| File name: | procexp.exe |
| Full analysis: | https://app.any.run/tasks/43890036-c0c5-4476-b8c2-b614e87600ed |
| Verdict: | Malicious activity |
| Analysis date: | March 26, 2018, 06:29:14 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 4410D1023F5FB229187824D0E4650586 |
| SHA1: | 261EAFAE071BA4B11F2A972300A3DCE61D1651E8 |
| SHA256: | BBEB590EA5150BA7304C124D2FA1C34F4CB4AE825B068F455045AA643E05CCDC |
| SSDEEP: | 49152:ihqGRrMaduD+frEYPloFh0/6gQV/4bPTytt6:ifMYycZ |
MALICIOUS
Loads the Task Scheduler COM API
- procexp.exe (PID: 3676)
- procexp.exe (PID: 2252)
SUSPICIOUS
Creates files in the Windows directory
- procexp.exe (PID: 2252)
Removes files from Windows directory
- procexp.exe (PID: 2252)
Creates files in the driver directory
- procexp.exe (PID: 2252)
Creates or modifies windows services
- procexp.exe (PID: 2252)
INFO
Loads rich edit control libraries
- procexp.exe (PID: 3676)
Dropped object may contain URL's
- procexp.exe (PID: 2252)
Reads settings of System Certificates
- procexp.exe (PID: 3676)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:02:04 23:09:33+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 12 |
| CodeSize: | 758784 |
| InitializedDataSize: | 1918976 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x9a548 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 16.12.0.0 |
| ProductVersionNumber: | 16.12.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Private build |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Sysinternals - www.sysinternals.com |
| FileDescription: | Sysinternals Process Explorer |
| FileVersion: | 16.12 |
| InternalName: | Process Explorer |
| LegalCopyright: | Copyright © 1998-2016 Mark Russinovich |
| LegalTrademarks: | Copyright (C) 1998-2016 Mark Russinovich |
| OriginalFileName: | Procexp.exe |
| ProductName: | Process Explorer |
| ProductVersion: | 16.12 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 04-Feb-2016 22:09:33 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Sysinternals - www.sysinternals.com |
| FileDescription: | Sysinternals Process Explorer |
| FileVersion: | 16.12 |
| InternalName: | Process Explorer |
| LegalCopyright: | Copyright © 1998-2016 Mark Russinovich |
| LegalTrademarks: | Copyright (C) 1998-2016 Mark Russinovich |
| OriginalFilename: | Procexp.exe |
| ProductName: | Process Explorer |
| ProductVersion: | 16.12 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000118 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 04-Feb-2016 22:09:33 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000B9398 | 0x000B9400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.48804 |
.rdata | 0x000BB000 | 0x0002B28E | 0x0002B400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.61454 |
.data | 0x000E7000 | 0x0002DA28 | 0x00009200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.68747 |
.rsrc | 0x00115000 | 0x00193D40 | 0x00193E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.03516 |
.reloc | 0x002A9000 | 0x0000C3C0 | 0x0000C400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.76789 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.13246 | 1904 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.46162 | 332 | Latin 1 / Western European | English - United States | RT_STRING |
3 | 3.40776 | 320 | Latin 1 / Western European | English - United States | RT_STRING |
4 | 2.62344 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
5 | 4.33181 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 5.37984 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 5.94402 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 5.59771 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 5.4153 | 3752 | Latin 1 / Western European | English - United States | RT_ICON |
10 | 2.01924 | 20 | Latin 1 / Western European | English - United States | RT_GROUP_CURSOR |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
CRYPT32.dll |
GDI32.dll |
KERNEL32.dll |
MPR.dll |
OLEAUT32.dll |
PSAPI.DLL |
SETUPAPI.dll |
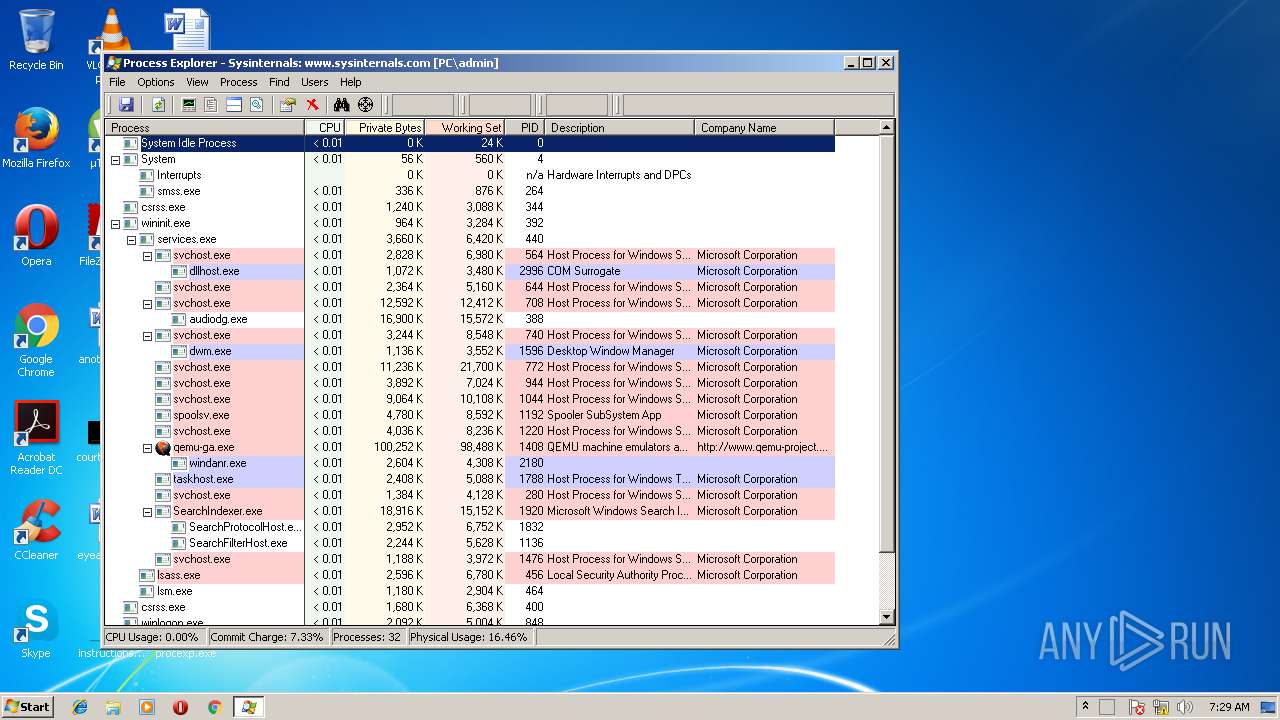
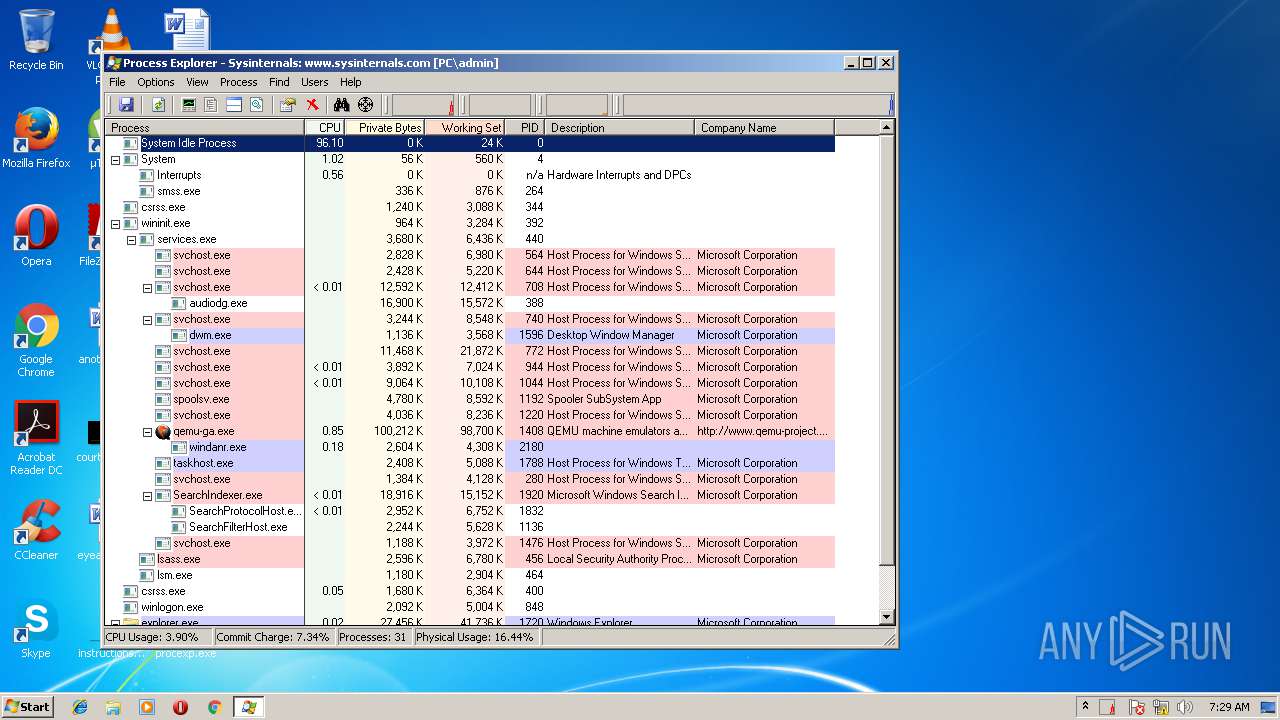
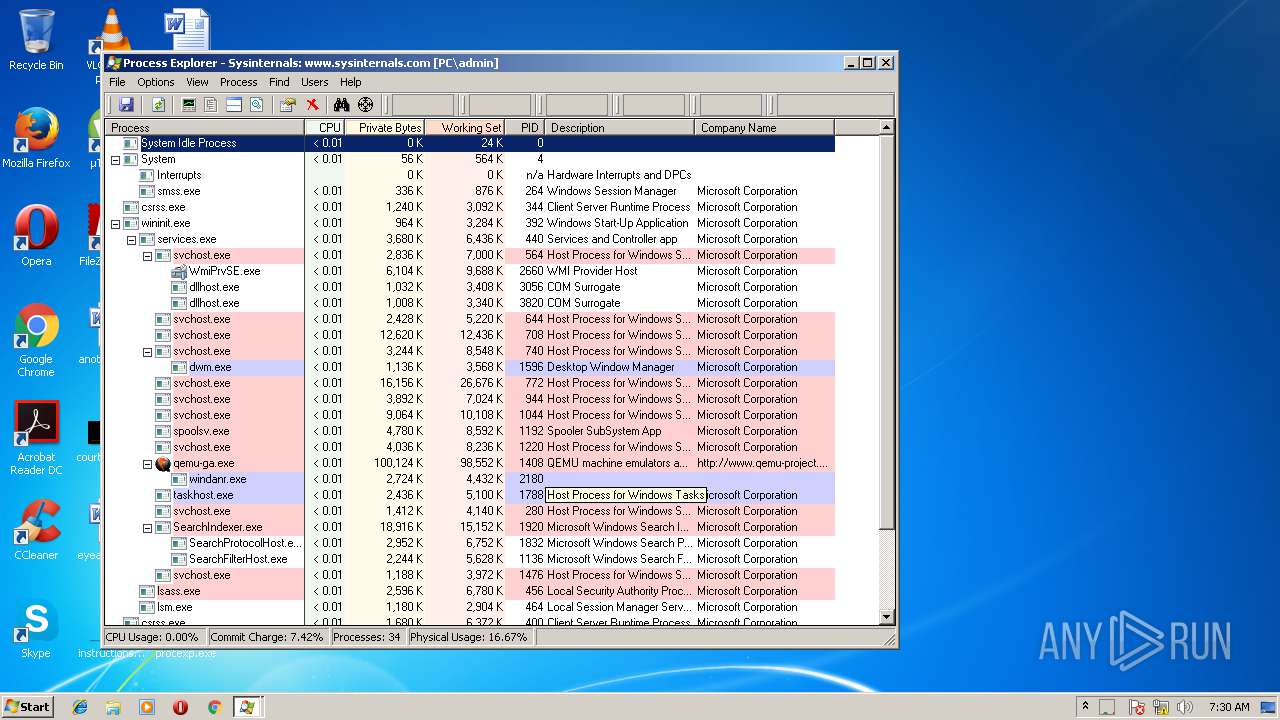
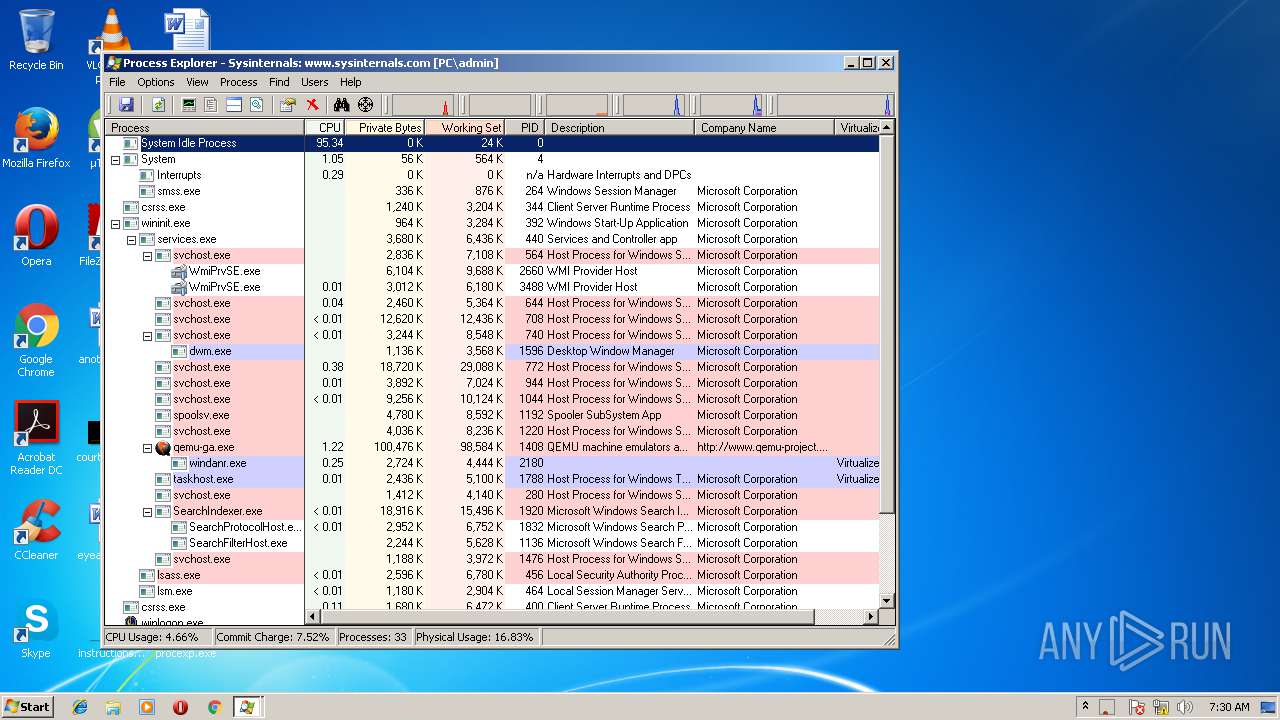
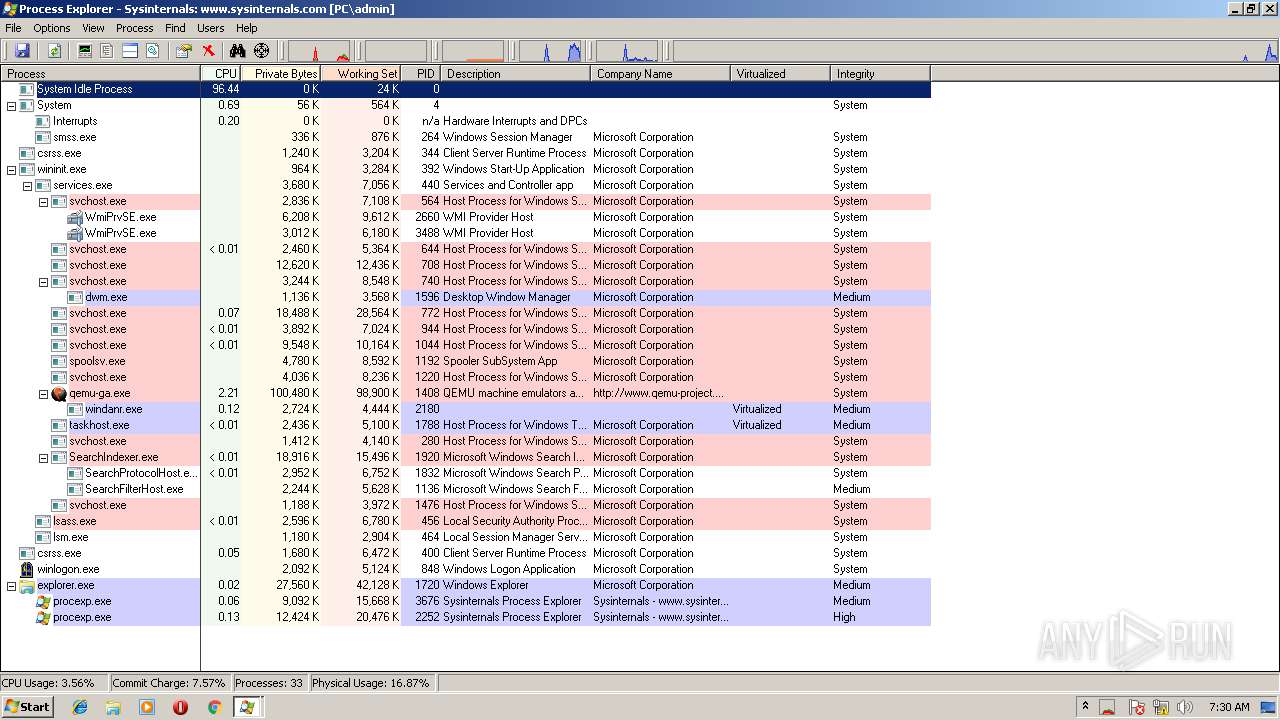
Total processes
39
Monitored processes
2
Malicious processes
1
Suspicious processes
0
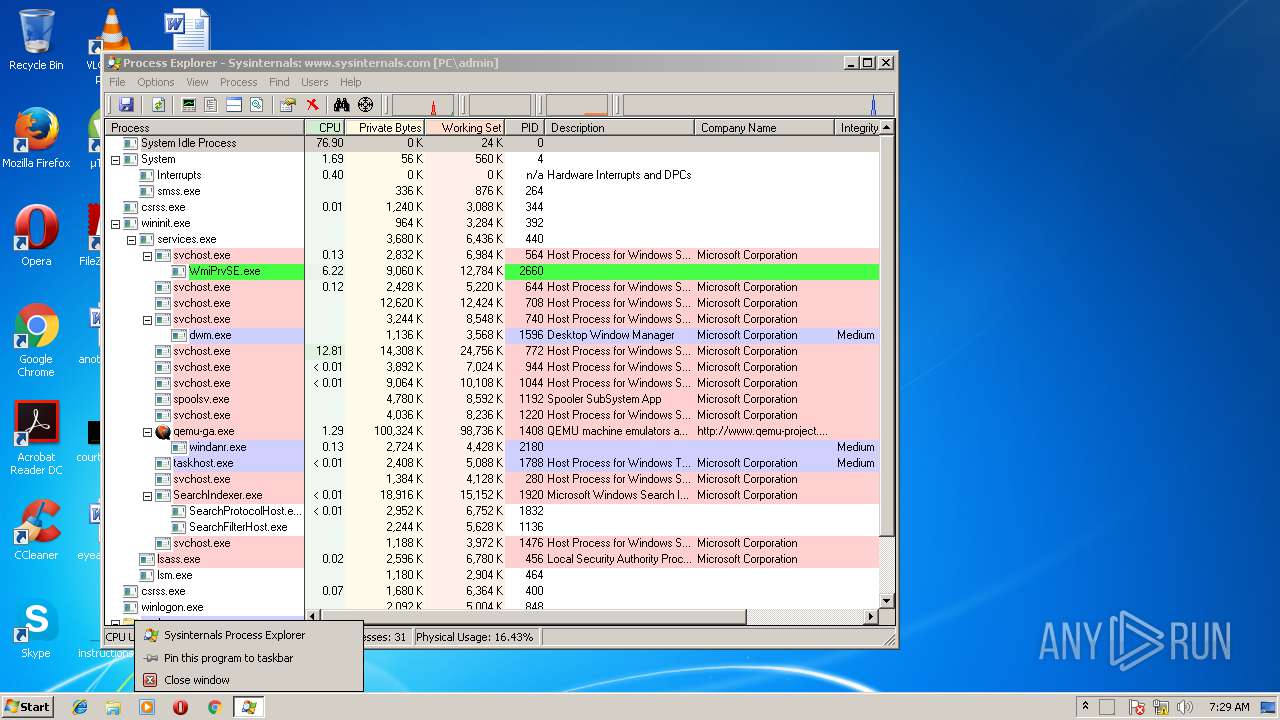
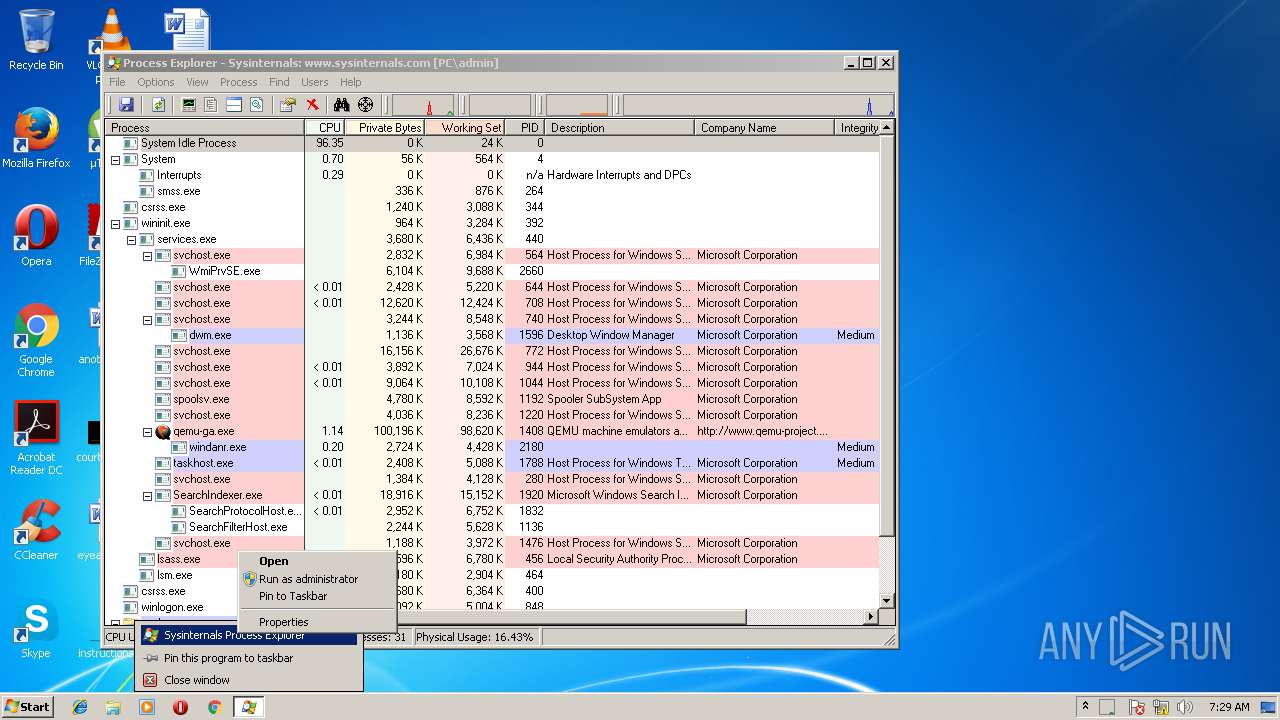
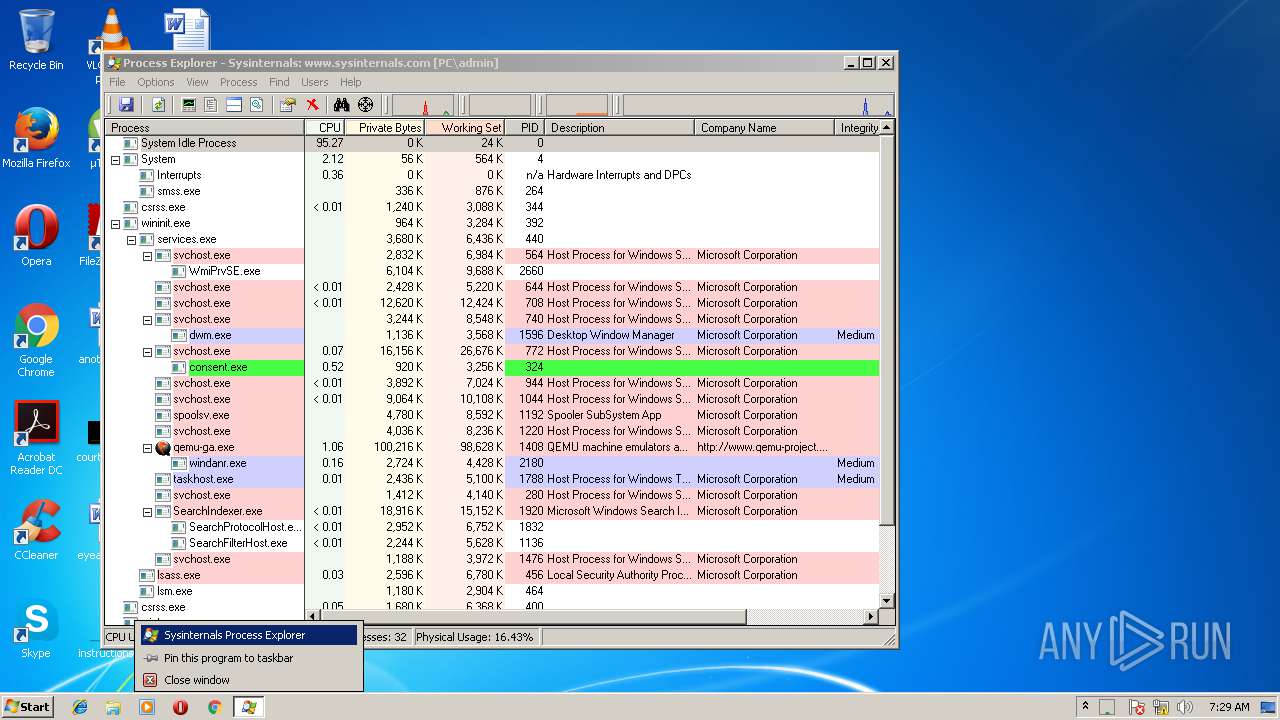
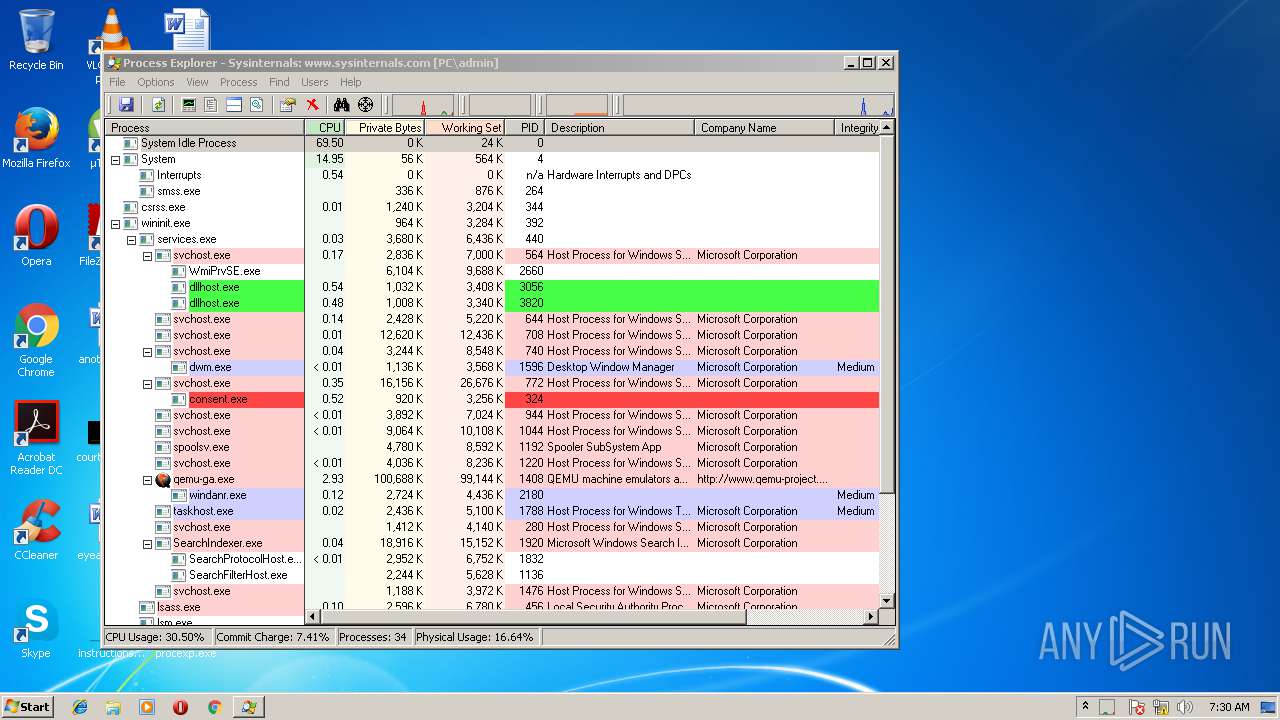
Behavior graph
Click at the process to see the details
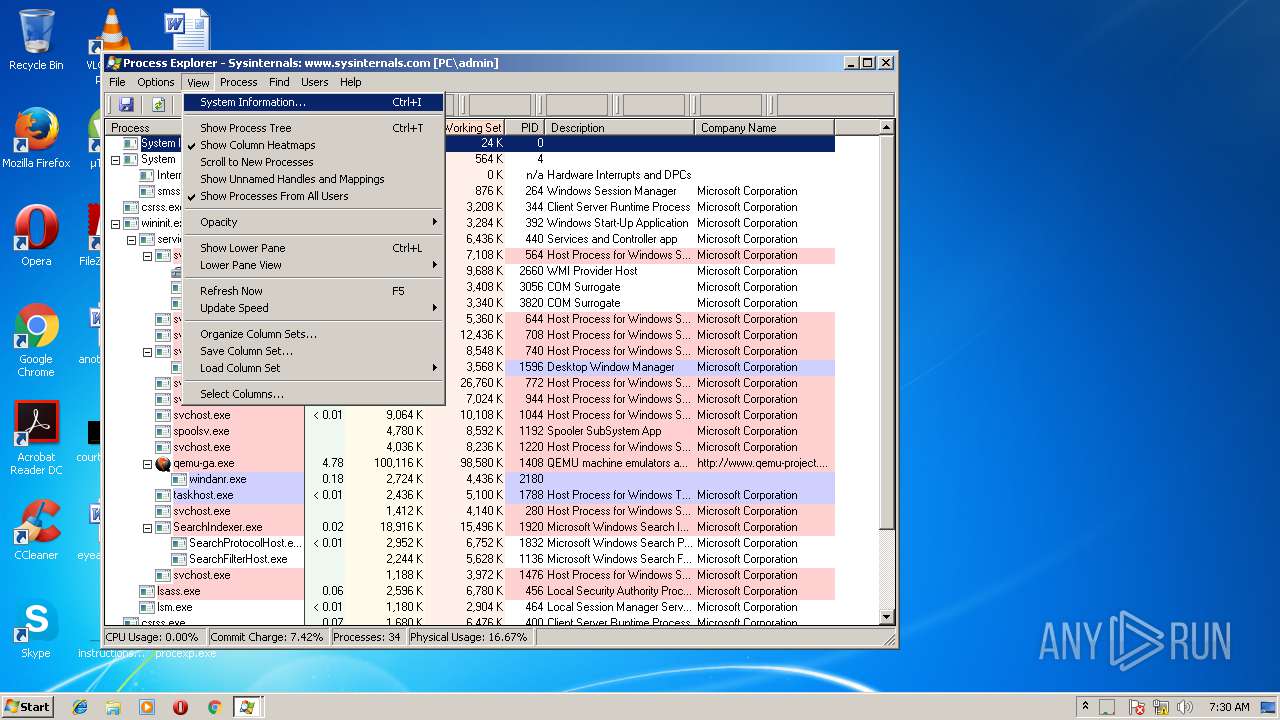
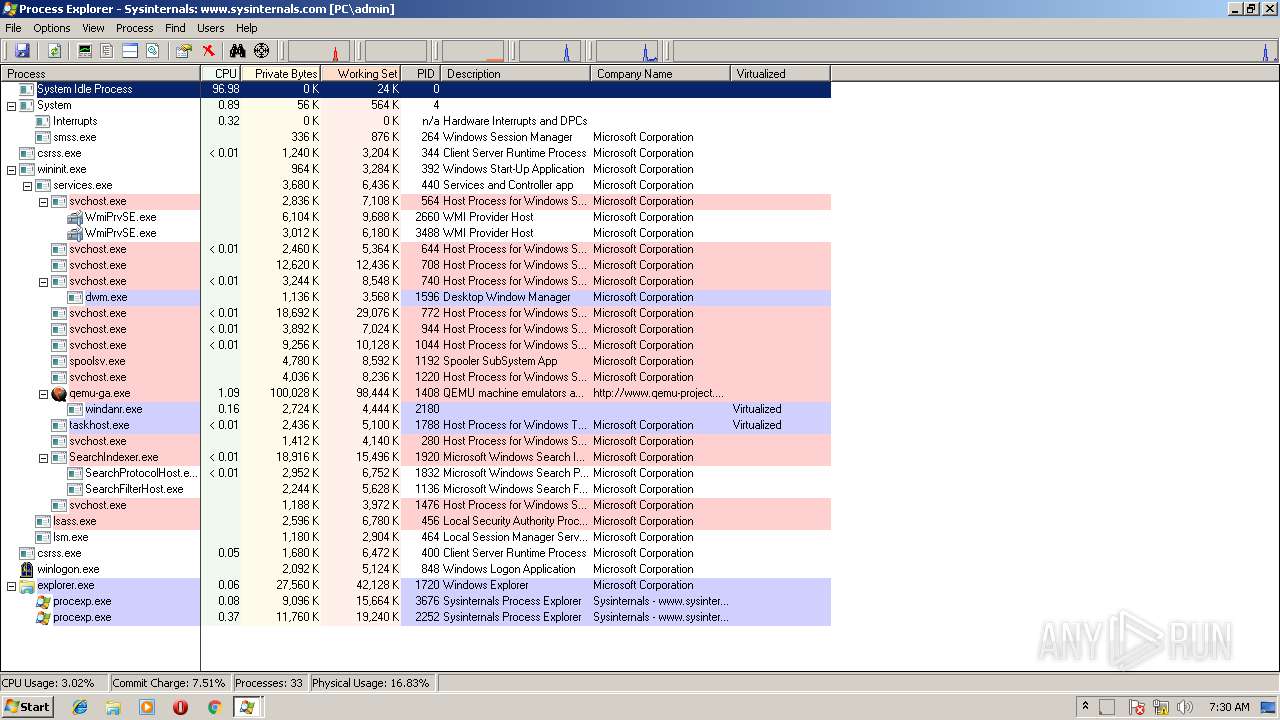
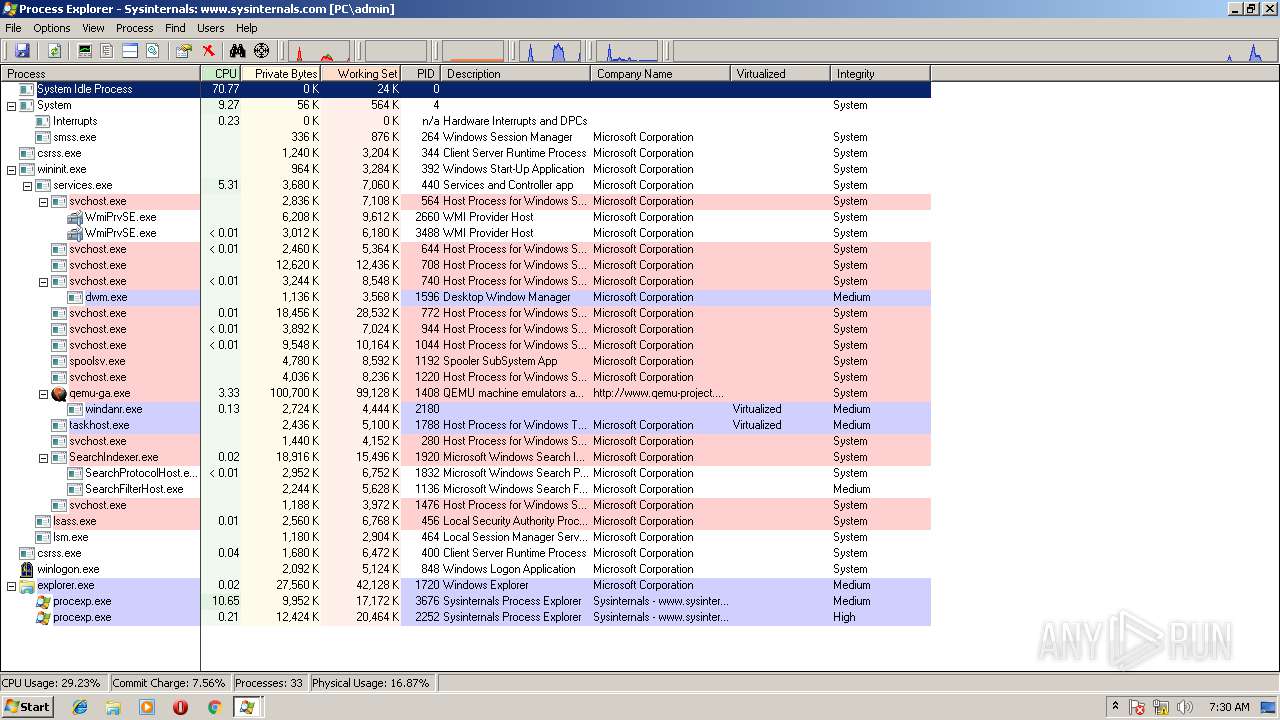
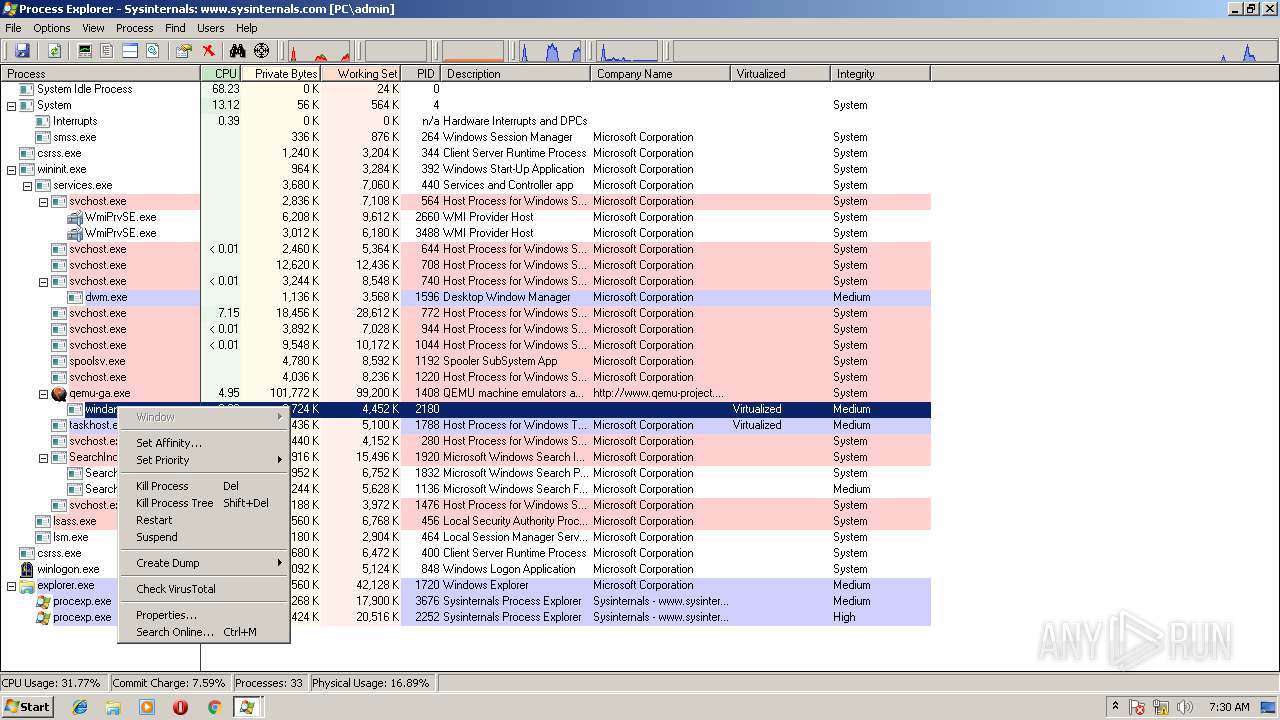
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2252 | "C:\Users\admin\Desktop\procexp.exe" | C:\Users\admin\Desktop\procexp.exe | explorer.exe | ||||||||||||
User: admin Company: Sysinternals - www.sysinternals.com Integrity Level: HIGH Description: Sysinternals Process Explorer Exit code: 0 Version: 16.12 Modules
| |||||||||||||||
| 3676 | "C:\Users\admin\Desktop\procexp.exe" | C:\Users\admin\Desktop\procexp.exe | — | explorer.exe | |||||||||||
User: admin Company: Sysinternals - www.sysinternals.com Integrity Level: MEDIUM Description: Sysinternals Process Explorer Exit code: 0 Version: 16.12 Modules
| |||||||||||||||
Total events
4 582
Read events
4 382
Write events
198
Delete events
2
Modification events
| (PID) Process: | (3676) procexp.exe | Key: | HKEY_CURRENT_USER\Software\Sysinternals\Process Explorer |
| Operation: | write | Name: | EulaAccepted |
Value: 1 | |||
| (PID) Process: | (2252) procexp.exe | Key: | HKEY_CURRENT_USER\Software\Sysinternals\Process Explorer |
| Operation: | write | Name: | EulaAccepted |
Value: 1 | |||
| (PID) Process: | (2252) procexp.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\PROCEXP152 |
| Operation: | write | Name: | Type |
Value: 1 | |||
| (PID) Process: | (2252) procexp.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\PROCEXP152 |
| Operation: | write | Name: | ErrorControl |
Value: 1 | |||
| (PID) Process: | (2252) procexp.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\PROCEXP152 |
| Operation: | write | Name: | Start |
Value: 3 | |||
| (PID) Process: | (2252) procexp.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\PROCEXP152 |
| Operation: | write | Name: | ImagePath |
Value: \??\C:\Windows\system32\Drivers\PROCEXP152.SYS | |||
| (PID) Process: | (2252) procexp.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\PROCEXP152\Enum |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2252) procexp.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\PROCEXP152 |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2252) procexp.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\.NET Memory Cache 4.0\Linkage |
| Operation: | write | Name: | Export |
Value: .NET Memory Cache 4.0 | |||
| (PID) Process: | (2252) procexp.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\MSDTC Bridge 3.0.0.0\Linkage |
| Operation: | write | Name: | Export |
Value: MSDTC Bridge 3.0.0.0 | |||
Executable files
0
Suspicious files
4
Text files
0
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3676 | procexp.exe | C:\Users\admin\AppData\Local\Temp\PROCEXP152.SYS | — | |
MD5:— | SHA256:— | |||
| 2252 | procexp.exe | C:\Windows\system32\Drivers\PROCEXP152.SYS | — | |
MD5:— | SHA256:— | |||
| 2252 | procexp.exe | C:\Users\admin\AppData\Local\Temp\Cab6D93.tmp | — | |
MD5:— | SHA256:— | |||
| 2252 | procexp.exe | C:\Users\admin\AppData\Local\Temp\Tar6D94.tmp | — | |
MD5:— | SHA256:— | |||
| 3676 | procexp.exe | C:\Users\admin\AppData\Local\Temp\CabA1E2.tmp | — | |
MD5:— | SHA256:— | |||
| 3676 | procexp.exe | C:\Users\admin\AppData\Local\Temp\TarA1E3.tmp | — | |
MD5:— | SHA256:— | |||
| 2252 | procexp.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\696F3DE637E6DE85B458996D49D759AD | der | |
MD5:E03CE4599A8AA4434501D9297B1C29AC | SHA256:E7E8859A02DDD04D502DD2AE95C7731466A983C3305AAB44828AC9F91E449D7F | |||
| 2252 | procexp.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\696F3DE637E6DE85B458996D49D759AD | binary | |
MD5:632BE59DC36C64304216DB725E9A566C | SHA256:9280BEE8650849CE5CDC14F9AE82331D98DB4CB4020462A29A673706A2EF21A1 | |||
| 2252 | procexp.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B8CC409ACDBF2A2FE04C56F2875B1FD6 | der | |
MD5:5E275DB761AA5A23AC651AF8F6C4A000 | SHA256:3B9B2F75B724FE5354D24A0EF729B8A2AAA8A9313166EAFB1F73B07CF1A745EF | |||
| 2252 | procexp.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B8CC409ACDBF2A2FE04C56F2875B1FD6 | binary | |
MD5:388F07BC0E3C359DDE846D321513CA4C | SHA256:BD6398B012C82820D8F251EC5B760DB03AEB56554D9CC6C88444A20722B489C7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.186.74:80 | http://crl.microsoft.com/pki/crl/products/microsoftrootcert.crl | unknown | der | 781 b | whitelisted |
— | — | GET | 200 | 2.16.186.74:80 | http://crl.microsoft.com/pki/crl/products/WinPCA.crl | unknown | der | 530 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 2.16.186.74:80 | crl.microsoft.com | Akamai International B.V. | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |