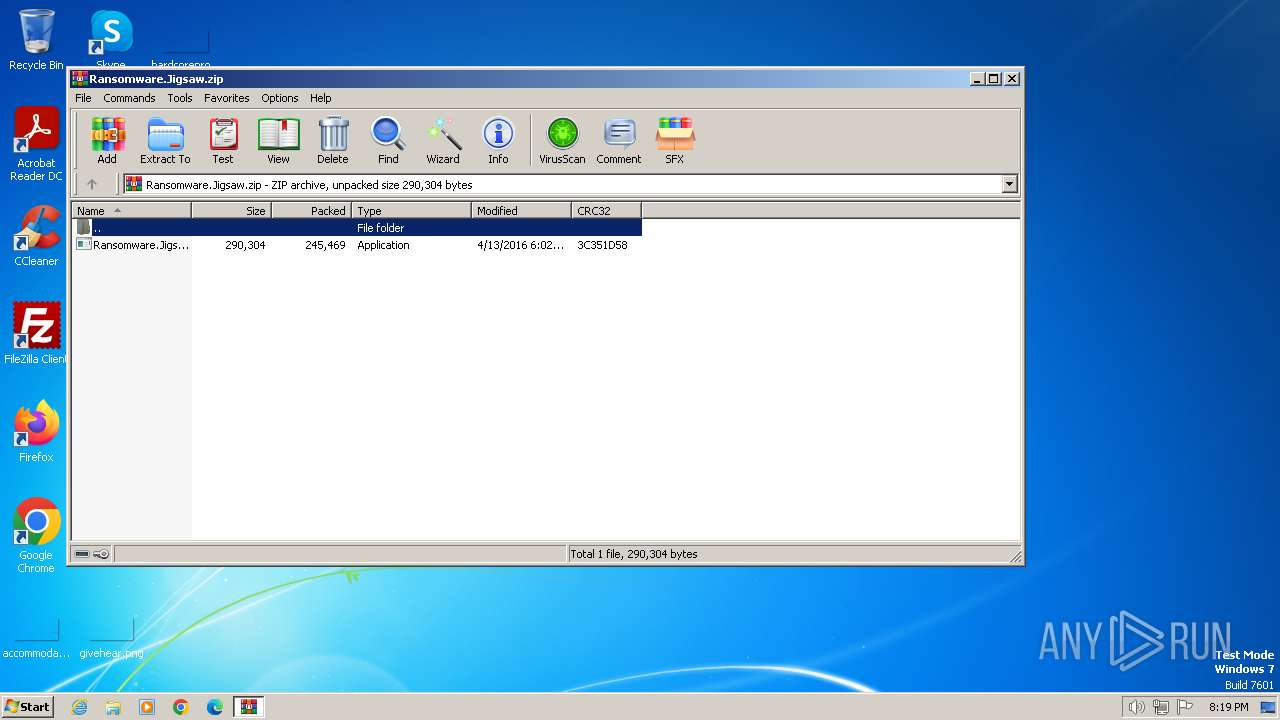
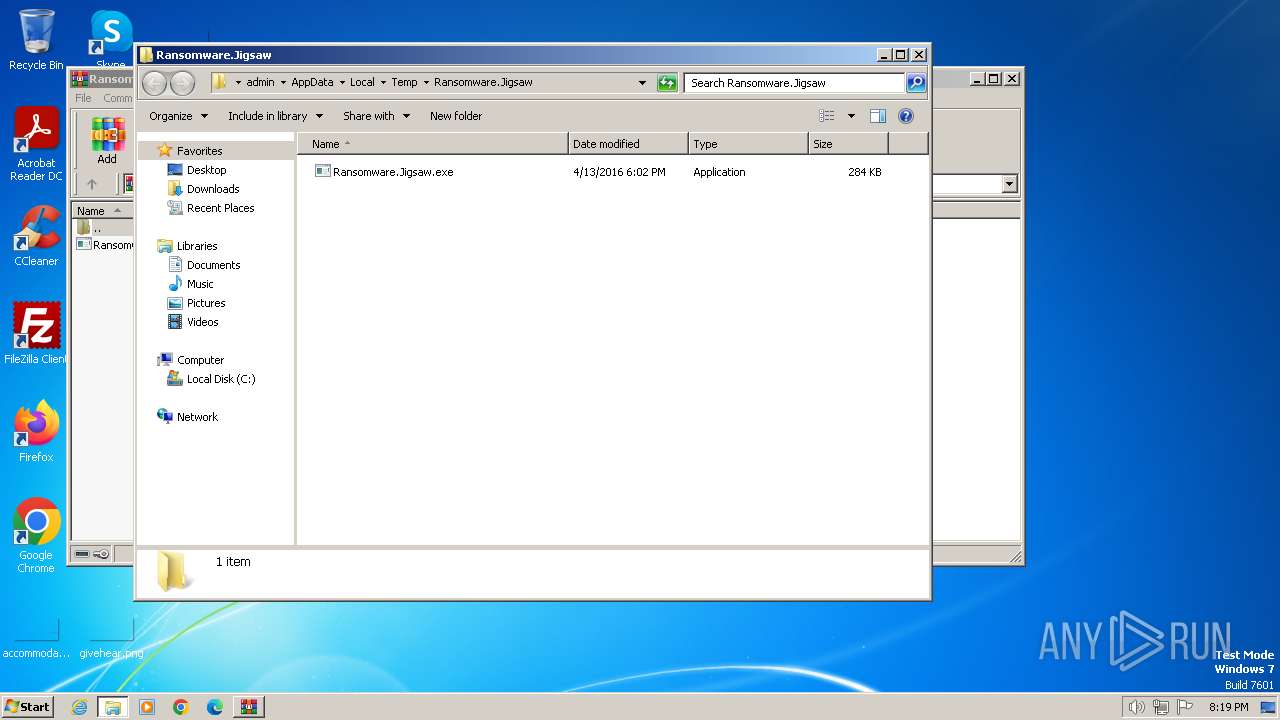
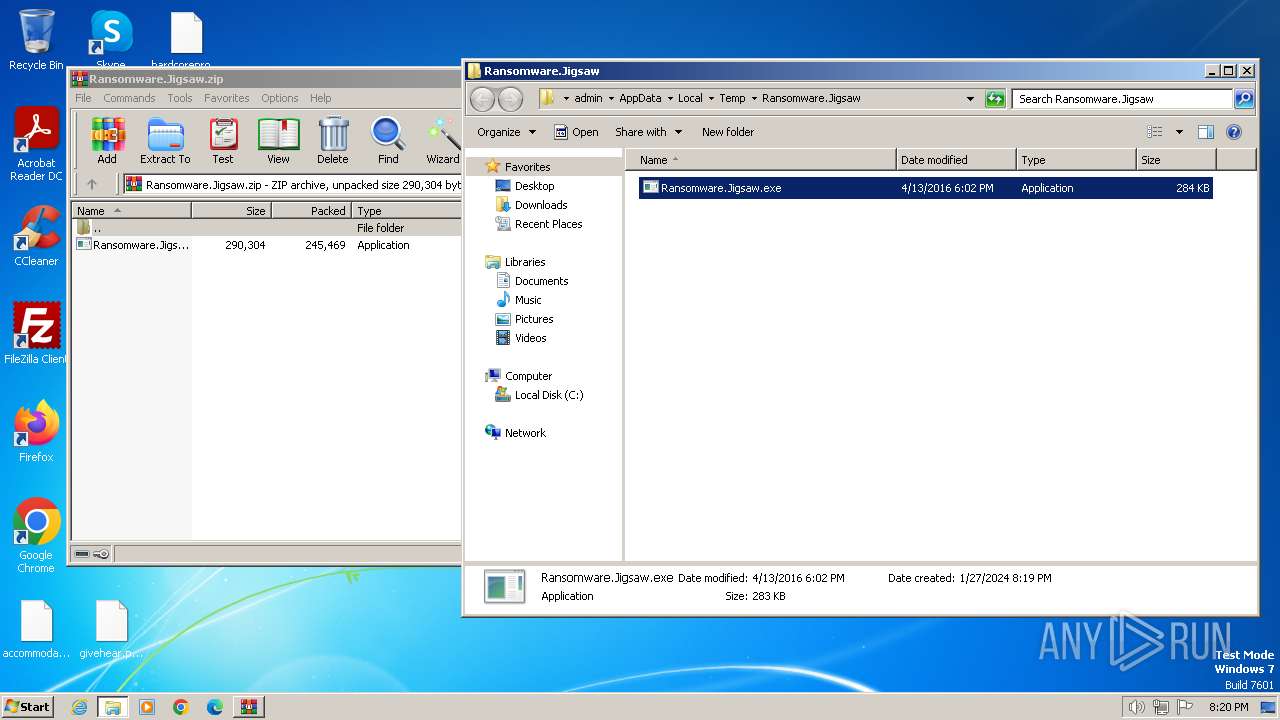
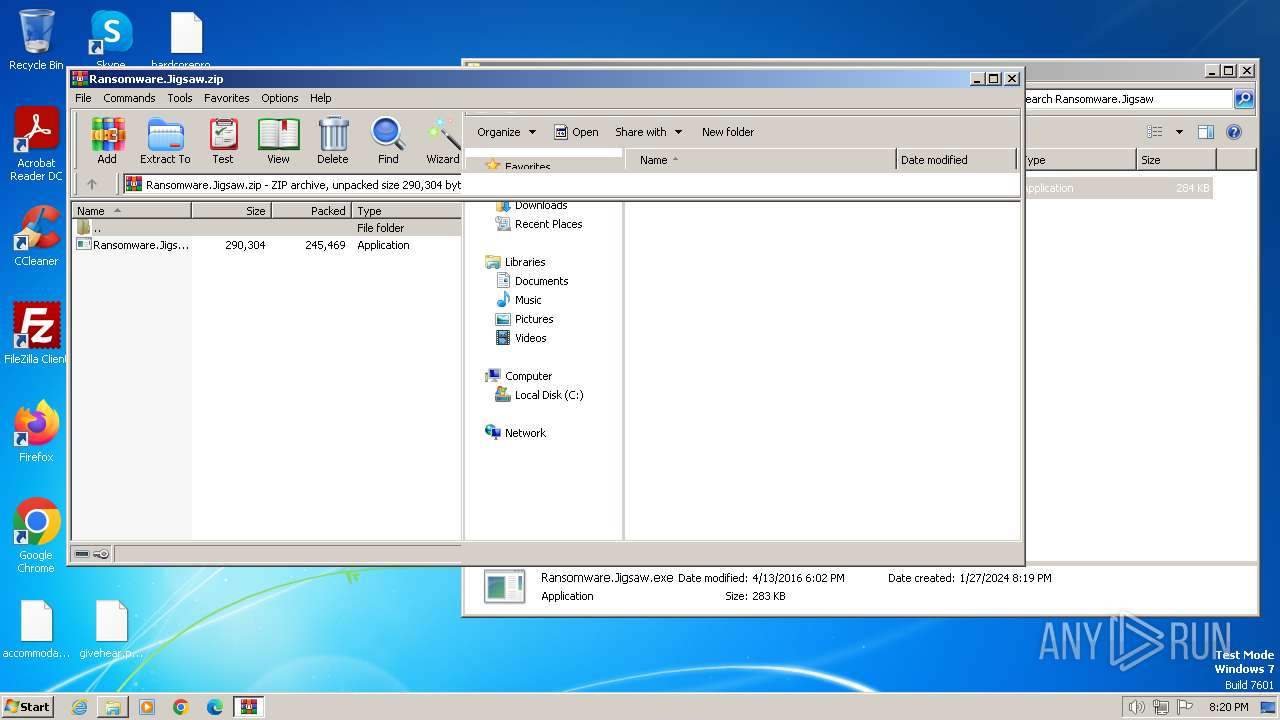
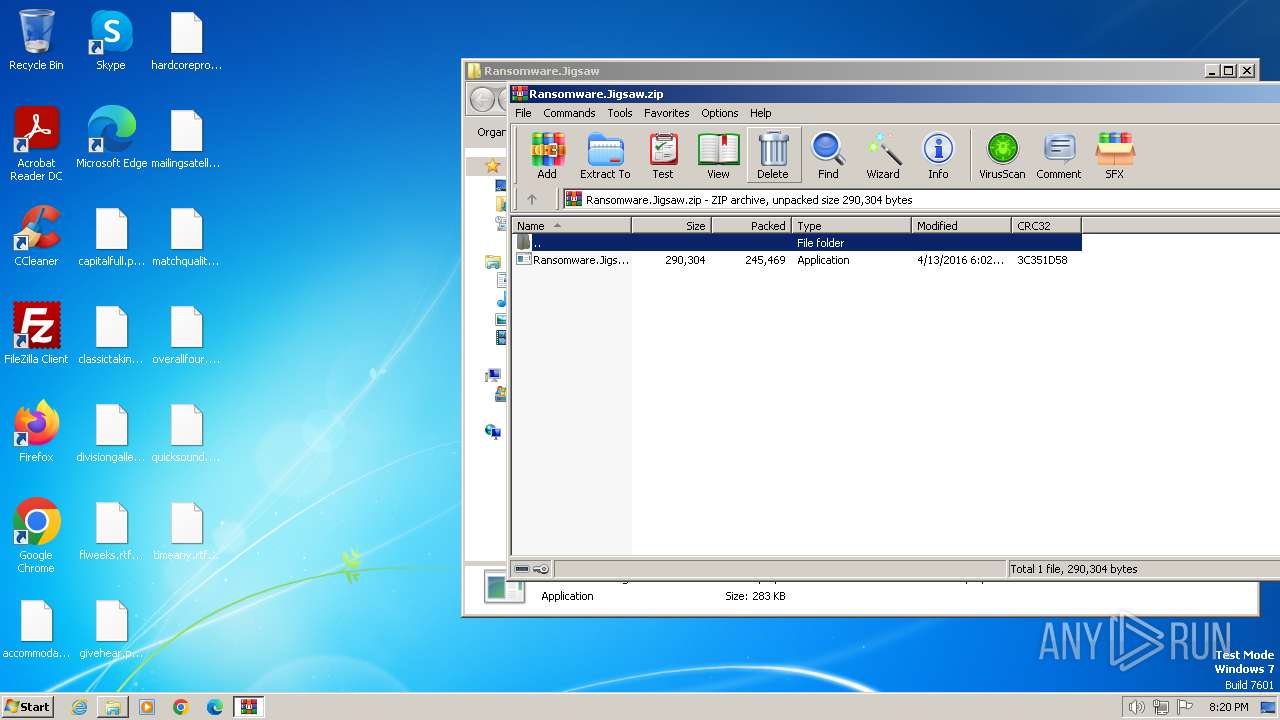
| File name: | Ransomware.Jigsaw.zip |
| Full analysis: | https://app.any.run/tasks/29736af4-9f05-418c-b125-36055ad91949 |
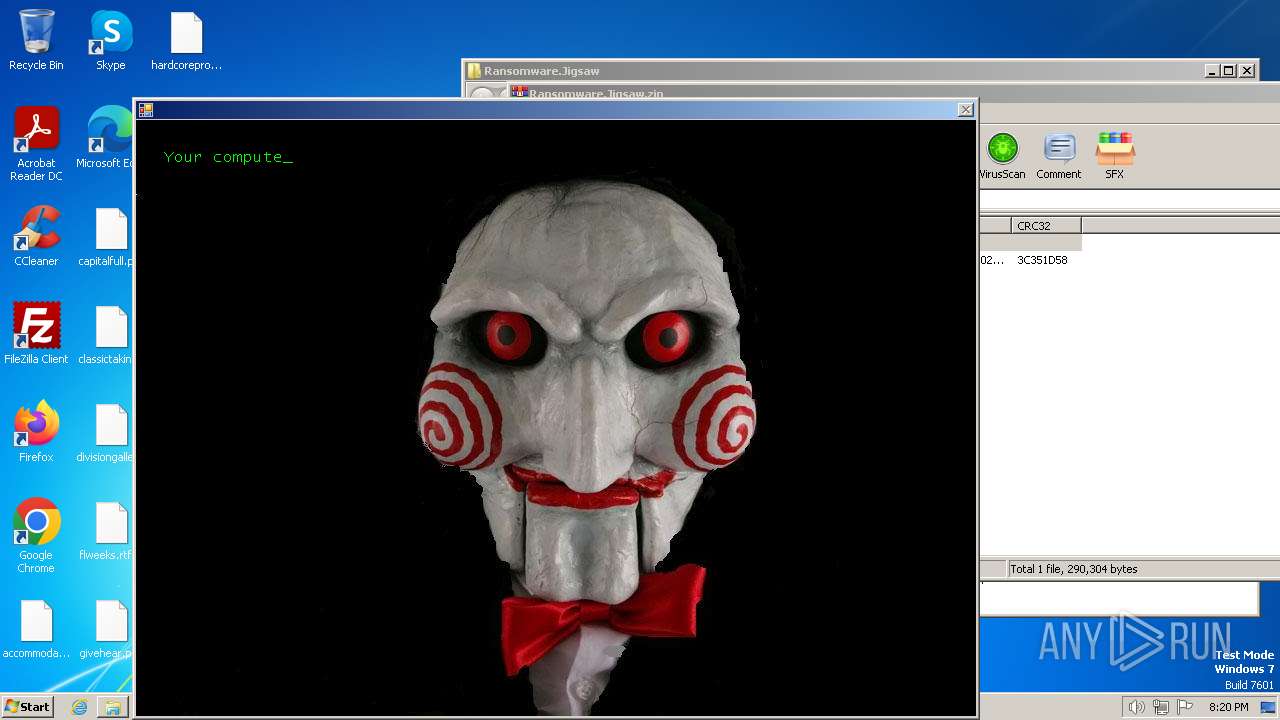
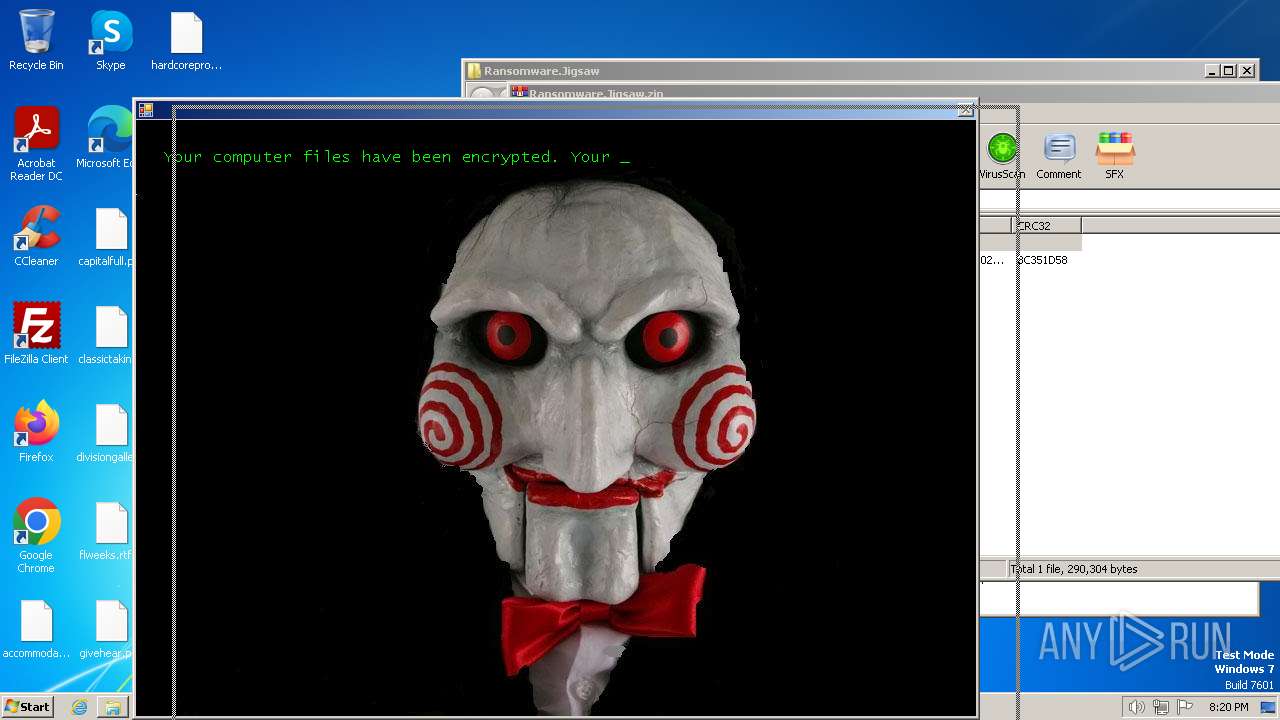
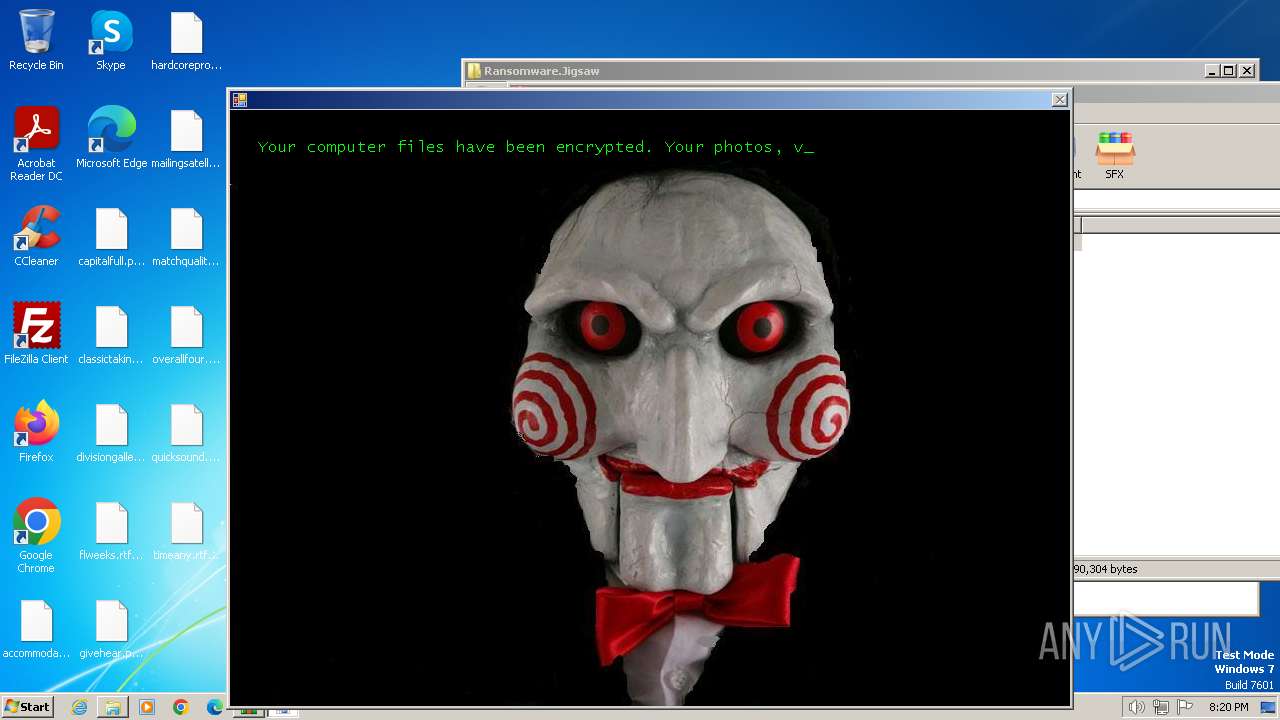
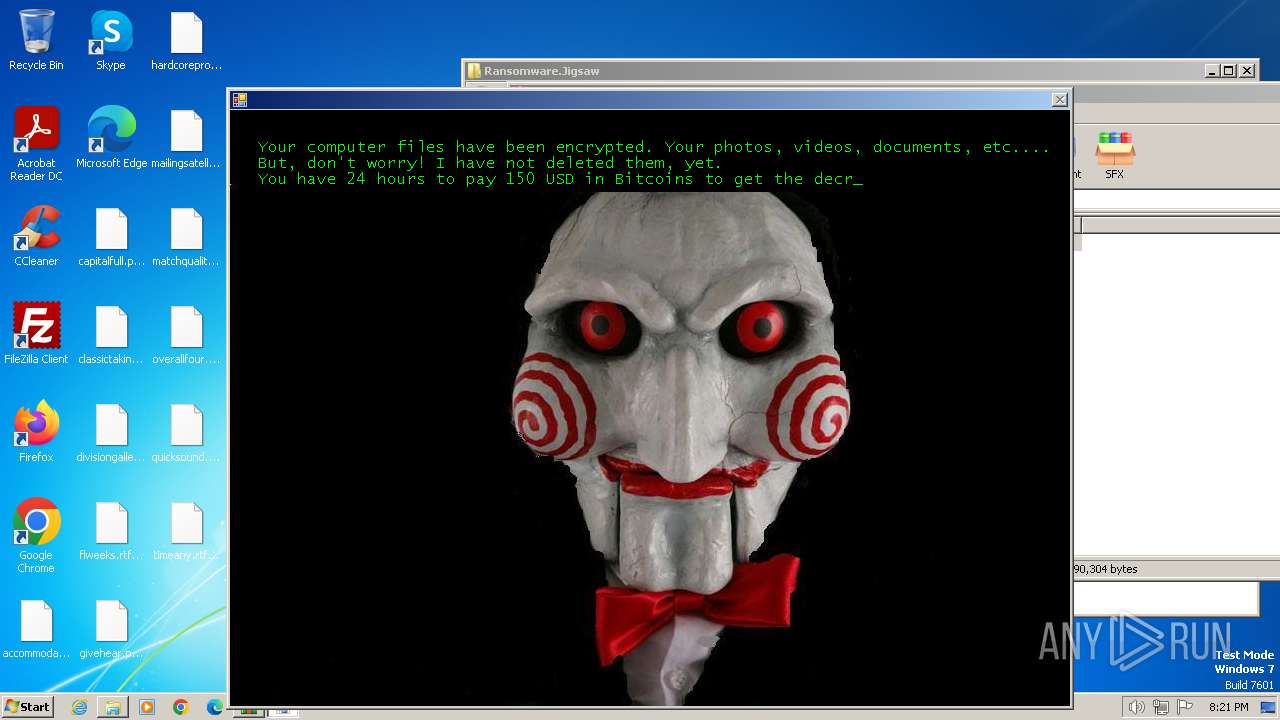
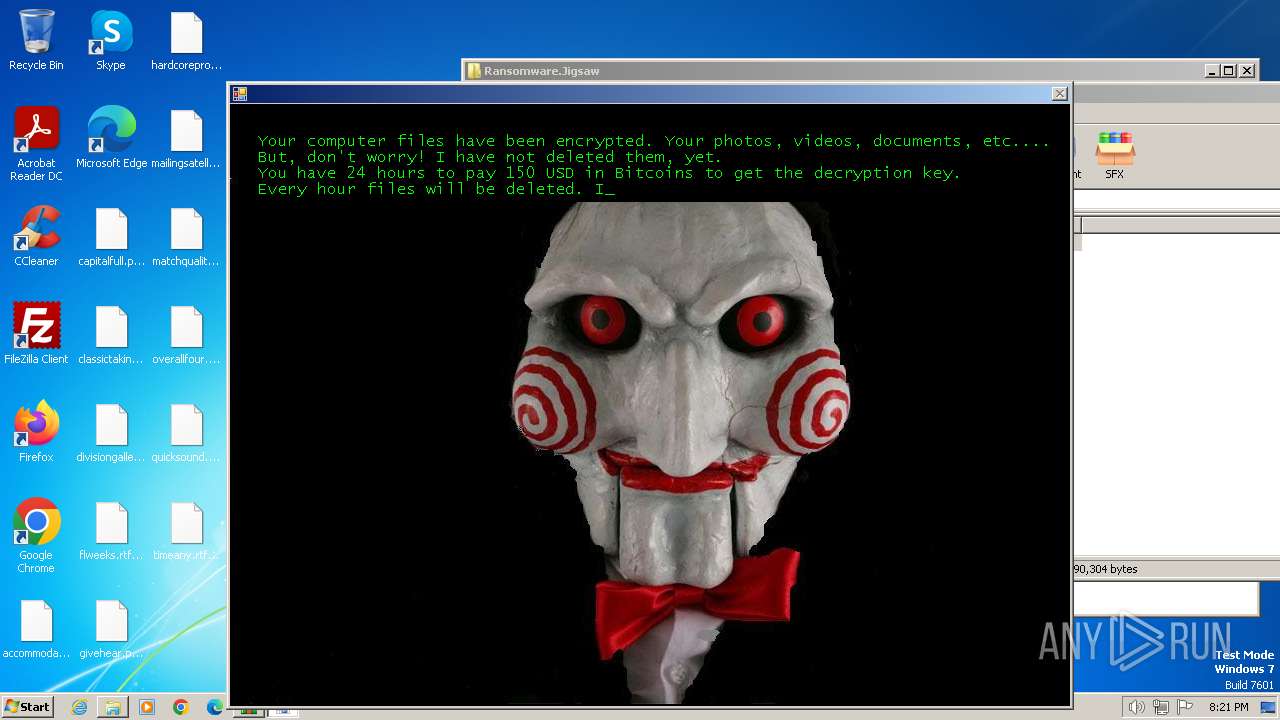
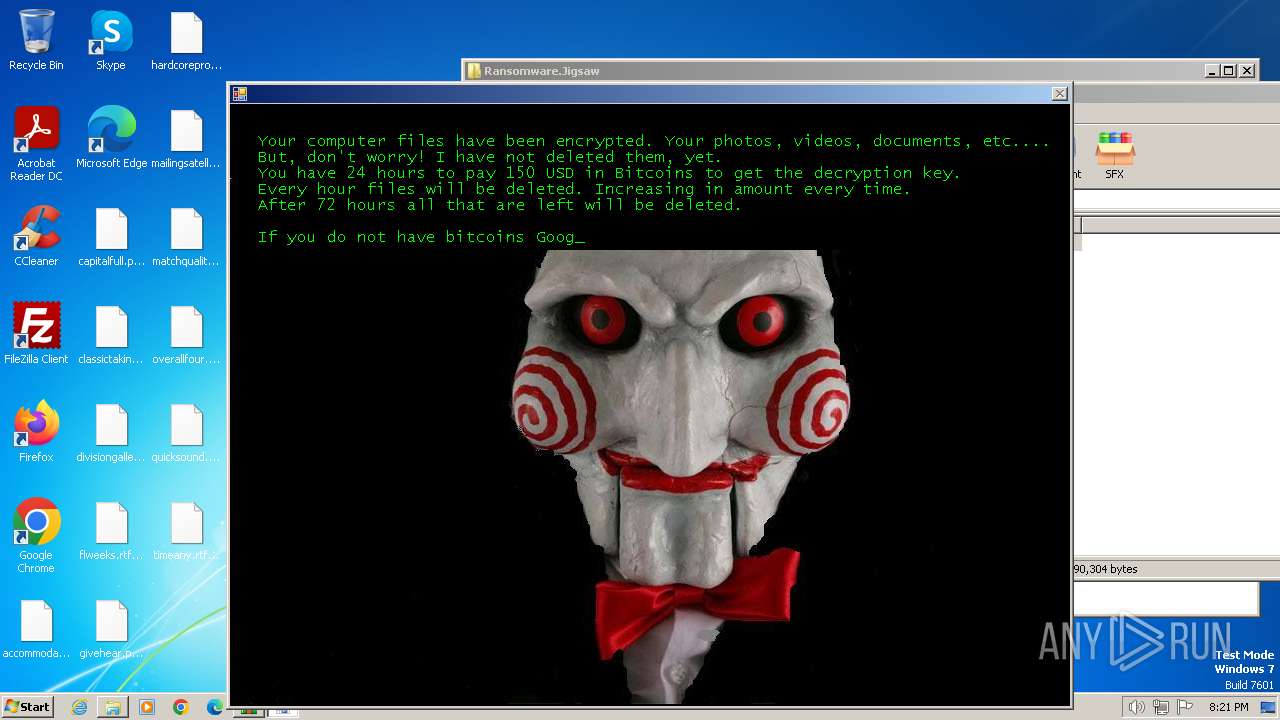
| Verdict: | Malicious activity |
| Analysis date: | January 27, 2024, 20:19:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 4161238E76DC9AE69C0C96FADE43B0BD |
| SHA1: | BF51E618D59253075D33461A353D20018AD177A6 |
| SHA256: | BC6C2A22CF086BB9F18E100866C83377A2C8CFB4F3B9CBC0330194D58EDDE7DF |
| SSDEEP: | 6144:t1fFd5AovOddCrdgRxvpohe+YWe+sLrjtTZBCOGkWNg1tMse8pHe0tSA2iUm:tppROdb1CheJPxnUg1JPeqSfiUm |
MALICIOUS
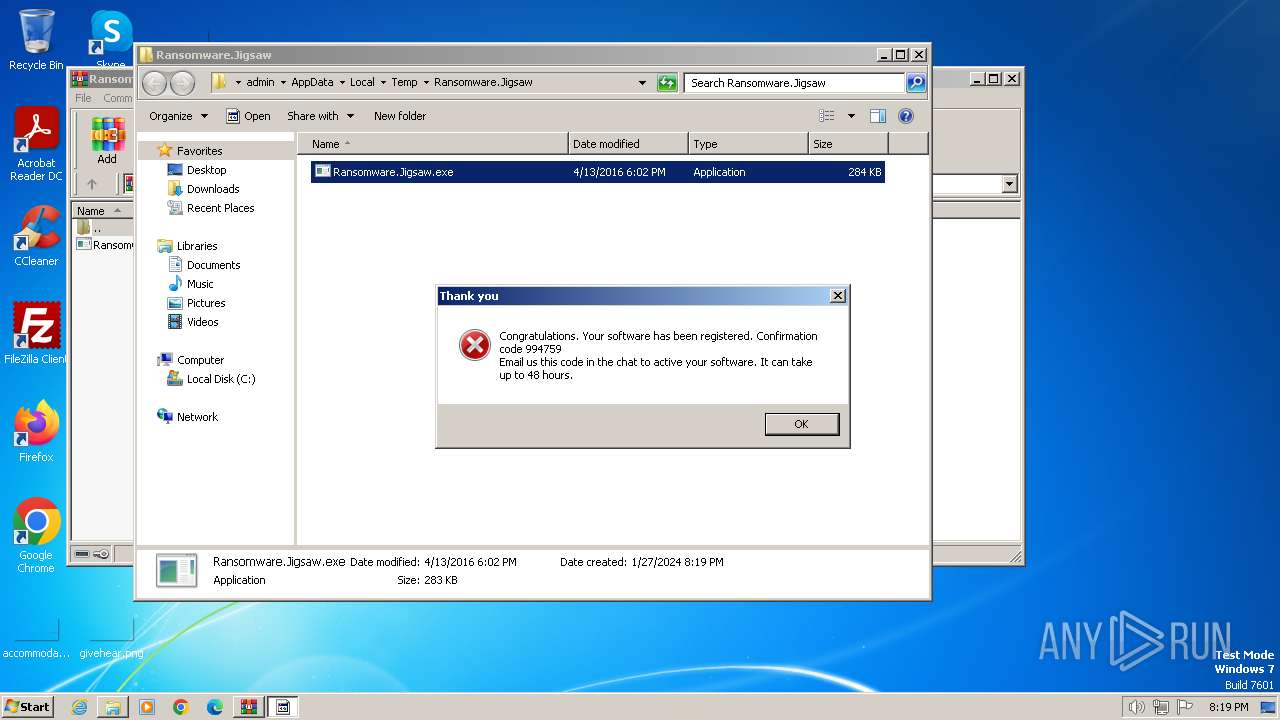
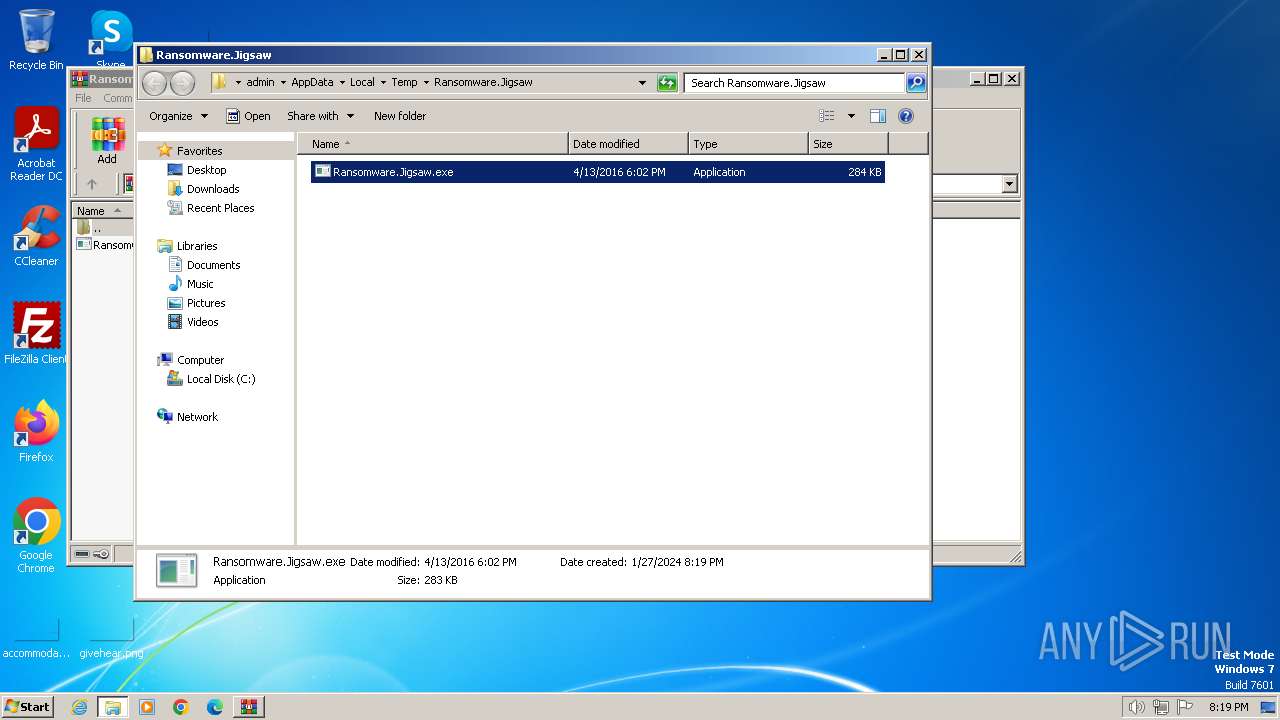
Drops the executable file immediately after the start
- Ransomware.Jigsaw.exe (PID: 2572)
- WinRAR.exe (PID: 2628)
- drpbx.exe (PID: 2484)
Changes the autorun value in the registry
- Ransomware.Jigsaw.exe (PID: 2504)
- Ransomware.Jigsaw.exe (PID: 3616)
- Ransomware.Jigsaw.exe (PID: 1820)
- Ransomware.Jigsaw.exe (PID: 968)
- Ransomware.Jigsaw.exe (PID: 2756)
- Ransomware.Jigsaw.exe (PID: 2356)
- Ransomware.Jigsaw.exe (PID: 3040)
- Ransomware.Jigsaw.exe (PID: 3112)
- Ransomware.Jigsaw.exe (PID: 3436)
- Ransomware.Jigsaw.exe (PID: 3568)
- Ransomware.Jigsaw.exe (PID: 3264)
Steals credentials from Web Browsers
- drpbx.exe (PID: 2484)
Modifies files in the Chrome extension folder
- drpbx.exe (PID: 2484)
Actions looks like stealing of personal data
- drpbx.exe (PID: 2484)
SUSPICIOUS
Executable content was dropped or overwritten
- Ransomware.Jigsaw.exe (PID: 2572)
Reads the Internet Settings
- Ransomware.Jigsaw.exe (PID: 2572)
- drpbx.exe (PID: 2484)
Starts itself from another location
- Ransomware.Jigsaw.exe (PID: 2572)
INFO
Checks supported languages
- Ransomware.Jigsaw.exe (PID: 2572)
- drpbx.exe (PID: 2484)
- Ransomware.Jigsaw.exe (PID: 2504)
- Ransomware.Jigsaw.exe (PID: 2756)
- Ransomware.Jigsaw.exe (PID: 3616)
- Ransomware.Jigsaw.exe (PID: 1820)
- Ransomware.Jigsaw.exe (PID: 968)
- Ransomware.Jigsaw.exe (PID: 2356)
- Ransomware.Jigsaw.exe (PID: 3040)
- Ransomware.Jigsaw.exe (PID: 3112)
- Ransomware.Jigsaw.exe (PID: 3436)
- Ransomware.Jigsaw.exe (PID: 3568)
- Ransomware.Jigsaw.exe (PID: 3264)
Reads the computer name
- Ransomware.Jigsaw.exe (PID: 2572)
- Ransomware.Jigsaw.exe (PID: 2504)
- Ransomware.Jigsaw.exe (PID: 2756)
- Ransomware.Jigsaw.exe (PID: 1820)
- Ransomware.Jigsaw.exe (PID: 3616)
- Ransomware.Jigsaw.exe (PID: 968)
- Ransomware.Jigsaw.exe (PID: 2356)
- Ransomware.Jigsaw.exe (PID: 3040)
- Ransomware.Jigsaw.exe (PID: 3112)
- Ransomware.Jigsaw.exe (PID: 3264)
- Ransomware.Jigsaw.exe (PID: 3436)
- Ransomware.Jigsaw.exe (PID: 3568)
- drpbx.exe (PID: 2484)
Manual execution by a user
- Ransomware.Jigsaw.exe (PID: 2572)
- Ransomware.Jigsaw.exe (PID: 2504)
- Ransomware.Jigsaw.exe (PID: 2756)
- Ransomware.Jigsaw.exe (PID: 1820)
- Ransomware.Jigsaw.exe (PID: 3616)
- Ransomware.Jigsaw.exe (PID: 968)
- Ransomware.Jigsaw.exe (PID: 2356)
- Ransomware.Jigsaw.exe (PID: 3040)
- Ransomware.Jigsaw.exe (PID: 3112)
- Ransomware.Jigsaw.exe (PID: 3436)
- Ransomware.Jigsaw.exe (PID: 3568)
- Ransomware.Jigsaw.exe (PID: 3264)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2628)
Creates files or folders in the user directory
- Ransomware.Jigsaw.exe (PID: 2572)
- drpbx.exe (PID: 2484)
Reads the machine GUID from the registry
- Ransomware.Jigsaw.exe (PID: 2572)
- Ransomware.Jigsaw.exe (PID: 2504)
- Ransomware.Jigsaw.exe (PID: 2756)
- drpbx.exe (PID: 2484)
- Ransomware.Jigsaw.exe (PID: 3616)
- Ransomware.Jigsaw.exe (PID: 1820)
- Ransomware.Jigsaw.exe (PID: 2356)
- Ransomware.Jigsaw.exe (PID: 3040)
- Ransomware.Jigsaw.exe (PID: 3112)
- Ransomware.Jigsaw.exe (PID: 968)
- Ransomware.Jigsaw.exe (PID: 3264)
- Ransomware.Jigsaw.exe (PID: 3436)
- Ransomware.Jigsaw.exe (PID: 3568)
Creates files in the program directory
- drpbx.exe (PID: 2484)
Create files in a temporary directory
- drpbx.exe (PID: 2484)
Reads Environment values
- drpbx.exe (PID: 2484)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2016:04:13 19:02:34 |
| ZipCRC: | 0x3c351d58 |
| ZipCompressedSize: | 245469 |
| ZipUncompressedSize: | 290304 |
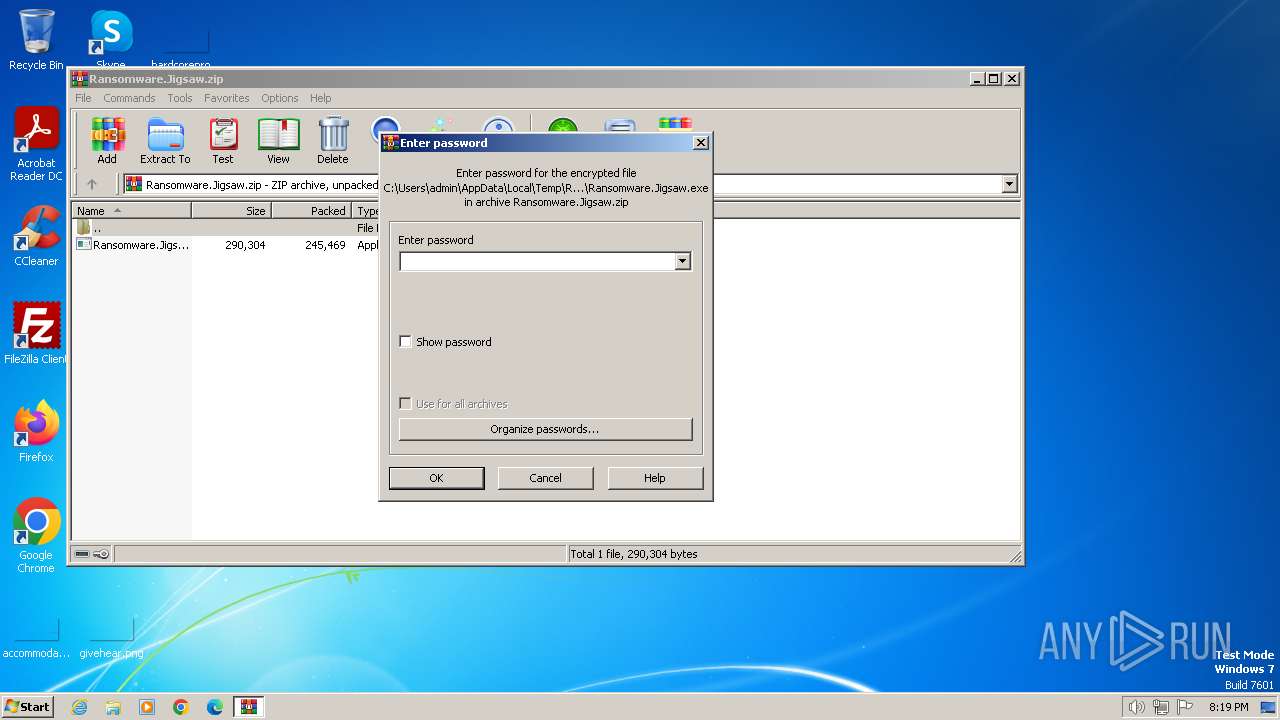
| ZipFileName: | Ransomware.Jigsaw.exe |
Total processes
52
Monitored processes
14
Malicious processes
2
Suspicious processes
11
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 968 | "C:\Users\admin\AppData\Local\Temp\Ransomware.Jigsaw\Ransomware.Jigsaw.exe" | C:\Users\admin\AppData\Local\Temp\Ransomware.Jigsaw\Ransomware.Jigsaw.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 37.0.2.5583 Modules
| |||||||||||||||
| 1820 | "C:\Users\admin\AppData\Local\Temp\Ransomware.Jigsaw\Ransomware.Jigsaw.exe" | C:\Users\admin\AppData\Local\Temp\Ransomware.Jigsaw\Ransomware.Jigsaw.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 37.0.2.5583 Modules
| |||||||||||||||
| 2356 | "C:\Users\admin\AppData\Local\Temp\Ransomware.Jigsaw\Ransomware.Jigsaw.exe" | C:\Users\admin\AppData\Local\Temp\Ransomware.Jigsaw\Ransomware.Jigsaw.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 37.0.2.5583 Modules
| |||||||||||||||
| 2484 | "C:\Users\admin\AppData\Local\Drpbx\drpbx.exe" C:\Users\admin\AppData\Local\Temp\Ransomware.Jigsaw\Ransomware.Jigsaw.exe | C:\Users\admin\AppData\Local\Drpbx\drpbx.exe | Ransomware.Jigsaw.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 37.0.2.5583 Modules
| |||||||||||||||
| 2504 | "C:\Users\admin\AppData\Local\Temp\Ransomware.Jigsaw\Ransomware.Jigsaw.exe" | C:\Users\admin\AppData\Local\Temp\Ransomware.Jigsaw\Ransomware.Jigsaw.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 37.0.2.5583 Modules
| |||||||||||||||
| 2572 | "C:\Users\admin\AppData\Local\Temp\Ransomware.Jigsaw\Ransomware.Jigsaw.exe" | C:\Users\admin\AppData\Local\Temp\Ransomware.Jigsaw\Ransomware.Jigsaw.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 37.0.2.5583 Modules
| |||||||||||||||
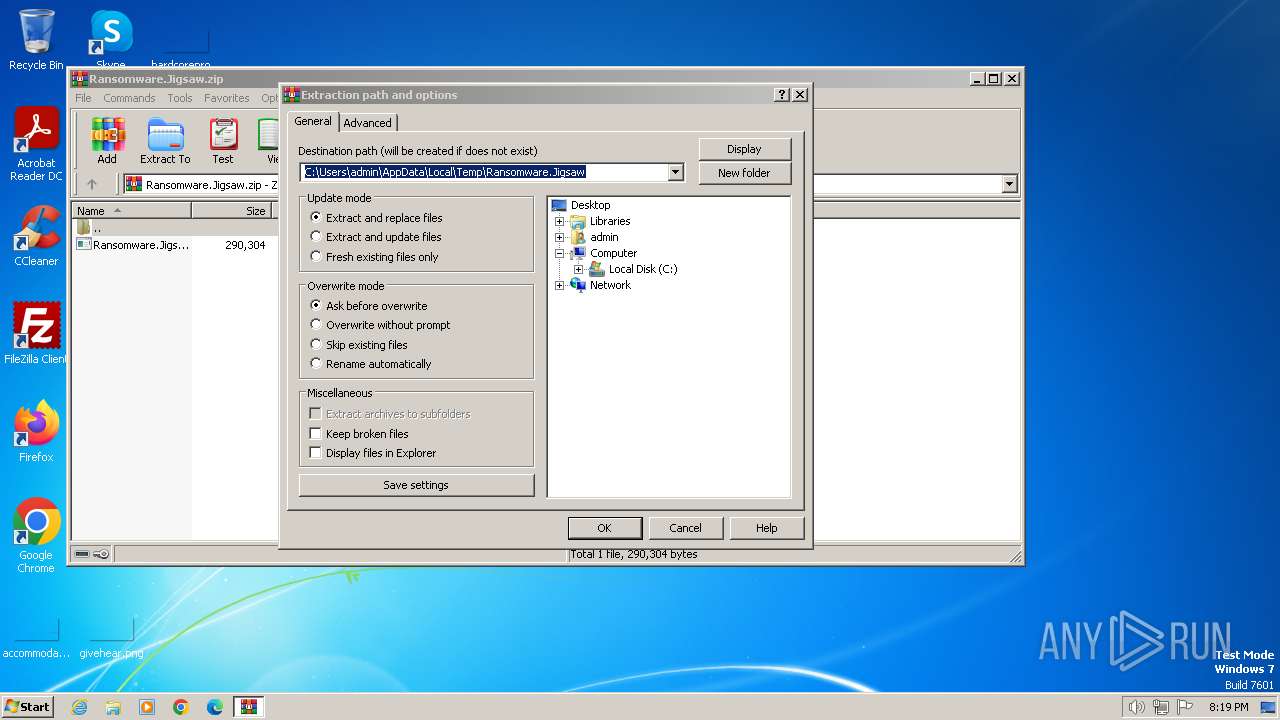
| 2628 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Ransomware.Jigsaw.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2756 | "C:\Users\admin\AppData\Local\Temp\Ransomware.Jigsaw\Ransomware.Jigsaw.exe" | C:\Users\admin\AppData\Local\Temp\Ransomware.Jigsaw\Ransomware.Jigsaw.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 37.0.2.5583 Modules
| |||||||||||||||
| 3040 | "C:\Users\admin\AppData\Local\Temp\Ransomware.Jigsaw\Ransomware.Jigsaw.exe" | C:\Users\admin\AppData\Local\Temp\Ransomware.Jigsaw\Ransomware.Jigsaw.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 37.0.2.5583 Modules
| |||||||||||||||
| 3112 | "C:\Users\admin\AppData\Local\Temp\Ransomware.Jigsaw\Ransomware.Jigsaw.exe" | C:\Users\admin\AppData\Local\Temp\Ransomware.Jigsaw\Ransomware.Jigsaw.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 37.0.2.5583 Modules
| |||||||||||||||
Total events
63 395
Read events
63 366
Write events
29
Delete events
0
Modification events
| (PID) Process: | (2628) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2628) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (2628) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (2628) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (2628) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (2628) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2628) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2628) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2628) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2572) Ransomware.Jigsaw.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
5
Suspicious files
890
Text files
54
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2484 | drpbx.exe | C:\MSOCache\All Users\{90140000-0015-040C-0000-0000000FF1CE}-C\branding.xml.fun | binary | |
MD5:D2112D5C5B9E497E6E4209DE70F2574C | SHA256:F43E43A77A95CB8C9159A1CEC6D038EF9A956EC3327BCFC95B998EC036B2D29C | |||
| 2484 | drpbx.exe | C:\MSOCache\All Users\{90140000-0015-040C-0000-0000000FF1CE}-C\AccessMUI.xml.fun | binary | |
MD5:C004E8491FF15DE08F1FA4E4C998A799 | SHA256:11F36C2CDDB7ACFBE430A304D826F2D3921826B33B08A9A82624AD6ADB3D3C74 | |||
| 2572 | Ransomware.Jigsaw.exe | C:\Users\admin\AppData\Roaming\Frfx\firefox.exe | executable | |
MD5:2773E3DC59472296CB0024BA7715A64E | SHA256:3AE96F73D805E1D3995253DB4D910300D8442EA603737A1428B613061E7F61E7 | |||
| 2484 | drpbx.exe | C:\MSOCache\All Users\{90140000-0015-0407-0000-0000000FF1CE}-C\branding.xml.fun | binary | |
MD5:AF3B47EE3239EE27A36DF974BA6FF35A | SHA256:FD6C354E84802174AB77076F4167F39BD68CAB971EC46A80000BDB8150F05CF5 | |||
| 2572 | Ransomware.Jigsaw.exe | C:\Users\admin\AppData\Local\Drpbx\drpbx.exe | executable | |
MD5:2773E3DC59472296CB0024BA7715A64E | SHA256:3AE96F73D805E1D3995253DB4D910300D8442EA603737A1428B613061E7F61E7 | |||
| 2484 | drpbx.exe | C:\MSOCache\All Users\{90140000-0015-0407-0000-0000000FF1CE}-C\AccessMUI.xml.fun | binary | |
MD5:B8E36A31142237D9E5C6A18056D448C1 | SHA256:9E30A1A8685998EC8227FAA33A0FD0B2485FF430C4A3D4FC41CDAC6C33F33BE7 | |||
| 2484 | drpbx.exe | C:\MSOCache\All Users\{90140000-0015-0407-0000-0000000FF1CE}-C\Setup.xml.fun | binary | |
MD5:26F9CD4F0D02DAD6930E5236953A470D | SHA256:53D145BB1F639490715965053E247D07633EC8C3A7EBCA2FBED934427968D25A | |||
| 2484 | drpbx.exe | C:\MSOCache\All Users\{90140000-0015-040C-0000-0000000FF1CE}-C\Setup.xml.fun | binary | |
MD5:9D19D98D71BBB006AED9379F74906F6B | SHA256:E32F5C1558986B99421C3F197F1FEFDF2CB485693FF4AD4963904CBBBEBB9574 | |||
| 2484 | drpbx.exe | C:\MSOCache\All Users\{90140000-0015-0412-0000-0000000FF1CE}-C\branding.xml.fun | binary | |
MD5:7B192D60D97933EB76C4BCEB21C8189C | SHA256:0A0193004AC8E5882C3797AC06378540FC0A31DE45E5828316CFA52C70FF6EC6 | |||
| 2484 | drpbx.exe | C:\MSOCache\All Users\{90140000-0015-0411-0000-0000000FF1CE}-C\branding.xml.fun | binary | |
MD5:4DB4DDE56A7D1D8B4BA2487F3834F59B | SHA256:5E665BA65BA94CDA7C8775B6D64877691B8C28F3714FF0FDF354905D5EA0CCBC | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
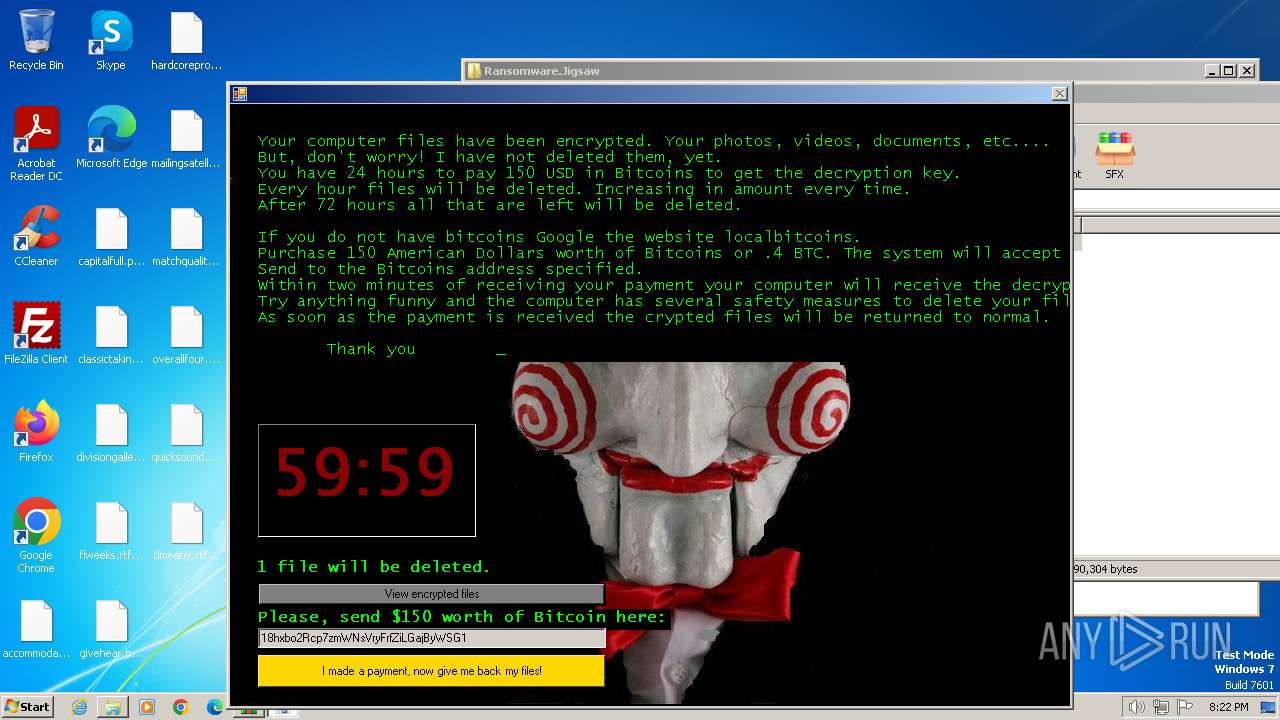
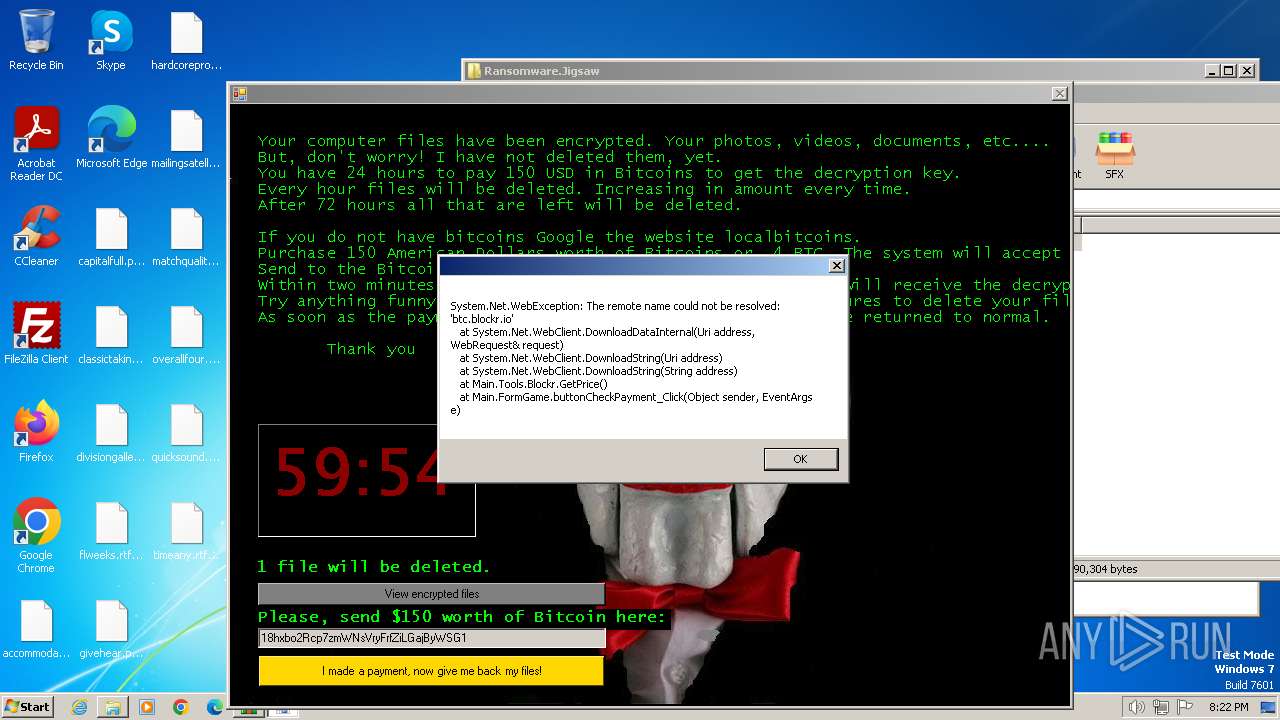
btc.blockr.io |
| unknown |