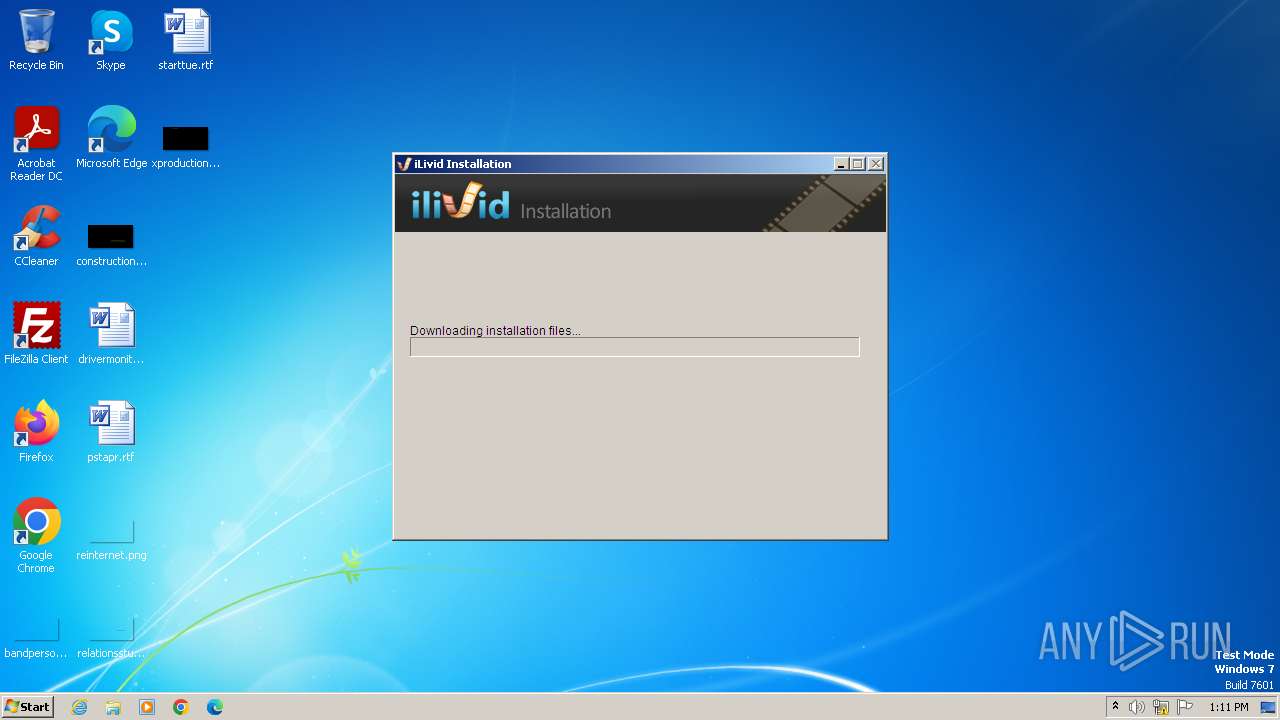
| File name: | ilivid.exe |
| Full analysis: | https://app.any.run/tasks/659e565b-109b-43fe-9da5-cae7d7c2a3ee |
| Verdict: | Malicious activity |
| Analysis date: | May 30, 2024, 12:11:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | B67E9F2F1B2F02259CD508077D969015 |
| SHA1: | 7C5BDCF5CA881F53FFC181783BF91ADF371D6E84 |
| SHA256: | BC536118BA28EB6FFAF020B29A9085CCD5CA202B87E06C40D43077A6632BEBAF |
| SSDEEP: | 49152:641SUP+ckqhzyFzPpDFANx7IThPbBT6N5e76Hm:6+SULkq1czpCT7ITh9Q5e7h |
MALICIOUS
Drops the executable file immediately after the start
- ilivid.exe (PID: 3972)
- ilivid.exe (PID: 1020)
Actions looks like stealing of personal data
- ilivid.exe (PID: 1020)
Steals credentials from Web Browsers
- ilivid.exe (PID: 1020)
SUSPICIOUS
Malware-specific behavior (creating "System.dll" in Temp)
- ilivid.exe (PID: 3972)
- ilivid.exe (PID: 1020)
Executable content was dropped or overwritten
- ilivid.exe (PID: 3972)
- ilivid.exe (PID: 1020)
The process creates files with name similar to system file names
- ilivid.exe (PID: 3972)
- ilivid.exe (PID: 1020)
Application launched itself
- ilivid.exe (PID: 3972)
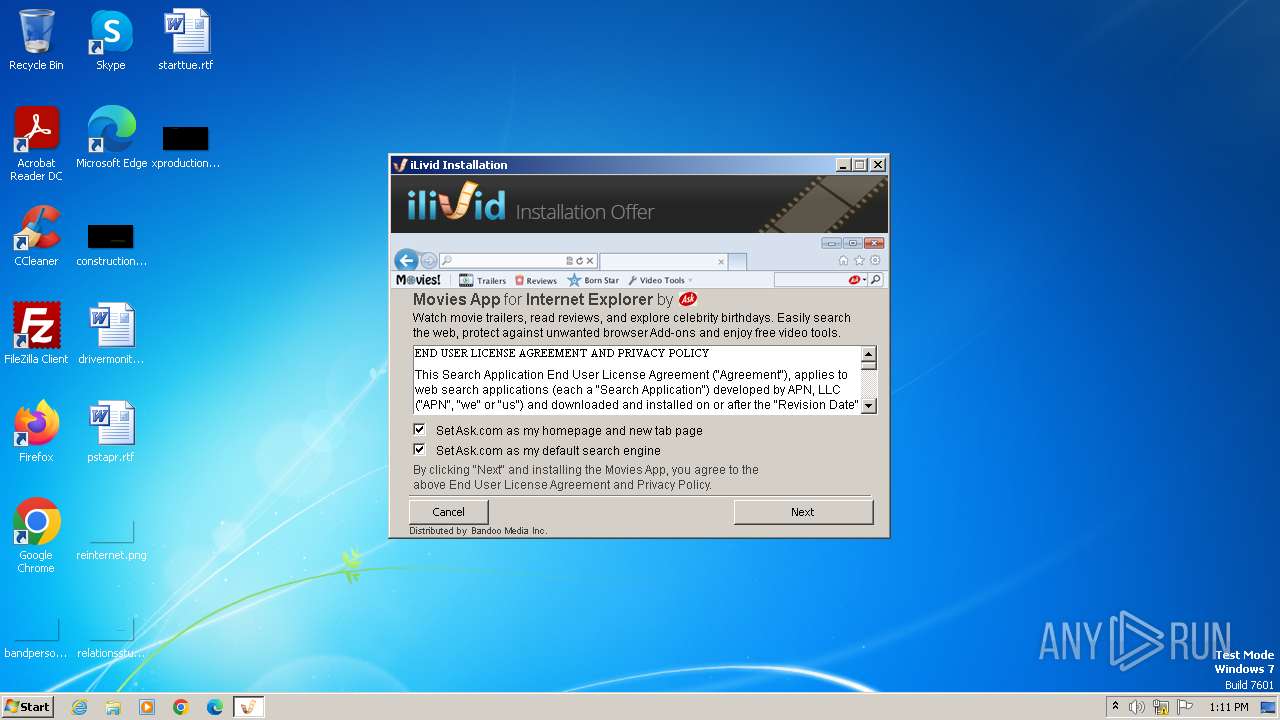
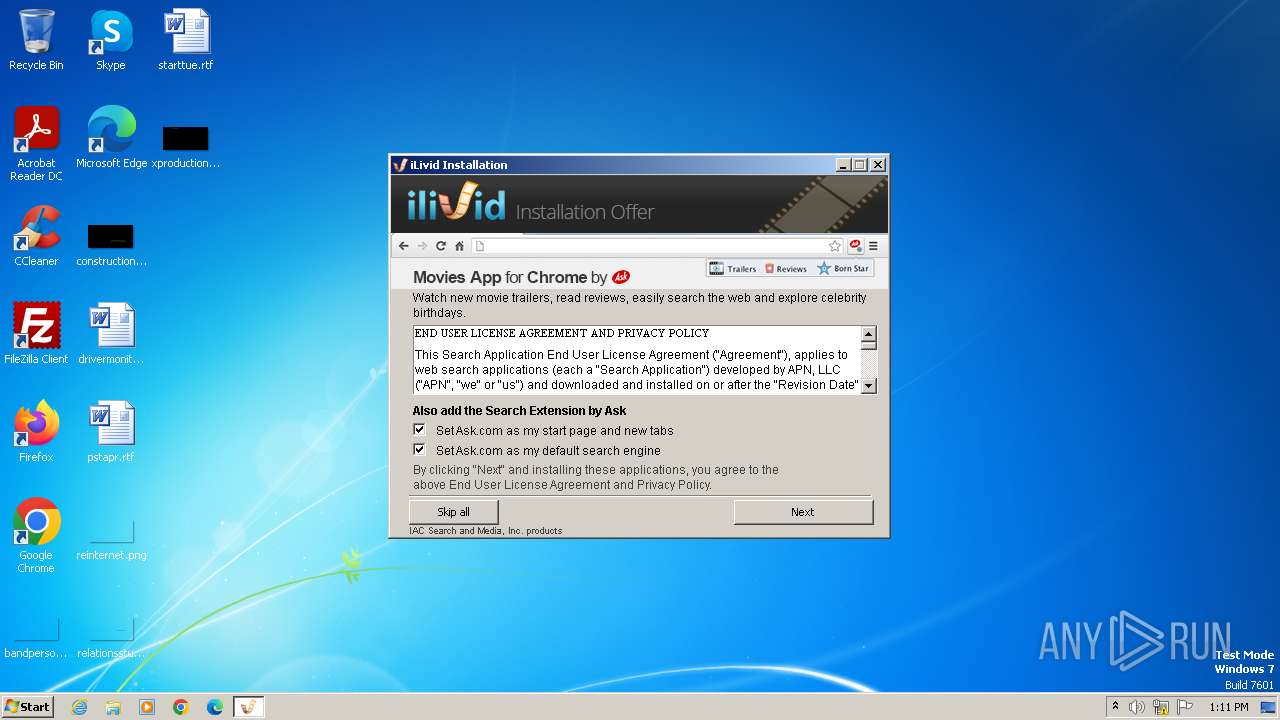
Reads Internet Explorer settings
- ilivid.exe (PID: 1020)
Reads security settings of Internet Explorer
- ilivid.exe (PID: 1020)
Reads Microsoft Outlook installation path
- ilivid.exe (PID: 1020)
Reads the Internet Settings
- ilivid.exe (PID: 1020)
INFO
Create files in a temporary directory
- ilivid.exe (PID: 3972)
- ilivid.exe (PID: 1020)
Checks supported languages
- ilivid.exe (PID: 3972)
- ilivid.exe (PID: 1020)
Reads the computer name
- ilivid.exe (PID: 3972)
- ilivid.exe (PID: 1020)
Process checks whether UAC notifications are on
- ilivid.exe (PID: 3972)
Reads Environment values
- ilivid.exe (PID: 1020)
Creates files or folders in the user directory
- ilivid.exe (PID: 1020)
Checks proxy server information
- ilivid.exe (PID: 1020)
Reads the machine GUID from the registry
- ilivid.exe (PID: 1020)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:02:24 19:20:04+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 29696 |
| InitializedDataSize: | 489984 |
| UninitializedDataSize: | 16896 |
| EntryPoint: | 0x38af |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 5.0.2.4833 |
| ProductVersionNumber: | 5.0.2.4833 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| CompanyName: | Bandoo Media Inc |
| FileDescription: | iLivid Install |
| FileVersion: | 5.0.2.4833 |
| LegalCopyright: | Copyright (c) 2015 |
| ProductName: | iLivid |
| ProductVersion: | 5.0.2.4833 |
Total processes
38
Monitored processes
2
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1020 | "C:\Users\admin\AppData\Local\Temp\ilivid.exe" /UAC:1014E /NCRC | C:\Users\admin\AppData\Local\Temp\ilivid.exe | ilivid.exe | ||||||||||||
User: admin Company: Bandoo Media Inc Integrity Level: HIGH Description: iLivid Install Version: 5.0.2.4833 Modules
| |||||||||||||||
| 3972 | "C:\Users\admin\AppData\Local\Temp\ilivid.exe" | C:\Users\admin\AppData\Local\Temp\ilivid.exe | explorer.exe | ||||||||||||
User: admin Company: Bandoo Media Inc Integrity Level: MEDIUM Description: iLivid Install Version: 5.0.2.4833 Modules
| |||||||||||||||
Total events
5 904
Read events
5 863
Write events
32
Delete events
9
Modification events
| (PID) Process: | (1020) ilivid.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Applications\ilivid.exe |
| Operation: | write | Name: | IsHostApp |
Value: | |||
| (PID) Process: | (1020) ilivid.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1020) ilivid.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1020) ilivid.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1020) ilivid.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1020) ilivid.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1020) ilivid.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1020) ilivid.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1020) ilivid.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1020) ilivid.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | ProxyServer |
Value: | |||
Executable files
14
Suspicious files
0
Text files
19
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1020 | ilivid.exe | C:\Users\admin\AppData\Local\Temp\nsl3AF8.tmp\UserInfo.dll | executable | |
MD5:C7CE0E47C83525983FD2C4C9566B4AAD | SHA256:6293408A5FA6D0F55F0A4D01528EB5B807EE9447A75A28B5986267475EBCD3AE | |||
| 3972 | ilivid.exe | C:\Users\admin\AppData\Local\Temp\nsj357A.tmp\UAC.dll | executable | |
MD5:A88BAAD3461D2E9928A15753B1D93FD7 | SHA256:C5AB2926C268257122D0342739E73573D7EEDA34C861BC7A68A02CBC69BD41AF | |||
| 3972 | ilivid.exe | C:\Users\admin\AppData\Local\Temp\nsj357A.tmp\System.dll | executable | |
MD5:BF712F32249029466FA86756F5546950 | SHA256:7851CB12FA4131F1FEE5DE390D650EF65CAC561279F1CFE70AD16CC9780210AF | |||
| 1020 | ilivid.exe | C:\Users\admin\AppData\Local\Temp\nsl3AF8.tmp\banner_chrome_36.bmp | image | |
MD5:708CE1CC7D980DD3672728ECBE4E55B1 | SHA256:44B246BC4552E0B092D37D8AF4216FBEE7D63203C7D426D180CBD48211465640 | |||
| 1020 | ilivid.exe | C:\Users\admin\AppData\Local\Temp\nsl3AF8.tmp\nsDialogs.dll | executable | |
MD5:4CCC4A742D4423F2F0ED744FD9C81F63 | SHA256:416133DD86C0DFF6B0FCAF1F46DFE97FDC85B37F90EFFB2D369164A8F7E13AE6 | |||
| 1020 | ilivid.exe | C:\Users\admin\AppData\Local\Temp\nsl3AF8.tmp\soffer.dll | executable | |
MD5:75A686C105524CB2BBC945176E1BFBF9 | SHA256:38AD5FFA77BF992DDDD8BB3998B3F616D55ECD5F5C541459480C1374A726FA44 | |||
| 1020 | ilivid.exe | C:\Users\admin\AppData\Local\Temp\nsl3AF8.tmp\nsArray.dll | executable | |
MD5:7FC4723BB0A4118E5F91047021D1AACD | SHA256:8F9BFEEBFA3B070B116DE61A63271B6C25AF0DBB4BBFB4AE73E334D1F8517EFD | |||
| 1020 | ilivid.exe | C:\Users\admin\AppData\Local\Temp\nsl3AF8.tmp\banner.bmp | image | |
MD5:1021FB81021BC073C0E9C31D27F1ECE9 | SHA256:E3EE55AE84B373211AFC1D5FE7F529EF08AAFE34A9C7CAF52D51FA0C20BEE16D | |||
| 1020 | ilivid.exe | C:\Users\admin\AppData\Local\Temp\nsl3AF8.tmp\banner_ff.bmp | image | |
MD5:937D41898BFD2235CEA8DF655E4CCB0F | SHA256:6CF7004C2A5263B73BCEFD62D14204AE71A914681A4F93301865726F283778D5 | |||
| 1020 | ilivid.exe | C:\Users\admin\AppData\Local\Temp\nsl3AF8.tmp\banner_ie.bmp | image | |
MD5:8813CCF246FD02A6799AAB19F693EF1F | SHA256:F1DEB335A8B9E3EA369314427B613C74208B6ED193FD4C6CF6D67851667DADC8 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
6
DNS requests
3
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
1088 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1020 | ilivid.exe | 49.13.77.253:80 | www.secondofferdelivery.com | Hetzner Online GmbH | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.secondofferdelivery.com |
| unknown |
dns.msftncsi.com |
| shared |
download.cdn.ilivid.com |
| unknown |