| File name: | var32.exe |
| Full analysis: | https://app.any.run/tasks/4f43c2ef-aaa1-4f68-abab-940dbf13907d |
| Verdict: | Malicious activity |
| Analysis date: | May 21, 2022, 10:46:58 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | C79BDB9EA133F2C2BFB14D8C9BF0A14B |
| SHA1: | 9CB6B03F8791EBAACA9C539AC89EF6A8DD556F61 |
| SHA256: | BC6D17AF4BE4AE752C7242DEDC2AB07C095143C58A8B5E7F441D9C2A7E813F62 |
| SSDEEP: | 6144:6p8I+IqVK0a2k4u/DU+iHvXTeP4kMY1XeQS:0P+rKokNDTEiPfXL |
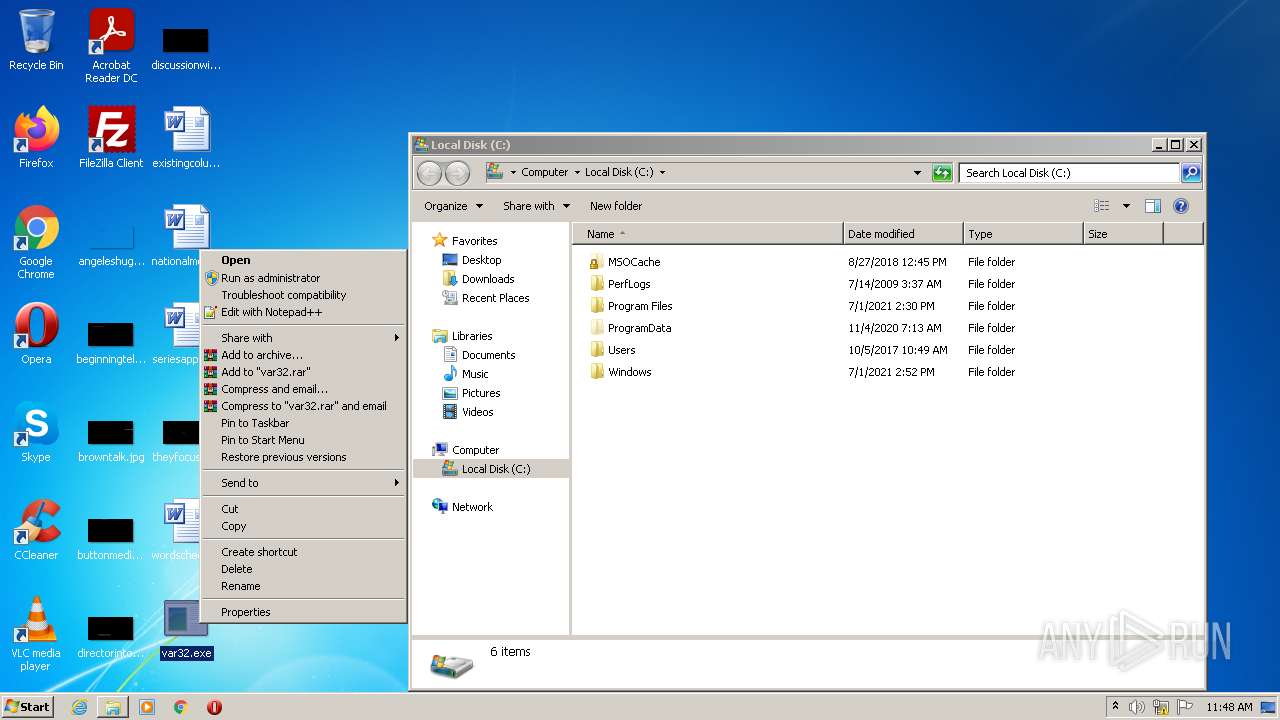
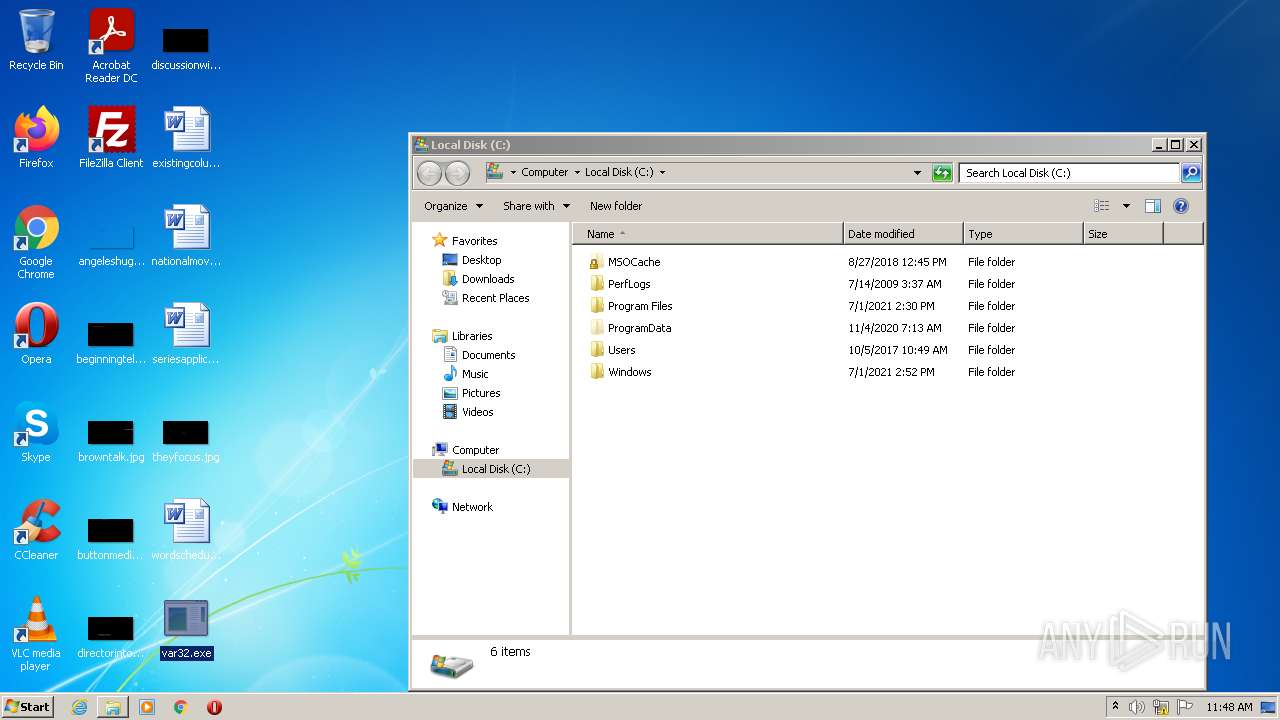
MALICIOUS
Runs injected code in another process
- var32.exe (PID: 880)
Application was injected by another process
- Explorer.EXE (PID: 1464)
Drops executable file immediately after starts
- Explorer.EXE (PID: 1464)
Changes the login/logoff helper path in the registry
- Explorer.EXE (PID: 1464)
SUSPICIOUS
Checks supported languages
- var32.exe (PID: 2952)
- var32.exe (PID: 880)
- var32.exe (PID: 2496)
- var32.exe (PID: 3228)
- var32.exe (PID: 2740)
- var32.exe (PID: 280)
- var32.exe (PID: 2660)
- var32.exe (PID: 4048)
- var32.exe (PID: 296)
- var32.exe (PID: 1864)
Reads the computer name
- var32.exe (PID: 880)
- var32.exe (PID: 3228)
- var32.exe (PID: 280)
- var32.exe (PID: 296)
- var32.exe (PID: 1864)
Application launched itself
- var32.exe (PID: 2952)
- var32.exe (PID: 2496)
- var32.exe (PID: 2740)
- var32.exe (PID: 4048)
- var32.exe (PID: 2660)
Executable content was dropped or overwritten
- Explorer.EXE (PID: 1464)
Drops a file with a compile date too recent
- Explorer.EXE (PID: 1464)
Reads default file associations for system extensions
- Explorer.EXE (PID: 1464)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| ProductVersion: | 1, 0, 4, 0 |
|---|---|
| OriginalFileName: | incognito.exe |
| InternalName: | incognito.exe |
| FileVersion: | 1, 0, 4, 0 |
| FileDescription: | ESET NOD32 and Sophos are a bunch of faggots! |
| CompanyName: | RTFLOL & MarjinZ |
| Comments: | You should replace this version information with your own custom one. |
| CharacterSet: | Unicode |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.0.4.0 |
| FileVersionNumber: | 1.0.4.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 5 |
| ImageVersion: | - |
| OSVersion: | 5 |
| EntryPoint: | 0x7cce |
| UninitializedDataSize: | - |
| InitializedDataSize: | 194048 |
| CodeSize: | 62464 |
| LinkerVersion: | 9 |
| PEType: | PE32 |
| TimeStamp: | 2010:03:28 14:14:22+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 28-Mar-2010 12:14:22 |
| Detected languages: |
|
| Comments: | You should replace this version information with your own custom one. |
| CompanyName: | RTFLOL & MarjinZ |
| FileDescription: | ESET NOD32 and Sophos are a bunch of faggots! |
| FileVersion: | 1, 0, 4, 0 |
| InternalName: | incognito.exe |
| OriginalFilename: | incognito.exe |
| ProductVersion: | 1, 0, 4, 0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 28-Mar-2010 12:14:22 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000F057 | 0x0000F200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.47412 |
.text1 | 0x00011000 | 0x00000028 | 0x00000200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 0.691177 |
.rdata | 0x00012000 | 0x000105D6 | 0x00010600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.91831 |
.data | 0x00023000 | 0x00004644 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.63061 |
.rsrc | 0x00028000 | 0x0001DAA4 | 0x0001DC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.9256 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.40262 | 828 | Latin 1 / Western European | English - United States | RT_VERSION |
2 | 7.84494 | 1231 | Latin 1 / Western European | Hindi - India | VJ80 |
3 | 7.83308 | 1231 | Latin 1 / Western European | Hindi - India | VJ80 |
4 | 7.83685 | 1231 | Latin 1 / Western European | Hindi - India | VJ80 |
5 | 7.84654 | 1231 | Latin 1 / Western European | Hindi - India | VJ80 |
6 | 7.86117 | 1231 | Latin 1 / Western European | Hindi - India | VJ80 |
7 | 7.85319 | 1231 | Latin 1 / Western European | Hindi - India | VJ80 |
8 | 7.83796 | 1231 | Latin 1 / Western European | Hindi - India | VJ80 |
9 | 7.82773 | 1231 | Latin 1 / Western European | Hindi - India | VJ80 |
10 | 7.85169 | 1231 | Latin 1 / Western European | Hindi - India | VJ80 |
Imports
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
46
Monitored processes
11
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 280 | "C:\Users\admin\Desktop\var32.exe" | C:\Users\admin\Desktop\var32.exe | — | var32.exe | |||||||||||
User: admin Company: RTFLOL & MarjinZ Integrity Level: MEDIUM Description: ESET NOD32 and Sophos are a bunch of faggots! Exit code: 0 Version: 1, 0, 4, 0 Modules
| |||||||||||||||
| 296 | "C:\Users\admin\Desktop\var32.exe" | C:\Users\admin\Desktop\var32.exe | — | var32.exe | |||||||||||
User: admin Company: RTFLOL & MarjinZ Integrity Level: MEDIUM Description: ESET NOD32 and Sophos are a bunch of faggots! Exit code: 0 Version: 1, 0, 4, 0 Modules
| |||||||||||||||
| 880 | "C:\Users\admin\Desktop\var32.exe" | C:\Users\admin\Desktop\var32.exe | — | var32.exe | |||||||||||
User: admin Company: RTFLOL & MarjinZ Integrity Level: MEDIUM Description: ESET NOD32 and Sophos are a bunch of faggots! Exit code: 0 Version: 1, 0, 4, 0 Modules
| |||||||||||||||
| 1464 | C:\Windows\Explorer.EXE | C:\Windows\Explorer.EXE | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1864 | "C:\Users\admin\Desktop\var32.exe" | C:\Users\admin\Desktop\var32.exe | — | var32.exe | |||||||||||
User: admin Company: RTFLOL & MarjinZ Integrity Level: HIGH Description: ESET NOD32 and Sophos are a bunch of faggots! Exit code: 0 Version: 1, 0, 4, 0 Modules
| |||||||||||||||
| 2496 | "C:\Users\admin\Desktop\var32.exe" | C:\Users\admin\Desktop\var32.exe | Explorer.EXE | ||||||||||||
User: admin Company: RTFLOL & MarjinZ Integrity Level: MEDIUM Description: ESET NOD32 and Sophos are a bunch of faggots! Exit code: 0 Version: 1, 0, 4, 0 Modules
| |||||||||||||||
| 2660 | "C:\Users\admin\Desktop\var32.exe" | C:\Users\admin\Desktop\var32.exe | Explorer.EXE | ||||||||||||
User: admin Company: RTFLOL & MarjinZ Integrity Level: MEDIUM Description: ESET NOD32 and Sophos are a bunch of faggots! Exit code: 0 Version: 1, 0, 4, 0 Modules
| |||||||||||||||
| 2740 | "C:\Users\admin\Desktop\var32.exe" | C:\Users\admin\Desktop\var32.exe | Explorer.EXE | ||||||||||||
User: admin Company: RTFLOL & MarjinZ Integrity Level: MEDIUM Description: ESET NOD32 and Sophos are a bunch of faggots! Exit code: 0 Version: 1, 0, 4, 0 Modules
| |||||||||||||||
| 2952 | "C:\Users\admin\Desktop\var32.exe" | C:\Users\admin\Desktop\var32.exe | Explorer.EXE | ||||||||||||
User: admin Company: RTFLOL & MarjinZ Integrity Level: MEDIUM Description: ESET NOD32 and Sophos are a bunch of faggots! Exit code: 0 Version: 1, 0, 4, 0 Modules
| |||||||||||||||
| 3228 | "C:\Users\admin\Desktop\var32.exe" | C:\Users\admin\Desktop\var32.exe | — | var32.exe | |||||||||||
User: admin Company: RTFLOL & MarjinZ Integrity Level: MEDIUM Description: ESET NOD32 and Sophos are a bunch of faggots! Exit code: 0 Version: 1, 0, 4, 0 Modules
| |||||||||||||||
Total events
5 489
Read events
5 439
Write events
50
Delete events
0
Modification events
| (PID) Process: | (1464) Explorer.EXE | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 0202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (1464) Explorer.EXE | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 01000000020000000D0000000C000000000000000B00000007000000060000000A0000000900000008000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (1464) Explorer.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Toolbar |
| Operation: | write | Name: | Locked |
Value: 1 | |||
| (PID) Process: | (1464) Explorer.EXE | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\34\Shell |
| Operation: | write | Name: | SniffedFolderType |
Value: Generic | |||
| (PID) Process: | (1464) Explorer.EXE | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1464) Explorer.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Winlogon |
| Operation: | write | Name: | Shell |
Value: explorer.exe,C:\RECYCLER\S-1-5-21-0142558076-5079412852-001653246-4163\MsMxEng.exe | |||
| (PID) Process: | (1464) Explorer.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | {S38OS404-1Q43-42S2-9305-67QR0O28SP23}\rkcybere.rkr |
Value: 0000000031000000670000006F382700000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF7085D2F77F6ED70100000000 | |||
| (PID) Process: | (1464) Explorer.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 00000000470100007B0200008B5B17013F0000004A0000008E0F0D004D006900630072006F0073006F00660074002E0049006E007400650072006E00650074004500780070006C006F007200650072002E00440065006600610075006C007400000028003E004000A4E75102B8E651020000000000000000000000000000080274E45102000008026CE25102000000000000D26CFFFFFFFF705911750000000000000000A4E251027C900D75000400000000000008E35102FFFFFFFF38EA7000FFFFFFFF080A7400D80E740030EA7000D4E25102F7AF3D7680D0707614F05102081D3E76E4613E766820700008E351020000000071000000BBF2CB00E8E25102A1693E766820700008E351020000000014E551023F613E766820700008E3510200000400000000800400000026E4510298E351025DA5147726E45102D26E147779A51477D6794D7526E4510210E65102000100006400610072E3510226E451026F0061006D0069006E0067005C006D006900630072006F0073006F0066007400CCE351023400000080E35102DE70310033003300350033003800310030003000F8E551025A000000A0E351021DA71477D6610E02D4E351025A00000010E651025C00000011000000104F7000084F7000F8E55102C4E3510220E40000D7F3CB00D0E351025E903E7620E45102D4E3510203943E760000000064561802FCE35102A9933E7664561802A8E45102D8511802BD933E7600000000D8511802A8E4510204E45102000000007200000032AC5D004D006900630072006F0073006F00660074002E00570069006E0064006F00770073002E0043006F006E00740072006F006C00500061006E0065006C00000045003700430036004500410037004400320037007D005C0063006D0064002E0065007800650000000000D45D38760000000005000000D80B3902000000000000000000000000000000000000000000000000CB0501AD000000000000000000000000000000000000000000000000000000000000000030E69D01A8323876B8E59D01C0E59D0154E59D0100000000000000000000000000000000480B39020000000005000000D80B390200000000340C390268E59D01B0E59D010000000000000000E8B93902050000002000000000000000000000000400400000001A0098E59D0100000000000000000000000000000000040000009EE69D0110E69D015DA5B3779EE69D01D26EB37779A5B377114526769EE69D0188E89D0104000000C6E69D0138E69D015DA5B377C6E69D01D26EB37779A5B37739452676C6E69D01B0E89D0100010000E8FE1C0012E69D01C6E69D0168E69D015DA5310033003300350033003800310011000000104F1D00084F1D001AE79D018CE69D015DA5B37774E60000B777588D24E69D015E90D47674E69D0128E69D010394D47600000000D422E60250E69D01A993D476D422E602FCE69D01481EE602BD93D47600000000481EE602FCE69D0158E69D01000000007200000032AC5D004D006900630072006F0073006F00660074002E00570069006E0064006F00770073002E0043006F006E00740072006F006C00500061006E0065006C00000045003700430036004500410037004400320037007D005C0063006D0064002E0065007800650000000000D45D38760000000005000000D80B3902000000000000000000000000000000000000000000000000CB0501AD000000000000000000000000000000000000000000000000000000000000000030E69D01A8323876B8E59D01C0E59D0154E59D0100000000000000000000000000000000480B39020000000005000000D80B390200000000340C390268E59D01B0E59D010000000000000000E8B93902050000002000000000000000000000000400400000001A0098E59D0100000000000000000000000000000000040000009EE69D0110E69D015DA5B3779EE69D01D26EB37779A5B377114526769EE69D0188E89D0104000000C6E69D0138E69D015DA5B377C6E69D01D26EB37779A5B37739452676C6E69D01B0E89D0100010000E8FE1C0012E69D01C6E69D0168E69D015DA5310033003300350033003800310011000000104F1D00084F1D001AE79D018CE69D015DA5B37774E60000B777588D24E69D015E90D47674E69D0128E69D010394D47600000000D422E60250E69D01A993D476D422E602FCE69D01481EE602BD93D47600000000481EE602FCE69D0158E69D01 | |||
| (PID) Process: | (1464) Explorer.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | P:\Hfref\nqzva\Qrfxgbc\ine32.rkr |
Value: 00000000010000000000000000000000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFFB0F9BD23006DD80100000000 | |||
| (PID) Process: | (1464) Explorer.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 00000000480100007B0200008B5B17013F0000004A0000008E0F0D004D006900630072006F0073006F00660074002E0049006E007400650072006E00650074004500780070006C006F007200650072002E00440065006600610075006C007400000028003E004000A4E75102B8E651020000000000000000000000000000080274E45102000008026CE25102000000000000D26CFFFFFFFF705911750000000000000000A4E251027C900D75000400000000000008E35102FFFFFFFF38EA7000FFFFFFFF080A7400D80E740030EA7000D4E25102F7AF3D7680D0707614F05102081D3E76E4613E766820700008E351020000000071000000BBF2CB00E8E25102A1693E766820700008E351020000000014E551023F613E766820700008E3510200000400000000800400000026E4510298E351025DA5147726E45102D26E147779A51477D6794D7526E4510210E65102000100006400610072E3510226E451026F0061006D0069006E0067005C006D006900630072006F0073006F0066007400CCE351023400000080E35102DE70310033003300350033003800310030003000F8E551025A000000A0E351021DA71477D6610E02D4E351025A00000010E651025C00000011000000104F7000084F7000F8E55102C4E3510220E40000D7F3CB00D0E351025E903E7620E45102D4E3510203943E760000000064561802FCE35102A9933E7664561802A8E45102D8511802BD933E7600000000D8511802A8E4510204E45102000000007200000032AC5D004D006900630072006F0073006F00660074002E00570069006E0064006F00770073002E0043006F006E00740072006F006C00500061006E0065006C00000045003700430036004500410037004400320037007D005C0063006D0064002E0065007800650000000000D45D38760000000005000000D80B3902000000000000000000000000000000000000000000000000CB0501AD000000000000000000000000000000000000000000000000000000000000000030E69D01A8323876B8E59D01C0E59D0154E59D0100000000000000000000000000000000480B39020000000005000000D80B390200000000340C390268E59D01B0E59D010000000000000000E8B93902050000002000000000000000000000000400400000001A0098E59D0100000000000000000000000000000000040000009EE69D0110E69D015DA5B3779EE69D01D26EB37779A5B377114526769EE69D0188E89D0104000000C6E69D0138E69D015DA5B377C6E69D01D26EB37779A5B37739452676C6E69D01B0E89D0100010000E8FE1C0012E69D01C6E69D0168E69D015DA5310033003300350033003800310011000000104F1D00084F1D001AE79D018CE69D015DA5B37774E60000B777588D24E69D015E90D47674E69D0128E69D010394D47600000000D422E60250E69D01A993D476D422E602FCE69D01481EE602BD93D47600000000481EE602FCE69D0158E69D01000000007200000032AC5D004D006900630072006F0073006F00660074002E00570069006E0064006F00770073002E0043006F006E00740072006F006C00500061006E0065006C00000045003700430036004500410037004400320037007D005C0063006D0064002E0065007800650000000000D45D38760000000005000000D80B3902000000000000000000000000000000000000000000000000CB0501AD000000000000000000000000000000000000000000000000000000000000000030E69D01A8323876B8E59D01C0E59D0154E59D0100000000000000000000000000000000480B39020000000005000000D80B390200000000340C390268E59D01B0E59D010000000000000000E8B93902050000002000000000000000000000000400400000001A0098E59D0100000000000000000000000000000000040000009EE69D0110E69D015DA5B3779EE69D01D26EB37779A5B377114526769EE69D0188E89D0104000000C6E69D0138E69D015DA5B377C6E69D01D26EB37779A5B37739452676C6E69D01B0E89D0100010000E8FE1C0012E69D01C6E69D0168E69D015DA5310033003300350033003800310011000000104F1D00084F1D001AE79D018CE69D015DA5B37774E60000B777588D24E69D015E90D47674E69D0128E69D010394D47600000000D422E60250E69D01A993D476D422E602FCE69D01481EE602BD93D47600000000481EE602FCE69D0158E69D01 | |||
Executable files
1
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1464 | Explorer.EXE | C:\RECYCLER\S-1-5-21-0142558076-5079412852-001653246-4163\MsMxEng.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
5
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Domain | IP | Reputation |
|---|---|---|
digitalmind.cn |
| malicious |
antipiracypetition.com |
| malicious |
freebieslounge.com |
| malicious |
Threats
Process | Message |
|---|---|
var32.exe | wS8_N_HSce_up_he_hMf3lnqVAsn8e_G9jqJl2_LpJpaDvvXceoDkMpU_qu_XV6_6RxhcW__vFZ3_h_XKAmb1vS7_2mfK3U5YRcoWib___HdXHH5_yn_VFTcmn_zAKDvChx1s_LHIi_JjLOPWB8yWF__Y_S__1WHF_9u2Ak_OFnrI_IolYJGaC9rbh8AWJG1_TqnGCoEA__wo1QsabKqbePybKw_Qx_w5pU8fLNwU8d6_lmuQl_JJ1MO_b_phrBPgzr4QAzs_PNhf__uf_H85__b8n__tLS_MprfOl__diiQekaIB_eRi5__P4_FE___p__8_Mi_Fn_T7Nb48JYENYWs_Wf_4w_sjwjVWqDgfjH_D_T9RvSWb_JW3vJoNYEpYs_mU_ZxrLs2lBLLxJ__VP46f1P9U____kr_owC_5C_gbtXvwy8_1_VYCQEcq7_TOxN_5KxYKpsb_e5EcHg75o_2_Q4uq__bbmbsl3RuBdRc6v7O2abjvFO_u___mLm_TKHHw8vpuVihEZsdAYLtW_thkiqFAQG__aCL_FvV841mFh_l9K_YBO7eso8bk_8piAc_uvpYyI4___2KJVPk_OUrOiAajSlA7xrvPDM3yzbjb_FgfShjop_7AD398Ip_rEp_TGV8sXt2_ON3osAe_1_oB_n5M__c5KTe9id6KRIw3GQqdi___wF2hv_bF_tSqR8R9eSzsugm_r_B7O92d_QBOz___yaTmbXQ5Js__vCJfhUCvRoY__D_W8Nccna_hWvJHPH6Lg5poJW_Pu5f_gA7EiCdOTzEGwuQbztN_iFL__escGaSY192Z_5u__DQ9Mz8381_IhERp__4B9jl_HYNj5T_uHYj2CICZqNASBf28_fqlVaL__FWYi_Y |
var32.exe | _v2lC_i3hFfNJsU1q_VcNCF1f1S___N_OFe_E1J___ASlUxvN2_oof_Jk5e_nU86_f6sUX1dVi_UAXRdzh_UF_GocgD_j_7U8cb_Pn_C9zYxOnF_Ni_IUQk_EIdJ_uF_6Zc_8cqgaHX3b_li61c6hT7_YkY_Ebml8TocbS1E7cip_NdNvLDuQ_o_YqieMkw7EDFqUPqR_ks4S |
var32.exe | ExCs_AkDxAC_TvXguU2GR4pZRn3YnHSqmsA78BMYKL6BFimt_oNVHRcXgwm4k9aGmDslyrxu5fHtlsx7jlQegDt_By_mwwe1kg5SF_lFtFsb1_1KAvOdlQPl8HhUq1YLJ_N4_A9VPu_ZUc5MQqS5dPzRJGqH__VZ4_Z___Q_6yBMSCno_x9__If9_u_TuD5Ix__t4_D_Q9jym_f_yl_w9_bY7bFAy5_A_7_rSf_pUR4H_a7__fIy_93aiI_UcnghjK6PkrA_Dld_d_AjNs_yiStkwK_sNPS_Xb8_IMm_mtTMJx_E_1cquJ1oSdWNXVJi4_3D4C2zofHDAlq9___iA9U8e_xh8DdDvys_v_m3fyTJL_R5_k2hP__4e_C7Mk_jErgEPOTE__XN8u_d65bfC__hNEPJV4R_K5dazl7r55N_If_L_DiIXc5T8_8C_SQhIK_hxel_kGx4n_yoOWO__1up_aMF6zA8khKma |
var32.exe | _Fj_p__paP3_esx6IC2xhwbC6f73s6pQw6_s_tq1Uydf_v3H9_m_wb_QCOUxn26_y7KqSN_KG_7___NA_LGwGJ_H6JN_2__wlhh_lnHLiPqh_iWH2nl_GIqffn91pB_B89kXU___Z_N9dW__8SZjZxFn_oazJH____ua_FNHw_V1v4yqQVqDJ8dXiNbip2AoNOt_6i4Fn__ZvWq5kZxW_hmtE_yV_9619n1__O3y1t_3Q_bMd8uA5_eHDgzWyq__H5gS_I_Xg_j_OcEq8p8uz488mes6TjVZpIHPb5_QBPRZxYD2Fw_u_jxWF_fYlh_O99Ral_ouHe___TJ8kLuqema_wQ_c_uAVtWxBqZxj_xUVsFbHsJw_n__iWPGXahfm34eaQ__U_HG_d_b_dtNSF_6142KGlA_QB9T62l58HZN_6ntS4zDU4t4V_g_YH__o8ef_YeK_Z9z8IF_c_eSOlur_DHL_TaAkyGiLvcerORBPset2NOli6_h_oi_rv6sA_ZSXbJ2a4qGaPRNLThfngZacya_IJ5L_S__Aq9Q__UUC_e_jSWON7TtSrqW17_SSISzHiU_3dF_ffh_ZvC_A_5v1LGae_Ct_qTtp3Mtqe86l7_DSgO__qQMh_b7_H_XV_78wg_h_GXTXFB5Gz2_6__aslXk_y6Ng_zOuUMR__9DDciLE9Bjrld2H8VFx_j8oxs_kfu2_s__Hp_9qBE2eFQlUCRI4r_V_x_g8RBK5_jI__ku_UR3xUeazN1_Lnl1NhgXLSmBZ9A_F_vcJnoBQKOWwEXl__a_Aws_B__J_39__WN_W__R2UXxANJ_r5BrUyTqDrA__wJud_GgL29CvBpv_qpX1K7A5_zvLQ4cNs__N_2 |
var32.exe | CNq1_2zQxHz1_NK57_b2g_H_Qmo_nLFQKeQK5UAl_Ydc4_6_IPRjv1uU___ce_q5_hx_jN_txE1lkORkX9I_JL_SAz9JbAqN54KKEdIGMp__8dEvn_aWS1Wmh2MFi_O_YKNZ4vNaT3_wA_mOiXR_3dNmE_c34uFWHt_q_M_2qEkiNXja_D5OFgzD_Dsiw__Ajw_e_6FX_MxJ4eBCOVE_JY_oSk_6EJsTgYQlq_Afkd2H_LewvA_J_UaF9yAQp8U_j_X4IEU_9V2a_P_PfS_y_9dZj7LUbZdv9iYCzF89u_NDgmxboJi_Vk1mJzU28UkLDf__Vj84LL3_e8QQ_9_jKj_gp_EgWD5_PvQuSzOkB |
var32.exe | a27_14jegaJv_qN9LTv2byR__b_W_K3QRF2aA_IU35BlzuGJlc_bt1SVxs__zEOa__P__c_z_TE_ybSSRxcoKXE_I9fm8PKi2FEF_FcON_kvSLxgeMZBXxuPb7ZI_qBjmwqU_91w3pz_c5pI7XKlGSWFDdknn_lw998_VfFG4mMlIS__kYZXzsaeSvbbEQk_hOHcjXCJna_l_duXbGD5RVLI_yPl7KV_CMwvLJ4mE4n_6Li_WzYPjBF__fs7cUrWAHujhVi8j9w_3CFE_jchy_1x5ZU__AnzJ_bhREG__wYOxpEUg99ivRVl6sOgB___Ay3_9CJ_aPmF41v_VCrBm9jrl2o9sNdh9xobpjxCo7_eVdOigtn_F_NMwiydhOjBjL_5FJ3BS4sTpmEbbP_DHyd_7_iFcsT3EiJ_diLCZw_PwRRJLl9KfzlTE_hv5rQvWRnaRyPUmzT_RwcfBPnLB9T5pDEWufU_X5Nc_VAN_7M__F8g9NeVp22sUUcZlWRCnK2ImhiCDV6i_FML_g9I98uXp_5_Htf__63x2GQ_8_53qx3B_S2dk6s_PHfsk5byY6msNbap_m_z56h_OdXTX______PA5F_P9d__qK_9HOEt7iyYp_j_OJnH_abp_H2dXyw_H_pa_jyB1_Twxxw2WV_W8avHOghU_N_dcd3gaH4L__E_h8_ip_H1C__aS4QCdBHZ61KjgdO7fq_JTst_S_jo_kly_1Pe__I_Rx_Dzud9R__y_aLVbWDhw___itUDuuiZXFuLl5XOfBVh__URN_ohzn_fxD1lgG7dn7_ypTA33u_zVQORS1DKreA3___Xx_F_W_cANkpZ_Rcg4_crr_7__2cQ_o2GV_w_YNQ__jzmeNIdiR__WHe8xf_sk2VE_V9Az4KWu_3fxugTfrk_p_LdZmW8Fso9YPBarljWcOzfo_vi_U_Ta_L14_yj__mGu7_RiIsq__Idx4_WQoyKpn__bt__5Z_vIrQ8uQLZt2_BOU33ru_R_uC82Li9yz_awl3XlX4RhR4Ar1_4gd_d_I |
var32.exe | B__9g1_r714Ny_DWLyun_FJ1_XpaZ_HCL7o9EzHH1AWPvRg48u3s_2Km7imMw4C1o_mefKkt7PiCgQTXm_Oj9aMHjVNrOU_c_Zj_W_3V5FdhvudoW7L84pK_nUh_tv__6__K__qUM_sIcpDTLpmLjcS_KnbO___QtvQP_6_p5s_Uzj6R_cg1_J8_4z_NcieGUMsjgJjw_P_ks_aoizfFIDeDVU8U_klgS_z_u49iL_sqW1M48N_k_BK_aYN3OV_Kd__b_74NsGk8UJdtHg7__d_NzakZG7fCu4IZXi1aghf6qRkOsKCBlLLmhPPAmJT3DVBM_X5y__gxL____ETxQqSxbHJra_k_KdmHi6__Ia4IT_mZUB_8_IvSouLVS_vGxKeRC__yogscm_Pw6nccW8B_eSOfAjj3QE__f1y_roB1WblCeyjz_VSYQf_R7Y_VzL_Nfcit5iLi8__cH_7AiDjL_7bWqT5LC_3_gB_XxEG__77V_SkSc8_naUo_mSpxH__gnr_dGfCI___TR_aphTp_KJJW__BEE9_vYz_c_bbs |
var32.exe | fQFGGFqDyvbt2h6A_oP1lY_b3QCR4gKaA9_7B__zKB8__kdk_S4Oo_y7X_VVz2c_kiu6_s_n9vmJQ_1B_Qzgp4W8UYnC6_2Svo__1__yKhjidY2_u_OAYTTiIEAK8MbB_M_MVVeszKn3zWHXgOFRzI___bf_HHx3I3Bj3cnJL5PeqH__F7Rmz8NfSZ2b_9d_KzXxM9R1UtS_RhsCb2vb4tH_q_2aspa_YUMmpkpkkws6__z9_Qq_6oyjtJ7A_2VA_VDRseQXfQE_WAQv__kvoi6IFt_EqrtGF__Ib3_w__BVgnQ2v532Wh9_2inn__2ZJnn_sVDa_b1ok__W_Nnh_AQpS9mLZxz_fSI2n63V63s6UdrfxT_7poQ_IhD8dC1i_quJa6LtAE1W_o_h4pebsPiD55Hab_s_hkGveBlf_MHOEbIbLDM4llRS3Ox_uPKBk_kF3_XUFVB3PV5_rlB1_YNBgNA |
var32.exe | A_yS__bC_jM_3hU___75pxRC____64ZEvvaH_z_gU39EWcV57_dsdfVI__jmQmbhLSnTpqkNld2E_x_C_8FKac__AkCGk_h_y__K7Ya3UX_TotWWZ_aACFxe___qr7V__1h99jijpf1Lj_fFQ9C__BjT_GLO_KZKygNPL_jU_eC_COWUqy2y_RKJss |
var32.exe | lf3BOX6_4OyfyasB3Ar_zv6HIO18hqNaN__IxNAjp_Er_dG66td_8_u_LSJkM_2aBIj8fHAvIdwg__cDhYdpiRMZsrMK_D9lbtD7_WQd7iP4I_k_8l6JDdX6YfIz9Qh_HWb1I_pmCQ_P6iN3jH2_ycA_dCpGHk__XrLExc_Y2MuVl4p_hU8e1UH_jlXx_vrS9399f_qKTBMmfSudtB_QpJo2Xrx8tnEczxq_gwwK2jrBLvdf_2_VB_ABlIhCiyLEgkv__piFUtmxiIICk_F1a_rh_X4LMkKrnja6J_n_CTgM_oT8UHPg_n_pdMmHT5TCSuf__YnevpPXQ_bT6oWT_1_G_h_uh5EGq___hSa7Ejl8z8_6a_DCL2kC_Ozd2pLo_LsZ_myiU6_L2Hn_zFfvB5_XsroIN3qTRYYVJ__4EM_e___Y_1ZS_ZhM_bFoDd_cz55OGEctm__ViJdJ__PYFO_e7W__Vs9g1xE_r_w_k_E__Bh_5_xkUrlPI__UGog_yt2W_4RVMlQlGce_H__NZ_xr__eKWCqQs4fyx__Y2vDS_k_r_BKS_2_thqMu6_R4m6_r9ej_4d39d1KKz_2R4T_X2_3L_FhsfO_WKr__Usi9FcA9uNys__a34XSaRp_amCM5Z5L35V_FNXuMSs2__QIH_2f_1k_SbspFRxU___VqM3_k_mTJMx9XfR_Lh9yqb |