analyze malware
- Huge database of samples and IOCs
- Custom VM setup
- Unlimited submissions
- Interactive approach
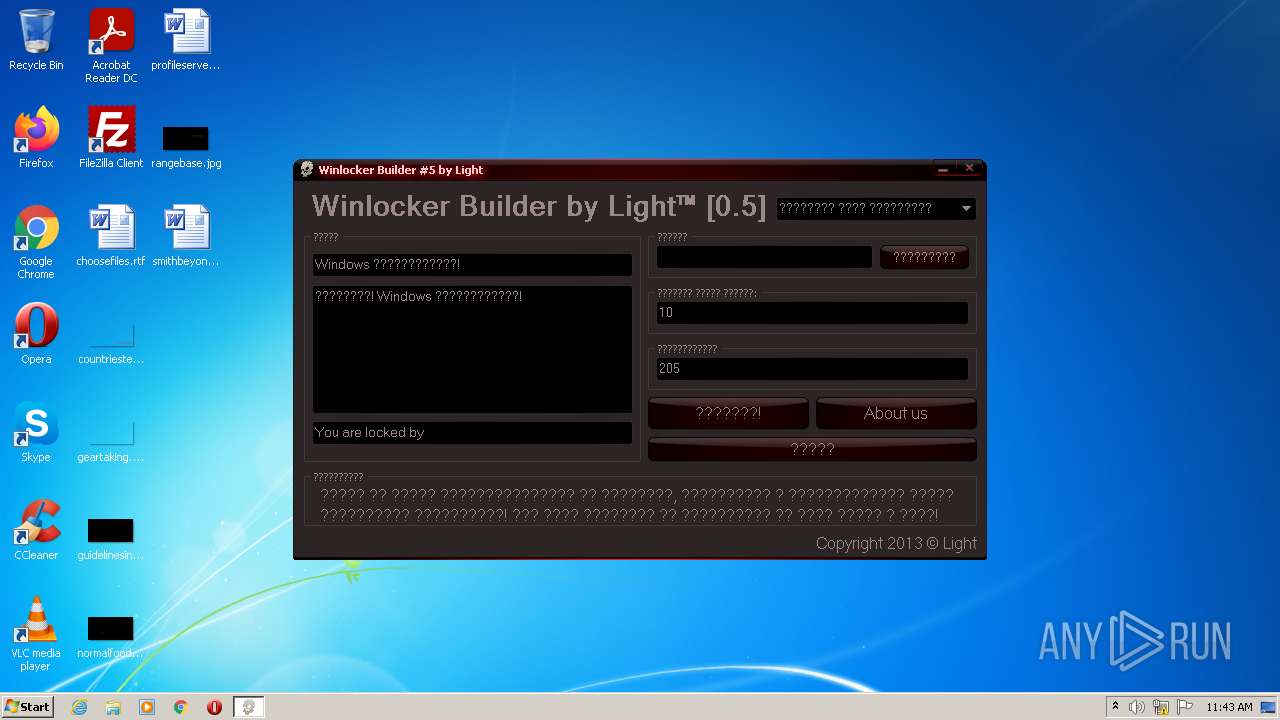
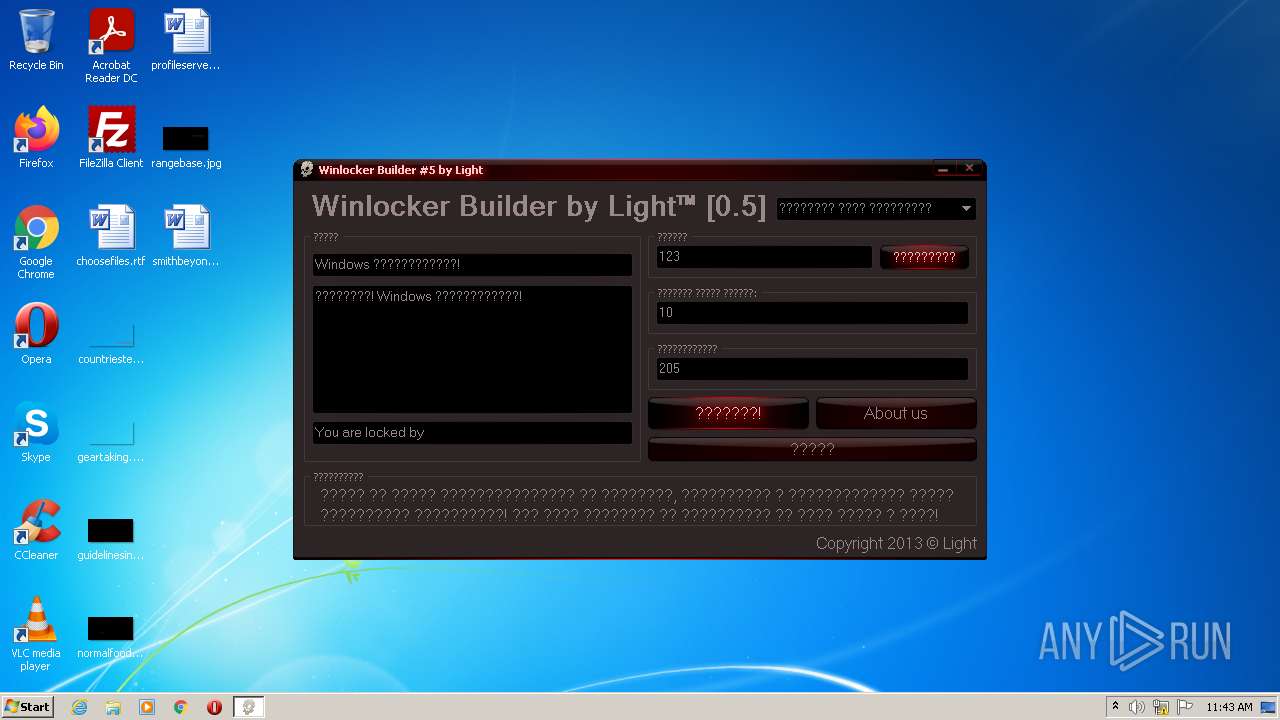
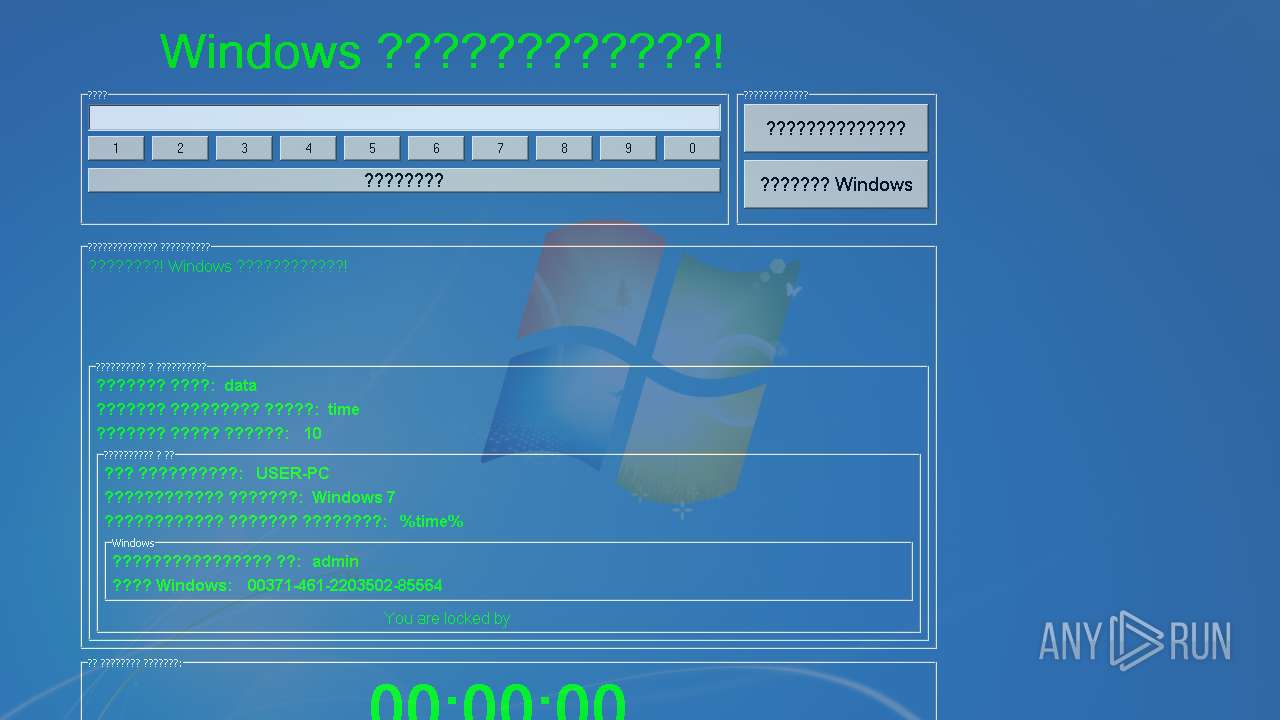
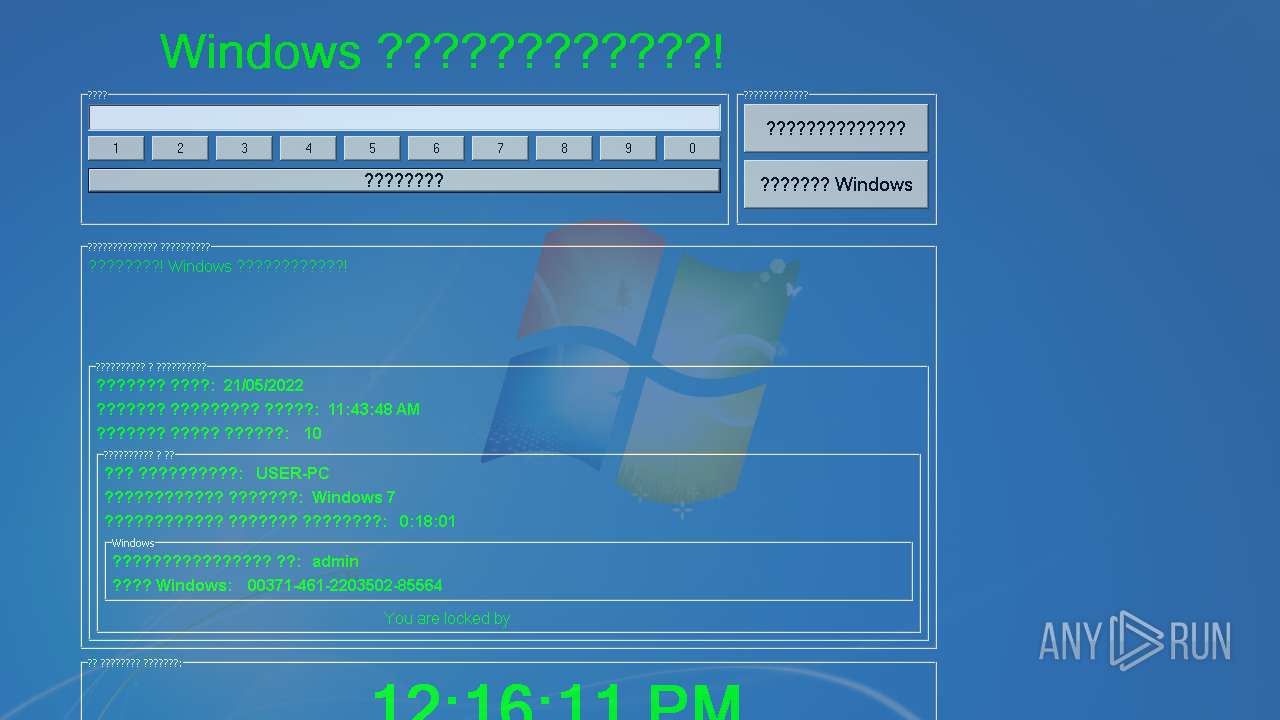
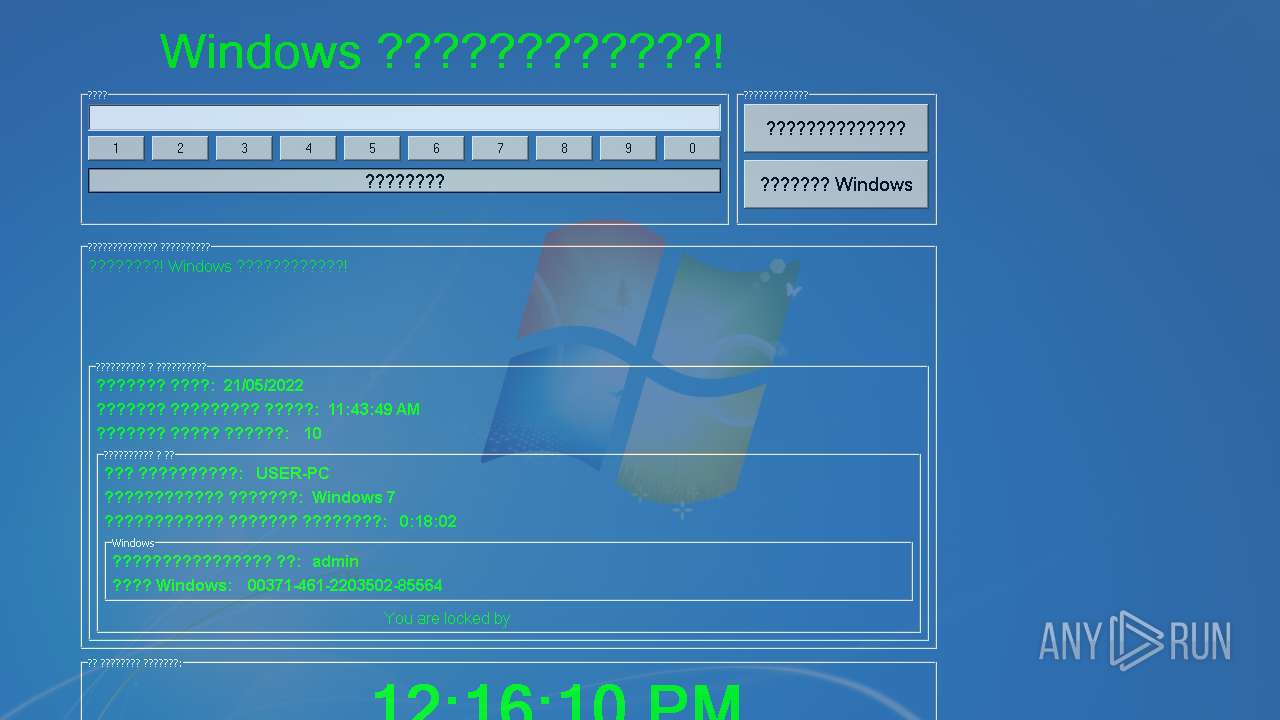
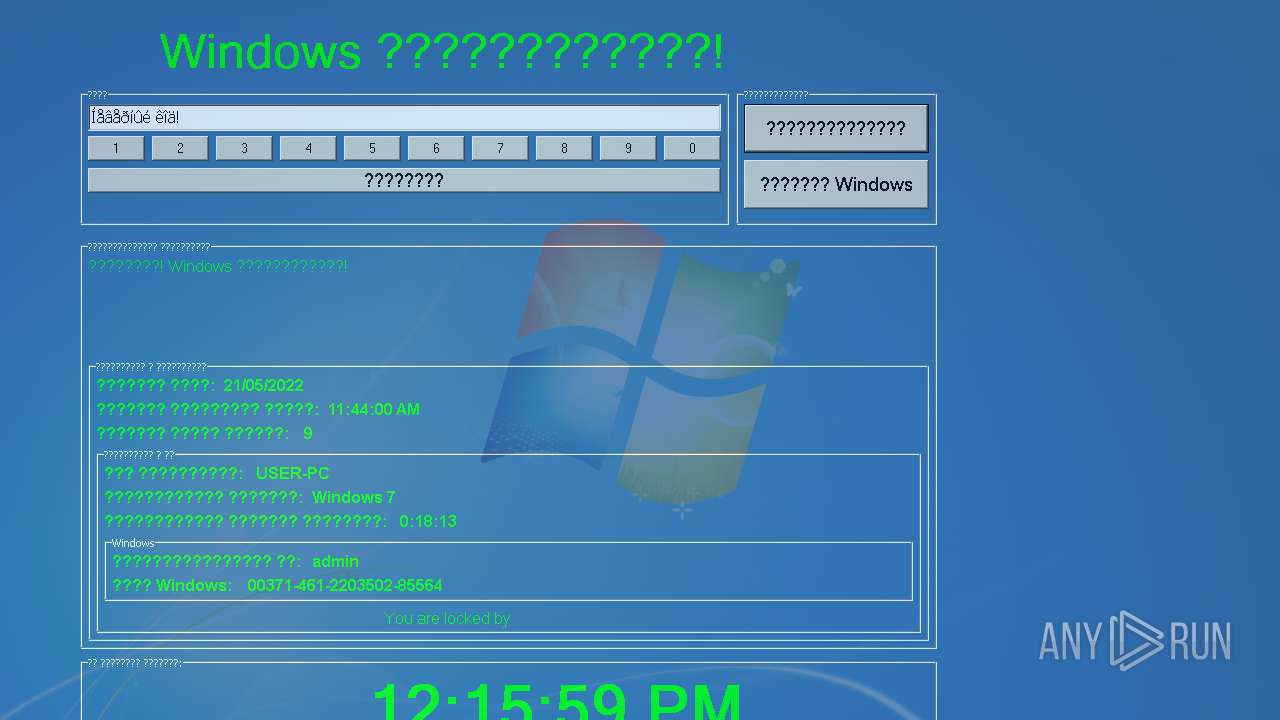
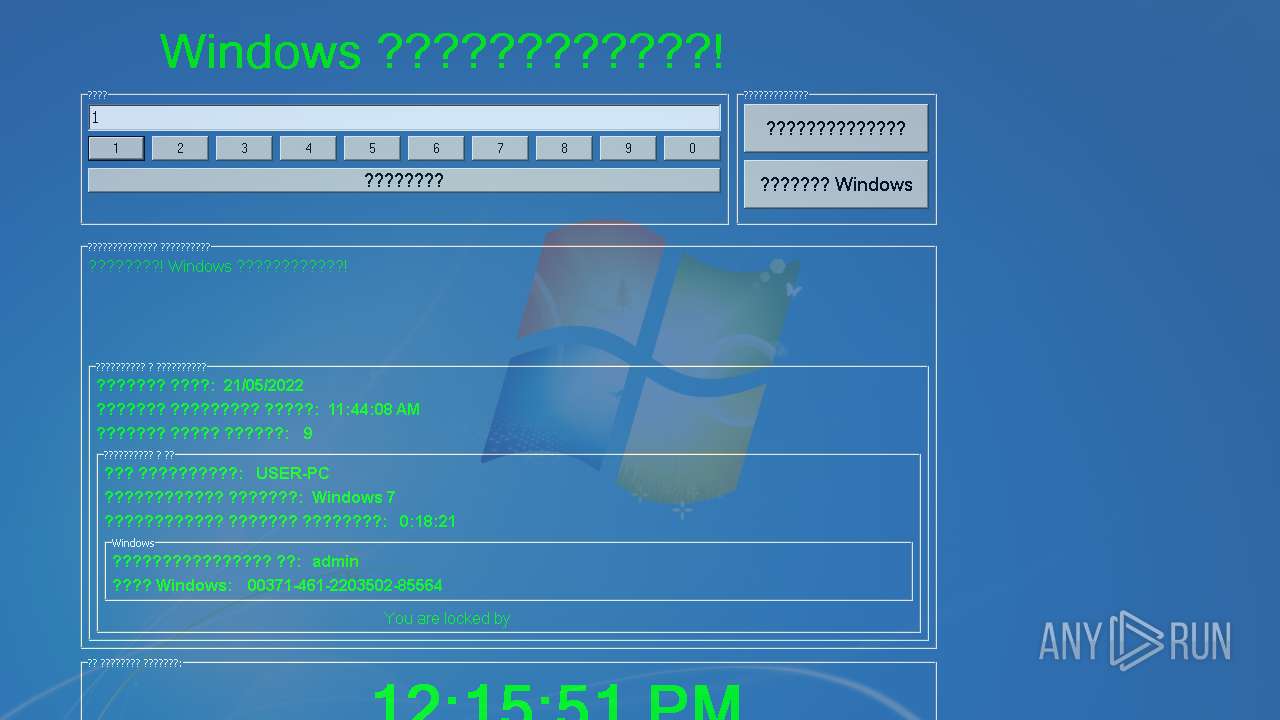
| File name: | Winlocker builder 0.5.exe |
| Full analysis: | https://app.any.run/tasks/d18a5ca3-b0b1-4dff-9fce-1c72a0eb05c6 |
| Verdict: | Malicious activity |
| Analysis date: | May 21, 2022, 10:43:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | CEC938ABA350D8D70D79407EC5C148BD |
| SHA1: | F92898A9B87C739AD6896472275B4F53E927DF48 |
| SHA256: | BCC15645592A6ADD5C91D3D097E63E8775B949BE72DE33FD7B06C5197C9A40FE |
| SSDEEP: | 24576:gIIsRnWG/PqWDA1E3KFcMJboKwk4BVxfAOR+iHOUiT4pSUCpM2W1GvgmrTsexT+0:lIGnWZ7iKwk4hfpKTSxC61GrTs8 |
MALICIOUS
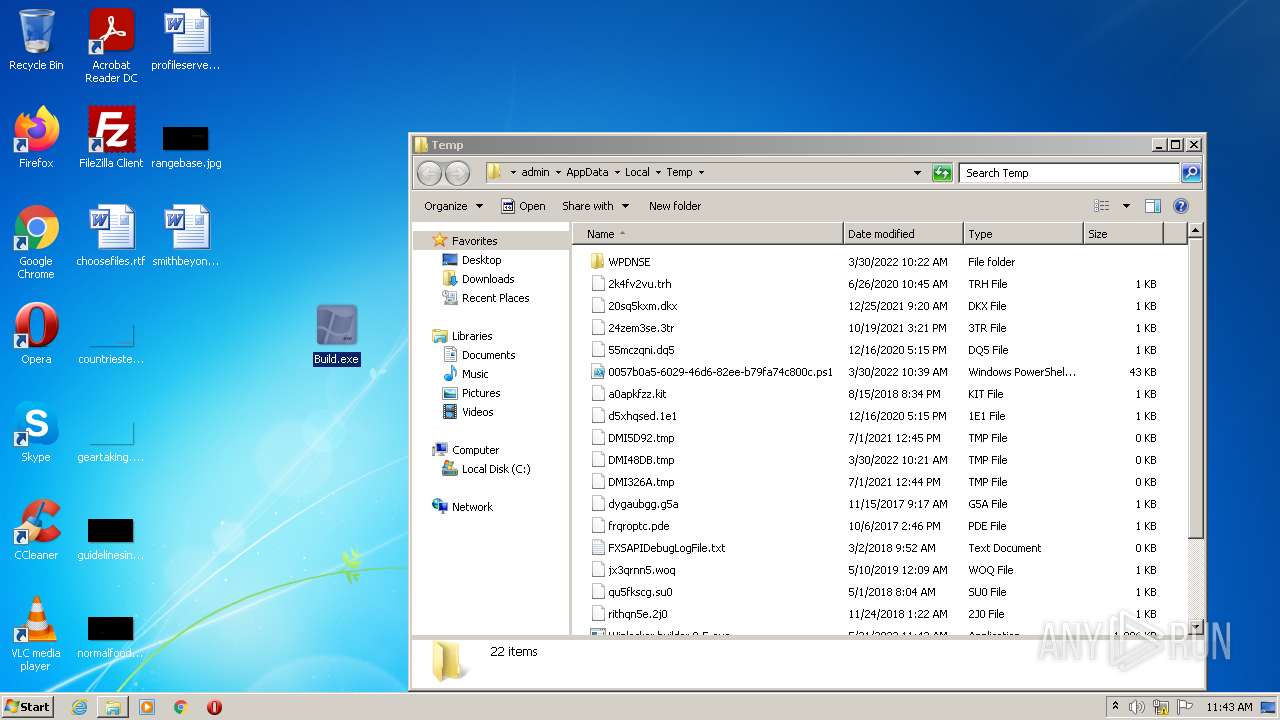
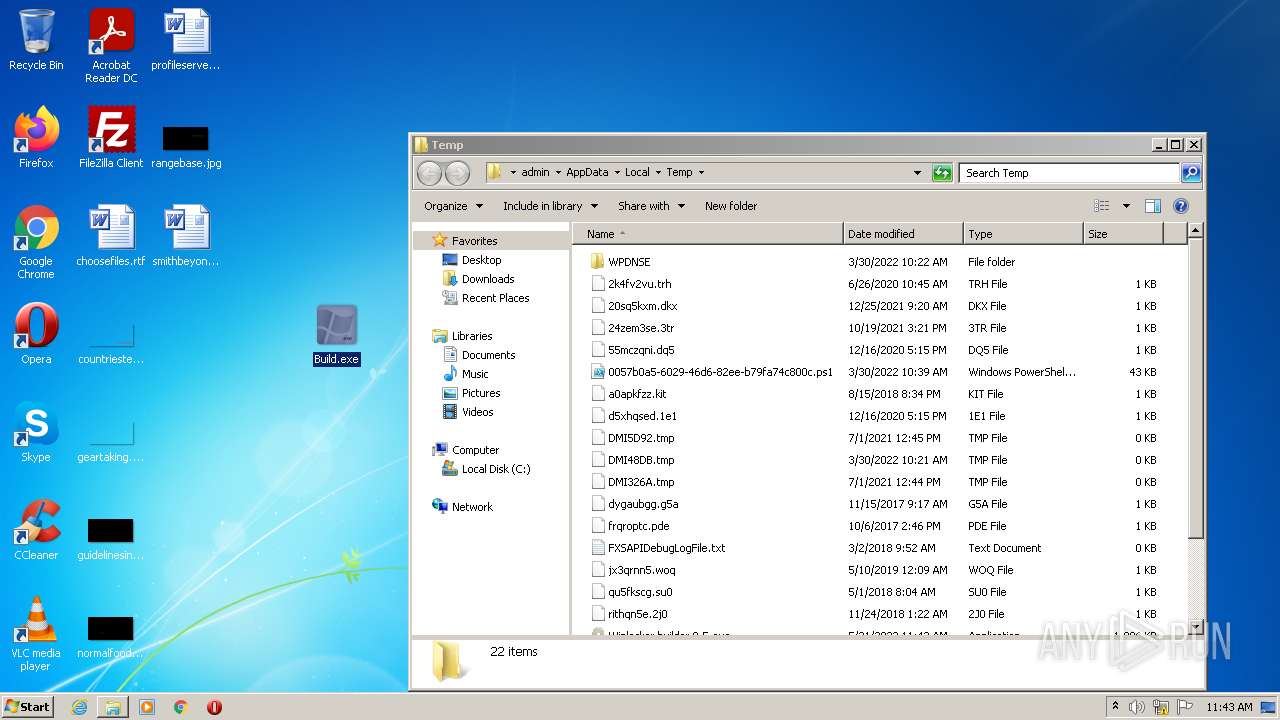
Drops executable file immediately after starts
- Winlocker builder 0.5.exe (PID: 2992)
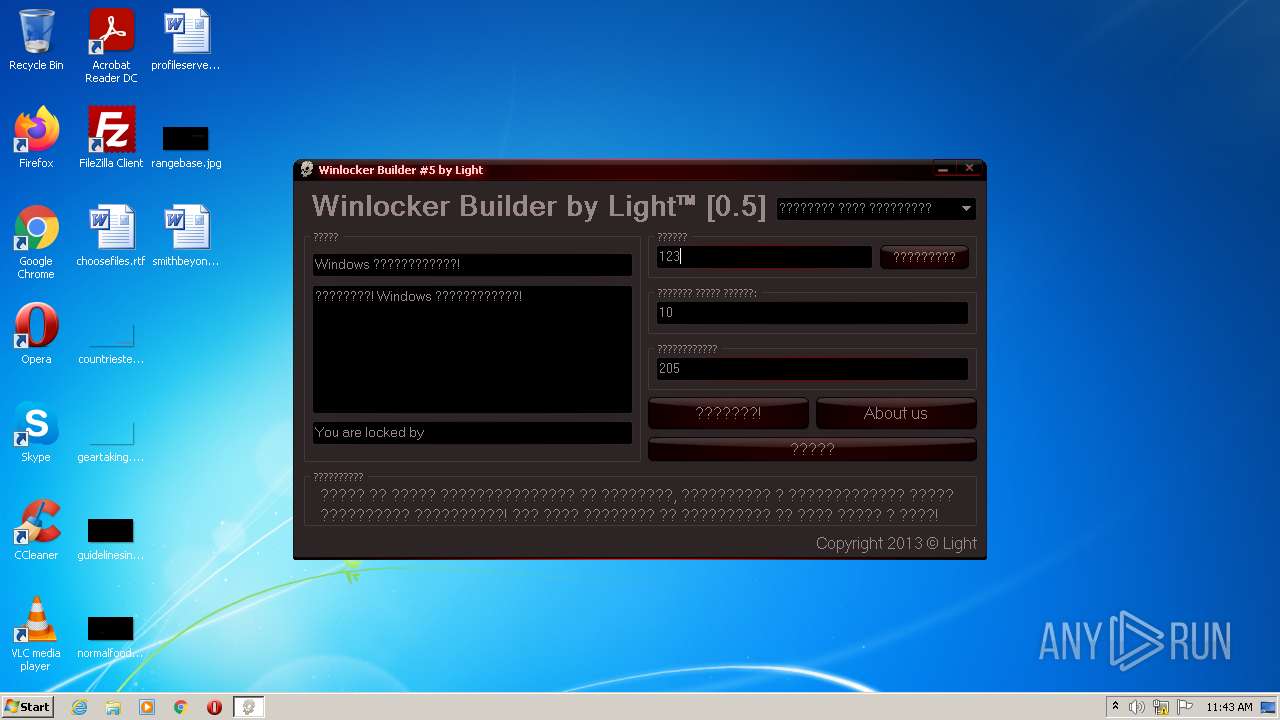
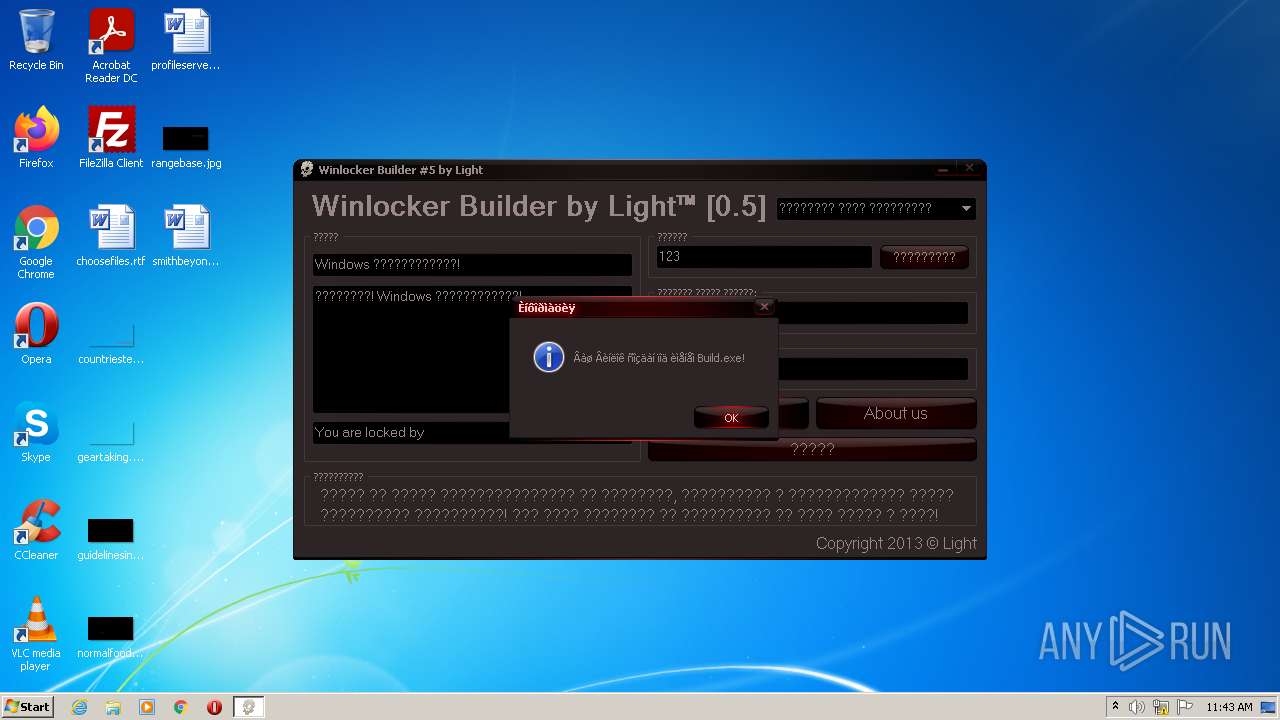
Application was dropped or rewritten from another process
- Build.exe (PID: 2044)
Changes the autorun value in the registry
- Build.exe (PID: 2044)
Changes the login/logoff helper path in the registry
- Build.exe (PID: 2044)
Loads the Task Scheduler COM API
- explorer.exe (PID: 1952)
SUSPICIOUS
Checks supported languages
- Winlocker builder 0.5.exe (PID: 2992)
- Build.exe (PID: 2044)
Reads the computer name
- Winlocker builder 0.5.exe (PID: 2992)
- Build.exe (PID: 2044)
Executable content was dropped or overwritten
- Winlocker builder 0.5.exe (PID: 2992)
Drops a file with a compile date too recent
- Winlocker builder 0.5.exe (PID: 2992)
Reads Windows owner or organization settings
- Build.exe (PID: 2044)
Reads the date of Windows installation
- explorer.exe (PID: 1952)
Reads Windows Product ID
- Build.exe (PID: 2044)
Reads default file associations for system extensions
- explorer.exe (PID: 1952)
INFO
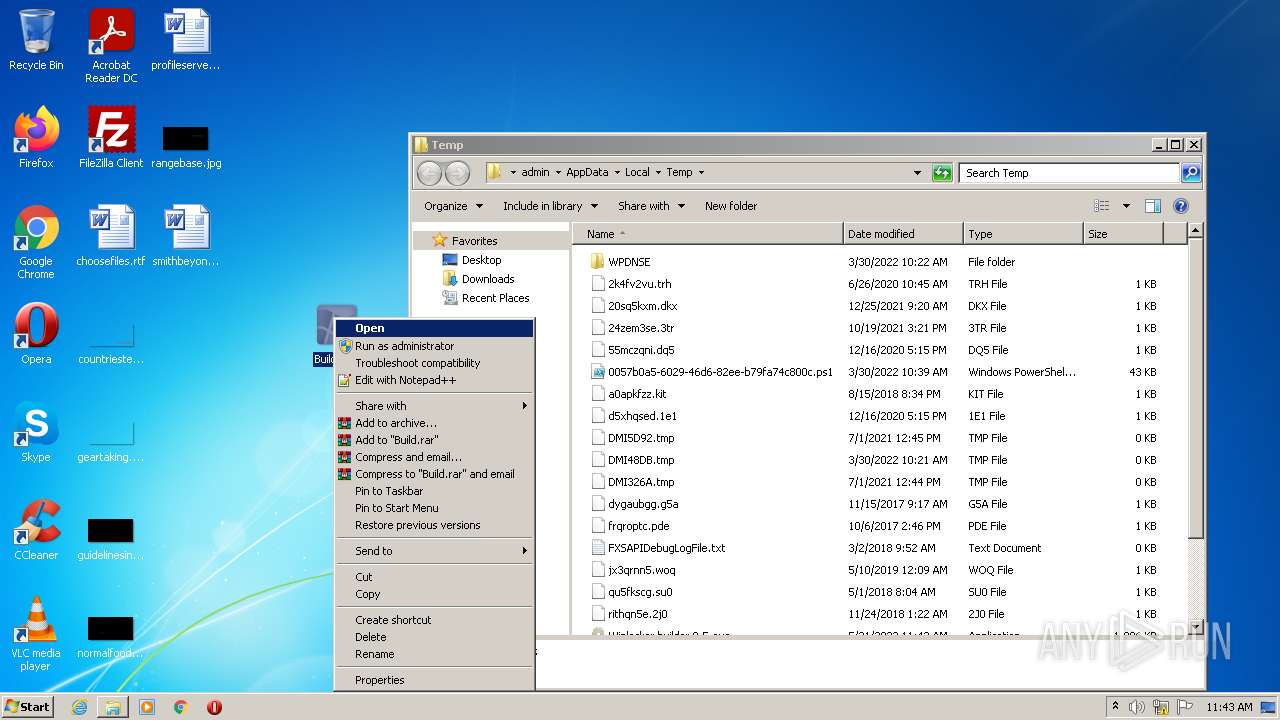
Manual execution by user
- verclsid.exe (PID: 2412)
- Build.exe (PID: 2044)
Checks supported languages
- verclsid.exe (PID: 2412)
- explorer.exe (PID: 1952)
Reads the computer name
- explorer.exe (PID: 1952)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Borland Delphi 7 (46.9) |
|---|---|---|
| .exe | | | Win32 Executable Borland Delphi 5 (31.8) |
| .exe | | | Win32 Executable Borland Delphi 6 (18.5) |
| .exe | | | Win32 Executable Delphi generic (1) |
| .scr | | | Windows screen saver (0.9) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x117488 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 902144 |
| CodeSize: | 1140224 |
| LinkerVersion: | 2.25 |
| PEType: | PE32 |
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x001164E8 | 0x00116600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.53612 |
DATA | 0x00118000 | 0x00004D30 | 0x00004E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.46387 |
BSS | 0x0011D000 | 0x00001085 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0011F000 | 0x00002690 | 0x00002800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.95623 |
.tls | 0x00122000 | 0x00000010 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00123000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.20692 |
.reloc | 0x00124000 | 0x0000CF58 | 0x0000D000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 6.69537 |
.rsrc | 0x00131000 | 0x000C7C00 | 0x000C7C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 7.09933 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.17015 | 752 | UNKNOWN | Russian - Russia | RT_MANIFEST |
2 | 2.80231 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
3 | 3.00046 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
4 | 2.56318 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
5 | 2.6949 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
6 | 2.62527 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
7 | 2.91604 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
3682 | 2.04342 | 76 | UNKNOWN | UNKNOWN | RT_STRING |
3683 | 2.92331 | 170 | UNKNOWN | UNKNOWN | RT_STRING |
3684 | 3.47221 | 390 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
gdi32.dll |
kernel32.dll |
ole32.dll |
oleaut32.dll |
shell32.dll |
user32.dll |
version.dll |
Total processes
43
Monitored processes
4
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
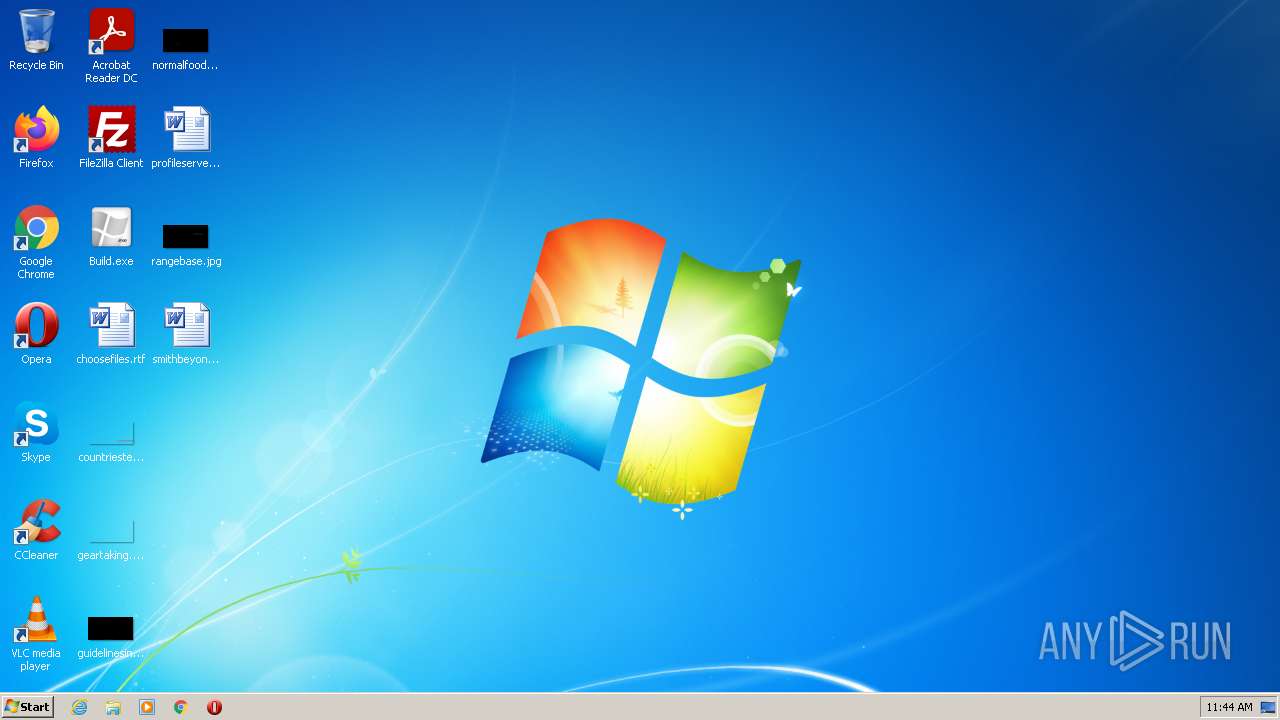
| 2992 | "C:\Users\admin\AppData\Local\Temp\Winlocker builder 0.5.exe" | C:\Users\admin\AppData\Local\Temp\Winlocker builder 0.5.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2412 | "C:\Windows\system32\verclsid.exe" /S /C {0B2C9183-C9FA-4C53-AE21-C900B0C39965} /I {0C733A8A-2A1C-11CE-ADE5-00AA0044773D} /X 0x401 | C:\Windows\system32\verclsid.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Extension CLSID Verification Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2044 | "C:\Users\admin\Desktop\Build.exe" | C:\Users\admin\Desktop\Build.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1952 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | Build.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Explorer Version: 6.1.7600.16385 (win7_rtm.090713-1255) | |||||||||||||||
Total events
3 670
Read events
3 564
Write events
103
Delete events
3
Modification events
| (PID) Process: | (2044) Build.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Winlogon |
| Operation: | write | Name: | Shell |
Value: C:\Users\admin\Desktop\Build.exe | |||
| (PID) Process: | (2044) Build.exe | Key: | HKEY_CURRENT_USER\System\CurrentControlSet\Control\SafeBoot |
| Operation: | write | Name: | AlternateShell |
Value: C:\Users\admin\Desktop\Build.exe | |||
| (PID) Process: | (2044) Build.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | userini |
Value: C:\Users\admin\Desktop\Build.exe | |||
| (PID) Process: | (2044) Build.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2044) Build.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2044) Build.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2044) Build.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2044) Build.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | delete value | Name: | userini |
Value: C:\Users\admin\Desktop\Build.exe | |||
| (PID) Process: | (2044) Build.exe | Key: | HKEY_CURRENT_USER\System\CurrentControlSet\Control\SafeBoot |
| Operation: | write | Name: | AlternateShell |
Value: cmd.exe | |||
| (PID) Process: | (2044) Build.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Winlogon |
| Operation: | write | Name: | Shell |
Value: Explorer.exe | |||
Executable files
1
Suspicious files
0
Text files
0
Unknown types
0
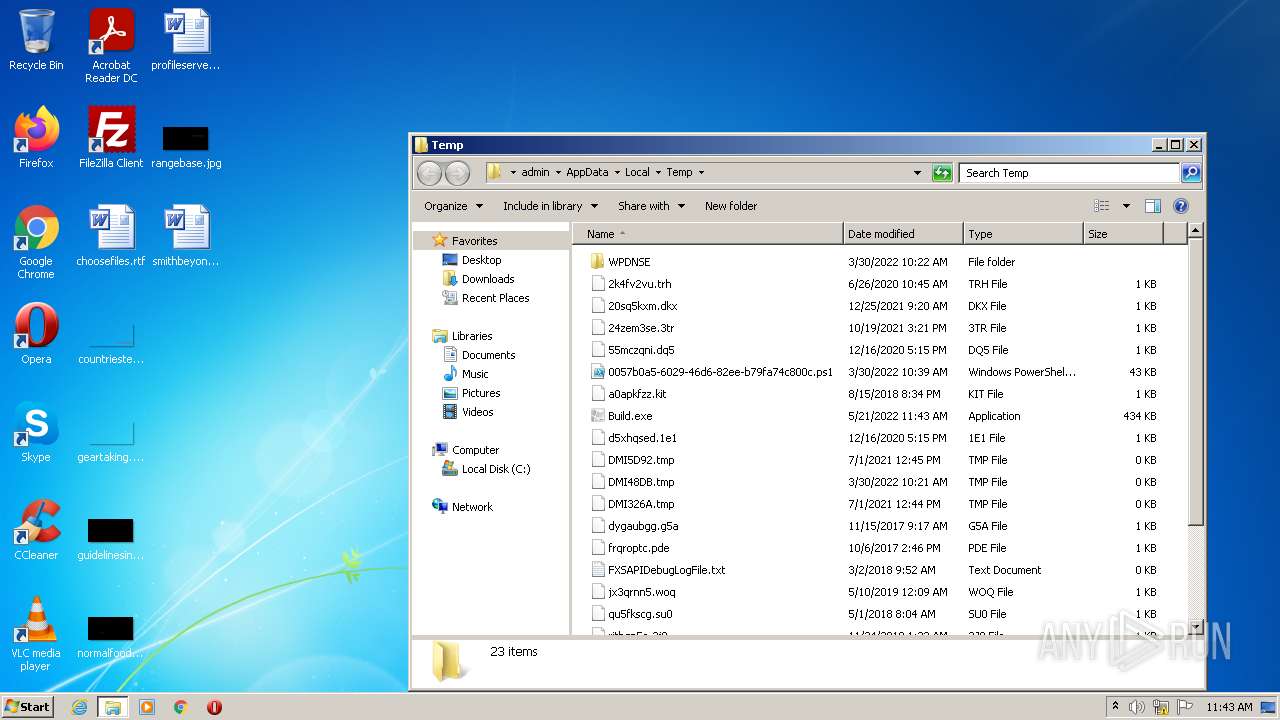
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2992 | Winlocker builder 0.5.exe | C:\Users\admin\AppData\Local\Temp\Build.exe | executable | |
MD5:A2D5336C6E3F7D22E1F0AEC6742F2FFE | SHA256:A90A88578CDB3C52F692901CB050A7A92698632DFCA2DF75EF44B417EA703431 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report