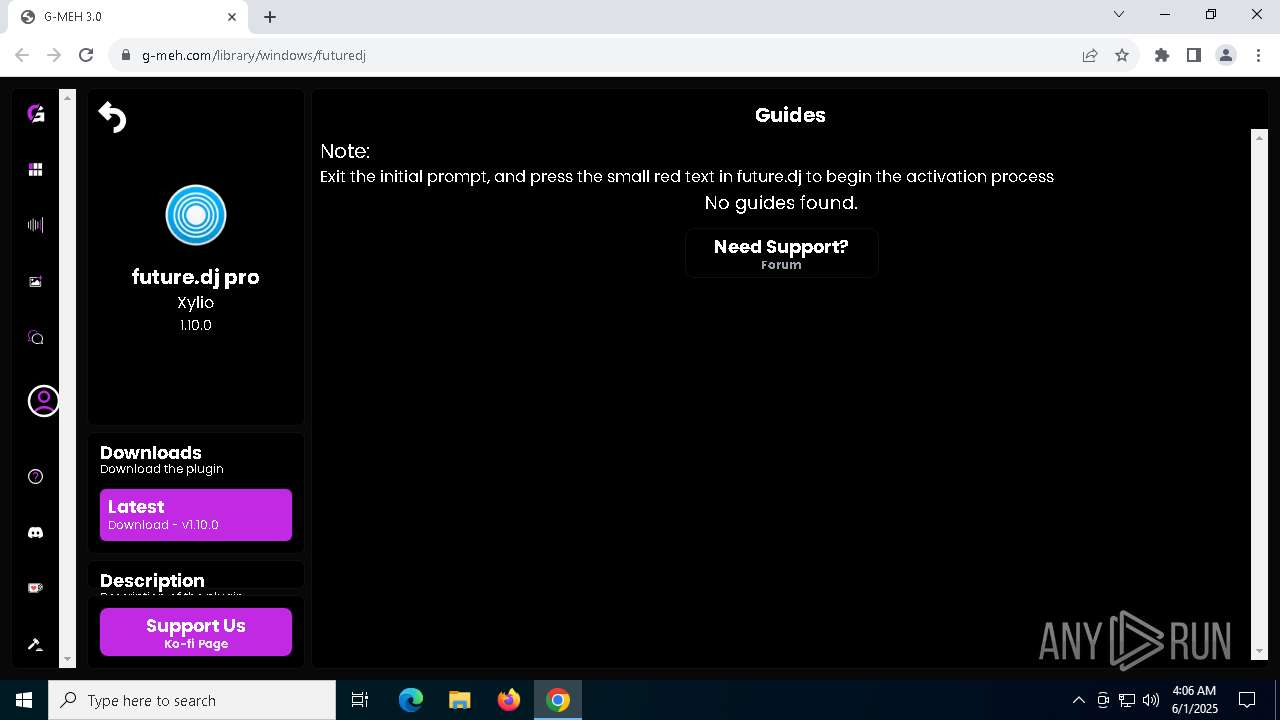
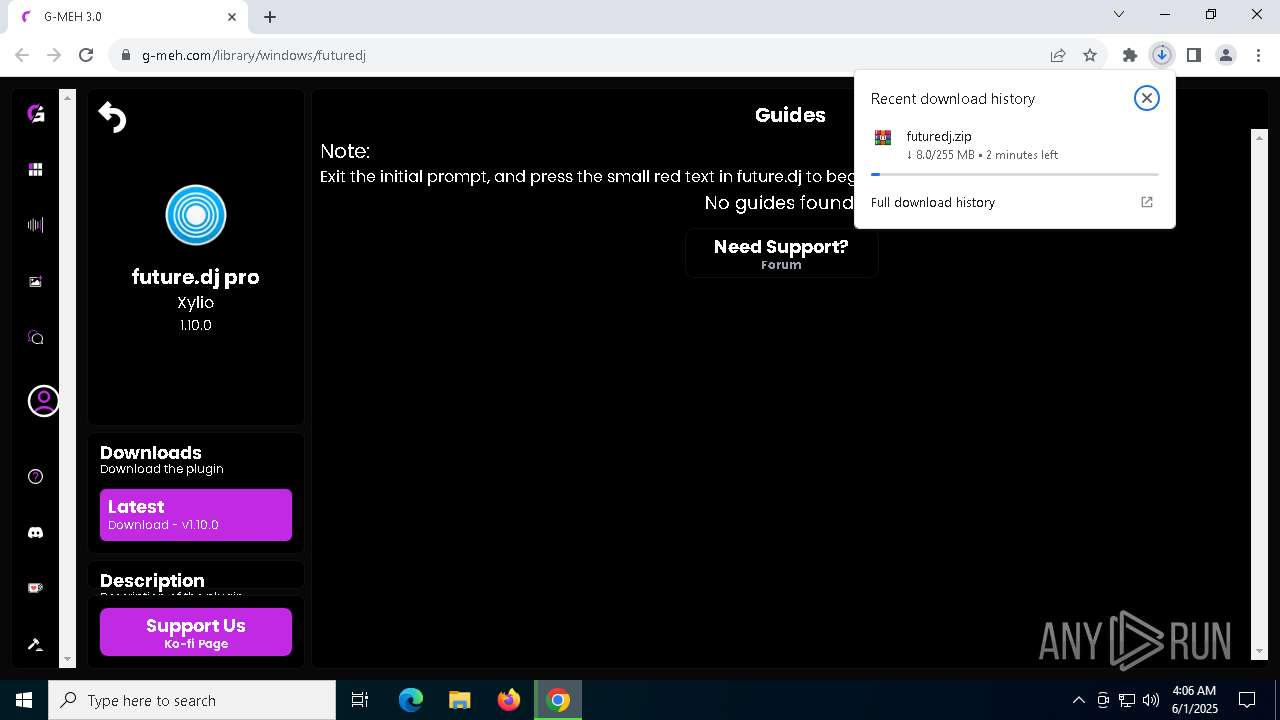
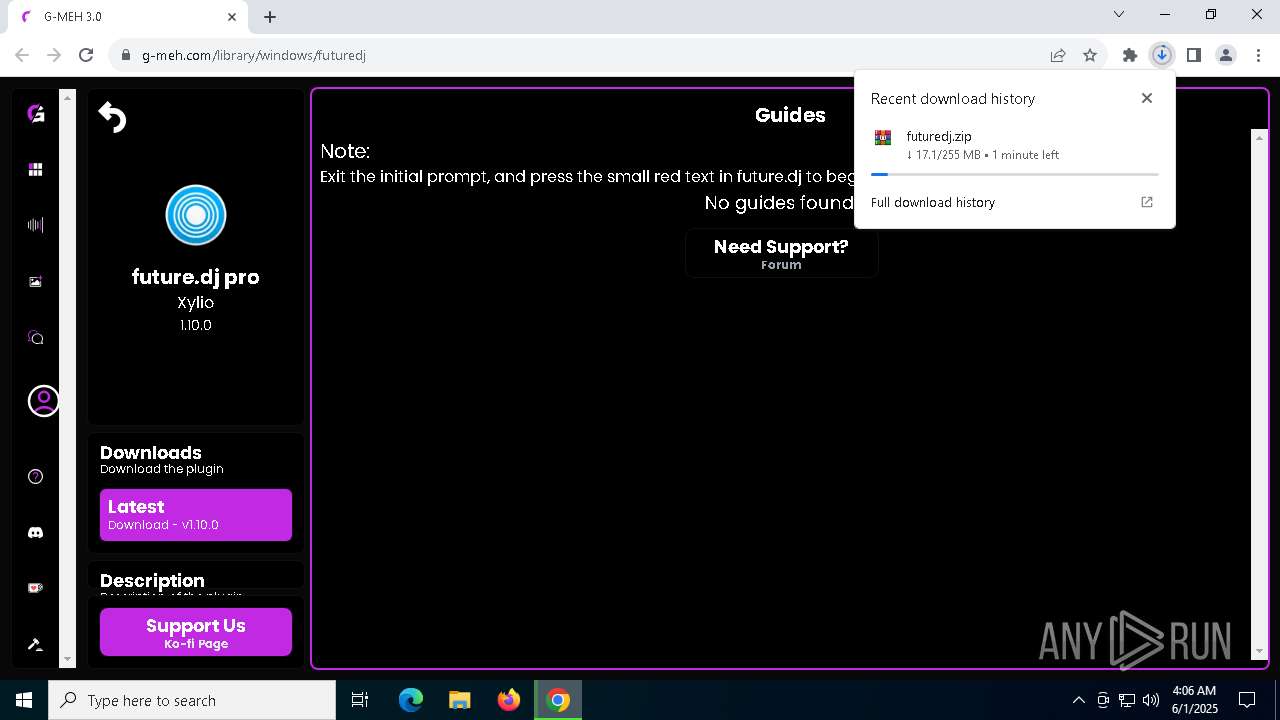
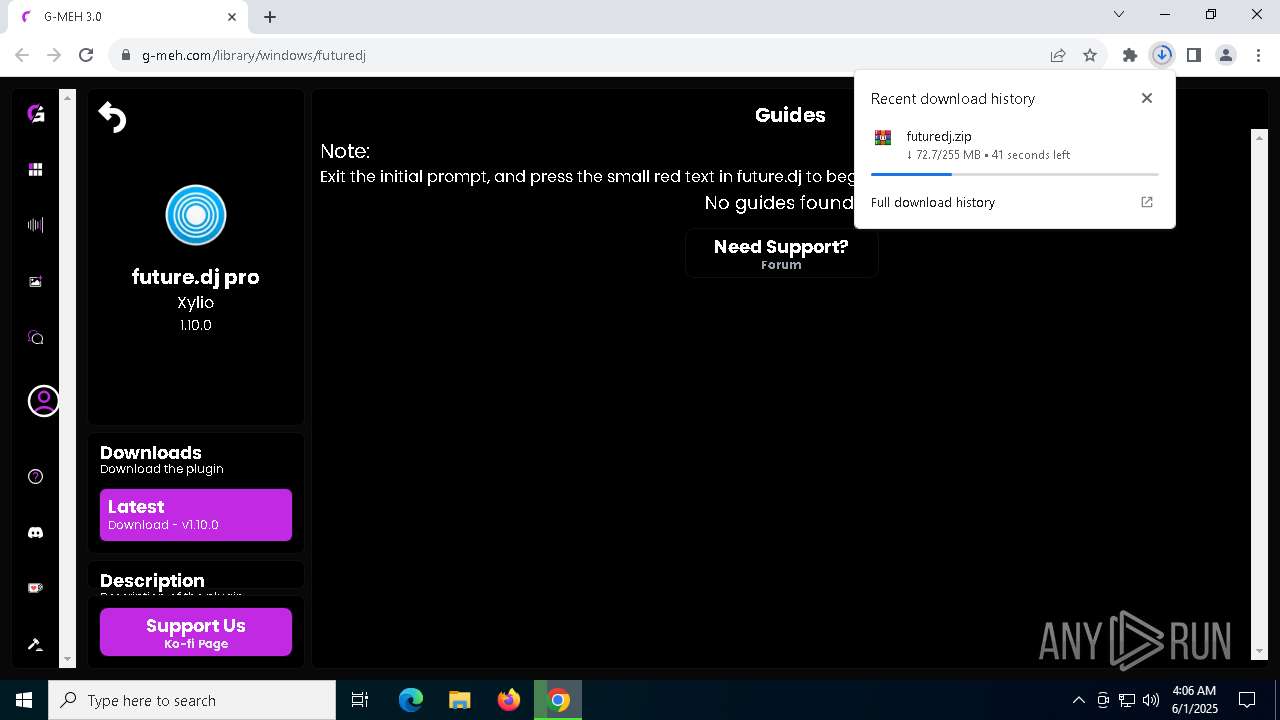
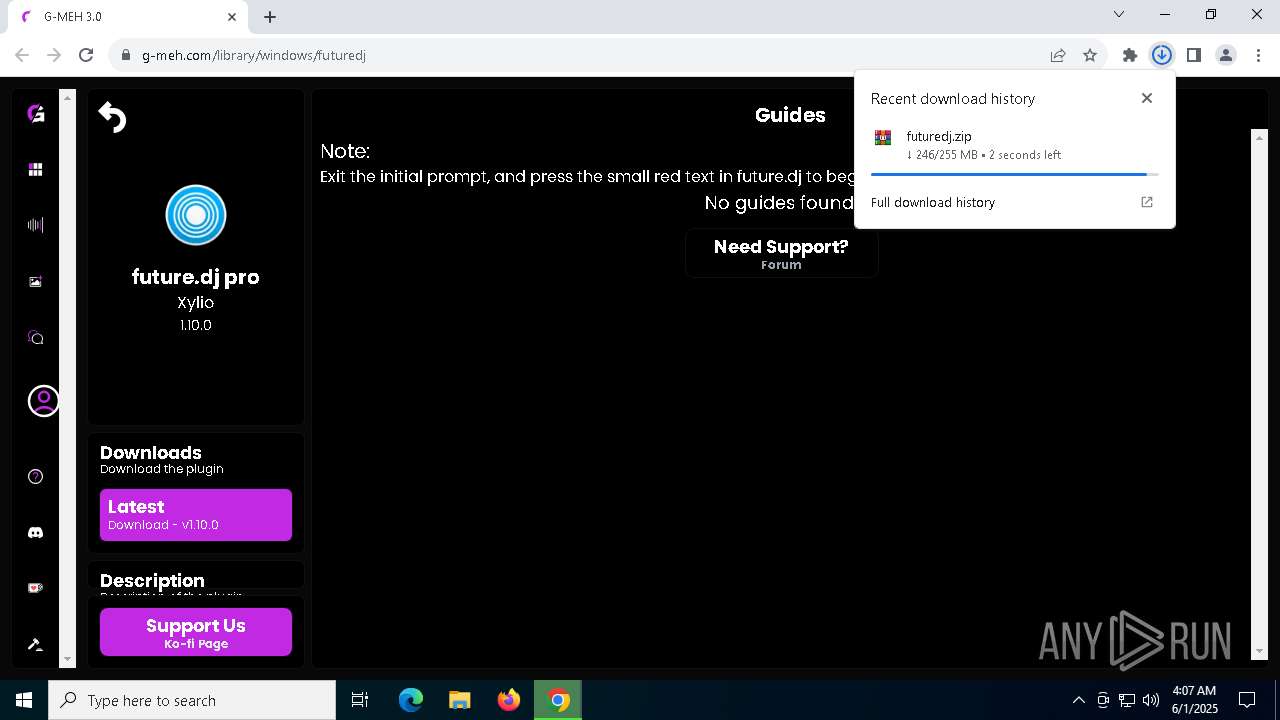
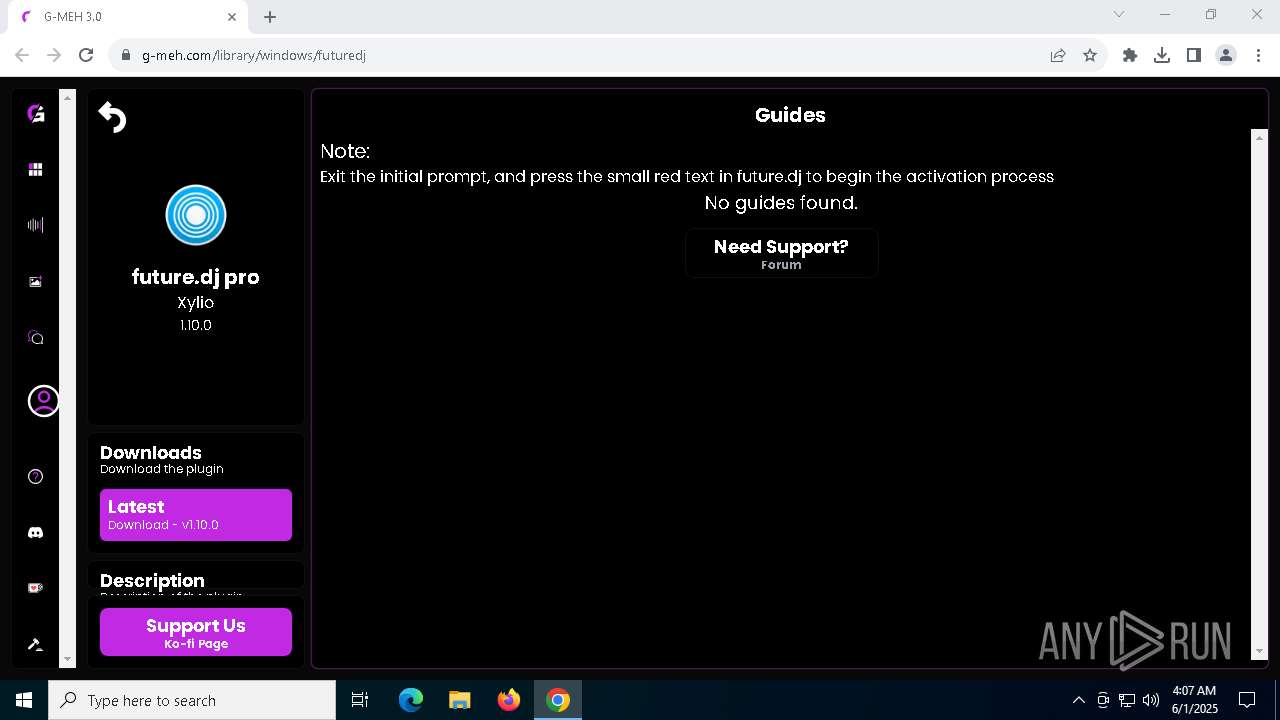
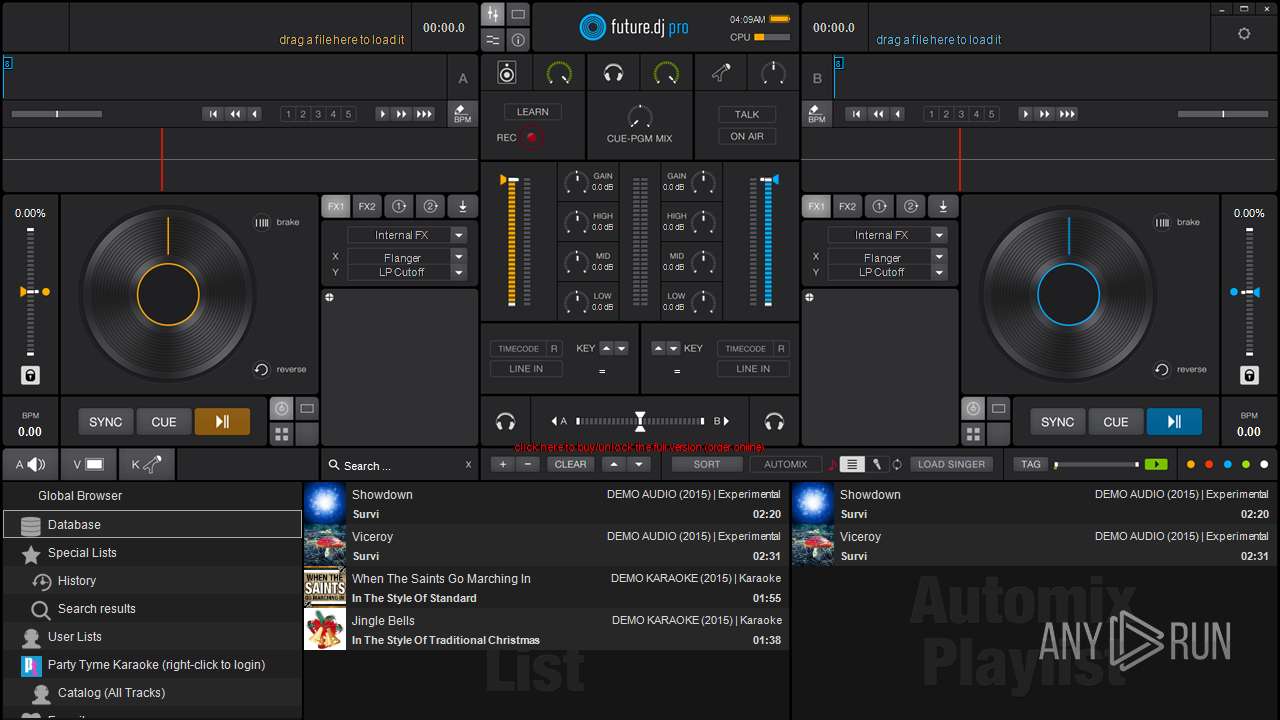
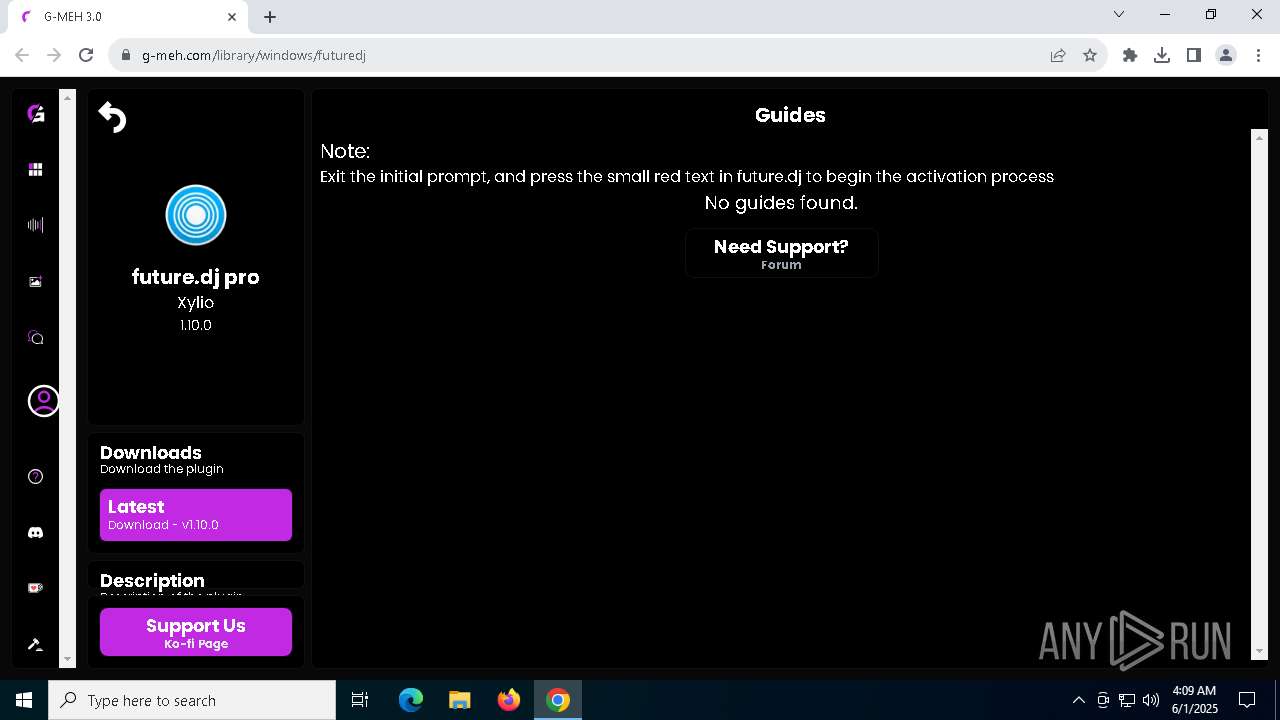
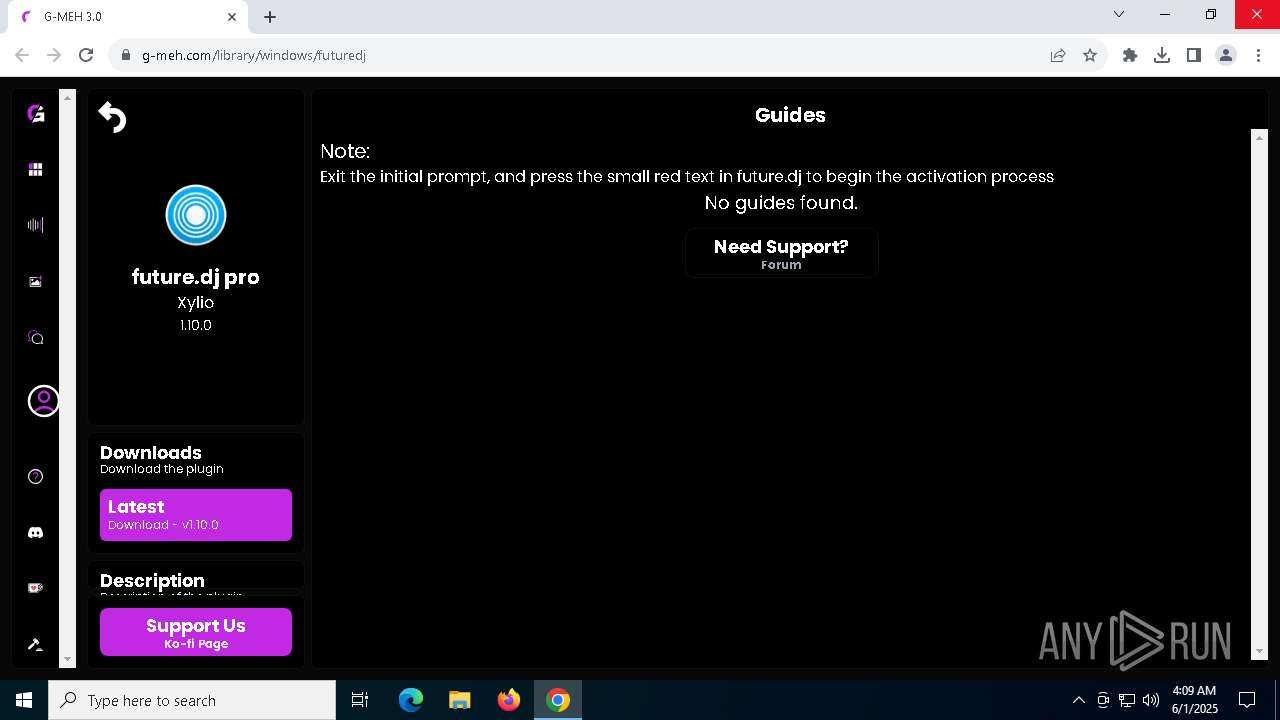
| URL: | https://g-meh.com/library/windows/futuredj |
| Full analysis: | https://app.any.run/tasks/1d33316c-2fce-4803-95c2-d76db8ddfdc2 |
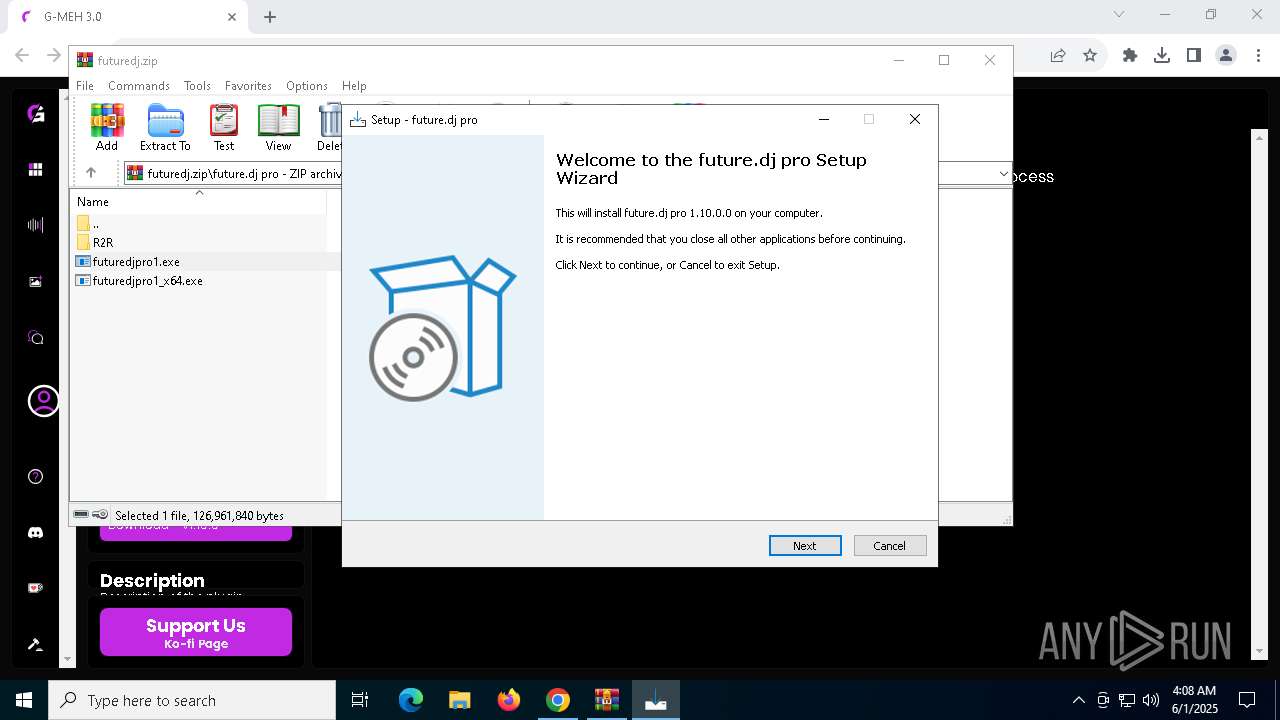
| Verdict: | Malicious activity |
| Analysis date: | June 01, 2025, 04:06:28 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | EAAA9CEE7761ABF676665A017293DAFF |
| SHA1: | FBA103AC17D8E8462C073CD7B30207E7C9C7775D |
| SHA256: | BC16627C2D06FF6430F0543DF6776DAC09C7CA466E8D83F771080F8C72360F03 |
| SSDEEP: | 3:N83ysl5Wn:2Cj |
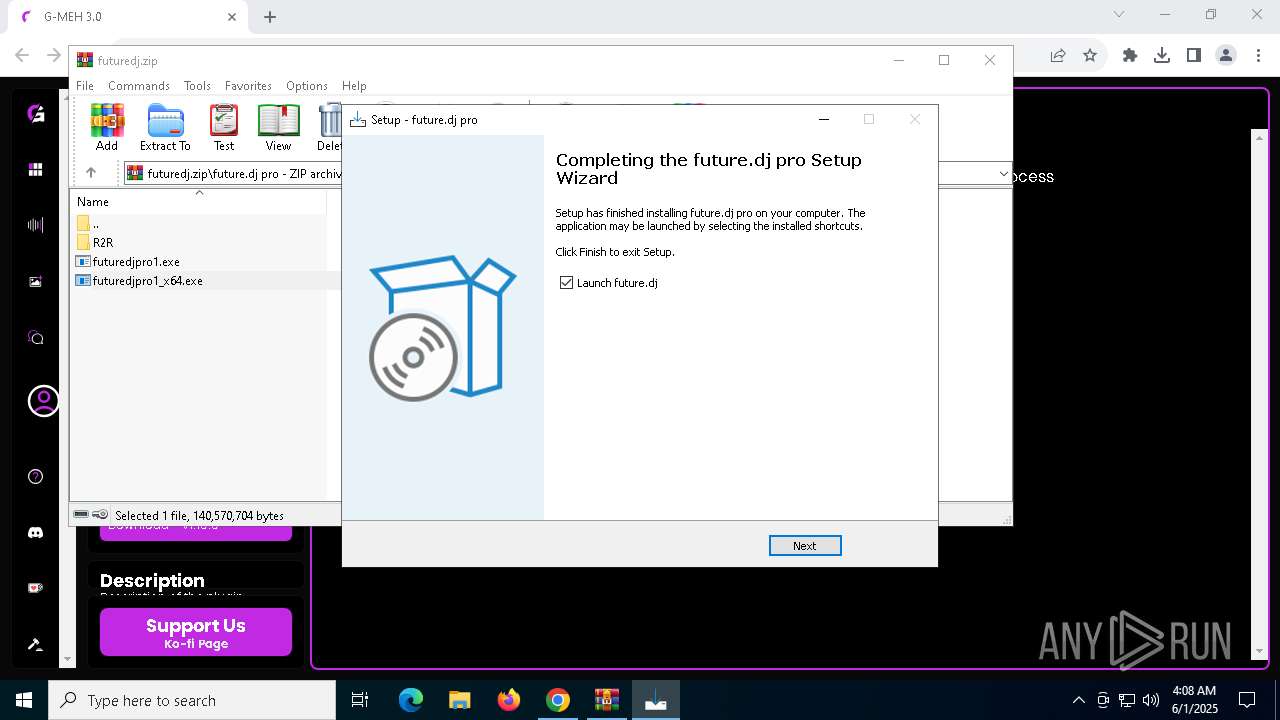
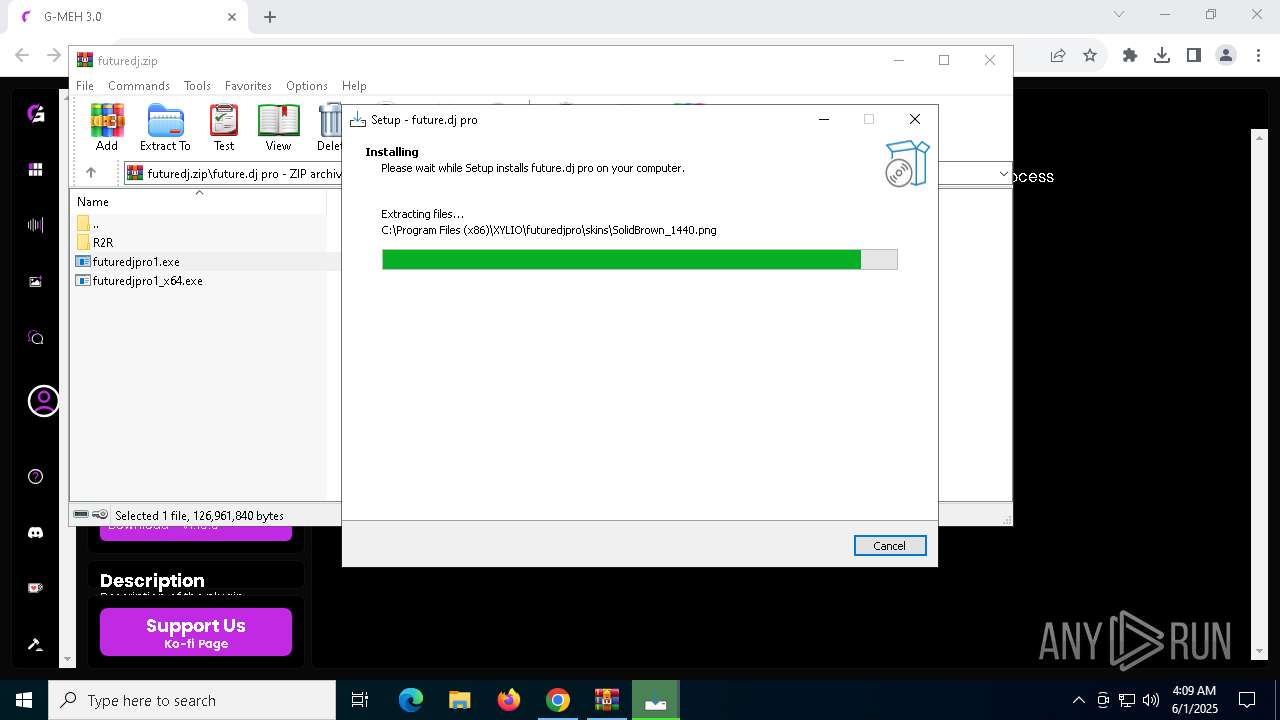
MALICIOUS
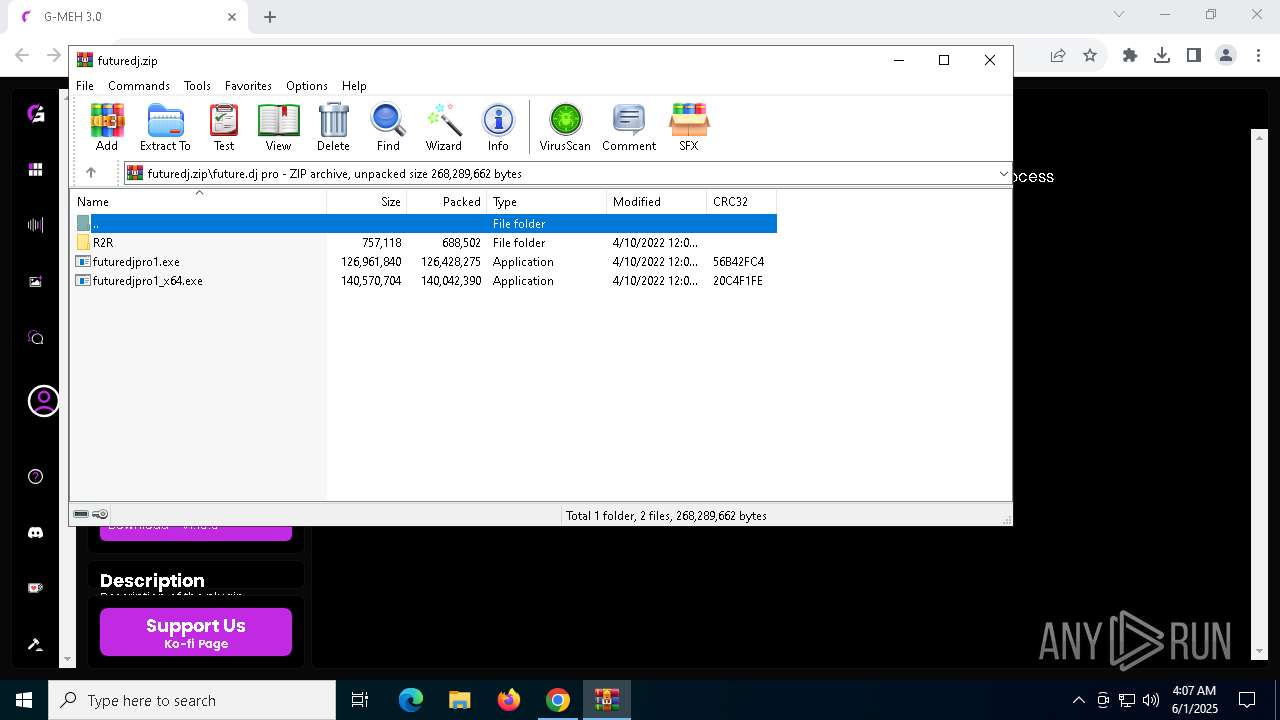
Executing a file with an untrusted certificate
- futuredjpro1_x64.exe (PID: 7312)
- futuredjpro1_x64.exe (PID: 7528)
- future.dj.exe (PID: 7232)
- futuredjpro1.exe (PID: 7592)
- crashpad_handler.exe (PID: 7396)
- futuredjpro1.exe (PID: 2776)
- future.dj.exe (PID: 1284)
- crashpad_handler.exe (PID: 7184)
SUSPICIOUS
Reads security settings of Internet Explorer
- futuredjpro1_x64.tmp (PID: 7184)
- WinRAR.exe (PID: 5568)
- futuredjpro1.tmp (PID: 512)
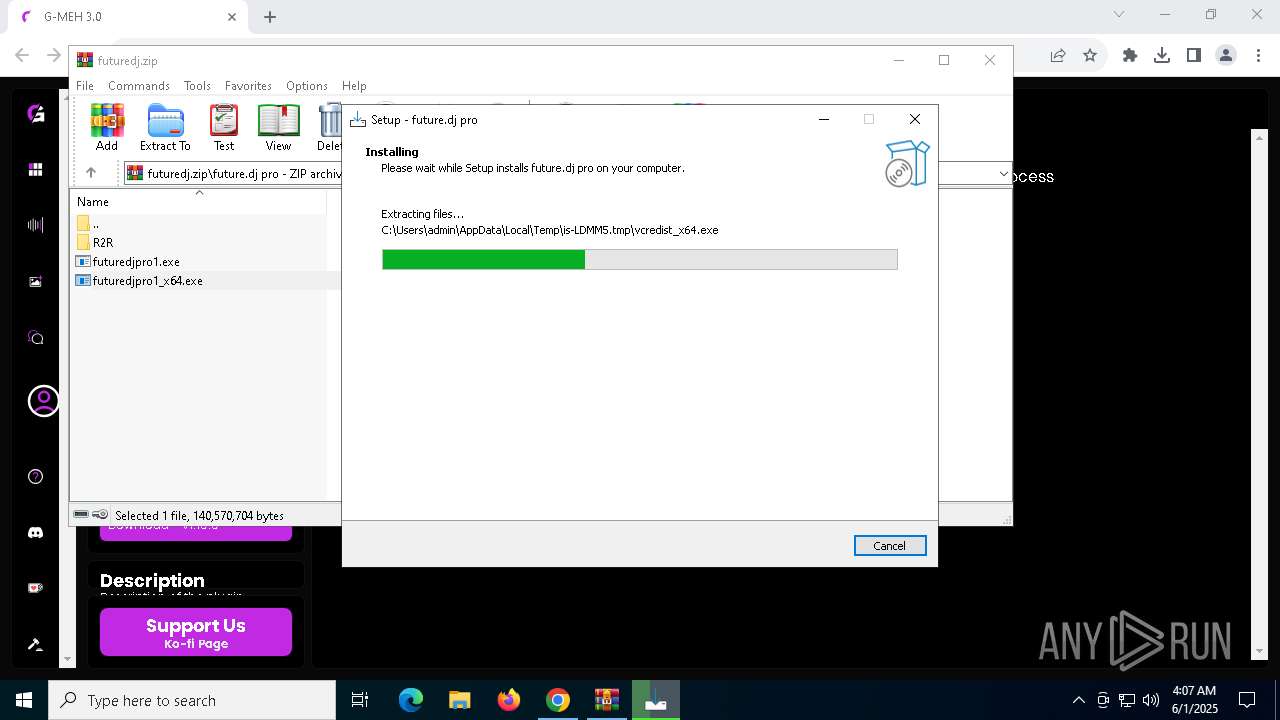
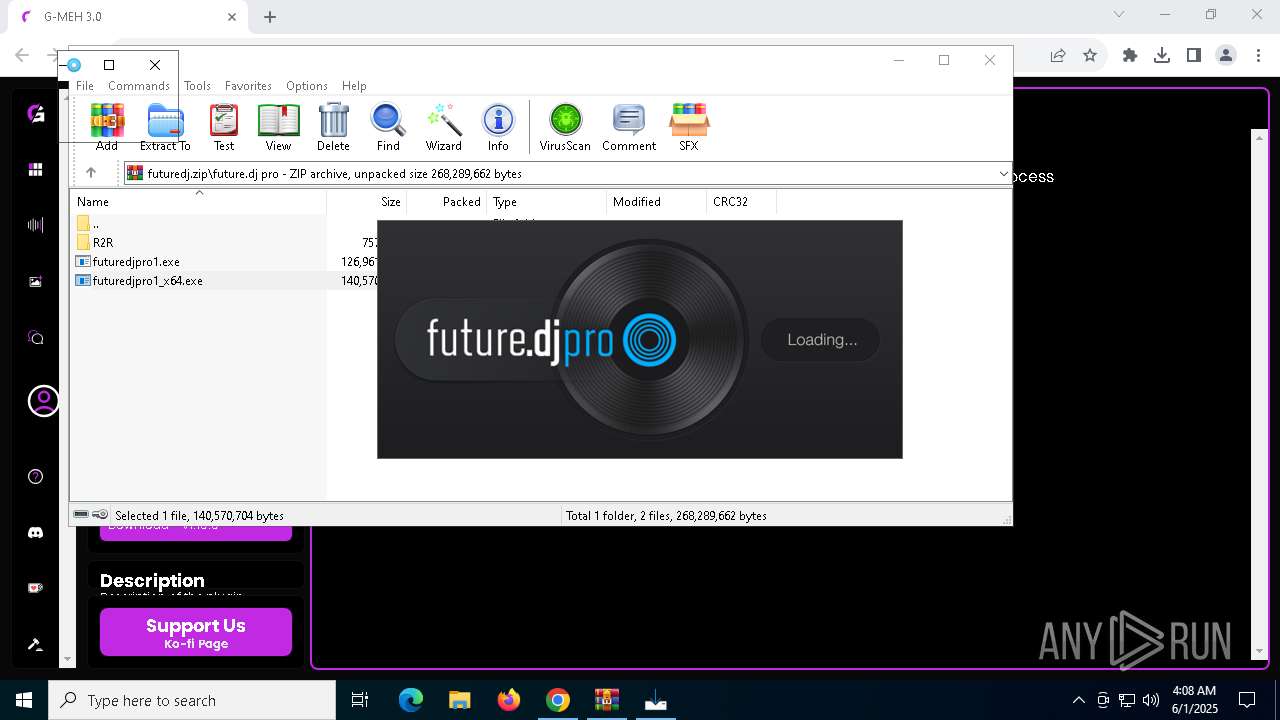
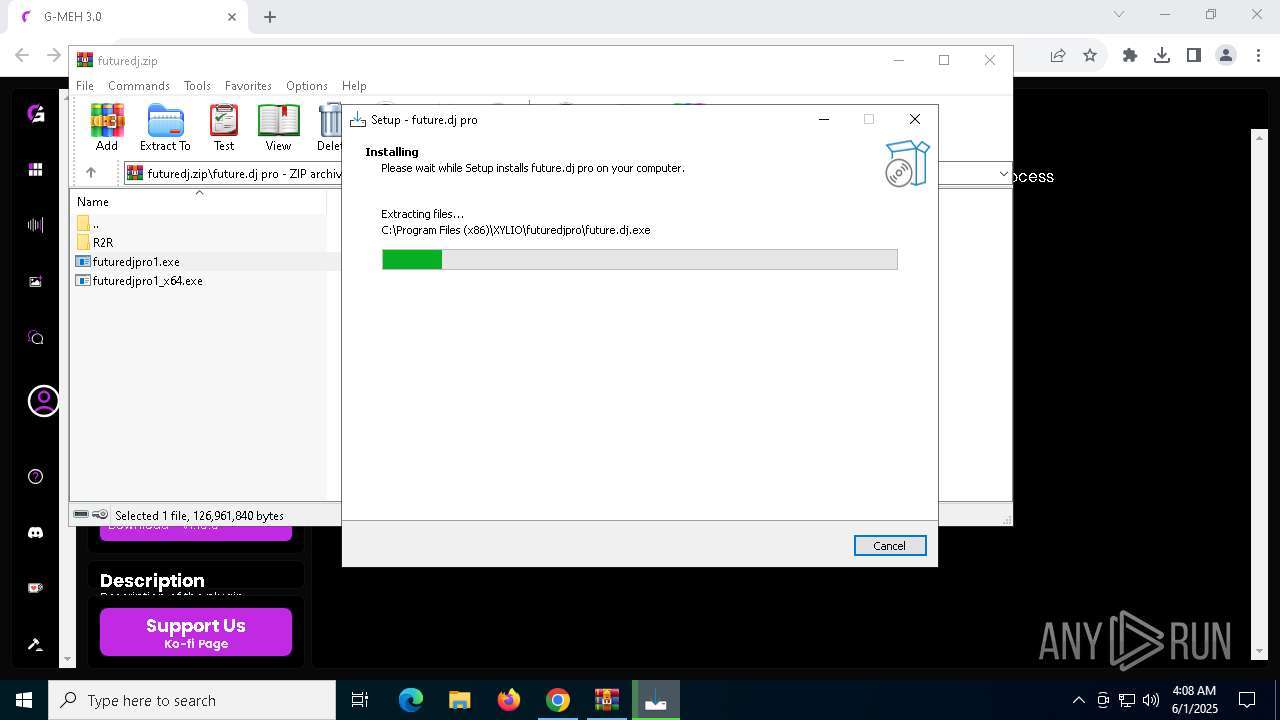
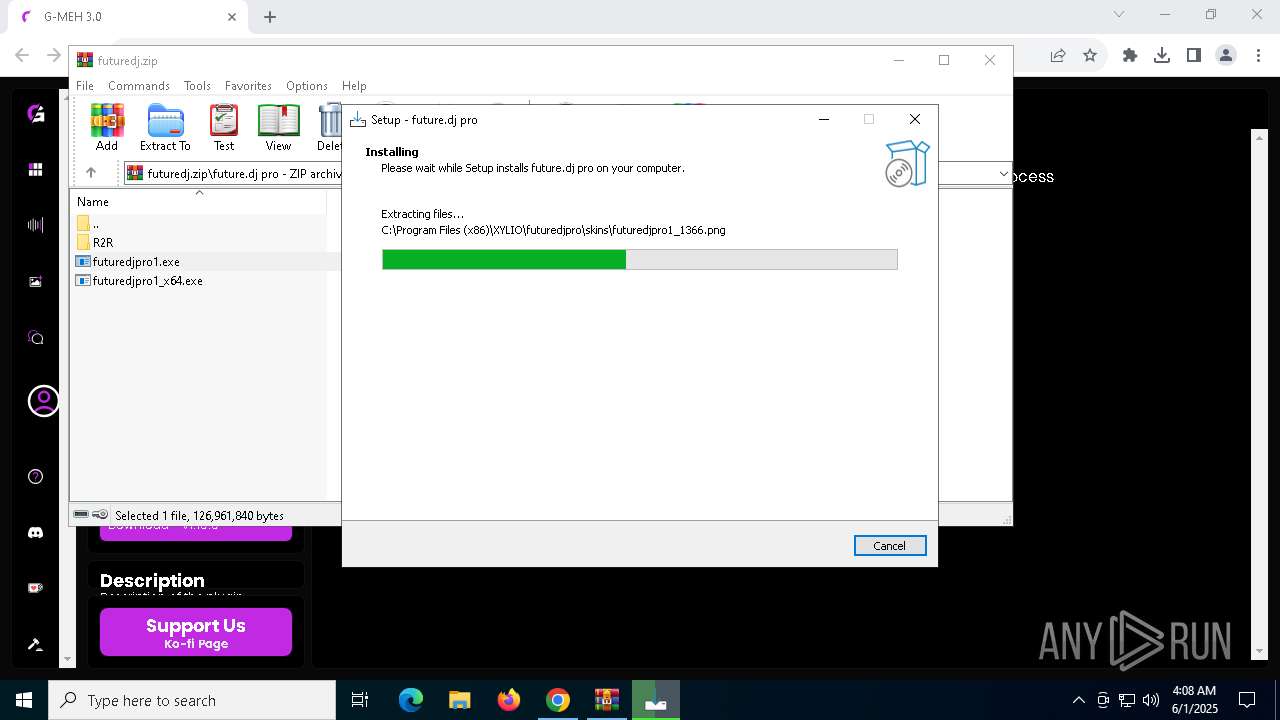
Executable content was dropped or overwritten
- futuredjpro1_x64.exe (PID: 7312)
- futuredjpro1_x64.exe (PID: 7528)
- futuredjpro1_x64.tmp (PID: 6560)
- vcredist_x64.exe (PID: 7768)
- vcredist_x64.exe (PID: 4628)
- futuredjpro1.exe (PID: 7592)
- futuredjpro1.exe (PID: 2776)
- futuredjpro1.tmp (PID: 5172)
- vcredist_x86.exe (PID: 5352)
- vcredist_x86.exe (PID: 6416)
Reads the Windows owner or organization settings
- futuredjpro1_x64.tmp (PID: 6560)
Process drops legitimate windows executable
- futuredjpro1_x64.tmp (PID: 6560)
- vcredist_x64.exe (PID: 7768)
- vcredist_x86.exe (PID: 5352)
- futuredjpro1.tmp (PID: 5172)
The process drops C-runtime libraries
- futuredjpro1_x64.tmp (PID: 6560)
- futuredjpro1.tmp (PID: 5172)
Changes Internet Explorer settings (feature browser emulation)
- futuredjpro1_x64.tmp (PID: 6560)
Starts a Microsoft application from unusual location
- vcredist_x64.exe (PID: 7768)
- vcredist_x64.exe (PID: 4628)
- vcredist_x86.exe (PID: 5352)
- vcredist_x86.exe (PID: 6416)
Searches for installed software
- vcredist_x64.exe (PID: 4628)
INFO
Application launched itself
- chrome.exe (PID: 4200)
Checks supported languages
- futuredjpro1_x64.tmp (PID: 7184)
- futuredjpro1_x64.tmp (PID: 6560)
- futuredjpro1_x64.exe (PID: 7312)
- futuredjpro1_x64.exe (PID: 7528)
- vcredist_x64.exe (PID: 7768)
- vcredist_x64.exe (PID: 4628)
- crashpad_handler.exe (PID: 7396)
- futuredjpro1.exe (PID: 7592)
- future.dj.exe (PID: 7232)
- futuredjpro1.tmp (PID: 512)
Create files in a temporary directory
- futuredjpro1_x64.exe (PID: 7312)
- futuredjpro1_x64.exe (PID: 7528)
- futuredjpro1_x64.tmp (PID: 6560)
- vcredist_x64.exe (PID: 4628)
- futuredjpro1.exe (PID: 7592)
Process checks computer location settings
- futuredjpro1_x64.tmp (PID: 7184)
- futuredjpro1.tmp (PID: 512)
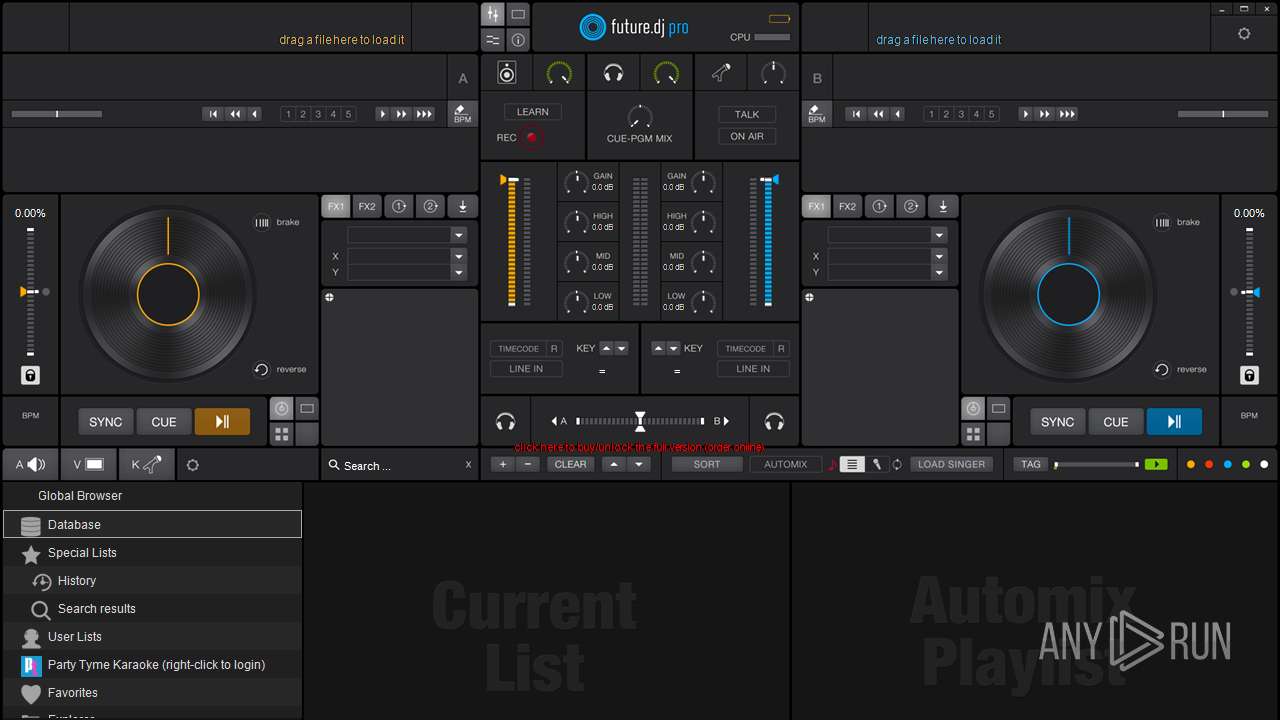
Reads the software policy settings
- slui.exe (PID: 1128)
- future.dj.exe (PID: 7232)
- slui.exe (PID: 2136)
Reads Microsoft Office registry keys
- chrome.exe (PID: 4200)
Reads the computer name
- futuredjpro1_x64.tmp (PID: 7184)
- futuredjpro1_x64.tmp (PID: 6560)
- vcredist_x64.exe (PID: 4628)
- future.dj.exe (PID: 7232)
- futuredjpro1.tmp (PID: 512)
The sample compiled with english language support
- futuredjpro1_x64.tmp (PID: 6560)
- vcredist_x64.exe (PID: 7768)
- vcredist_x64.exe (PID: 4628)
- futuredjpro1.tmp (PID: 5172)
- vcredist_x86.exe (PID: 6416)
- vcredist_x86.exe (PID: 5352)
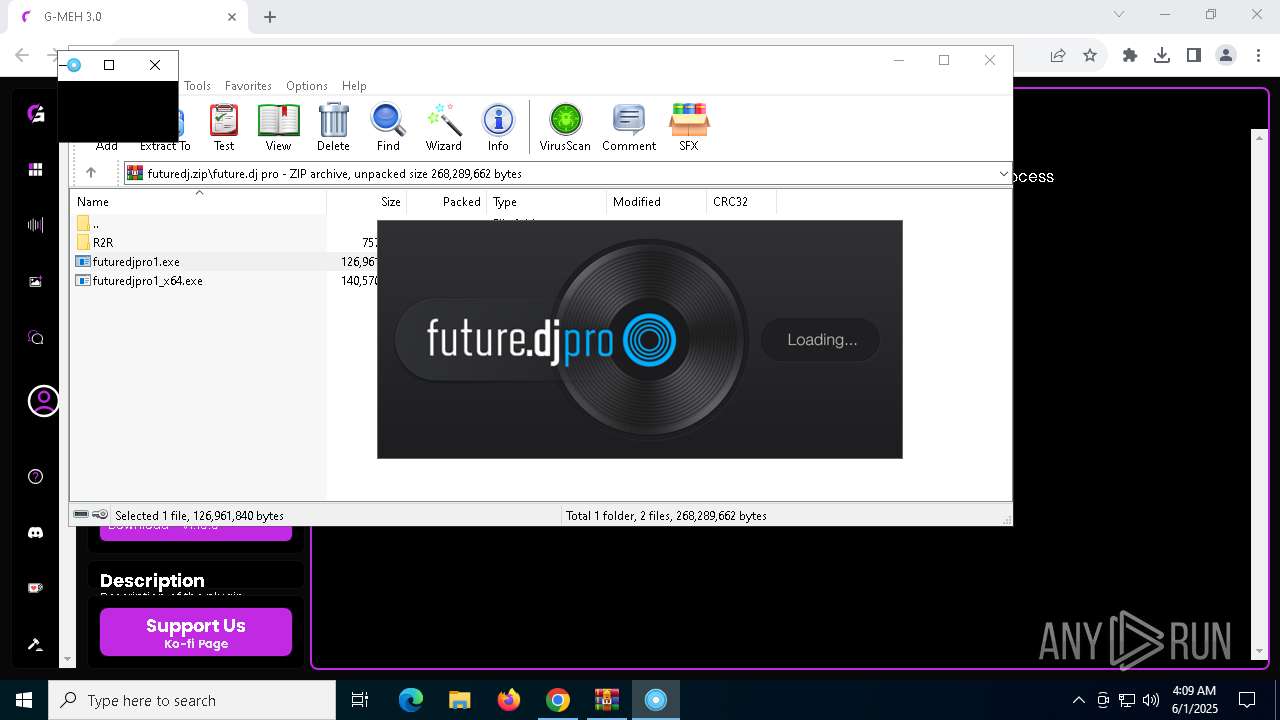
Detects InnoSetup installer (YARA)
- futuredjpro1_x64.tmp (PID: 7184)
- futuredjpro1_x64.exe (PID: 7528)
- futuredjpro1_x64.tmp (PID: 6560)
- futuredjpro1_x64.exe (PID: 7312)
Compiled with Borland Delphi (YARA)
- futuredjpro1_x64.exe (PID: 7312)
- futuredjpro1_x64.tmp (PID: 7184)
- futuredjpro1_x64.exe (PID: 7528)
- futuredjpro1_x64.tmp (PID: 6560)
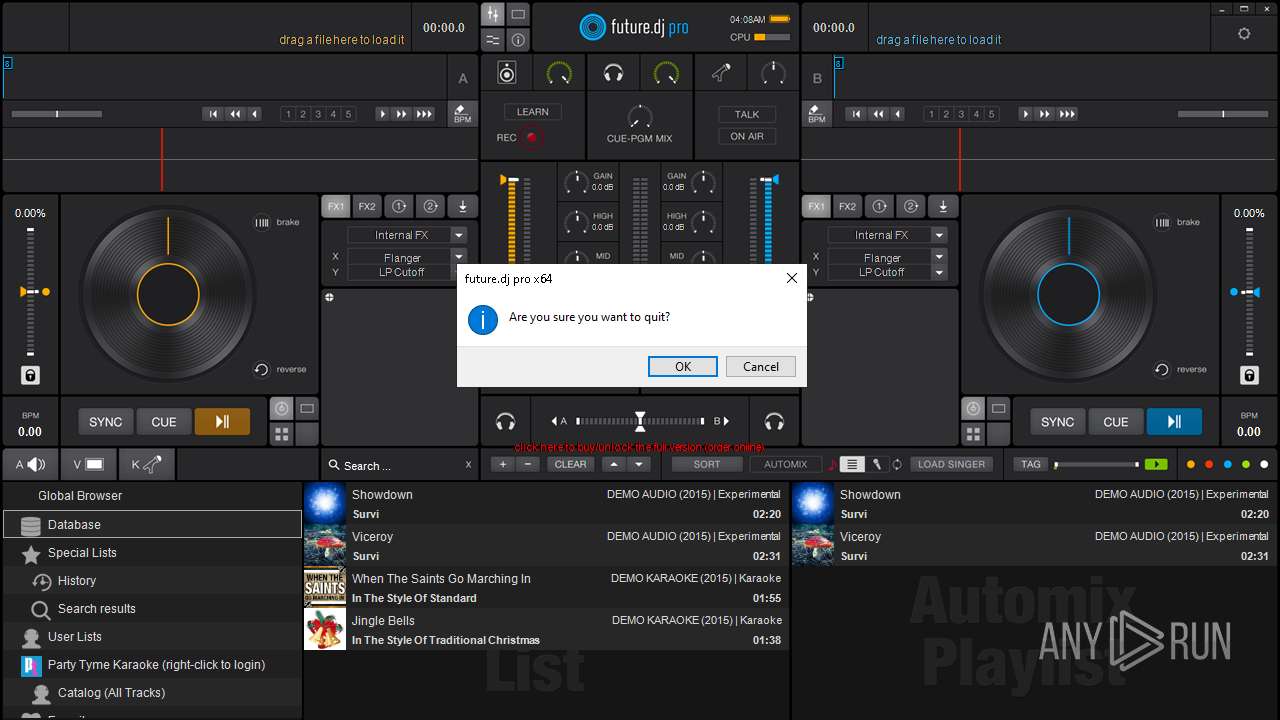
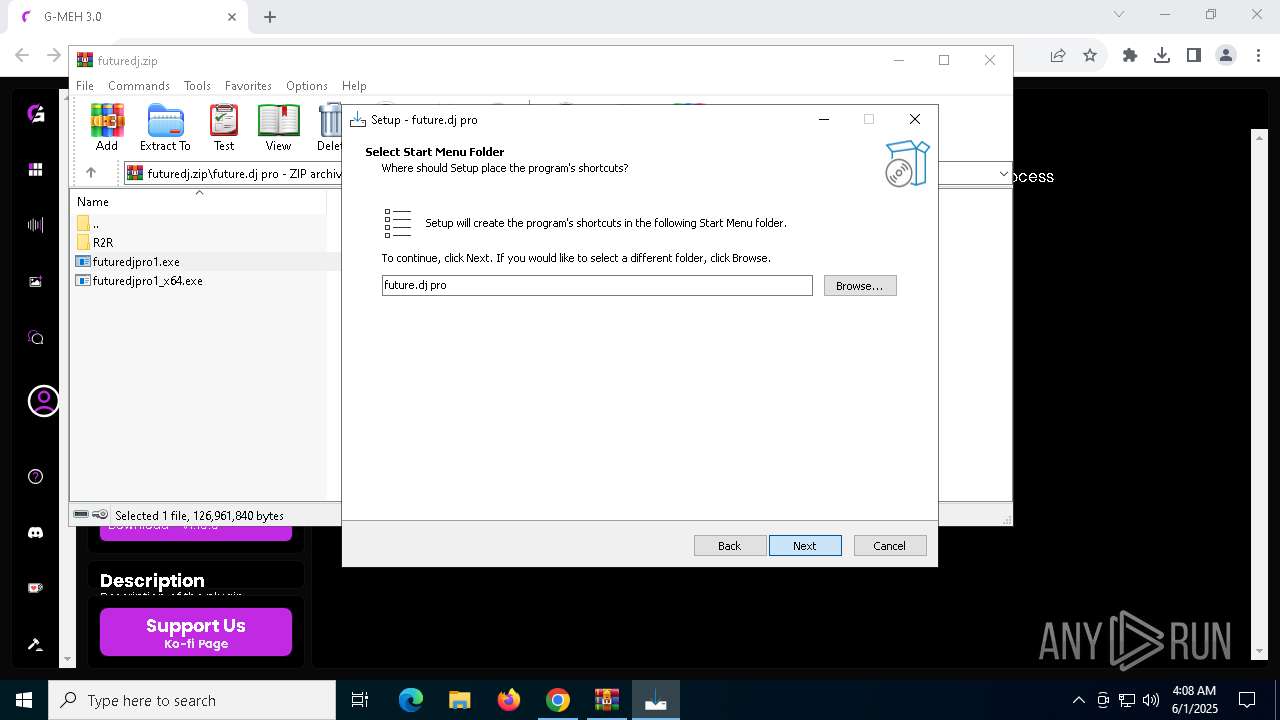
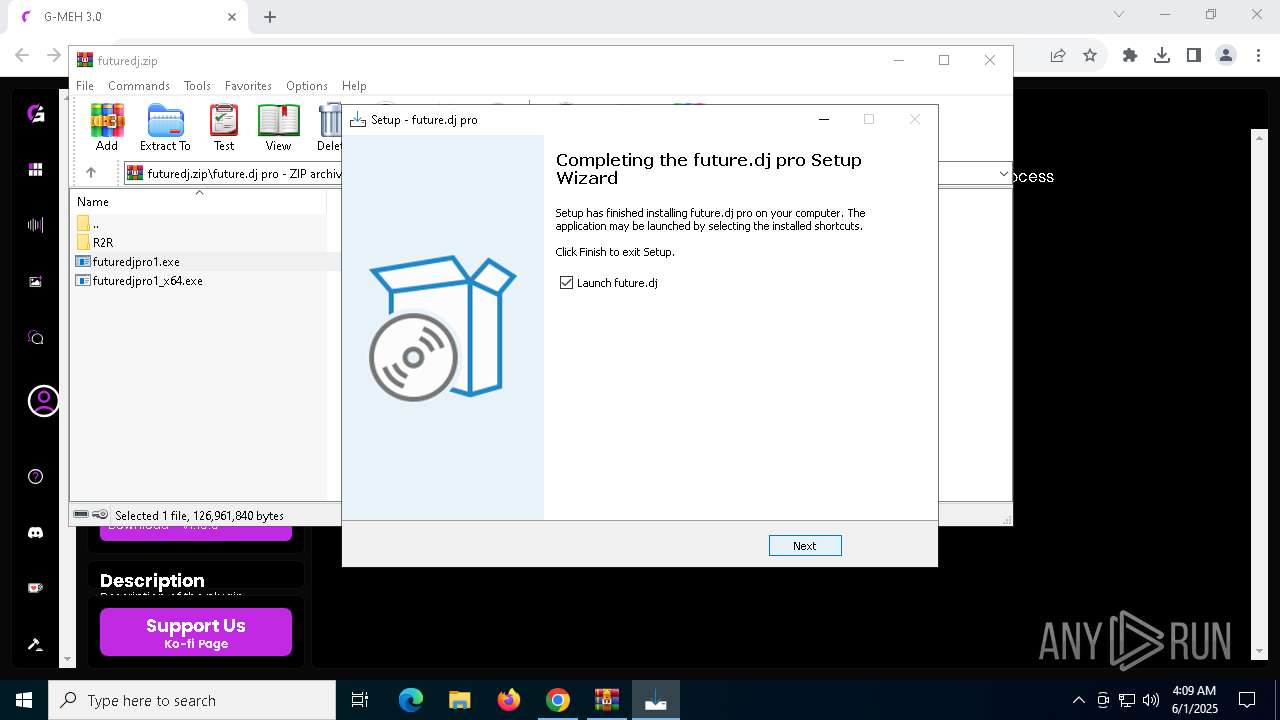
Creates a software uninstall entry
- futuredjpro1_x64.tmp (PID: 6560)
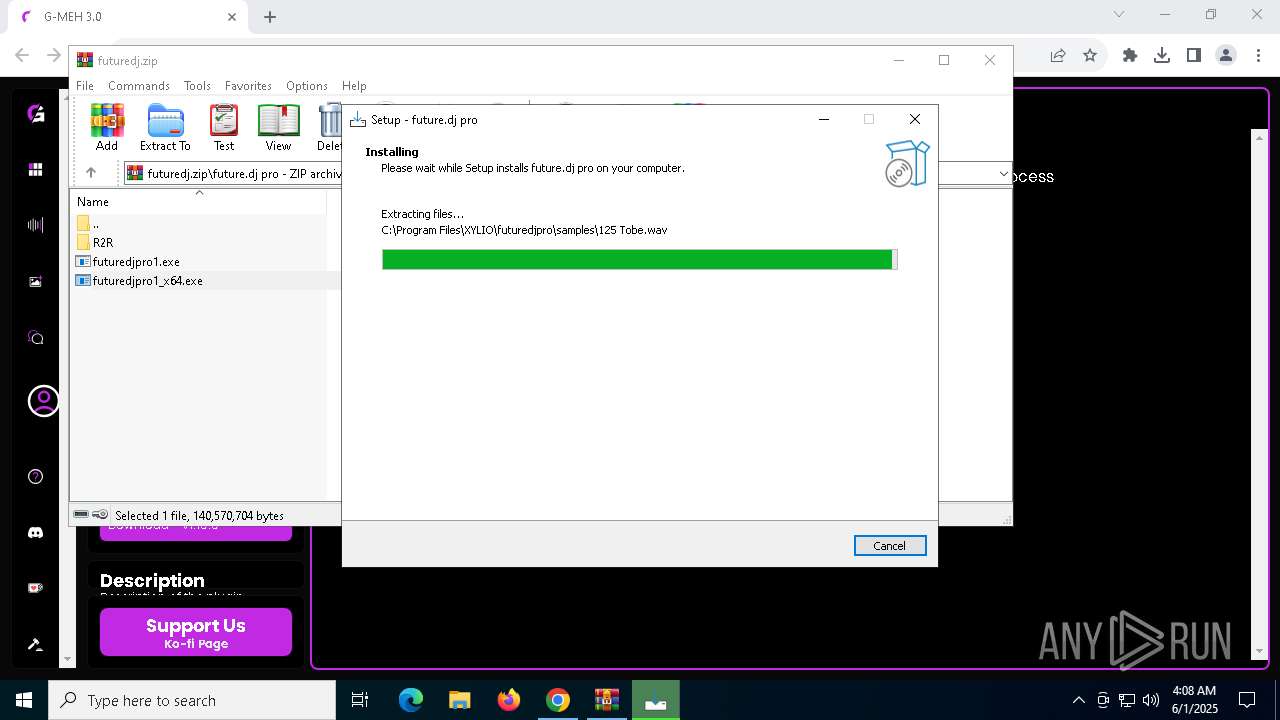
Creates files in the program directory
- futuredjpro1_x64.tmp (PID: 6560)
Creates files or folders in the user directory
- crashpad_handler.exe (PID: 7396)
- future.dj.exe (PID: 7232)
Reads the machine GUID from the registry
- future.dj.exe (PID: 7232)
Reads CPU info
- future.dj.exe (PID: 7232)
Checks proxy server information
- slui.exe (PID: 2136)
- future.dj.exe (PID: 7232)
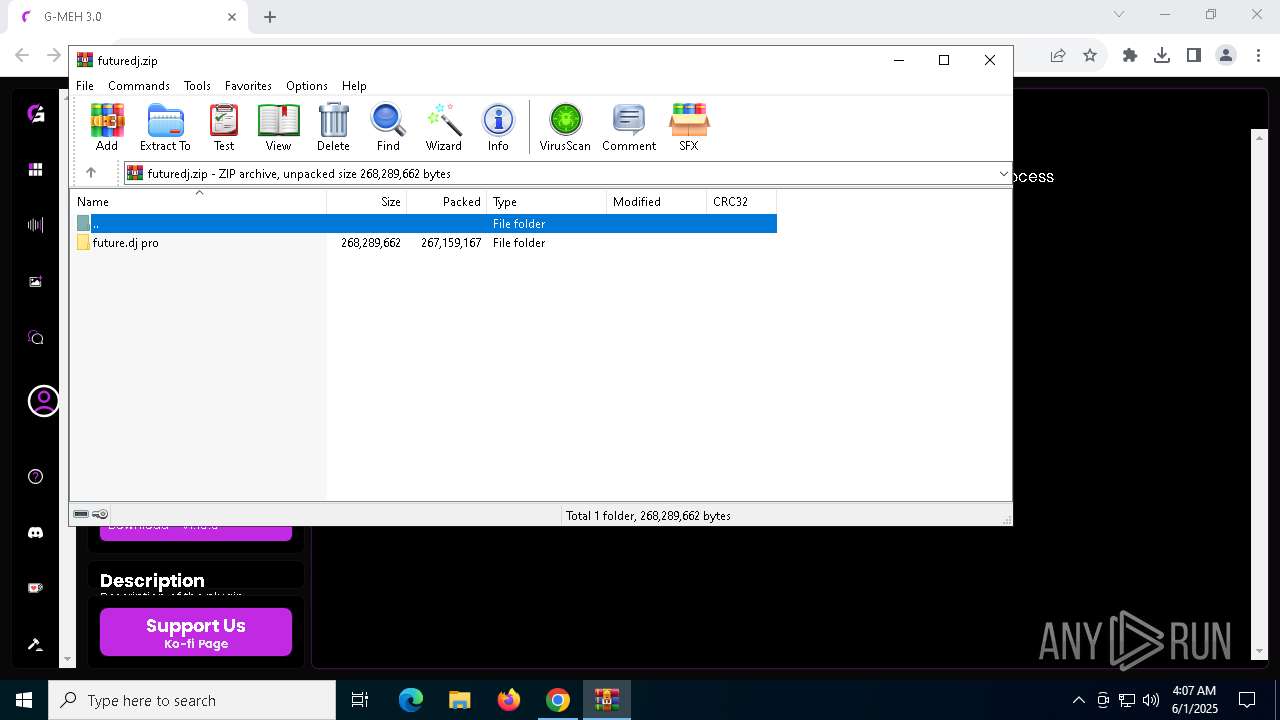
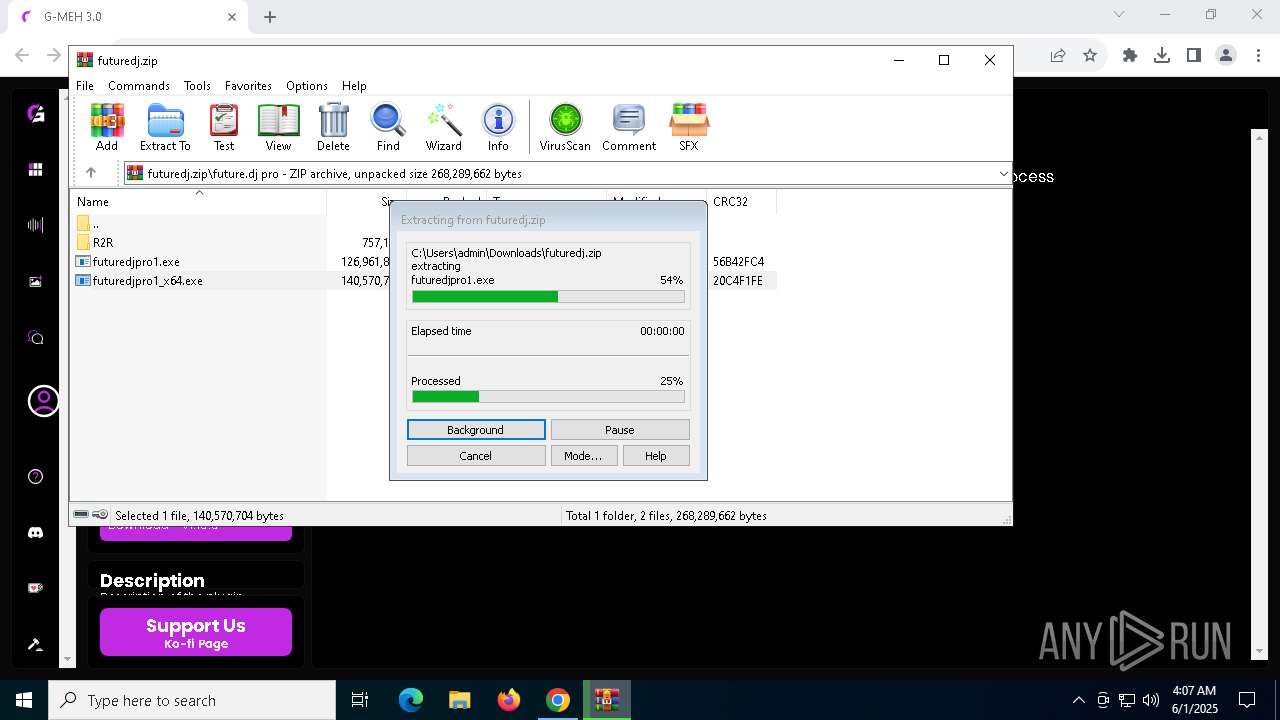
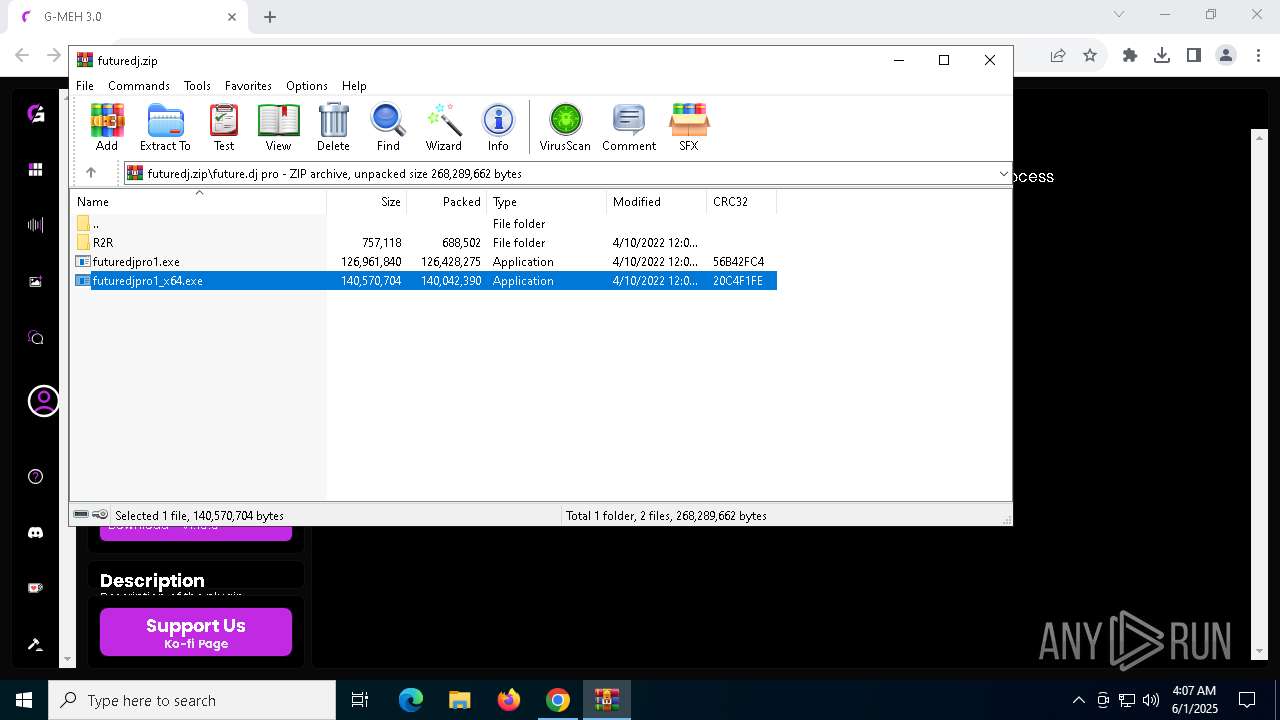
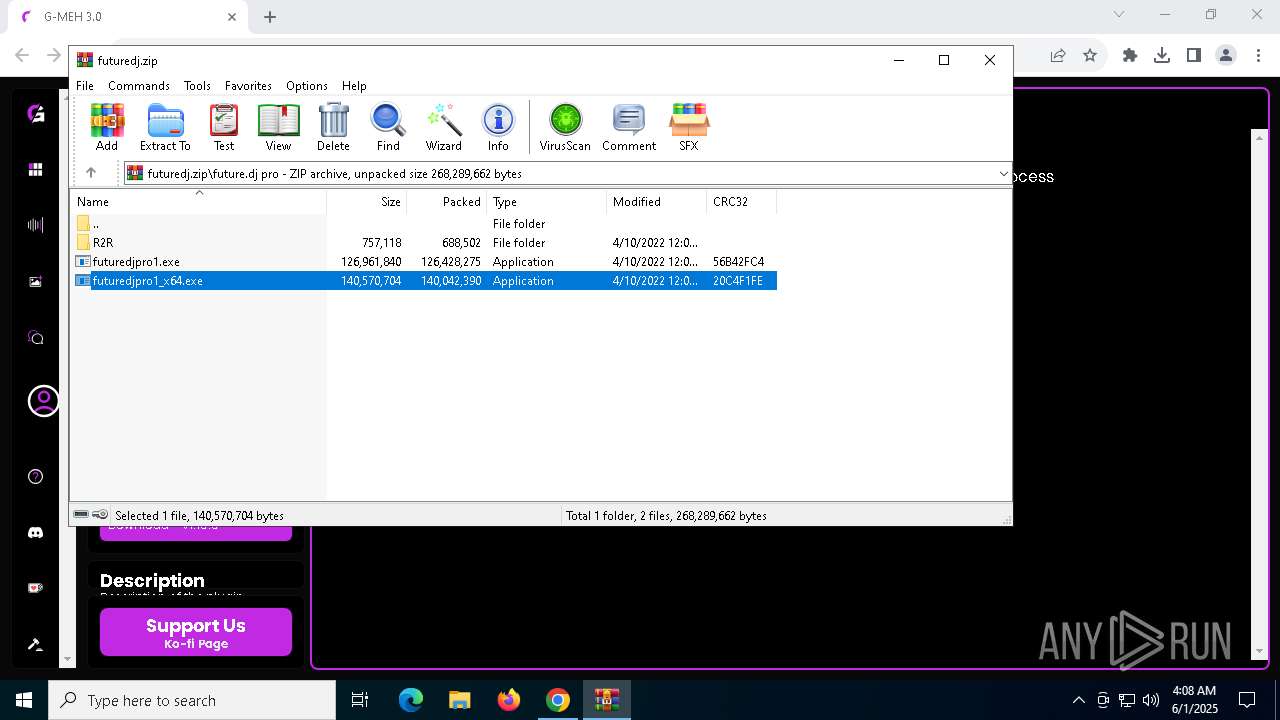
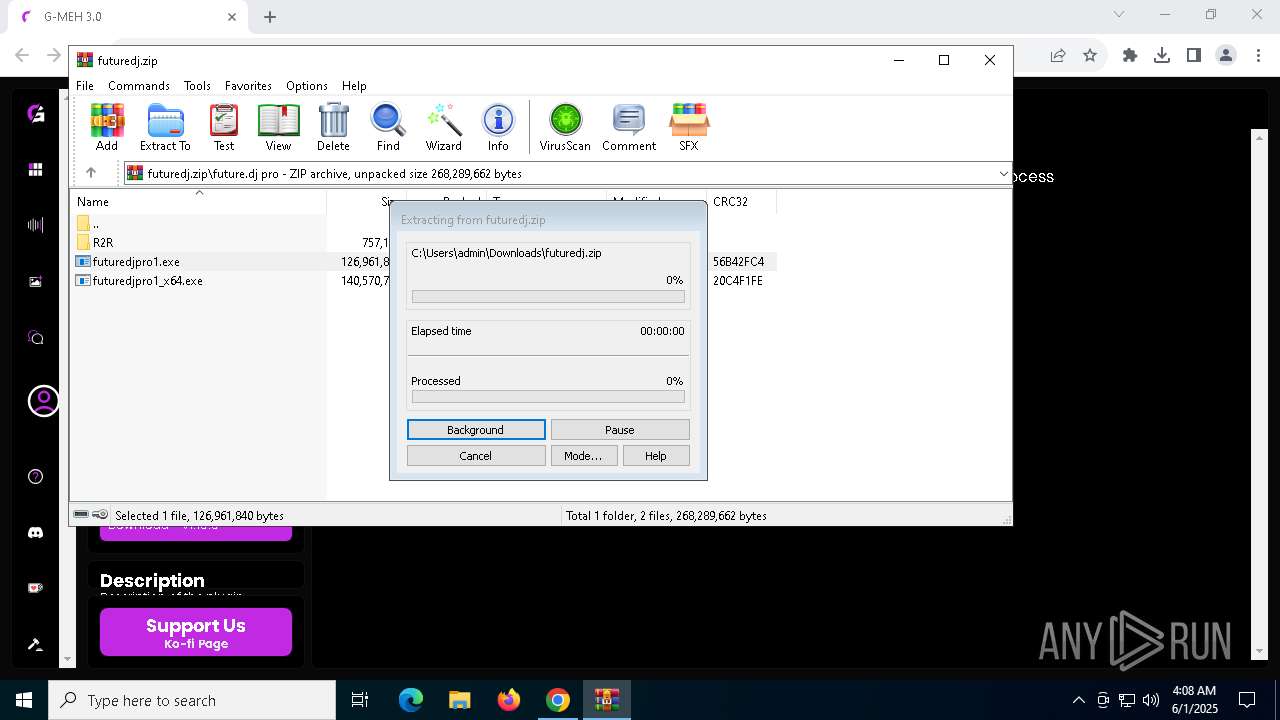
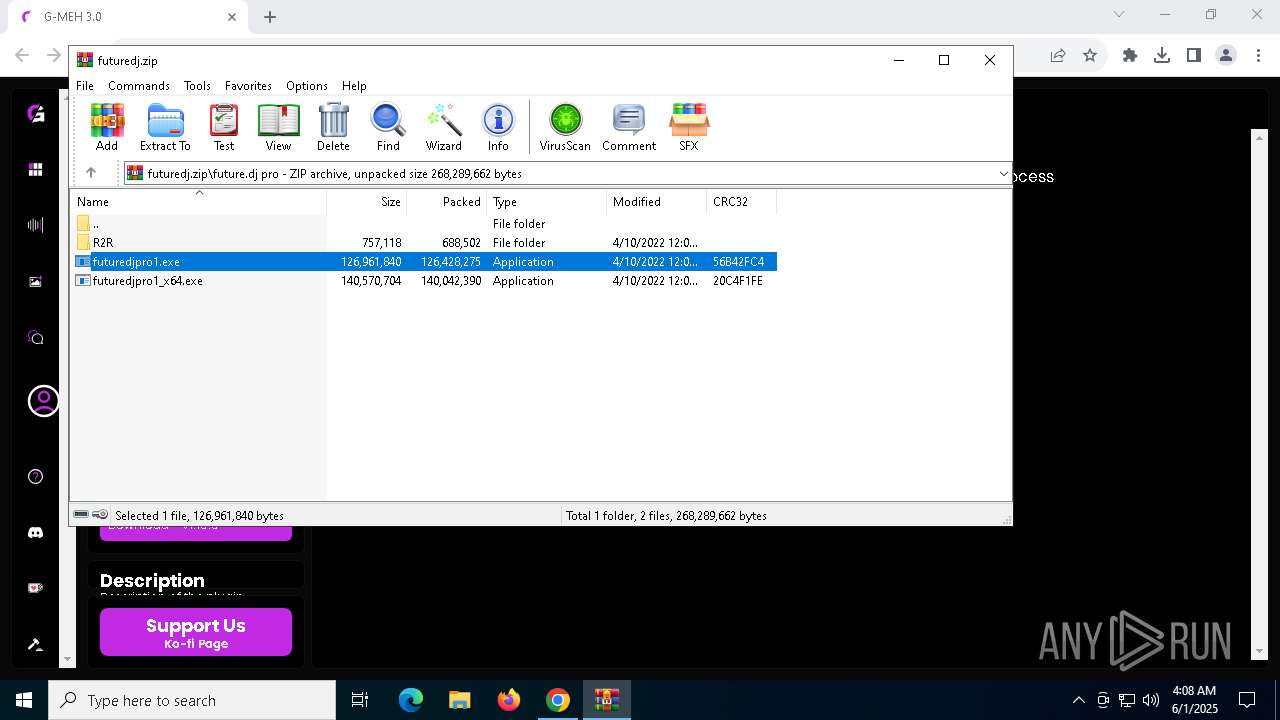
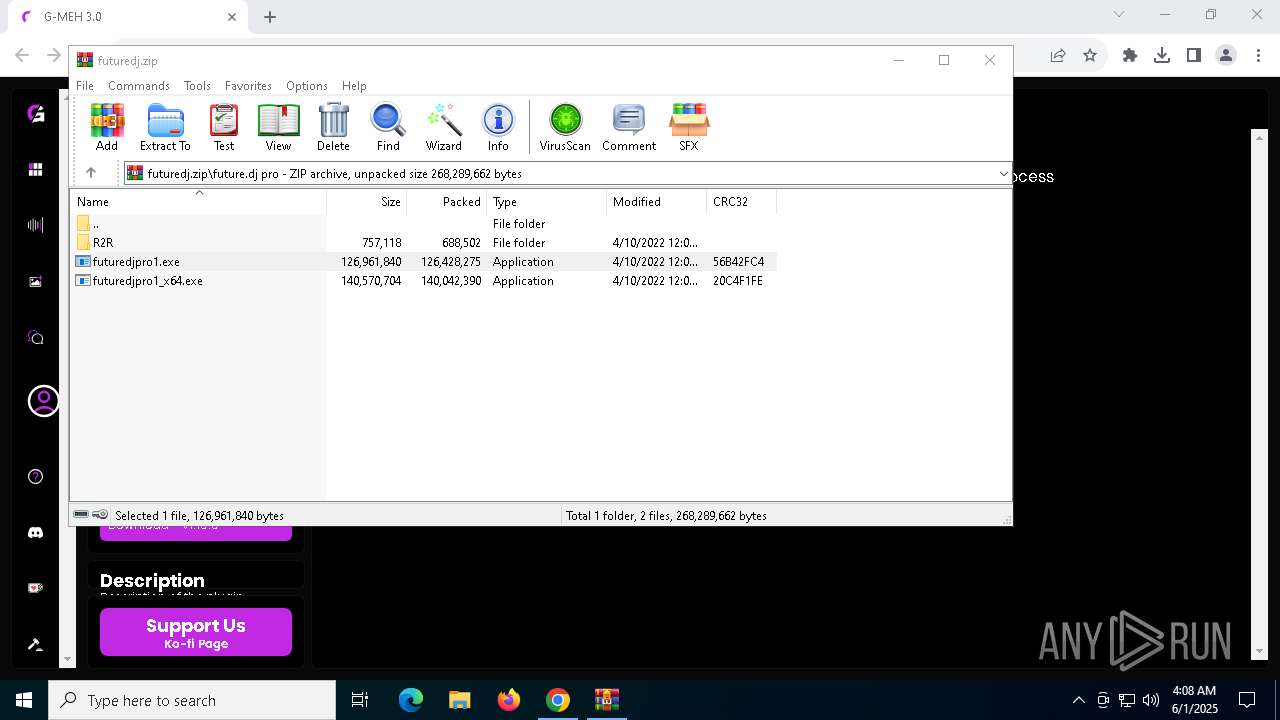
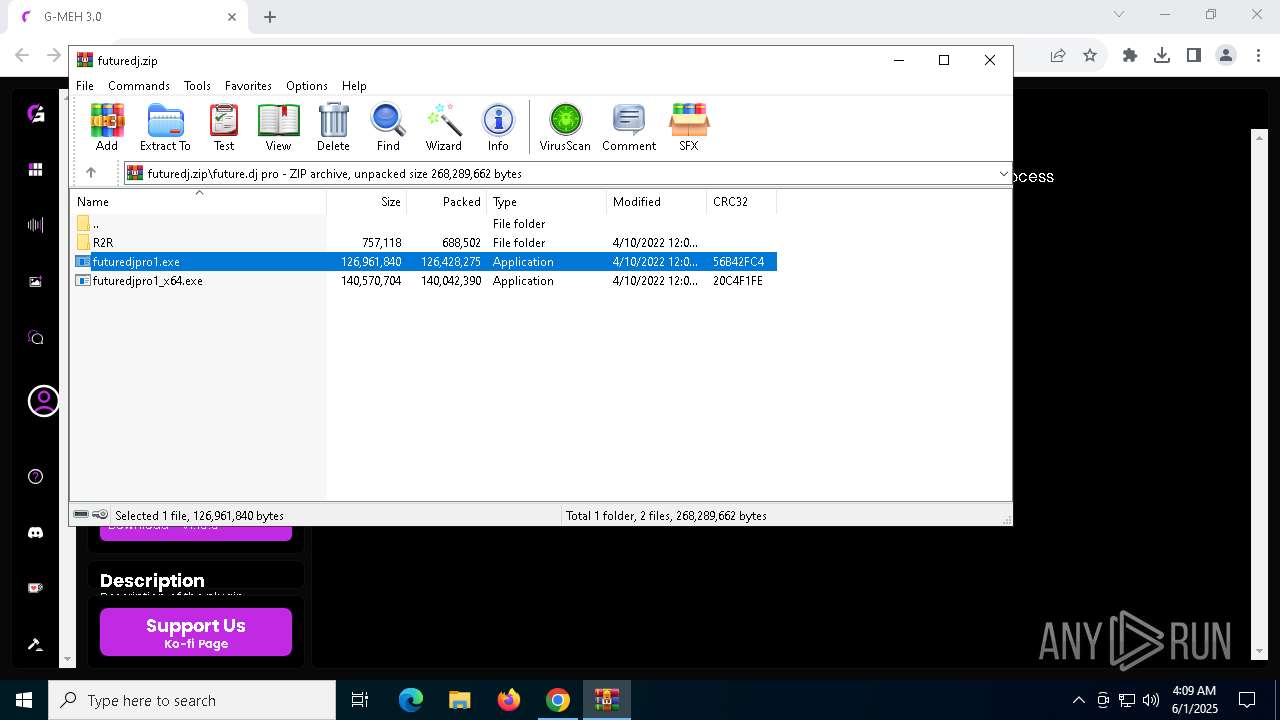
Executable content was dropped or overwritten
- WinRAR.exe (PID: 5568)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
176
Monitored processes
38
Malicious processes
10
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
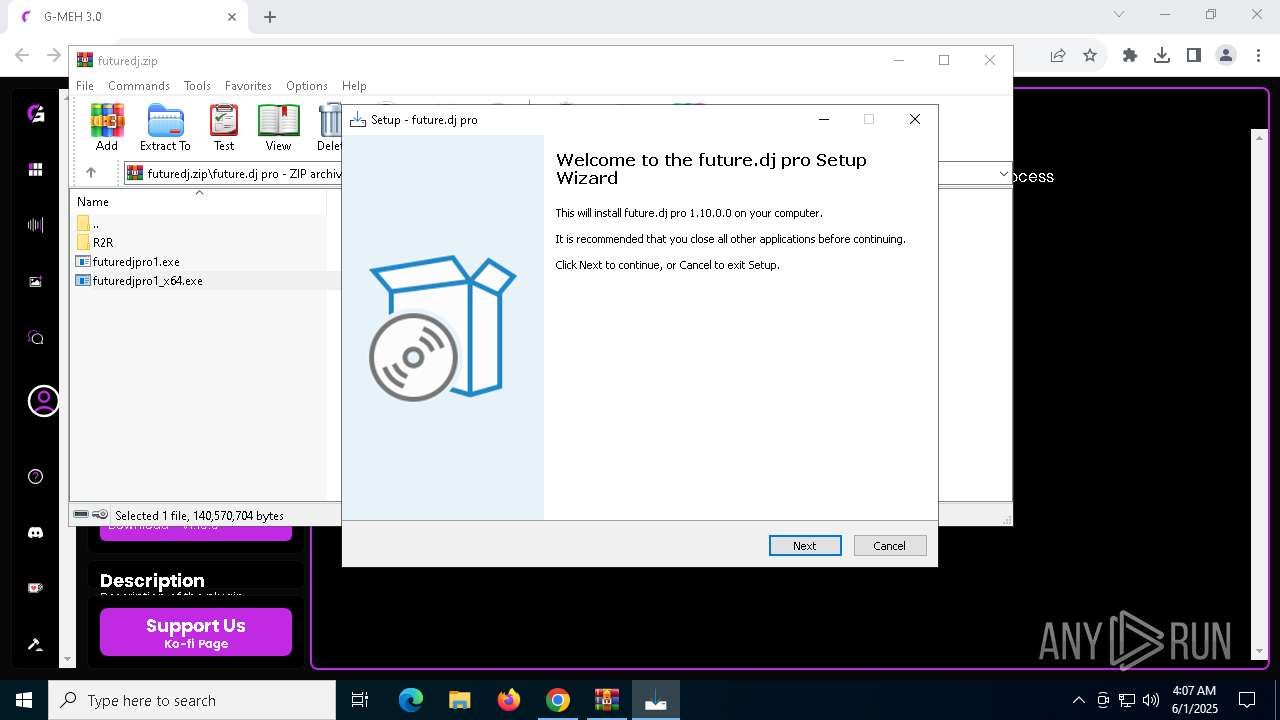
| 512 | "C:\Users\admin\AppData\Local\Temp\is-QURNS.tmp\futuredjpro1.tmp" /SL5="$30432,126107026,831488,C:\Users\admin\AppData\Local\Temp\Rar$EXa5568.23645\future.dj pro\futuredjpro1.exe" | C:\Users\admin\AppData\Local\Temp\is-QURNS.tmp\futuredjpro1.tmp | — | futuredjpro1.exe | |||||||||||
User: admin Company: XYLIO Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 1128 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
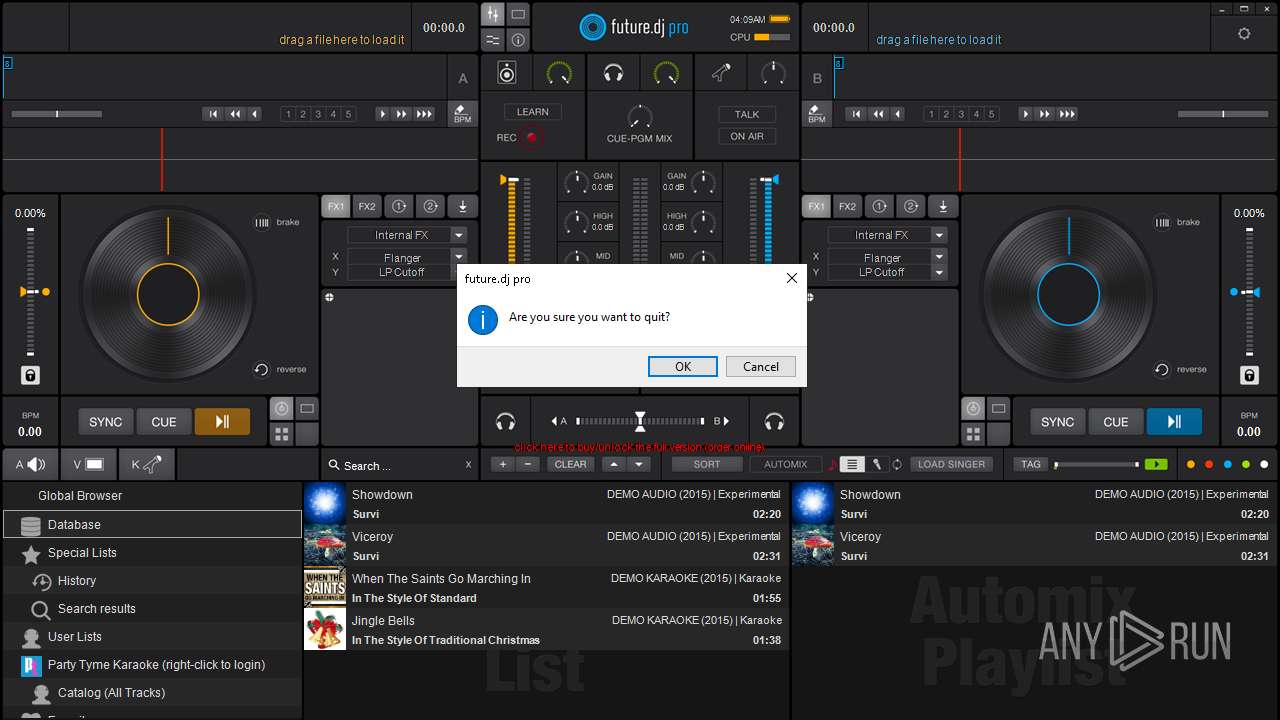
| 1284 | "C:\Program Files (x86)\XYLIO\futuredjpro\future.dj.exe" | C:\Program Files (x86)\XYLIO\futuredjpro\future.dj.exe | futuredjpro1.tmp | ||||||||||||
User: admin Integrity Level: MEDIUM Description: future.dj pro mixing software Exit code: 0 Version: 1, 10, 0, 0 Modules
| |||||||||||||||
| 2040 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=2976 --field-trial-handle=1828,i,1713975248896676665,10136367825191532751,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2136 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2616 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=3020 --field-trial-handle=1828,i,1713975248896676665,10136367825191532751,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2776 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa5568.23645\future.dj pro\futuredjpro1.exe" /SPAWNWND=$90328 /NOTIFYWND=$30432 | C:\Users\admin\AppData\Local\Temp\Rar$EXa5568.23645\future.dj pro\futuredjpro1.exe | futuredjpro1.tmp | ||||||||||||
User: admin Company: XYLIO Integrity Level: HIGH Description: future.dj pro Exit code: 0 Version: 1.10.0.0 Modules
| |||||||||||||||
| 3036 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgABAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=1832 --field-trial-handle=1828,i,1713975248896676665,10136367825191532751,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 3100 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4200 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking --disable-features=OptimizationGuideModelDownloading,OptimizationHintsFetching,OptimizationTargetPrediction,OptimizationHints "https://g-meh.com/library/windows/futuredj" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
Total events
12 714
Read events
12 617
Write events
90
Delete events
7
Modification events
| (PID) Process: | (4200) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (4200) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (4200) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4200) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (4200) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (4200) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.zip\OpenWithProgids |
| Operation: | write | Name: | WinRAR.ZIP |
Value: | |||
| (PID) Process: | (8160) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 01000000000000007613ACB4AAD2DB01 | |||
| (PID) Process: | (5568) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (5568) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (5568) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
Executable files
247
Suspicious files
230
Text files
1 014
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4200 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF11f4ec.TMP | — | |
MD5:— | SHA256:— | |||
| 4200 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4200 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF11f50b.TMP | — | |
MD5:— | SHA256:— | |||
| 4200 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4200 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF11f51b.TMP | — | |
MD5:— | SHA256:— | |||
| 4200 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4200 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF11f52b.TMP | — | |
MD5:— | SHA256:— | |||
| 4200 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4200 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old~RF11f53a.TMP | — | |
MD5:— | SHA256:— | |||
| 4200 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
27
TCP/UDP connections
64
DNS requests
56
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1452 | SIHClient.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.20.245.139:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7704 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/d2h35fn62bb25y57wur7fuqmby_1326/efniojlnjndmcbiieegkicadnoecjjef_1326_all_mvjo26dw4auk2xeiynlzuanqle.crx3 | unknown | — | — | whitelisted |
7704 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/d2h35fn62bb25y57wur7fuqmby_1326/efniojlnjndmcbiieegkicadnoecjjef_1326_all_mvjo26dw4auk2xeiynlzuanqle.crx3 | unknown | — | — | whitelisted |
7704 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/d2h35fn62bb25y57wur7fuqmby_1326/efniojlnjndmcbiieegkicadnoecjjef_1326_all_mvjo26dw4auk2xeiynlzuanqle.crx3 | unknown | — | — | whitelisted |
7704 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/d2h35fn62bb25y57wur7fuqmby_1326/efniojlnjndmcbiieegkicadnoecjjef_1326_all_mvjo26dw4auk2xeiynlzuanqle.crx3 | unknown | — | — | whitelisted |
7704 | svchost.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac6mhlwypzipnufijdvfyhdgvt4q_67/khaoiebndkojlmppeemjhbpbandiljpe_67_win_kfegpqlp6gezs4ree2ol2br2ym.crx3 | unknown | — | — | whitelisted |
7704 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/d2h35fn62bb25y57wur7fuqmby_1326/efniojlnjndmcbiieegkicadnoecjjef_1326_all_mvjo26dw4auk2xeiynlzuanqle.crx3 | unknown | — | — | whitelisted |
7704 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/d2h35fn62bb25y57wur7fuqmby_1326/efniojlnjndmcbiieegkicadnoecjjef_1326_all_mvjo26dw4auk2xeiynlzuanqle.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
7636 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
7572 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.20.245.139:80 | crl.microsoft.com | Akamai International B.V. | SE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.219.150.101:80 | www.microsoft.com | AKAMAI-AS | CL | whitelisted |
4200 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2112 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5972 | chrome.exe | 142.251.168.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
5972 | chrome.exe | 172.67.156.6:443 | g-meh.com | CLOUDFLARENET | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
g-meh.com |
| malicious |
accounts.google.com |
| whitelisted |
rum.cronitor.io |
| unknown |
o4508966577242112.ingest.de.sentry.io |
| whitelisted |
static.cloudflareinsights.com |
| whitelisted |
a.nel.cloudflare.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5972 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
5972 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] An application monitoring request to sentry .io |