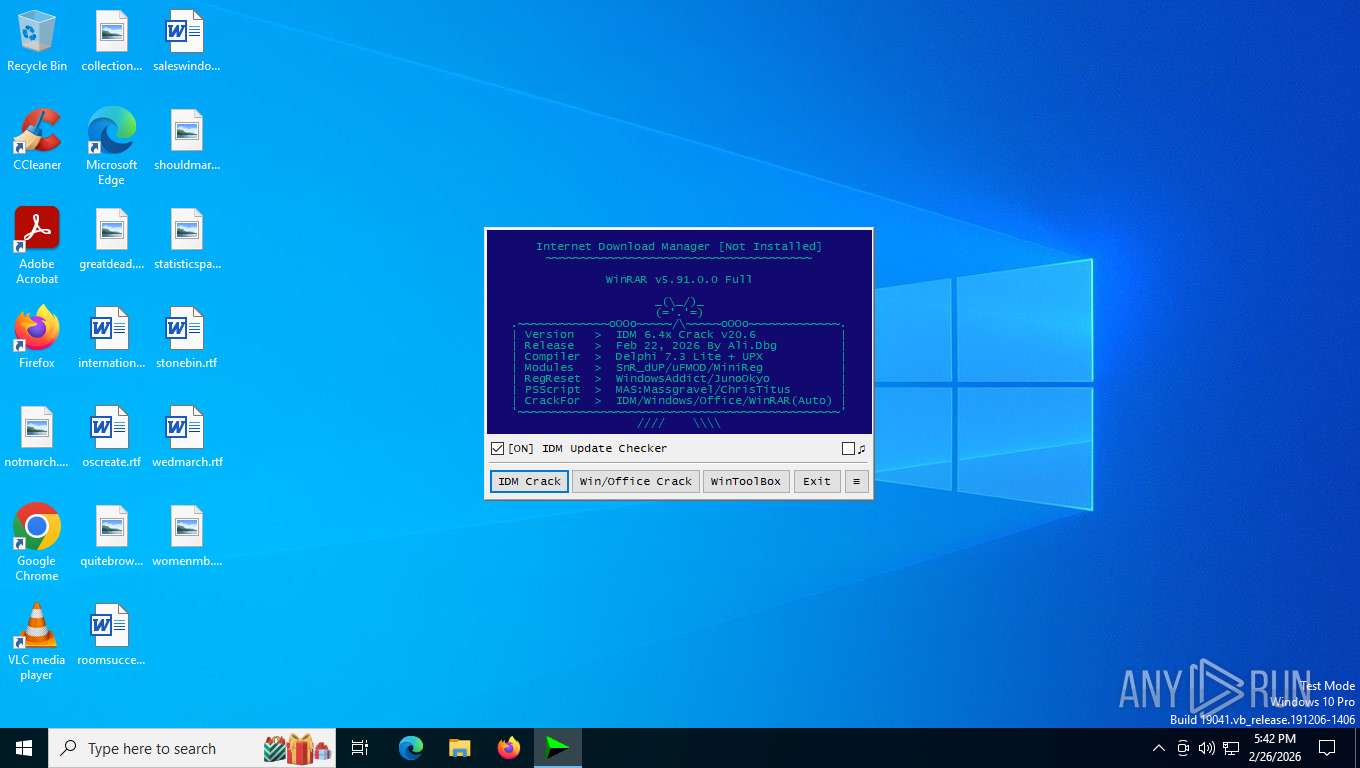
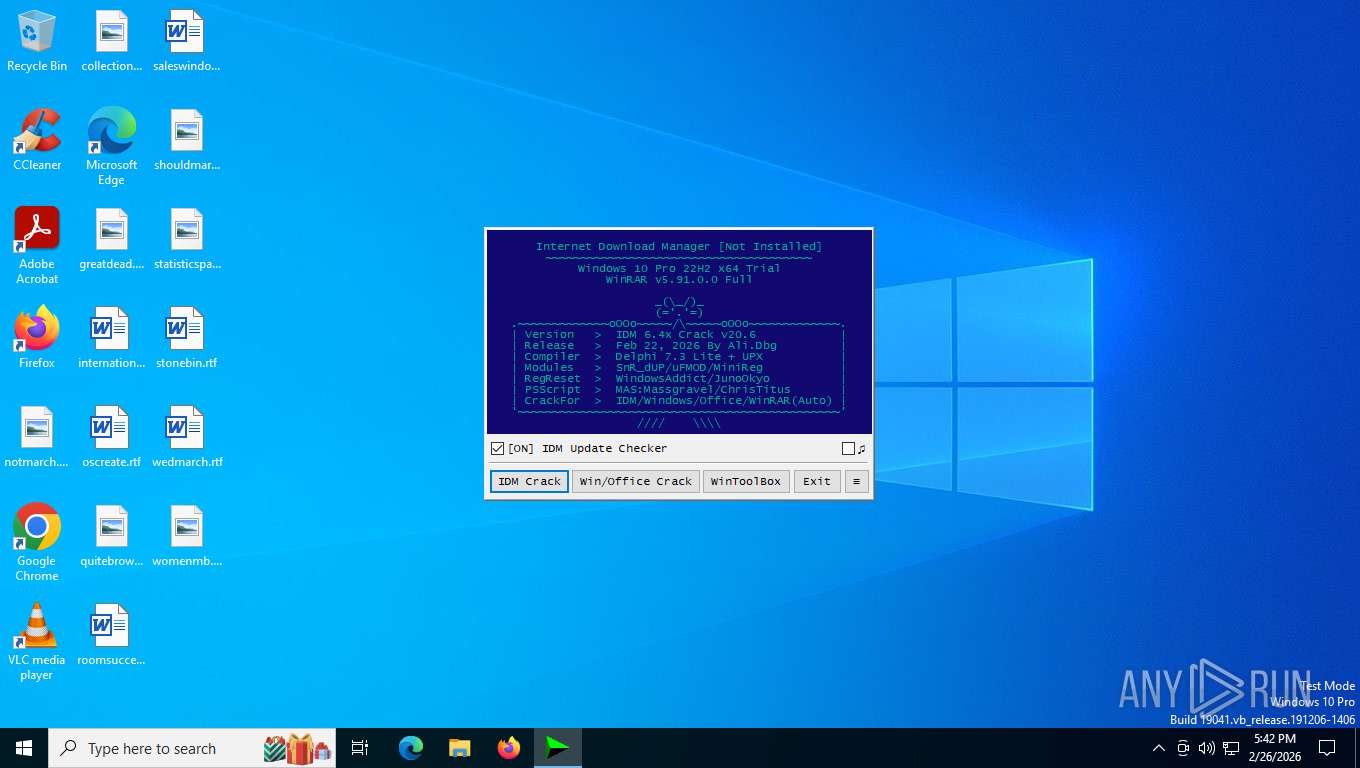
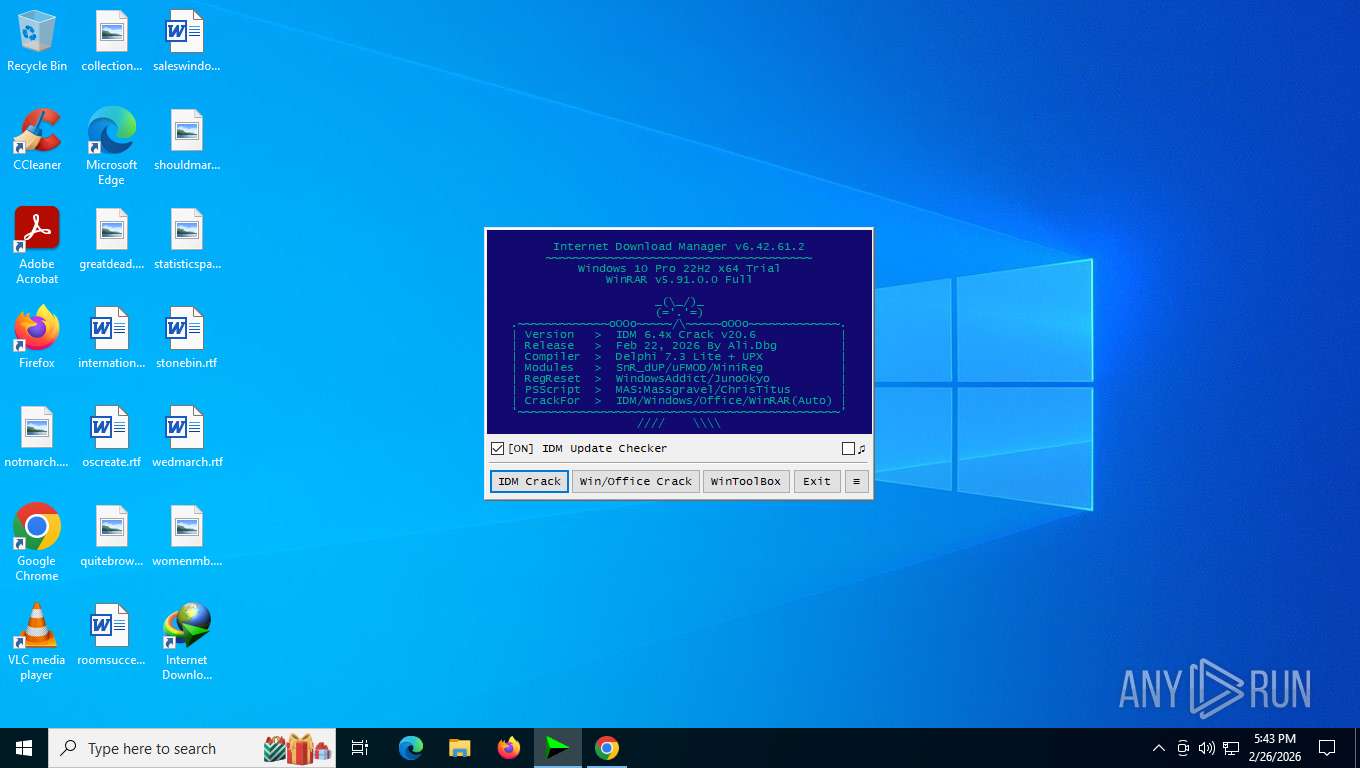
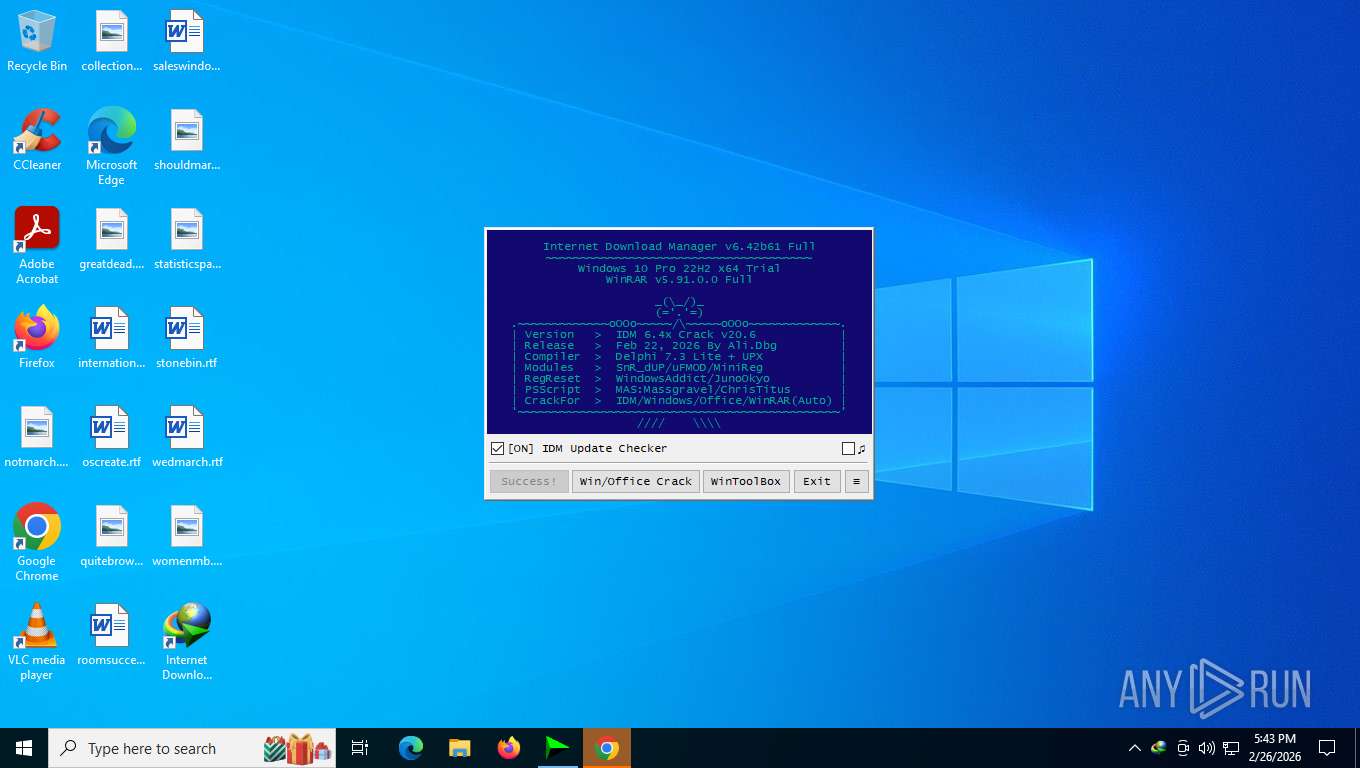
| File name: | IDM_6.4x_Crack_v20.6.exe |
| Full analysis: | https://app.any.run/tasks/7ab6d075-1c23-4adb-8caa-41c641e55342 |
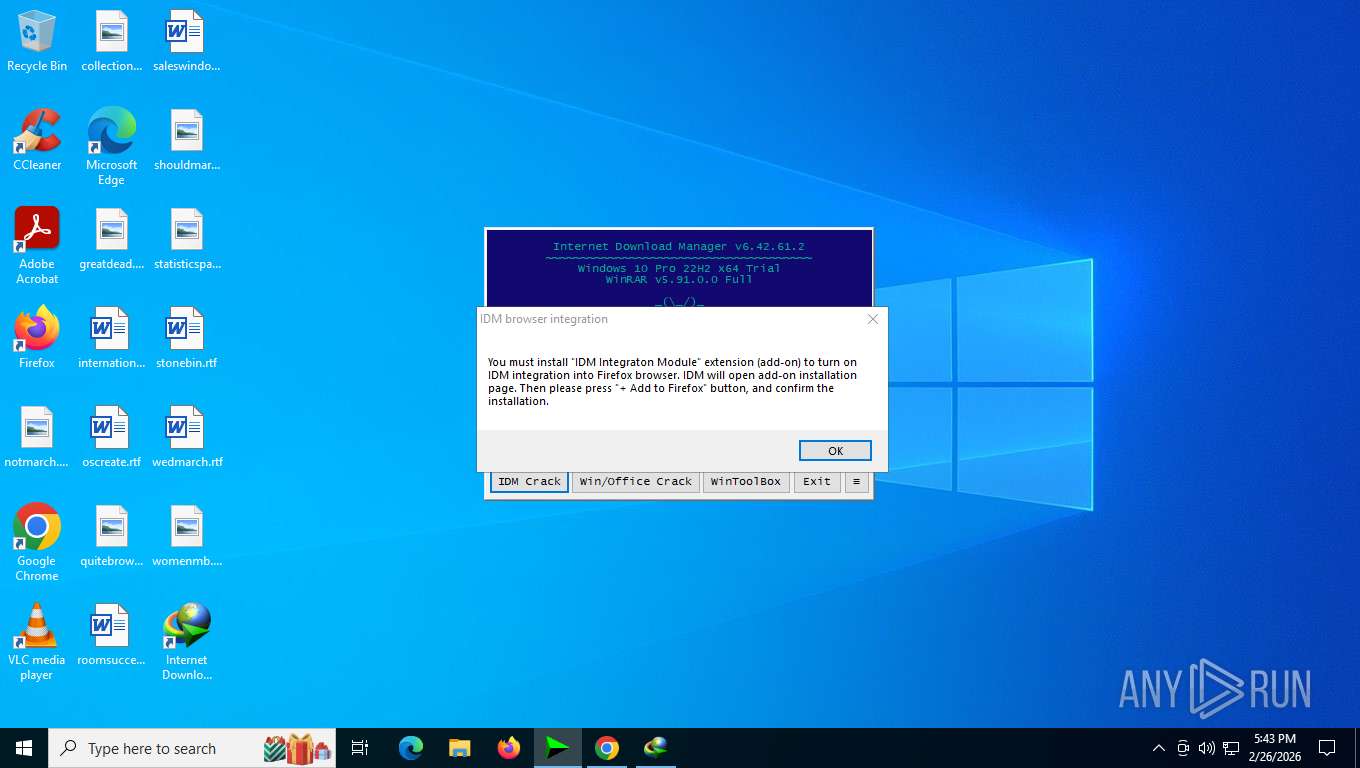
| Verdict: | Malicious activity |
| Analysis date: | February 26, 2026, 22:42:43 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 3 sections |
| MD5: | 99E93F400964B6C8BAB5A18E0E216500 |
| SHA1: | 2CFA756887BA67240C73791782386BD389A83454 |
| SHA256: | BCB21F1B4B14892370D2E935BCDB20FEAE7FF36D8D7EAB8BF24A72EF43B01F89 |
| SSDEEP: | 1536:P2mUIXFZXu1fXibzkqzEjHpOfNlGAwnmxiEvIsYwAF:P2aPXu1fczfz8HpGMA6mcVVwAF |
MALICIOUS
Creates internet connection object (SCRIPT)
- wscript.exe (PID: 9176)
Opens an HTTP connection (SCRIPT)
- wscript.exe (PID: 9176)
Reads the value of a key from the registry (SCRIPT)
- cscript.exe (PID: 6056)
- cscript.exe (PID: 5356)
- cscript.exe (PID: 8920)
- cscript.exe (PID: 4924)
- cscript.exe (PID: 848)
- cscript.exe (PID: 6108)
- cscript.exe (PID: 6084)
- cscript.exe (PID: 9068)
- cscript.exe (PID: 6000)
- cscript.exe (PID: 3120)
- cscript.exe (PID: 6696)
- cscript.exe (PID: 5592)
Sends HTTP request (SCRIPT)
- wscript.exe (PID: 9176)
Deletes a file (SCRIPT)
- wscript.exe (PID: 9176)
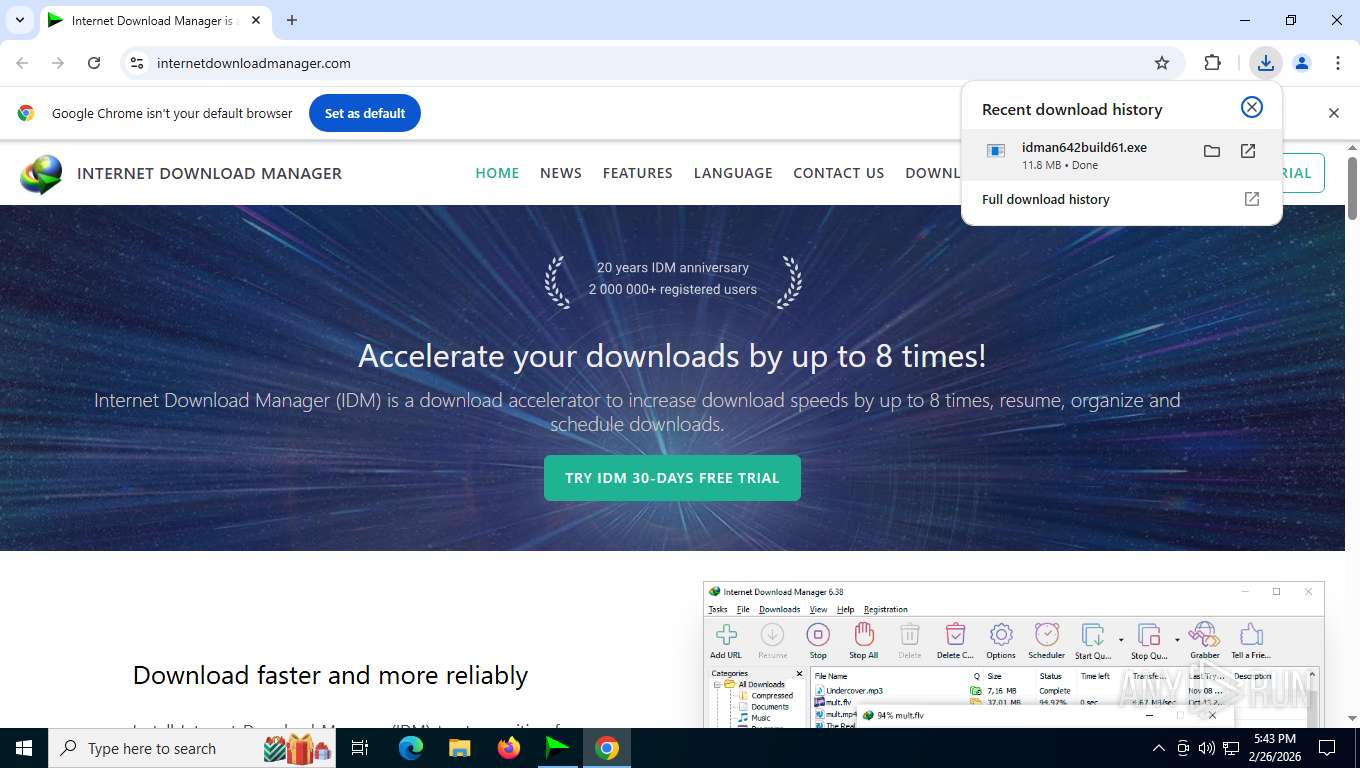
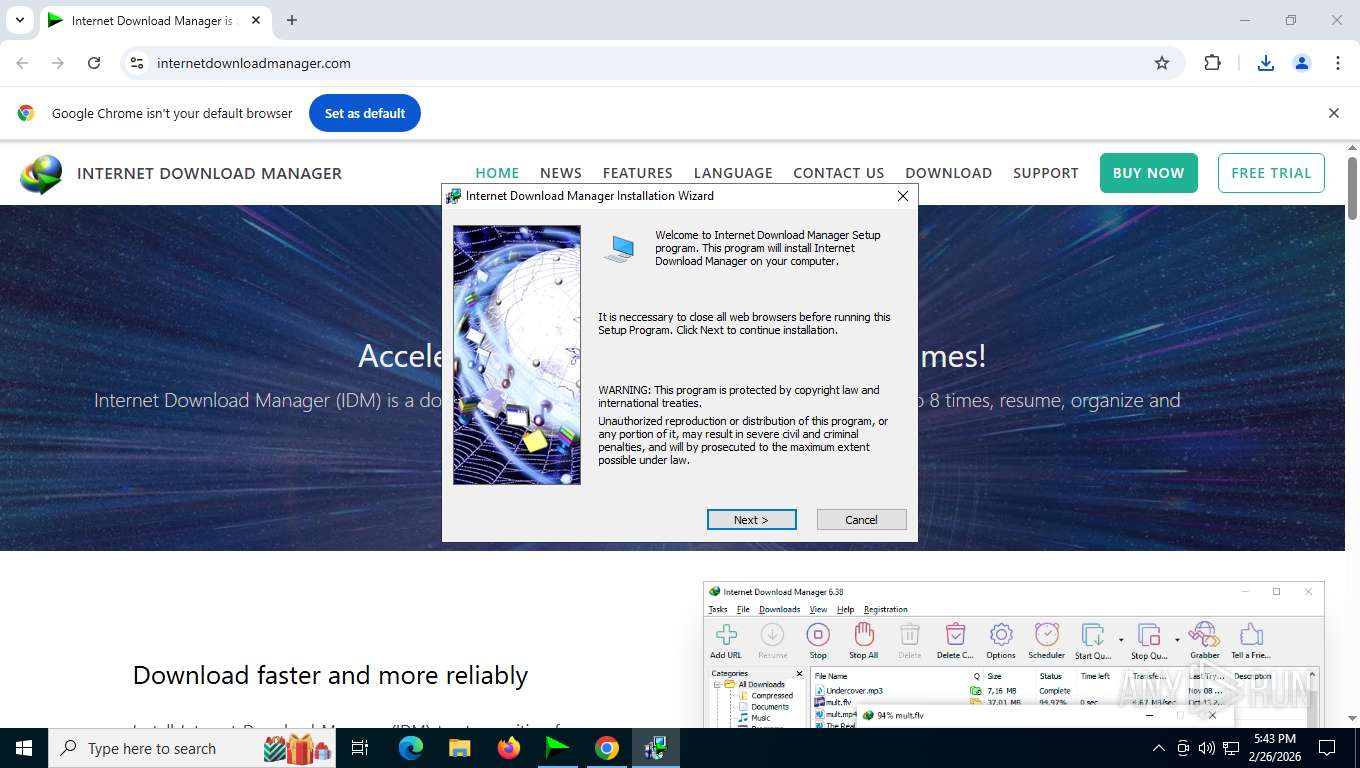
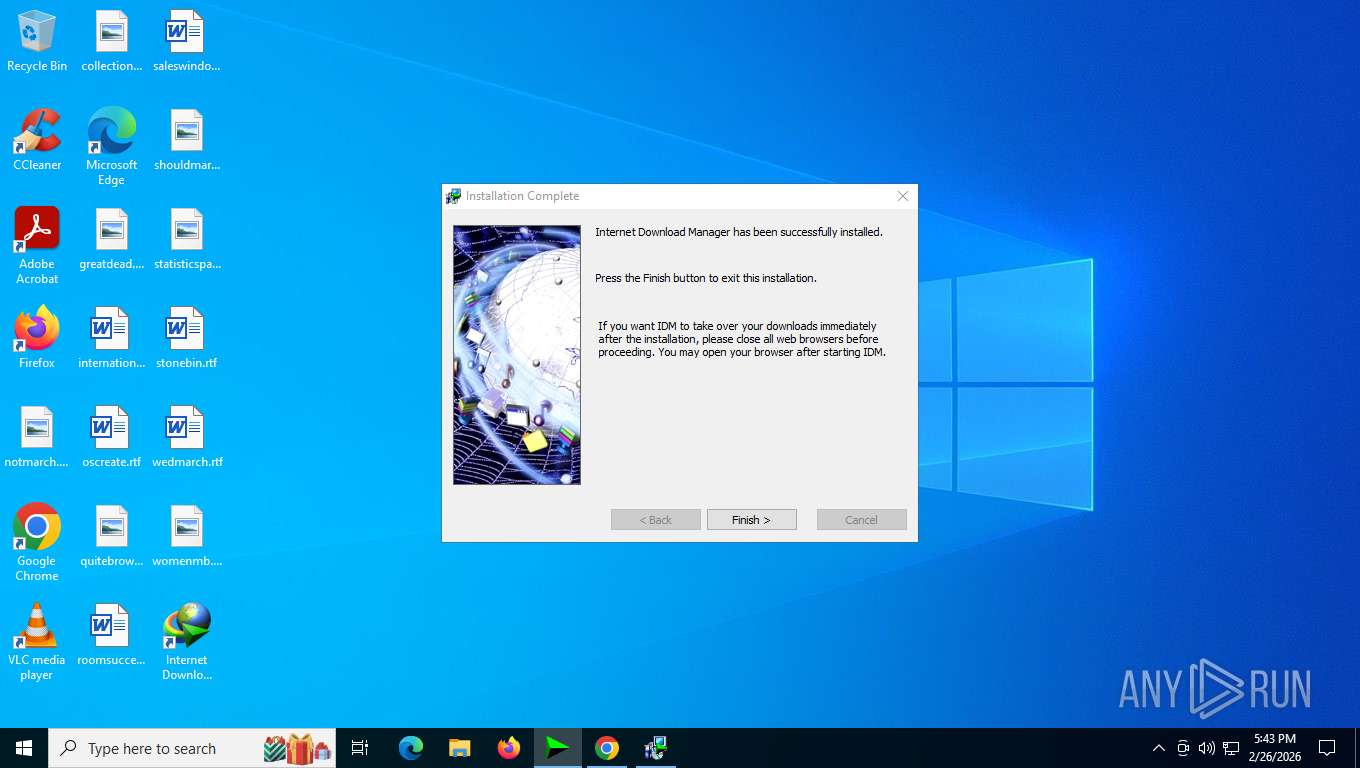
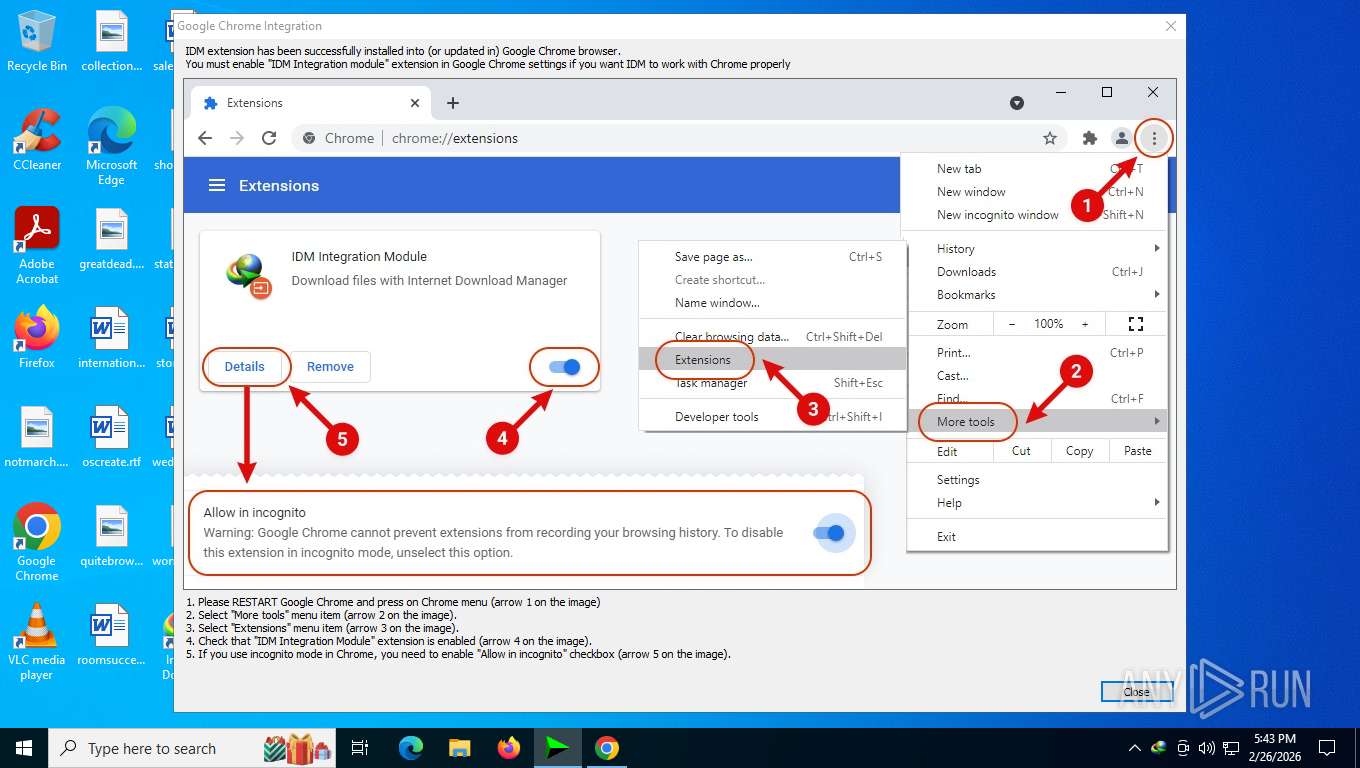
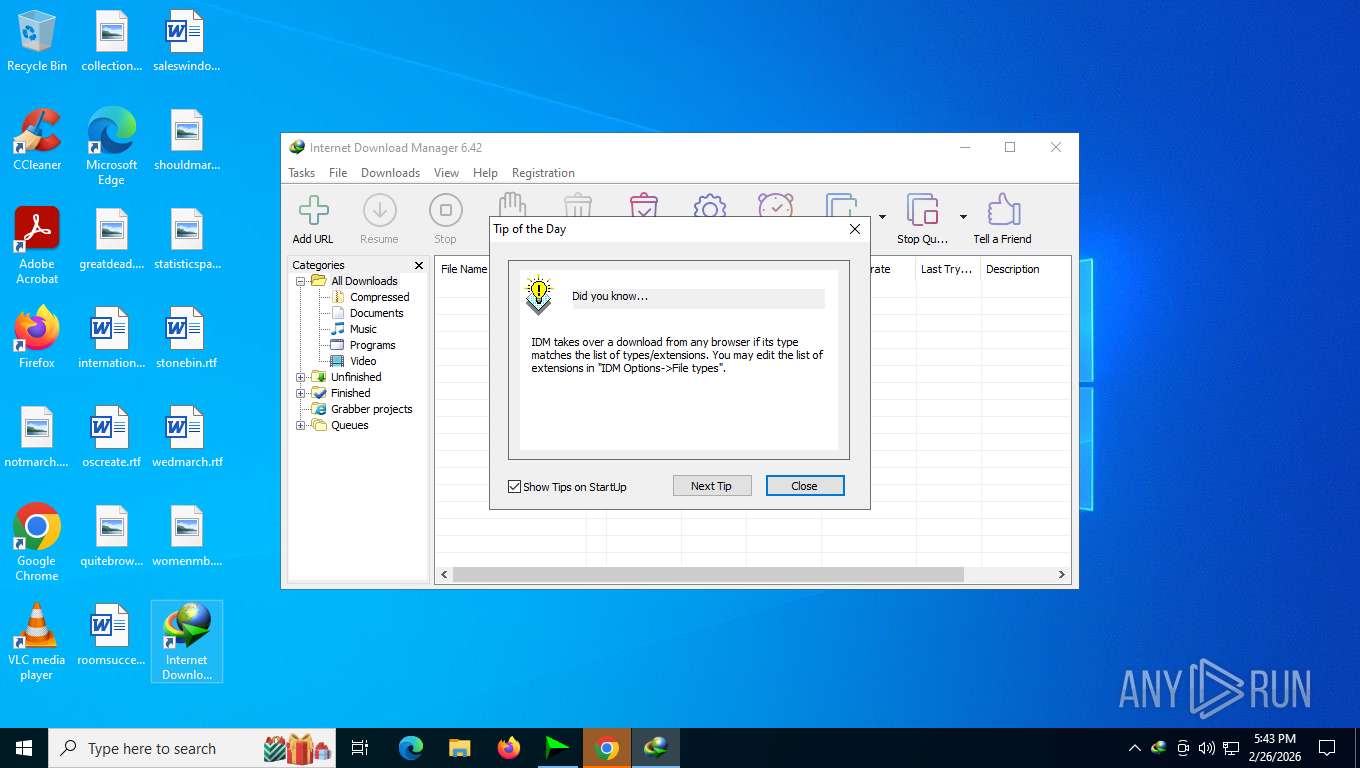
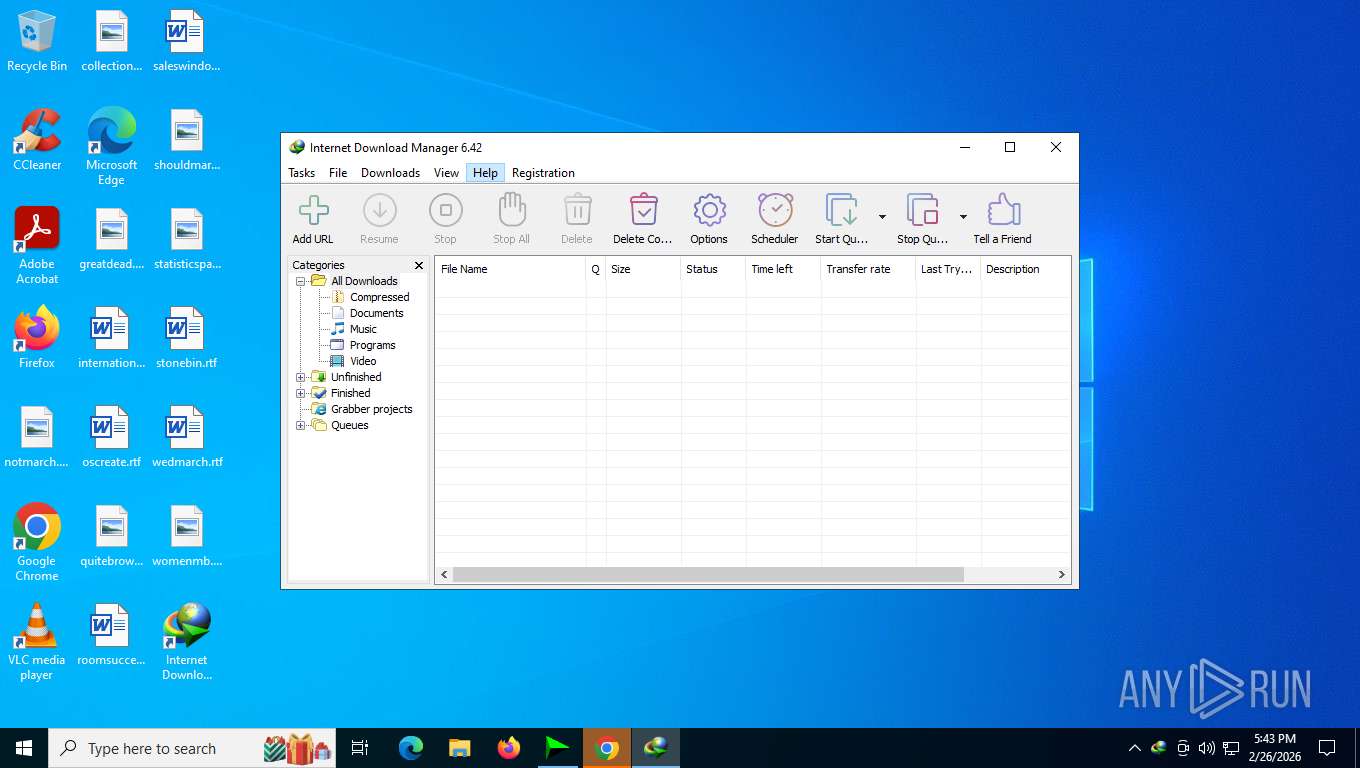
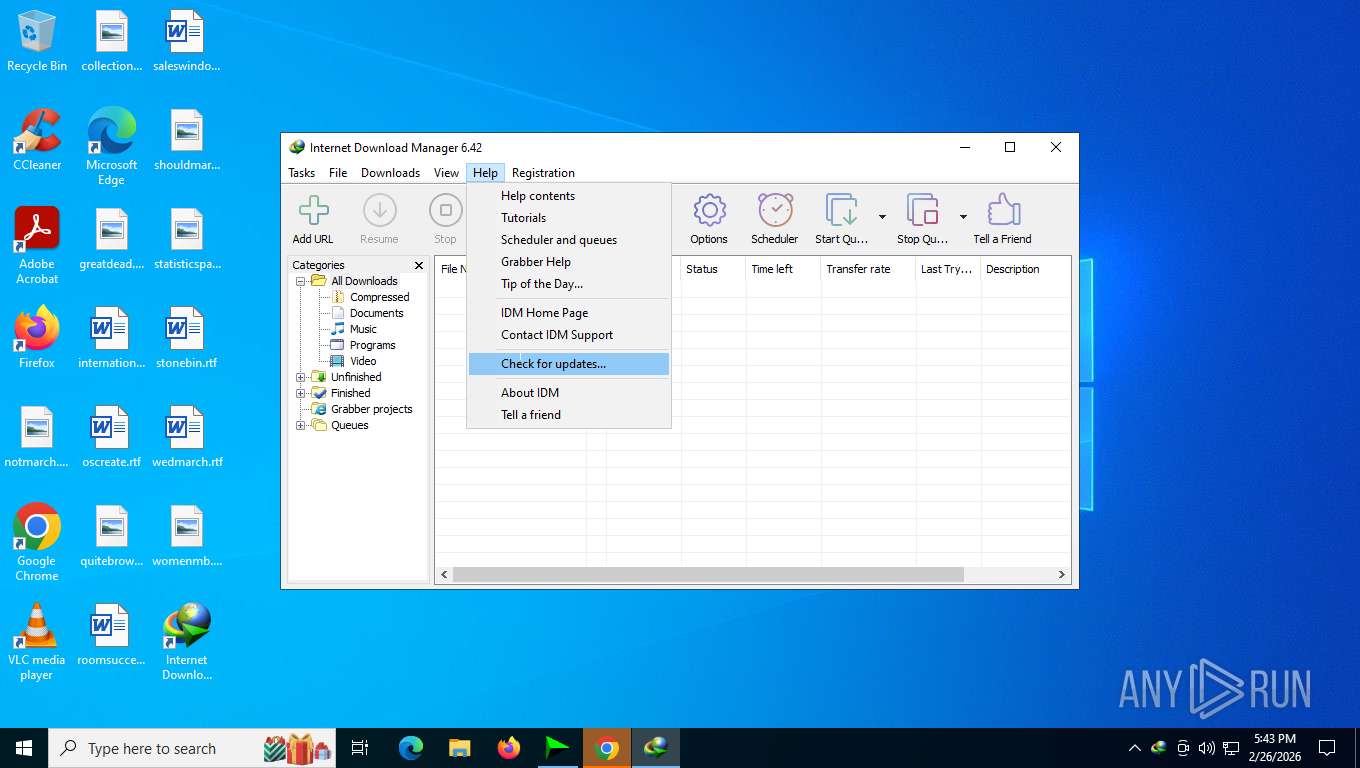
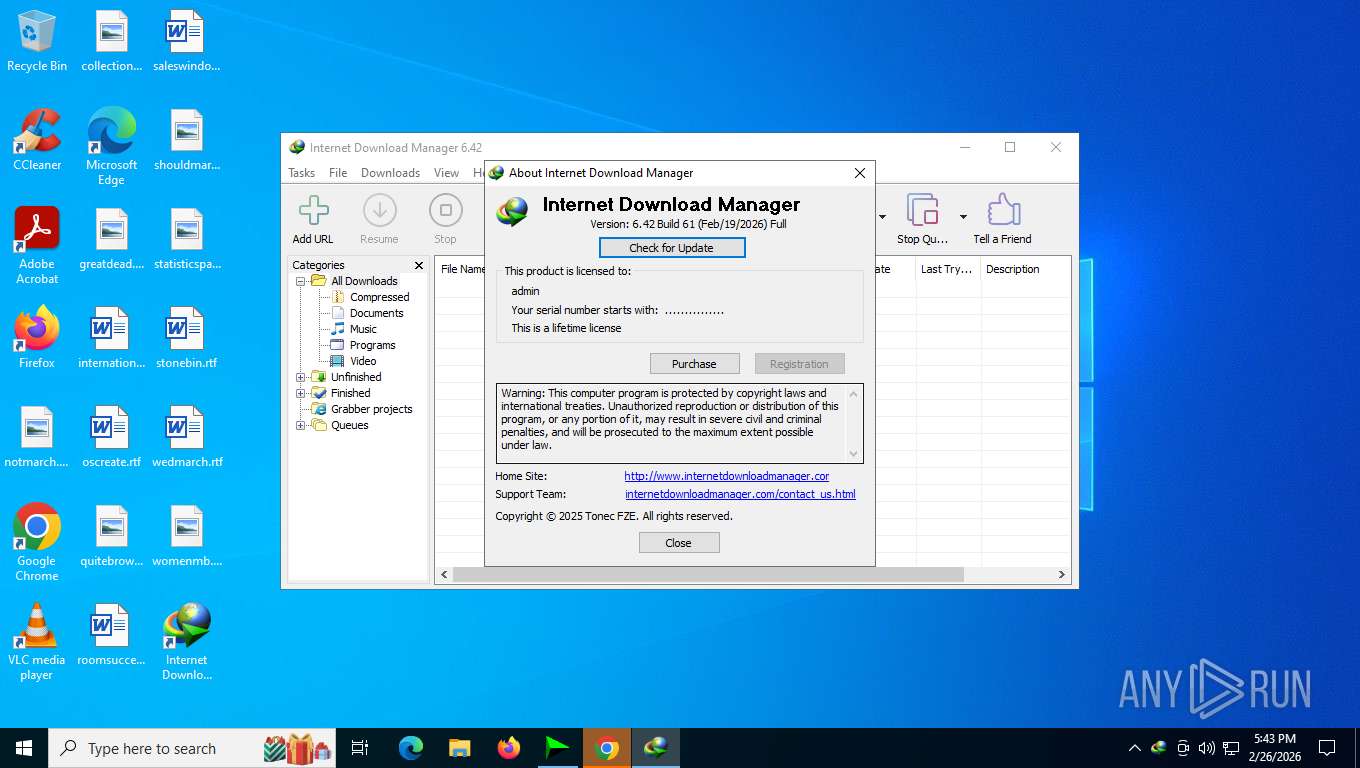
IDM has been detected
- chrome.exe (PID: 7464)
- idman642build61.exe (PID: 4584)
- IDM1.tmp (PID: 2548)
- IDMan.exe (PID: 2460)
Registers / Runs the DLL via REGSVR32.EXE
- IDM1.tmp (PID: 2548)
- IDMan.exe (PID: 2460)
- Uninstall.exe (PID: 2976)
- IDMan.exe (PID: 7396)
GENERIC has been found (auto)
- rundll32.exe (PID: 6568)
- drvinst.exe (PID: 6232)
Changes the autorun value in the registry
- rundll32.exe (PID: 6568)
- IDMan.exe (PID: 2460)
Starts NET.EXE for service management
- Uninstall.exe (PID: 2976)
- net.exe (PID: 6896)
SUSPICIOUS
The process executes VB scripts
- wscript.exe (PID: 9176)
- cscript.exe (PID: 6056)
- cscript.exe (PID: 5356)
- cscript.exe (PID: 8920)
- cscript.exe (PID: 4924)
- cscript.exe (PID: 848)
- cscript.exe (PID: 6108)
- cscript.exe (PID: 6084)
- cscript.exe (PID: 9068)
- cscript.exe (PID: 6000)
- cscript.exe (PID: 3120)
- cscript.exe (PID: 6696)
- cscript.exe (PID: 5592)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 9176)
Gets full path of the running script (SCRIPT)
- wscript.exe (PID: 9176)
Uses WMI to retrieve WMI-managed resources (SCRIPT)
- cscript.exe (PID: 6056)
- cscript.exe (PID: 8920)
- cscript.exe (PID: 5356)
- cscript.exe (PID: 4924)
- cscript.exe (PID: 848)
- cscript.exe (PID: 6108)
- cscript.exe (PID: 6084)
- cscript.exe (PID: 9068)
- cscript.exe (PID: 6000)
- cscript.exe (PID: 3120)
- cscript.exe (PID: 6696)
- cscript.exe (PID: 5592)
Adds, changes, or deletes HTTP request header (SCRIPT)
- wscript.exe (PID: 9176)
Enumerates operating system information (Win32_OperatingSystem) (SCRIPT)
- cscript.exe (PID: 6056)
- cscript.exe (PID: 8920)
- cscript.exe (PID: 5356)
- cscript.exe (PID: 4924)
- cscript.exe (PID: 848)
- cscript.exe (PID: 6108)
- cscript.exe (PID: 6084)
- cscript.exe (PID: 9068)
- cscript.exe (PID: 6000)
- cscript.exe (PID: 3120)
- cscript.exe (PID: 6696)
- cscript.exe (PID: 5592)
Accesses WMI object caption (SCRIPT)
- cscript.exe (PID: 6056)
- cscript.exe (PID: 8920)
- cscript.exe (PID: 5356)
- cscript.exe (PID: 4924)
- cscript.exe (PID: 848)
- cscript.exe (PID: 6108)
- cscript.exe (PID: 6084)
- cscript.exe (PID: 9068)
- cscript.exe (PID: 6000)
- cscript.exe (PID: 3120)
- cscript.exe (PID: 6696)
- cscript.exe (PID: 5592)
Executes WMI query (SCRIPT)
- cscript.exe (PID: 6056)
- cscript.exe (PID: 5356)
- cscript.exe (PID: 4924)
- cscript.exe (PID: 8920)
- cscript.exe (PID: 848)
- cscript.exe (PID: 6108)
- cscript.exe (PID: 6084)
- cscript.exe (PID: 9068)
- cscript.exe (PID: 6000)
- cscript.exe (PID: 3120)
- cscript.exe (PID: 6696)
- cscript.exe (PID: 5592)
Accesses operating system name via WMI (SCRIPT)
- cscript.exe (PID: 6056)
- cscript.exe (PID: 8920)
- cscript.exe (PID: 5356)
- cscript.exe (PID: 4924)
- cscript.exe (PID: 848)
- cscript.exe (PID: 6108)
- cscript.exe (PID: 6084)
- cscript.exe (PID: 9068)
- cscript.exe (PID: 6000)
- cscript.exe (PID: 3120)
- cscript.exe (PID: 5592)
- cscript.exe (PID: 6696)
Sets XML DOM element text (SCRIPT)
- wscript.exe (PID: 9176)
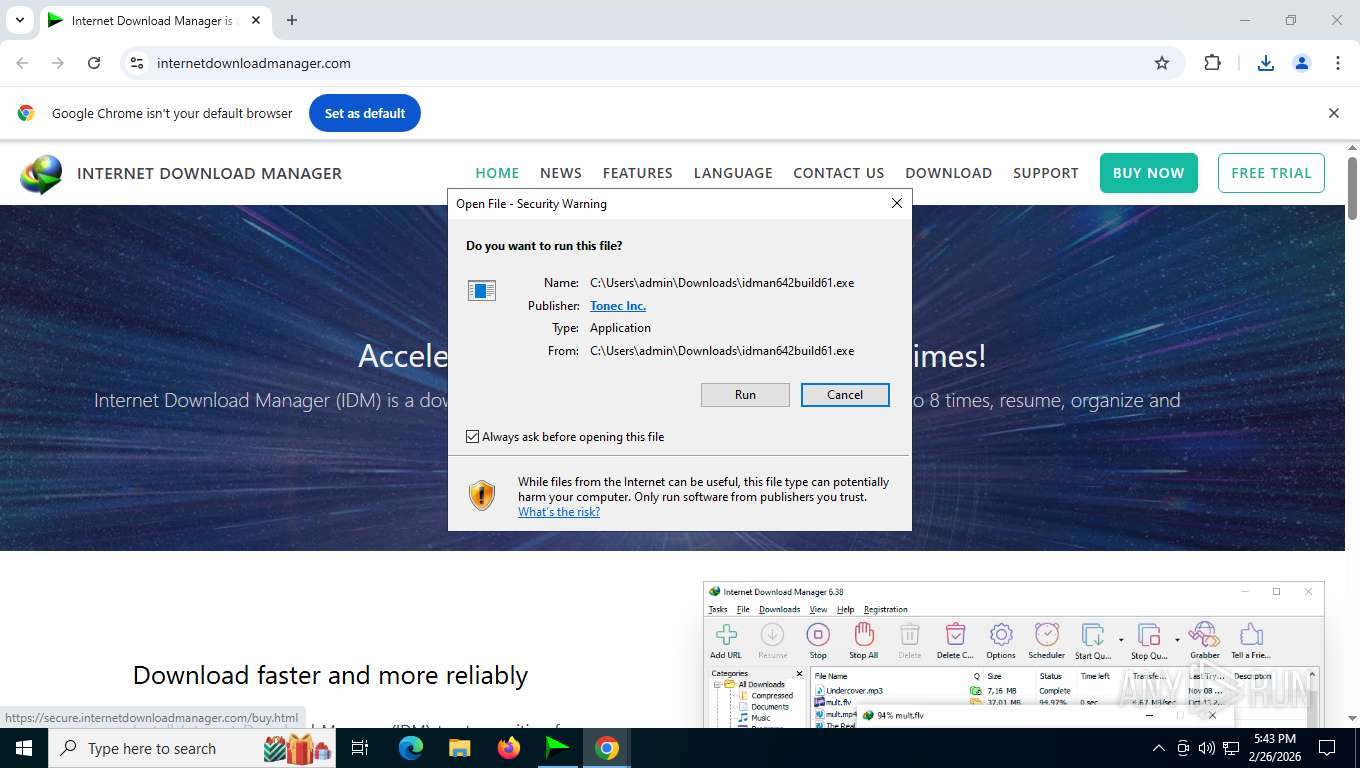
Starts application with an unusual extension
- idman642build61.exe (PID: 4584)
- cmd.exe (PID: 4728)
The process creates files with name similar to system file names
- IDM1.tmp (PID: 2548)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 6664)
- IDM1.tmp (PID: 2548)
- regsvr32.exe (PID: 2448)
- regsvr32.exe (PID: 8488)
- IDMan.exe (PID: 2460)
- regsvr32.exe (PID: 8716)
- regsvr32.exe (PID: 6820)
- regsvr32.exe (PID: 8324)
- regsvr32.exe (PID: 6596)
- regsvr32.exe (PID: 1848)
Executable content was dropped or overwritten
- IDMan.exe (PID: 2460)
- rundll32.exe (PID: 6568)
- IDM_6.4x_Crack_v20.6.exe (PID: 5764)
Drops a system driver (possible attempt to evade defenses)
- rundll32.exe (PID: 6568)
- drvinst.exe (PID: 6232)
Uses RUNDLL32.EXE to load library
- Uninstall.exe (PID: 2976)
Creates or modifies Windows services
- Uninstall.exe (PID: 2976)
Executing commands from a ".bat" file
- IDM_6.4x_Crack_v20.6.exe (PID: 5764)
- cmd.exe (PID: 4728)
Uses REG/REGEDIT.EXE to modify registry
- IDM_6.4x_Crack_v20.6.exe (PID: 5764)
- cmd.exe (PID: 4728)
- cmd.exe (PID: 8644)
Application launched itself
- cmd.exe (PID: 2148)
- cmd.exe (PID: 4728)
Starts CMD.EXE for commands execution
- IDM_6.4x_Crack_v20.6.exe (PID: 5764)
- cmd.exe (PID: 4728)
- cmd.exe (PID: 2148)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 4728)
- cmd.exe (PID: 4664)
- cmd.exe (PID: 7288)
Possibly malicious use of IEX has been detected
- powershell.exe (PID: 1432)
- powershell.exe (PID: 7120)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 4728)
Hides command output
- cmd.exe (PID: 4664)
- cmd.exe (PID: 8644)
INFO
Create files in a temporary directory
- IDM_6.4x_Crack_v20.6.exe (PID: 5764)
- idman642build61.exe (PID: 4584)
- IDM1.tmp (PID: 2548)
- IDMan.exe (PID: 2460)
- rundll32.exe (PID: 6568)
- IDMan.exe (PID: 7396)
- IDMan.exe (PID: 7100)
- reg.exe (PID: 6108)
Reads security settings of Internet Explorer
- cscript.exe (PID: 6056)
- IDM_6.4x_Crack_v20.6.exe (PID: 5764)
- cscript.exe (PID: 8920)
- cscript.exe (PID: 5356)
- cscript.exe (PID: 4924)
- cscript.exe (PID: 848)
- cscript.exe (PID: 6108)
- IDM1.tmp (PID: 2548)
- IDMan.exe (PID: 2460)
- Uninstall.exe (PID: 2976)
- runonce.exe (PID: 7896)
- cscript.exe (PID: 6084)
- IDMan.exe (PID: 7396)
- IDMan.exe (PID: 7100)
- cscript.exe (PID: 9068)
- IDMan.exe (PID: 7864)
- cscript.exe (PID: 6000)
- cscript.exe (PID: 3120)
- cscript.exe (PID: 6696)
- cscript.exe (PID: 5592)
Reads the computer name
- IDM_6.4x_Crack_v20.6.exe (PID: 5764)
- idman642build61.exe (PID: 4584)
- IDM1.tmp (PID: 2548)
- idmBroker.exe (PID: 5632)
- IDMan.exe (PID: 2460)
- Uninstall.exe (PID: 2976)
- drvinst.exe (PID: 6232)
- drvinst.exe (PID: 7916)
- IDMan.exe (PID: 7396)
- MediumILStart.exe (PID: 9048)
- IDMan.exe (PID: 7100)
- IDMIntegrator64.exe (PID: 5224)
- IDMan.exe (PID: 7864)
Checks supported languages
- IDM_6.4x_Crack_v20.6.exe (PID: 5764)
- idman642build61.exe (PID: 4584)
- IDM1.tmp (PID: 2548)
- idmBroker.exe (PID: 5632)
- IDMan.exe (PID: 2460)
- Uninstall.exe (PID: 2976)
- drvinst.exe (PID: 6232)
- drvinst.exe (PID: 7916)
- IDMan.exe (PID: 7396)
- MediumILStart.exe (PID: 9048)
- IDMan.exe (PID: 7100)
- IDMIntegrator64.exe (PID: 5224)
- IDMan.exe (PID: 7864)
- chcp.com (PID: 848)
Drops script file
- cscript.exe (PID: 6056)
- IDM_6.4x_Crack_v20.6.exe (PID: 5764)
- wscript.exe (PID: 9176)
- cscript.exe (PID: 5356)
- cscript.exe (PID: 8920)
- cscript.exe (PID: 4924)
- cscript.exe (PID: 848)
- cscript.exe (PID: 6108)
- IDMan.exe (PID: 2460)
- chrome.exe (PID: 2788)
- firefox.exe (PID: 8796)
- cscript.exe (PID: 6084)
- IDMan.exe (PID: 7396)
- cmd.exe (PID: 4728)
- IDMan.exe (PID: 7100)
- powershell.exe (PID: 1432)
- powershell.exe (PID: 8704)
- powershell.exe (PID: 9112)
- cscript.exe (PID: 9068)
- cscript.exe (PID: 6000)
- powershell.exe (PID: 7732)
- cscript.exe (PID: 3120)
- powershell.exe (PID: 7120)
- cscript.exe (PID: 6696)
- cscript.exe (PID: 5592)
Process checks computer location settings
- IDM_6.4x_Crack_v20.6.exe (PID: 5764)
- IDM1.tmp (PID: 2548)
- IDMan.exe (PID: 2460)
- Uninstall.exe (PID: 2976)
- IDMan.exe (PID: 7100)
Checks proxy server information
- wscript.exe (PID: 9176)
- IDMan.exe (PID: 2460)
- IDMan.exe (PID: 7396)
- IDMan.exe (PID: 7100)
Application launched itself
- chrome.exe (PID: 7464)
- firefox.exe (PID: 6000)
- firefox.exe (PID: 8796)
Executable content was dropped or overwritten
- chrome.exe (PID: 7464)
- chrome.exe (PID: 7764)
Creates files or folders in the user directory
- IDM_6.4x_Crack_v20.6.exe (PID: 5764)
- IDM1.tmp (PID: 2548)
- IDMan.exe (PID: 2460)
Launching a file from the Downloads directory
- chrome.exe (PID: 7464)
The sample compiled with english language support
- chrome.exe (PID: 7464)
- chrome.exe (PID: 7764)
- IDMan.exe (PID: 2460)
- rundll32.exe (PID: 6568)
- drvinst.exe (PID: 6232)
- IDM_6.4x_Crack_v20.6.exe (PID: 5764)
INTERNETDOWNLOADMANAGER mutex has been found
- idman642build61.exe (PID: 4584)
- IDM1.tmp (PID: 2548)
- IDMan.exe (PID: 2460)
- IDMan.exe (PID: 7396)
- IDMIntegrator64.exe (PID: 5224)
- IDMan.exe (PID: 7864)
- IDMan.exe (PID: 7100)
Creates files in the program directory
- IDM1.tmp (PID: 2548)
- IDMan.exe (PID: 2460)
- IDM_6.4x_Crack_v20.6.exe (PID: 5764)
Creates a software uninstall entry
- IDM1.tmp (PID: 2548)
Disables trace logs
- IDMan.exe (PID: 2460)
- IDMan.exe (PID: 7396)
- IDMan.exe (PID: 7100)
- IDMan.exe (PID: 7864)
Reads the machine GUID from the registry
- IDMan.exe (PID: 2460)
- drvinst.exe (PID: 6232)
- IDMan.exe (PID: 7396)
- IDMan.exe (PID: 7100)
- IDMan.exe (PID: 7864)
Manual execution by a user
- firefox.exe (PID: 6000)
- IDMan.exe (PID: 7864)
Launching a file from a Registry key
- rundll32.exe (PID: 6568)
- IDMan.exe (PID: 2460)
Reads the time zone
- runonce.exe (PID: 7896)
Checks operating system version
- cmd.exe (PID: 4728)
Search a value from a registry key
- reg.exe (PID: 4280)
- cmd.exe (PID: 2788)
- reg.exe (PID: 3152)
- cmd.exe (PID: 8644)
- reg.exe (PID: 1464)
- reg.exe (PID: 7212)
- reg.exe (PID: 8352)
- reg.exe (PID: 8780)
- reg.exe (PID: 3208)
- reg.exe (PID: 3552)
- reg.exe (PID: 6332)
- reg.exe (PID: 2236)
- reg.exe (PID: 2148)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 1432)
- powershell.exe (PID: 7120)
Changes the display of characters in the console
- cmd.exe (PID: 4728)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (38.3) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (26.2) |
| .exe | | | Win16/32 Executable Delphi generic (12) |
| .exe | | | Generic Win/DOS Executable (11.6) |
| .exe | | | DOS Executable Generic (11.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:19 22:22:17+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 65536 |
| InitializedDataSize: | 8192 |
| UninitializedDataSize: | 192512 |
| EntryPoint: | 0x3ee70 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
308
Monitored processes
158
Malicious processes
22
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 404 | regsvr32.exe /s "C:\Program Files (x86)\Internet Download Manager\downlWithIDM64.dll" | C:\Windows\SysWOW64\regsvr32.exe | — | IDMan.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 416 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=6716,i,5015171016495999687,10026510386099016217,262144 --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=6768 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: HIGH Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 684 | reg add HKCU\IAS_TEST | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 848 | cscript //nologo "C:\Users\admin\AppData\Local\Temp\\WININF.vbs" | C:\Windows\SysWOW64\cscript.exe | — | IDM_6.4x_Crack_v20.6.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 848 | chcp 65001 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1172 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --field-trial-handle=6248,i,5015171016495999687,10026510386099016217,262144 --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=6728 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1188 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --field-trial-handle=2348,i,5015171016495999687,10026510386099016217,262144 --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=2368 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1344 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --field-trial-handle=6812,i,5015171016495999687,10026510386099016217,262144 --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=6568 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1424 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1432 | powershell.exe "$f=[io.file]::ReadAllText('C:\Users\admin\AppData\Local\Temp\BATCLEN.bat') -split ':PowerShellTest:\s*';iex ($f[1])" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
54 837
Read events
54 128
Write events
537
Delete events
172
Modification events
| (PID) Process: | (5764) IDM_6.4x_Crack_v20.6.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\PowerShell\1\ShellIds\ScriptedDiagnostics |
| Operation: | write | Name: | ExecutionPolicy |
Value: Bypass | |||
| (PID) Process: | (9176) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (9176) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (9176) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (5764) IDM_6.4x_Crack_v20.6.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows Script Host\Settings |
| Operation: | write | Name: | Enabled |
Value: 1 | |||
| (PID) Process: | (5764) IDM_6.4x_Crack_v20.6.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Wow6432Node\Microsoft\Windows Script Host\Settings |
| Operation: | write | Name: | Enabled |
Value: 1 | |||
| (PID) Process: | (5764) IDM_6.4x_Crack_v20.6.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows Script Host\Settings |
| Operation: | write | Name: | Enabled |
Value: 1 | |||
| (PID) Process: | (5764) IDM_6.4x_Crack_v20.6.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | DisableRegistryTools |
Value: 0 | |||
| (PID) Process: | (5764) IDM_6.4x_Crack_v20.6.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | DisableCMD |
Value: 0 | |||
| (PID) Process: | (5764) IDM_6.4x_Crack_v20.6.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | DisableTaskMgr |
Value: 0 | |||
Executable files
21
Suspicious files
211
Text files
199
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7464 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old~RF1e6b4a.TMP | — | |
MD5:— | SHA256:— | |||
| 7464 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7464 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF1e6b4a.TMP | — | |
MD5:— | SHA256:— | |||
| 7464 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7464 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF1e6b5a.TMP | — | |
MD5:— | SHA256:— | |||
| 7464 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old~RF1e6b5a.TMP | — | |
MD5:— | SHA256:— | |||
| 7464 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF1e6b6a.TMP | — | |
MD5:— | SHA256:— | |||
| 7464 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7464 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7464 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
81
TCP/UDP connections
68
DNS requests
79
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5568 | SearchApp.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAjTxtAB8my1oj8MfWpz%2F7Y%3D | unknown | — | — | whitelisted |
5568 | SearchApp.exe | GET | 200 | 204.79.197.203:80 | http://oneocsp.microsoft.com/ocsp/MFQwUjBQME4wTDAJBgUrDgMCGgUABBQ3L3%2F%2Fa6ADK8NraY2GXzVaYrHG4AQUb6t%2B2v%2BXQ3LsO2d33oJhNYhHQoUCEzMAAAAGb6JMMcOVb6sAAAAAAAY%3D | unknown | — | — | whitelisted |
9176 | wscript.exe | GET | 200 | 142.250.186.67:80 | http://c.pki.goog/r/gsr1.crl | unknown | — | — | whitelisted |
9176 | wscript.exe | GET | 200 | 142.250.186.67:80 | http://c.pki.goog/r/r4.crl | unknown | — | — | whitelisted |
9176 | wscript.exe | GET | 200 | 188.114.97.3:443 | https://idm.0dy.ir/?_nc=63769.51 | unknown | xml | 150 b | malicious |
356 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7764 | chrome.exe | GET | 200 | 142.250.186.78:80 | http://clients2.google.com/time/1/current?cup2key=8:BZddYpls4jUtAYus2XvJuY-CiU_J8ixQ44pefkLpkRA&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
7764 | chrome.exe | POST | 200 | 142.251.127.84:443 | https://accounts.google.com/ListAccounts?gpsia=1&source=ChromiumBrowser&json=standard | unknown | — | 17 b | whitelisted |
7764 | chrome.exe | GET | 200 | 142.251.127.95:443 | https://safebrowsingohttpgateway.googleapis.com/v1/ohttp/hpkekeyconfig?key=AIzaSyA2KlwBX3mkFo30om9LUFYQhpqLoa_BNhE | unknown | — | 41 b | whitelisted |
7764 | chrome.exe | GET | 200 | 67.18.60.145:443 | https://internetdownloadmanager.com/main.css | unknown | — | 66.0 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
7240 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7212 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5568 | SearchApp.exe | 23.11.206.98:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
5568 | SearchApp.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
5568 | SearchApp.exe | 204.79.197.203:80 | oneocsp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
9176 | wscript.exe | 188.114.97.3:443 | idm.0dy.ir | CLOUDFLARENET | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
oneocsp.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
idm.0dy.ir |
| malicious |
c.pki.goog |
| whitelisted |
clients2.google.com |
| whitelisted |
internetdownloadmanager.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7240 | svchost.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
7764 | chrome.exe | Potentially Bad Traffic | ET INFO PE EXE or DLL Windows file download HTTP |
7764 | chrome.exe | Misc activity | ET INFO EXE IsDebuggerPresent (Used in Malware Anti-Debugging) |
7764 | chrome.exe | Misc activity | ET INFO Packed Executable Download |