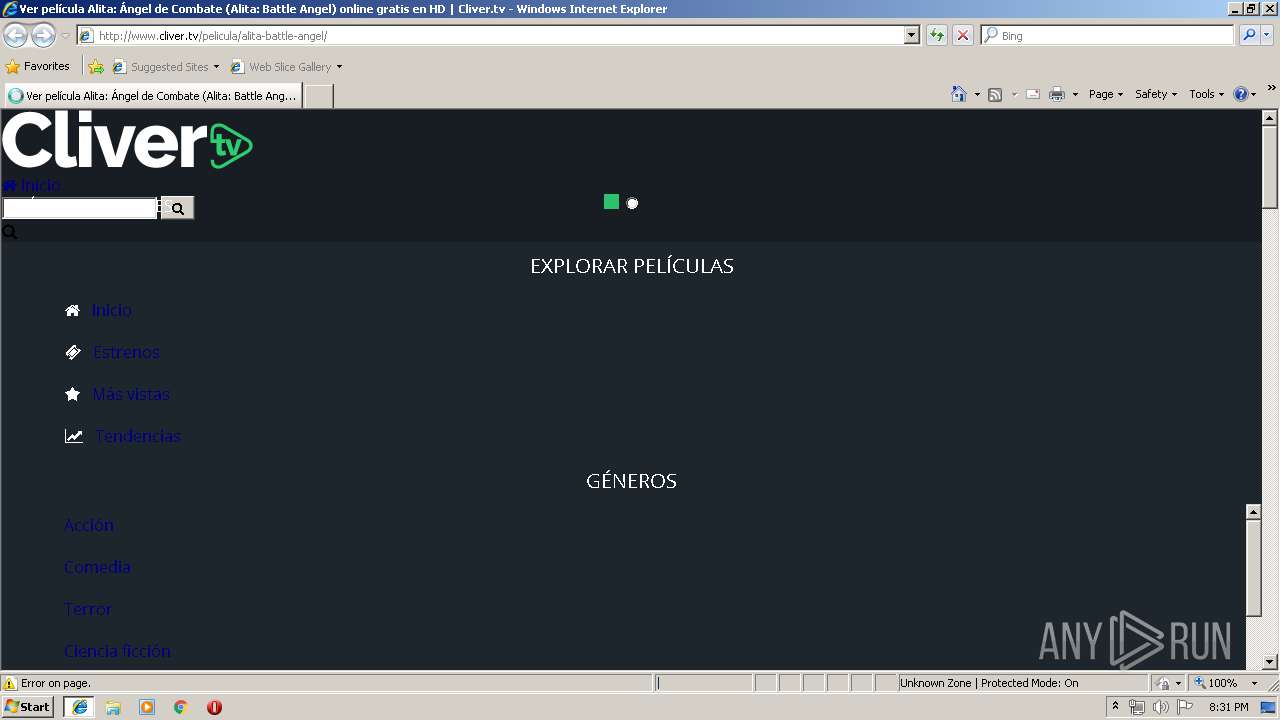
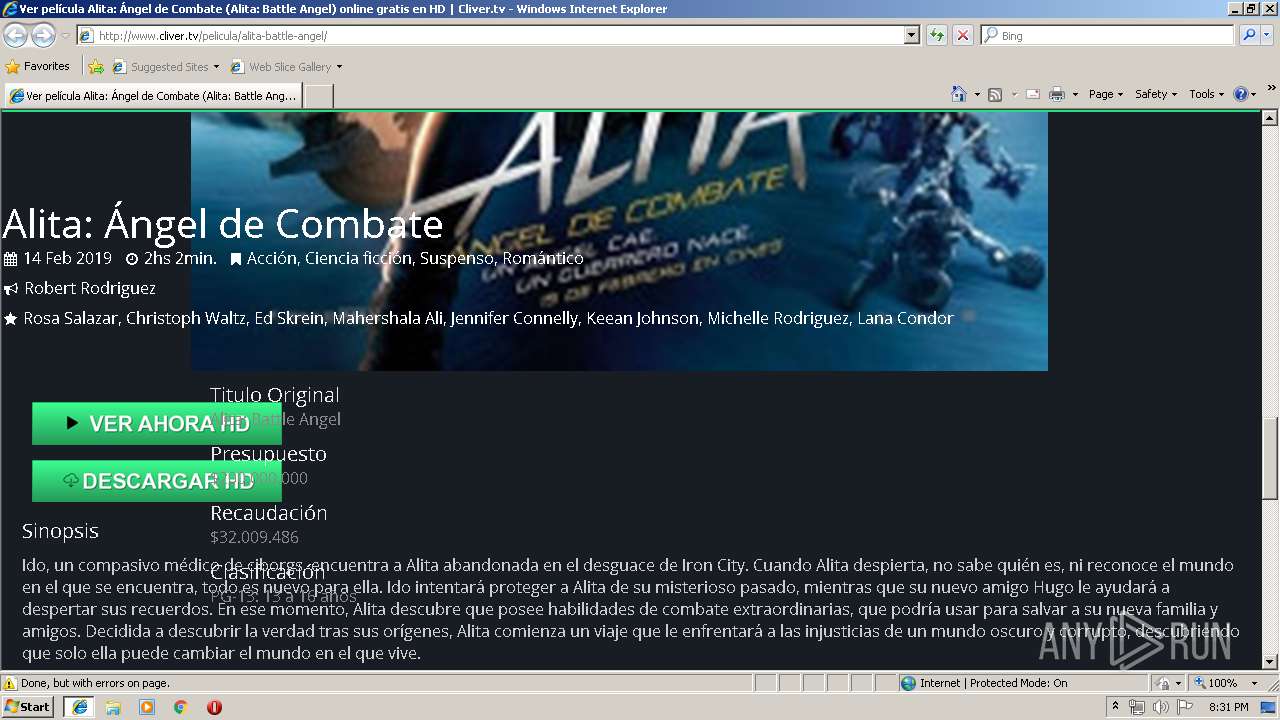
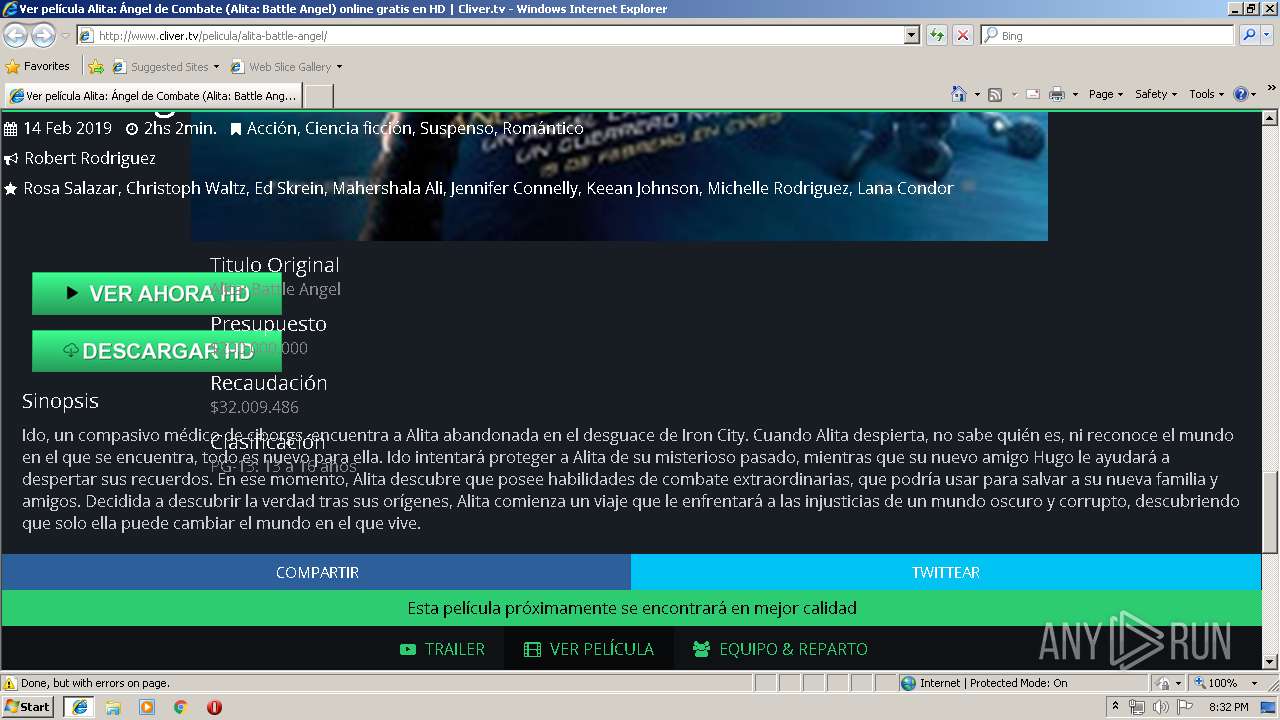
| URL: | http://www.cliver.tv/pelicula/alita-battle-angel/ |
| Full analysis: | https://app.any.run/tasks/5cb048df-ba61-4b41-a23d-b8ca0983a705 |
| Verdict: | Malicious activity |
| Analysis date: | May 10, 2019, 19:31:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | B145EF1D93BF7E7FE7A9EAE77EDEF20F |
| SHA1: | D31D9CA0D964DDE1376AFA7F4E97629E916C7282 |
| SHA256: | BC598F5F6C09364584E27E7D10982A36FFF471E87E5F9133CDF402620BDC34C0 |
| SSDEEP: | 3:N1KJS4EVMqf4HERRJAIE2AJK:Cc4BCKE3OIl |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Creates files in the user directory
- iexplore.exe (PID: 2840)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 3216)
- iexplore.exe (PID: 3108)
Application launched itself
- iexplore.exe (PID: 3108)
Reads internet explorer settings
- iexplore.exe (PID: 2840)
Reads settings of System Certificates
- iexplore.exe (PID: 2840)
Reads Internet Cache Settings
- iexplore.exe (PID: 2840)
- iexplore.exe (PID: 3108)
Changes internet zones settings
- iexplore.exe (PID: 3108)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
34
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2840 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3108 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3108 | "C:\Program Files\Internet Explorer\iexplore.exe" http://www.cliver.tv/pelicula/alita-battle-angel/ | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3216 | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 26.0 r0 Exit code: 0 Version: 26,0,0,131 Modules
| |||||||||||||||
Total events
622
Read events
491
Write events
129
Delete events
2
Modification events
| (PID) Process: | (3108) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3108) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3108) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3108) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (3108) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3108) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000071000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3108) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {37018C53-735A-11E9-B63D-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (3108) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (3108) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 1 | |||
| (PID) Process: | (3108) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E307050005000A0013001F002100AD00 | |||
Executable files
0
Suspicious files
1
Text files
76
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2840 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\AFXJ7R80\alita-battle-angel[1].txt | — | |
MD5:— | SHA256:— | |||
| 2840 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\AFXJ7R80\alita-battle-angel[1].htm | html | |
MD5:— | SHA256:— | |||
| 2840 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\64G2O12W\d13jhr4vol1304_cloudfront_net[1] | text | |
MD5:— | SHA256:— | |||
| 2840 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\64G2O12W\wurfl[1].js | text | |
MD5:— | SHA256:— | |||
| 2840 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\3C43R1OX\styles.min[1].css | text | |
MD5:— | SHA256:— | |||
| 2840 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\3C43R1OX\lnTy7hix9-QVFBfZC80E2o6iT18[1].js | text | |
MD5:— | SHA256:— | |||
| 2840 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\64G2O12W\css[1].txt | text | |
MD5:— | SHA256:— | |||
| 2840 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 2840 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\2L1B7264\js[1] | text | |
MD5:— | SHA256:— | |||
| 2840 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\index.dat | dat | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
57
TCP/UDP connections
31
DNS requests
16
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2840 | iexplore.exe | GET | 204 | 52.200.52.74:80 | http://relandssymphoking.info/SWtKUXpmVCkiRxhZczAZHlIzBhcEPR0JCi07ejUjAz0yIykfUjB3DiAPd2ZNeF5zYlw5Ai5sS28YPjAOPBh3ZVwgBSw+RywZOD4IbFl6OBRsWXoiHzsdIz8dbFl6PB89AyU1X3tbJzAUKAwvI197WyM/DCYIKyUTJgVvYjtsWXoFAzkODyMIJhlvYjtsWXoeGCMOKSVfe1suPh86BW0lX3tbOSQKOQQ4JV97Wz45EzpOeGEKOwQ6NAg9Em9jSiYZb2NKJA4+ORUtTTxsS2dYfn9DZ1psJQooDHdgXDkfPj1HeF5/Zk94XXxoTntZeg | US | — | — | whitelisted |
2840 | iexplore.exe | GET | 204 | 52.200.52.74:80 | http://relandssymphoking.info/ZWwxaWFKU1IaXCs5ayEsVSl0ClJQNFUeGVUlVjwIISRgBCA9KXdPFQwIDF5WVFkIXEcVBVVUUF1KQh0AERlCVFdcSlgHBwpRFx9cVEIBR1FLXxcdEQQLDFhHFRhFBVxUWQReVFRaB1BVV1kA | US | — | — | whitelisted |
2840 | iexplore.exe | GET | 204 | 52.200.52.74:80 | http://relandssymphoking.info/YUVXRzBOejQ0DTUob3RnDAtydXY2ImNiAiMTDyNUNCgvEnsnMhAeXC9gZQUWFSwzegdWdGJ+A0c1PiMNUGMkM1EVMCR6AUcsOSFfXGMhegFPdmNpCU90cTNAACJqdhYRMSMrDVBwYnAFUHNhfgRTdWM | US | — | — | whitelisted |
2840 | iexplore.exe | GET | 204 | 52.200.52.74:80 | http://relandssymphoking.info/TEg0aUFjd1cafB97RCIgJzwCPXIBB1IxCwUEBR4uLyNTGxYEPANPNSUsCV52fX0NXGc8IVBUcHRuRx0gOD1HVHBqIVoPLnFuQlRwYngaWW9/bkAZICt1BU8xODxYVHB5fQNccHp+DV1zeXk | US | — | — | whitelisted |
2840 | iexplore.exe | GET | 200 | 13.53.154.184:80 | http://wurfl.io/wurfl.js | US | text | 339 b | whitelisted |
2840 | iexplore.exe | GET | 200 | 104.24.116.77:80 | http://www.cliver.tv/cdn-cgi/apps/head/lnTy7hix9-QVFBfZC80E2o6iT18.js | US | text | 7.11 Kb | shared |
2840 | iexplore.exe | GET | 200 | 104.24.116.77:80 | http://www.cliver.tv/css/styles.min.css?v=1.1.359 | US | text | 21.5 Kb | shared |
2840 | iexplore.exe | GET | 200 | 104.24.116.77:80 | http://www.cliver.tv/js/code.js | US | text | 26.5 Kb | shared |
2840 | iexplore.exe | GET | 200 | 104.24.116.77:80 | http://www.cliver.tv/pelicula/alita-battle-angel/ | US | html | 6.91 Kb | shared |
2840 | iexplore.exe | GET | 200 | 104.24.116.77:80 | http://www.cliver.tv/js/code.js?_=1557516694267 | US | text | 26.5 Kb | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2840 | iexplore.exe | 173.192.101.24:443 | p347187.clksite.com | SoftLayer Technologies Inc. | US | suspicious |
2840 | iexplore.exe | 108.168.193.189:443 | mybestmv.com | SoftLayer Technologies Inc. | US | suspicious |
2840 | iexplore.exe | 104.24.116.77:80 | www.cliver.tv | Cloudflare Inc | US | shared |
2840 | iexplore.exe | 216.58.210.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2840 | iexplore.exe | 172.217.16.202:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
2840 | iexplore.exe | 216.58.210.8:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
2840 | iexplore.exe | 13.53.154.184:80 | wurfl.io | — | US | unknown |
2840 | iexplore.exe | 13.32.222.69:80 | d13jhr4vol1304.cloudfront.net | Amazon.com, Inc. | US | whitelisted |
— | — | 31.13.90.6:443 | connect.facebook.net | Facebook, Inc. | IE | whitelisted |
3108 | iexplore.exe | 13.107.21.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.cliver.tv |
| unknown |
fonts.googleapis.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
wurfl.io |
| whitelisted |
d13jhr4vol1304.cloudfront.net |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
www.bing.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
relandssymphoking.info |
| unknown |
www.google-analytics.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2840 | iexplore.exe | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |