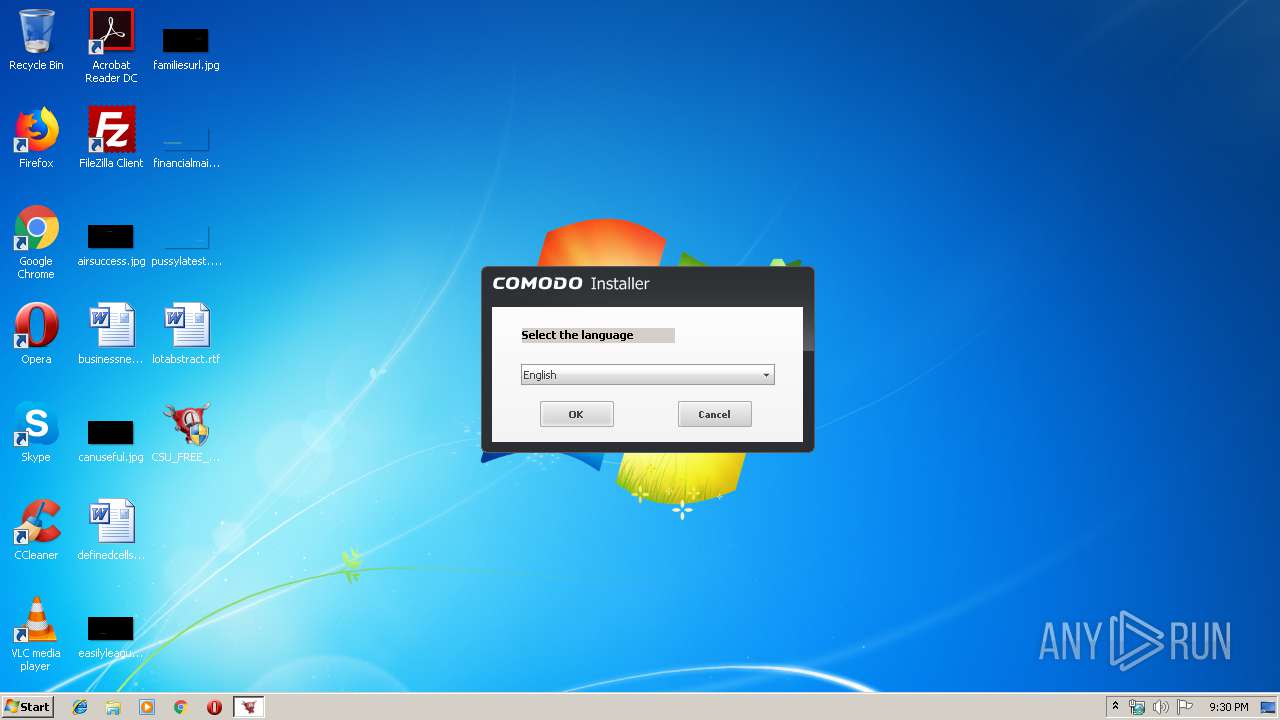
| File name: | CSU_FREE_Setup.exe |
| Full analysis: | https://app.any.run/tasks/2989660d-8968-4c53-8905-cc175d5e7056 |
| Verdict: | Malicious activity |
| Analysis date: | October 14, 2019, 20:29:53 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 6D8A51607F64379A7CFB21F4BBDEBE0B |
| SHA1: | 93E094813810CB908A3CA65FFA89694D5E5C561D |
| SHA256: | BC05751004A2D18C863C9E63A8A22B601B90A83FD95E6898B4DE80FAD65EC66A |
| SSDEEP: | 393216:lEHiCEBENWXf3a15YB4xE4DBNMTc4CfSlZR6Z4j:lVAjPYB4xE4DBNMAB/aj |
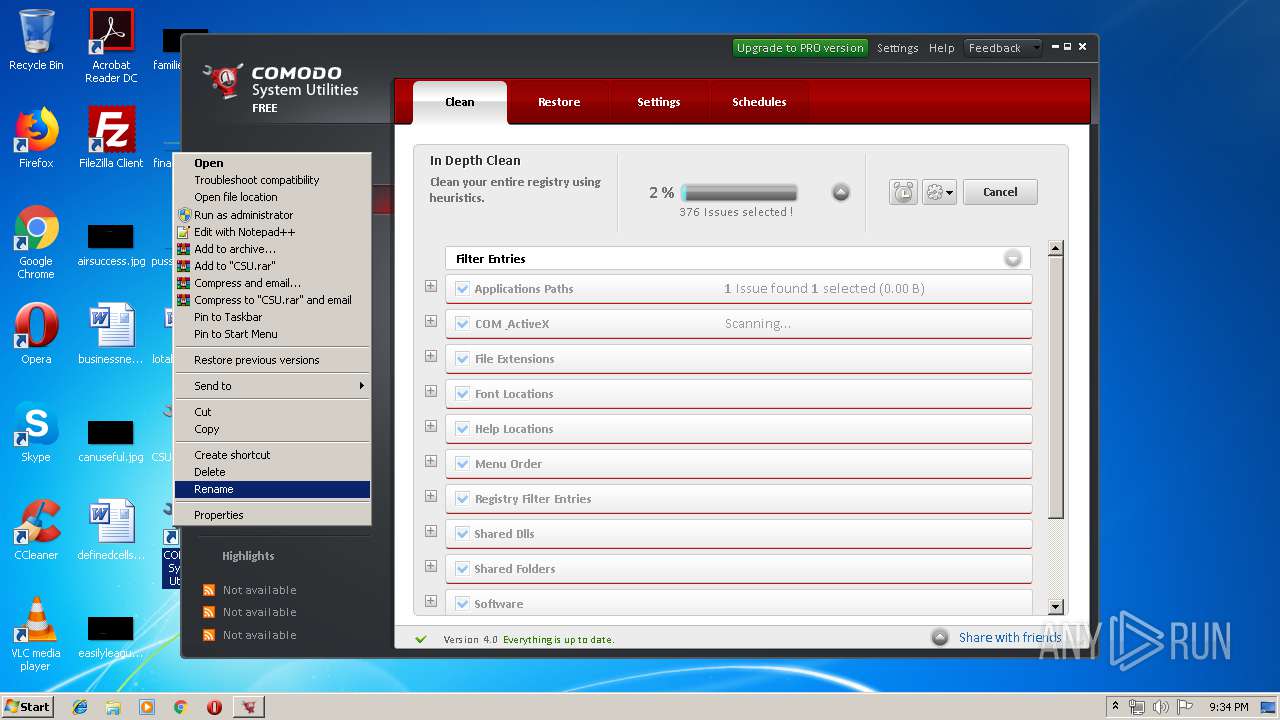
MALICIOUS
Loads dropped or rewritten executable
- CSU_CLI.exe (PID: 532)
- CSU_FREE_Setup.exe (PID: 3256)
- CSURestore.exe (PID: 2660)
- CSUService.exe (PID: 1248)
- CSU.exe (PID: 1412)
- CSU.exe (PID: 2448)
- CSU.exe (PID: 2720)
- CSU.exe (PID: 2600)
- CSU.exe (PID: 3964)
- CSU.exe (PID: 3032)
Loads the Task Scheduler COM API
- CSU_CLI.exe (PID: 532)
- CSU.exe (PID: 2448)
Application was dropped or rewritten from another process
- CSURestore.exe (PID: 2660)
- CSUService.exe (PID: 1248)
- CSU_CLI.exe (PID: 532)
- CSU.exe (PID: 1412)
- CSU.exe (PID: 2448)
- CSU.exe (PID: 2720)
- CSU.exe (PID: 3964)
- CSU.exe (PID: 2600)
- CSU.exe (PID: 3032)
Actions looks like stealing of personal data
- CSU_CLI.exe (PID: 532)
Changes settings of System certificates
- CSU.exe (PID: 3964)
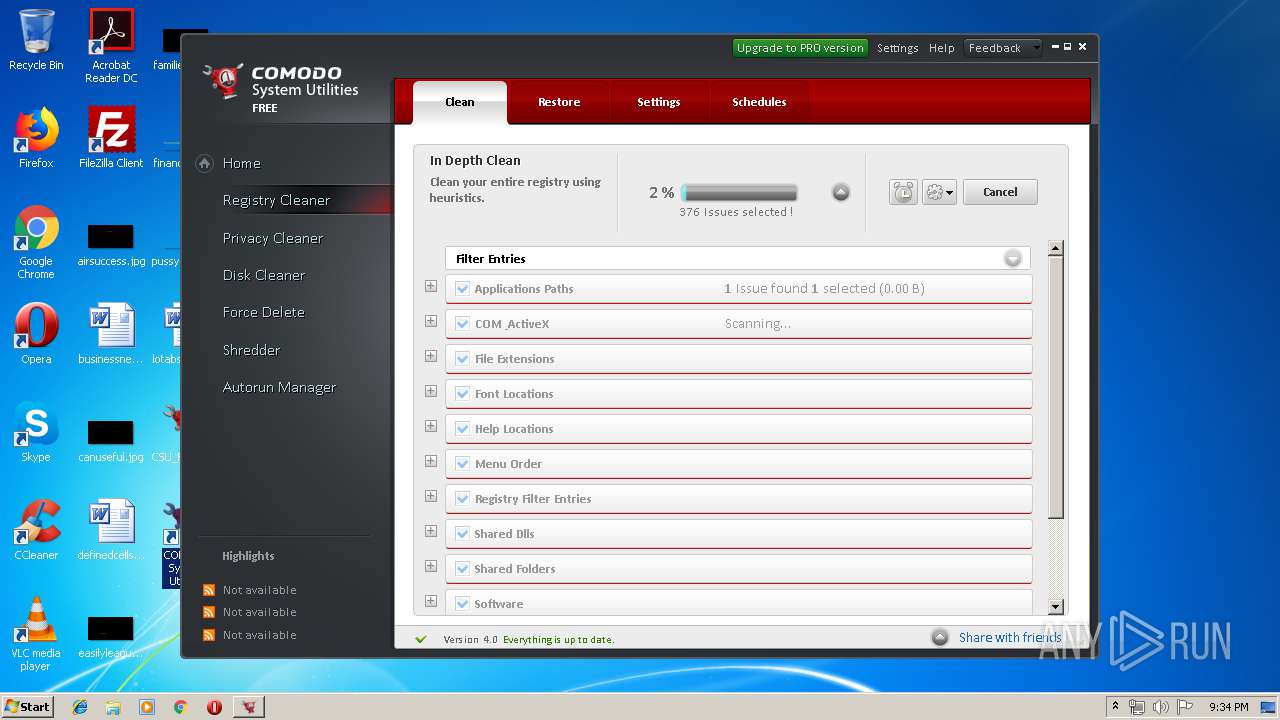
SUSPICIOUS
Executed as Windows Service
- vssvc.exe (PID: 736)
- CSUService.exe (PID: 1248)
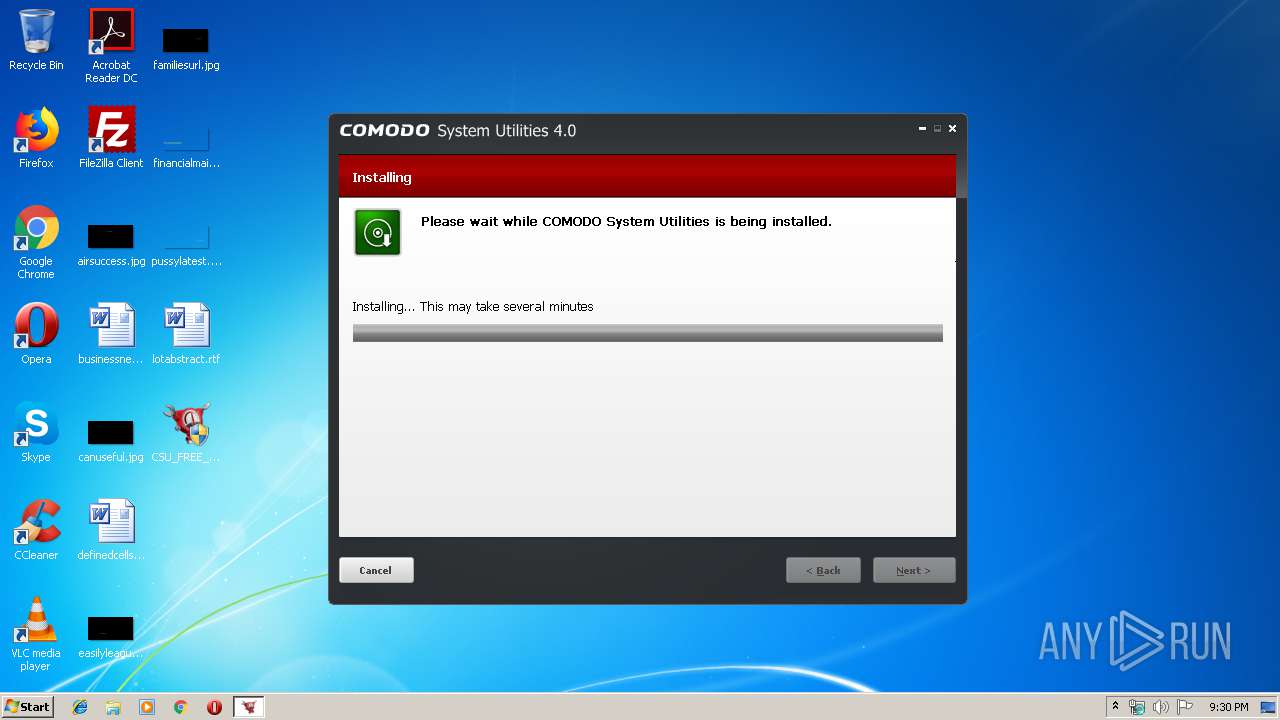
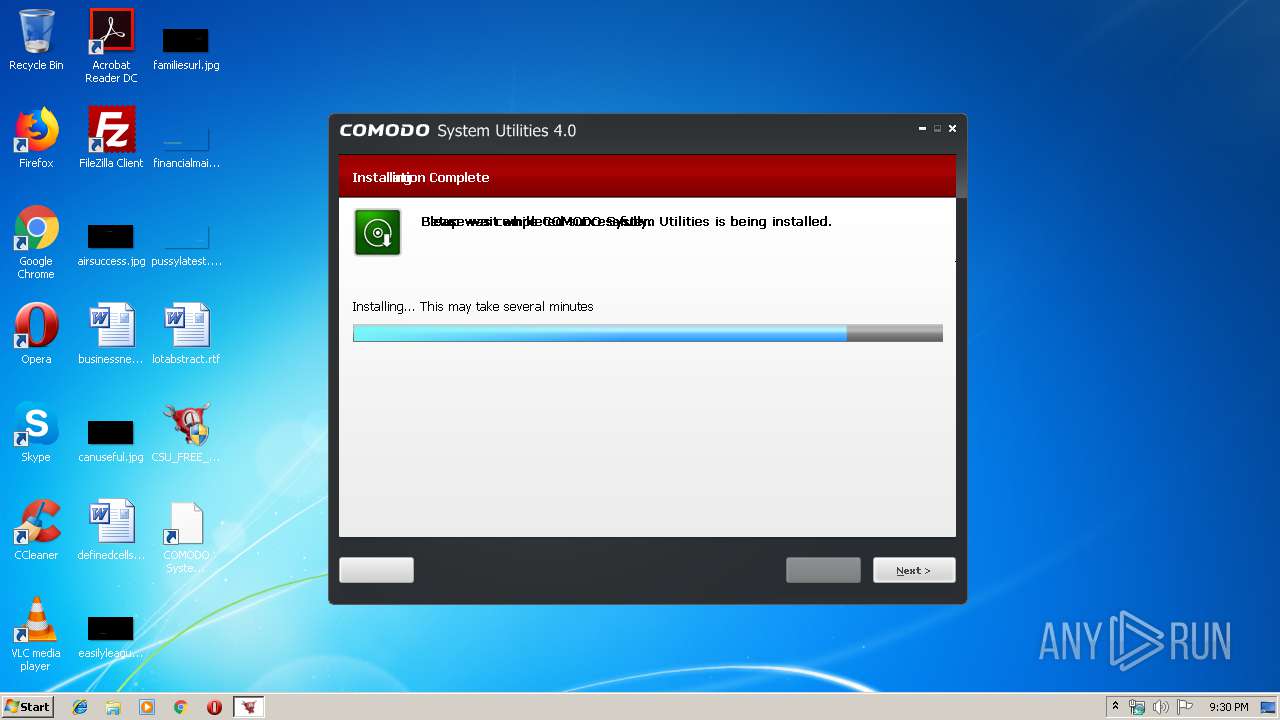
Executable content was dropped or overwritten
- CSU_FREE_Setup.exe (PID: 3256)
Creates files in the Windows directory
- CSU_FREE_Setup.exe (PID: 3256)
- CSU_CLI.exe (PID: 532)
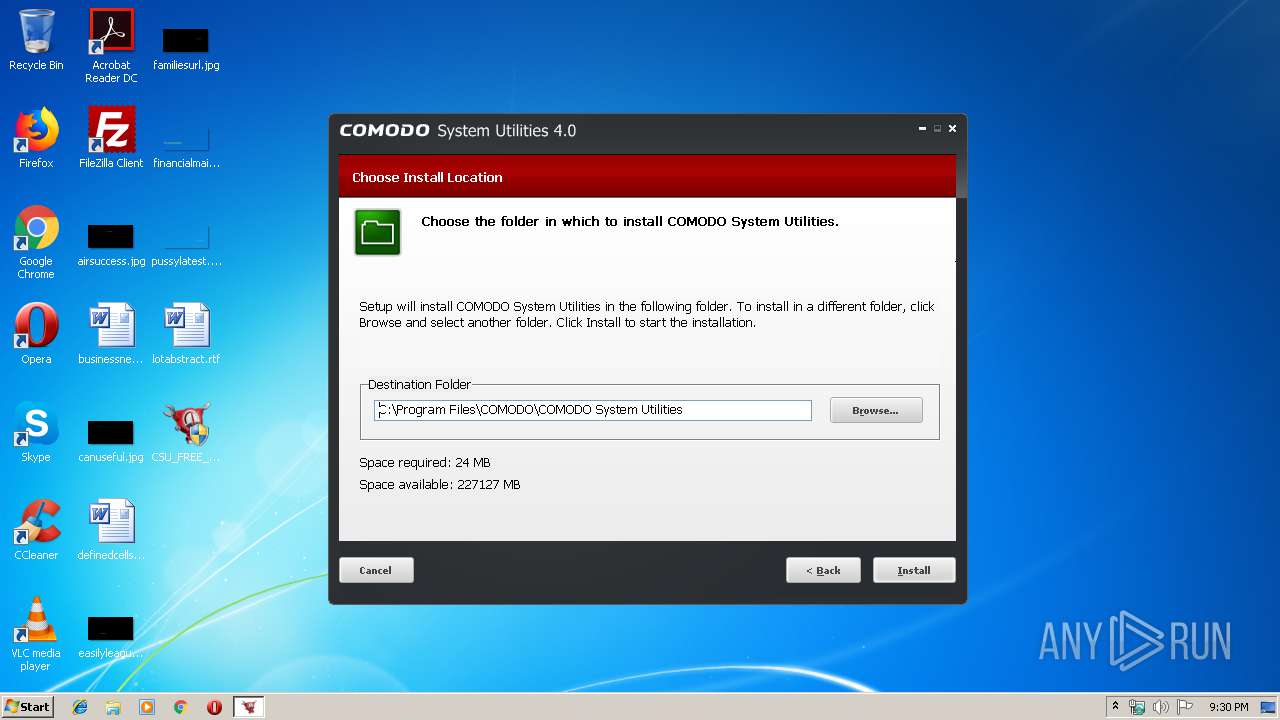
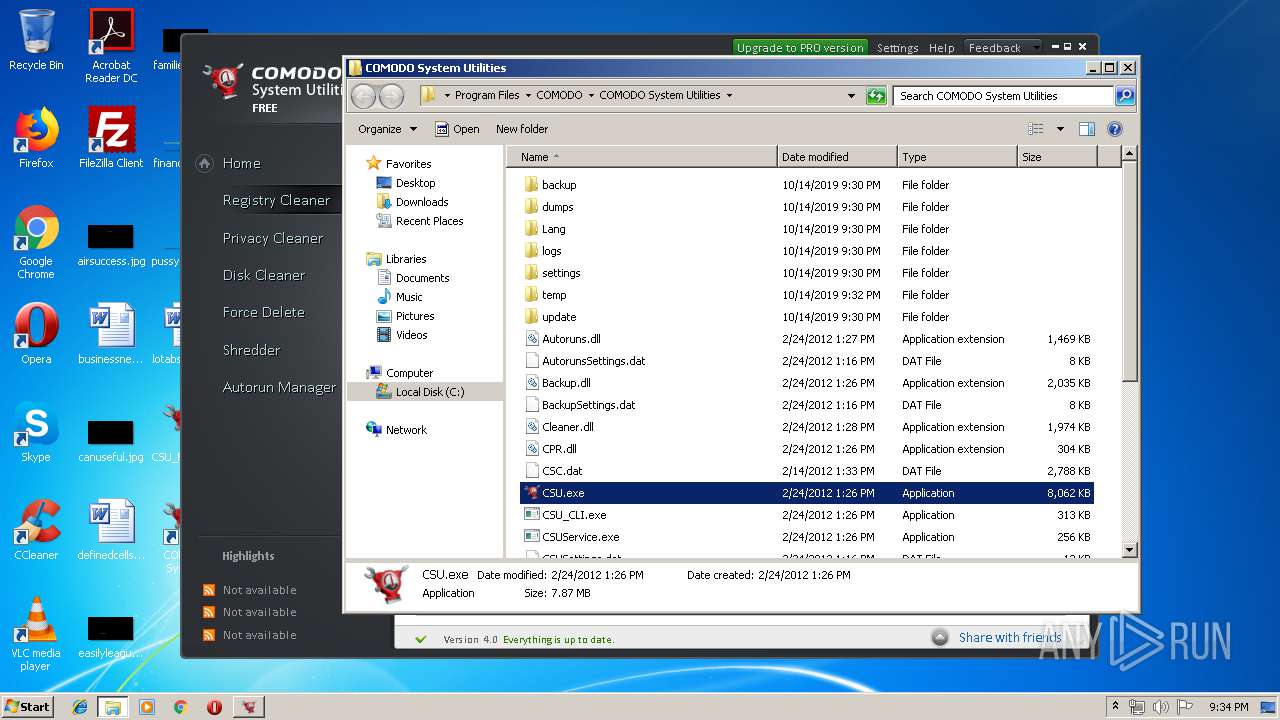
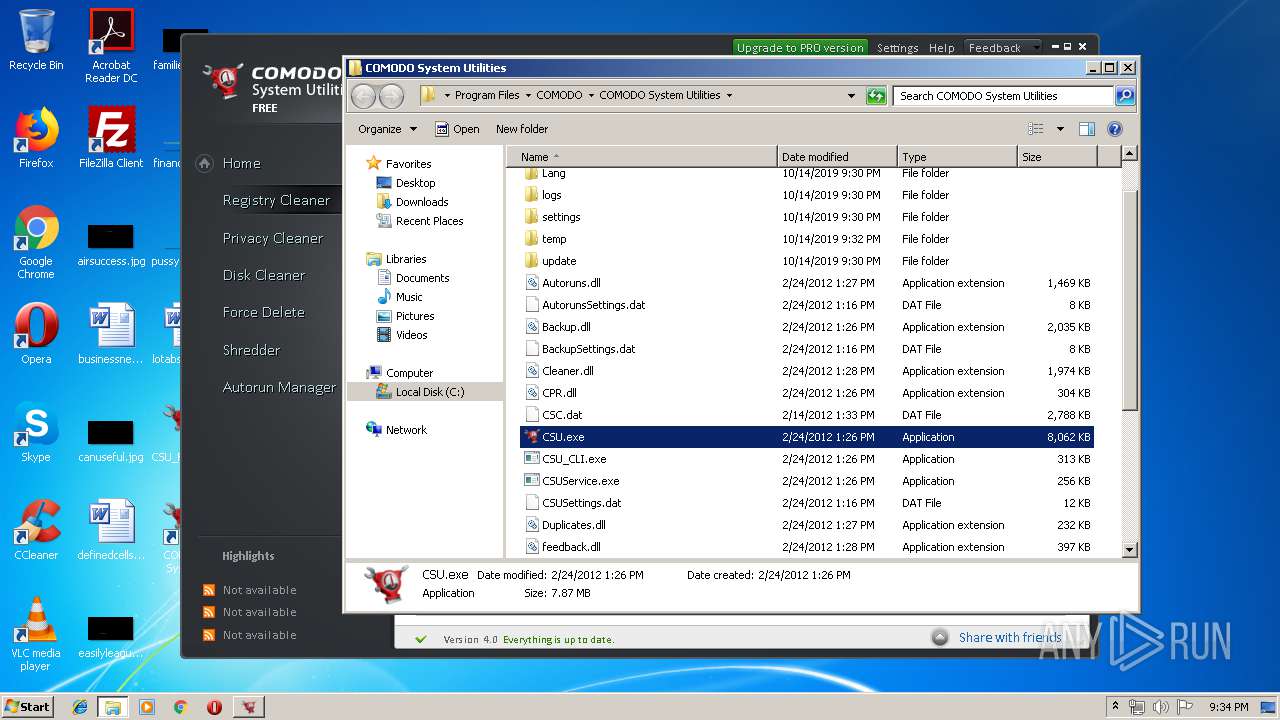
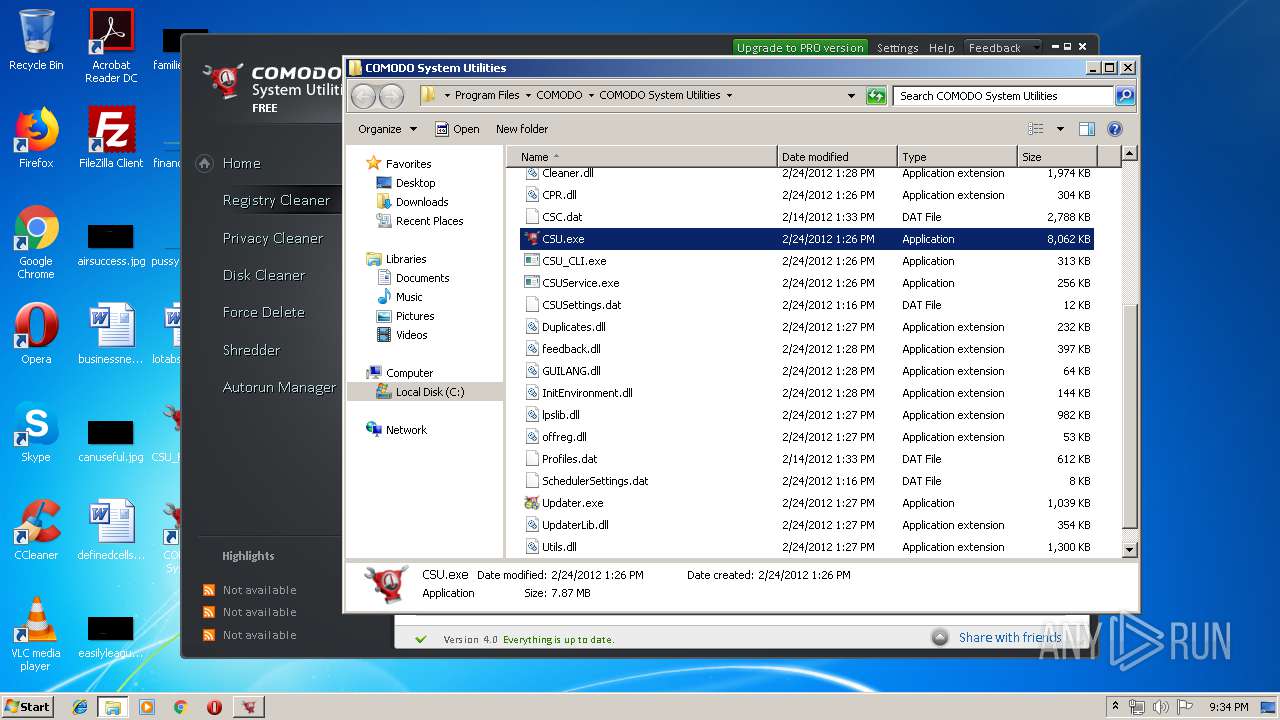
