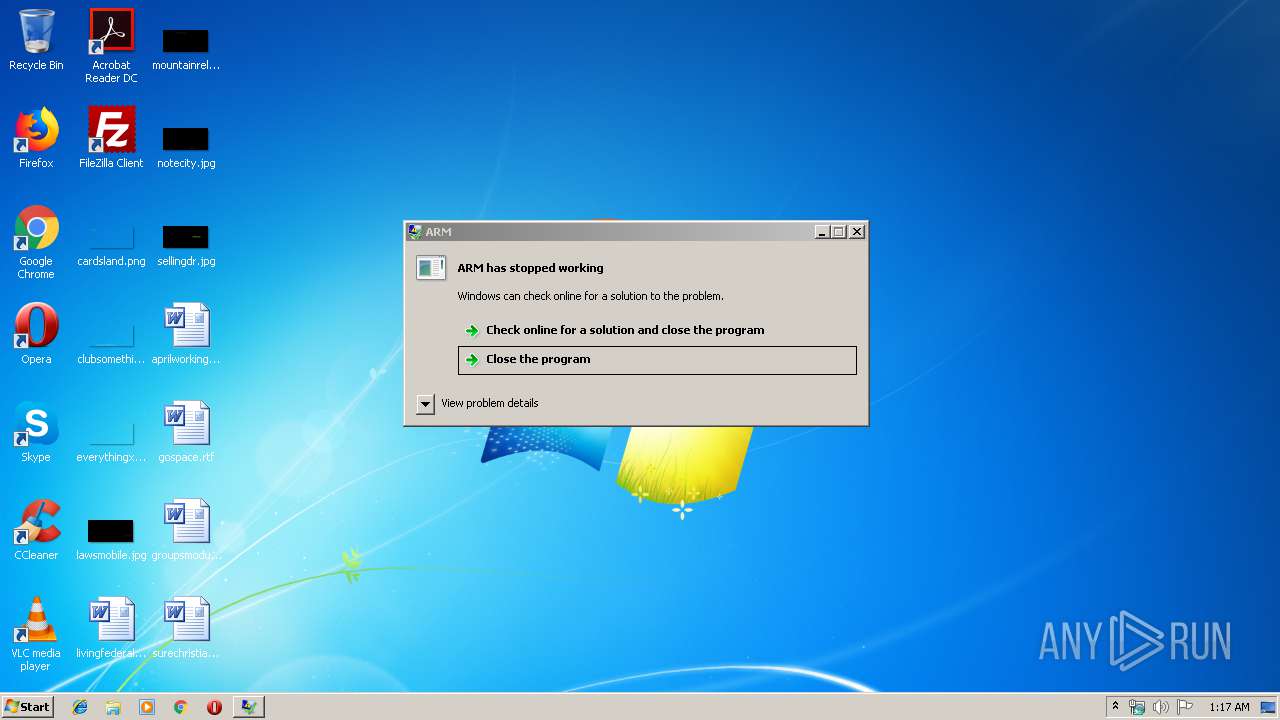
INFO
Application was crashed
- ARM.exe (PID: 2980)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:08:14 21:15:49+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 188416 |
| InitializedDataSize: | 69632 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1cab5 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 14-Aug-2016 19:15:49 |
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 14-Aug-2016 19:15:49 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0002DFE8 | 0x0002E000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.71025 |
.rdata | 0x0002F000 | 0x000099D0 | 0x00009A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.15287 |
.data | 0x00039000 | 0x0001F8B8 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.29547 |
.gfids | 0x00059000 | 0x000000F0 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.12367 |
.rsrc | 0x0005A000 | 0x00004714 | 0x00004800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.17139 |
.reloc | 0x0005F000 | 0x00001F8C | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.62986 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.25329 | 1875 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 3.88998 | 1384 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 4.12176 | 744 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 4.68705 | 2216 | Latin 1 / Western European | UNKNOWN | RT_ICON |
7 | 3.66634 | 508 | Latin 1 / Western European | UNKNOWN | RT_STRING |
8 | 3.71728 | 582 | Latin 1 / Western European | UNKNOWN | RT_STRING |
9 | 3.74776 | 476 | Latin 1 / Western European | UNKNOWN | RT_STRING |
10 | 3.55807 | 220 | Latin 1 / Western European | UNKNOWN | RT_STRING |
11 | 3.90128 | 1128 | Latin 1 / Western European | UNKNOWN | RT_STRING |
12 | 3.68258 | 356 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
COMCTL32.dll (delay-loaded) |
KERNEL32.dll |
Total processes
34
Monitored processes
2
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2848 | "C:\Users\admin\AppData\Local\Temp\Release.exe" | C:\Users\admin\AppData\Local\Temp\Release.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2980 | "C:\Users\admin\AppData\Local\Temp\sdfsdfsd\ARM.exe" | C:\Users\admin\AppData\Local\Temp\sdfsdfsd\ARM.exe | Release.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: ARM Exit code: 3762504530 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
370
Read events
366
Write events
4
Delete events
0
Modification events
| (PID) Process: | (2848) Release.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2848) Release.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
4
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2848 | Release.exe | C:\Users\admin\AppData\Local\Temp\sdfsdfsd\ARM.exe | executable | |
MD5:— | SHA256:— | |||
| 2980 | ARM.exe | C:\Users\admin\AppData\Local\arm.logs\FileZilla\info.txt | text | |
MD5:— | SHA256:— | |||
| 2848 | Release.exe | C:\Users\admin\AppData\Local\Temp\sdfsdfsd\Newtonsoft.Json.dll | executable | |
MD5:633E5B8199D4FA9F43F088099375044B | SHA256:73919F46FA73CF7B9407BC3806719C7738C55BAE10A75890545069F0441EE74D | |||
| 2980 | ARM.exe | C:\Users\admin\AppData\Local\arm.logs\Discord\info.txt | text | |
MD5:9BB181C80AE642BB1E5A6C33DC3A6FF7 | SHA256:6FF04E0CF3FBC0AFD2391D09675ABC0D906833F1E8CAB2DDE5BDCF121CBE4ADE | |||
| 2848 | Release.exe | C:\Users\admin\AppData\Local\Temp\sdfsdfsd\System.Data.SQLite.dll | executable | |
MD5:D22A635632C52DDBCADBA773E69A927D | SHA256:4DB46839D5C6CBFABBD6B1F61B3B9AD5A725B0B0F84F5A0AB12694F7B8320AC9 | |||
| 2848 | Release.exe | C:\Users\admin\AppData\Local\Temp\sdfsdfsd\SQLite.Interop.dll | executable | |
MD5:300869D92CC4A8EACE34418C23A42ADB | SHA256:98D78727D940C8F7B67EF7CA17743AA50B883A7CB9B26614D85B5D57C3863A69 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report