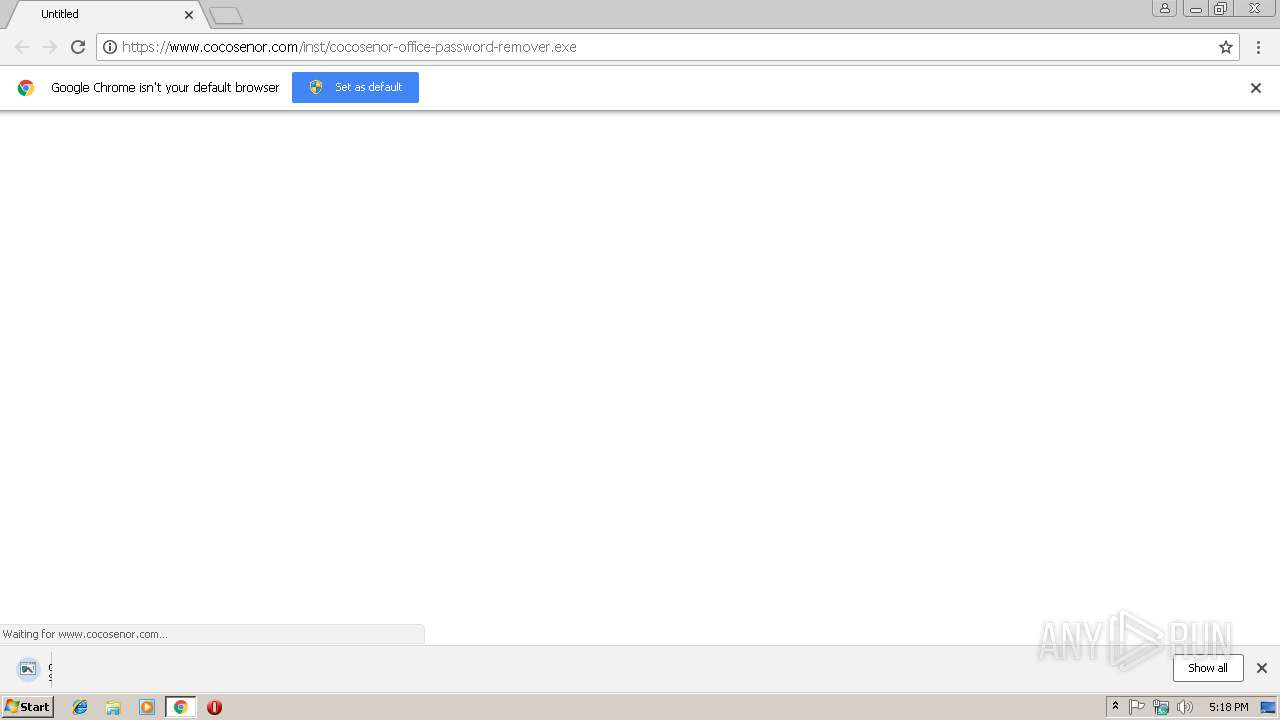
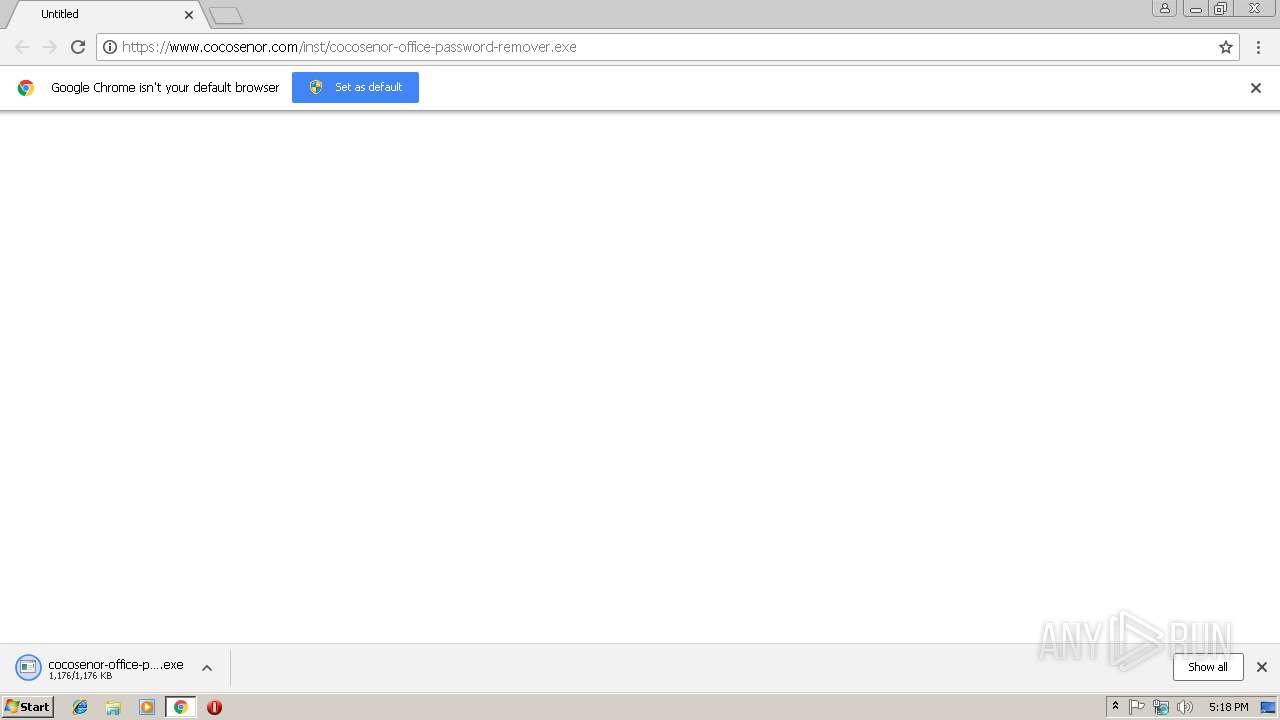
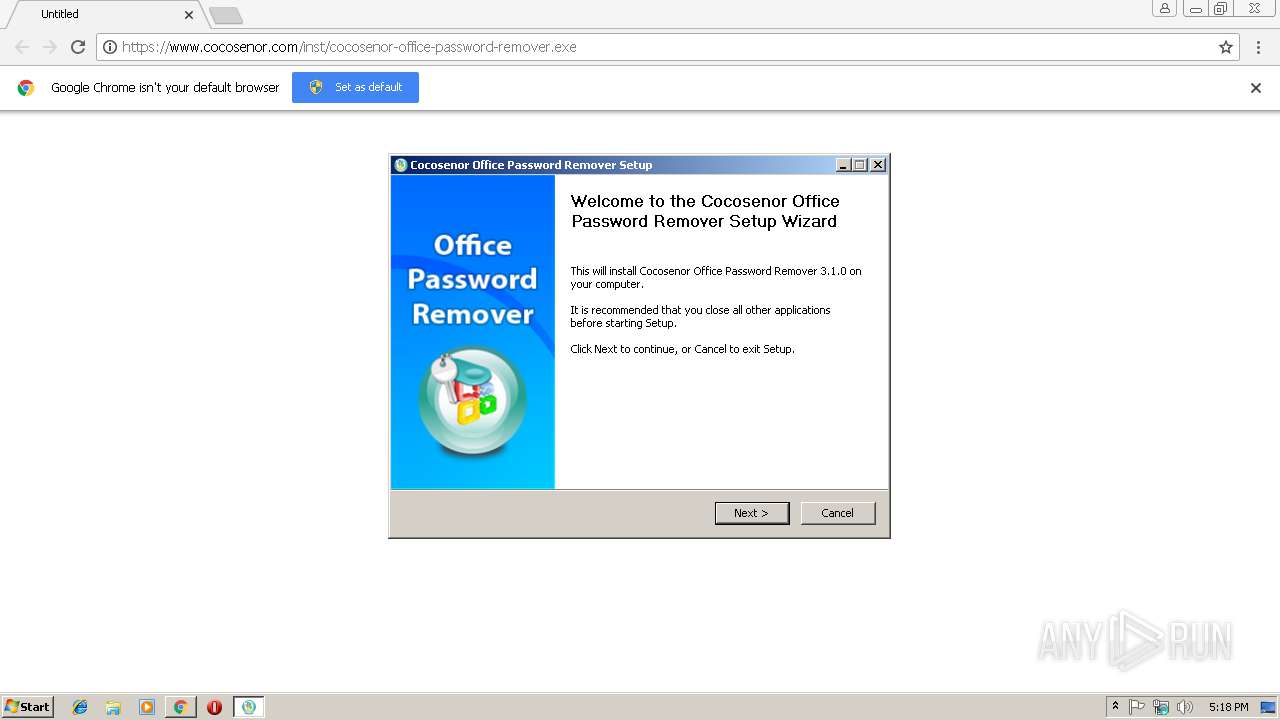
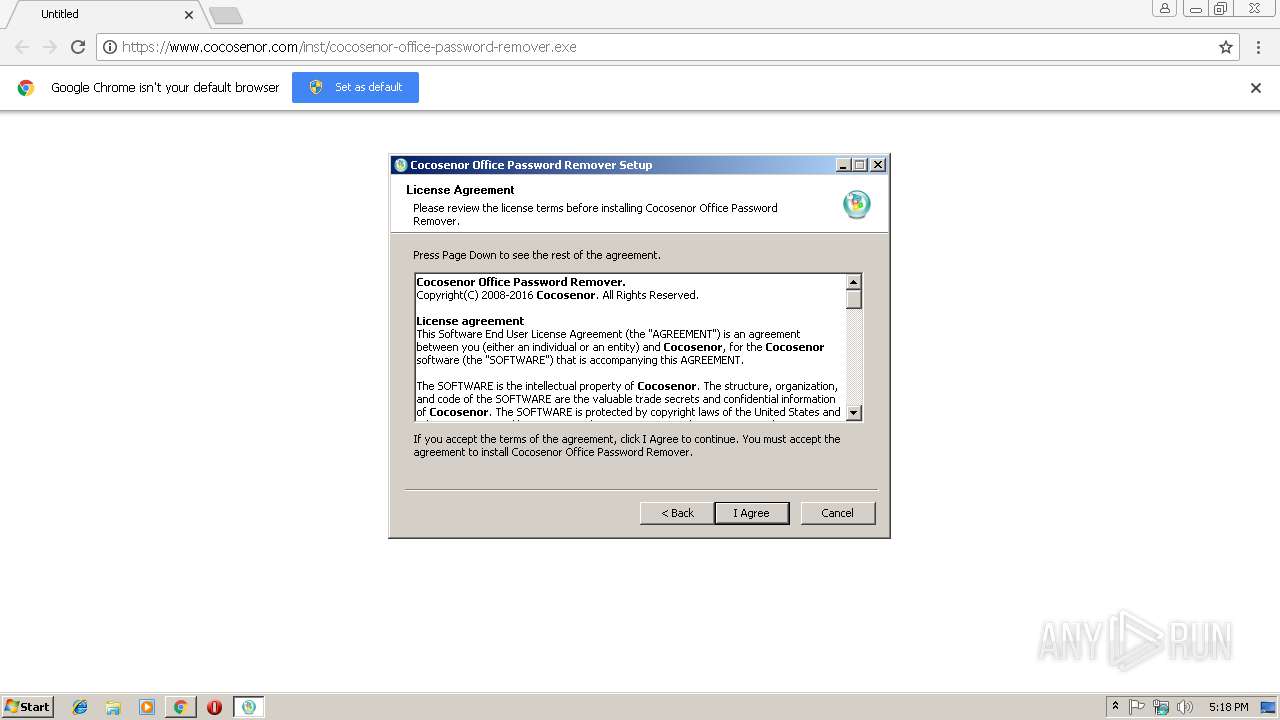
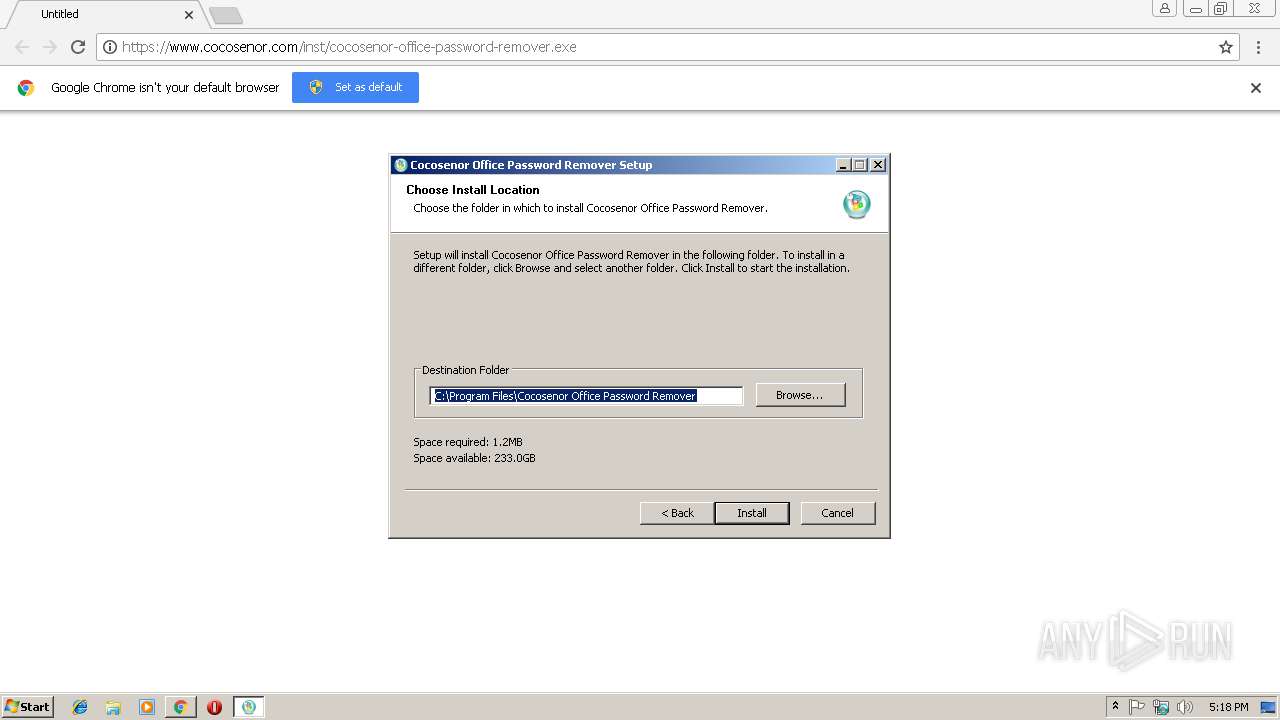
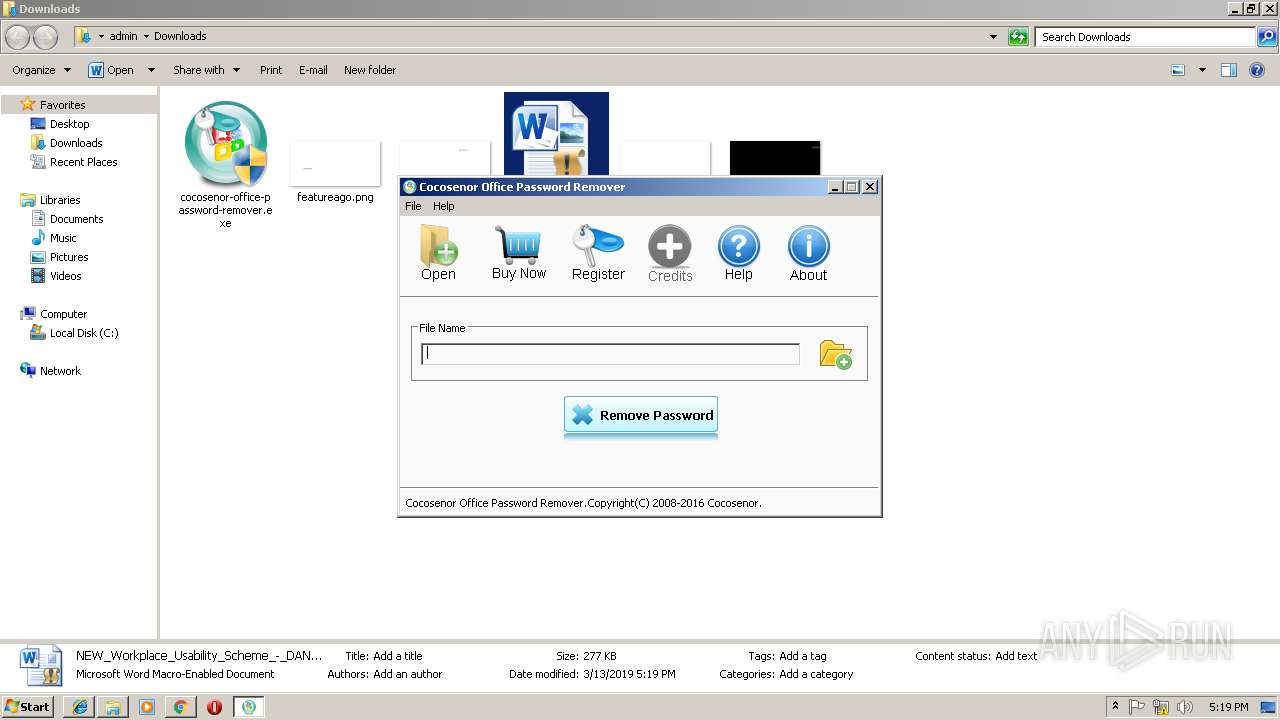
| URL: | https://www.cocosenor.com/inst/cocosenor-office-password-remover.exe |
| Full analysis: | https://app.any.run/tasks/b583ee77-4e19-4382-9e7c-c14a53ab4be0 |
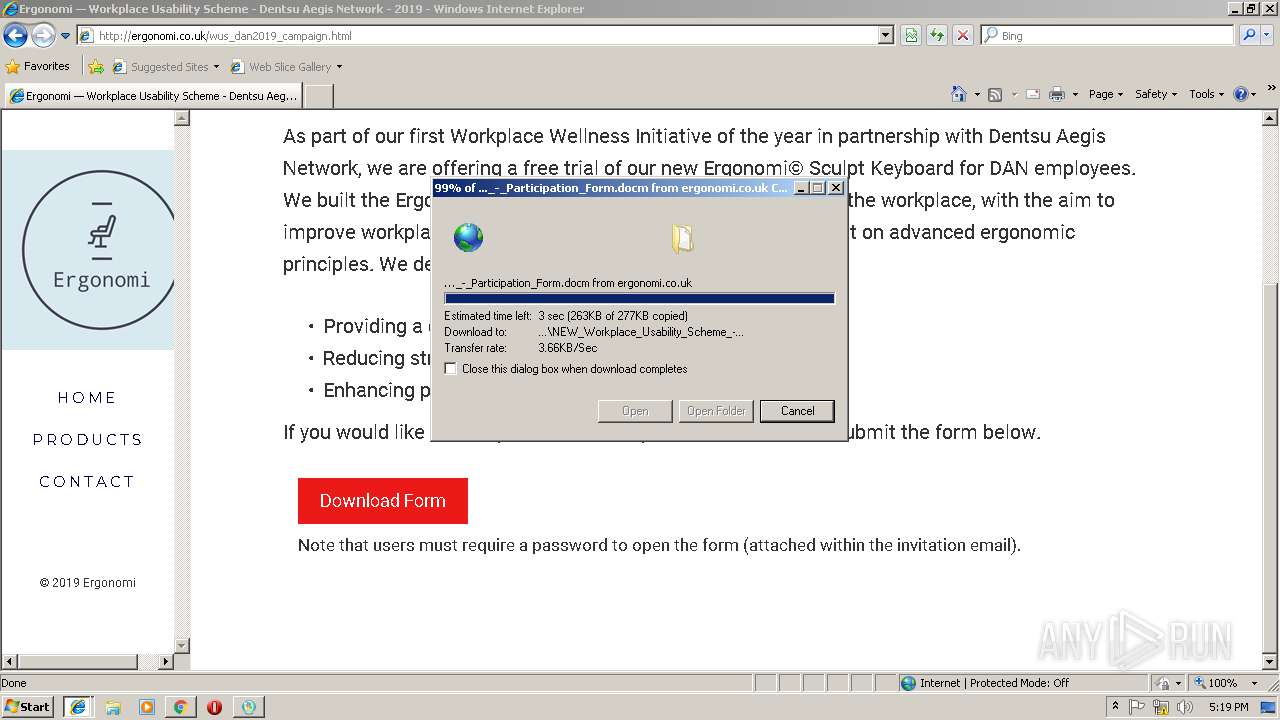
| Verdict: | Malicious activity |
| Analysis date: | March 13, 2019, 17:18:15 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 39515AE958B82B2549D332D360545908 |
| SHA1: | 7B771769F0577530B435A5B490D13822A000E504 |
| SHA256: | BC4C050B12125746E7B66D1ECD0A0A86AF182883731AB85BFD66CFE58D8AF5C5 |
| SSDEEP: | 3:N8DSLjWFpT5FfHE0MBYn:2OLqFZTc7e |
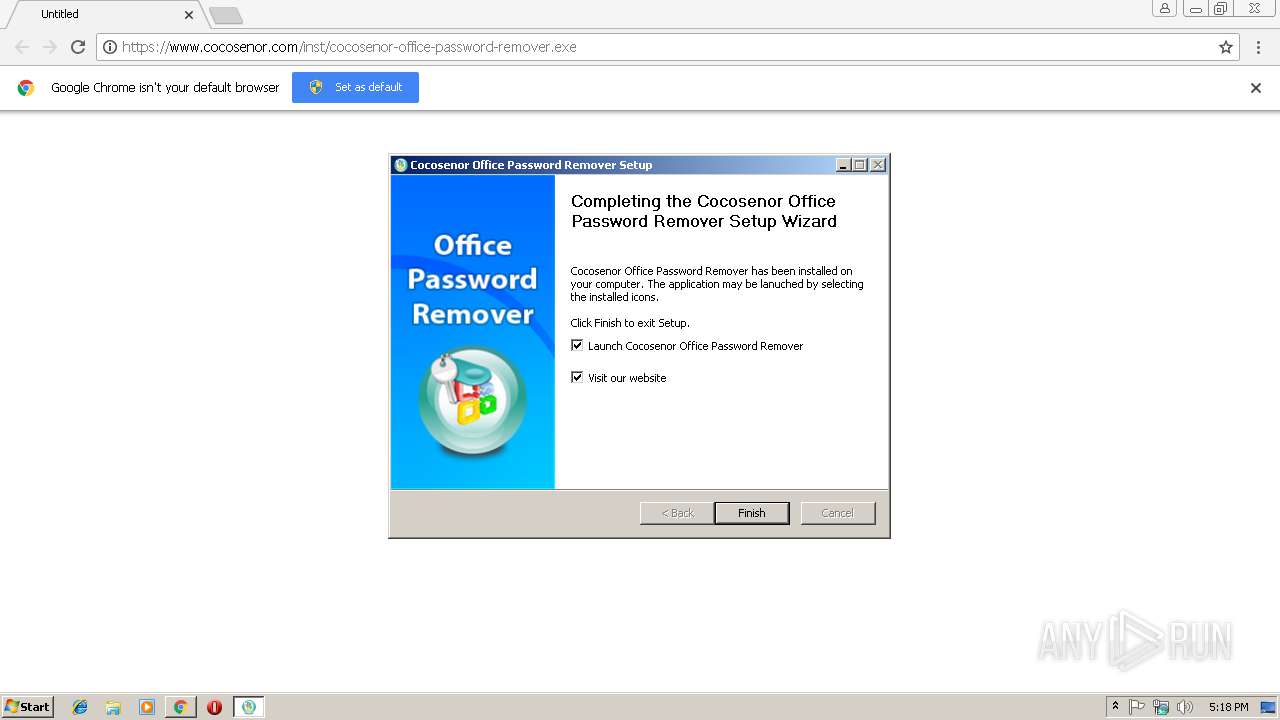
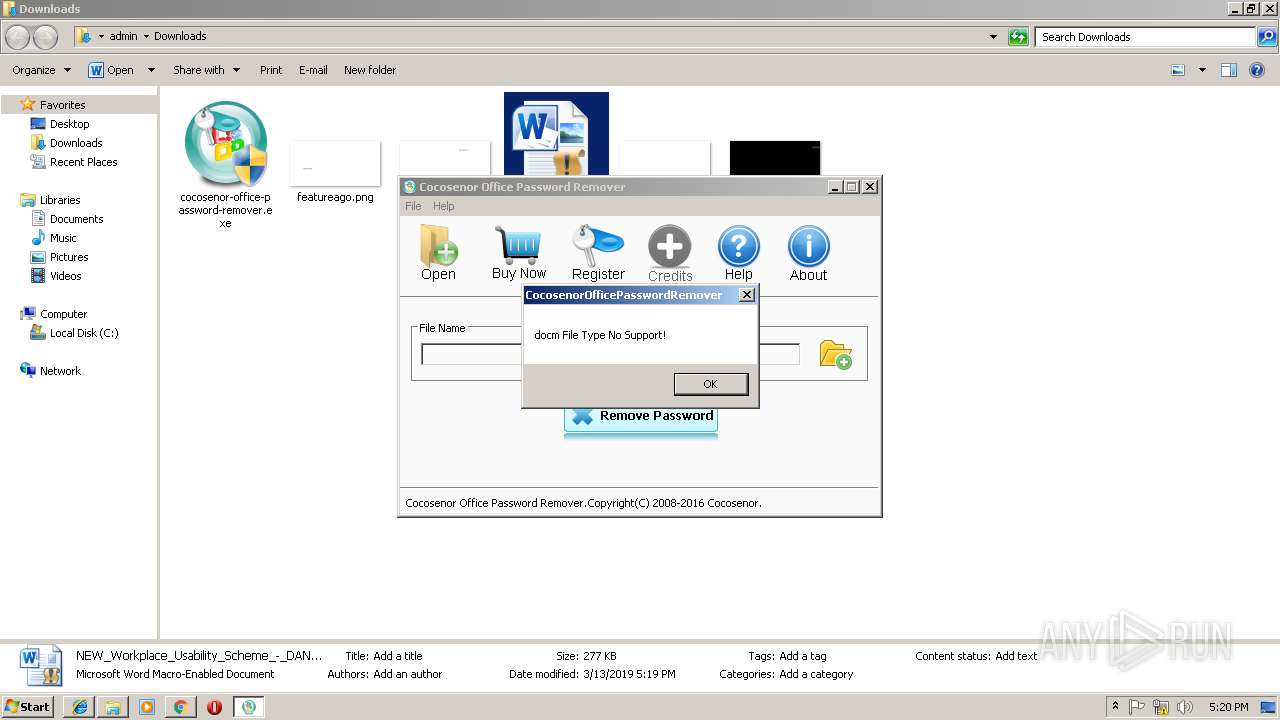
MALICIOUS
Application was dropped or rewritten from another process
- cocosenor-office-password-remover.exe (PID: 3160)
- CocosenorOfficePasswordRemover.exe (PID: 2208)
- cocosenor-office-password-remover.exe (PID: 3964)
Loads dropped or rewritten executable
- cocosenor-office-password-remover.exe (PID: 3160)
- CocosenorOfficePasswordRemover.exe (PID: 2208)
SUSPICIOUS
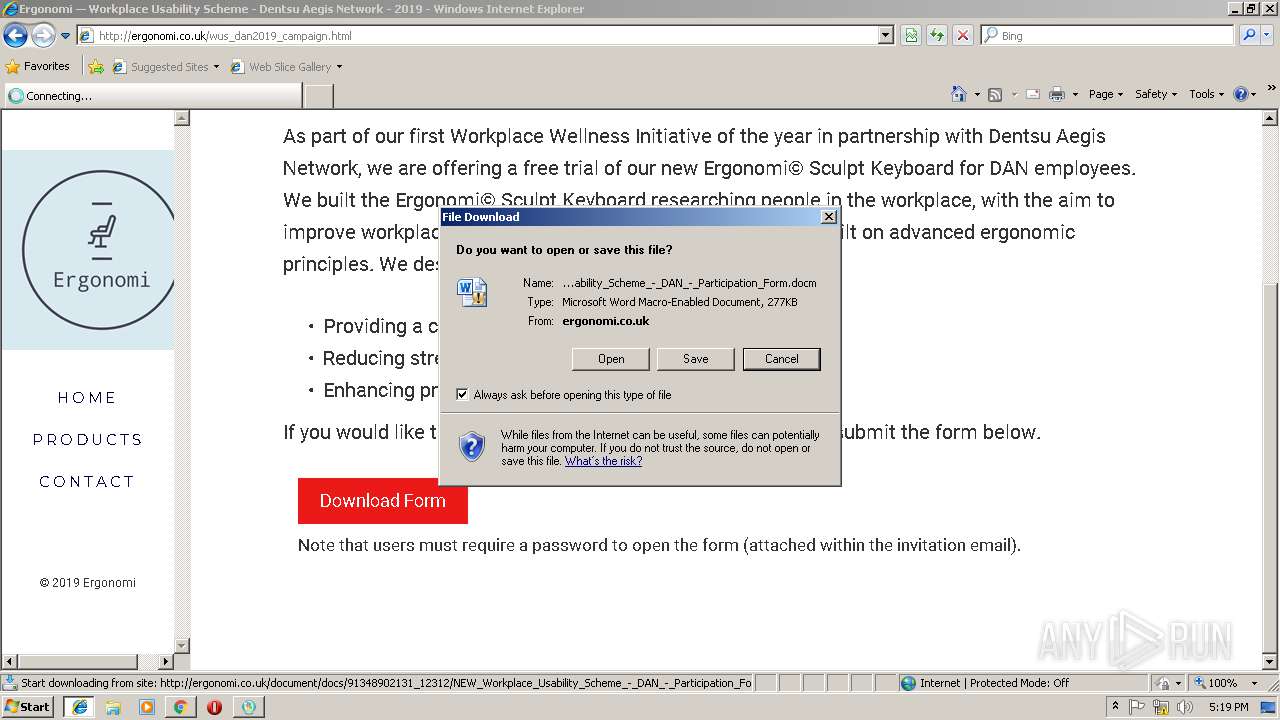
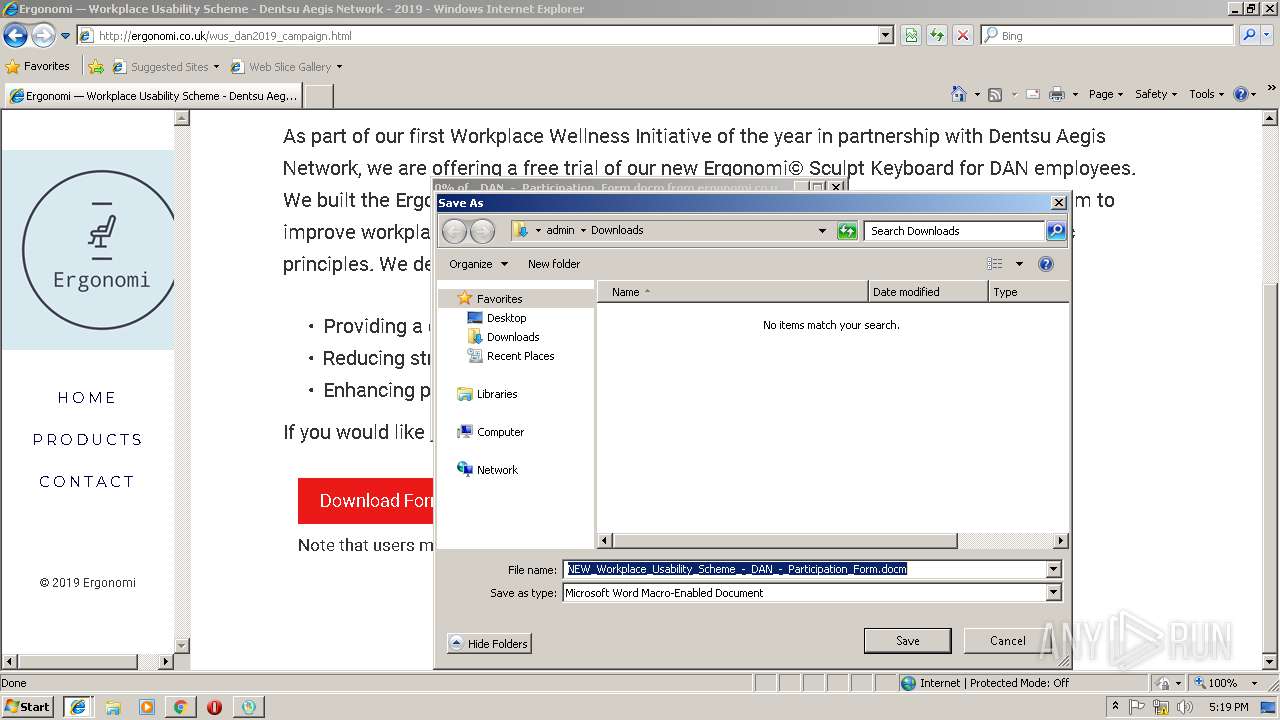
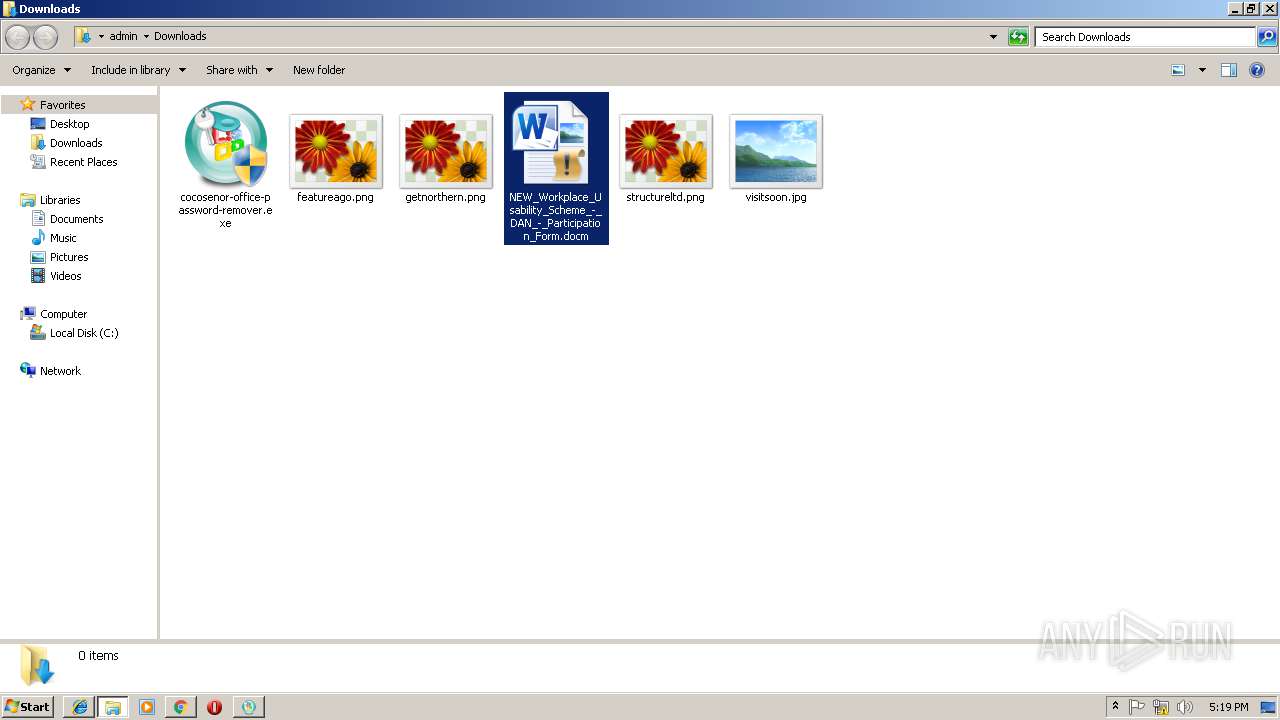
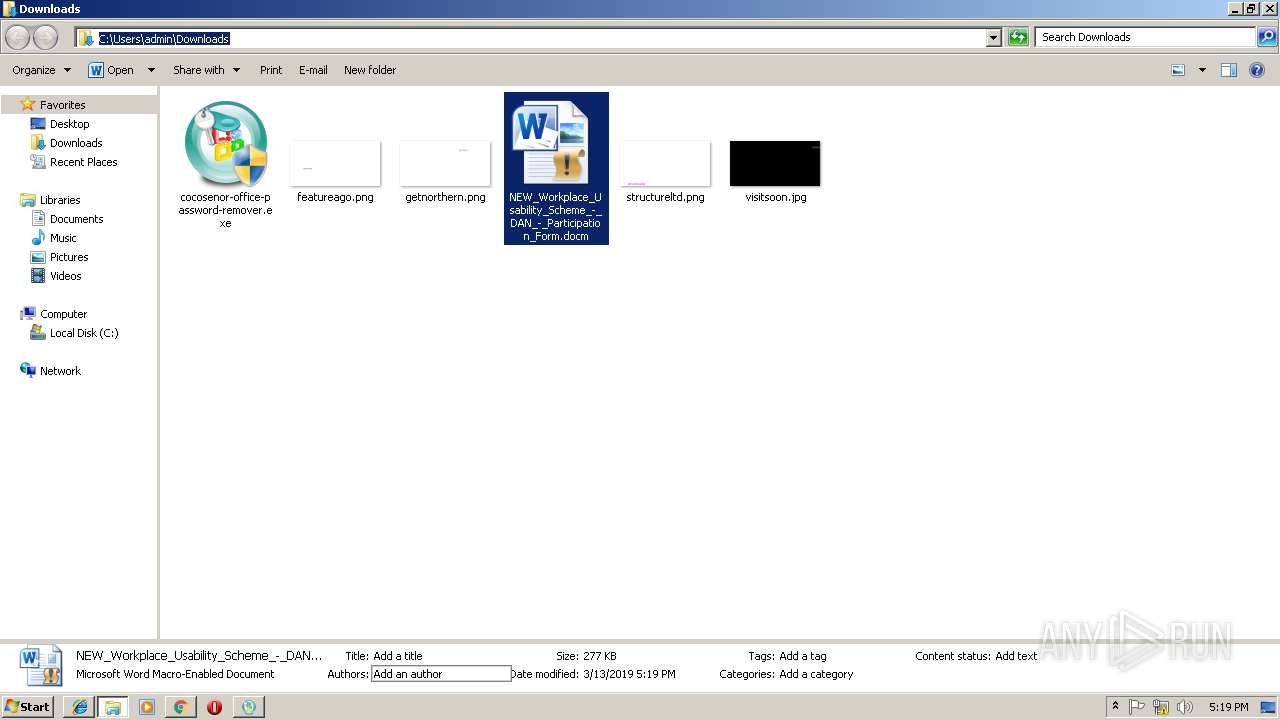
Executable content was dropped or overwritten
- chrome.exe (PID: 3384)
- cocosenor-office-password-remover.exe (PID: 3160)
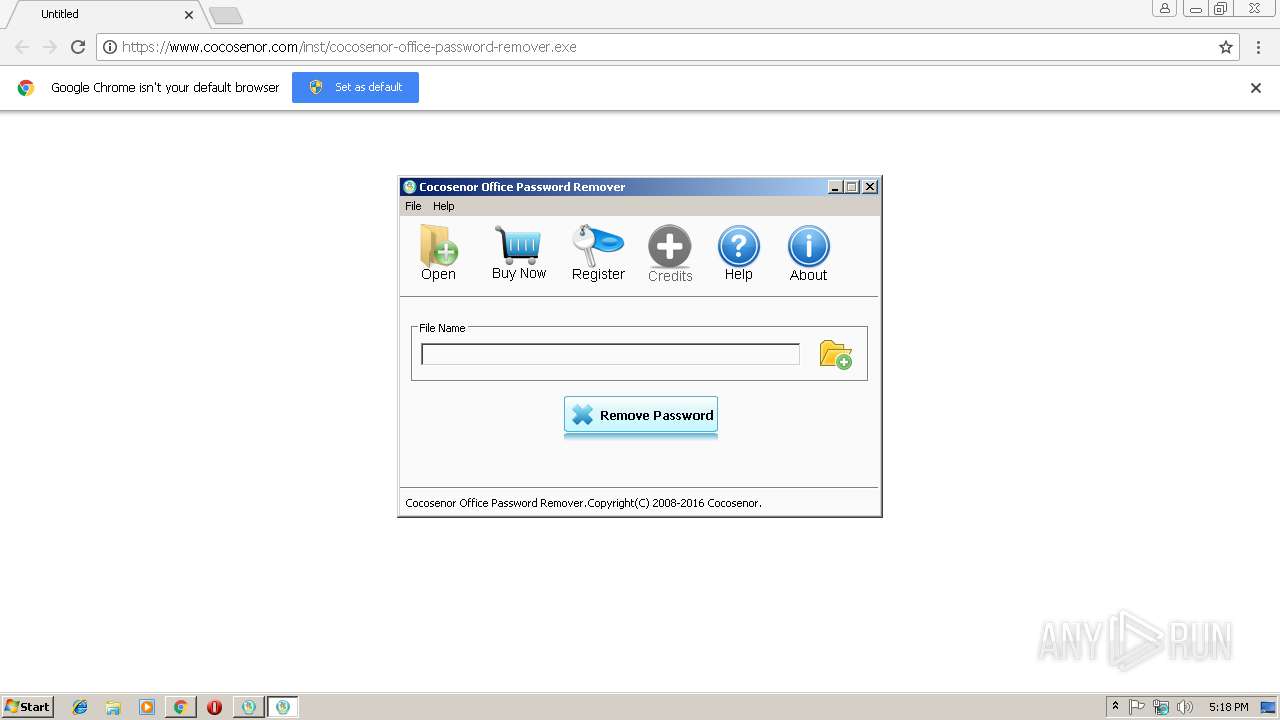
Creates files in the program directory
- cocosenor-office-password-remover.exe (PID: 3160)
Creates files in the user directory
- cocosenor-office-password-remover.exe (PID: 3160)
Creates a software uninstall entry
- cocosenor-office-password-remover.exe (PID: 3160)
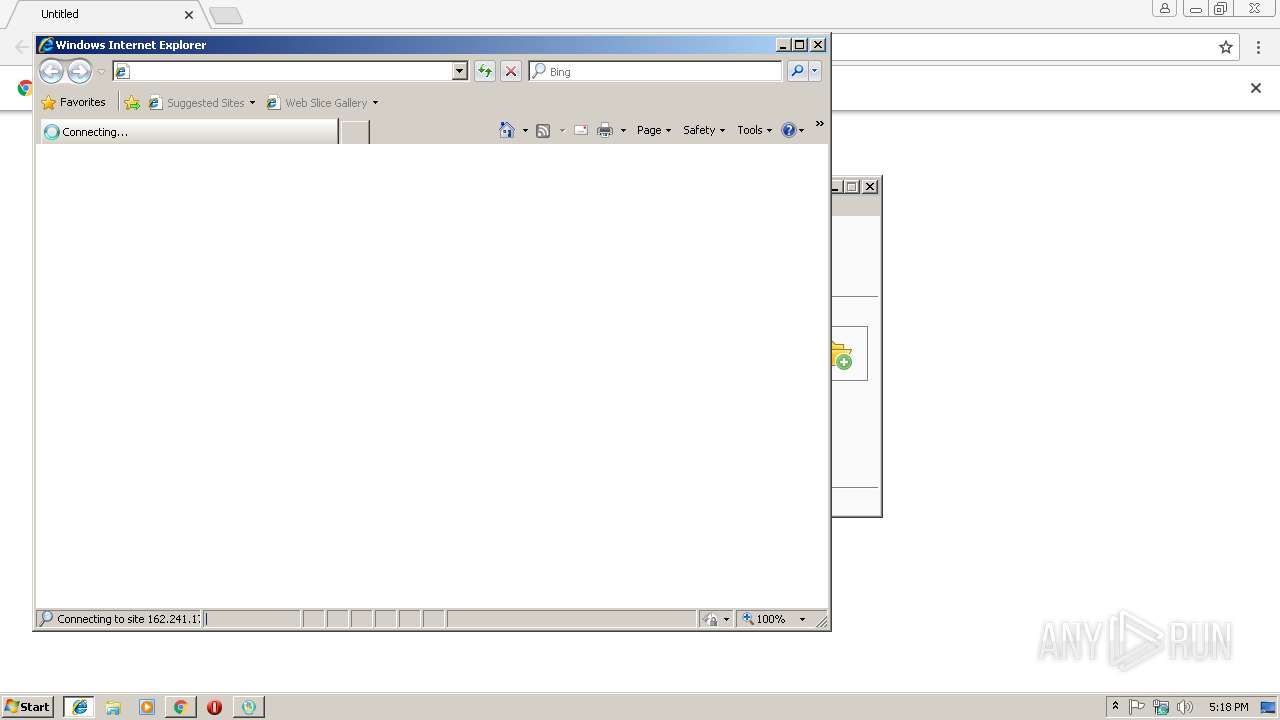
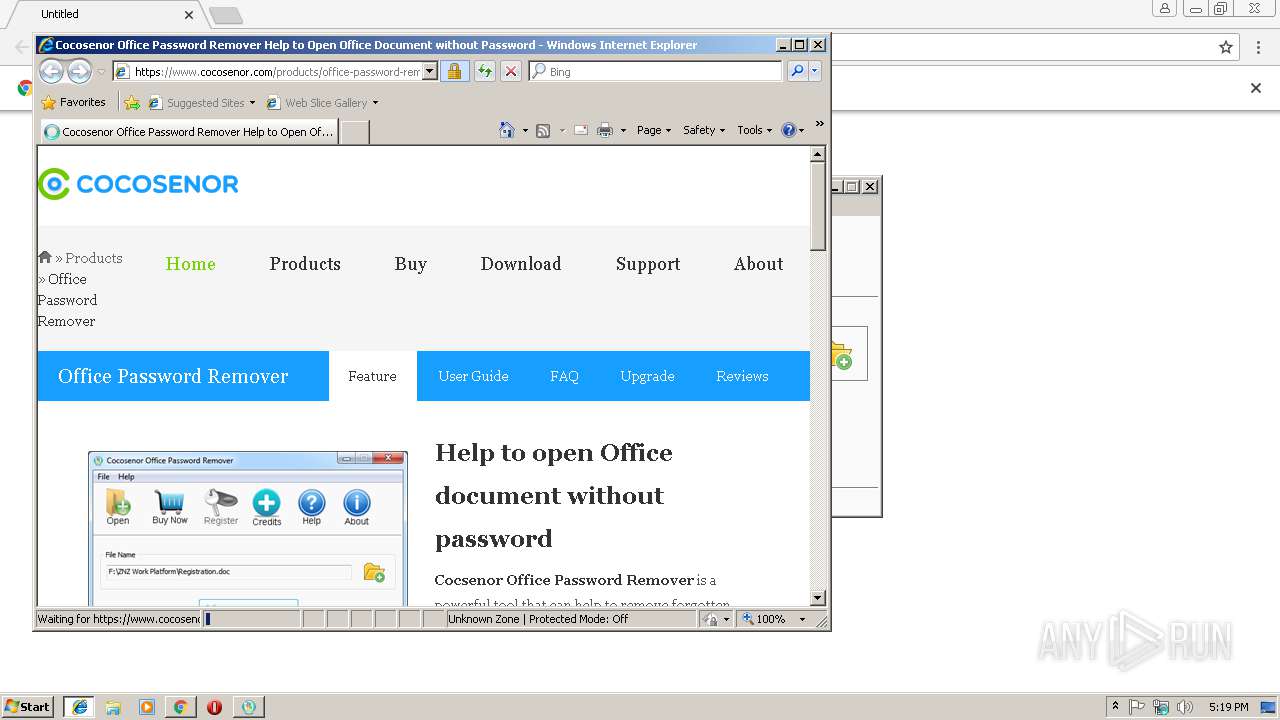
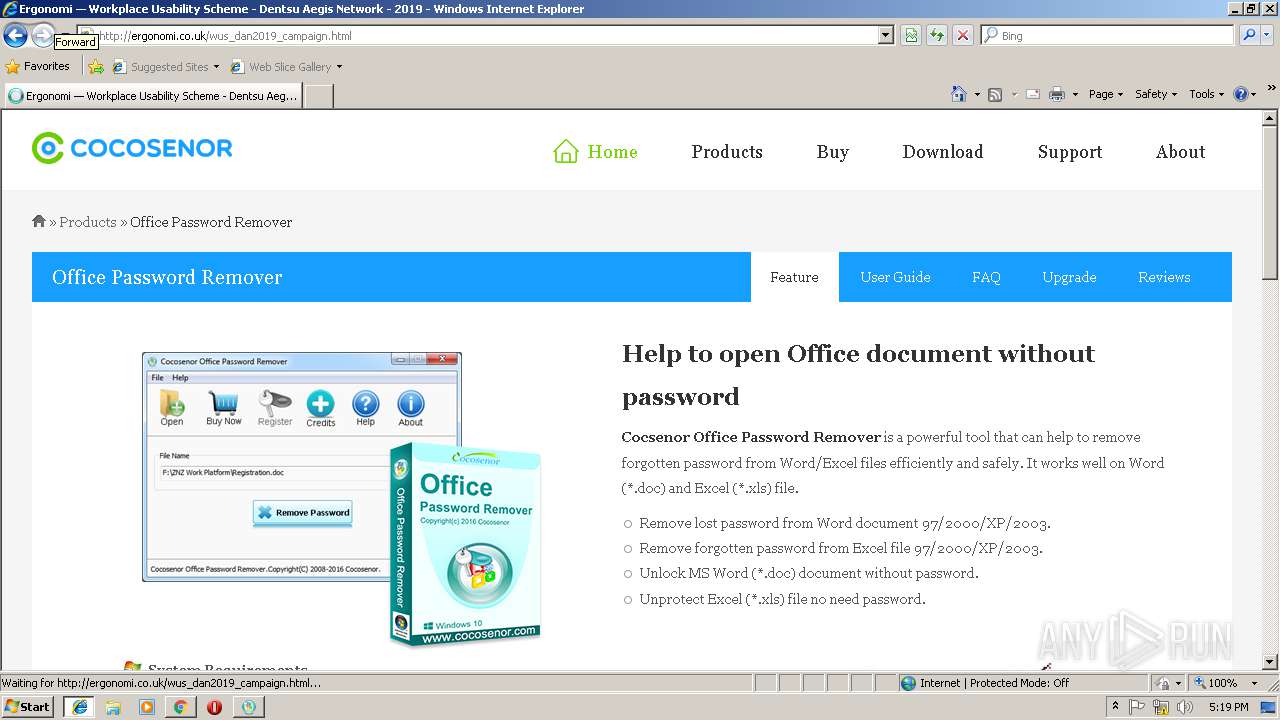
Starts Internet Explorer
- cocosenor-office-password-remover.exe (PID: 3160)
INFO
Application launched itself
- chrome.exe (PID: 3384)
- iexplore.exe (PID: 3444)
Reads Internet Cache Settings
- chrome.exe (PID: 3384)
- iexplore.exe (PID: 2784)
Changes internet zones settings
- iexplore.exe (PID: 3444)
Creates files in the user directory
- iexplore.exe (PID: 3444)
- iexplore.exe (PID: 2784)
Changes settings of System certificates
- iexplore.exe (PID: 2784)
Reads internet explorer settings
- iexplore.exe (PID: 2784)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2784)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 2784)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
51
Monitored processes
15
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1832 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=944,242606157672125368,8062065844879851193,131072 --enable-features=PasswordImport --service-pipe-token=4FF06B6EAE765D4E6A9019CAB33F4FBE --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4FF06B6EAE765D4E6A9019CAB33F4FBE --renderer-client-id=3 --mojo-platform-channel-handle=2032 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2160 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=68.0.3440.106 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x6f5300b0,0x6f5300c0,0x6f5300cc | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2208 | "C:\Program Files\Cocosenor Office Password Remover\CocosenorOfficePasswordRemover.exe" | C:\Program Files\Cocosenor Office Password Remover\CocosenorOfficePasswordRemover.exe | — | cocosenor-office-password-remover.exe | |||||||||||
User: admin Company: Cocosenor Integrity Level: HIGH Description: Office Password Remover Exit code: 0 Version: 3.1.0 Modules
| |||||||||||||||
| 2736 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=944,242606157672125368,8062065844879851193,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=D24AAD625AB16B6FA0E38663173B429A --mojo-platform-channel-handle=888 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2784 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3444 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3012 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=944,242606157672125368,8062065844879851193,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=932533808C43930BD135BBFF6B90B743 --mojo-platform-channel-handle=2632 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
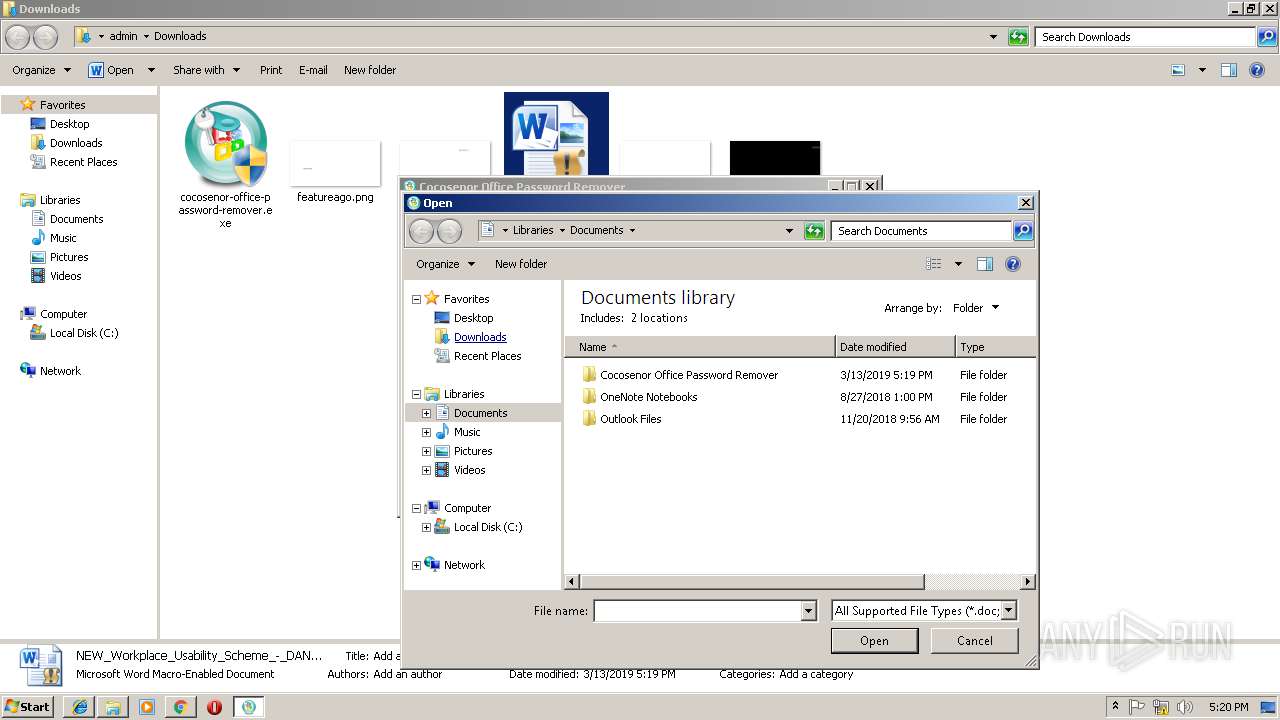
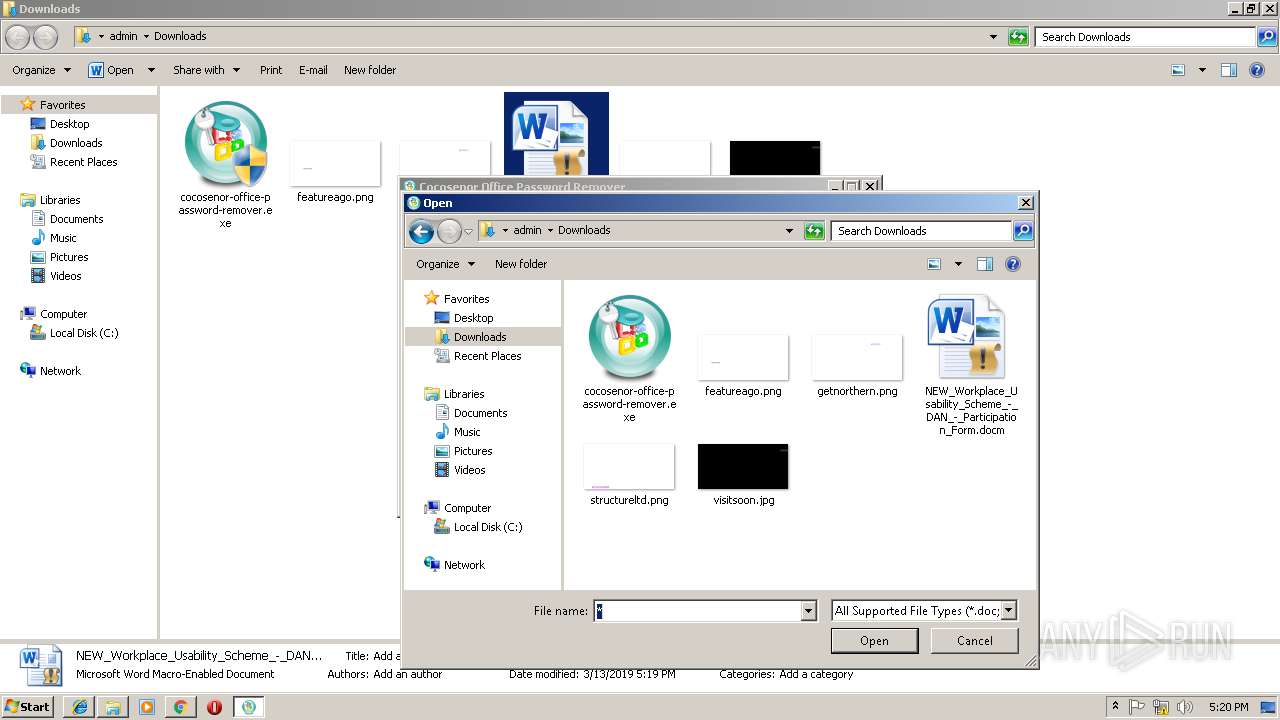
| 3160 | "C:\Users\admin\Downloads\cocosenor-office-password-remover.exe" | C:\Users\admin\Downloads\cocosenor-office-password-remover.exe | chrome.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3360 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=944,242606157672125368,8062065844879851193,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=B3766E82E6949D53ADA5B1401E097777 --mojo-platform-channel-handle=2564 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3384 | "C:\Program Files\Google\Chrome\Application\chrome.exe" https://www.cocosenor.com/inst/cocosenor-office-password-remover.exe | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3444 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | cocosenor-office-password-remover.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 915
Read events
2 617
Write events
289
Delete events
9
Modification events
| (PID) Process: | (3384) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3384) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3384) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3588) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3384-13196971114762500 |
Value: 259 | |||
| (PID) Process: | (3384) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3384) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3384) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (3384) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3384) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3384-13196971114762500 |
Value: 259 | |||
| (PID) Process: | (3384) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
7
Suspicious files
24
Text files
177
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3384 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\0ee052eb-c6f4-450e-a905-552ccf560be2.tmp | — | |
MD5:— | SHA256:— | |||
| 3384 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3384 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3384 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3384 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
| 3384 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\51dbe84d-86b2-40ba-9f89-08bcc2399ad5.tmp | — | |
MD5:— | SHA256:— | |||
| 3384 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3384 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old~RF198756.TMP | text | |
MD5:— | SHA256:— | |||
| 3384 | chrome.exe | C:\Users\admin\Downloads\781d75c7-7d46-4fc4-9ed0-1e75020d9bd9.tmp | — | |
MD5:— | SHA256:— | |||
| 3384 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
24
TCP/UDP connections
38
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2784 | iexplore.exe | GET | — | 34.248.179.131:80 | http://ergonomi.co.uk/js/modernizr-2.6.2.min.js | IE | — | — | unknown |
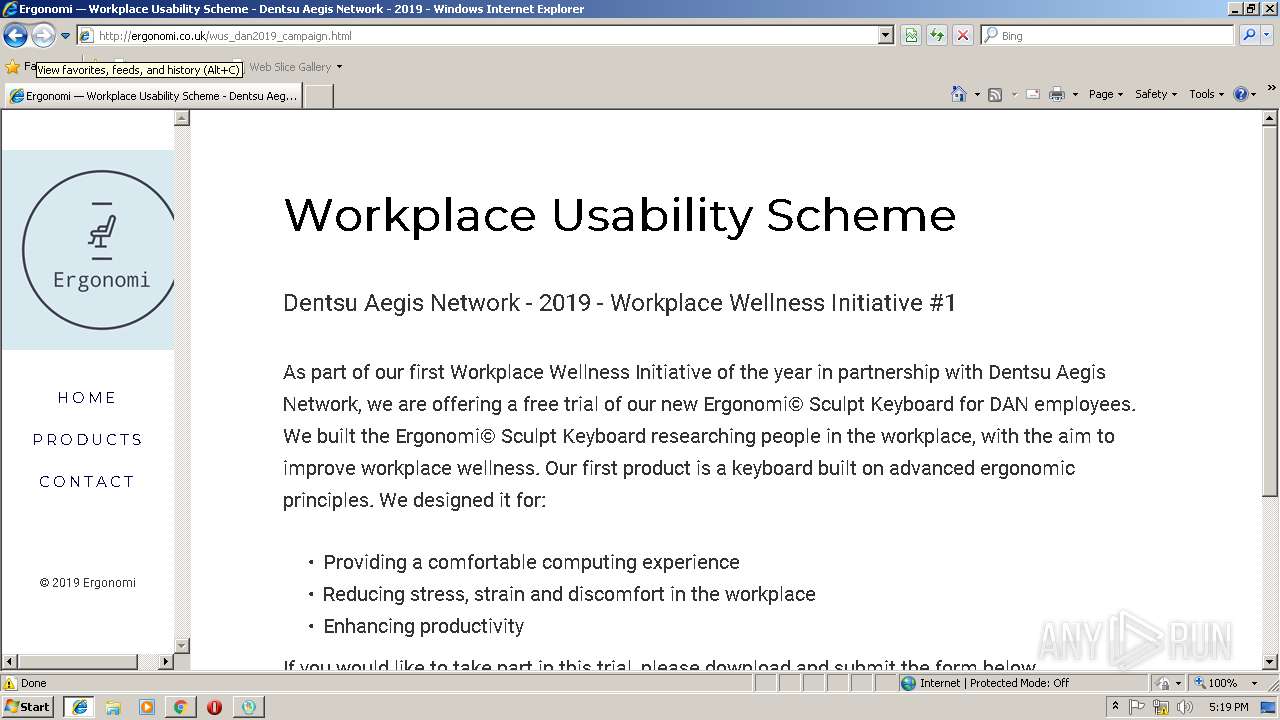
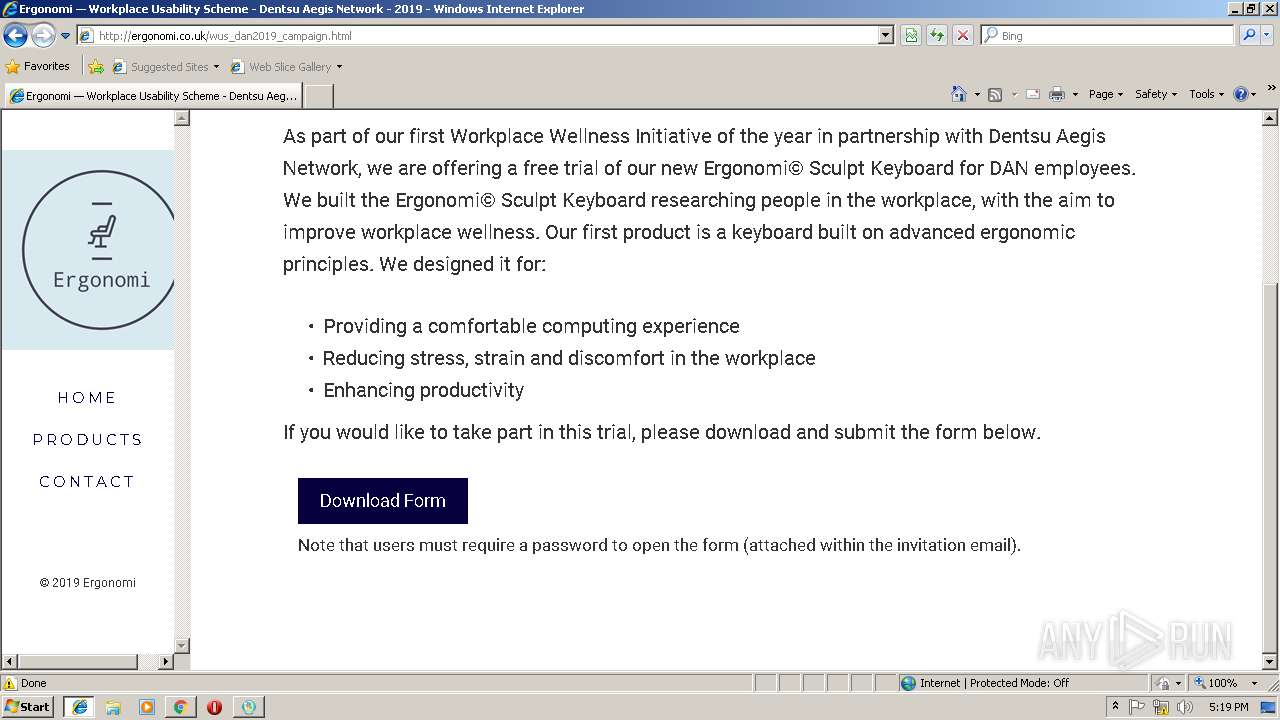
2784 | iexplore.exe | GET | 200 | 34.248.179.131:80 | http://ergonomi.co.uk/wus_dan2019_campaign.html | IE | html | 1.95 Kb | unknown |
2784 | iexplore.exe | GET | 200 | 34.248.179.131:80 | http://ergonomi.co.uk/css/icomoon.css | IE | text | 40.4 Kb | unknown |
2784 | iexplore.exe | GET | 200 | 34.248.179.131:80 | http://ergonomi.co.uk/css/style.css | IE | text | 22.5 Kb | unknown |
2784 | iexplore.exe | GET | 200 | 34.248.179.131:80 | http://ergonomi.co.uk/fonts/icomoon/icomoon.eot?195opb | IE | eot | 223 Kb | unknown |
2784 | iexplore.exe | GET | 200 | 34.248.179.131:80 | http://ergonomi.co.uk/logo.png | IE | image | 10.1 Kb | unknown |
2784 | iexplore.exe | GET | 200 | 34.248.179.131:80 | http://ergonomi.co.uk/fonts/icomoon/icomoon.eot?srf3rx | IE | eot | 223 Kb | unknown |
2784 | iexplore.exe | GET | 200 | 34.248.179.131:80 | http://ergonomi.co.uk/css/animate.css | IE | text | 69.8 Kb | unknown |
2784 | iexplore.exe | GET | 200 | 34.248.179.131:80 | http://ergonomi.co.uk/js/respond.min.js | IE | html | 4.28 Kb | unknown |
2784 | iexplore.exe | GET | 200 | 34.248.179.131:80 | http://ergonomi.co.uk/js/bootstrap.min.js | IE | text | 35.9 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2784 | iexplore.exe | 162.241.172.26:443 | www.cocosenor.com | CyrusOne LLC | US | unknown |
3444 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3384 | chrome.exe | 172.217.21.195:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3384 | chrome.exe | 162.241.172.26:443 | www.cocosenor.com | CyrusOne LLC | US | unknown |
3384 | chrome.exe | 172.217.22.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3384 | chrome.exe | 216.58.205.237:443 | accounts.google.com | Google Inc. | US | whitelisted |
2784 | iexplore.exe | 104.20.3.47:443 | secure.statcounter.com | Cloudflare Inc | US | shared |
2784 | iexplore.exe | 216.58.208.35:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2784 | iexplore.exe | 172.217.22.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3384 | chrome.exe | 216.58.210.10:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.cocosenor.com |
| unknown |
www.gstatic.com |
| whitelisted |
accounts.google.com |
| shared |
sb-ssl.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
www.bing.com |
| whitelisted |
secure.statcounter.com |
| whitelisted |
c.statcounter.com |
| whitelisted |
ergonomi.co.uk |
| unknown |