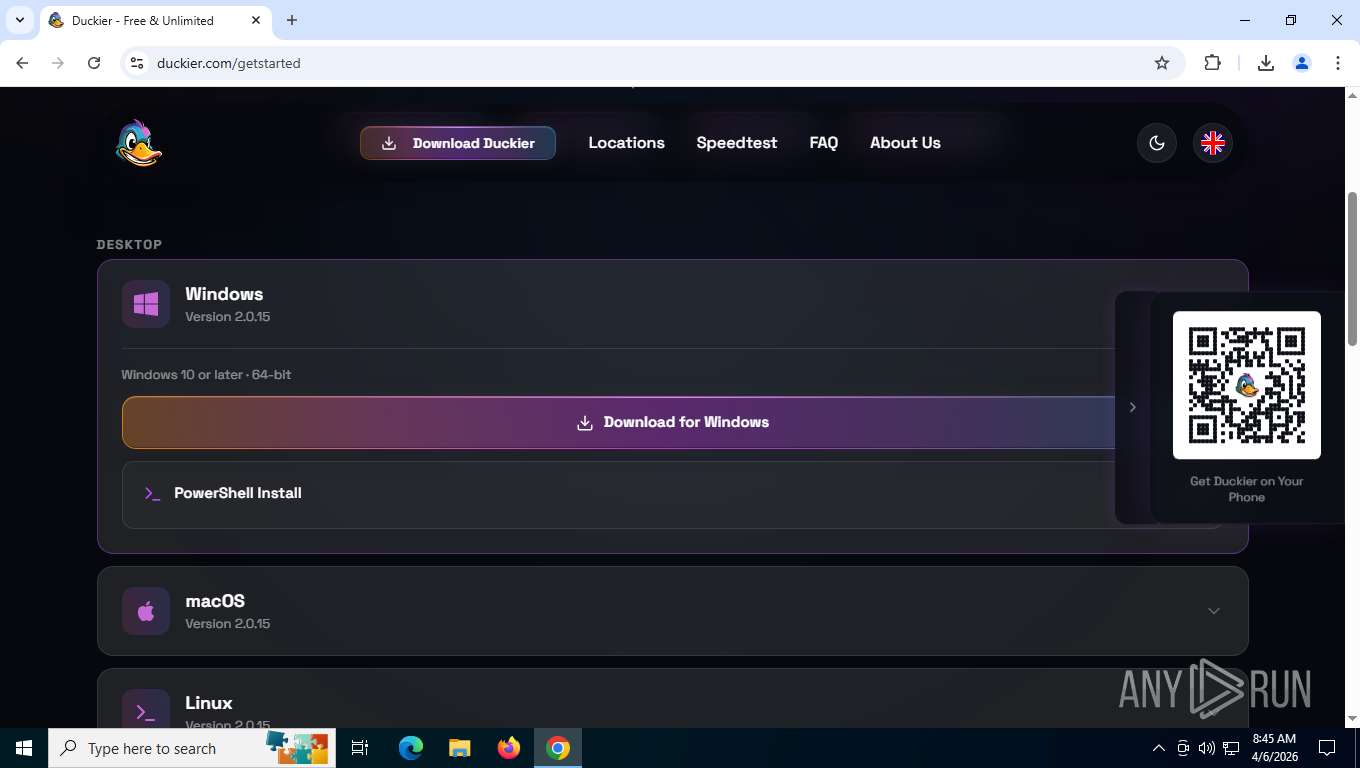
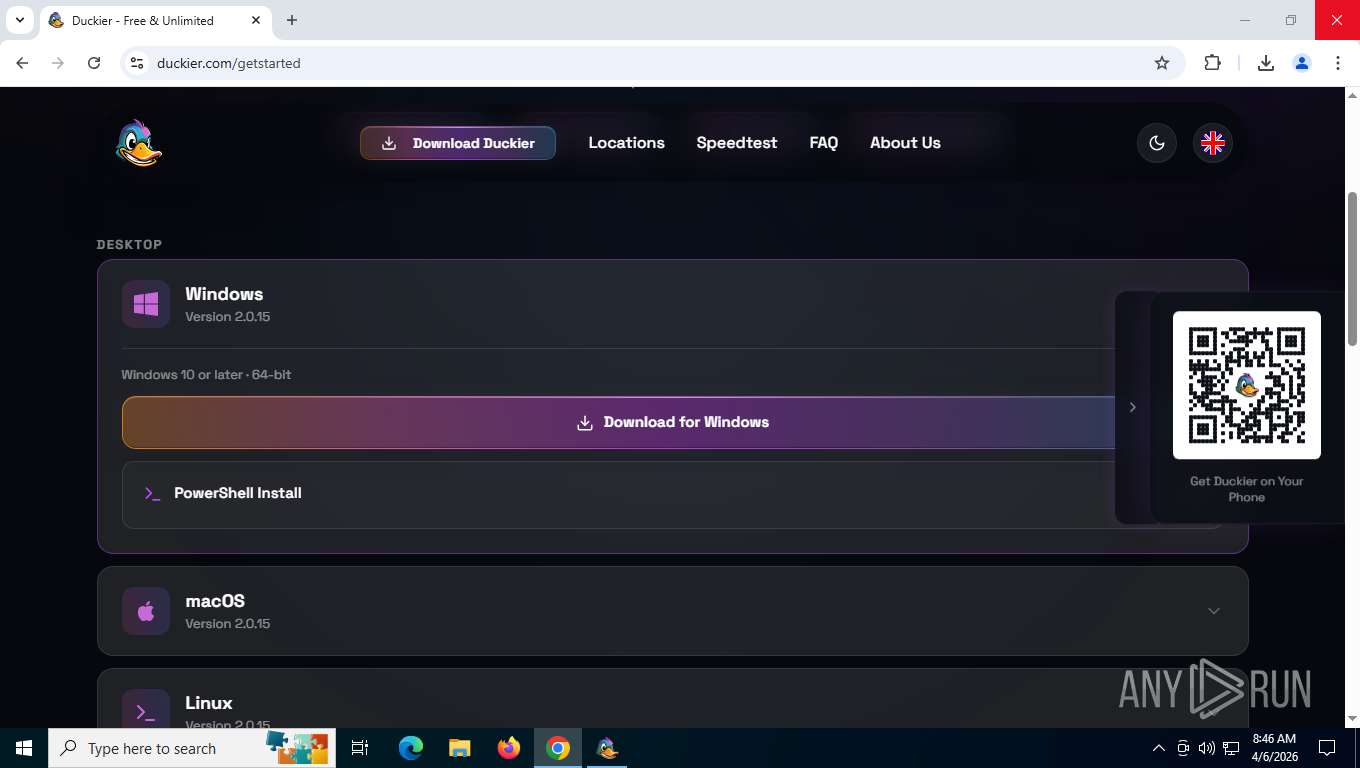
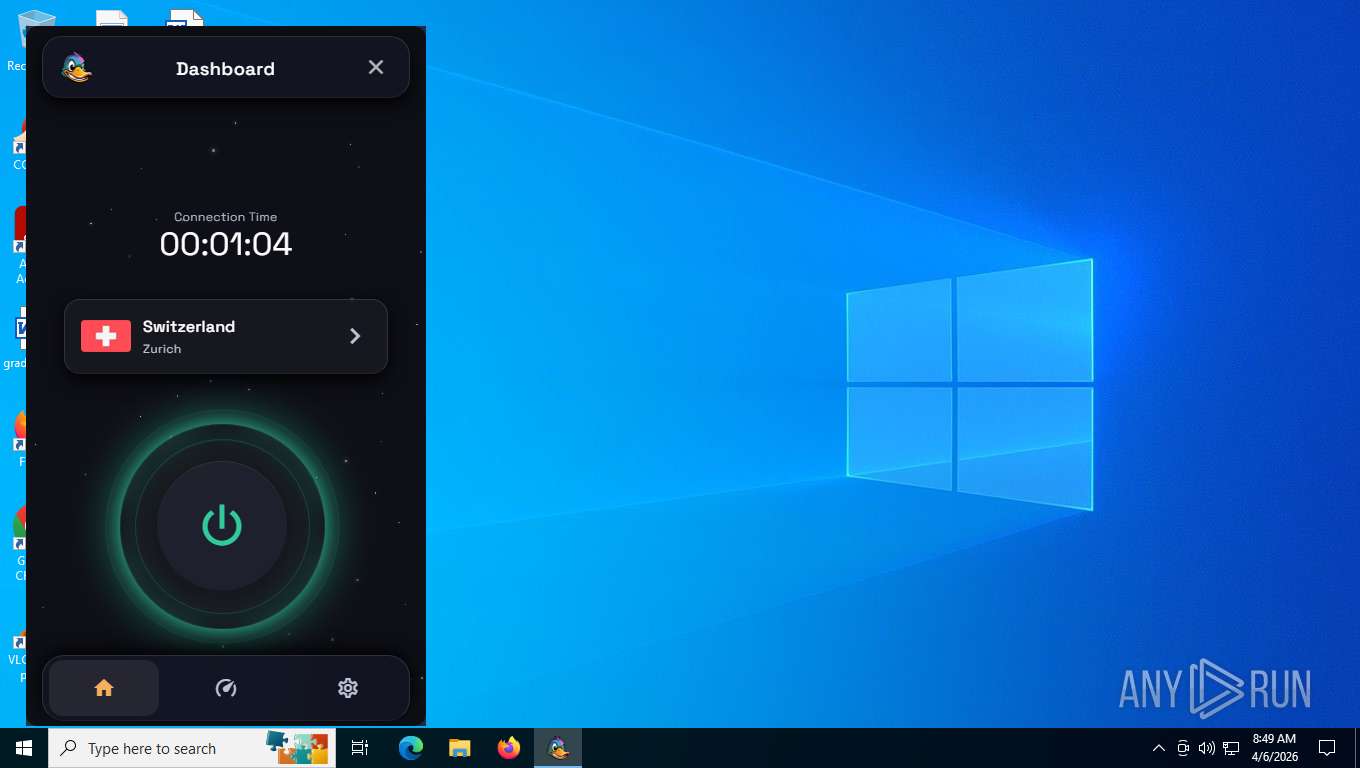
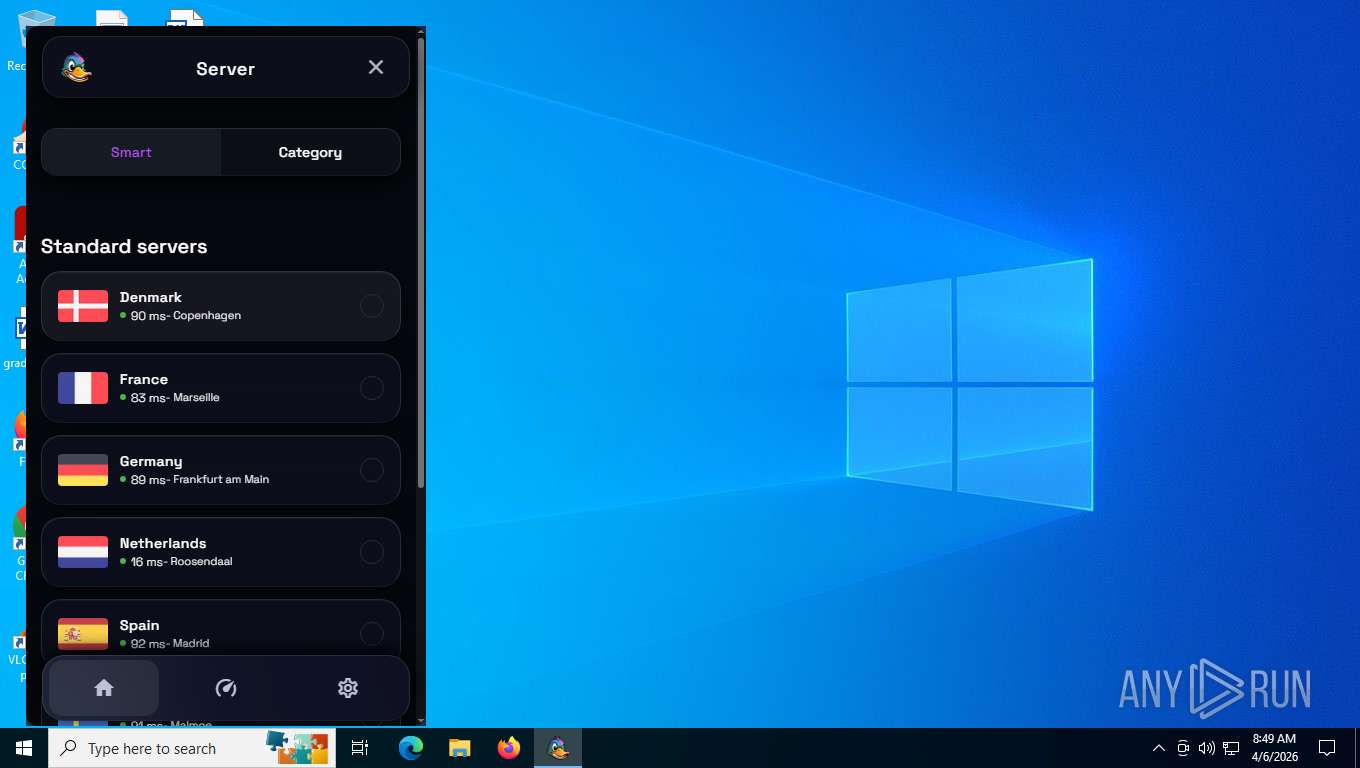
| URL: | duckier.com |
| Full analysis: | https://app.any.run/tasks/8a06cbaf-9fa6-4ff9-91c7-97ce93f06a8a |
| Verdict: | Malicious activity |
| Analysis date: | April 06, 2026, 12:45:22 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 51BFA09B99D6C44104E46A6198A9AE96 |
| SHA1: | 69AEF912122C7AC46A0A8DC06E5DB6F294891859 |
| SHA256: | BC74052A02CDEA18EA76255A3EE18E4F9AB3B021CCB892C1F892BD32B354C88F |
| SSDEEP: | 3:IddI:EI |
MALICIOUS
Scans artifacts that could help determine the target
- msedgewebview2.exe (PID: 2268)
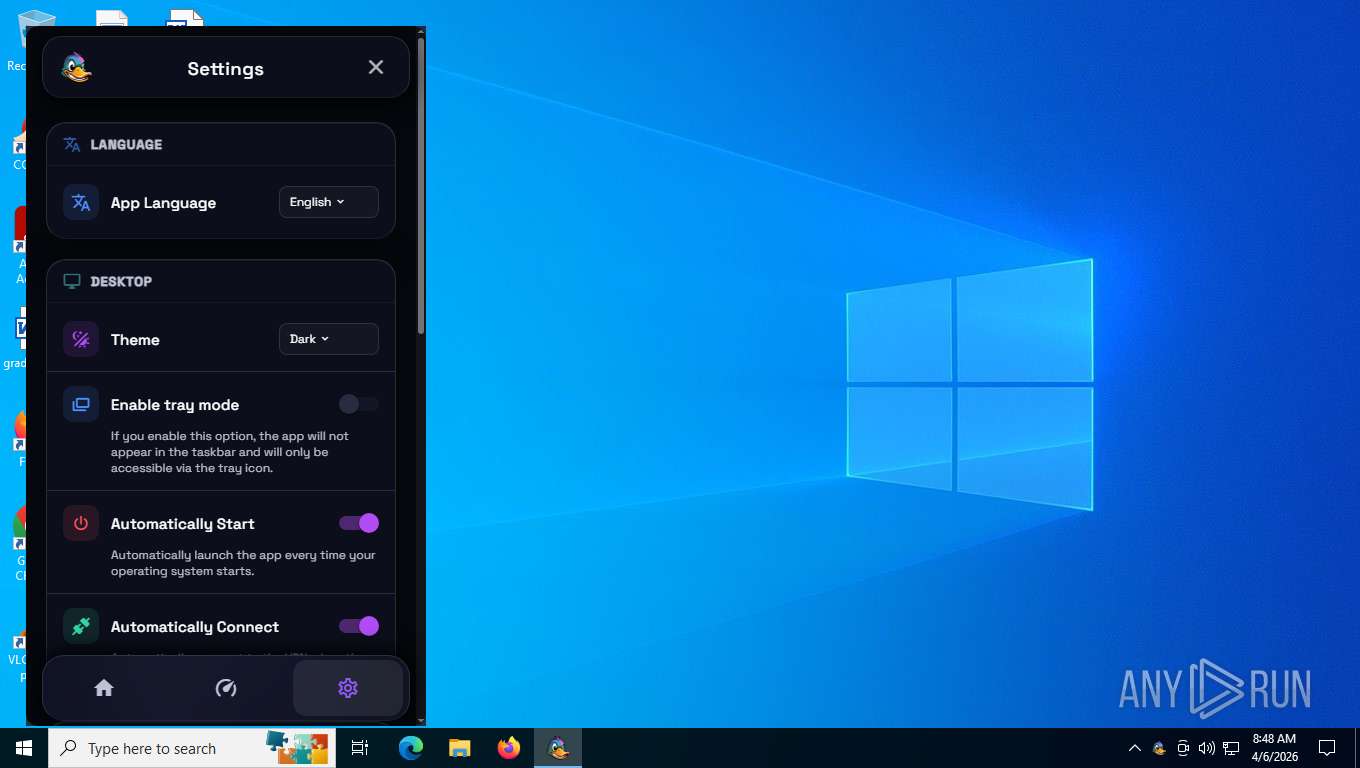
Changes the autorun value in the registry
- Duckier.exe (PID: 7760)
SUSPICIOUS
The process creates files with name similar to system file names
- duckier.exe (PID: 784)
Malware-specific behavior (creating "System.dll" in Temp)
- duckier.exe (PID: 784)
Searches for installed software
- duckier.exe (PID: 784)
- setup.exe (PID: 8368)
- msedgewebview2.exe (PID: 2268)
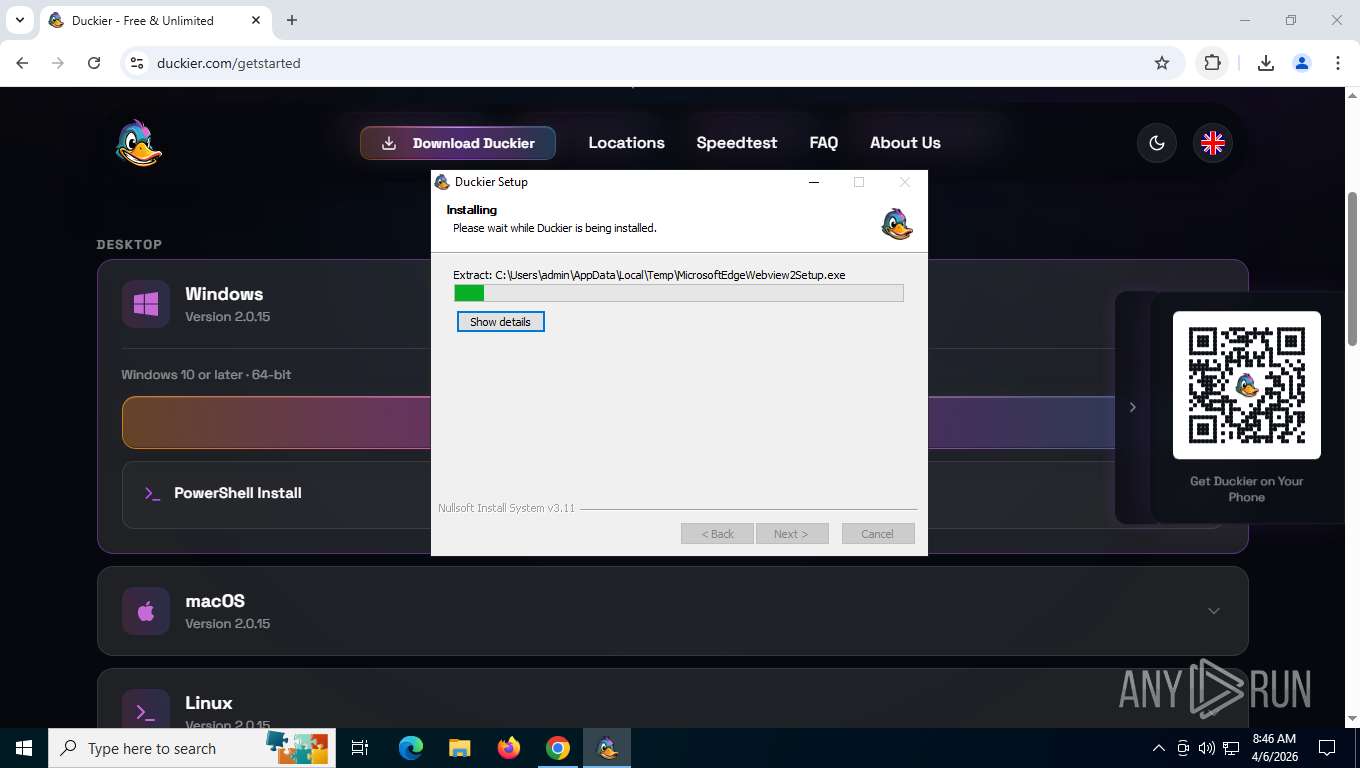
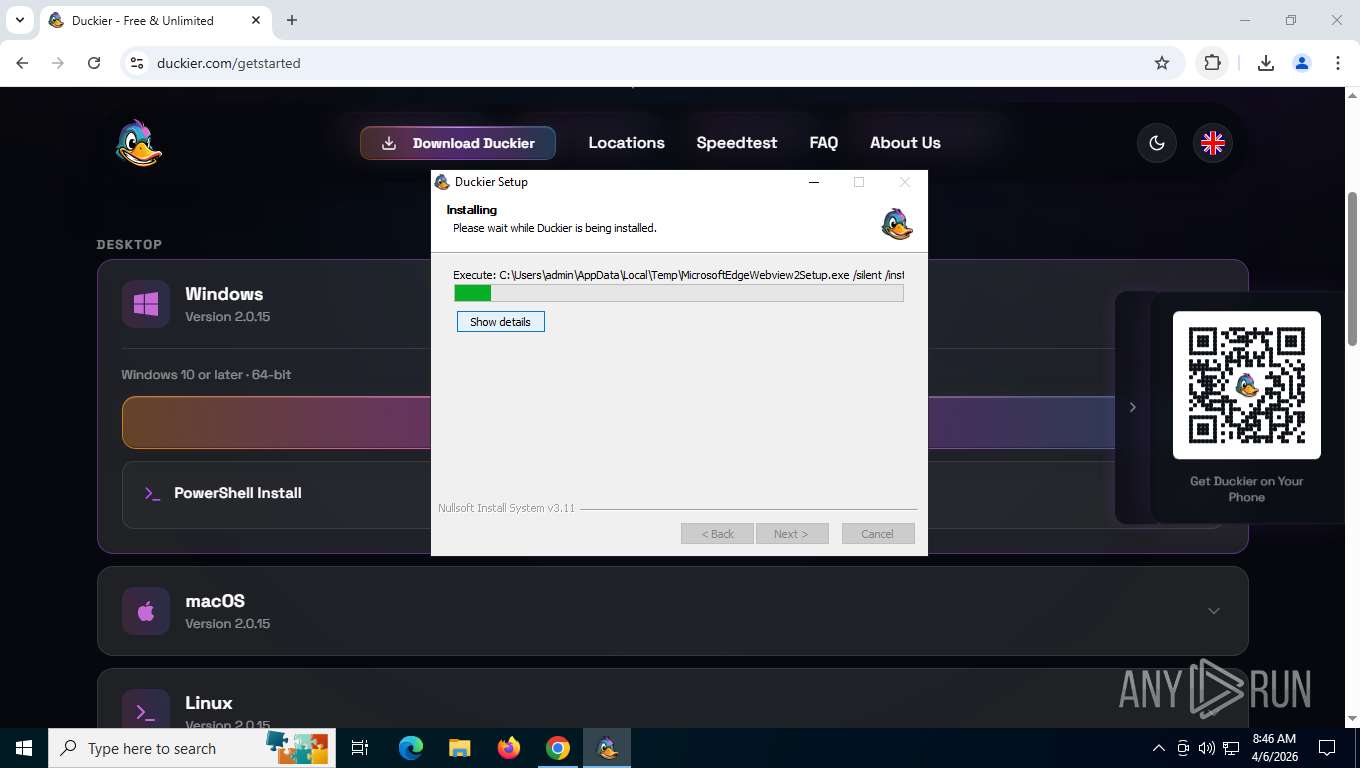
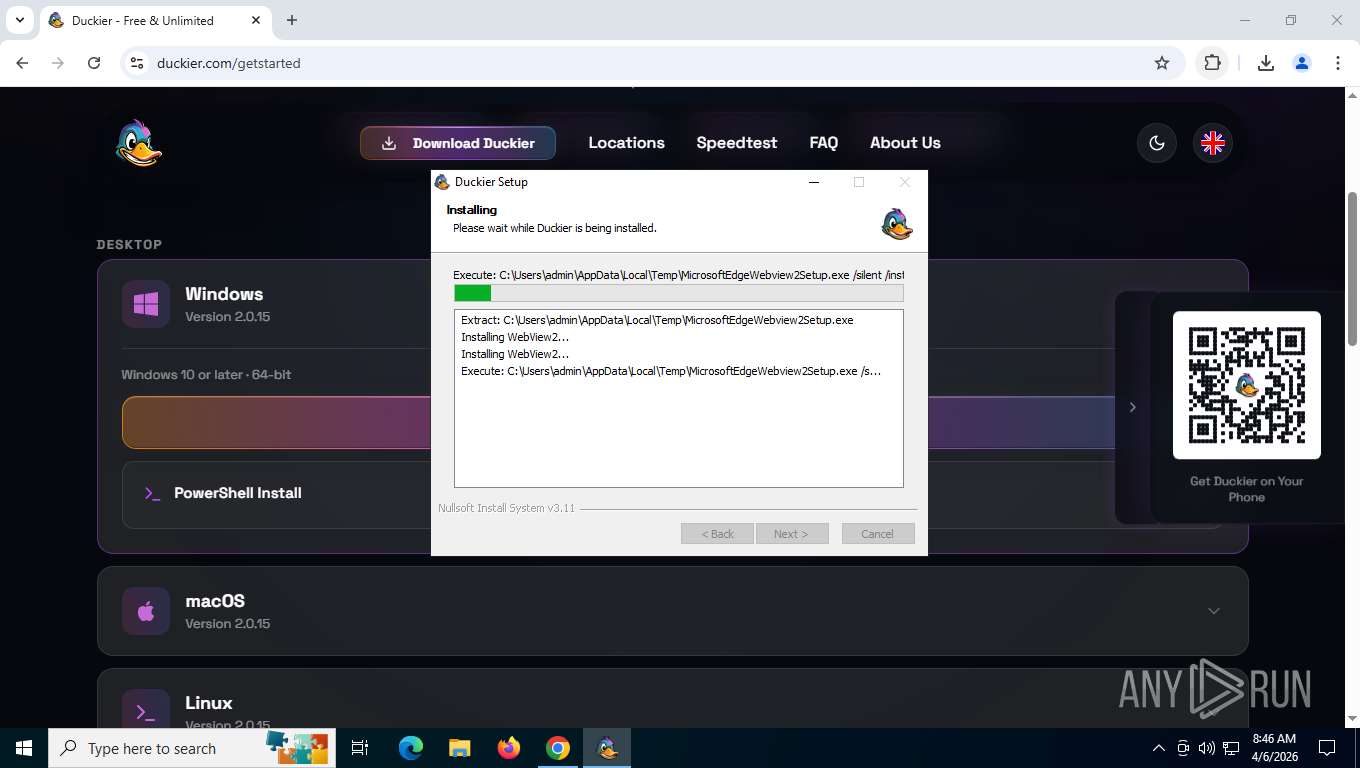
Starts a Microsoft application from unusual location
- MicrosoftEdgeWebview2Setup.exe (PID: 5660)
- MicrosoftEdgeUpdate.exe (PID: 7636)
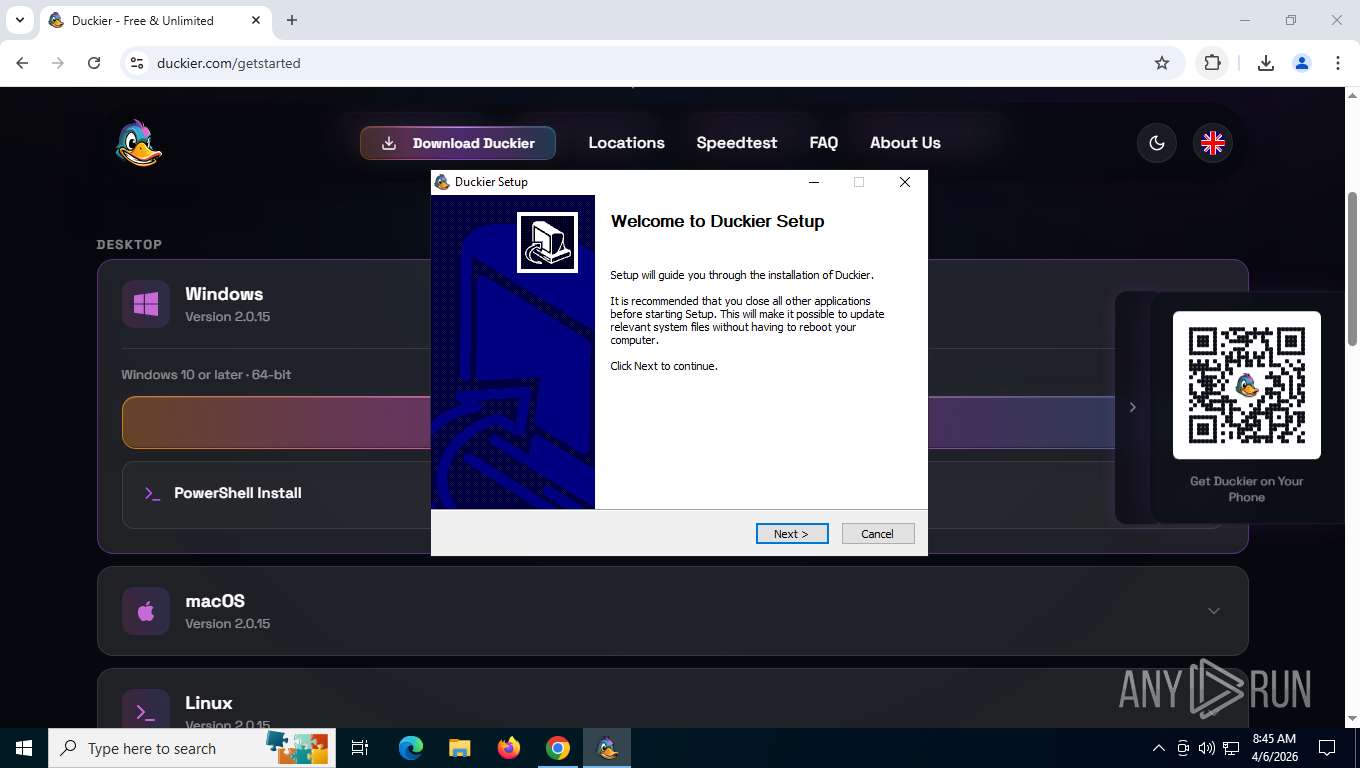
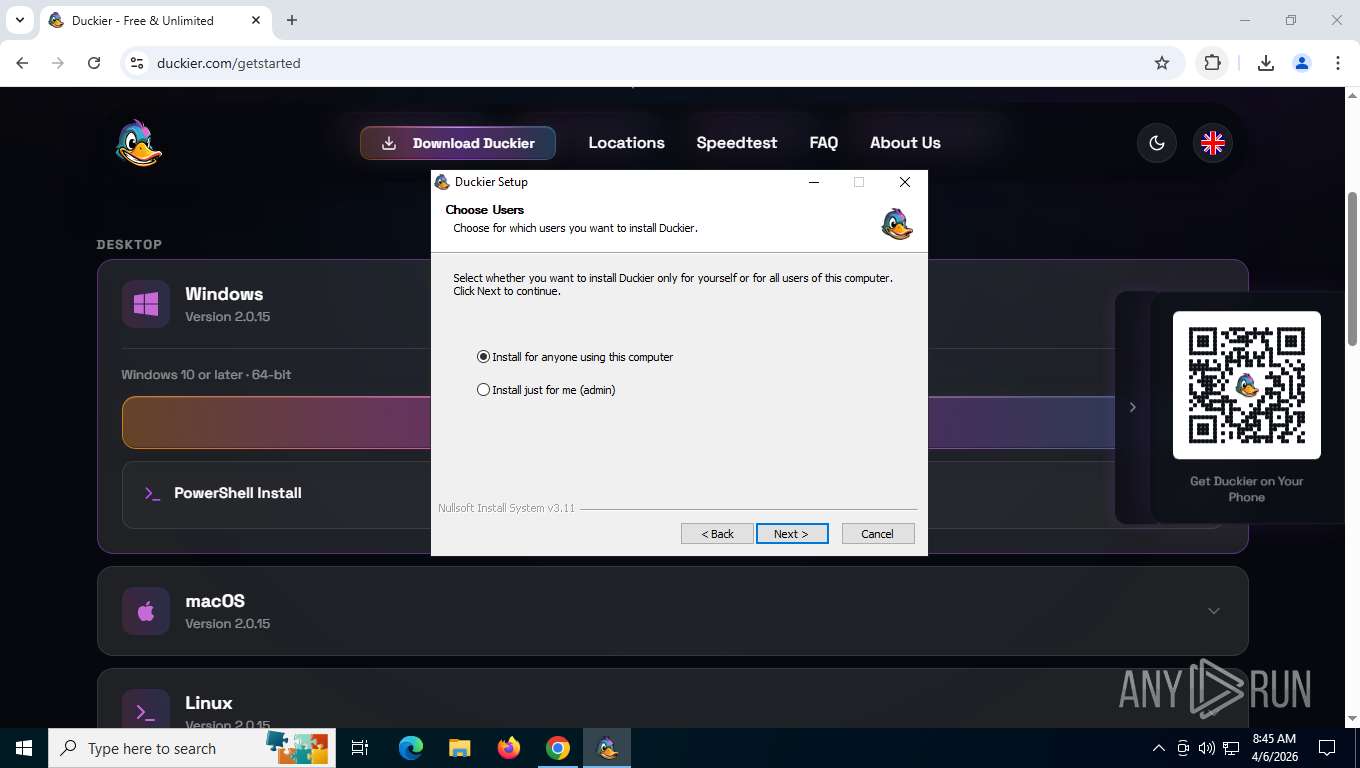
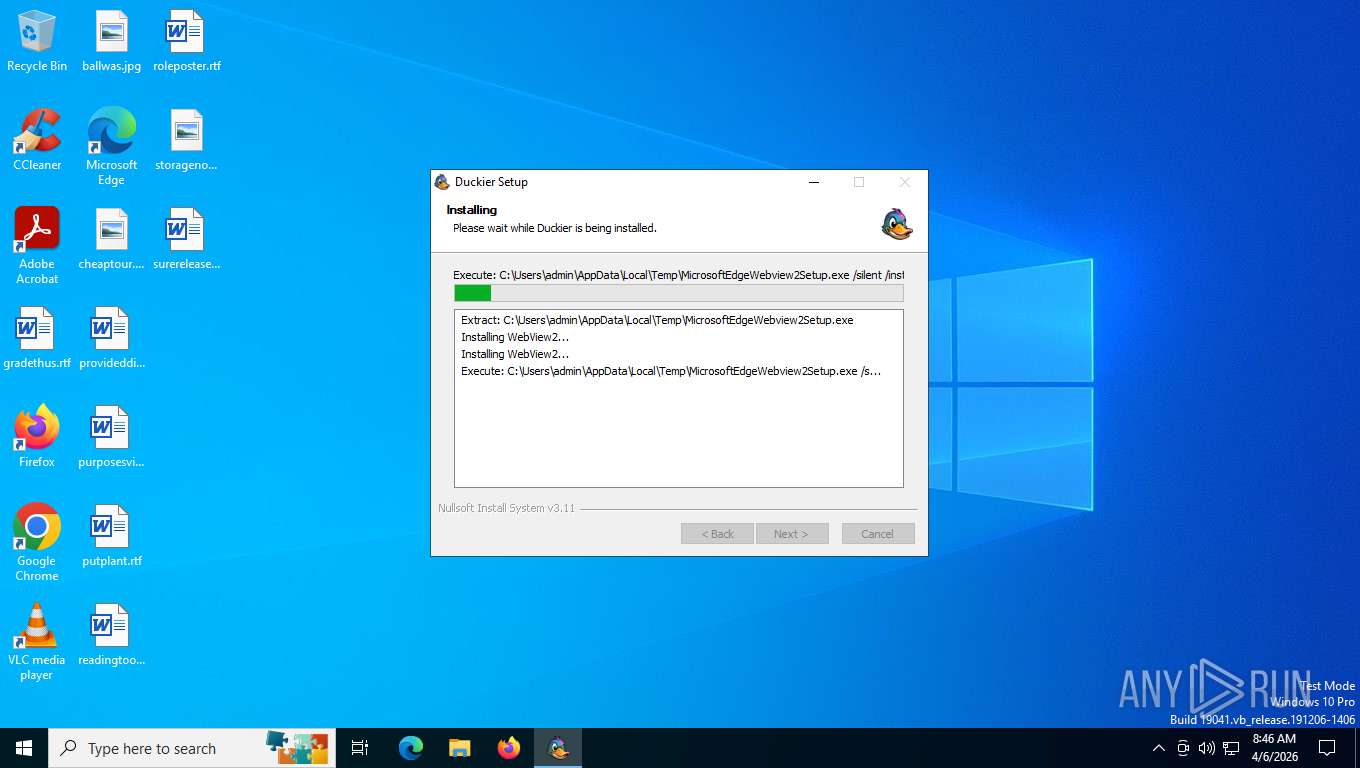
Silent install from TEMP directory
- duckier.exe (PID: 784)
Disables SEHOP
- MicrosoftEdgeUpdate.exe (PID: 7636)
Starts itself from another location
- MicrosoftEdgeUpdate.exe (PID: 7636)
Creates/Modifies COM task schedule object
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 6112)
- MicrosoftEdgeUpdate.exe (PID: 3448)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 2324)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 7868)
Executes as Windows Service
- MicrosoftEdgeUpdate.exe (PID: 2420)
- duckiervpn-daemon.exe (PID: 9104)
Application launched itself
