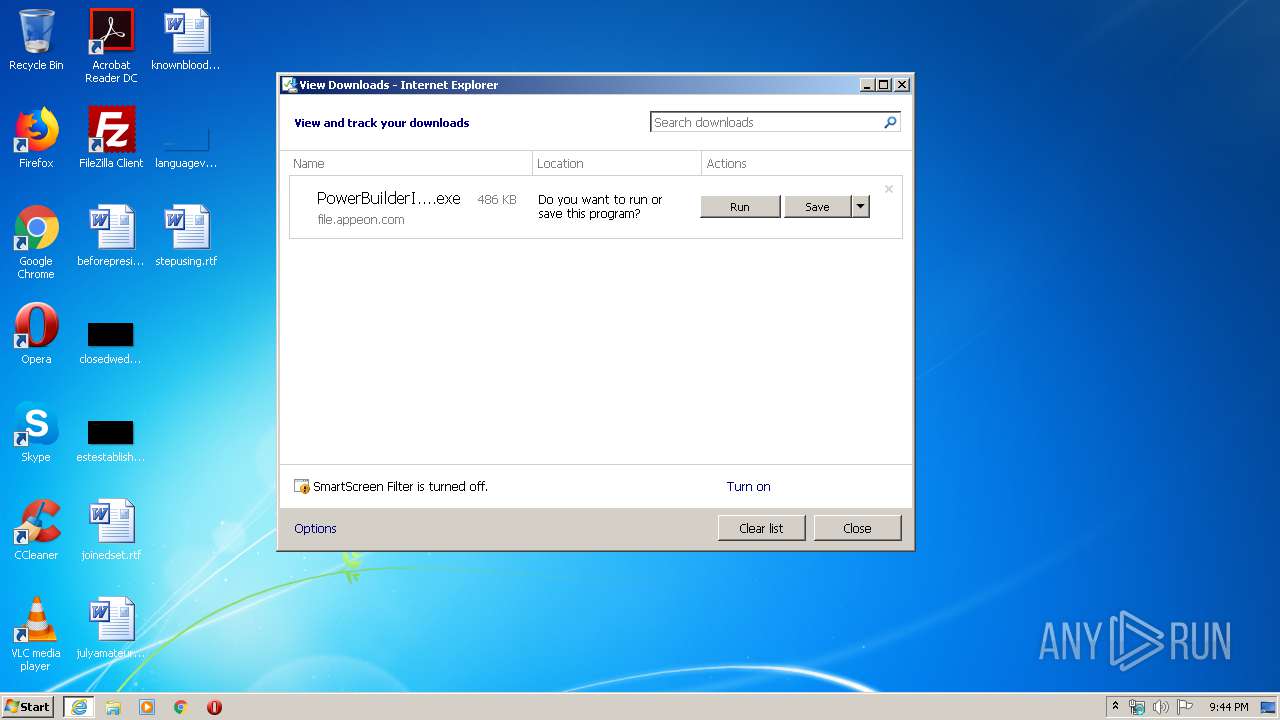
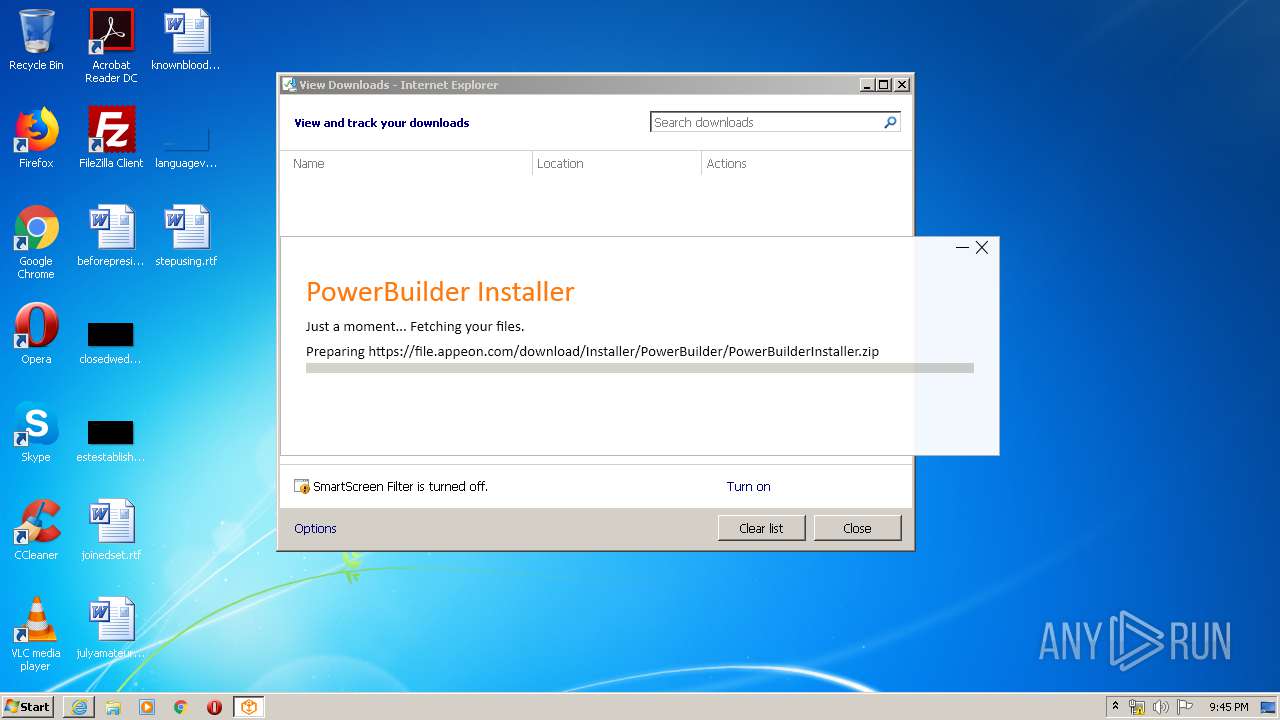
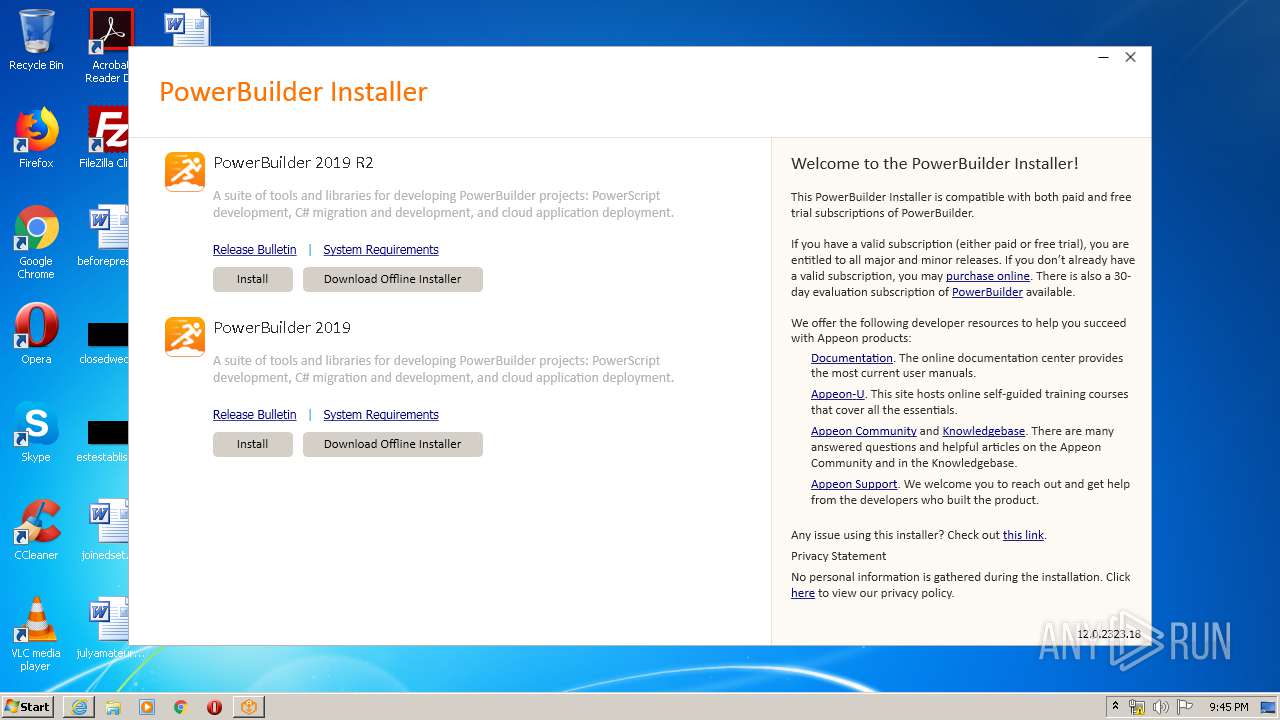
| URL: | https://file.appeon.com/download/Installer/PowerBuilder/PowerBuilderInstaller_bootstrapper.exe |
| Full analysis: | https://app.any.run/tasks/b3ac2d3c-de85-4c6b-aa46-047a315d2c44 |
| Verdict: | Malicious activity |
| Analysis date: | April 15, 2020, 20:43:55 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | DC0FF2A0B224FDD081F17F37BD54DB85 |
| SHA1: | 2F76DF57D7CF54E82FA773BA91598CF19F20C3FB |
| SHA256: | BC56F31AC3A48FBDDB792FF781A88C78F957FF51595FD61360ABE32CA26E0AEE |
| SSDEEP: | 3:N8QAAKL4gXK3AJ4aAzJ4dREgXeRWRXEw4A:2VvhXPWtiREgXOWxEw4A |
MALICIOUS
Application was dropped or rewritten from another process
- PowerBuilderInstaller.Check.exe (PID: 940)
- PowerBuilderInstaller_setup.exe (PID: 2544)
- PowerBuilderInstaller_setup.exe (PID: 4000)
- PowerBuilderInstaller.exe (PID: 3548)
- PowerBuilderInstaller.exe (PID: 280)
- PowerBuilderInstaller_bootstrapper.exe (PID: 4072)
Actions looks like stealing of personal data
- PowerBuilderInstaller_bootstrapper.exe (PID: 4072)
Loads dropped or rewritten executable
- PowerBuilderInstaller.exe (PID: 280)
Changes settings of System certificates
- PowerBuilderInstaller_setup.exe (PID: 2544)
SUSPICIOUS
Executable content was dropped or overwritten
- iexplore.exe (PID: 3408)
- iexplore.exe (PID: 3552)
- PowerBuilderInstaller_bootstrapper.exe (PID: 4072)
- PowerBuilderInstaller_setup.exe (PID: 2544)
Reads Environment values
- PowerBuilderInstaller_setup.exe (PID: 2544)
- PowerBuilderInstaller.exe (PID: 280)
Creates files in the program directory
- PowerBuilderInstaller_setup.exe (PID: 2544)
- PowerBuilderInstaller.exe (PID: 280)
Uses WMIC.EXE to obtain a system information
- cmd.exe (PID: 2568)
- cmd.exe (PID: 2376)
Starts CMD.EXE for commands execution
- PowerBuilderInstaller.exe (PID: 280)
Searches for installed software
- PowerBuilderInstaller.exe (PID: 280)
Adds / modifies Windows certificates
- PowerBuilderInstaller_setup.exe (PID: 2544)
INFO
Reads settings of System Certificates
- iexplore.exe (PID: 3552)
- PowerBuilderInstaller_setup.exe (PID: 2544)
- iexplore.exe (PID: 3408)
Reads Internet Cache Settings
- iexplore.exe (PID: 3552)
- iexplore.exe (PID: 3408)
Changes internet zones settings
- iexplore.exe (PID: 3552)
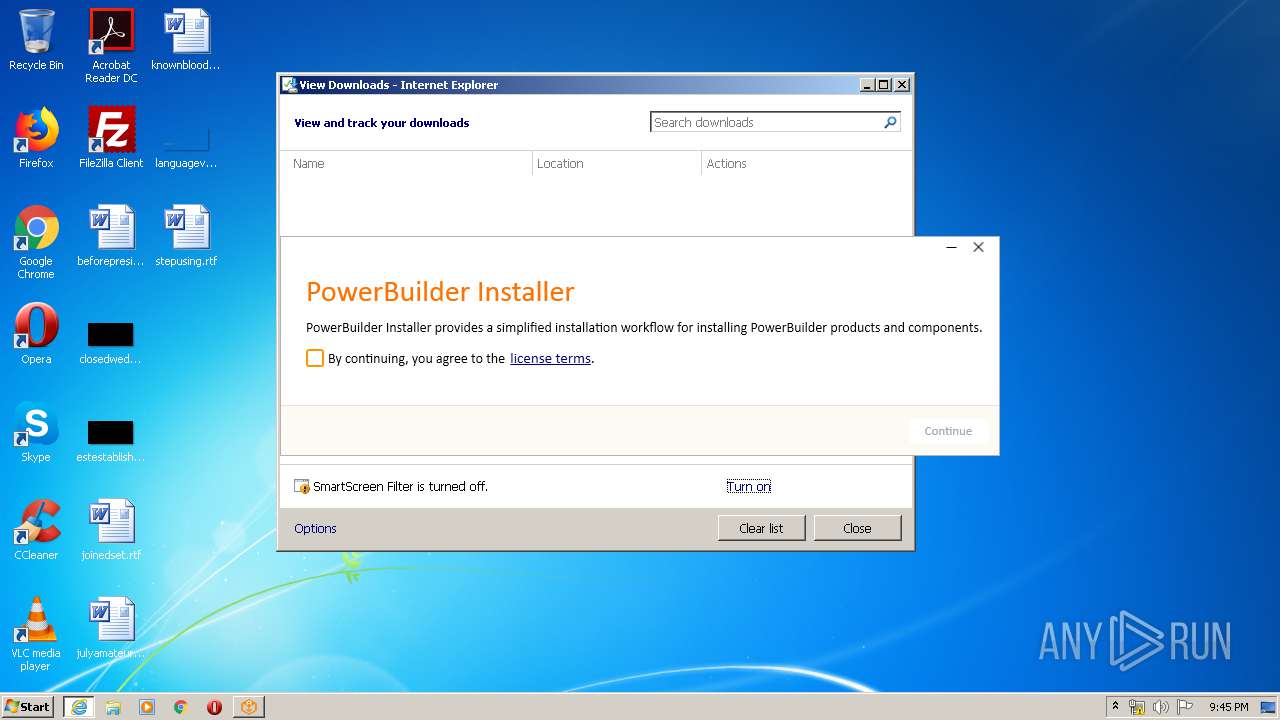
Modifies the phishing filter of IE
- iexplore.exe (PID: 3552)
Creates files in the user directory
- iexplore.exe (PID: 3552)
Changes settings of System certificates
- iexplore.exe (PID: 3552)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3552)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
59
Monitored processes
14
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 280 | "C:\Program Files\Appeon\PowerBuilder Installer\PowerBuilderInstaller.exe" | C:\Program Files\Appeon\PowerBuilder Installer\PowerBuilderInstaller.exe | PowerBuilderInstaller_setup.exe | ||||||||||||
User: admin Company: Appeon Integrity Level: HIGH Description: PowerBuilderInstaller Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 940 | "C:\Users\admin\AppData\Local\Temp\RarSFX0\PowerBuilderInstaller.Check.exe" | C:\Users\admin\AppData\Local\Temp\RarSFX0\PowerBuilderInstaller.Check.exe | — | PowerBuilderInstaller_bootstrapper.exe | |||||||||||
User: admin Company: Appeon Integrity Level: MEDIUM Description: PowerBuilderInstaller.Check Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1352 | findstr /C:"KB2999226" | C:\Windows\system32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1516 | wmic qfe GET hotfixid | C:\Windows\System32\Wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2376 | cmd /c ""C:\Users\admin\AppData\Local\Temp\hotfix.bat"" | C:\Windows\system32\cmd.exe | — | PowerBuilderInstaller.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2544 | "C:\Users\admin\AppData\Local\Temp\RarSFX0\PowerBuilderInstaller_setup.exe" | C:\Users\admin\AppData\Local\Temp\RarSFX0\PowerBuilderInstaller_setup.exe | PowerBuilderInstaller.Check.exe | ||||||||||||
User: admin Company: Appeon Integrity Level: HIGH Description: PowerBuilderInstaller.Update Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2568 | cmd /c ""C:\Users\admin\AppData\Local\Temp\hotfix.bat"" | C:\Windows\system32\cmd.exe | — | PowerBuilderInstaller.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3388 | wmic qfe GET hotfixid | C:\Windows\System32\Wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3408 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3552 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3548 | "C:\Program Files\Appeon\PowerBuilder Installer\PowerBuilderInstaller.exe" | C:\Program Files\Appeon\PowerBuilder Installer\PowerBuilderInstaller.exe | — | PowerBuilderInstaller_setup.exe | |||||||||||
User: admin Company: Appeon Integrity Level: HIGH Description: PowerBuilderInstaller Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
7 312
Read events
2 470
Write events
3 654
Delete events
1 188
Modification events
| (PID) Process: | (3552) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 2949383494 | |||
| (PID) Process: | (3552) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30806886 | |||
| (PID) Process: | (3552) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3552) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3552) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3552) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3552) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3552) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3552) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3552) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
17
Suspicious files
20
Text files
18
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3408 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabE71C.tmp | — | |
MD5:— | SHA256:— | |||
| 3408 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarE71D.tmp | — | |
MD5:— | SHA256:— | |||
| 3408 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\PowerBuilderInstaller_bootstrapper.exe.1pc429i.partial | — | |
MD5:— | SHA256:— | |||
| 3552 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF6168240A69364078.TMP | — | |
MD5:— | SHA256:— | |||
| 3552 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\PowerBuilderInstaller_bootstrapper.exe.1pc429i.partial:Zone.Identifier | — | |
MD5:— | SHA256:— | |||
| 3552 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\CabCBBF.tmp | — | |
MD5:— | SHA256:— | |||
| 3552 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\TarCBC0.tmp | — | |
MD5:— | SHA256:— | |||
| 3552 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\VersionManager\verCC5E.tmp | — | |
MD5:— | SHA256:— | |||
| 3552 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\AWEYKZUW.txt | — | |
MD5:— | SHA256:— | |||
| 3552 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\VDNVDI81.txt | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
14
DNS requests
7
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3408 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA9bw6F2y3ieICDHiTyBZ7Q%3D | US | der | 1.47 Kb | whitelisted |
3552 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
3408 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAVG%2Fhgj9%2BGUHaOfzhTEYXM%3D | US | der | 471 b | whitelisted |
1052 | svchost.exe | GET | 200 | 205.185.216.10:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 56.0 Kb | whitelisted |
3408 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA9bw6F2y3ieICDHiTyBZ7Q%3D | US | der | 1.47 Kb | whitelisted |
3408 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAVG%2Fhgj9%2BGUHaOfzhTEYXM%3D | US | der | 471 b | whitelisted |
3552 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
3552 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3408 | iexplore.exe | 104.239.197.199:443 | file.appeon.com | Rackspace Ltd. | US | unknown |
3408 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3552 | iexplore.exe | 204.79.197.200:443 | ieonline.microsoft.com | Microsoft Corporation | US | whitelisted |
2544 | PowerBuilderInstaller_setup.exe | 104.239.197.199:443 | file.appeon.com | Rackspace Ltd. | US | unknown |
280 | PowerBuilderInstaller.exe | 104.239.197.199:443 | file.appeon.com | Rackspace Ltd. | US | unknown |
1052 | svchost.exe | 205.185.216.10:80 | www.download.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
3552 | iexplore.exe | 72.21.81.200:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3552 | iexplore.exe | 152.199.19.161:443 | r20swj13mr.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3552 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
file.appeon.com |
| unknown |
ocsp.digicert.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
ieonline.microsoft.com |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |