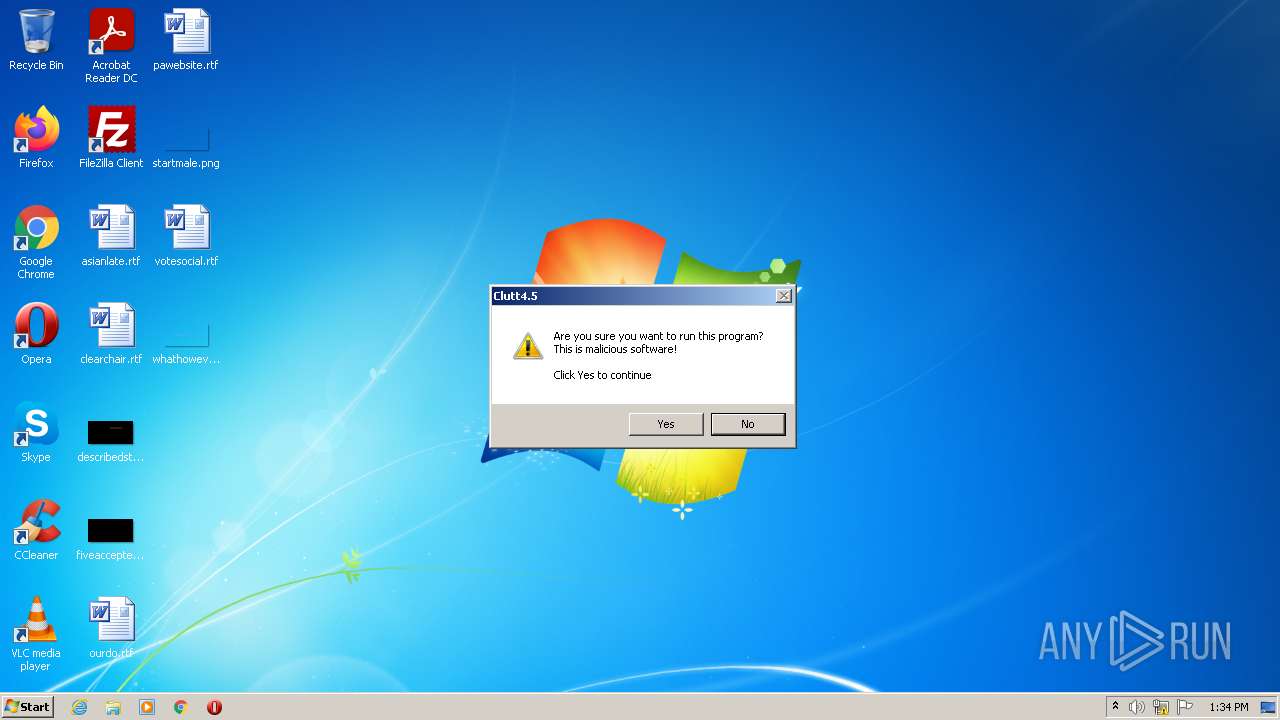
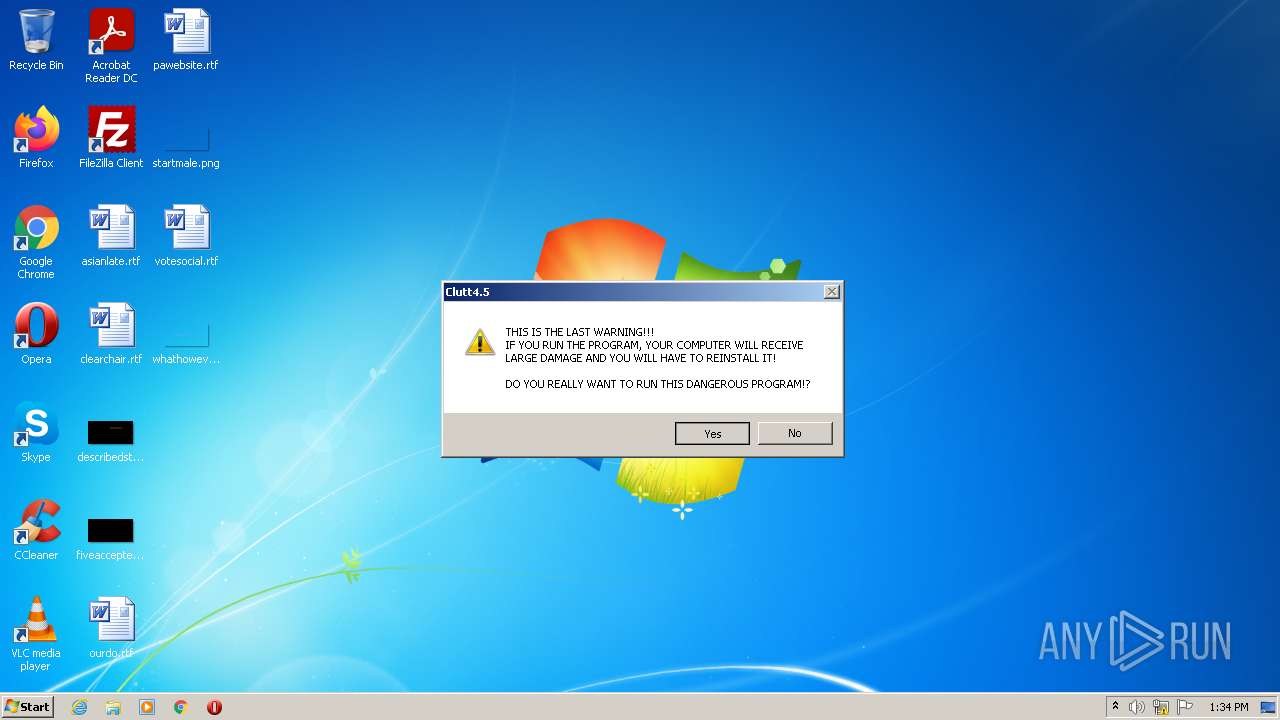
| File name: | Clutt4.5.exe |
| Full analysis: | https://app.any.run/tasks/4e5cd50b-256d-409d-b348-102c51889ecf |
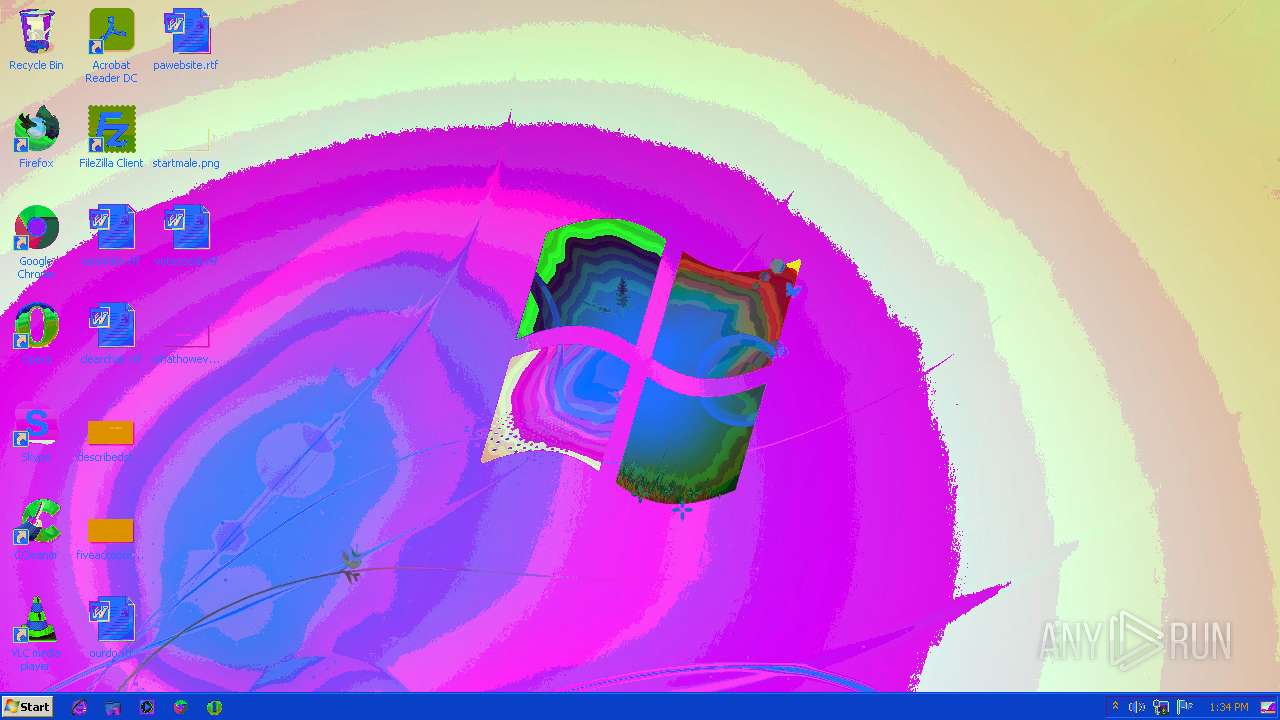
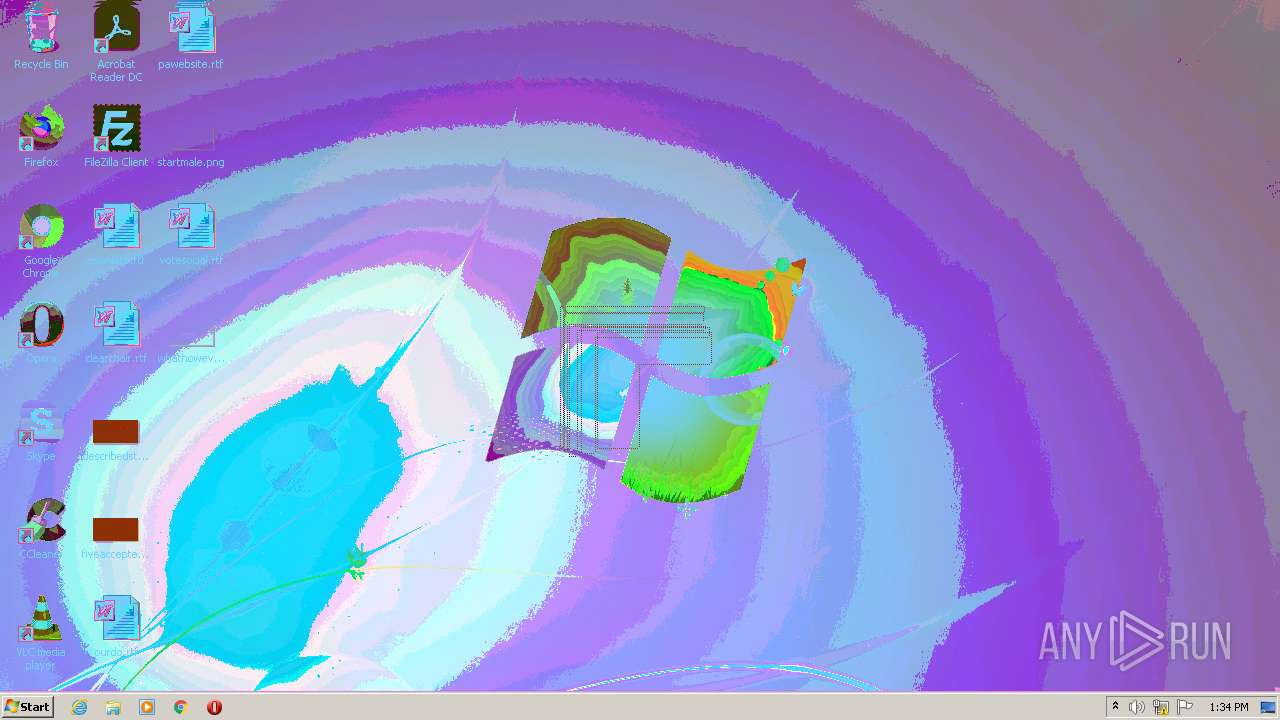
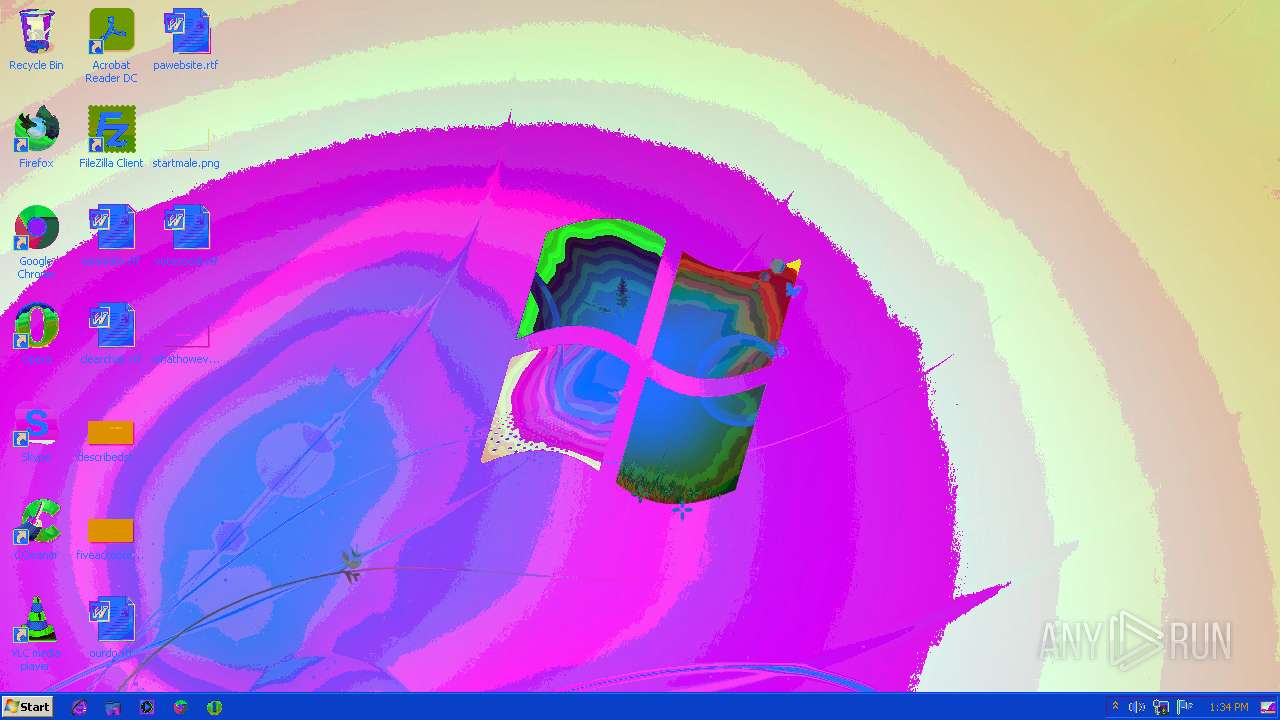
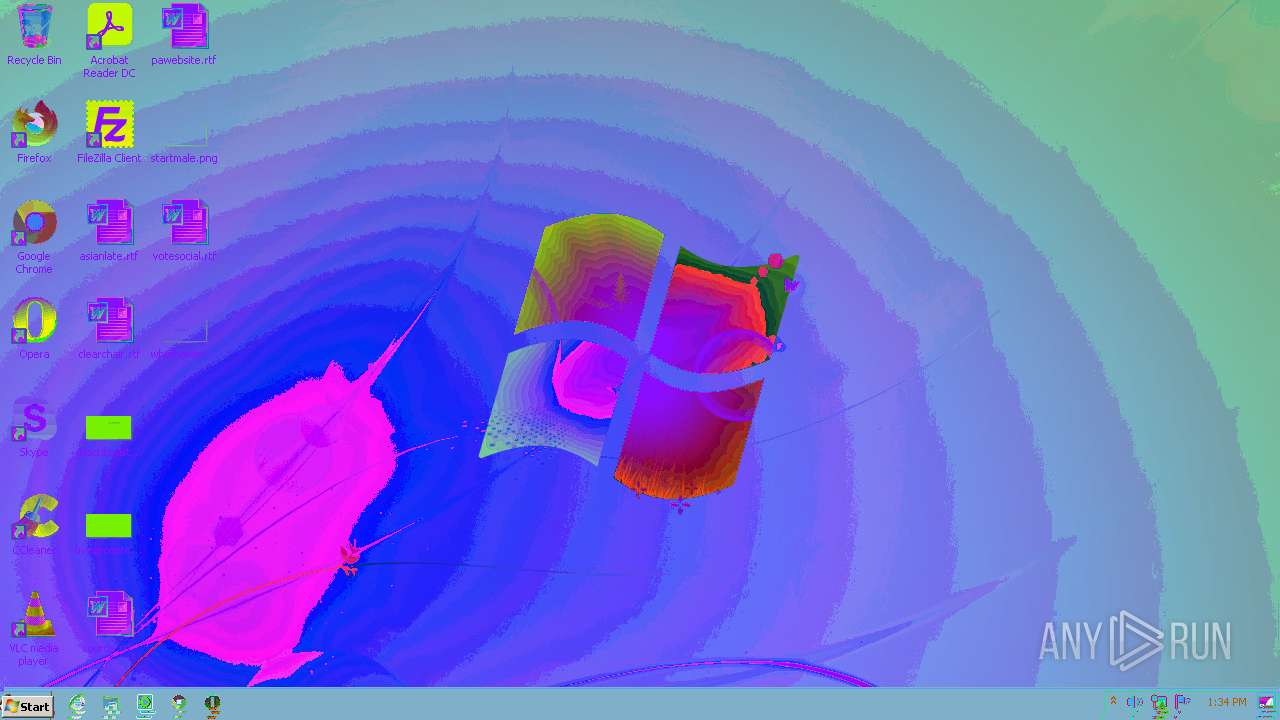
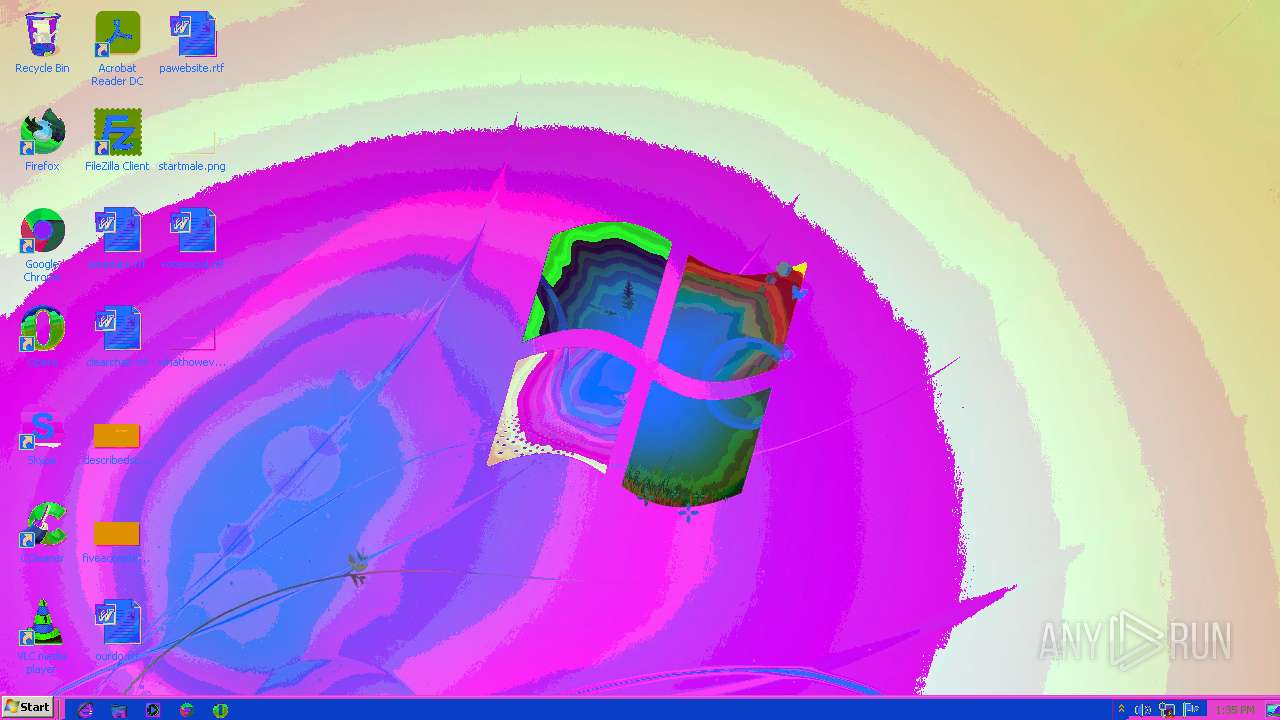
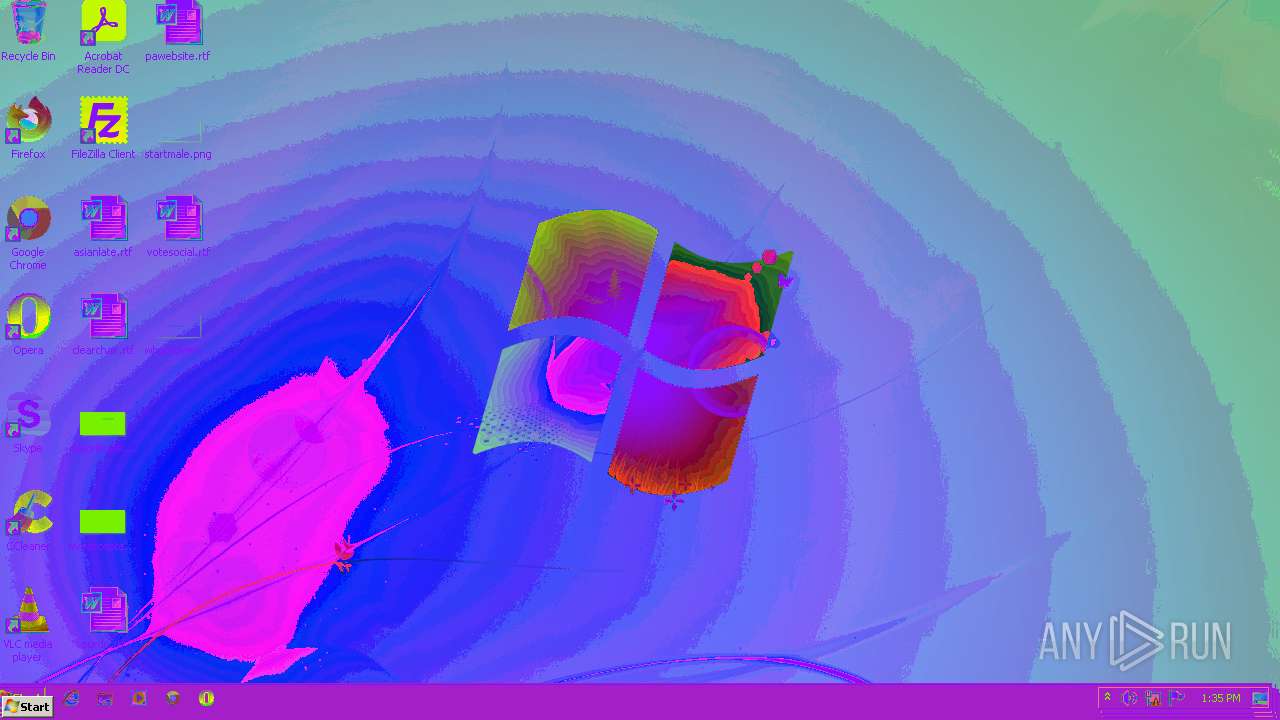
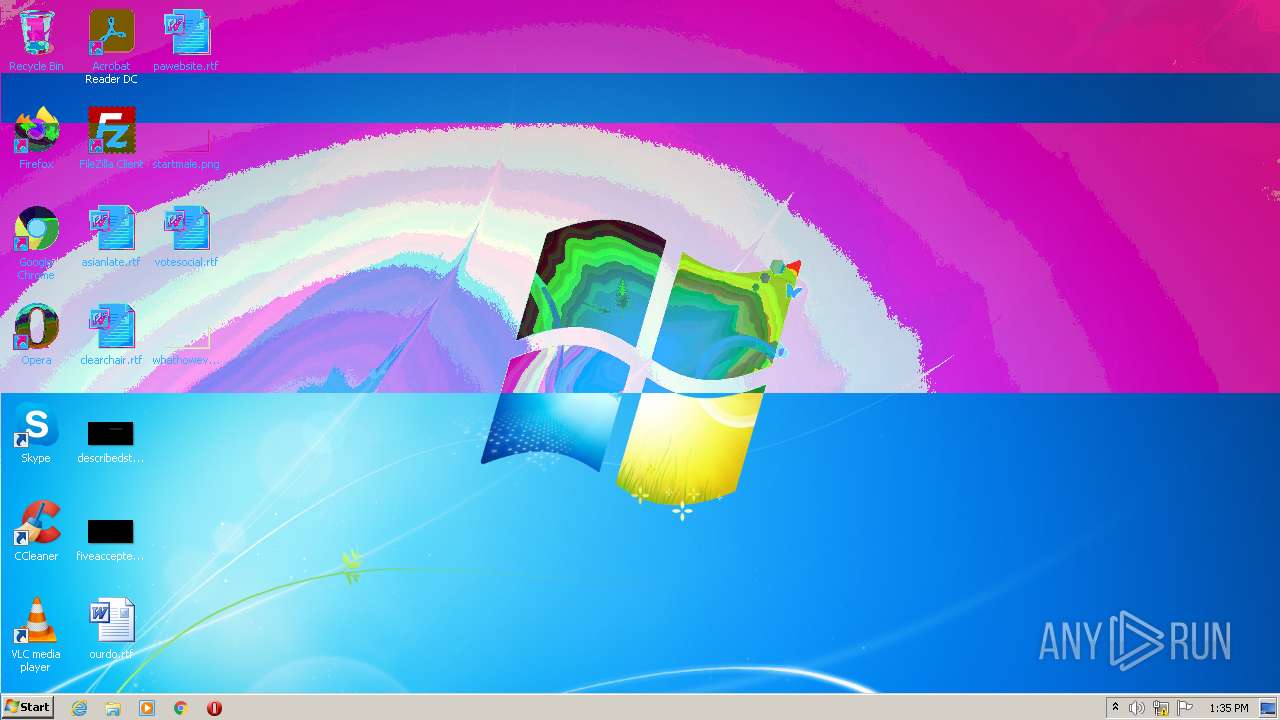
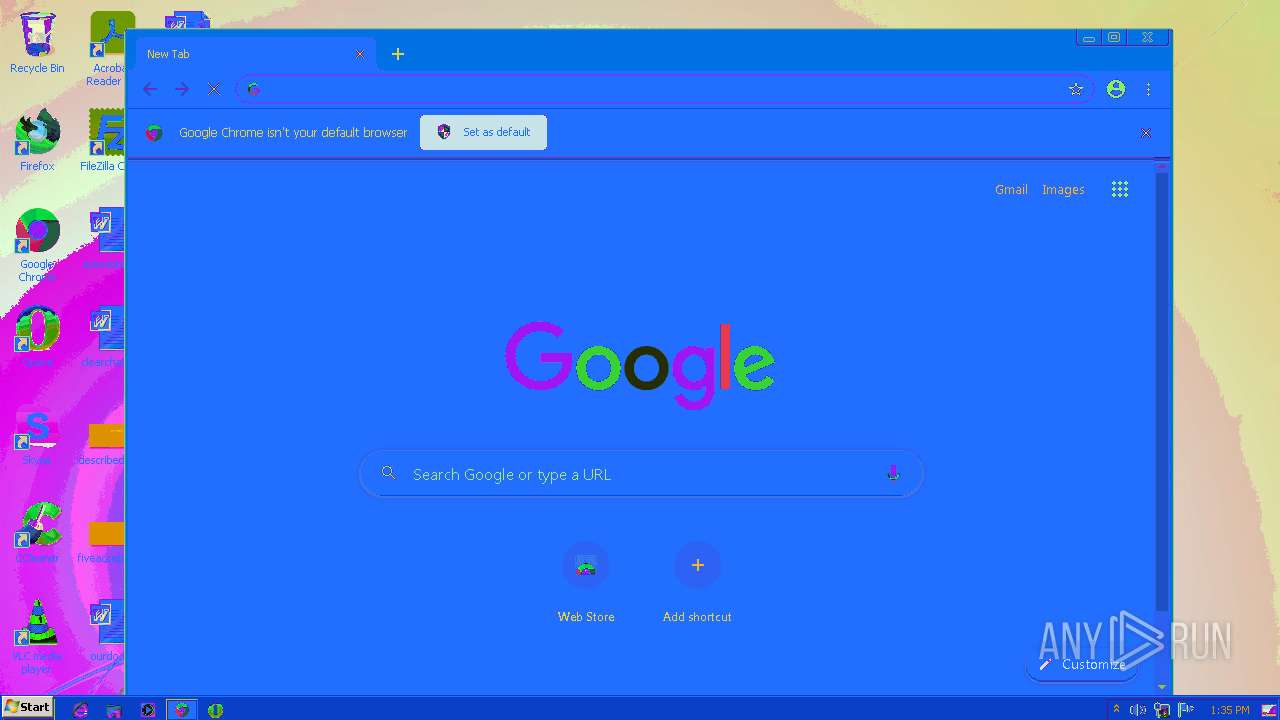
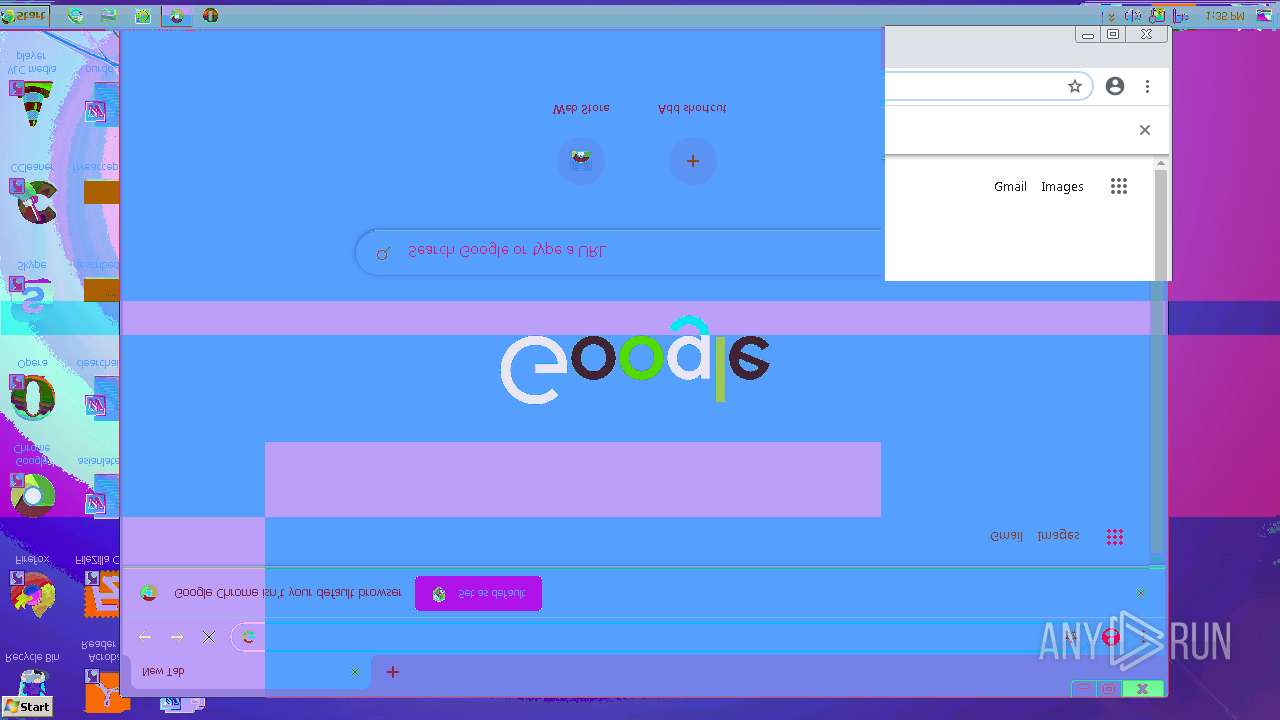
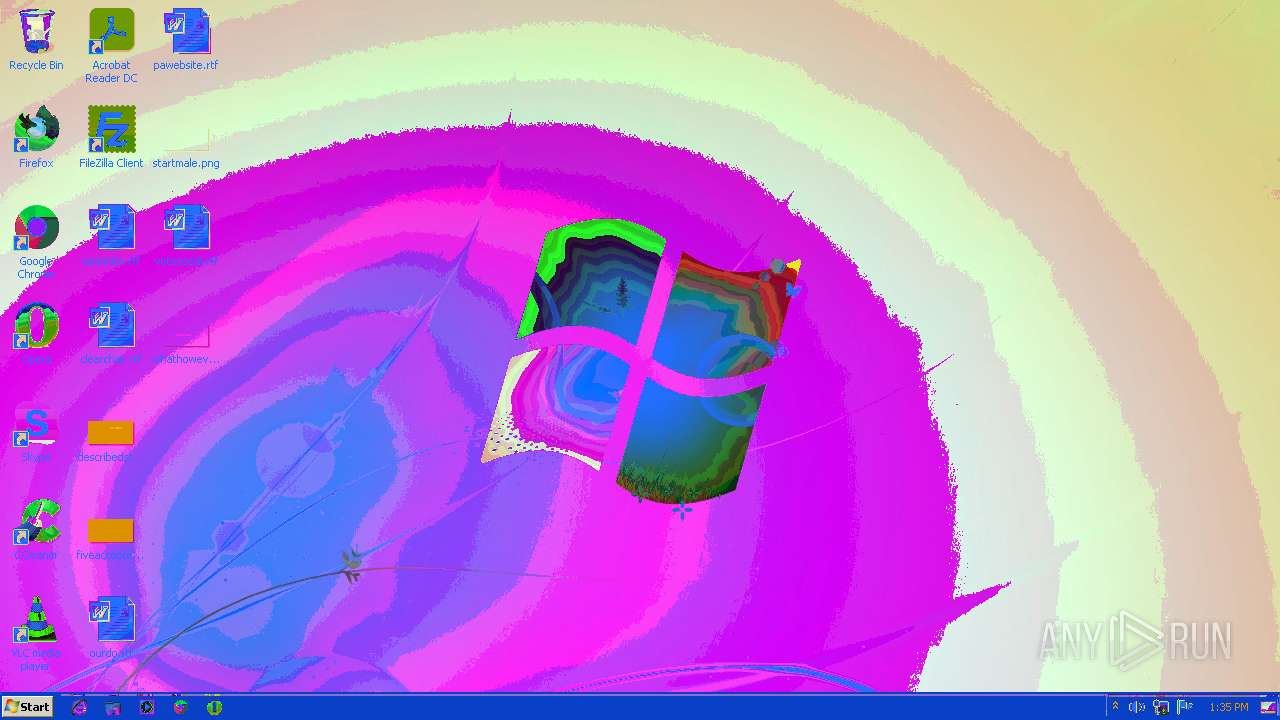
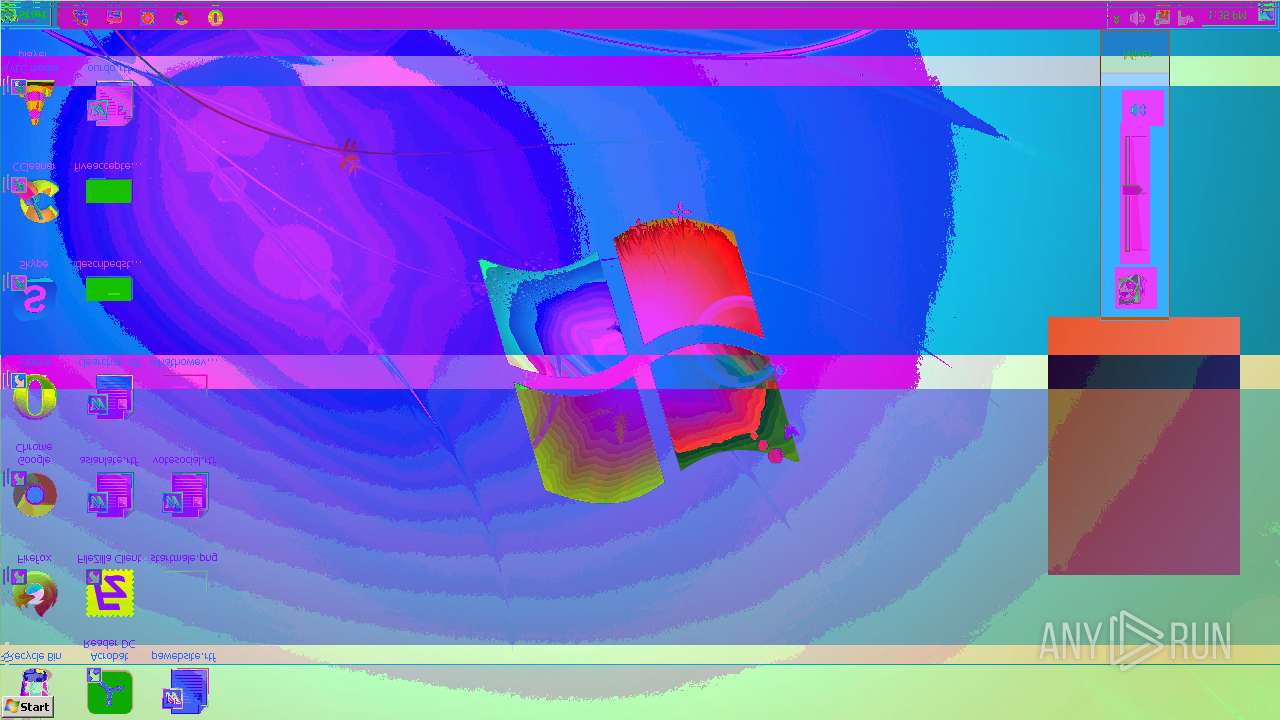
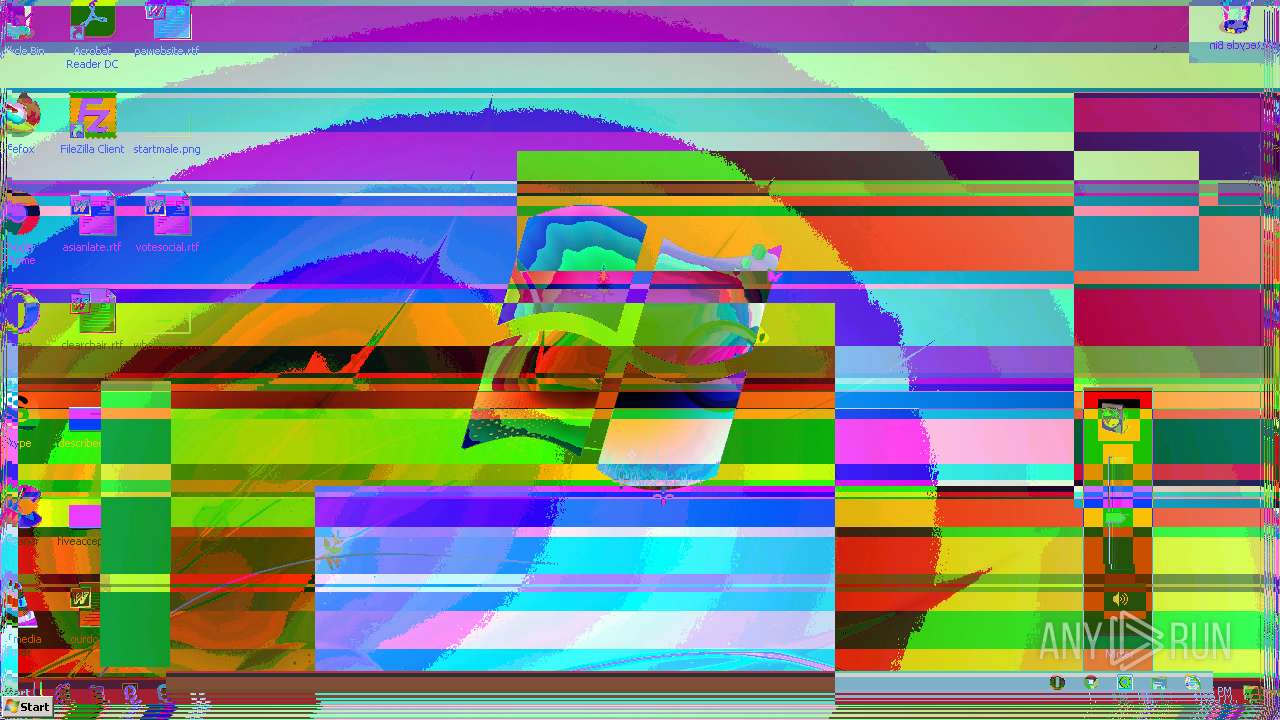
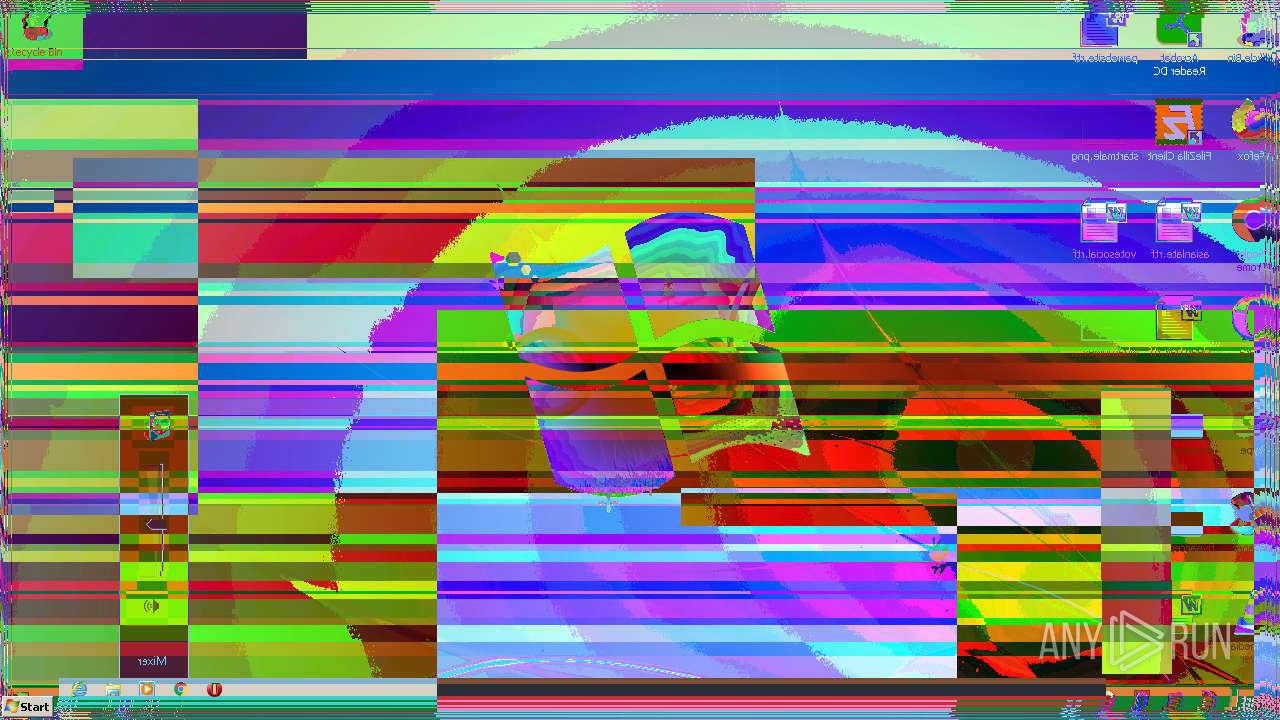
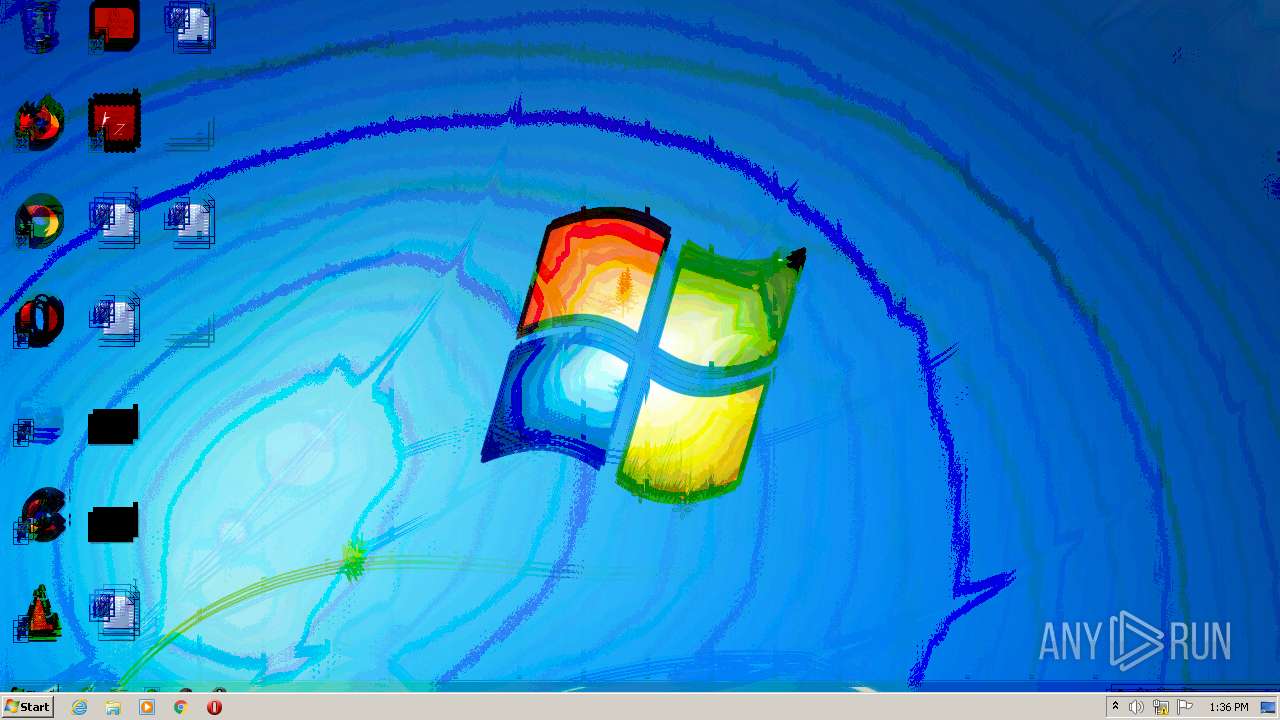
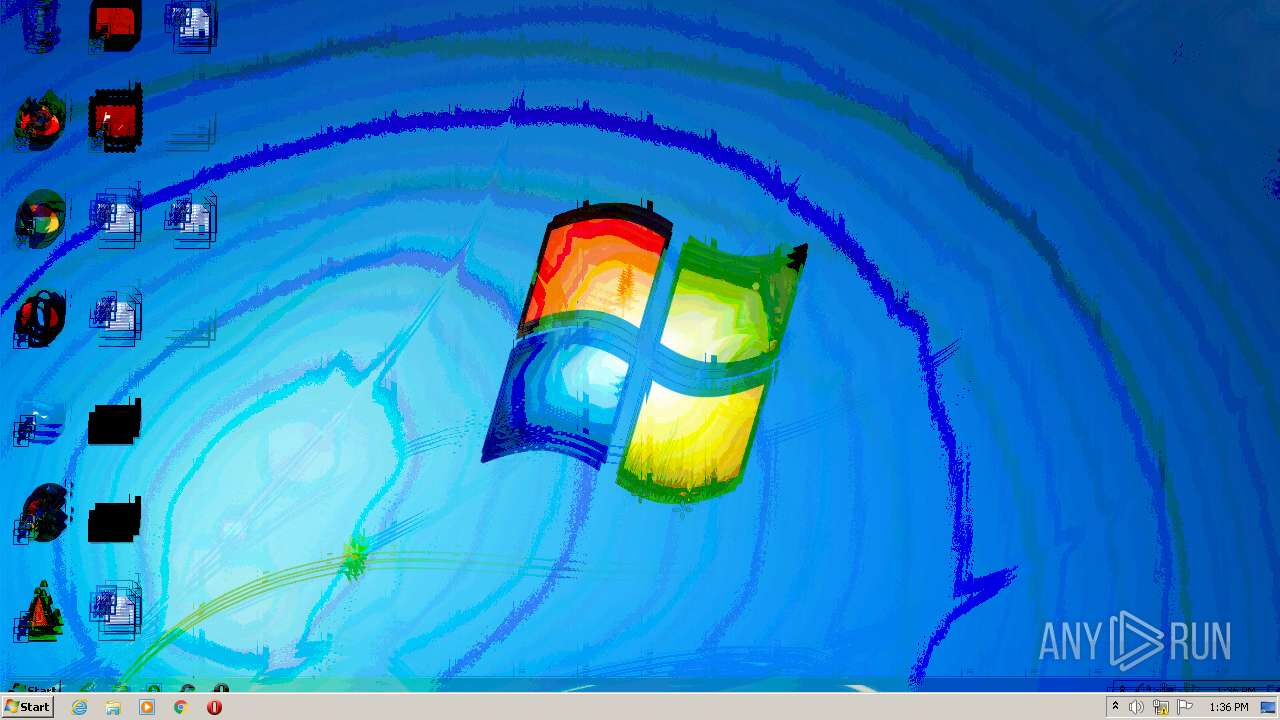
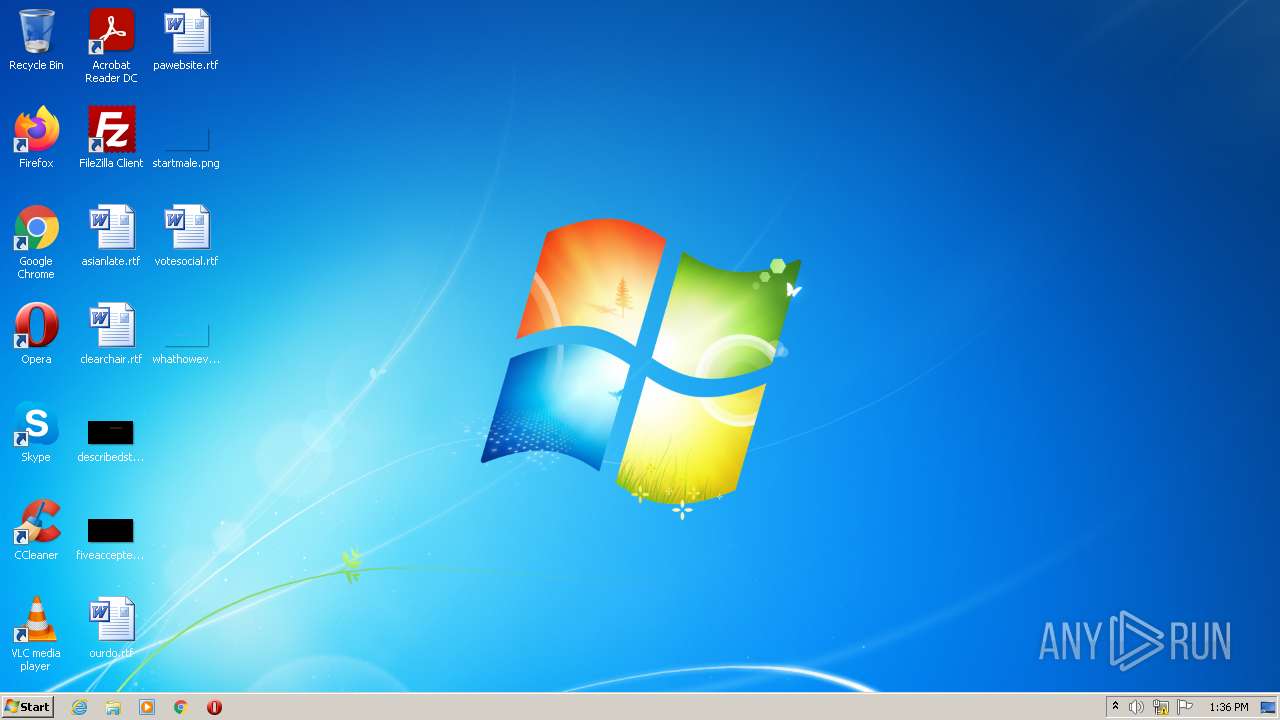
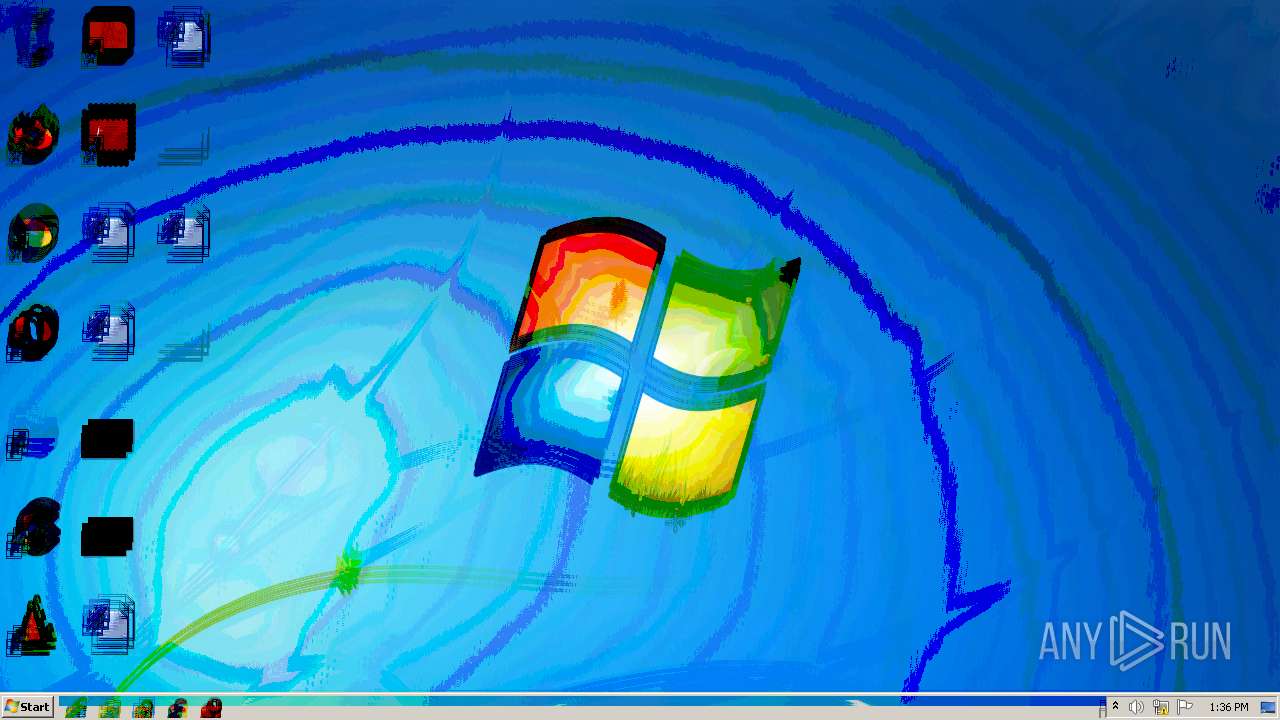
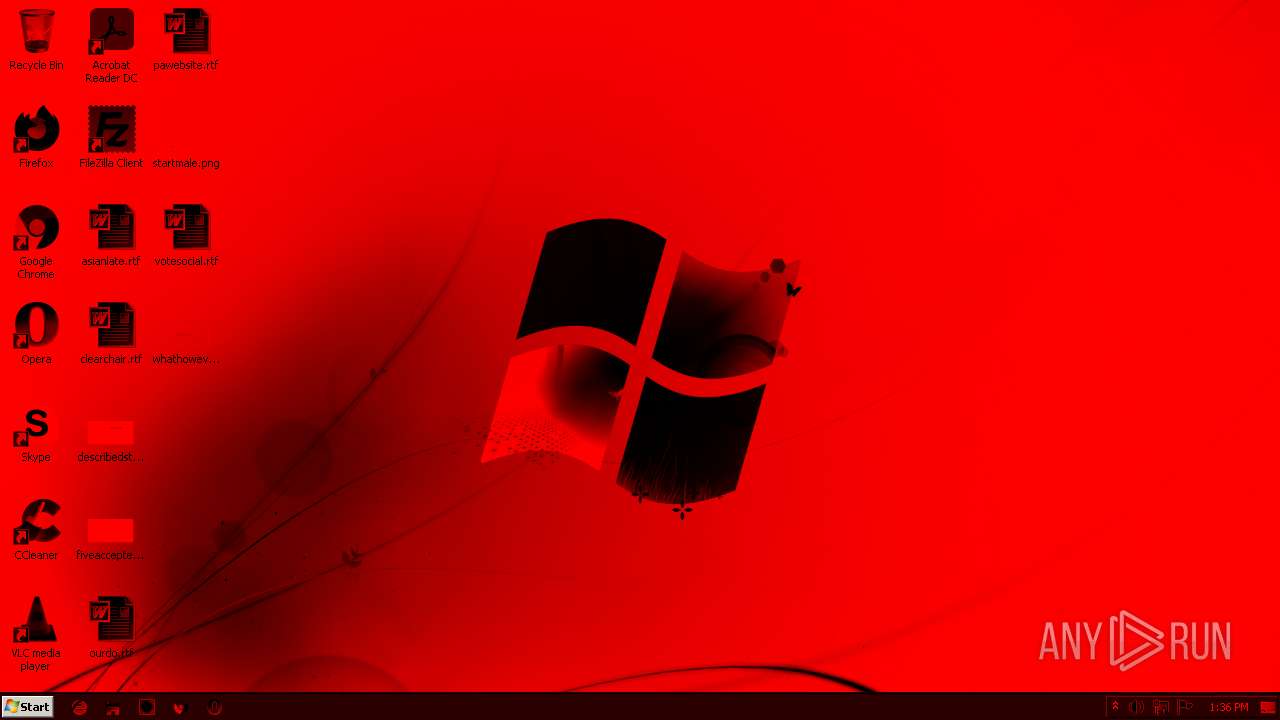
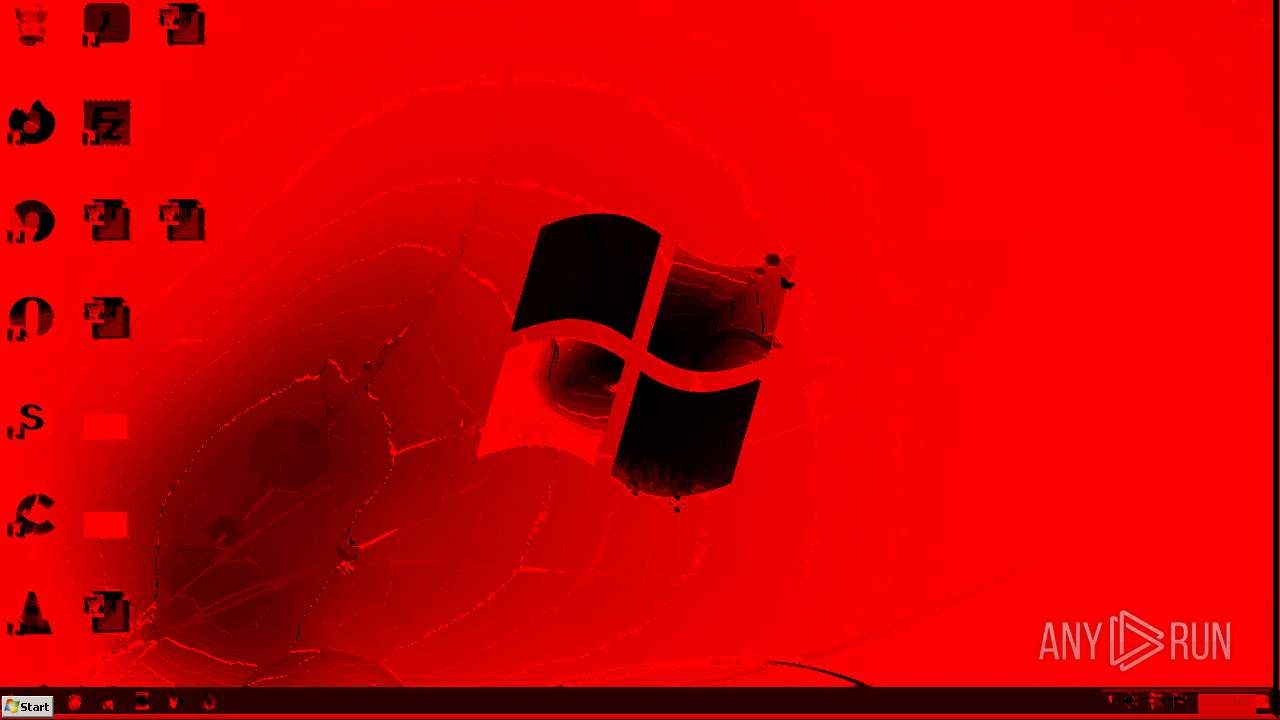
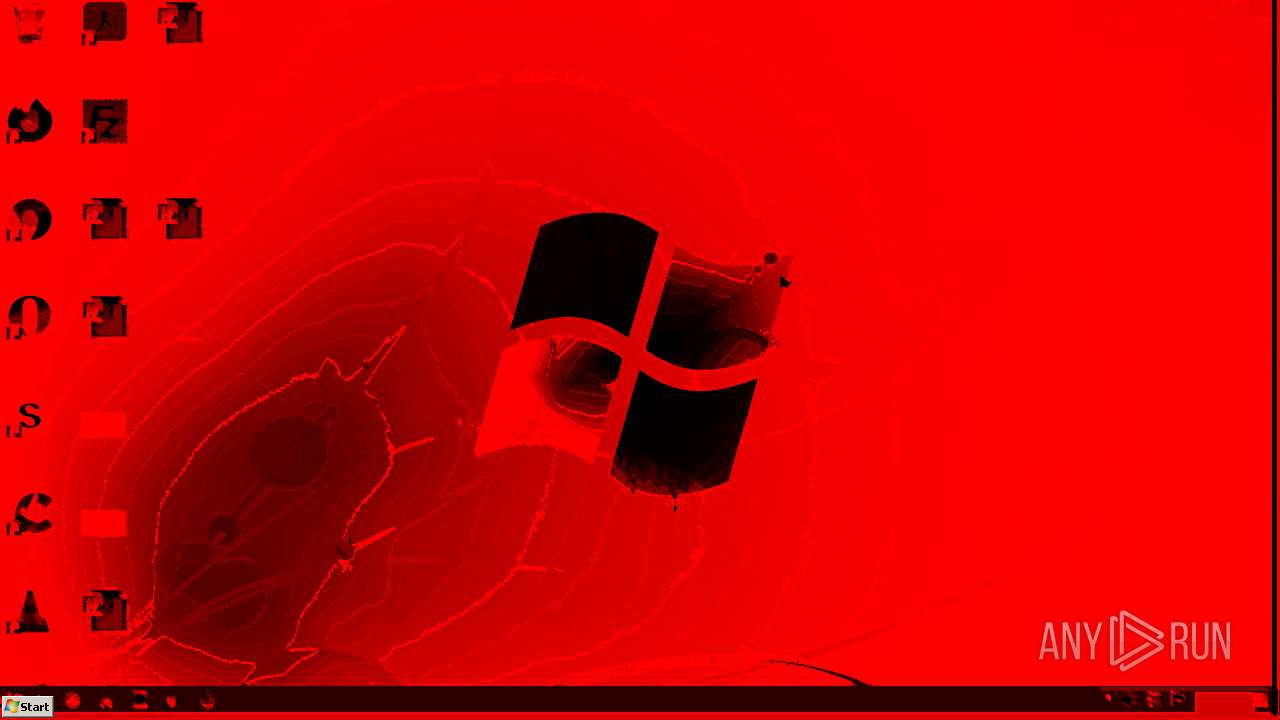
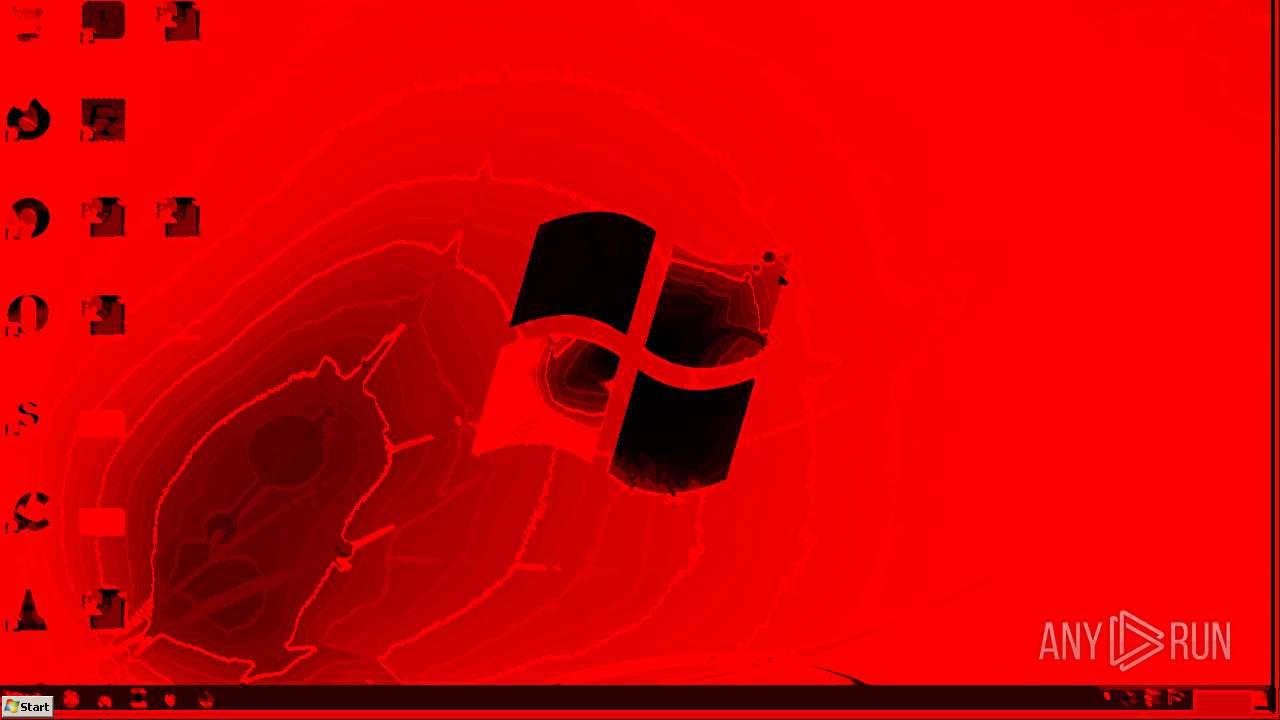
| Verdict: | Malicious activity |
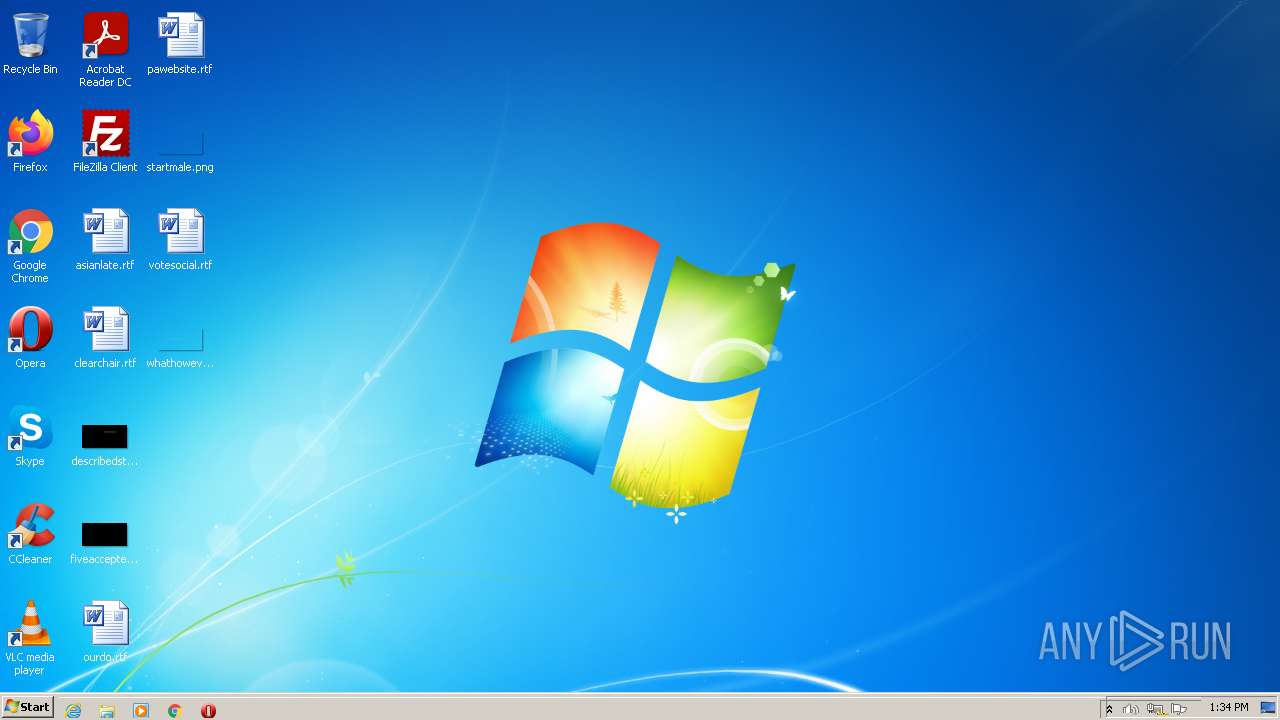
| Analysis date: | February 10, 2022, 13:34:00 |
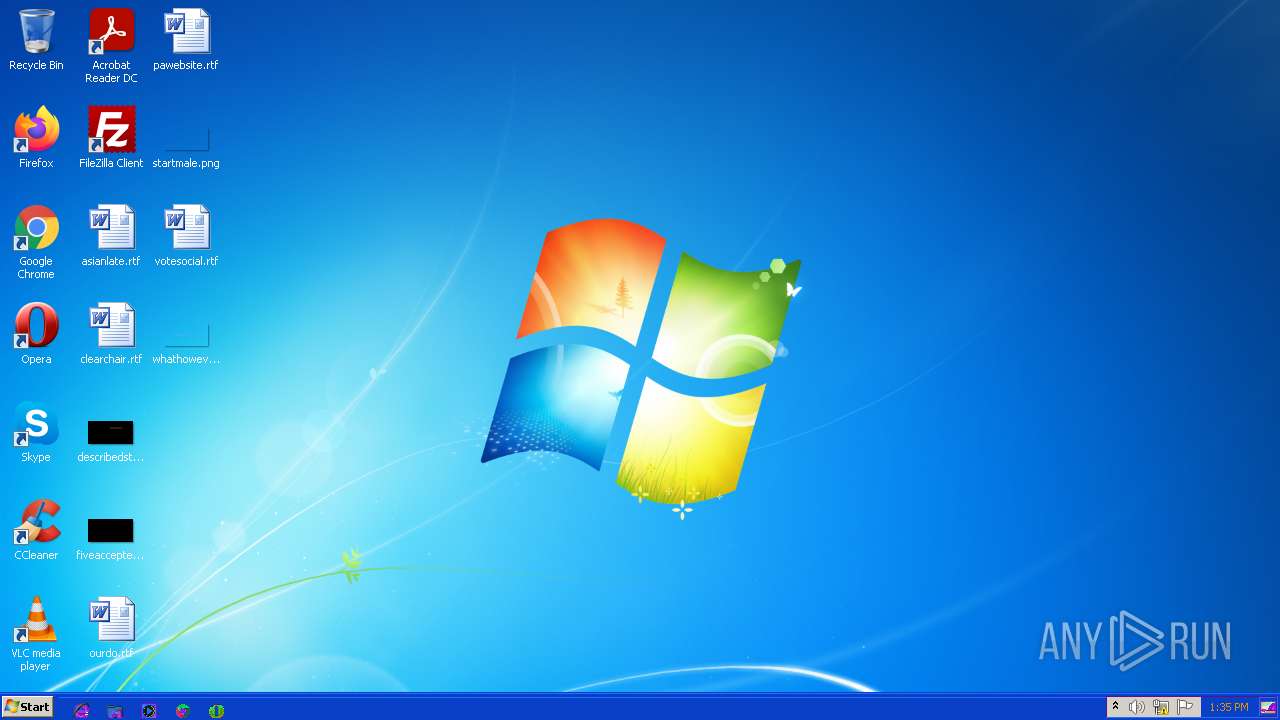
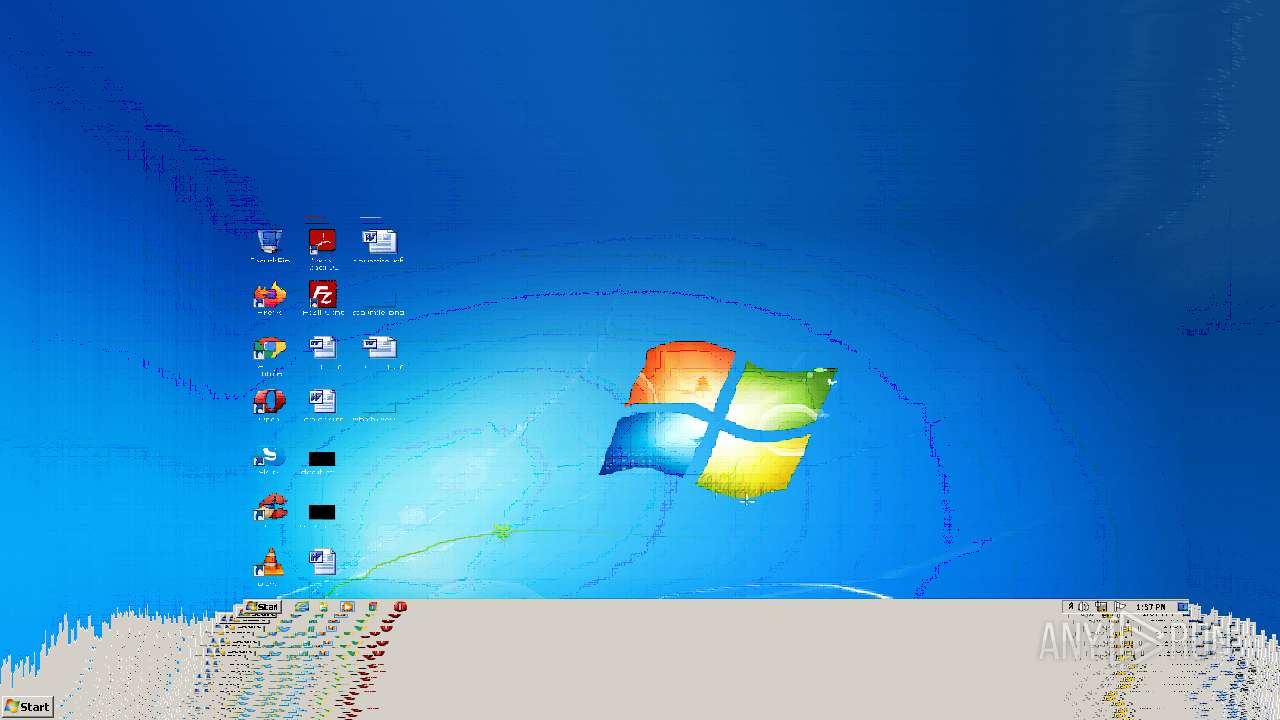
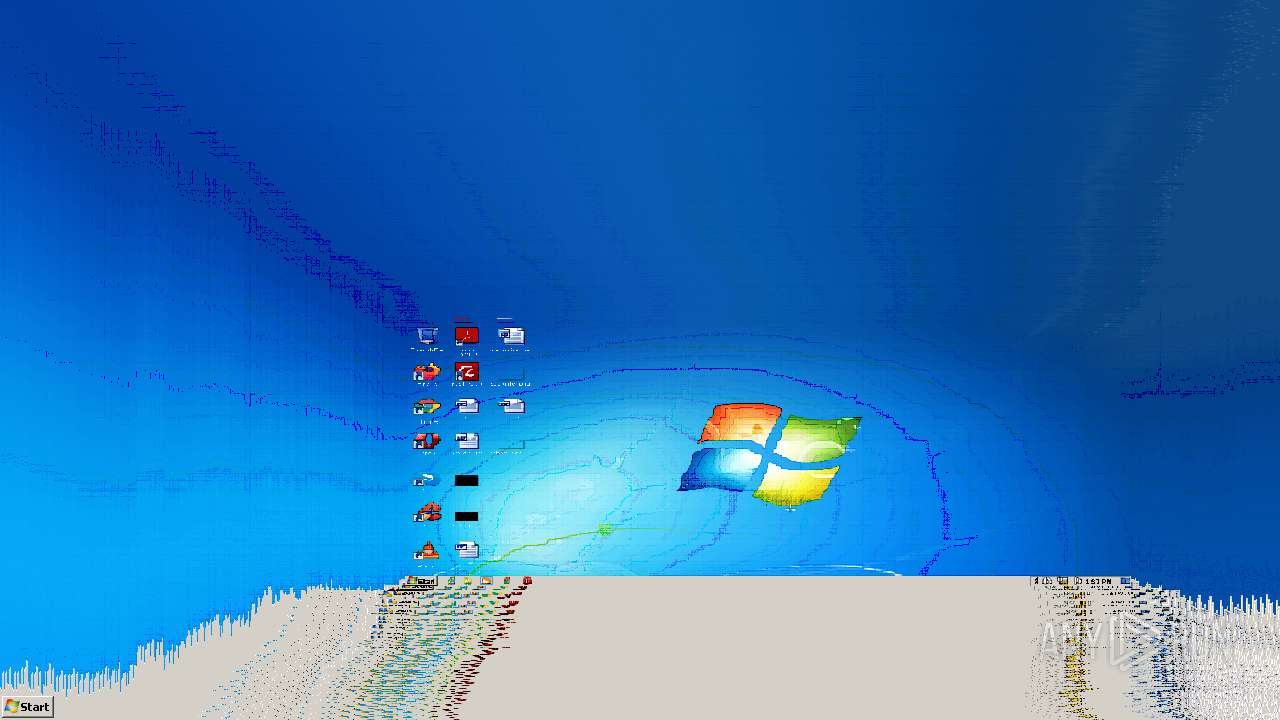
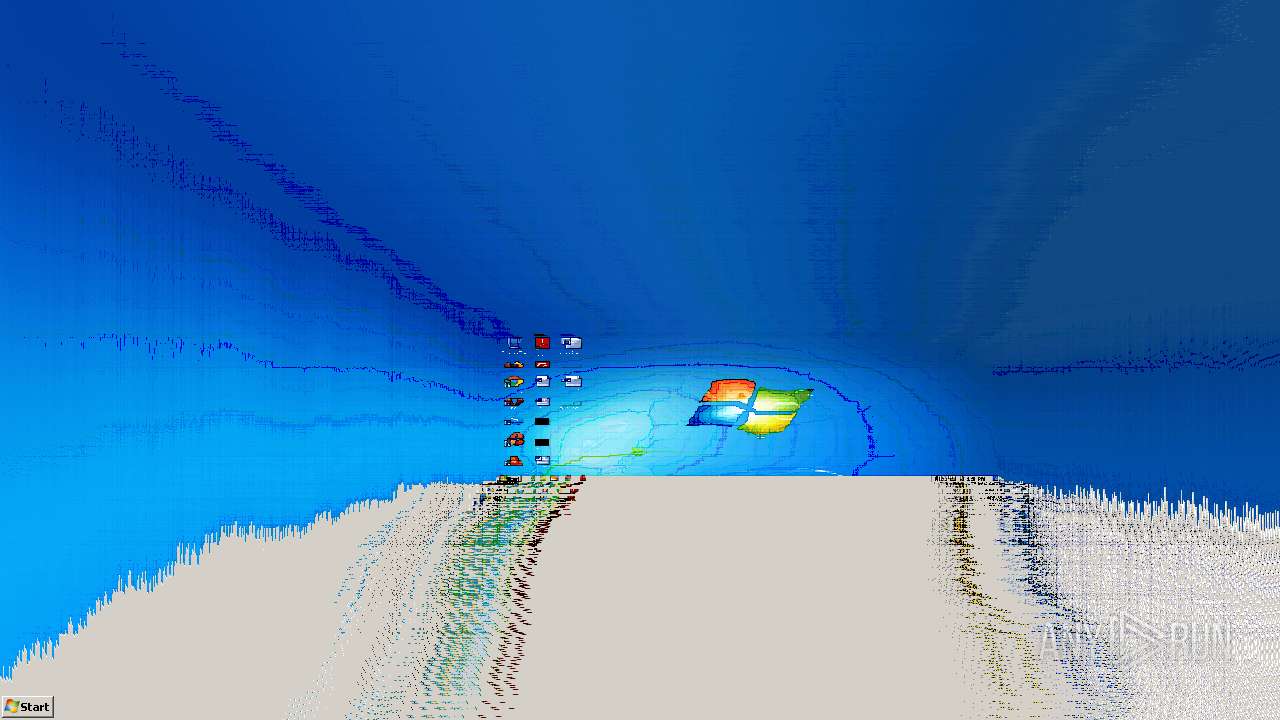
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 1C466F4DB7A44E5E25931CB9DB7A5AE3 |
| SHA1: | 0E41B8DB428D8FFB1C5863D732C138BB396F72AF |
| SHA256: | BC341EB878EAF2DE2E293C8049FA11910E8AF64DD3D6271635F68F32878F60B8 |
| SSDEEP: | 98304:Ow+MK0UsBDvRmvpLICugLPdGf9N+lUDMK0UsBDvRmvpLICugLPdGf9N+5KiwQ:OD0UCvNMPcz+eL0UCvNMPcz+Qi9 |
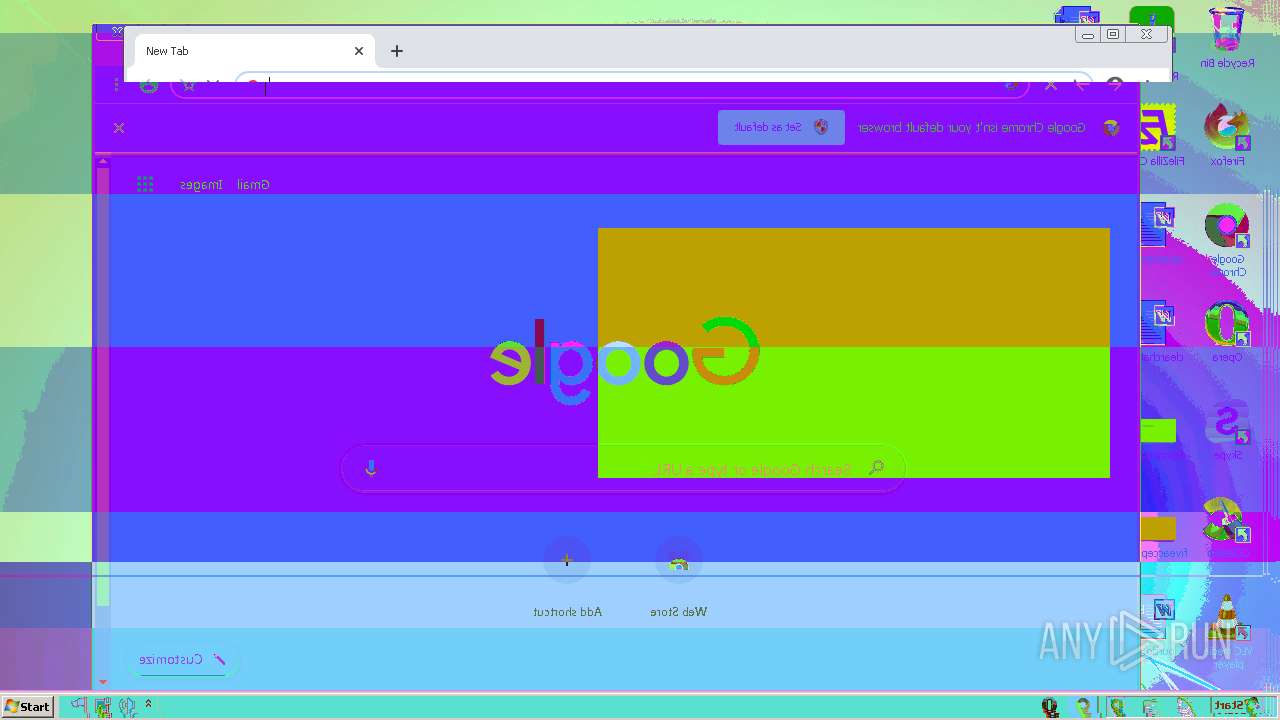
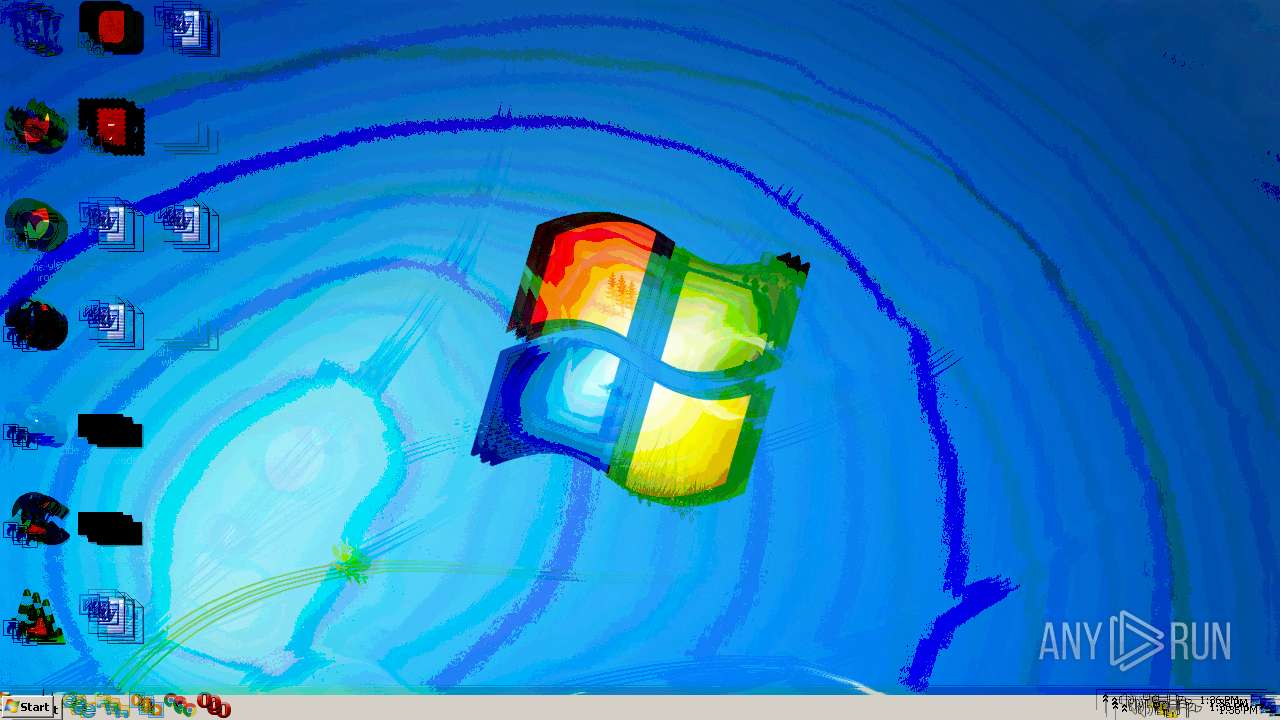
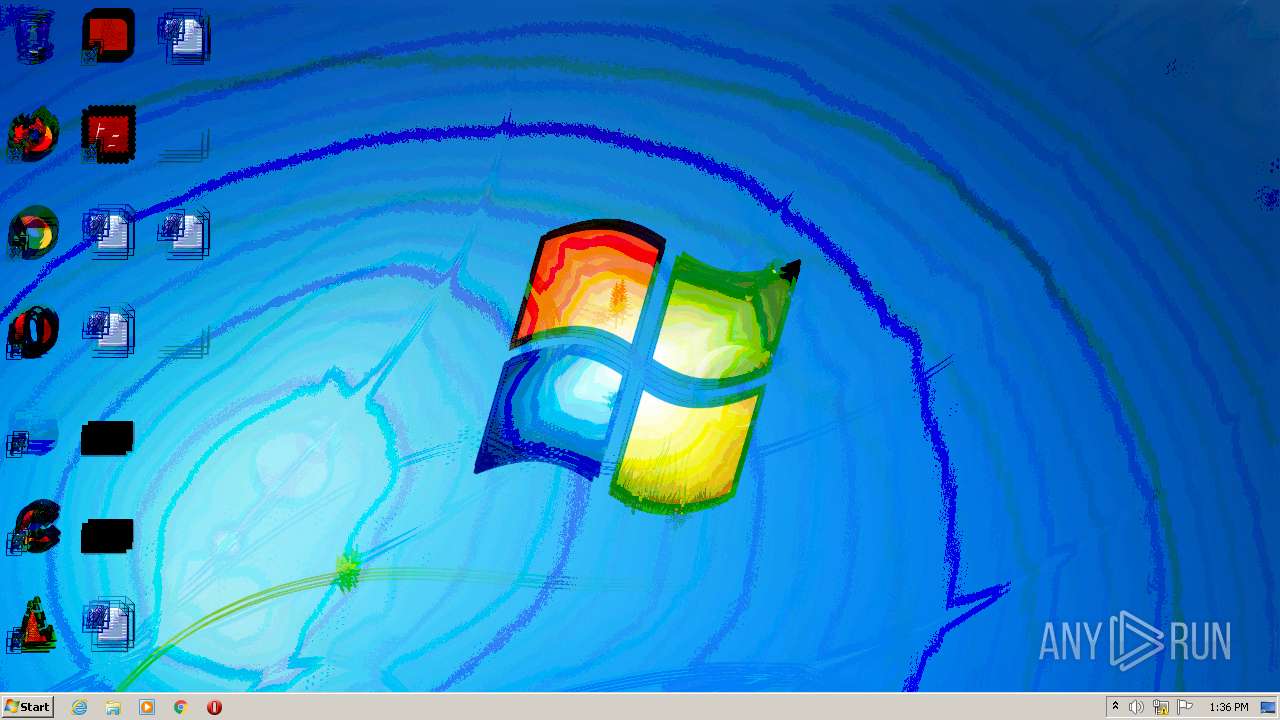
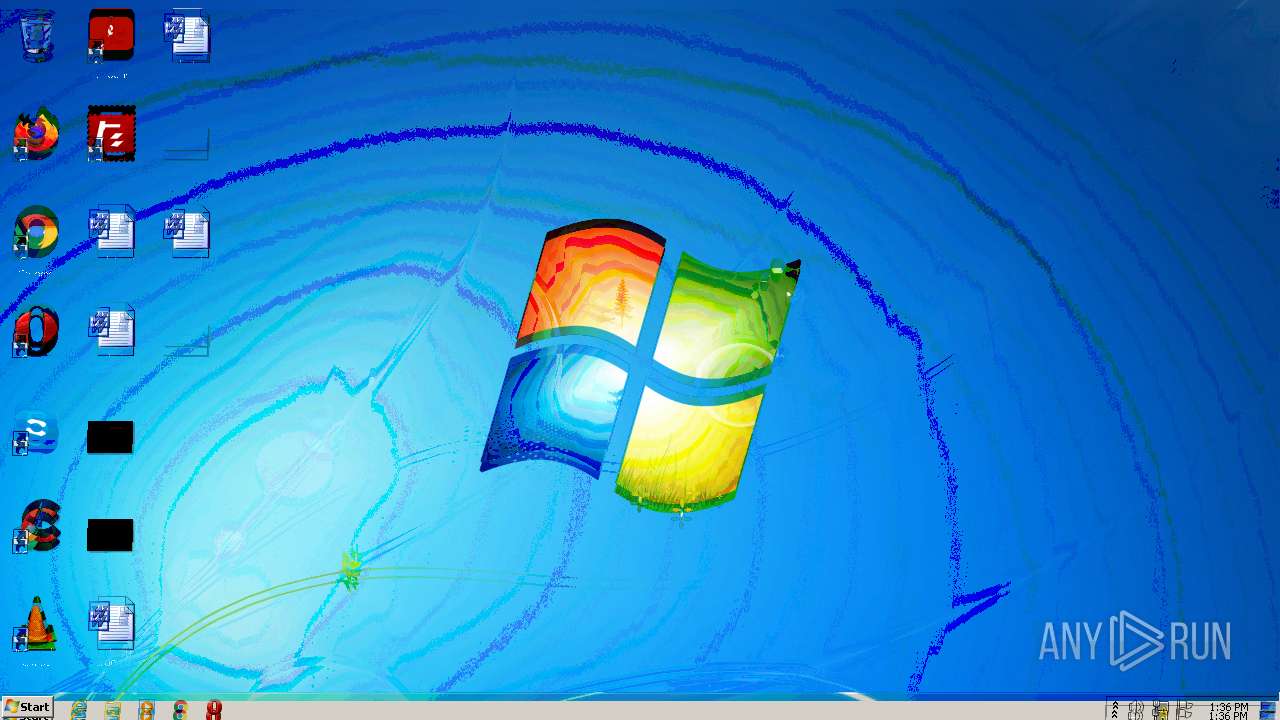
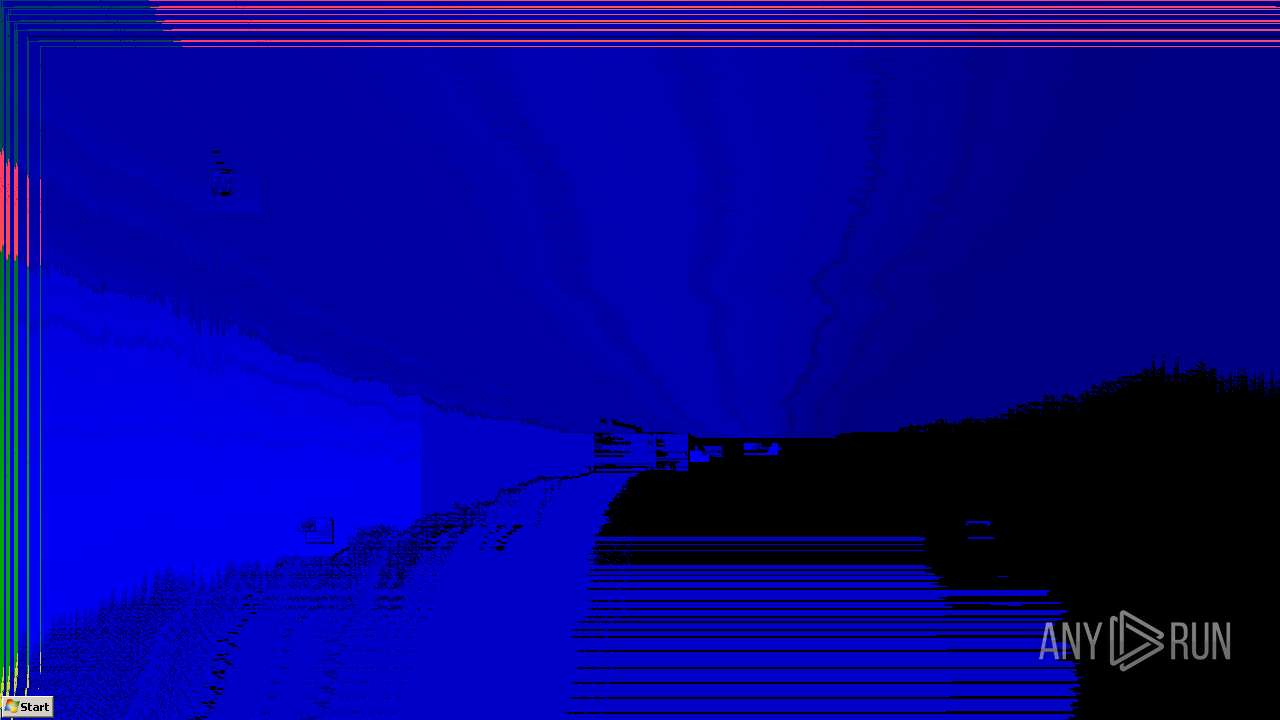
MALICIOUS
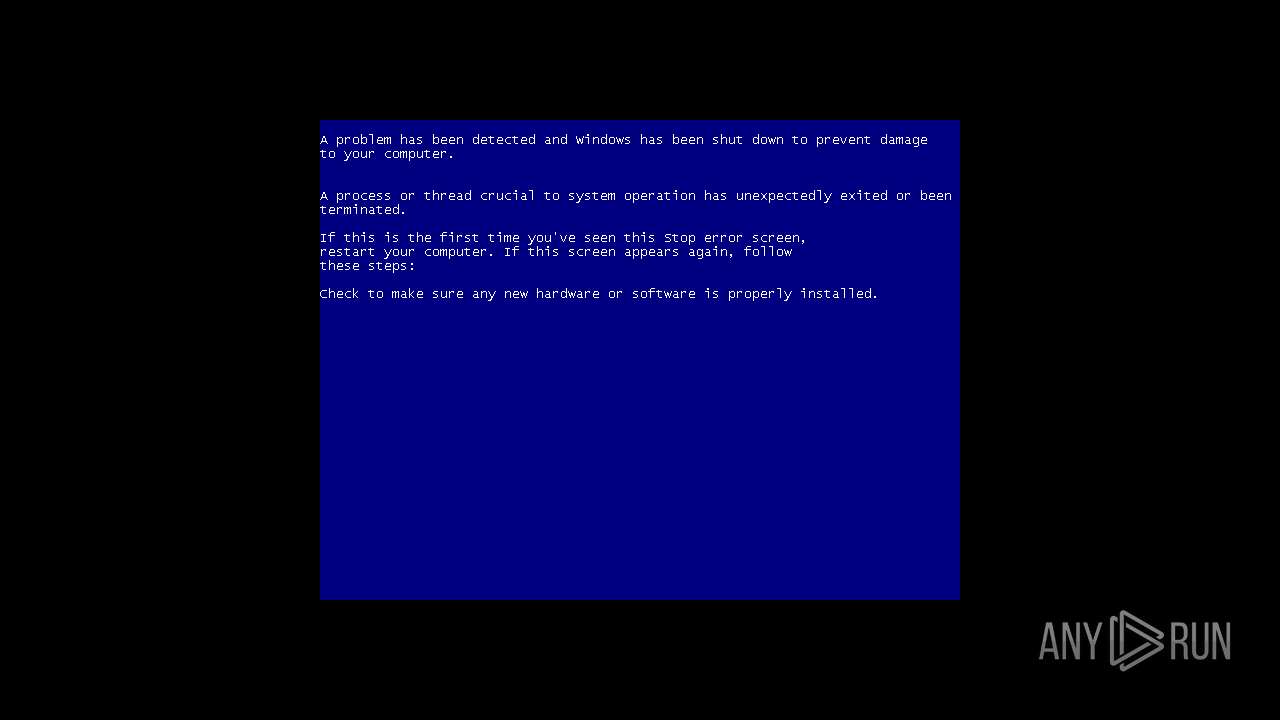
Disables registry editing tools (regedit)
- Clutt4.5.exe (PID: 3368)
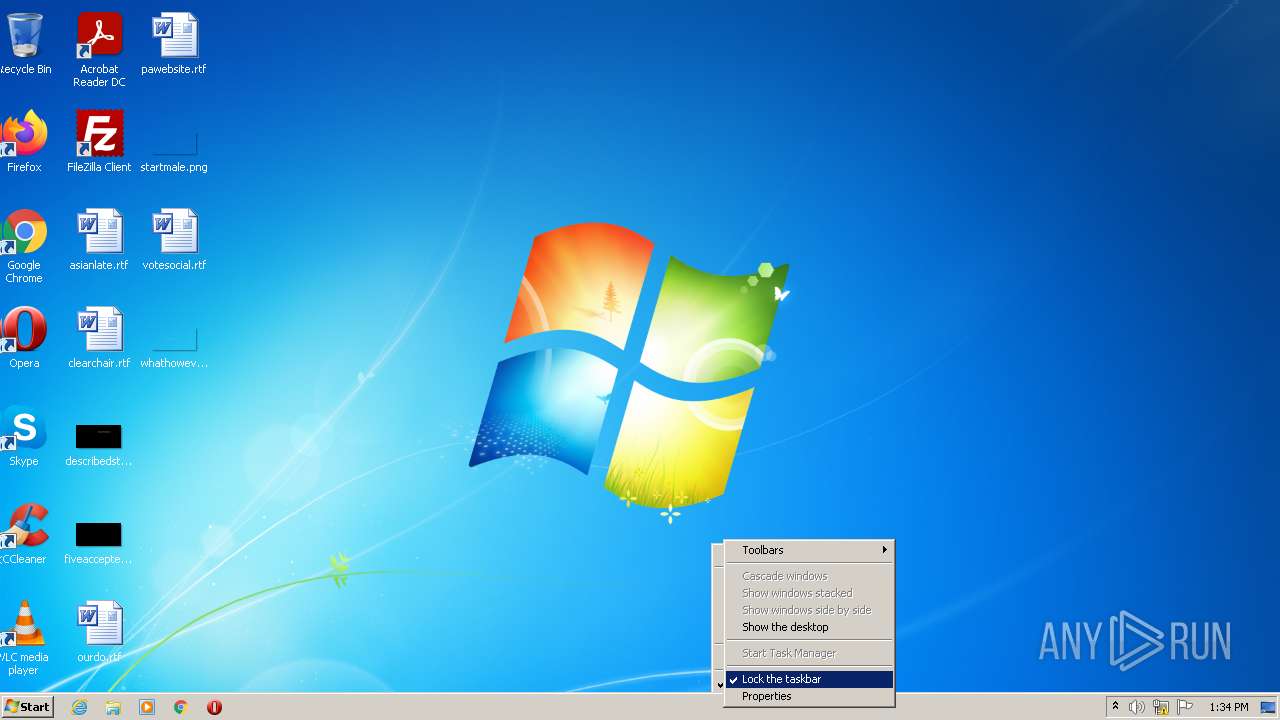
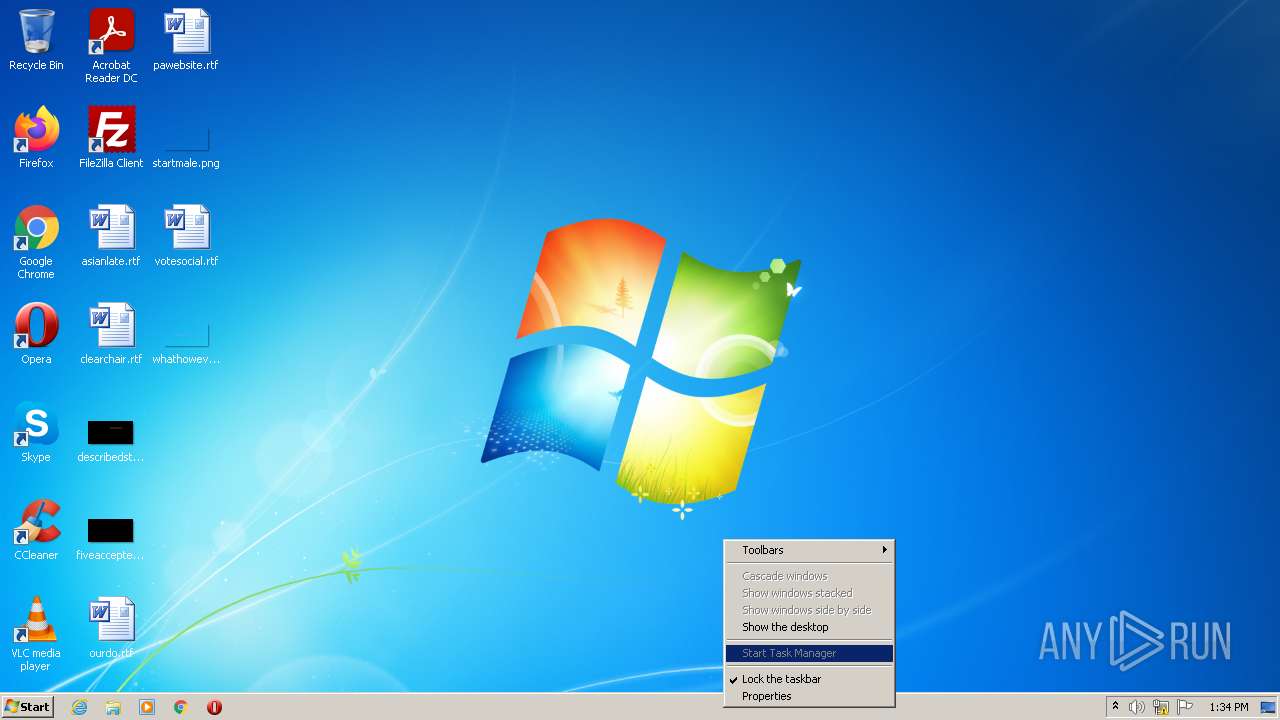
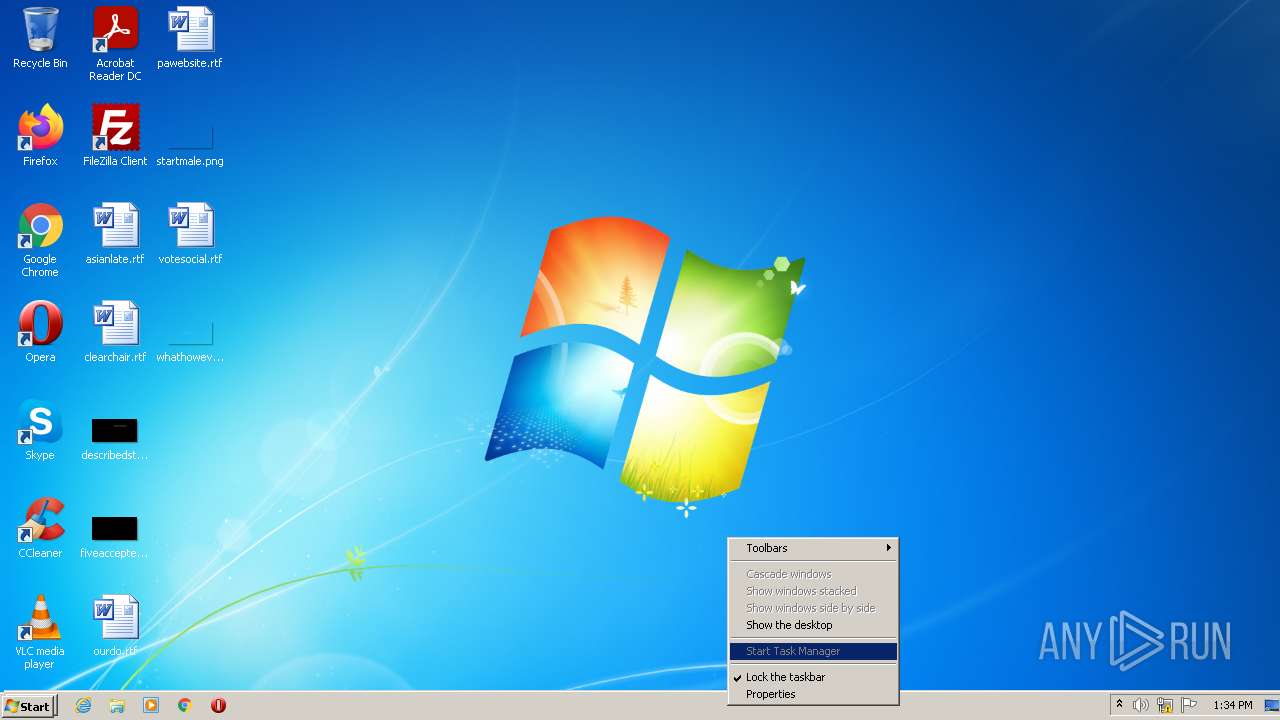
Task Manager has been disabled (taskmgr)
- Clutt4.5.exe (PID: 3368)
Application was dropped or rewritten from another process
- MBR.exe (PID: 2100)
SUSPICIOUS
Creates files in the Windows directory
- Clutt4.5.exe (PID: 3368)
Checks supported languages
- Clutt4.5.exe (PID: 3368)
- MBR.exe (PID: 2100)
Drops a file with a compile date too recent
- Clutt4.5.exe (PID: 3368)
Executable content was dropped or overwritten
- Clutt4.5.exe (PID: 3368)
Reads the computer name
- MBR.exe (PID: 2100)
- Clutt4.5.exe (PID: 3368)
INFO
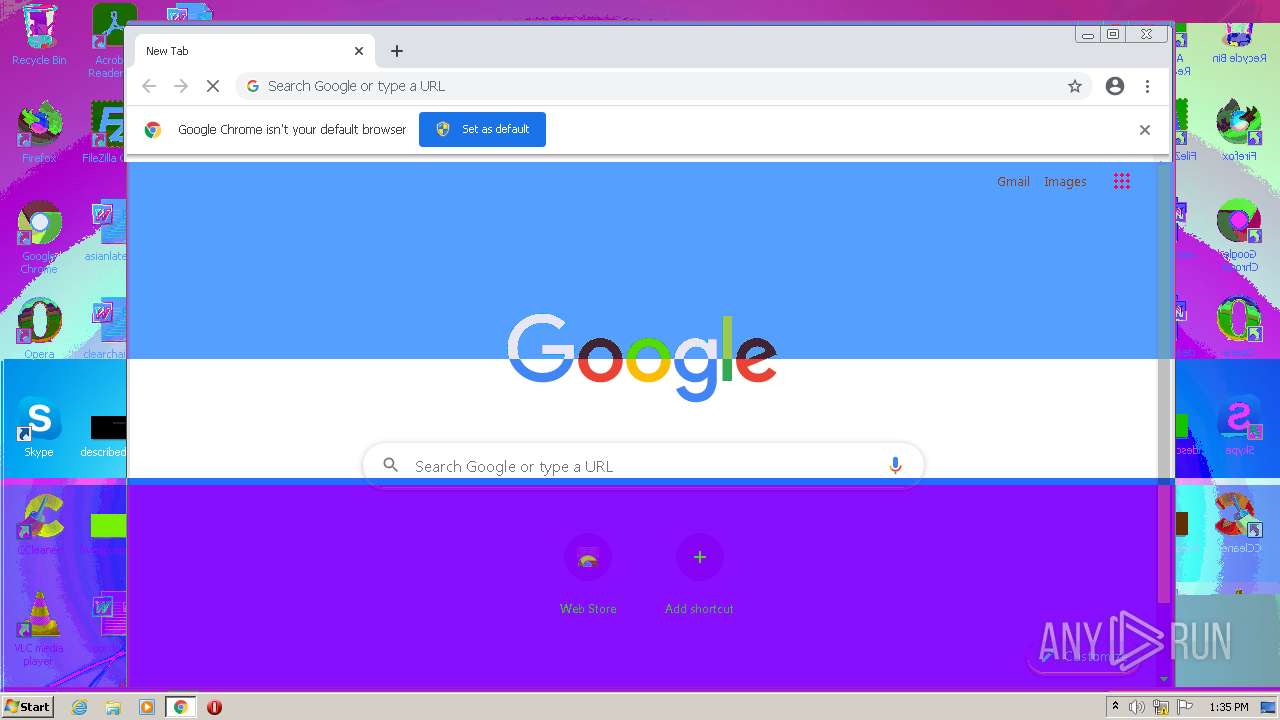
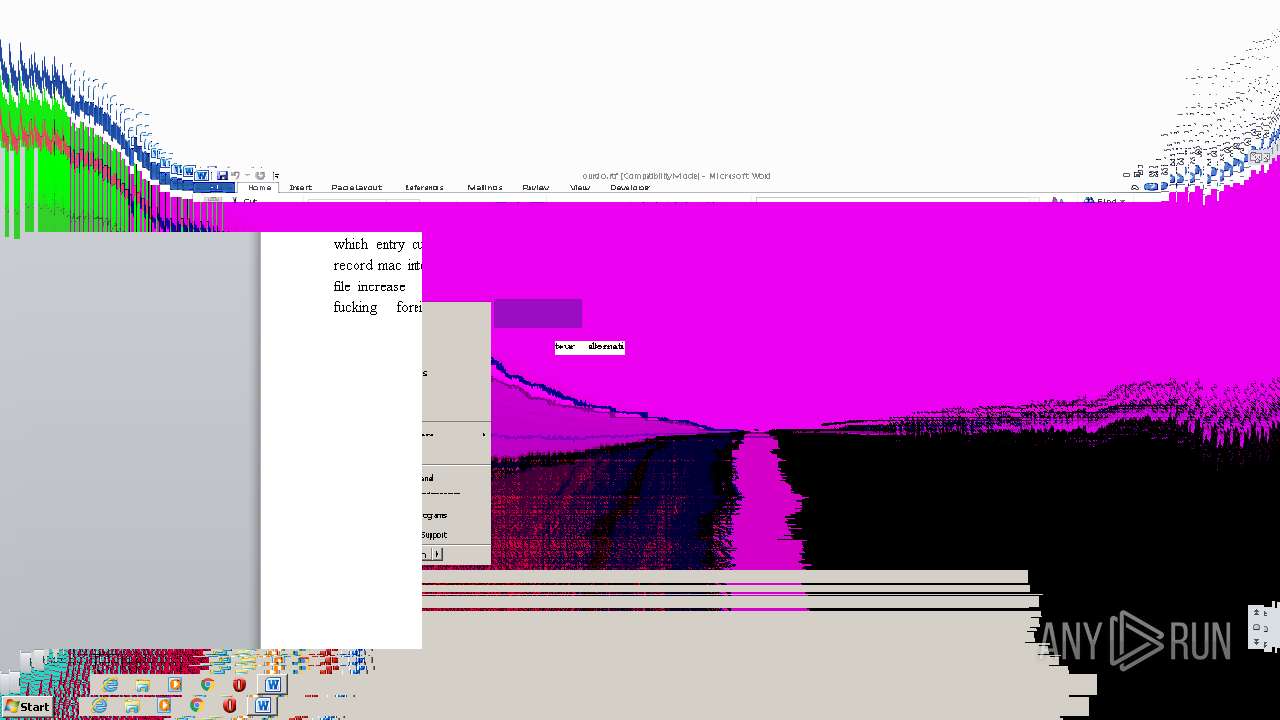
Manual execution by user
- chrome.exe (PID: 3044)
- WINWORD.EXE (PID: 2812)
- SndVol.exe (PID: 2172)
Checks supported languages
- chrome.exe (PID: 2376)
- chrome.exe (PID: 1388)
- chrome.exe (PID: 2524)
- chrome.exe (PID: 3044)
- chrome.exe (PID: 3136)
- chrome.exe (PID: 3624)
- chrome.exe (PID: 1708)
- chrome.exe (PID: 1236)
- chrome.exe (PID: 3760)
- WINWORD.EXE (PID: 2812)
- chrome.exe (PID: 4084)
- SndVol.exe (PID: 2172)
Application launched itself
- chrome.exe (PID: 3044)
Reads the computer name
- chrome.exe (PID: 3044)
- chrome.exe (PID: 2524)
- chrome.exe (PID: 1388)
- chrome.exe (PID: 3136)
- SndVol.exe (PID: 2172)
- WINWORD.EXE (PID: 2812)
Reads the hosts file
- chrome.exe (PID: 2524)
- chrome.exe (PID: 3044)
Reads settings of System Certificates
- chrome.exe (PID: 2524)
Creates files in the user directory
- WINWORD.EXE (PID: 2812)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2812)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (41) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (36.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.6) |
| .exe | | | Win32 Executable (generic) (5.9) |
| .exe | | | Win16/32 Executable Delphi generic (2.7) |
EXIF
EXE
| AssemblyVersion: | 4.5.0.0 |
|---|---|
| ProductVersion: | 4.5.0.0 |
| ProductName: | Clutt4.5 |
| OriginalFileName: | Clutt4.5.exe |
| LegalTrademarks: | - |
| LegalCopyright: | Copyright © 2021 |
| InternalName: | Clutt4.5.exe |
| FileVersion: | 4.5.0.0 |
| FileDescription: | Clutt4.5 |
| CompanyName: | Clutter Destructive |
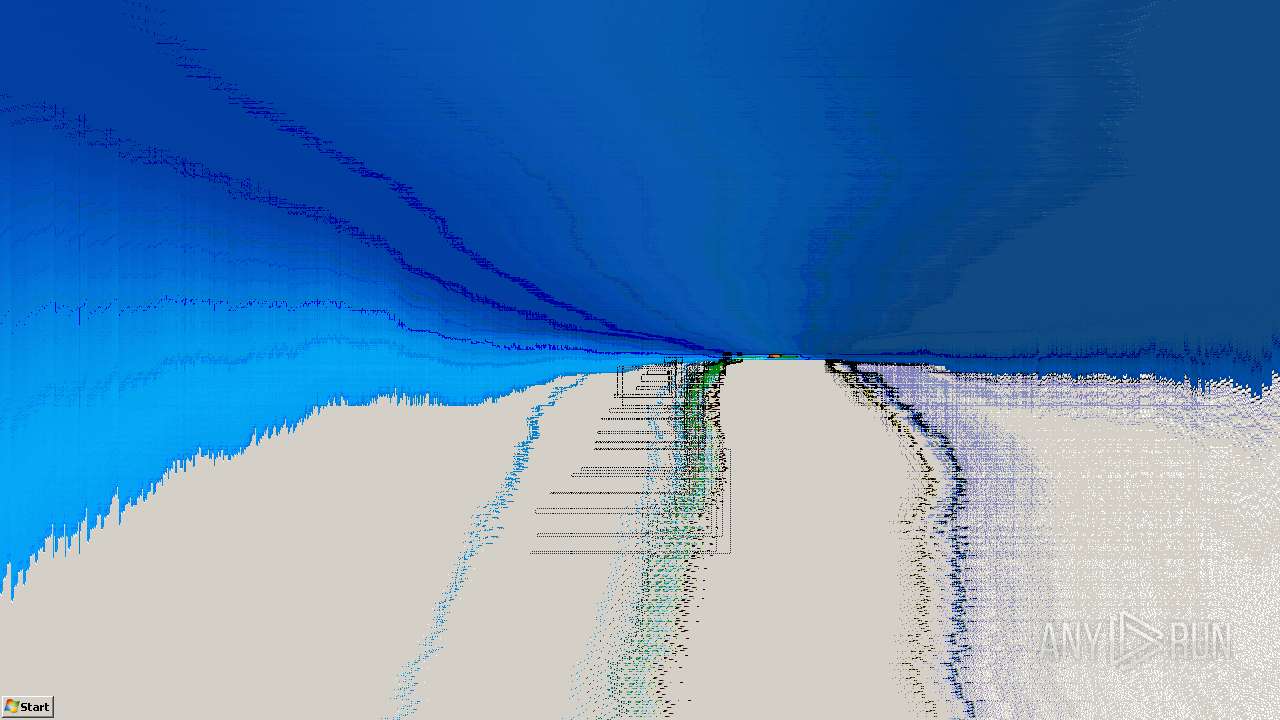
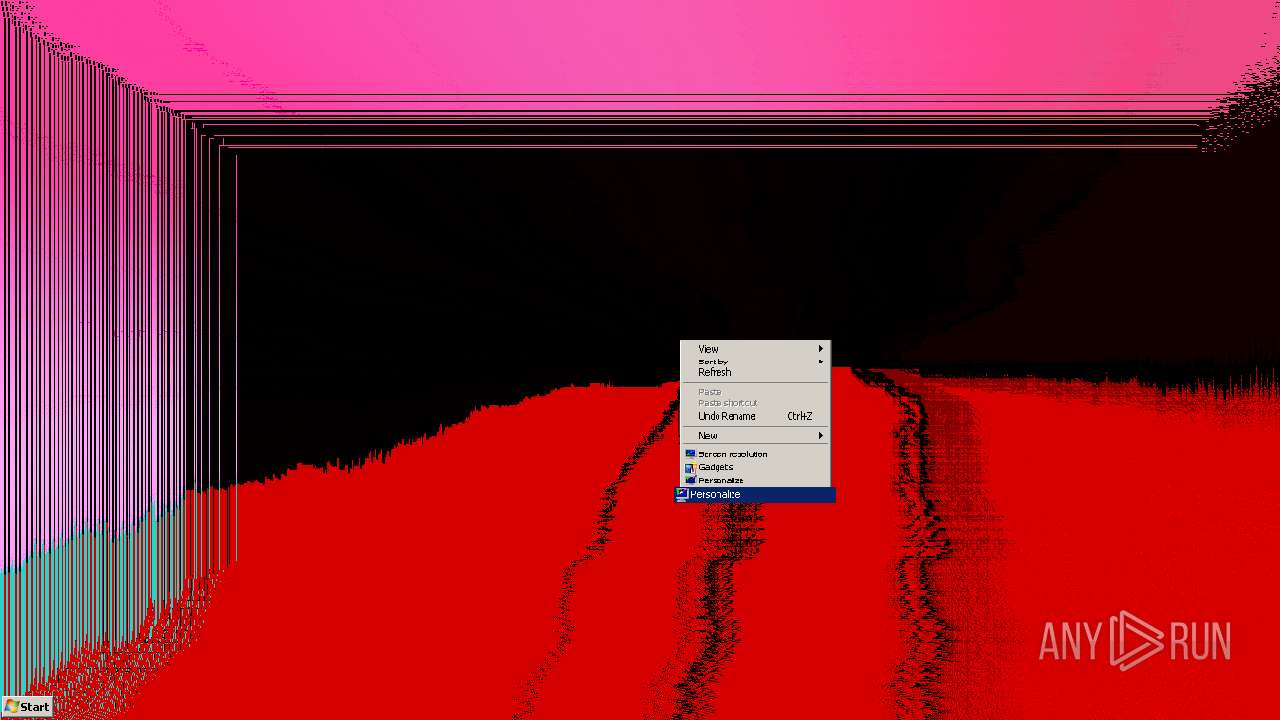
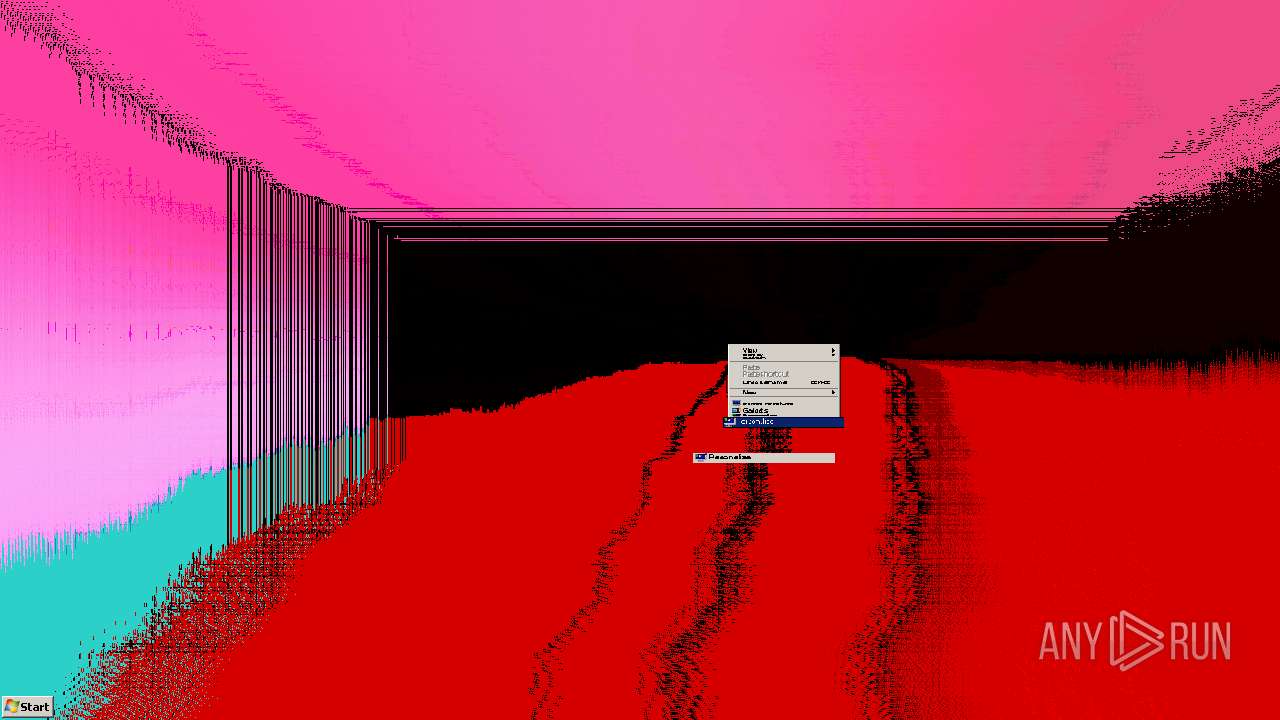
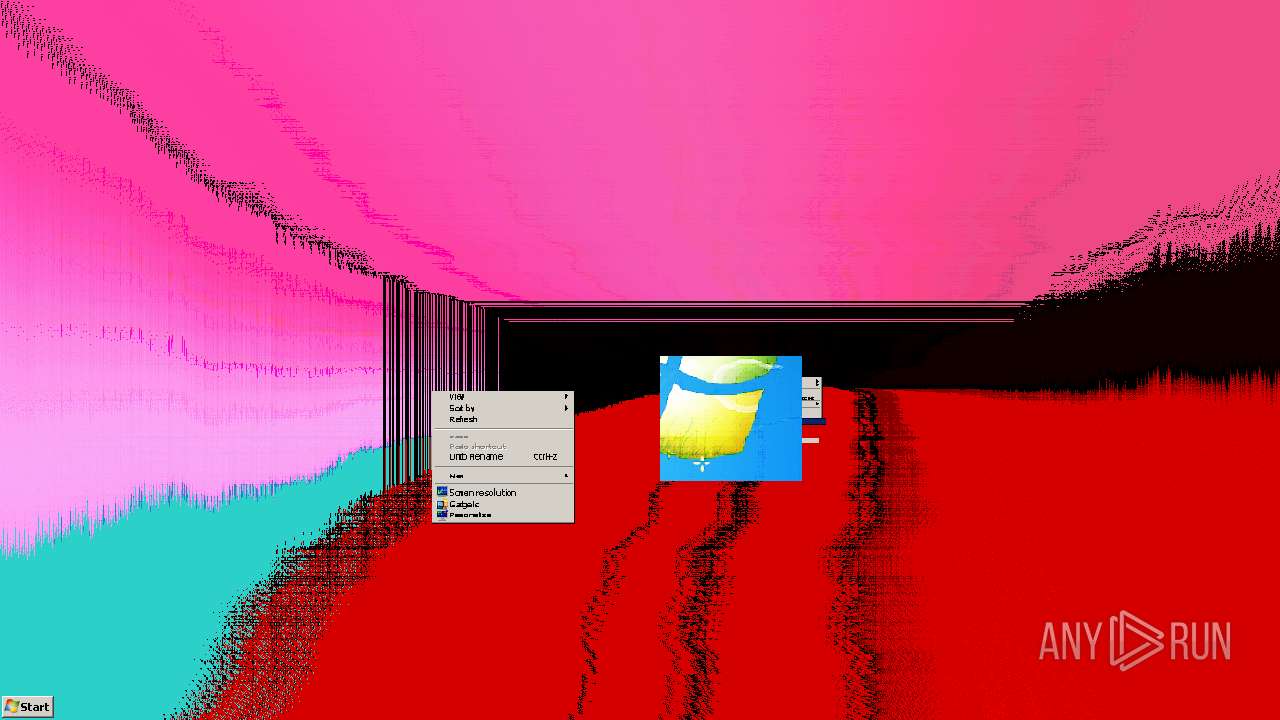
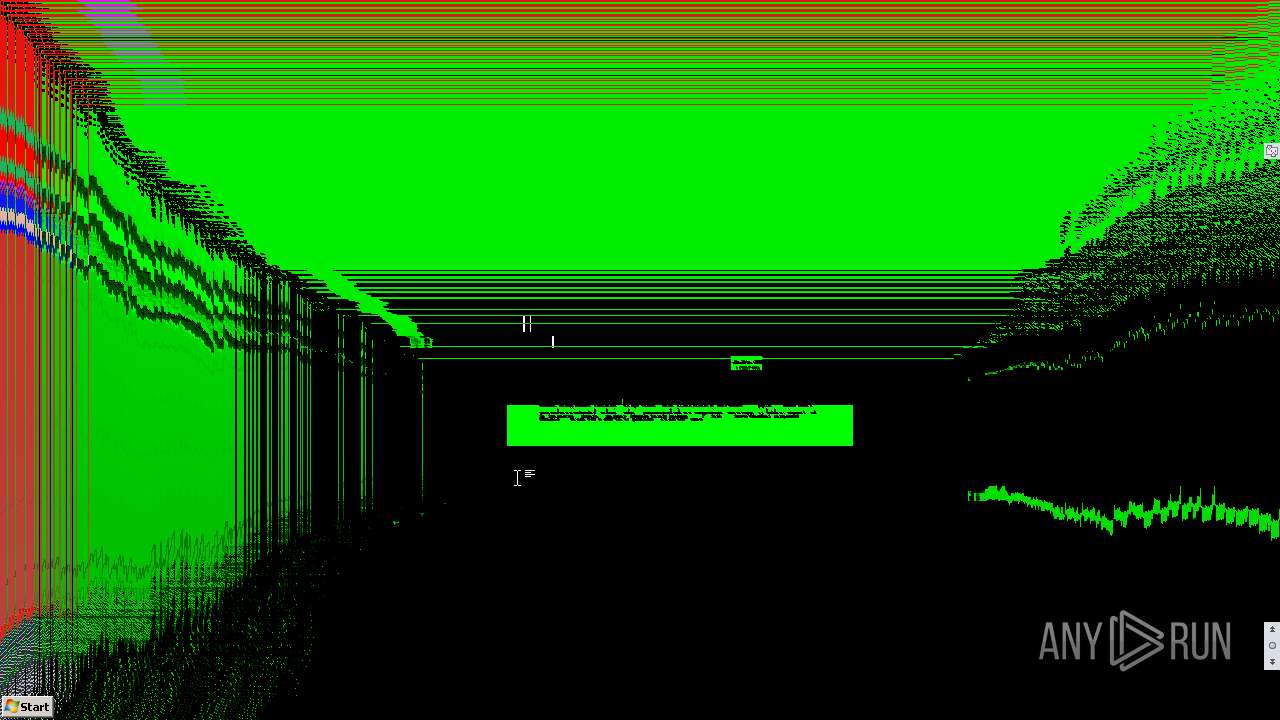
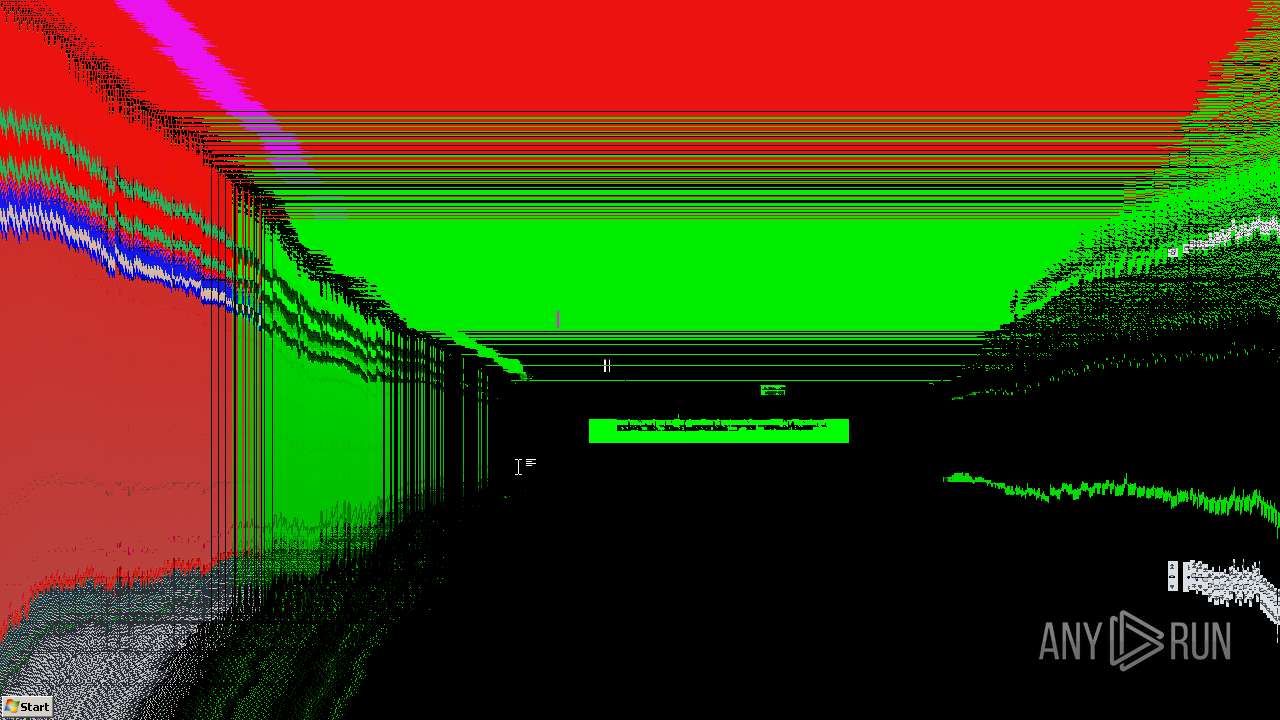
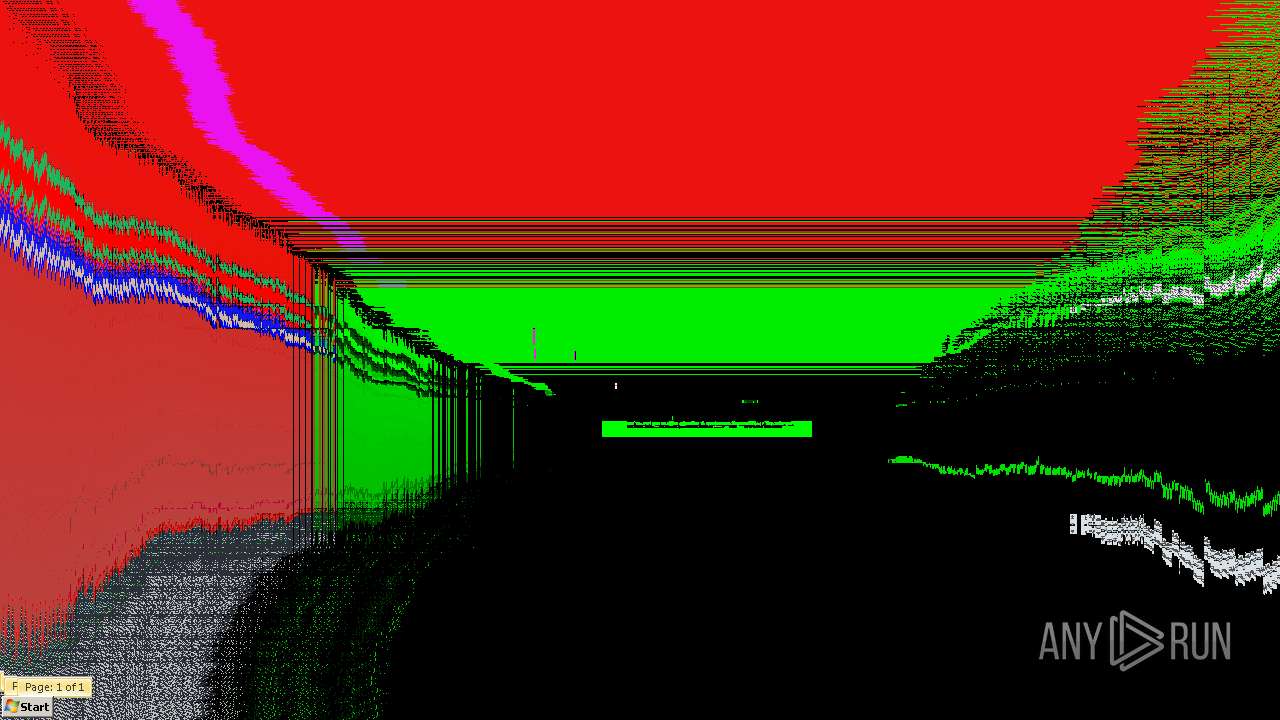
| Comments: | Destructive gdi trojan by cyber soldier |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 4.5.0.0 |
| FileVersionNumber: | 4.5.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x34a00a |
| UninitializedDataSize: | - |
| InitializedDataSize: | 181248 |
| CodeSize: | 3238400 |
| LinkerVersion: | 48 |
| PEType: | PE32 |
| TimeStamp: | 2071:03:31 19:15:09+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 23-Feb-1935 10:46:53 |
| Comments: | Destructive gdi trojan by cyber soldier |
| CompanyName: | Clutter Destructive |
| FileDescription: | Clutt4.5 |
| FileVersion: | 4.5.0.0 |
| InternalName: | Clutt4.5.exe |
| LegalCopyright: | Copyright © 2021 |
| LegalTrademarks: | - |
| OriginalFilename: | Clutt4.5.exe |
| ProductName: | Clutt4.5 |
| ProductVersion: | 4.5.0.0 |
| Assembly Version: | 4.5.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 23-Feb-1935 10:46:53 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
a$][>R\x1cb\x1c~ | 0x00002000 | 0x00007E1C | 0x00008000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.99467 |
.text | 0x0000A000 | 0x00316700 | 0x00316800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.61263 |
.rsrc | 0x00322000 | 0x00024158 | 0x00024200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.68098 |
.reloc | 0x00348000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.0980042 |
0x0034A000 | 0x00000010 | 0x00000200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 0.122276 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00772 | 3168 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 5.59121 | 67624 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 5.81785 | 16936 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 5.77947 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 5.96052 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 5.76416 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
32512 | 2.79908 | 90 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
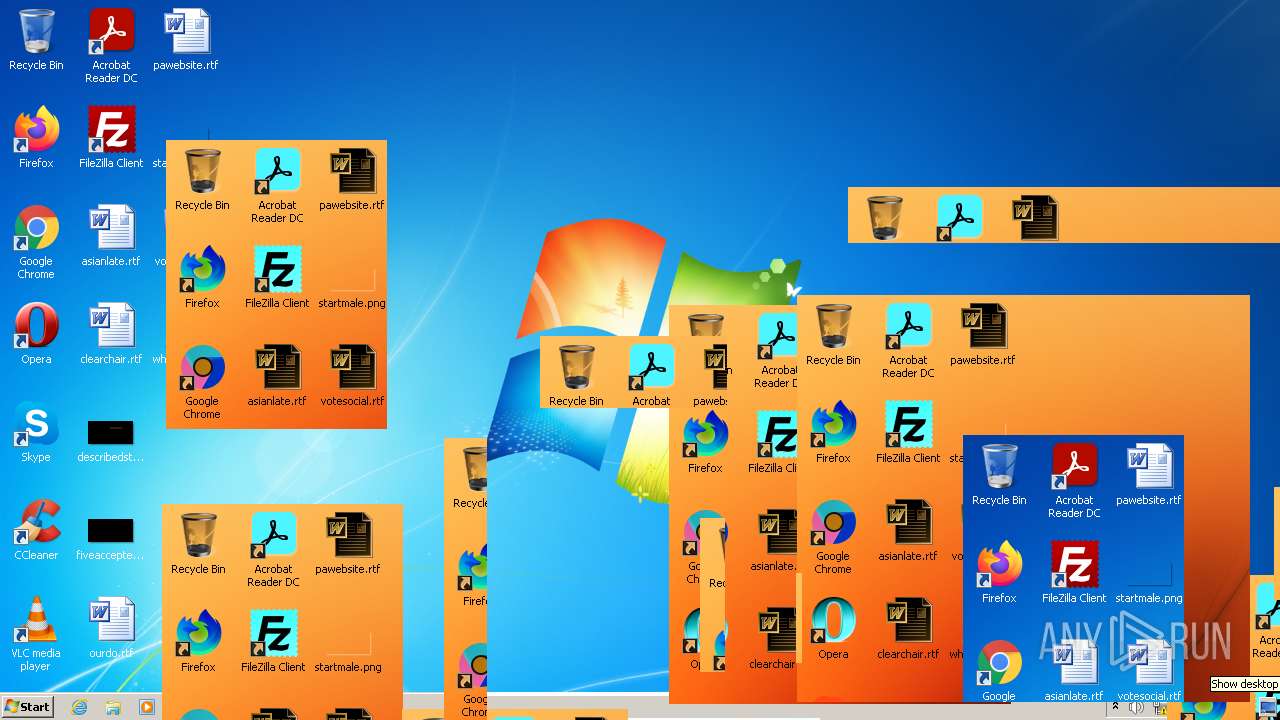
Total processes
55
Monitored processes
15
Malicious processes
1
Suspicious processes
0
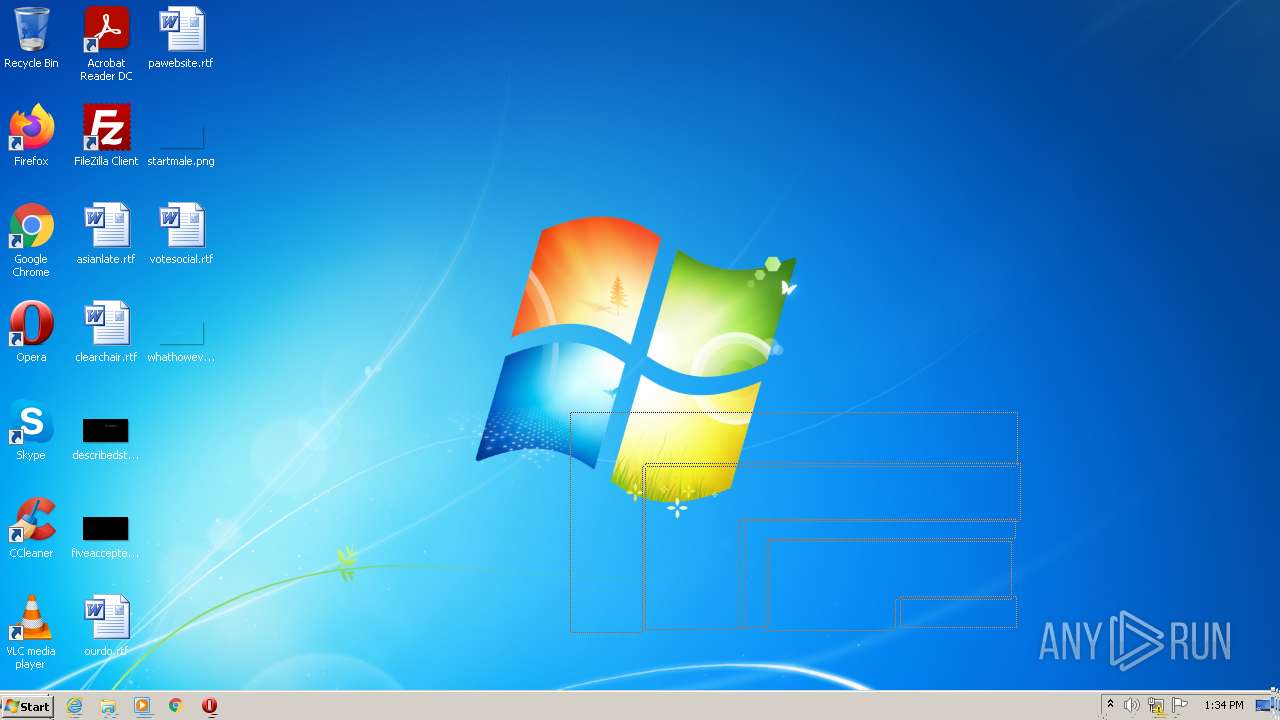
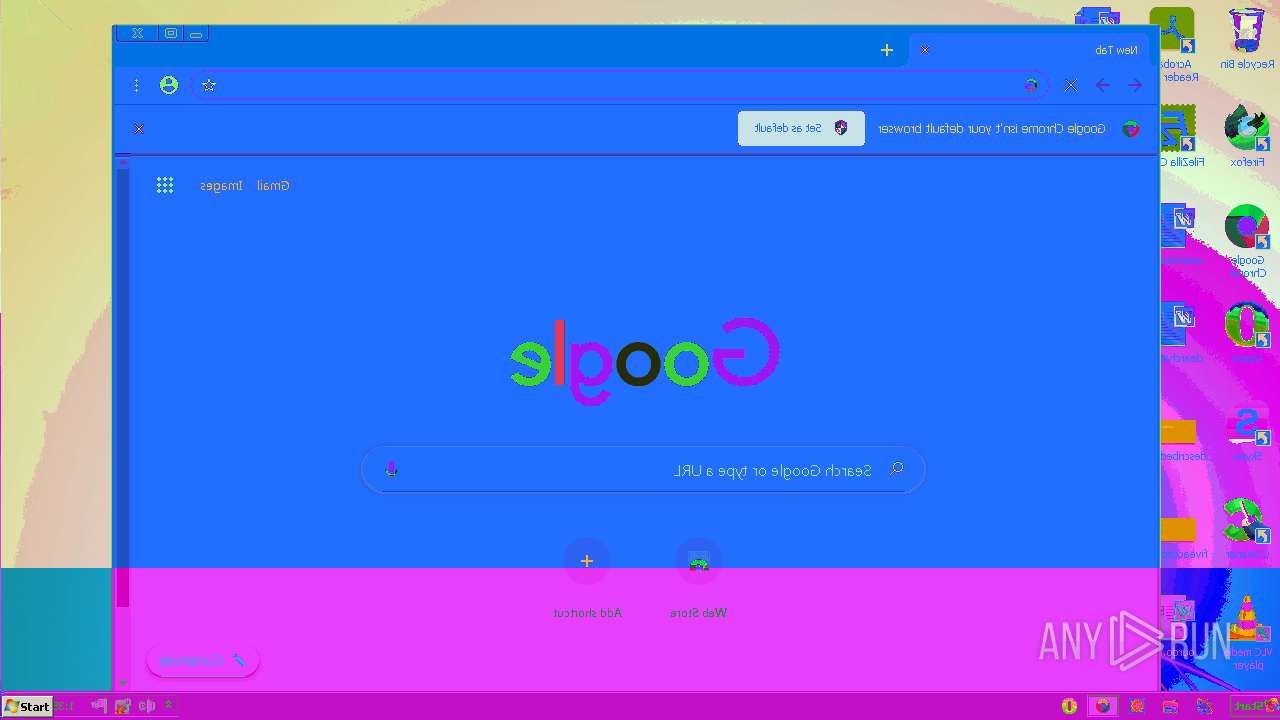
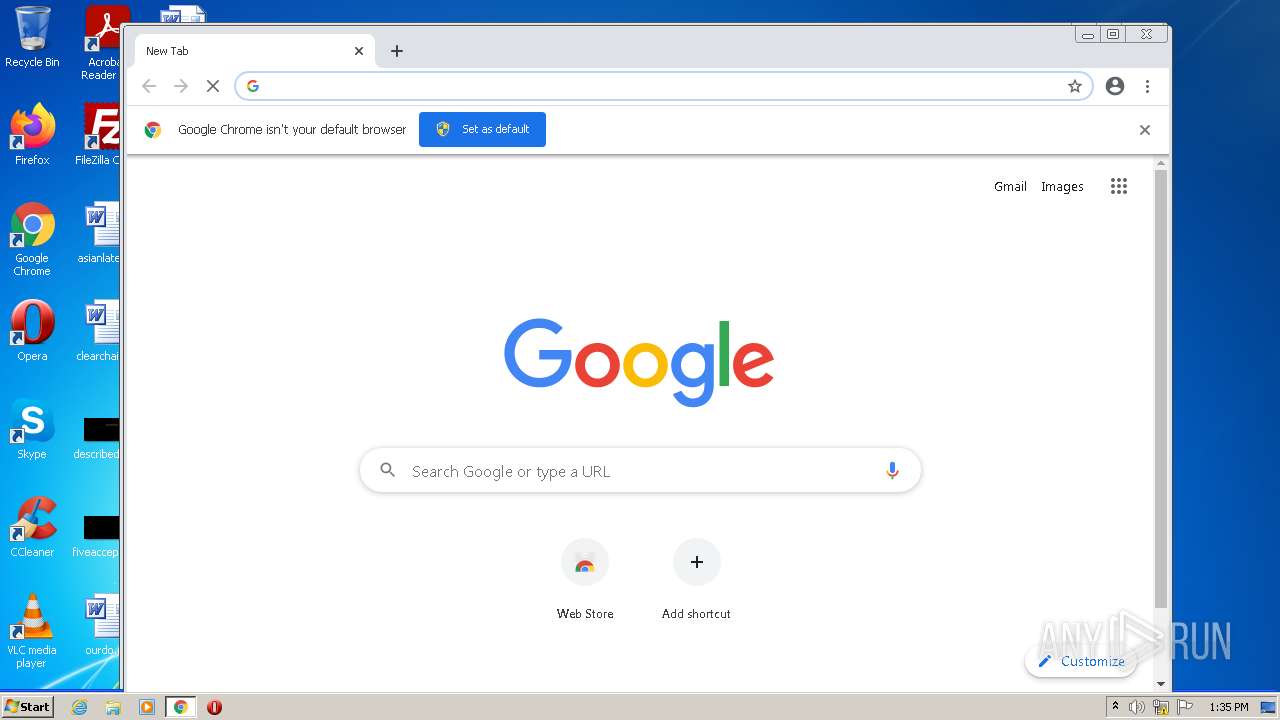
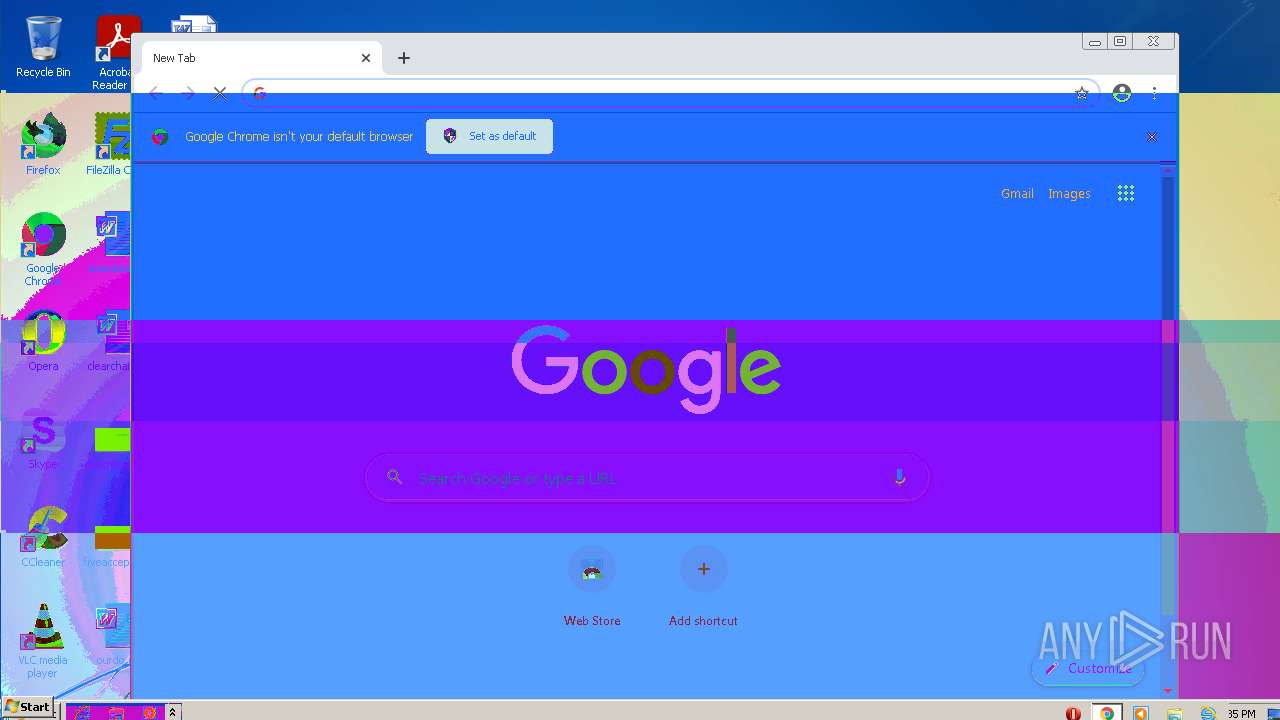
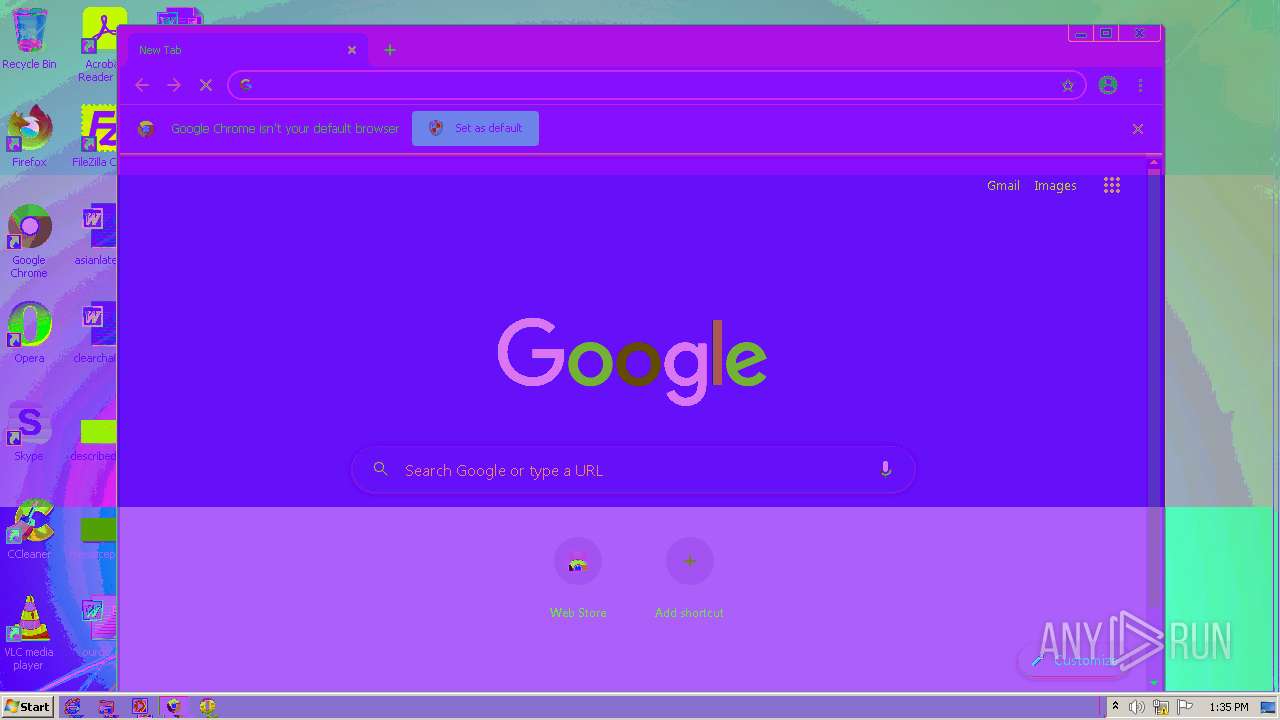
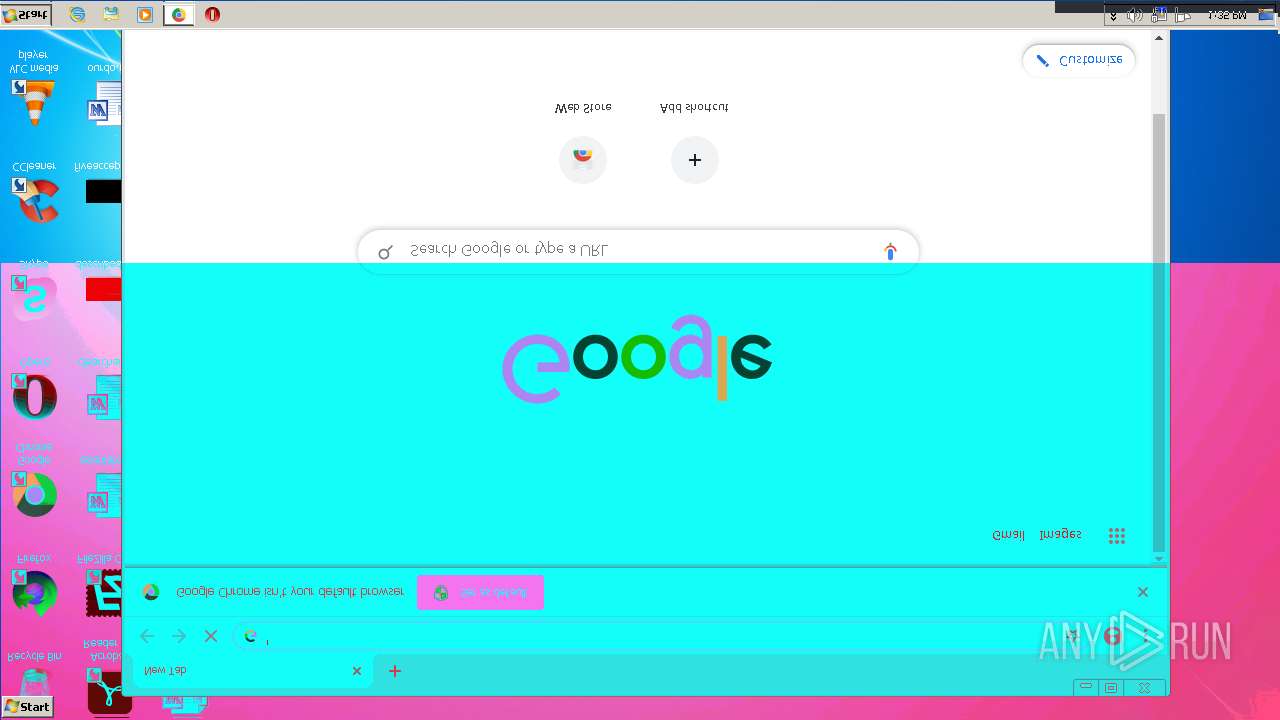
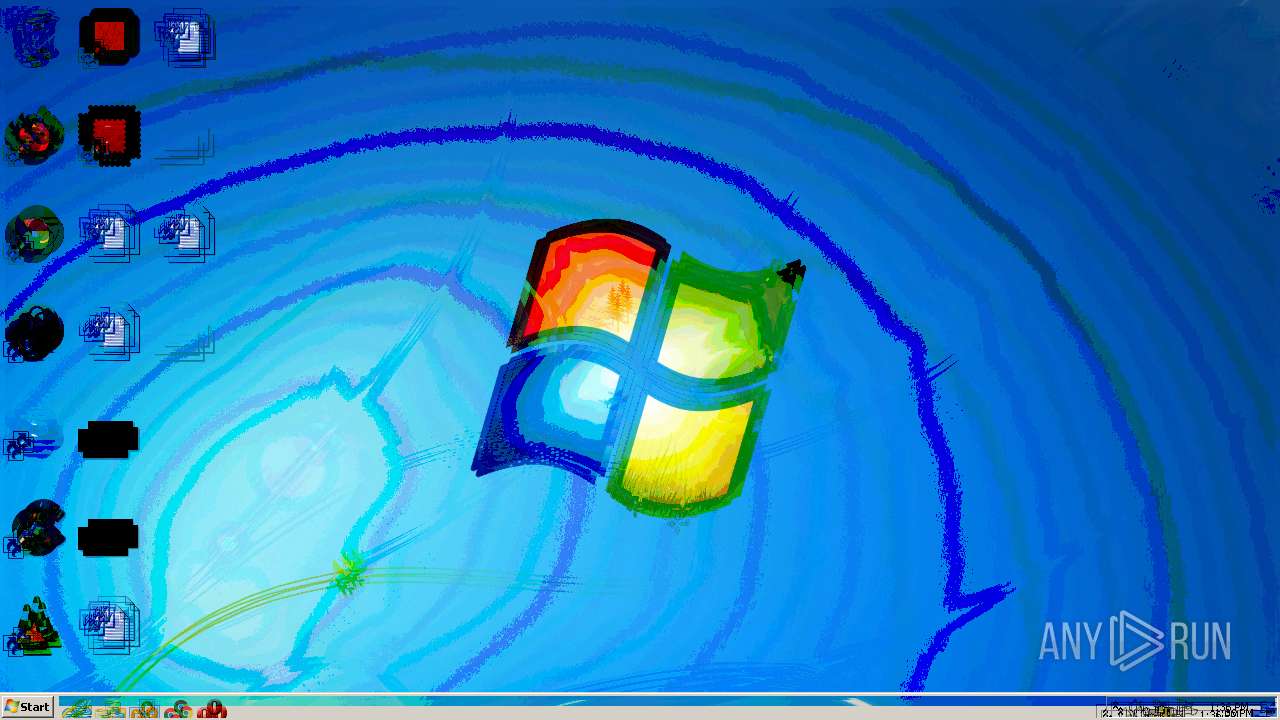
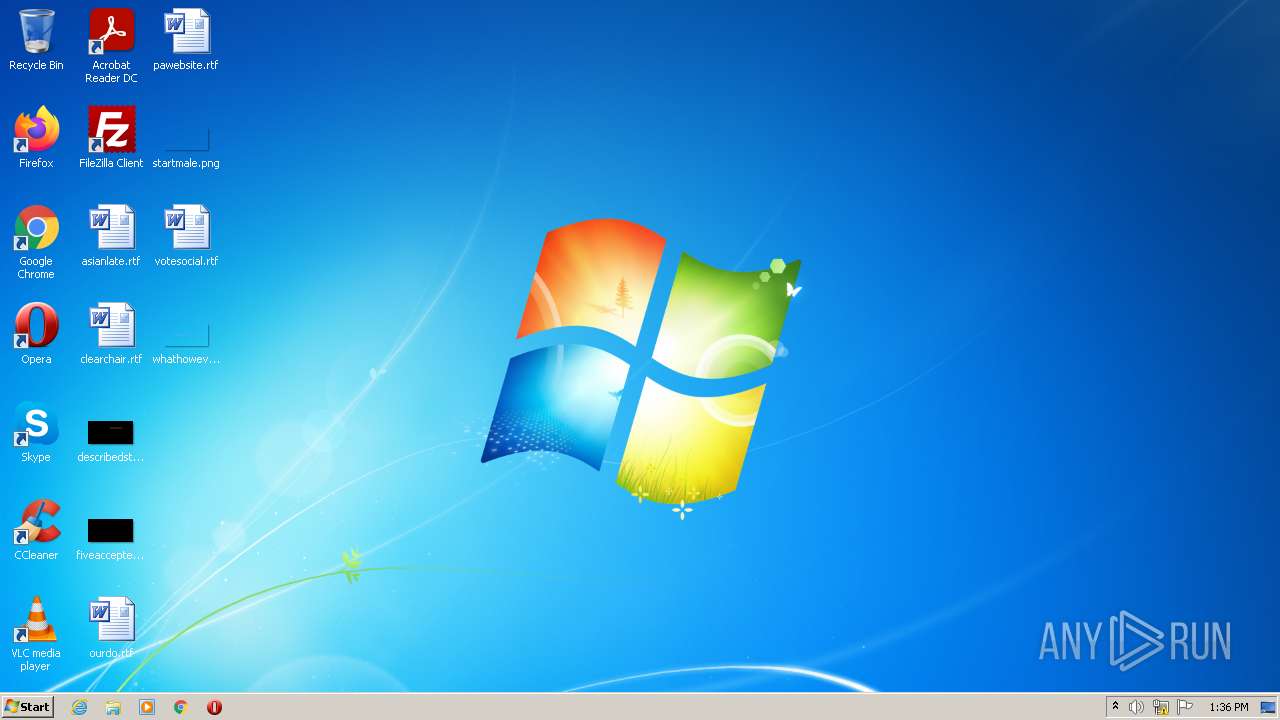
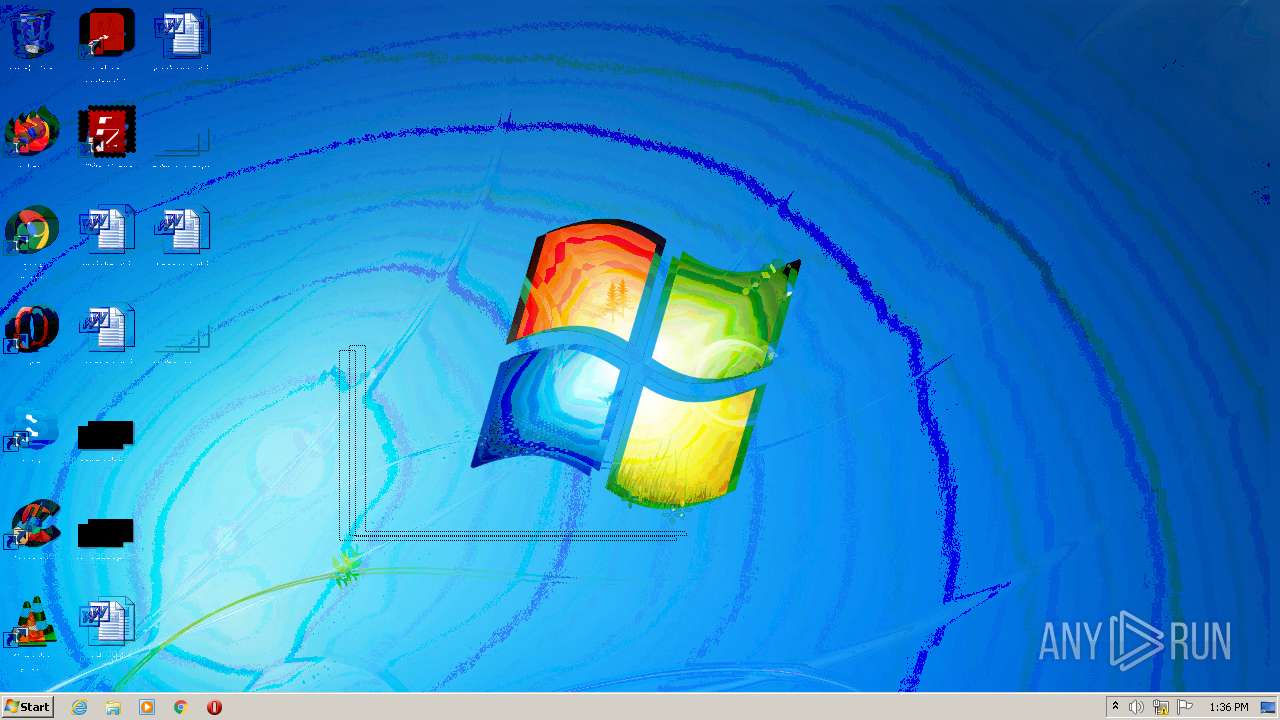
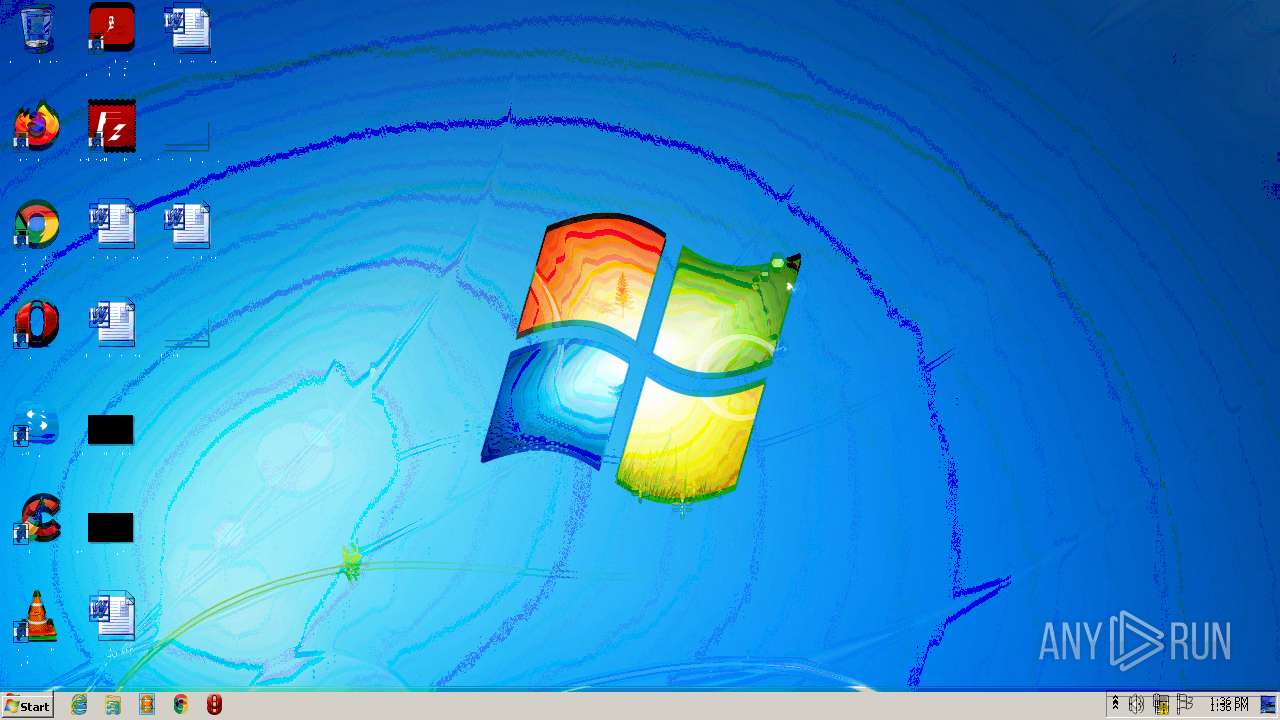
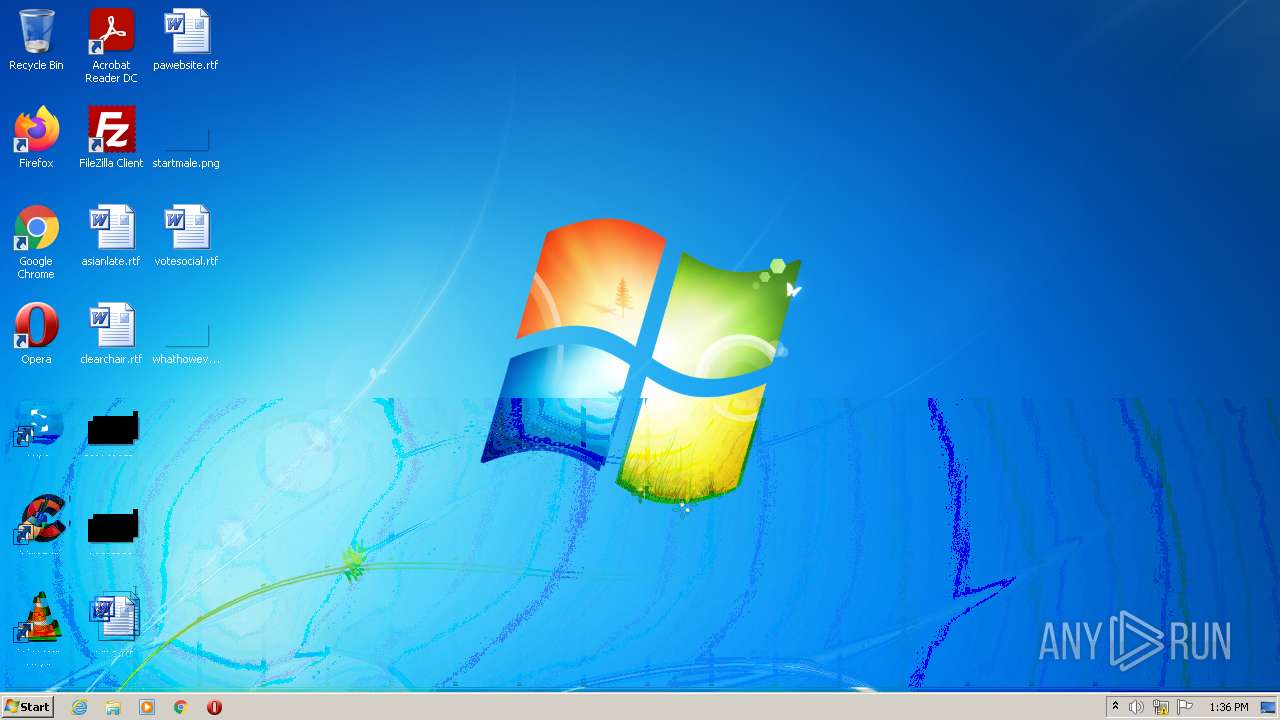
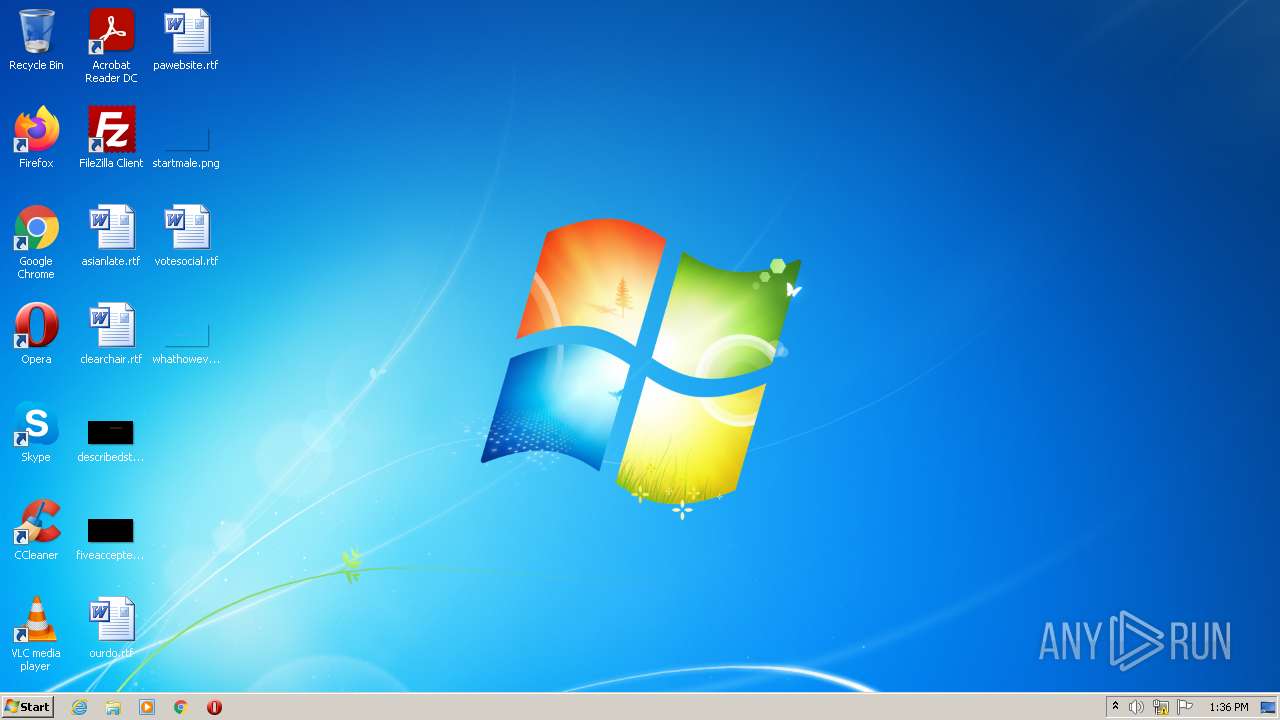
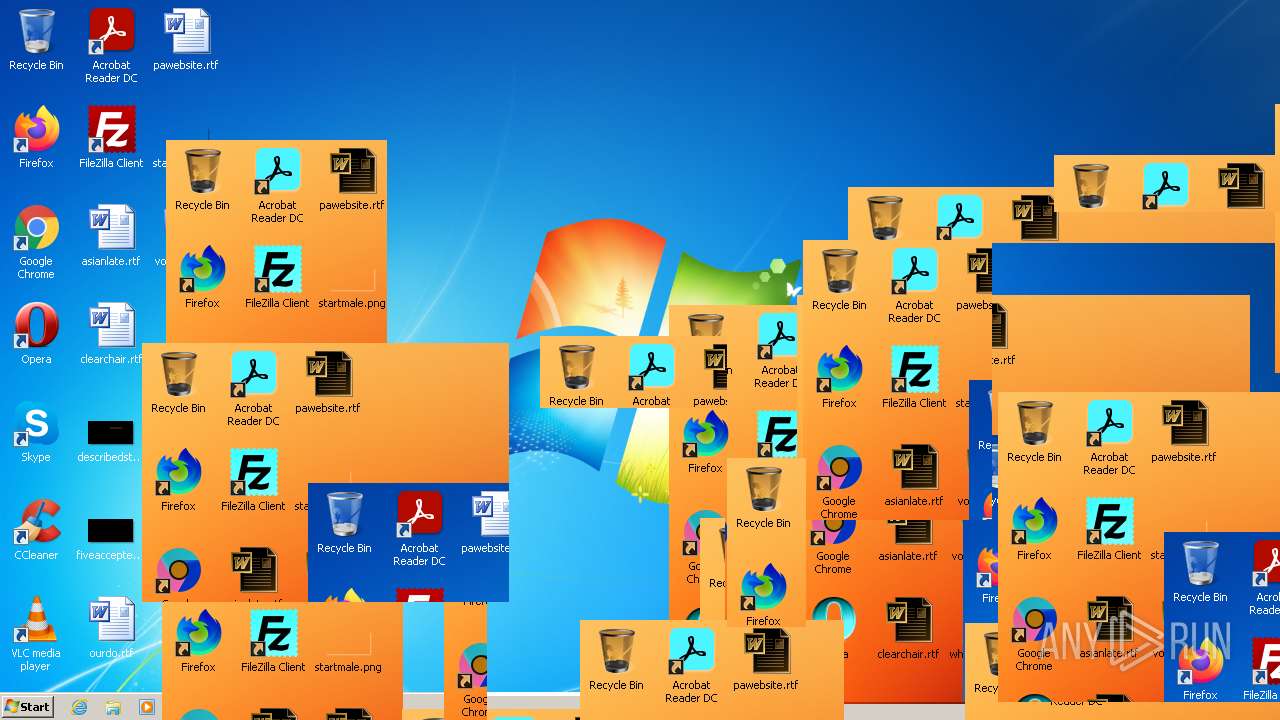
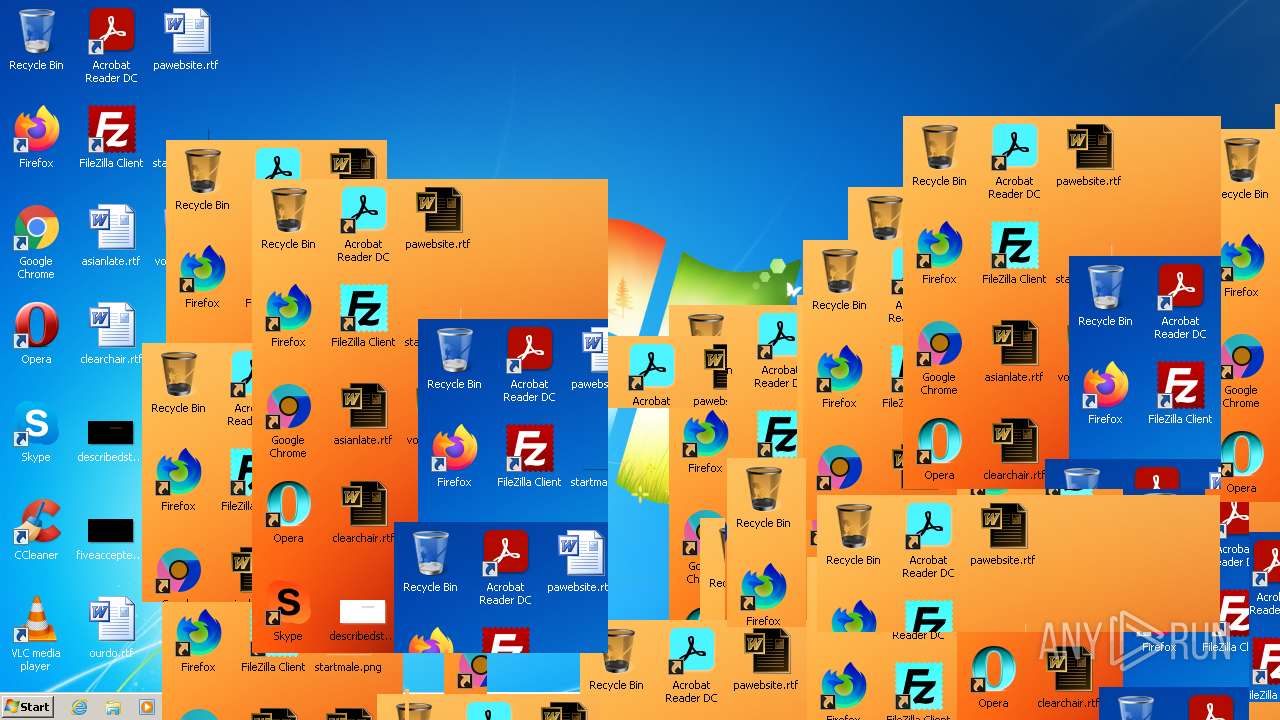
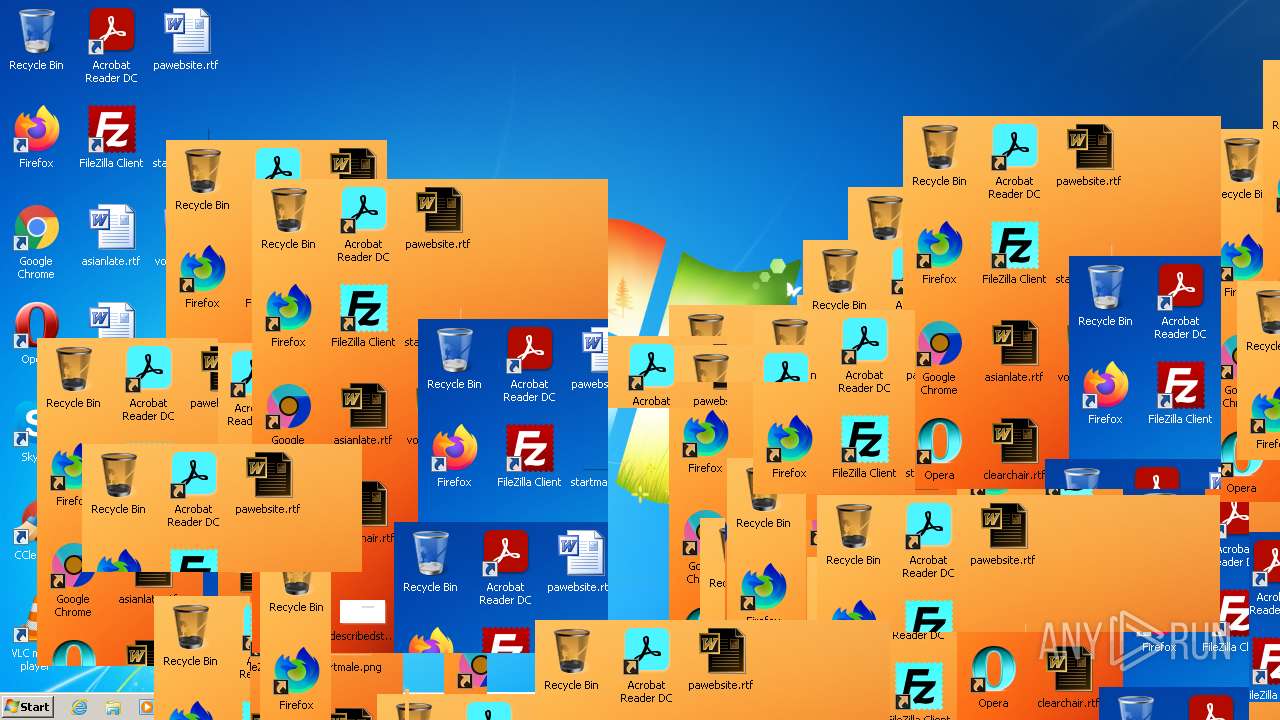
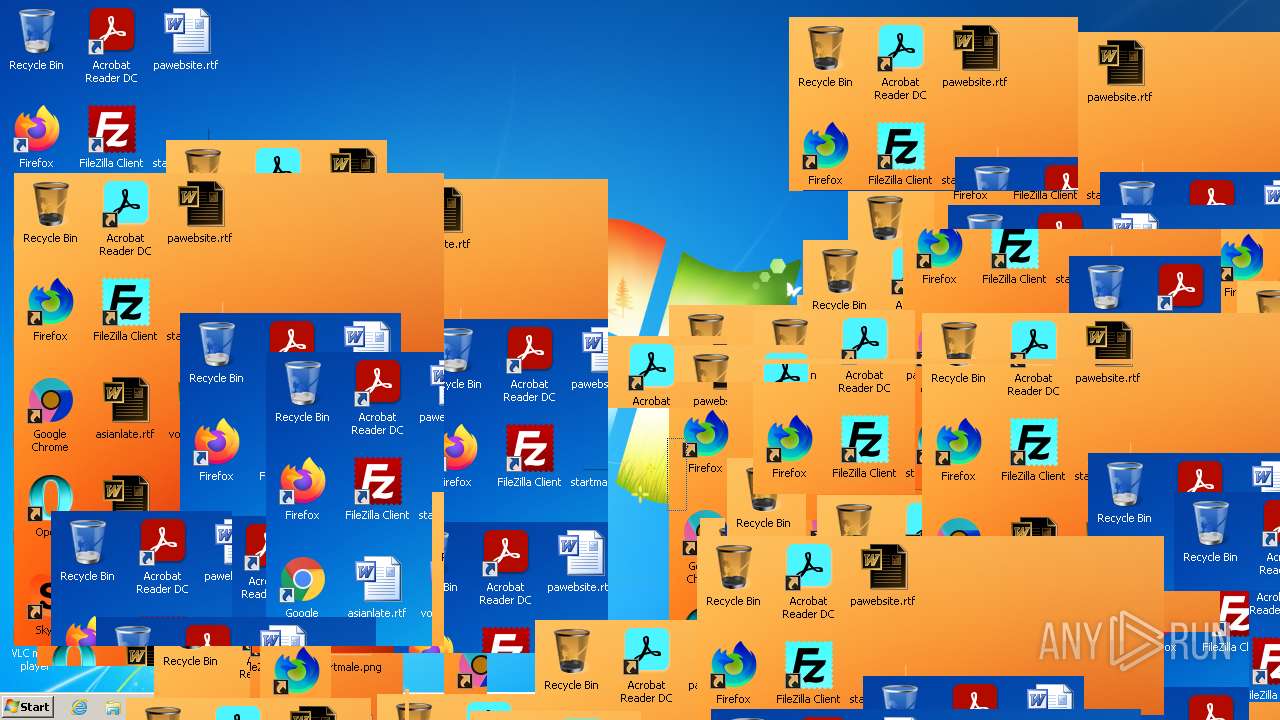
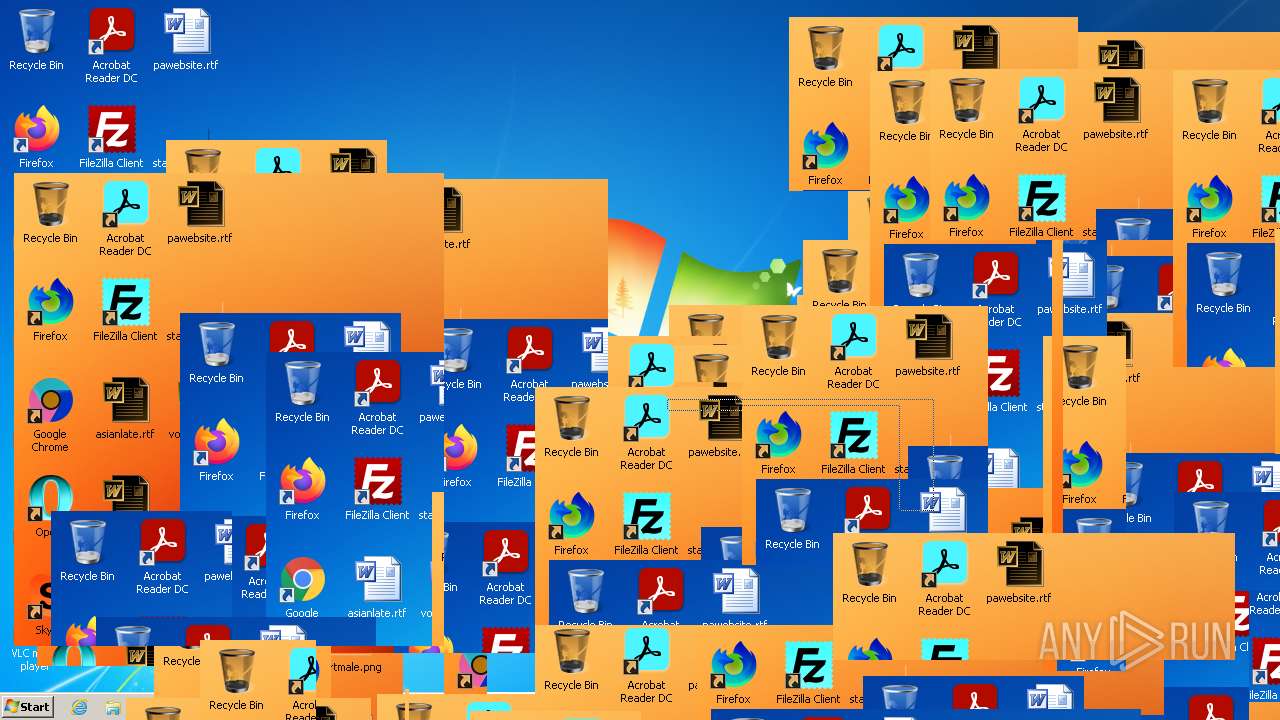
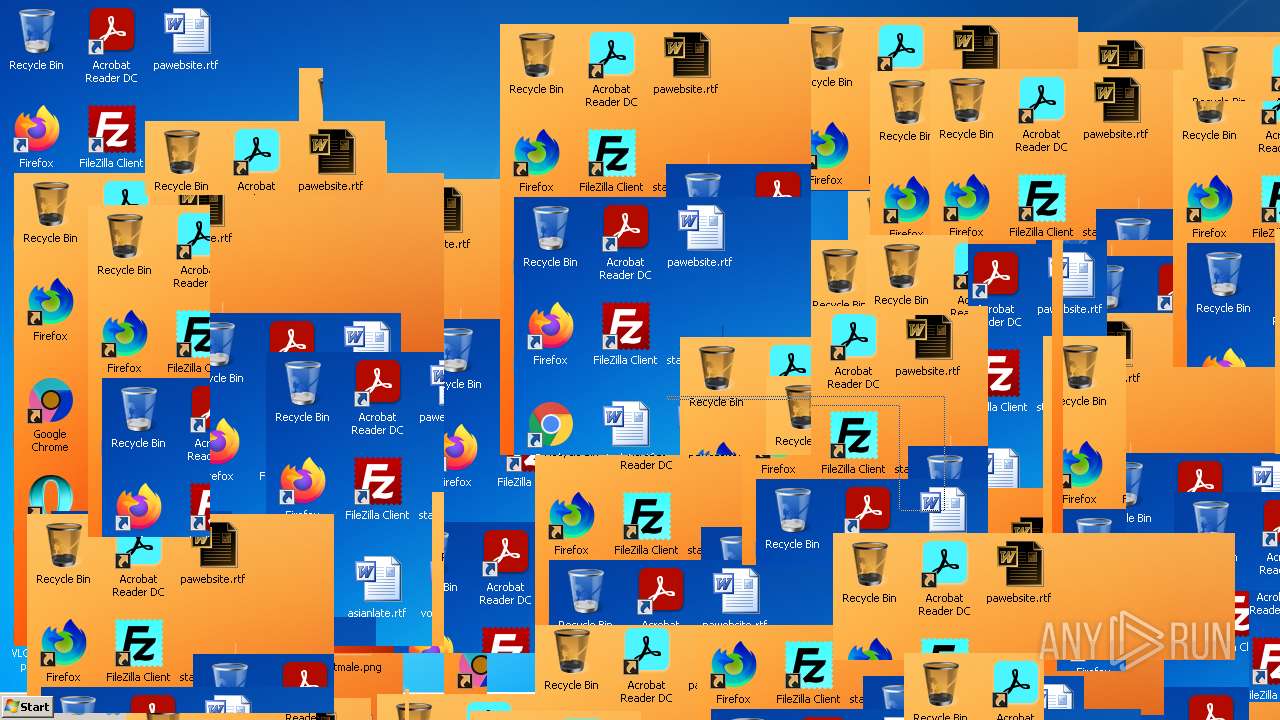
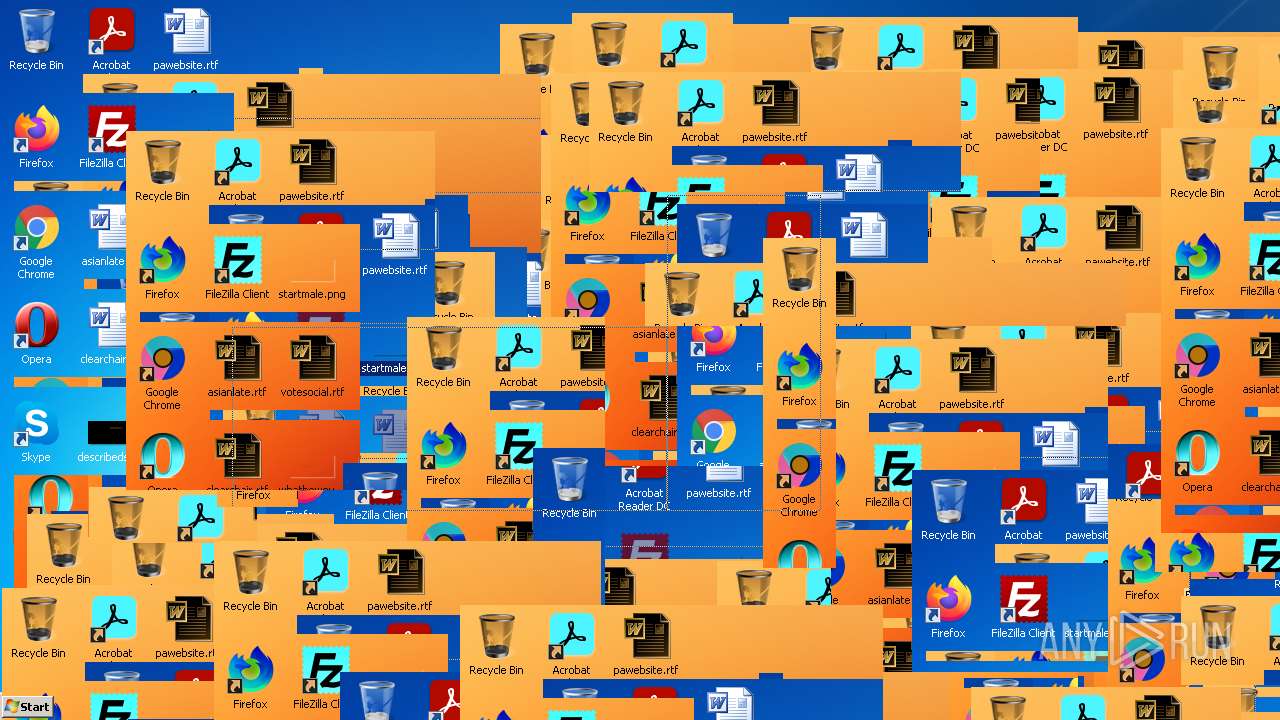
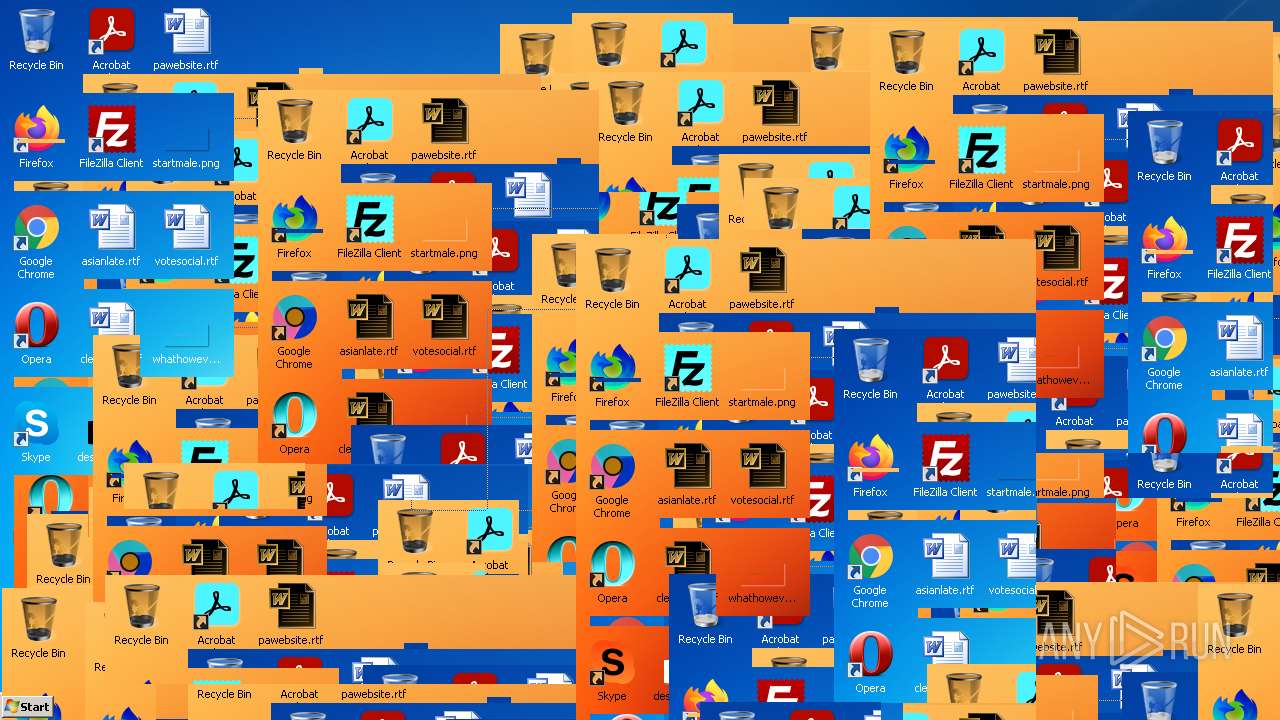
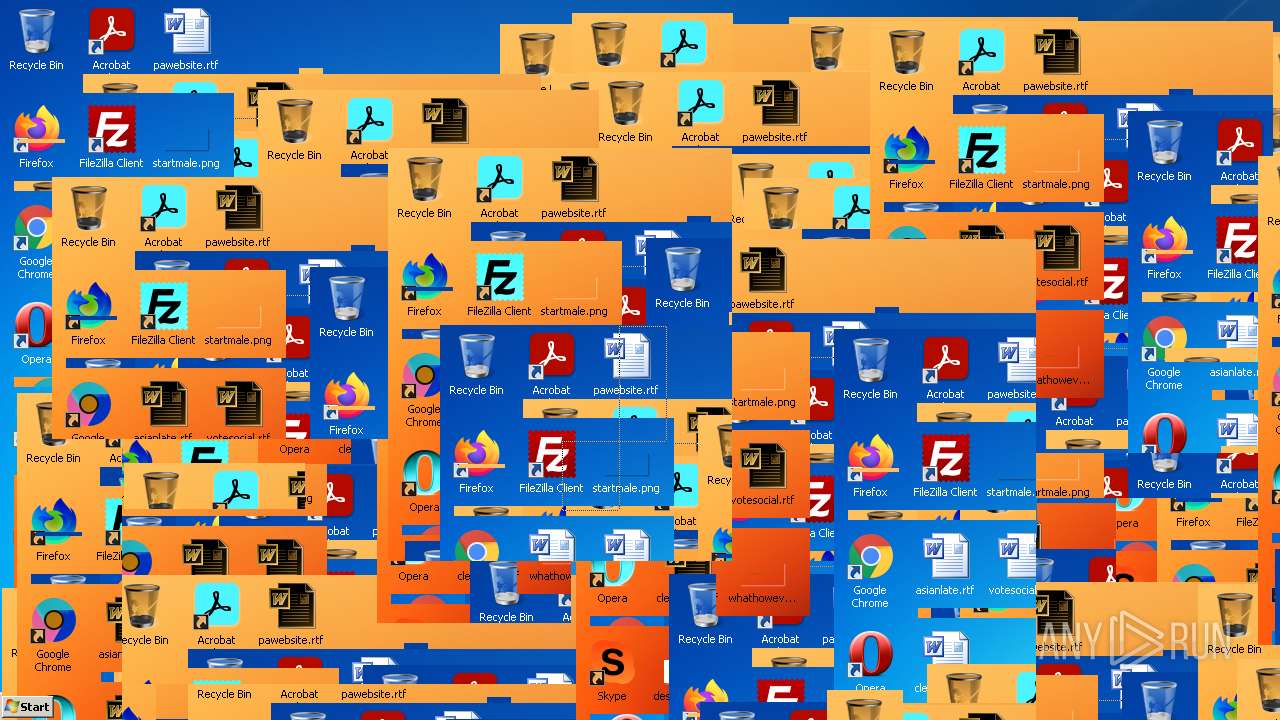
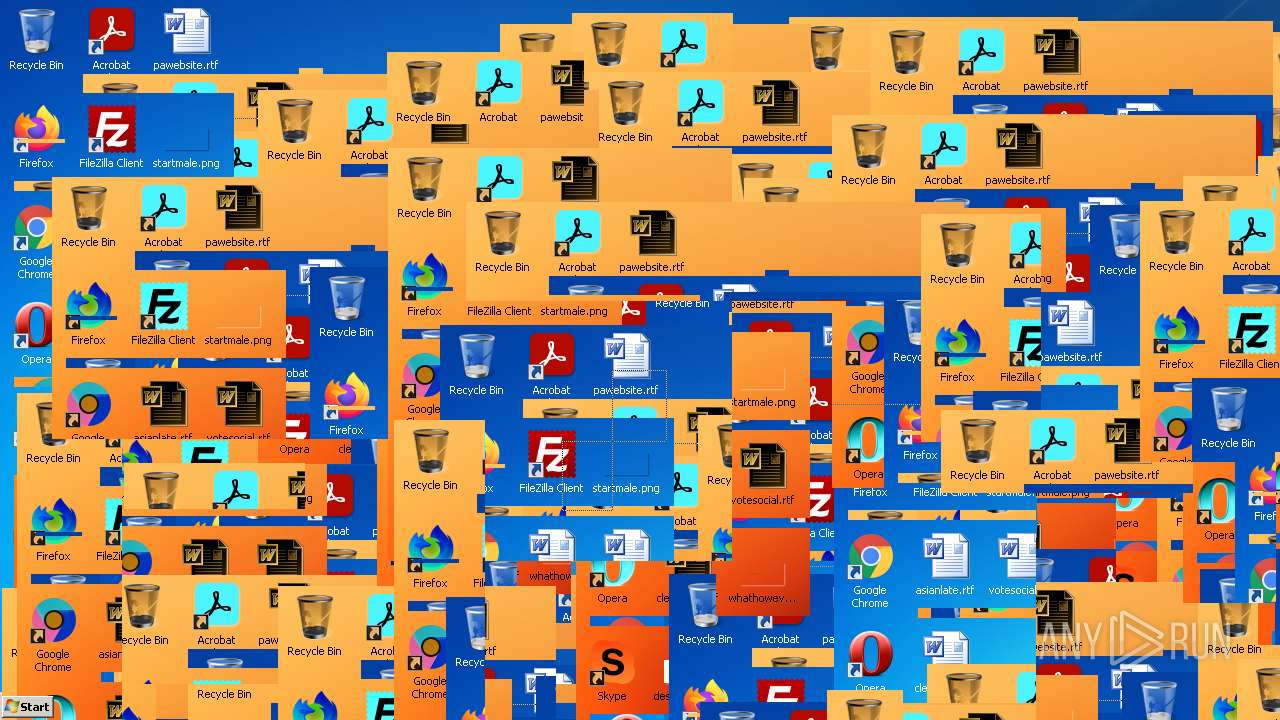
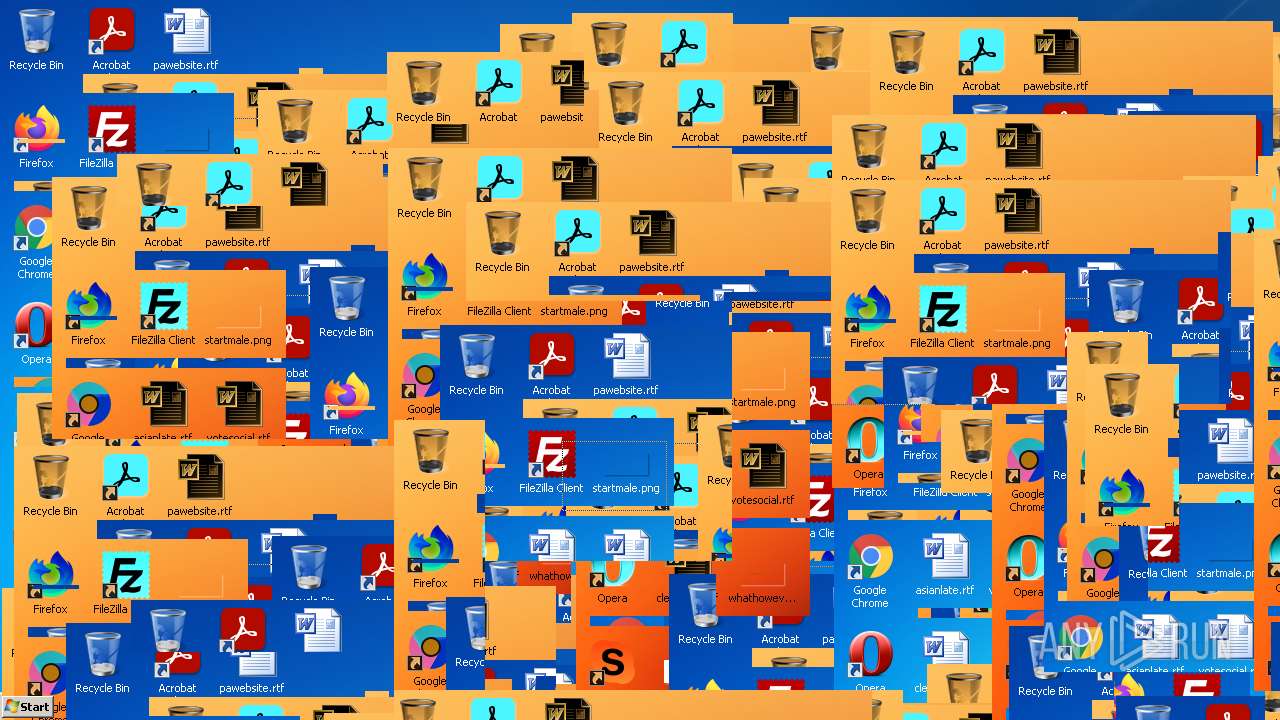
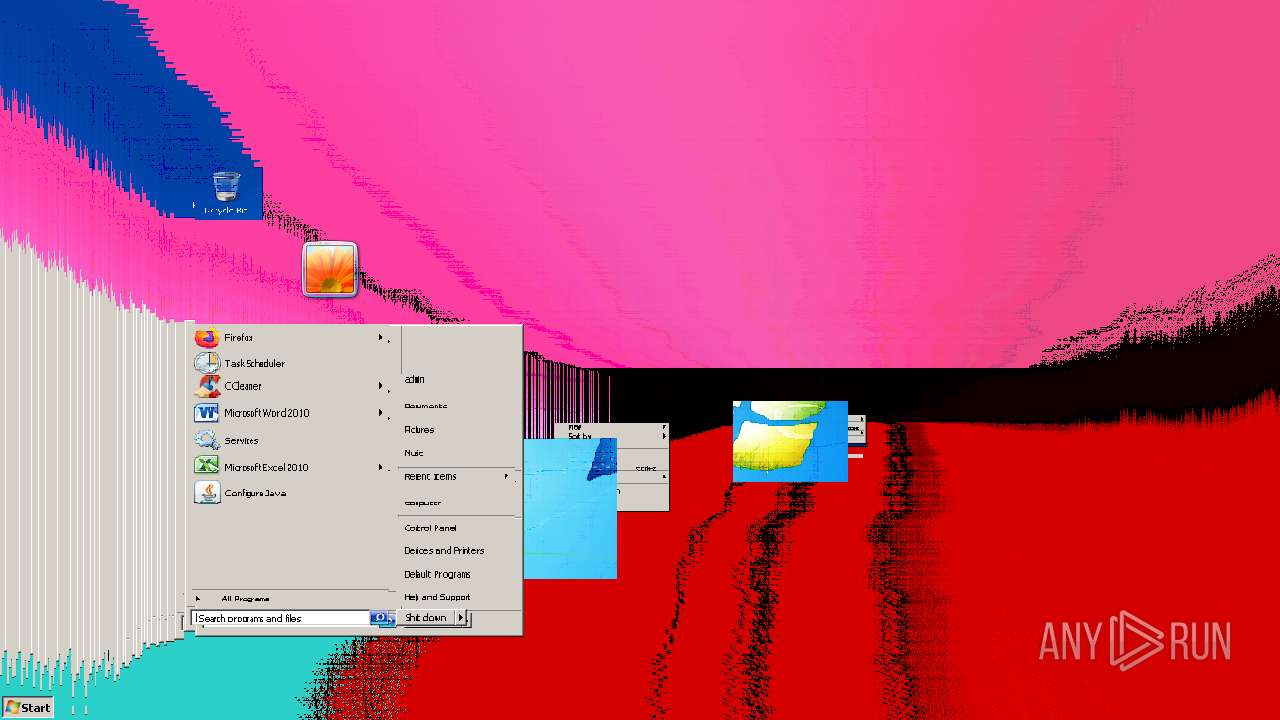
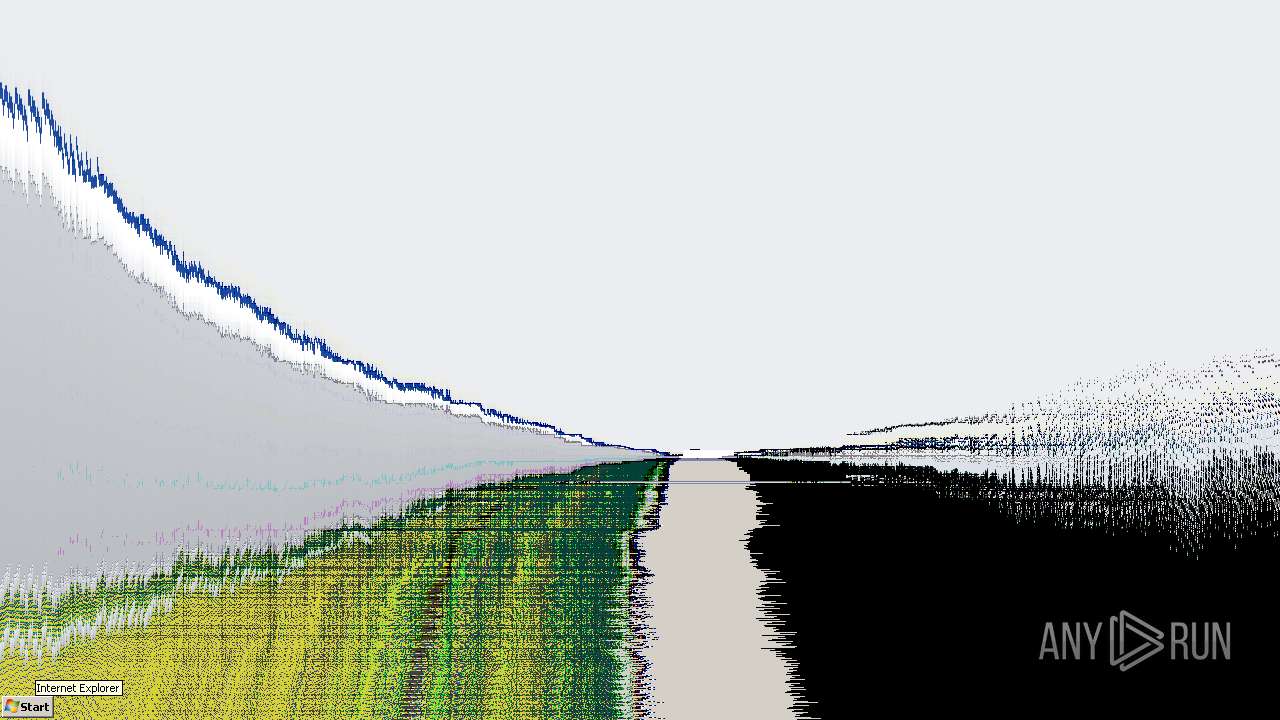
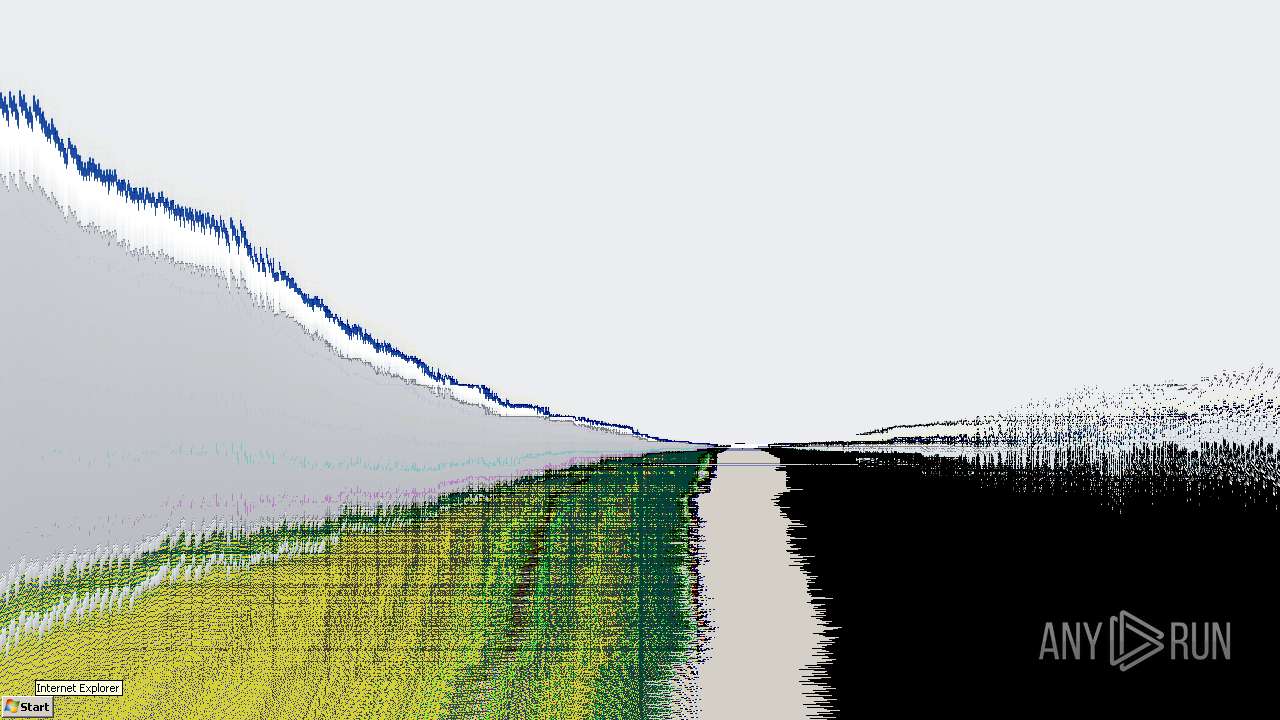
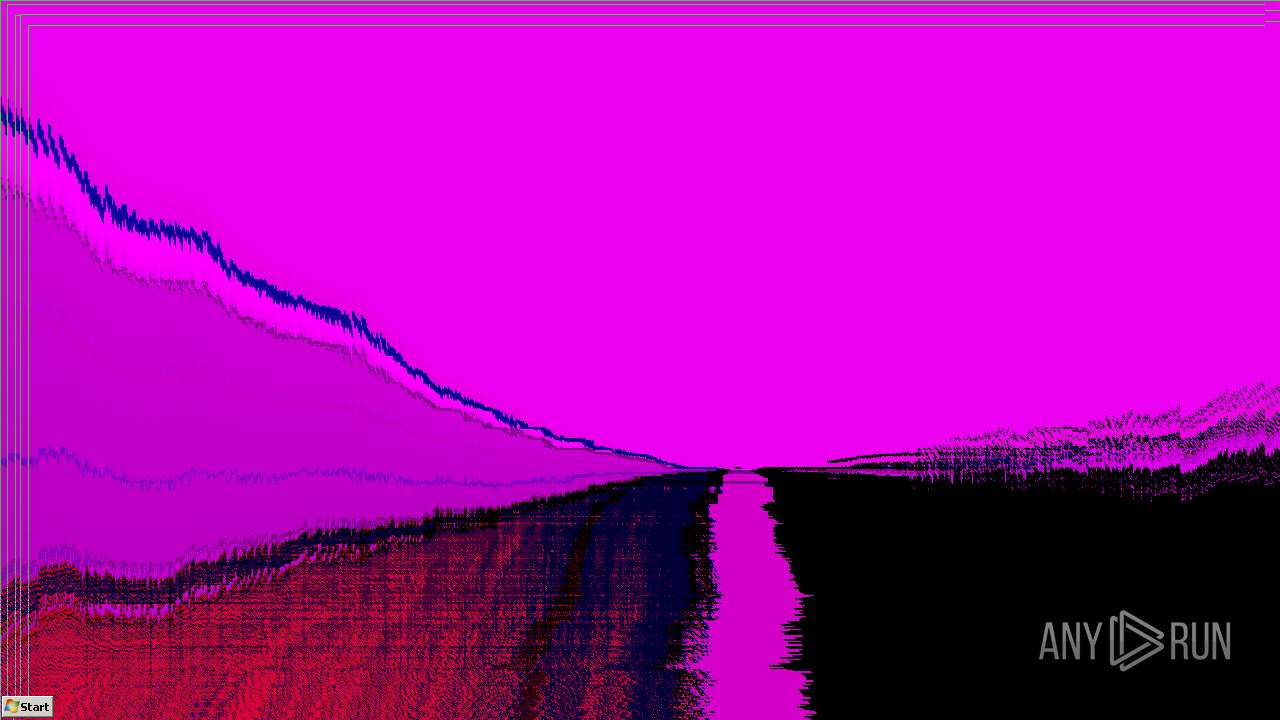
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1236 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,11649160545672780859,8257128829790975961,131072 --enable-features=PasswordImport --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2368 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1388 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1048,11649160545672780859,8257128829790975961,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --mojo-platform-channel-handle=1056 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1708 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,11649160545672780859,8257128829790975961,131072 --enable-features=PasswordImport --lang=en-US --instant-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1964 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1988 | "C:\Users\admin\AppData\Local\Temp\Clutt4.5.exe" | C:\Users\admin\AppData\Local\Temp\Clutt4.5.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Clutter Destructive Integrity Level: MEDIUM Description: Clutt4.5 Exit code: 3221226540 Version: 4.5.0.0 Modules
| |||||||||||||||
| 2100 | "C:\Windows\MBR.exe" | C:\Windows\MBR.exe | — | Clutt4.5.exe | |||||||||||
User: admin Integrity Level: HIGH Description: Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
| 2172 | SndVol.exe -f 46335089 6076 | C:\Windows\system32\SndVol.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Volume Mixer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2376 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=86.0.4240.198 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6e8ed988,0x6e8ed998,0x6e8ed9a4 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2524 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --field-trial-handle=1048,11649160545672780859,8257128829790975961,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --mojo-platform-channel-handle=1412 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2812 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\ourdo.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3044 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 3221225547 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
12 907
Read events
12 173
Write events
593
Delete events
141
Modification events
| (PID) Process: | (3368) Clutt4.5.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | DisableTaskMgr |
Value: 1 | |||
| (PID) Process: | (3368) Clutt4.5.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | DisableRegistryTools |
Value: 1 | |||
| (PID) Process: | (3368) Clutt4.5.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3368) Clutt4.5.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3368) Clutt4.5.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3368) Clutt4.5.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3044) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3044) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3044) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3044) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
Executable files
1
Suspicious files
13
Text files
47
Unknown types
23
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-62051490-BE4.pma | — | |
MD5:— | SHA256:— | |||
| 3368 | Clutt4.5.exe | C:\Windows\colorpcm.wav | wav | |
MD5:F8D70162455F4072A8C873056FAFC043 | SHA256:2FB81066AB0D4E4F0F371E0CC5BF89995E9C63265ACDA131F715761D14BF9495 | |||
| 3368 | Clutt4.5.exe | C:\Windows\glitch3pcm.wav | wav | |
MD5:550FAD71629A333C7169473E09DBFD36 | SHA256:0B40B129EFA7CCC3941F3E5163ED07883A2B9A7FC5DFB5EFC23818B1A2F4F48D | |||
| 3368 | Clutt4.5.exe | C:\Windows\glitch2pcm.wav | wav | |
MD5:23E1CD34DC48A5DF7851E54649A0F892 | SHA256:90E3E0FAC8083D462471088BD422FF20DF6672C07D2D8D4665D03A5F93D7D0FC | |||
| 3368 | Clutt4.5.exe | C:\Windows\glitchpcm.wav | wav | |
MD5:1A61882B77969DC665281D970B4E29BD | SHA256:51682D617603883C106D3DD435F819D150F7922B0999F60A65248EE983045695 | |||
| 3044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 3368 | Clutt4.5.exe | C:\Windows\scrasepcm.wav | wav | |
MD5:CAC95825D6F78117E3A75C182CDB6631 | SHA256:A519FE2A9557D353270166EEFEE1E0D47FB5868587769099B0341AA1F29F5BFA | |||
| 3368 | Clutt4.5.exe | C:\Windows\glitch5pcm.wav | wav | |
MD5:4805BEC33E1C0EAFA7CBE5B090F7C73C | SHA256:8AD9F9968261B733447FD592065EEA837EA17E783A294A0522230131828F3905 | |||
| 3368 | Clutt4.5.exe | C:\Windows\rainbowpcm.wav | wav | |
MD5:DD015164D49E41575CB5132C333AD211 | SHA256:C5174A231ABA688E6BB129AE6A4AF50FB9D197C74B010E026E72175BA6500687 | |||
| 3368 | Clutt4.5.exe | C:\Windows\shakepcm.wav | wav | |
MD5:ADE521FB28D0DA0AA9184AE786FA61FD | SHA256:06DD2C7DDB1C107E4C1D31FABA1ABCFF70BE6F53BF743110C22B25FC669A2ACA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
9
DNS requests
8
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2524 | chrome.exe | 142.250.186.106:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2524 | chrome.exe | 142.250.185.99:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2524 | chrome.exe | 142.250.186.77:443 | accounts.google.com | Google Inc. | US | suspicious |
2524 | chrome.exe | 142.250.186.35:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2524 | chrome.exe | 142.250.181.227:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2524 | chrome.exe | 142.250.185.228:443 | www.google.com | Google Inc. | US | whitelisted |
2524 | chrome.exe | 142.250.184.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2524 | chrome.exe | 172.217.18.110:443 | clients2.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.google.com |
| malicious |
clients2.google.com |
| whitelisted |
accounts.google.com |
| shared |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |