| File name: | LV2020-V46-PROD-913.exe |
| Full analysis: | https://app.any.run/tasks/85989b5b-bbea-4bb6-970a-656e46eb96dc |
| Verdict: | Suspicious activity |
| Analysis date: | September 04, 2019, 16:34:48 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, InstallShield self-extracting archive |
| MD5: | 873B5B189EF4340ED51AB90DA2FDFC48 |
| SHA1: | E33C92A5B47C3BFC4B3BA32A1277398E98B0F40C |
| SHA256: | BBEB00D95615AB9C9741C2C9F22FD4BCC45E5587974B06F6FA16E36EA906CFE5 |
| SSDEEP: | 393216:KebtGlLzg3McrZ3RteQf2LgvltT/HB+cDkI57jdfaMSgv0zeurwcYANH:klLzgPHteQagvlJvAlI5v0zoe |
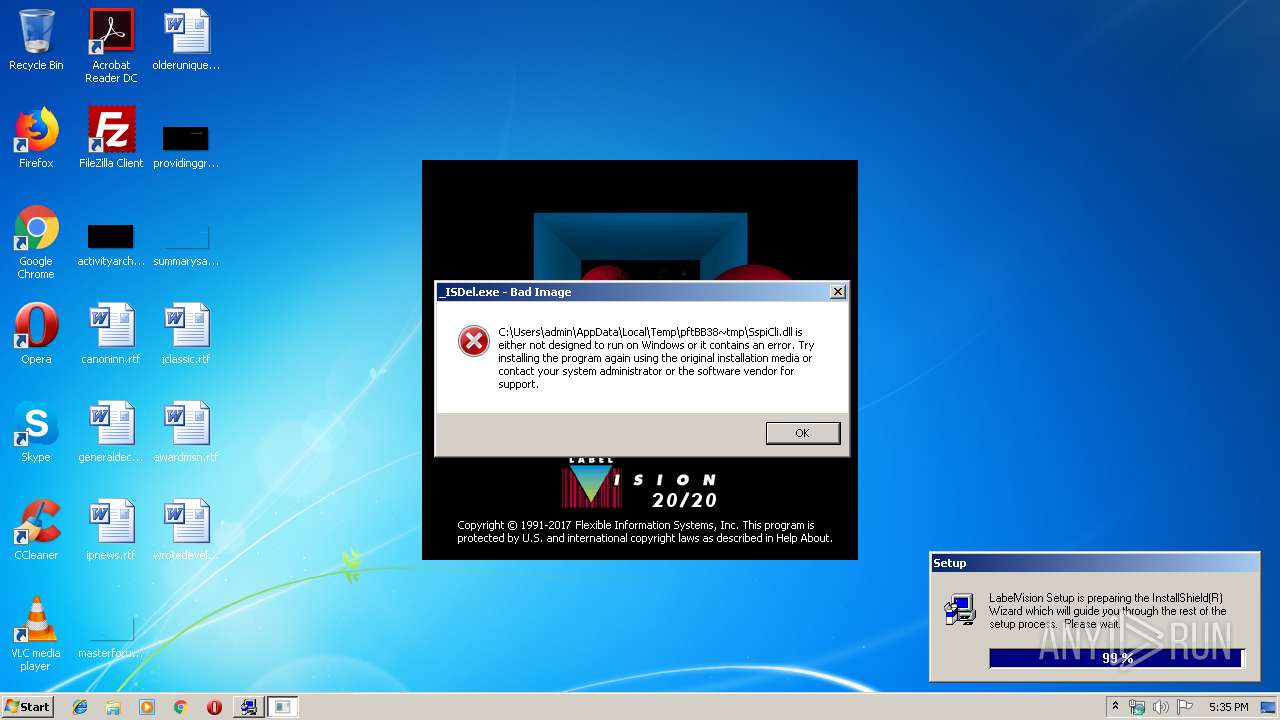
MALICIOUS
Loads dropped or rewritten executable
- Setup.exe (PID: 3300)
- _INS5576._MP (PID: 3564)
Application was dropped or rewritten from another process
- Setup.exe (PID: 3300)
- _ISDEL.EXE (PID: 3160)
- _INS5576._MP (PID: 3564)
SUSPICIOUS
Starts application with an unusual extension
- Setup.exe (PID: 3300)
Executable content was dropped or overwritten
- LV2020-V46-PROD-913.exe (PID: 560)
- Setup.exe (PID: 3300)
- _INS5576._MP (PID: 3564)
Creates files in the Windows directory
- Setup.exe (PID: 3300)
- _INS5576._MP (PID: 3564)
Removes files from Windows directory
- _INS5576._MP (PID: 3564)
INFO
Dropped object may contain Bitcoin addresses
- _INS5576._MP (PID: 3564)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ 4.x (53) |
|---|---|---|
| .exe | | | InstallShield setup (16.9) |
| .exe | | | Win32 Executable MS Visual C++ (generic) (12.2) |
| .exe | | | Win64 Executable (generic) (10.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (2.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1999:01:07 19:10:41+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 5 |
| CodeSize: | 72192 |
| InitializedDataSize: | 72704 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xce00 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.4.1.0 |