- MicrosoftEdgeUpdate.exe (PID: 2420)
- msedgewebview2.exe (PID: 2268)
Uses TASKKILL.EXE to kill process
- duckier.exe (PID: 784)
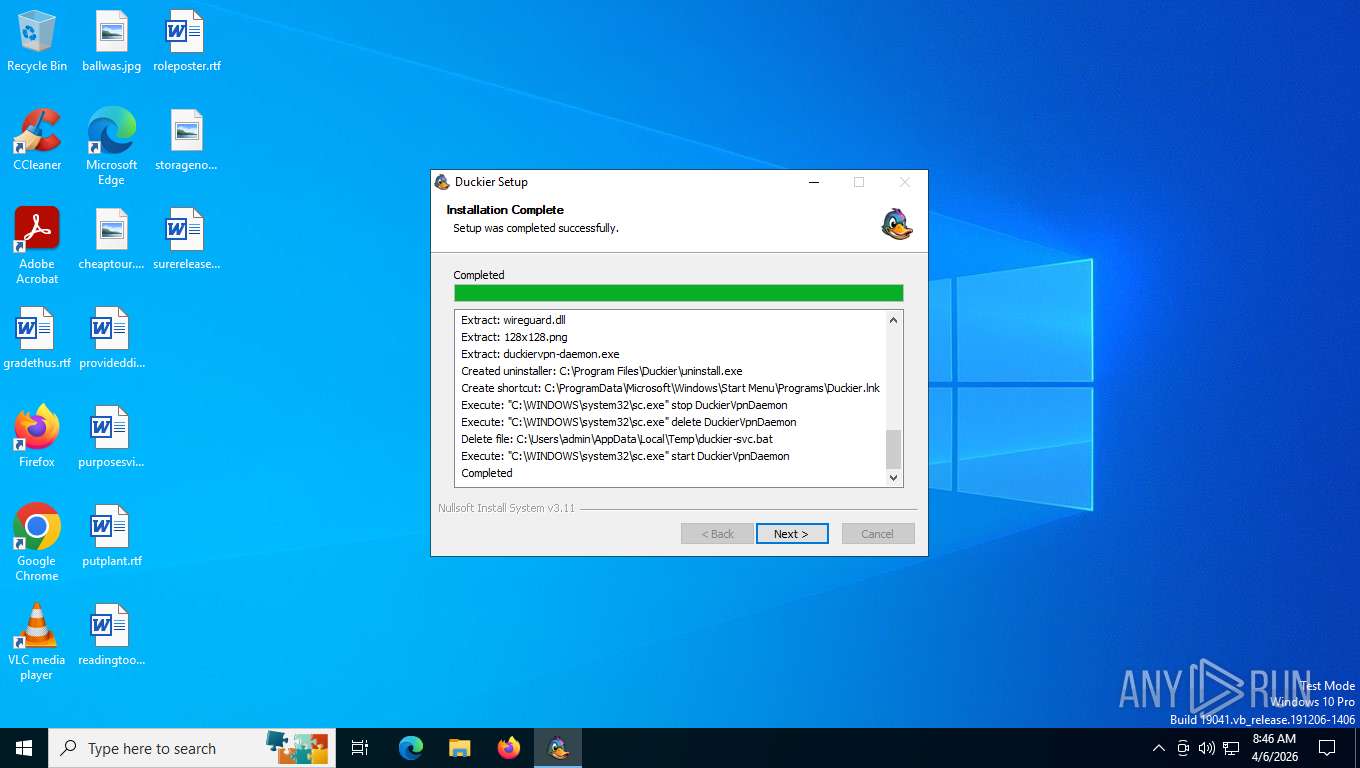
Stops a currently running service
- sc.exe (PID: 8776)
Deletes a service using sc.exe
- sc.exe (PID: 8852)
Windows service management via SC.EXE
- sc.exe (PID: 8852)
- sc.exe (PID: 9032)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 8924)
- cmd.exe (PID: 2332)
- cmd.exe (PID: 2160)
Creates a new Windows service
- sc.exe (PID: 8984)
Executing commands from a ".bat" file
- duckier.exe (PID: 784)
Restarts service on failure
- sc.exe (PID: 9004)
The process hide an interactive prompt from the user
- Duckier.exe (PID: 7760)
The process bypasses the loading of PowerShell profile settings
- Duckier.exe (PID: 7760)
Starts POWERSHELL.EXE for commands execution
- Duckier.exe (PID: 7760)
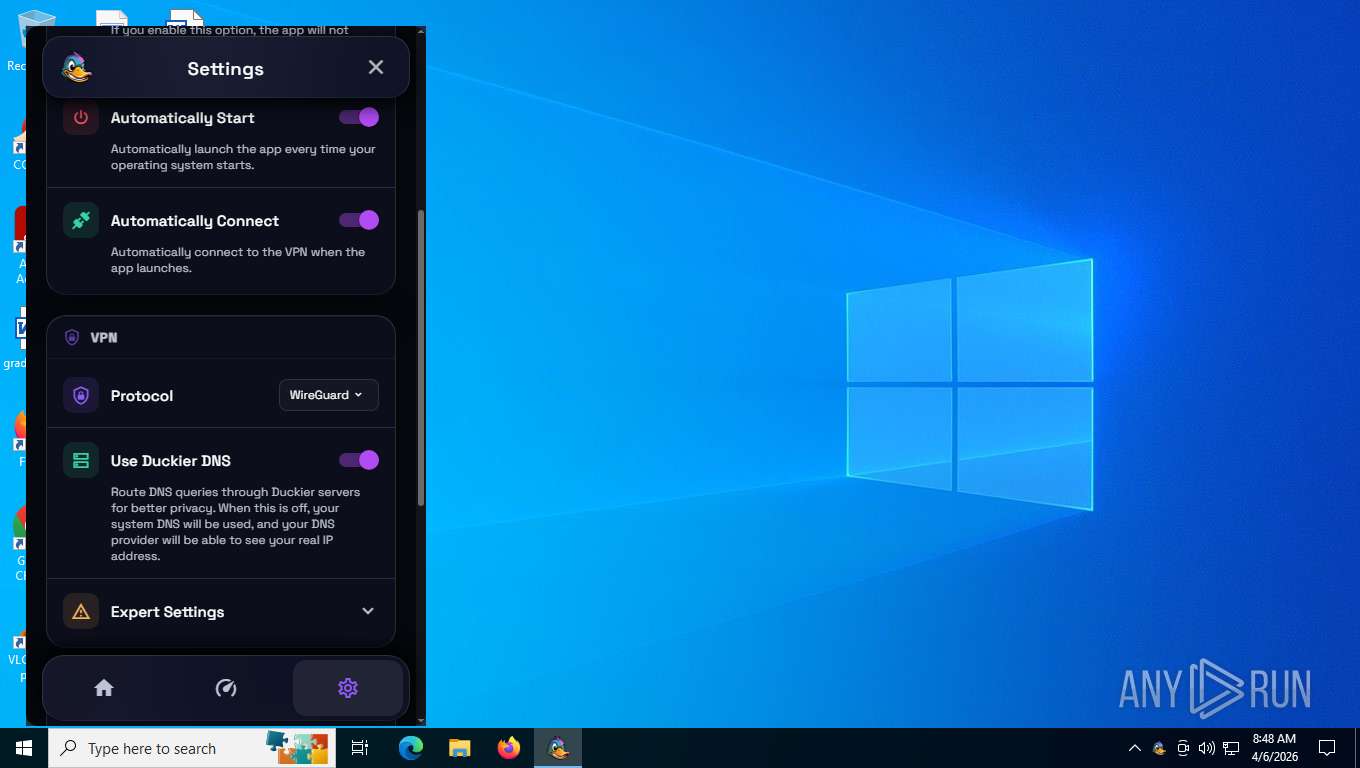
Drops a system driver (possible attempt to evade defenses)
- duckiervpn-daemon.exe (PID: 9104)
- drvinst.exe (PID: 8620)
Suspicious use of NETSH.EXE
- duckiervpn-daemon.exe (PID: 9104)
Gets system UUID (POWERSHELL)
- powershell.exe (PID: 1728)
- powershell.exe (PID: 1832)
INFO
Application launched itself
- chrome.exe (PID: 7260)
Launching a file from the Downloads directory
- chrome.exe (PID: 7260)
Checks supported languages
- duckier.exe (PID: 784)
- MicrosoftEdgeWebview2Setup.exe (PID: 5660)
- MicrosoftEdgeUpdate.exe (PID: 7636)
- MicrosoftEdgeUpdate.exe (PID: 1108)
- MicrosoftEdgeUpdate.exe (PID: 3448)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 6112)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 7868)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 2324)
- MicrosoftEdgeUpdate.exe (PID: 6272)
- MicrosoftEdgeUpdate.exe (PID: 8036)
- MicrosoftEdgeUpdate.exe (PID: 2420)
- MicrosoftEdgeUpdate.exe (PID: 7420)
- setup.exe (PID: 8368)
- MicrosoftEdge_X64_146.0.3856.97.exe (PID: 8348)
- MicrosoftEdgeUpdate.exe (PID: 8516)
- duckiervpn-daemon.exe (PID: 9104)
- msedgewebview2.exe (PID: 2268)
- msedgewebview2.exe (PID: 8176)
- Duckier.exe (PID: 7760)
- msedgewebview2.exe (PID: 6536)
- msedgewebview2.exe (PID: 1176)
- msedgewebview2.exe (PID: 2676)
- msedgewebview2.exe (PID: 2828)
- msedgewebview2.exe (PID: 5788)
- msedgewebview2.exe (PID: 8416)
- msedgewebview2.exe (PID: 5304)
- msedgewebview2.exe (PID: 3320)
- drvinst.exe (PID: 2420)
- msedgewebview2.exe (PID: 8476)
- drvinst.exe (PID: 8620)
Reads the computer name
- duckier.exe (PID: 784)
- MicrosoftEdgeUpdate.exe (PID: 7636)
- MicrosoftEdgeUpdate.exe (PID: 1108)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 6112)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 7868)
- MicrosoftEdgeUpdate.exe (PID: 6272)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 2324)
- MicrosoftEdgeUpdate.exe (PID: 8036)
- MicrosoftEdgeUpdate.exe (PID: 3448)
- MicrosoftEdgeUpdate.exe (PID: 2420)
- MicrosoftEdgeUpdate.exe (PID: 7420)
- MicrosoftEdge_X64_146.0.3856.97.exe (PID: 8348)
- setup.exe (PID: 8368)
- MicrosoftEdgeUpdate.exe (PID: 8516)
- duckiervpn-daemon.exe (PID: 9104)
- Duckier.exe (PID: 7760)
- msedgewebview2.exe (PID: 2268)
- msedgewebview2.exe (PID: 1176)
- msedgewebview2.exe (PID: 6536)
- drvinst.exe (PID: 8620)
- drvinst.exe (PID: 2420)
Create files in a temporary directory
- duckier.exe (PID: 784)
- MicrosoftEdgeUpdate.exe (PID: 7636)
- msedgewebview2.exe (PID: 2268)
Reads Environment values
- MicrosoftEdgeUpdate.exe (PID: 6272)
- MicrosoftEdgeUpdate.exe (PID: 7420)
- MicrosoftEdgeUpdate.exe (PID: 8516)
- msedgewebview2.exe (PID: 2268)
There is functionality for taking screenshot (YARA)
- duckier.exe (PID: 784)
Process checks computer location settings
- MicrosoftEdgeUpdate.exe (PID: 7636)
- setup.exe (PID: 8368)
- msedgewebview2.exe (PID: 2268)
- msedgewebview2.exe (PID: 2828)
Reads security settings of Internet Explorer
- MicrosoftEdgeUpdate.exe (PID: 7636)
- msedgewebview2.exe (PID: 2268)
Creates a software uninstall entry
- setup.exe (PID: 8368)
- duckier.exe (PID: 784)
Application based on Rust
- duckiervpn-daemon.exe (PID: 9104)
Creates files or folders in the user directory
- msedgewebview2.exe (PID: 2268)
- msedgewebview2.exe (PID: 8176)
- Duckier.exe (PID: 7760)
- msedgewebview2.exe (PID: 6536)
Reads CPU info
- msedgewebview2.exe (PID: 2268)
Reads the machine GUID from the registry
- msedgewebview2.exe (PID: 2268)
- Duckier.exe (PID: 7760)
- drvinst.exe (PID: 8620)
Launching a file from a Registry key
- Duckier.exe (PID: 7760)
Checks operating system version
- Duckier.exe (PID: 7760)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
241
Monitored processes
89
Malicious processes
4
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 508 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=4832,i,16371395990919609586,13859720529030905590,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=5948 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 784 | "C:\Users\admin\Downloads\duckier.exe" | C:\Users\admin\Downloads\duckier.exe | chrome.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Duckier Exit code: 0 Version: 2.0.15 Modules
| |||||||||||||||
| 1108 | "C:\Program Files (x86)\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe" /regsvc | C:\Program Files (x86)\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe | — | MicrosoftEdgeUpdate.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Update Exit code: 0 Version: 1.3.225.7 Modules
| |||||||||||||||
| 1152 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=8 --field-trial-handle=4340,i,16371395990919609586,13859720529030905590,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=3624 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1176 | "C:\Program Files (x86)\Microsoft\EdgeWebView\Application\146.0.3856.97\msedgewebview2.exe" --type=gpu-process --noerrdialogs --user-data-dir="C:\Users\admin\AppData\Local\com.duckier.app\EBWebView" --webview-exe-name=Duckier.exe --webview-exe-version=2.0.15 --embedded-browser-webview=1 --embedded-browser-webview-dpi-awareness=2 --gpu-preferences=SAAAAAAAAADgAAAEAAAAAAAAAAAAAGAAAQAAAAAAAAAAAAAAAAAAAAIAAAAAAAAAAAAAAAAAAAAQAAAAAAAAABAAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --startup-read-main-dll --metrics-shmem-handle=1712,i,3150033741811533945,6600588214627543526,262144 --field-trial-handle=1848,i,14261739105767078715,5351185638868997389,262144 --disable-features=msPdfOOUI,msSmartScreenProtection,msWebOOUI --variations-seed-version --pseudonymization-salt-handle=1852,i,1911819240387968130,6619922344327694527,4 --trace-process-track-uuid=3190708988185955192 --mojo-platform-channel-handle=1824 /prefetch:2 | C:\Program Files (x86)\Microsoft\EdgeWebView\Application\146.0.3856.97\msedgewebview2.exe | — | msedgewebview2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge WebView2 Version: 146.0.3856.97 Modules
| |||||||||||||||
| 1280 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --extension-process --enable-dinosaur-easter-egg-alt-images --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=7 --field-trial-handle=4104,i,16371395990919609586,13859720529030905590,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=4120 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1400 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --field-trial-handle=5144,i,16371395990919609586,13859720529030905590,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=5684 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1728 | "powershell" -NoProfile -NonInteractive -Command "(Get-CimInstance -ClassName Win32_ComputerSystemProduct).UUID" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | Duckier.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1780 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1832 | "powershell" -NoProfile -NonInteractive -Command "(Get-CimInstance -ClassName Win32_ComputerSystemProduct).UUID" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | Duckier.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
33 445
Read events
31 667
Write events
1 646
Delete events
132
Modification events
| (PID) Process: | (2724) slui.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\3d\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\System32\sppcomapi.dll,-3200 |
Value: Software Licensing | |||
| (PID) Process: | (1108) MicrosoftEdgeUpdate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\AppID\{A6B716CB-028B-404D-B72C-50E153DD68DA} |
| Operation: | write | Name: | ServiceParameters |
Value: /comsvc | |||
| (PID) Process: | (1108) MicrosoftEdgeUpdate.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\EventLog\Application\edgeupdatem |
| Operation: | write | Name: | EventMessageFile |
Value: C:\Program Files (x86)\Microsoft\EdgeUpdate\1.3.225.7\msedgeupdate.dll | |||
| (PID) Process: | (1108) MicrosoftEdgeUpdate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\CLSID\{A6B716CB-028B-404D-B72C-50E153DD68DA}\ProgID |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (1108) MicrosoftEdgeUpdate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\CLSID\{A6B716CB-028B-404D-B72C-50E153DD68DA}\VersionIndependentProgID |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (1108) MicrosoftEdgeUpdate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\CLSID\{A6B716CB-028B-404D-B72C-50E153DD68DA} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (1108) MicrosoftEdgeUpdate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\CLSID\{A6B716CB-028B-404D-B72C-50E153DD68DA} |
| Operation: | write | Name: | AppID |
Value: {A6B716CB-028B-404D-B72C-50E153DD68DA} | |||
| (PID) Process: | (1108) MicrosoftEdgeUpdate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\CLSID\{EA92A799-267E-4DF5-A6ED-6A7E0684BB8A}\ProgID |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (1108) MicrosoftEdgeUpdate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\CLSID\{EA92A799-267E-4DF5-A6ED-6A7E0684BB8A}\VersionIndependentProgID |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (1108) MicrosoftEdgeUpdate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\CLSID\{EA92A799-267E-4DF5-A6ED-6A7E0684BB8A} |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
0
Suspicious files
21
Text files
69
Unknown types
845
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7260 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old~RFe04af.TMP | — | |
MD5:— | SHA256:— | |||
| 7260 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7260 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old~RFe04ce.TMP | — | |
MD5:— | SHA256:— | |||
| 7260 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\LOG.old~RFe04de.TMP | — | |
MD5:— | SHA256:— | |||
| 7260 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RFe04de.TMP | — | |
MD5:— | SHA256:— | |||
| 7260 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RFe04de.TMP | — | |
MD5:— | SHA256:— | |||
| 7260 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7260 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7260 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7260 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
157
TCP/UDP connections
103
DNS requests
97
Threats
13
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7844 | chrome.exe | GET | 200 | 188.114.96.3:443 | https://duckier.com/ | US | binary | 123 Kb | unknown |
7844 | chrome.exe | GET | 200 | 142.251.110.139:80 | http://clients2.google.com/time/1/current?cup2key=8:51ncJH1konFy3vugrYGC5WyEDwvSIWhMpcZgmLVT-0g&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | binary | 105 b | whitelisted |
7844 | chrome.exe | GET | 200 | 188.114.96.3:443 | https://duckier.com/css/duckier.css?v=5 | US | binary | 125 Kb | unknown |
7844 | chrome.exe | GET | 200 | 188.114.96.3:443 | https://duckier.com/css/style.css | US | binary | 23.3 Kb | unknown |
7844 | chrome.exe | GET | 200 | 188.114.96.3:443 | https://duckier.com/css/duckier-page.css?v=11 | US | binary | 565 Kb | unknown |
7844 | chrome.exe | GET | 200 | 188.114.96.3:443 | https://duckier.com/css/misc.css | US | binary | 8.20 Kb | unknown |
7844 | chrome.exe | GET | 200 | 188.114.96.3:443 | https://duckier.com/js/duckier-particles.js | US | binary | 5.59 Kb | unknown |
7844 | chrome.exe | GET | 200 | 188.114.96.3:443 | https://duckier.com/js/app.js?12 | US | binary | 3.35 Kb | unknown |
7844 | chrome.exe | GET | 200 | 188.114.96.3:443 | https://duckier.com/js/jquery.paging.js | US | binary | 18.9 Kb | unknown |
7844 | chrome.exe | GET | 200 | 188.114.96.3:443 | https://duckier.com/js/jquery.cookie.js | US | binary | 3.05 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
6260 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5276 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 92.123.104.67:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
8028 | slui.exe | 48.192.1.65:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
7844 | chrome.exe | 142.251.110.139:80 | clients2.google.com | GOOGLE | US | whitelisted |
7844 | chrome.exe | 192.178.183.95:443 | safebrowsingohttpgateway.googleapis.com | GOOGLE | US | whitelisted |
7844 | chrome.exe | 142.251.127.94:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
7844 | chrome.exe | 142.251.127.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
duckier.com |
| unknown |
accounts.google.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7844 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
7844 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
7844 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Global content delivery network (unpkg .com) |
7844 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Global content delivery network (unpkg .com) |
7844 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Global content delivery network (unpkg .com) |
7844 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Global content delivery network (unpkg .com) |
7844 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
7844 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Global content delivery network (unpkg .com) |
7844 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Global content delivery network (unpkg .com) |
7844 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
Process | Message |
|---|---|
msedgewebview2.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\com.duckier.app directory exists )
|