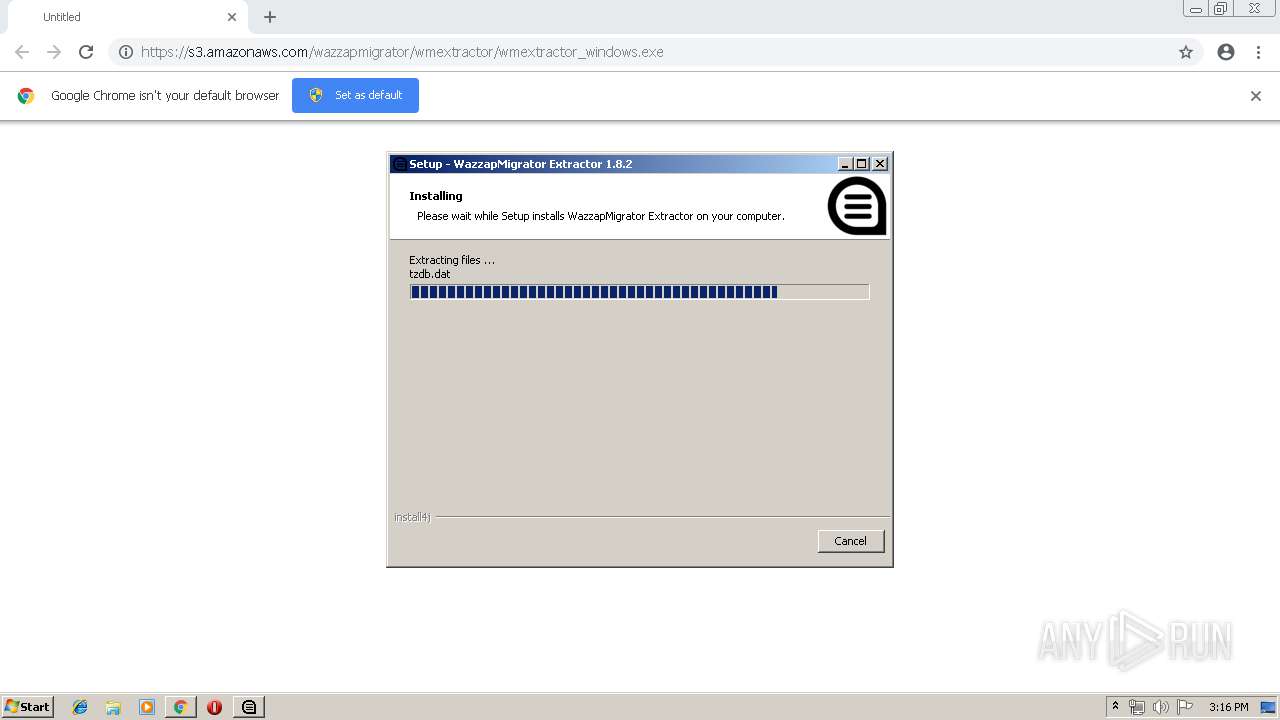
| URL: | https://s3.amazonaws.com/wazzapmigrator/wmextractor/wmextractor_windows.exe |
| Full analysis: | https://app.any.run/tasks/5fa77575-ca64-4446-8fa6-067339e82979 |
| Verdict: | Malicious activity |
| Analysis date: | May 25, 2019, 14:14:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 56C689FDF29F1988AC3A9E07E68ABD2B |
| SHA1: | B5F3FD3AEB5744DAC80E7044B06BB876B6B14061 |
| SHA256: | BCB37173A9088424EF1CE45E87574317285685092170DDE43764120D23CCA69E |
| SSDEEP: | 3:N8H7WtSE0VgXKP/TA:2H5JYKDA |
MALICIOUS
Loads dropped or rewritten executable
- unpack200.exe (PID: 2592)
- java.exe (PID: 1748)
- unpack200.exe (PID: 3180)
- wmextractor_windows.exe (PID: 2744)
- wmextractor_windows.exe (PID: 3124)
- WazzapMigrator Extractor.exe (PID: 980)
- java.exe (PID: 4044)
Application was dropped or rewritten from another process
- java.exe (PID: 1748)
- unpack200.exe (PID: 3180)
- unpack200.exe (PID: 2592)
- WazzapMigrator Extractor.exe (PID: 980)
- java.exe (PID: 4044)
- WazzapMigrator Extractor.exe (PID: 2860)
- WazzapMigrator Extractor.exe (PID: 3964)
- WazzapMigrator Extractor.exe (PID: 3068)
- WazzapMigrator Extractor.exe (PID: 1480)
SUSPICIOUS
Creates files in the user directory
- wmextractor_windows.exe (PID: 2744)
Application launched itself
- wmextractor_windows.exe (PID: 2744)
Executable content was dropped or overwritten
- wmextractor_windows.exe (PID: 2744)
- wmextractor_windows.exe (PID: 3124)
Creates a software uninstall entry
- wmextractor_windows.exe (PID: 3124)
Starts Internet Explorer
- WazzapMigrator Extractor.exe (PID: 980)
Creates files in the program directory
- WazzapMigrator Extractor.exe (PID: 980)
- wmextractor_windows.exe (PID: 3124)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2628)
INFO
Reads Internet Cache Settings
- chrome.exe (PID: 2628)
- iexplore.exe (PID: 3148)
- iexplore.exe (PID: 3172)
Application launched itself
- chrome.exe (PID: 2628)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3148)
Manual execution by user
- WazzapMigrator Extractor.exe (PID: 3964)
- WazzapMigrator Extractor.exe (PID: 2860)
- WazzapMigrator Extractor.exe (PID: 3068)
- WazzapMigrator Extractor.exe (PID: 1480)
Changes settings of System certificates
- iexplore.exe (PID: 3148)
Changes internet zones settings
- iexplore.exe (PID: 3172)
Reads internet explorer settings
- iexplore.exe (PID: 3148)
Creates files in the user directory
- iexplore.exe (PID: 3148)
Reads settings of System Certificates
- iexplore.exe (PID: 3148)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
80
Monitored processes
34
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 124 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=940,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3073130059320344791 --mojo-platform-channel-handle=4316 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 980 | "C:\Program Files\wmextractor\WazzapMigrator Extractor.exe" | C:\Program Files\wmextractor\WazzapMigrator Extractor.exe | wmextractor_windows.exe | ||||||||||||
User: admin Company: NBS SRL unipersonale Integrity Level: HIGH Description: WazzapMigrator Extractor Exit code: 0 Version: 1.8.2 Modules
| |||||||||||||||
| 1336 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=940,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3641485067689169148 --mojo-platform-channel-handle=4408 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1356 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=940,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13010302469510904847 --mojo-platform-channel-handle=4120 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1472 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=940,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=15161745938690816544 --mojo-platform-channel-handle=888 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1480 | "C:\Program Files\wmextractor\WazzapMigrator Extractor.exe" | C:\Program Files\wmextractor\WazzapMigrator Extractor.exe | explorer.exe | ||||||||||||
User: admin Company: NBS SRL unipersonale Integrity Level: HIGH Description: WazzapMigrator Extractor Exit code: 0 Version: 1.8.2 Modules
| |||||||||||||||
| 1660 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=940,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1069894889668734475 --mojo-platform-channel-handle=3932 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1748 | c:\users\admin\appdata\local\temp\E4J24C~1.TMP\jre\bin\java.exe -version | c:\users\admin\appdata\local\temp\E4J24C~1.TMP\jre\bin\java.exe | — | wmextractor_windows.exe | |||||||||||
User: admin Company: BellSoft Integrity Level: MEDIUM Description: LibericaJDK Platform binary Exit code: 0 Version: 12.0.1 Modules
| |||||||||||||||
| 1904 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=940,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --service-pipe-token=6540198023234917099 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6540198023234917099 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1928 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1912 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=940,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11276178747340085653 --mojo-platform-channel-handle=3980 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
1 938
Read events
1 732
Write events
199
Delete events
7
Modification events
| (PID) Process: | (2628) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2628) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2628) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2628) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2628) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2188) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2628-13203267296743375 |
Value: 259 | |||
| (PID) Process: | (2628) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2628) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2628) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (2628) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2628-13203267296743375 |
Value: 259 | |||
Executable files
177
Suspicious files
40
Text files
600
Unknown types
22
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2628 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2628 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2628 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2628 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 2628 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 2628 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\f83d95c4-d131-4416-aa73-a5e425c33f4d.tmp | — | |
MD5:— | SHA256:— | |||
| 2628 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2628 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2628 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2628 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
45
DNS requests
33
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2628 | chrome.exe | GET | 200 | 209.85.165.43:80 | http://r5---sn-q4flrn7d.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=85.203.20.11&mm=28&mn=sn-q4flrn7d&ms=nvh&mt=1558793260&mv=u&pl=24&shardbypass=yes | US | crx | 842 Kb | whitelisted |
2628 | chrome.exe | GET | 302 | 216.58.207.46:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 503 b | whitelisted |
3172 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
3148 | iexplore.exe | GET | 200 | 52.85.182.216:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
2628 | chrome.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 56.1 Kb | whitelisted |
3148 | iexplore.exe | GET | 301 | 213.171.183.166:80 | http://www.wazzapmigrator.com/faq/how-get-unencrypted-itunes-backup | IT | html | 364 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 213.171.183.166:80 | www.wazzapmigrator.com | SEEWEB s.r.l. | IT | unknown |
3148 | iexplore.exe | 216.58.207.74:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3172 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3148 | iexplore.exe | 213.171.183.166:443 | www.wazzapmigrator.com | SEEWEB s.r.l. | IT | unknown |
2628 | chrome.exe | 172.217.16.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2628 | chrome.exe | 172.217.22.109:443 | accounts.google.com | Google Inc. | US | whitelisted |
2628 | chrome.exe | 172.217.23.132:443 | www.google.com | Google Inc. | US | whitelisted |
2628 | chrome.exe | 216.58.208.35:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2628 | chrome.exe | 172.217.22.78:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
2628 | chrome.exe | 52.216.227.211:443 | s3.amazonaws.com | Amazon.com, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
s3.amazonaws.com |
| shared |
accounts.google.com |
| shared |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |