| File name: | COVID-19 Positive Staff Member Update ID8098 Monday 03302020.msg |
| Full analysis: | https://app.any.run/tasks/cfbc1278-86d8-4924-8683-9a2921d09083 |
| Verdict: | Malicious activity |
| Analysis date: | March 31, 2020, 07:24:33 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | 3D0F16121CD54427F73F55533B404C02 |
| SHA1: | 0D120487E19E162A92BB8BC5FD58383A25A87AE7 |
| SHA256: | BC5C82CB6C1364FCAF9BB5364CCC72482F6752C399BE06C2EEC853A9AF0CCE94 |
| SSDEEP: | 768:IAsSeGzsUI/rubmdOG50LWsKsWsK6IQDojsJiX6PqkfKdGNEefHYlKR2fYl06NFQ:IOYabSOI0LWEWChDisJTqv1PJ |
MALICIOUS
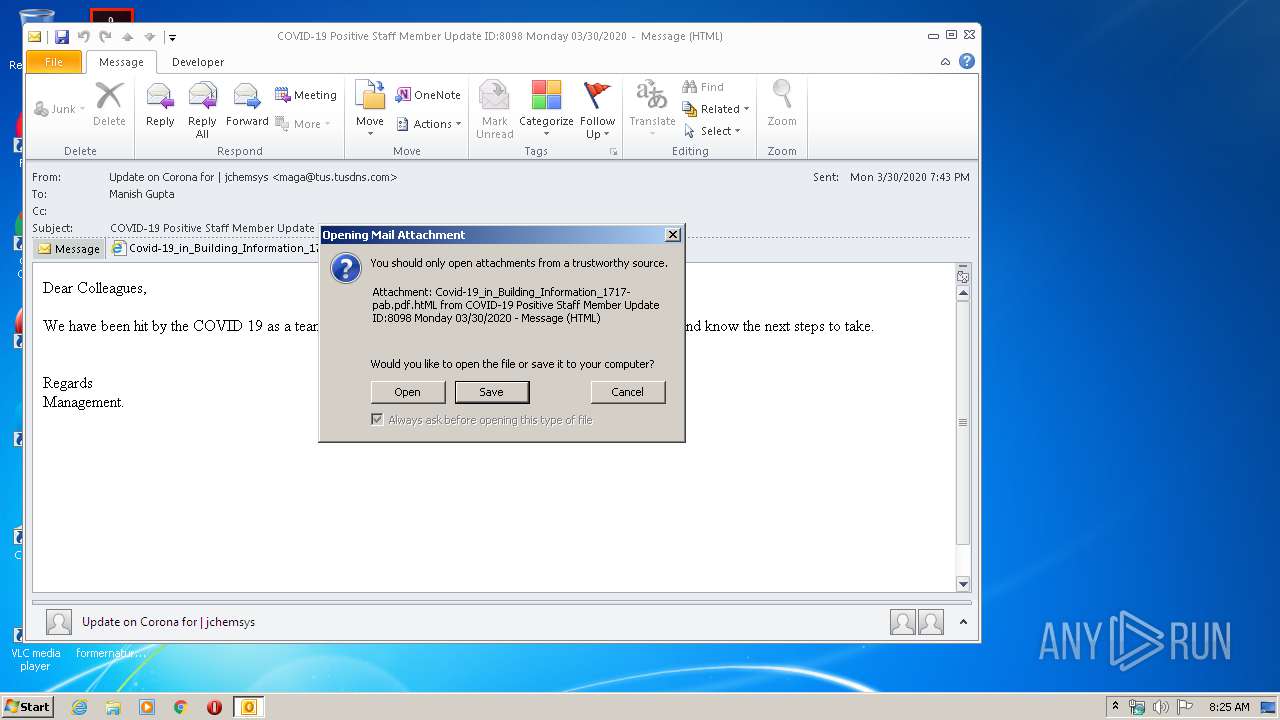
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 2952)
SUSPICIOUS
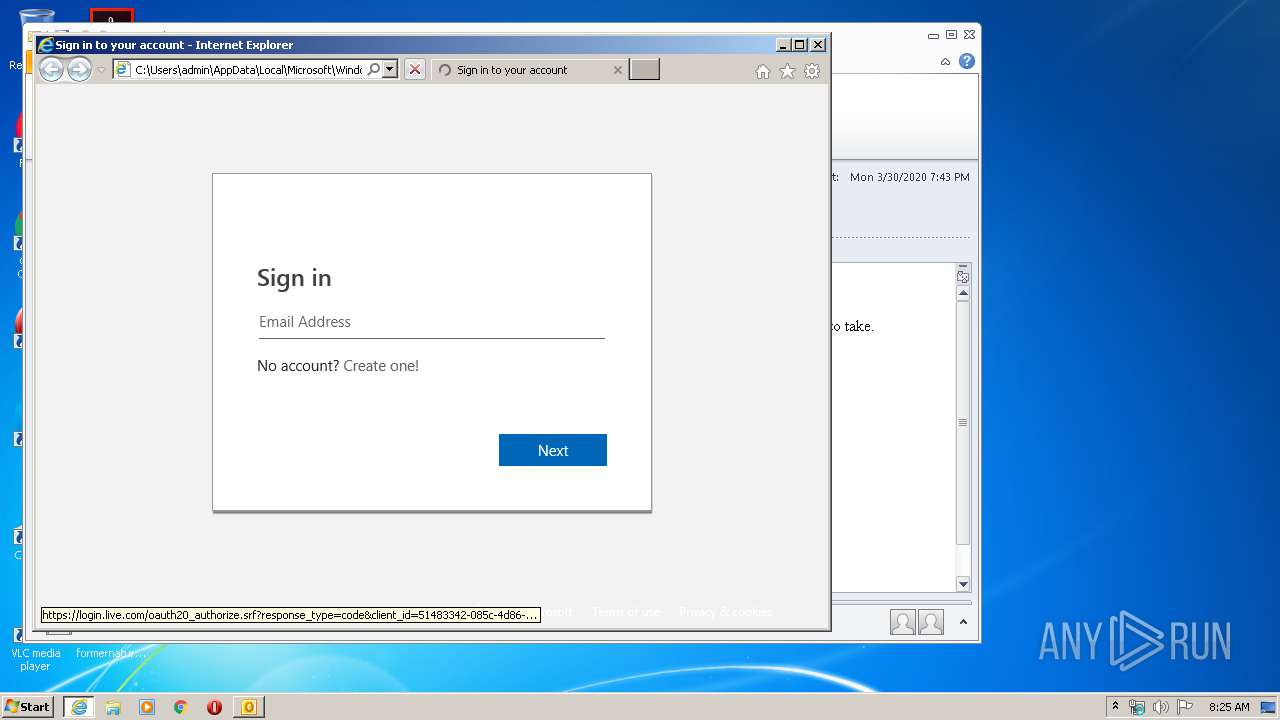
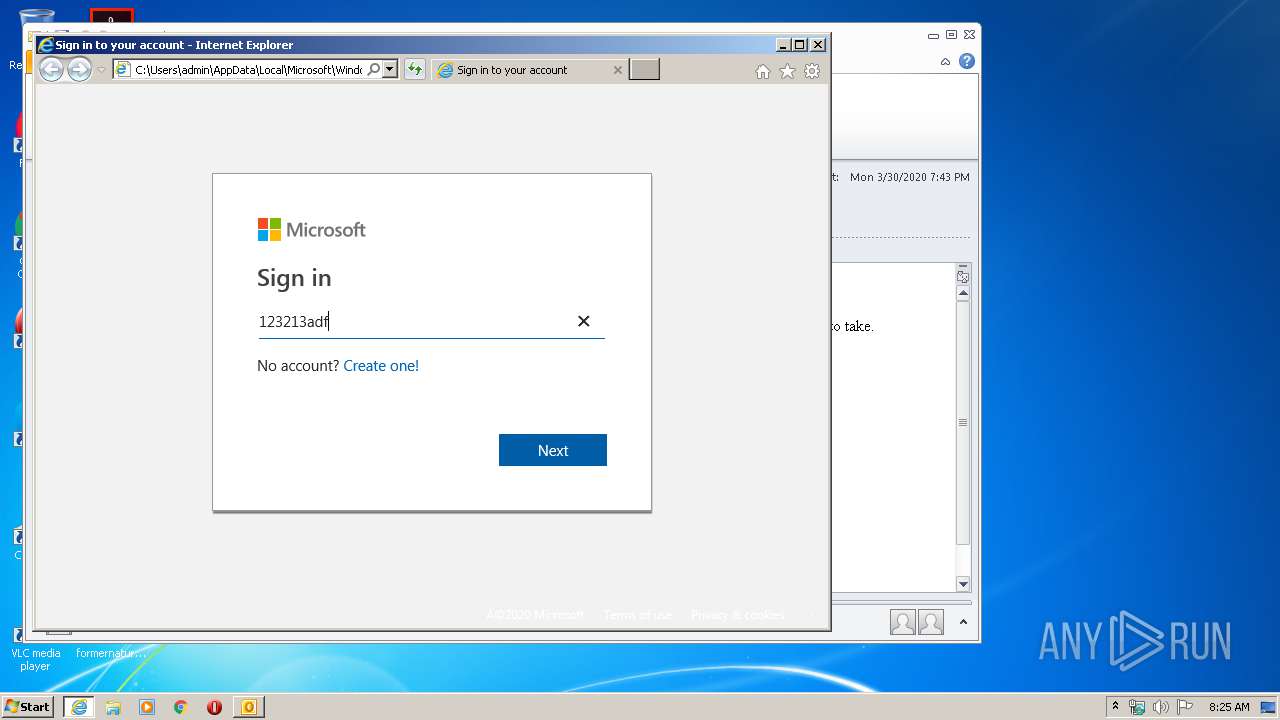
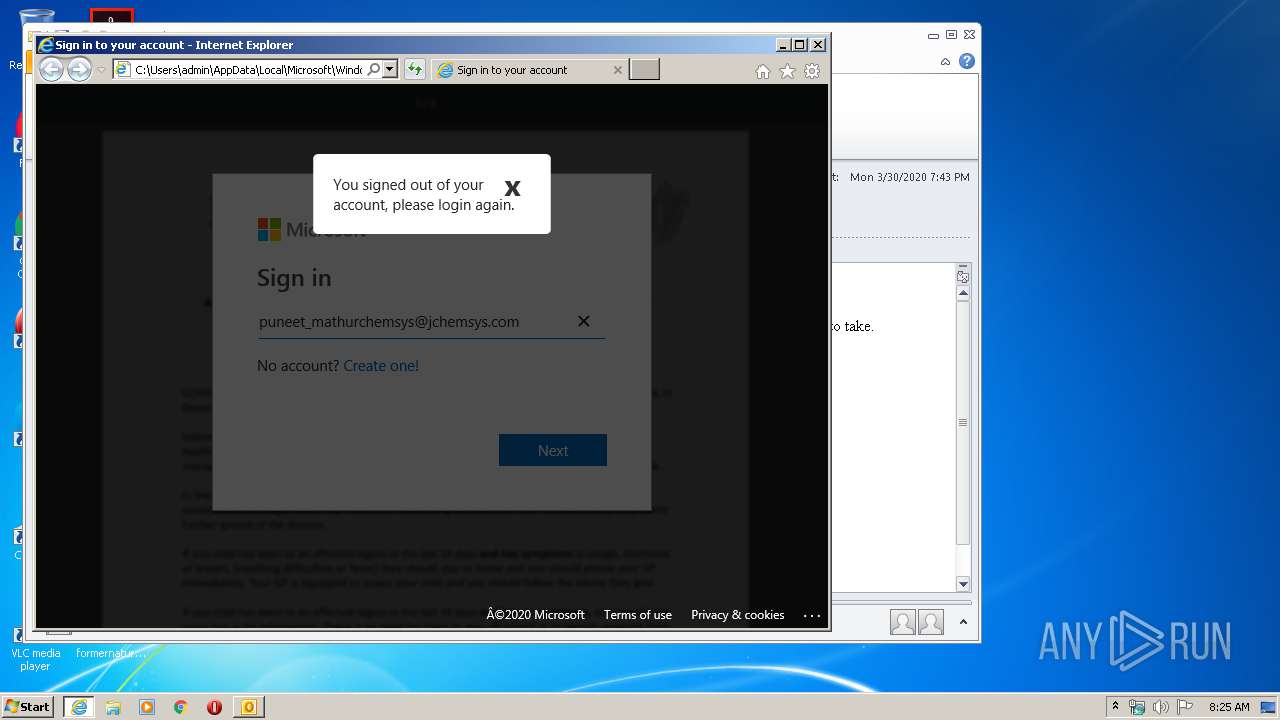
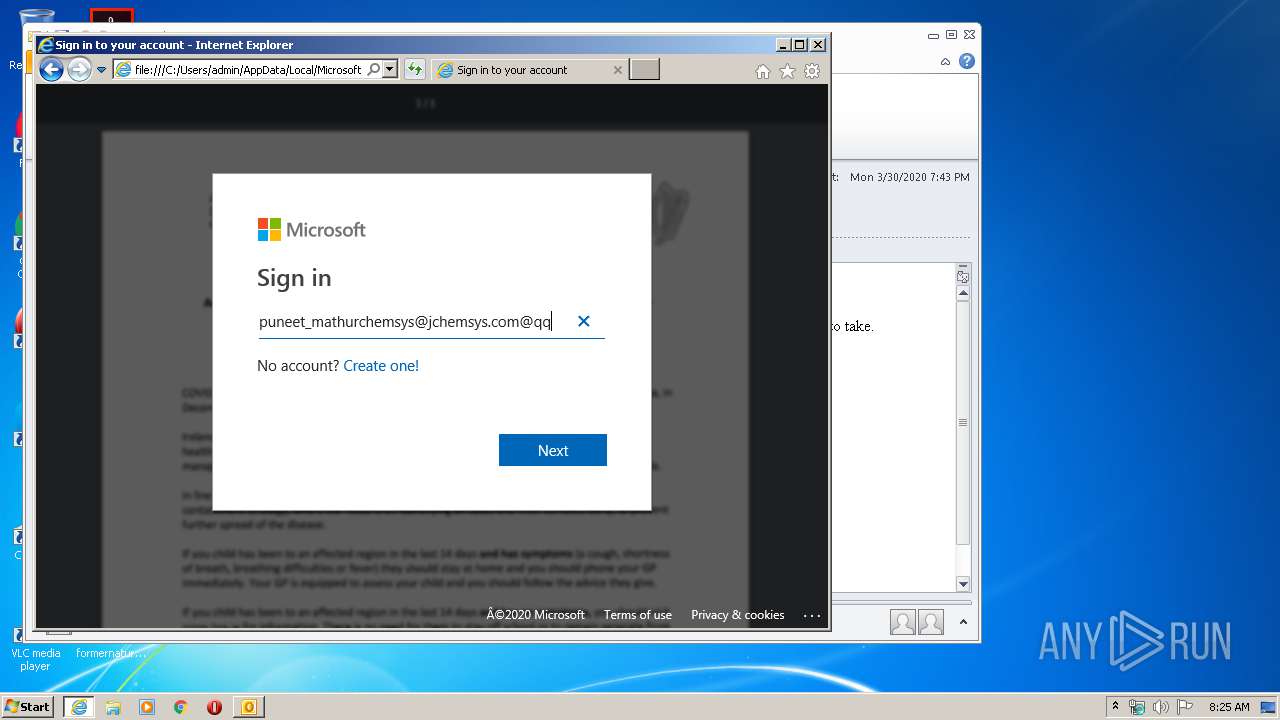
Starts Internet Explorer
- OUTLOOK.EXE (PID: 2952)
Creates files in the user directory
- OUTLOOK.EXE (PID: 2952)
INFO
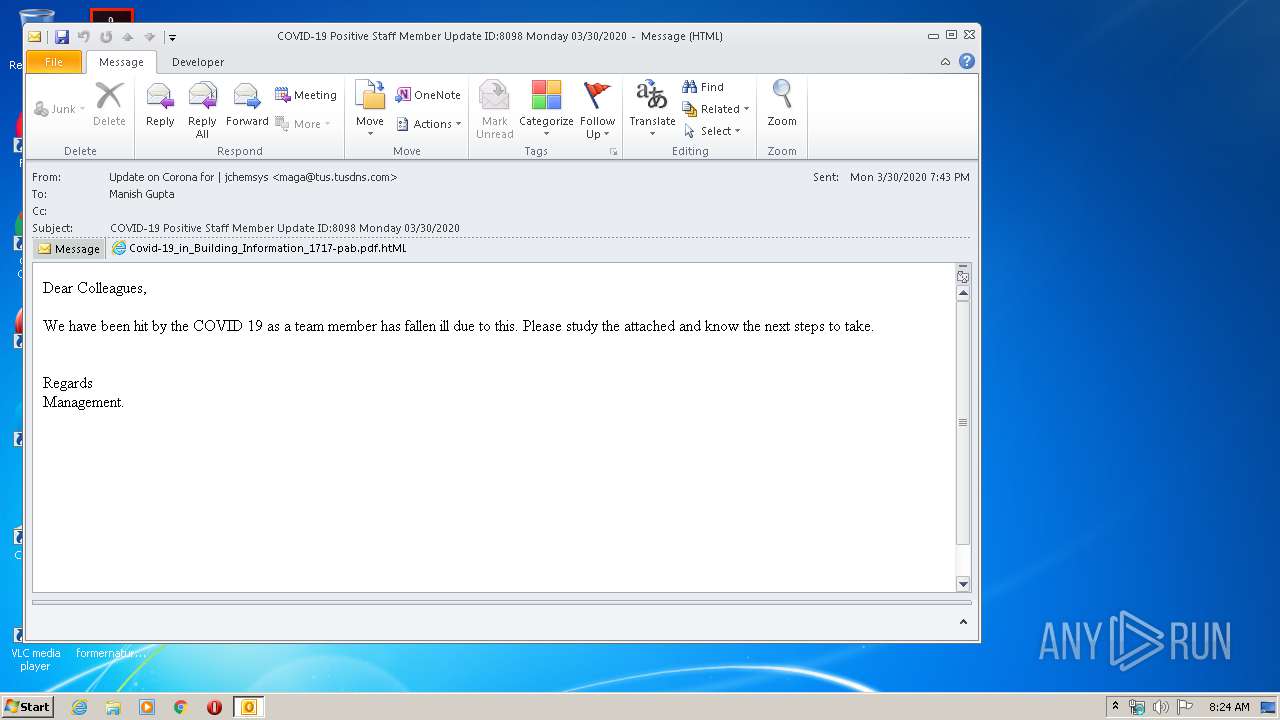
Drops Coronavirus (possible) decoy
- OUTLOOK.EXE (PID: 2952)
Reads Internet Cache Settings
- iexplore.exe (PID: 2824)
- iexplore.exe (PID: 1168)
- OUTLOOK.EXE (PID: 2952)
Changes internet zones settings
- iexplore.exe (PID: 2824)
Reads internet explorer settings
- iexplore.exe (PID: 1168)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 2952)
Changes settings of System certificates
- iexplore.exe (PID: 2824)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2824)
Reads settings of System Certificates
- iexplore.exe (PID: 2824)
- iexplore.exe (PID: 1168)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
38
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1168 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2824 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2824 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\UPI6MK7G\Covid-19_in_Building_Information_1717-pab pdf.htML | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2952 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\COVID-19 Positive Staff Member Update ID8098 Monday 03302020.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
Total events
5 913
Read events
3 963
Write events
1 489
Delete events
461
Modification events
| (PID) Process: | (2952) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2952) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2952) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2952) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2952) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2952) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2952) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2952) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2952) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (2952) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
0
Suspicious files
22
Text files
43
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2952 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR6AA9.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2952 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\UPI6MK7G\Covid-19_in_Building_Information_1717-pab pdf (2).htML\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 2952 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 2952 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2952 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\UPI6MK7G\Covid-19_in_Building_Information_1717-pab pdf (2).htML | html | |
MD5:— | SHA256:— | |||
| 2824 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2952 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\UPI6MK7G\Covid-19_in_Building_Information_1717-pab pdf.htML | html | |
MD5:— | SHA256:— | |||
| 1168 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\errorPageStrings[1] | text | |
MD5:— | SHA256:— | |||
| 1168 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\styles[1].css | html | |
MD5:— | SHA256:— | |||
| 2952 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\mapisvc.inf | text | |
MD5:48DD6CAE43CE26B992C35799FCD76898 | SHA256:7BFE1F3691E2B4FB4D61FBF5E9F7782FBE49DA1342DBD32201C2CC8E540DBD1A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
35
DNS requests
20
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2824 | iexplore.exe | GET | 200 | 166.62.13.1:80 | http://ozturkkilcadir.com/favicon.ico | US | — | — | suspicious |
1168 | iexplore.exe | GET | 200 | 2.21.242.197:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | NL | der | 1.37 Kb | whitelisted |
1168 | iexplore.exe | GET | 200 | 2.21.242.197:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | NL | der | 1.37 Kb | whitelisted |
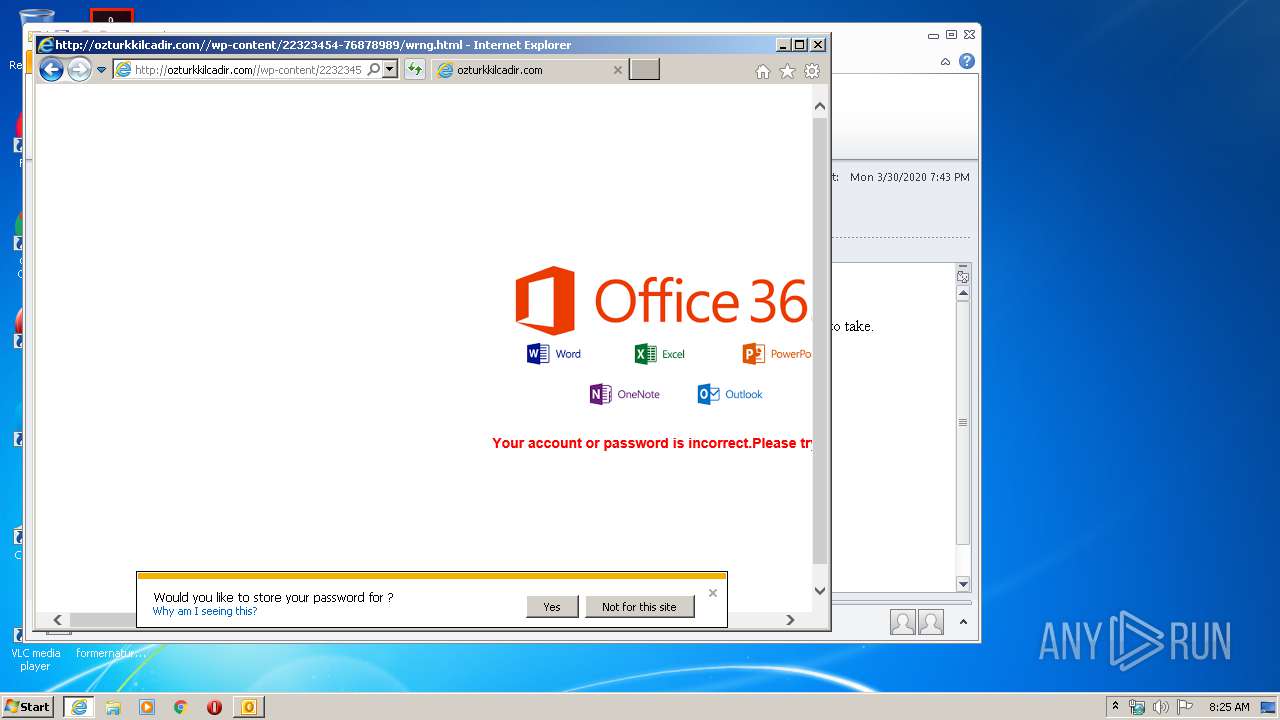
1168 | iexplore.exe | GET | 200 | 166.62.13.1:80 | http://ozturkkilcadir.com//wp-content/22323454-76878989/wrng.html | US | text | 761 b | suspicious |
1168 | iexplore.exe | GET | 200 | 2.21.242.197:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | NL | der | 1.37 Kb | whitelisted |
1168 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR8sWZUnKvbRO5iJhat9GV793rVlAQUrb2YejS0Jvf6xCZU7wO94CTLVBoCECdm7lbrSfOOq9dwovyE3iI%3D | US | der | 471 b | whitelisted |
1168 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBReAhtobFzTvhaRmVeJ38QUchY9AwQUu69%2BAj36pvE8hI6t7jiY7NkyMtQCECsuburZdTZsFIpu26N8jAc%3D | US | der | 727 b | whitelisted |
1168 | iexplore.exe | GET | 200 | 172.217.23.131:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
1168 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR8sWZUnKvbRO5iJhat9GV793rVlAQUrb2YejS0Jvf6xCZU7wO94CTLVBoCECdm7lbrSfOOq9dwovyE3iI%3D | US | der | 471 b | whitelisted |
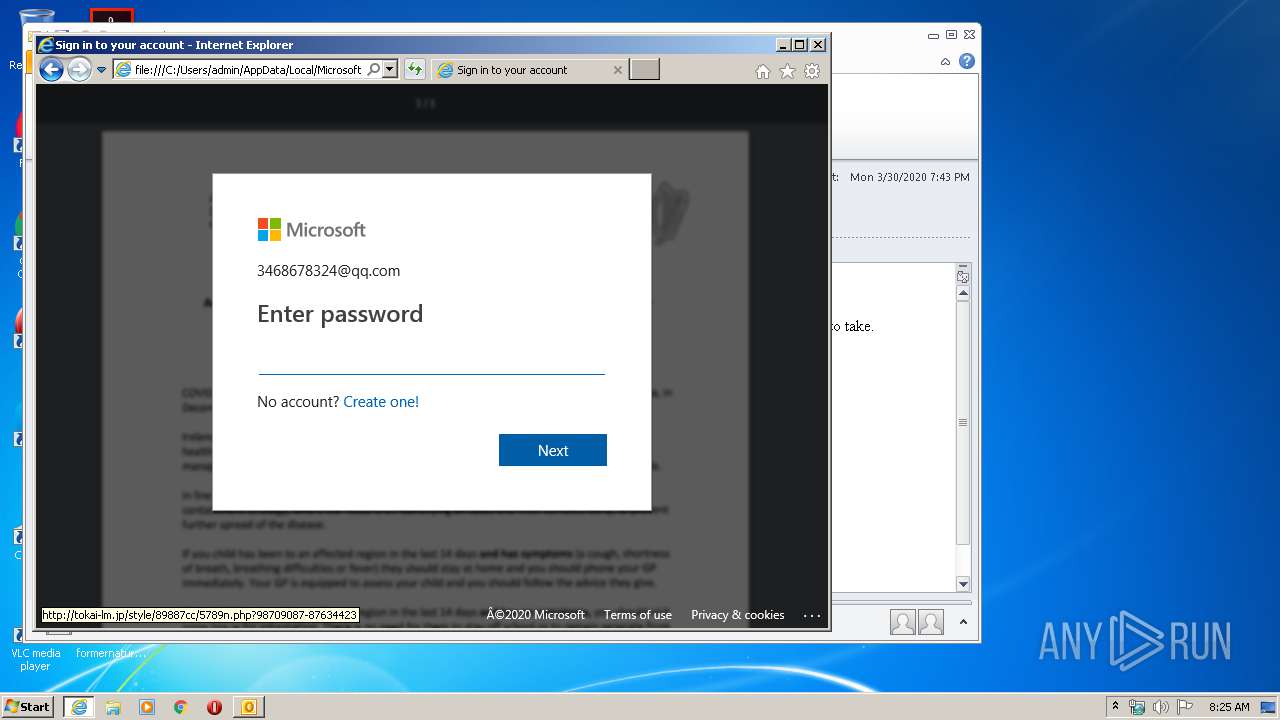
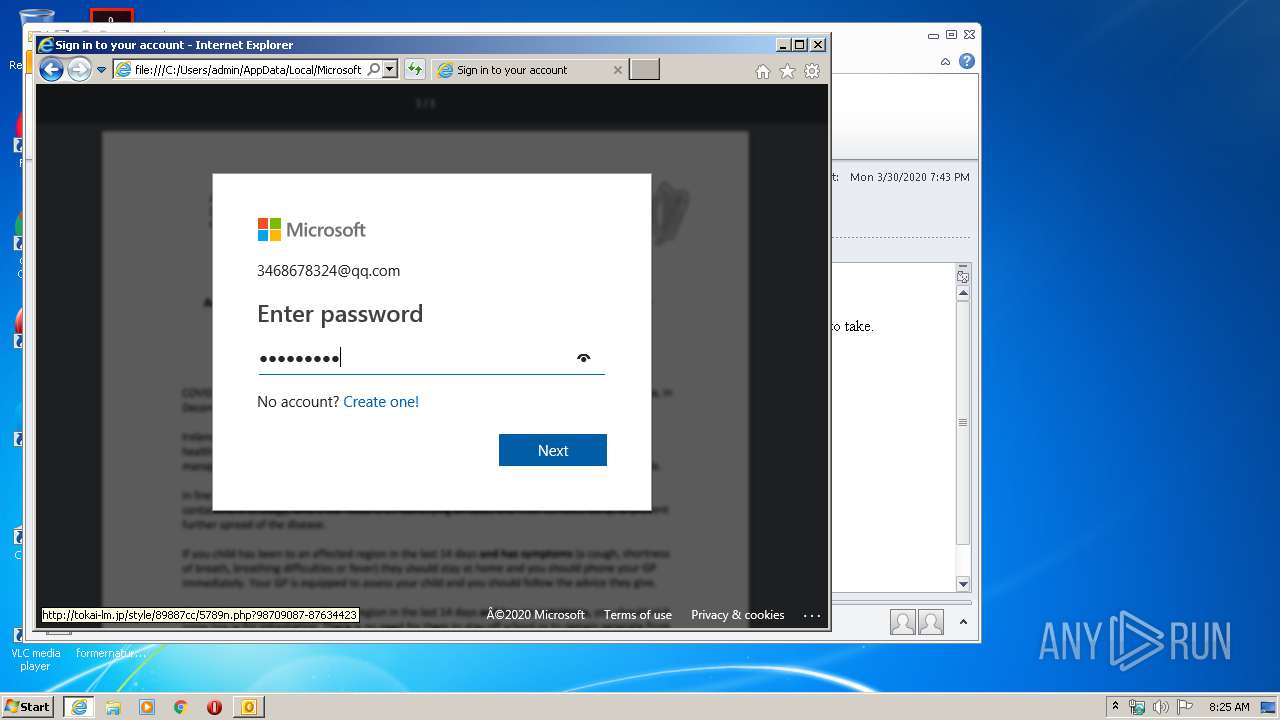
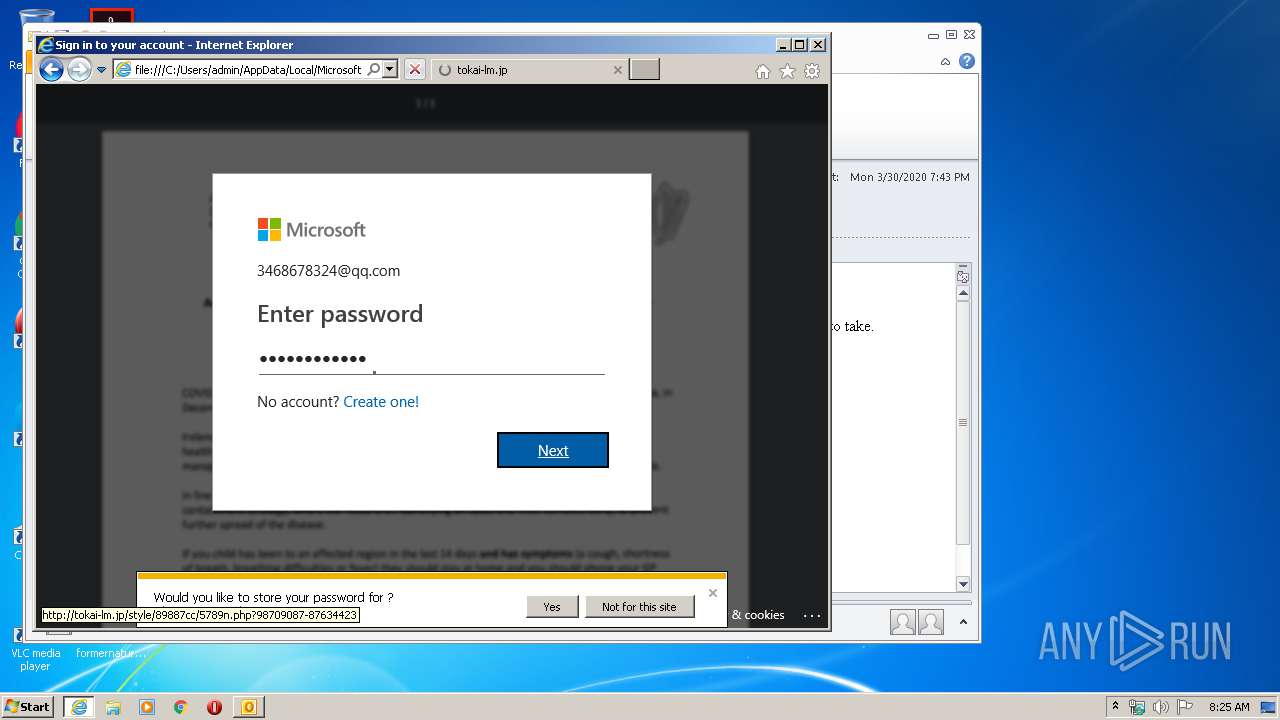
1168 | iexplore.exe | POST | 302 | 150.60.156.116:80 | http://tokai-lm.jp/style/89887cc/5789n.php?98709087-87634423 | JP | binary | 20 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2824 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1168 | iexplore.exe | 50.87.153.159:80 | ibuykenya.com | Unified Layer | US | suspicious |
1168 | iexplore.exe | 184.31.91.84:443 | secure.aadcdn.microsoftonline-p.com | Akamai International B.V. | NL | whitelisted |
1168 | iexplore.exe | 51.15.16.245:80 | i.postimg.cc | Online S.a.s. | NL | unknown |
1168 | iexplore.exe | 209.197.3.24:443 | code.jquery.com | Highwinds Network Group, Inc. | US | malicious |
1168 | iexplore.exe | 51.15.27.129:443 | i.ibb.co | Online S.a.s. | NL | unknown |
1168 | iexplore.exe | 51.15.16.245:443 | i.postimg.cc | Online S.a.s. | NL | unknown |
2824 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
1168 | iexplore.exe | 2.21.242.197:80 | isrg.trustid.ocsp.identrust.com | Akamai International B.V. | NL | whitelisted |
1168 | iexplore.exe | 151.139.128.14:80 | ocsp.usertrust.com | Highwinds Network Group, Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
ibuykenya.com |
| suspicious |
secure.aadcdn.microsoftonline-p.com |
| whitelisted |
i.postimg.cc |
| whitelisted |
code.jquery.com |
| whitelisted |
i.ibb.co |
| shared |
www.bing.com |
| whitelisted |
api.bing.com |
| whitelisted |
isrg.trustid.ocsp.identrust.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
1168 | iexplore.exe | Potential Corporate Privacy Violation | ET POLICY Http Client Body contains pass= in cleartext |