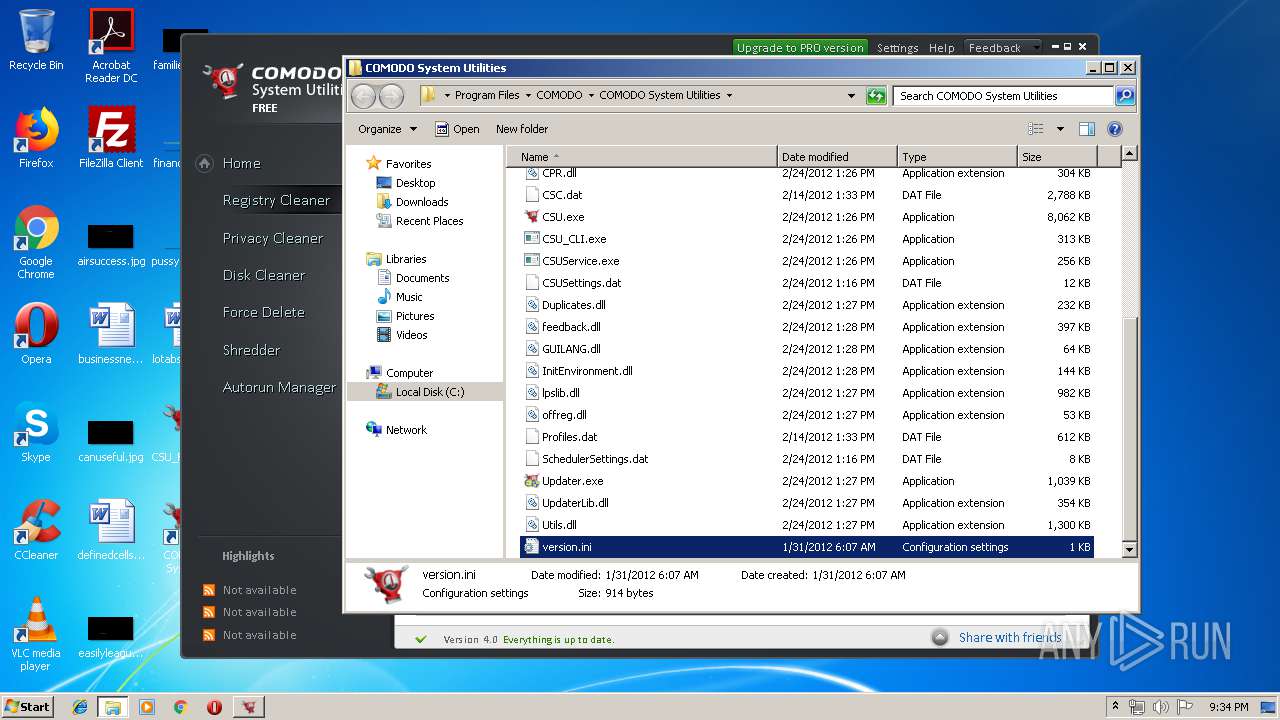
Creates files in the program directory
- CSU_FREE_Setup.exe (PID: 3256)
- CSU_CLI.exe (PID: 532)
Creates a software uninstall entry
- CSU_FREE_Setup.exe (PID: 3256)
Searches for installed software
- CSU_CLI.exe (PID: 532)
Application launched itself
- CSU.exe (PID: 2600)
Reads internet explorer settings
- CSU.exe (PID: 3964)
Creates files in the user directory
- CSU.exe (PID: 3964)
Adds / modifies Windows certificates
- CSU.exe (PID: 3964)
Removes files from Windows directory
- CSU_CLI.exe (PID: 532)
Reads the cookies of Mozilla Firefox
- CSU_CLI.exe (PID: 532)
Reads default file associations for system extensions
- CSU_CLI.exe (PID: 532)
INFO
Low-level read access rights to disk partition
- vssvc.exe (PID: 736)
Manual execution by user
- CSU.exe (PID: 3032)
- NOTEPAD.EXE (PID: 3816)
Dropped object may contain TOR URL's
- CSU.exe (PID: 3964)
Reads settings of System Certificates
- CSU.exe (PID: 3964)
Dropped object may contain Bitcoin addresses
- CSU_CLI.exe (PID: 532)
- CSU_FREE_Setup.exe (PID: 3256)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2010:04:10 14:19:31+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 25600 |
| InitializedDataSize: | 431104 |
| UninitializedDataSize: | 16896 |
| EntryPoint: | 0x354b |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.0.30135.26 |
| ProductVersionNumber: | 4.0.30135.26 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
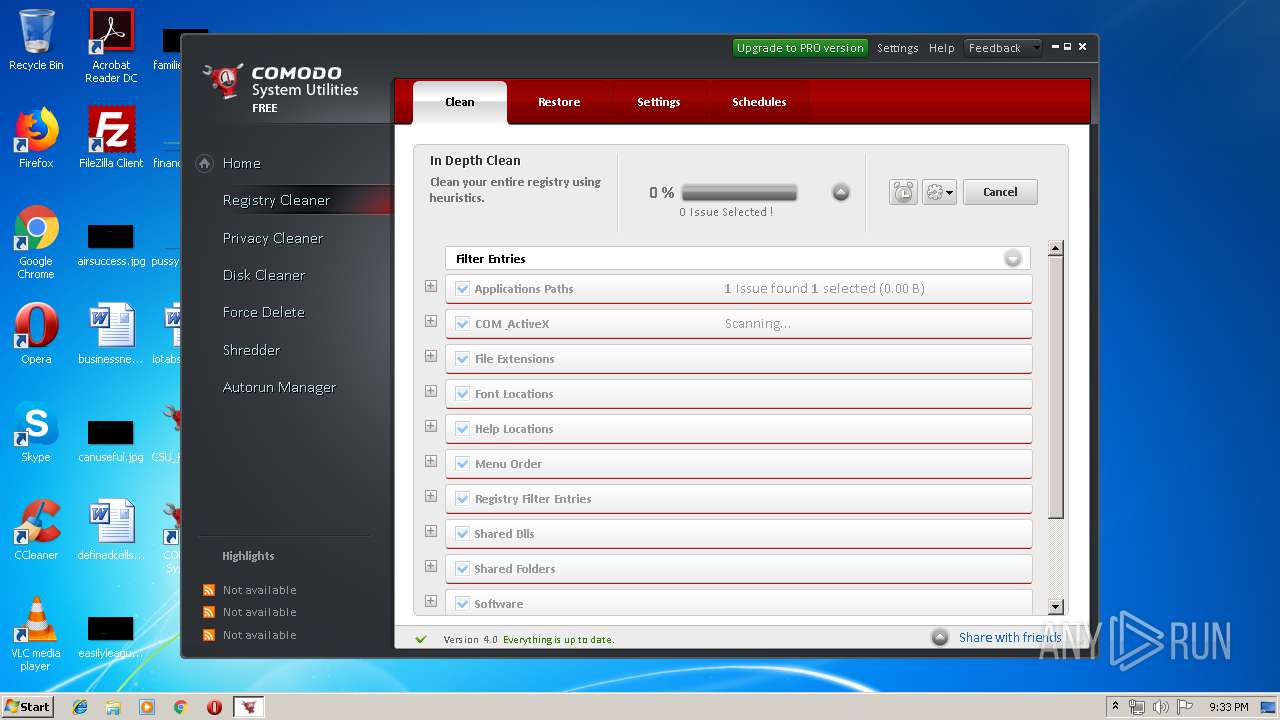
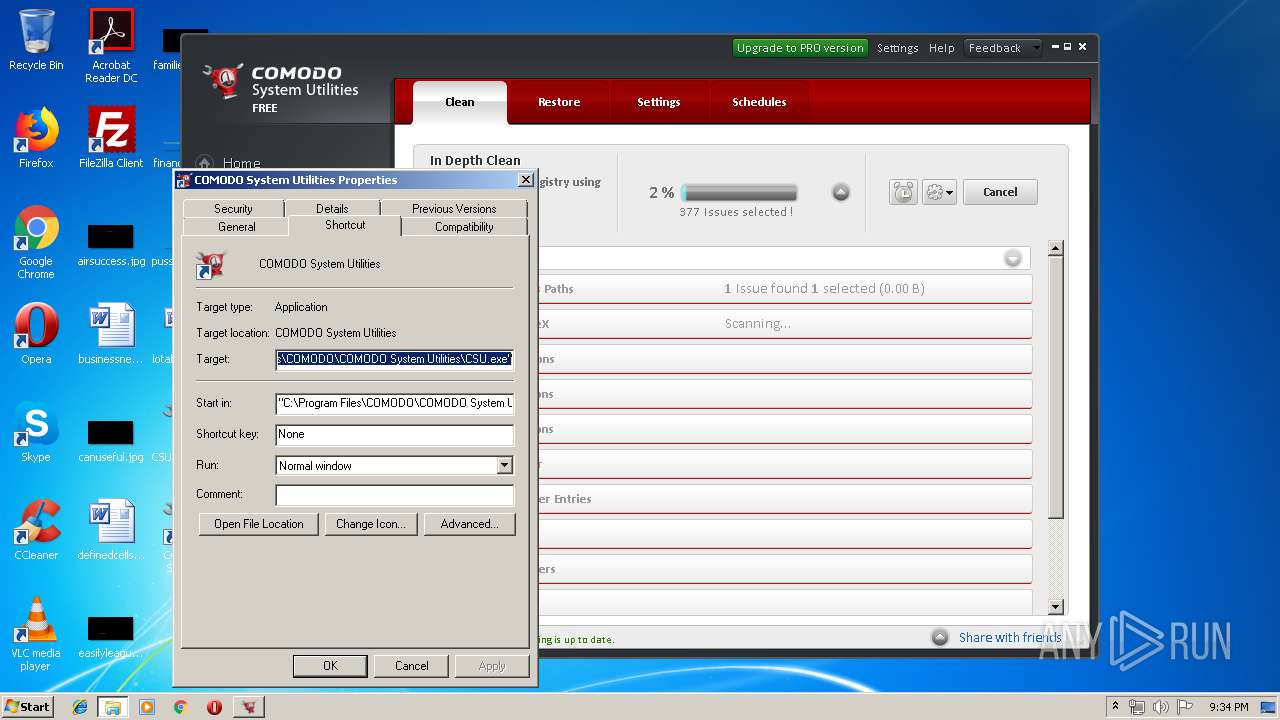
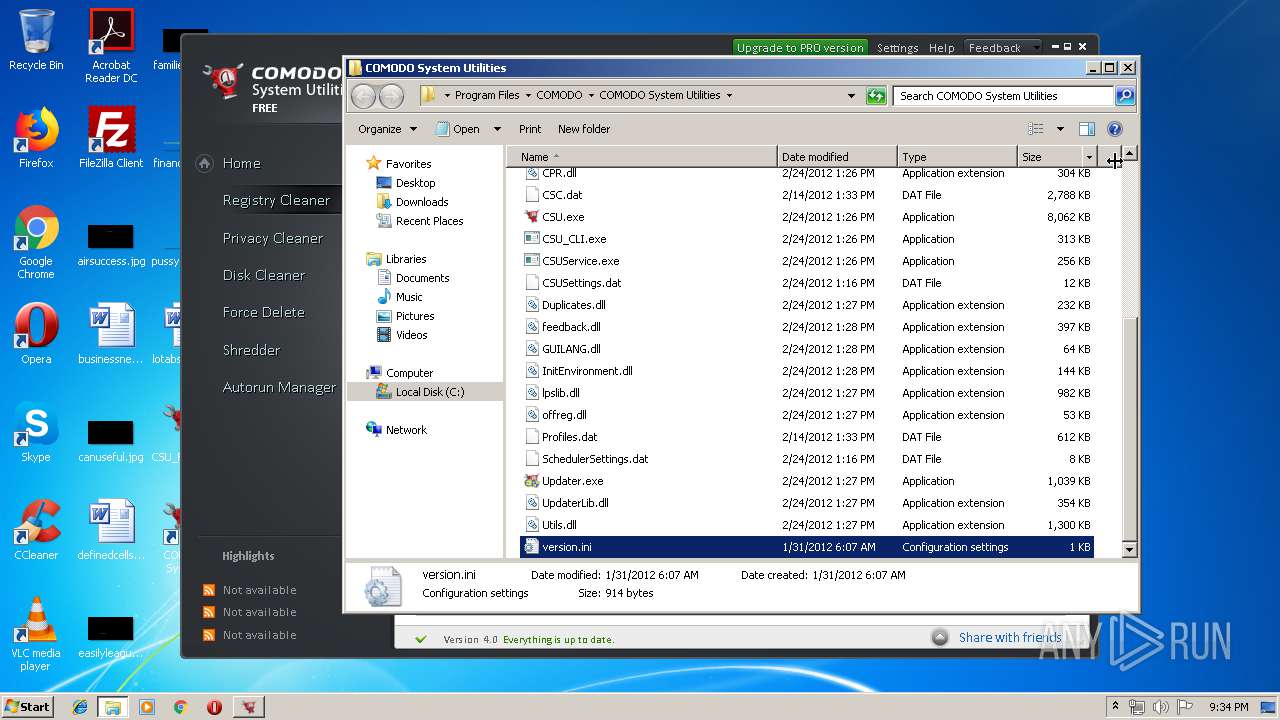
| CompanyName: | COMODO |
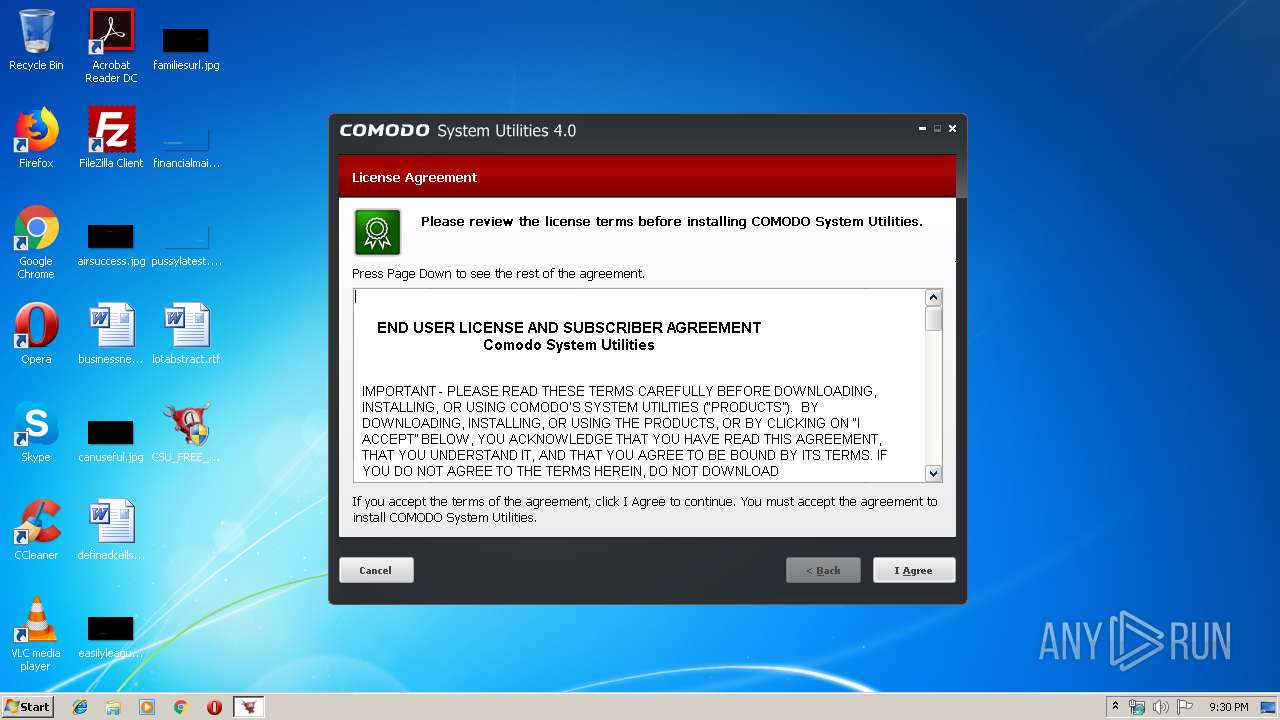
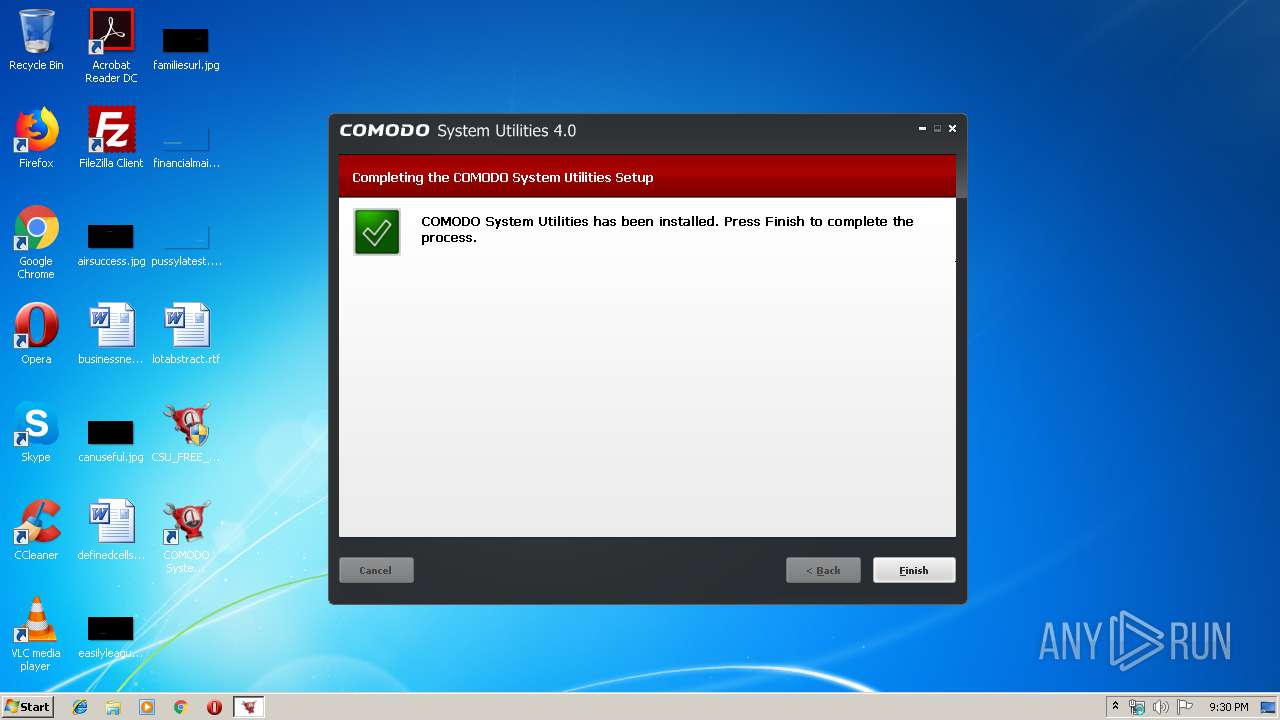
| FileDescription: | COMODO System Utilities setup |
| FileVersion: | 4.0 build 26 |
| LegalCopyright: | Copyright (C) 2008-2010 Comodo Security Solutions, Inc. All rights reserved. |
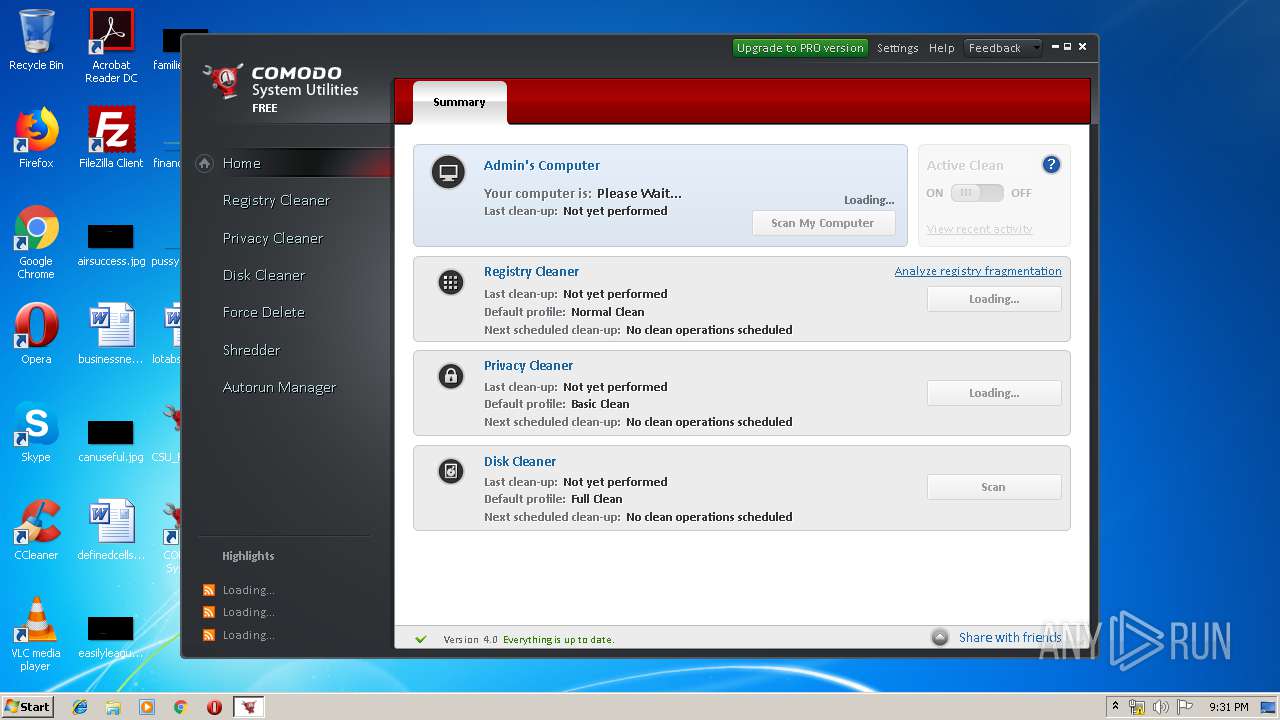
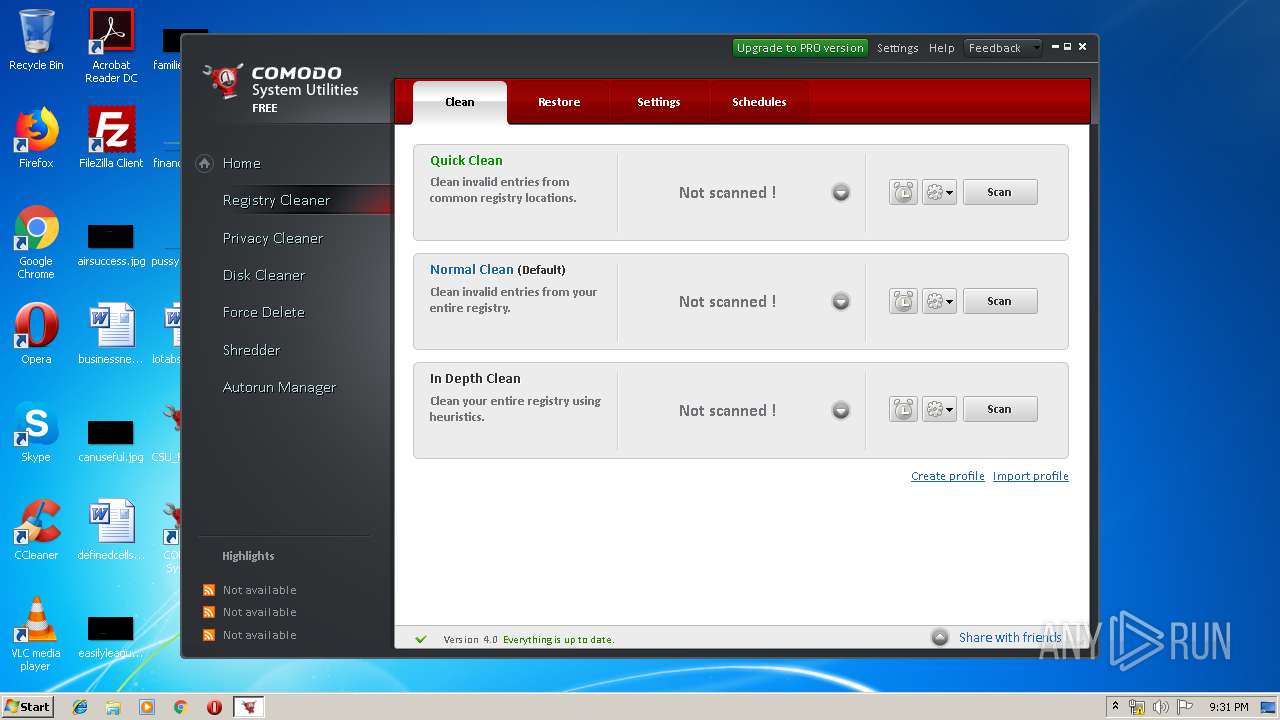
| ProductName: | COMODO System Utilities |
| ProductVersion: | 4.0 build 26 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 10-Apr-2010 12:19:31 |
| Detected languages: |
|
| CompanyName: | COMODO |
| FileDescription: | COMODO System Utilities setup |
| FileVersion: | 4.0 build 26 |
| LegalCopyright: | Copyright (C) 2008-2010 Comodo Security Solutions, Inc. All rights reserved. |
| ProductName: | COMODO System Utilities |
| ProductVersion: | 4.0 build 26 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 10-Apr-2010 12:19:31 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000063A2 | 0x00006400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.48045 |
.rdata | 0x00008000 | 0x000018F2 | 0x00001A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.88829 |
.data | 0x0000A000 | 0x0006669C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.42988 |
.ndata | 0x00071000 | 0x00111000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00182000 | 0x000403C8 | 0x00040400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.04781 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.19535 | 735 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 7.98234 | 53951 | UNKNOWN | English - United States | RT_ICON |
3 | 7.74106 | 42265 | UNKNOWN | English - United States | RT_ICON |
4 | 3.97724 | 19496 | UNKNOWN | English - United States | RT_ICON |
5 | 7.94953 | 15726 | UNKNOWN | English - United States | RT_ICON |
6 | 3.13531 | 10344 | UNKNOWN | English - United States | RT_ICON |
7 | 4.27416 | 9640 | UNKNOWN | English - United States | RT_ICON |
8 | 4.62996 | 4264 | UNKNOWN | English - United States | RT_ICON |
9 | 4.80717 | 3752 | UNKNOWN | English - United States | RT_ICON |
10 | 4.83662 | 2440 | UNKNOWN | English - United States | RT_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
61
Monitored processes
13
Malicious processes
9
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 532 | CSU_CLI.exe /service "admin" | C:\Program Files\COMODO\COMODO System Utilities\CSU_CLI.exe | CSUService.exe | ||||||||||||
User: SYSTEM Company: Comodo Security Solutions, Inc. Integrity Level: SYSTEM Description: Comodo System Utilities Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 736 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1248 | "C:\Program Files\COMODO\COMODO System Utilities\CSUService.exe" | C:\Program Files\COMODO\COMODO System Utilities\CSUService.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Comodo Security Solutions, Inc. Integrity Level: SYSTEM Description: Comodo System Utilities Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 1412 | "C:\Program Files\COMODO\COMODO System Utilities\CSU.exe" /a 0 "" | C:\Program Files\COMODO\COMODO System Utilities\CSU.exe | — | CSU_FREE_Setup.exe | |||||||||||
User: admin Company: Comodo Security Solutions, Inc. Integrity Level: HIGH Description: Comodo System Utilities Exit code: 0 Version: 4.0.226743.26 Modules
| |||||||||||||||
| 2448 | "C:\Program Files\COMODO\COMODO System Utilities\CSU.exe" runasadmin /a 0 "" | C:\Program Files\COMODO\COMODO System Utilities\CSU.exe | CSU.exe | ||||||||||||
User: admin Company: Comodo Security Solutions, Inc. Integrity Level: HIGH Description: Comodo System Utilities Exit code: 0 Version: 4.0.226743.26 Modules
| |||||||||||||||
| 2600 | elevation | C:\Program Files\COMODO\COMODO System Utilities\CSU.exe | — | CSU.exe | |||||||||||
User: admin Company: Comodo Security Solutions, Inc. Integrity Level: MEDIUM Description: Comodo System Utilities Exit code: 0 Version: 4.0.226743.26 Modules
| |||||||||||||||
| 2660 | "C:\Users\admin\AppData\Local\Temp\nstC37B.tmp\CSURestore.exe" /create_restore | C:\Users\admin\AppData\Local\Temp\nstC37B.tmp\CSURestore.exe | — | CSU_FREE_Setup.exe | |||||||||||
User: admin Company: TODO: <Company name> Integrity Level: HIGH Description: TODO: <File description> Exit code: 0 Version: 1.0.0.1 Modules
| |||||||||||||||
| 2720 | elevation /a 0 "" | C:\Program Files\COMODO\COMODO System Utilities\CSU.exe | — | CSU.exe | |||||||||||
User: admin Company: Comodo Security Solutions, Inc. Integrity Level: HIGH Description: Comodo System Utilities Exit code: 0 Version: 4.0.226743.26 Modules
| |||||||||||||||
| 3032 | "C:\Program Files\COMODO\COMODO System Utilities\CSU.exe" | C:\Program Files\COMODO\COMODO System Utilities\CSU.exe | — | explorer.exe | |||||||||||
User: admin Company: Comodo Security Solutions, Inc. Integrity Level: MEDIUM Description: Comodo System Utilities Exit code: 0 Version: 4.0.226743.26 Modules
| |||||||||||||||
| 3256 | "C:\Users\admin\Desktop\CSU_FREE_Setup.exe" | C:\Users\admin\Desktop\CSU_FREE_Setup.exe | explorer.exe | ||||||||||||
User: admin Company: COMODO Integrity Level: HIGH Description: COMODO System Utilities setup Exit code: 80 Version: 4.0 build 26 Modules
| |||||||||||||||
Total events
43 472
Read events
43 223
Write events
227
Delete events
22
Modification events
| (PID) Process: | (2660) CSURestore.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 400000000000000056D80139CE82D501640A00003C0A0000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2660) CSURestore.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 400000000000000056D80139CE82D501640A00003C0A0000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2660) CSURestore.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 33 | |||
| (PID) Process: | (2660) CSURestore.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4000000000000000B2715C39CE82D501640A00003C0A0000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2660) CSURestore.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000000CD45E39CE82D501640A0000400D0000E8030000010000000000000000000000112496238C162949B8D0BB0F6F96C0AA0000000000000000 | |||
| (PID) Process: | (736) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 400000000000000090AB7639CE82D501E002000044010000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (736) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 400000000000000090AB7639CE82D501E0020000900F0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (736) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 400000000000000090AB7639CE82D501E0020000740F0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (736) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000EA0D7939CE82D501E00200007C030000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (736) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Leave) |
Value: 4000000000000000F8348039CE82D501E002000044010000E8030000000000000100000000000000000000000000000000000000000000000000000000000000 | |||
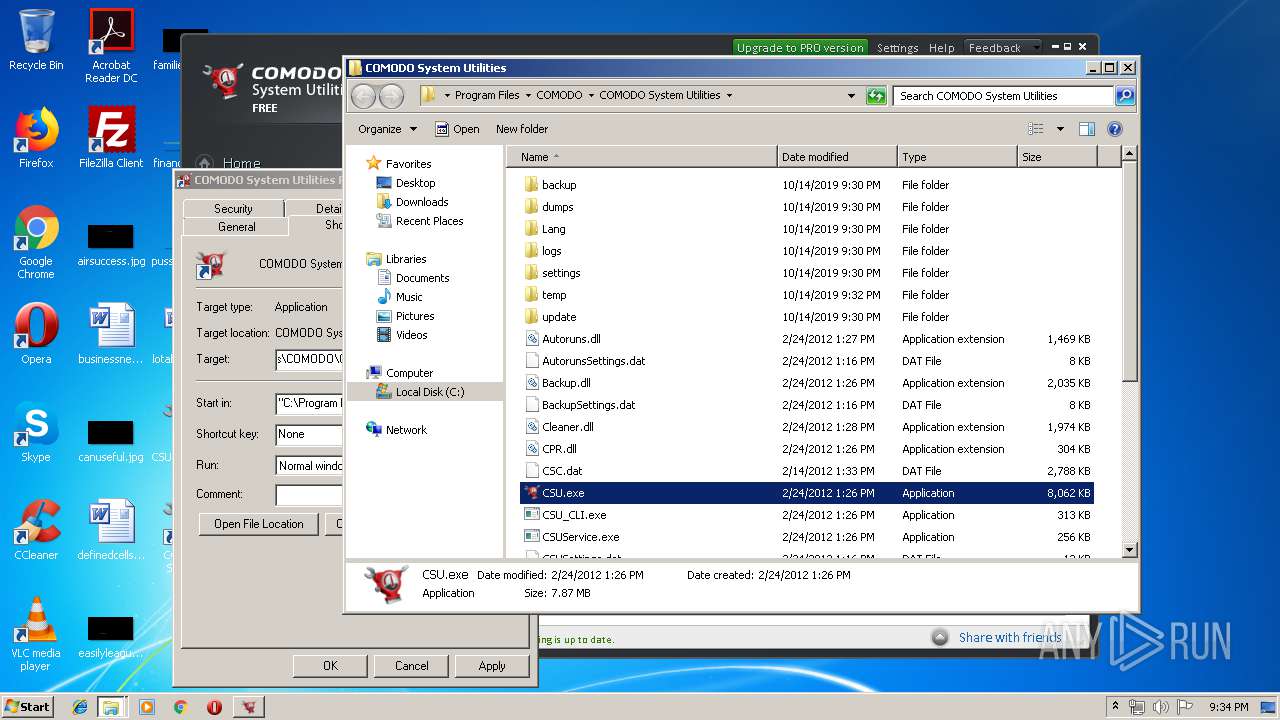
Executable files
47
Suspicious files
5
Text files
57
Unknown types
19
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3256 | CSU_FREE_Setup.exe | C:\Users\admin\AppData\Local\Temp\nstC37B.tmp\Utils.dll | executable | |
MD5:— | SHA256:— | |||
| 3256 | CSU_FREE_Setup.exe | C:\Users\admin\AppData\Local\Temp\nstC37B.tmp\CSURestore.exe | executable | |
MD5:— | SHA256:— | |||
| 3256 | CSU_FREE_Setup.exe | C:\Users\admin\AppData\Local\Temp\nstC37B.tmp\offreg.dll | executable | |
MD5:— | SHA256:— | |||
| 3256 | CSU_FREE_Setup.exe | C:\Users\admin\AppData\Local\Temp\CSU\Skin.skf | dbf | |
MD5:— | SHA256:— | |||
| 3256 | CSU_FREE_Setup.exe | C:\Users\admin\AppData\Local\Temp\CSU\content.bmp | image | |
MD5:— | SHA256:— | |||
| 3256 | CSU_FREE_Setup.exe | C:\Users\admin\AppData\Local\Temp\nstC37B.tmp\ioSpecial.ini | text | |
MD5:— | SHA256:— | |||
| 3256 | CSU_FREE_Setup.exe | C:\Users\admin\AppData\Local\Temp\nstC37B.tmp\feedback.dll | executable | |
MD5:— | SHA256:— | |||
| 3256 | CSU_FREE_Setup.exe | C:\Users\admin\AppData\Local\Temp\nstC37B.tmp\System.dll | executable | |
MD5:959EA64598B9A3E494C00E8FA793BE7E | SHA256:03CD57AB00236C753E7DDEEE8EE1C10839ACE7C426769982365531042E1F6F8B | |||
| 2660 | CSURestore.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 3256 | CSU_FREE_Setup.exe | C:\Users\admin\AppData\Local\Temp\nstC37B.tmp\UserInfo.dll | executable | |
MD5:D16E06C5DE8FB8213A0464568ED9852F | SHA256:728472BA312AE8AF7F30D758AB473E0772477A68FCD1D2D547DAFE6D8800D531 | |||
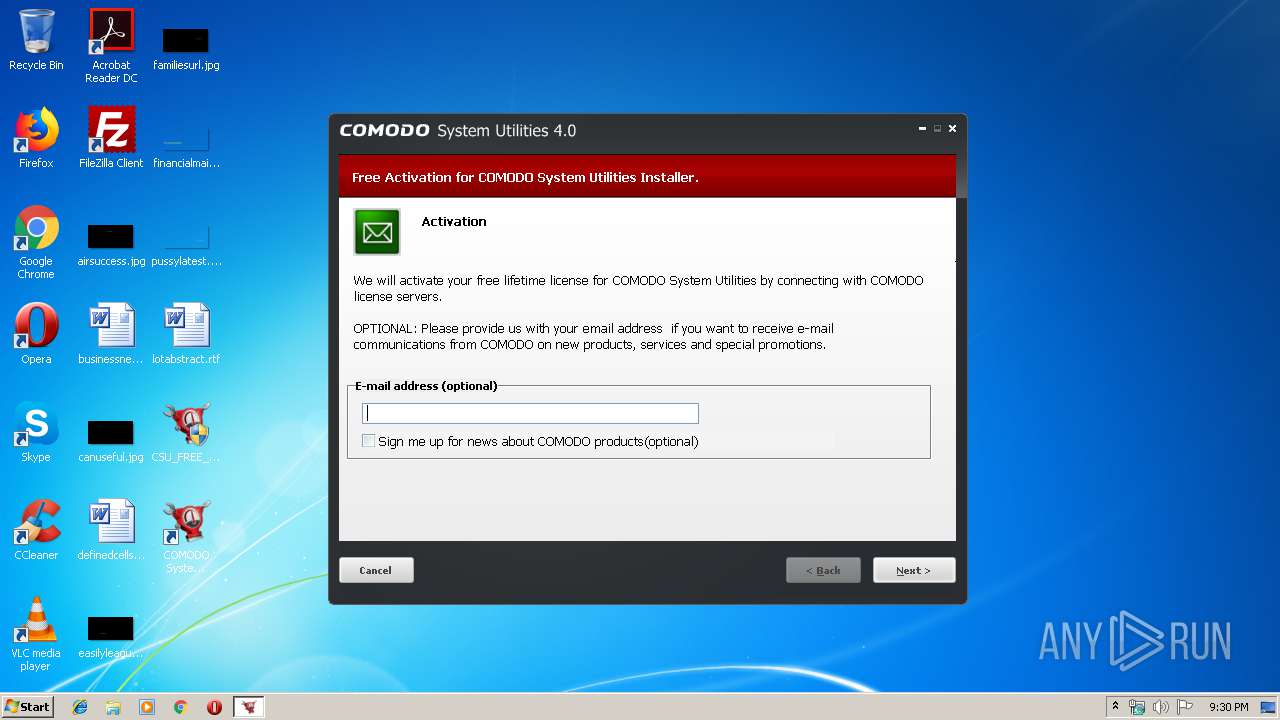
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
20
TCP/UDP connections
26
DNS requests
10
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3964 | CSU.exe | GET | 304 | 178.255.82.1:80 | http://downloads.comodo.com/cpa/v2/HtmlFiles/facebook2.html | GB | — | — | unknown |
3964 | CSU.exe | GET | 302 | 31.13.92.36:80 | http://www.facebook.com/plugins/like.php?href=http%3A%2F%2Fwww.facebook.com%2Fpages%2FComodo-Round-the-Clock%2F133629923323698&layout=standard&show_faces=false&width=450&action=like&colorscheme=light&height=20 | IE | — | — | whitelisted |
3964 | CSU.exe | GET | — | 31.13.92.36:80 | http://www.facebook.com/plugins/like.php?href=http%3A%2F%2Fwww.facebook.com%2Fpages%2FComodo-Round-the-Clock%2F133629923323698&layout=standard&show_faces=false&width=450&action=like&colorscheme=light&height=20 | IE | — | — | whitelisted |
3964 | CSU.exe | GET | 302 | 31.13.92.36:80 | http://www.facebook.com/plugins/like.php?href=http%3A%2F%2Fwww.facebook.com%2Fpages%2FComodo-Round-the-Clock%2F133629923323698&layout=standard&show_faces=false&width=450&action=like&colorscheme=light&height=20 | IE | — | — | whitelisted |
3964 | CSU.exe | GET | 200 | 104.37.182.3:80 | http://cdn.download.comodo.com/csc/download/updates/CFM%204.0/version_free.ini | US | text | 895 b | whitelisted |
3964 | CSU.exe | GET | 200 | 178.255.82.1:80 | http://downloads.comodo.com/cpa/v2/HtmlFiles/facebook2.html | GB | html | 4.09 Kb | unknown |
3964 | CSU.exe | GET | 200 | 178.255.82.1:80 | http://downloads.comodo.com/cpa/v2/res/style.css | GB | text | 583 b | unknown |
3964 | CSU.exe | GET | 200 | 178.255.82.1:80 | http://downloads.comodo.com/cpa/v2/res/facebook_logo.jpg | GB | image | 2.85 Kb | unknown |
3964 | CSU.exe | GET | 200 | 178.255.82.1:80 | http://downloads.comodo.com/cpa/v2/res/over_red.png | GB | image | 3.12 Kb | unknown |
3964 | CSU.exe | GET | 200 | 178.255.82.1:80 | http://downloads.comodo.com/cpa/v2/CSC_config_cpa | GB | xml | 332 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2448 | CSU.exe | 91.199.212.132:80 | secure.comodo.net | Comodo CA Ltd | GB | unknown |
3964 | CSU.exe | 172.217.21.206:80 | gdata.youtube.com | Google Inc. | US | whitelisted |
3964 | CSU.exe | 199.66.205.228:80 | system-utilities.comodo.com | CCANET Limited | US | unknown |
3964 | CSU.exe | 178.255.82.1:80 | downloads.comodo.com | CCANET Limited | GB | unknown |
3964 | CSU.exe | 199.66.205.228:443 | system-utilities.comodo.com | CCANET Limited | US | unknown |
3964 | CSU.exe | 178.255.82.5:80 | download.comodo.com | CCANET Limited | GB | suspicious |
3964 | CSU.exe | 172.217.18.110:80 | www.google-analytics.com | Google Inc. | US | whitelisted |
3964 | CSU.exe | 104.37.182.3:80 | cdn.download.comodo.com | ISPrime, Inc. | US | suspicious |
3964 | CSU.exe | 31.13.92.36:80 | www.facebook.com | Facebook, Inc. | IE | whitelisted |
3964 | CSU.exe | 31.13.92.36:443 | www.facebook.com | Facebook, Inc. | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
secure.comodo.net |
| unknown |
system-utilities.comodo.com |
| unknown |
gdata.youtube.com |
| whitelisted |
downloads.comodo.com |
| unknown |
download.comodo.com |
| whitelisted |
cdn.download.comodo.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
www.facebook.com |
| whitelisted |
static.xx.fbcdn.net |
| whitelisted |
fls.security.comodo.com |
| suspicious |