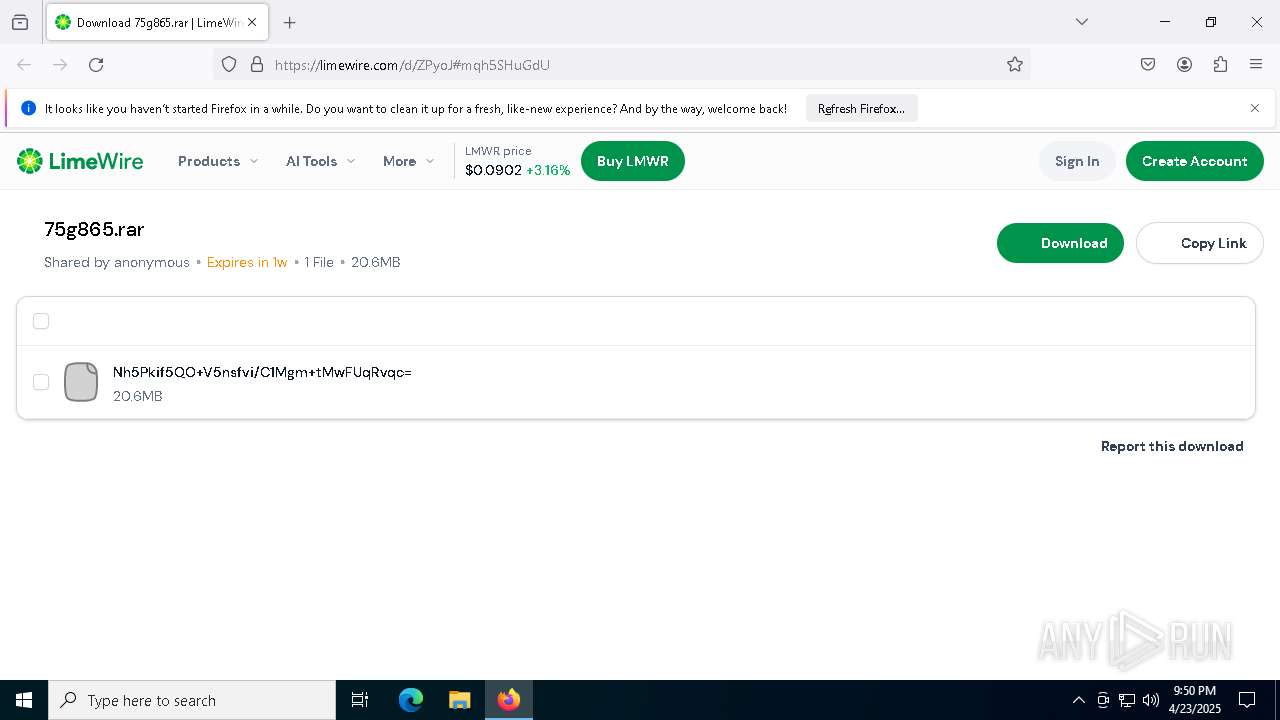
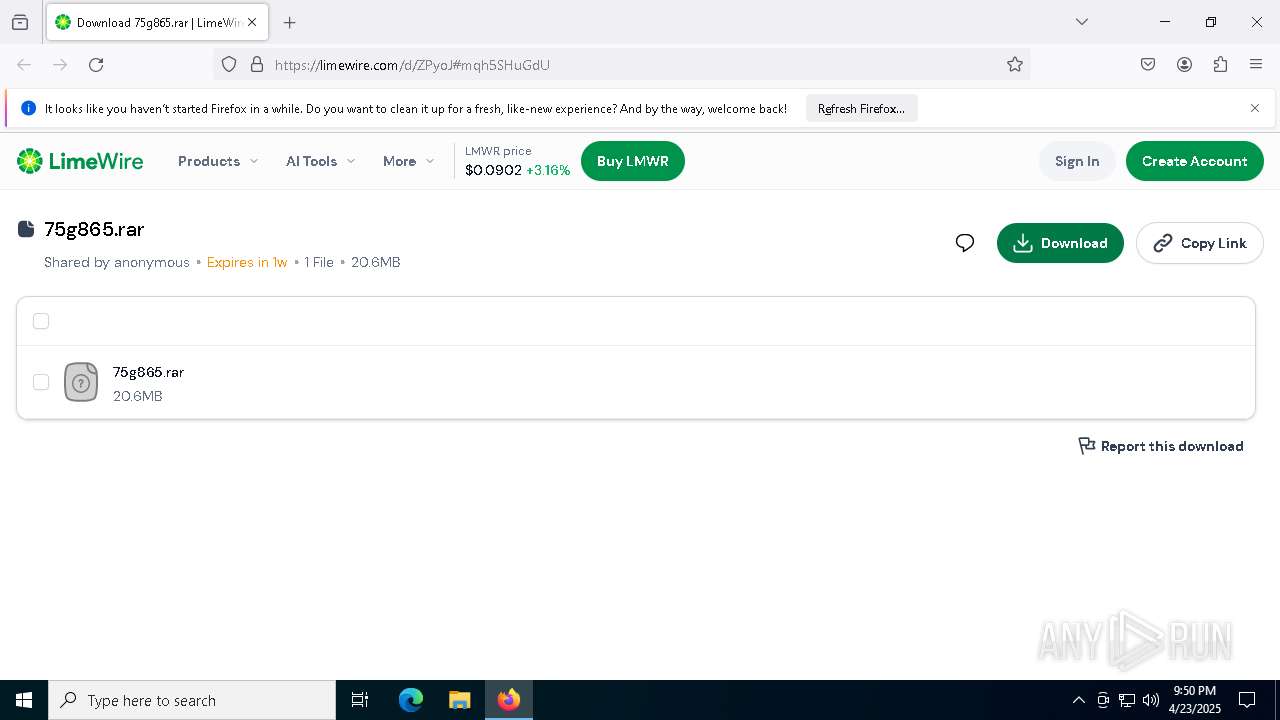
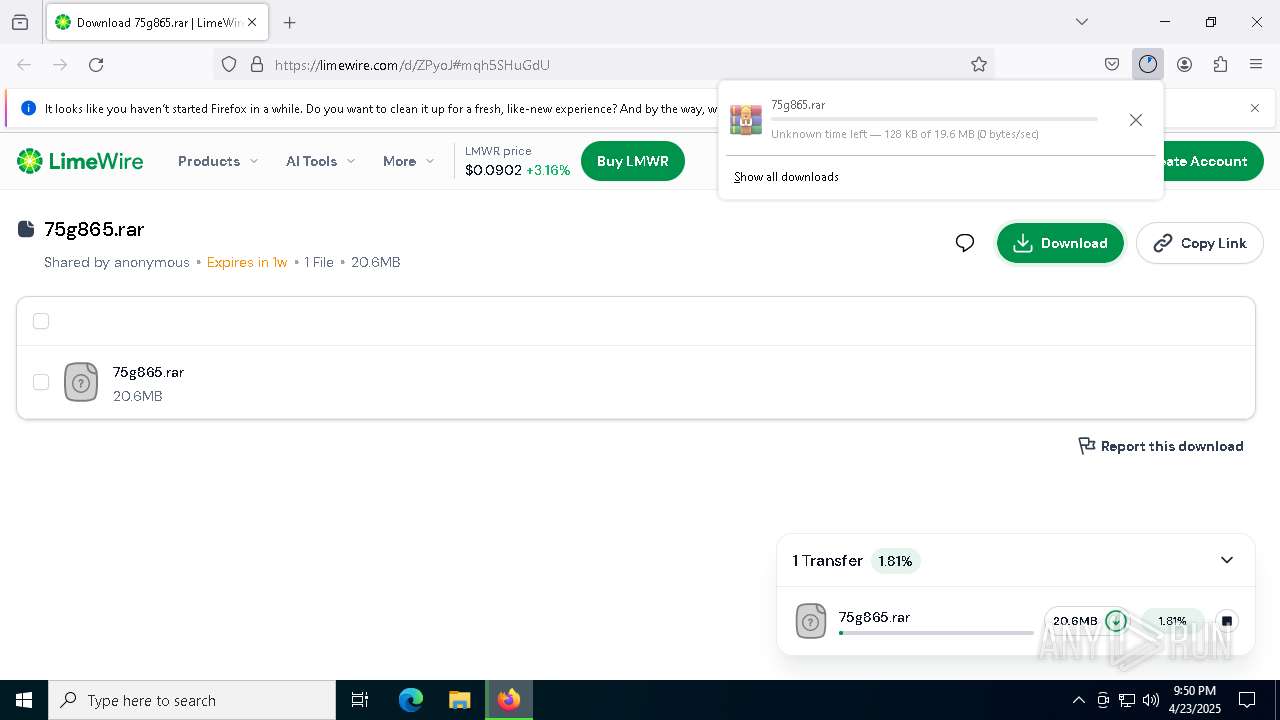
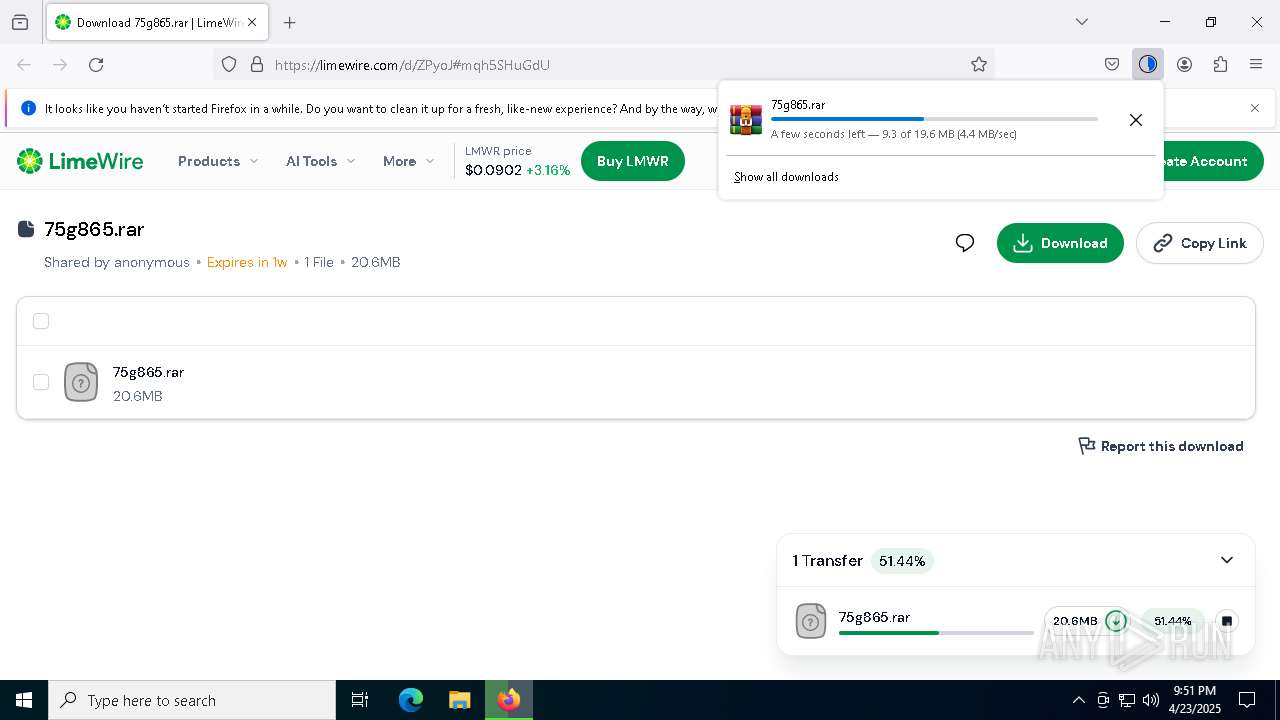
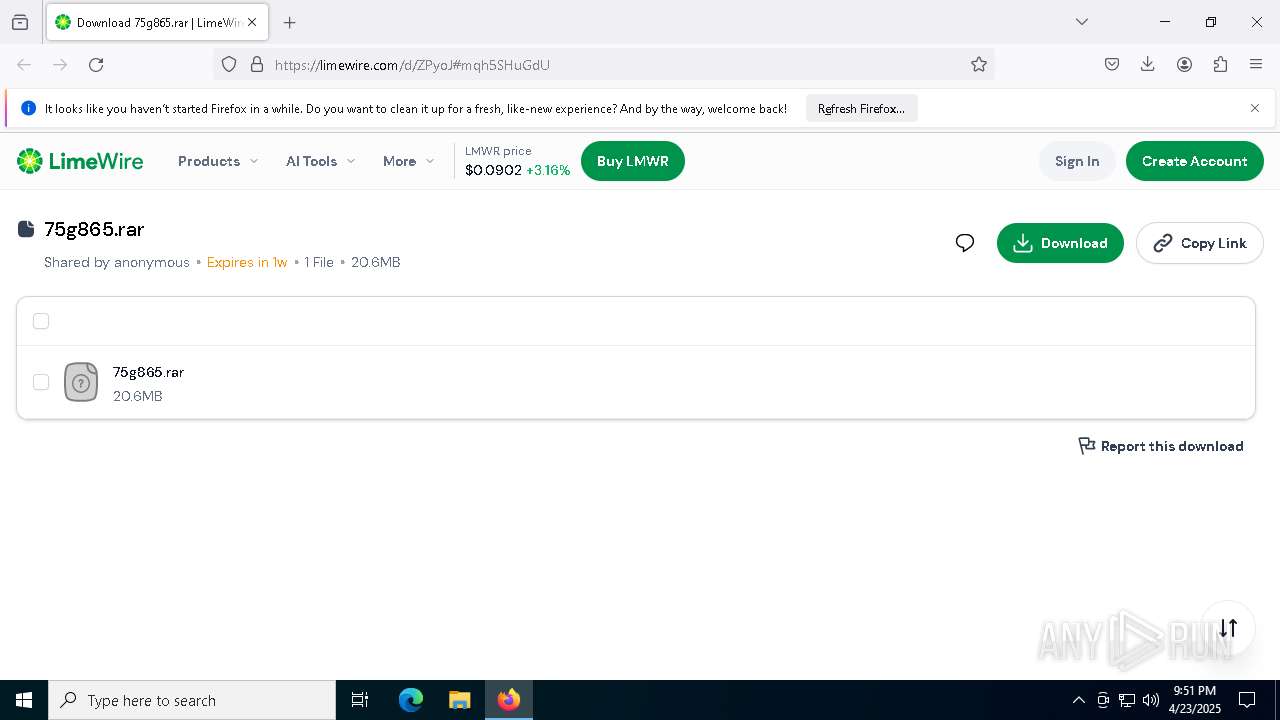
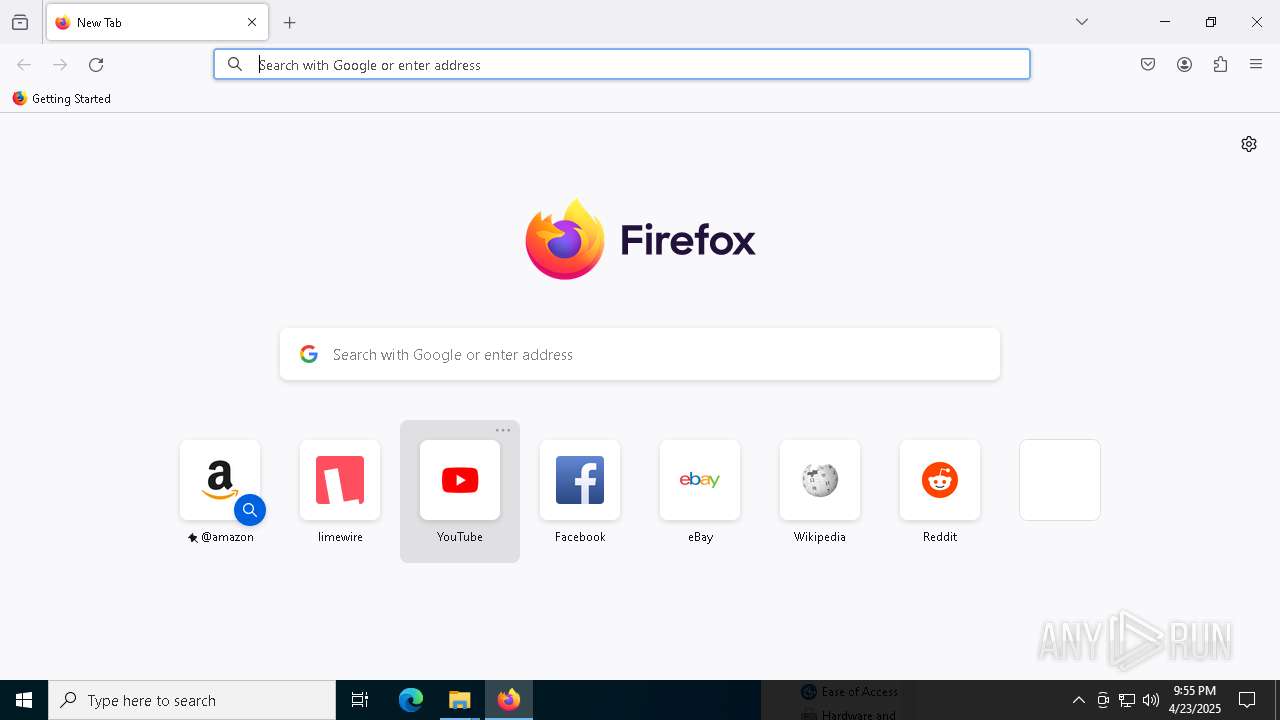
| URL: | https://limewire.com/d/ZPyoJ#mqh5SHuGdU |
| Full analysis: | https://app.any.run/tasks/f377b22a-7450-4e68-8004-94acb1a7b121 |
| Verdict: | Malicious activity |
| Analysis date: | April 23, 2025, 21:50:38 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 0B2938A6ED799FD600EBC7A7734EED53 |
| SHA1: | 25686603FCC82D5C7652DF274FD43B12E10E8851 |
| SHA256: | BC4478EA33256609FEE0DE43E7A377A4A2FB4524903CC78CFD4F315824988414 |
| SSDEEP: | 3:N8MIA/enK97vfViBw:2MIA/eK97ViG |
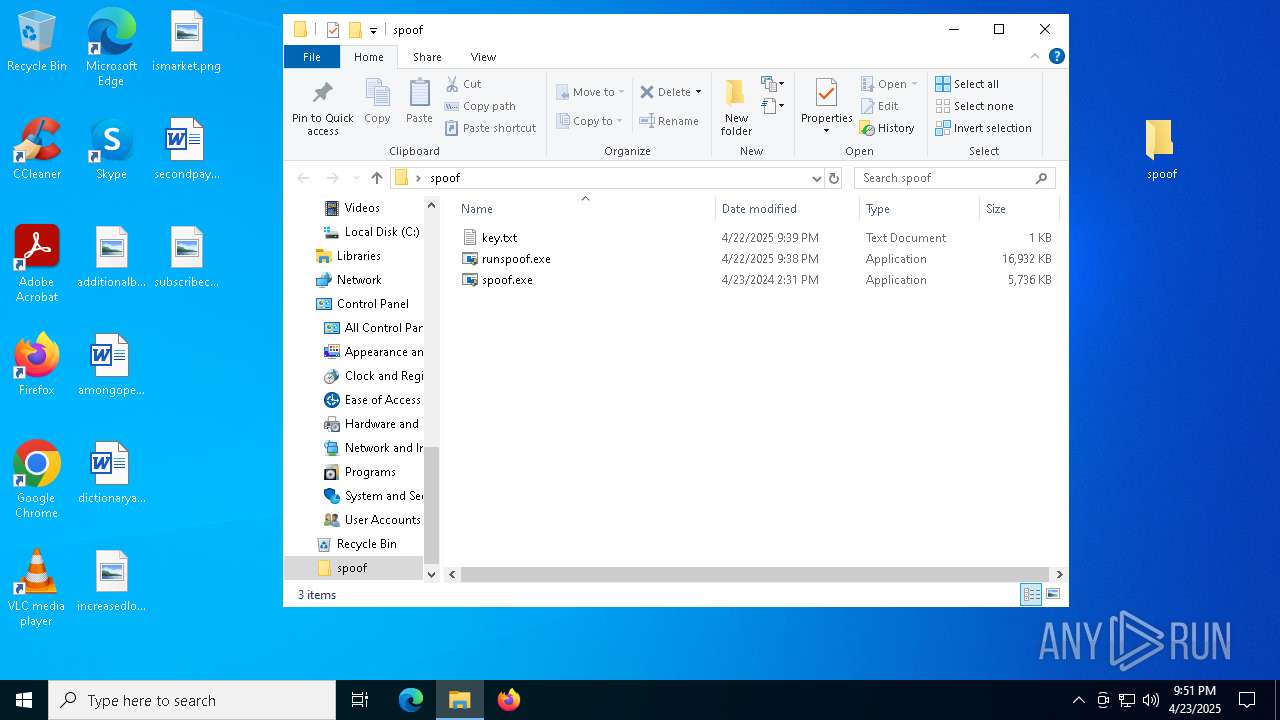
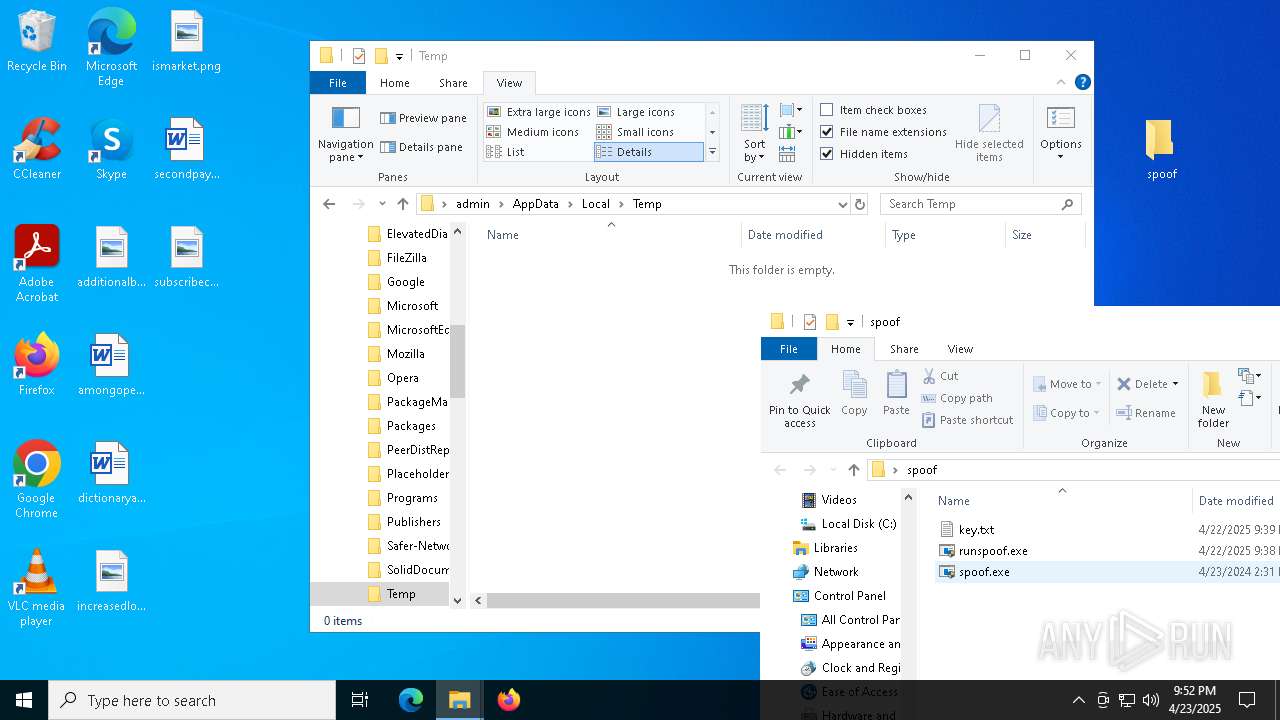
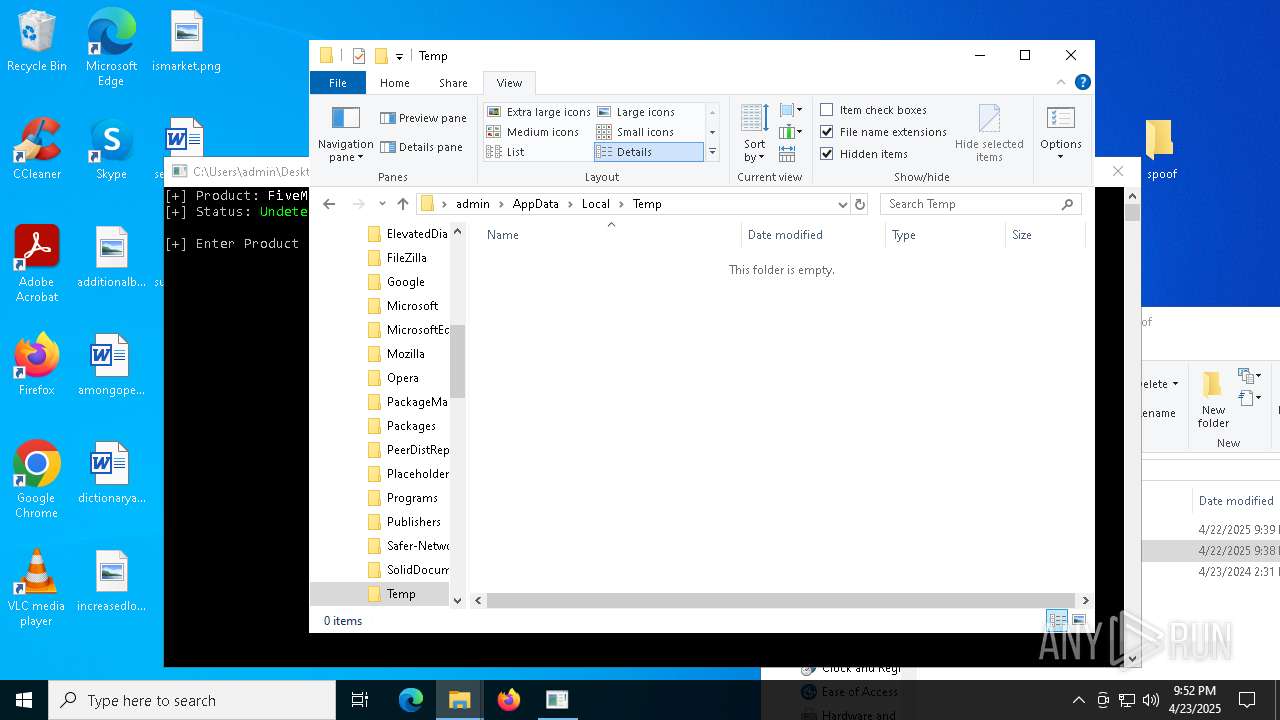
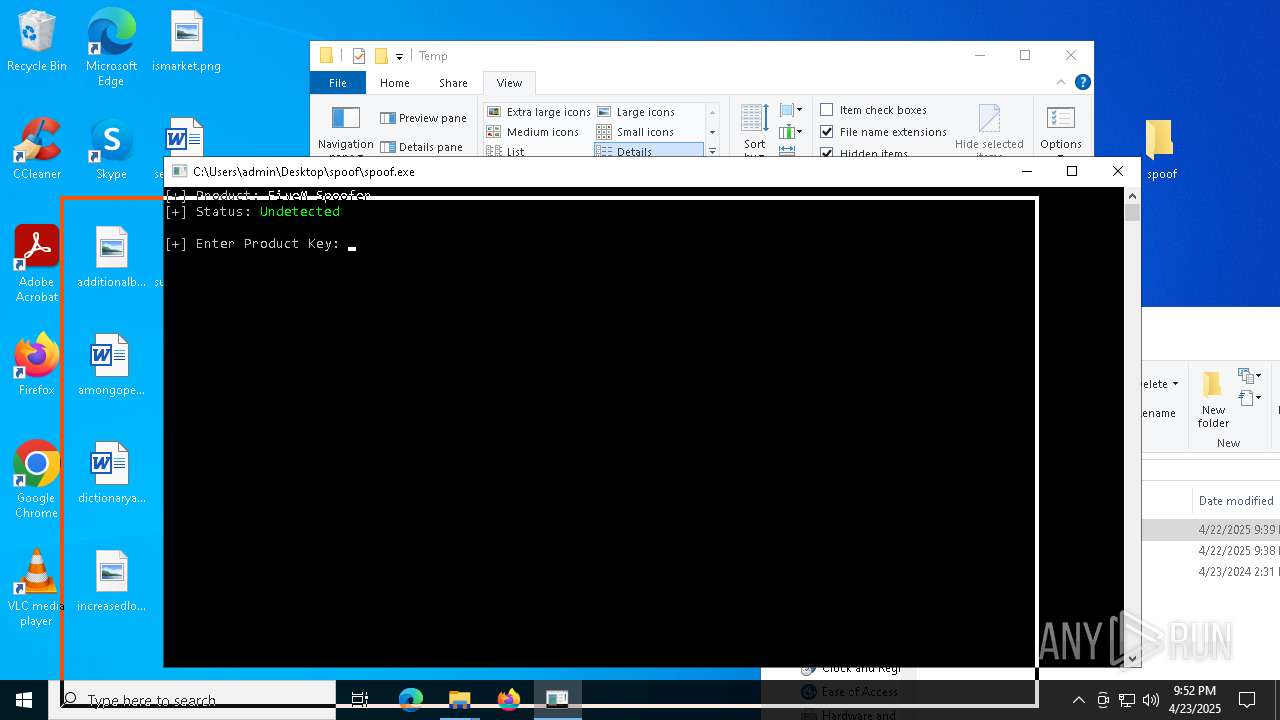
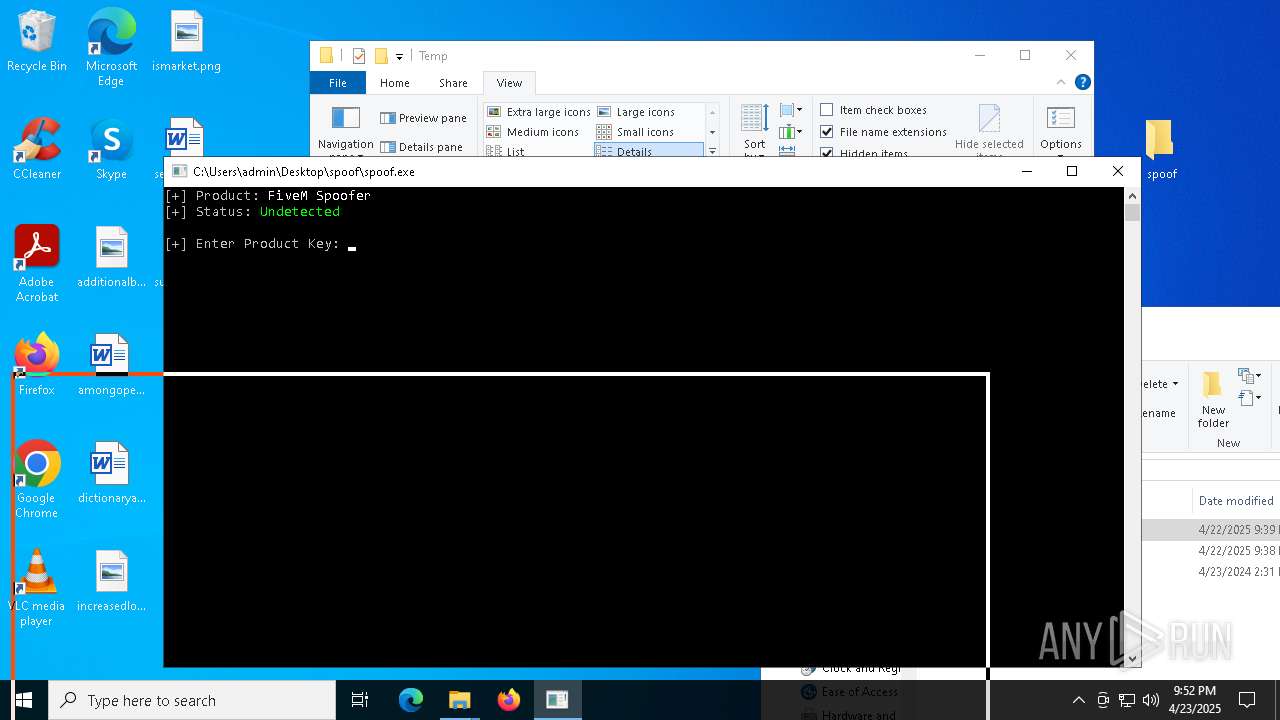
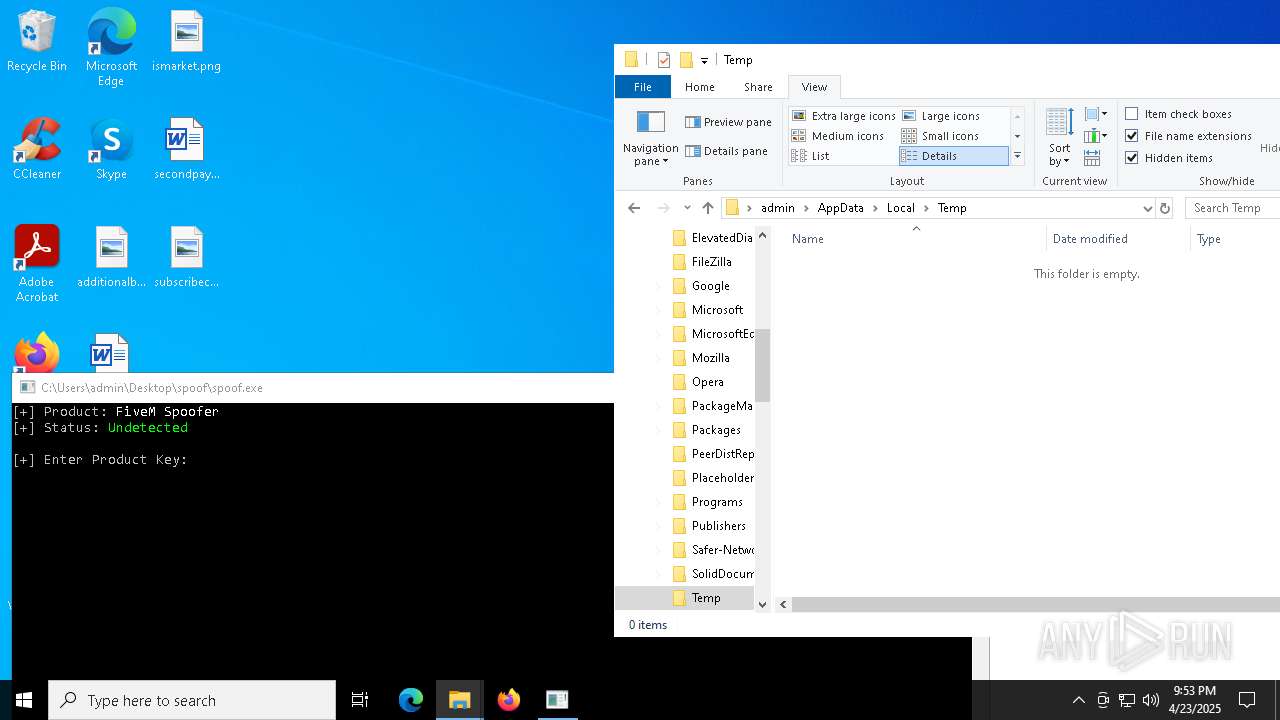
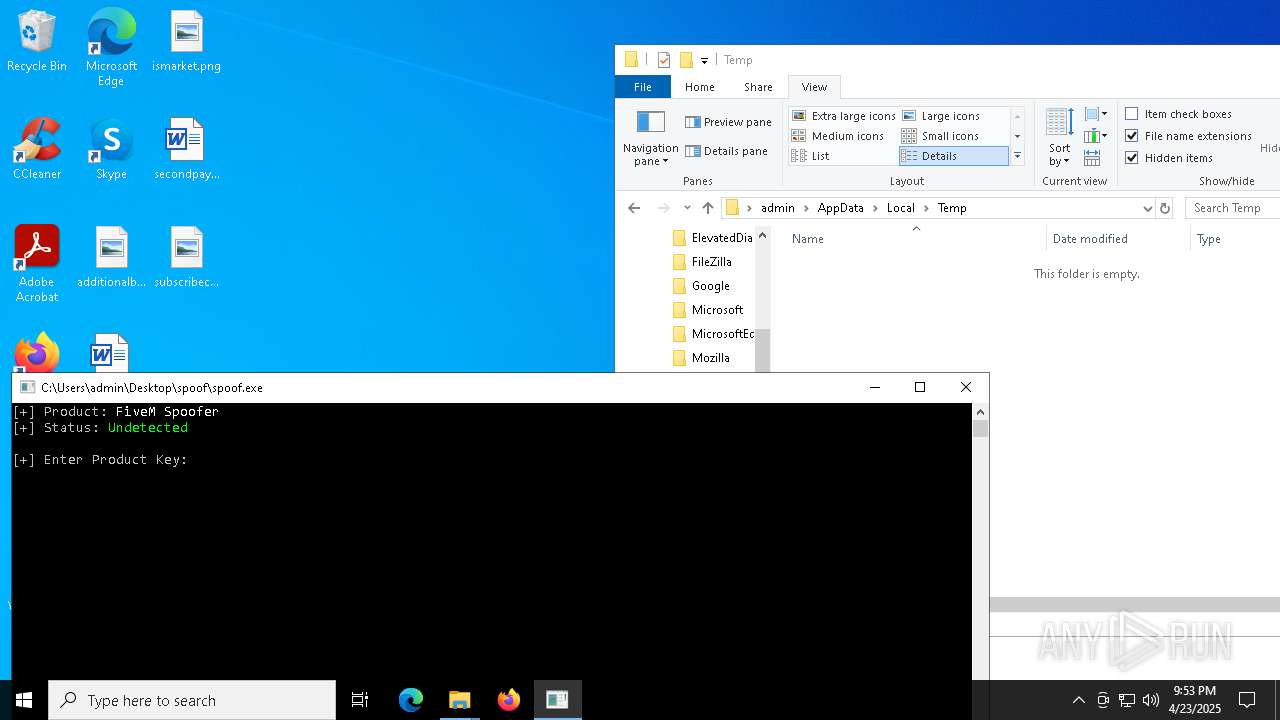
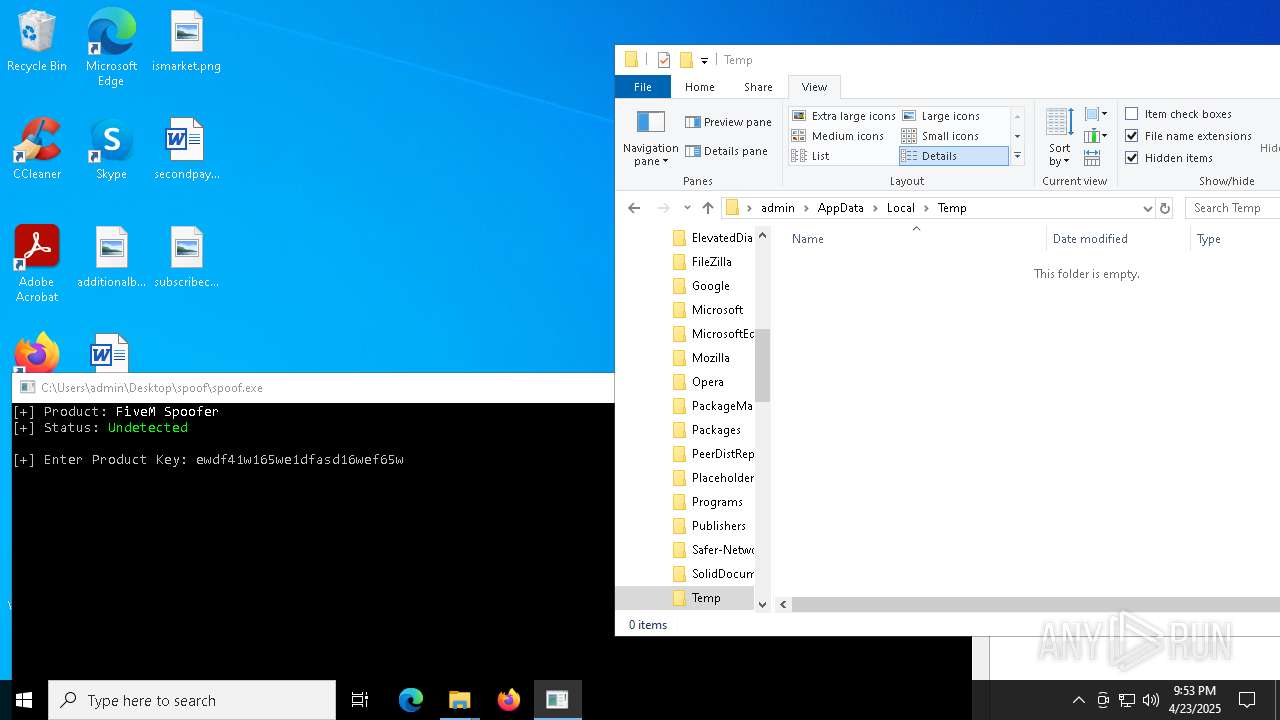
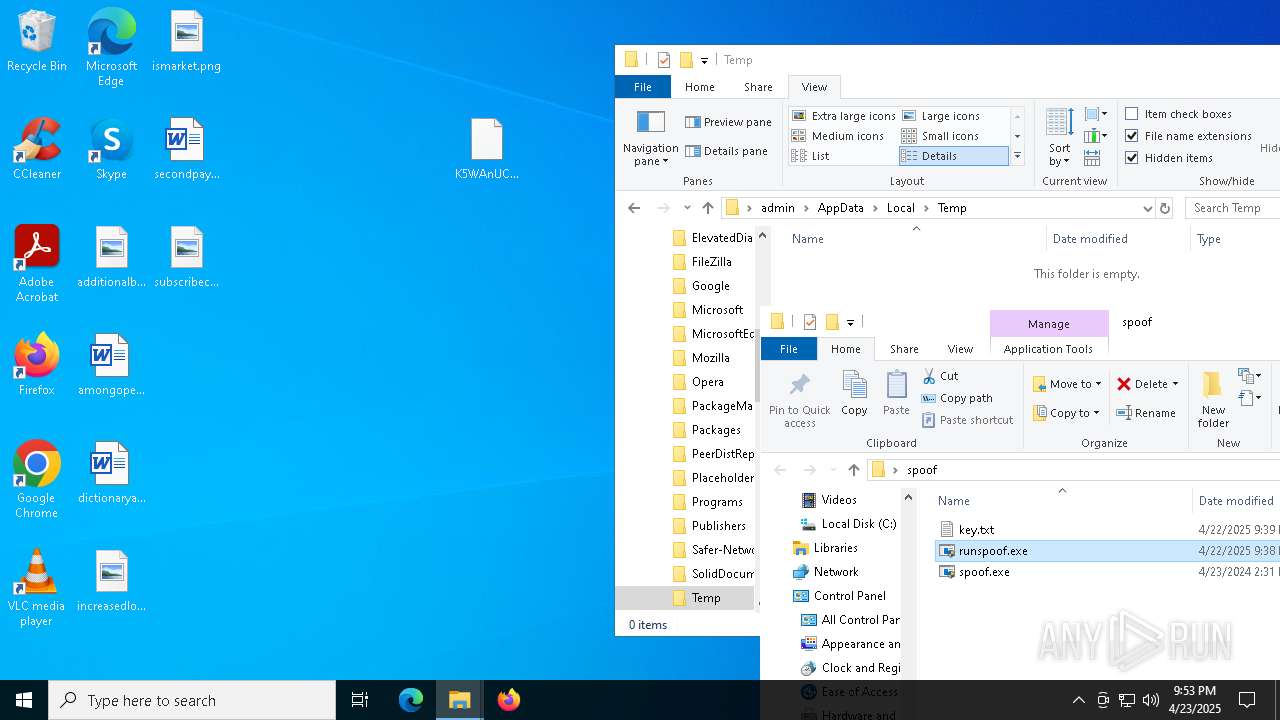
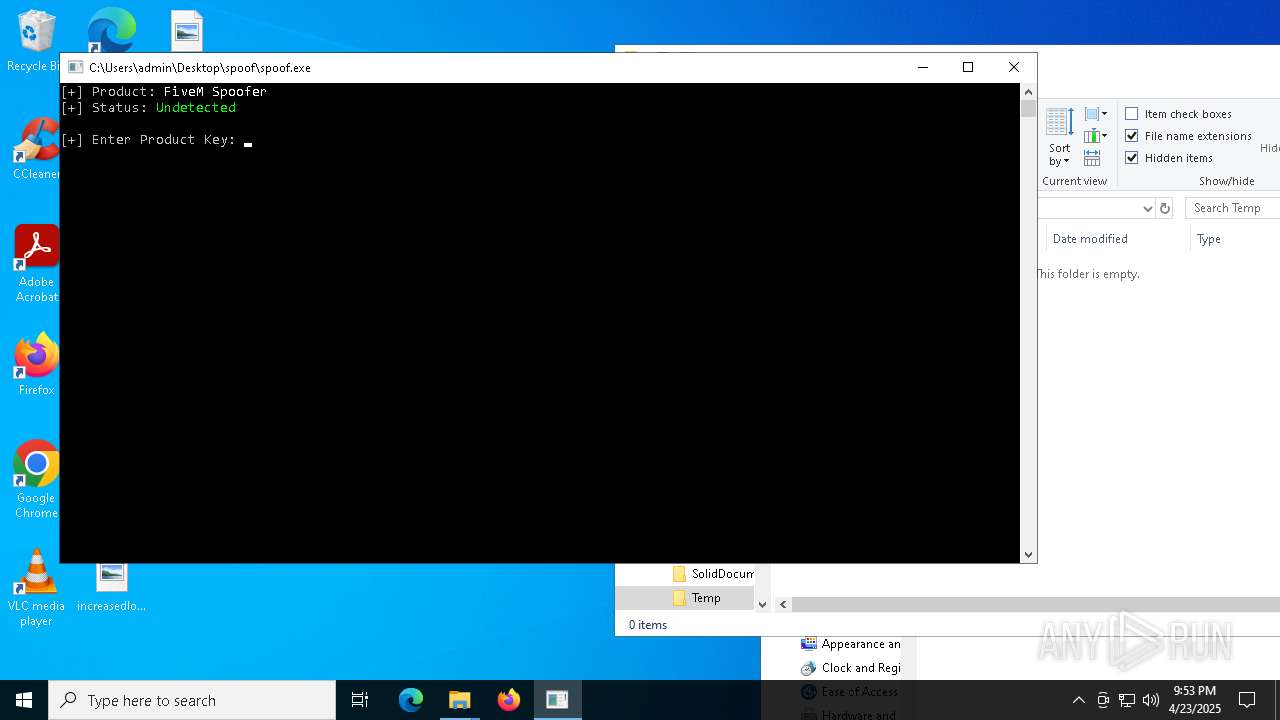
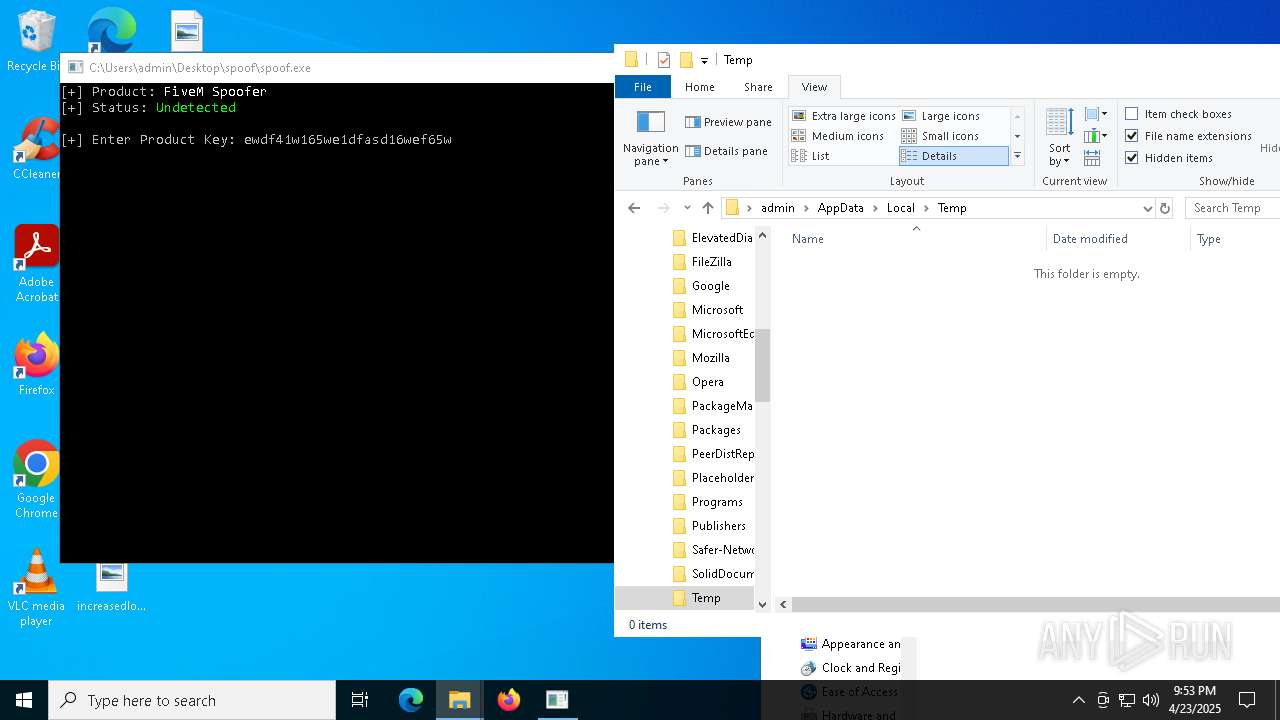
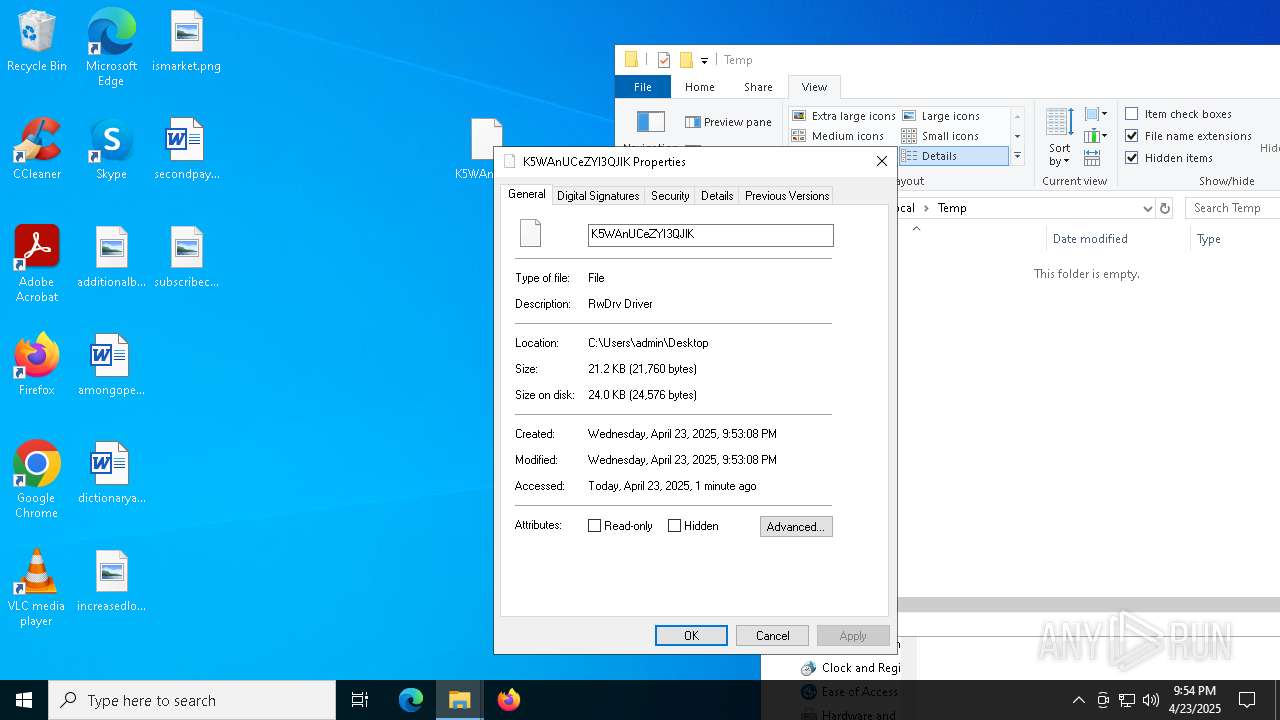
MALICIOUS
Vulnerable driver has been detected
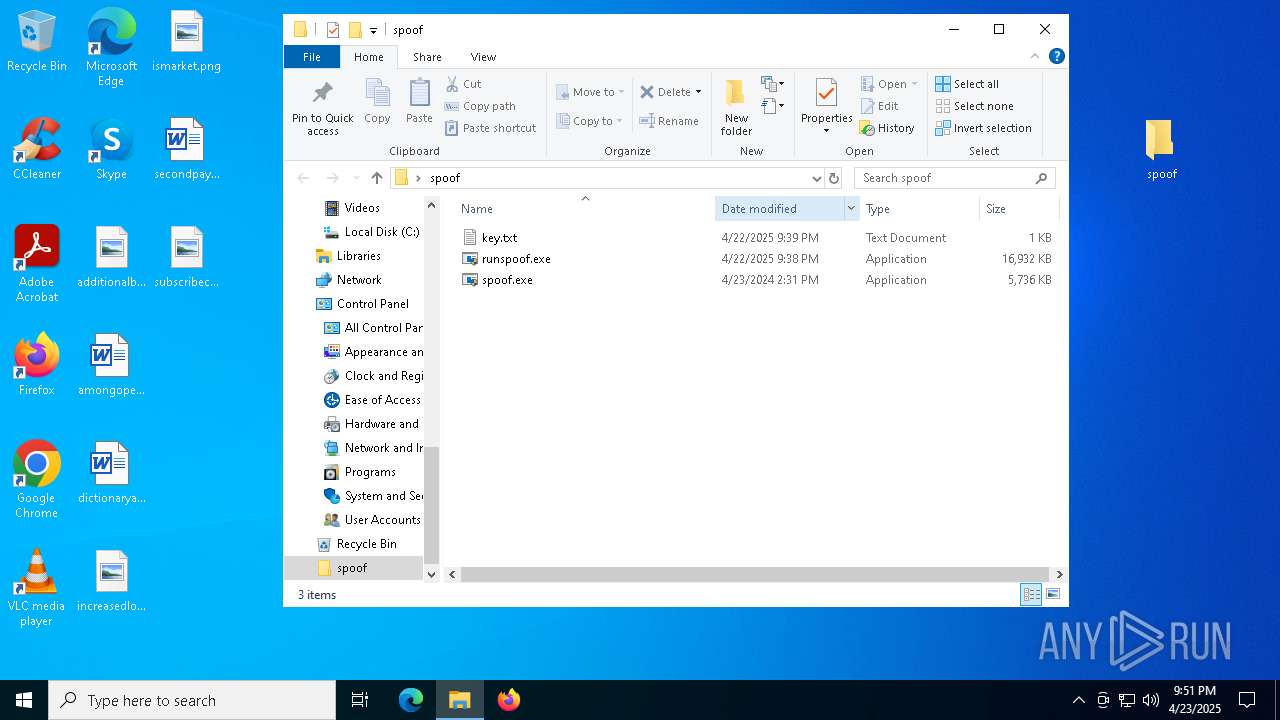
- spoof.exe (PID: 3156)
SUSPICIOUS
Reads security settings of Internet Explorer
- ShellExperienceHost.exe (PID: 8188)
- runspoof.exe (PID: 7048)
- runspoof.exe (PID: 4220)
Reads the BIOS version
- spoof.exe (PID: 8080)
- spoof.exe (PID: 3156)
- spoof.exe (PID: 7804)
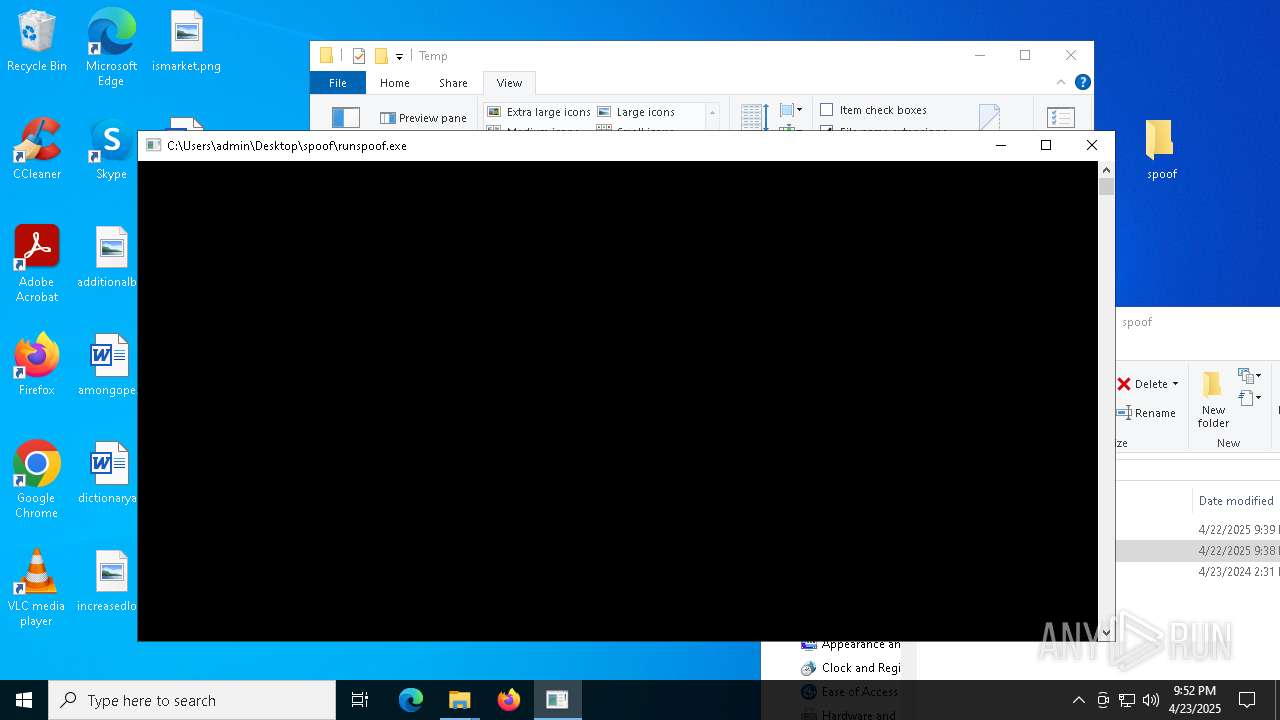
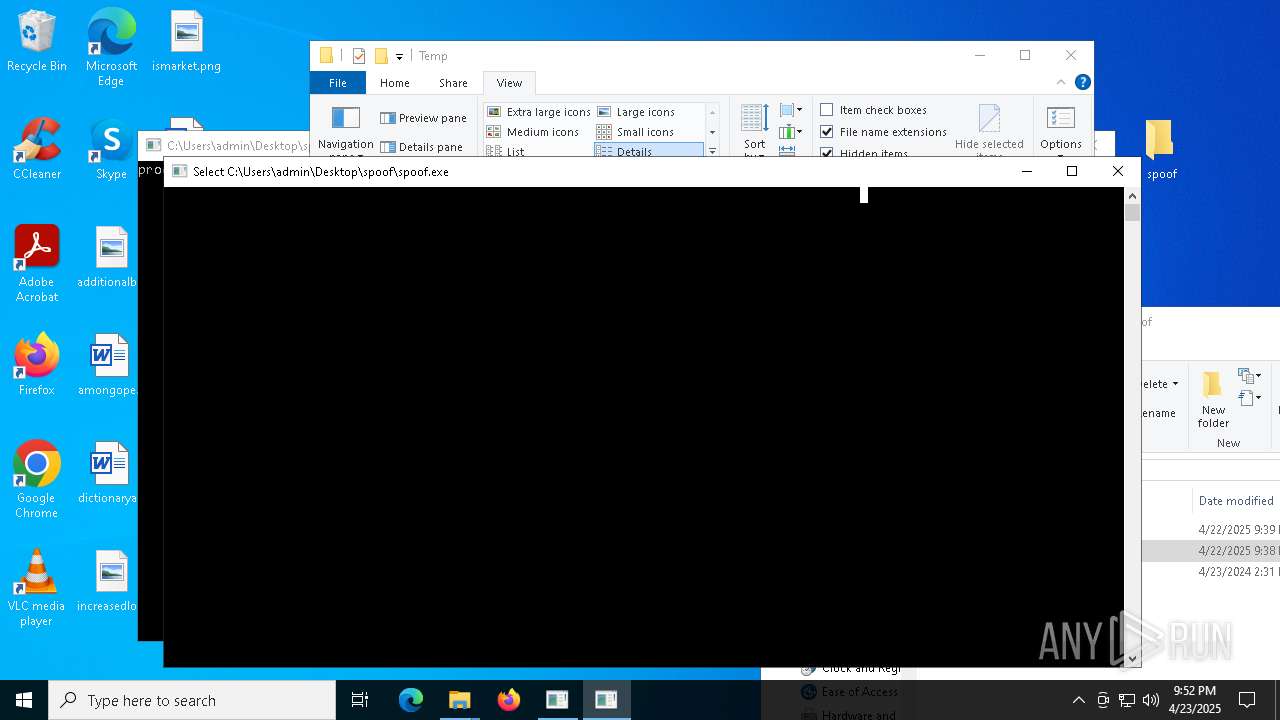
Starts CMD.EXE for commands execution
- spoof.exe (PID: 8080)
- spoof.exe (PID: 3156)
Reads the date of Windows installation
- spoof.exe (PID: 8080)
- spoof.exe (PID: 3156)
- spoof.exe (PID: 7804)
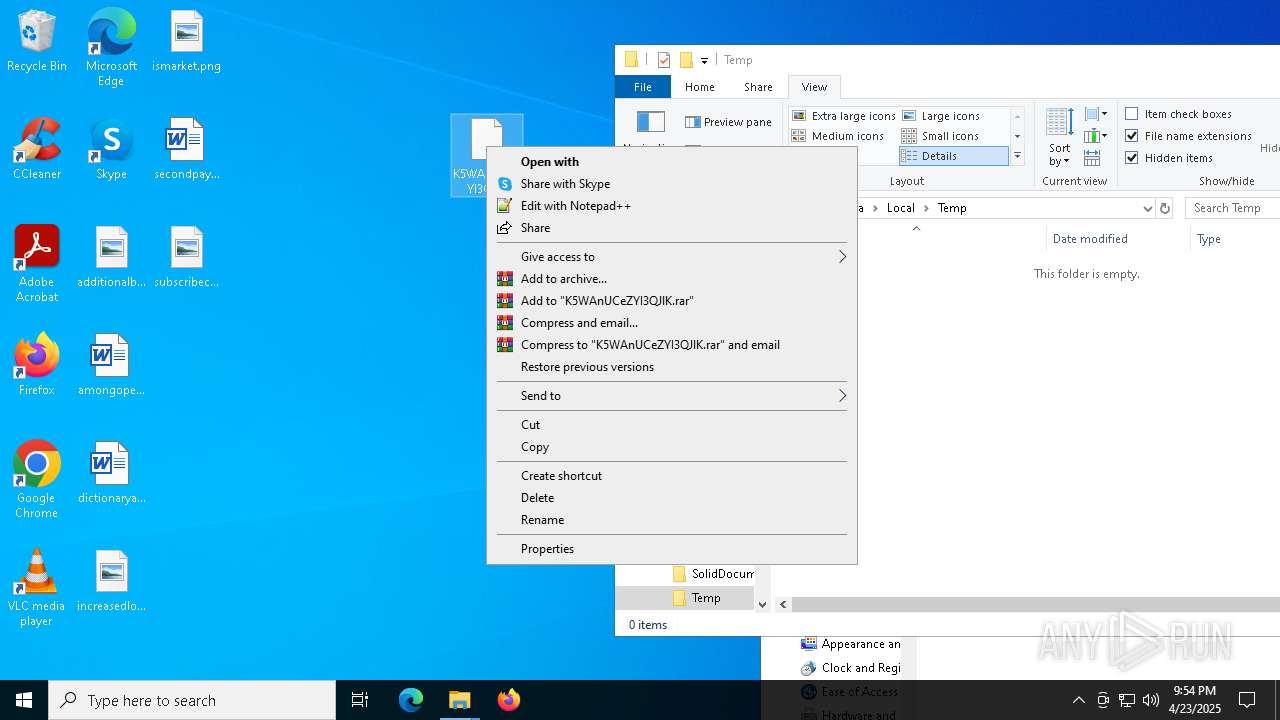
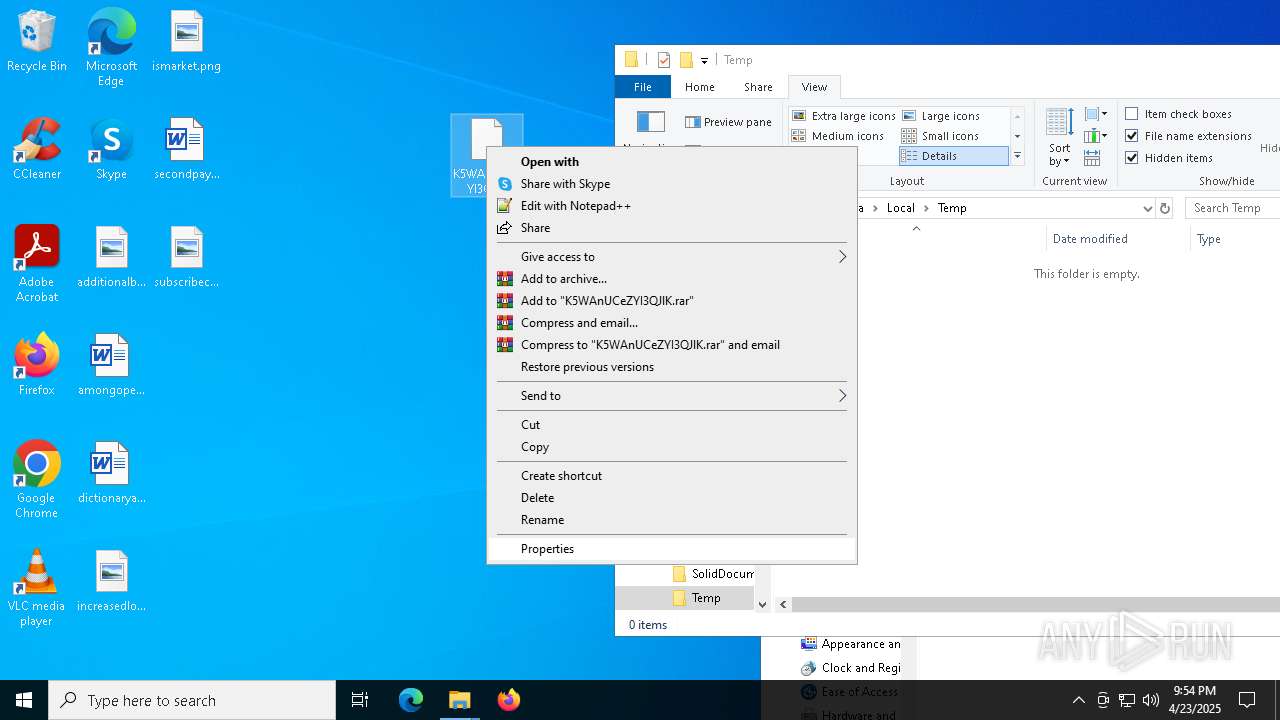
Starts application with an unusual extension
- cmd.exe (PID: 6476)
- cmd.exe (PID: 7972)
Hides command output
- cmd.exe (PID: 6476)
- cmd.exe (PID: 7972)
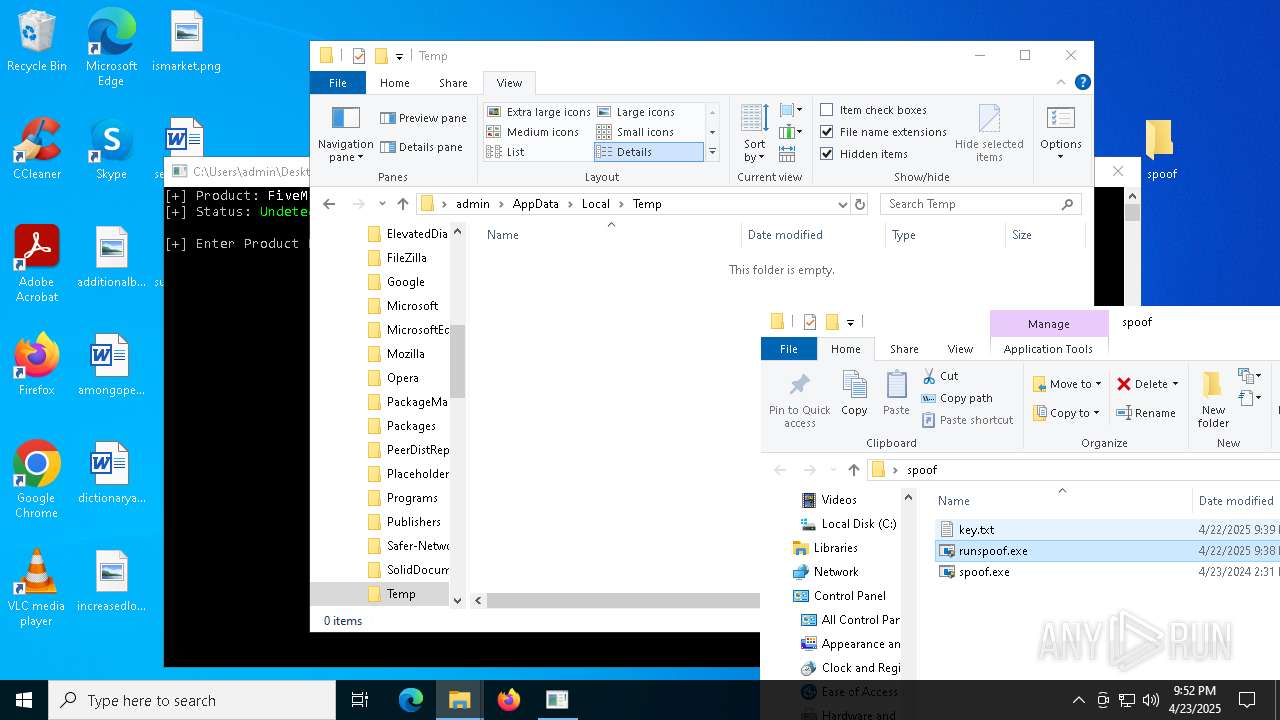
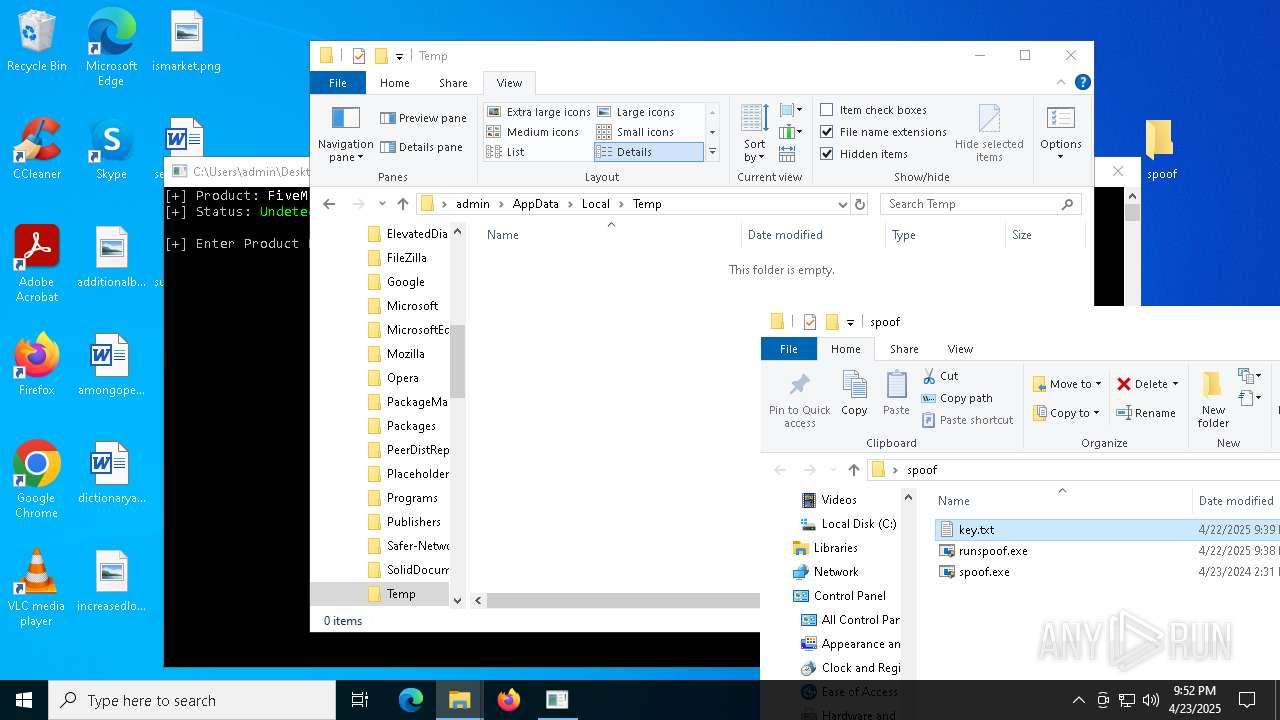
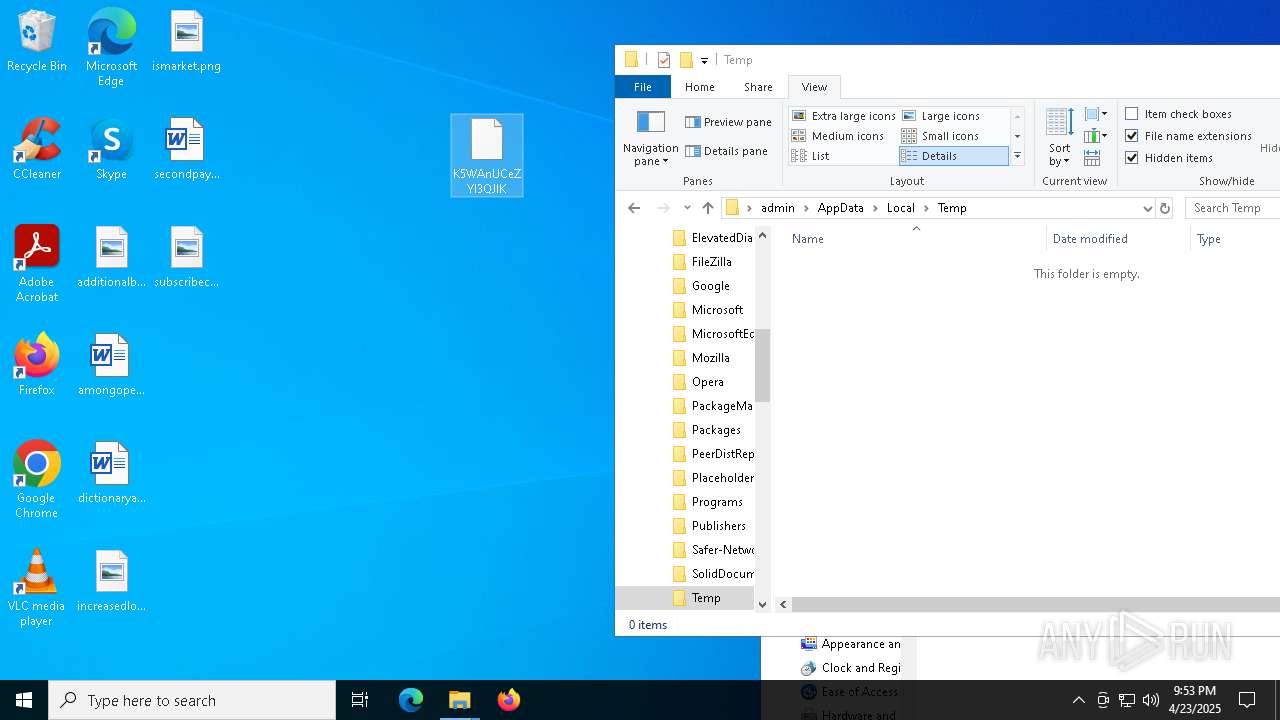
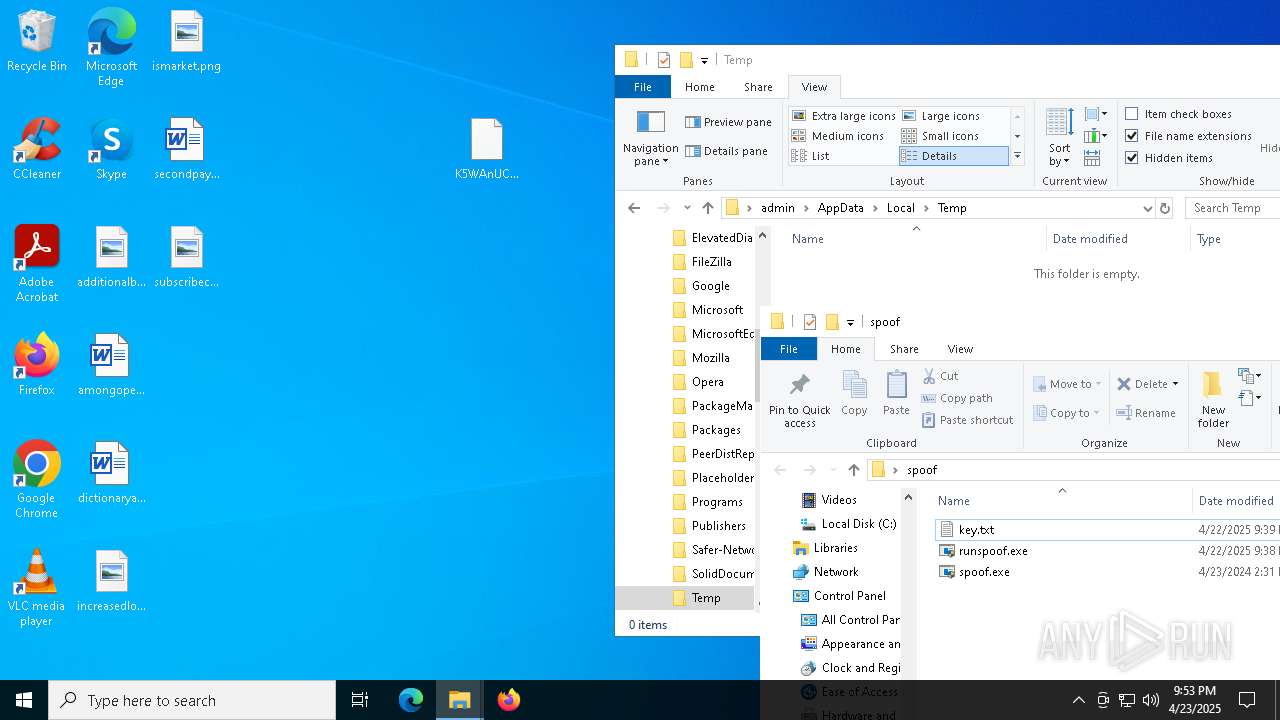
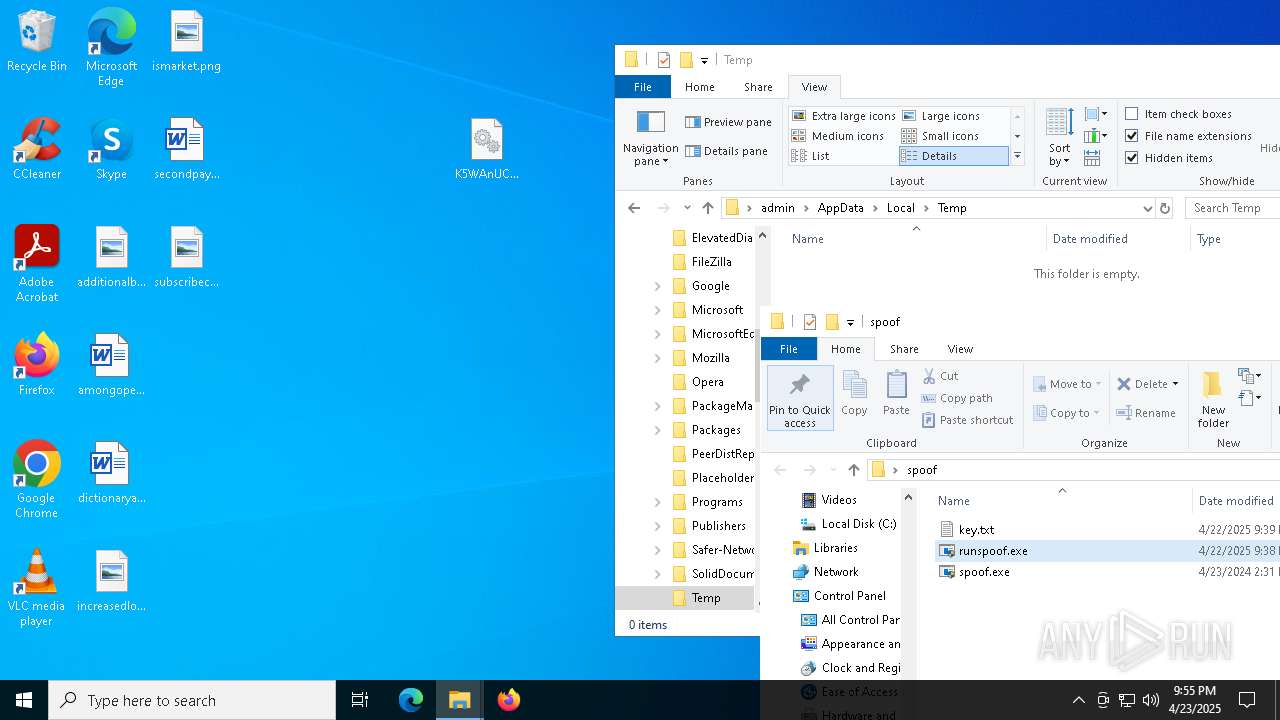
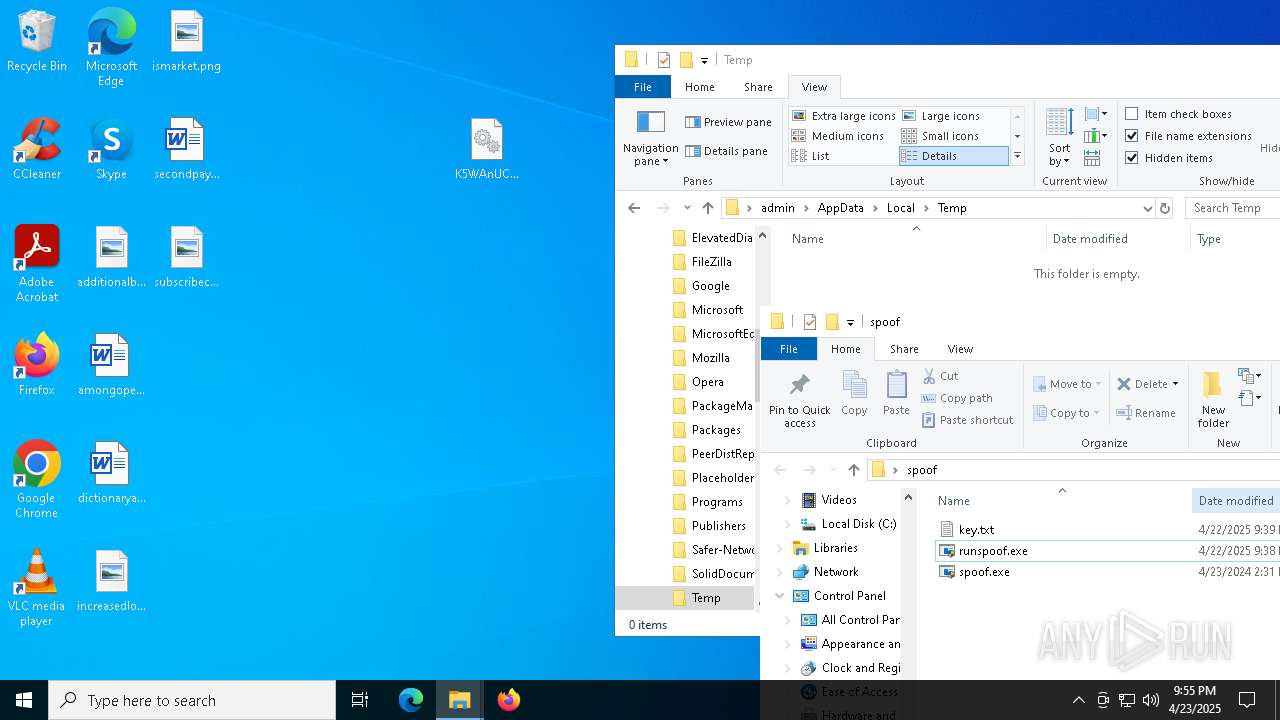
Executable content was dropped or overwritten
- spoof.exe (PID: 8080)
- spoof.exe (PID: 3156)
Creates or modifies Windows services
- spoof.exe (PID: 8080)
- spoof.exe (PID: 3156)
Connects to unusual port
- spoof.exe (PID: 7804)
INFO
Application launched itself
- firefox.exe (PID: 6480)
- firefox.exe (PID: 1196)
- firefox.exe (PID: 6808)
- firefox.exe (PID: 7436)
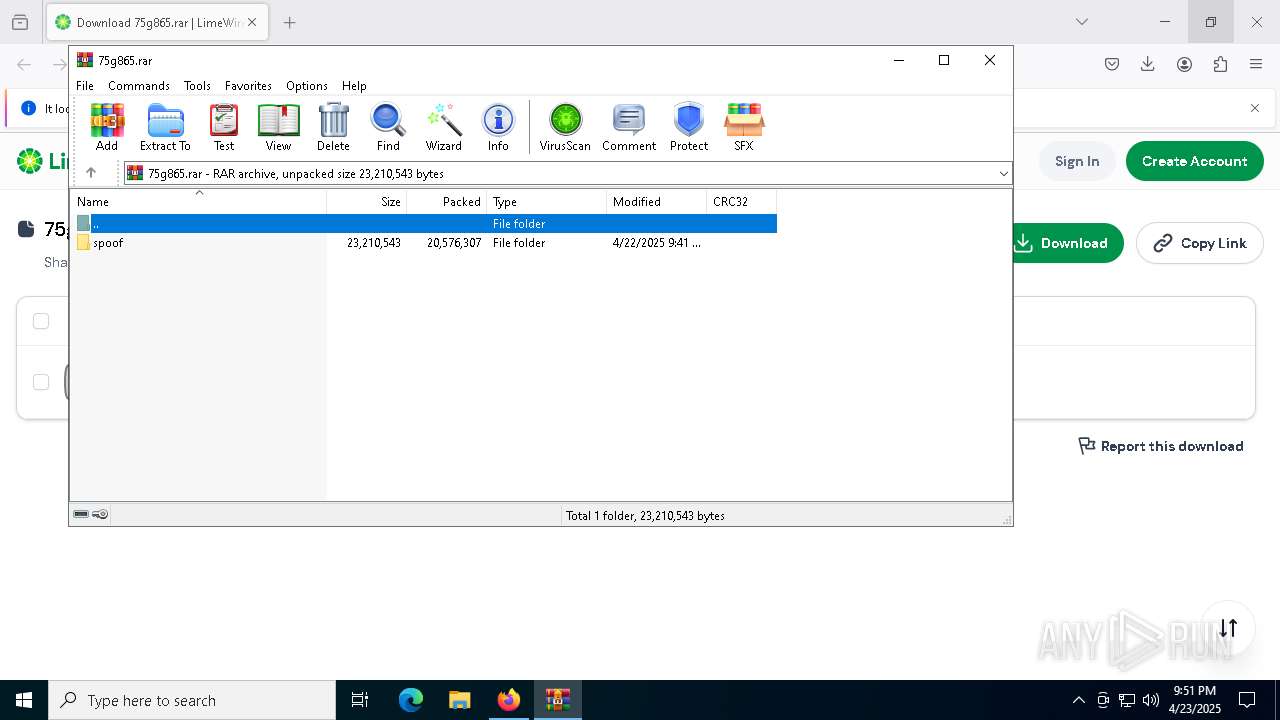
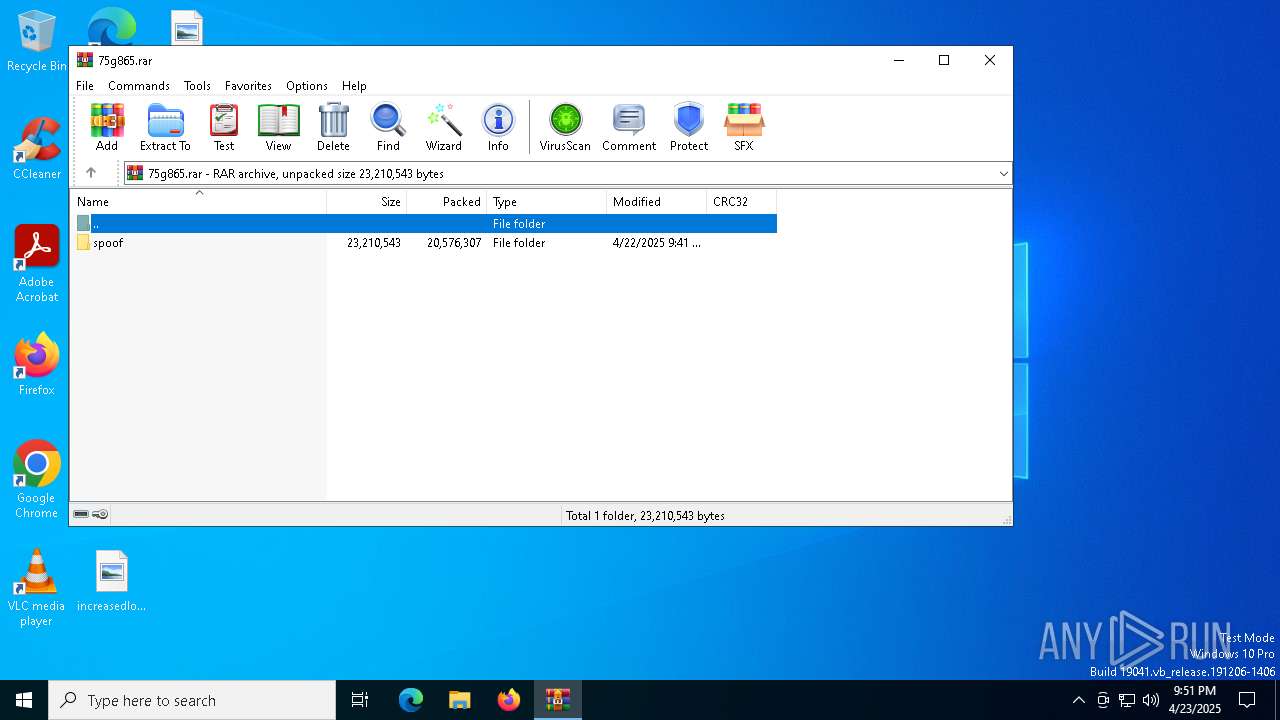
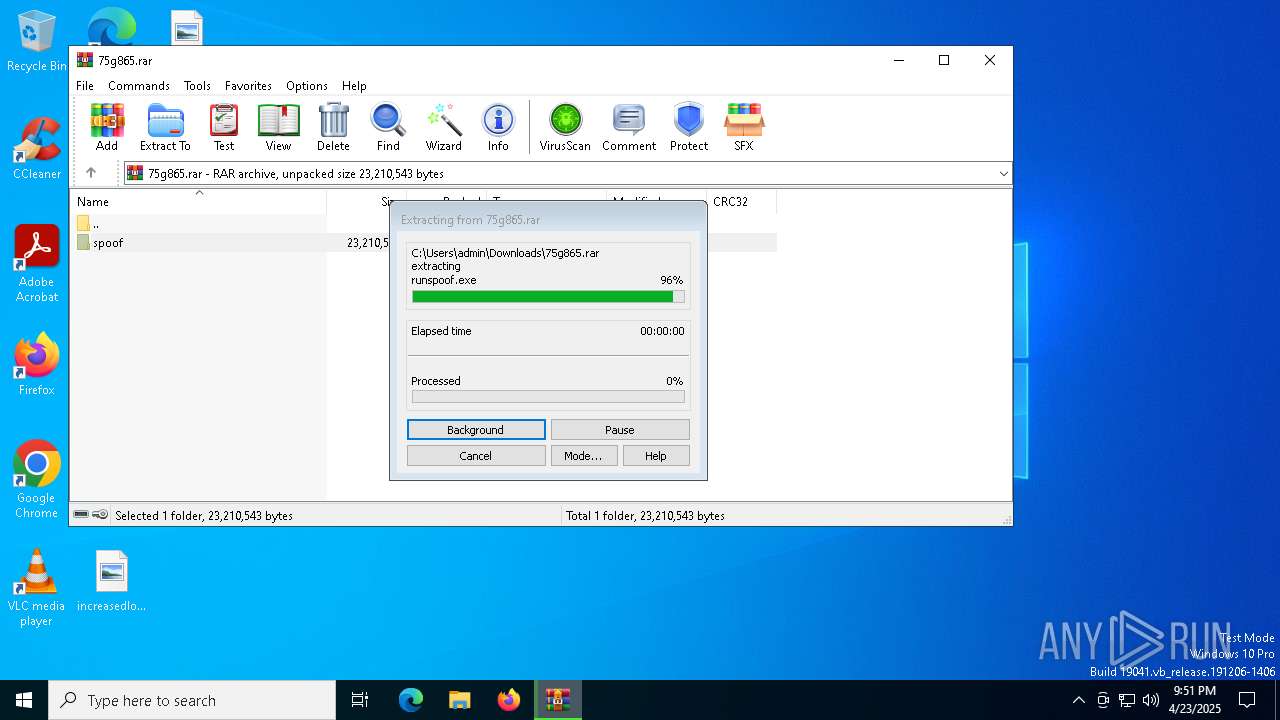
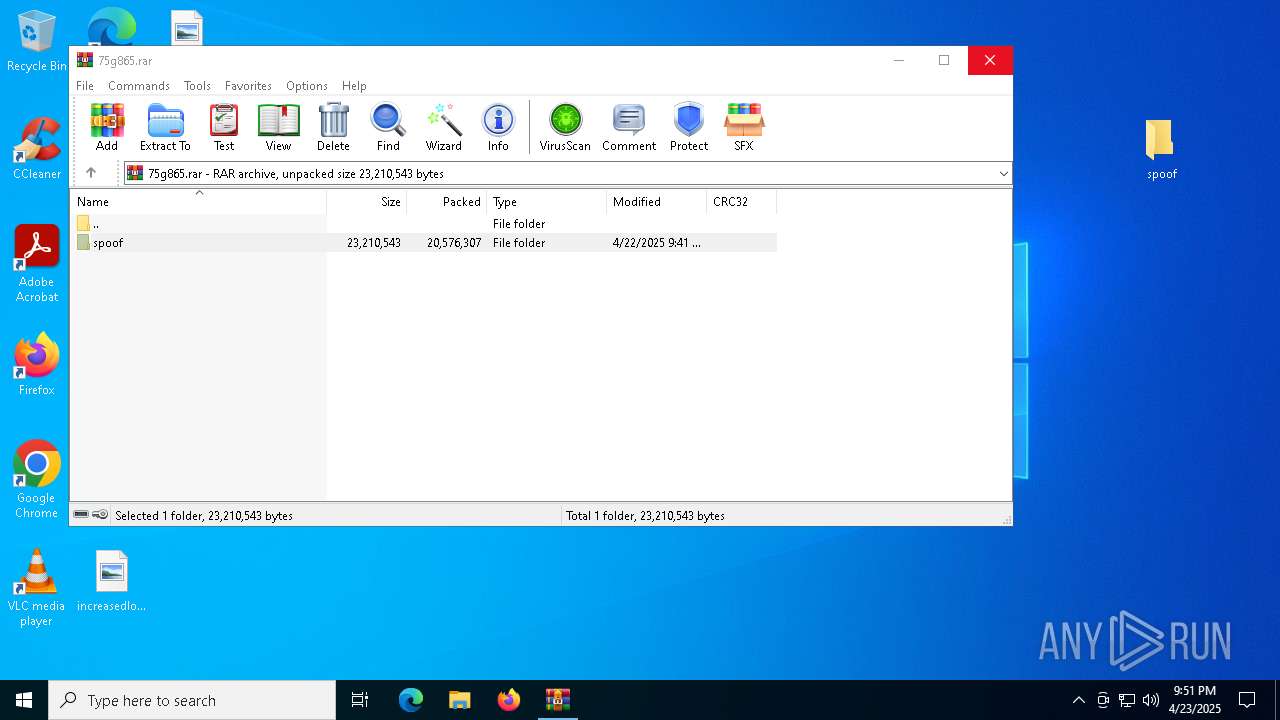
Executable content was dropped or overwritten
- WinRAR.exe (PID: 4188)
Checks supported languages
- ShellExperienceHost.exe (PID: 8188)
- runspoof.exe (PID: 7048)
- spoof.exe (PID: 8080)
- chcp.com (PID: 4120)
- runspoof.exe (PID: 4220)
- spoof.exe (PID: 3156)
- spoof.exe (PID: 7804)
- chcp.com (PID: 2644)
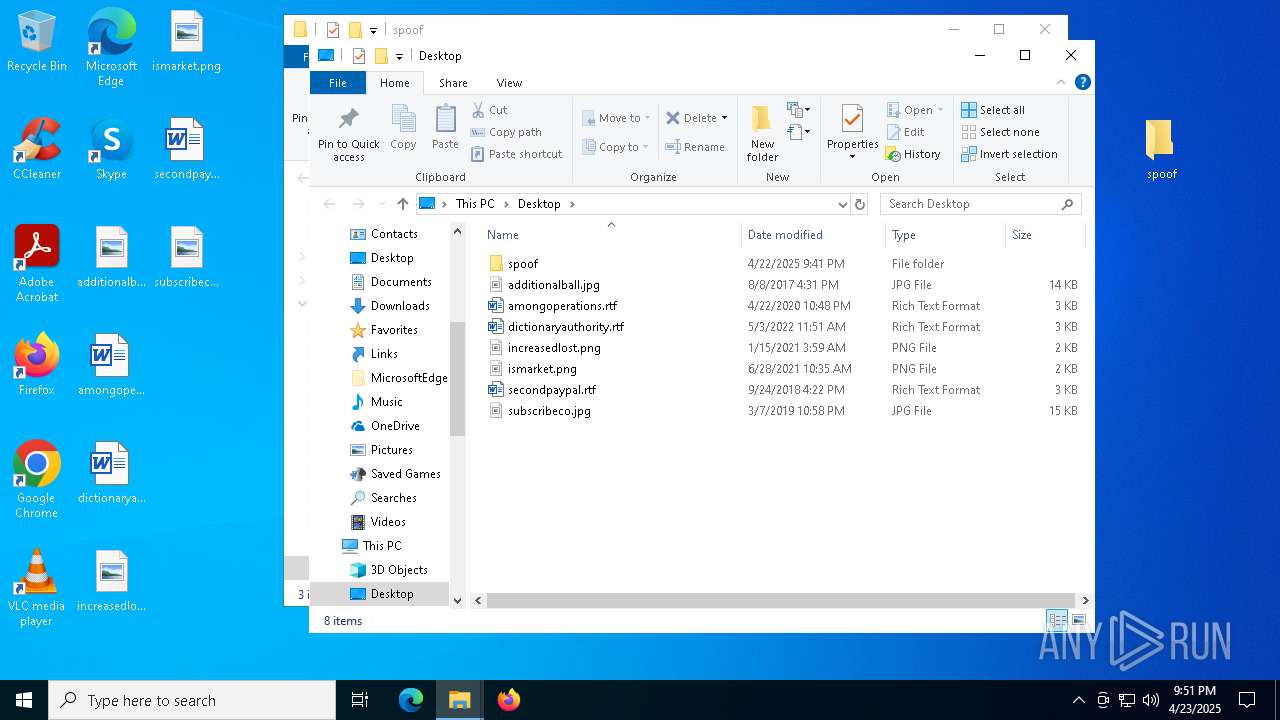
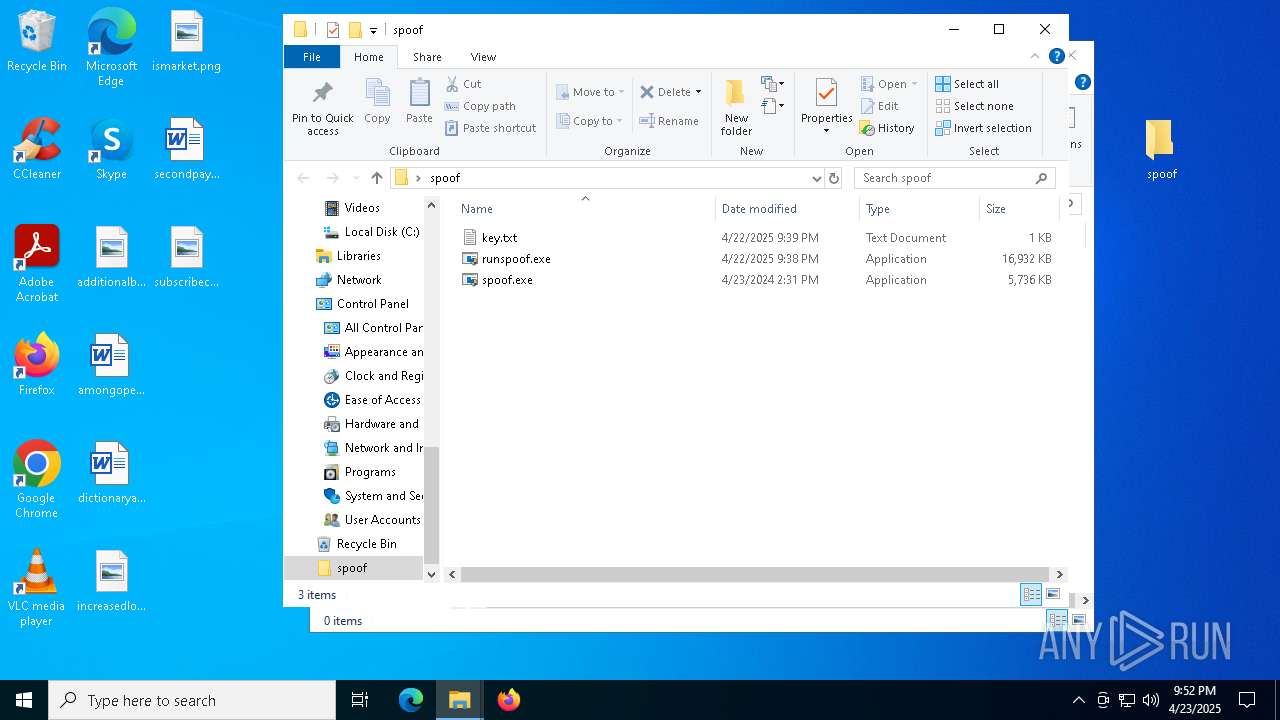
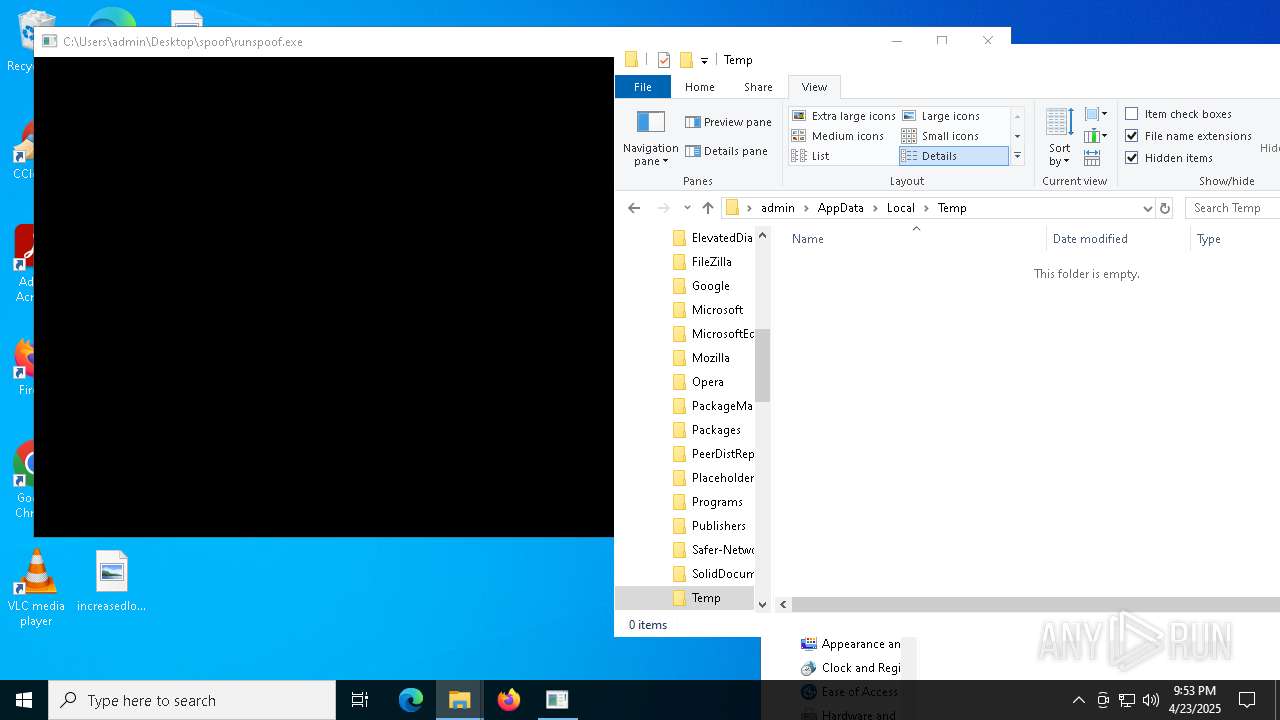
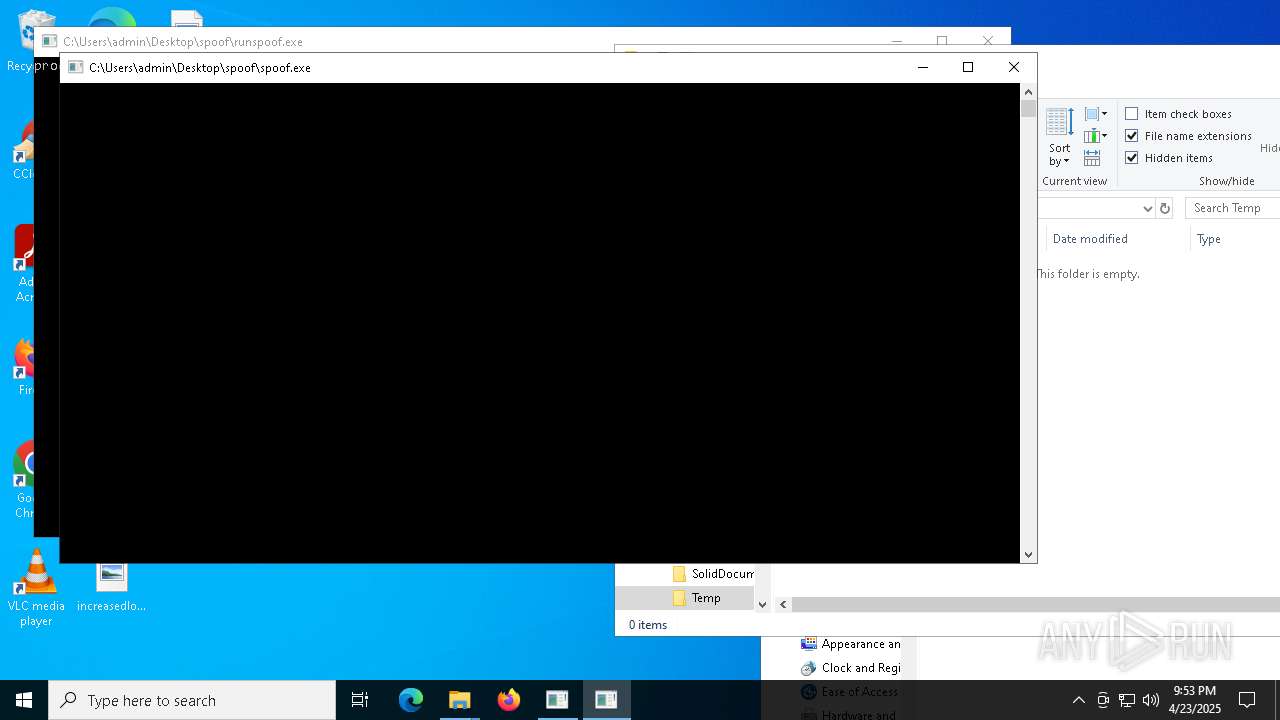
Manual execution by a user
- WinRAR.exe (PID: 4188)
- runspoof.exe (PID: 7720)
- runspoof.exe (PID: 7048)
- notepad.exe (PID: 7920)
- runspoof.exe (PID: 7196)
- runspoof.exe (PID: 4220)
- firefox.exe (PID: 7436)
- spoof.exe (PID: 7020)
- spoof.exe (PID: 7804)
Reads the computer name
- ShellExperienceHost.exe (PID: 8188)
- runspoof.exe (PID: 7048)
- spoof.exe (PID: 8080)
- runspoof.exe (PID: 4220)
- spoof.exe (PID: 3156)
- spoof.exe (PID: 7804)
Reads the software policy settings
- slui.exe (PID: 5988)
- runspoof.exe (PID: 7048)
- slui.exe (PID: 7524)
- runspoof.exe (PID: 4220)
Checks proxy server information
- runspoof.exe (PID: 7048)
- slui.exe (PID: 7524)
- runspoof.exe (PID: 4220)
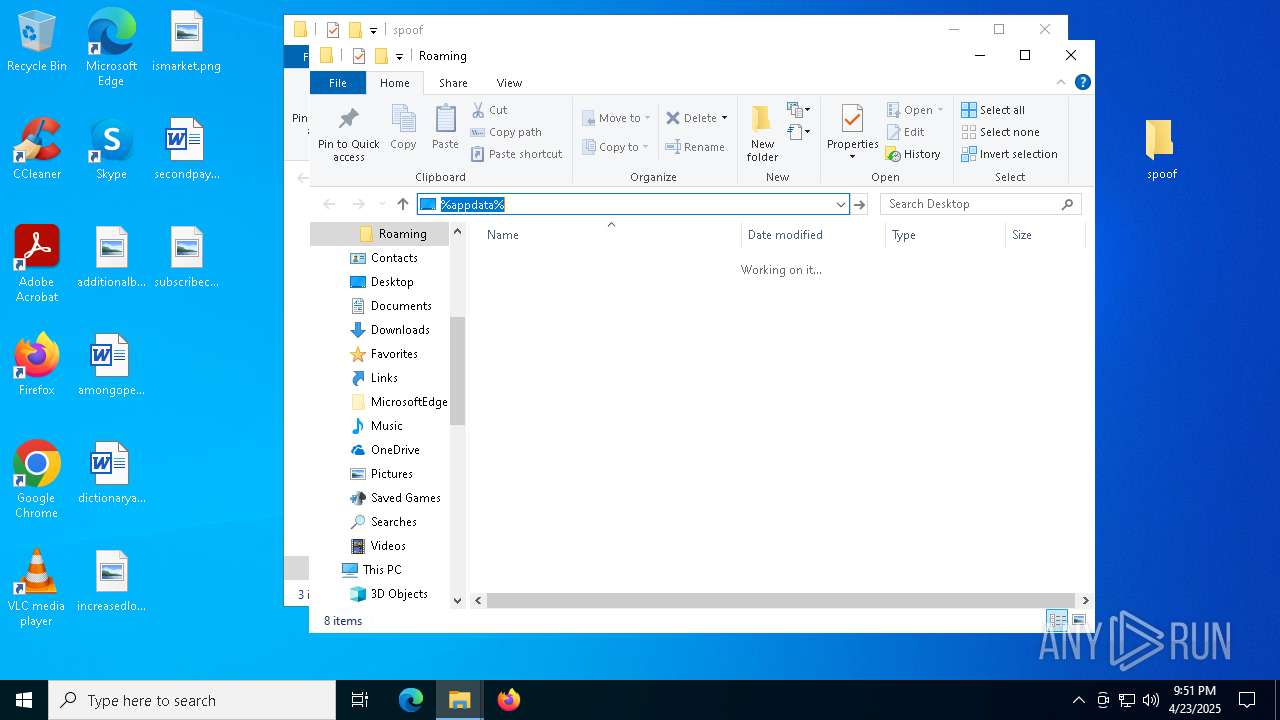
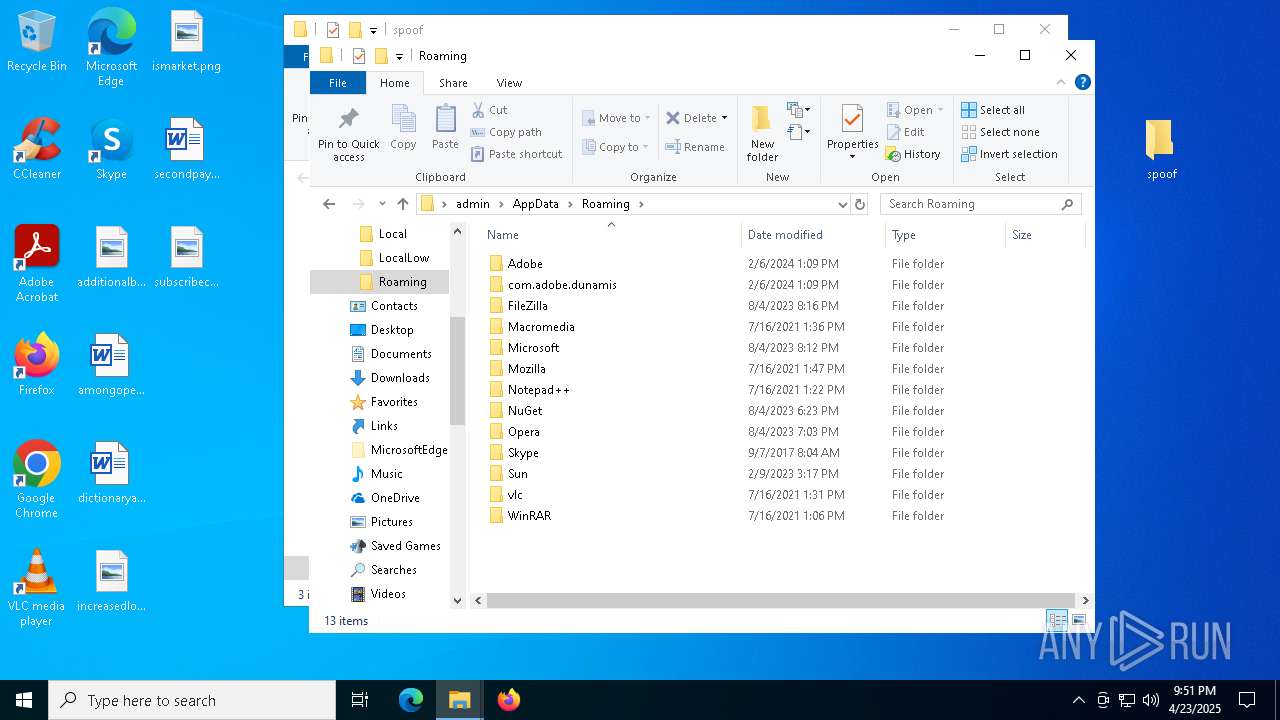
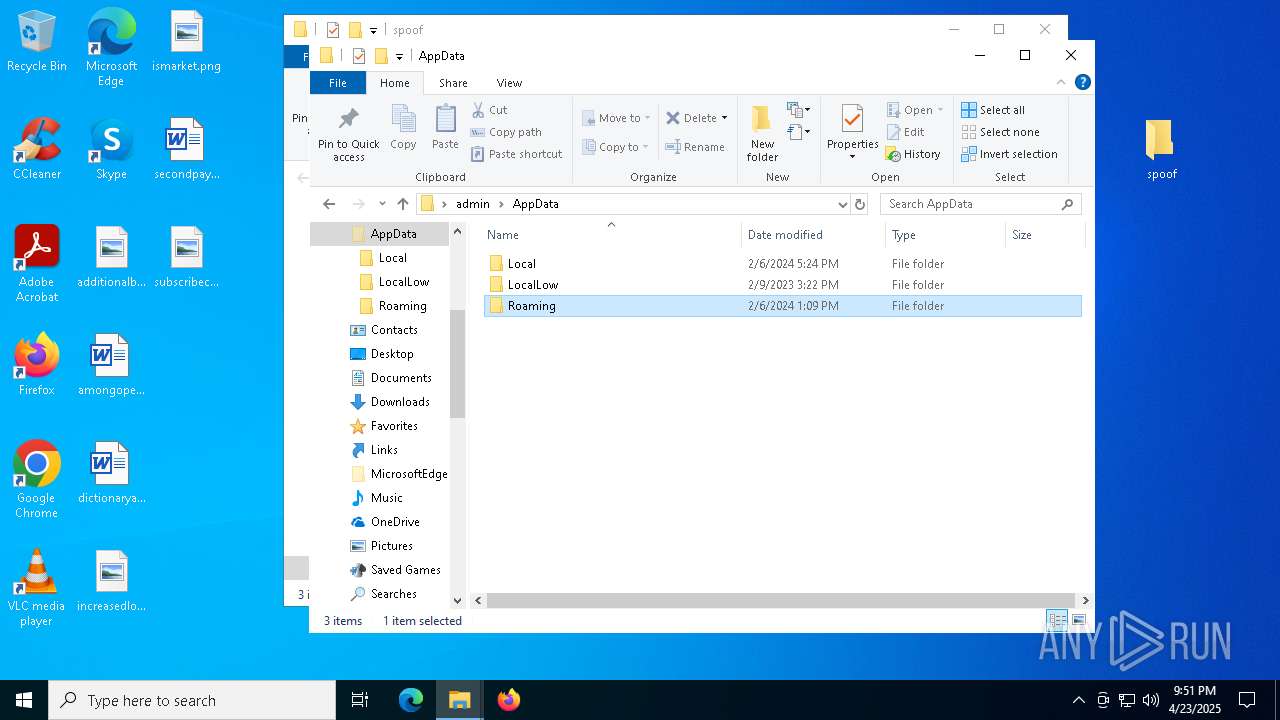
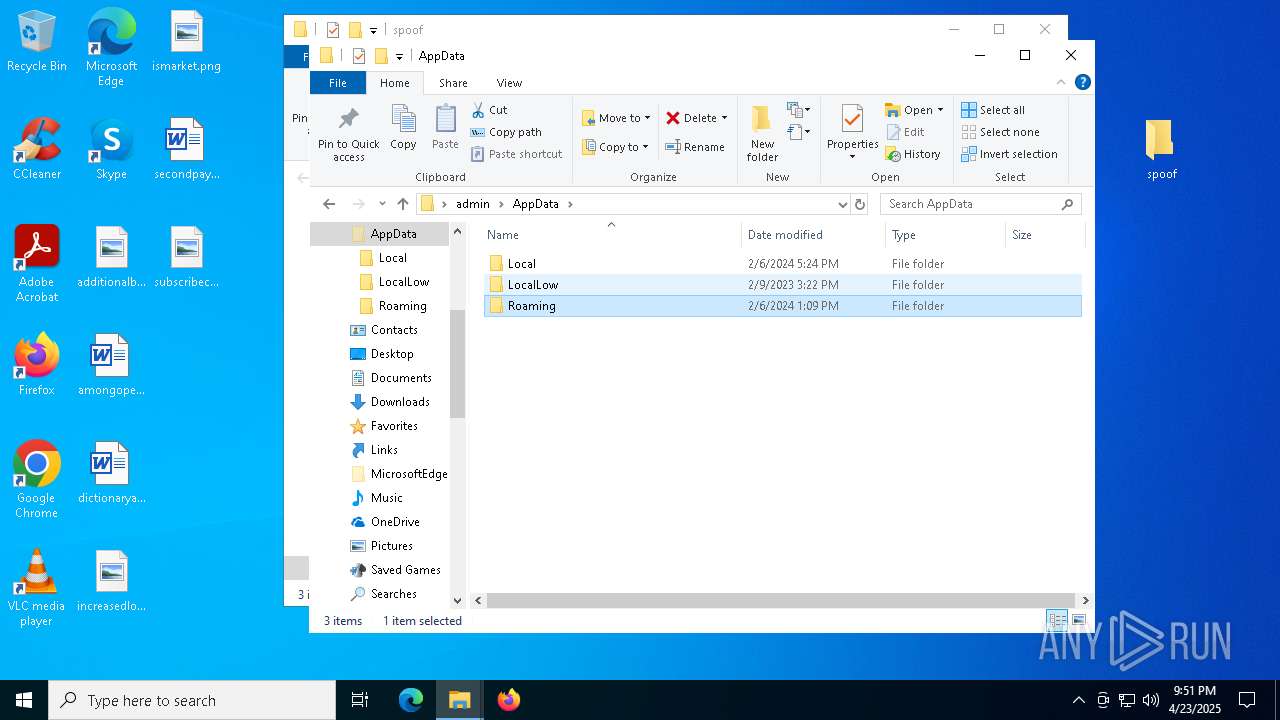
Creates files or folders in the user directory
- runspoof.exe (PID: 7048)
Reads the machine GUID from the registry
- runspoof.exe (PID: 7048)
- runspoof.exe (PID: 4220)
Process checks whether UAC notifications are on
- spoof.exe (PID: 8080)
- spoof.exe (PID: 3156)
- spoof.exe (PID: 7804)
Reads Windows Product ID
- spoof.exe (PID: 8080)
- spoof.exe (PID: 3156)
- spoof.exe (PID: 7804)
Reads product name
- spoof.exe (PID: 8080)
- spoof.exe (PID: 3156)
- spoof.exe (PID: 7804)
Reads Environment values
- spoof.exe (PID: 8080)
- spoof.exe (PID: 3156)
- spoof.exe (PID: 7804)
Changes the display of characters in the console
- cmd.exe (PID: 6476)
- cmd.exe (PID: 7972)
Reads security settings of Internet Explorer
- notepad.exe (PID: 7920)
Themida protector has been detected
- spoof.exe (PID: 8080)
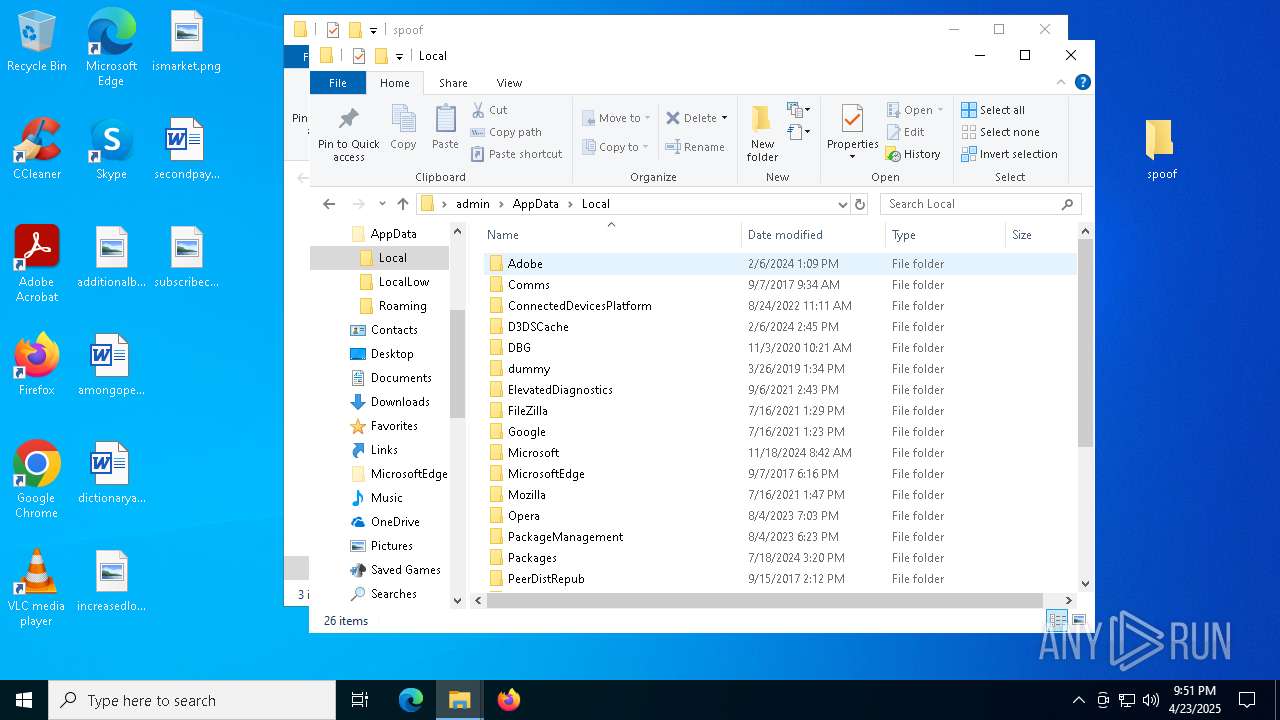
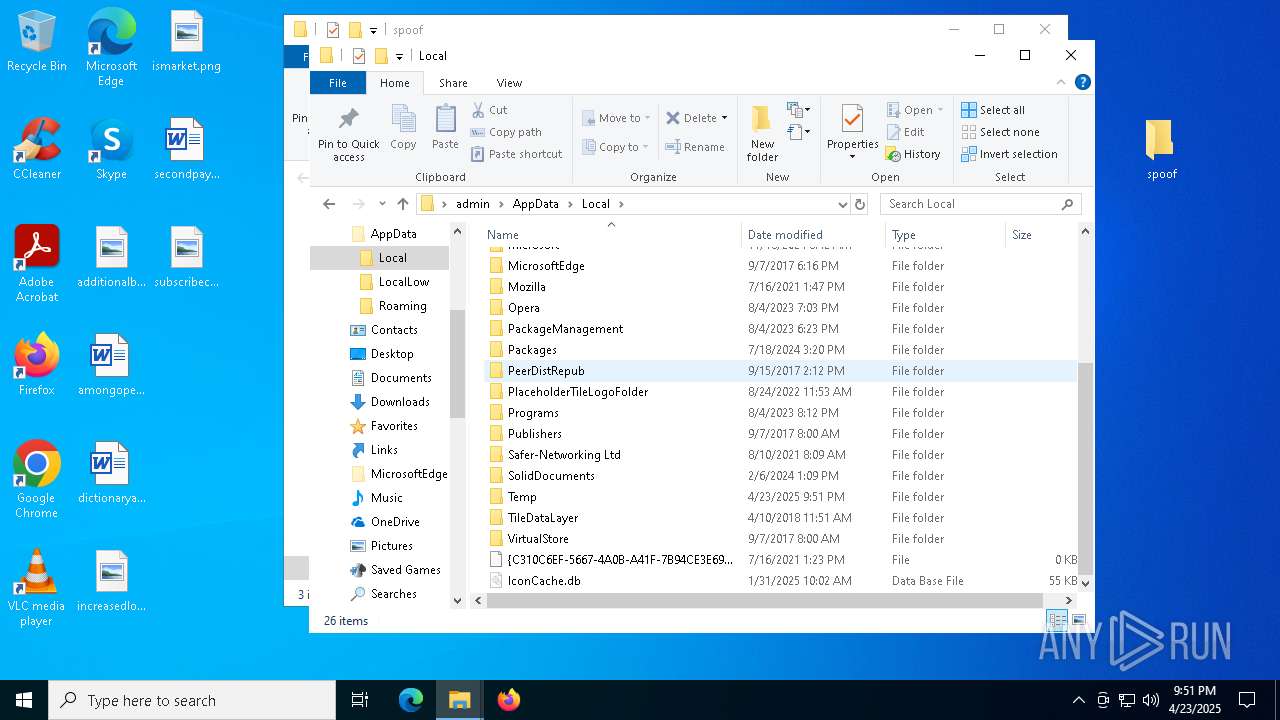
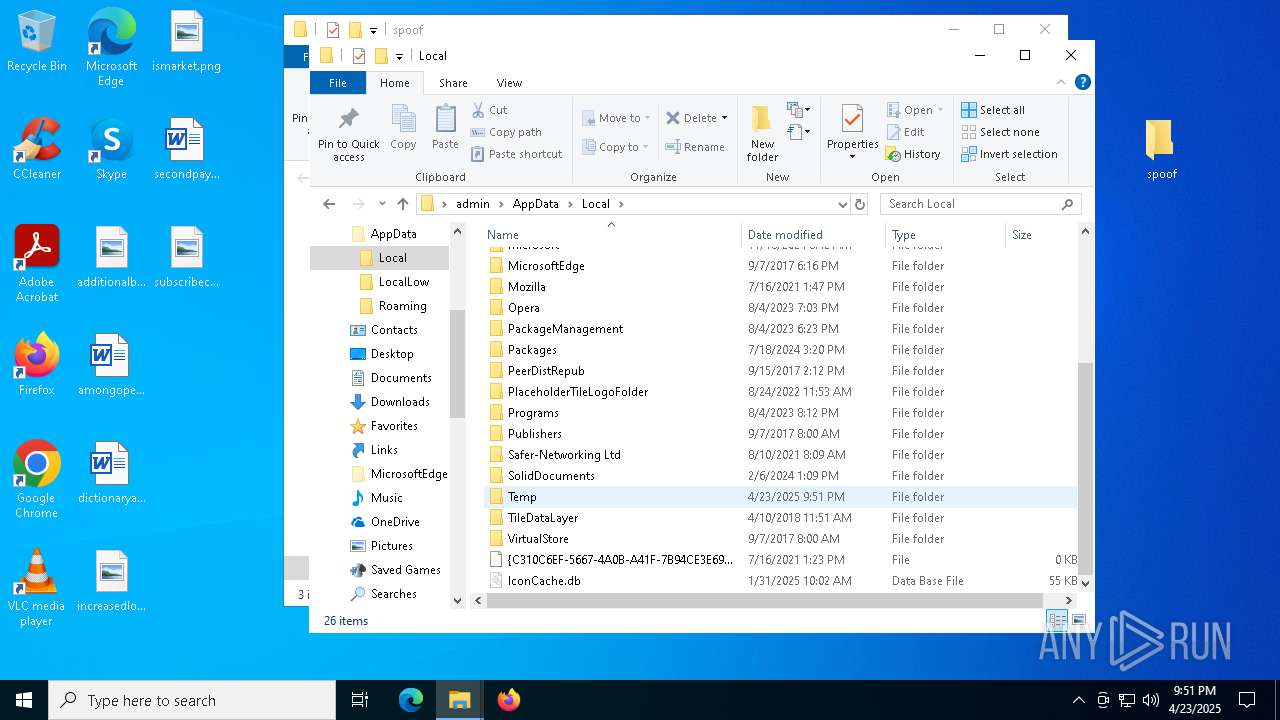
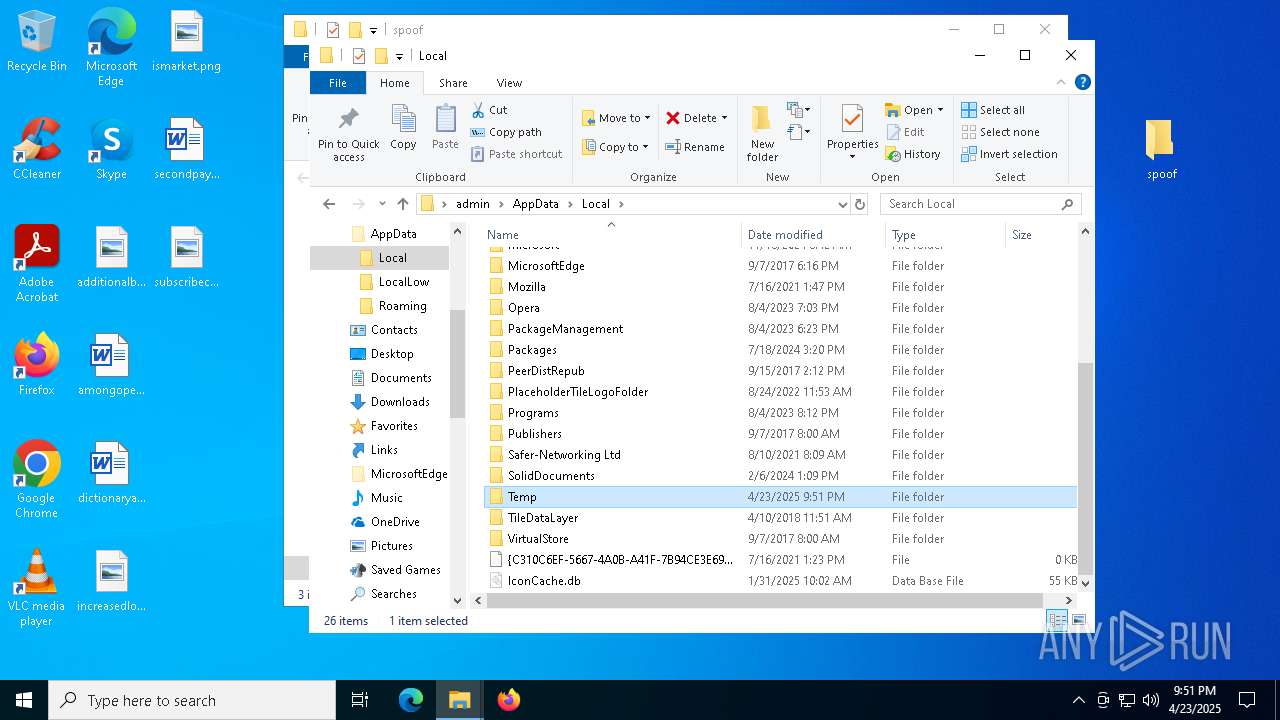
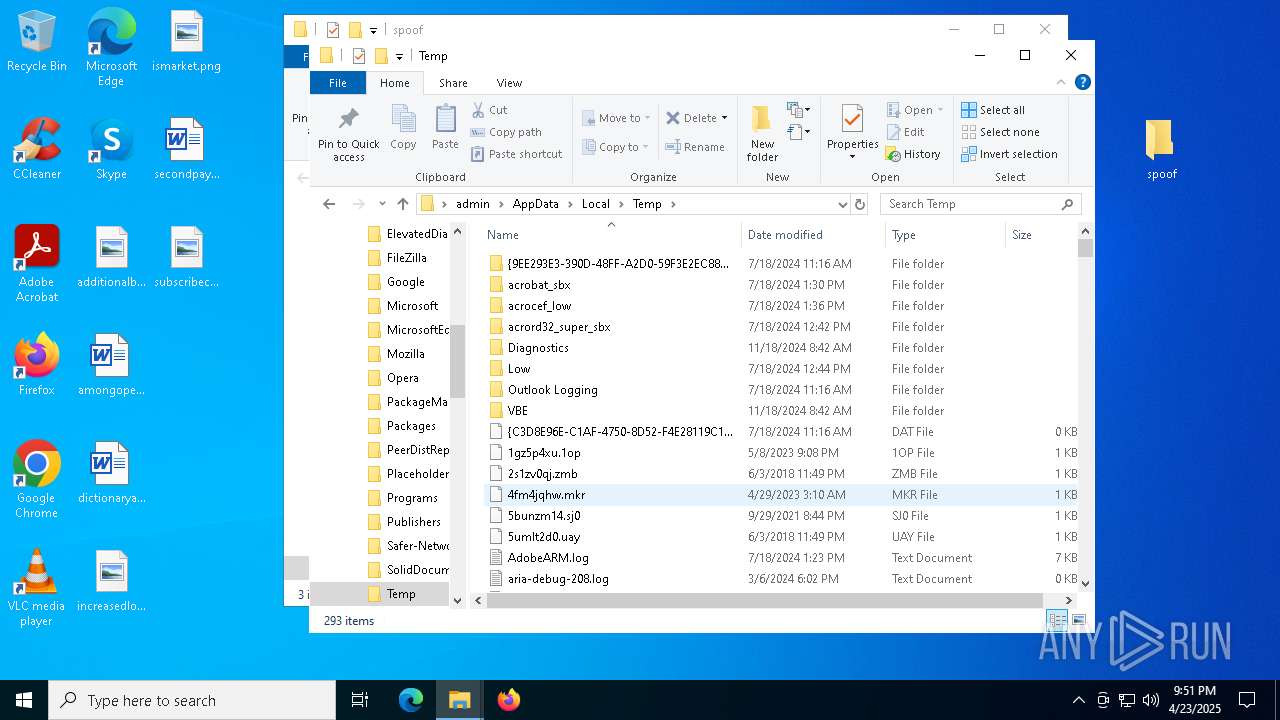
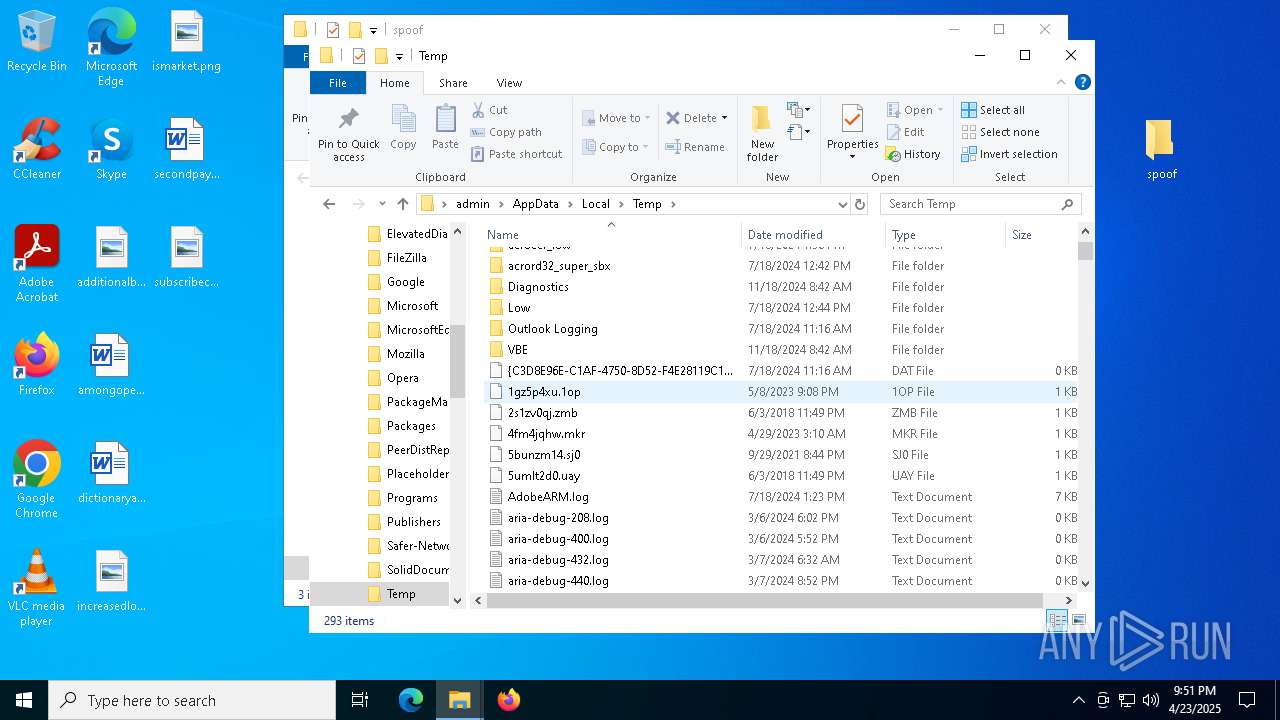
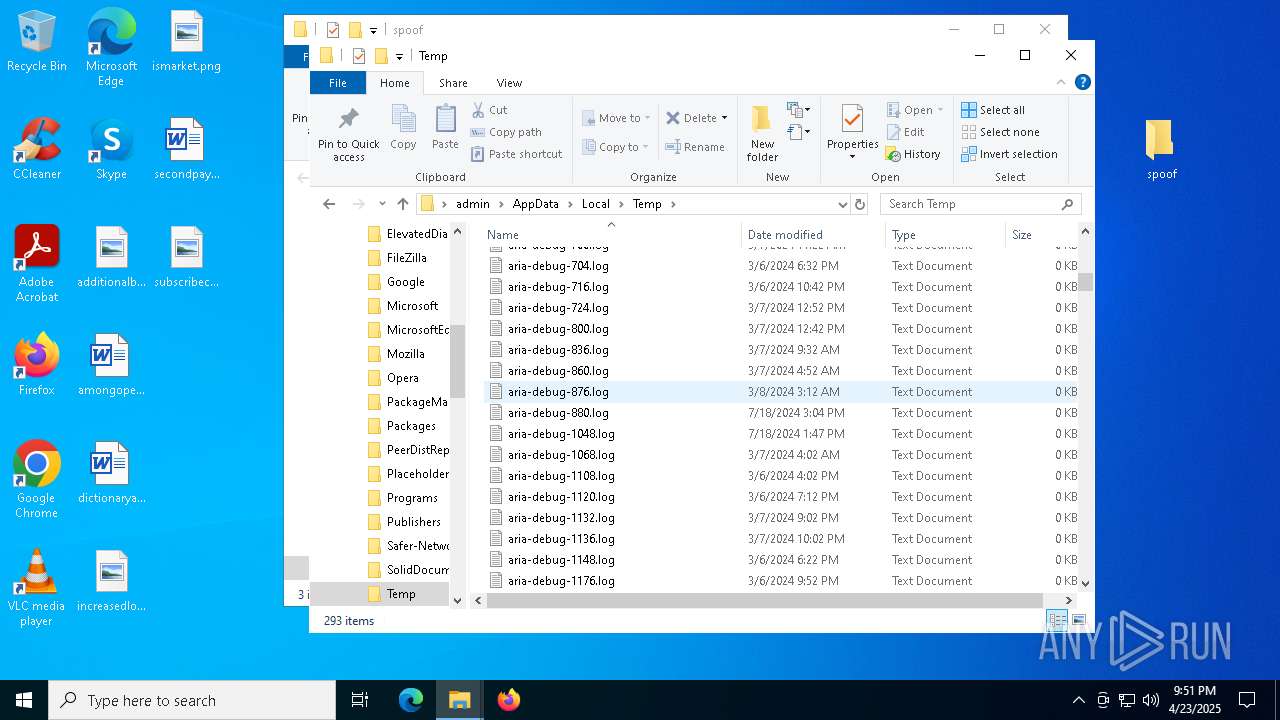
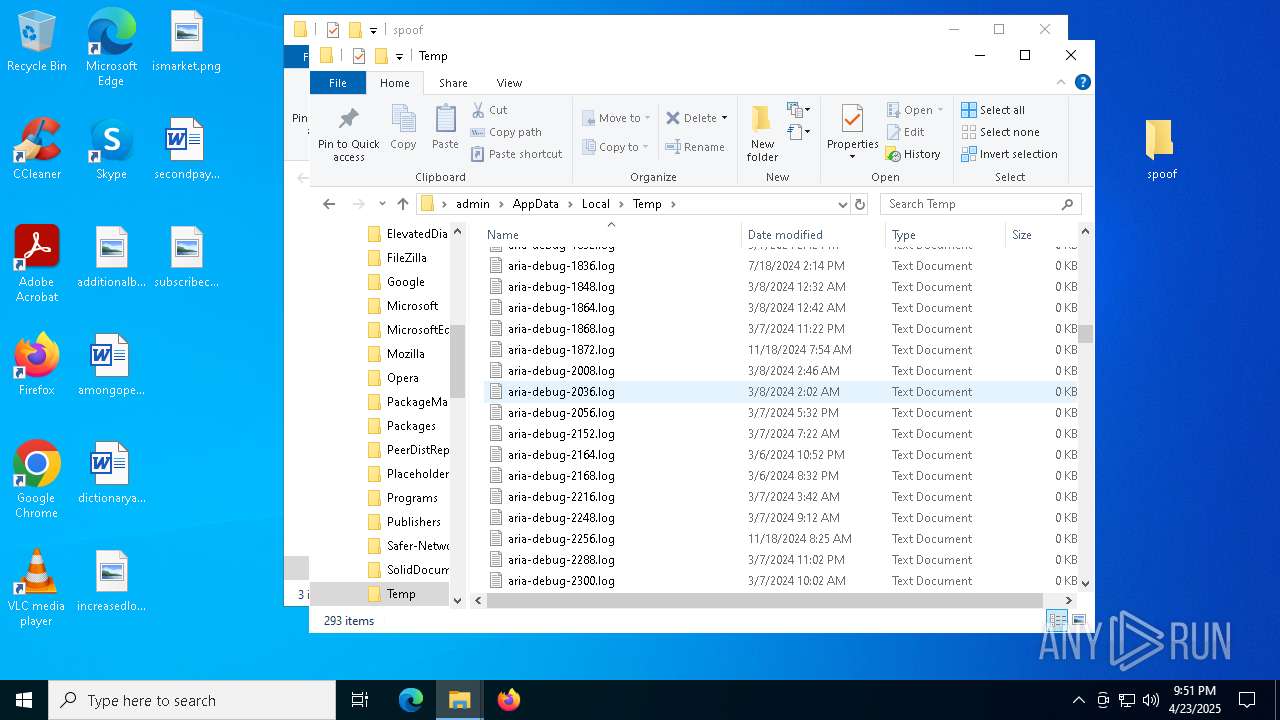
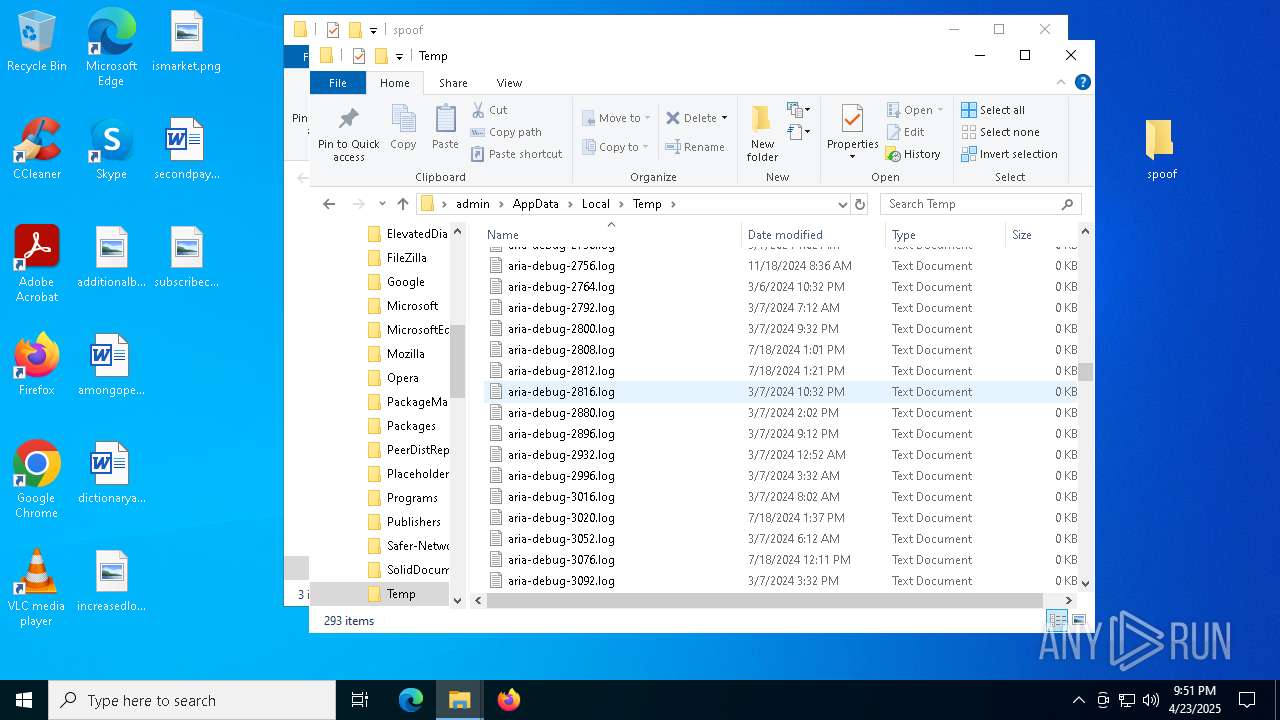
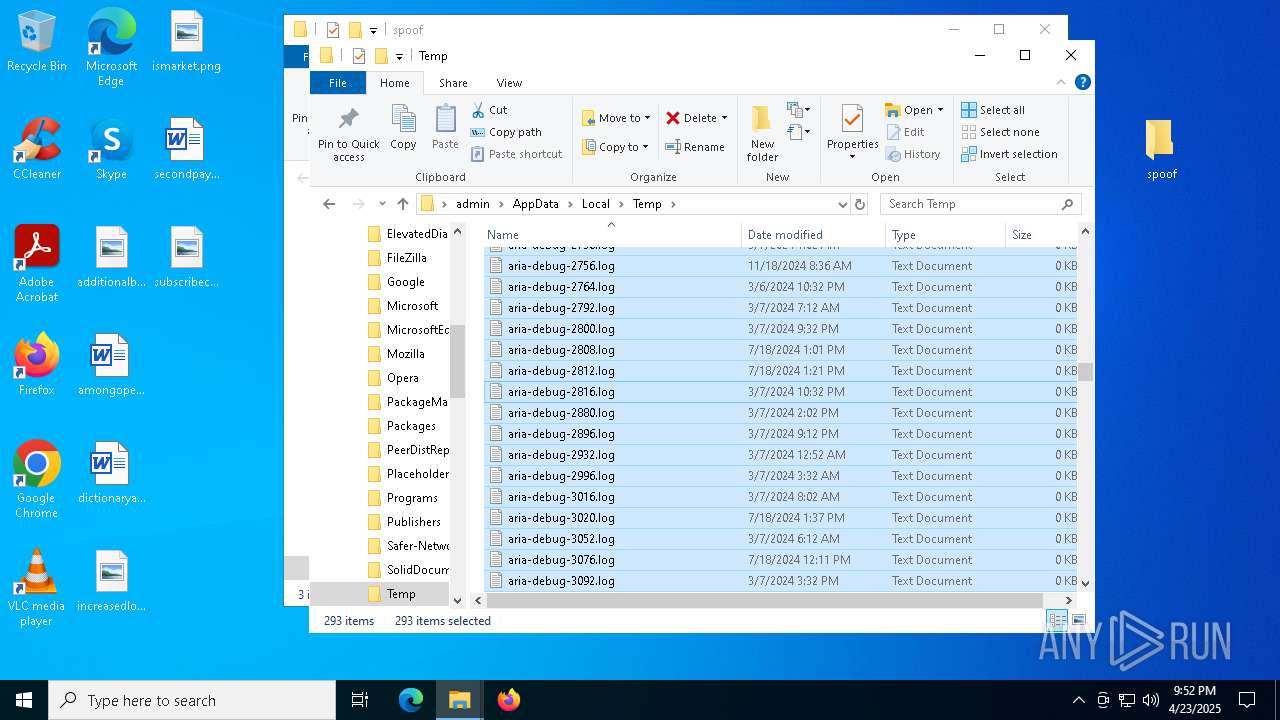
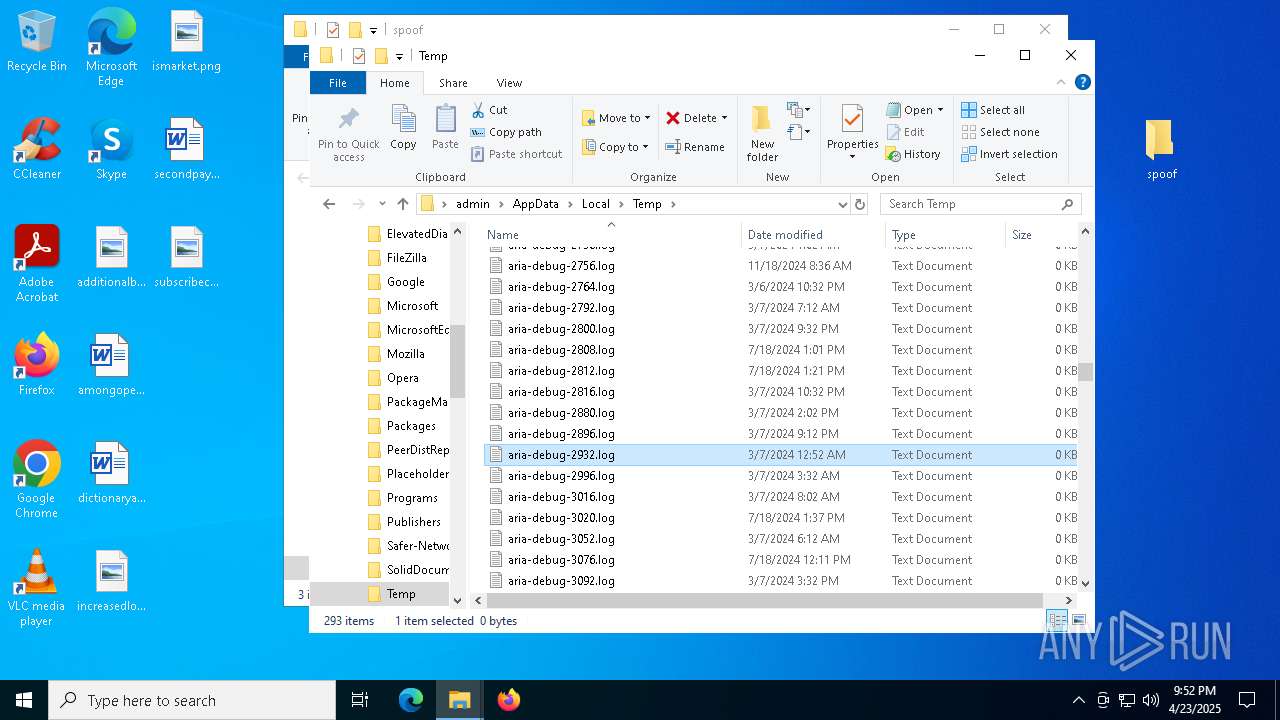
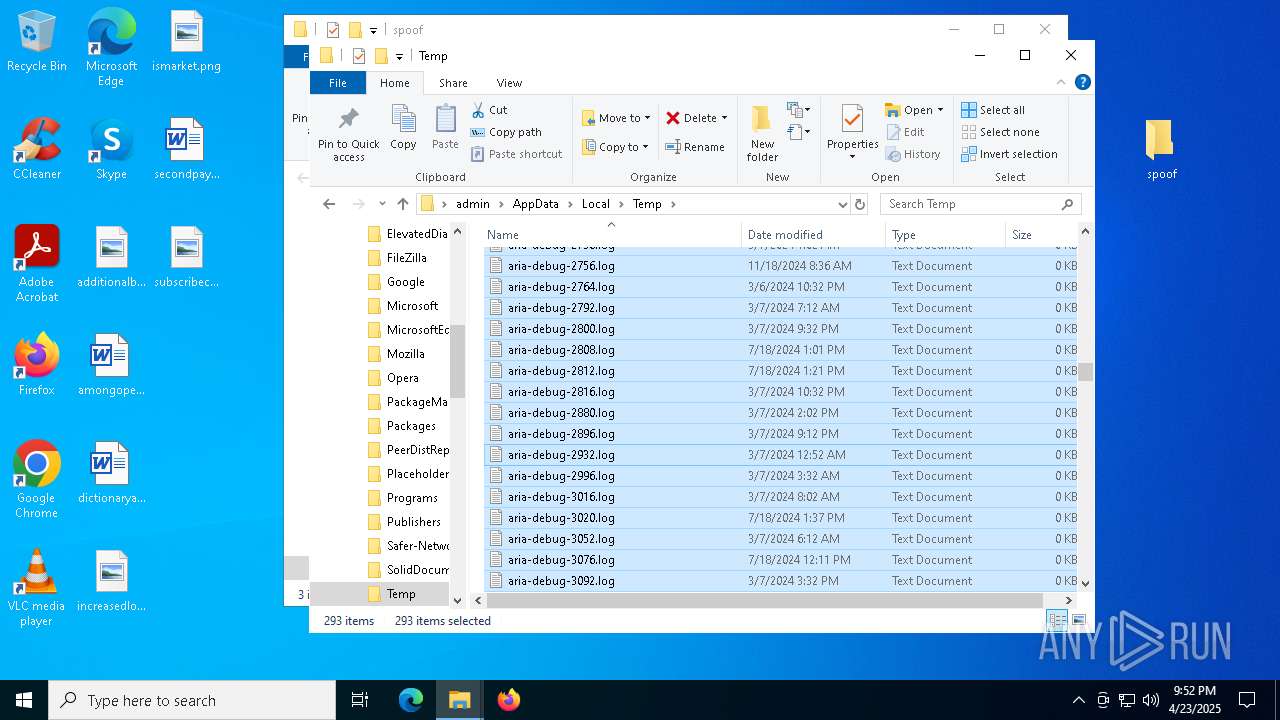
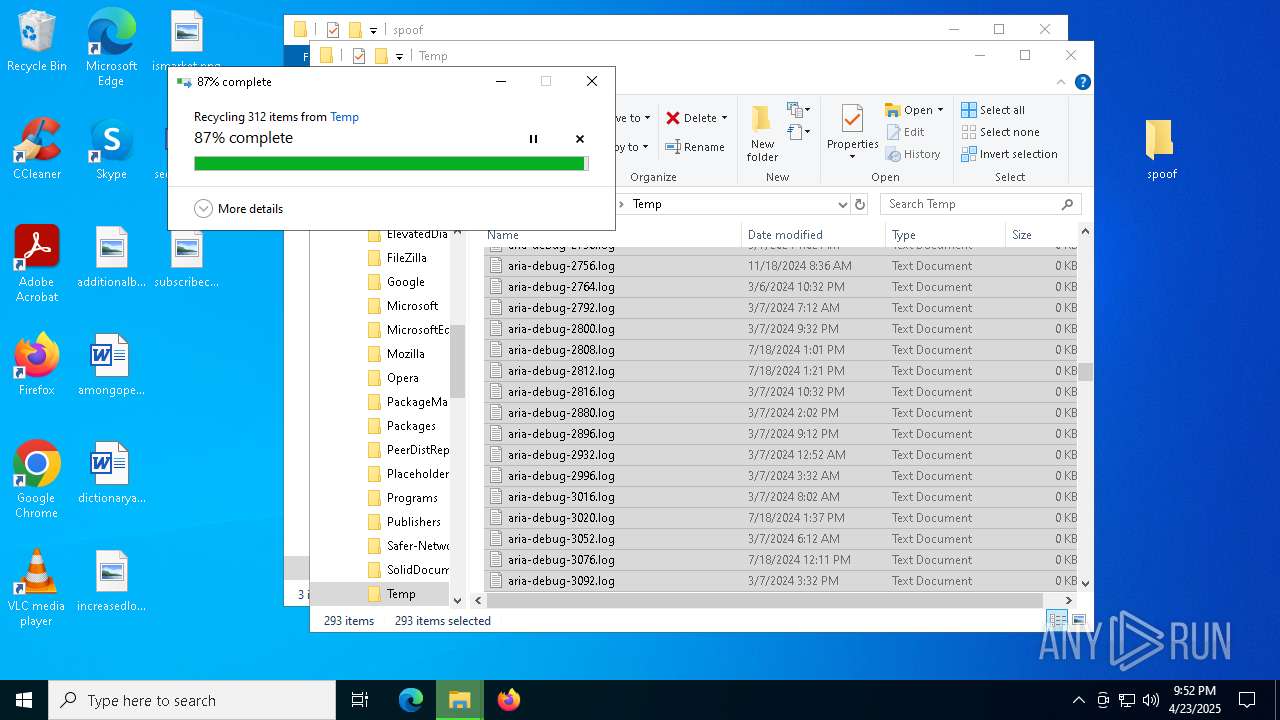
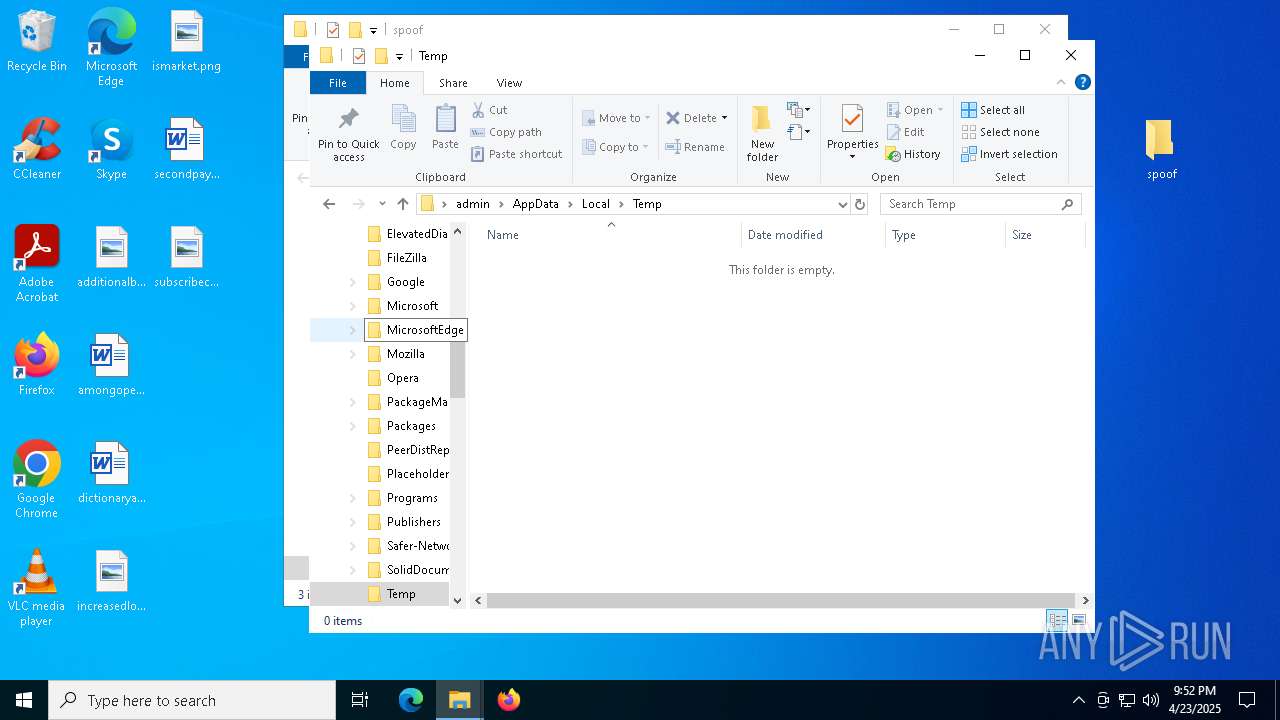
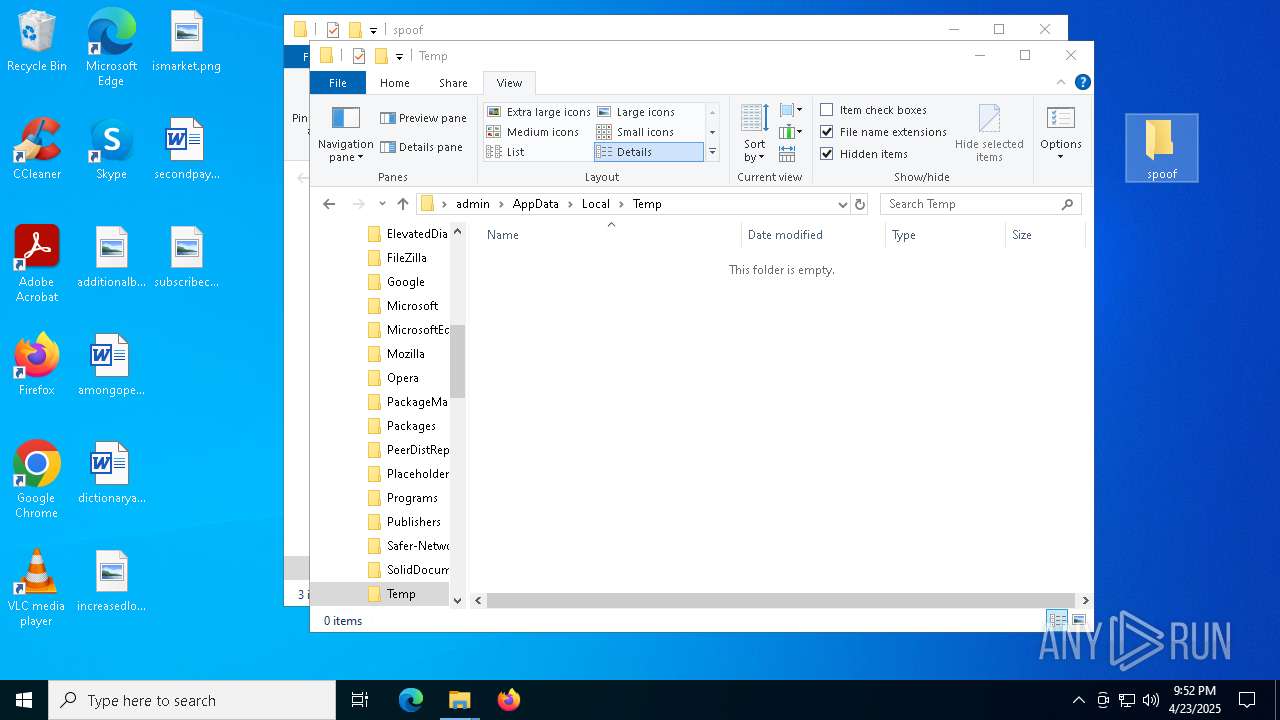
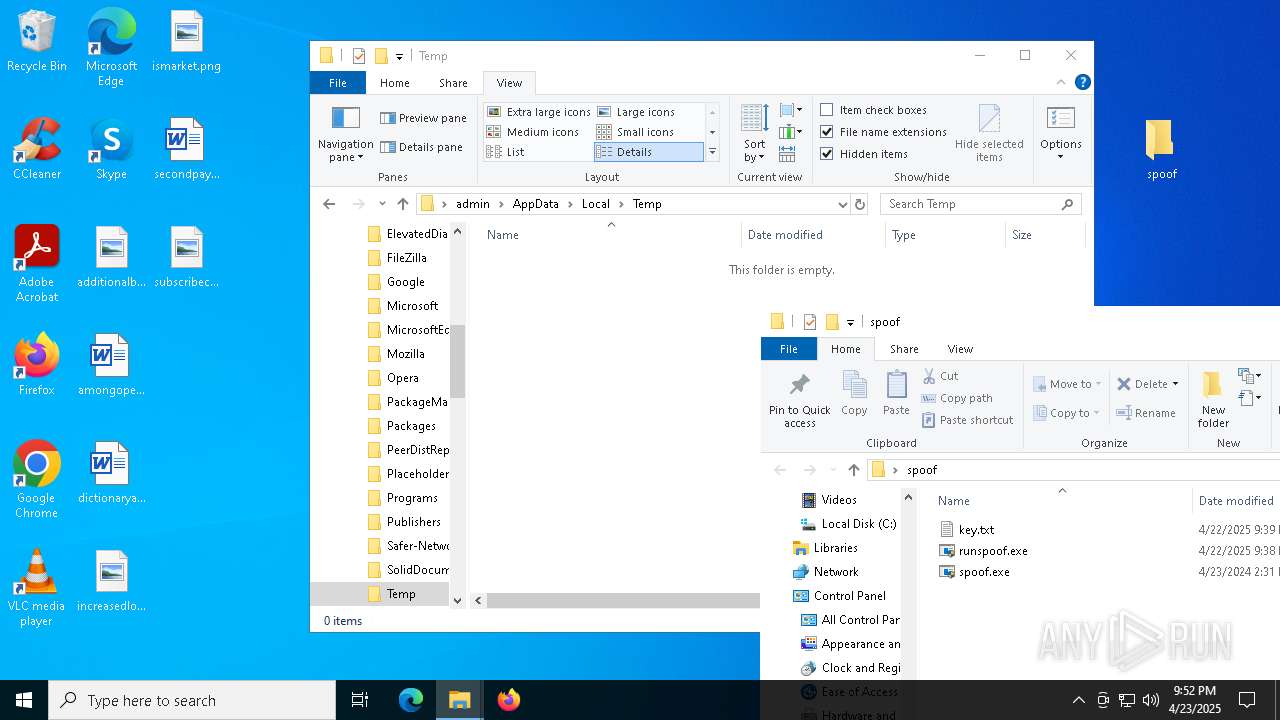
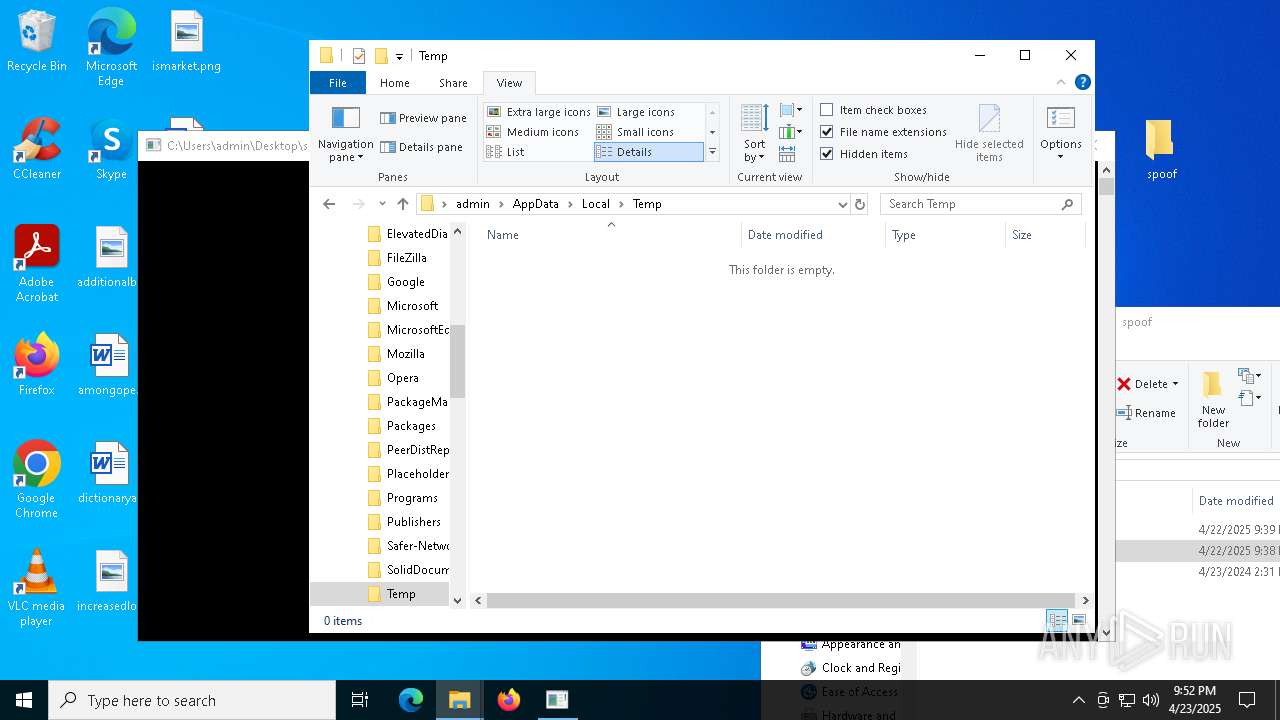
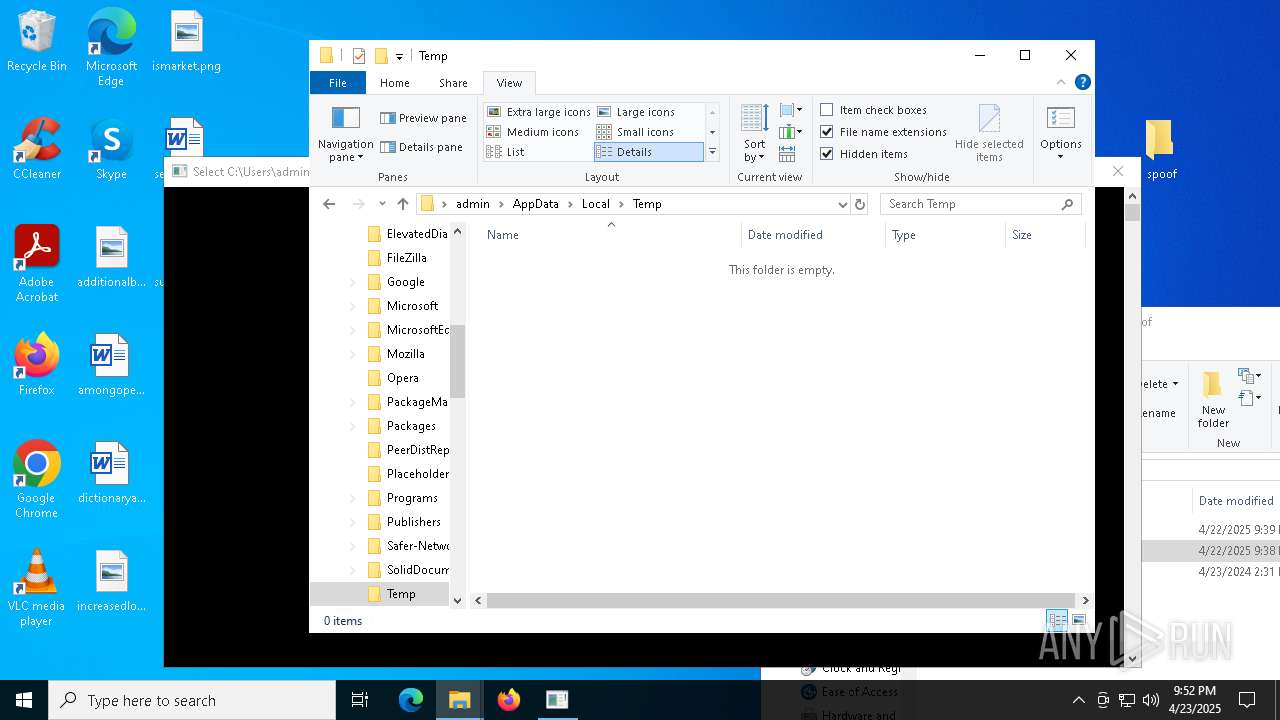
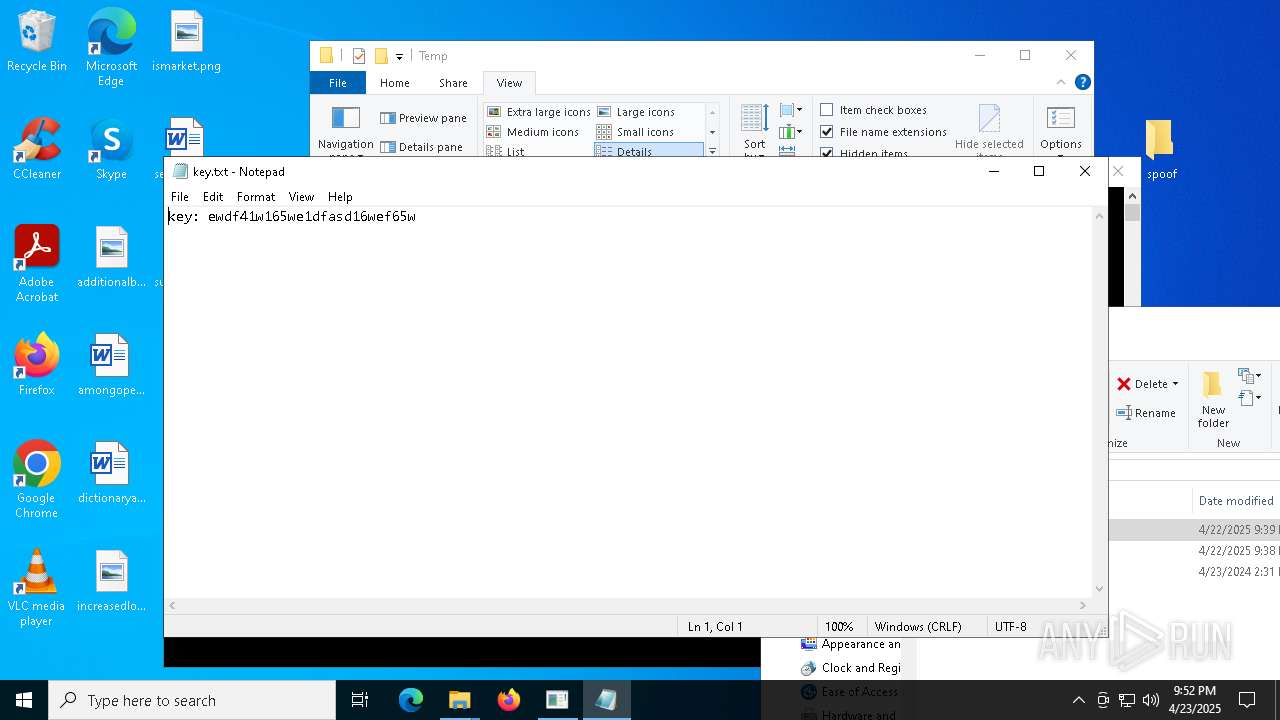
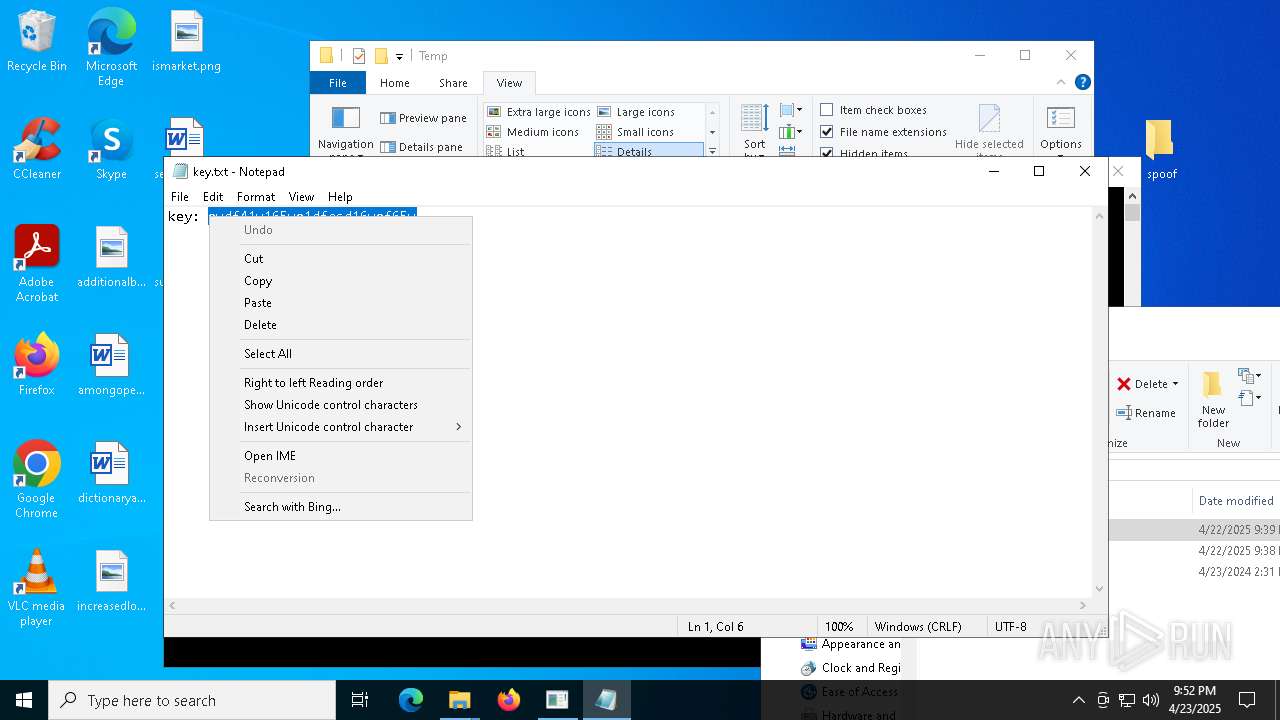
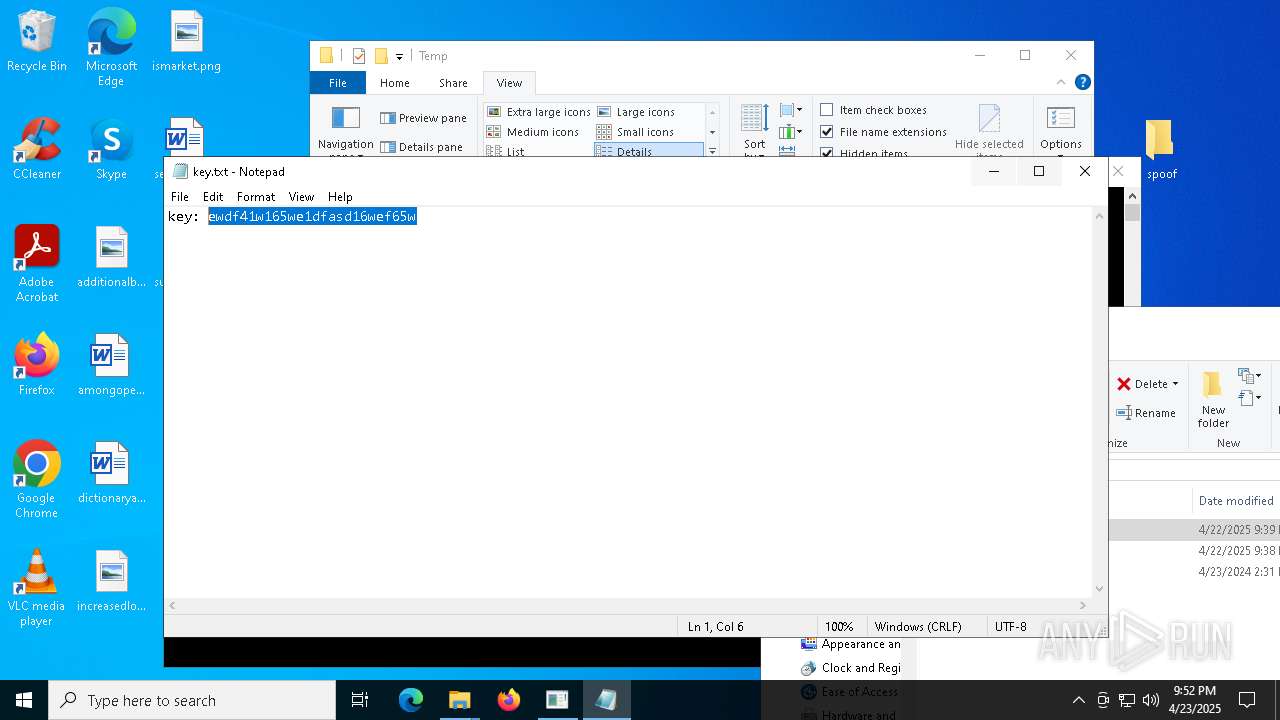
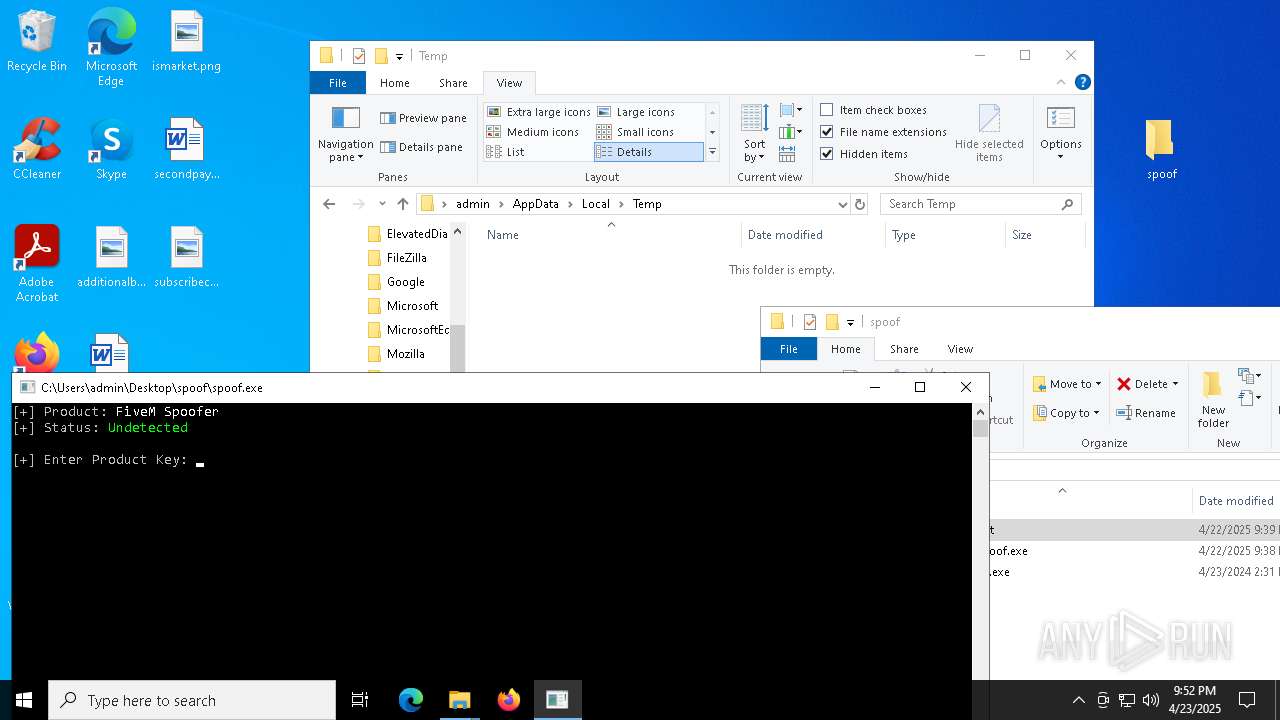
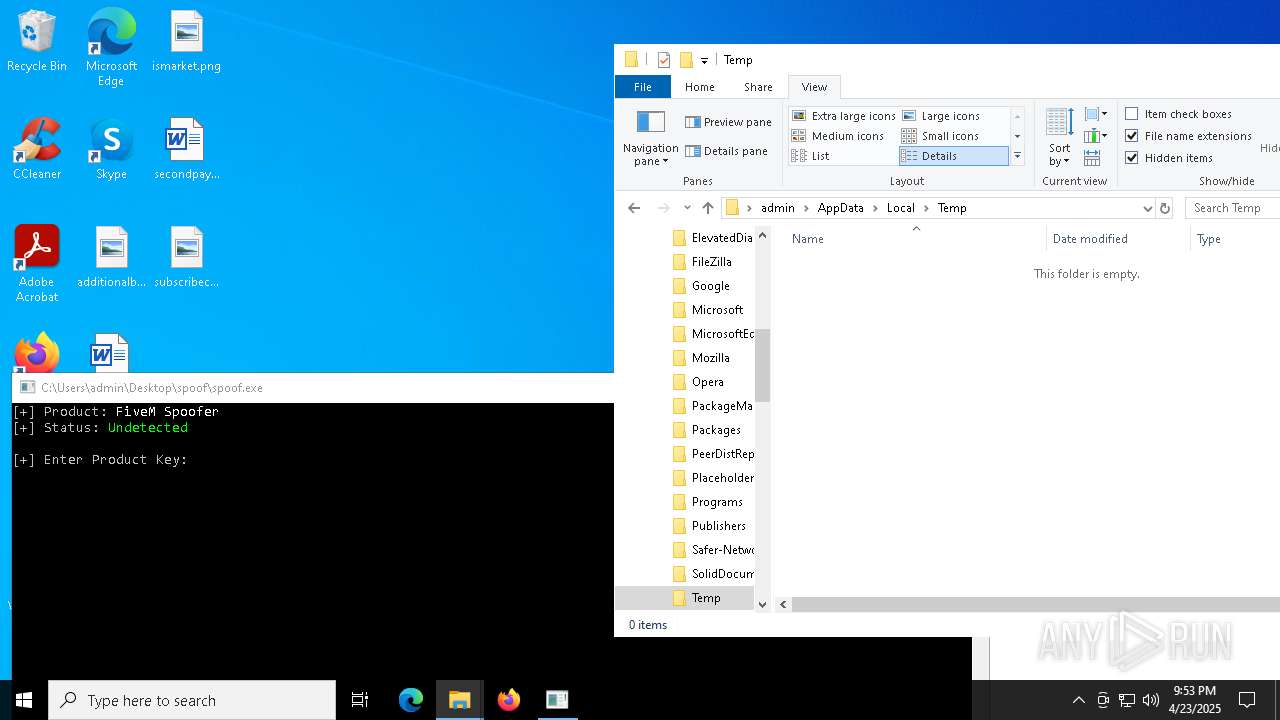
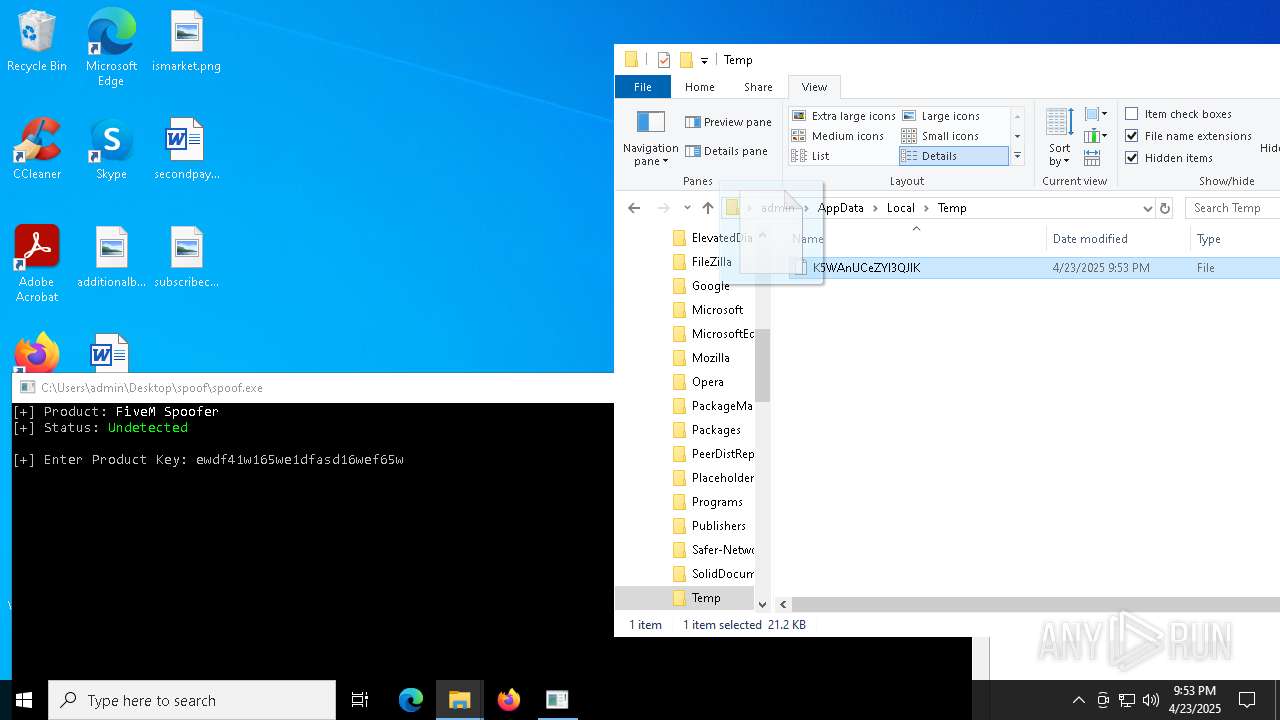
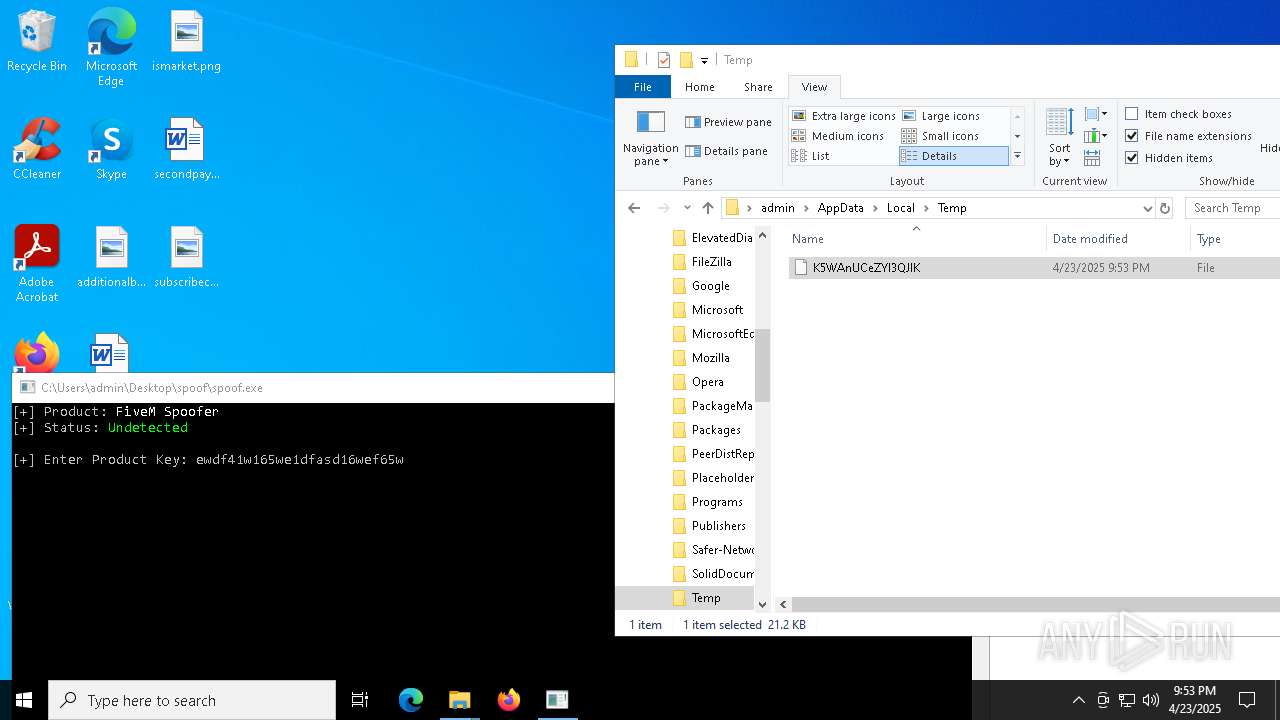
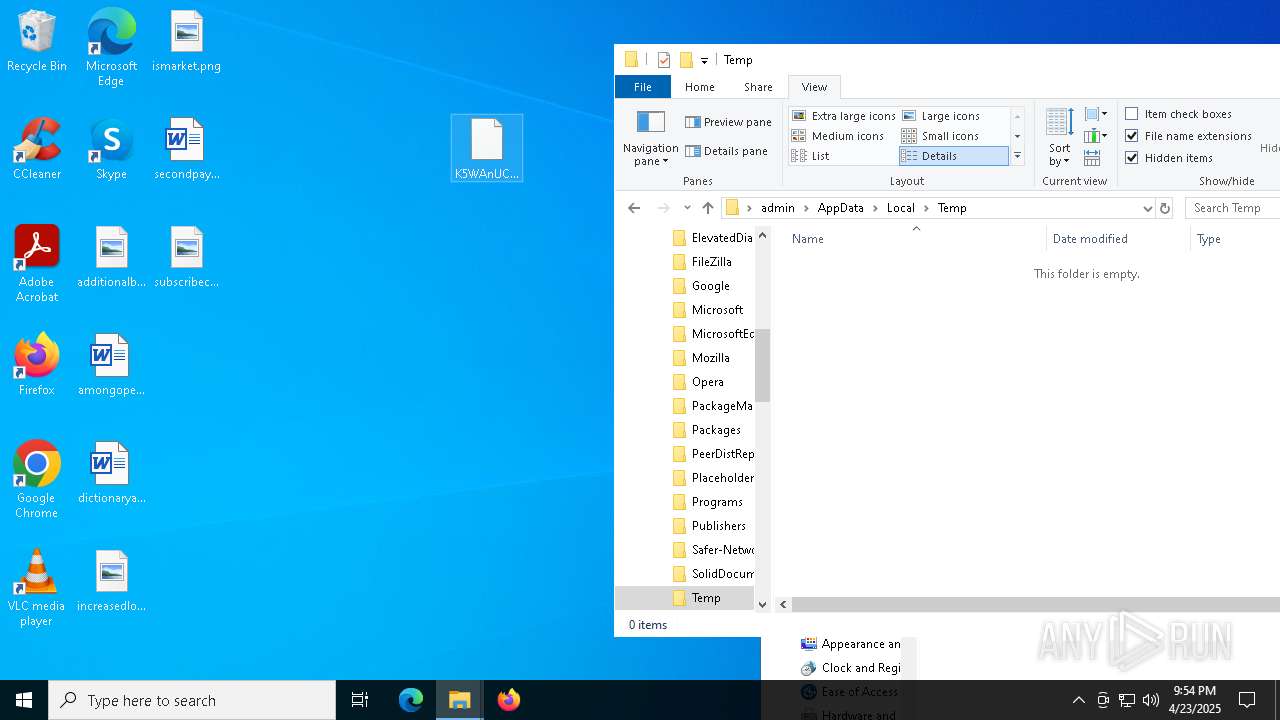
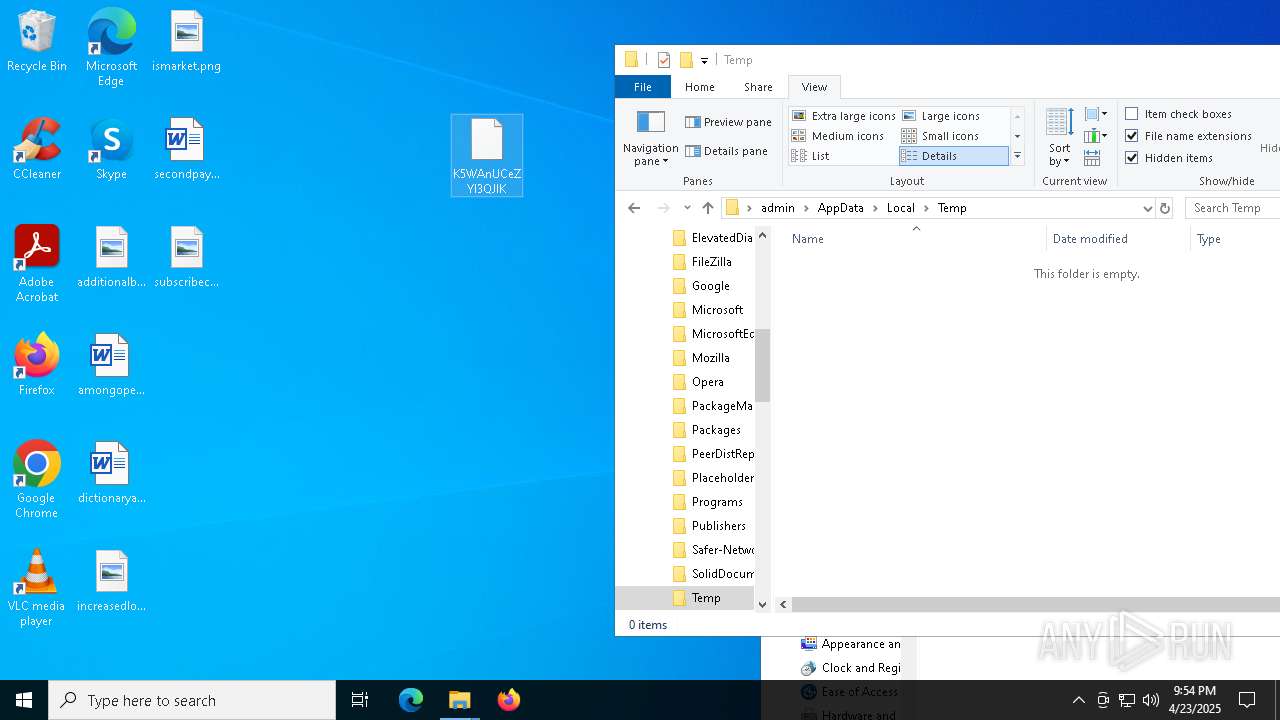
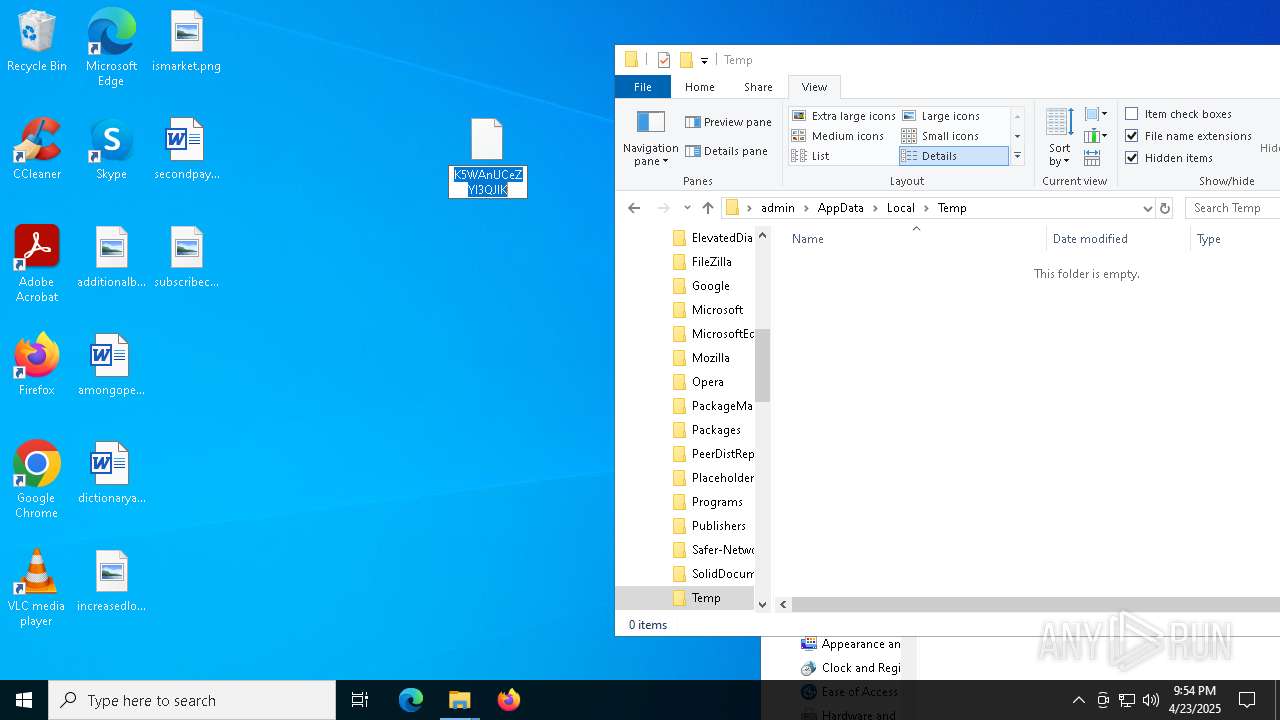
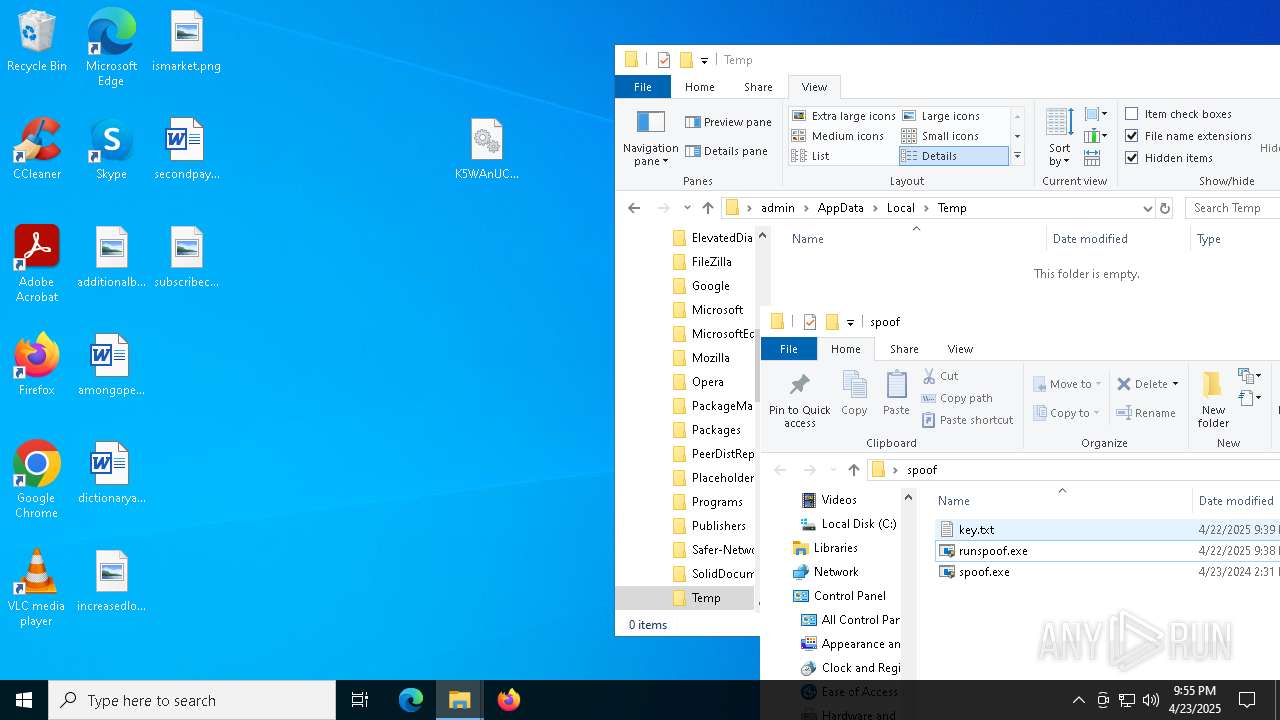
Create files in a temporary directory
- spoof.exe (PID: 8080)
- spoof.exe (PID: 3156)
The sample compiled with english language support
- spoof.exe (PID: 3156)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
192
Monitored processes
56
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1088 | C:\WINDOWS\System32\rundll32.exe shell32.dll,SHCreateLocalServerRunDll {c82192ee-6cb5-4bc0-9ef0-fb818773790a} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1196 | "C:\Program Files\Mozilla Firefox\firefox.exe" https://limewire.com/d/ZPyoJ#mqh5SHuGdU | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 1568 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=4960 -childID 4 -isForBrowser -prefsHandle 5092 -prefMapHandle 4852 -prefsLen 31198 -prefMapSize 244583 -jsInitHandle 1432 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {039cc83e-1801-465b-98a3-ba72e6c4fe03} 6808 "\\.\pipe\gecko-crash-server-pipe.6808" 2043ffe94d0 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 2320 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | runspoof.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2644 | chcp 65001 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3096 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=4200 -childID 2 -isForBrowser -prefsHandle 4232 -prefMapHandle 4228 -prefsLen 36588 -prefMapSize 244583 -jsInitHandle 1432 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {b0f97f05-cdf4-490e-b803-402d5f7d1607} 6808 "\\.\pipe\gecko-crash-server-pipe.6808" 2043ffe7310 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
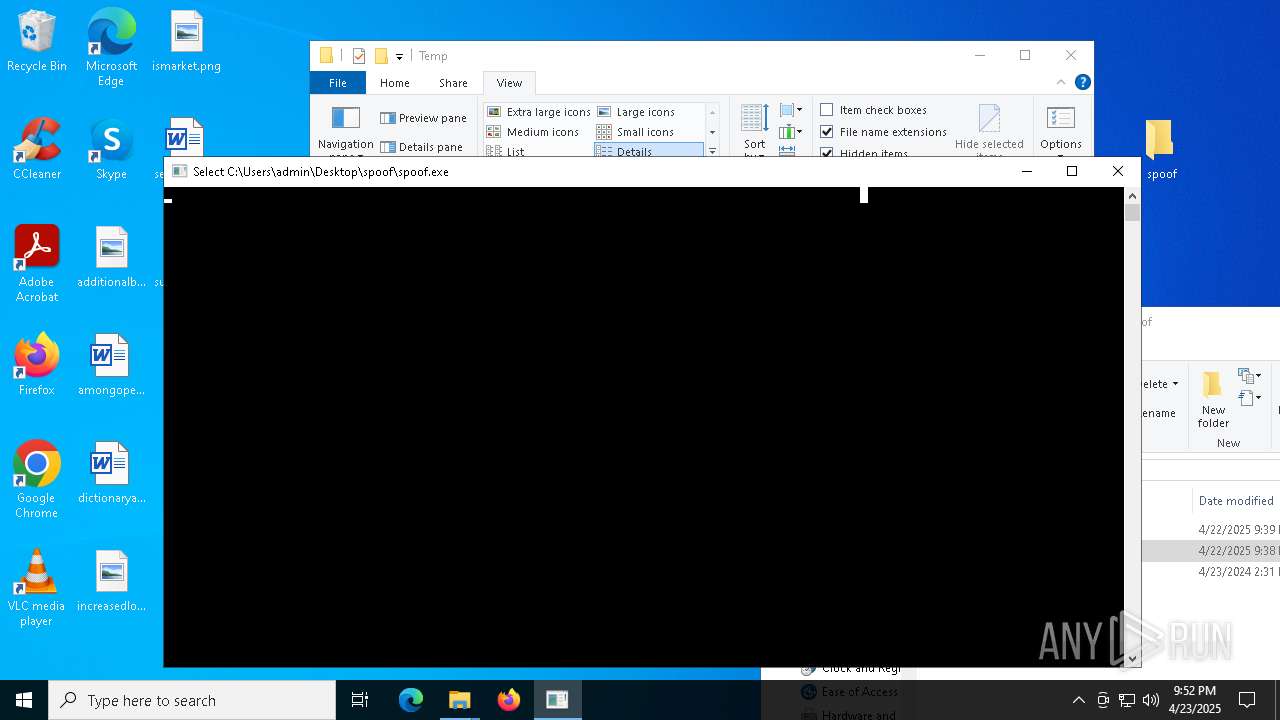
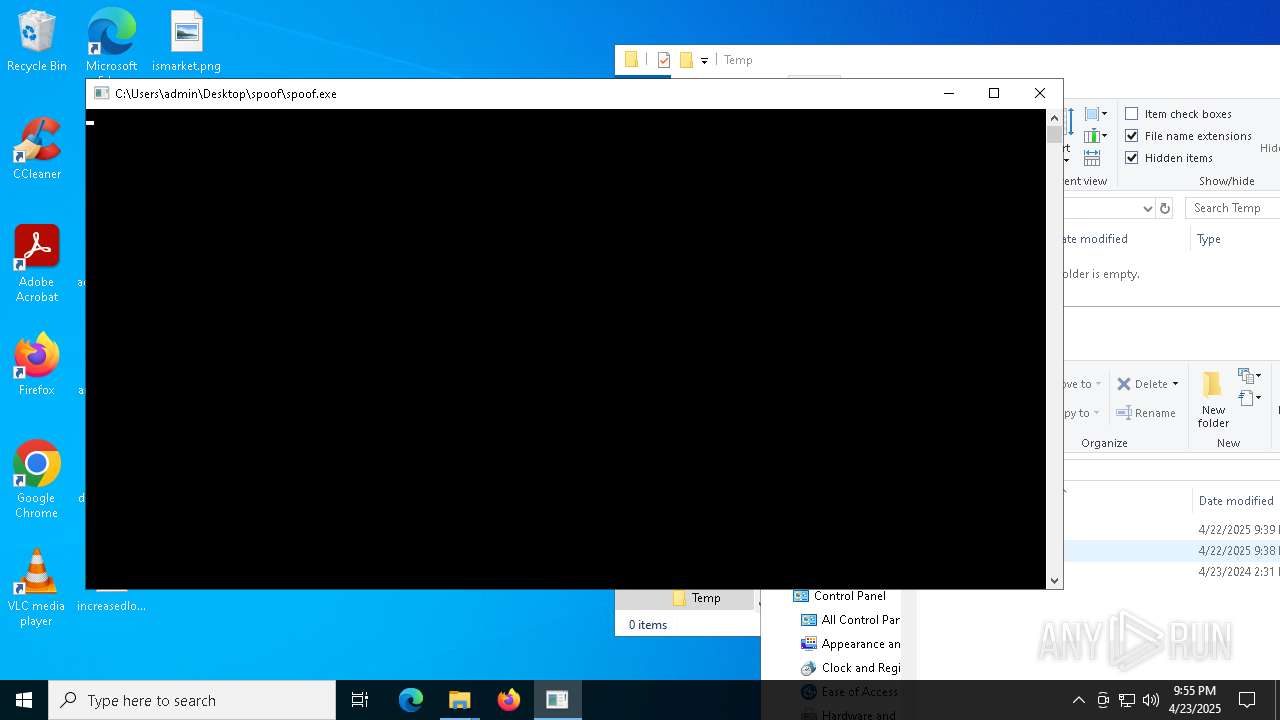
| 3156 | "C:\Users\admin\Desktop\spoof\spoof.exe" | C:\Users\admin\Desktop\spoof\spoof.exe | runspoof.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3272 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=1700 -parentBuildID 20240213221259 -prefsHandle 1736 -prefMapHandle 1716 -prefsLen 31031 -prefMapSize 244583 -appDir "C:\Program Files\Mozilla Firefox\browser" - {4fa34728-c158-4bec-8cab-7405d0bffeda} 1196 "\\.\pipe\gecko-crash-server-pipe.1196" 1ef958f1410 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 1 Version: 123.0 Modules
| |||||||||||||||
| 3396 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | spoof.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3676 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | runspoof.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
36 995
Read events
36 959
Write events
34
Delete events
2
Modification events
| (PID) Process: | (1196) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (4188) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\75g865.rar | |||
| (PID) Process: | (4188) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4188) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4188) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (4188) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (4188) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (4188) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (4188) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (4188) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
Executable files
4
Suspicious files
281
Text files
40
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1196 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 1196 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cookies.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 1196 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\AlternateServices.bin | binary | |
MD5:5F3CB82849C1701C6CF801D9E039756D | SHA256:0AA6127454EDF8DCF7ED6B9A0A5D6A443FC8F51271AB9B2624066A79267F8CFC | |||
| 1196 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\urlCache-current.bin | binary | |
MD5:297E88D7CEB26E549254EC875649F4EB | SHA256:8B75D4FB1845BAA06122888D11F6B65E6A36B140C54A72CC13DF390FD7C95702 | |||
| 1196 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3561288849sdhlie.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 1196 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 1196 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 1196 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 1196 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 1196 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\SiteSecurityServiceState.bin | binary | |
MD5:D35E9FA9AB6A254CB504D253D2D8DDF7 | SHA256:AA07E227121171B851F7202696A0C00ACB3390A7B8FC222EC81D44FAAD5B9F2C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
64
TCP/UDP connections
150
DNS requests
186
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.19.11.105:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.19.11.105:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1196 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
1196 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
1196 | firefox.exe | POST | 200 | 2.16.168.113:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
1196 | firefox.exe | POST | 200 | 2.16.168.113:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
1196 | firefox.exe | POST | 200 | 172.217.16.131:80 | http://o.pki.goog/s/wr3/cgo | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 2.19.11.105:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.19.11.105:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
— | — | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
2104 | svchost.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
5496 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1196 | firefox.exe | 34.36.137.203:443 | contile.services.mozilla.com | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
limewire.com |
| unknown |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
spocs.getpocket.com |
| whitelisted |
content-signature-2.cdn.mozilla.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare R2 Storage (r2 .cloudflarestorage .com) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare R2 Storage (r2 .cloudflarestorage .com) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare R2 Storage (r2 .cloudflarestorage .com) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |