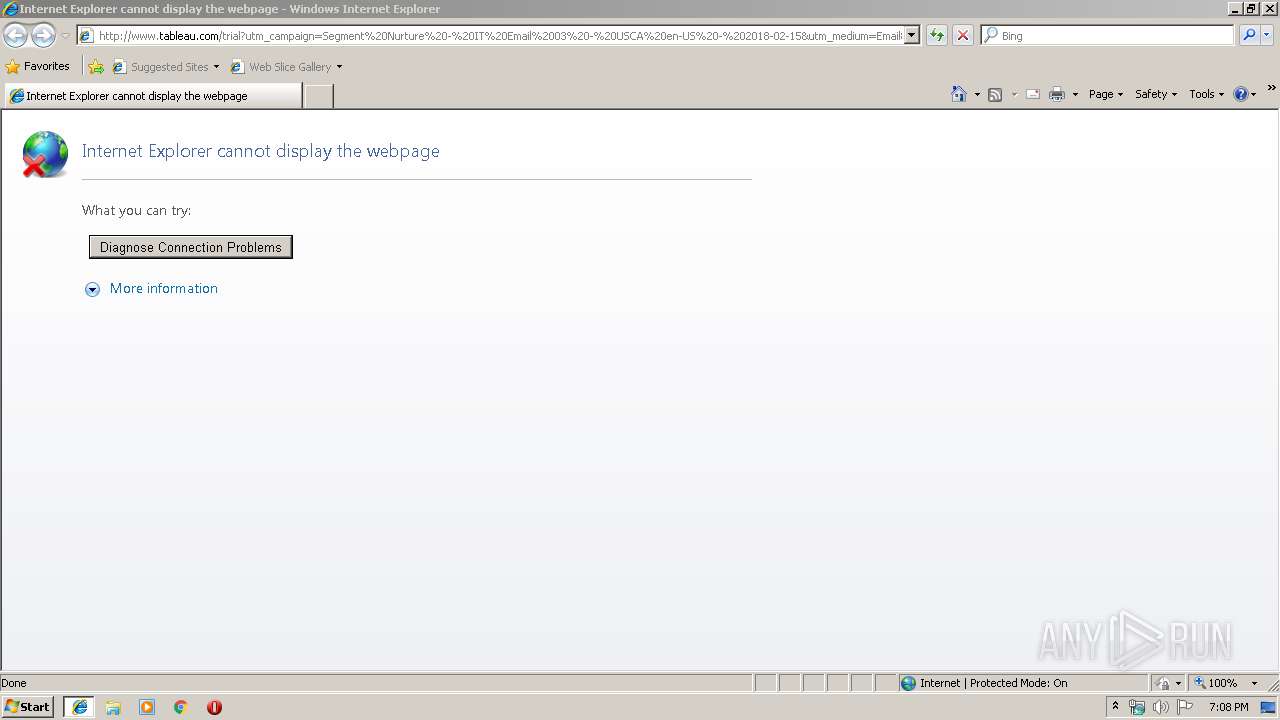
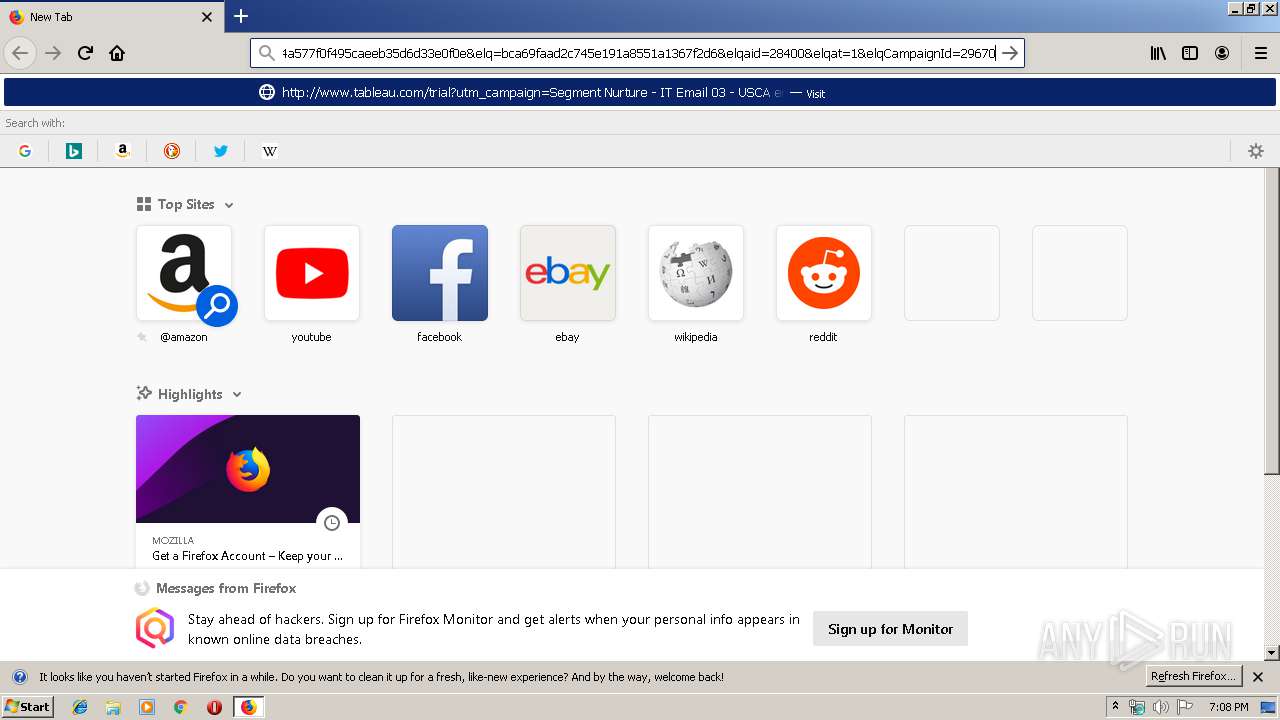
| URL: | http://www.tableau.com/trial?utm_campaign=Segment%20Nurture%20-%20IT%20Email%2003%20-%20USCA%20en-US%20-%202018-02-15&utm_medium=Email&utm_source=Eloqua&domain=cityofrochester.gov&eid=CTBLS000022677336&elqTrackId=e80a4a577f0f495caeeb35d6d33e0f0e&elq=bca69faad2c745e191a8551a1367f2d6&elqaid=28400&elqat=1&elqCampaignId=29670 |
| Full analysis: | https://app.any.run/tasks/2083f804-aab7-4e33-8f94-e977142087f3 |
| Verdict: | Malicious activity |
| Analysis date: | October 09, 2019, 18:07:48 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 954DF0E7E10785A803BAF572EF3C8173 |
| SHA1: | 4FB61943B8EAC6F404F7E0B51D47187929391676 |
| SHA256: | BCA5A0FA68897CE45333FE8805734159F96E9FF6542F54F45612BE68D63A0798 |
| SSDEEP: | 6:Cc4wE/8mkyQrBYMYxRReNwfWRJhREC+DIv4VS/8rg9O1dPVLWDLgan:9mk9vemNwmJpvgS/8sOtLWXB |
MALICIOUS
No malicious indicators.SUSPICIOUS
Creates files in the program directory
- firefox.exe (PID: 1228)
INFO
Reads internet explorer settings
- iexplore.exe (PID: 3408)
Manual execution by user
- chrome.exe (PID: 3788)
- firefox.exe (PID: 3784)
Reads the hosts file
- chrome.exe (PID: 3296)
- chrome.exe (PID: 3788)
Application launched itself
- chrome.exe (PID: 3788)
- iexplore.exe (PID: 2700)
- firefox.exe (PID: 1228)
Reads CPU info
- firefox.exe (PID: 1228)
Reads Internet Cache Settings
- iexplore.exe (PID: 3408)
Creates files in the user directory
- firefox.exe (PID: 1228)
Changes internet zones settings
- iexplore.exe (PID: 2700)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
52
Monitored processes
18
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 324 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,6818291249290363953,4226138245266337544,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14812201224869290781 --mojo-platform-channel-handle=3052 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1228 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 1364 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,6818291249290363953,4226138245266337544,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16815194365956435015 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2444 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1652 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="1228.13.720703849\1184790616" -childID 2 -isForBrowser -prefsHandle 2760 -prefMapHandle 2772 -prefsLen 5996 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 1228 "\\.\pipe\gecko-crash-server-pipe.1228" 2784 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 1684 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="1228.0.1913262041\1022247358" -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 1228 "\\.\pipe\gecko-crash-server-pipe.1228" 1140 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 1852 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6d8da9d0,0x6d8da9e0,0x6d8da9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2180 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1004,6818291249290363953,4226138245266337544,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=10588225255261726221 --mojo-platform-channel-handle=904 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,6818291249290363953,4226138245266337544,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11591076264979113338 --mojo-platform-channel-handle=3348 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2632 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="1228.20.776995367\1984500042" -childID 3 -isForBrowser -prefsHandle 3748 -prefMapHandle 3752 -prefsLen 7129 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 1228 "\\.\pipe\gecko-crash-server-pipe.1228" 3764 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 2700 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
793
Read events
696
Write events
93
Delete events
4
Modification events
| (PID) Process: | (2700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000093000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {BBE50A99-EABF-11E9-AB4C-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 2 | |||
| (PID) Process: | (2700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E3070A00030009001200080003008203 | |||
Executable files
0
Suspicious files
129
Text files
101
Unknown types
81
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2700 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2700 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3408 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 3408 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\MSIMGSIZ.DAT | smt | |
MD5:— | SHA256:— | |||
| 3788 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3408 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\B5AVM6AV\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
| 3408 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\QHOT701A\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
| 3408 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\IKLLQX71\noConnect[1] | image | |
MD5:3CB8FACCD5DE434D415AB75C17E8FD86 | SHA256:6976C426E3AC66D66303C114B22B2B41109A7DE648BA55FFC3E5A53BD0DB09E7 | |||
| 3788 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3408 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\QHOT701A\errorPageStrings[1] | text | |
MD5:1A0563F7FB85A678771450B131ED66FD | SHA256:EB5678DE9D8F29CA6893D4E6CA79BD5AB4F312813820FE4997B009A2B1A1654C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
34
TCP/UDP connections
102
DNS requests
196
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1228 | firefox.exe | GET | 301 | 104.109.76.169:80 | http://www.tableau.com/trial?utm_campaign=Segment%20Nurture%20-%20IT%20Email%2003%20-%20USCA%20en-US%20-%202018-02-15&utm_medium=Email&utm_source=Eloqua&domain=cityofrochester.gov&eid=CTBLS000022677336&elqTrackId=e80a4a577f0f495caeeb35d6d33e0f0e&elq=bca69faad2c745e191a8551a1367f2d6&elqaid=28400&elqat=1&elqCampaignId=29670 | NL | — | — | suspicious |
1228 | firefox.exe | POST | 200 | 151.139.128.14:80 | http://ocsp.sectigo.com/ | US | der | 471 b | whitelisted |
1228 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://status.rapidssl.com/ | US | der | 471 b | shared |
1228 | firefox.exe | POST | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/ | US | der | 472 b | whitelisted |
1228 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
1228 | firefox.exe | POST | 200 | 52.222.149.110:80 | http://ocsp.sca1b.amazontrust.com/ | US | der | 471 b | whitelisted |
1228 | firefox.exe | POST | 200 | 2.21.242.245:80 | http://ocsp.int-x3.letsencrypt.org/ | NL | der | 527 b | whitelisted |
1228 | firefox.exe | POST | 200 | 172.217.22.67:80 | http://ocsp.pki.goog/gts1o1 | US | der | 471 b | whitelisted |
1228 | firefox.exe | POST | 200 | 172.217.22.67:80 | http://ocsp.pki.goog/gts1o1 | US | der | 472 b | whitelisted |
1228 | firefox.exe | POST | 200 | 172.217.22.67:80 | http://ocsp.pki.goog/gts1o1 | US | der | 472 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3296 | chrome.exe | 172.217.23.163:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2700 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3408 | iexplore.exe | 104.109.76.169:80 | www.tableau.com | Akamai International B.V. | NL | whitelisted |
3296 | chrome.exe | 172.217.21.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1228 | firefox.exe | 2.16.186.112:80 | detectportal.firefox.com | Akamai International B.V. | — | whitelisted |
1228 | firefox.exe | 35.160.40.106:443 | push.services.mozilla.com | Amazon.com, Inc. | US | malicious |
1228 | firefox.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1228 | firefox.exe | 172.217.22.67:80 | www.gstatic.com | Google Inc. | US | whitelisted |
1228 | firefox.exe | 54.69.207.70:443 | tiles.services.mozilla.com | Amazon.com, Inc. | US | unknown |
3296 | chrome.exe | 172.217.16.142:443 | clients2.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
www.tableau.com |
| suspicious |
dns.msftncsi.com |
| shared |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1044 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1044 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |