| File name: | Roblox.exe |
| Full analysis: | https://app.any.run/tasks/dd2d9269-58d6-427c-9897-19c69d8d9b90 |
| Verdict: | Malicious activity |
| Analysis date: | April 12, 2025, 13:20:48 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 6 sections |
| MD5: | 772DD5C983D078B226E378CAA673B656 |
| SHA1: | C22A73188909CD09DD4B0ABD02F55259EDAF76BC |
| SHA256: | BC8F4EA8F5FF857B15799F5147F640E594D8711884B9C6A61FAE689D7F74FFC8 |
| SSDEEP: | 24576:TgAHvqz/pY+lfo+Ro1SaXgZgqagqCeQWxH9XZeYKDh6ri8id31PovTsvjaYk5ewK:NQBhohwZgqWQ+9XZKDh6ri8id31AvTOh |
MALICIOUS
Executing a file with an untrusted certificate
- Roblox.exe (PID: 7188)
- Roblox.exe (PID: 1452)
- Roblox.exe (PID: 2284)
- Roblox.exe (PID: 7084)
- Roblox.exe (PID: 7496)
- Roblox.exe (PID: 7756)
SUSPICIOUS
Application launched itself
- Roblox.exe (PID: 2284)
- Roblox.exe (PID: 7496)
- Roblox.exe (PID: 1452)
Reads security settings of Internet Explorer
- Roblox.exe (PID: 7188)
- Roblox.exe (PID: 1452)
- Roblox.exe (PID: 2284)
- Roblox.exe (PID: 7496)
- Roblox.exe (PID: 7756)
- Roblox.exe (PID: 7084)
- ShellExperienceHost.exe (PID: 4172)
The process drops C-runtime libraries
- Roblox.exe (PID: 7496)
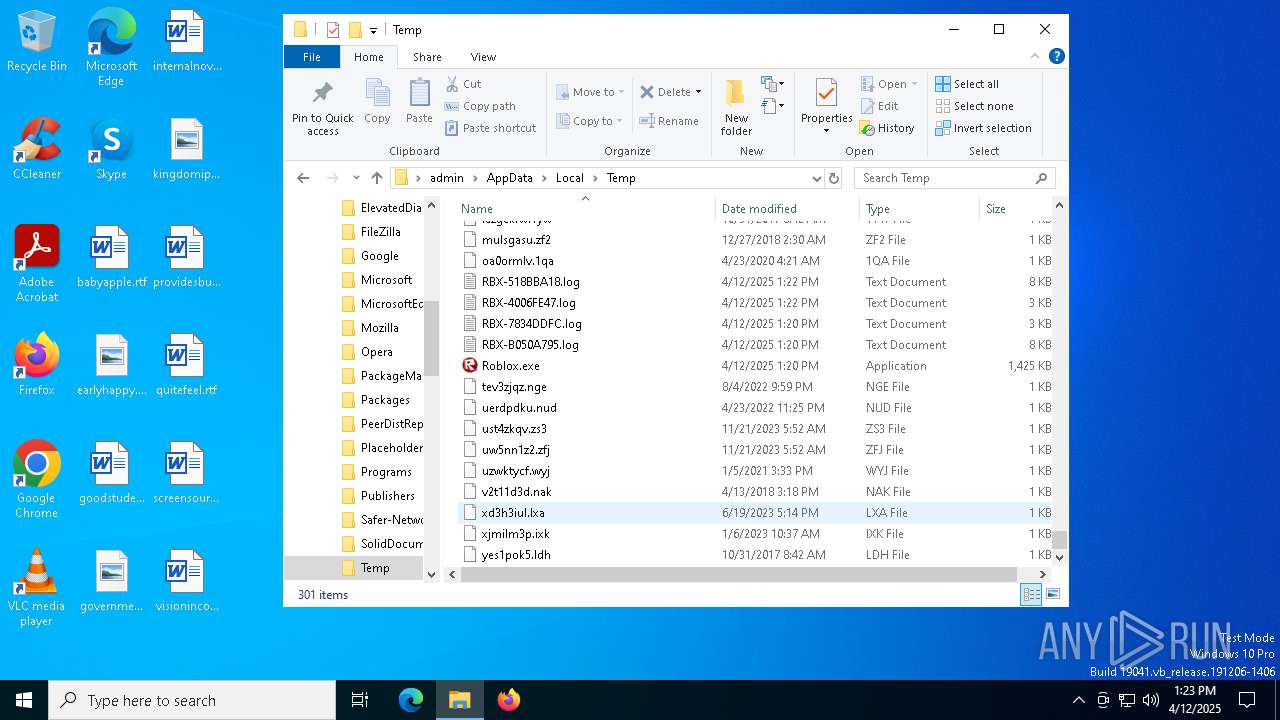
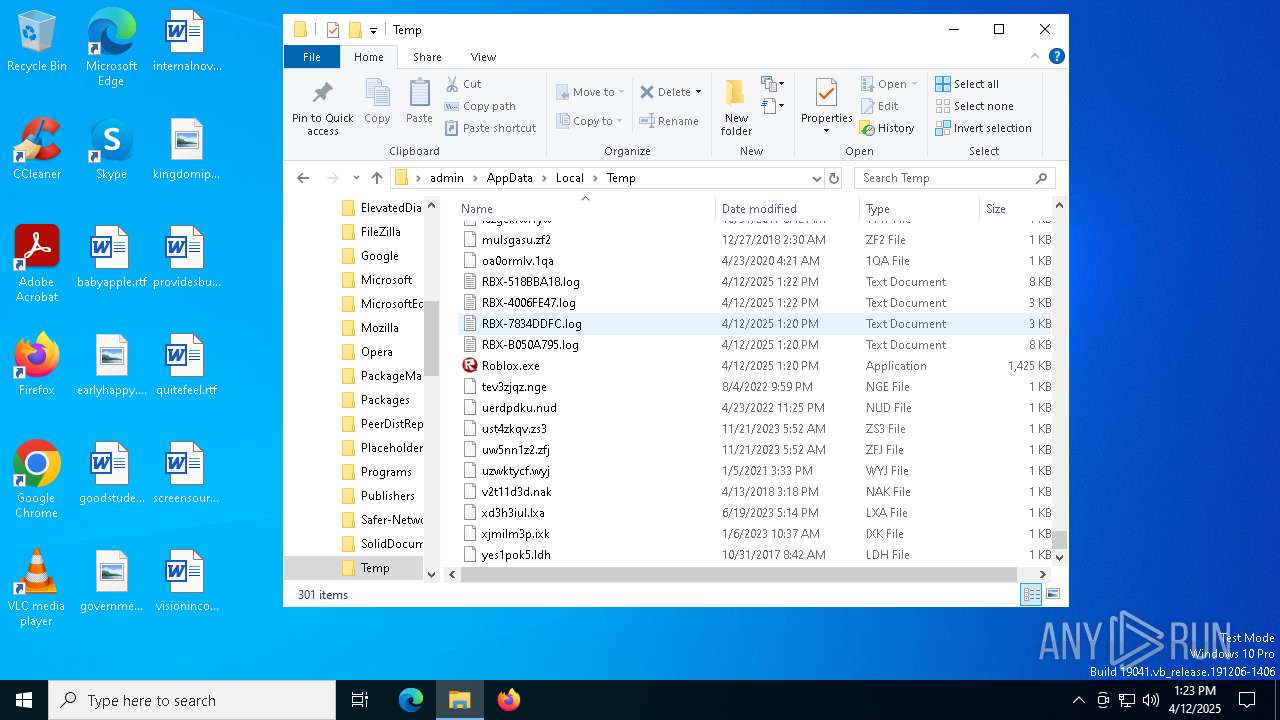
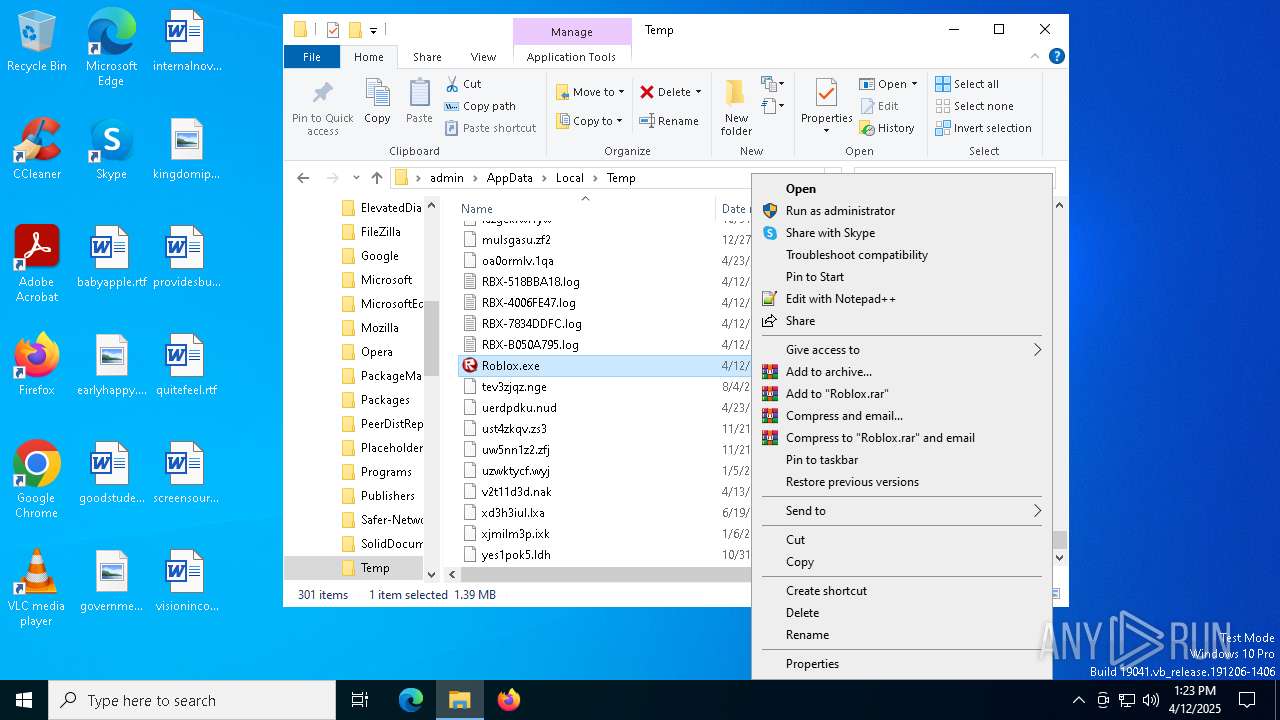
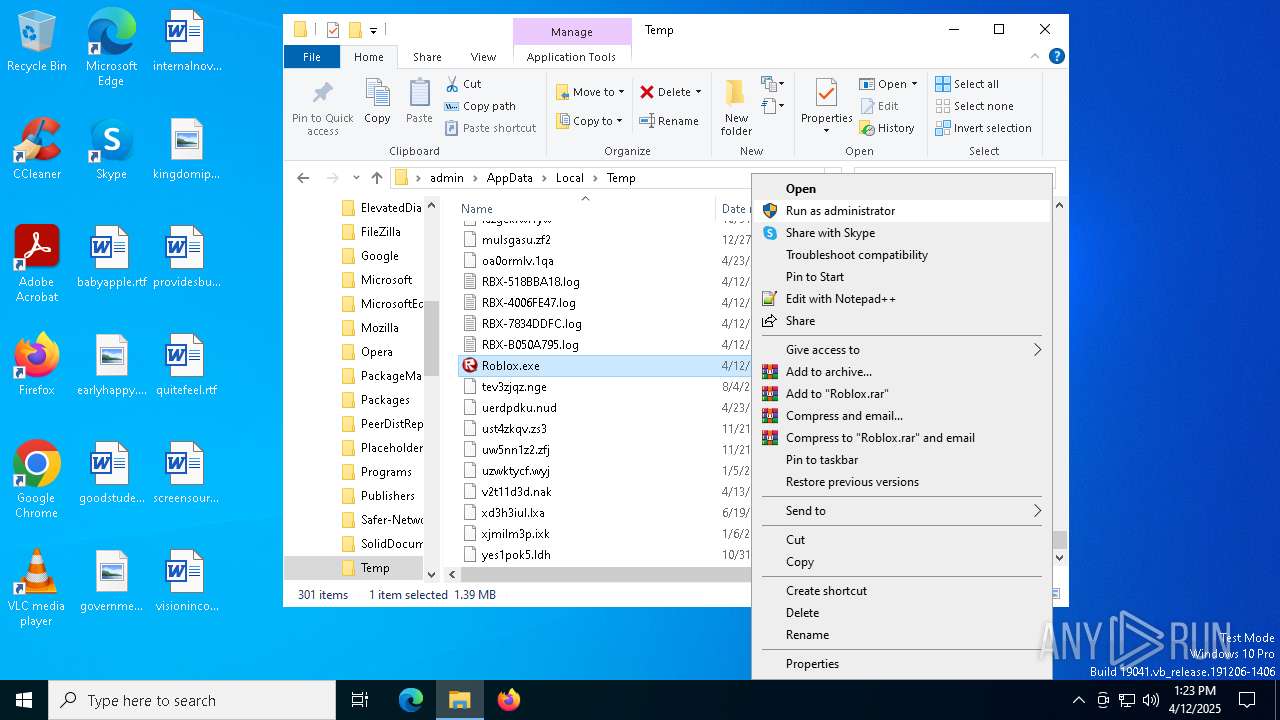
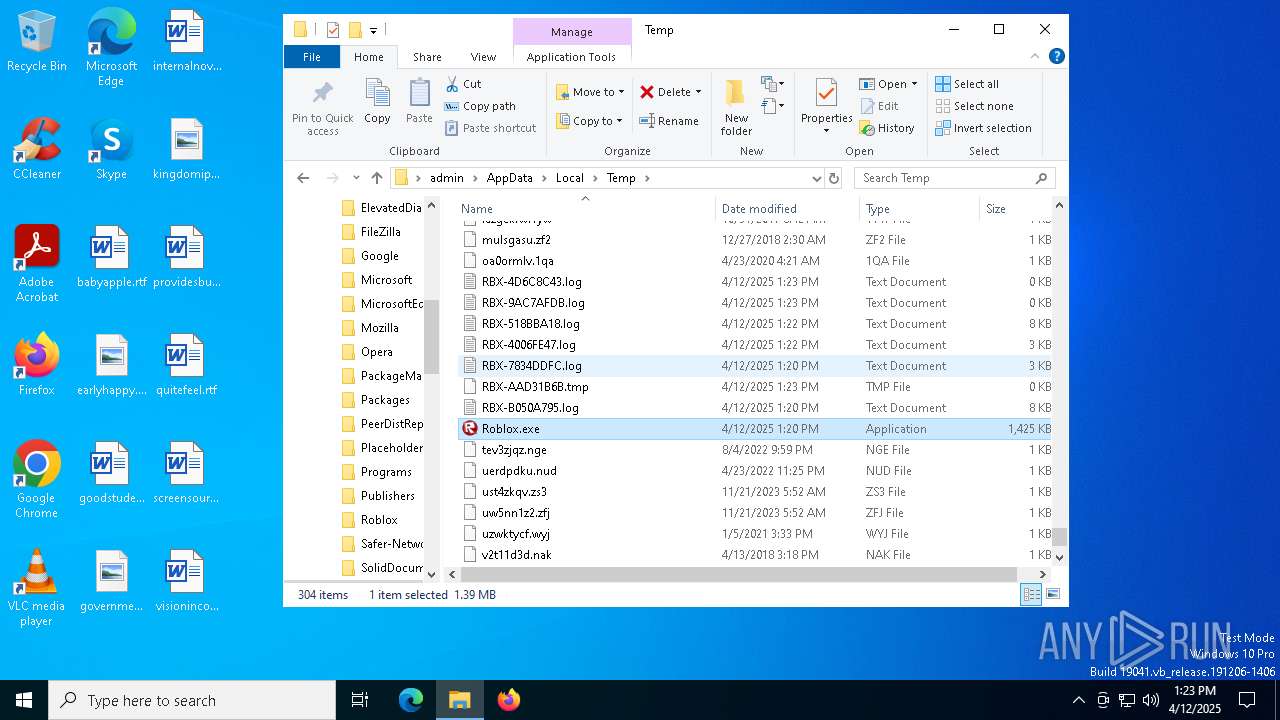
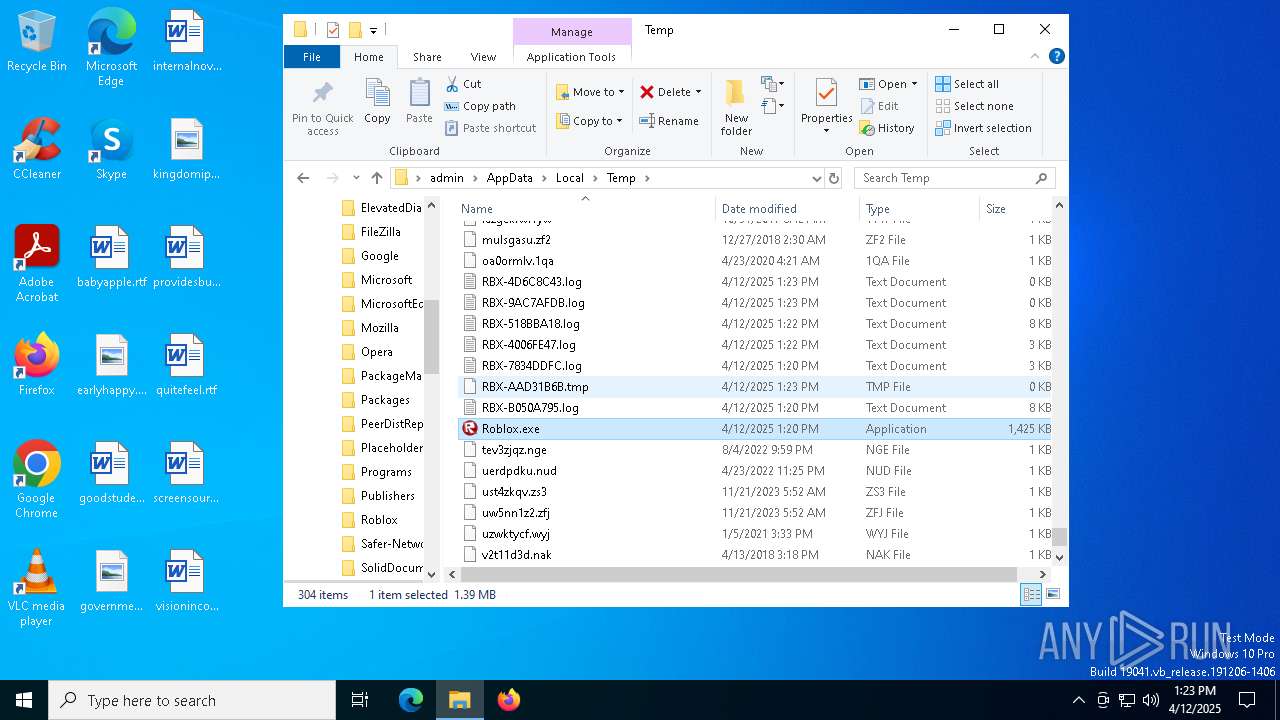
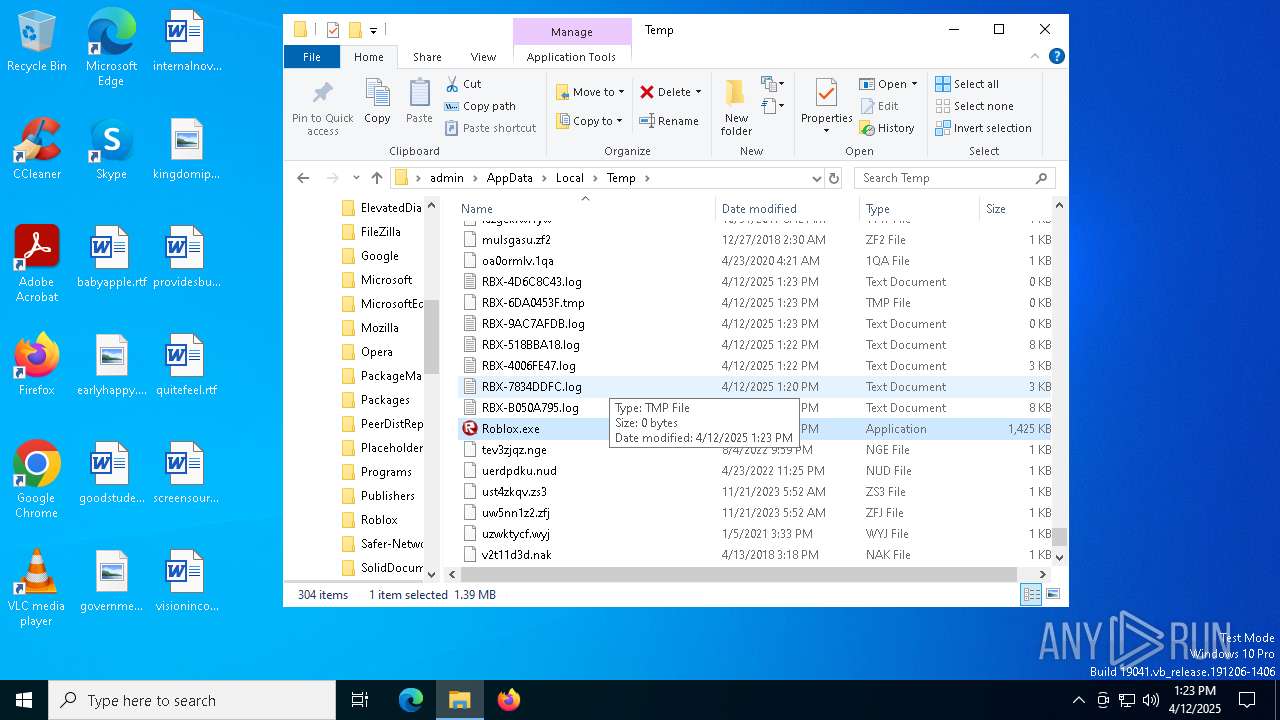
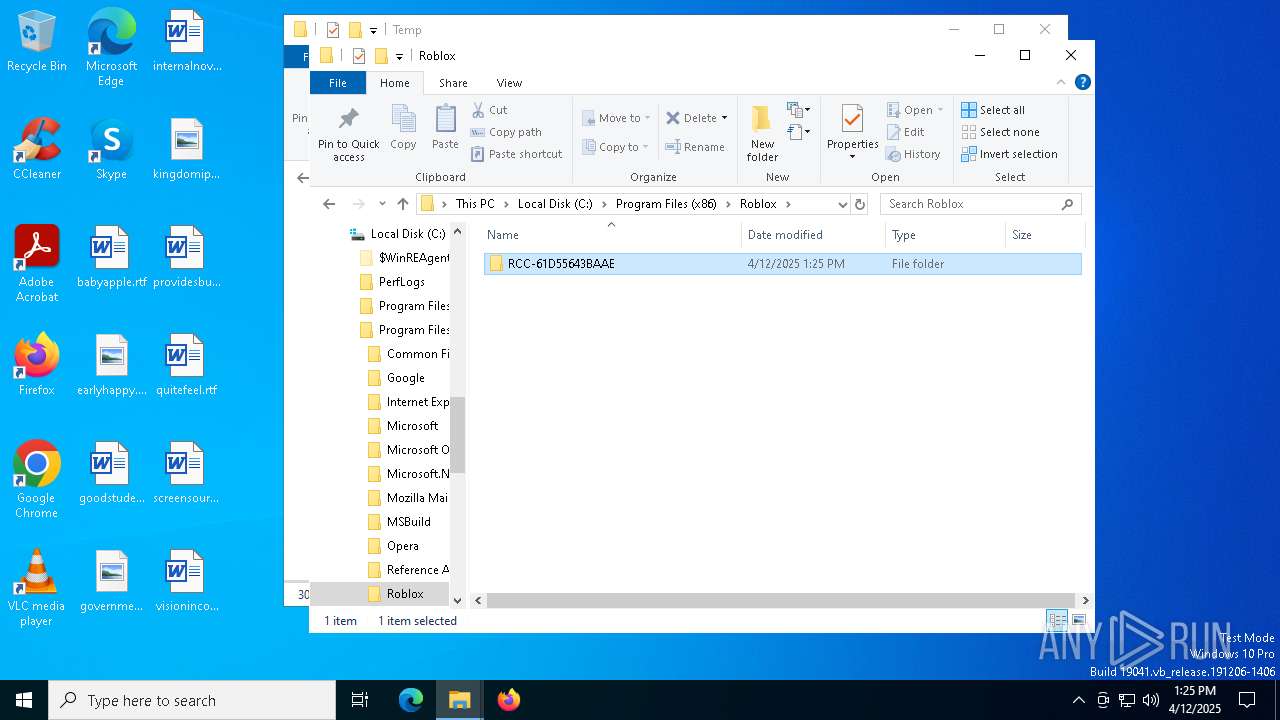
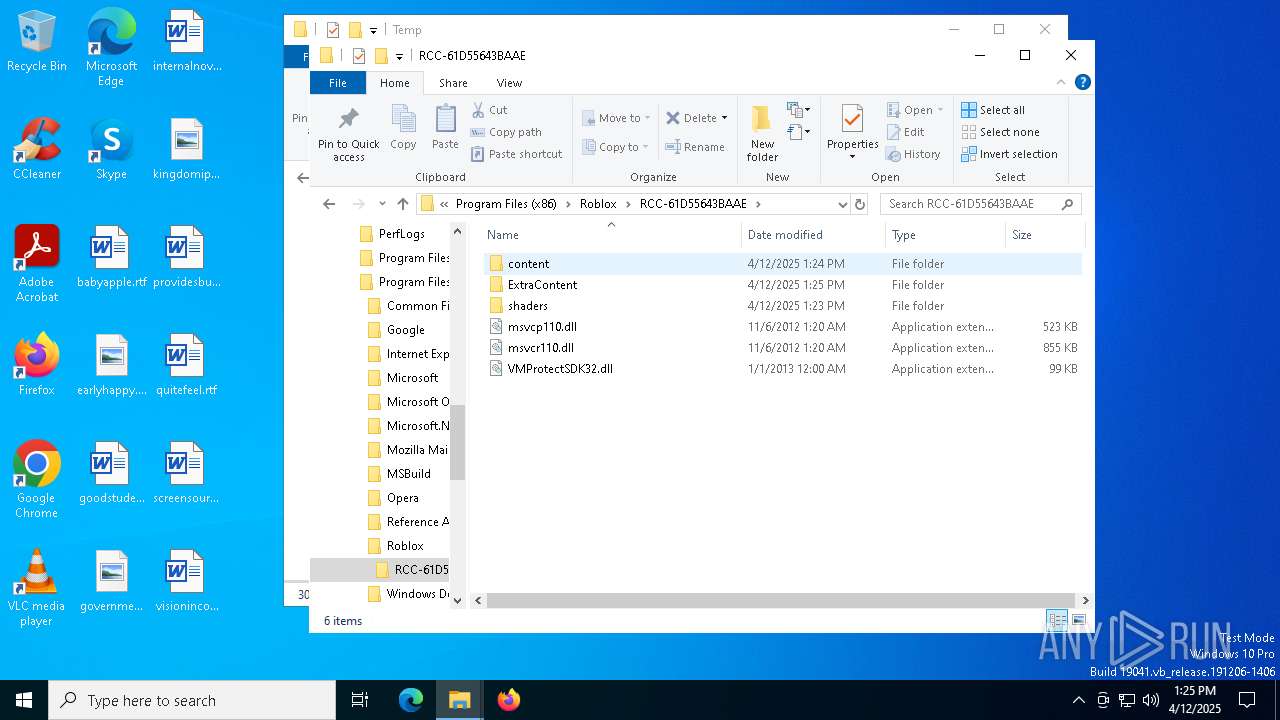
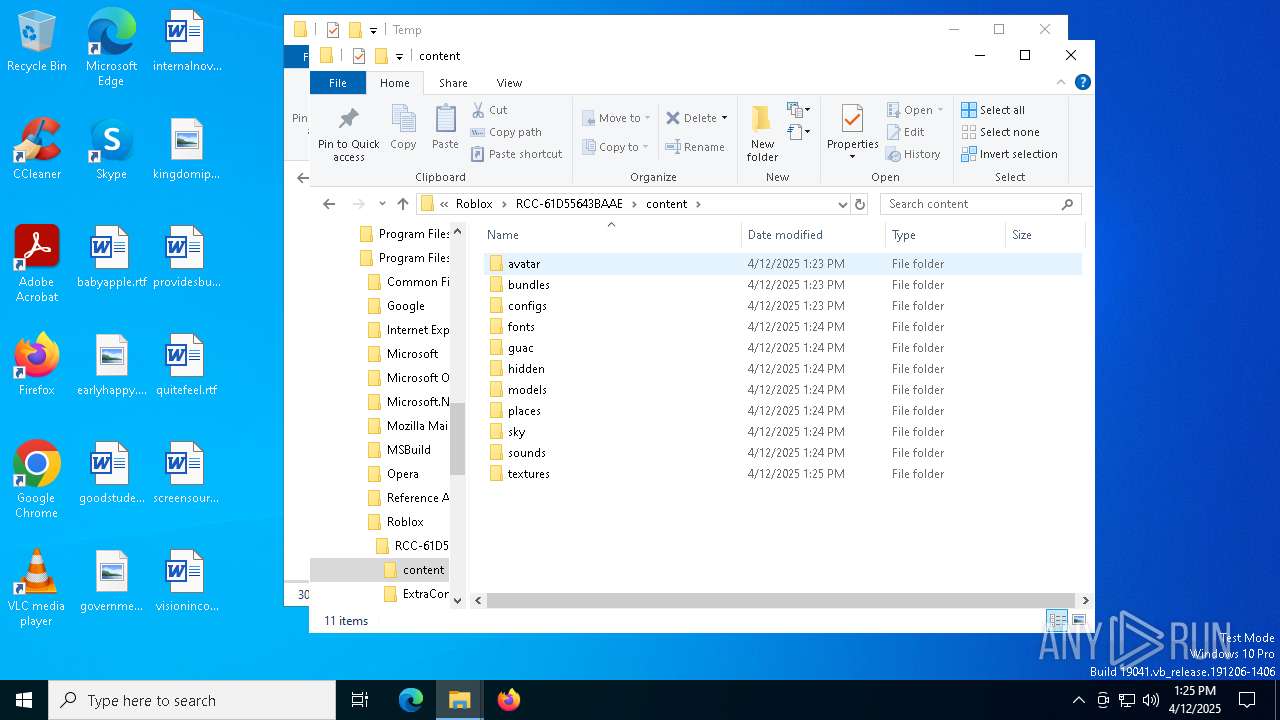
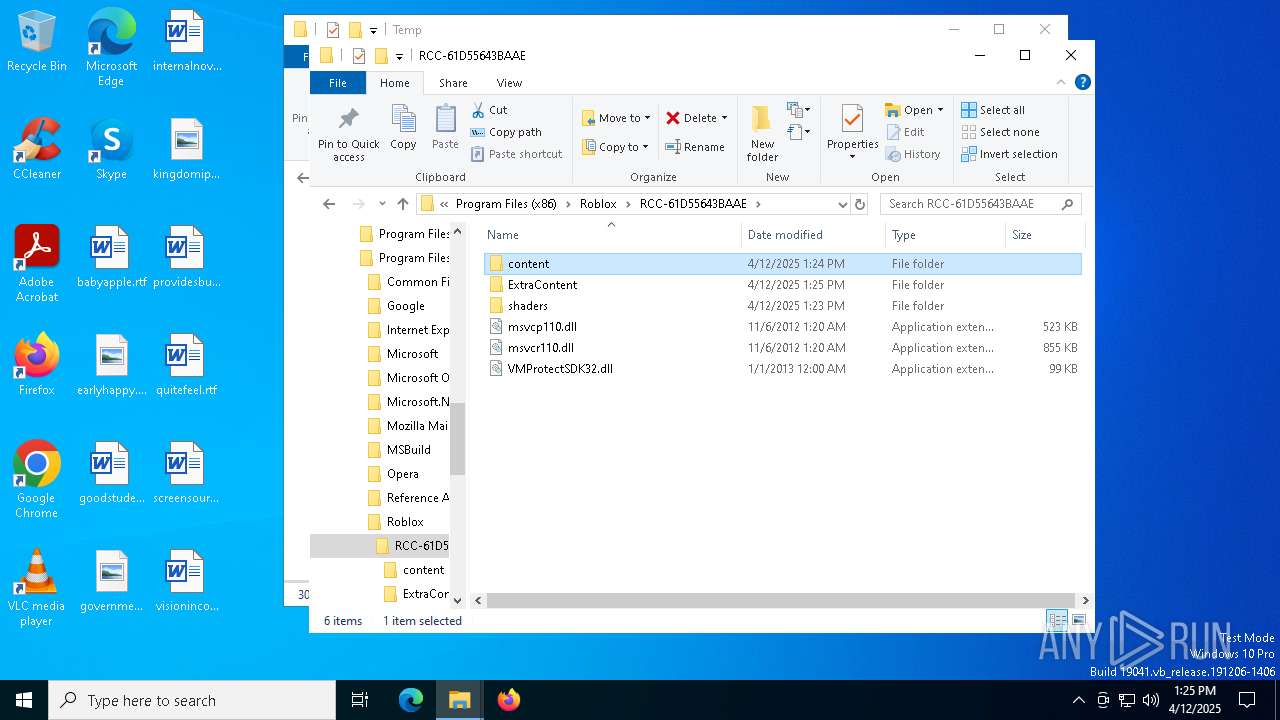
Executable content was dropped or overwritten
- Roblox.exe (PID: 7496)
Process drops legitimate windows executable
- Roblox.exe (PID: 7496)
INFO
Checks supported languages
- Roblox.exe (PID: 2284)
- Roblox.exe (PID: 1452)
- Roblox.exe (PID: 7188)
- Roblox.exe (PID: 7084)
- Roblox.exe (PID: 7496)
- Roblox.exe (PID: 7756)
- ShellExperienceHost.exe (PID: 4172)
The sample compiled with english language support
- Roblox.exe (PID: 2284)
- Roblox.exe (PID: 7496)
Reads the computer name
- Roblox.exe (PID: 2284)
- Roblox.exe (PID: 7188)
- Roblox.exe (PID: 1452)
- Roblox.exe (PID: 7084)
- Roblox.exe (PID: 7496)
- Roblox.exe (PID: 7756)
- ShellExperienceHost.exe (PID: 4172)
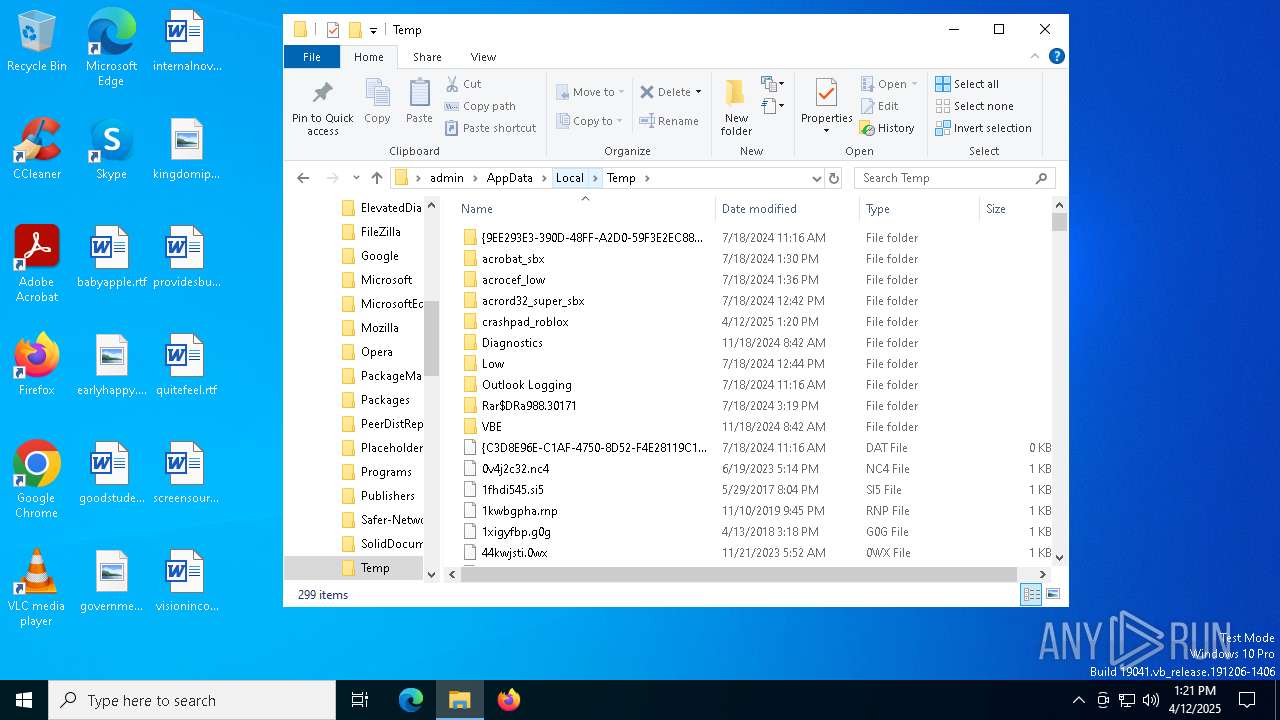
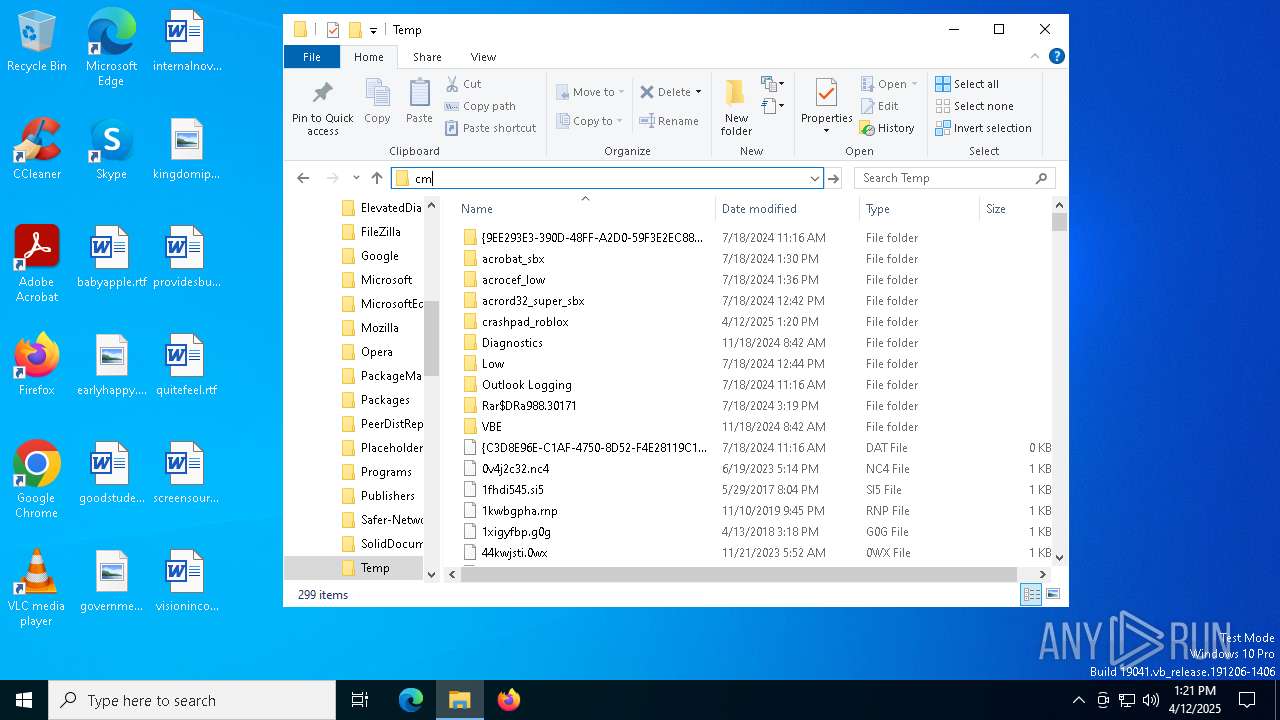
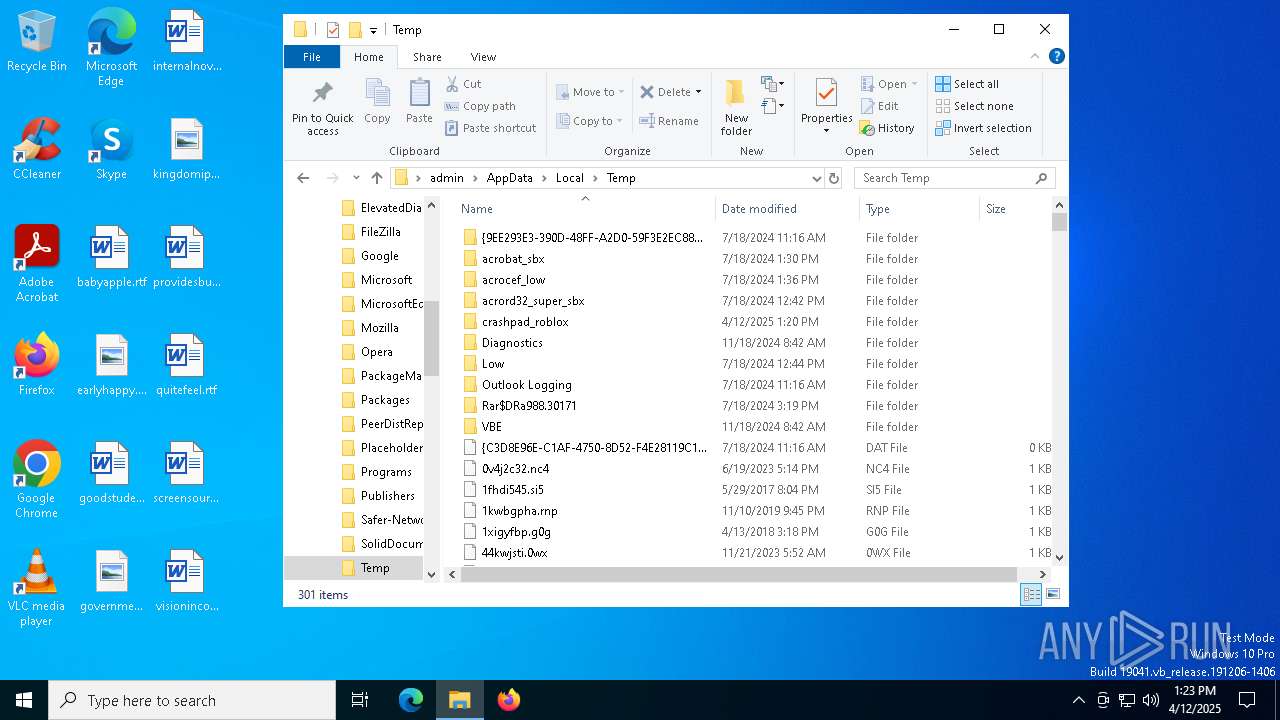
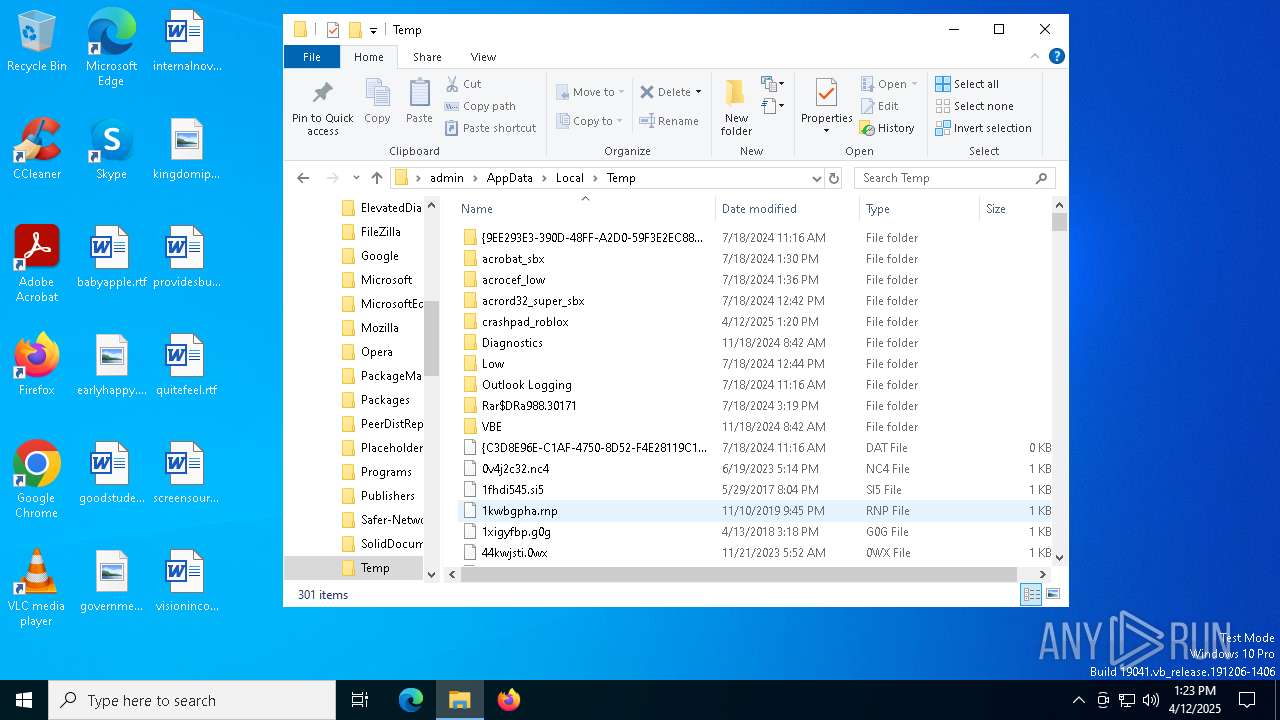
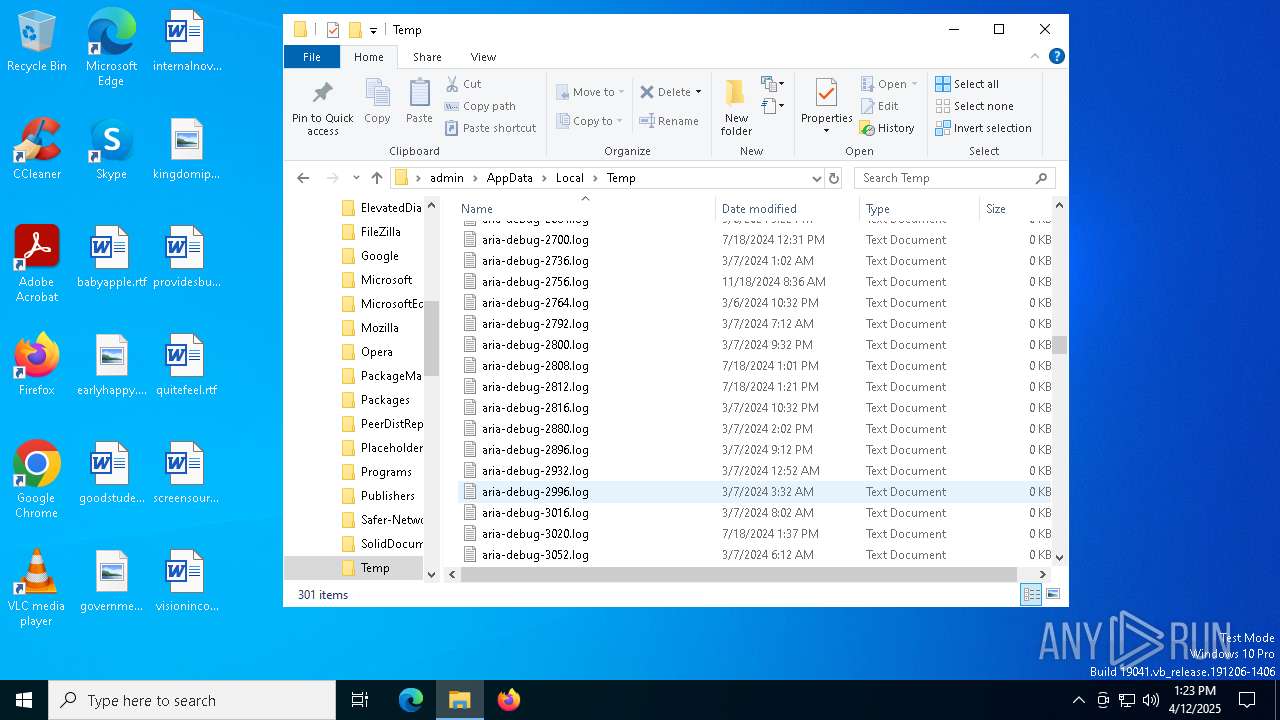
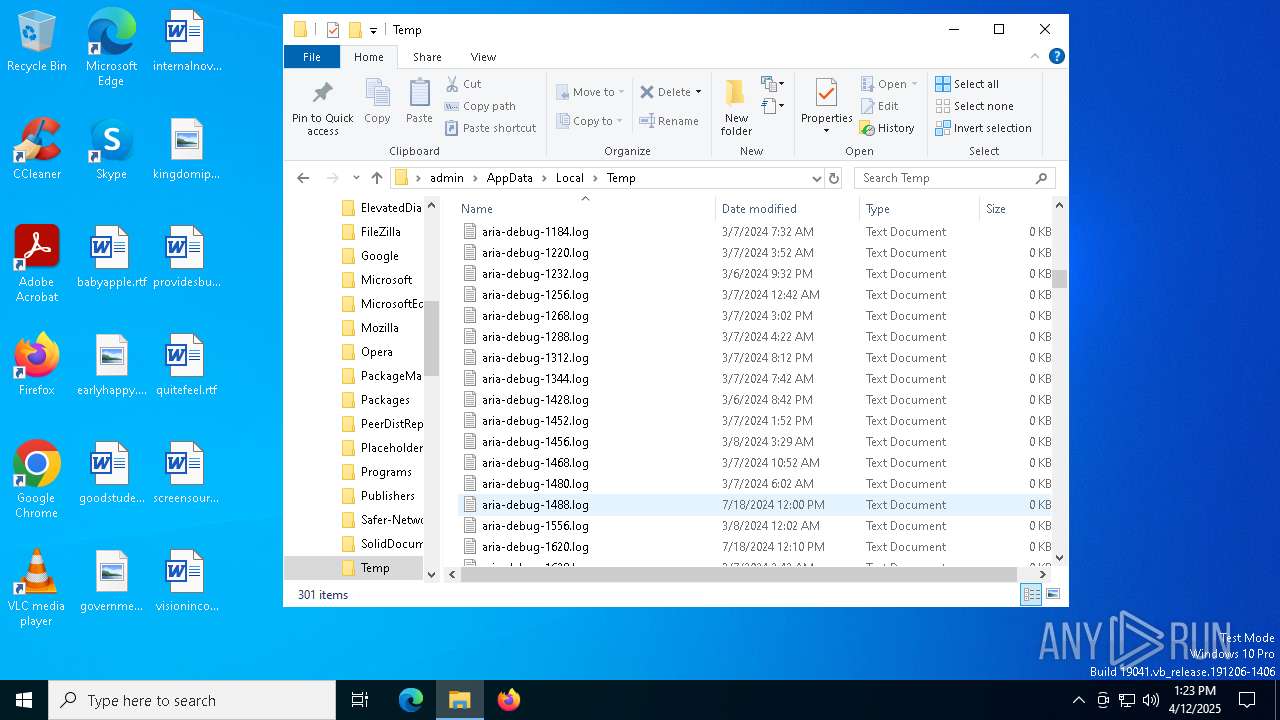
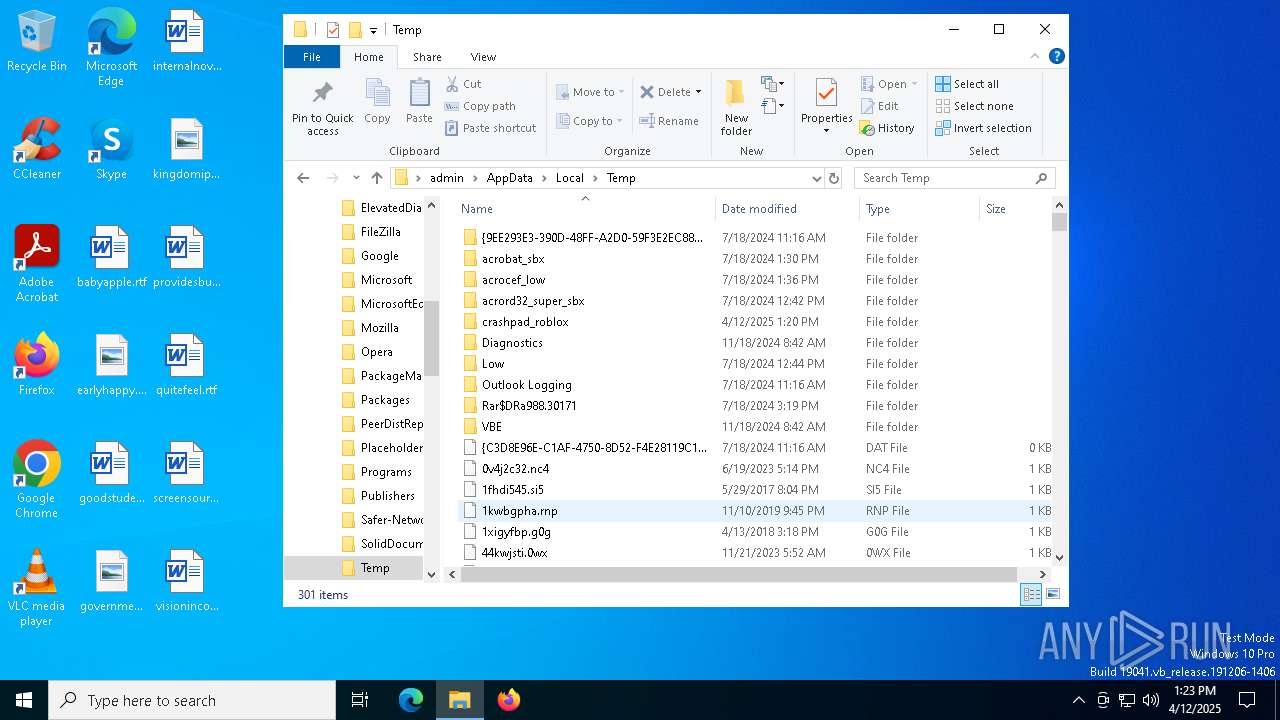
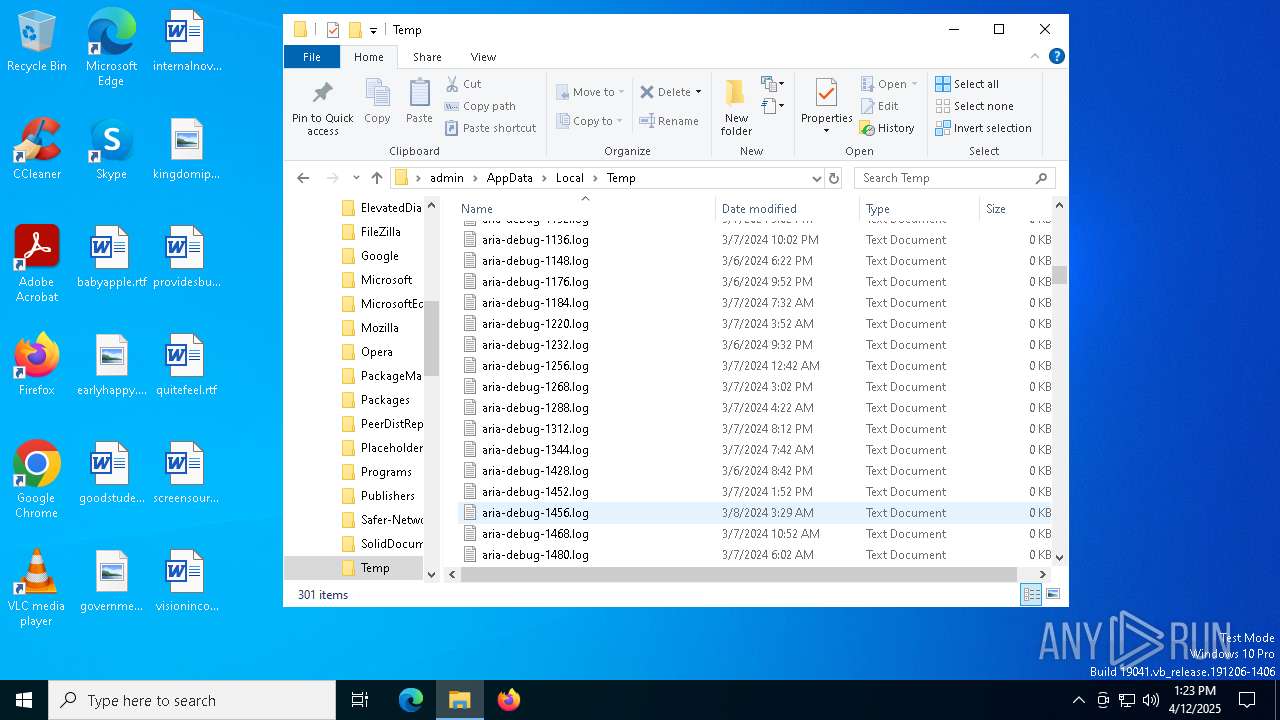
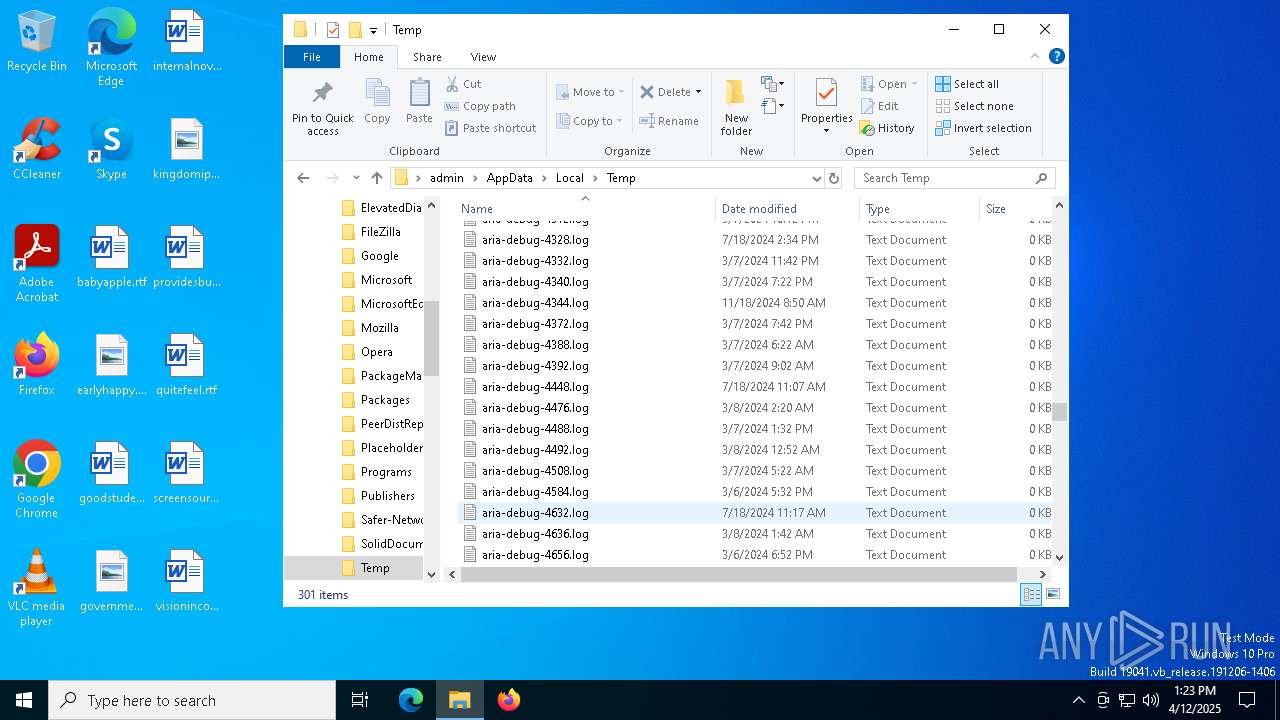
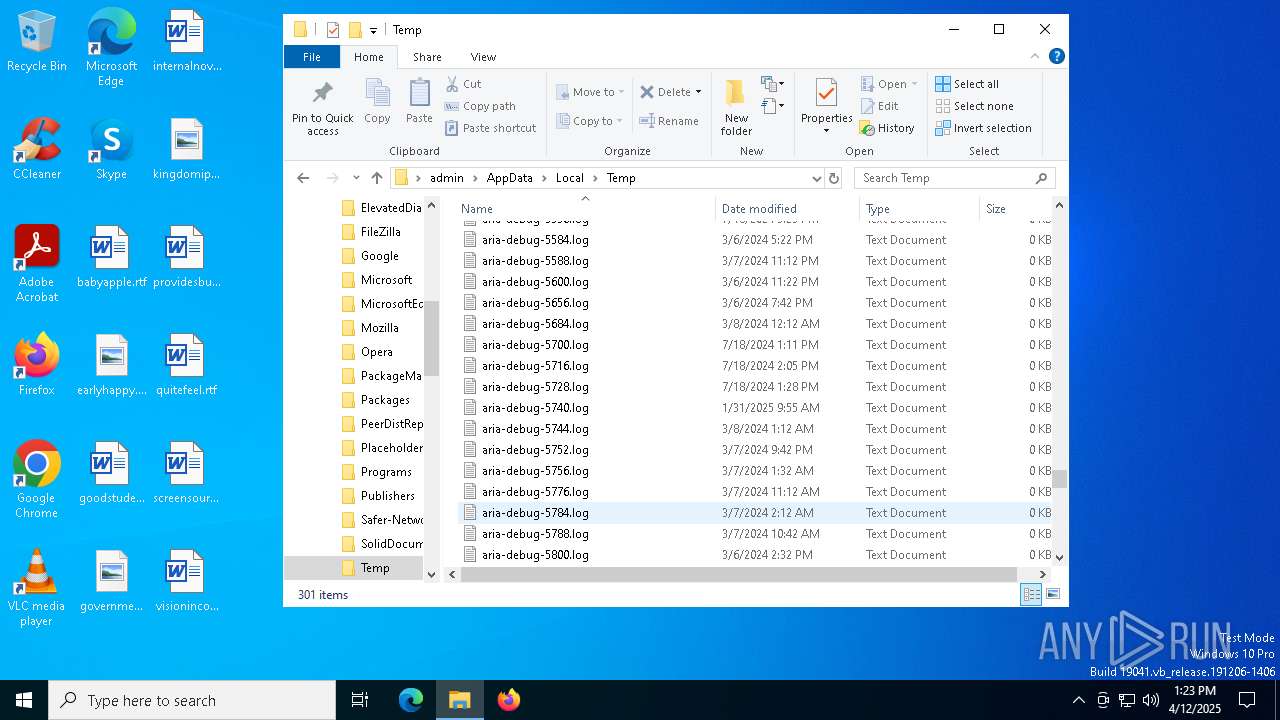
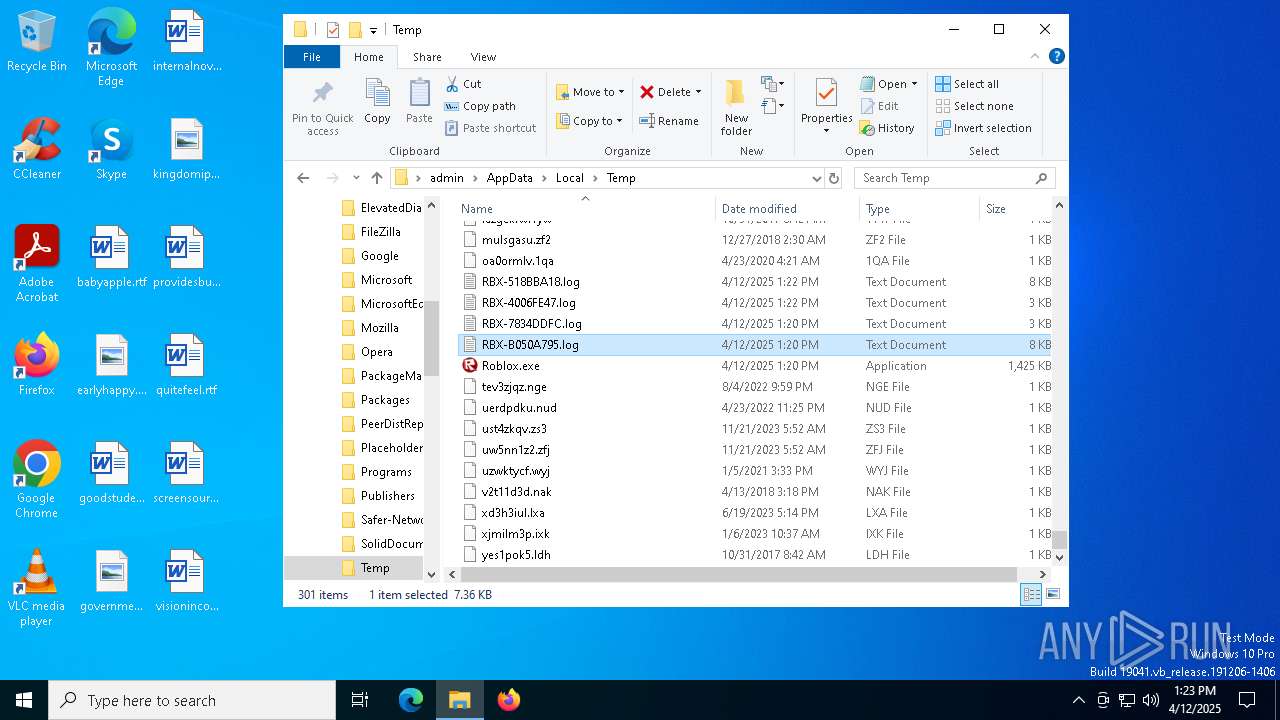
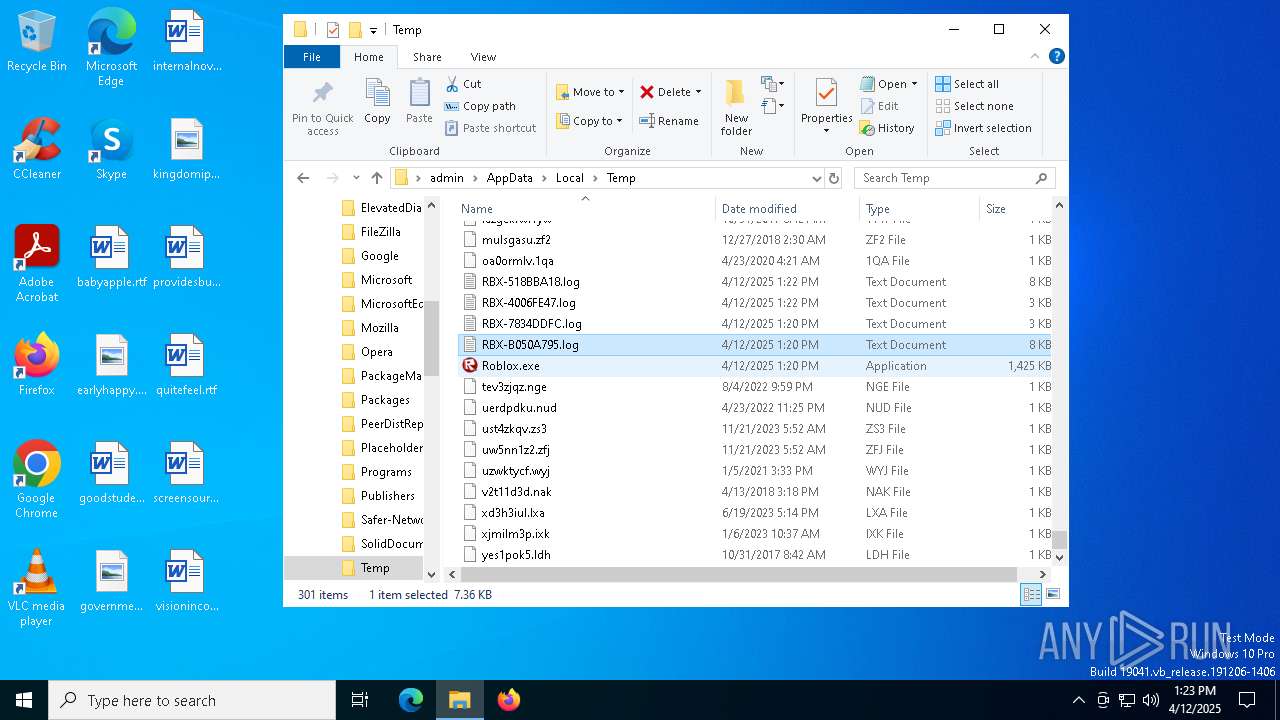
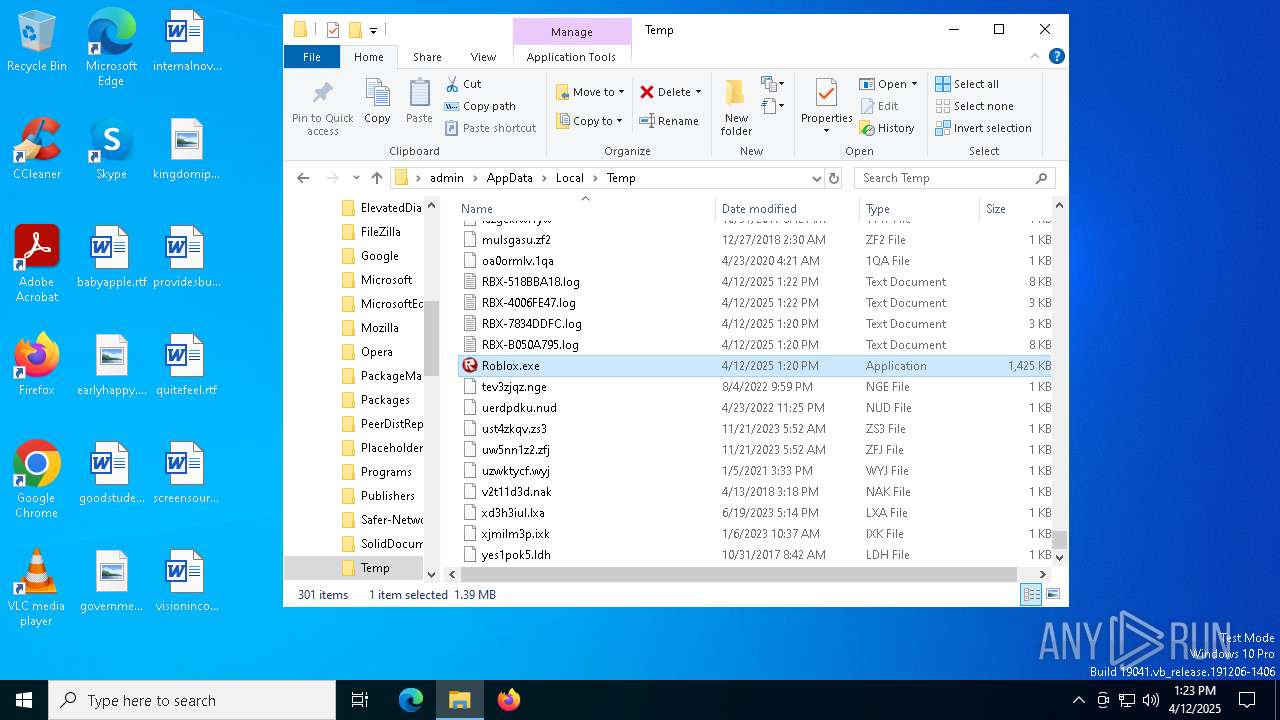
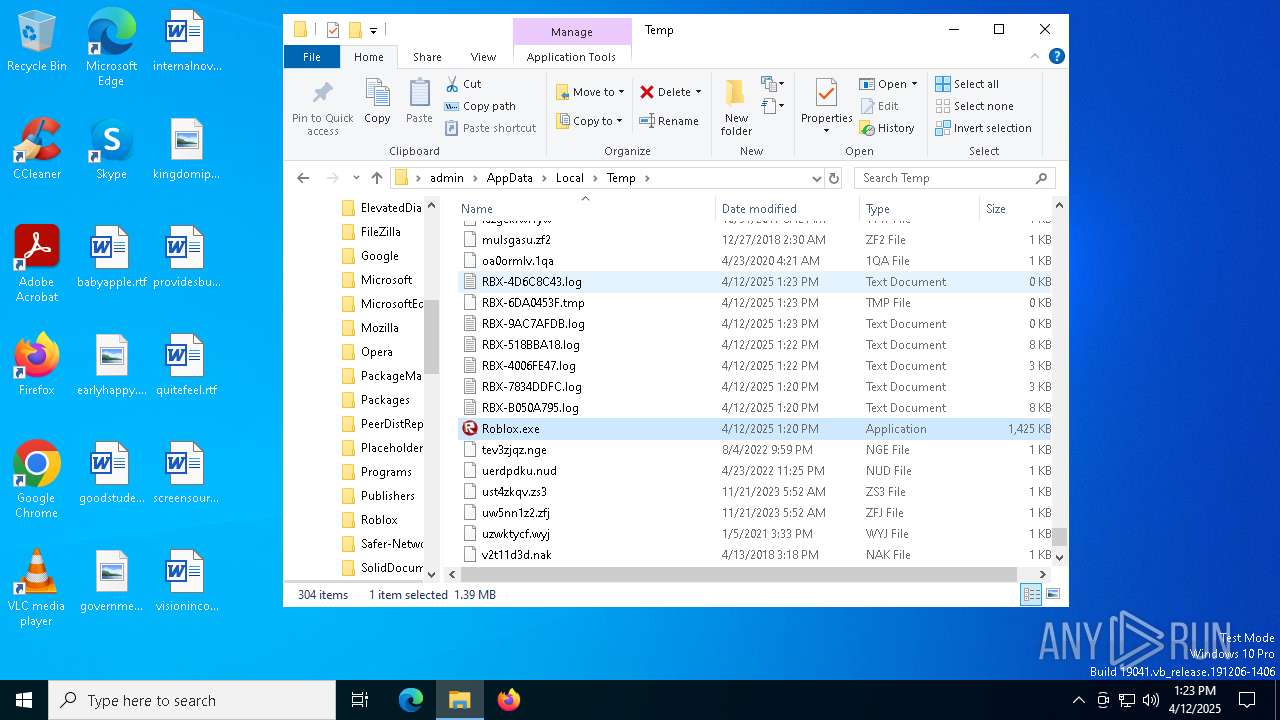
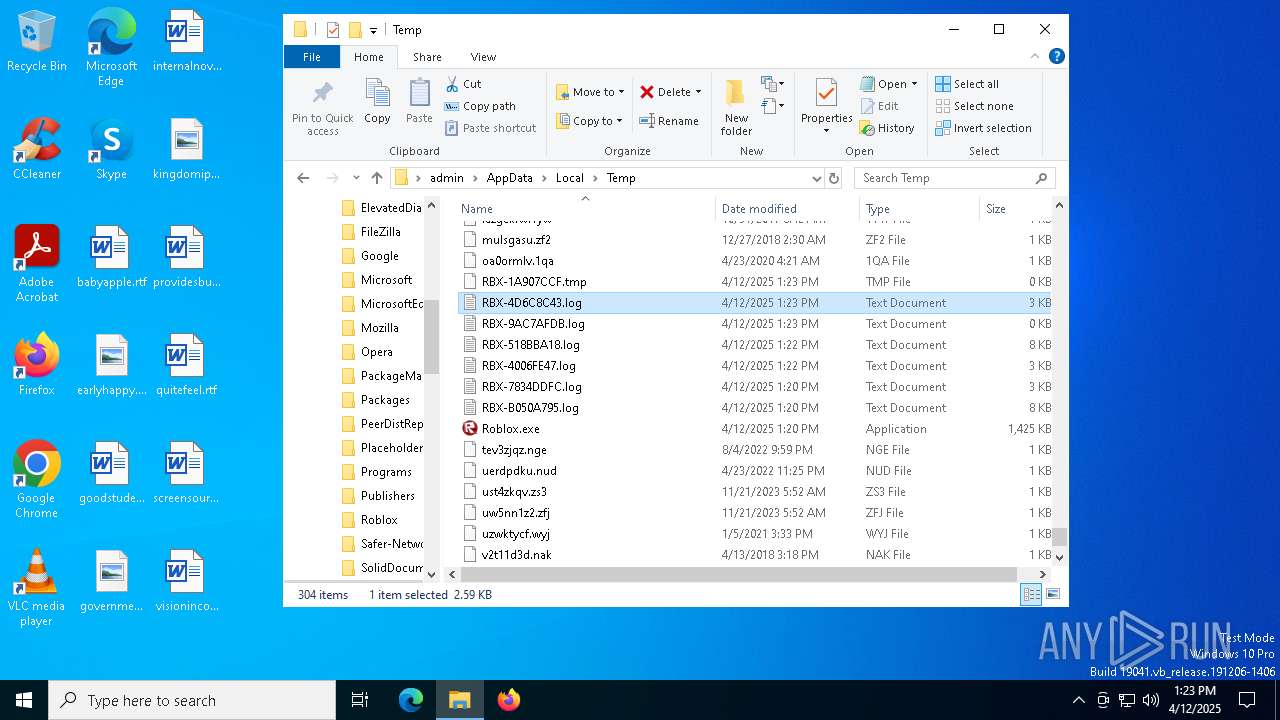
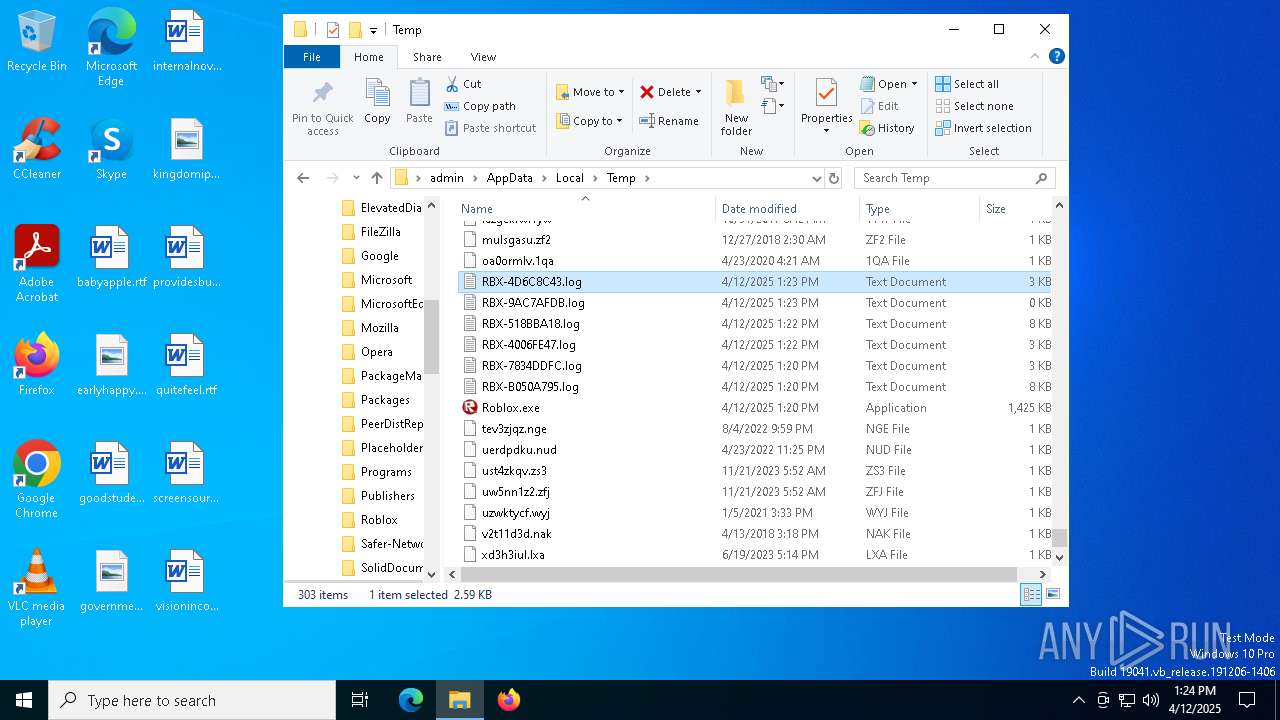
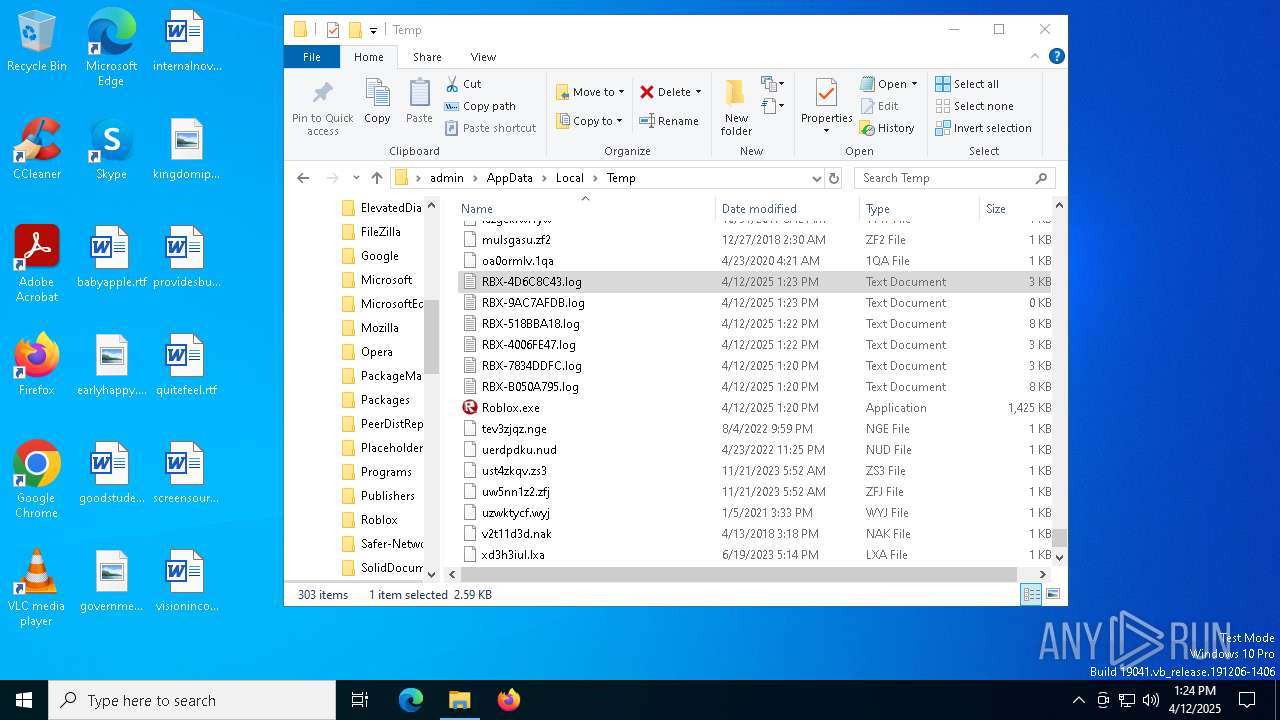
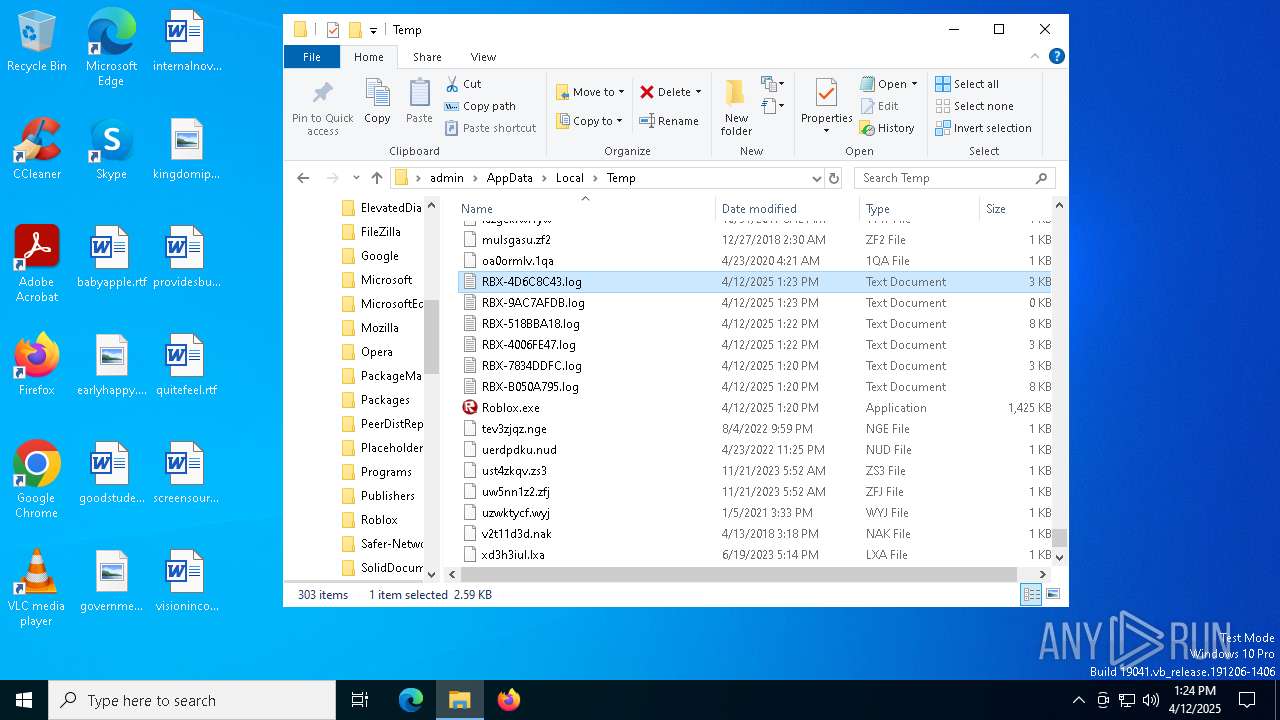
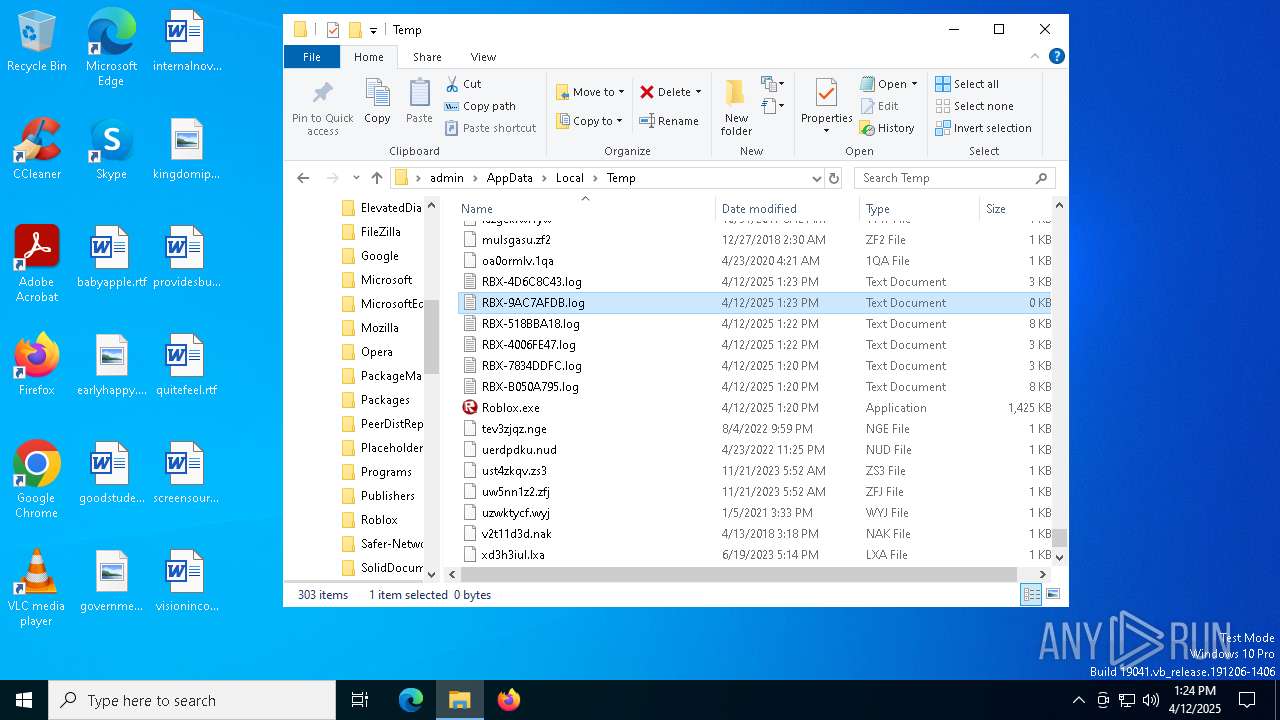
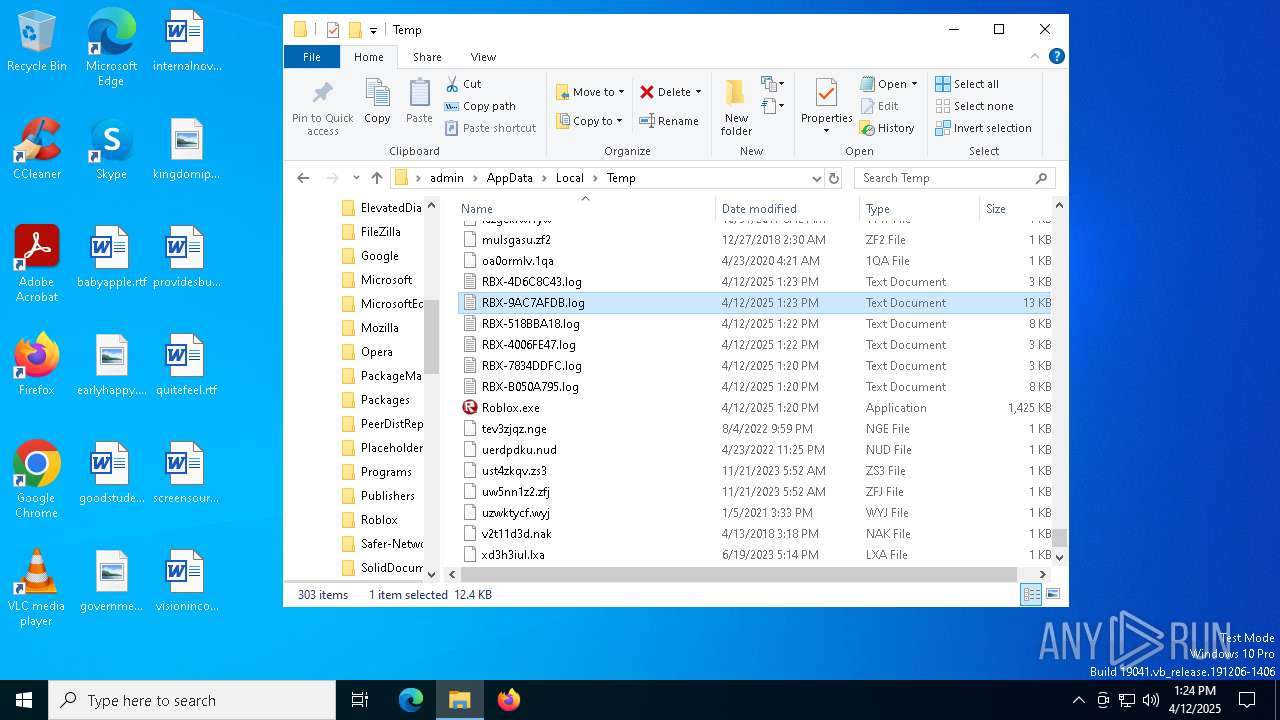
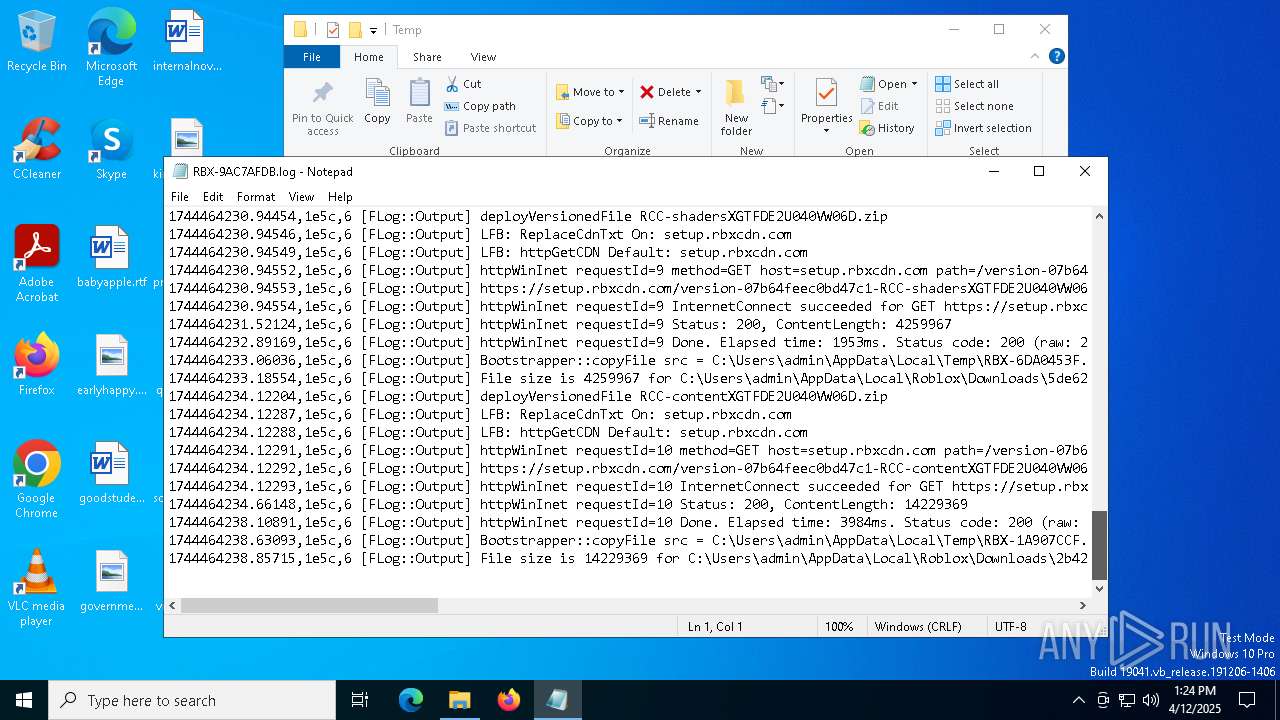
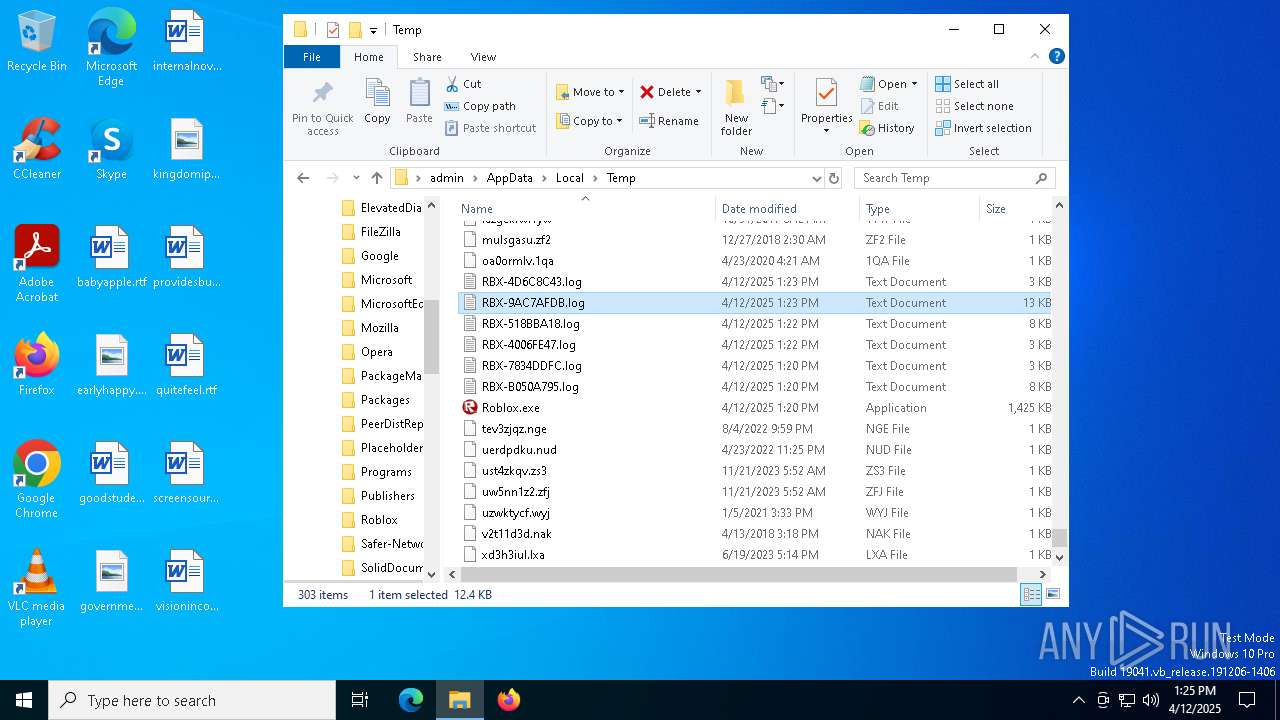
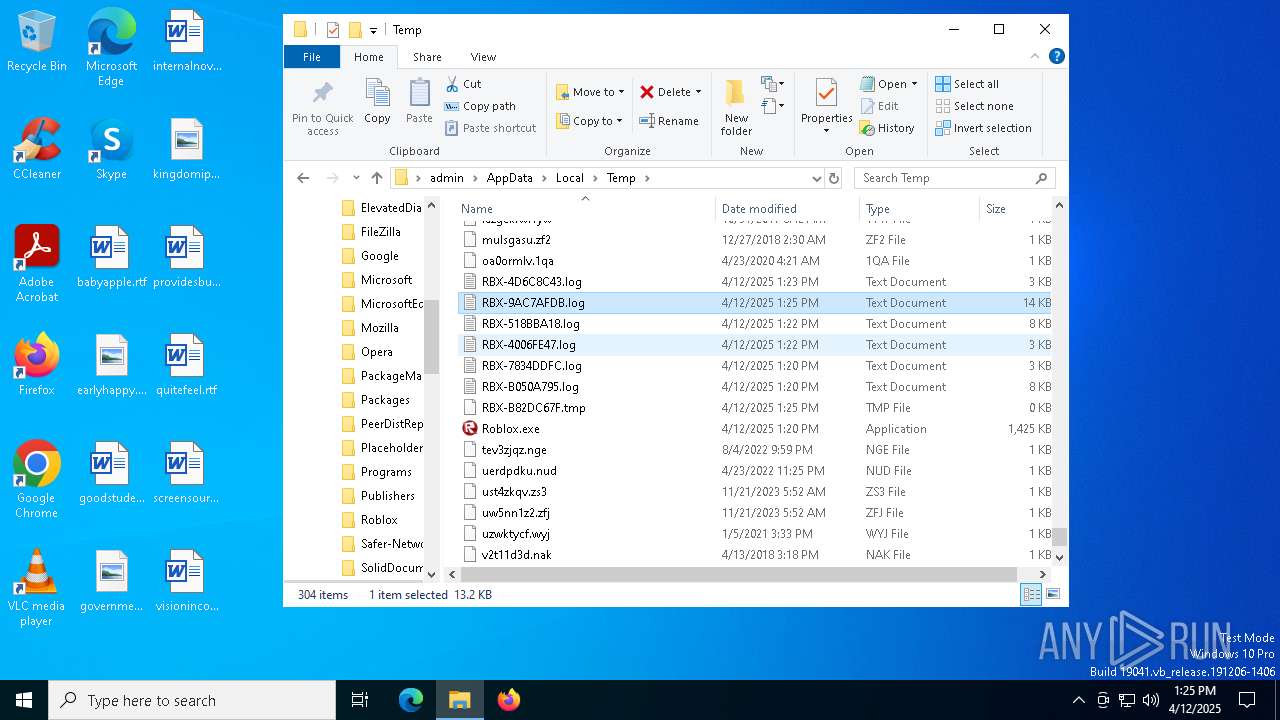
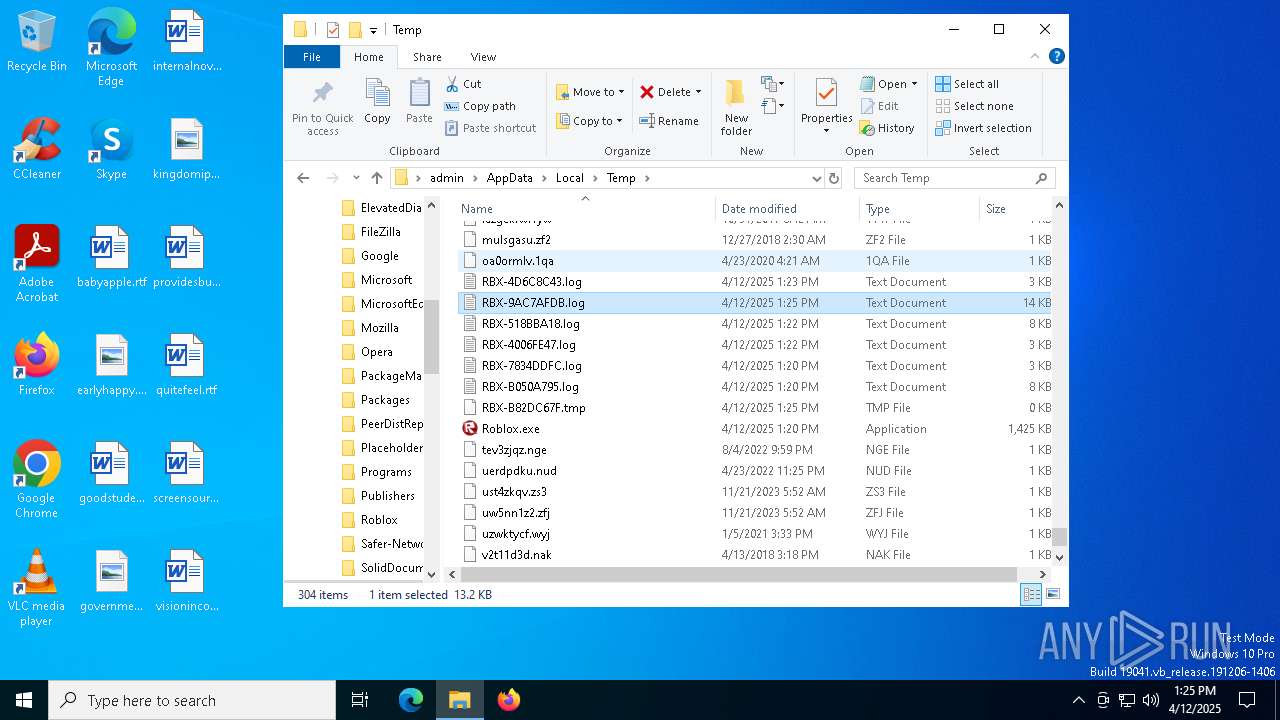
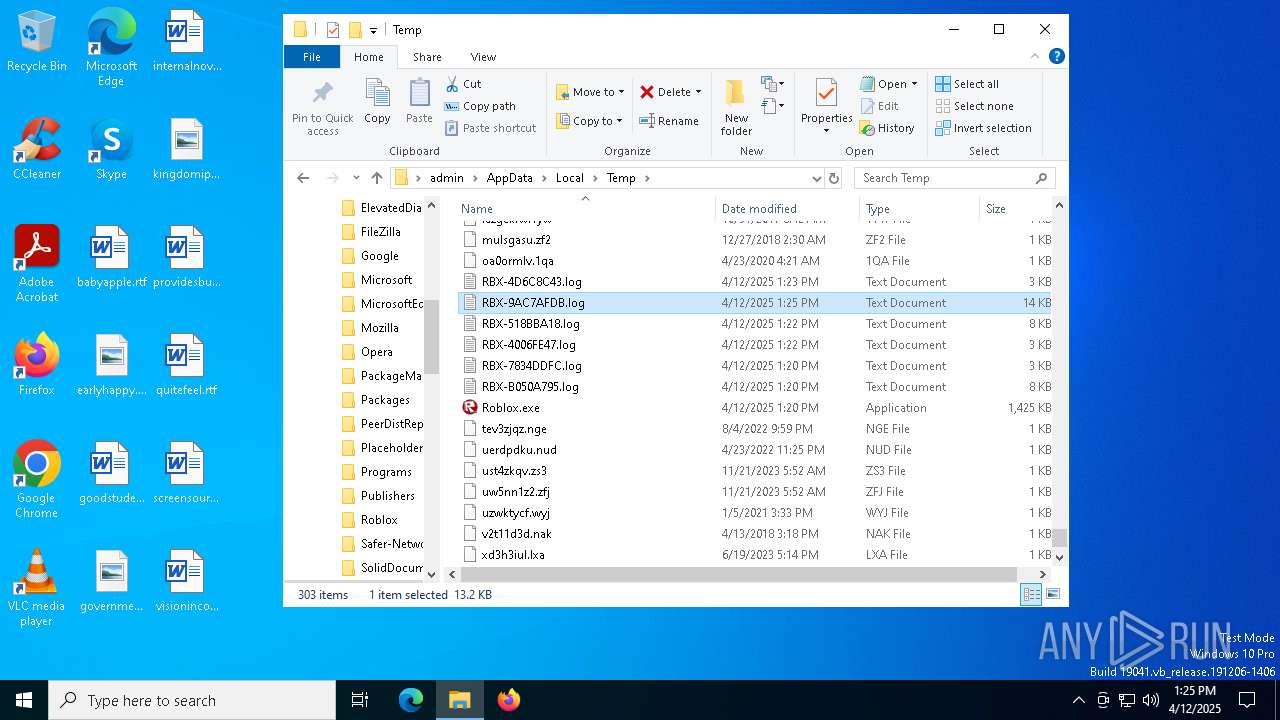
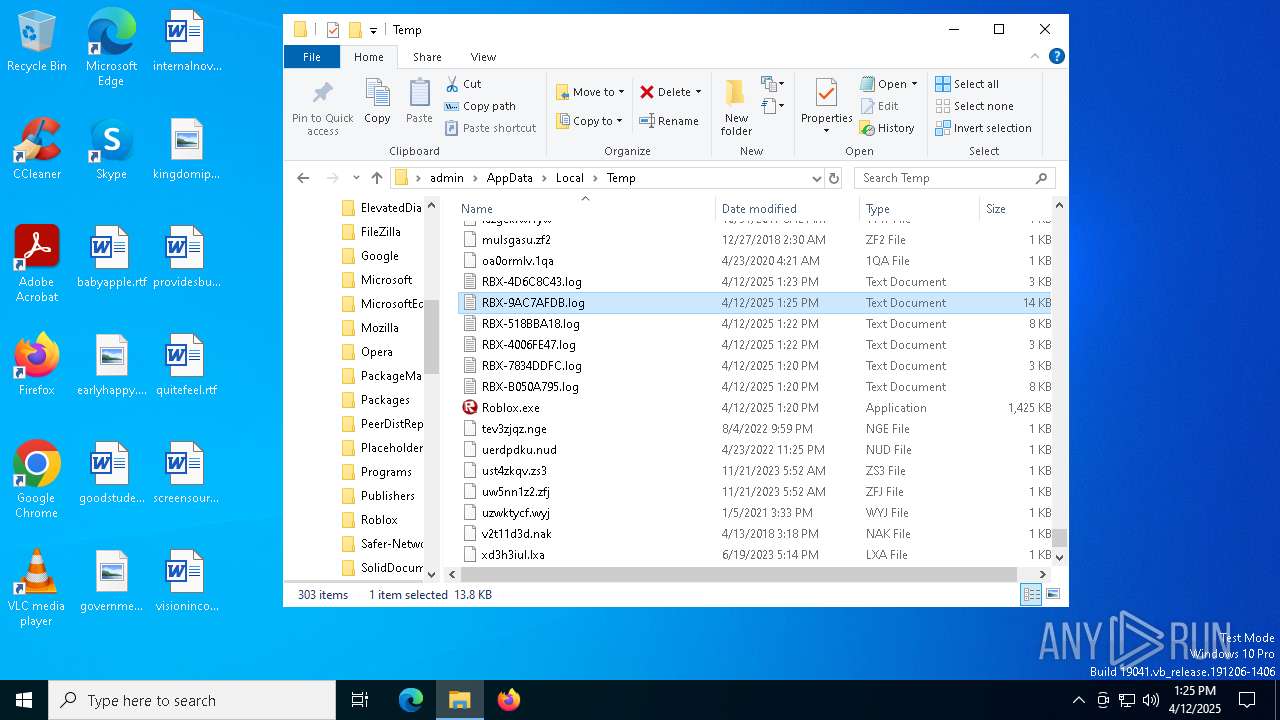
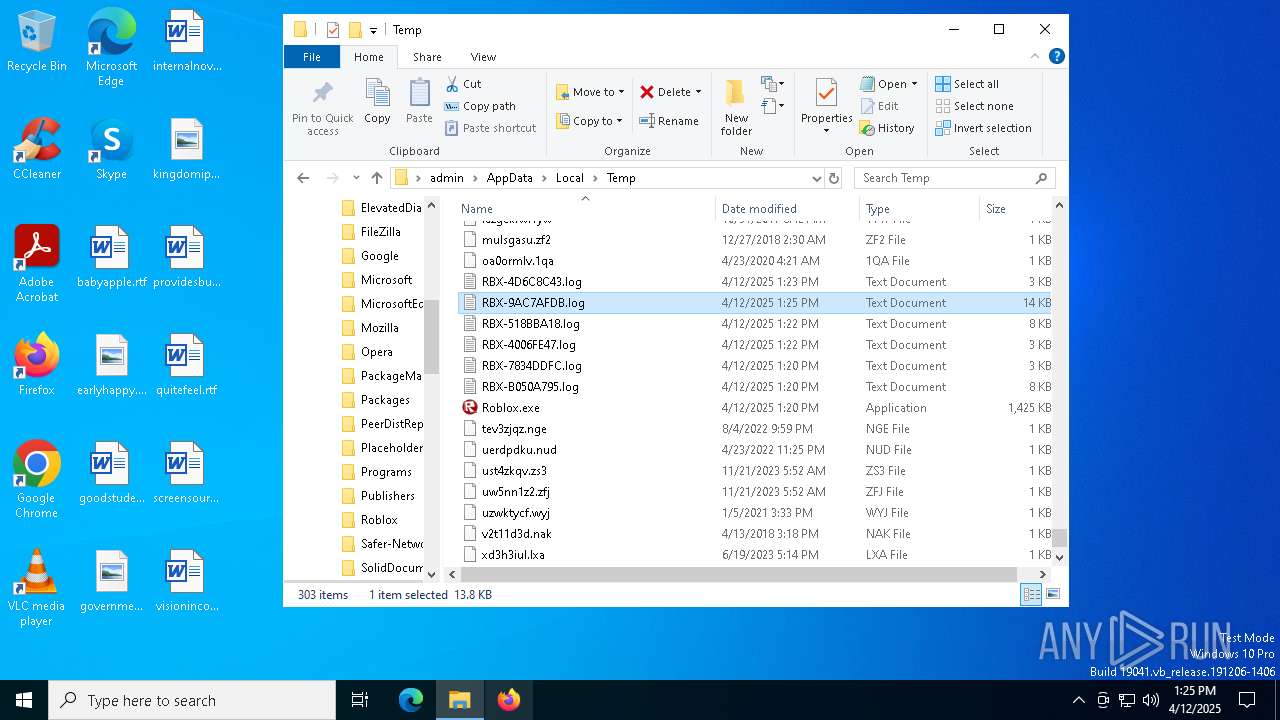
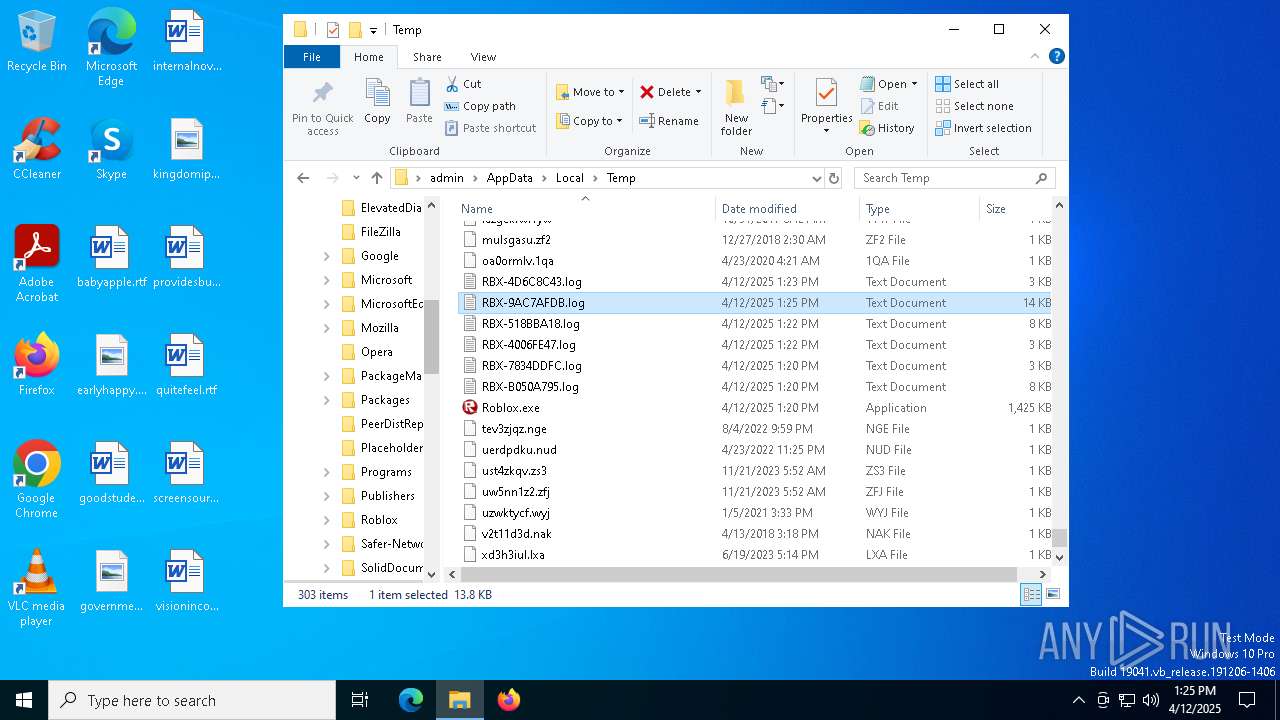
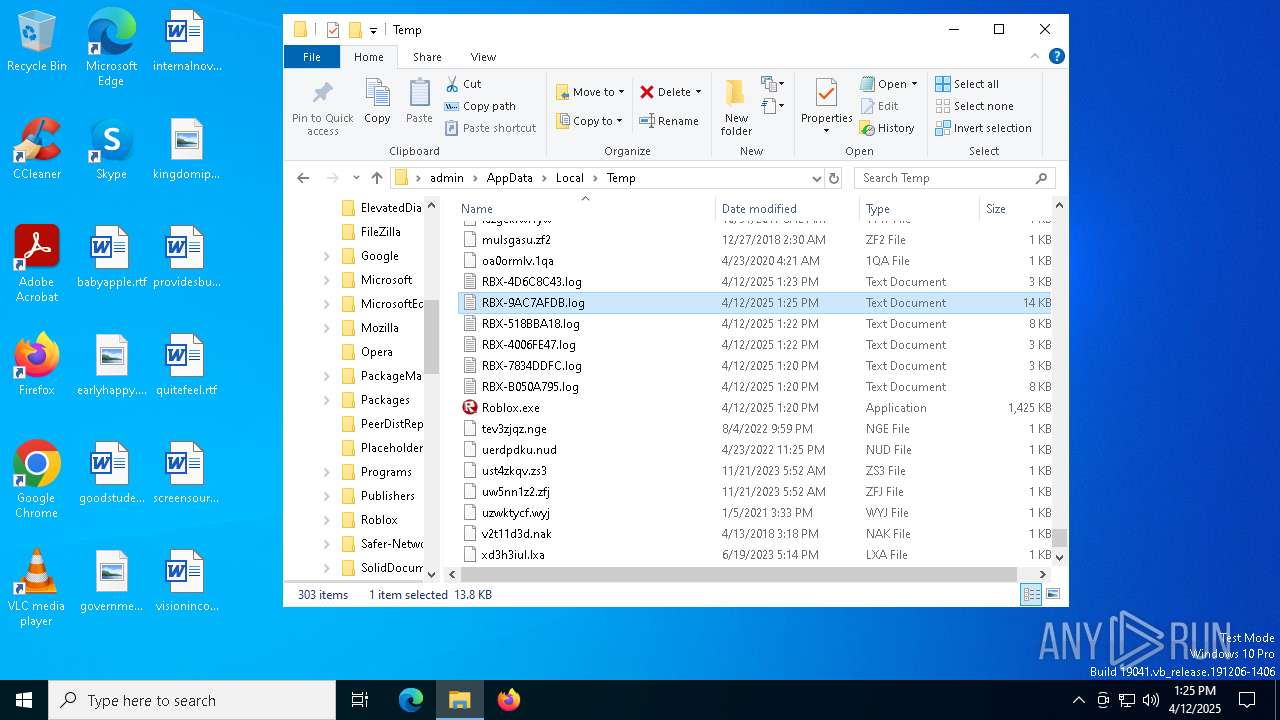
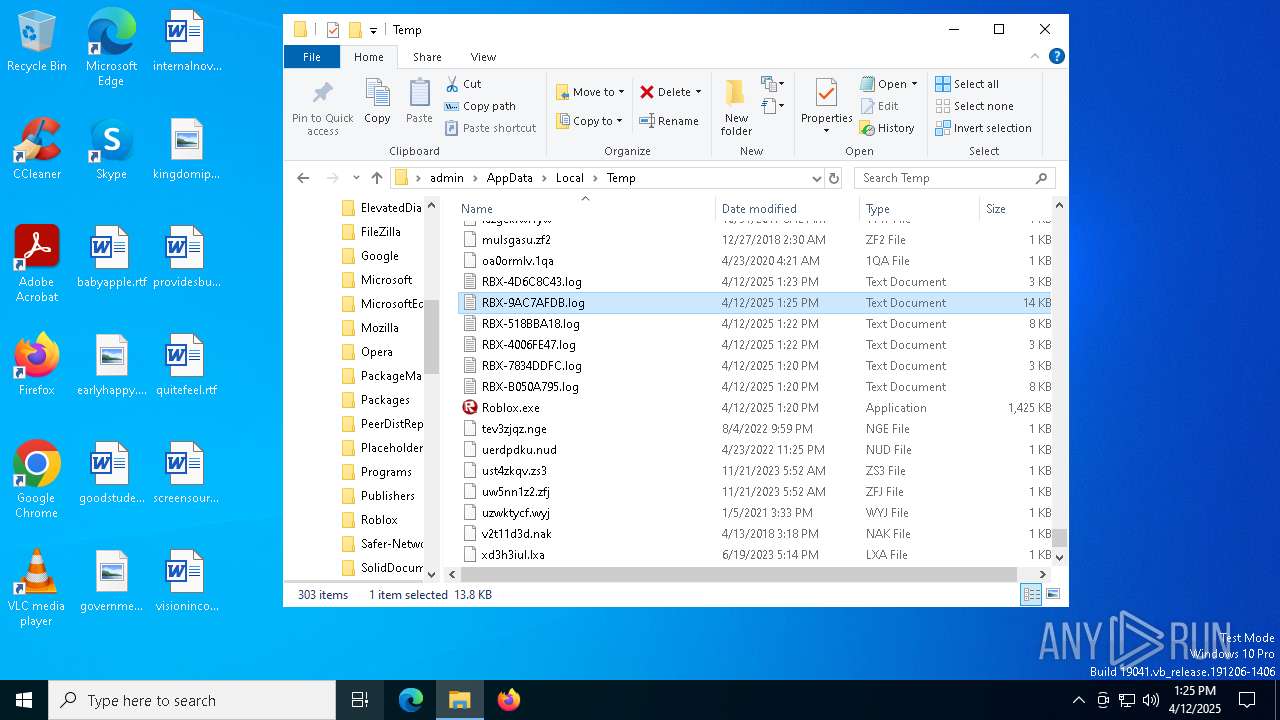
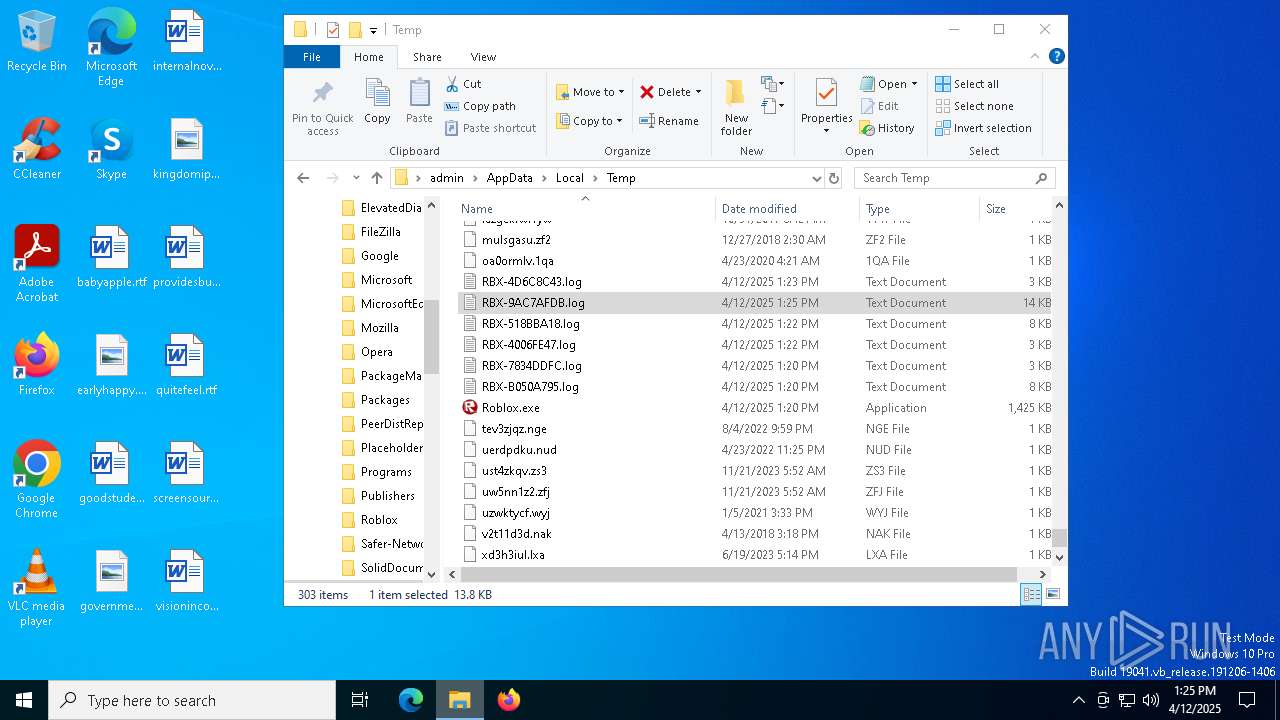
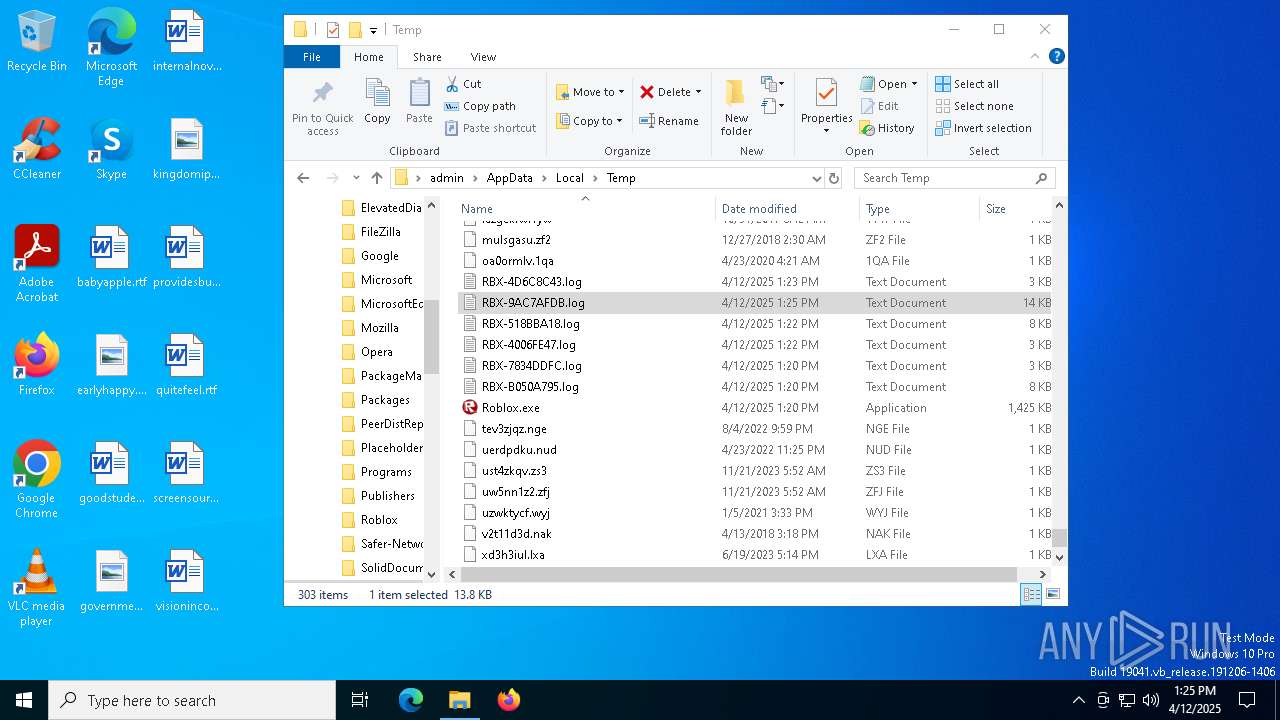
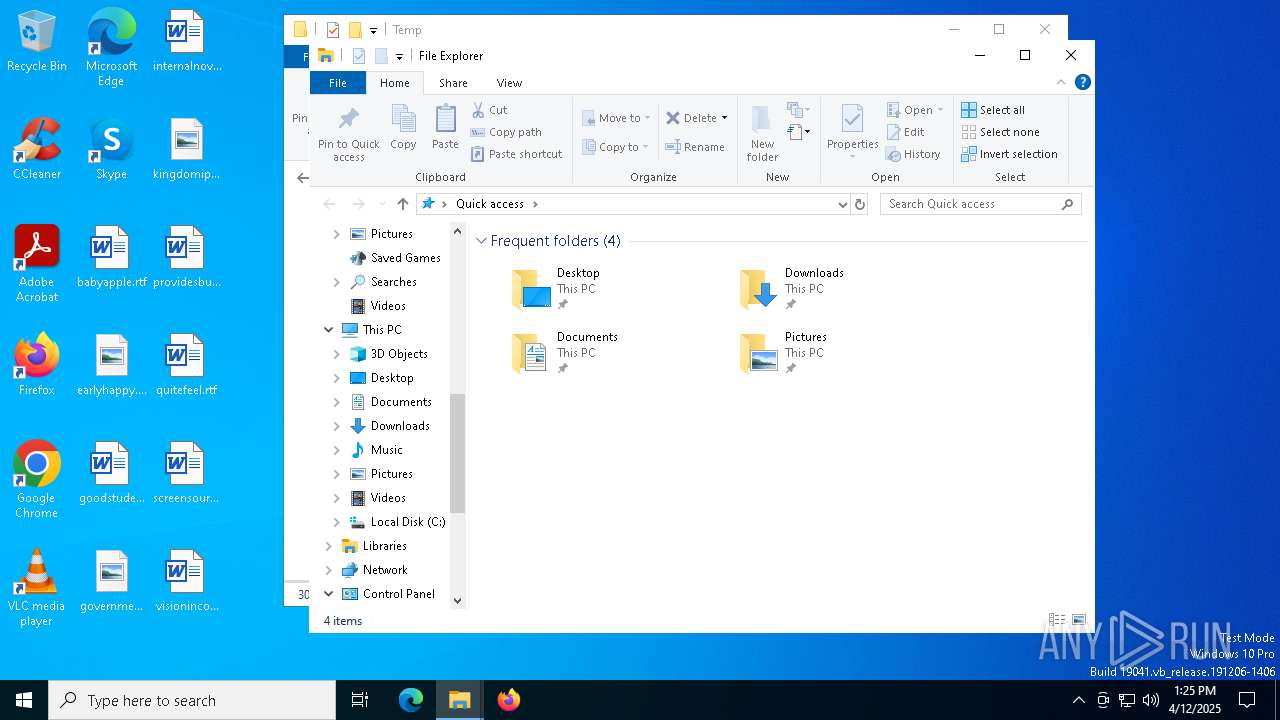
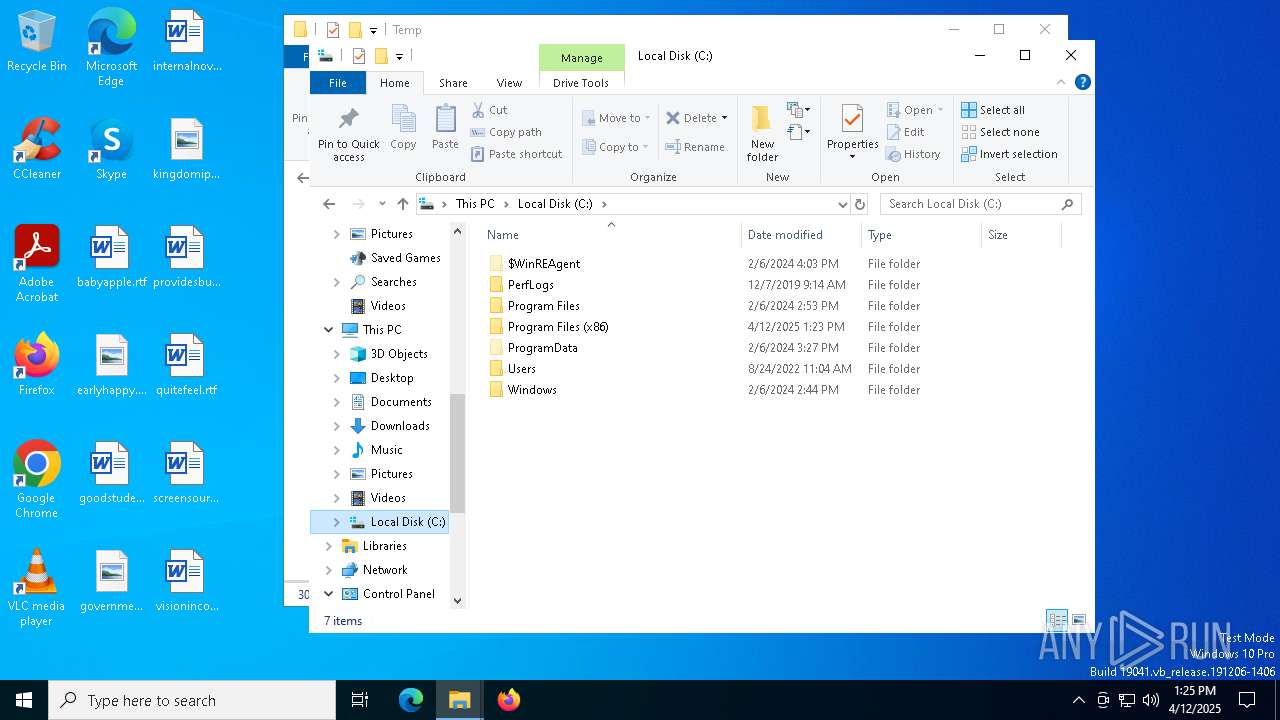
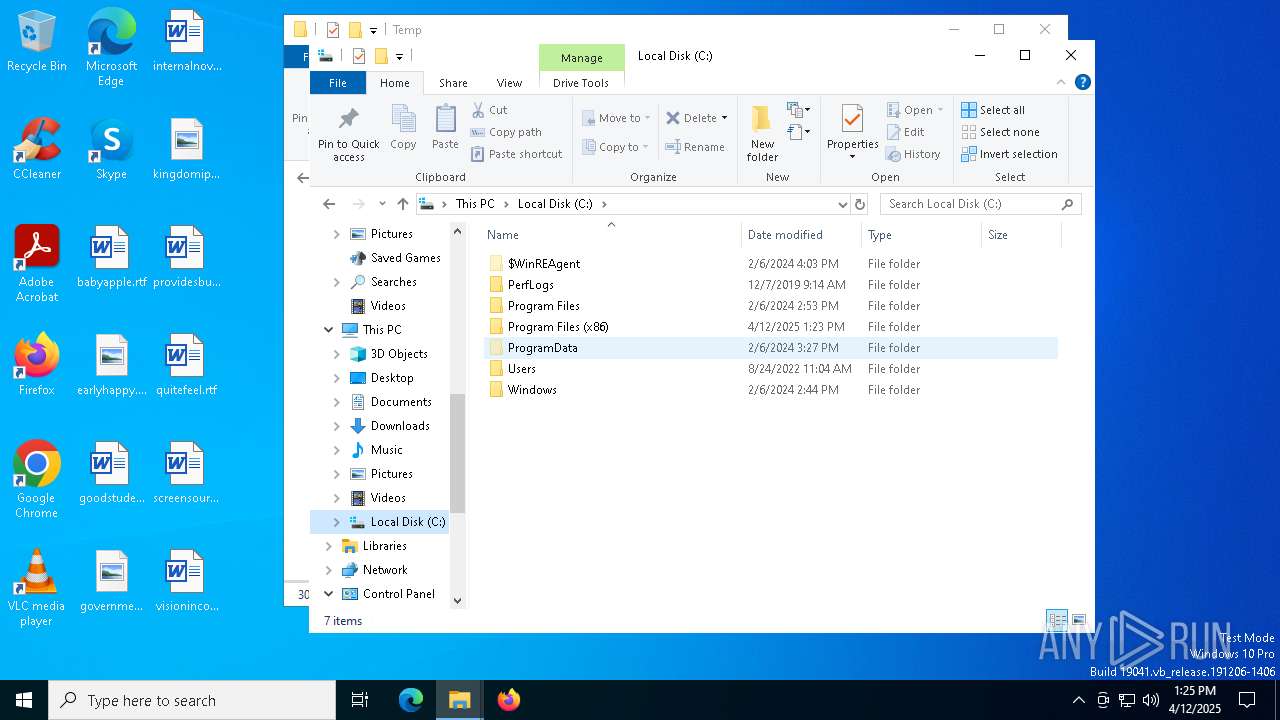
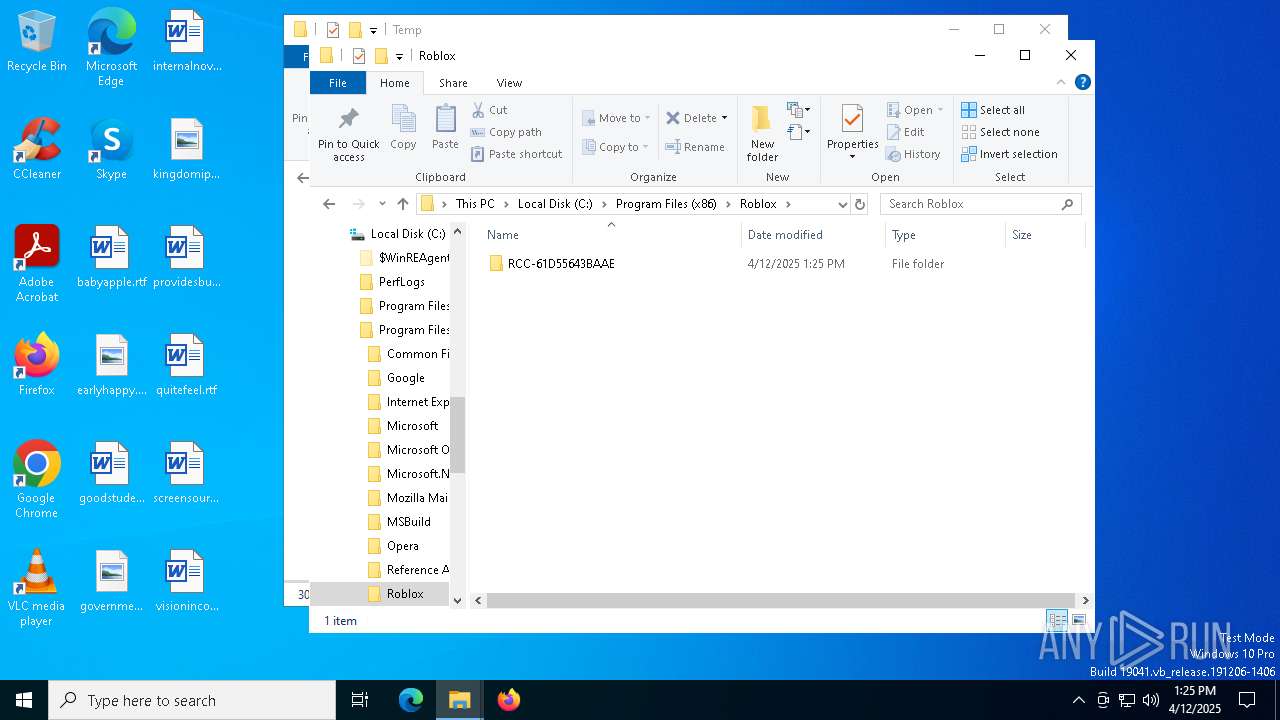
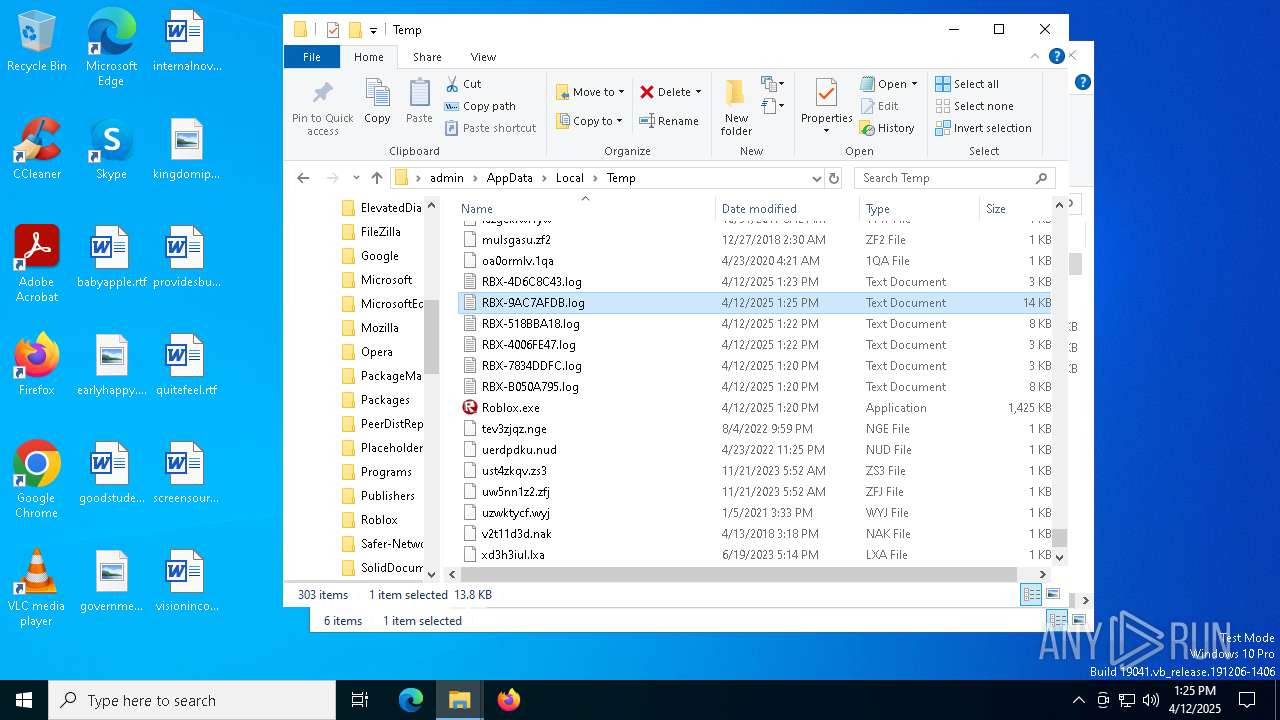
Create files in a temporary directory
- Roblox.exe (PID: 2284)
- Roblox.exe (PID: 7188)
- Roblox.exe (PID: 1452)
- Roblox.exe (PID: 7084)
- Roblox.exe (PID: 7496)
- Roblox.exe (PID: 7756)
Checks proxy server information
- Roblox.exe (PID: 2284)
- Roblox.exe (PID: 7188)
- Roblox.exe (PID: 1452)
- Roblox.exe (PID: 7084)
- slui.exe (PID: 1164)
- Roblox.exe (PID: 7756)
- Roblox.exe (PID: 7496)
Reads the machine GUID from the registry
- Roblox.exe (PID: 7188)
- Roblox.exe (PID: 1452)
- Roblox.exe (PID: 2284)
- Roblox.exe (PID: 7084)
- Roblox.exe (PID: 7496)
- Roblox.exe (PID: 7756)
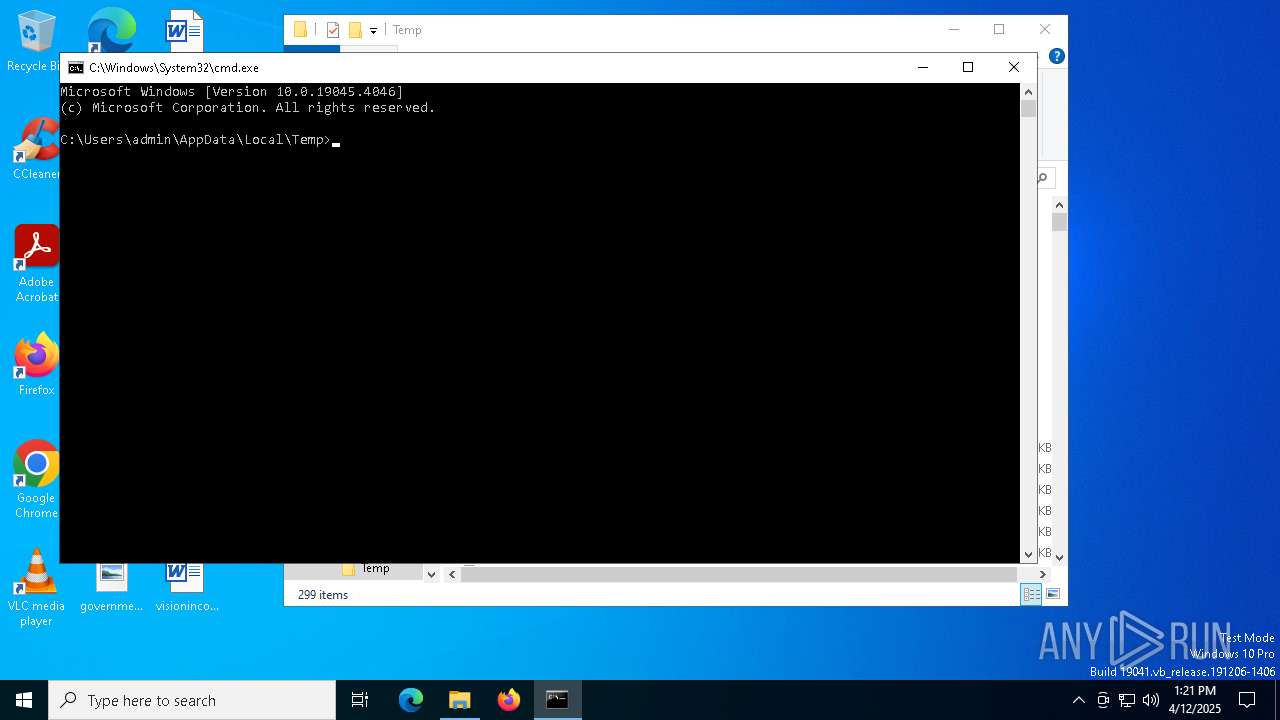
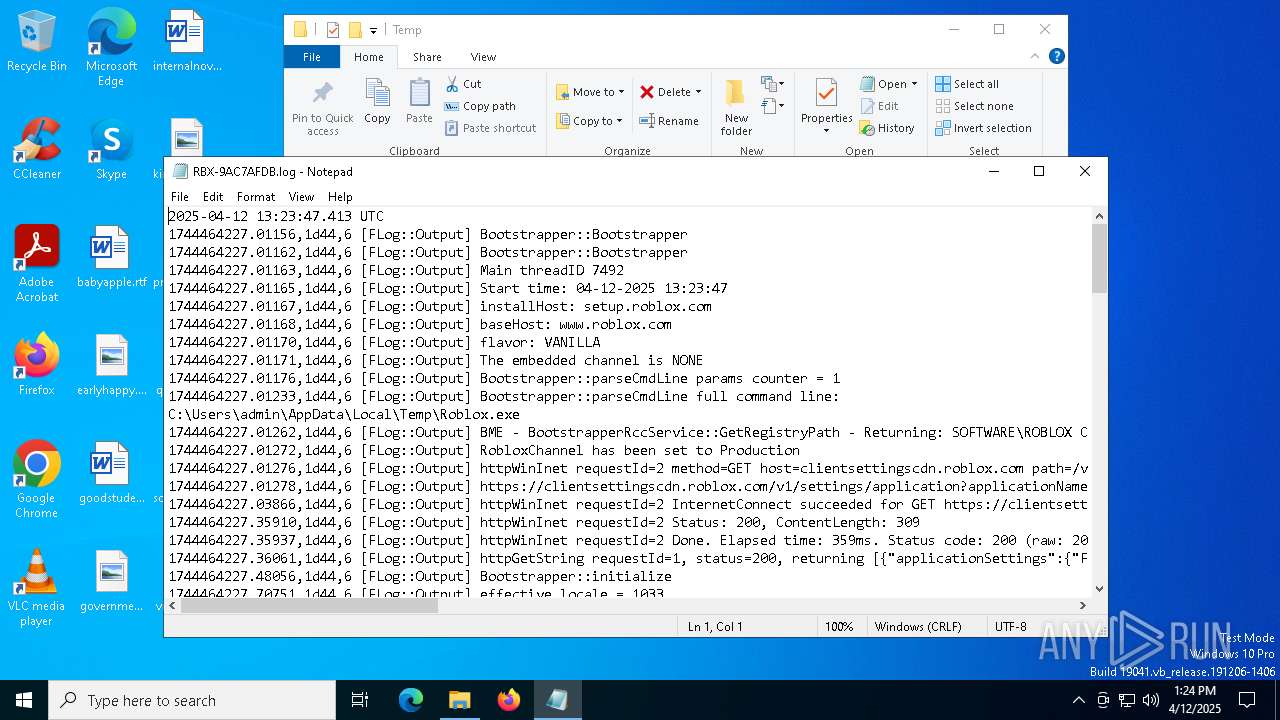
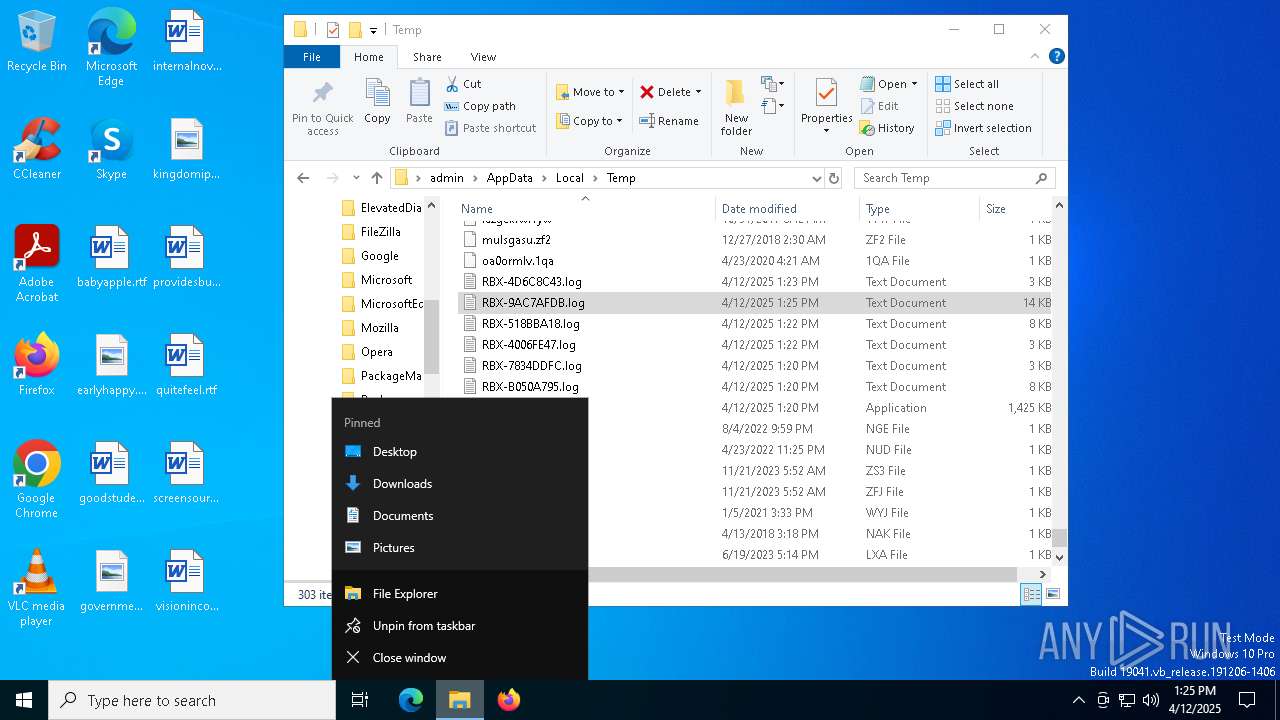
Manual execution by a user
- cmd.exe (PID: 6824)
- Roblox.exe (PID: 7496)
- notepad.exe (PID: 5156)
- notepad.exe (PID: 1388)
- notepad.exe (PID: 5228)
- notepad.exe (PID: 2552)
- notepad.exe (PID: 1128)
- notepad.exe (PID: 2644)
- cmd.exe (PID: 872)
Reads the software policy settings
- Roblox.exe (PID: 2284)
- slui.exe (PID: 7332)
- Roblox.exe (PID: 1452)
- slui.exe (PID: 1164)
- Roblox.exe (PID: 7496)
- Roblox.exe (PID: 7756)
Creates files or folders in the user directory
- Roblox.exe (PID: 2284)
- Roblox.exe (PID: 1452)
- Roblox.exe (PID: 7496)
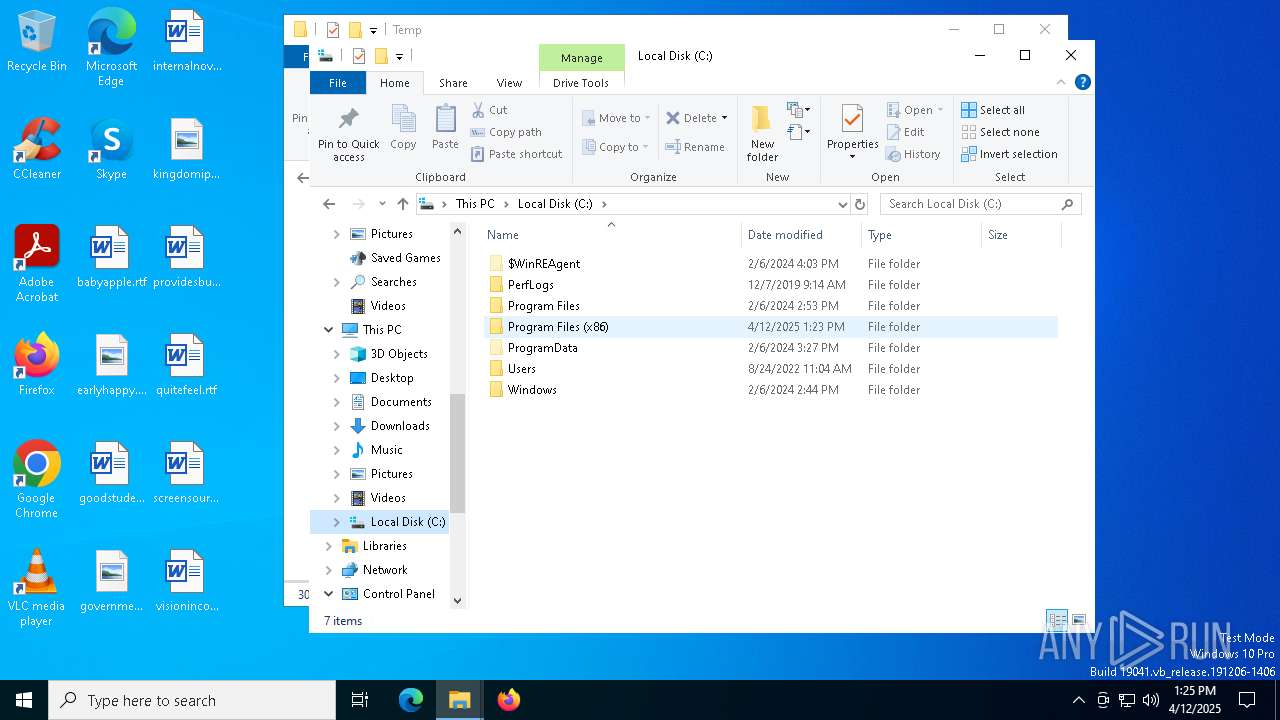
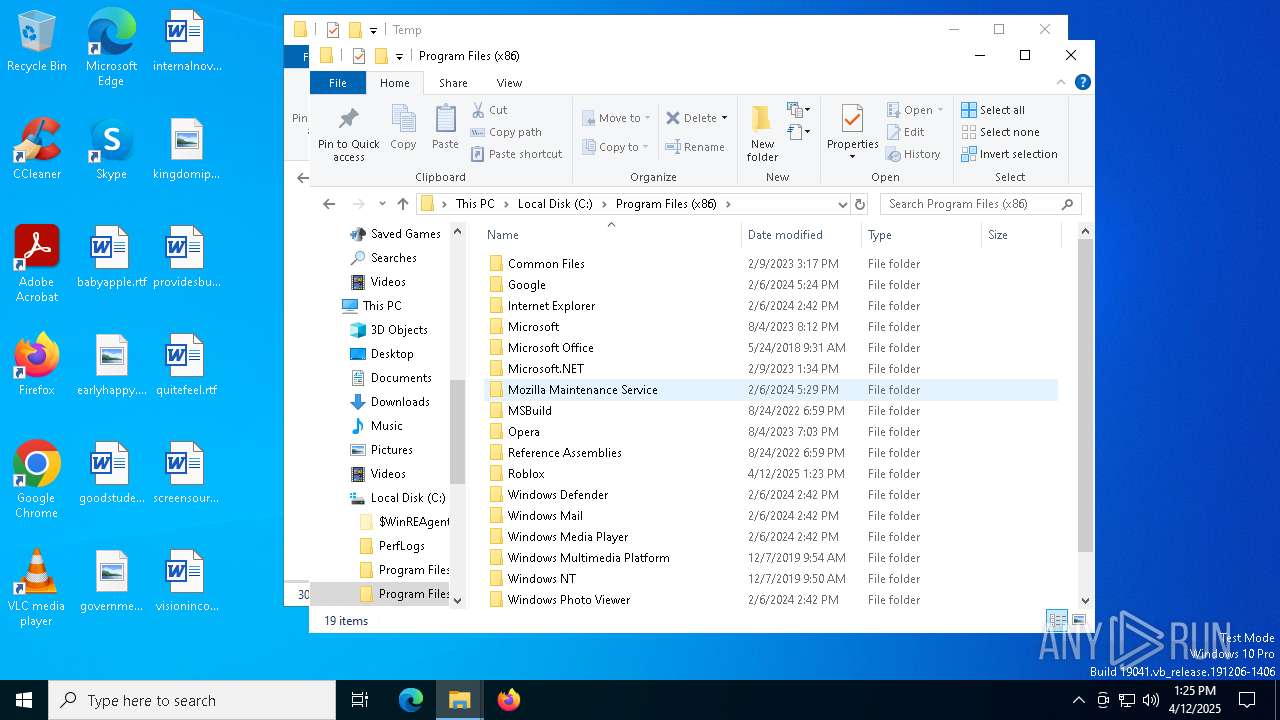
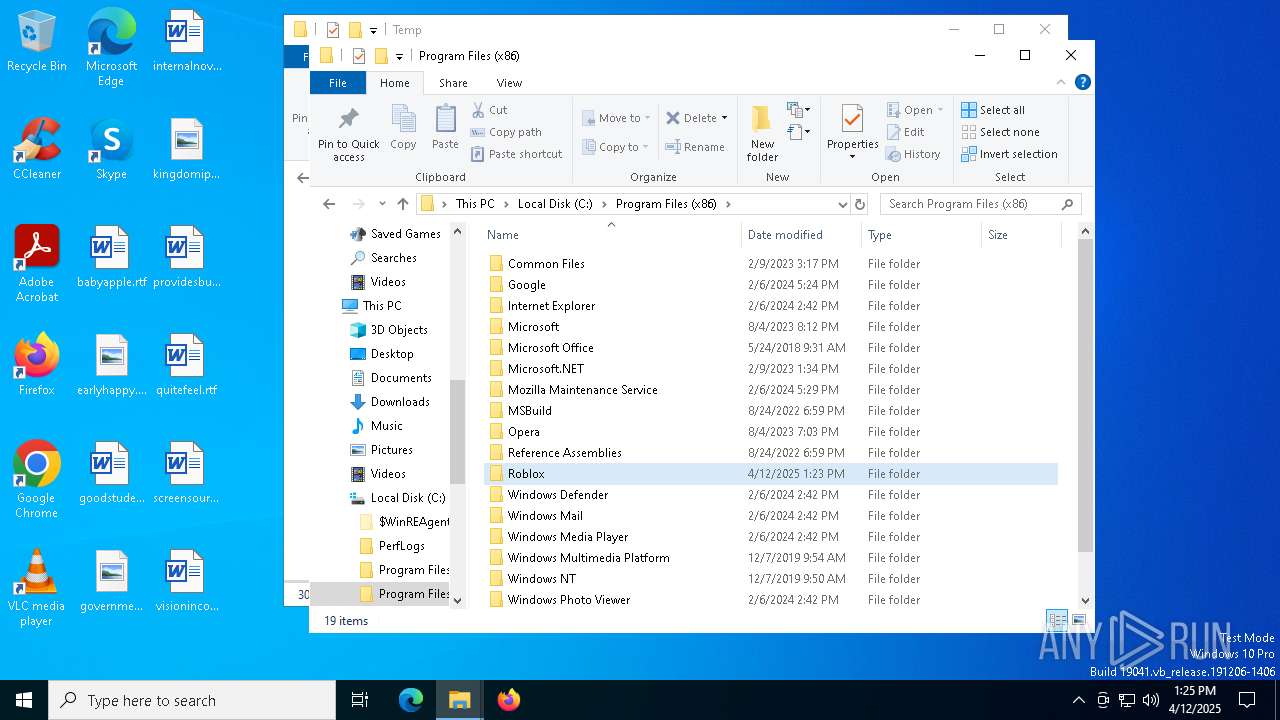
Creates files in the program directory
- Roblox.exe (PID: 7496)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:01:22 00:02:34+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.16 |
| CodeSize: | 1006592 |
| InitializedDataSize: | 444416 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xae2d5 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.6.0.23788 |
| ProductVersionNumber: | 1.6.0.23788 |
| FileFlagsMask: | 0x0017 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Roblox Corporation |
| FileDescription: | Roblox |
| FileVersion: | 1, 6, 0, 417004 |
| LegalCopyright: | Copyright © 2020 Roblox Corporation. All rights reserved. |
| OriginalFileName: | Roblox.exe |
| ProductName: | Roblox Bootstrapper |
| ProductVersion: | 1, 6, 0, 417004 |
Total processes
158
Monitored processes
22
Malicious processes
3
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 872 | "C:\Windows\System32\cmd.exe" | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
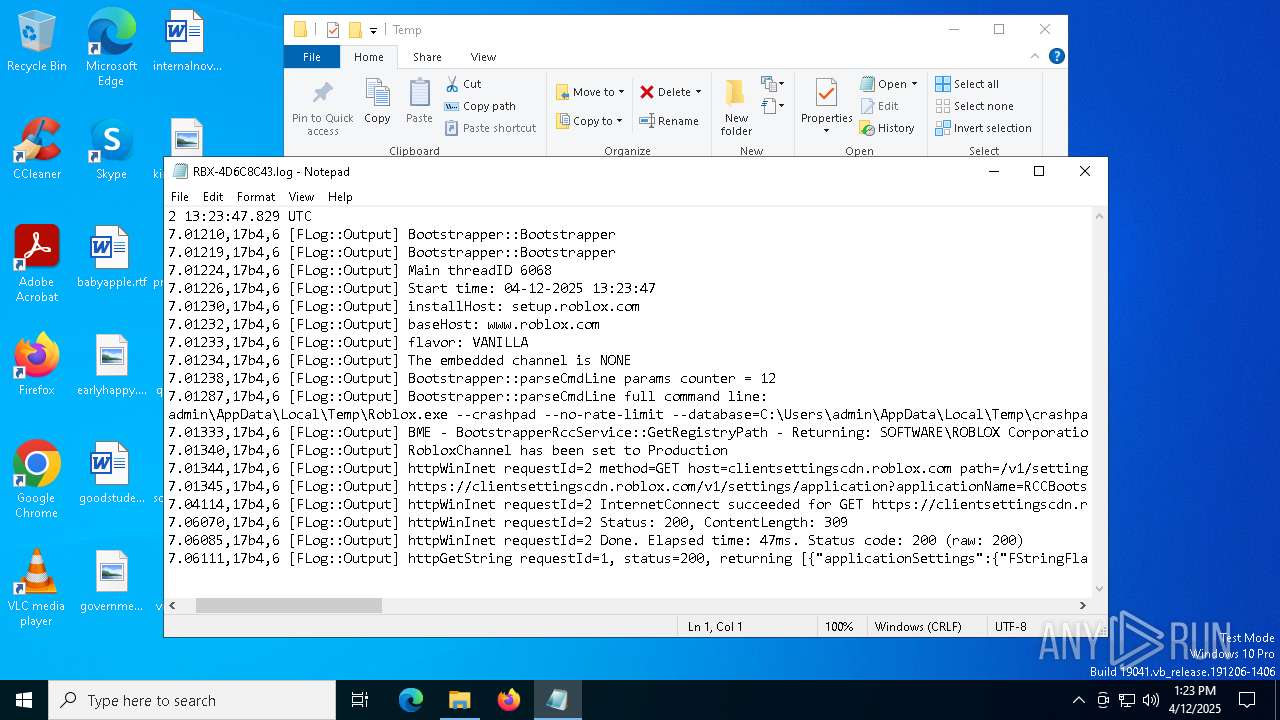
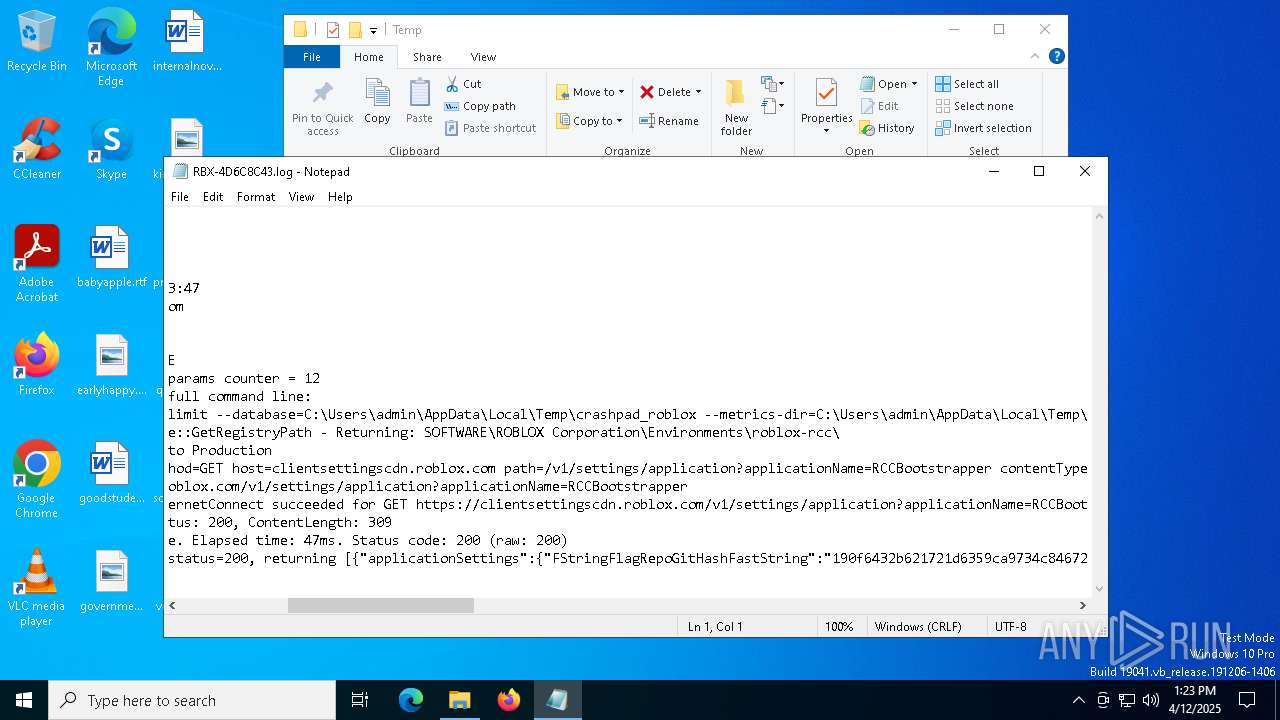
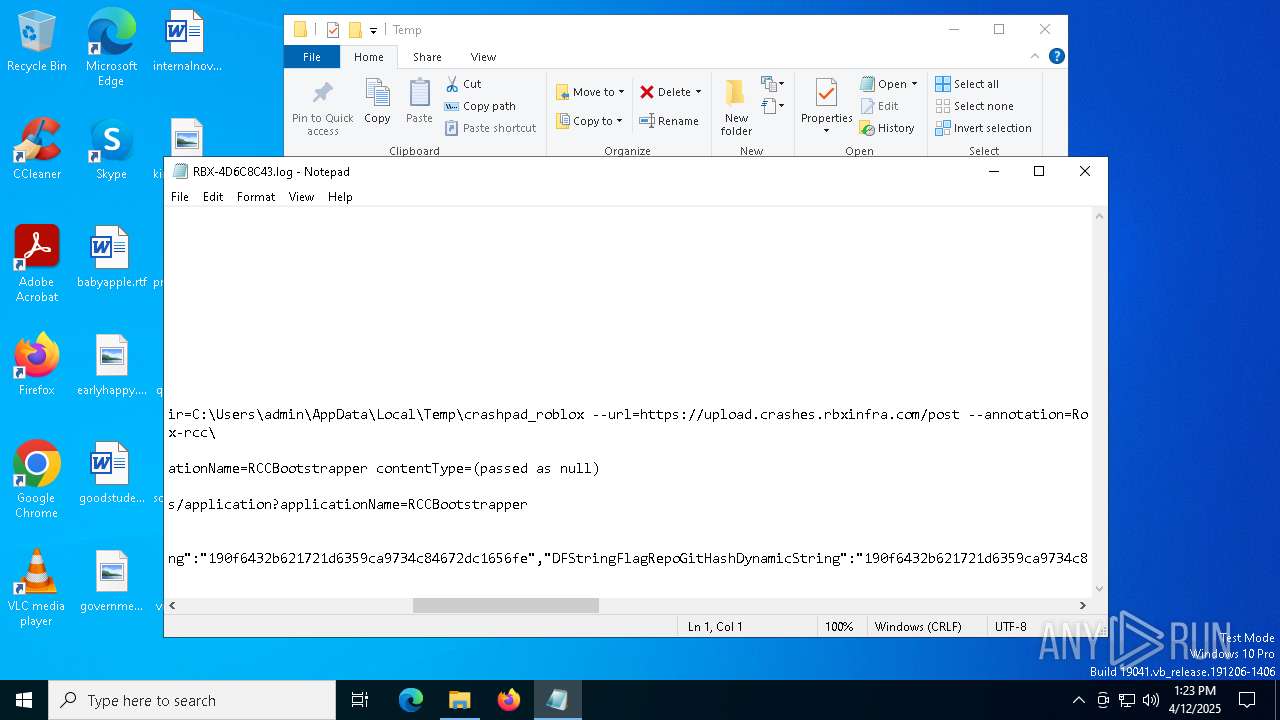
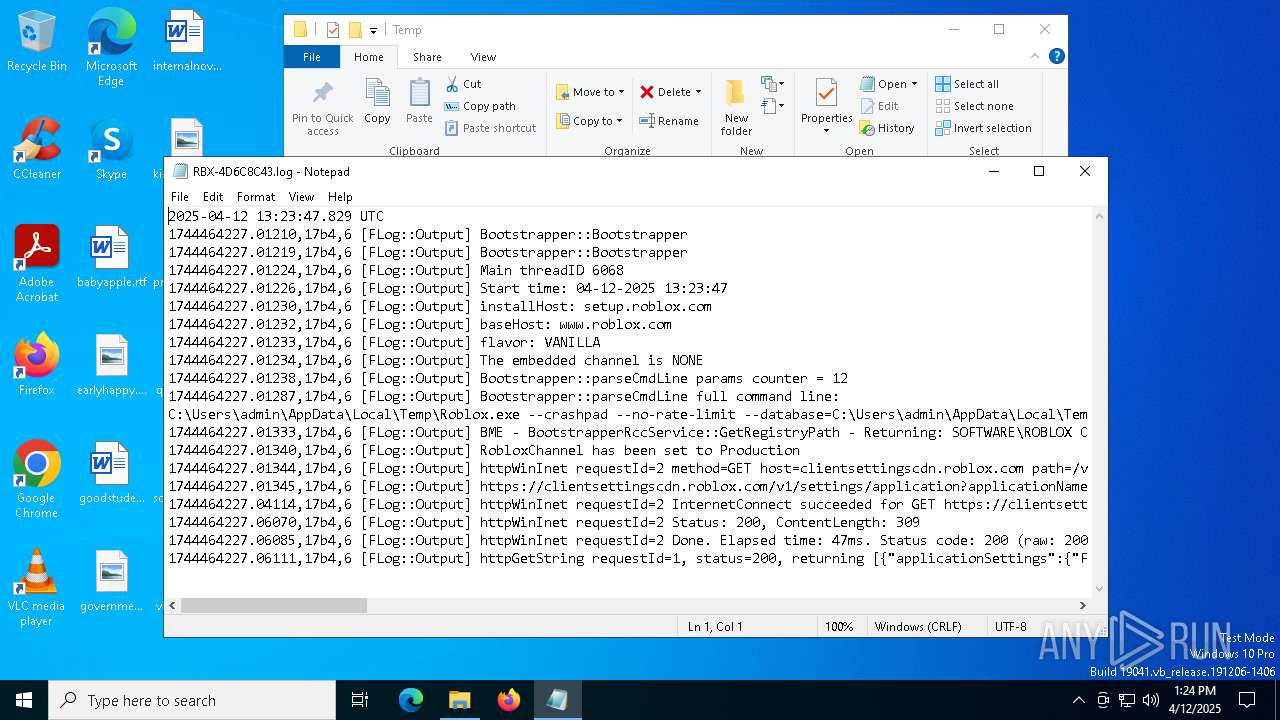
| 1128 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\Temp\RBX-4D6C8C43.log | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1164 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1388 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\Temp\RBX-4D6C8C43.log | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
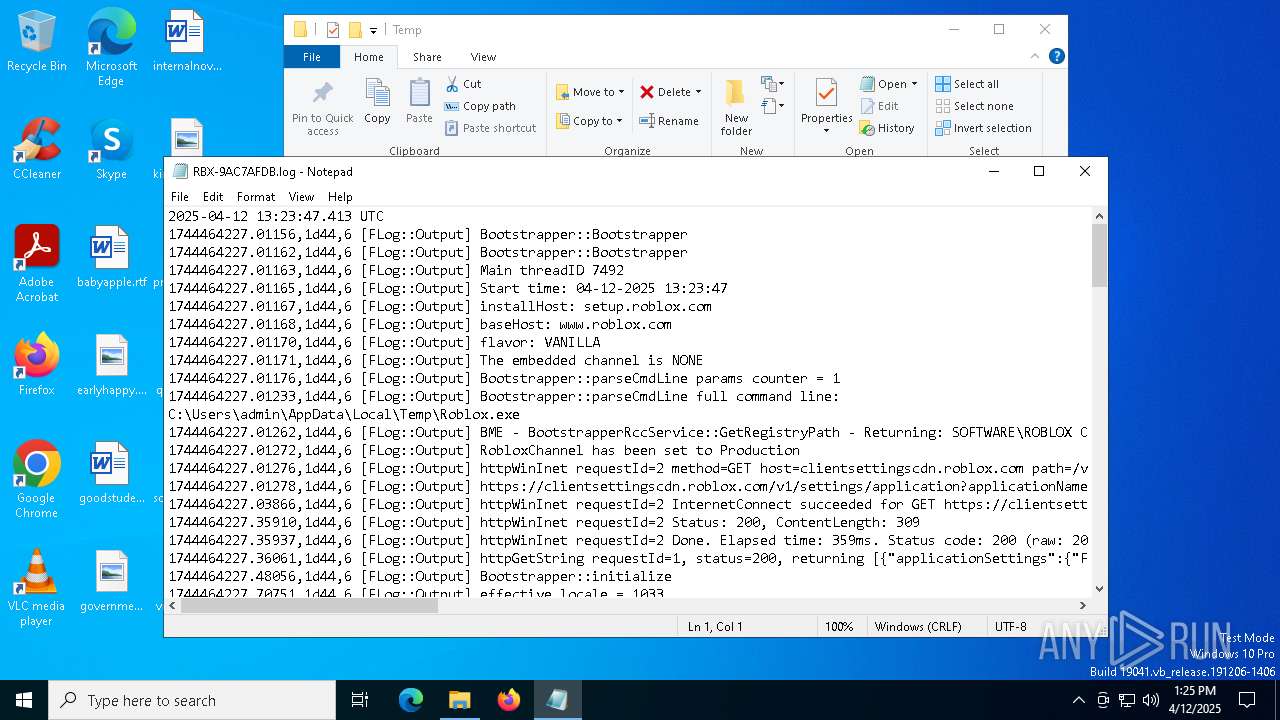
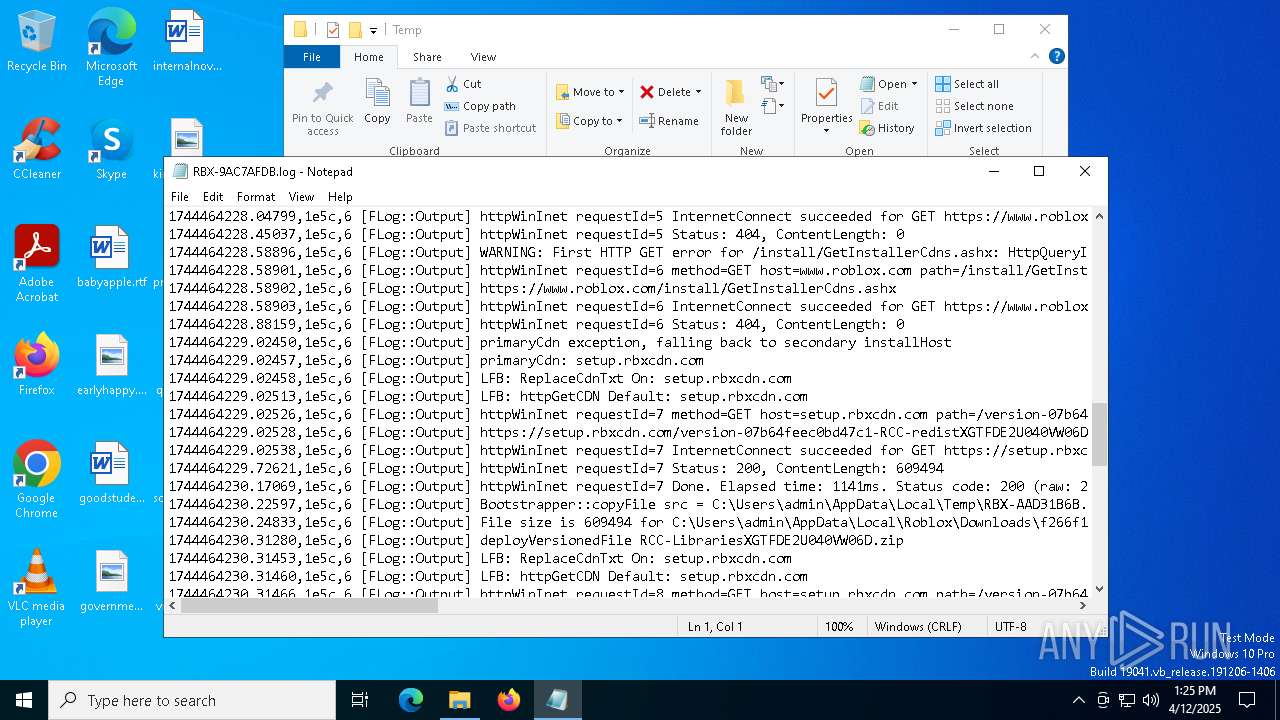
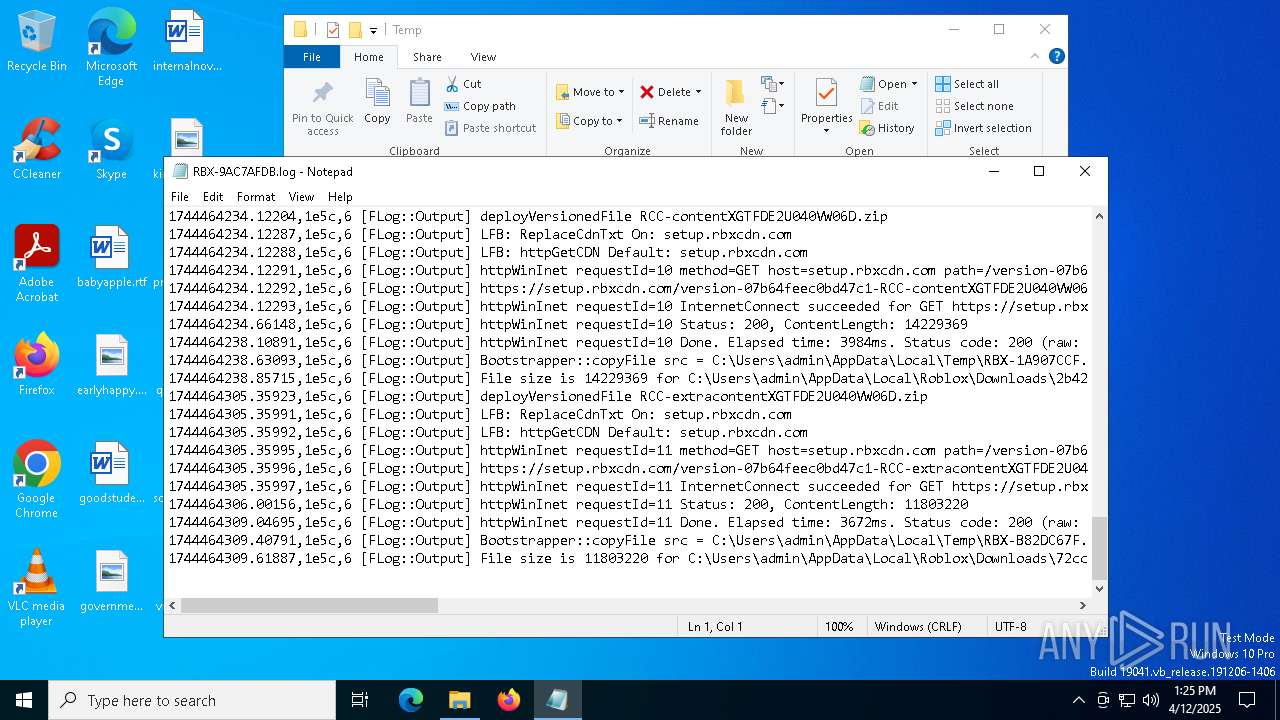
| 1452 | Roblox.exe -debug | C:\Users\admin\AppData\Local\Temp\Roblox.exe | cmd.exe | ||||||||||||
User: admin Company: Roblox Corporation Integrity Level: MEDIUM Description: Roblox Exit code: 4294967295 Version: 1, 6, 0, 417004 Modules
| |||||||||||||||
| 2284 | "C:\Users\admin\AppData\Local\Temp\Roblox.exe" | C:\Users\admin\AppData\Local\Temp\Roblox.exe | explorer.exe | ||||||||||||
User: admin Company: Roblox Corporation Integrity Level: MEDIUM Description: Roblox Exit code: 4294967295 Version: 1, 6, 0, 417004 Modules
| |||||||||||||||
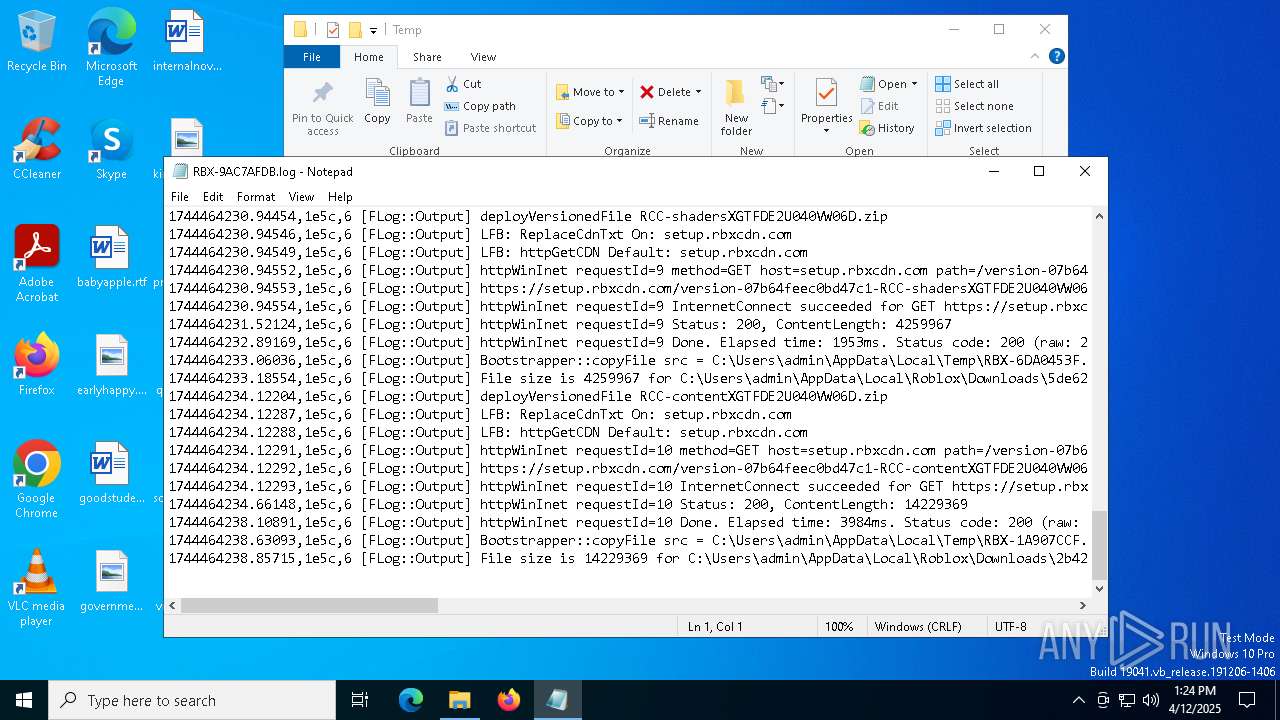
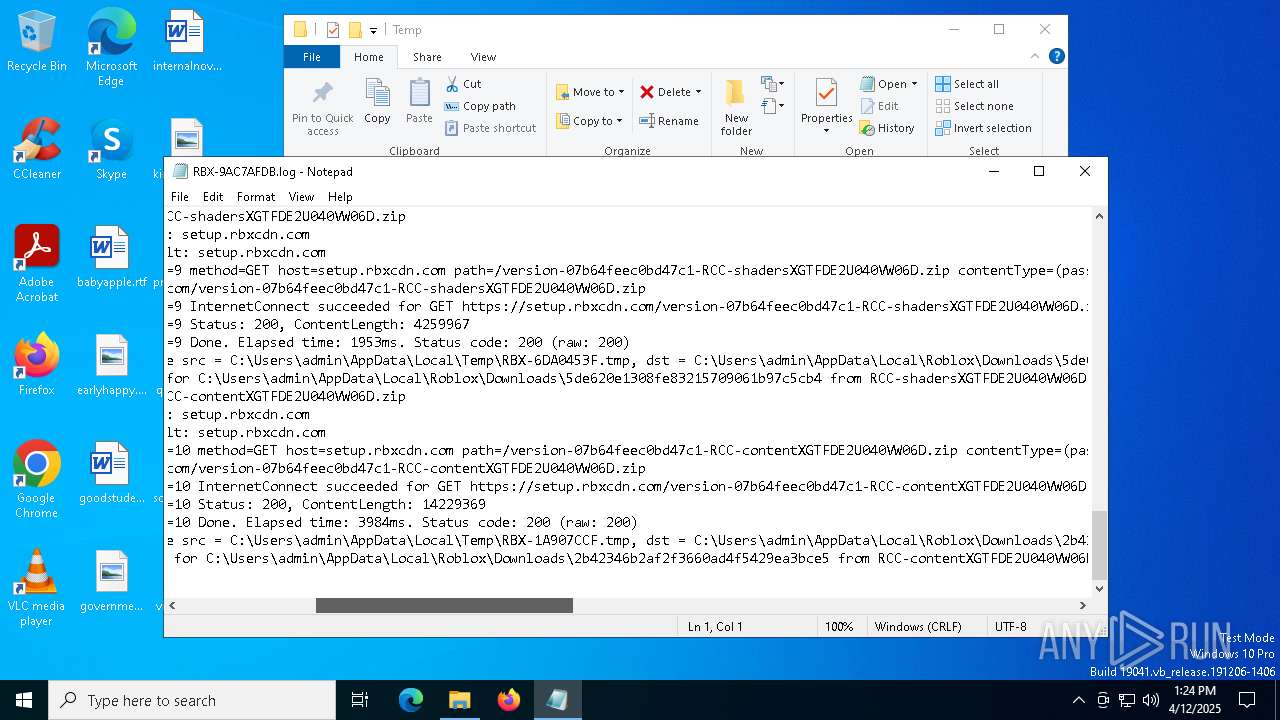
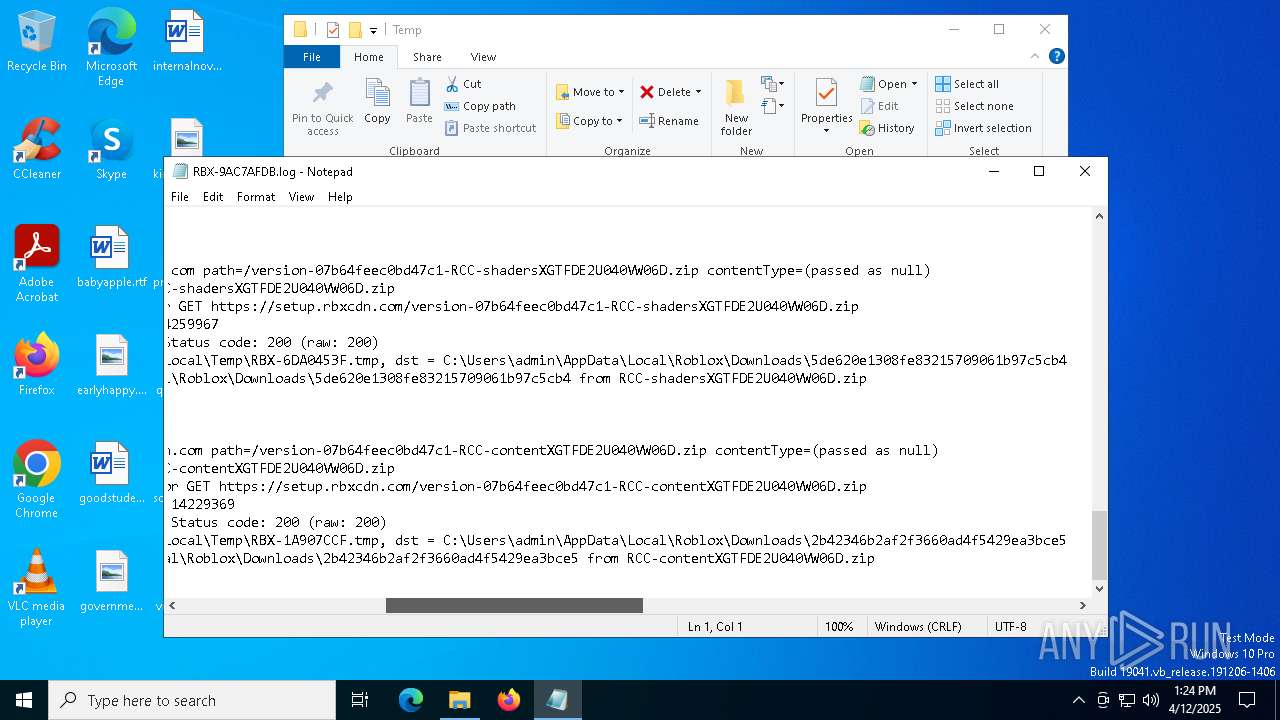
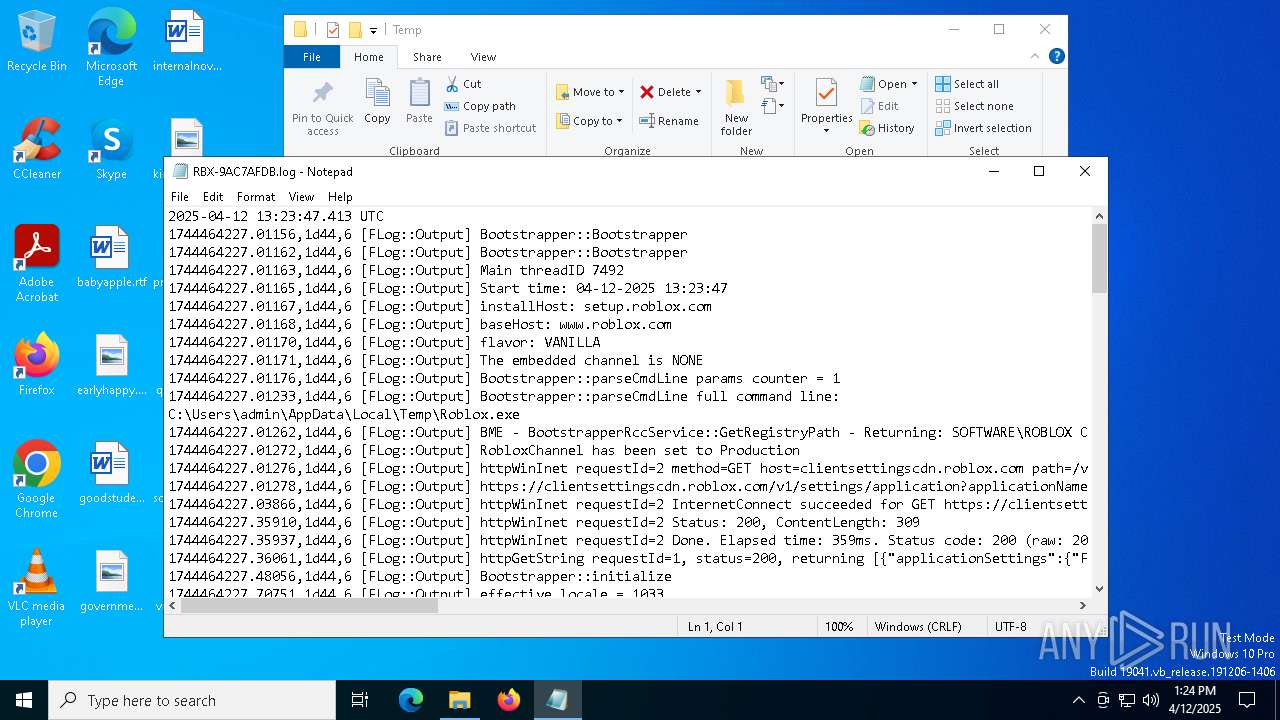
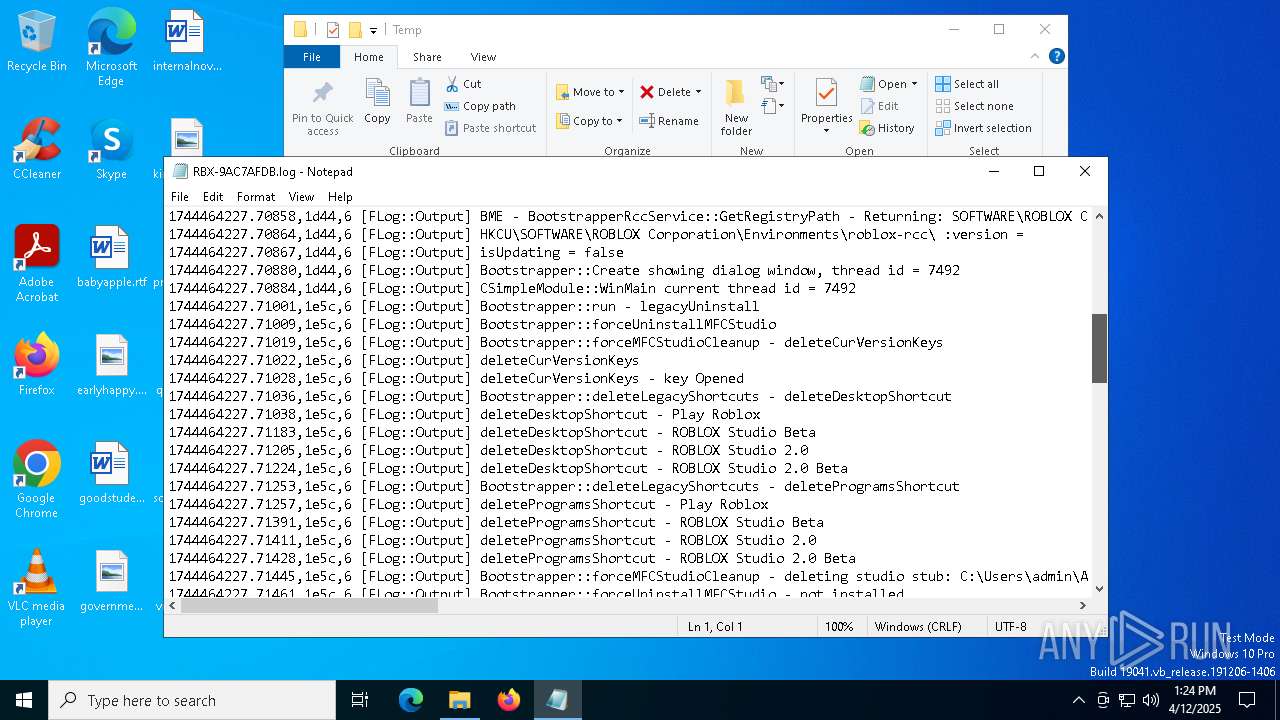
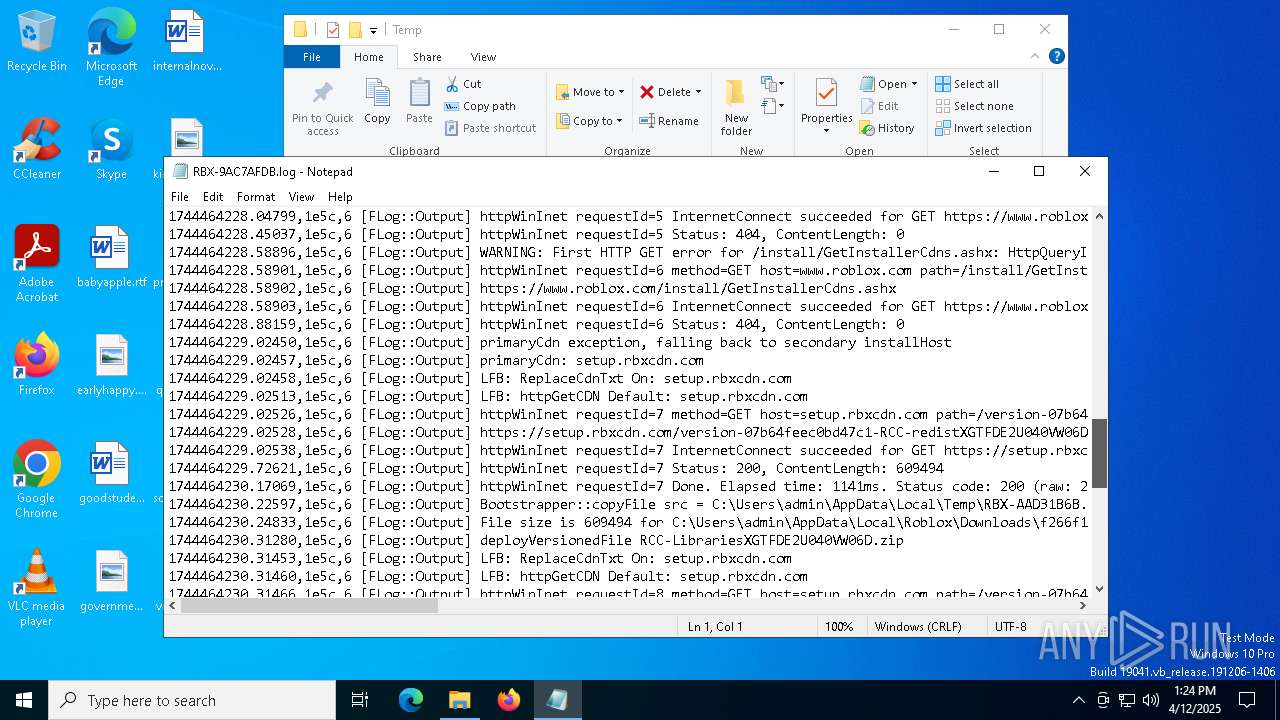
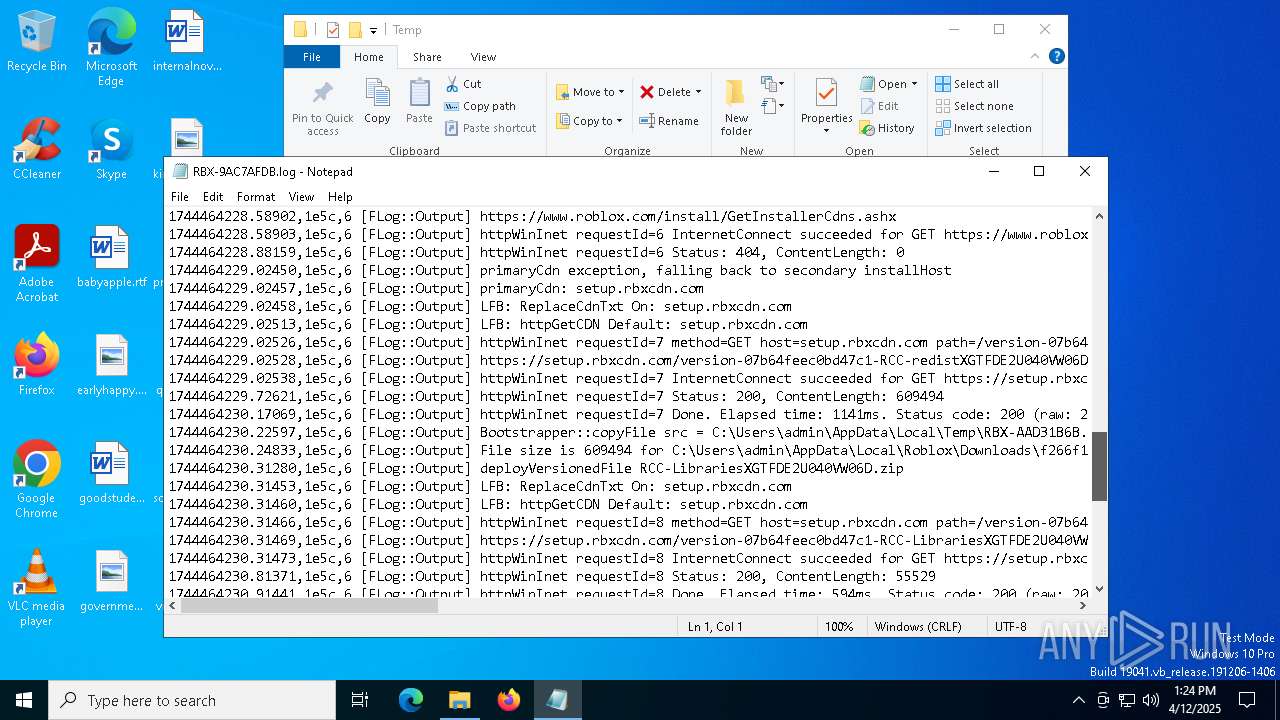
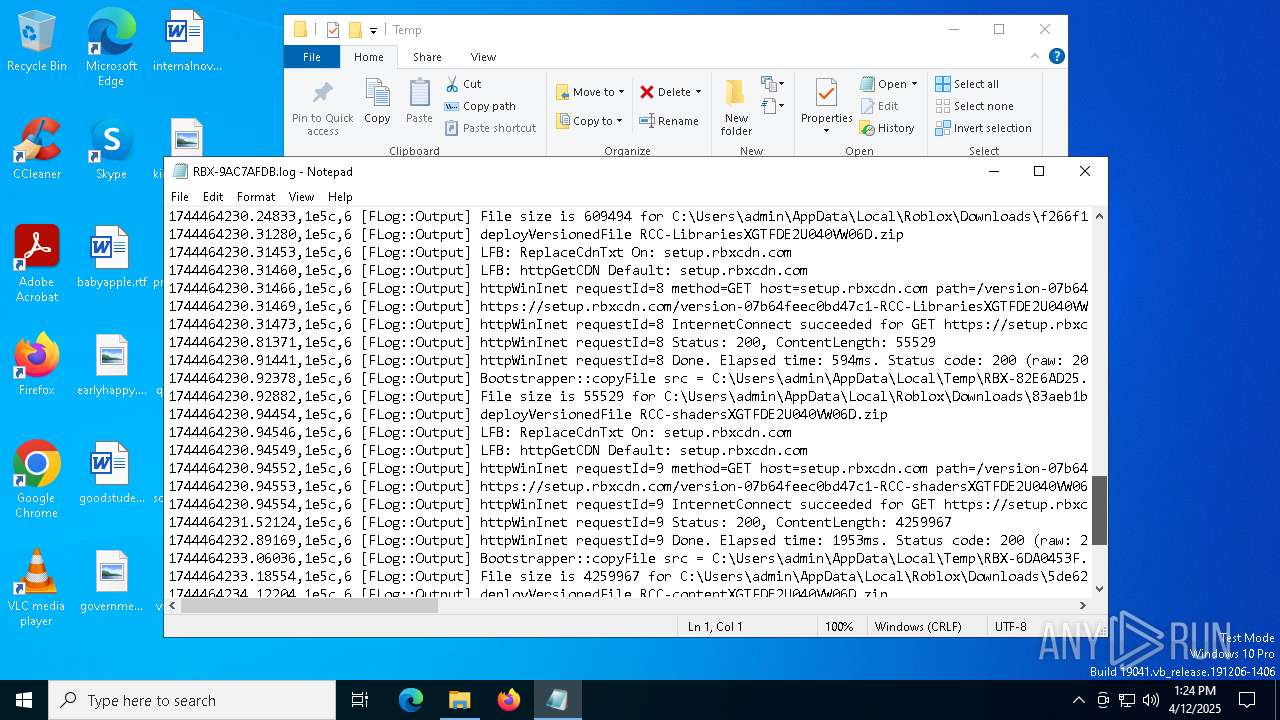
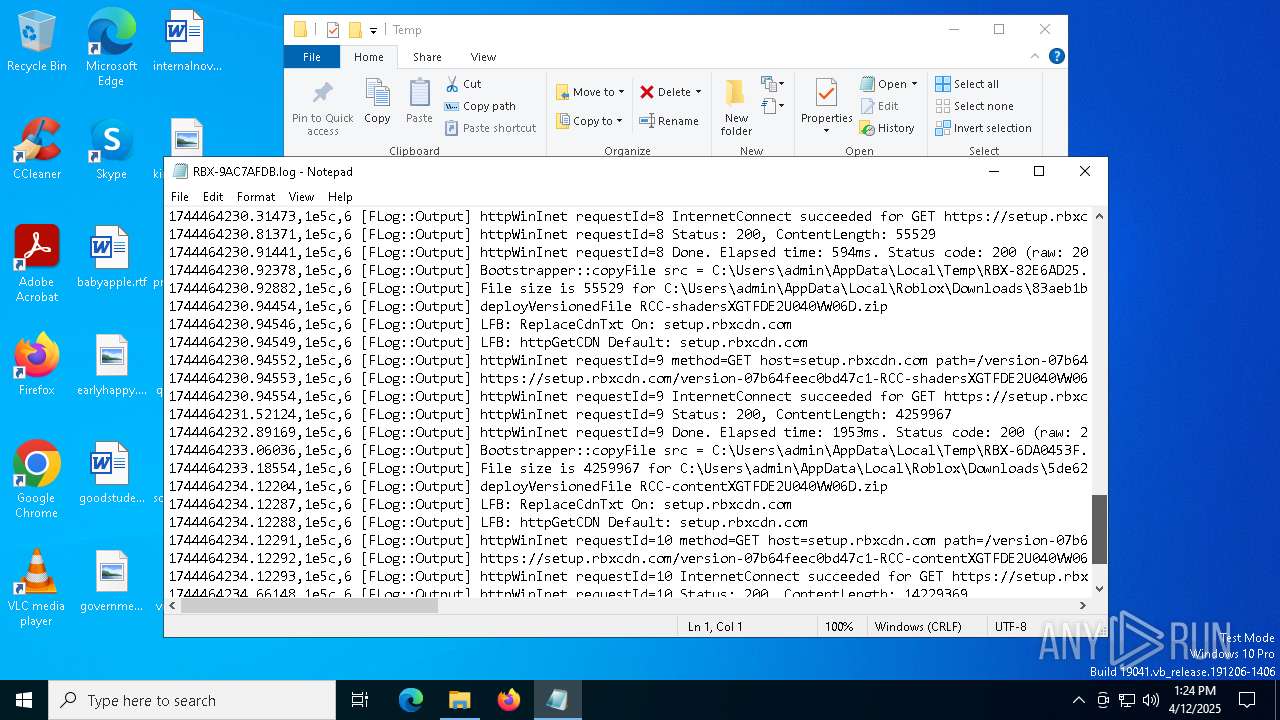
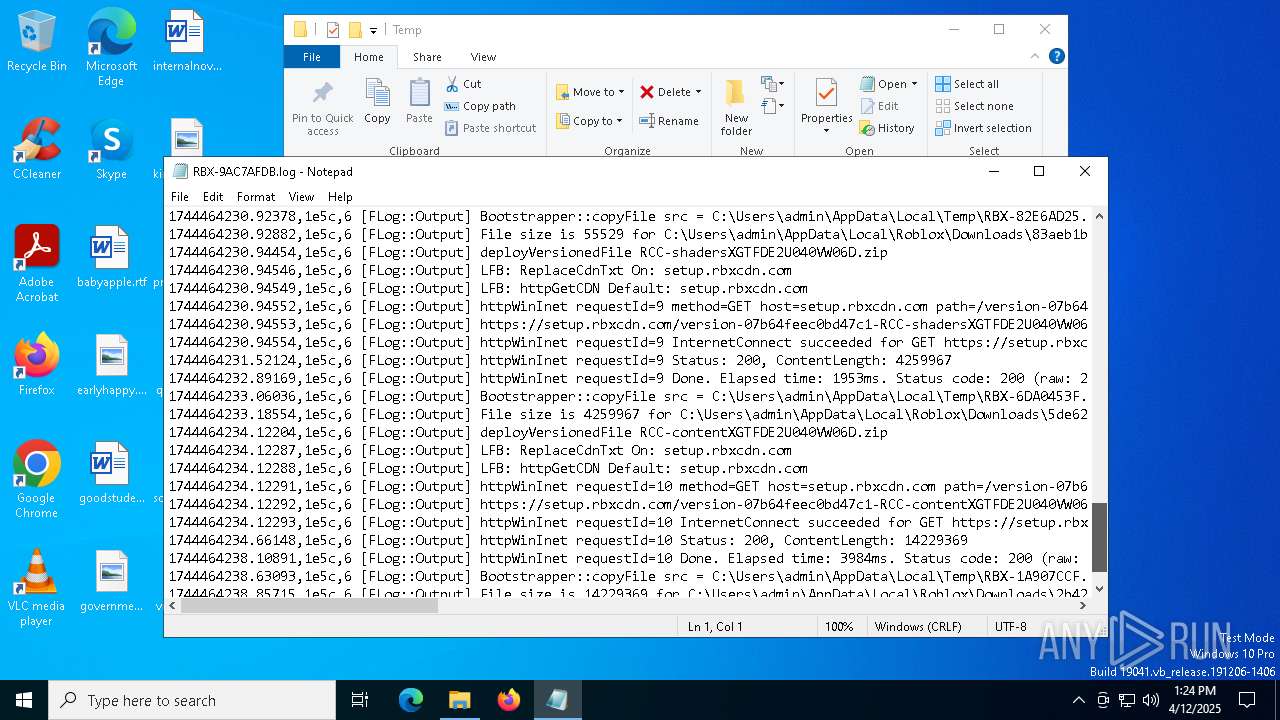
| 2552 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\Temp\RBX-9AC7AFDB.log | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2644 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\Temp\RBX-9AC7AFDB.log | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4172 | "C:\WINDOWS\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe" -ServerName:App.AppXtk181tbxbce2qsex02s8tw7hfxa9xb3t.mca | C:\Windows\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Shell Experience Host Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4244 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
6 124
Read events
6 083
Write events
35
Delete events
6
Modification events
| (PID) Process: | (2284) Roblox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2284) Roblox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2284) Roblox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2284) Roblox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\ROBLOX Corporation\Roblox |
| Operation: | write | Name: | CPath |
Value: C:\Users\admin\AppData\LocalLow\rbxcsettings.rbx | |||
| (PID) Process: | (2284) Roblox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\ROBLOX Corporation\Environments |
| Operation: | delete value | Name: | curStudioVer |
Value: | |||
| (PID) Process: | (2284) Roblox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\ROBLOX Corporation\Environments |
| Operation: | delete value | Name: | curStudioUrl |
Value: | |||
| (PID) Process: | (2284) Roblox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\RobloxReg\ETags |
| Operation: | write | Name: | RCC-redistXGTFDE2U040VW06D.zip |
Value: | |||
| (PID) Process: | (2284) Roblox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\RobloxReg\ETags |
| Operation: | write | Name: | RCC-LibrariesXGTFDE2U040VW06D.zip |
Value: | |||
| (PID) Process: | (2284) Roblox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\RobloxReg\ETags |
| Operation: | write | Name: | RCC-shadersXGTFDE2U040VW06D.zip |
Value: | |||
| (PID) Process: | (2284) Roblox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\RobloxReg\ETags |
| Operation: | write | Name: | RCC-contentXGTFDE2U040VW06D.zip |
Value: | |||
Executable files
3
Suspicious files
372
Text files
2 126
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2284 | Roblox.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | binary | |
MD5:6EC34697B5E535625F4287F4AB99F0BC | SHA256:E8E0345E65F69786EA3D8A11A1AF4A8F02AF567A0B6953CFAE578636764C1081 | |||
| 7496 | Roblox.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\72BA427A91F50409B9EAC87F2B59B951_4AB5D5FF0B7710A9A4DE10A70092573B | binary | |
MD5:DA839BB55F72D26463690AA642352CDA | SHA256:BB8C819A812FB1812A83BD2D86D4B87C29E49A3E5BAD154635521194EF4DC334 | |||
| 2284 | Roblox.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | binary | |
MD5:30BA57DA02913F189236C15C51663E85 | SHA256:986265D92021B9E634BF9CC46802486BBEFC0A2DB96036633EEF256DE487D822 | |||
| 2284 | Roblox.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\RR3E01RZ\application[1].json | binary | |
MD5:D5B60635B3C3010F84CCFA0E22B81C29 | SHA256:89AB4CD6F35C64231E94D567EB2664315644AA7E670D452ED95F46E512607BCB | |||
| 1452 | Roblox.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\E4DJRUXW\GetCurrentClientVersionUpload[1].json | text | |
MD5:54963F91EE62707C89C6EB14056289FE | SHA256:F199BF62530758A88C74A6FF25BAC3B9E84AC530992542EEF3628CEBB9BFF014 | |||
| 7496 | Roblox.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\72BA427A91F50409B9EAC87F2B59B951_9A56D42A09C1372383E1C30886BED5F2 | binary | |
MD5:B68DC0F6AFFE905CB169D6B2561920F2 | SHA256:B367F381DABDF7E73225032581EE4A6C4D6770304810376DE76D3C1B38B2AF79 | |||
| 2284 | Roblox.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\07CEF2F654E3ED6050FFC9B6EB844250_BACC6CD2B29F18349081C9FD2343833B | binary | |
MD5:9F0CCB453257DA53C862F8B6E34FB3A5 | SHA256:E8136BB51FC1BC420B4918123A8FF88AE8889A6165169A3972ACFCD0A65915EC | |||
| 1452 | Roblox.exe | C:\Users\admin\AppData\Local\Temp\RBX-518BBA18.log | text | |
MD5:4754F400DC13DA24A261D78815933CB3 | SHA256:A361A29DC025F1EDE03FEF2E4127DC7C944CE5EAA1F5C3392C1A01AADB177C7B | |||
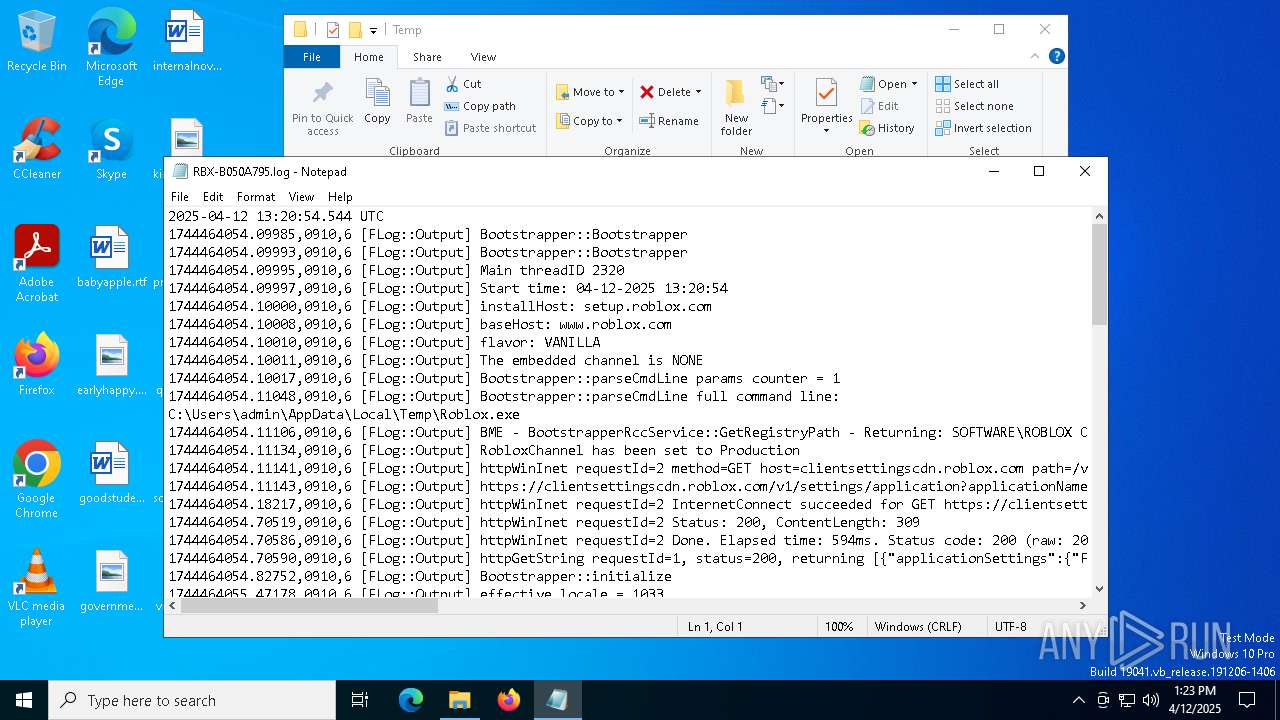
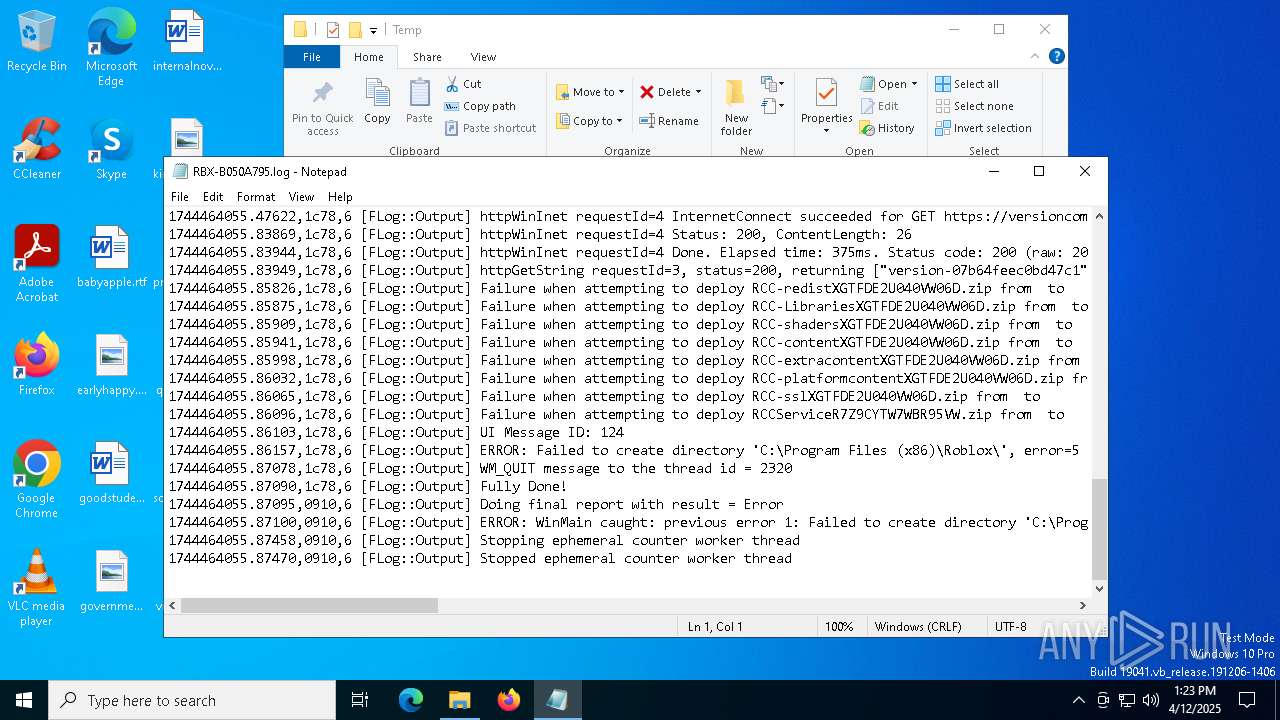
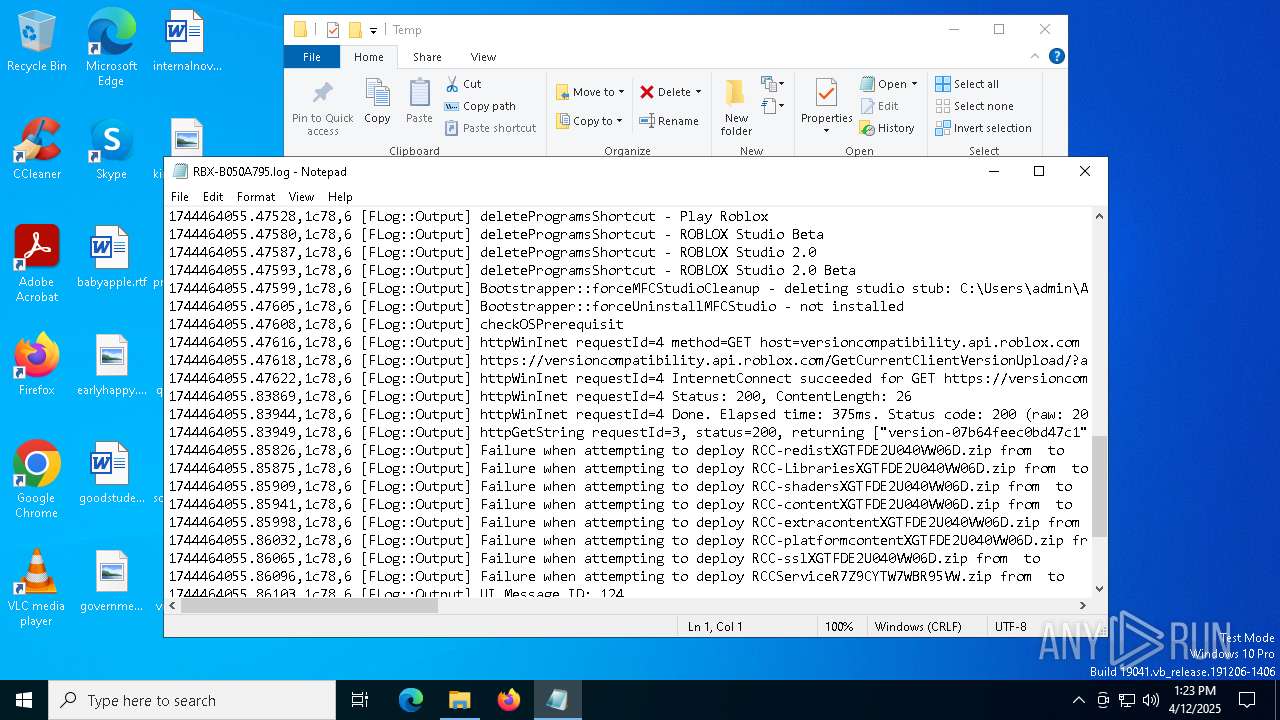
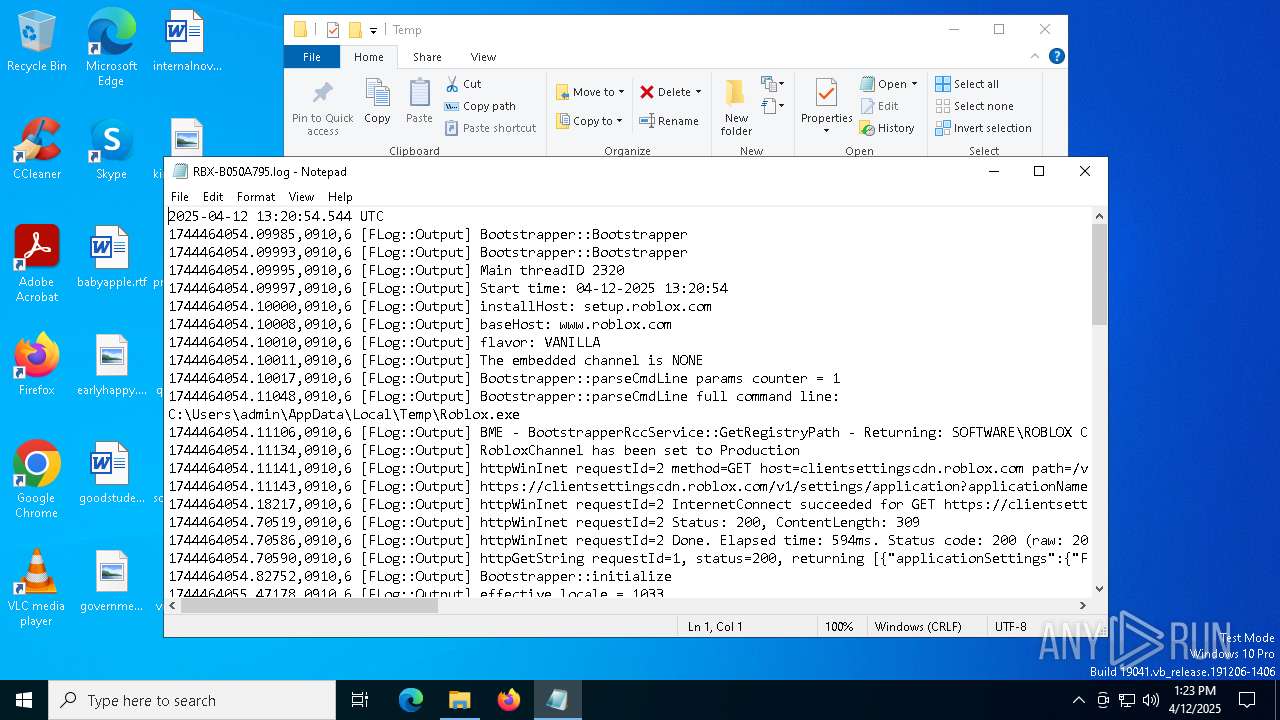
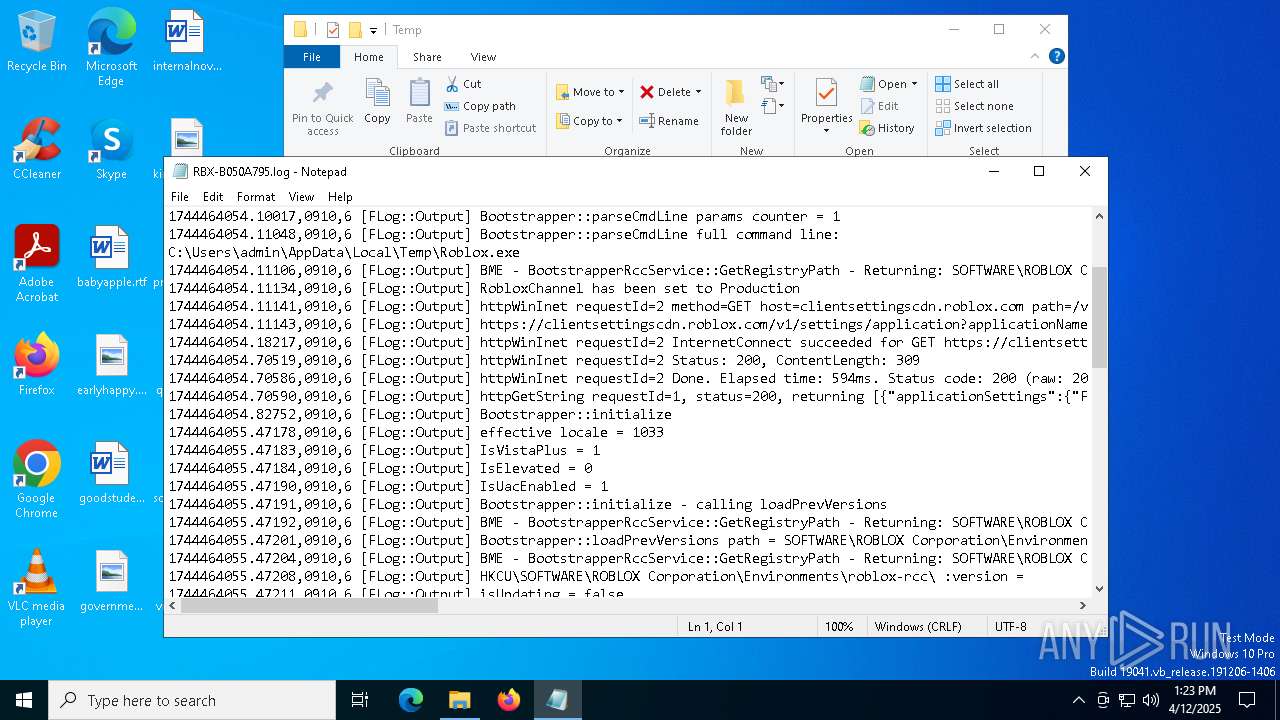
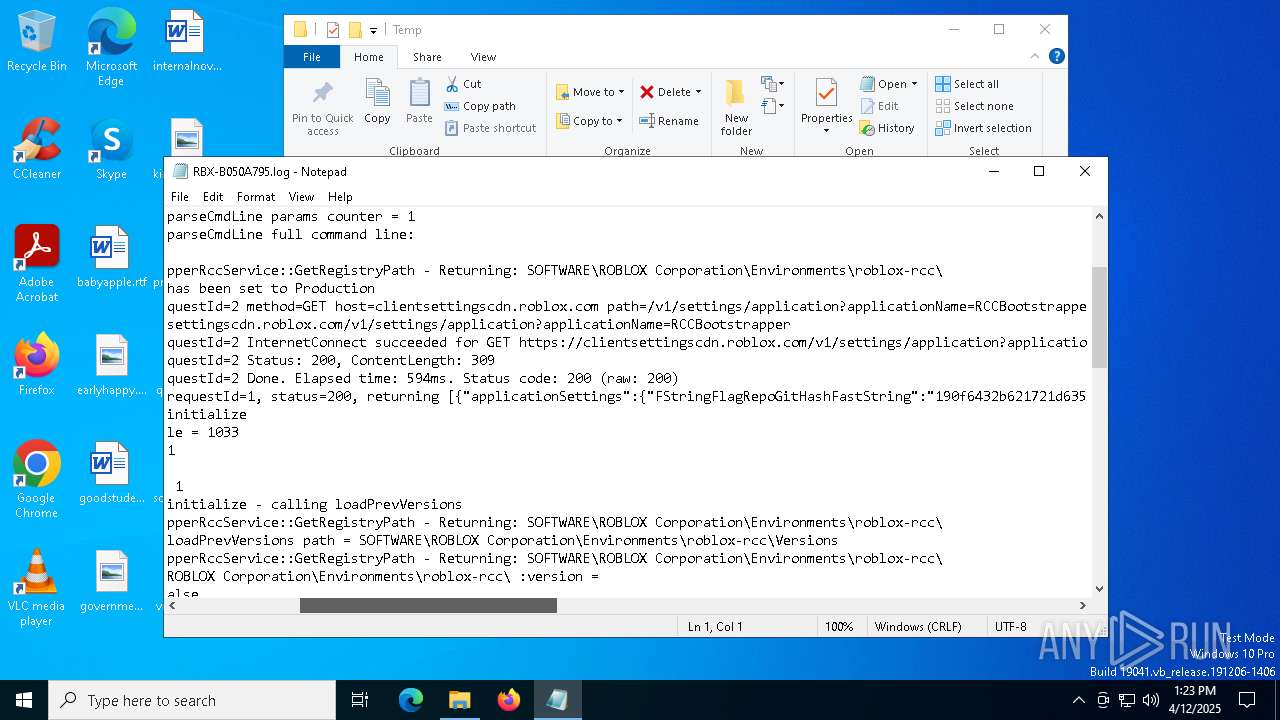
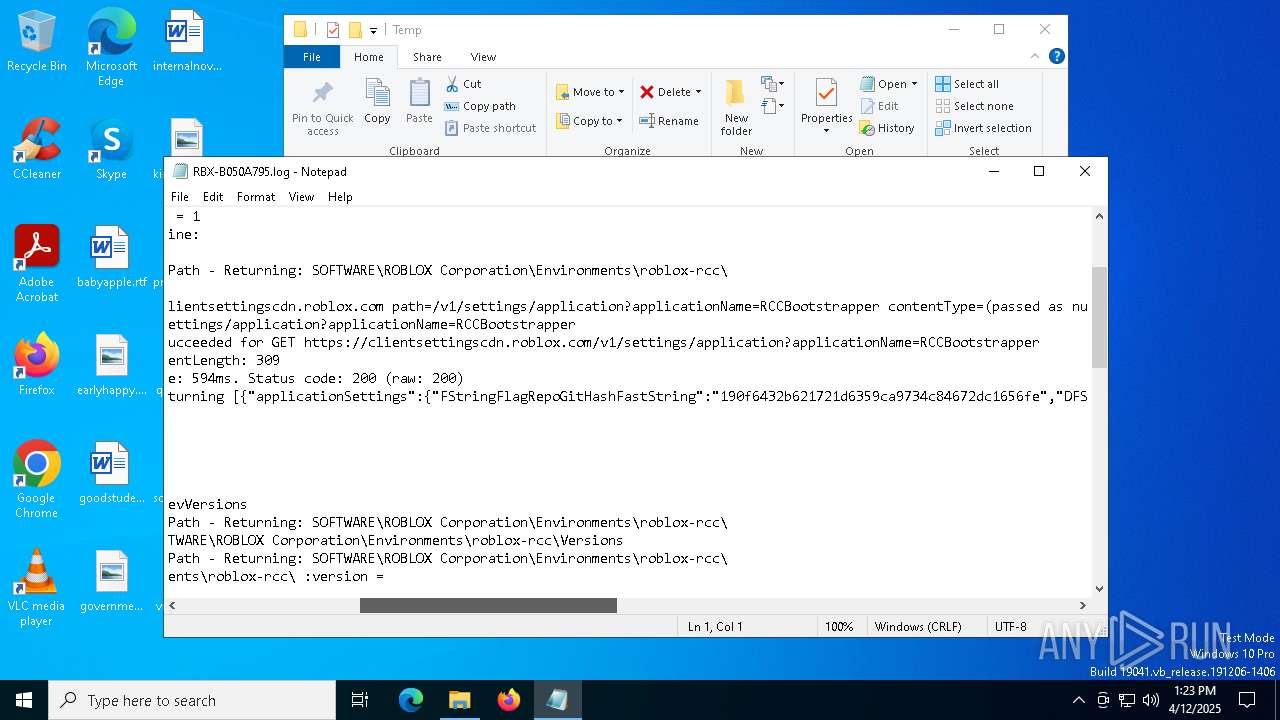
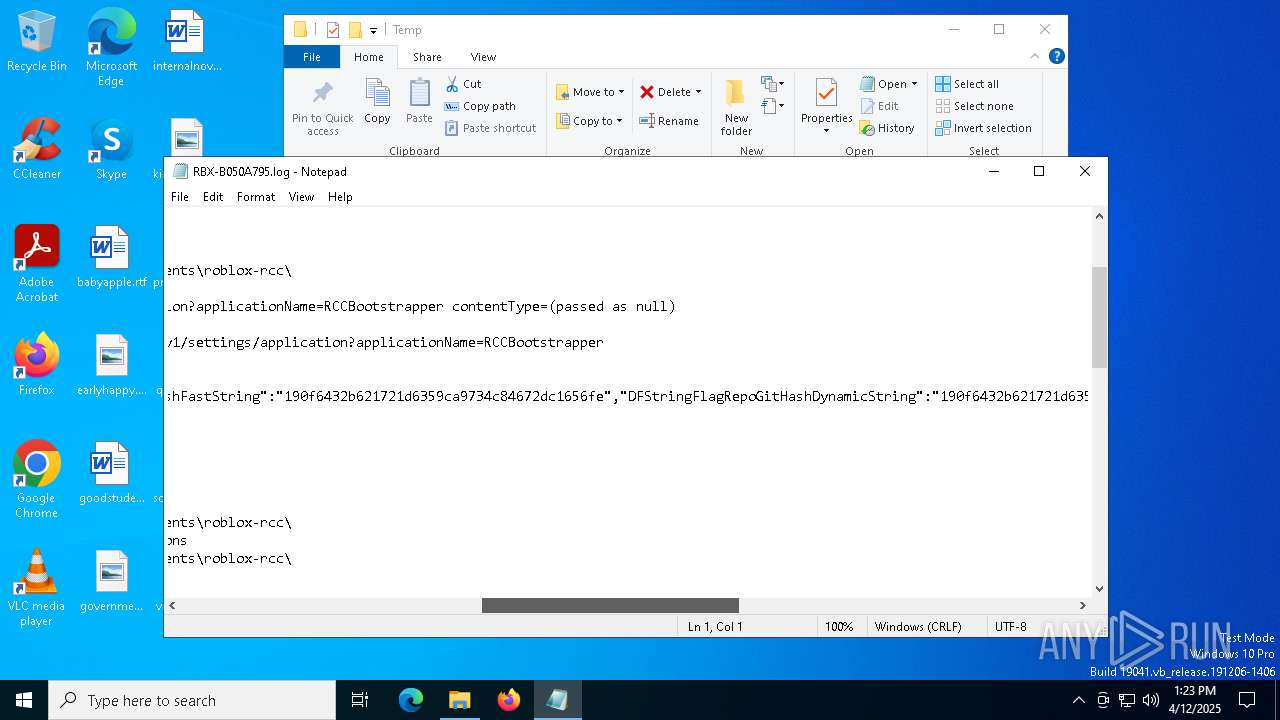
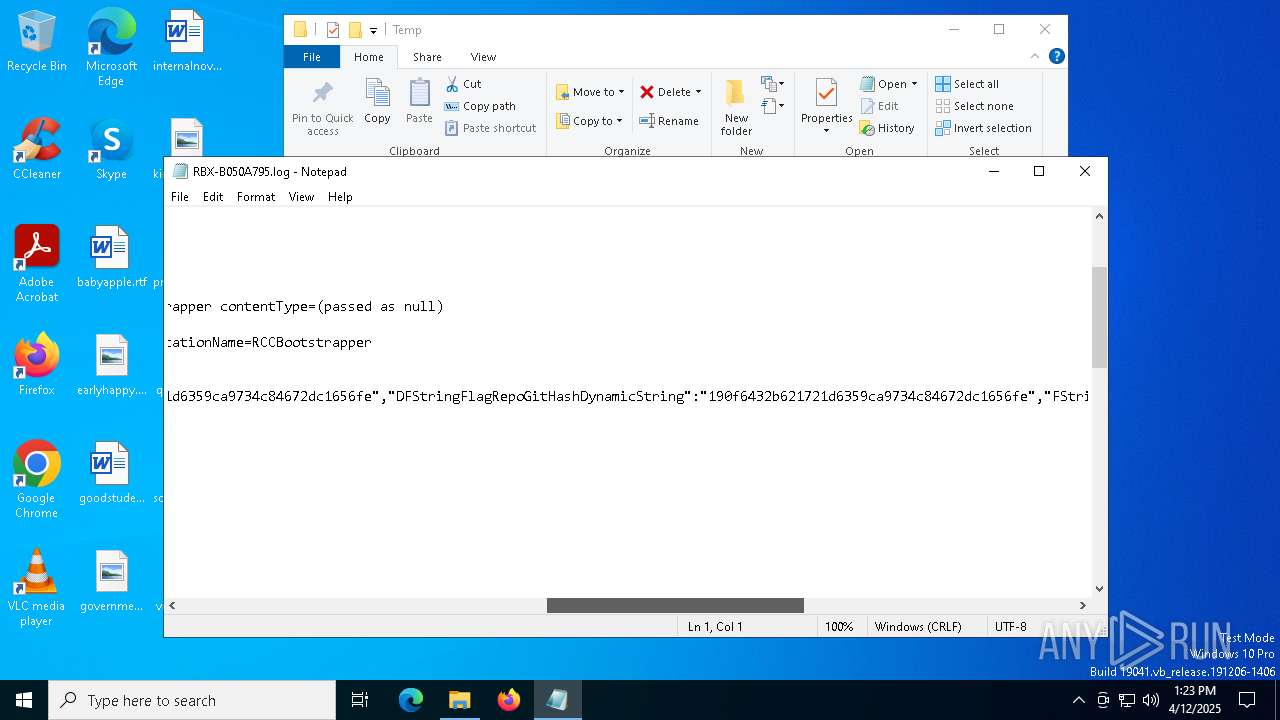
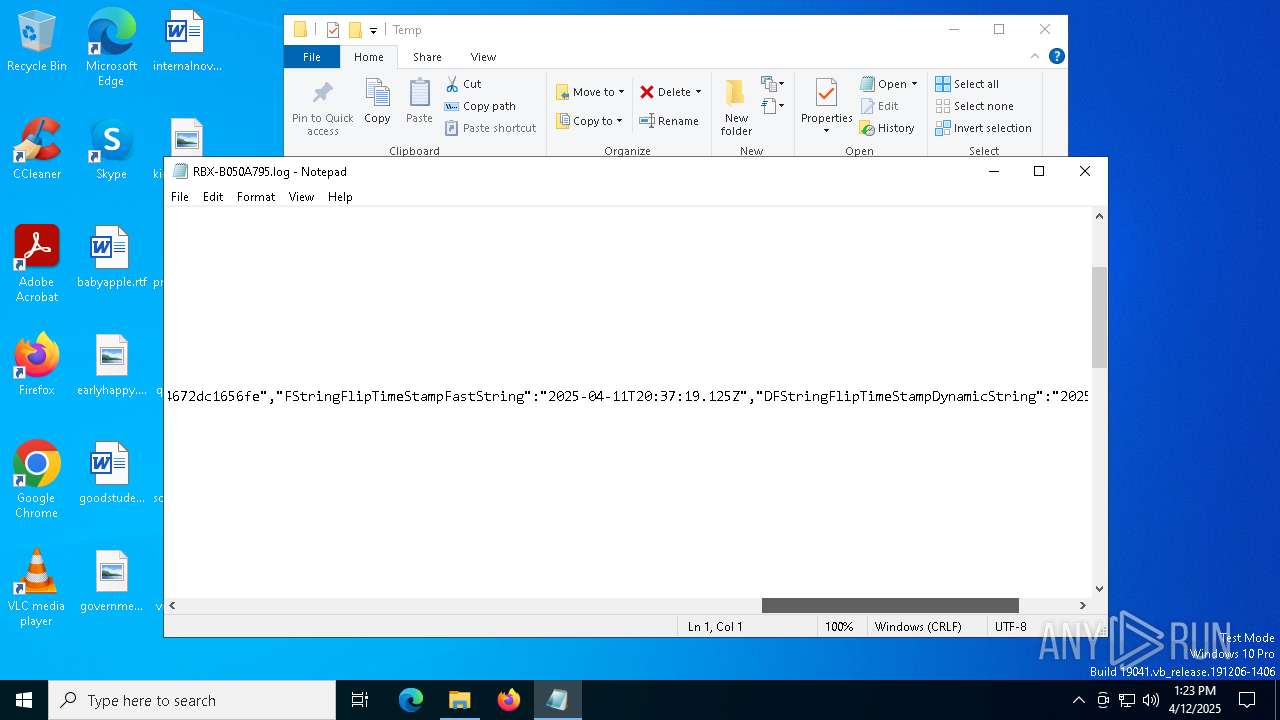
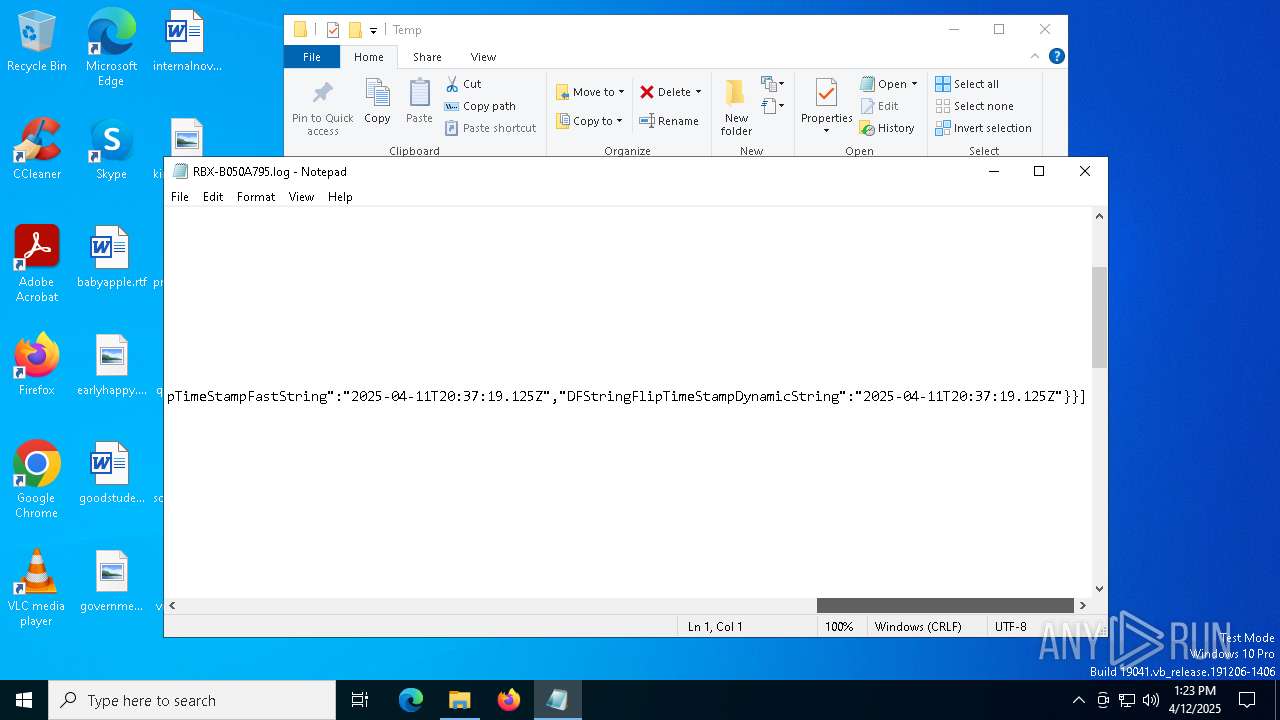
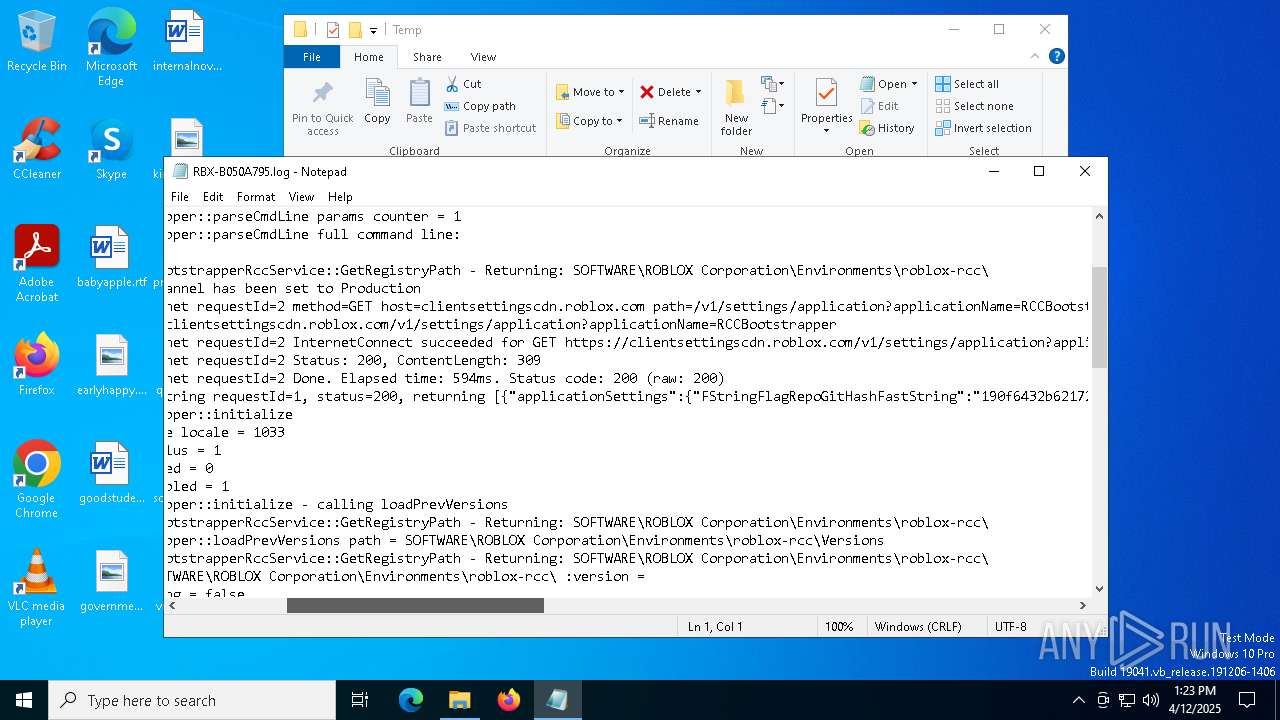
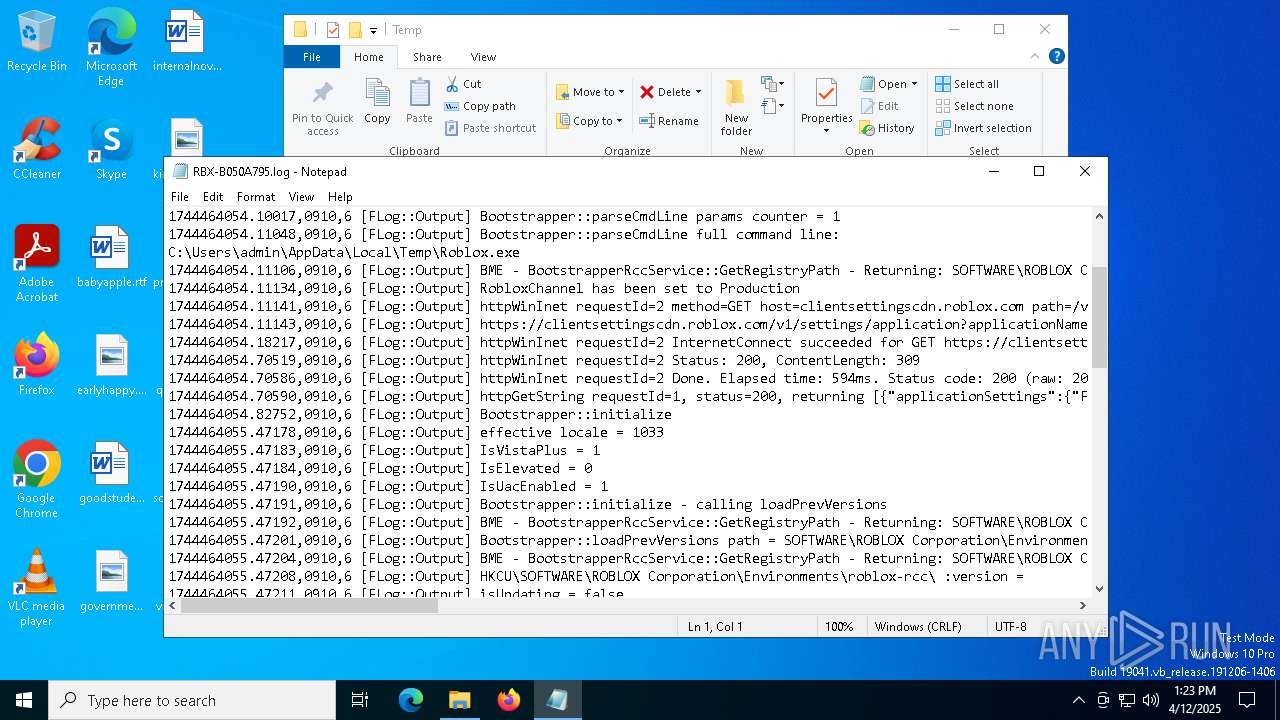
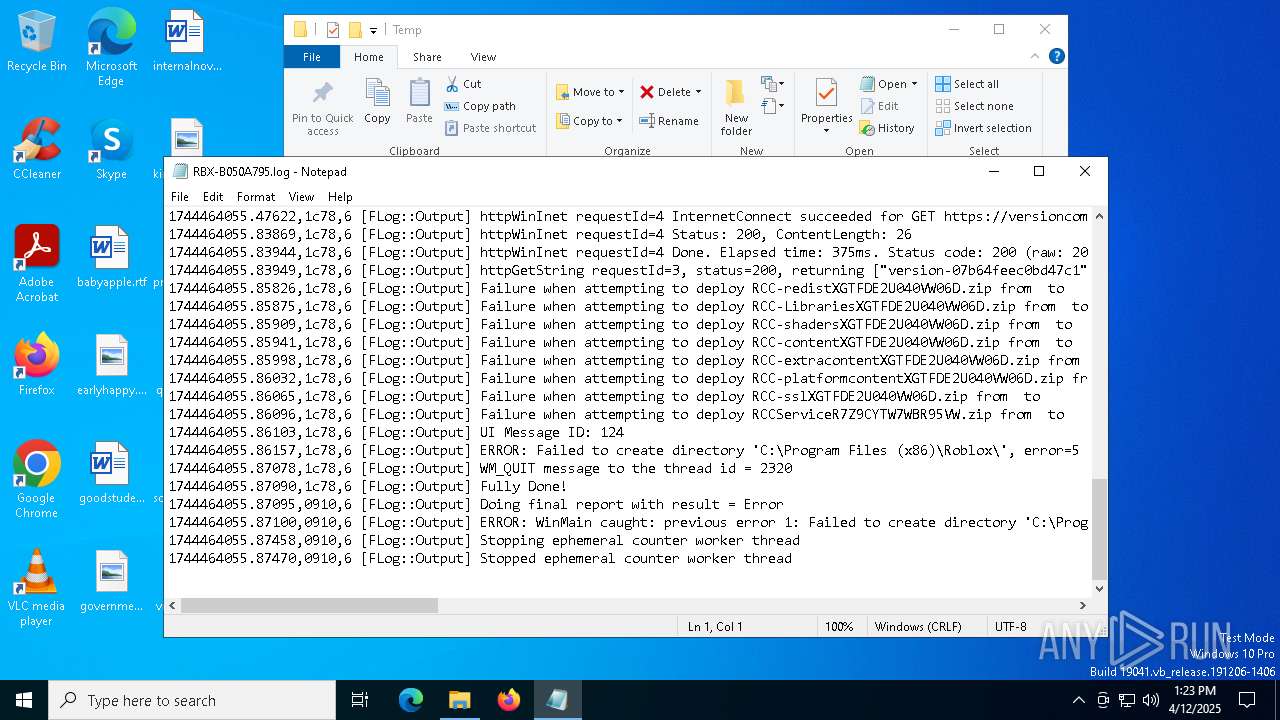
| 2284 | Roblox.exe | C:\Users\admin\AppData\Local\Temp\RBX-B050A795.log | text | |
MD5:8AEAEB9113204A151E0DE4E2ED65FE2C | SHA256:7FDCC9F3CA83FD26EDD76B4DED775E96088F6690DE3CB11916813F2C27B30DE0 | |||
| 2284 | Roblox.exe | C:\Users\admin\AppData\Local\Temp\crashpad_roblox\settings.dat | binary | |
MD5:397648E9A1515281080DF33BB9374DA7 | SHA256:D5F8611967E6E9B28B1A0E7CA9F9A339F0566B1B02A351AF0873EA466908F87B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
41
DNS requests
50
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2284 | Roblox.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | unknown | binary | 1.42 Kb | whitelisted |
7496 | Roblox.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQh80WaEMqmyEvaHjlisSfVM4p8SAQUF9nWJSdn%2BTHCSUPZMDZEjGypT%2BsCEGxUlMUNeuJZOXh%2FQAMe0fk%3D | US | binary | 471 b | whitelisted |
2284 | Roblox.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEBN9U5yqfDGppDNwGWiEeo0%3D | US | binary | 2.18 Kb | whitelisted |
— | — | GET | 200 | 2.18.121.139:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | FR | binary | 825 b | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
7496 | Roblox.exe | GET | 200 | 18.161.96.75:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwdzEkpLy9ROx7U76vGUhC06D6E%3D | US | binary | 1.40 Kb | whitelisted |
7496 | Roblox.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQh80WaEMqmyEvaHjlisSfVM4p8SAQUF9nWJSdn%2BTHCSUPZMDZEjGypT%2BsCEA4jaMy2rxGsbBqVpNHwqqg%3D | US | binary | 471 b | whitelisted |
7960 | SIHClient.exe | GET | 200 | 104.85.1.163:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | NL | binary | 419 b | whitelisted |
7960 | SIHClient.exe | GET | 200 | 104.85.1.163:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | NL | binary | 407 b | whitelisted |
2284 | Roblox.exe | GET | 200 | 18.245.38.41:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwdzEkzUBtJnwJkc3SmanzgxeYU%3D | US | binary | 1.40 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.18.121.139:80 | crl.microsoft.com | AKAMAI-AS | FR | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2284 | Roblox.exe | 52.222.236.6:443 | clientsettingscdn.roblox.com | AMAZON-02 | US | whitelisted |
2284 | Roblox.exe | 18.245.38.41:80 | ocsp.rootca1.amazontrust.com | — | US | whitelisted |
2284 | Roblox.exe | 128.116.44.3:443 | versioncompatibility.api.roblox.com | ROBLOX-PRODUCTION | US | whitelisted |
2284 | Roblox.exe | 104.18.38.233:80 | ocsp.comodoca.com | CLOUDFLARENET | — | whitelisted |
2284 | Roblox.exe | 172.64.149.23:80 | ocsp.comodoca.com | CLOUDFLARENET | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
clientsettingscdn.roblox.com |
| whitelisted |
ocsp.rootca1.amazontrust.com |
| whitelisted |
setup.rbxcdn.qq.com |
| whitelisted |
clientsettingscdn.roblox.qq.com |
| whitelisted |
setup.rbxcdn.com |
| whitelisted |
setup-ak.rbxcdn.com |
| whitelisted |
setup-ll.rbxcdn.com |
| whitelisted |