| ProductVersionNumber: | 2.4.1.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | InstallShield Software Corporation |
| FileDescription: | PackageForTheWeb Stub |
| FileVersion: | 2.04.001 |
| InternalName: | STUB.EXE |
| LegalCopyright: | Copyright © 1996-1999 InstallShield Software Corporation |
| OriginalFileName: | STUB32.EXE |
| ProductName: | PackageForTheWeb Stub |
| ProductVersion: | 2.04.001 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 07-Jan-1999 18:10:41 |
| Detected languages: |
|
| CompanyName: | InstallShield Software Corporation |
| FileDescription: | PackageForTheWeb Stub |
| FileVersion: | 2.04.001 |
| InternalName: | STUB.EXE |
| LegalCopyright: | Copyright © 1996-1999 InstallShield Software Corporation |
| OriginalFilename: | STUB32.EXE |
| ProductName: | PackageForTheWeb Stub |
| ProductVersion: | 2.04.001 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 07-Jan-1999 18:10:41 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00011906 | 0x00011A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.54735 |
.rdata | 0x00013000 | 0x0000055B | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.88663 |
.data | 0x00014000 | 0x00006E14 | 0x00003200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.78328 |
.idata | 0x0001B000 | 0x00000F7C | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.36381 |
.rsrc | 0x0001C000 | 0x000095B4 | 0x00009600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.988 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.44713 | 860 | UNKNOWN | English - United States | RT_VERSION |
2 | 3.5531 | 934 | UNKNOWN | English - United States | RT_STRING |
3 | 3.27378 | 1216 | UNKNOWN | English - United States | RT_STRING |
4 | 3.13305 | 318 | UNKNOWN | English - United States | RT_STRING |
19 | 2.86832 | 186 | UNKNOWN | English - United States | RT_STRING |
20 | 3.31313 | 1002 | UNKNOWN | English - United States | RT_STRING |
21 | 2.99445 | 154 | UNKNOWN | English - United States | RT_STRING |
102 | 3.14058 | 11776 | UNKNOWN | English - United States | AVI |
103 | 2.47702 | 34 | UNKNOWN | English - United States | RT_GROUP_ICON |
104 | 2.16096 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
LZ32.dll |
SHELL32.dll |
USER32.dll |
Total processes
40
Monitored processes
5
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 560 | "C:\Users\admin\AppData\Local\Temp\LV2020-V46-PROD-913.exe" | C:\Users\admin\AppData\Local\Temp\LV2020-V46-PROD-913.exe | explorer.exe | ||||||||||||
User: admin Company: InstallShield Software Corporation Integrity Level: HIGH Description: PackageForTheWeb Stub Exit code: 0 Version: 2.04.001 Modules
| |||||||||||||||
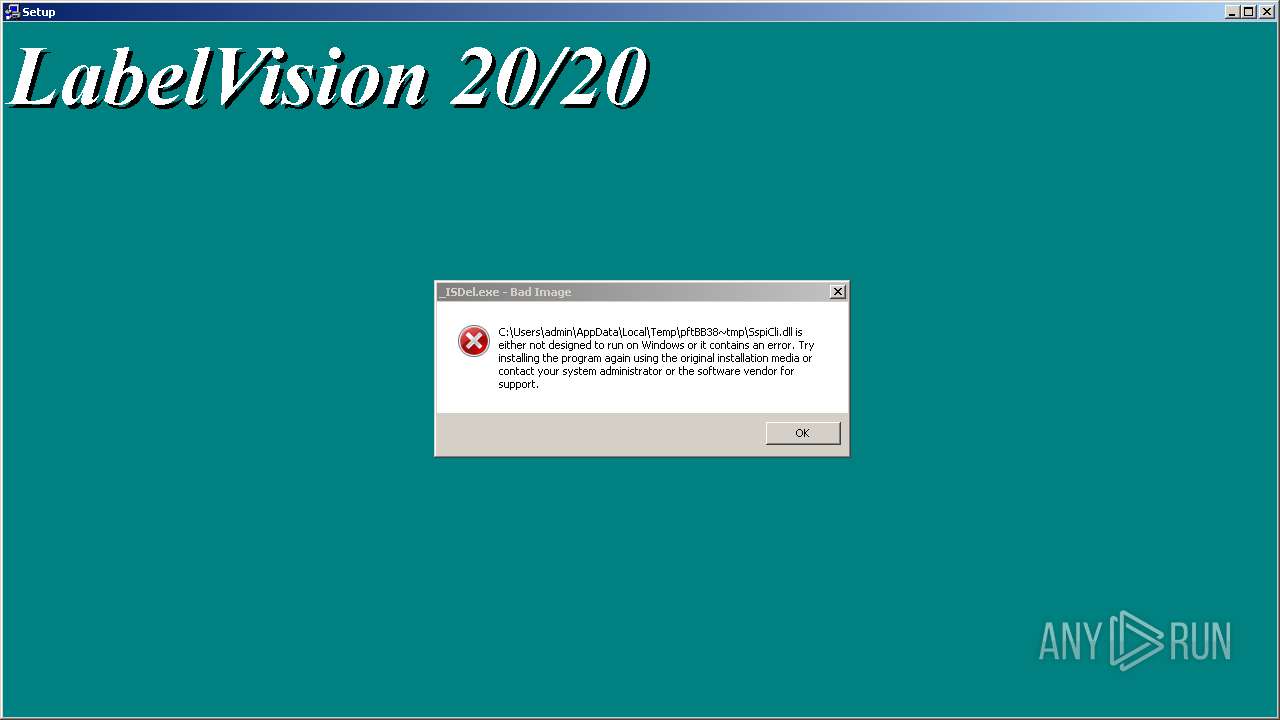
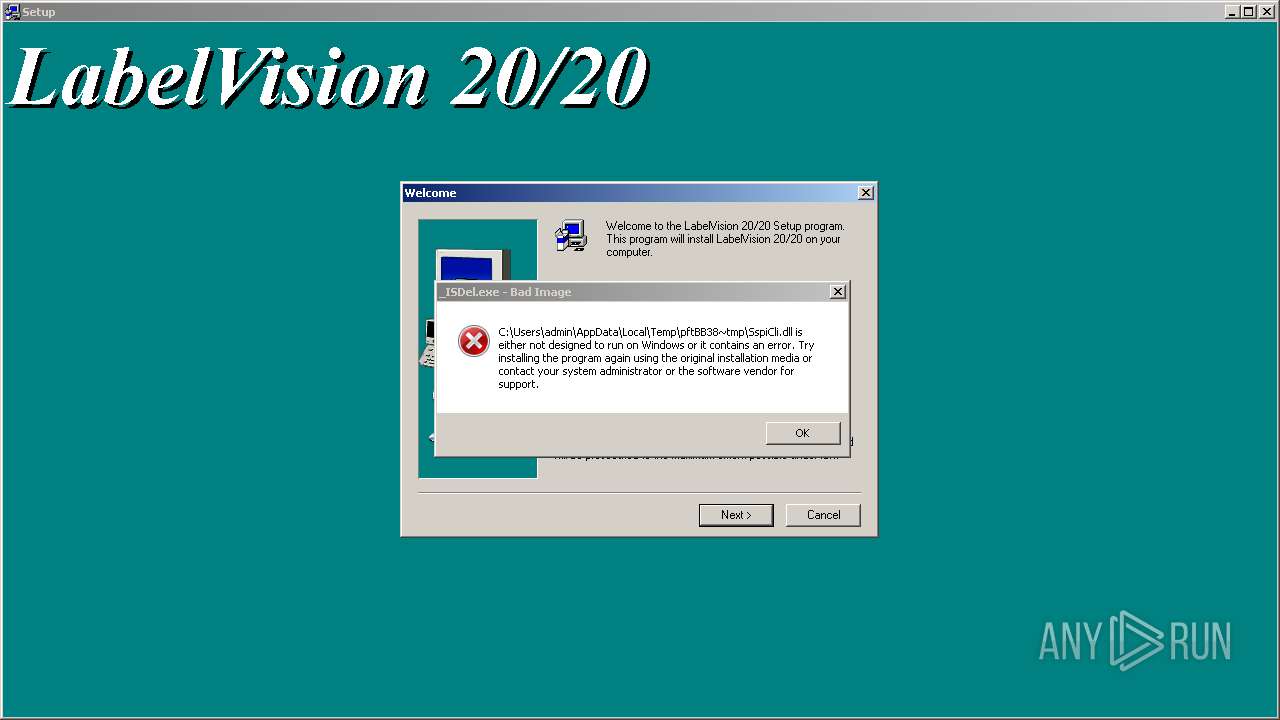
| 3160 | C:\Users\admin\AppData\Local\Temp\pftBB38~tmp\_ISDEL.EXE | C:\Users\admin\AppData\Local\Temp\pftBB38~tmp\_ISDEL.EXE | — | Setup.exe | |||||||||||
User: admin Company: InstallShield Software Corporation Integrity Level: HIGH Description: 32-bit InstallShield Deleter. Exit code: 0 Version: 5, 51, 138, 0 Modules
| |||||||||||||||
| 3300 | "C:\Users\admin\AppData\Local\Temp\pftBB38~tmp\Setup.exe" /SMS | C:\Users\admin\AppData\Local\Temp\pftBB38~tmp\Setup.exe | LV2020-V46-PROD-913.exe | ||||||||||||
User: admin Company: InstallShield Software Corporation Integrity Level: HIGH Description: 32-bit Setup Launcher Exit code: 0 Version: 5, 52, 164, 0 Modules
| |||||||||||||||
| 3564 | C:\Users\admin\AppData\Local\Temp\_ISTMP1.DIR\_INS5576._MP | C:\Users\admin\AppData\Local\Temp\_ISTMP1.DIR\_INS5576._MP | Setup.exe | ||||||||||||
User: admin Company: InstallShield Software Corporation Integrity Level: HIGH Description: InstallShield Engine Exit code: 0 Version: 5, 53, 168, 0 Modules
| |||||||||||||||
| 3652 | "C:\Users\admin\AppData\Local\Temp\LV2020-V46-PROD-913.exe" | C:\Users\admin\AppData\Local\Temp\LV2020-V46-PROD-913.exe | — | explorer.exe | |||||||||||
User: admin Company: InstallShield Software Corporation Integrity Level: MEDIUM Description: PackageForTheWeb Stub Exit code: 3221226540 Version: 2.04.001 Modules
| |||||||||||||||
Total events
38
Read events
37
Write events
0
Delete events
1
Modification events
| (PID) Process: | (3564) _INS5576._MP | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Flexible Information Systems, Inc.\LabelVision\LVTEMP |
| Operation: | delete key | Name: | |
Value: | |||
Executable files
20
Suspicious files
7
Text files
25
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 560 | LV2020-V46-PROD-913.exe | C:\Users\admin\AppData\Local\Temp\extBB18.tmp | — | |
MD5:— | SHA256:— | |||
| 560 | LV2020-V46-PROD-913.exe | C:\Users\admin\AppData\Local\Temp\pftBB38~tmp\pftw1.pkg | — | |
MD5:— | SHA256:— | |||
| 560 | LV2020-V46-PROD-913.exe | C:\Users\admin\AppData\Local\Temp\pftBB38~tmp\data1.cab | — | |
MD5:— | SHA256:— | |||
| 560 | LV2020-V46-PROD-913.exe | C:\Users\admin\AppData\Local\Temp\plfBB17.tmp | text | |
MD5:— | SHA256:— | |||
| 560 | LV2020-V46-PROD-913.exe | C:\Users\admin\AppData\Local\Temp\pftBB38~tmp\DATA.TAG | text | |
MD5:— | SHA256:— | |||
| 560 | LV2020-V46-PROD-913.exe | C:\Users\admin\AppData\Local\Temp\pftBB38~tmp\autorun.inf | ini | |
MD5:— | SHA256:— | |||
| 560 | LV2020-V46-PROD-913.exe | C:\Users\admin\AppData\Local\Temp\pftBB38~tmp\AclFull.exe | executable | |
MD5:— | SHA256:— | |||
| 560 | LV2020-V46-PROD-913.exe | C:\Users\admin\AppData\Local\Temp\pftBB38~tmp\data1.hdr | compressed | |
MD5:— | SHA256:— | |||
| 560 | LV2020-V46-PROD-913.exe | C:\Users\admin\AppData\Local\Temp\pftBB38~tmp\lang.dat | text | |
MD5:70627BD56FE92A5C97027CBBD88BACD0 | SHA256:B67A09F3FE25B08025810BBB20B8FAE05672D0A723F2DBED84F04224A89E6344 | |||
| 560 | LV2020-V46-PROD-913.exe | C:\Users\admin\AppData\Local\Temp\pftBB38~tmp\SETUP.INI | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report