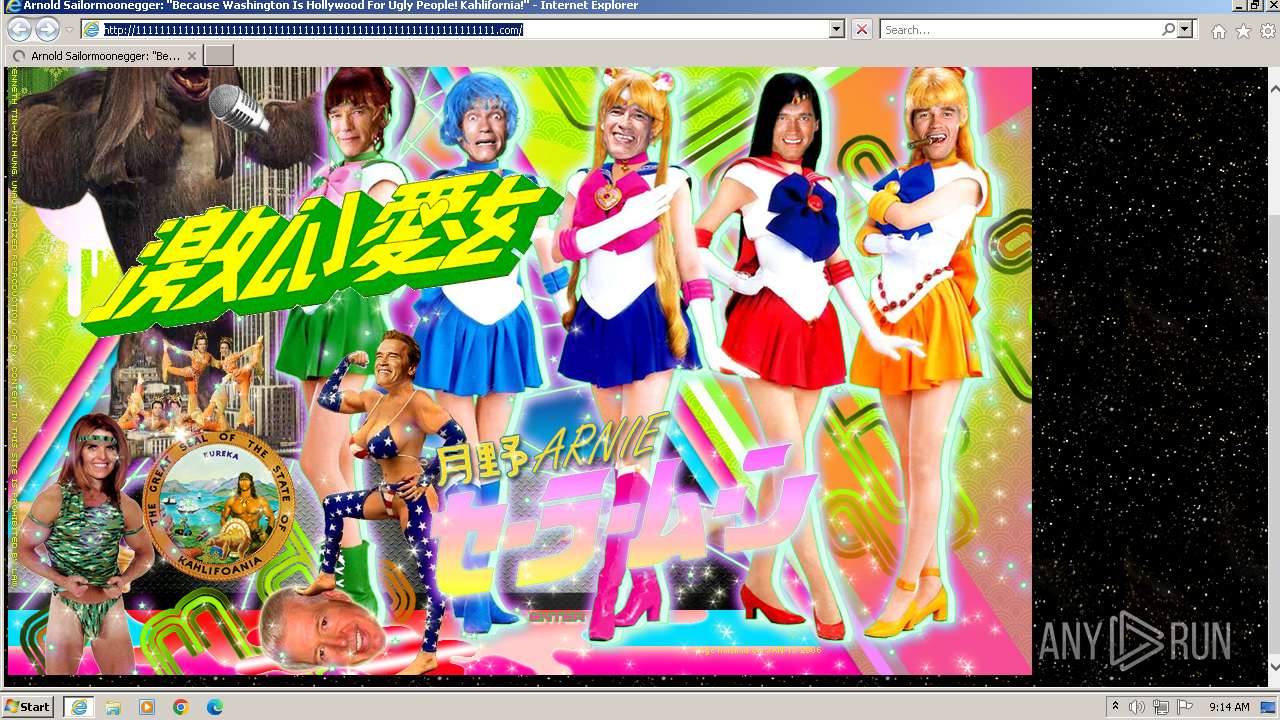
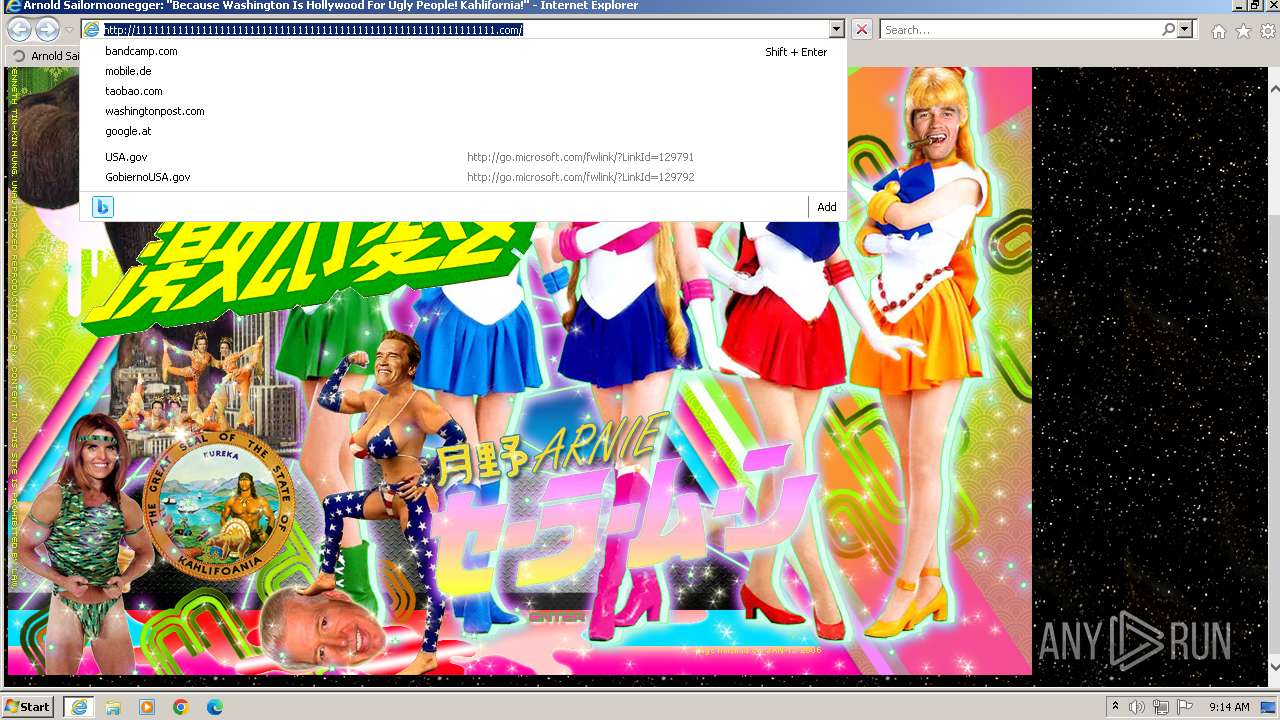
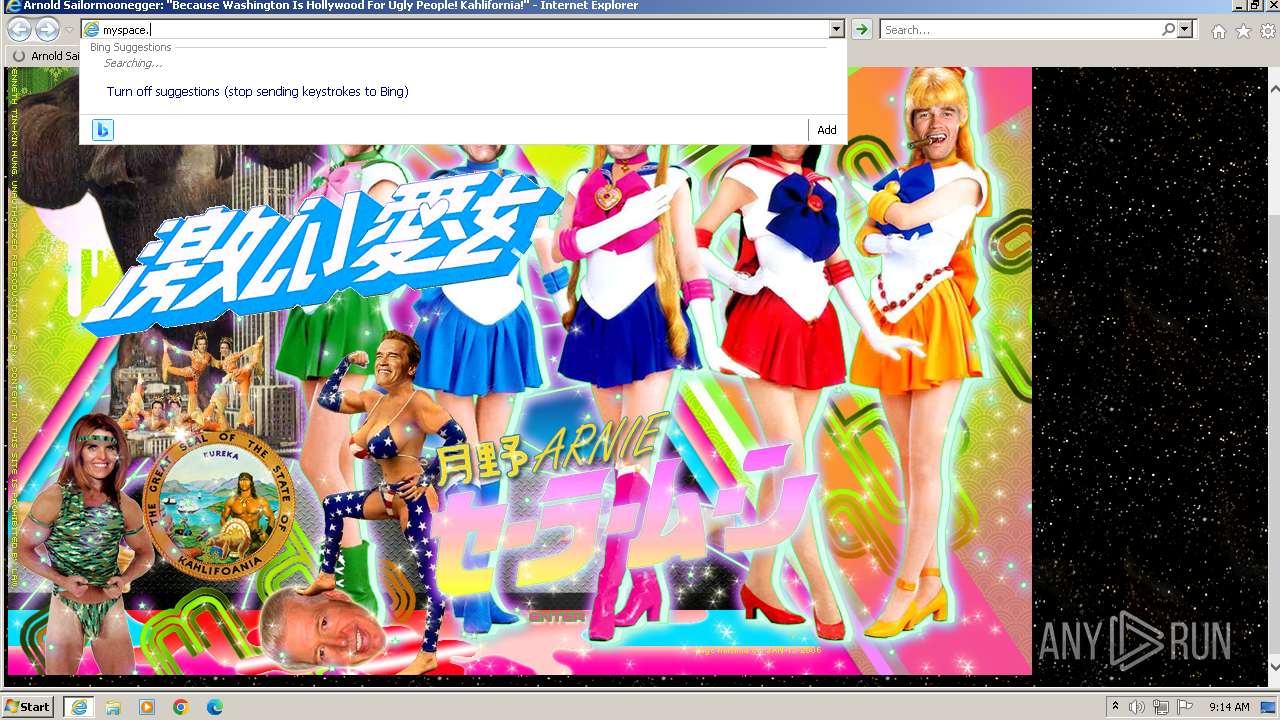
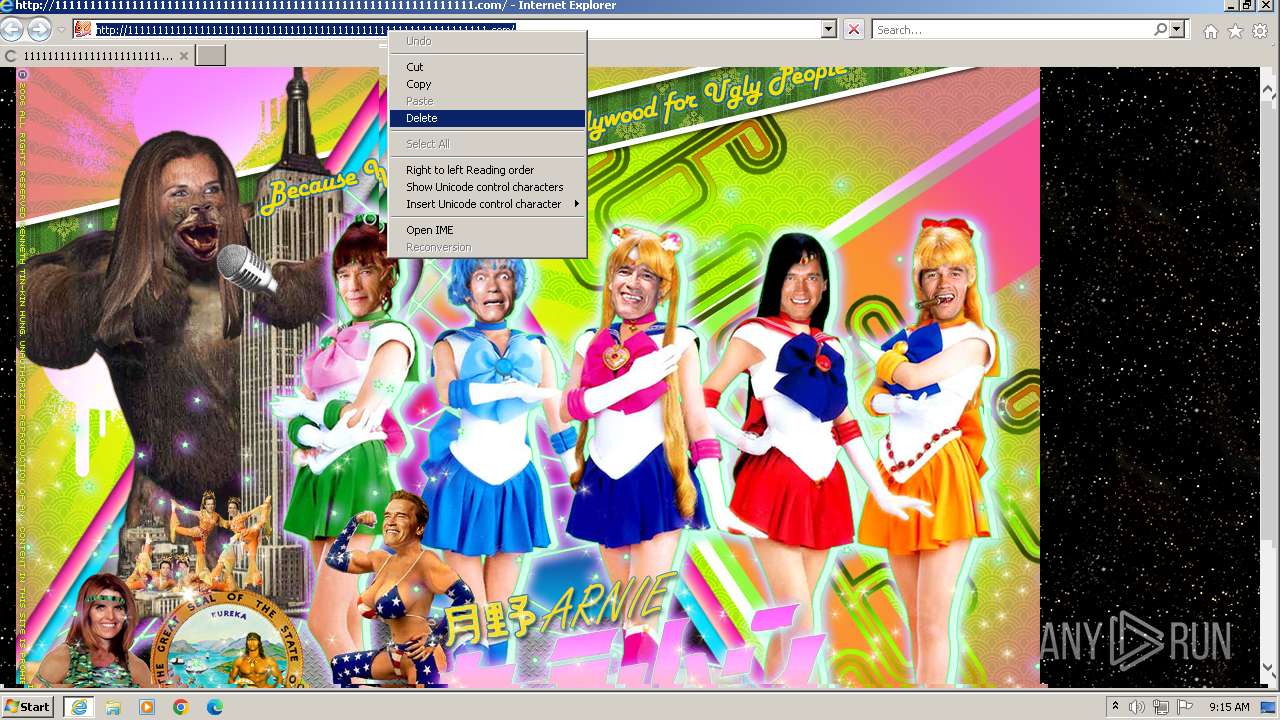
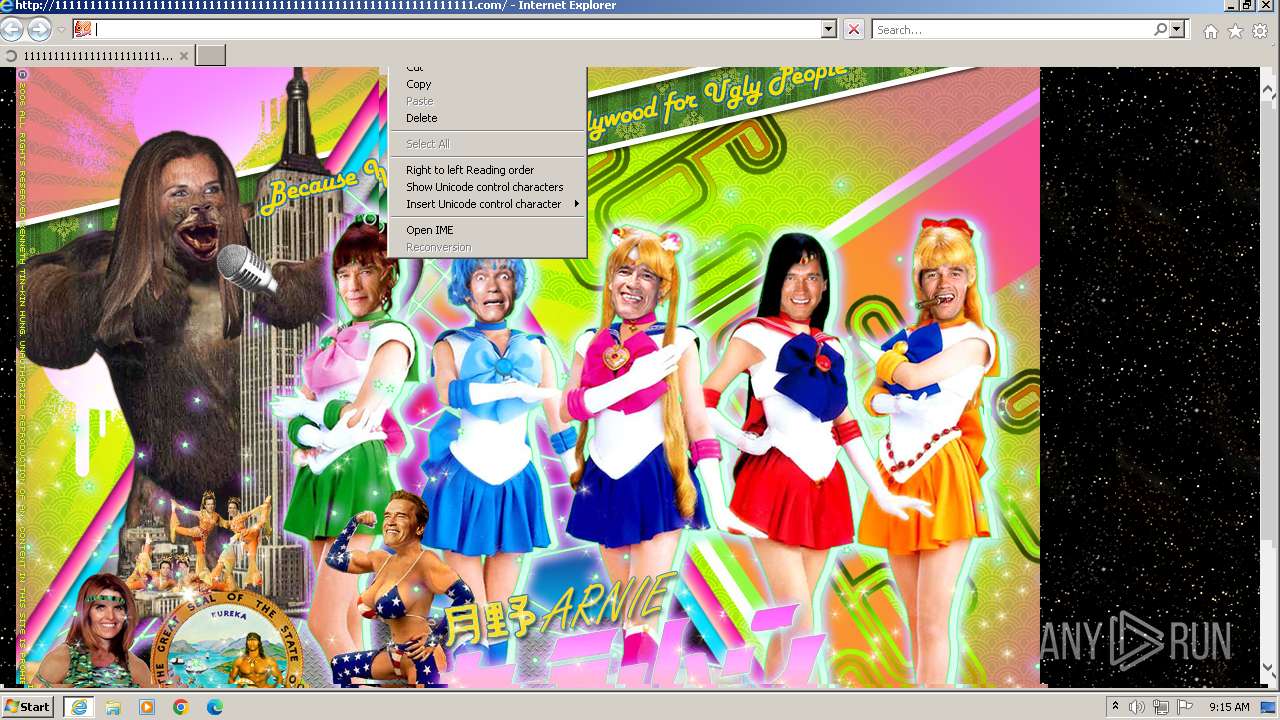
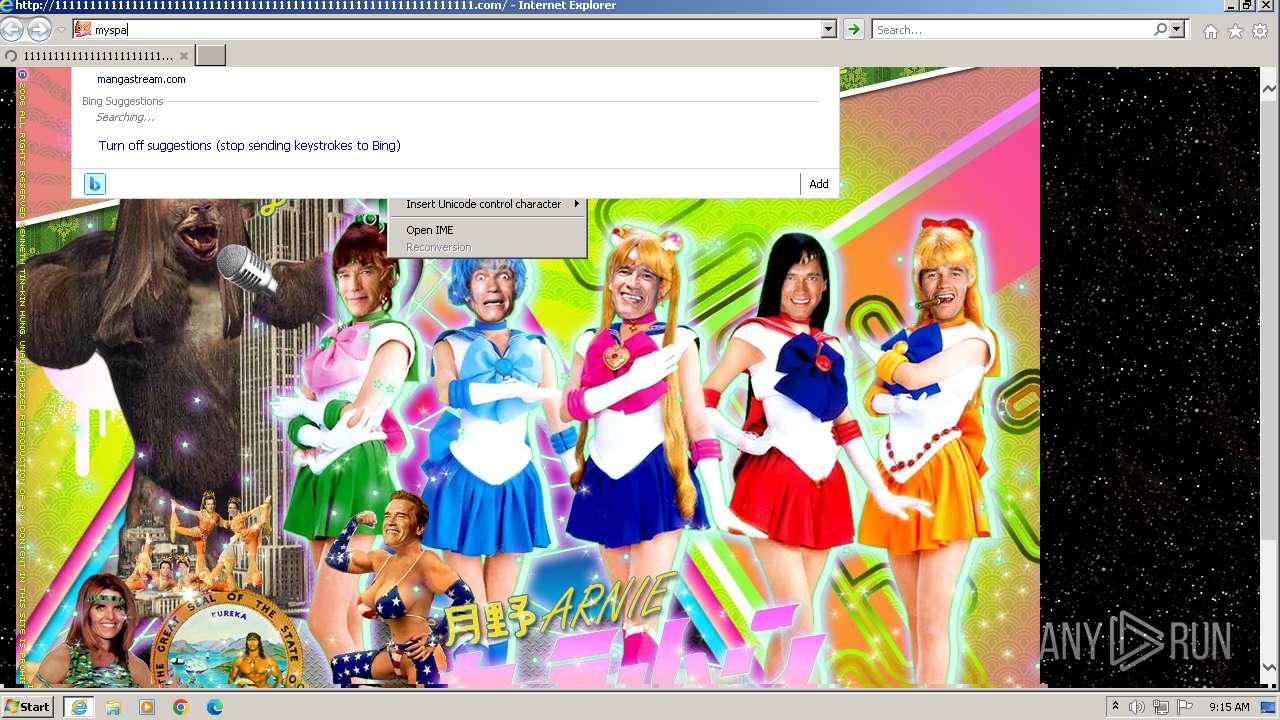
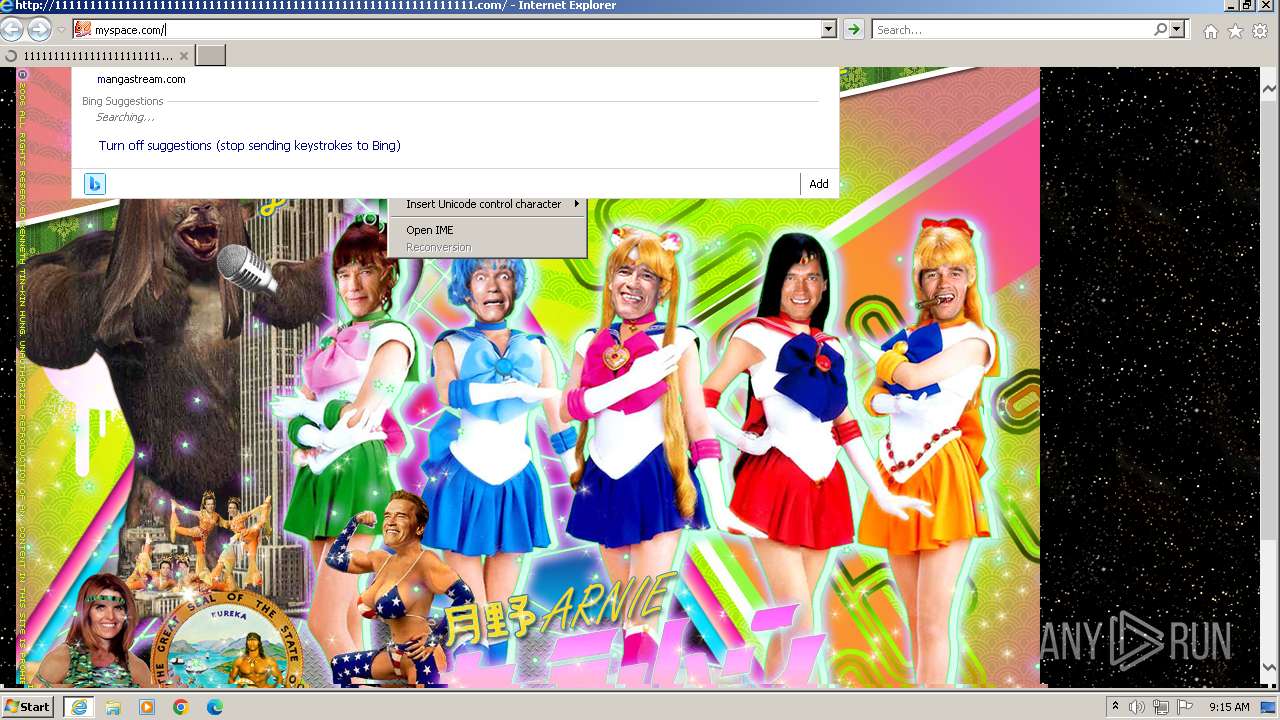
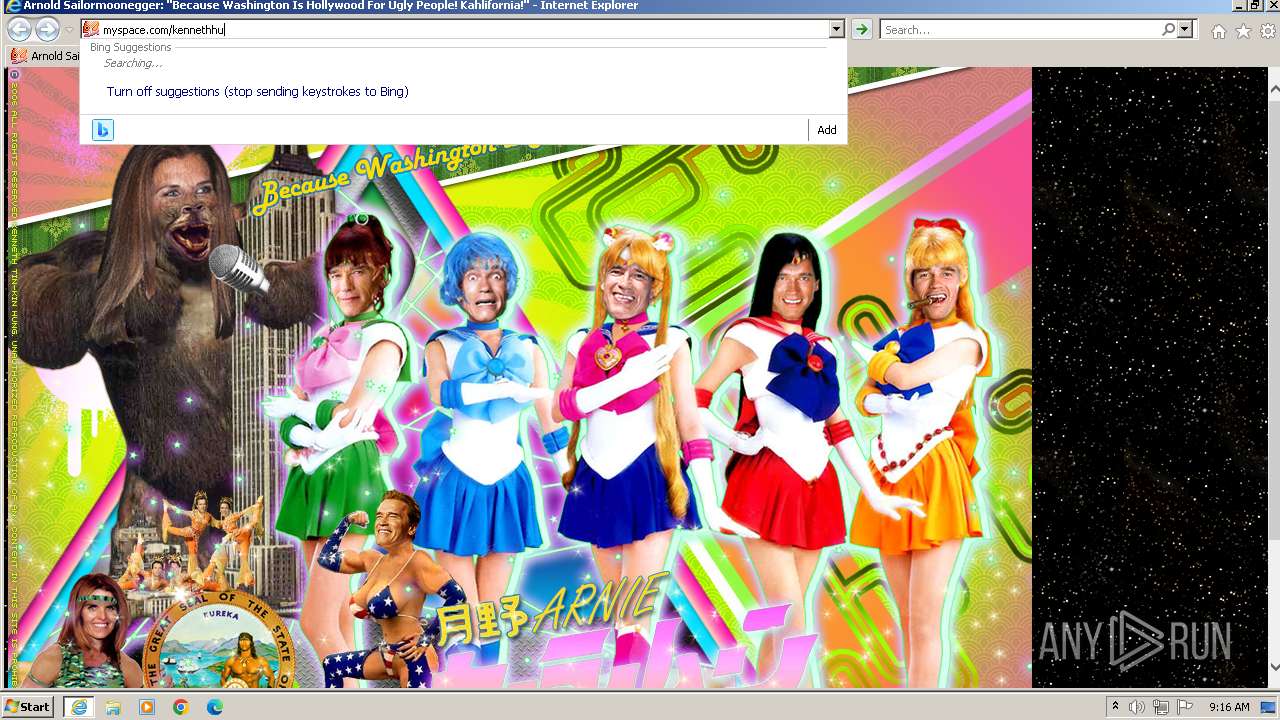
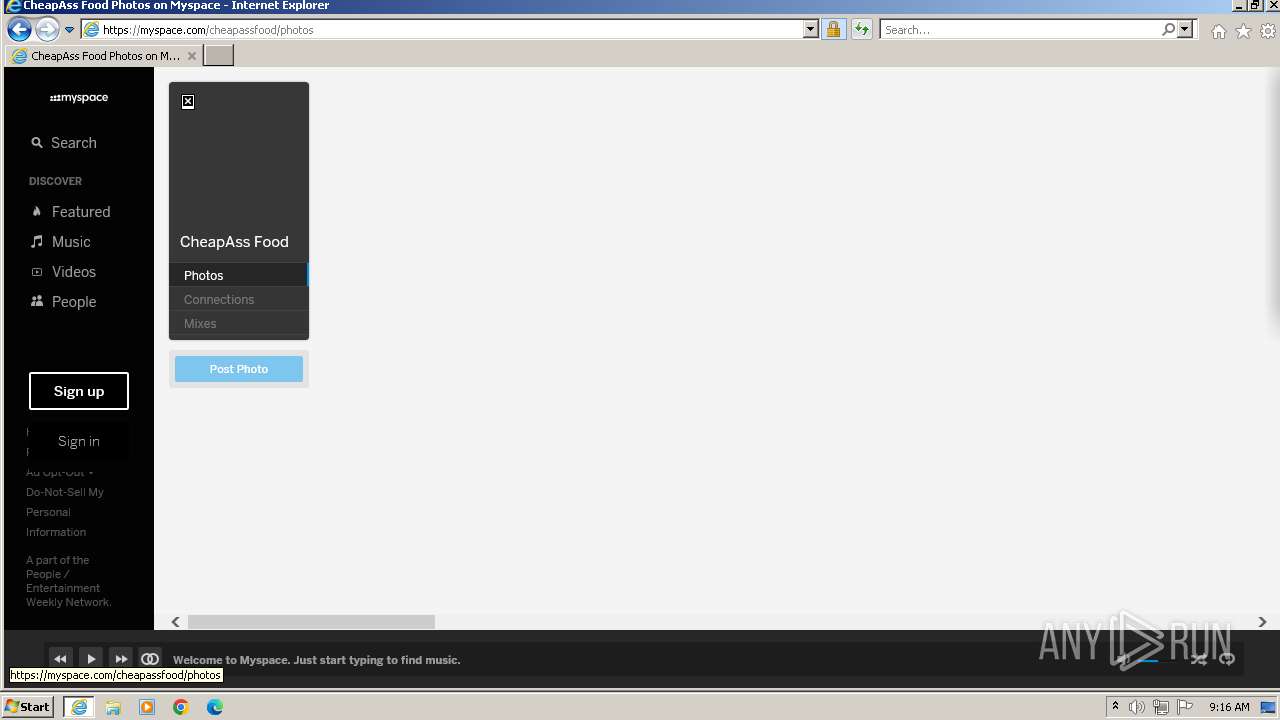
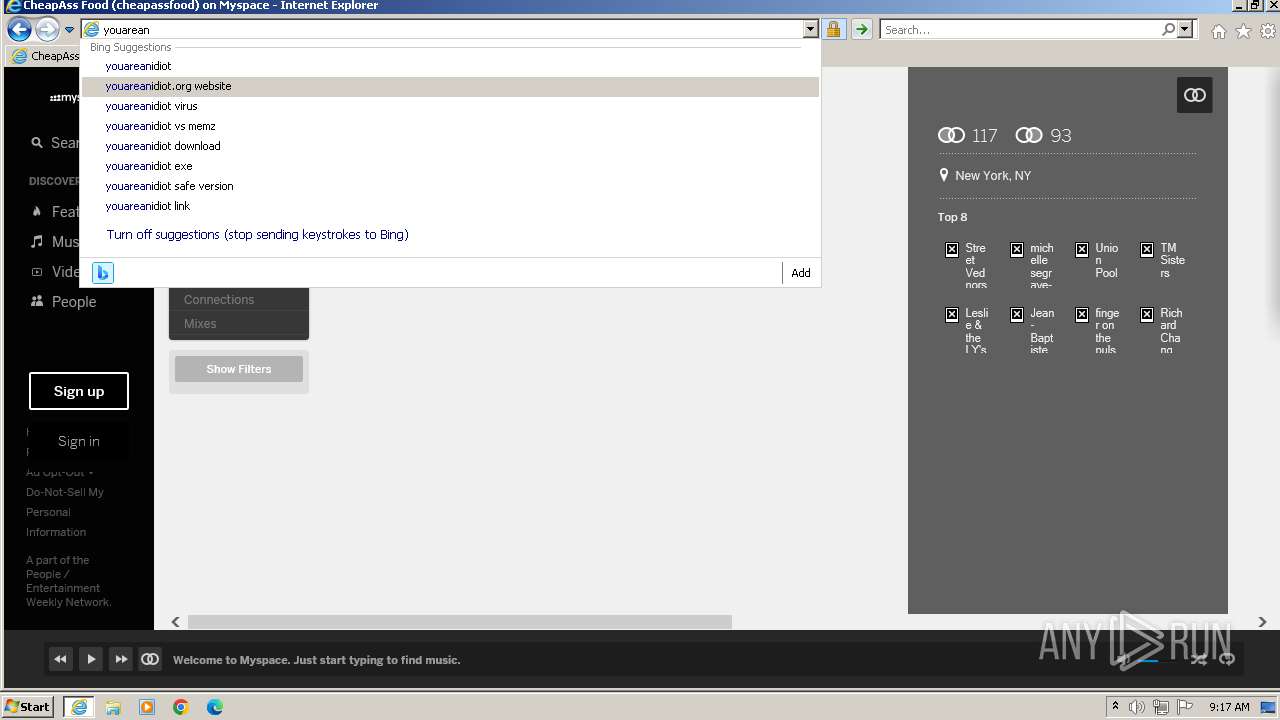
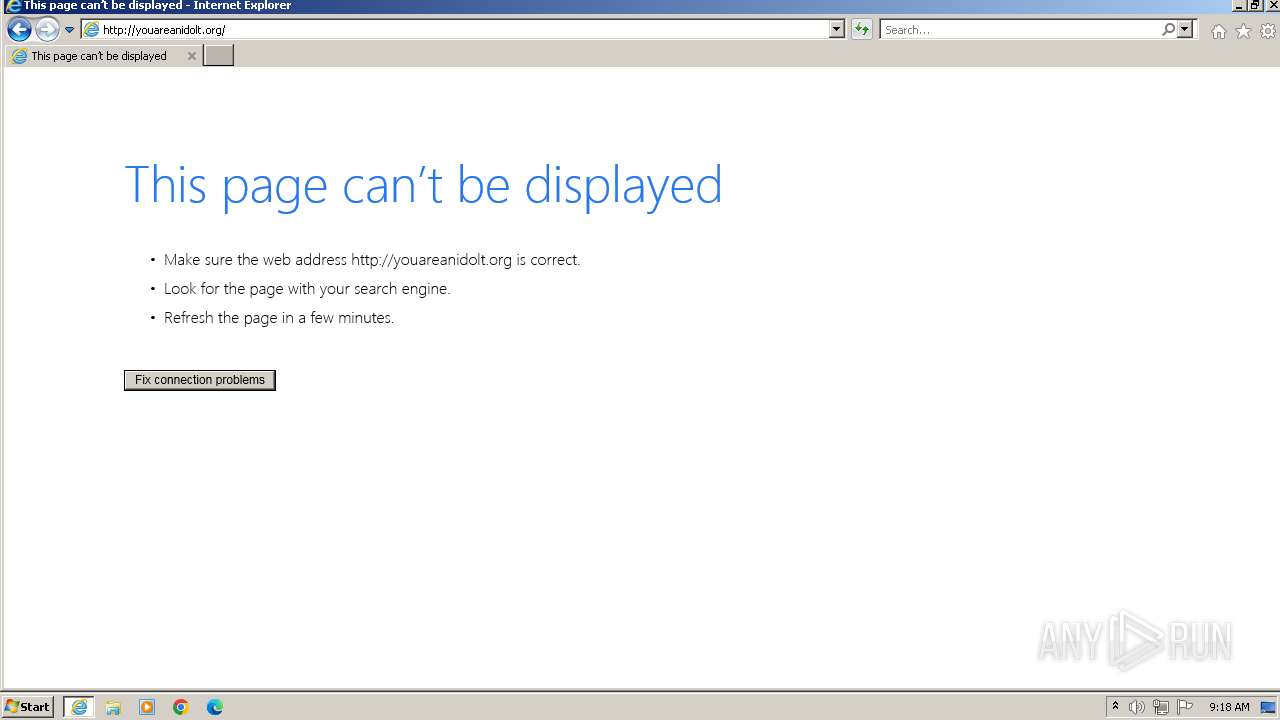
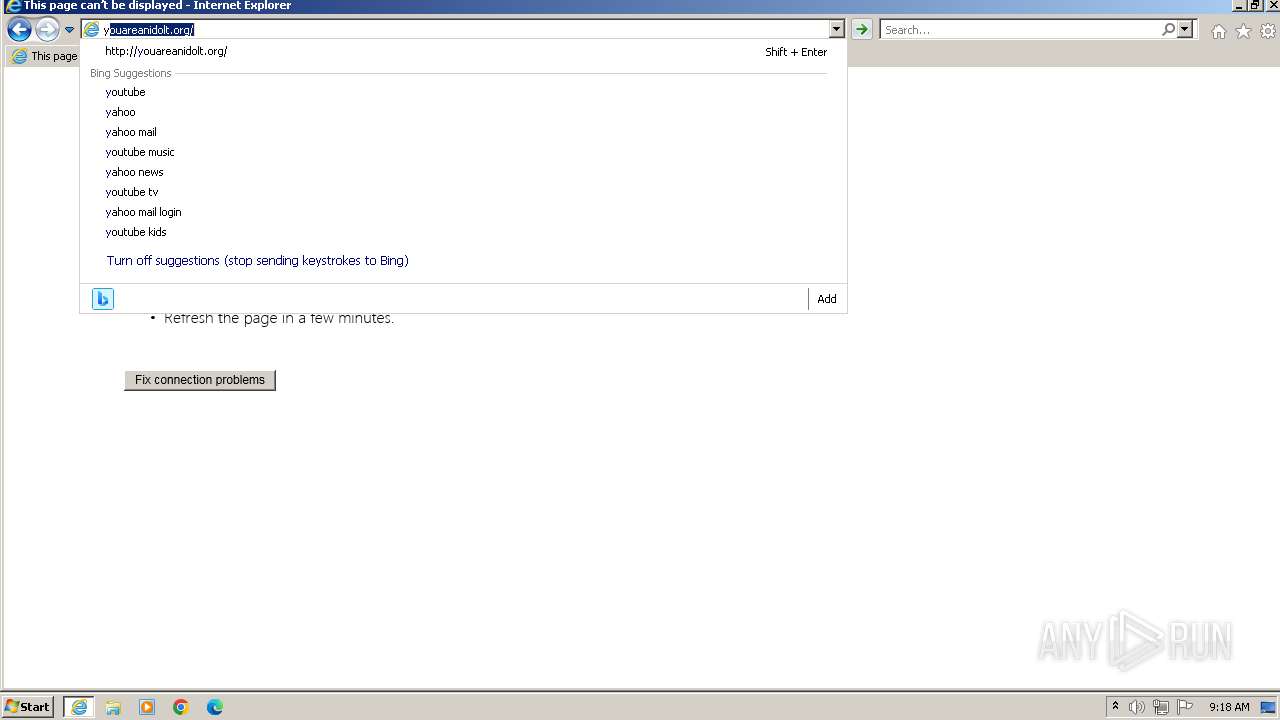
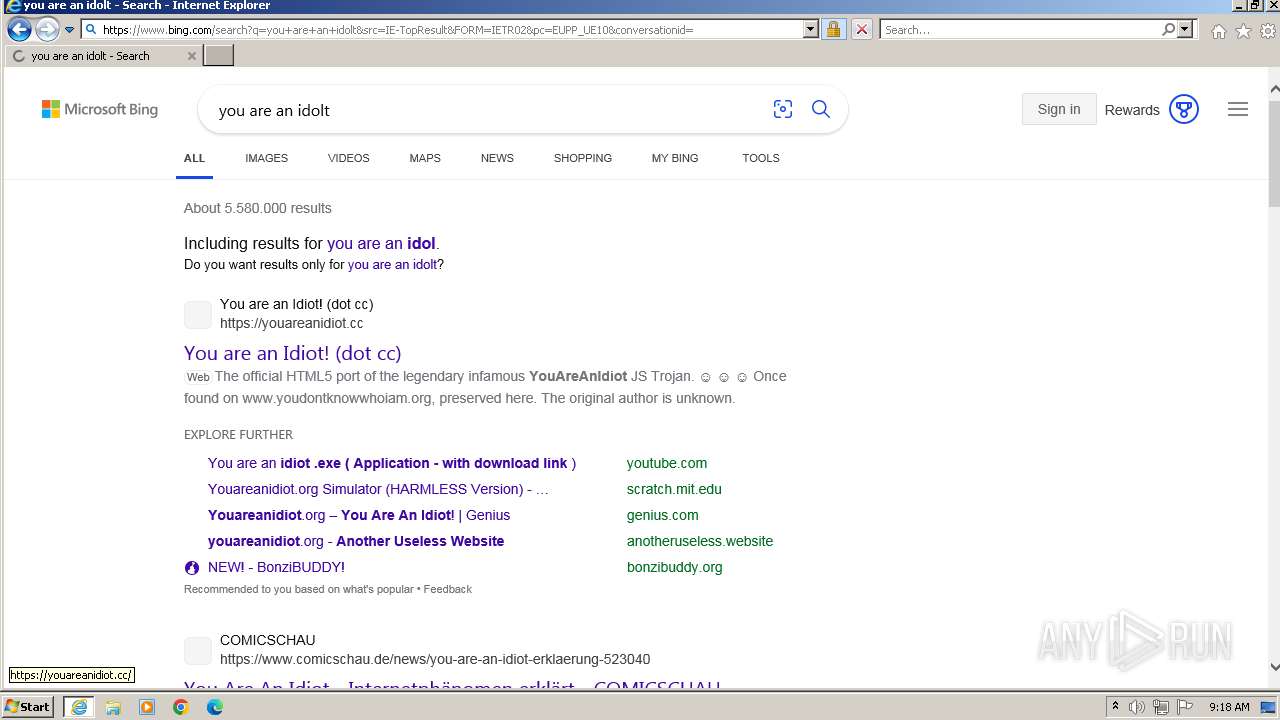
| URL: | 111111111111111111111111111111111111111111111111111111111111.com |
| Full analysis: | https://app.any.run/tasks/96ee8d9e-ea16-4f1a-beef-7df35ad7c1cb |
| Verdict: | Malicious activity |
| Analysis date: | November 24, 2023, 09:13:49 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| SHA1: | D90174546F68A1B3B9D7316F6980B479F2122DF2 |
| SHA256: | BC138AAF45F2F20CF9A181B84F7297055B4B000BA0FCCC8E593D882F17519DFD |
| SSDEEP: | 3:NDMKI:uT |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Checks supported languages
- wmpnscfg.exe (PID: 1128)
Reads the computer name
- wmpnscfg.exe (PID: 1128)
Manual execution by a user
- wmpnscfg.exe (PID: 1128)
Application launched itself
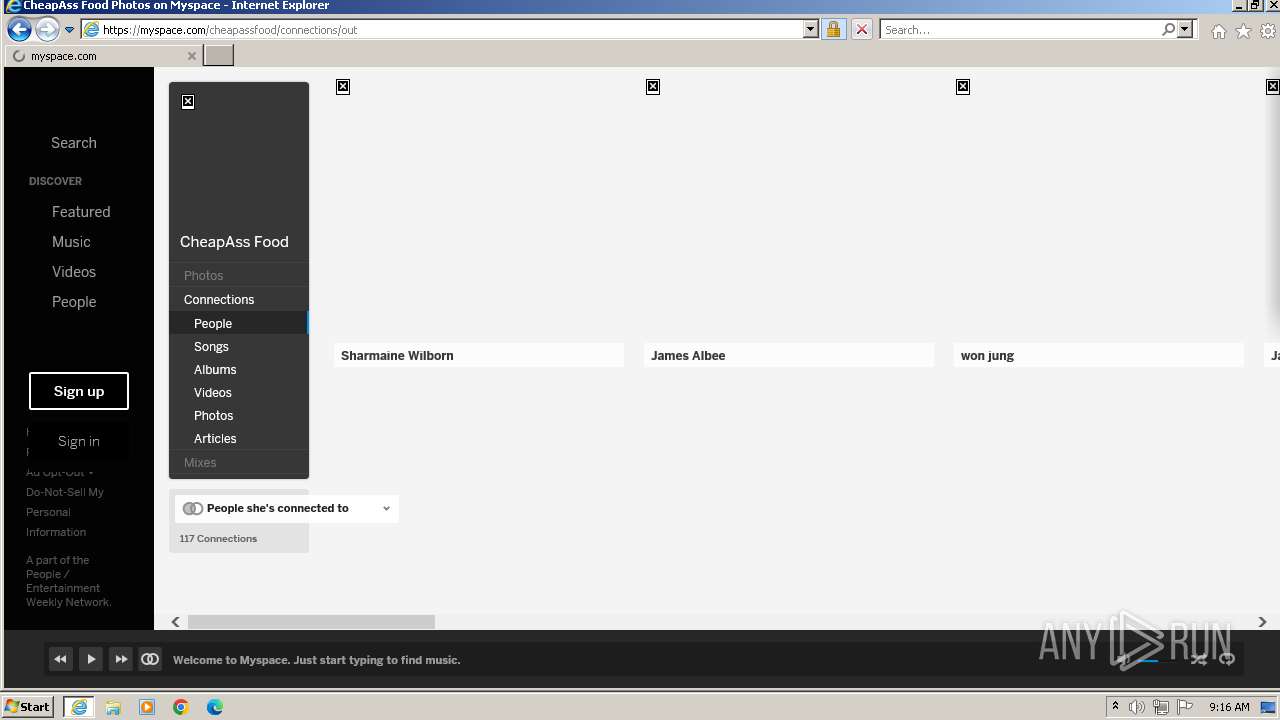
- iexplore.exe (PID: 2876)
Reads the machine GUID from the registry
- wmpnscfg.exe (PID: 1128)
The process uses the downloaded file
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 3204)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
46
Monitored processes
4
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1128 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2496 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2876 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
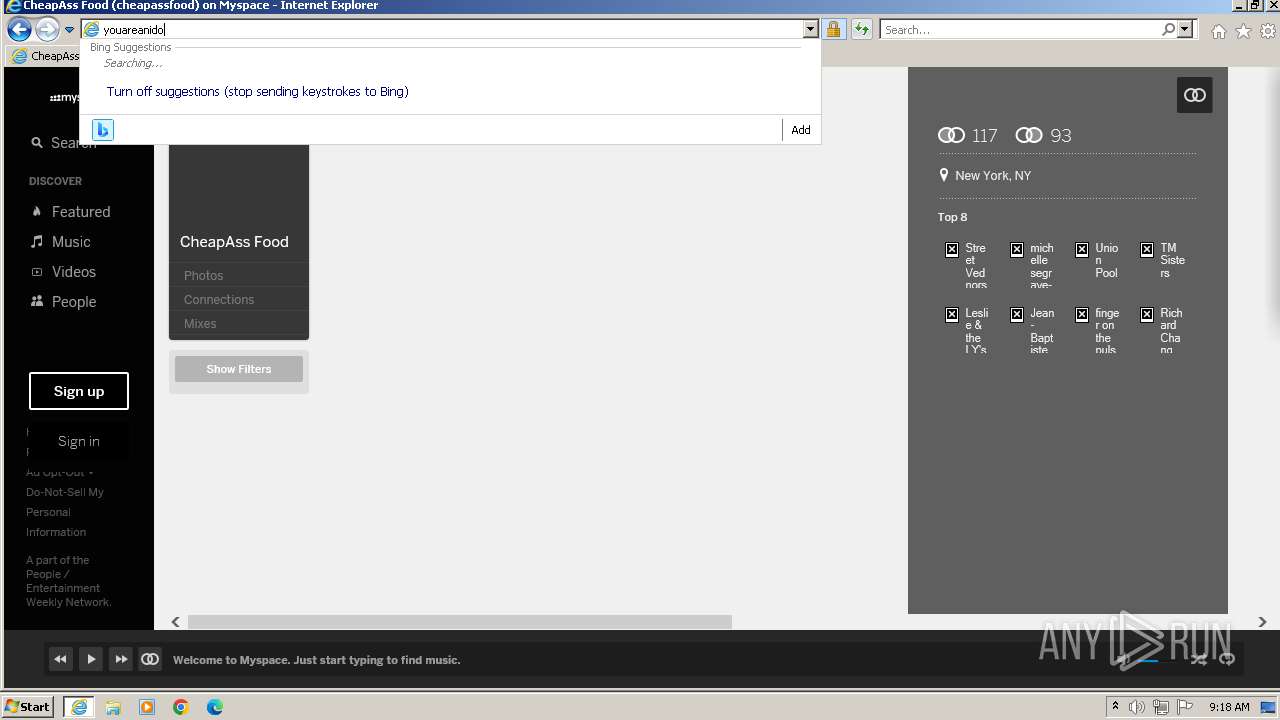
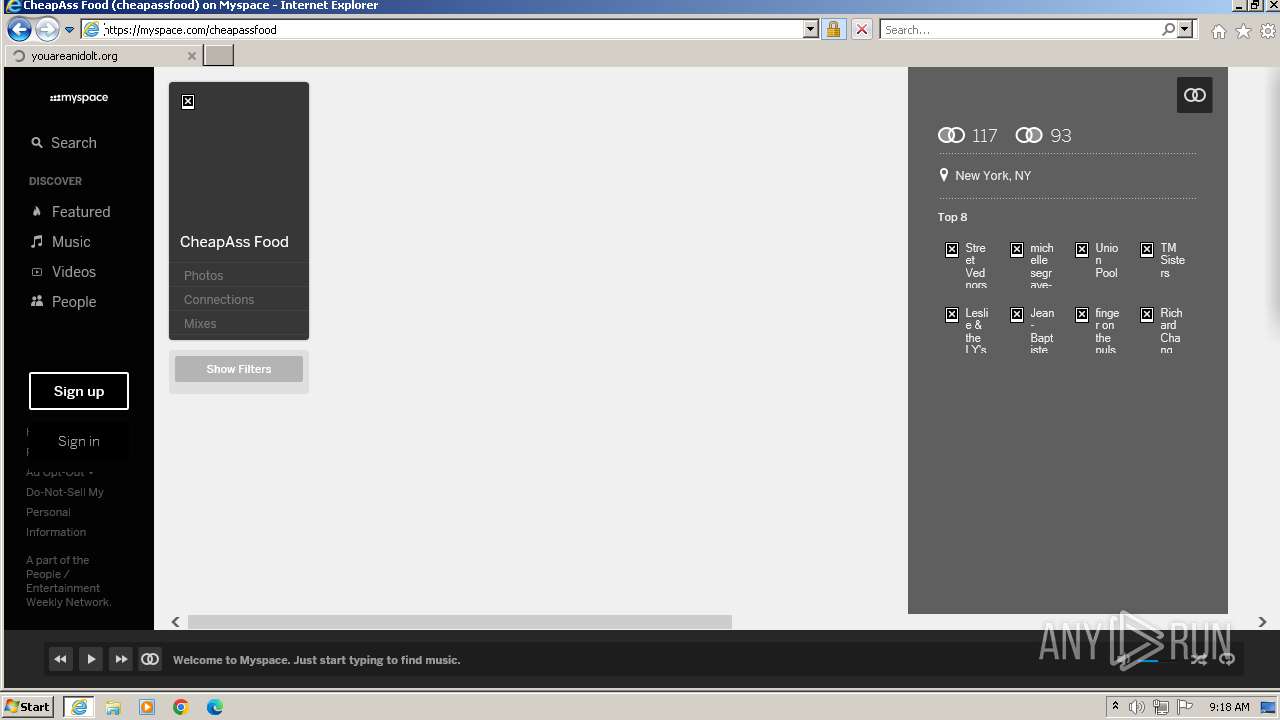
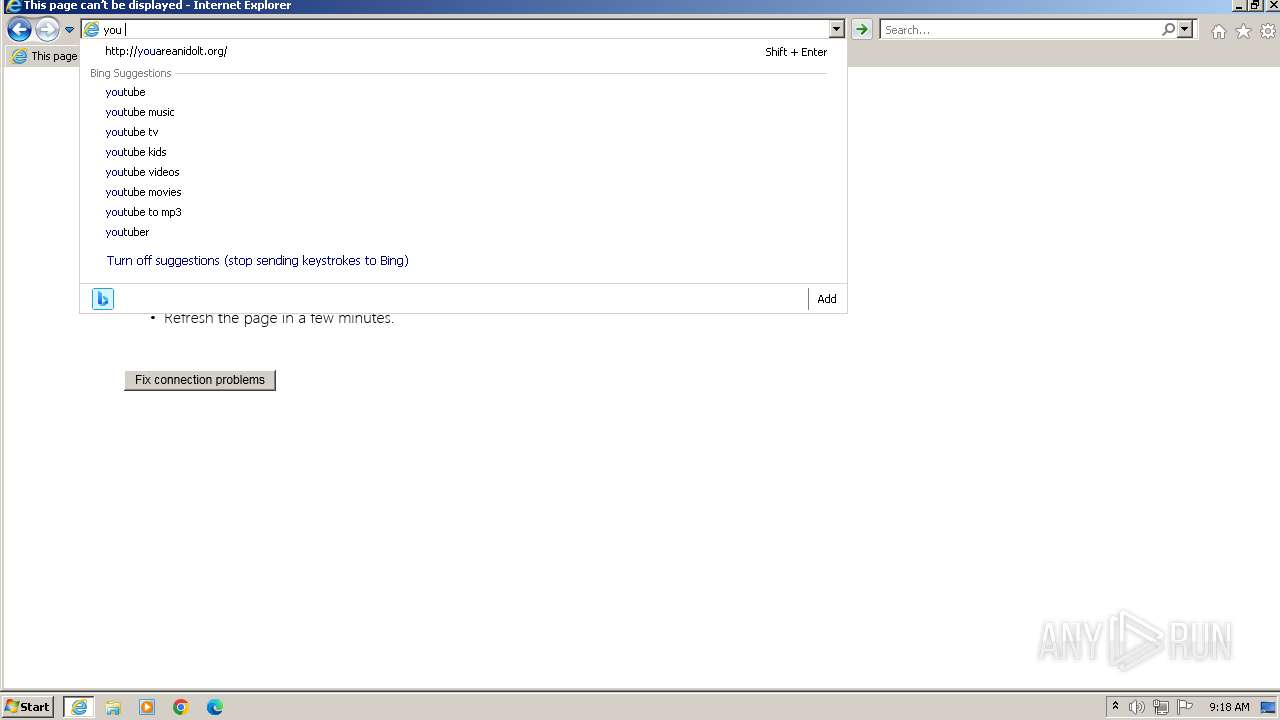
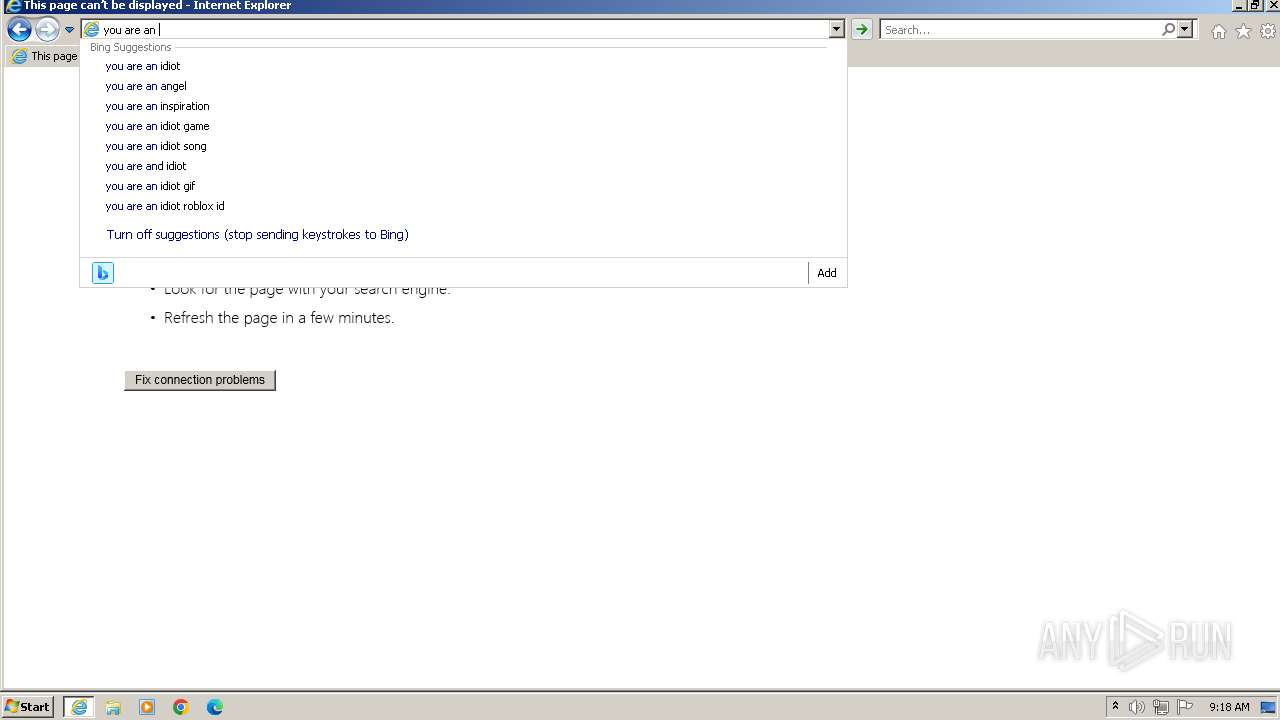
| 2876 | "C:\Program Files\Internet Explorer\iexplore.exe" "111111111111111111111111111111111111111111111111111111111111.com" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3204 | C:\Windows\system32\Macromed\Flash\FlashUtil32_32_0_0_453_ActiveX.exe -Embedding | C:\Windows\System32\Macromed\Flash\FlashUtil32_32_0_0_453_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 32.0 r0 Exit code: 0 Version: 32,0,0,453 Modules
| |||||||||||||||
Total events
43 736
Read events
43 536
Write events
197
Delete events
3
Modification events
| (PID) Process: | (2876) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (2876) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (2876) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (2876) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2876) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2876) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2876) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2876) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2876) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2876) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
0
Suspicious files
113
Text files
367
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2496 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\28N7QOG6.htm | html | |
MD5:5A8AD9E6BBB9C42EE5124ED54F8DC901 | SHA256:1FFB2CD43668A2CA6659A9D9D21C5EC1B921FCB9CFB561E7484A9CC9099F5315 | |||
| 2496 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\arniegun[1].gif | image | |
MD5:52C3C3ADBE6F60BAB80912F8CBA8A4C2 | SHA256:6F7E03CF52E739C305B33522D3C007C6C36B0A839CC872CE1844C23CF16C78E1 | |||
| 2876 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:83166CFBAC0F447171FFB3AF972A1DC7 | SHA256:720353997184079A0720C2FFC14C4FB4499015943B684E31FD8EBB274E629ED0 | |||
| 2496 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\holyplasticbeefy[1].gif | image | |
MD5:B1C3C1C6C22AC90B421BDA4439727432 | SHA256:E824A68801EA2D3D6CBE4E2DA0286514EDE46FDEBBB8F2B4BBAC1299FAAD869F | |||
| 2496 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\deepspace[1].gif | image | |
MD5:BB13707F9BE2A1DEEBD8731B2462A849 | SHA256:56E321770CFC41E2EE60AE283D2EC282587366C9EECEC0FEE74B46CFCC991D07 | |||
| 2496 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\sailarwordsimages[1].gif | image | |
MD5:437B914F45386E719F7129516BA22015 | SHA256:95A2B0144D56245BF2A592C7EBA80D06E037F271278A2B2E7E9C11E36E615DEB | |||
| 2876 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\80237EE4964FC9C409AAF55BF996A292_C5130A0BDC8C859A2757D77746C10868 | binary | |
MD5:A4EB5FBFE7C1092C3ED29FDEE30A8959 | SHA256:50112DC8D8A1CAC38DD81AA47F7ED878A81979D5C2C02629527D31235822A0F0 | |||
| 2876 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:1BFE591A4FE3D91B03CDF26EAACD8F89 | SHA256:9CF94355051BF0F4A45724CA20D1CC02F76371B963AB7D1E38BD8997737B13D8 | |||
| 2876 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\StructuredQuery.log | text | |
MD5:32418AAD6A59377813B0DCA5B0B79EDB | SHA256:D9E699252C740D93344BCC332D739B13FB6B5261F3430ACB75D5E19ED7638D06 | |||
| 2876 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\favicon[2].ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
38
TCP/UDP connections
208
DNS requests
115
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
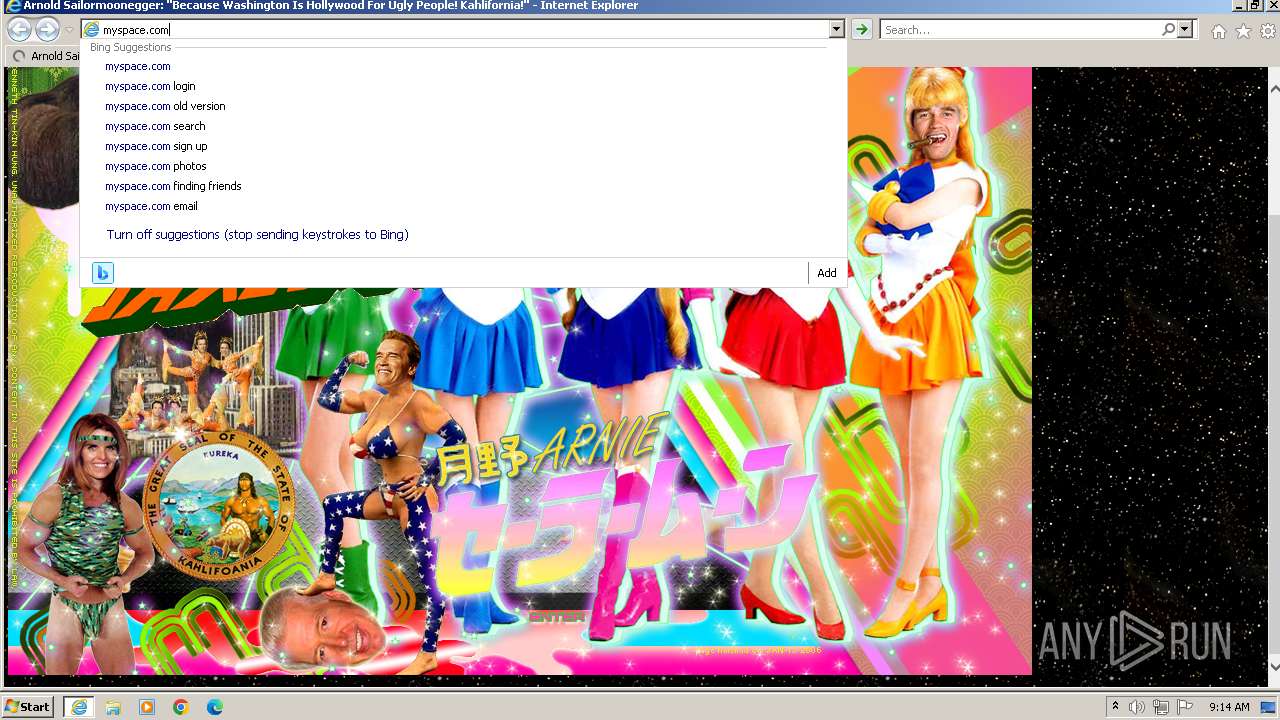
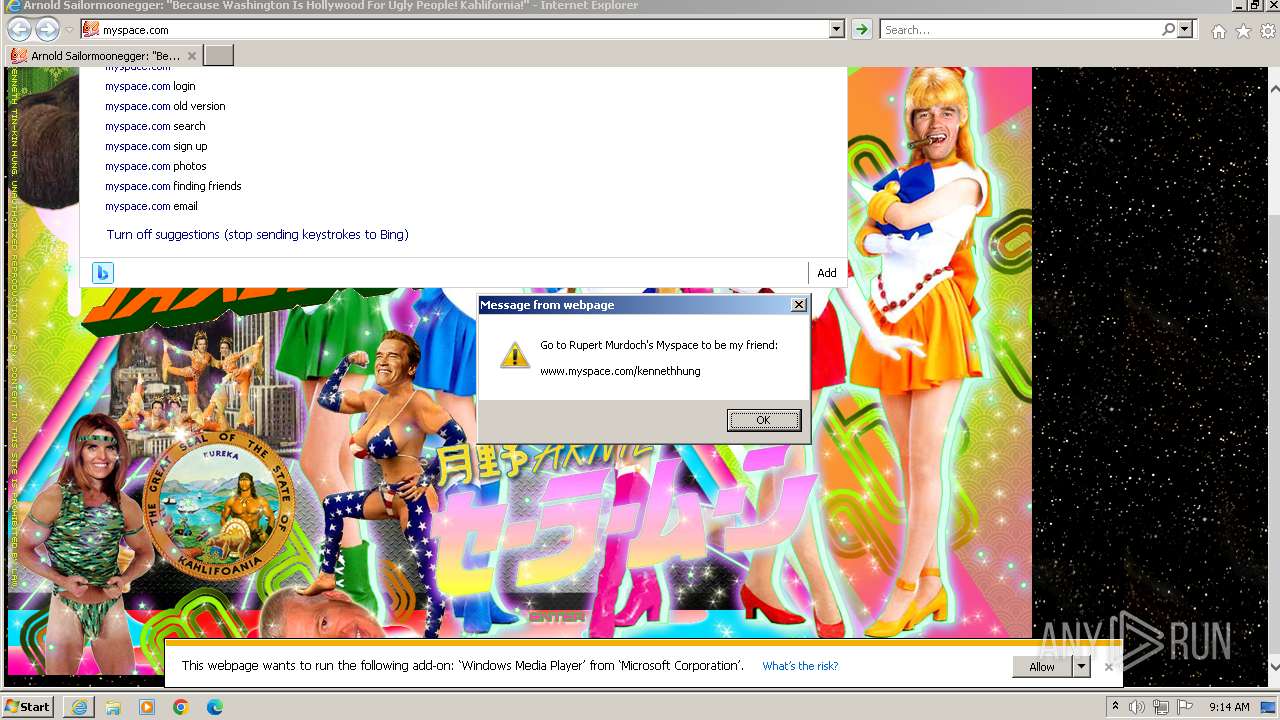
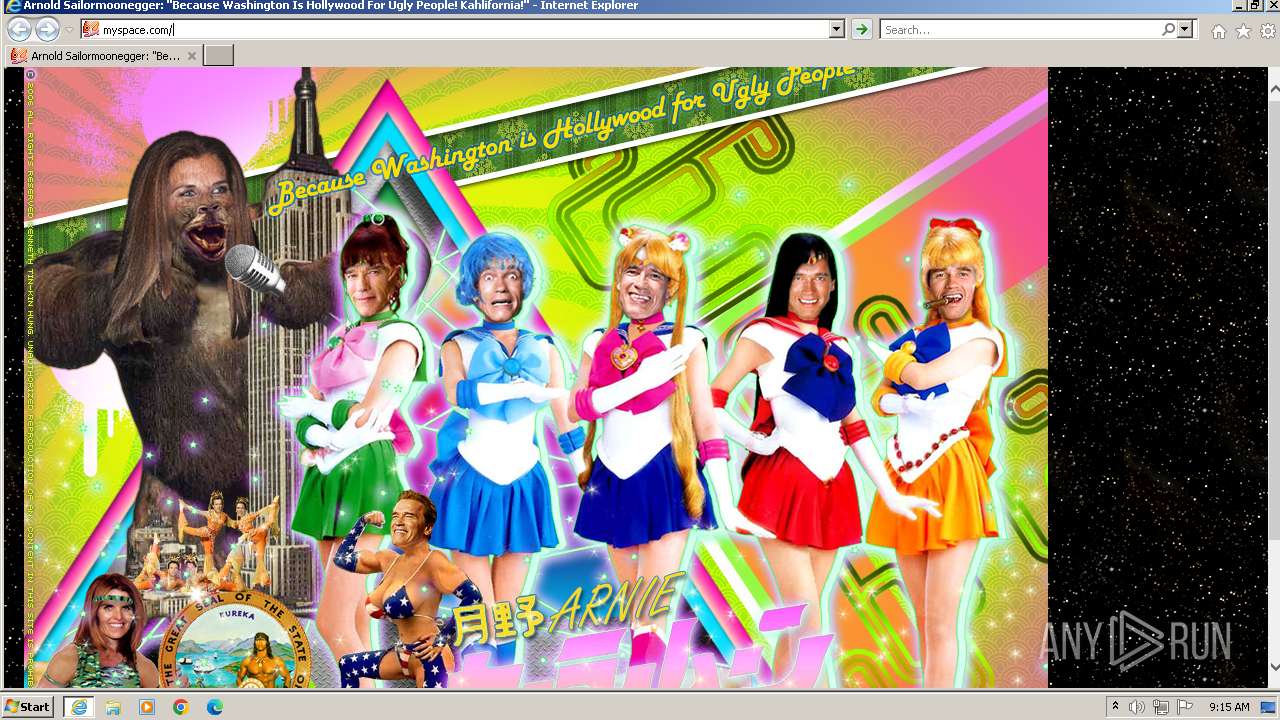
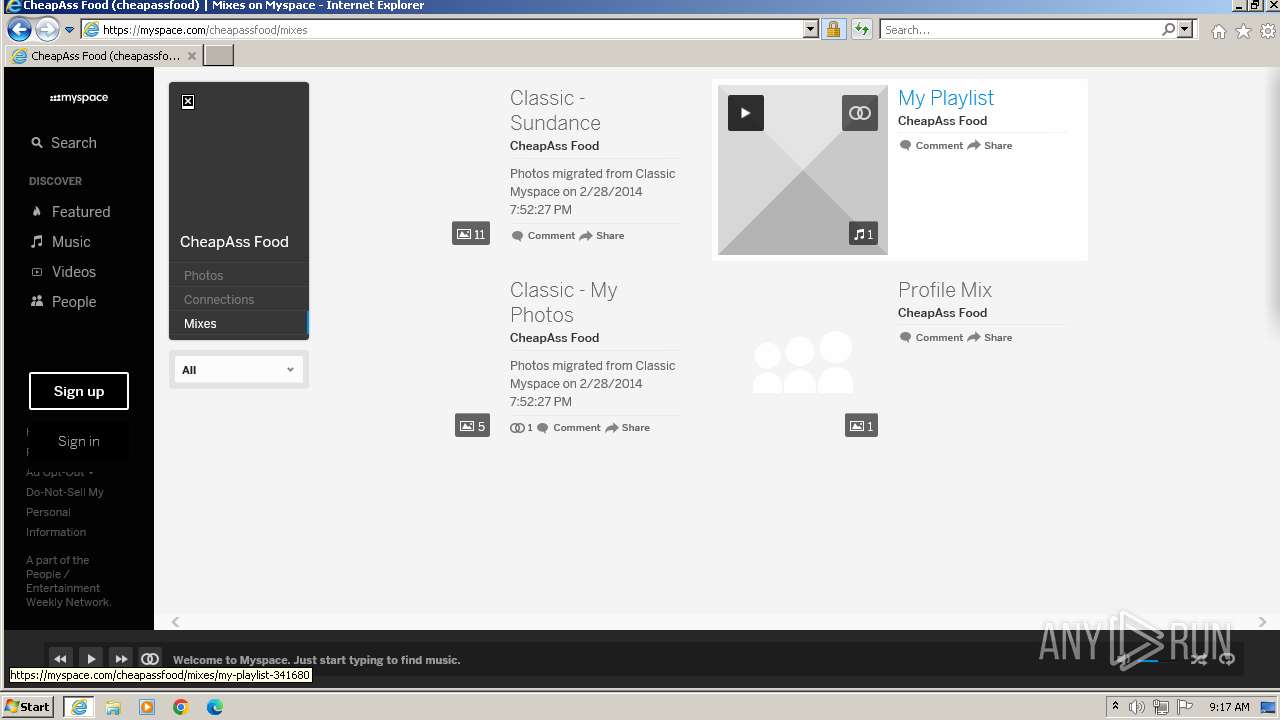
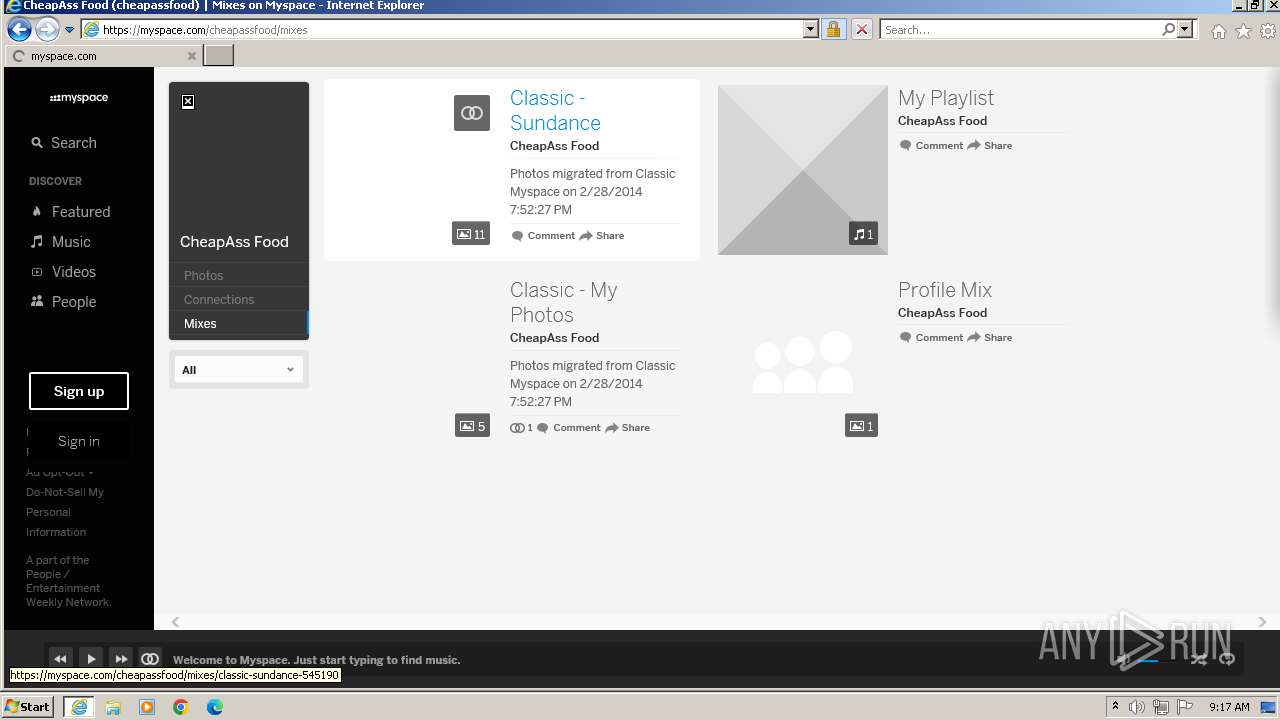
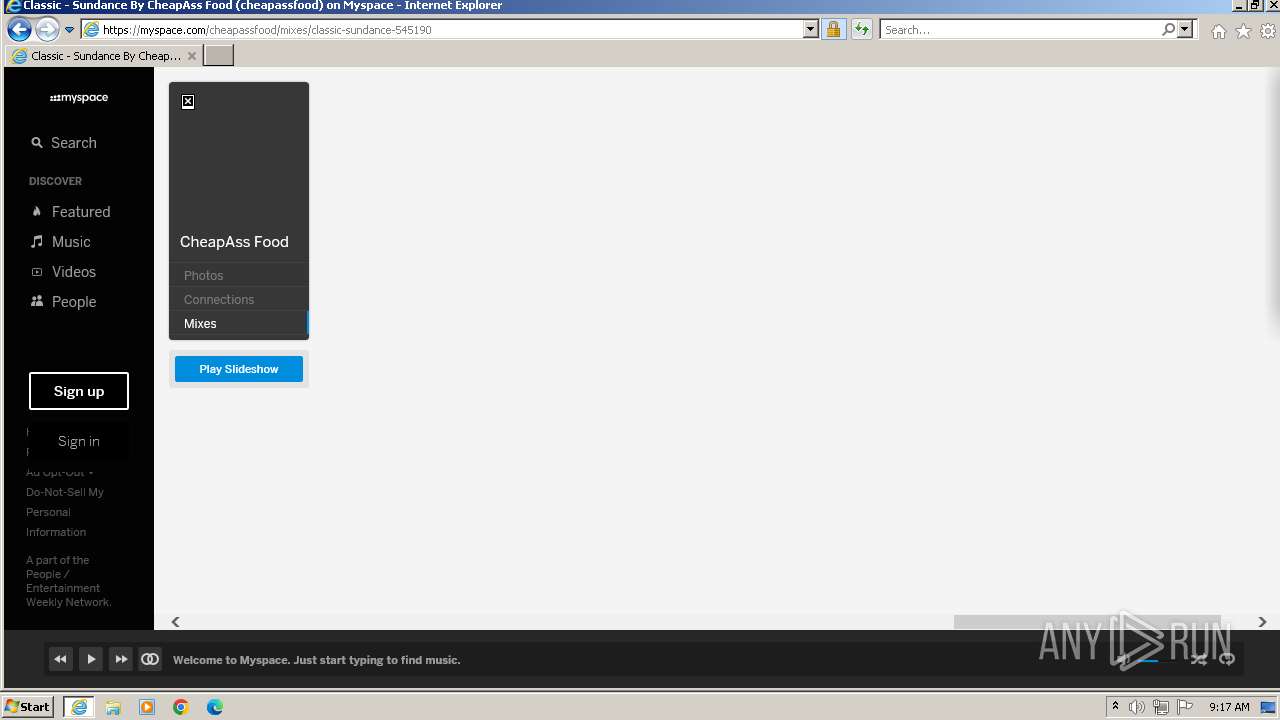
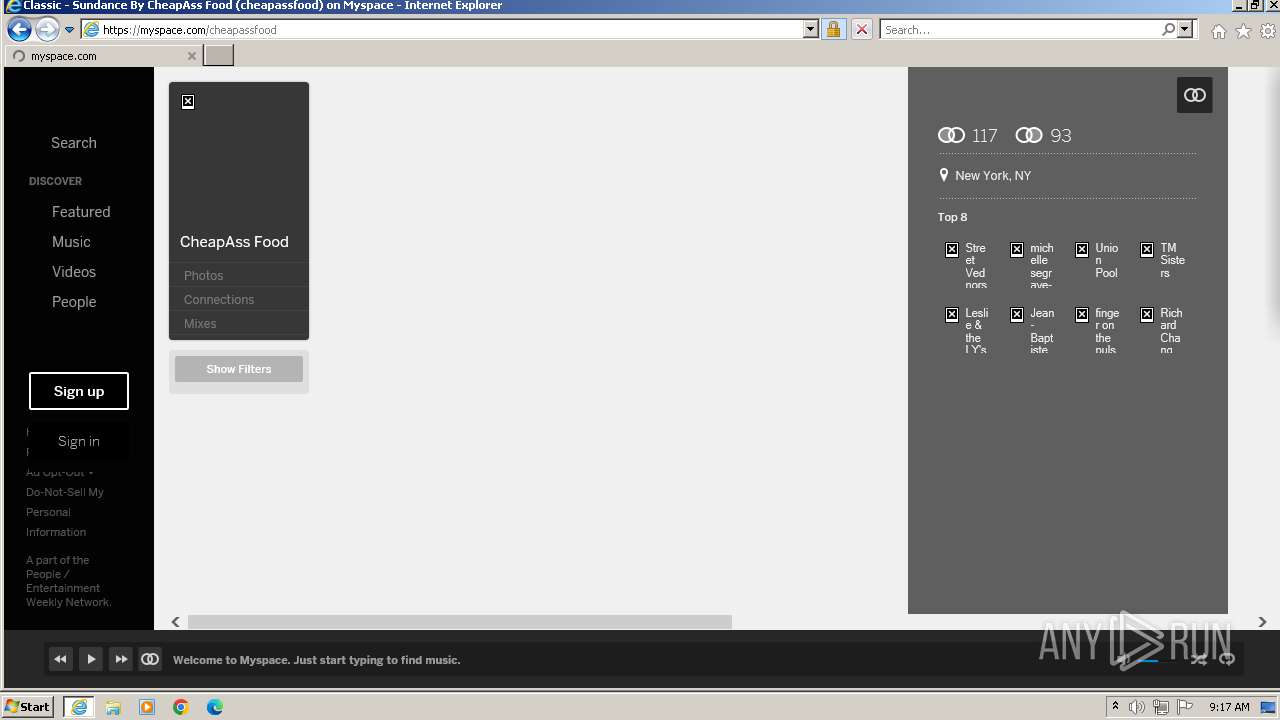
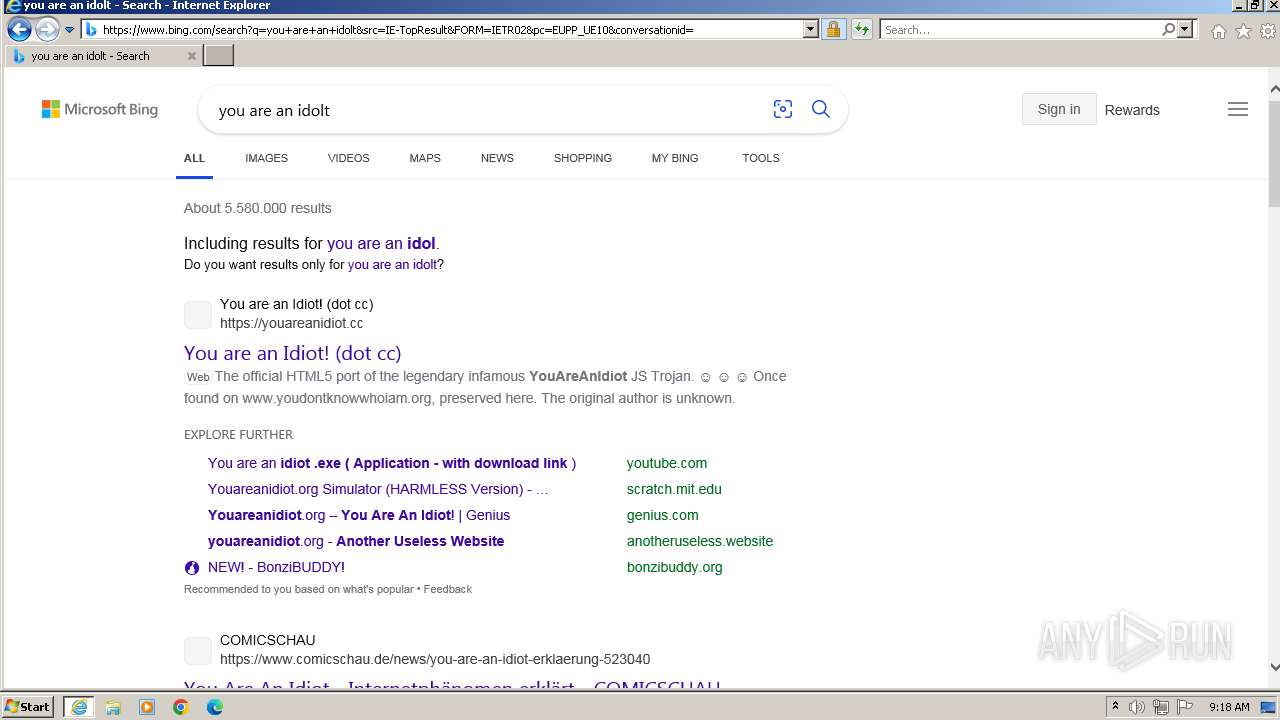
2496 | iexplore.exe | GET | 200 | 72.167.56.241:80 | http://111111111111111111111111111111111111111111111111111111111111.com/ | unknown | html | 1.77 Kb | unknown |
2496 | iexplore.exe | GET | 200 | 72.167.56.241:80 | http://111111111111111111111111111111111111111111111111111111111111.com/arnie/deepspace.gif | unknown | image | 14.5 Kb | unknown |
2496 | iexplore.exe | GET | 200 | 72.167.56.241:80 | http://111111111111111111111111111111111111111111111111111111111111.com/arnie/sailarwordsimages.gif | unknown | image | 52.3 Kb | unknown |
2496 | iexplore.exe | GET | 200 | 72.167.56.241:80 | http://111111111111111111111111111111111111111111111111111111111111.com/arnie/holyplasticbeefy.gif | unknown | image | 34.3 Kb | unknown |
2496 | iexplore.exe | GET | 200 | 72.167.56.241:80 | http://111111111111111111111111111111111111111111111111111111111111.com/arnie/arnie.jpg | unknown | image | 553 Kb | unknown |
2496 | iexplore.exe | GET | 200 | 72.167.56.241:80 | http://111111111111111111111111111111111111111111111111111111111111.com/arnie/arniegun.gif | unknown | image | 104 Kb | unknown |
2876 | iexplore.exe | GET | 200 | 23.55.161.134:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?ded6c50385f5ac11 | unknown | compressed | 4.66 Kb | unknown |
2876 | iexplore.exe | GET | 200 | 23.55.161.134:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?05c7055415a02138 | unknown | compressed | 4.66 Kb | unknown |
2876 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAqvpsXKY8RRQeo74ffHUxc%3D | unknown | binary | 471 b | unknown |
1080 | svchost.exe | GET | 304 | 23.55.161.134:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?68f52e492152febd | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2496 | iexplore.exe | 72.167.56.241:80 | 111111111111111111111111111111111111111111111111111111111111.com | GO-DADDY-COM-LLC | US | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
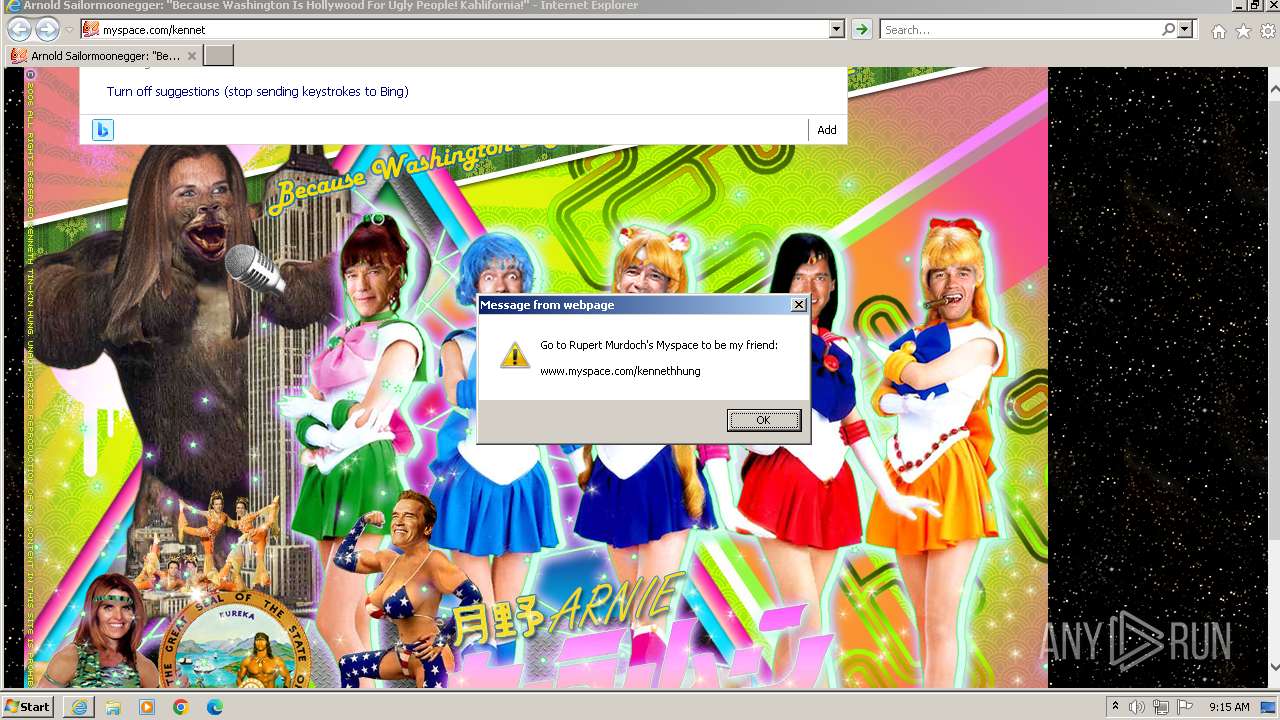
2876 | iexplore.exe | 204.79.197.200:443 | www.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2876 | iexplore.exe | 23.55.161.134:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
2876 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1080 | svchost.exe | 23.55.161.134:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
2496 | iexplore.exe | 13.107.13.80:443 | api.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
111111111111111111111111111111111111111111111111111111111111.com |
| unknown |
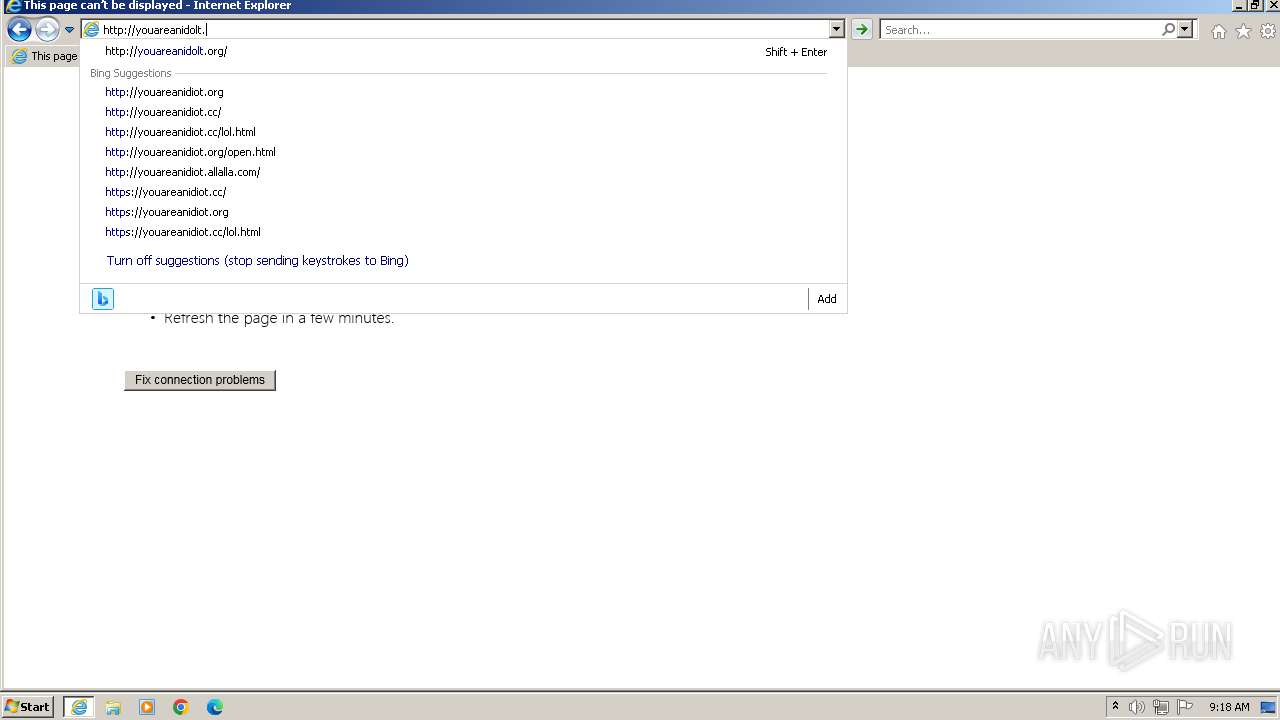
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
iecvlist.microsoft.com |
| unknown |
r20swj13mr.microsoft.com |
| whitelisted |
dns.msftncsi.com |
| shared |
ieonline.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |