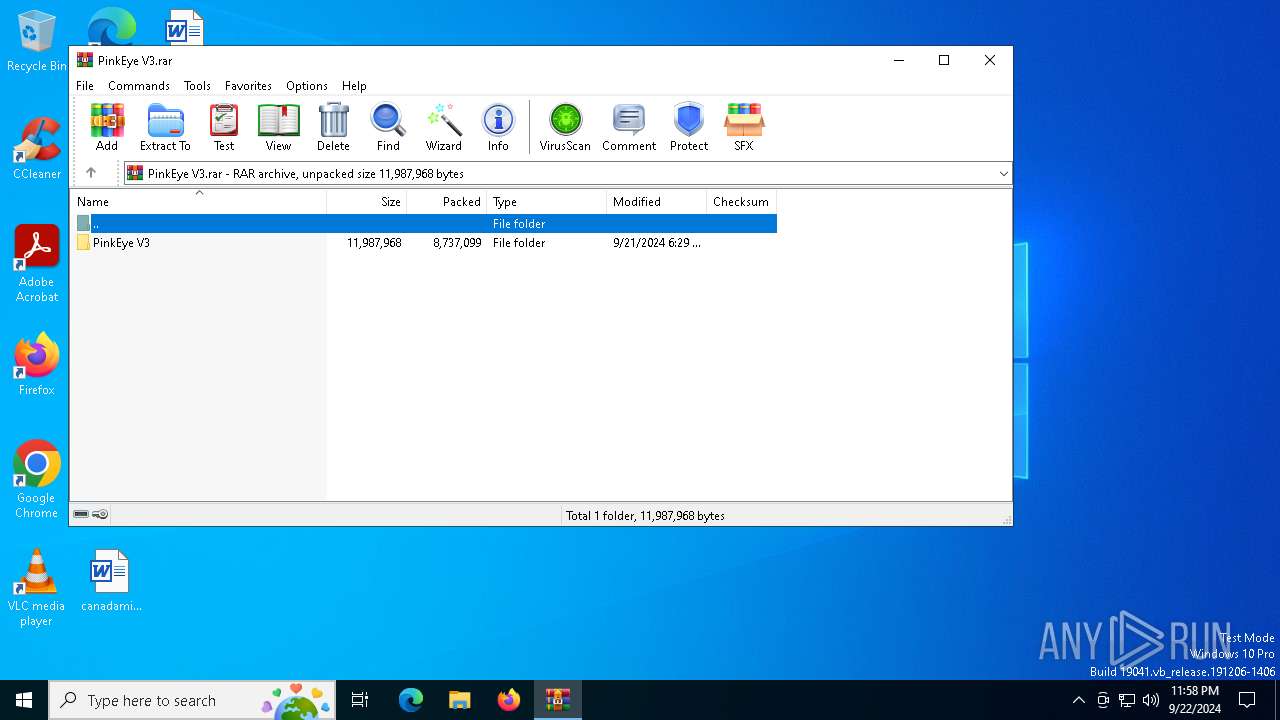
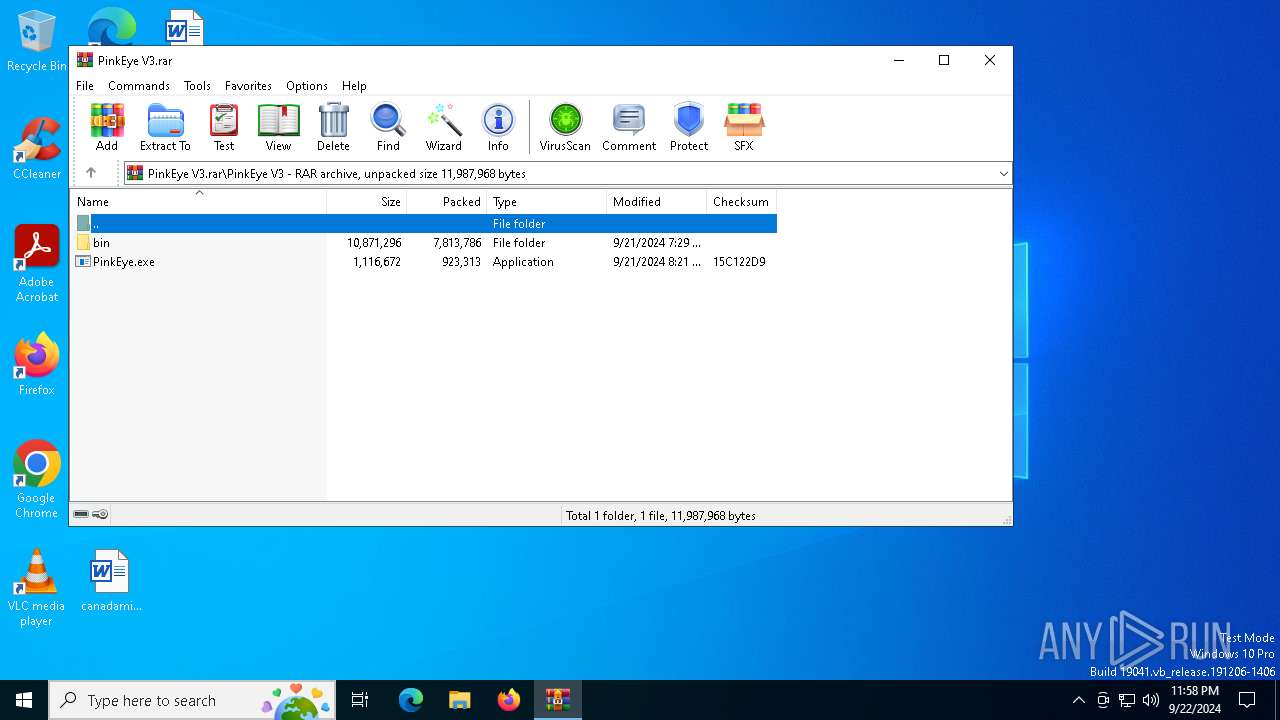
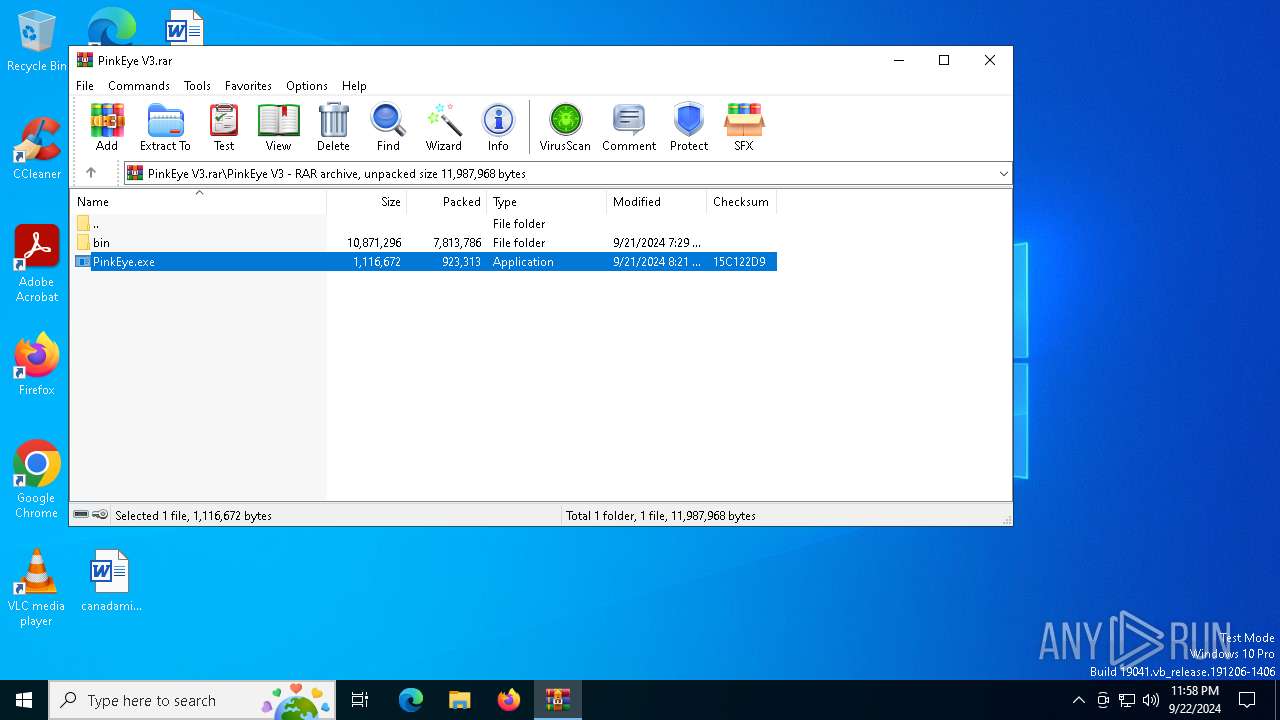
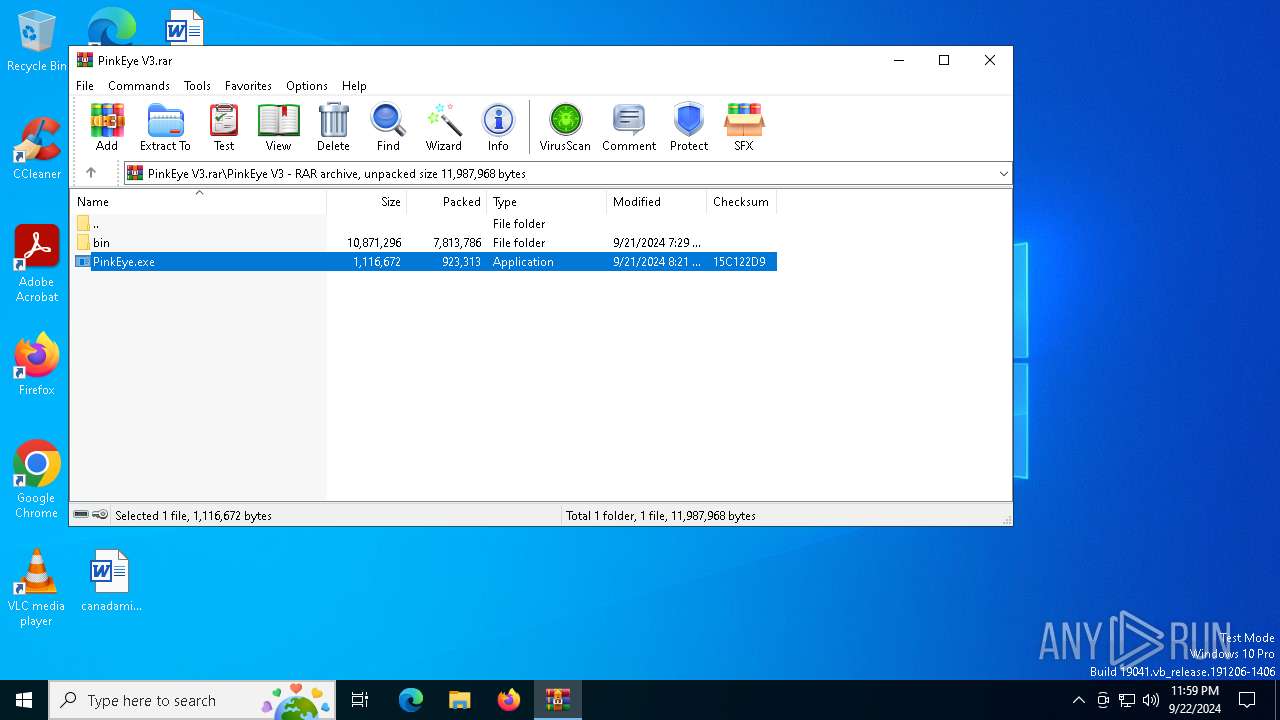
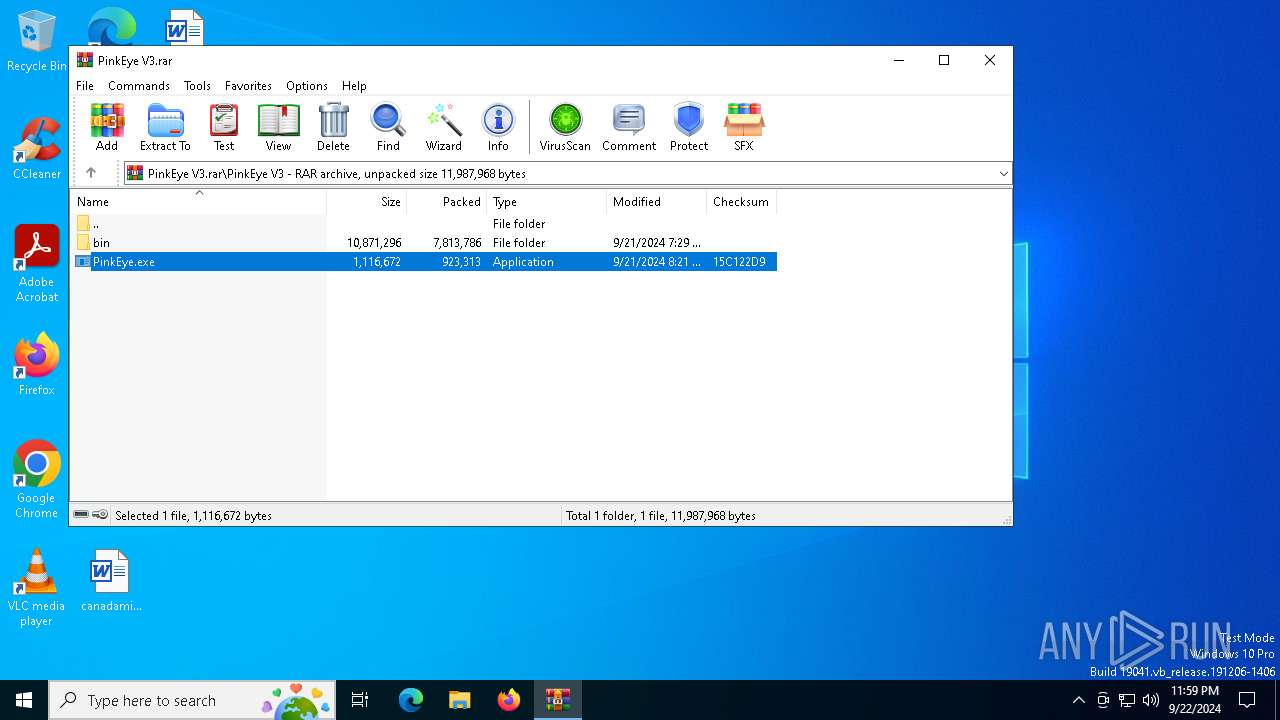
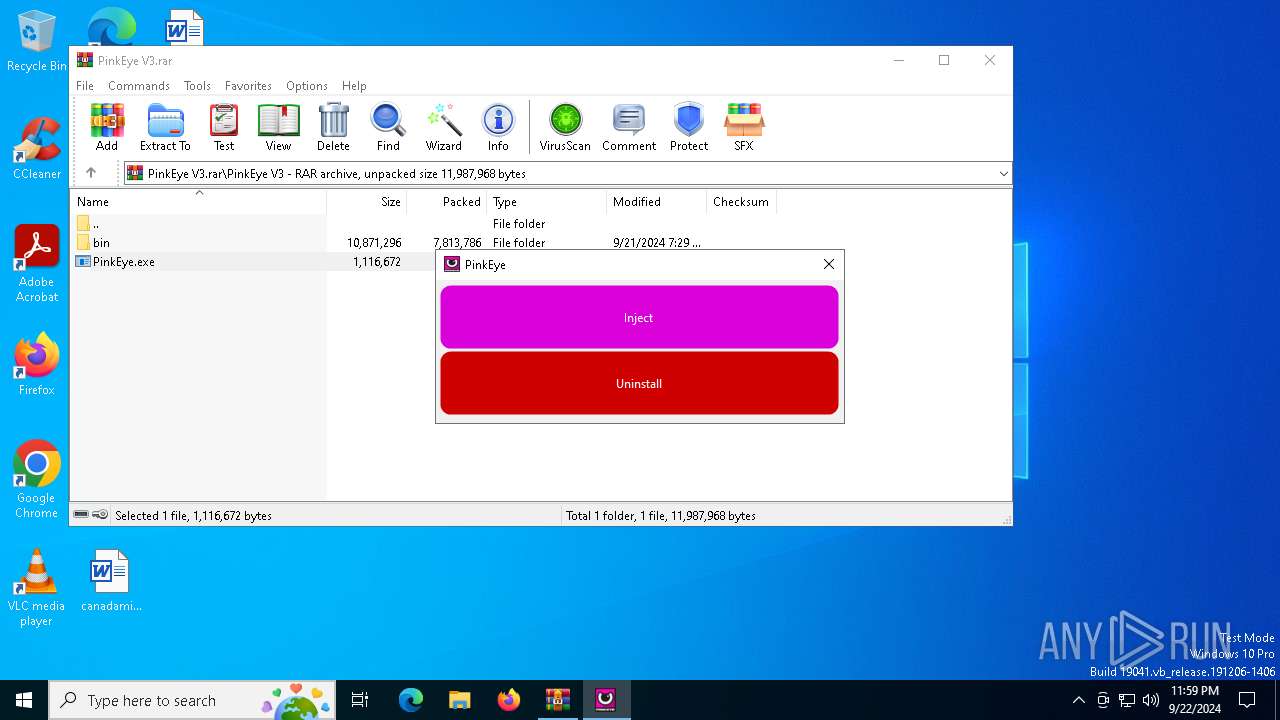
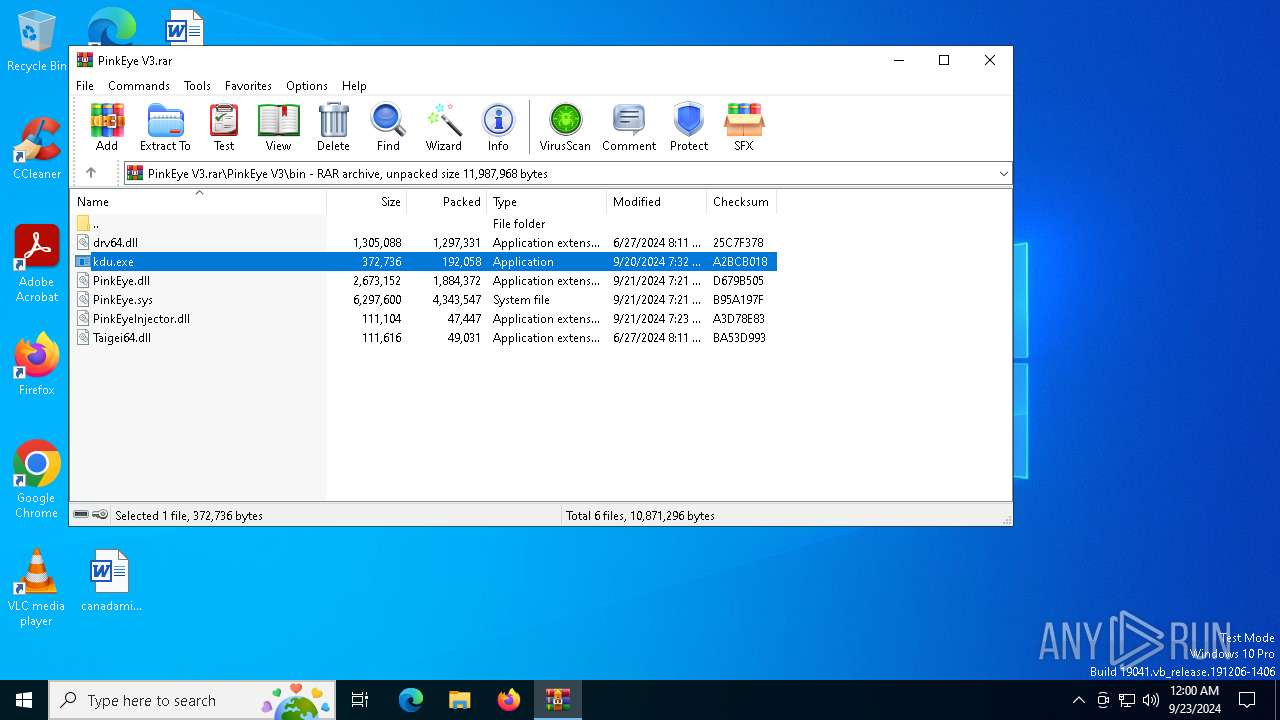
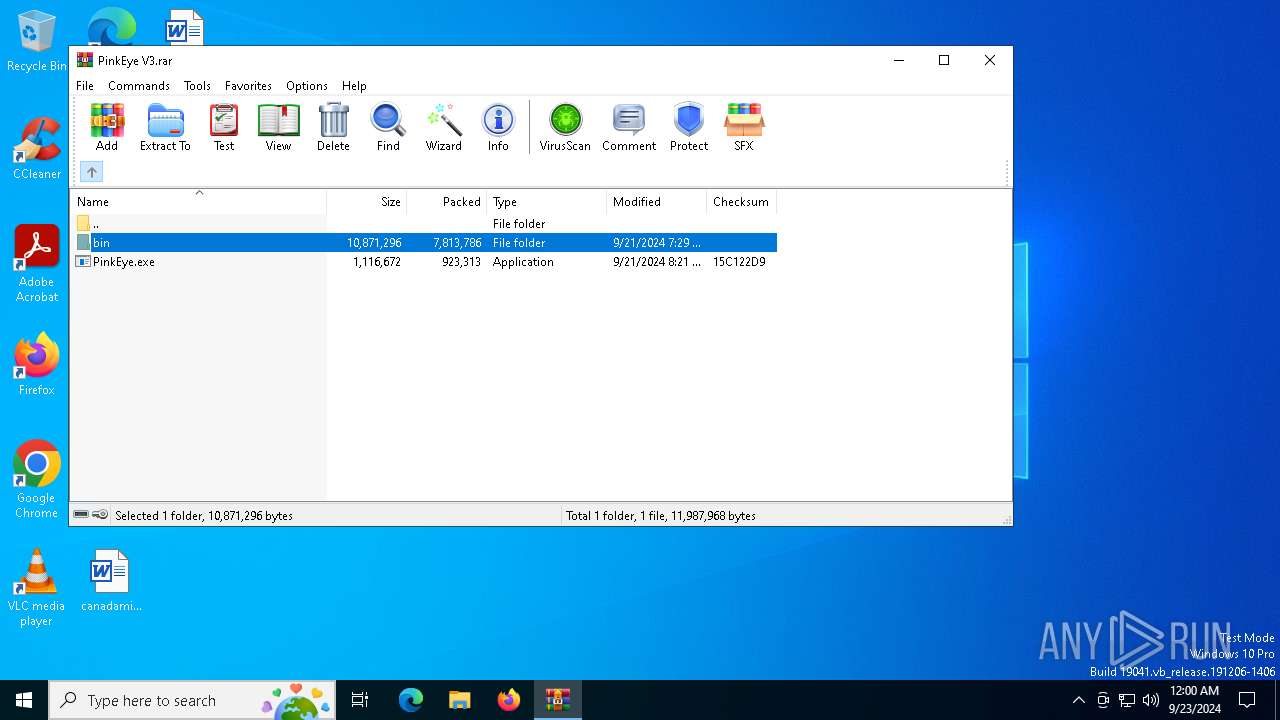
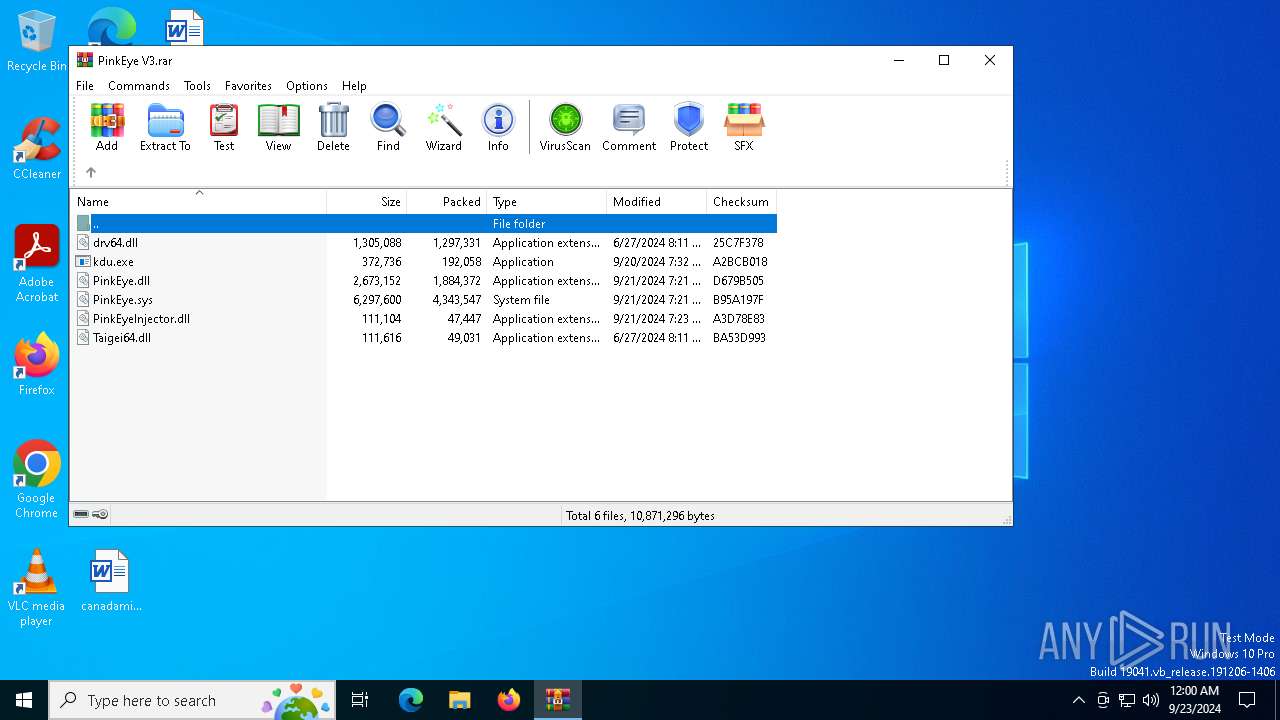
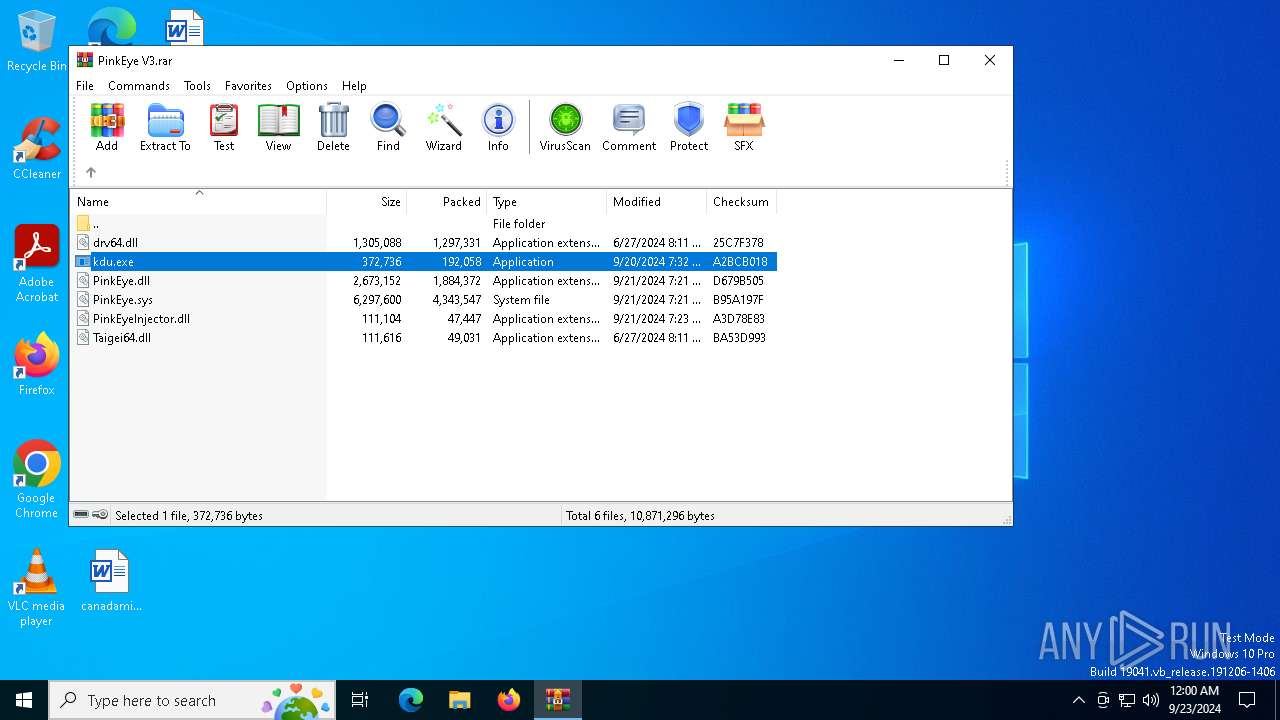
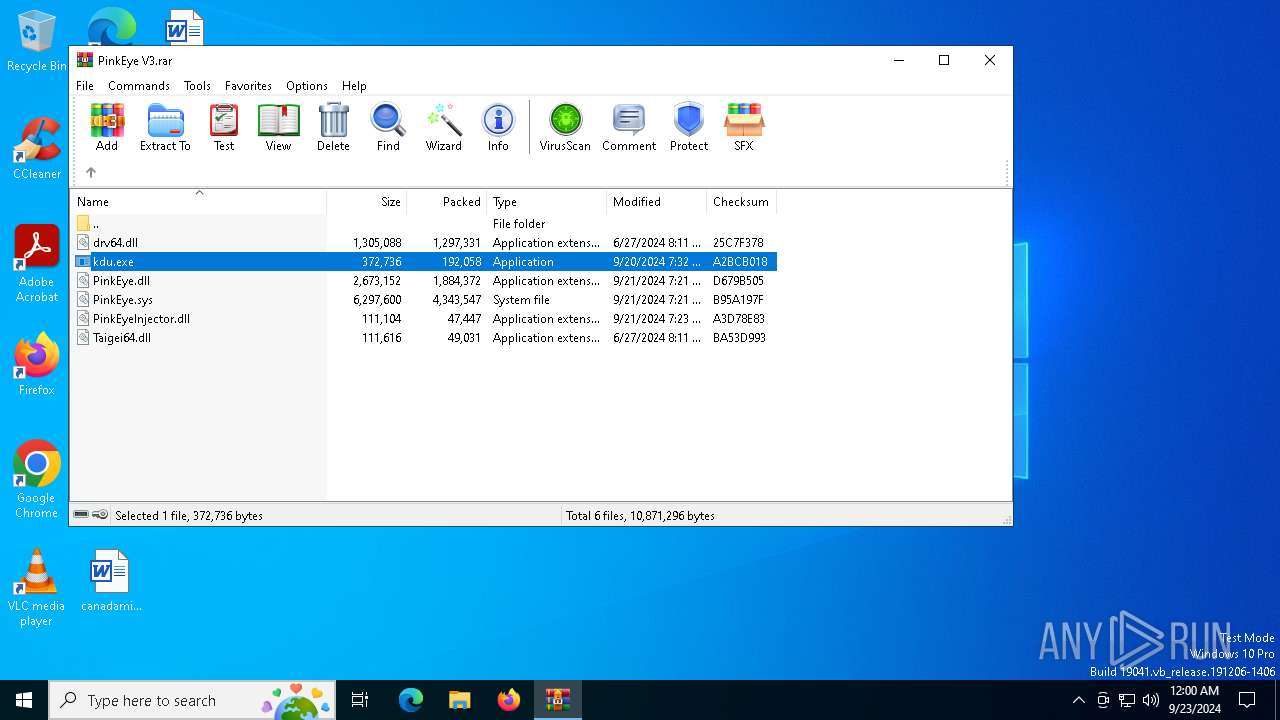
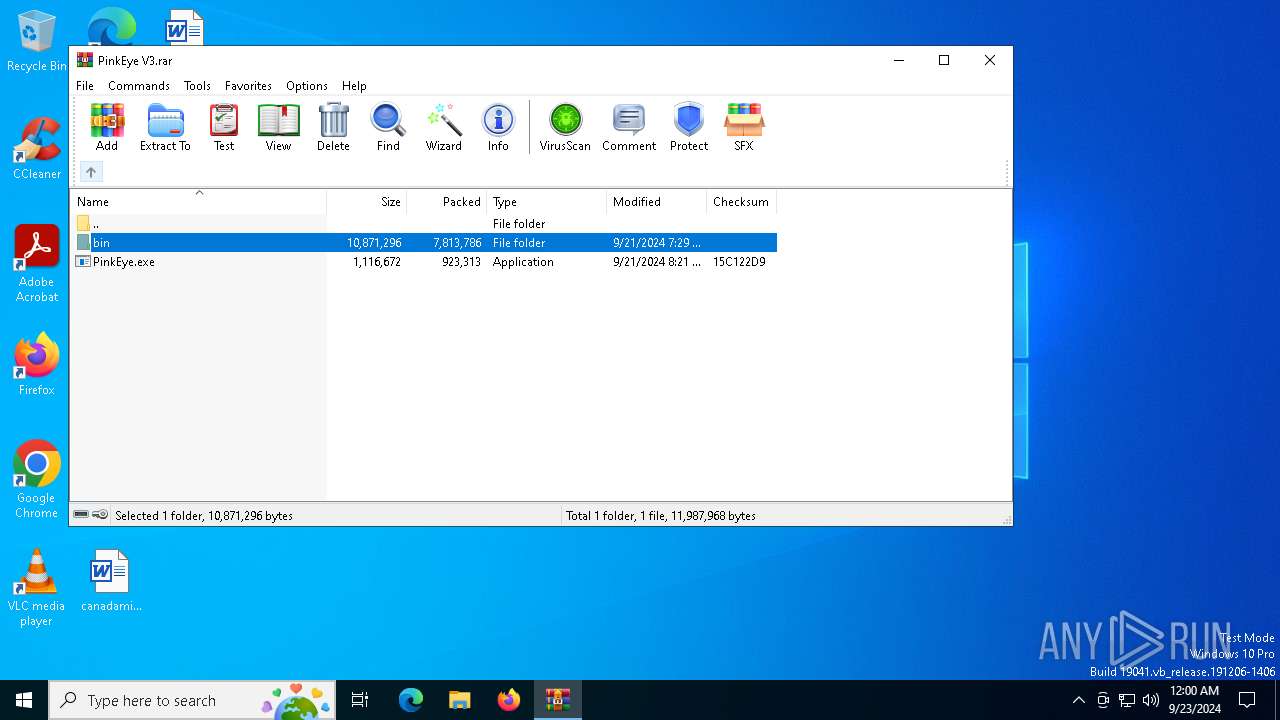
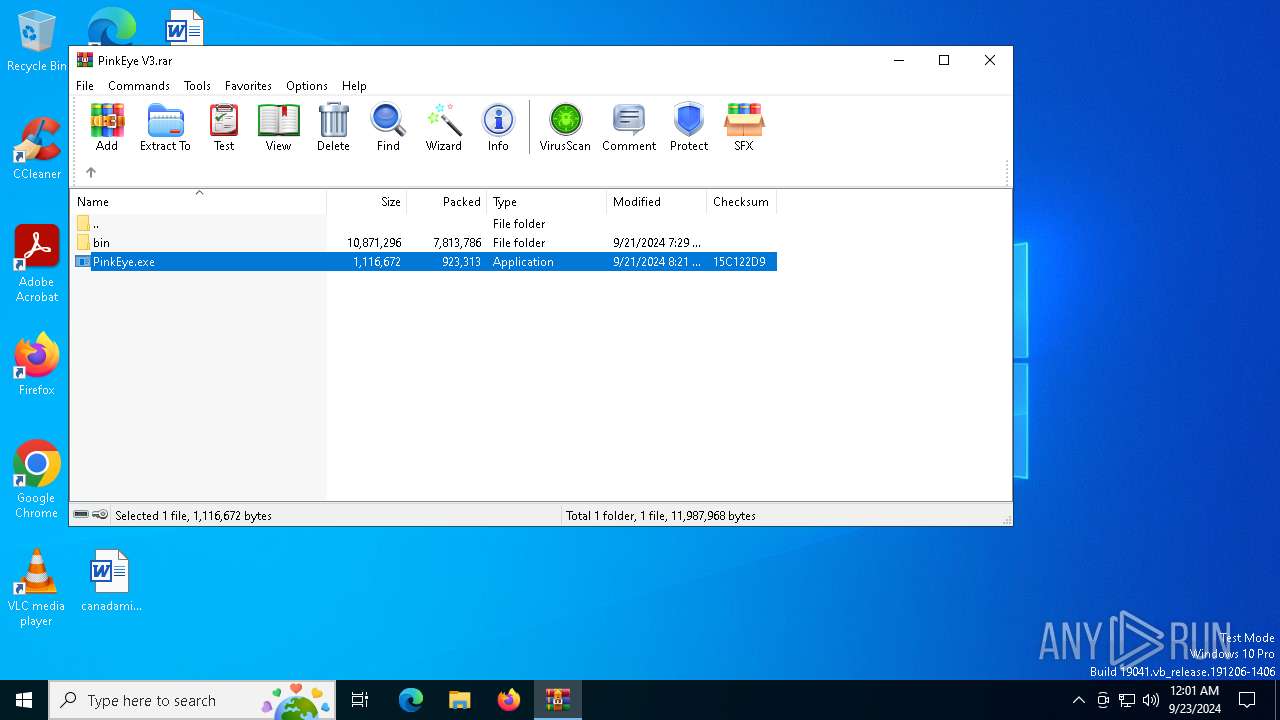
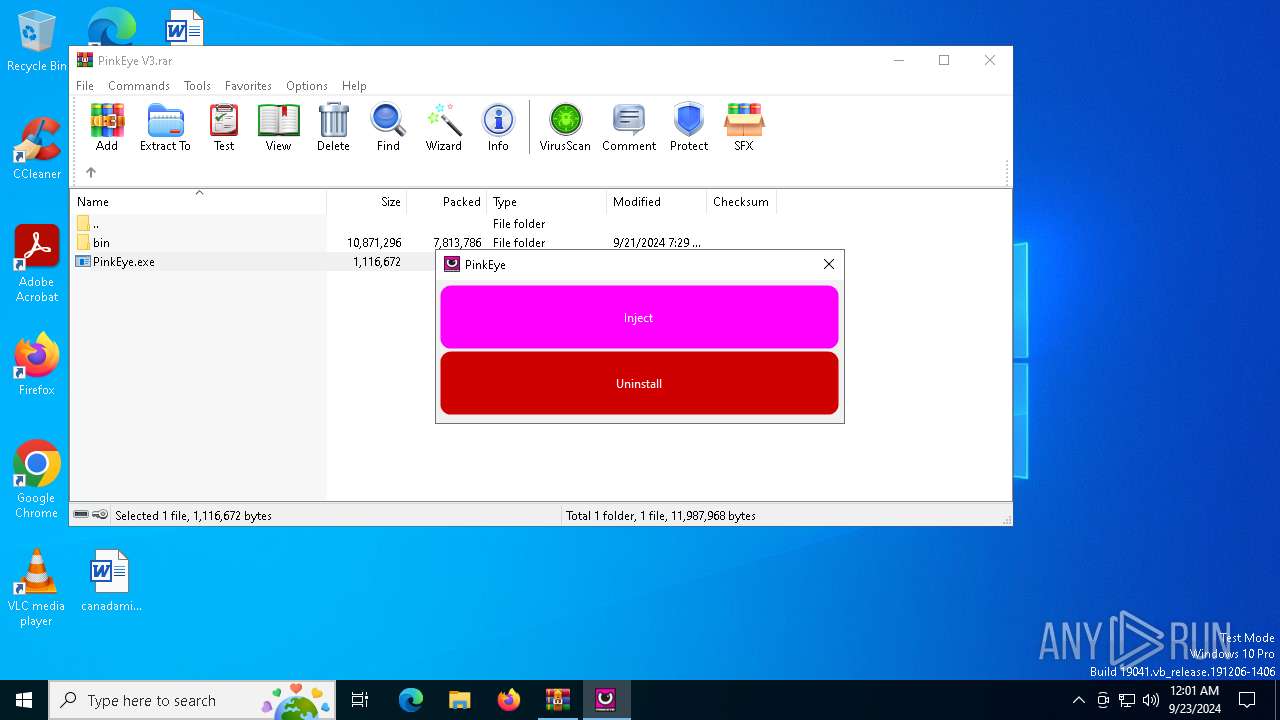
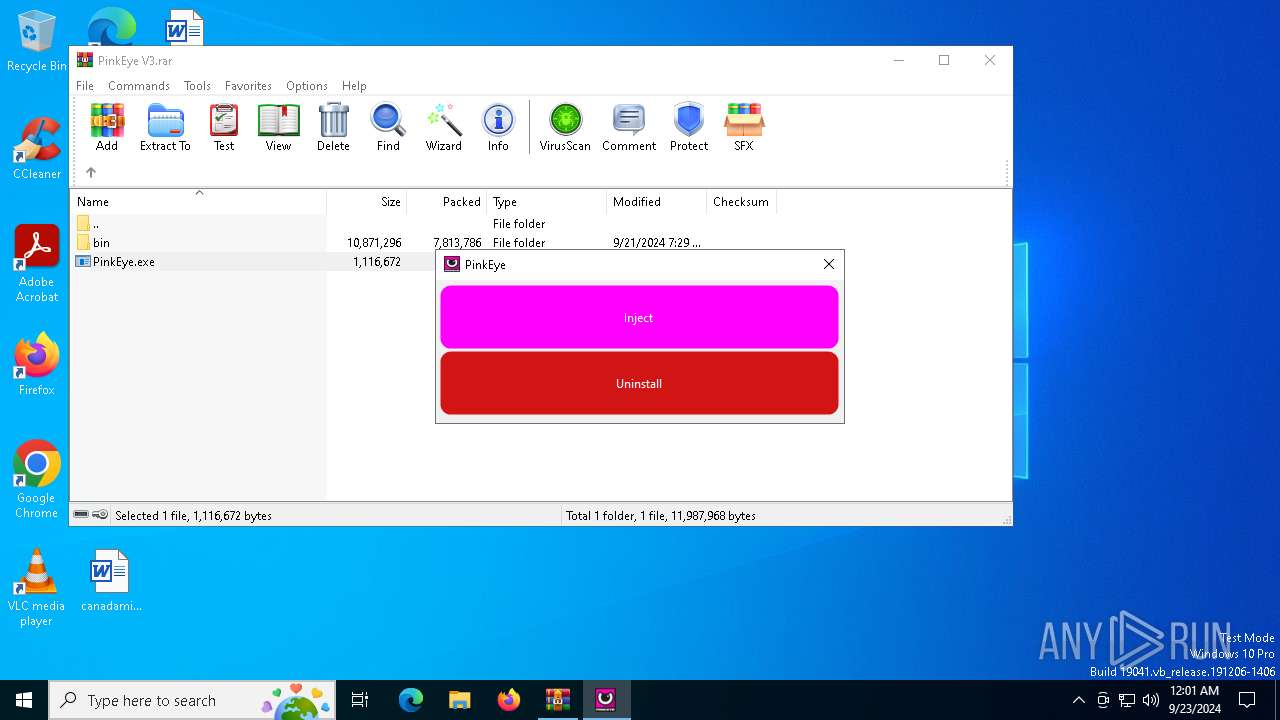
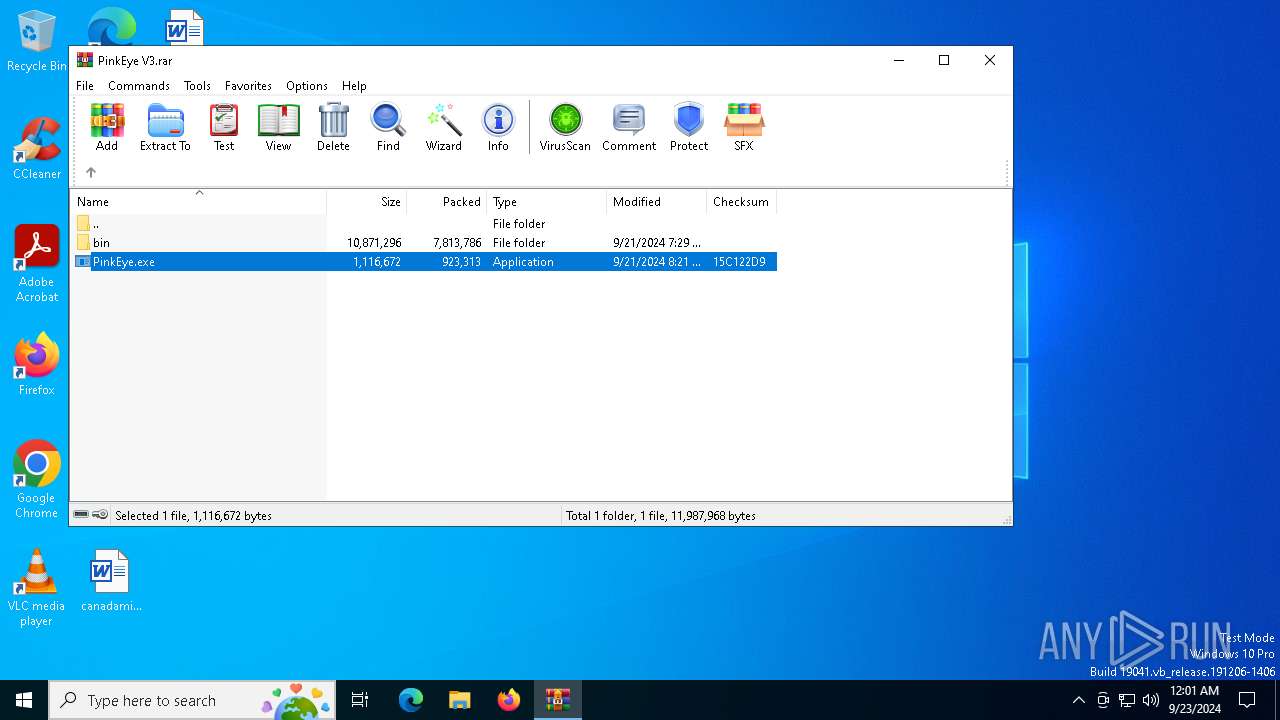
| File name: | PinkEye V3.rar |
| Full analysis: | https://app.any.run/tasks/c840dda3-957c-4b52-b69e-80ce195ca490 |
| Verdict: | Malicious activity |
| Analysis date: | September 22, 2024, 23:58:26 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 17C7723D5E0D3CC167E8F8C1BB122F6F |
| SHA1: | CD0DBE61706B0320EEFD952F1702A8AAD33DD699 |
| SHA256: | BC789AF02D1EEA9D2713C7D50544AC84F728E39424CEDA1D4F4A6B03B05AD28E |
| SSDEEP: | 98304:HZCl7Mz25j+Wki3jpPKTTuo53MUmczyKfq1qDSXAqsMjSW4M8Sg2fy44NJ1wWoRZ:68UZ+r9JNRLSoLy |
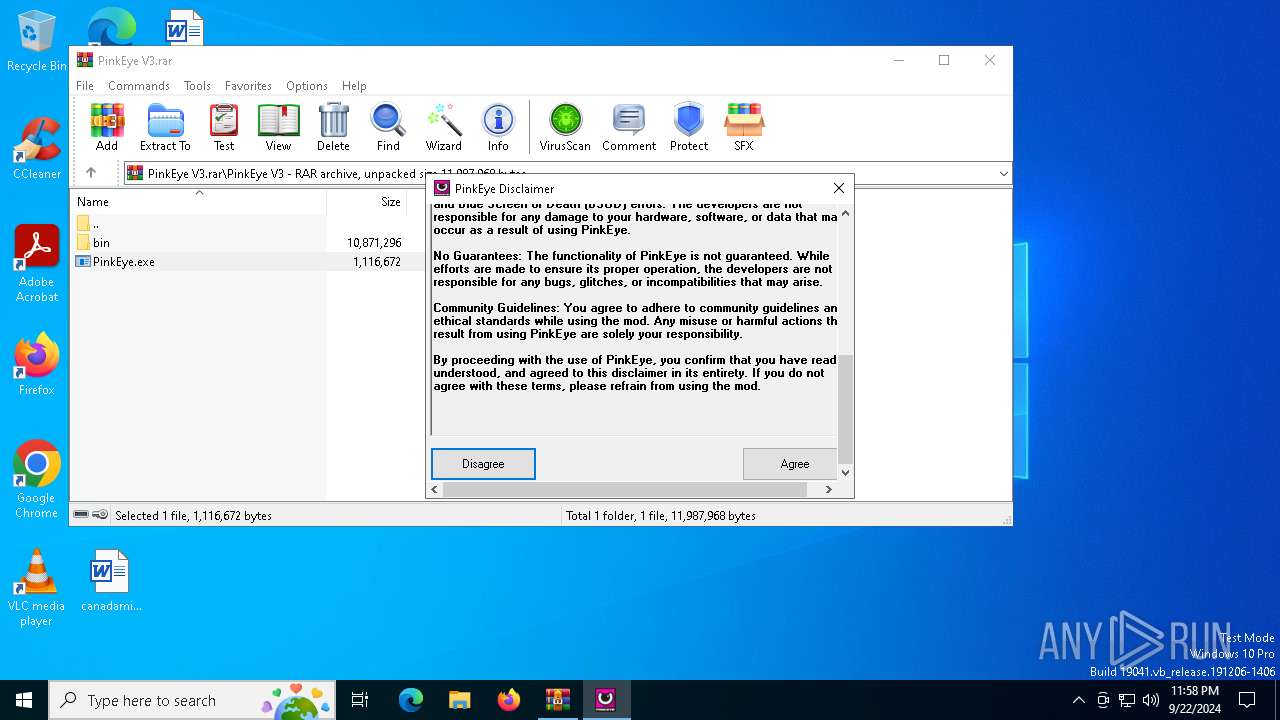
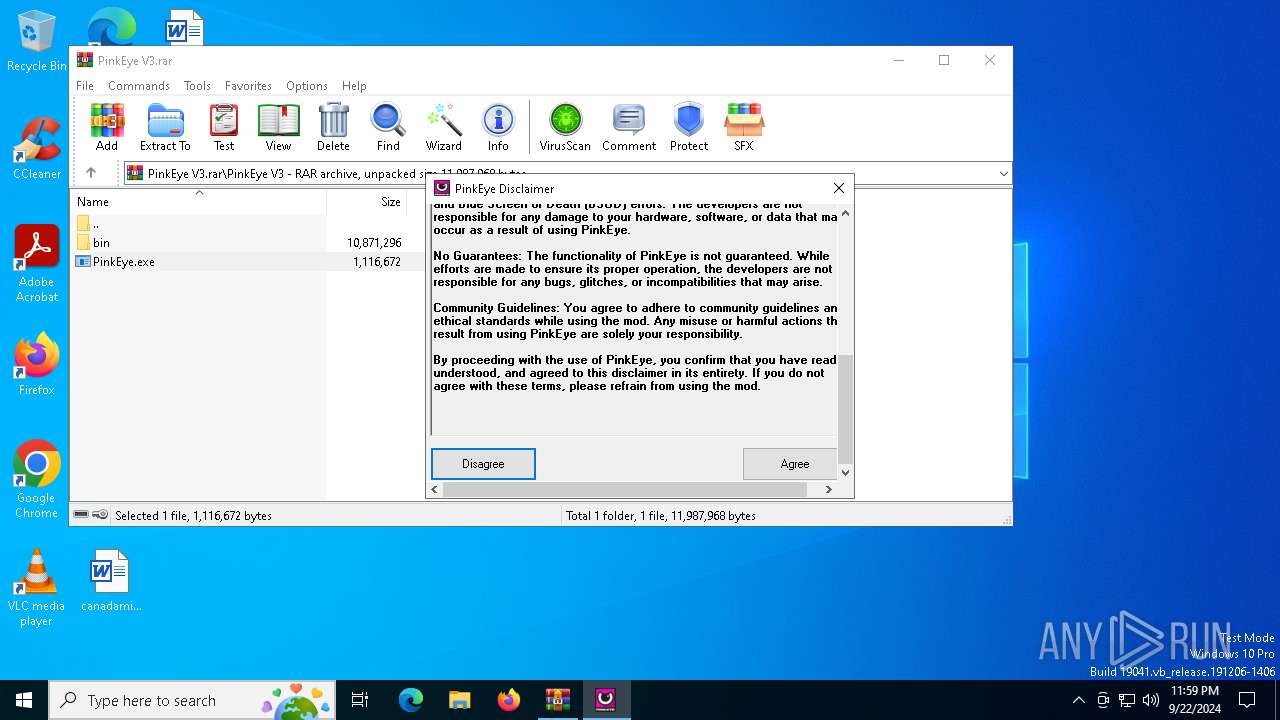
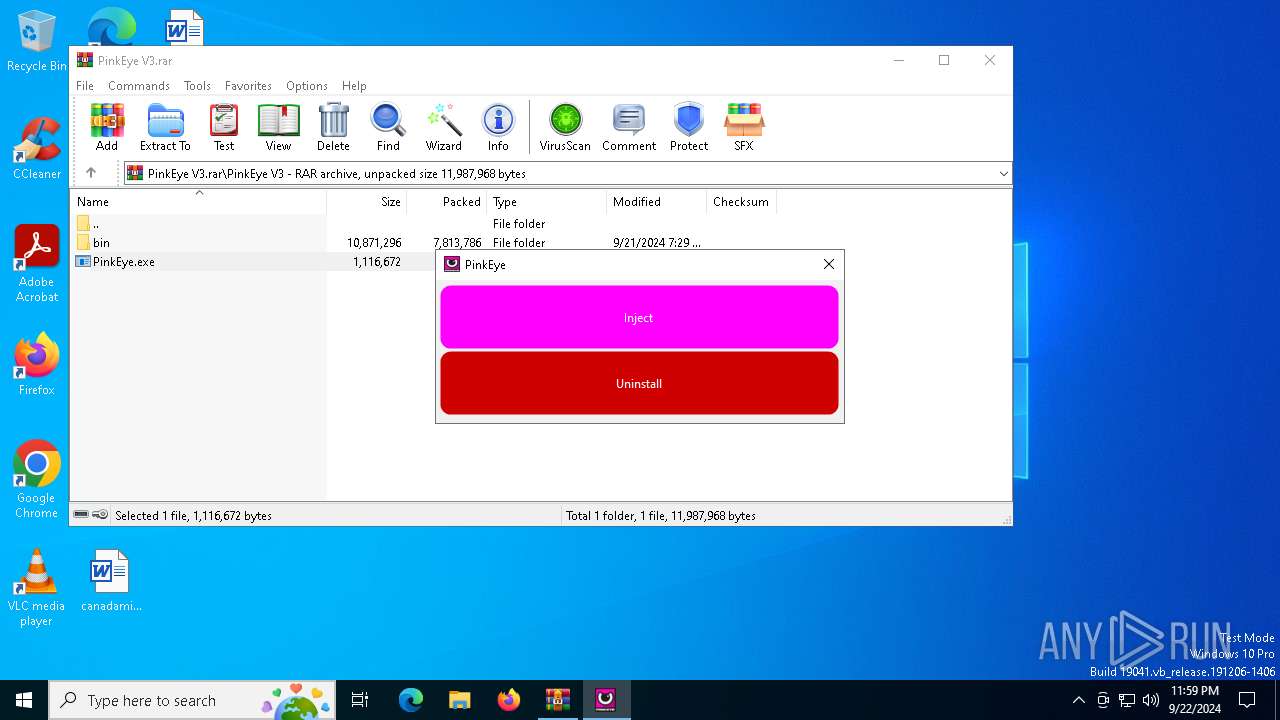
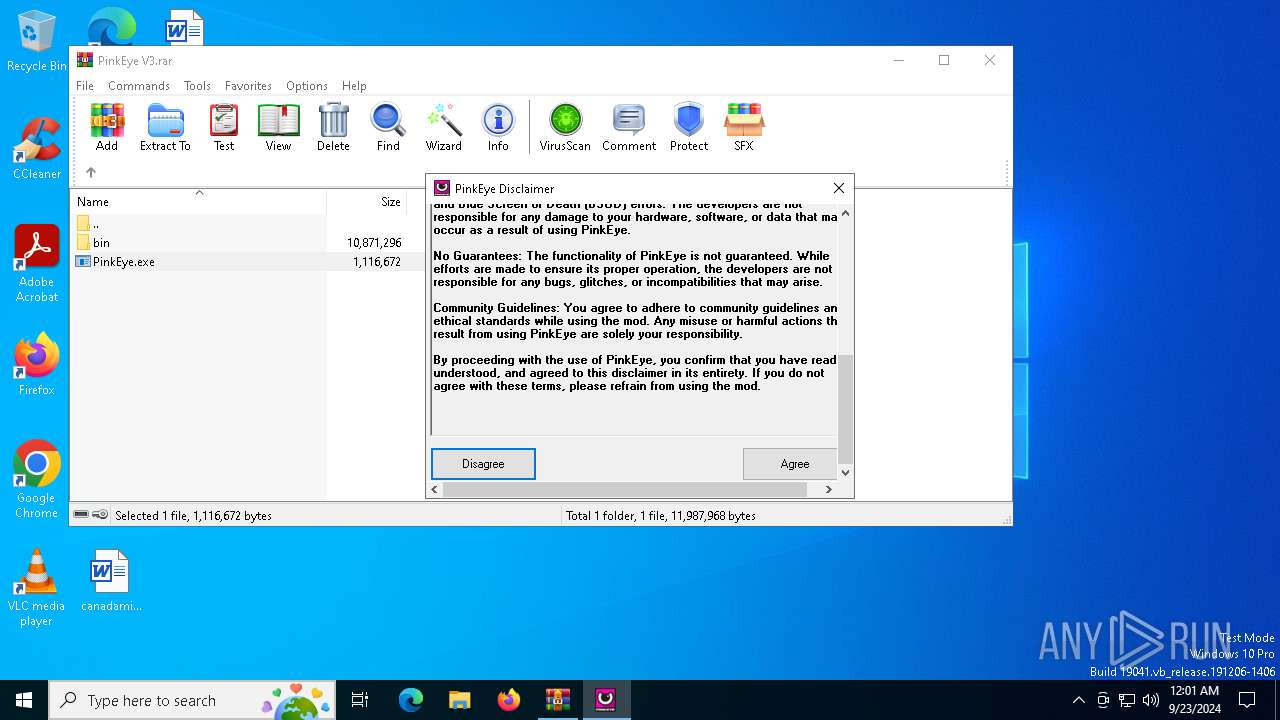
MALICIOUS
XORed URL has been found (YARA)
- PinkEye.exe (PID: 6276)
- PinkEye.exe (PID: 6108)
- PinkEye.exe (PID: 2452)
SUSPICIOUS
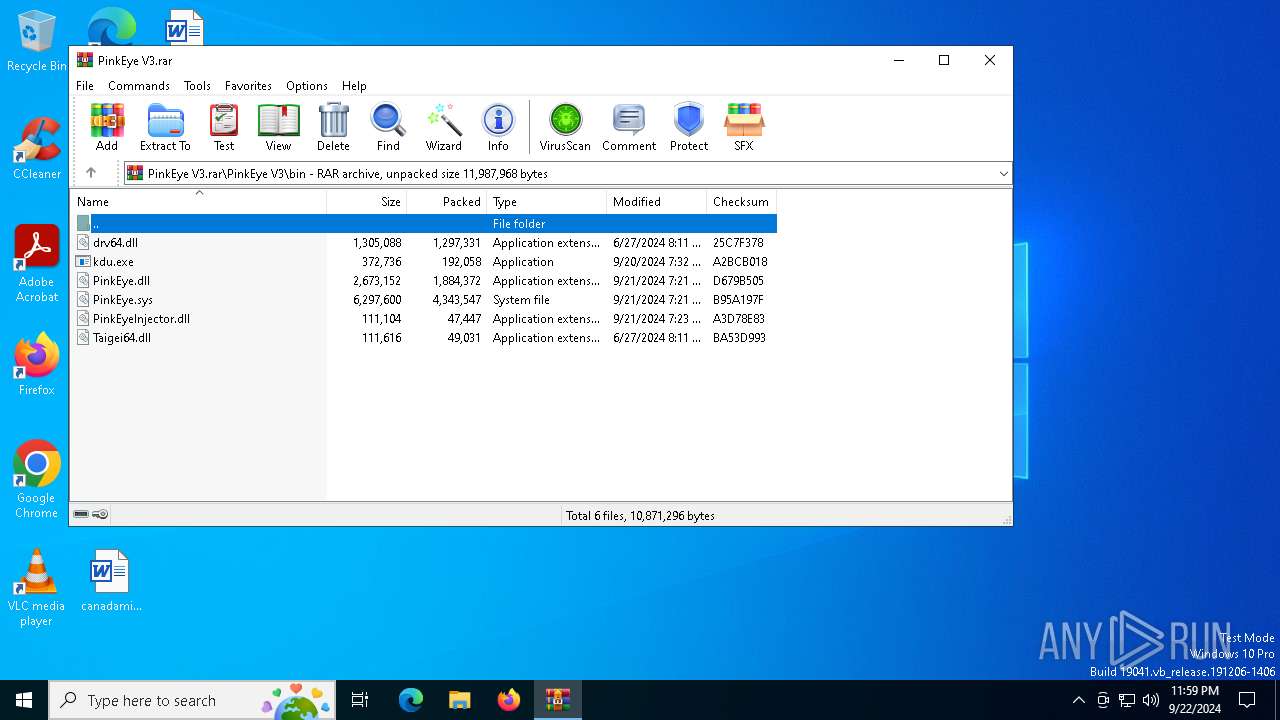
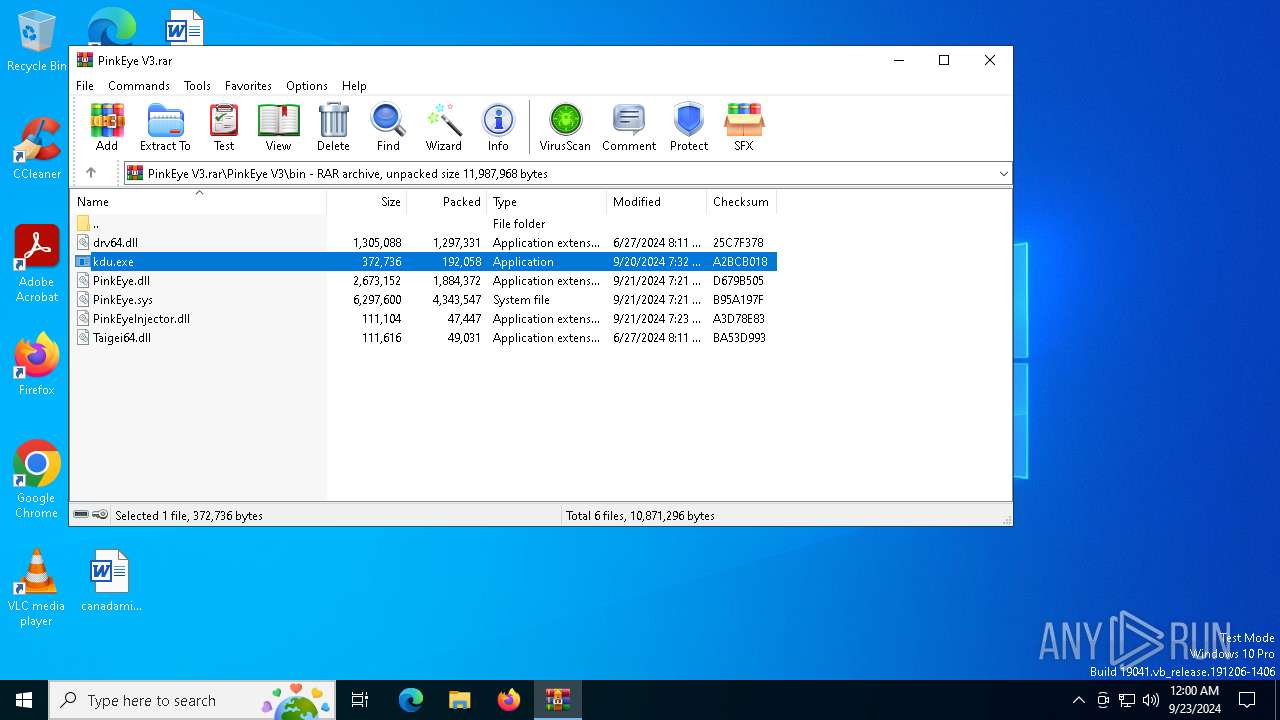
Drops a system driver (possible attempt to evade defenses)
- WinRAR.exe (PID: 5244)
- kdu.exe (PID: 6612)
- kdu.exe (PID: 6632)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 5244)
- PinkEye.exe (PID: 6276)
Executable content was dropped or overwritten
- PinkEye.exe (PID: 6108)
- kdu.exe (PID: 6612)
- kdu.exe (PID: 6632)
There is functionality for taking screenshot (YARA)
- PinkEye.exe (PID: 6108)
- PinkEye.exe (PID: 2452)
INFO
Checks supported languages
- PinkEye.exe (PID: 6276)
Disables trace logs
- PinkEye.exe (PID: 6276)
Reads the machine GUID from the registry
- PinkEye.exe (PID: 6276)
The process uses the downloaded file
- PinkEye.exe (PID: 6276)
- WinRAR.exe (PID: 5244)
Reads Environment values
- PinkEye.exe (PID: 6276)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 5244)
Checks proxy server information
- PinkEye.exe (PID: 6276)
Reads the software policy settings
- PinkEye.exe (PID: 6276)
Reads the computer name
- PinkEye.exe (PID: 6276)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
153
Monitored processes
20
Malicious processes
4
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1280 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa5244.34321\PinkEye V3\PinkEye.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa5244.34321\PinkEye V3\PinkEye.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: PinkEye Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1636 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa5244.46499\PinkEye V3\bin\kdu.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa5244.46499\PinkEye V3\bin\kdu.exe | — | WinRAR.exe | |||||||||||
User: admin Company: UG North Integrity Level: MEDIUM Description: Kernel Driver Utility Exit code: 3221226540 Version: 1.4.2.2404 Modules
| |||||||||||||||
| 1728 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2132 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa5244.44860\PinkEye V3\bin\kdu.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa5244.44860\PinkEye V3\bin\kdu.exe | WinRAR.exe | ||||||||||||
User: admin Company: UG North Integrity Level: HIGH Description: Kernel Driver Utility Exit code: 0 Version: 1.4.2.2404 Modules
| |||||||||||||||
| 2452 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa5244.47291\PinkEye V3\PinkEye.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa5244.47291\PinkEye V3\PinkEye.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: PinkEye Exit code: 4294967295 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3972 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa5244.46254\PinkEye V3\bin\kdu.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa5244.46254\PinkEye V3\bin\kdu.exe | — | WinRAR.exe | |||||||||||
User: admin Company: UG North Integrity Level: MEDIUM Description: Kernel Driver Utility Exit code: 3221226540 Version: 1.4.2.2404 Modules
| |||||||||||||||
| 4784 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa5244.47291\PinkEye V3\PinkEye.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa5244.47291\PinkEye V3\PinkEye.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: PinkEye Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
| 5244 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\PinkEye V3.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 5248 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa5244.38472\PinkEye V3\PinkEye.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa5244.38472\PinkEye V3\PinkEye.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: PinkEye Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
| 6108 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa5244.38472\PinkEye V3\PinkEye.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa5244.38472\PinkEye V3\PinkEye.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: PinkEye Exit code: 4294967295 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
9 127
Read events
9 075
Write events
48
Delete events
4
Modification events
| (PID) Process: | (5244) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (5244) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\PinkEye V3.rar | |||
| (PID) Process: | (5244) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (5244) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (5244) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (5244) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6276) PinkEye.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\PinkEye_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6276) PinkEye.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\PinkEye_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (6276) PinkEye.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\PinkEye_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (6276) PinkEye.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\PinkEye_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
Executable files
54
Suspicious files
0
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
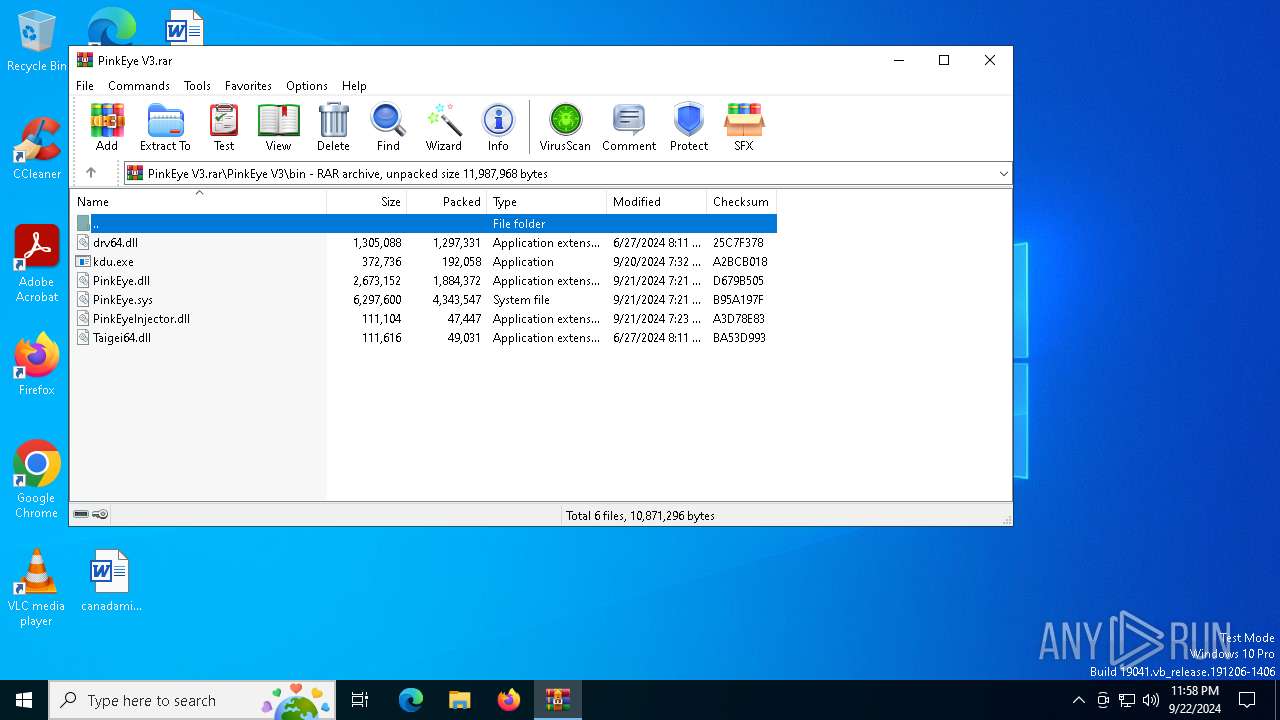
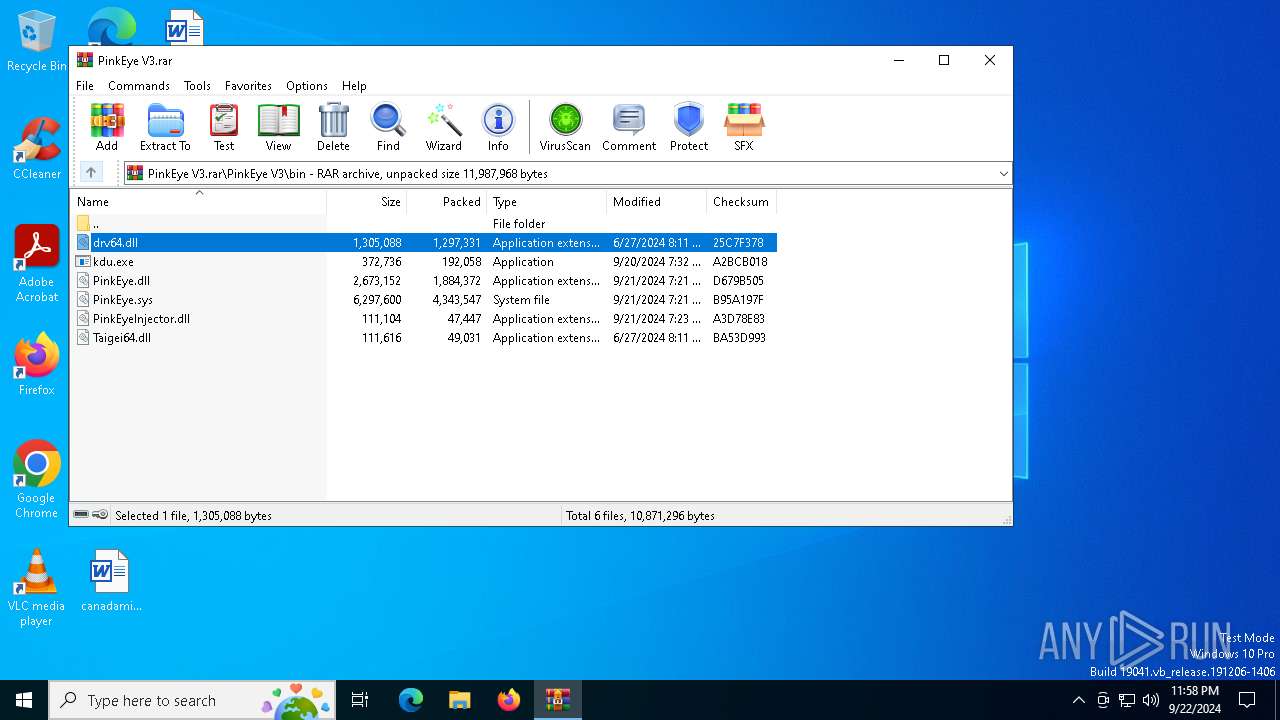
| 5244 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa5244.34321\PinkEye V3\bin\PinkEye.dll | executable | |
MD5:02581065B40026B5084E4BFBED72B7BC | SHA256:60DB7851ECC1C8A30DE8FEC84180809C31531715BDB2B5388164DD082610FE86 | |||
| 5244 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa5244.34321\PinkEye V3\bin\PinkEyeInjector.dll | executable | |
MD5:DACB7F81464C2D8A38815816A80C6AF9 | SHA256:E3E4358FF8B5BC4B9911343D74E0F6EB6FD48B9572169AB9326828A7AAC8C121 | |||
| 5244 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa5244.34321\PinkEye V3\bin\PinkEye.sys | executable | |
MD5:D4C0AB9BBAF8E31A192E00AEFA4D552A | SHA256:16B6A6705B076E559EF570292A9CCB02B63B2A872D83EC16CDA79203338C96FA | |||
| 5244 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa5244.38472\PinkEye V3\bin\PinkEye.sys | executable | |
MD5:D4C0AB9BBAF8E31A192E00AEFA4D552A | SHA256:16B6A6705B076E559EF570292A9CCB02B63B2A872D83EC16CDA79203338C96FA | |||
| 5244 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa5244.34321\PinkEye V3\bin\Taigei64.dll | executable | |
MD5:36646DEF204EF6B717652747A9749E1E | SHA256:0E2660D68D58023B1A3C34E5BC3E39620C773A16323DFADA7074FEC72400B087 | |||
| 5244 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa5244.34321\PinkEye V3\PinkEye.exe | executable | |
MD5:BC84E79206DD01379464181B9F3DD4FE | SHA256:D0383E478C64618AB0617AACB3175DC4452B61324DDA1040B74FC67A173A7AB5 | |||
| 5244 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa5244.38472\PinkEye V3\bin\Taigei64.dll | executable | |
MD5:36646DEF204EF6B717652747A9749E1E | SHA256:0E2660D68D58023B1A3C34E5BC3E39620C773A16323DFADA7074FEC72400B087 | |||
| 5244 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa5244.38472\PinkEye V3\bin\kdu.exe | executable | |
MD5:274B133D2DDA1FF37F94AF121FF86102 | SHA256:7B31A5CDE6A837B82918EC7E1C881C297AE180CD1C36CFEFB0390B928A2FE91A | |||
| 5244 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa5244.38472\PinkEye V3\bin\PinkEyeInjector.dll | executable | |
MD5:DACB7F81464C2D8A38815816A80C6AF9 | SHA256:E3E4358FF8B5BC4B9911343D74E0F6EB6FD48B9572169AB9326828A7AAC8C121 | |||
| 5244 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa5244.38472\PinkEye V3\PinkEye.exe | executable | |
MD5:BC84E79206DD01379464181B9F3DD4FE | SHA256:D0383E478C64618AB0617AACB3175DC4452B61324DDA1040B74FC67A173A7AB5 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
37
DNS requests
18
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
740 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2064 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4780 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4780 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
740 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1084 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
740 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2064 | svchost.exe | 40.126.32.72:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2064 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
stand.sh |
| unknown |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |