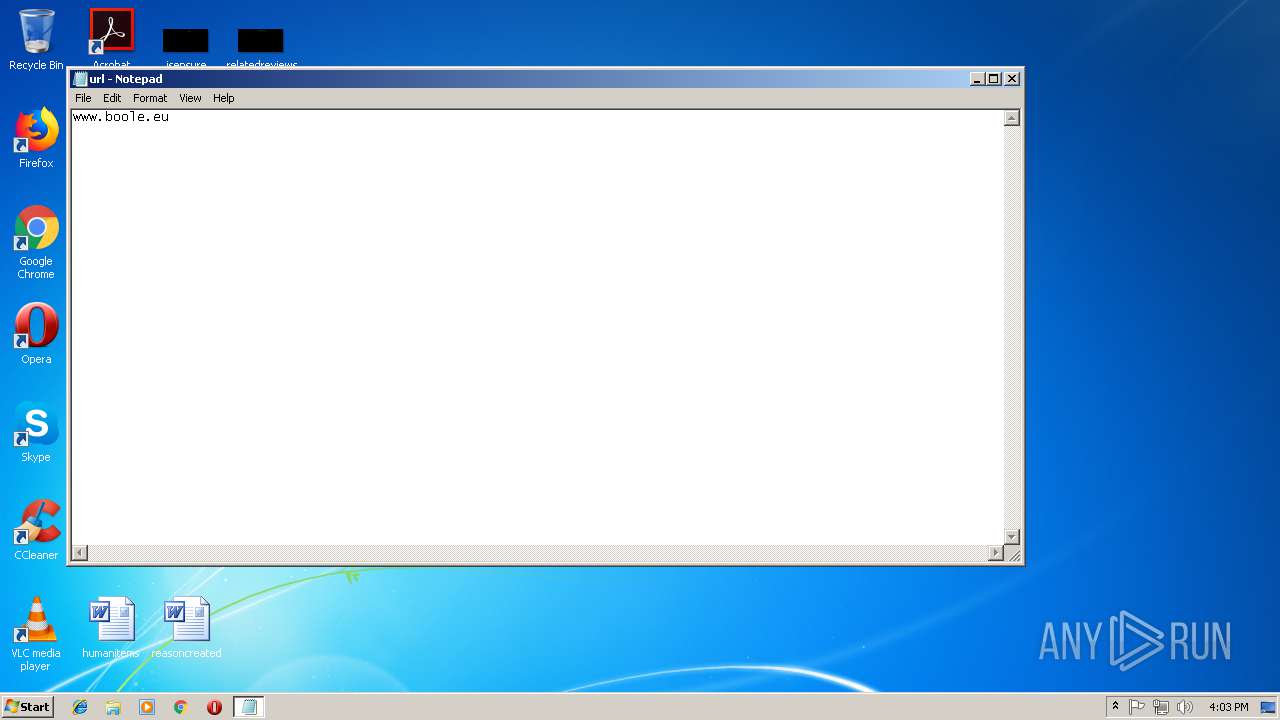
| File name: | url.txt |
| Full analysis: | https://app.any.run/tasks/1adfb8a5-88ea-447b-996b-f20b766c8e8e |
| Verdict: | Malicious activity |
| Analysis date: | September 19, 2018, 15:02:46 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with no line terminators |
| MD5: | D567C75F12CD23822A02E918F0EAF169 |
| SHA1: | 0155ECC62B98945568C846C2446798A6A5BF225D |
| SHA256: | BC30219A56D09E7DB23E5D30A40B942C2762B2465548A47C674E65C8FBA2ABA0 |
| SSDEEP: | 3:ErAp:R |
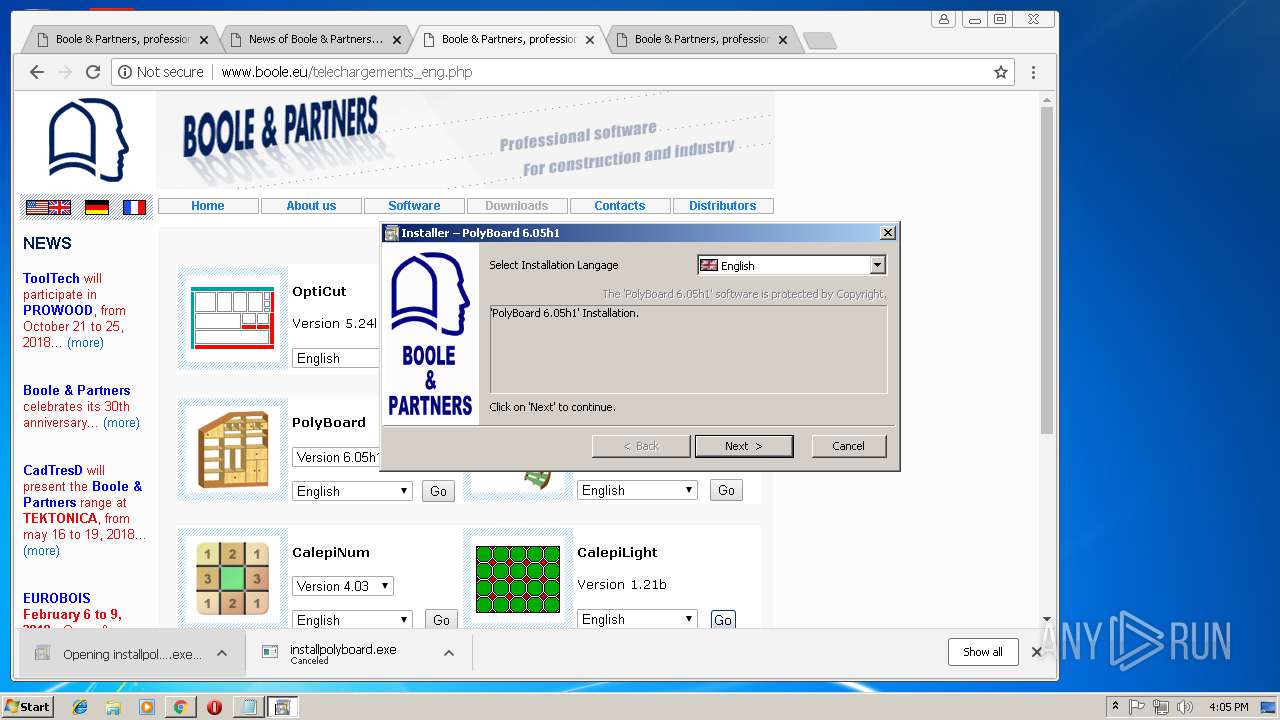
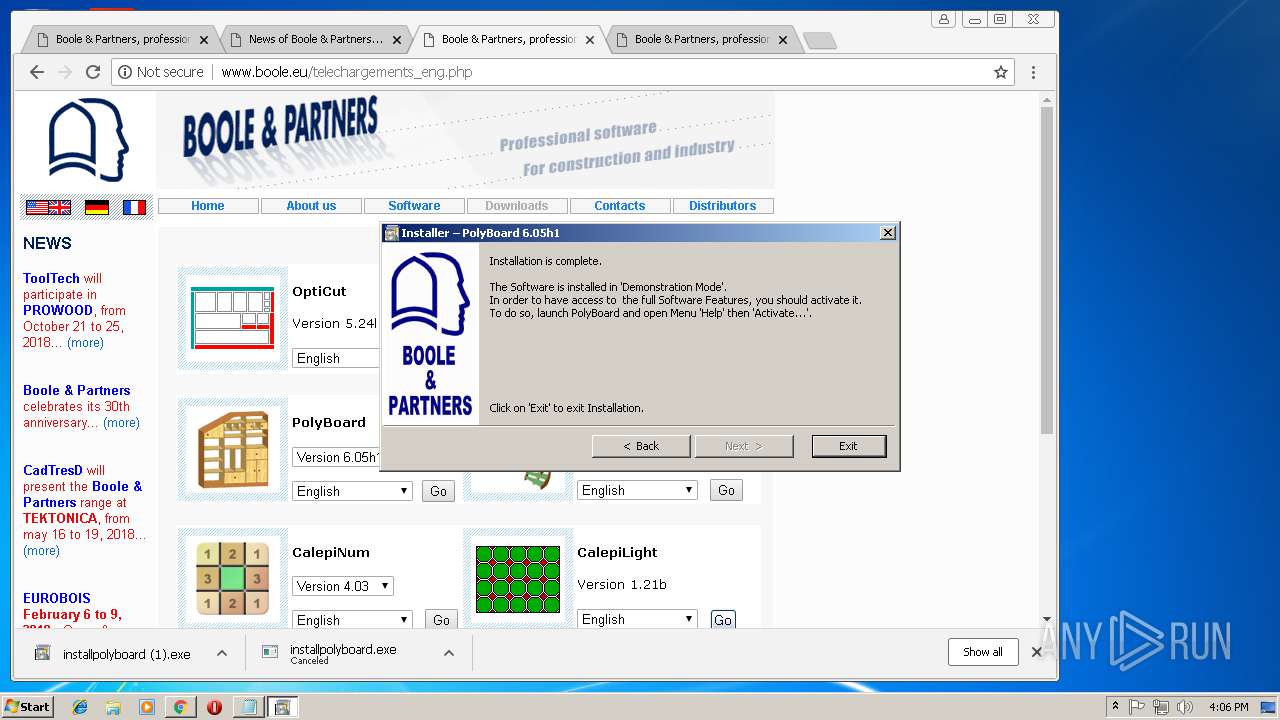
MALICIOUS
Application was dropped or rewritten from another process
- installpolyboard (1).exe (PID: 2148)
- installpolyboard (1).exe (PID: 1216)
- Polyboard.exe (PID: 3324)
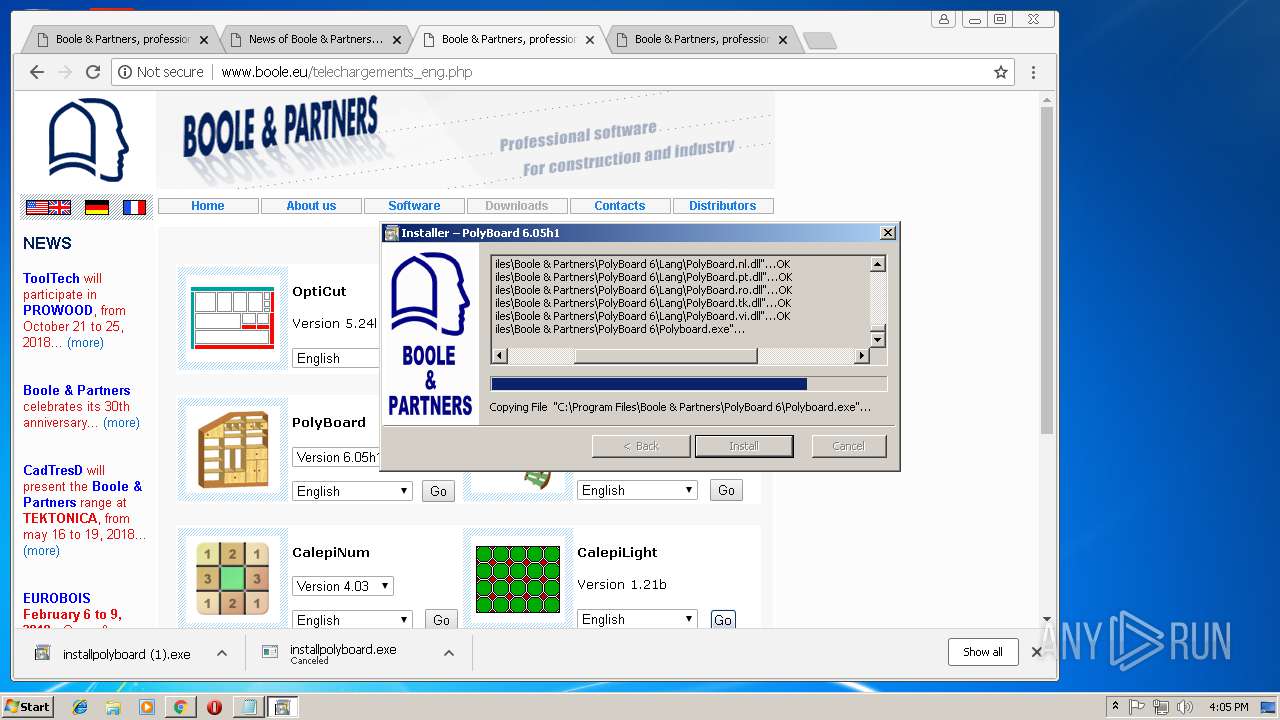
Loads dropped or rewritten executable
- installpolyboard (1).exe (PID: 2148)
- Polyboard.exe (PID: 3324)
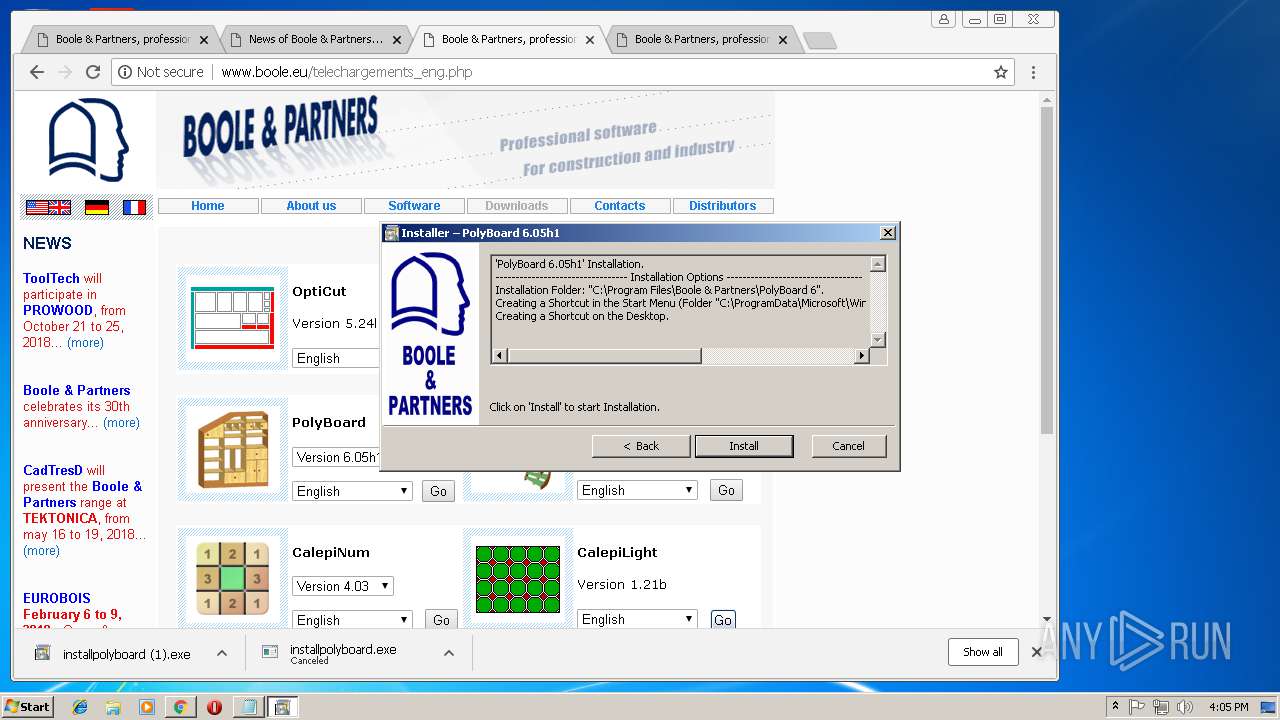
SUSPICIOUS
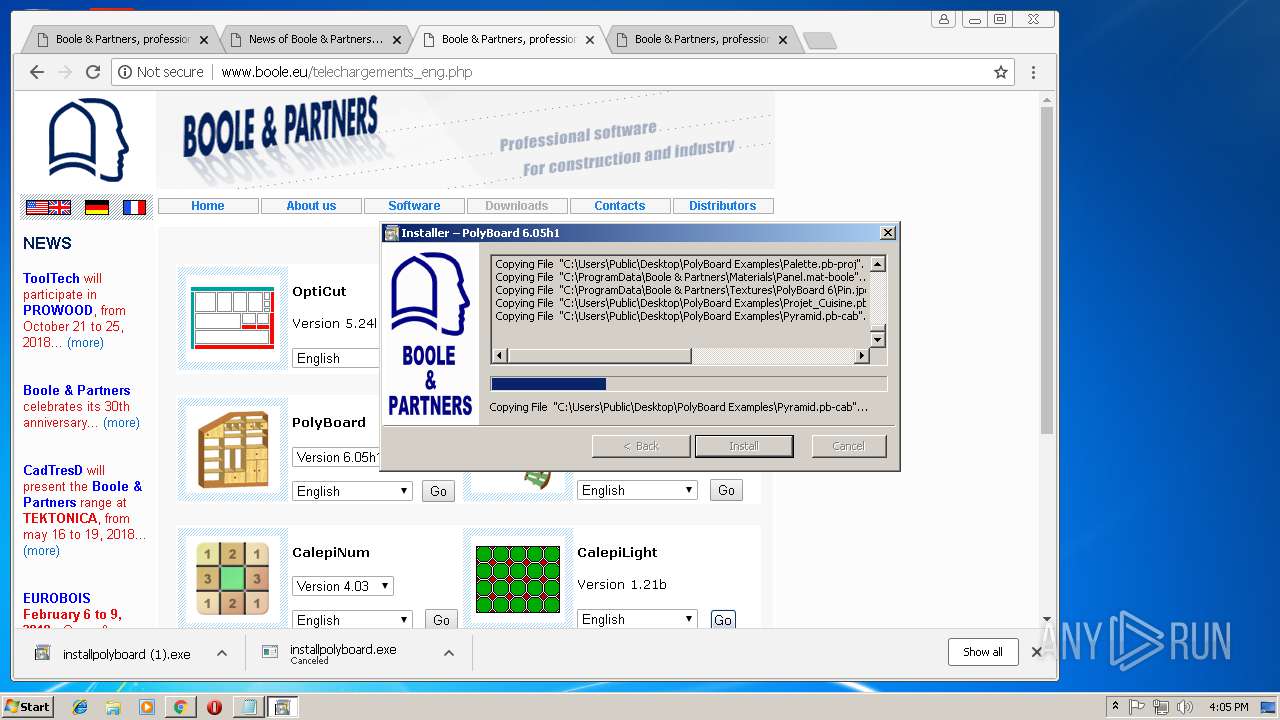
Executable content was dropped or overwritten
- chrome.exe (PID: 3444)
- installpolyboard (1).exe (PID: 2148)
Creates files in the program directory
- installpolyboard (1).exe (PID: 2148)
Creates files in the user directory
- installpolyboard (1).exe (PID: 2148)
Creates files in the Windows directory
- installpolyboard (1).exe (PID: 2148)
Creates or modifies windows services
- installpolyboard (1).exe (PID: 2148)
- DllHost.exe (PID: 1384)
Searches for installed software
- installpolyboard (1).exe (PID: 2148)
- DllHost.exe (PID: 1384)
Removes files from Windows directory
- installpolyboard (1).exe (PID: 2148)
Creates a software uninstall entry
- installpolyboard (1).exe (PID: 2148)
Modifies the open verb of a shell class
- Polyboard.exe (PID: 3324)
INFO
Reads Internet Cache Settings
- chrome.exe (PID: 3444)
Application launched itself
- chrome.exe (PID: 3444)
Dropped object may contain Bitcoin addresses
- installpolyboard (1).exe (PID: 2148)
Low-level read access rights to disk partition
- vssvc.exe (PID: 280)
Creates files in the user directory
- chrome.exe (PID: 3444)
Creates or modifies windows services
- vssvc.exe (PID: 280)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
64
Monitored processes
25
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 280 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1012 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=844,4444055486697290461,114004481875036964,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=522D367A4832359A3BA835D7F0C4A2DD --mojo-platform-channel-handle=896 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1192 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=844,4444055486697290461,114004481875036964,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=85C85780E970AD2248FAA32404DBA6BC --mojo-platform-channel-handle=992 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
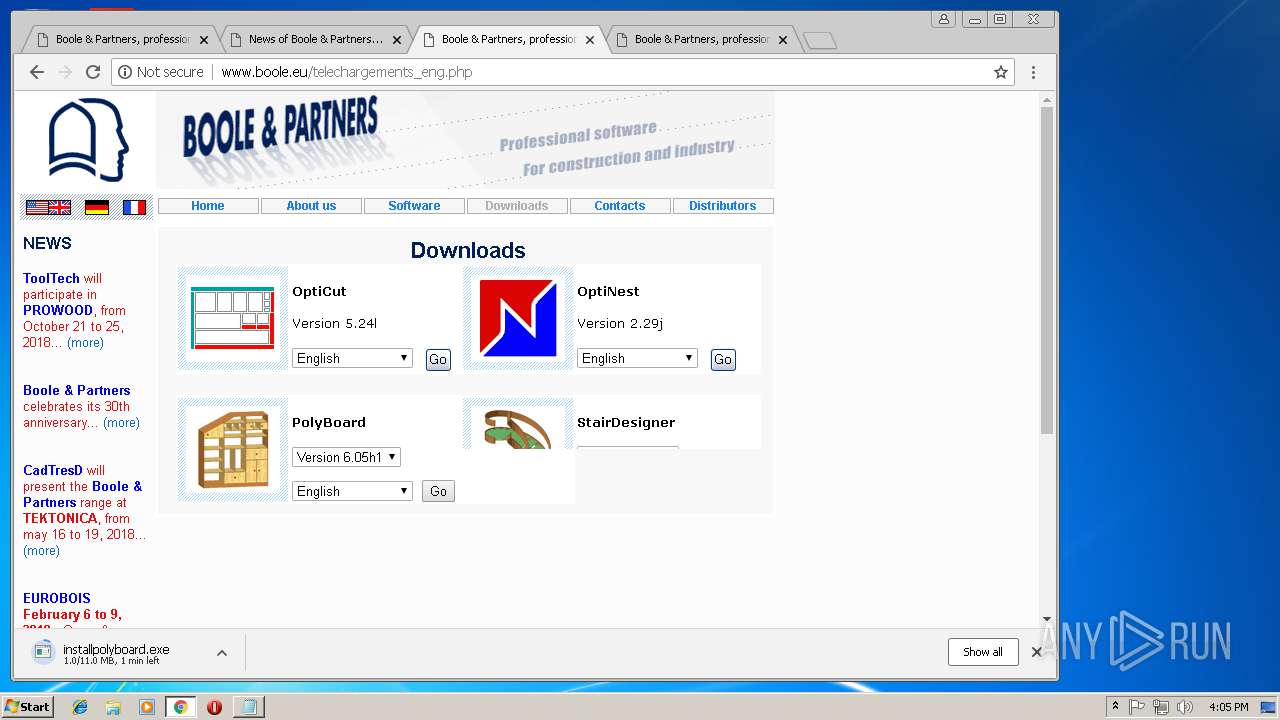
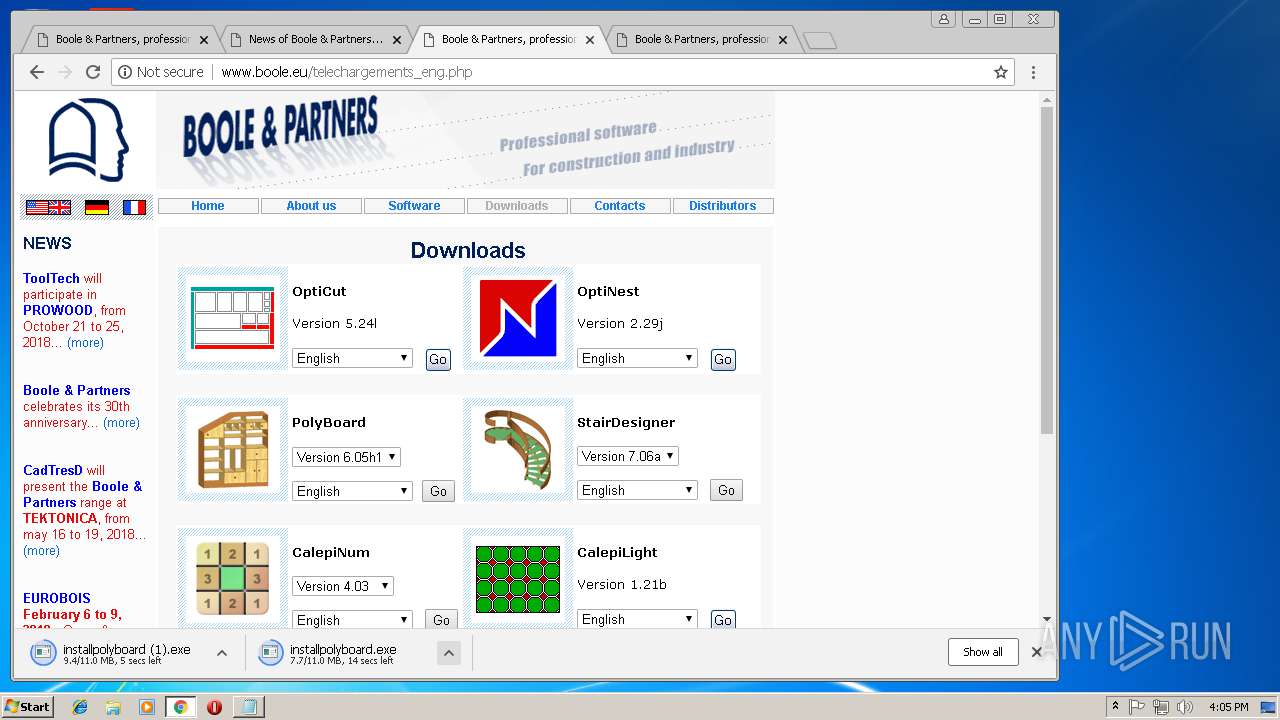
| 1216 | "C:\Users\admin\Downloads\installpolyboard (1).exe" | C:\Users\admin\Downloads\installpolyboard (1).exe | — | chrome.exe | |||||||||||
User: admin Company: Boole & Partners Integrity Level: MEDIUM Description: Installeur PolyBoard 6.05h1 Exit code: 3221226540 Version: 2.2.0.3 Modules
| |||||||||||||||
| 1384 | C:\Windows\system32\DllHost.exe /Processid:{F32D97DF-E3E5-4CB9-9E3E-0EB5B4E49801} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1672 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=844,4444055486697290461,114004481875036964,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=2ED712A1D2B5AEE25D1F792354749B40 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2ED712A1D2B5AEE25D1F792354749B40 --renderer-client-id=7 --mojo-platform-channel-handle=3760 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2116 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=844,4444055486697290461,114004481875036964,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=E31F4DE5F482C84D15CFF489F5429B99 --mojo-platform-channel-handle=2640 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2148 | "C:\Users\admin\Downloads\installpolyboard (1).exe" | C:\Users\admin\Downloads\installpolyboard (1).exe | chrome.exe | ||||||||||||
User: admin Company: Boole & Partners Integrity Level: HIGH Description: Installeur PolyBoard 6.05h1 Exit code: 0 Version: 2.2.0.3 Modules
| |||||||||||||||
| 2312 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=68.0.3440.106 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x702200b0,0x702200c0,0x702200cc | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2344 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=844,4444055486697290461,114004481875036964,131072 --enable-features=PasswordImport --service-pipe-token=0D265E19F091C132540187AD8D8B8A63 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=0D265E19F091C132540187AD8D8B8A63 --renderer-client-id=3 --mojo-platform-channel-handle=2092 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
1 434
Read events
1 125
Write events
305
Delete events
4
Modification events
| (PID) Process: | (2760) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3444-13181843021876125 |
Value: 259 | |||
| (PID) Process: | (3444) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3444) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3444) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3444) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3444) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3444) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2524-13180983711809570 |
Value: 0 | |||
| (PID) Process: | (3444) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3444) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3444-13181843021876125 |
Value: 259 | |||
| (PID) Process: | (3444) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
24
Suspicious files
80
Text files
190
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3444 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3444 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF44887e.TMP | — | |
MD5:— | SHA256:— | |||
| 3444 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000012.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3444 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000012.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3444 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\16e797a4-09a7-4f38-8464-ab20a0c4abe3.tmp | — | |
MD5:— | SHA256:— | |||
| 3444 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3444 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\LOG.old~RF44887e.TMP | text | |
MD5:— | SHA256:— | |||
| 3444 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\IndexedDB\https_www.google.de_0.indexeddb.leveldb\000001.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3444 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3444 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
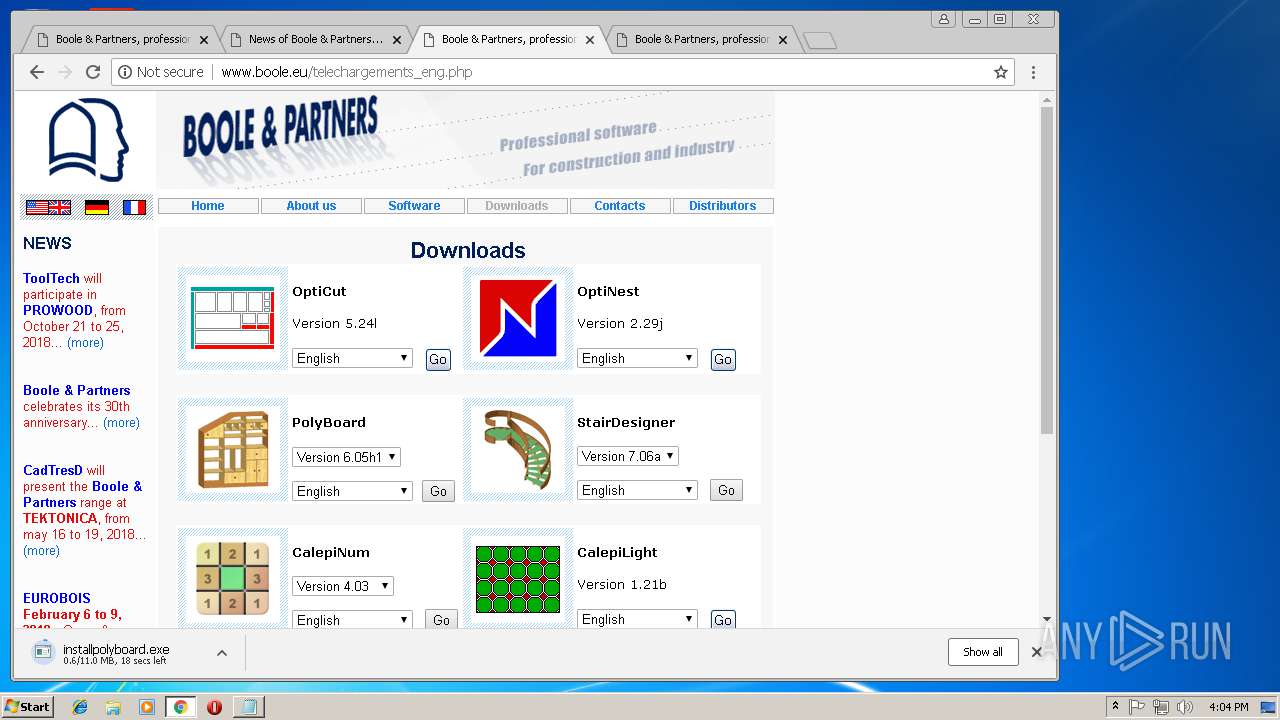
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
29
TCP/UDP connections
52
DNS requests
15
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
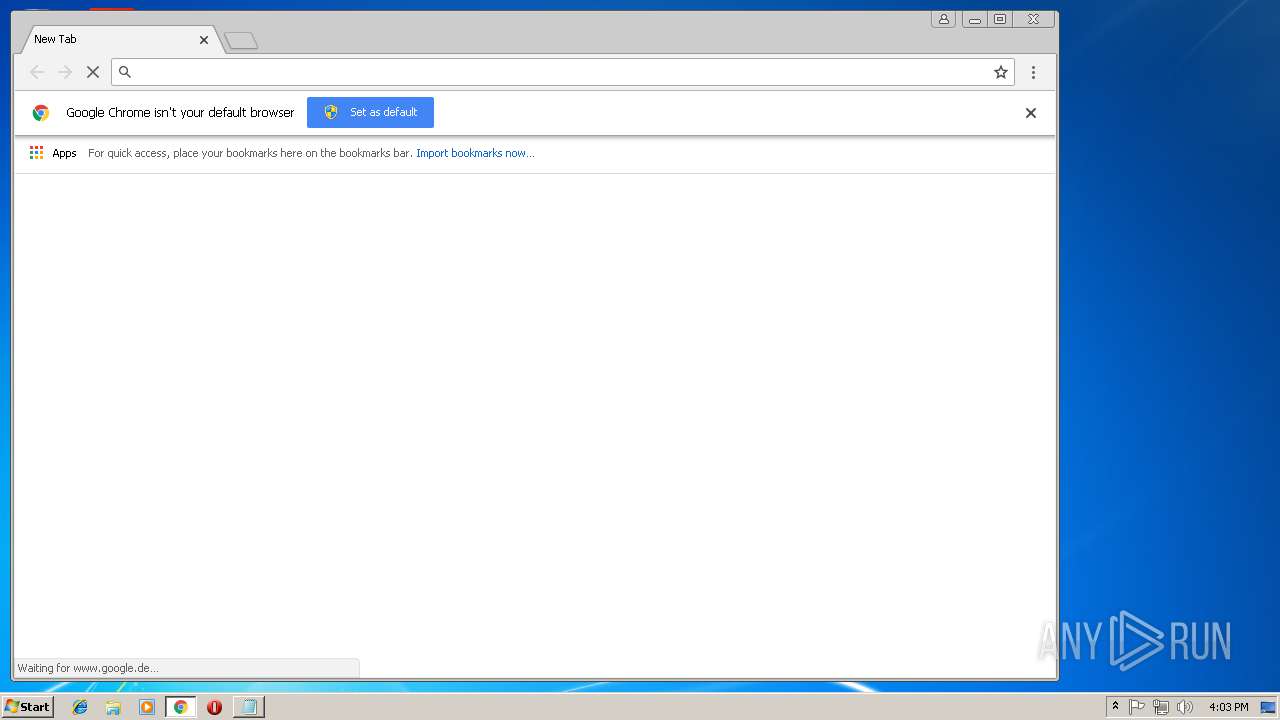
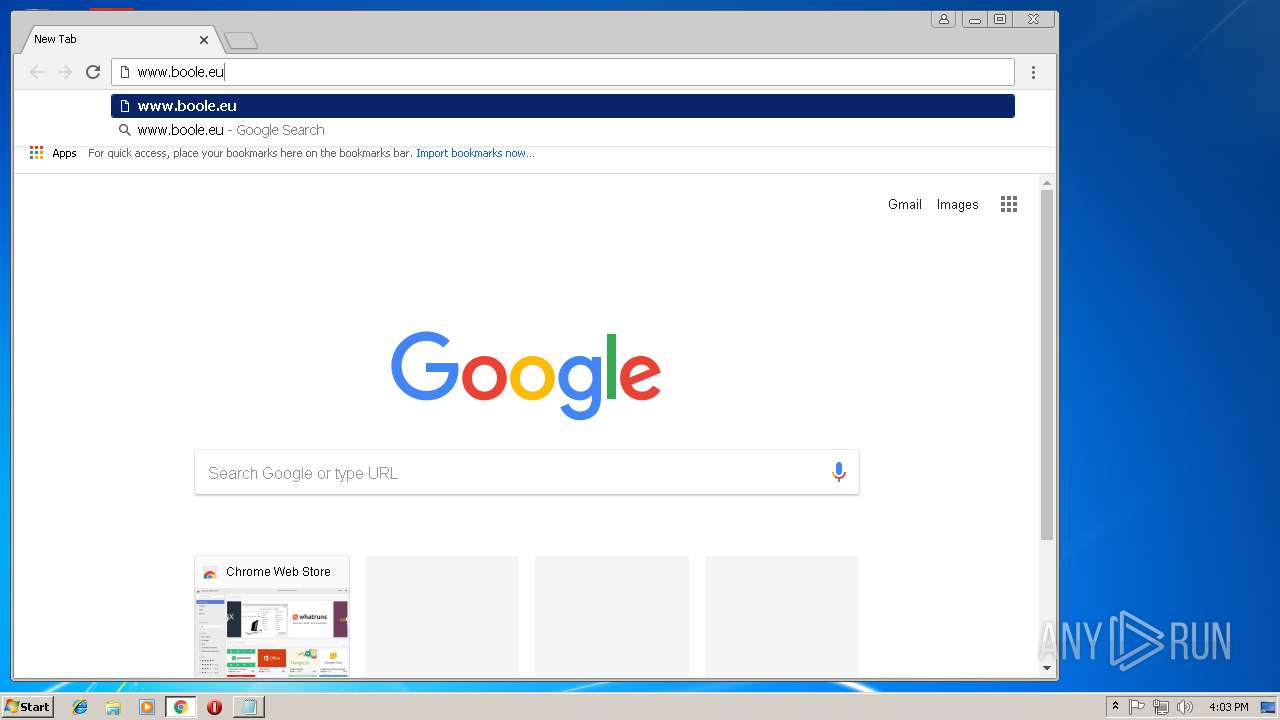
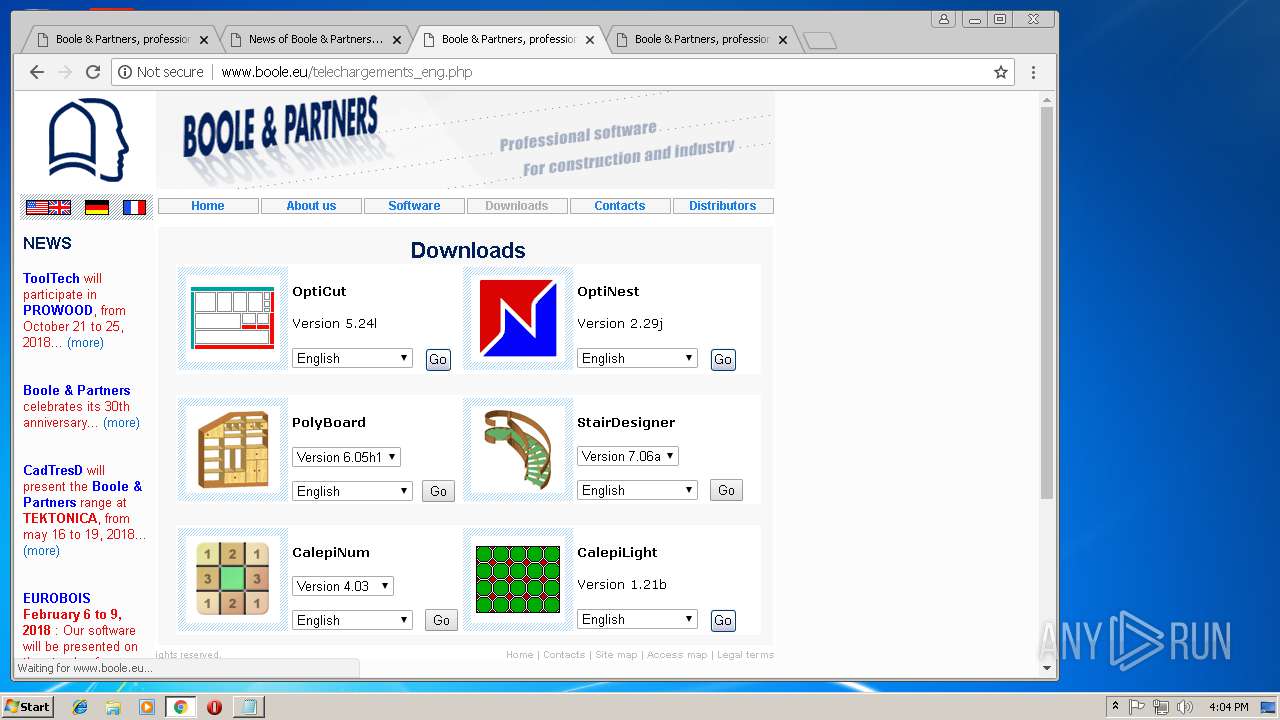
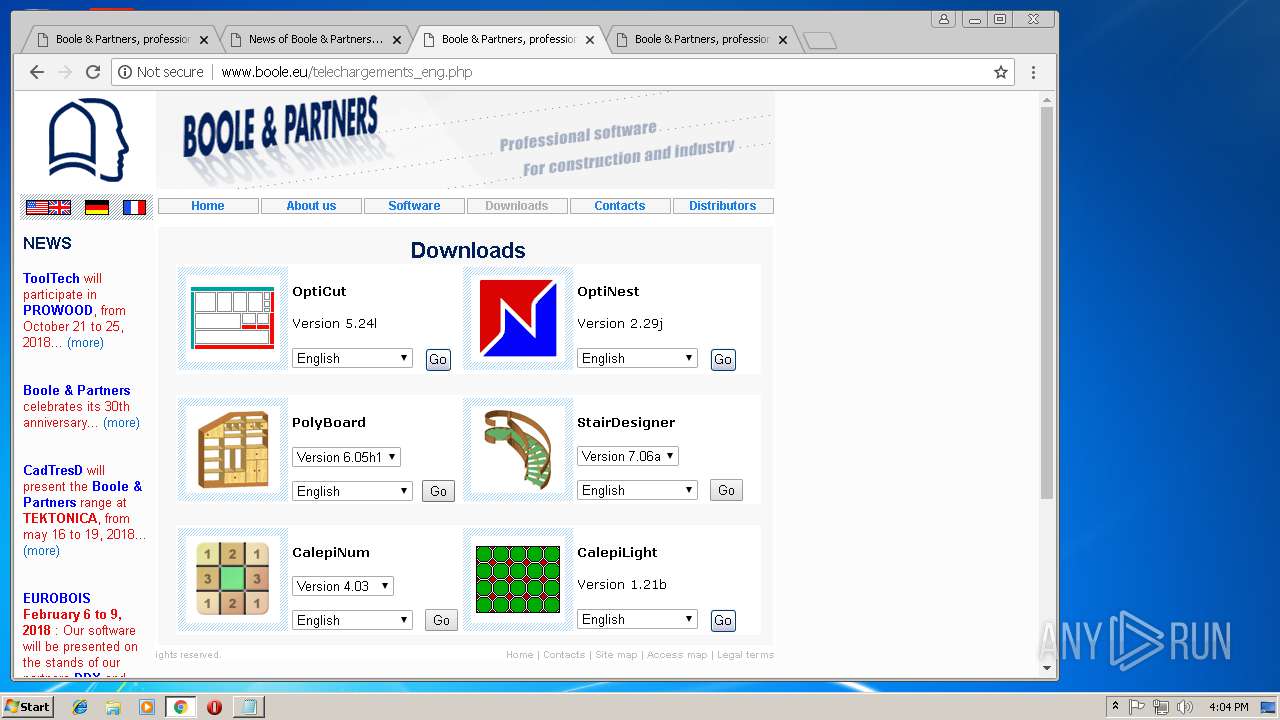
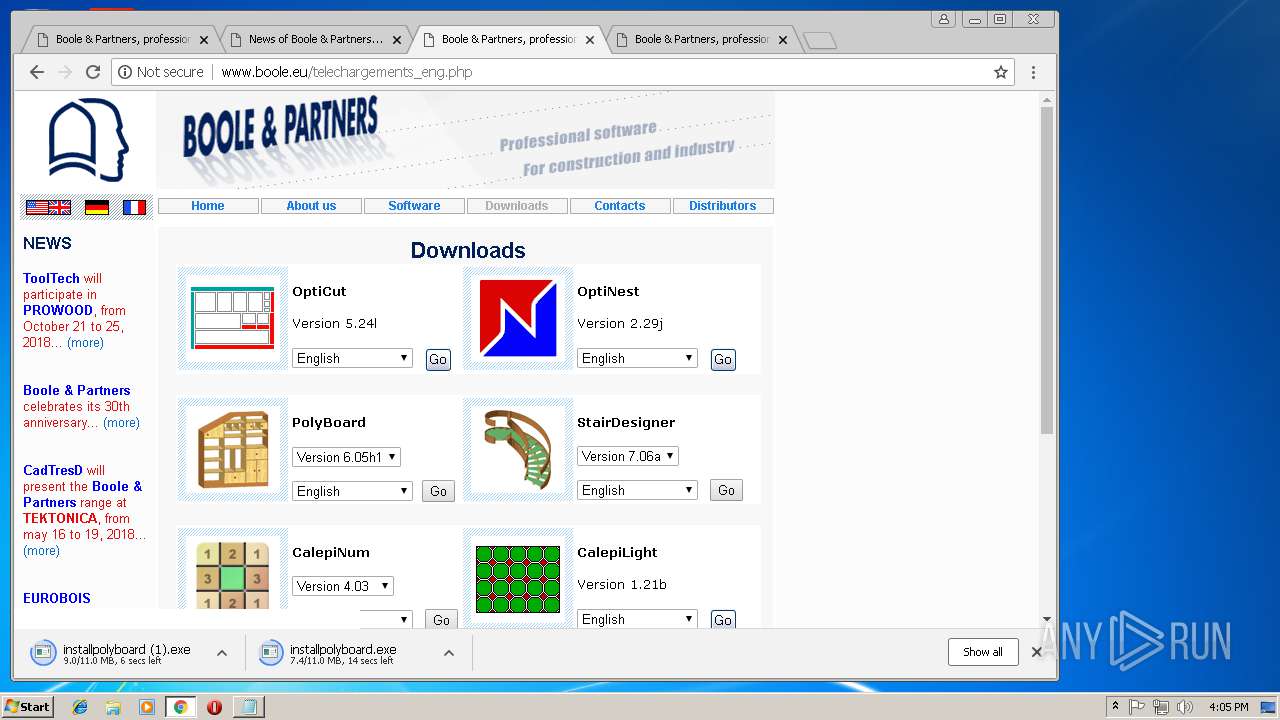
3444 | chrome.exe | GET | 200 | 81.88.48.95:80 | http://www.boole.eu/images/bg_opti.gif | IT | image | 233 b | malicious |
3444 | chrome.exe | GET | 200 | 81.88.48.95:80 | http://www.boole.eu/images/bg_design.gif | IT | image | 287 b | malicious |
3444 | chrome.exe | GET | 200 | 81.88.48.95:80 | http://www.boole.eu/images/bg_calepi.gif | IT | image | 268 b | malicious |
3444 | chrome.exe | GET | 200 | 81.88.48.95:80 | http://www.boole.eu/news_eng.php | IT | html | 8.93 Kb | malicious |
3444 | chrome.exe | GET | 200 | 81.88.48.95:80 | http://www.boole.eu/news_eng.php | IT | html | 8.93 Kb | malicious |
3444 | chrome.exe | GET | 200 | 81.88.48.95:80 | http://www.boole.eu/ | IT | html | 11.0 Kb | malicious |
3444 | chrome.exe | GET | 200 | 81.88.48.95:80 | http://www.boole.eu/mystyle.css | IT | text | 8.54 Kb | malicious |
3444 | chrome.exe | GET | 200 | 81.88.48.95:80 | http://www.boole.eu/images/mini_opticoupe.gif | IT | image | 1010 b | malicious |
3444 | chrome.exe | GET | 200 | 81.88.48.95:80 | http://www.boole.eu/images/mini_poly.gif | IT | image | 1.87 Kb | malicious |
3444 | chrome.exe | GET | 404 | 81.88.48.95:80 | http://www.boole.eu/favicon.ico | IT | html | 209 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3444 | chrome.exe | 216.58.207.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3444 | chrome.exe | 172.217.18.10:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3444 | chrome.exe | 172.217.18.163:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3444 | chrome.exe | 172.217.21.237:443 | accounts.google.com | Google Inc. | US | whitelisted |
3444 | chrome.exe | 172.217.18.3:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3444 | chrome.exe | 81.88.48.95:80 | www.boole.eu | Register.it SpA | IT | suspicious |
3444 | chrome.exe | 172.217.23.132:443 | www.google.com | Google Inc. | US | whitelisted |
3444 | chrome.exe | 216.58.208.46:443 | clients1.google.com | Google Inc. | US | whitelisted |
3444 | chrome.exe | 172.217.18.14:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.google.de |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
www.google.com |
| malicious |
www.google.co.uk |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
www.boole.eu |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3444 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3444 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
Process | Message |
|---|---|
installpolyboard (1).exe | DLL_PROCESS_ATTACH |
installpolyboard (1).exe | DLL_PROCESS_ATTACH |
installpolyboard (1).exe | DLL_PROCESS_DETACH |
installpolyboard (1).exe | DLL_PROCESS_DETACH |