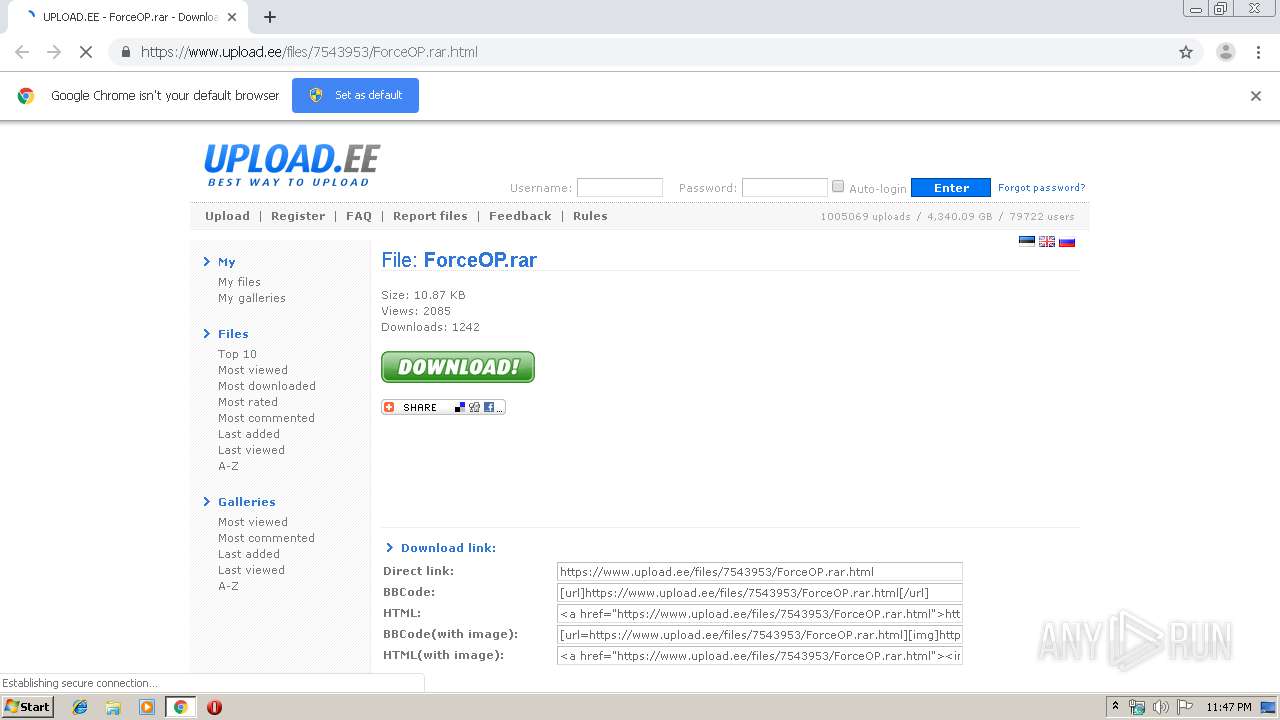
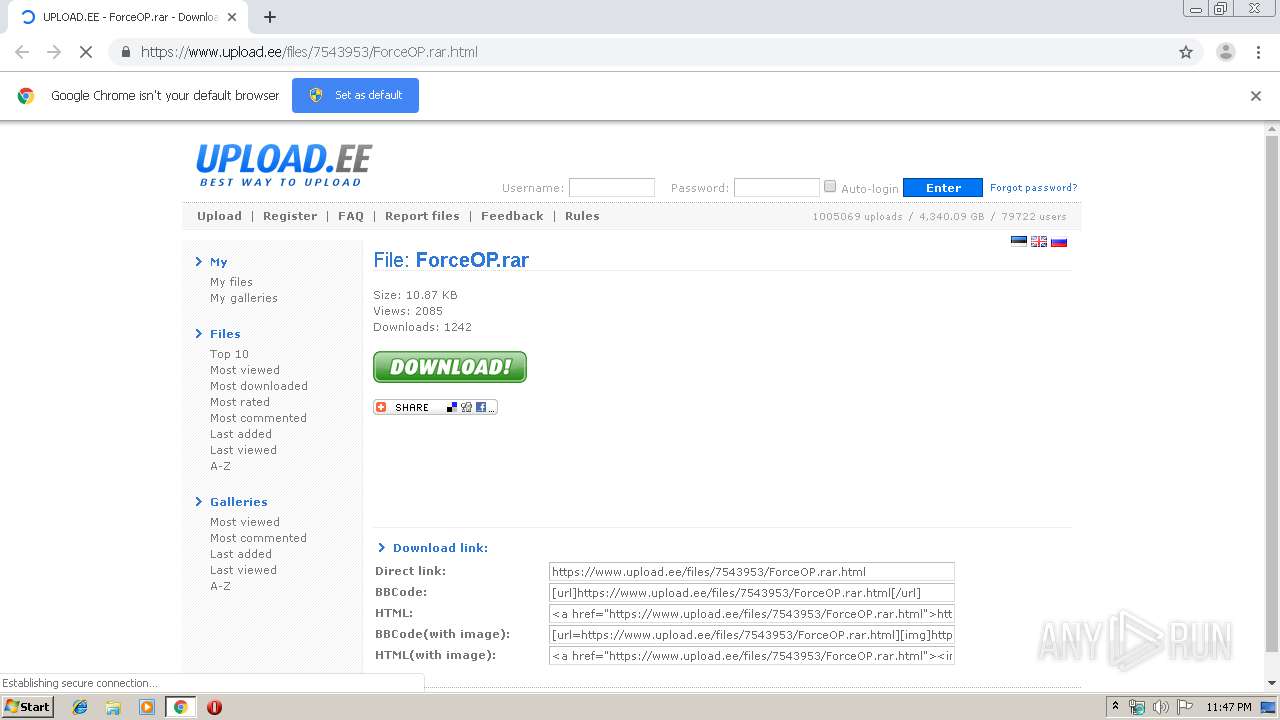
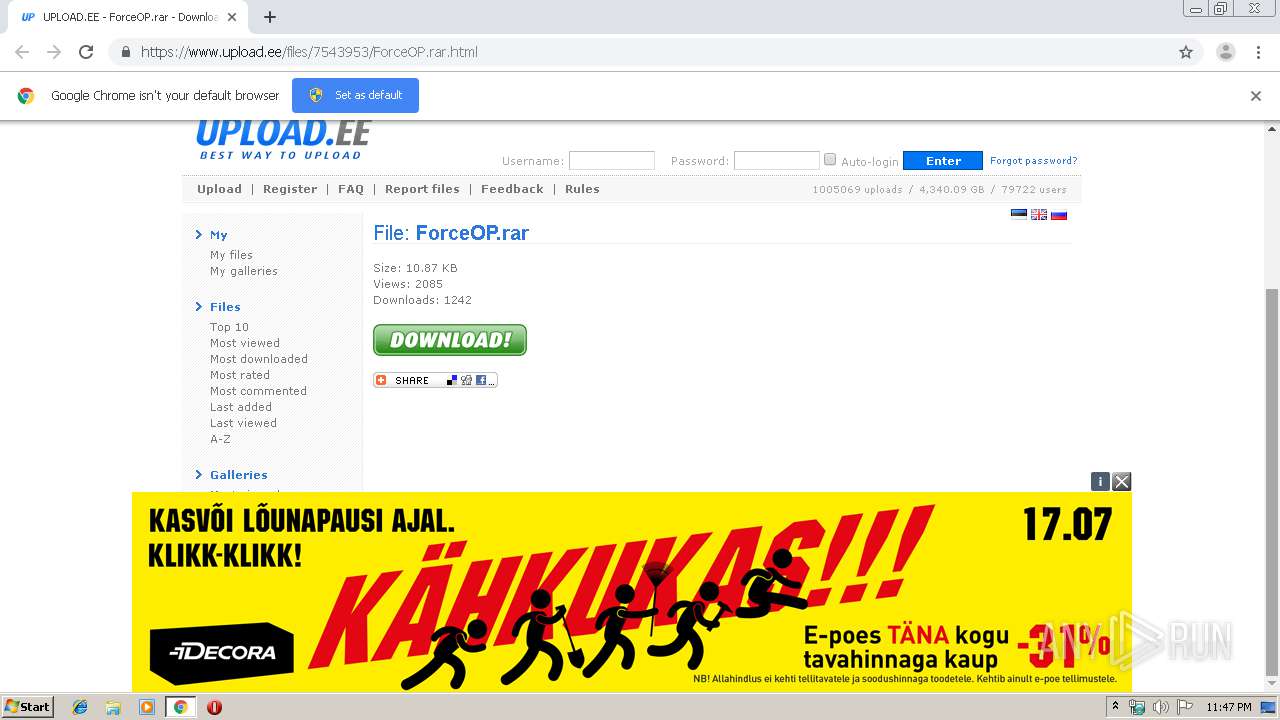
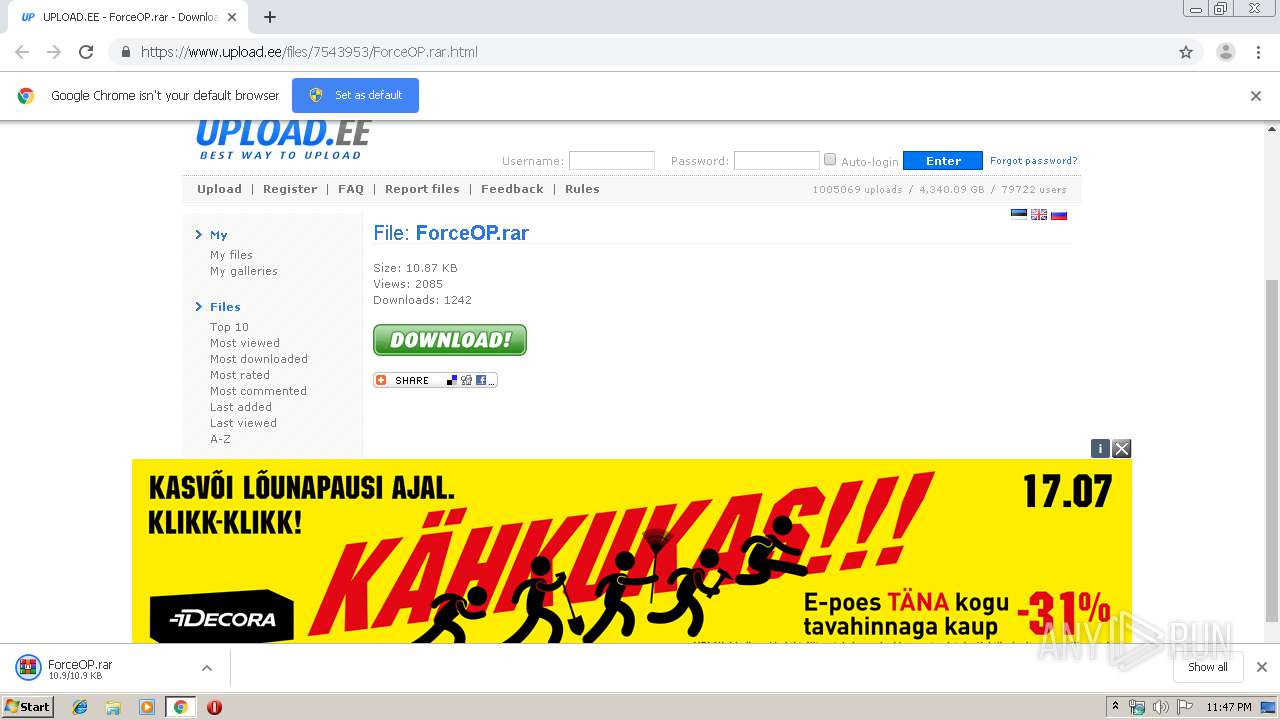
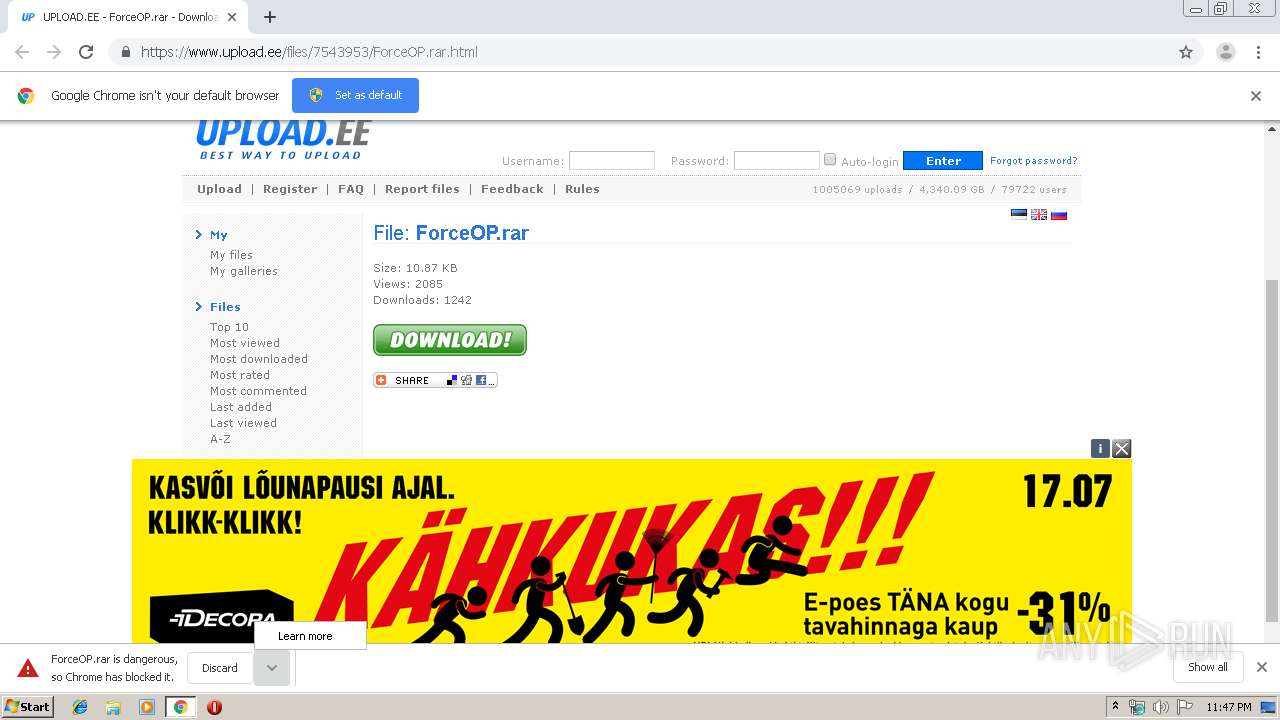
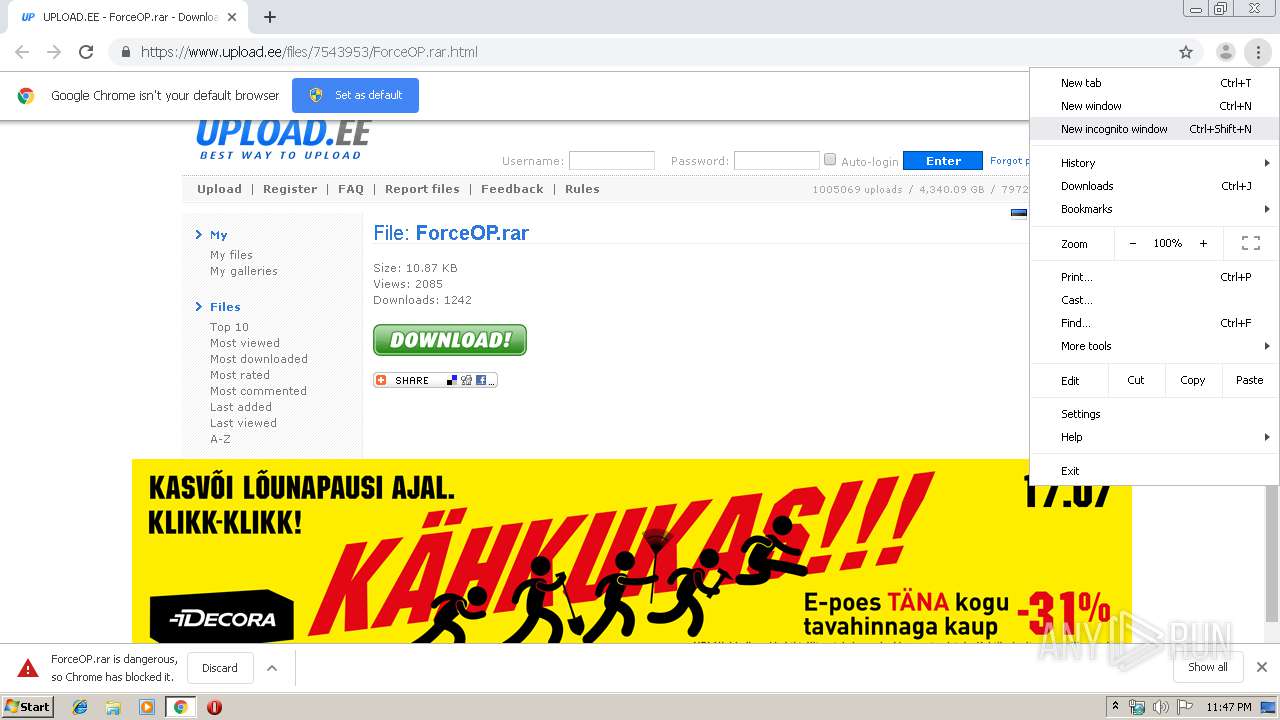
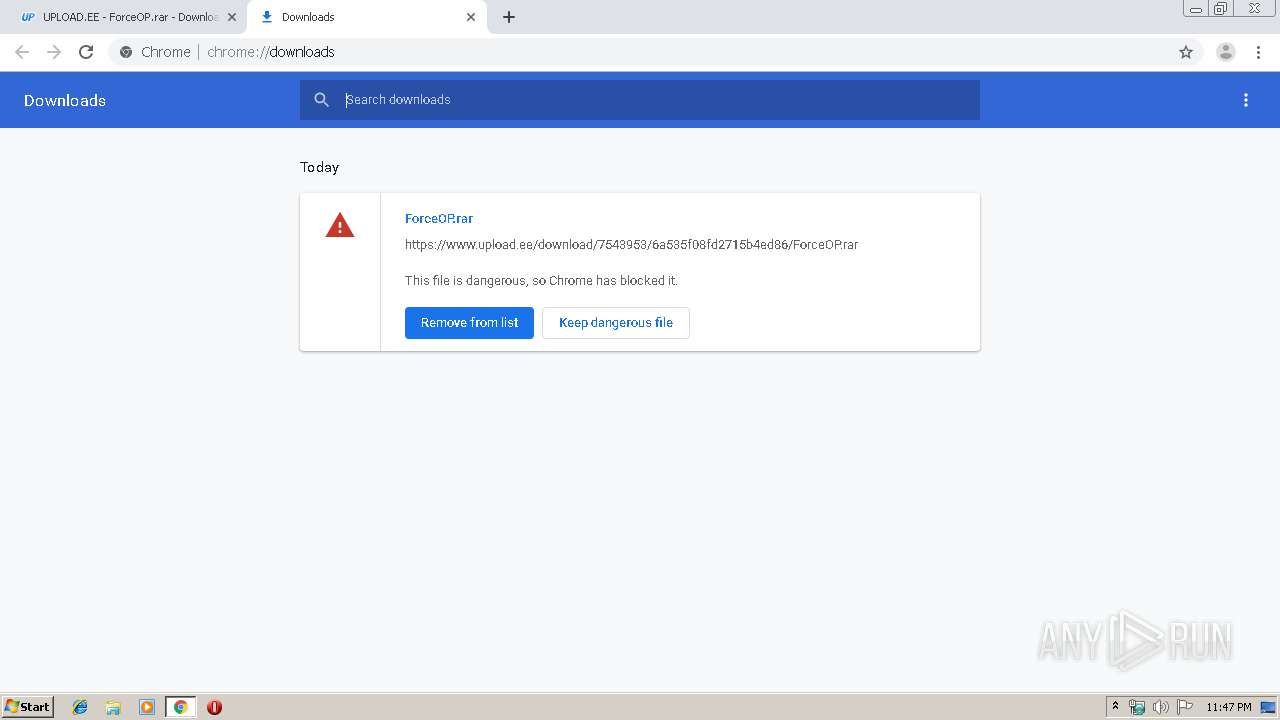
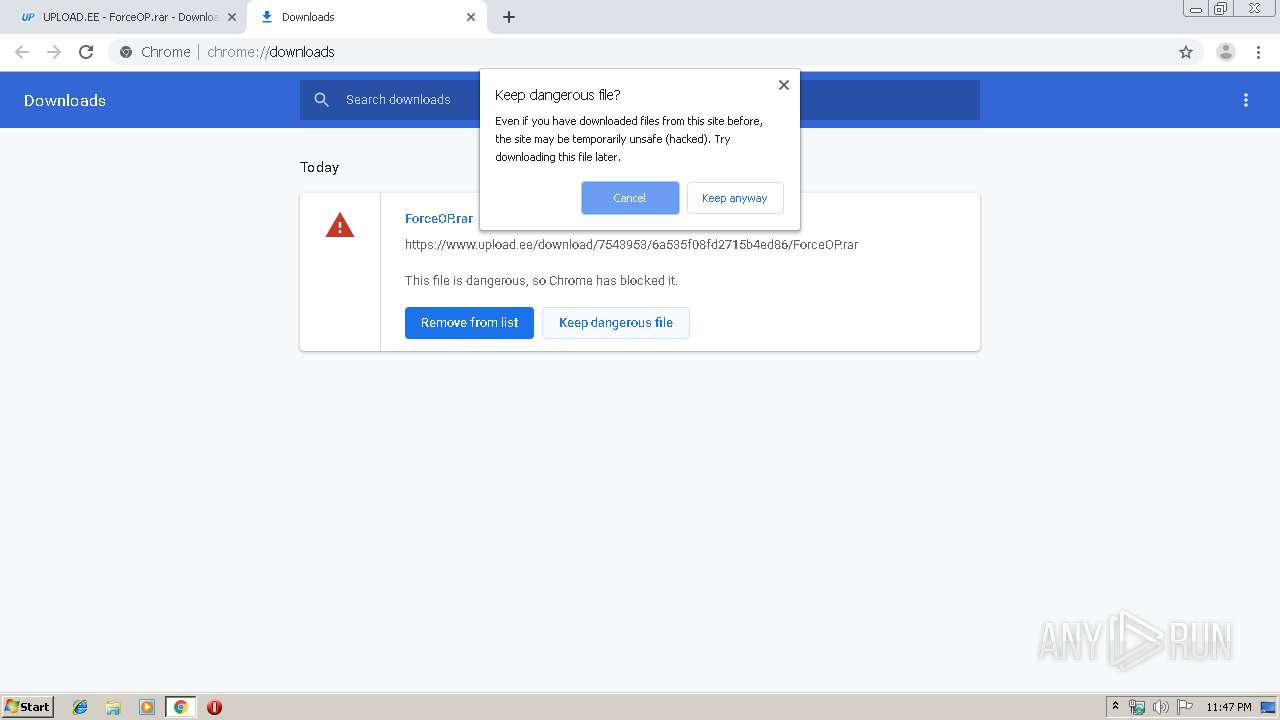
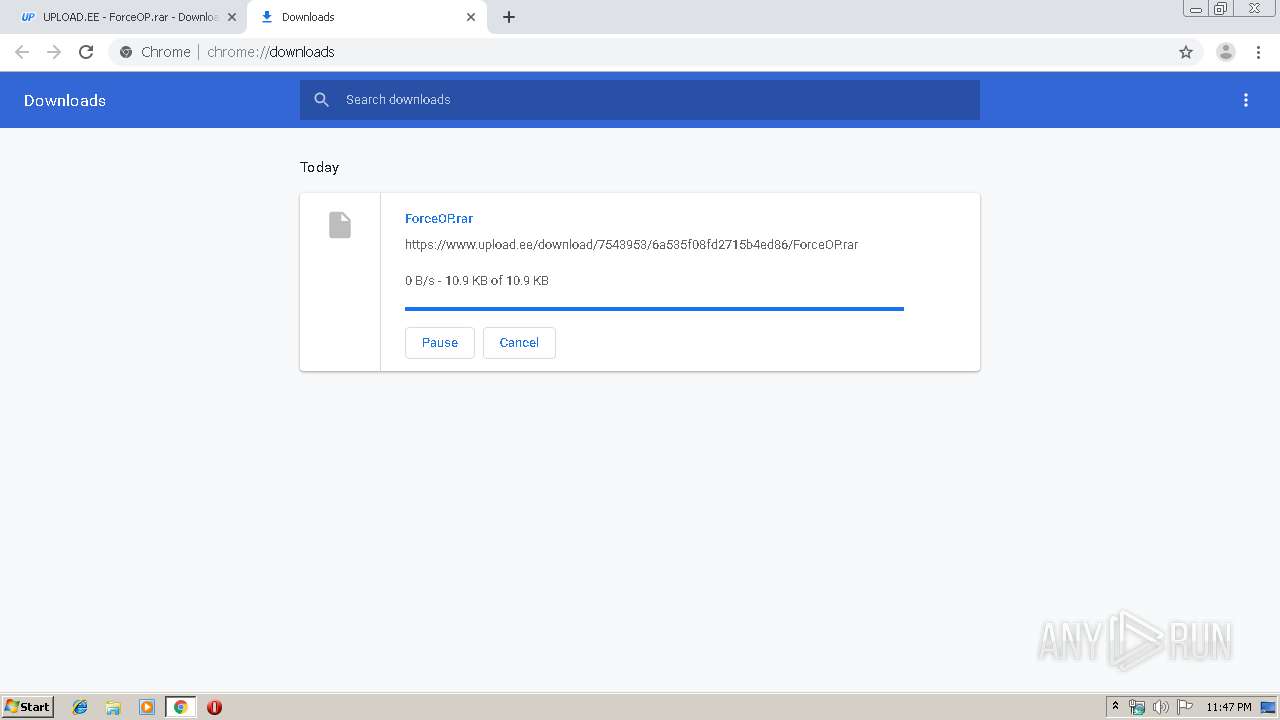
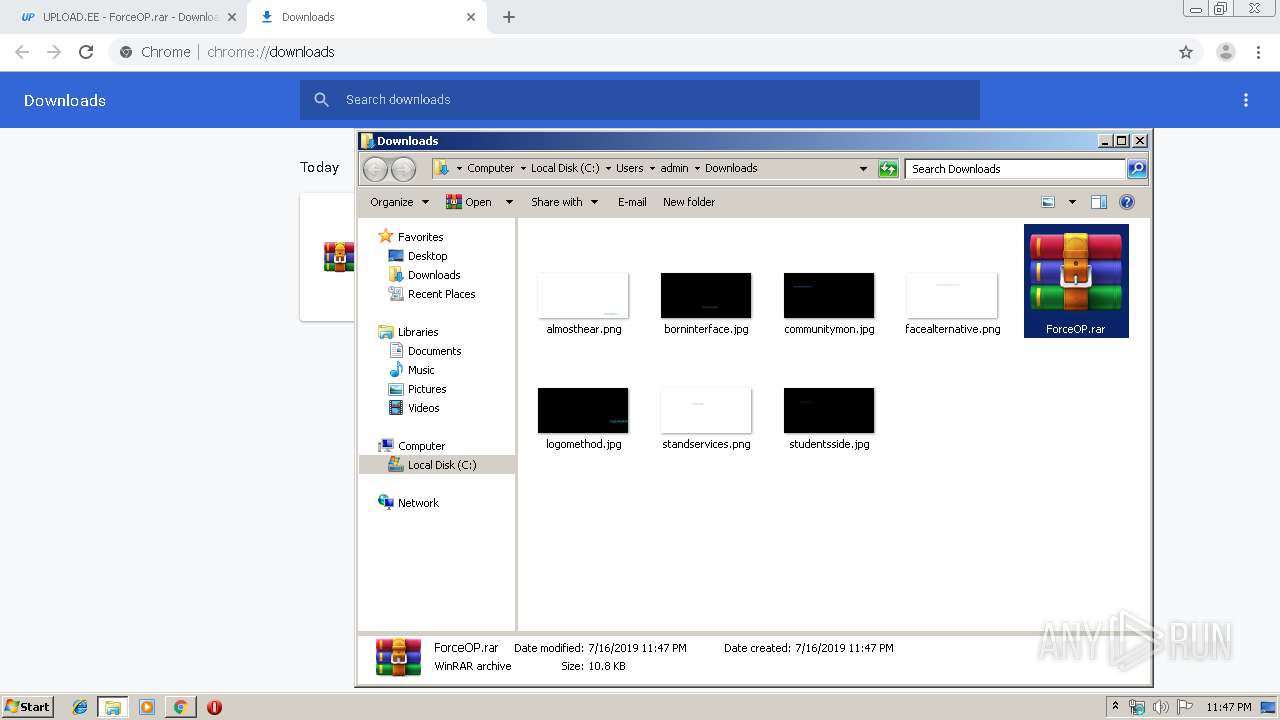
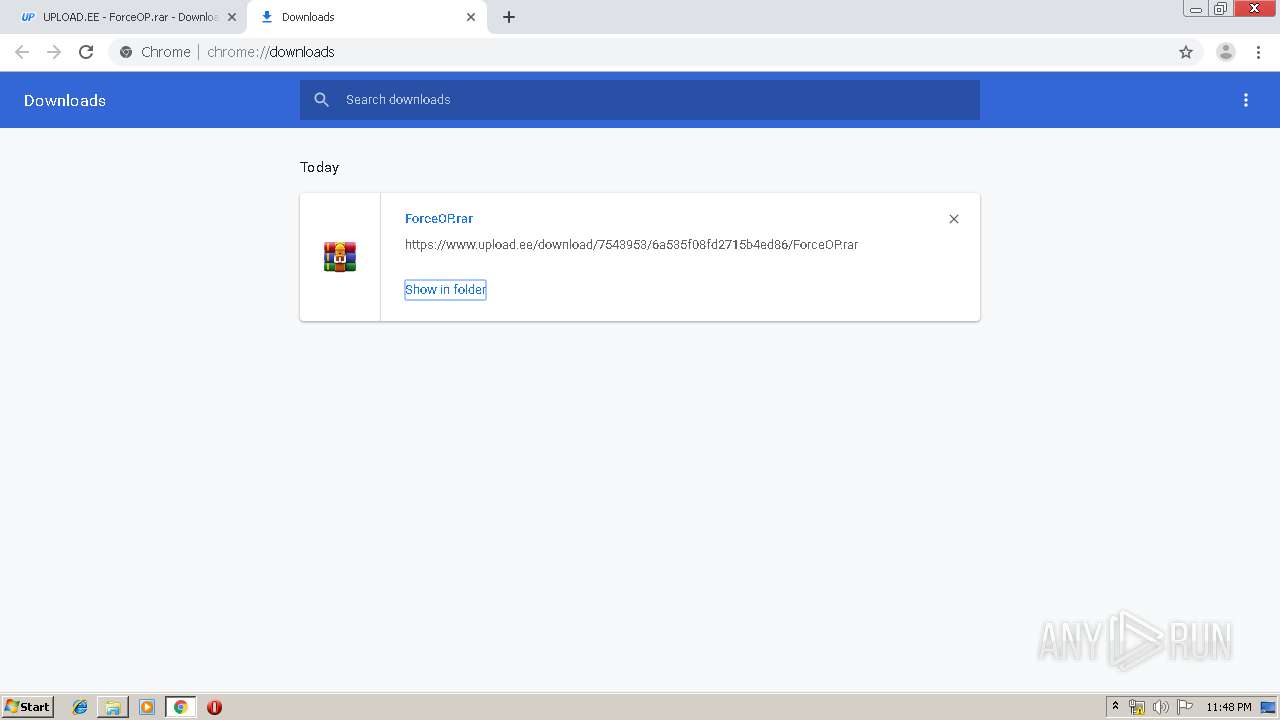
| URL: | https://www.upload.ee/files/7543953/ForceOP.rar.html |
| Full analysis: | https://app.any.run/tasks/ebf0df93-f08e-4d87-ae6e-39e83e206a5f |
| Verdict: | Malicious activity |
| Analysis date: | July 16, 2019, 22:46:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | B33DB44B5860AA3EB8E9BA9D616536DA |
| SHA1: | F5D93FD449DF642EBCD64BC870FBA2253AD98A45 |
| SHA256: | BBE953919E68019EBC95927C6C808EEEEA8B06C9EF22F0BC406980204C76D4FF |
| SSDEEP: | 3:N8DSLr7MJmSEQHN4sn:2OLr0KQtHn |
MALICIOUS
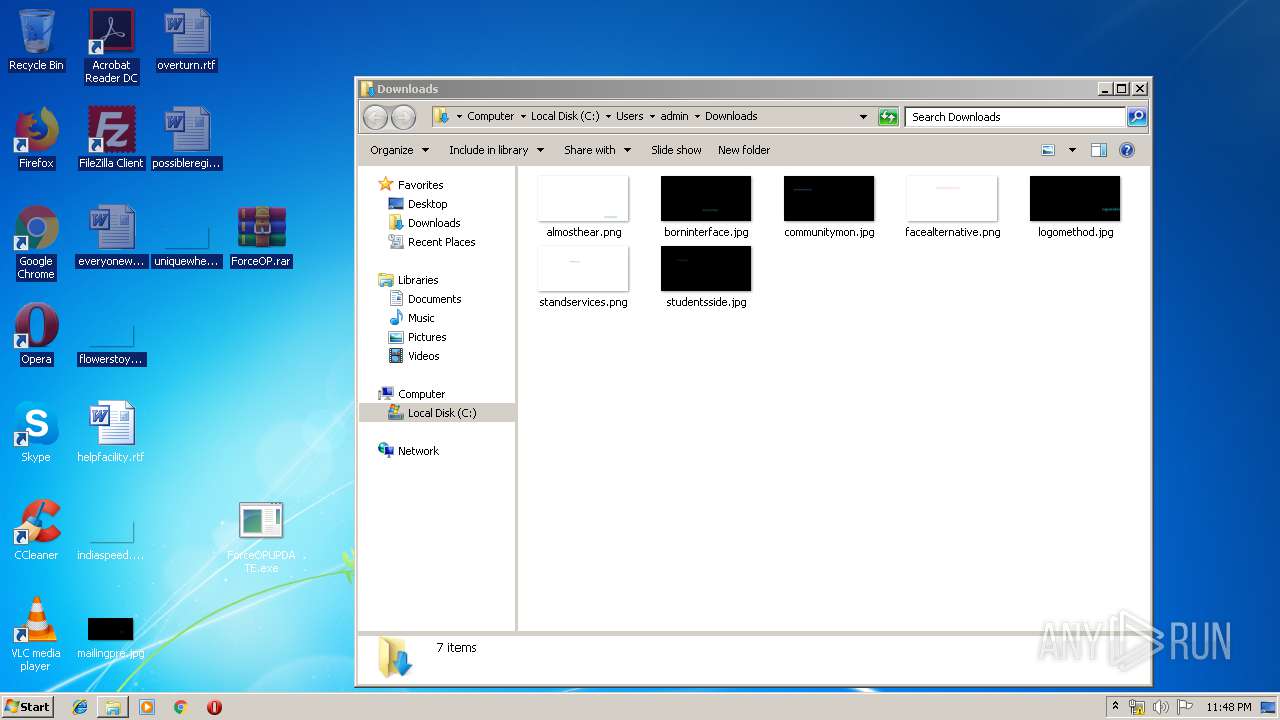
Application was dropped or rewritten from another process
- ForceOPUPDATE.exe (PID: 2748)
- ForceOPUPDATE.exe (PID: 3464)
- ForceOPUPDATE.exe (PID: 2532)
- ForceOPUPDATE.exe (PID: 3244)
- ForceOPUPDATE.exe (PID: 956)
- ForceOPUPDATE.exe (PID: 2968)
- ForceOPUPDATE.exe (PID: 2604)
- ForceOPUPDATE.exe (PID: 564)
- ForceOPUPDATE.exe (PID: 652)
- ForceOPUPDATE.exe (PID: 3088)
- ForceOPUPDATE.exe (PID: 2512)
- ForceOPUPDATE.exe (PID: 2408)
- ForceOPUPDATE.exe (PID: 3548)
- ForceOPUPDATE.exe (PID: 2220)
- ForceOPUPDATE.exe (PID: 4012)
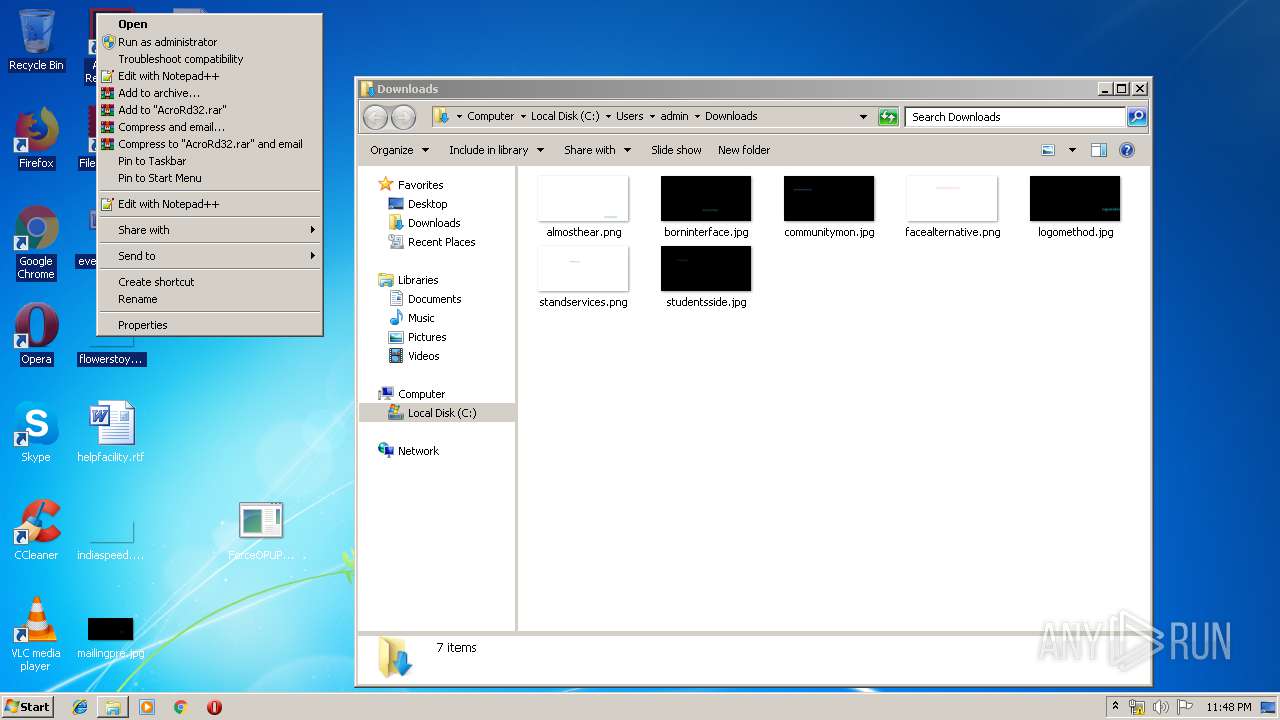
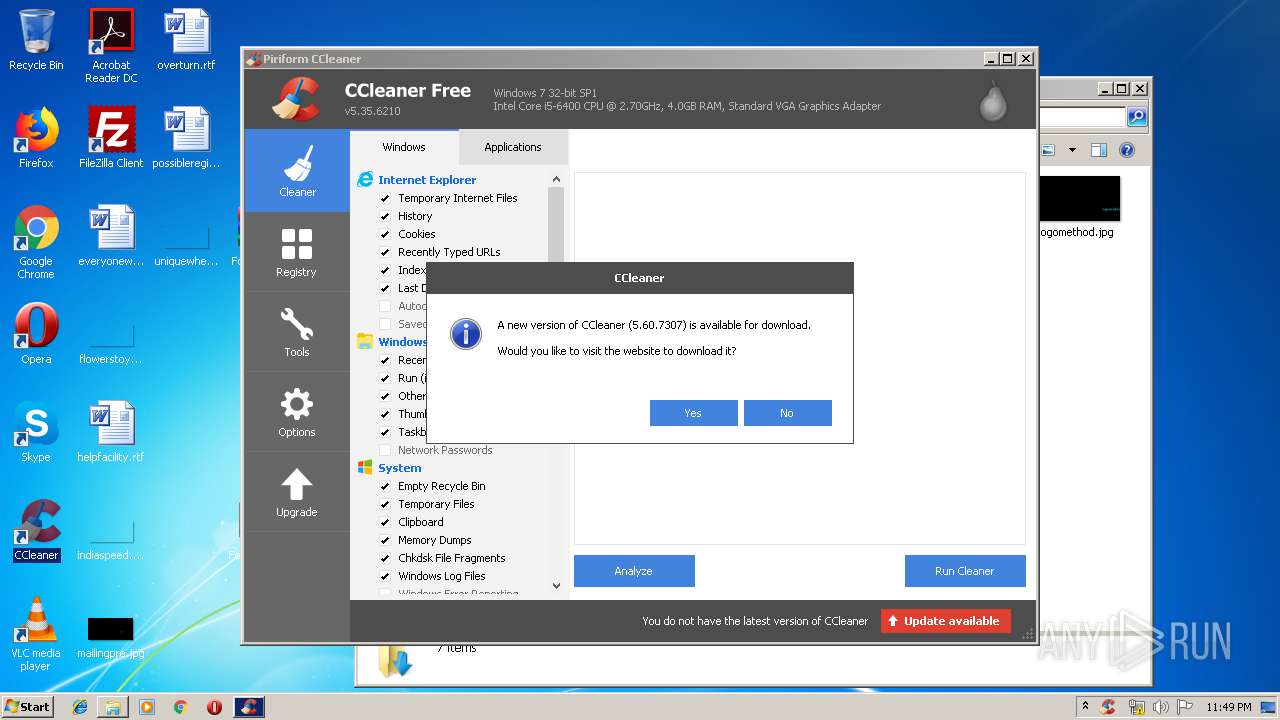
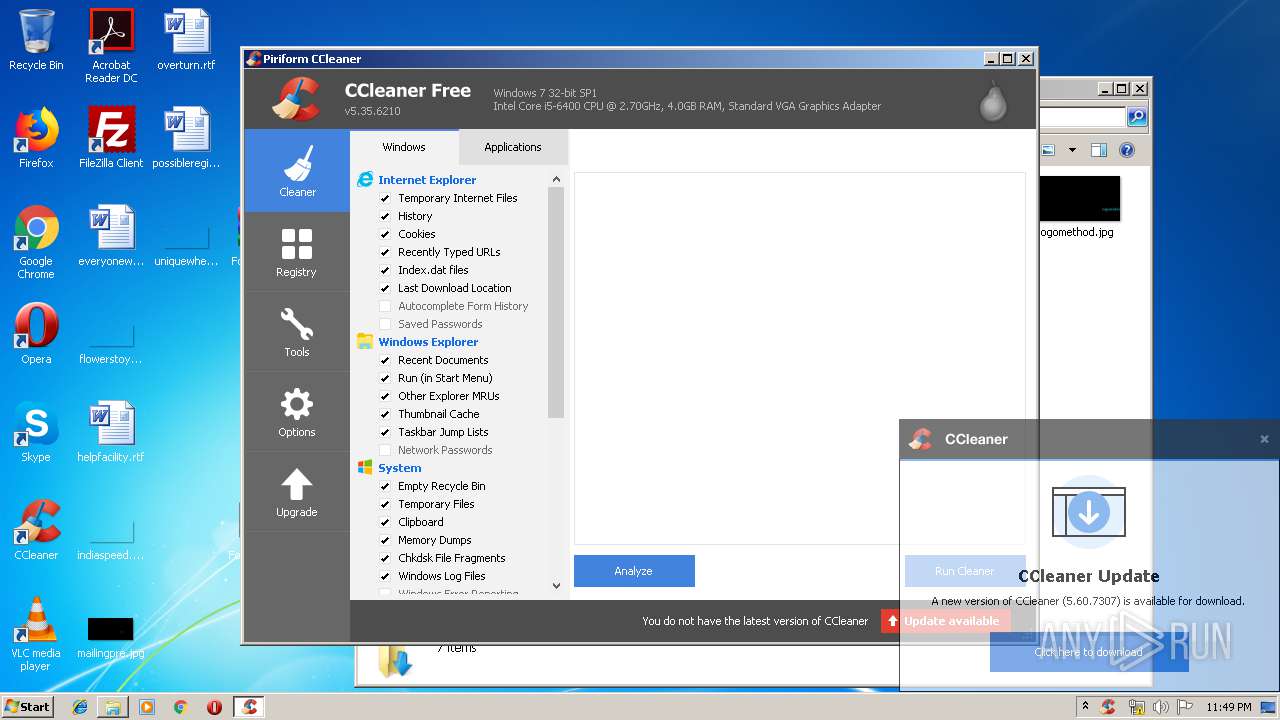
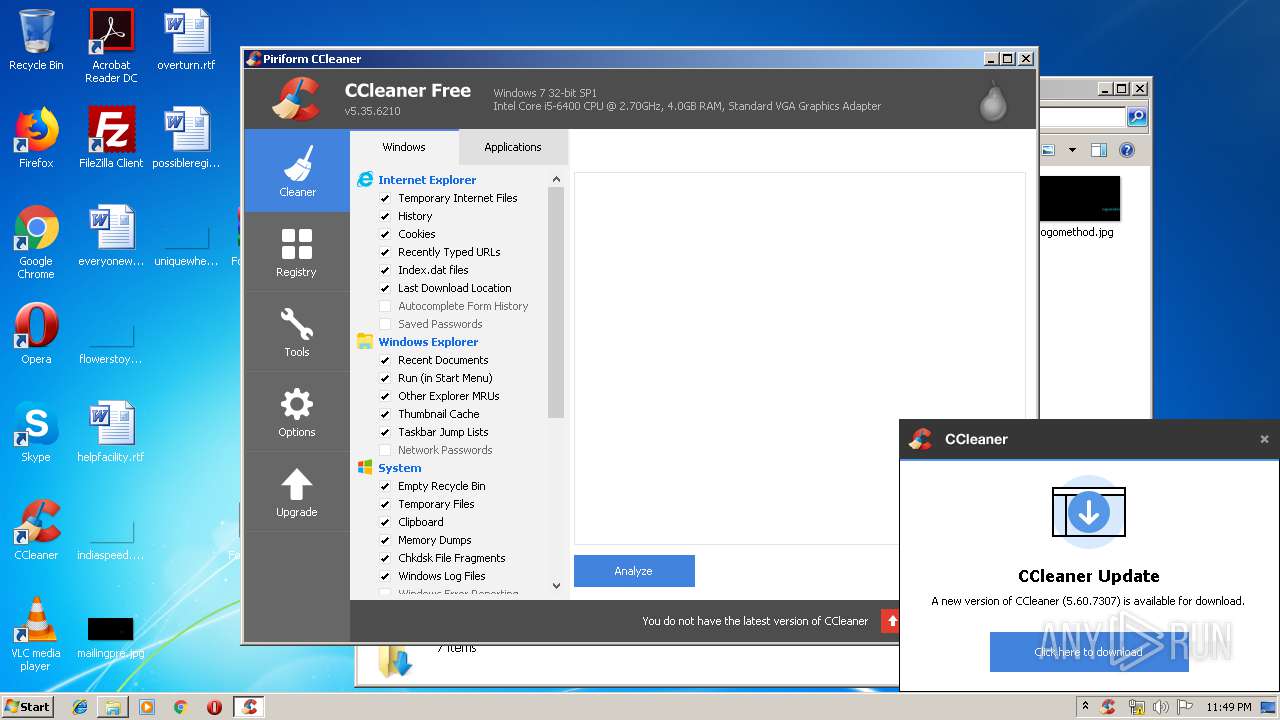
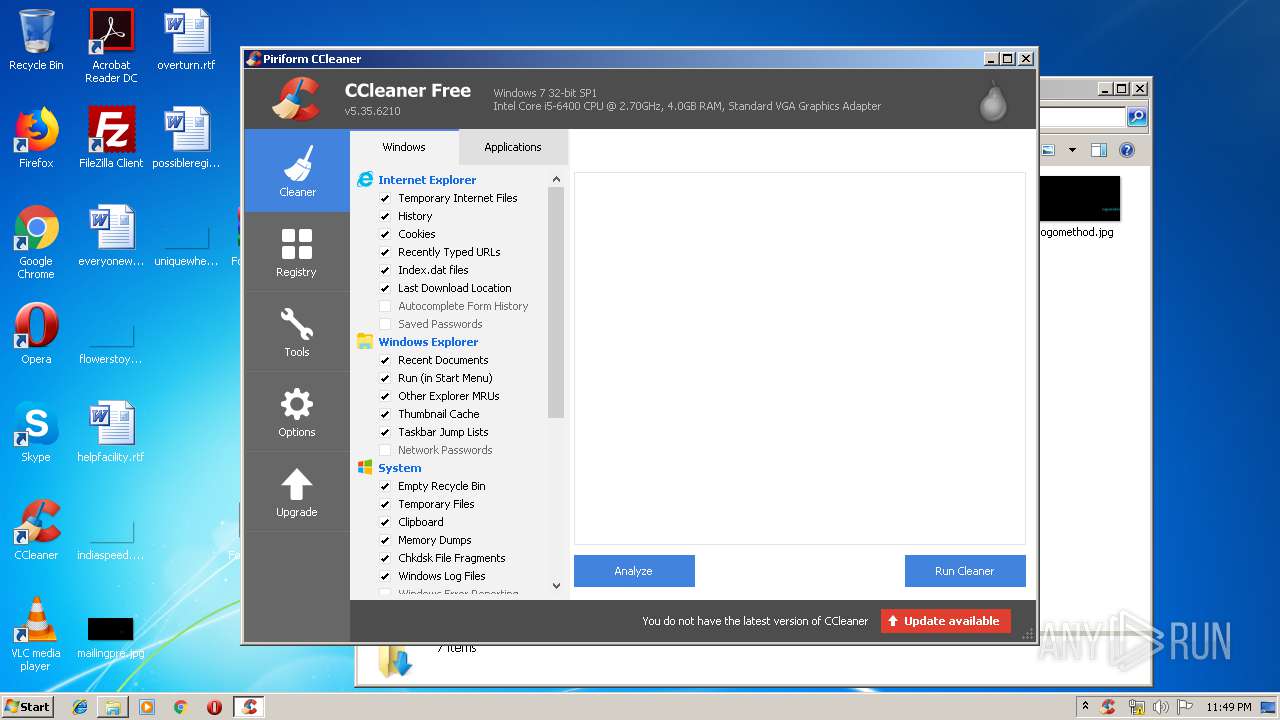
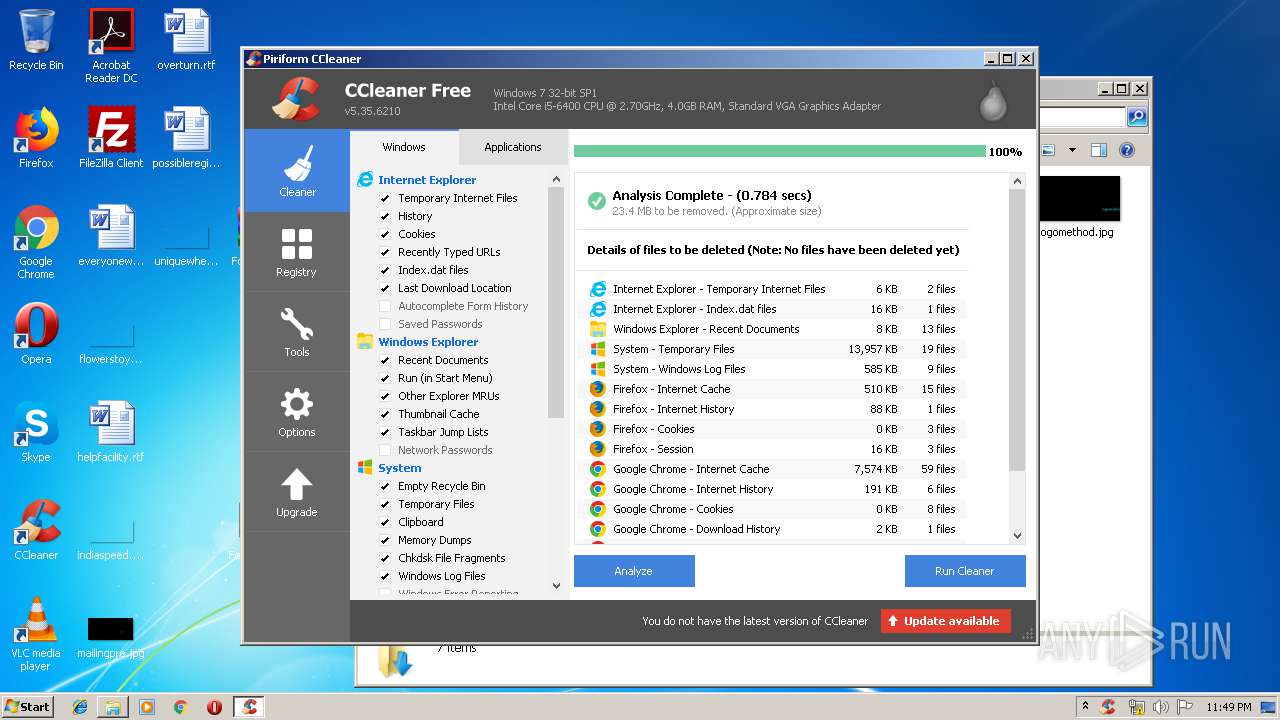
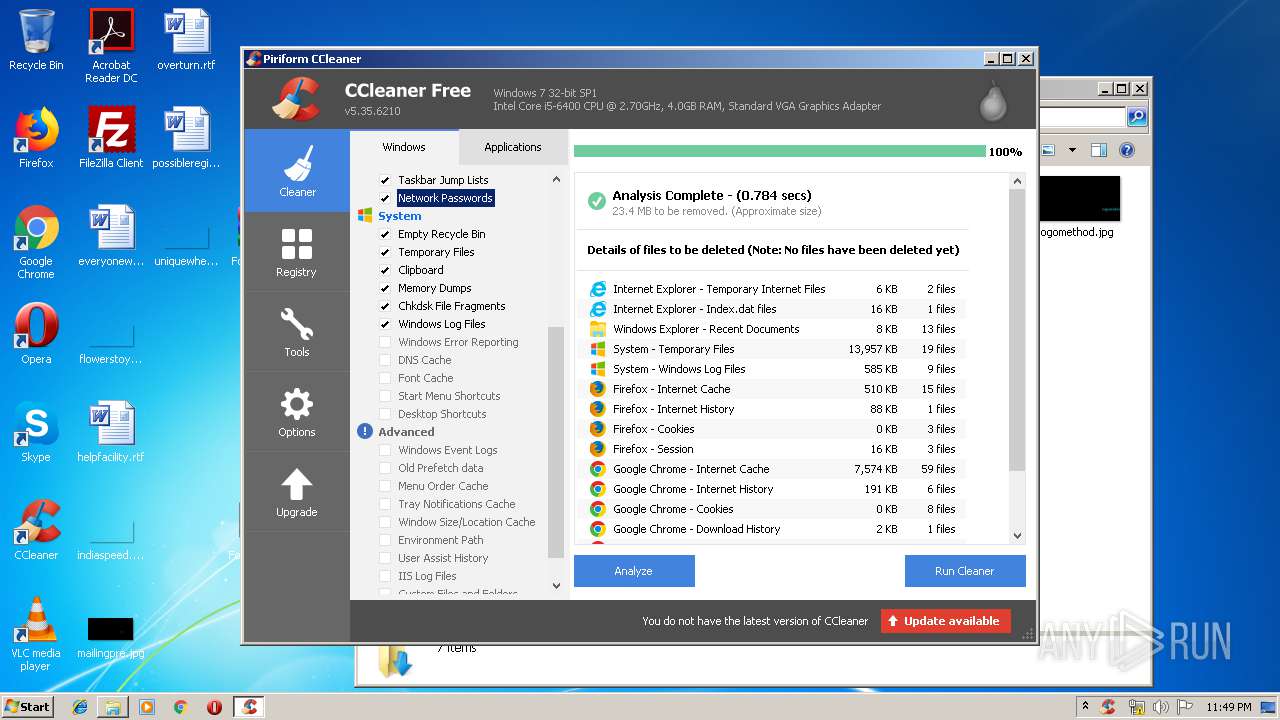
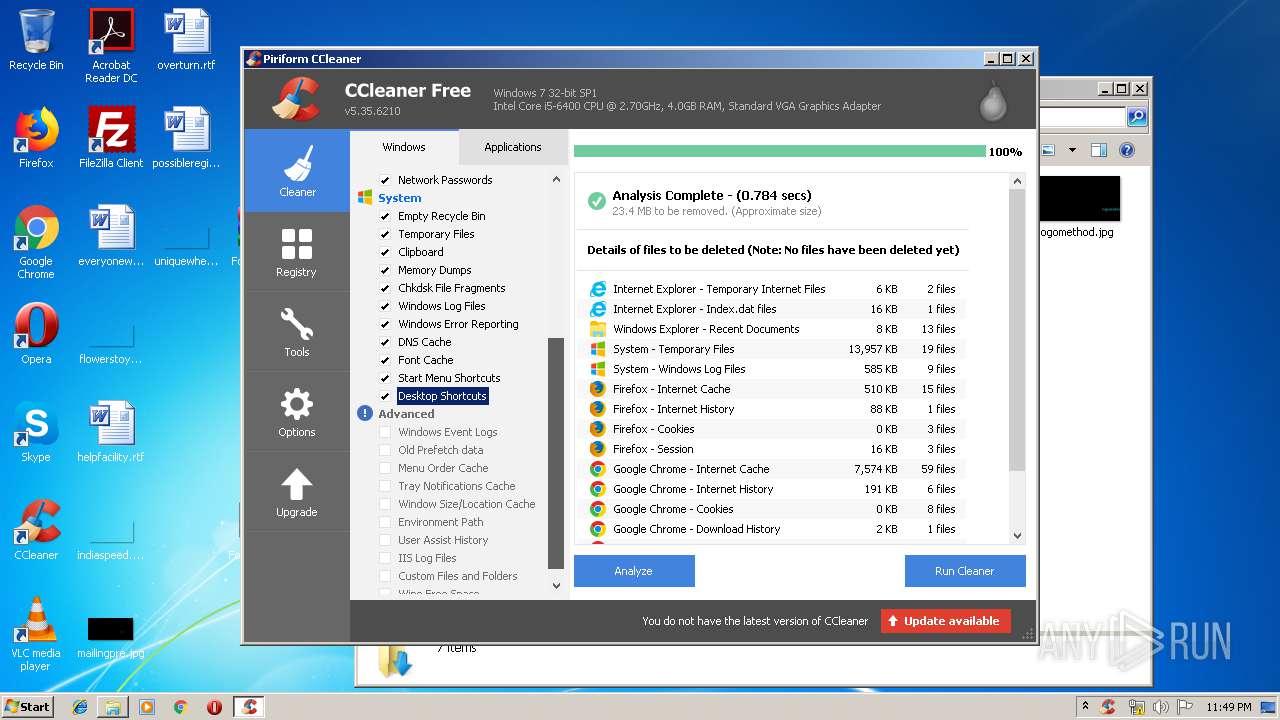
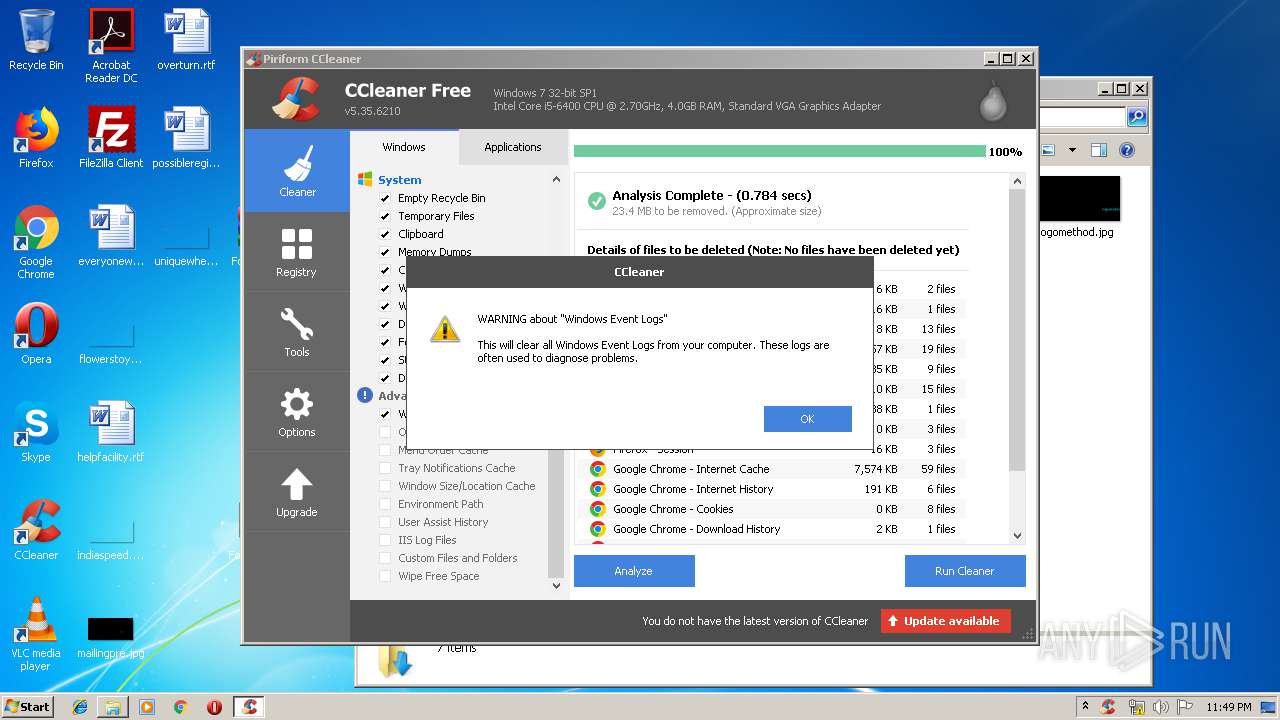
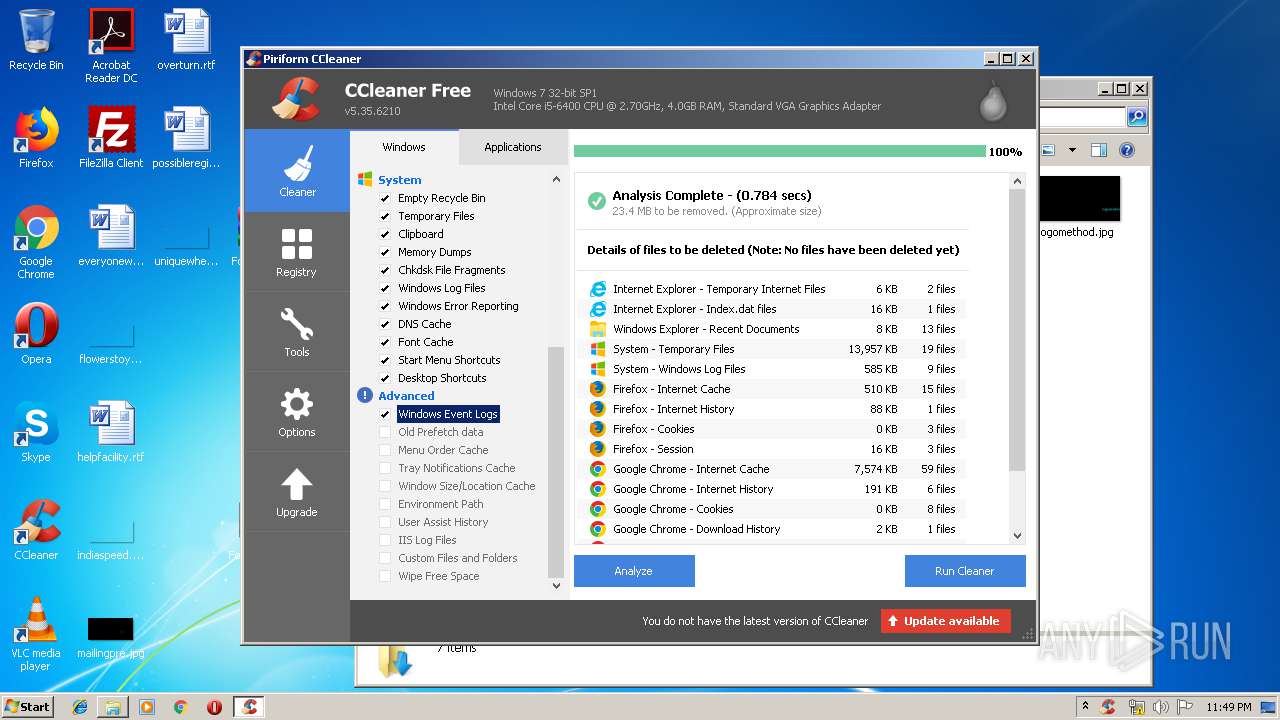
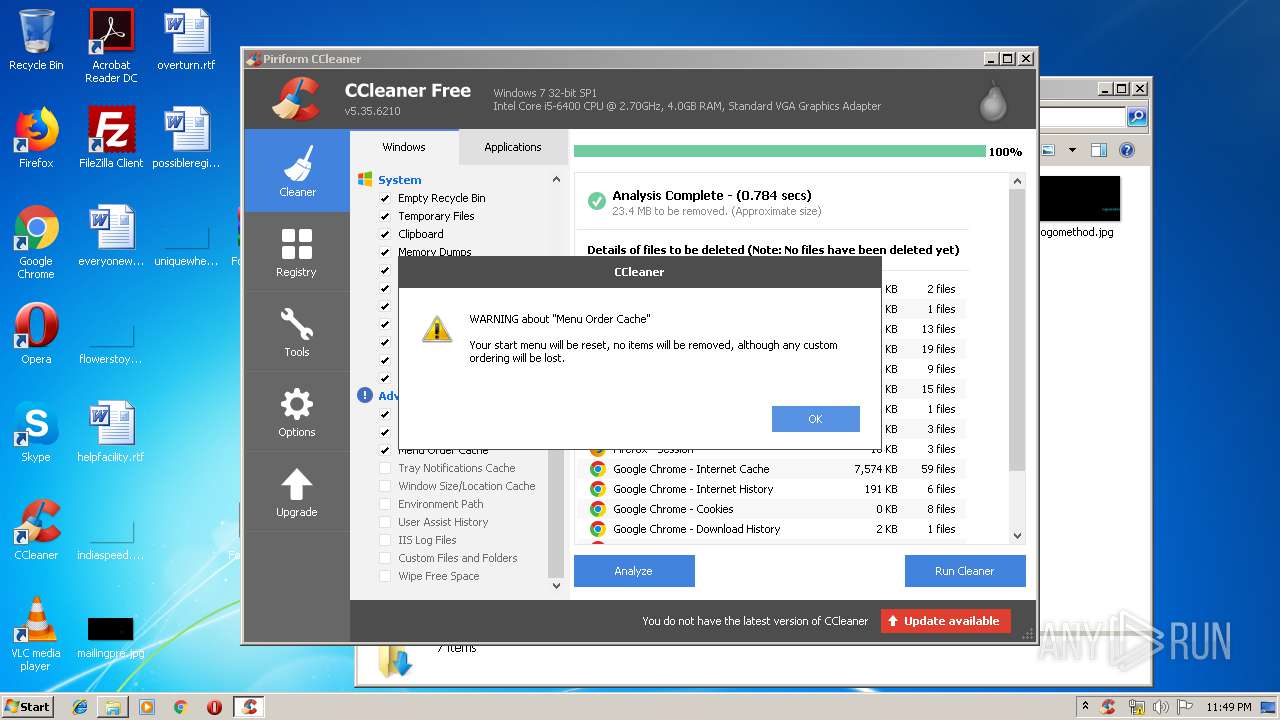
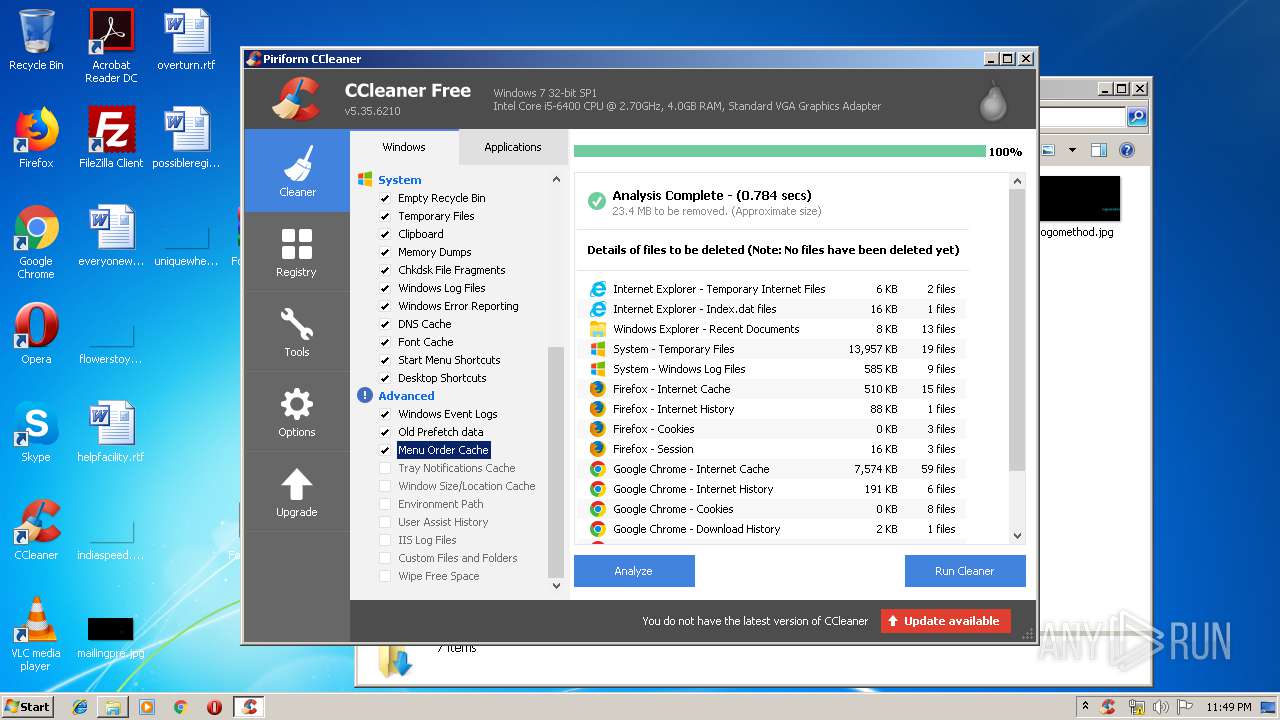
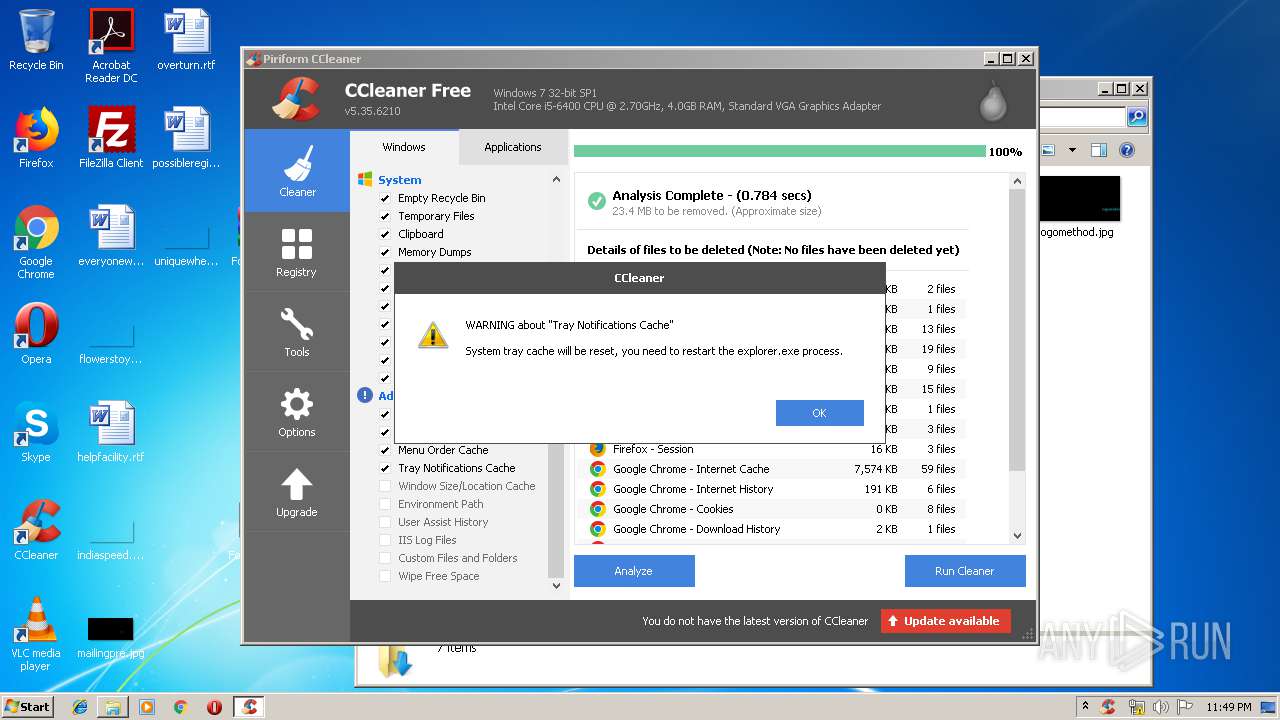
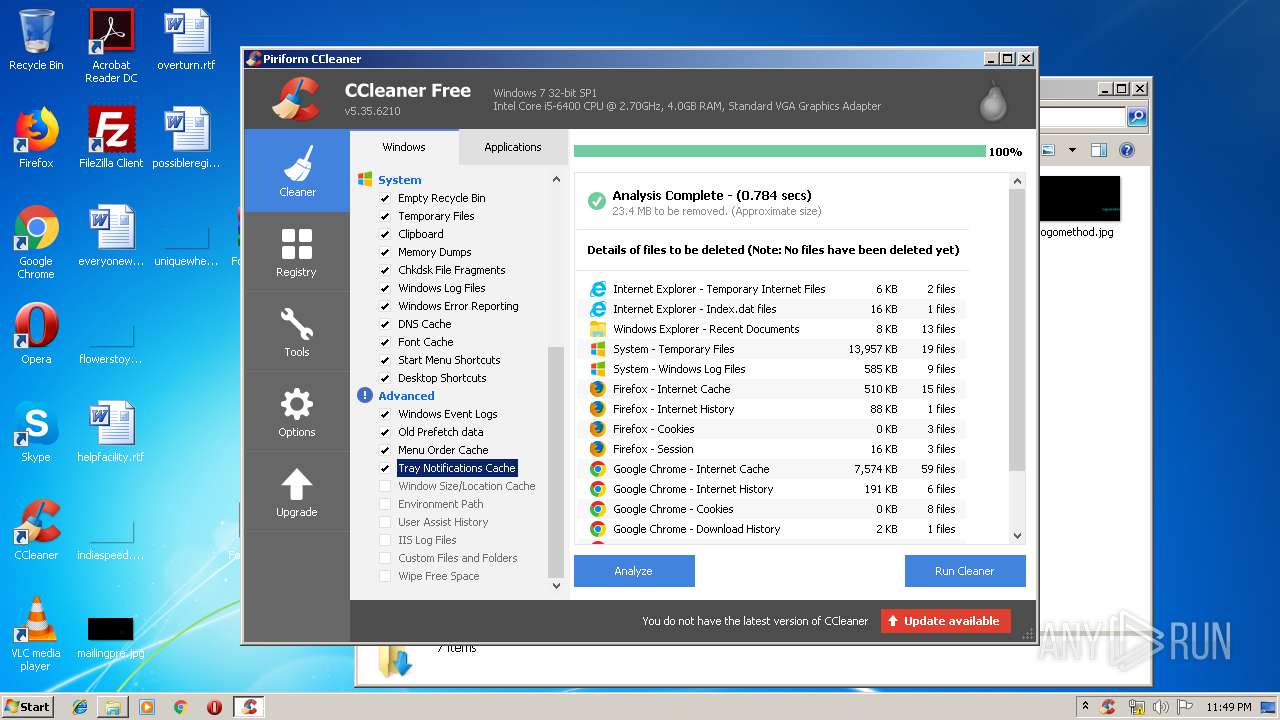
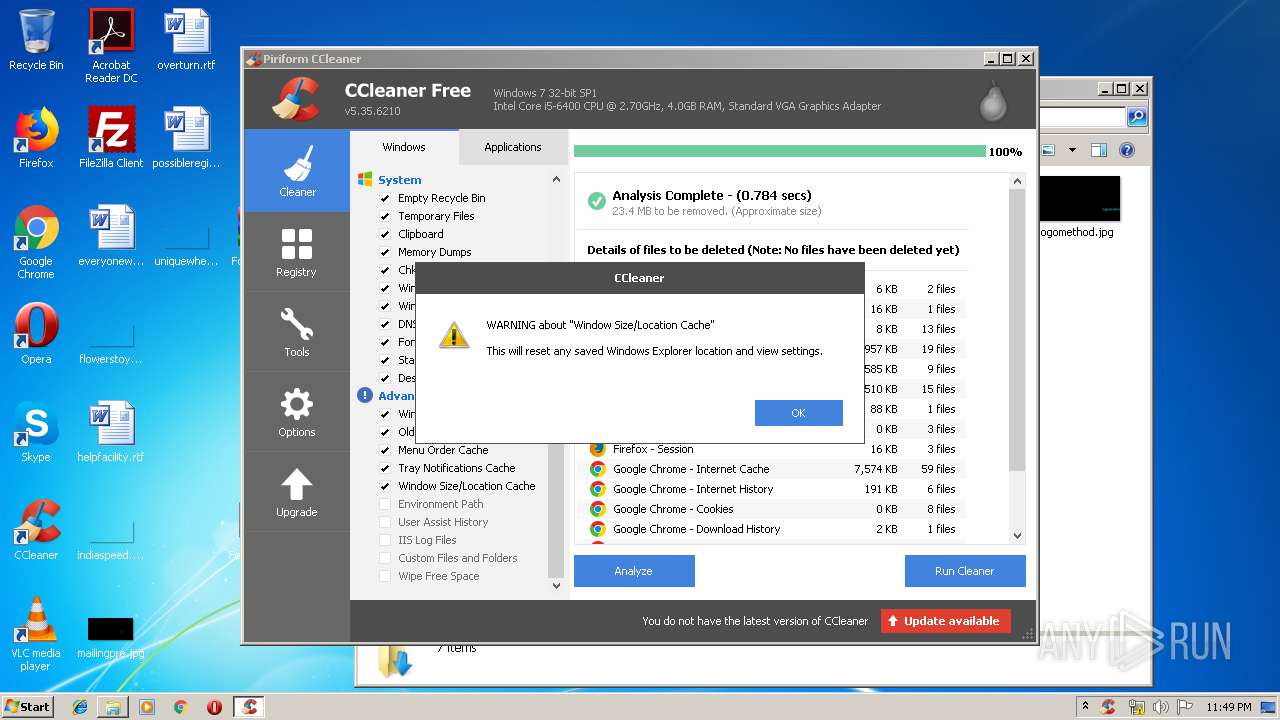
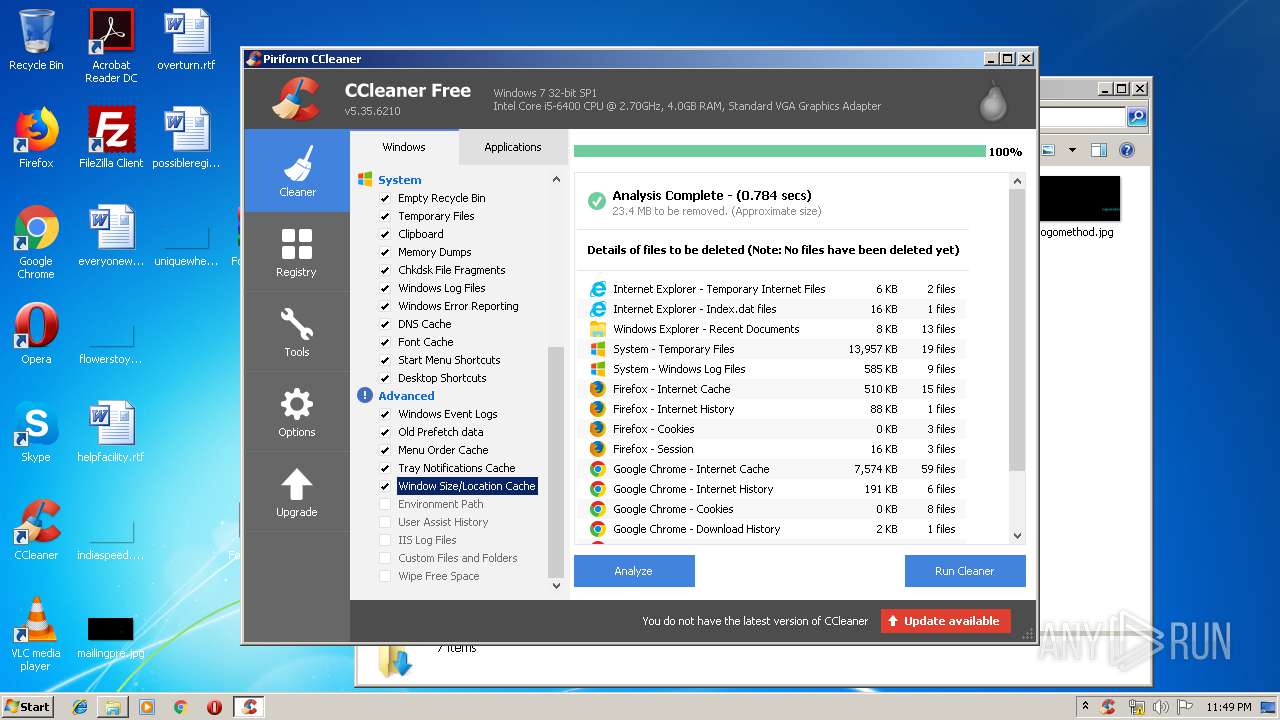
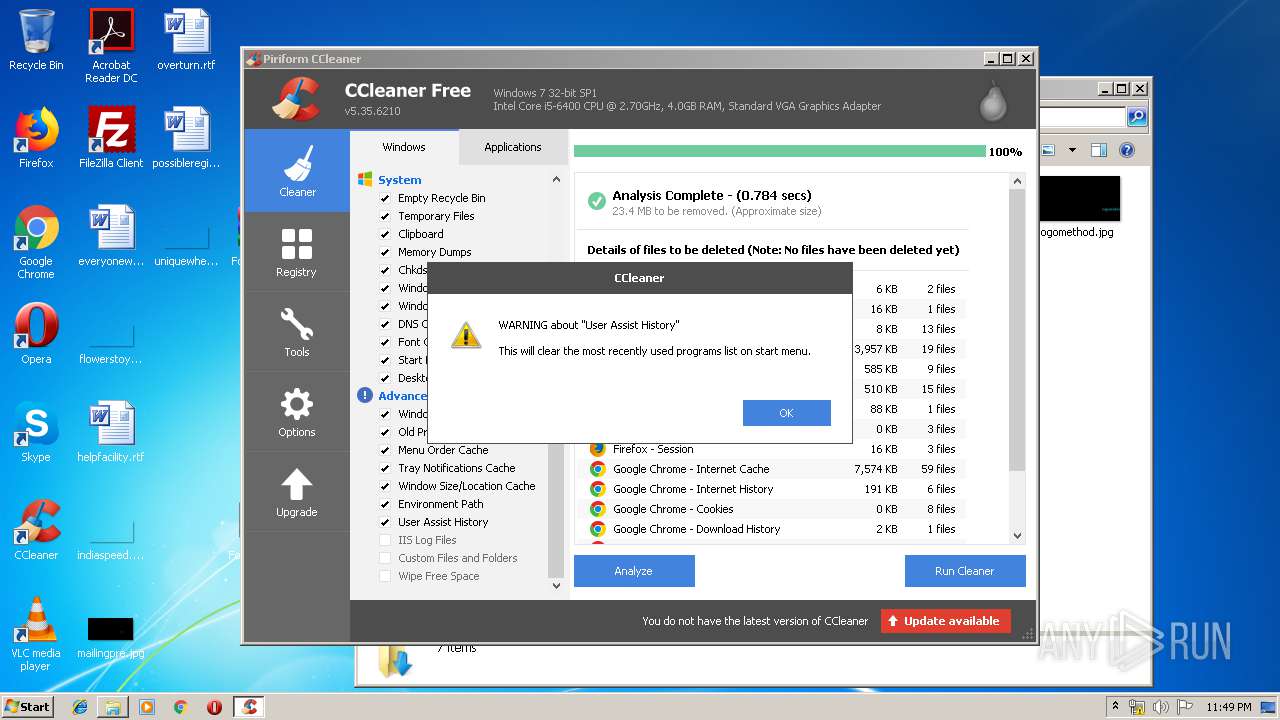
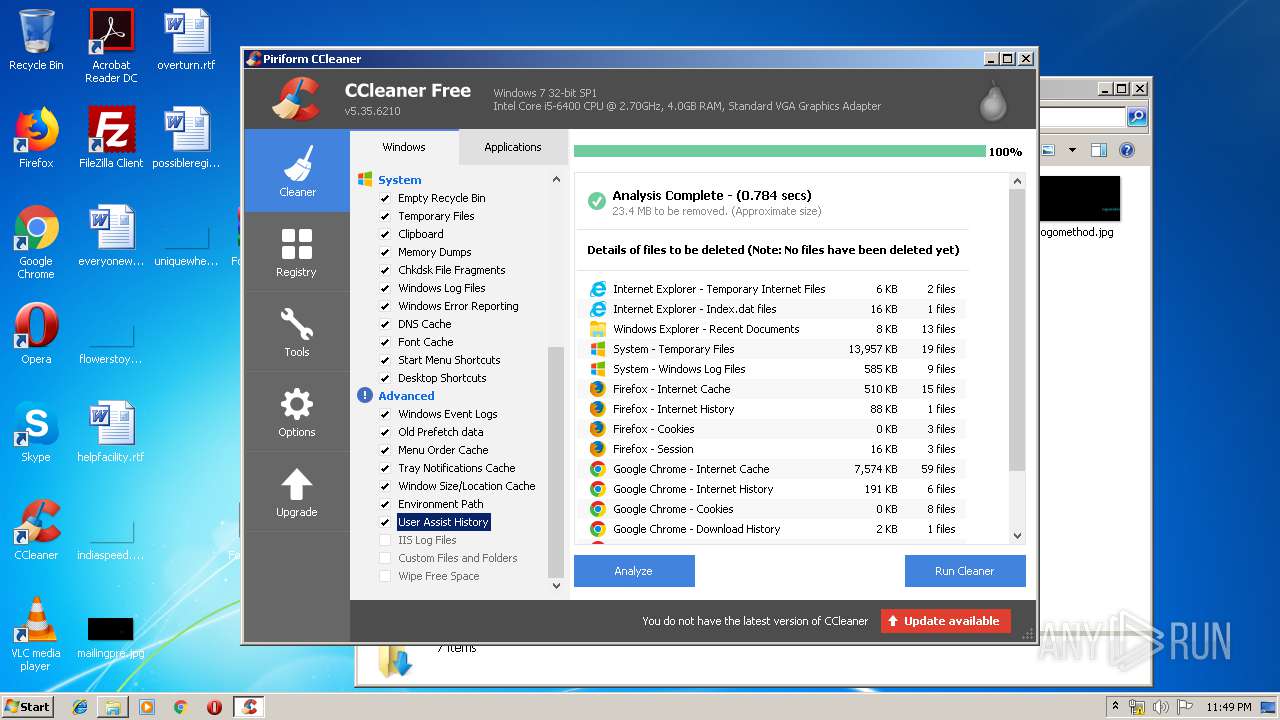
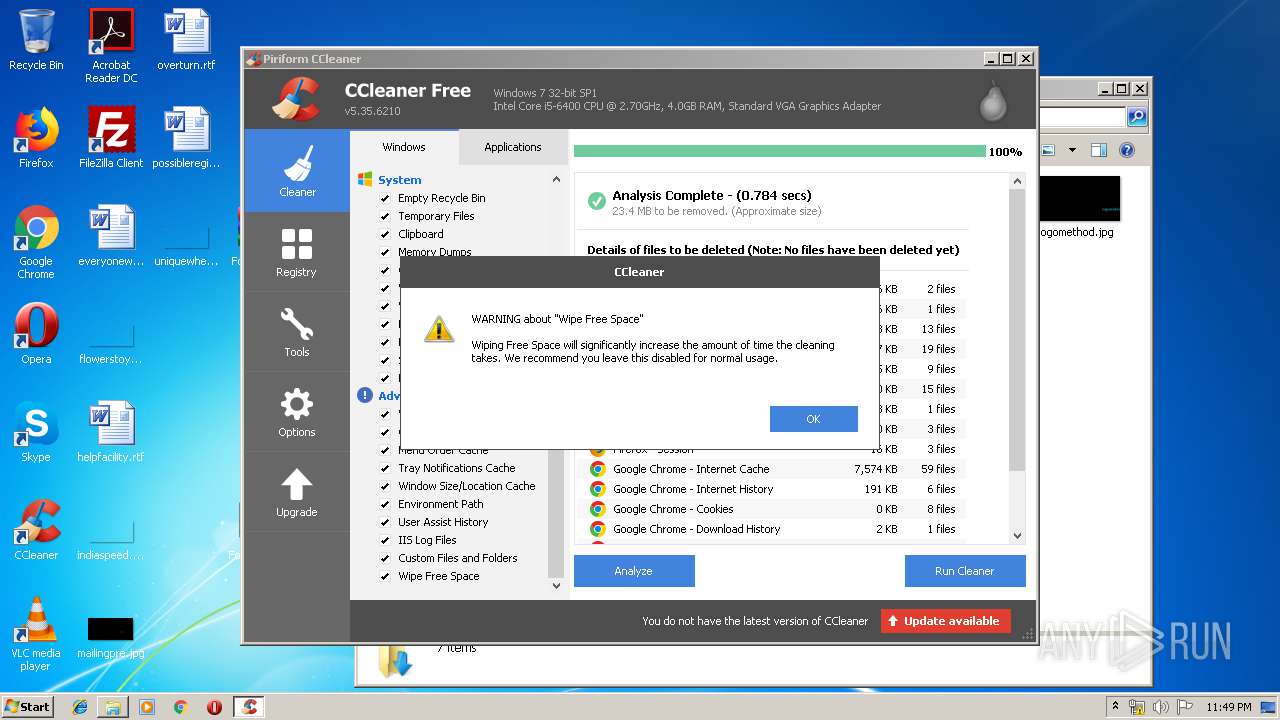
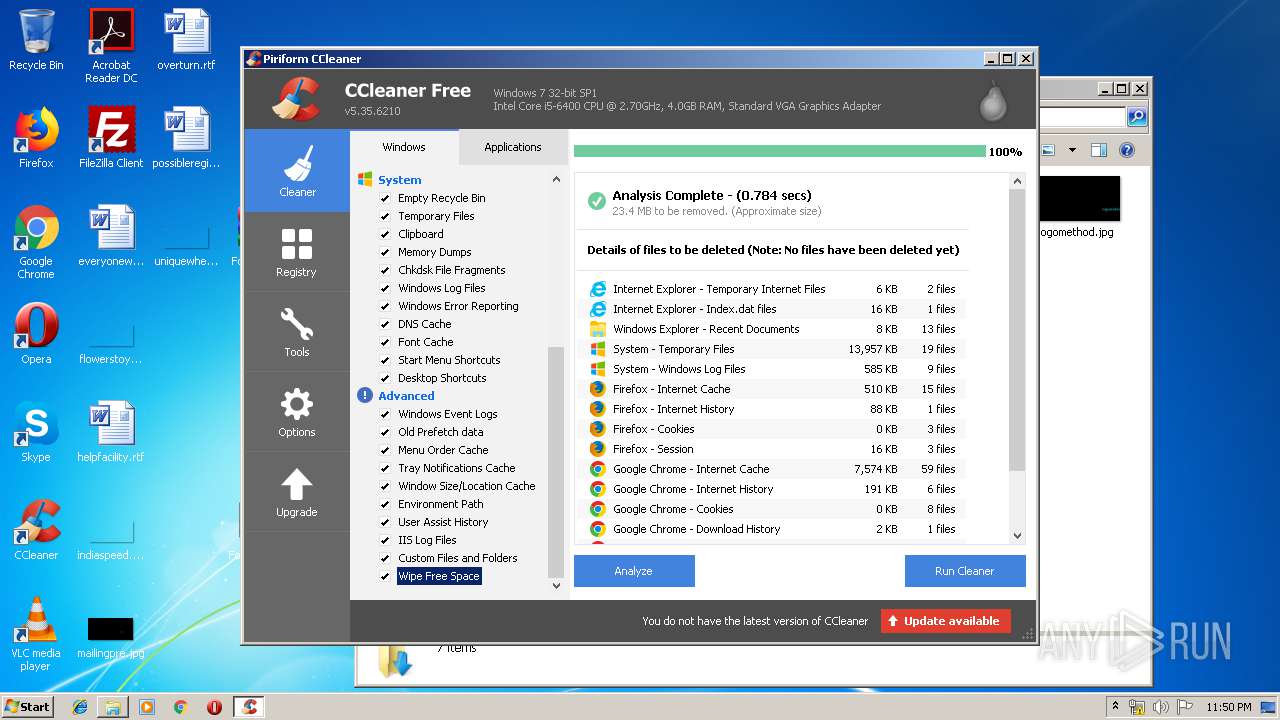
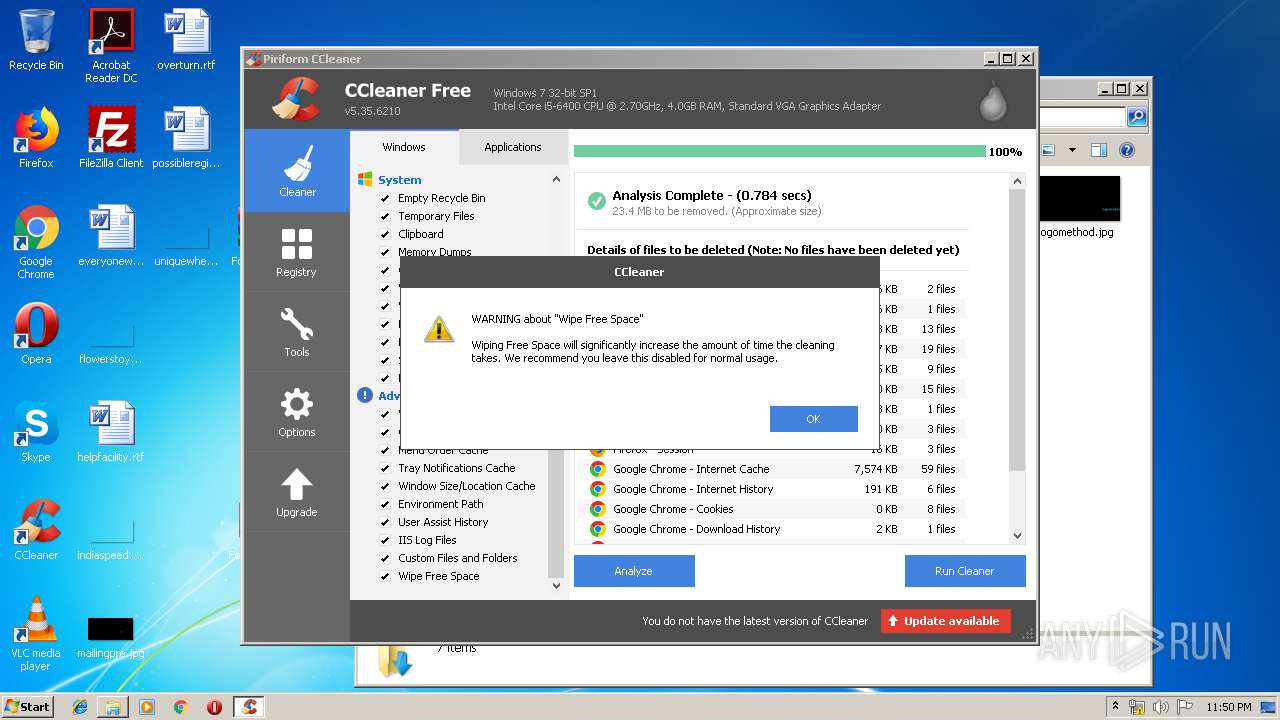
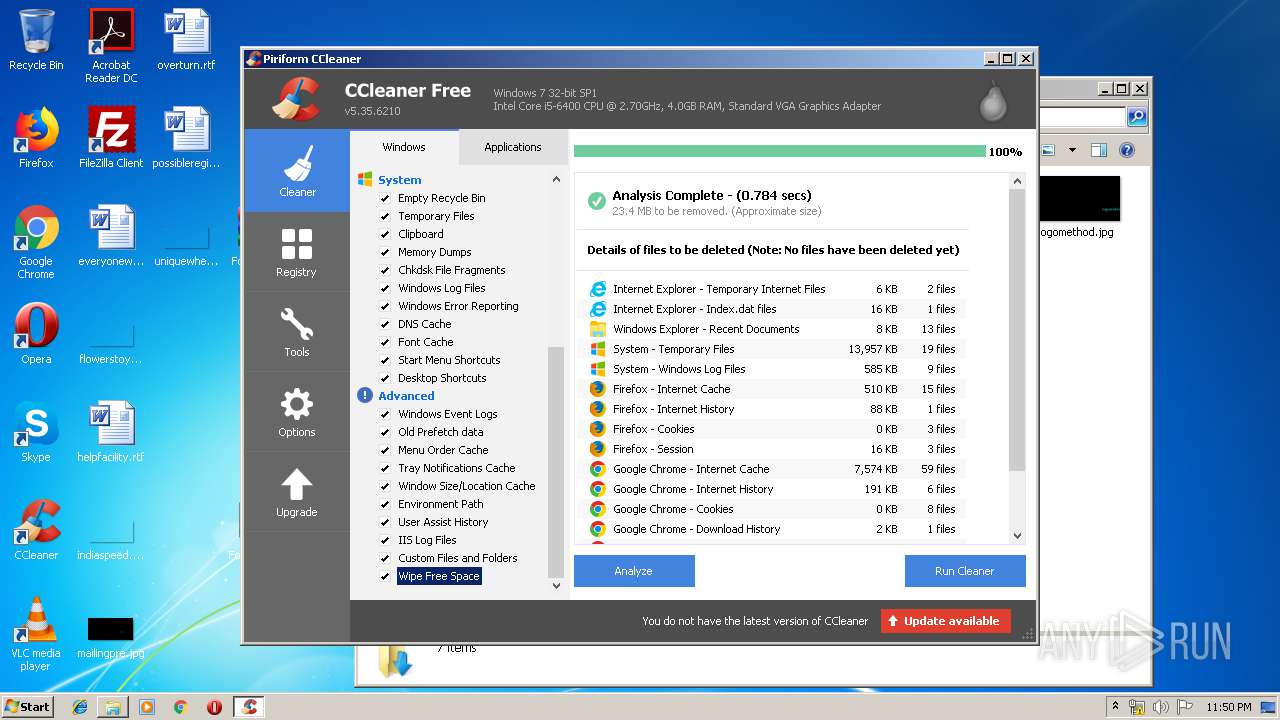
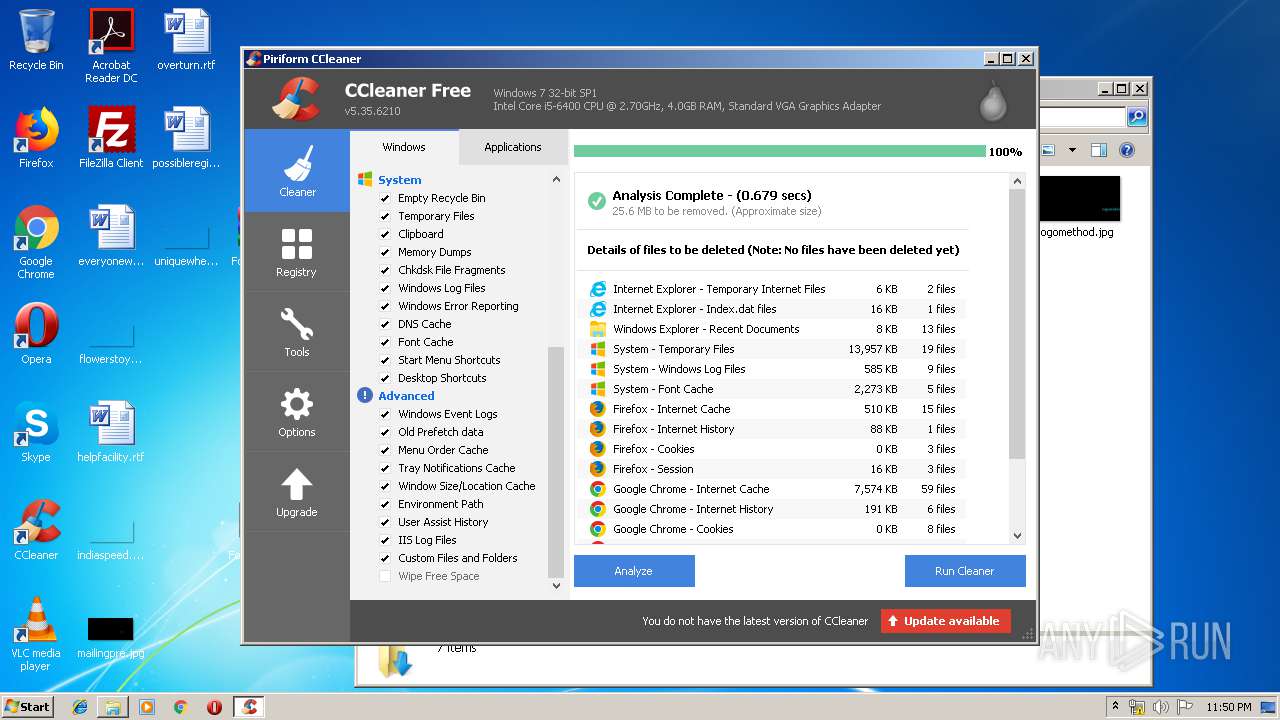
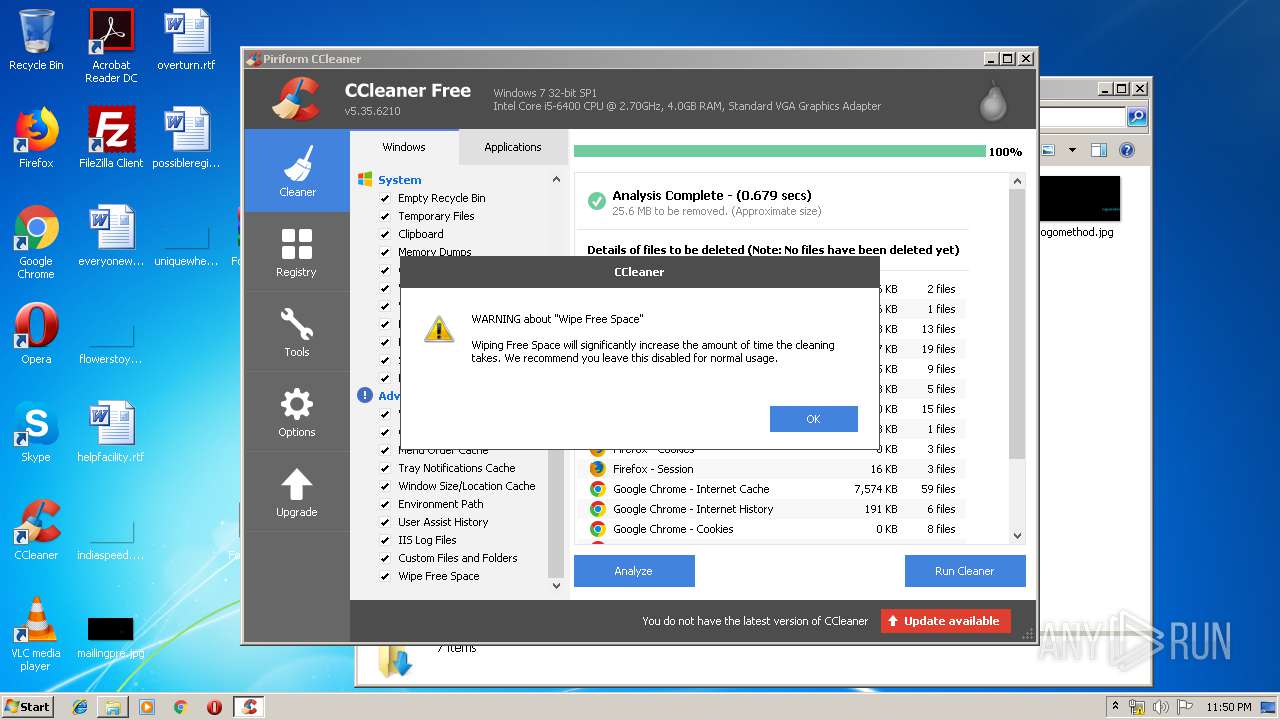
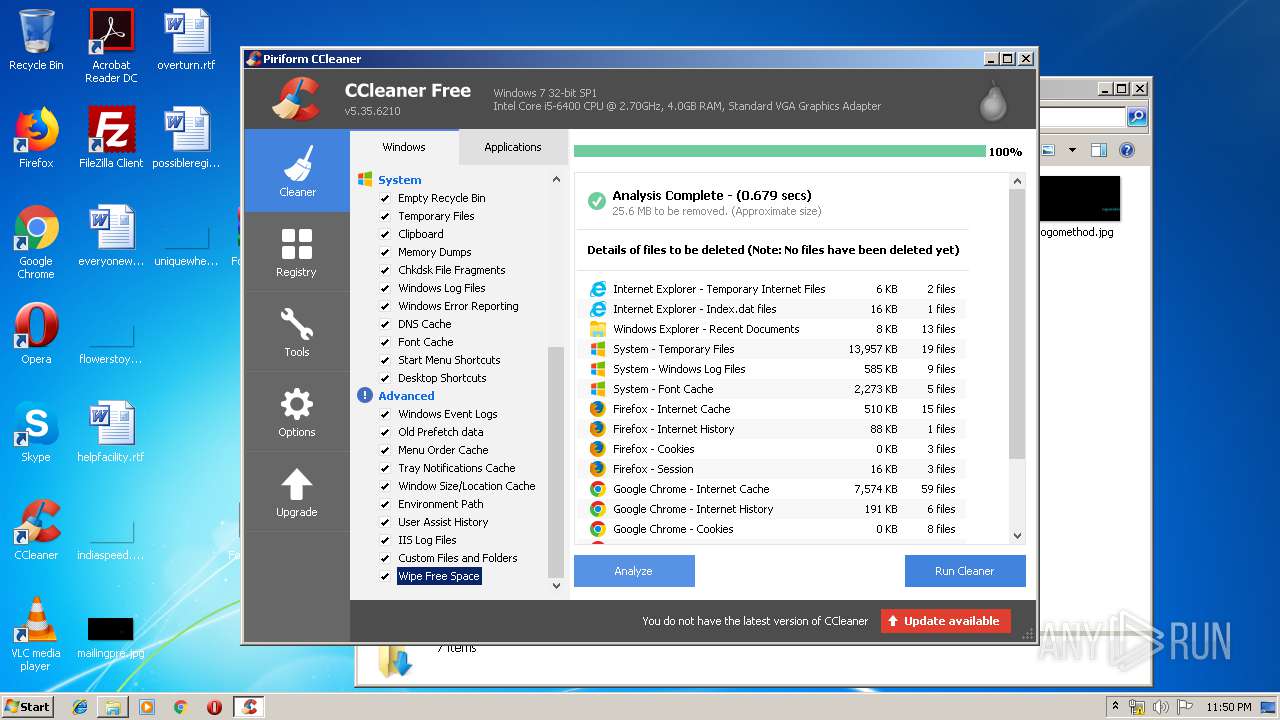
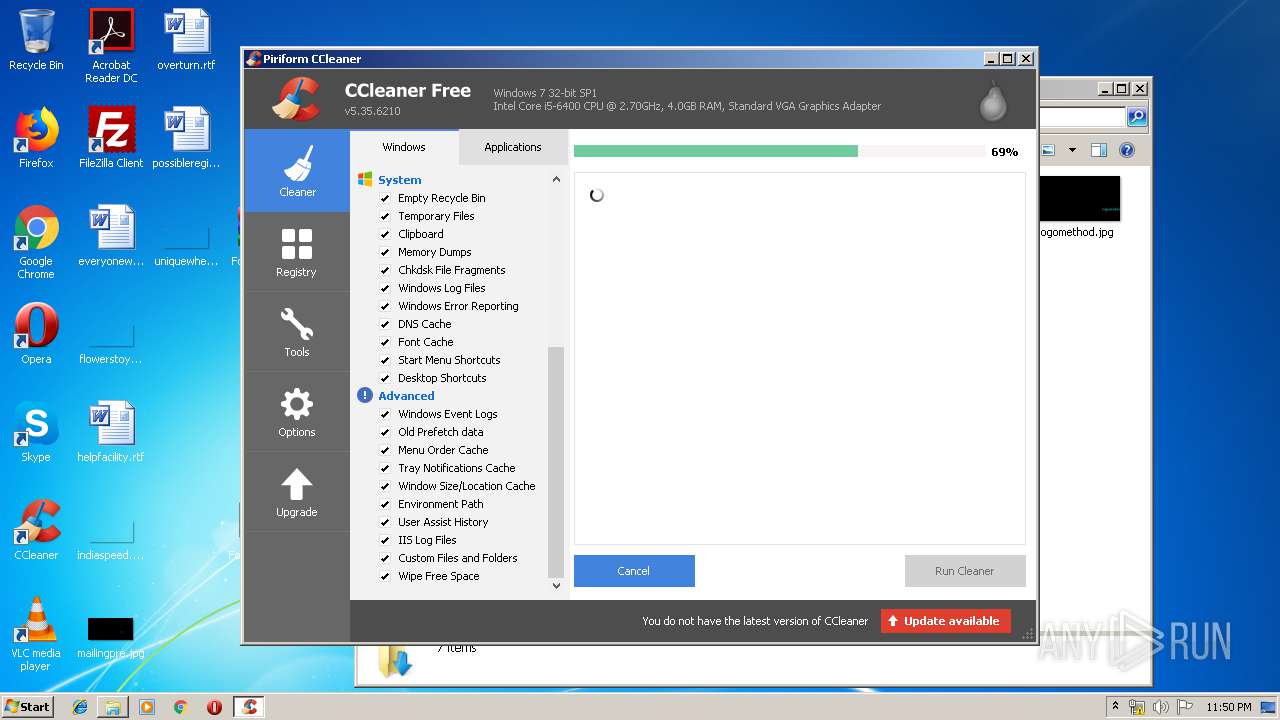
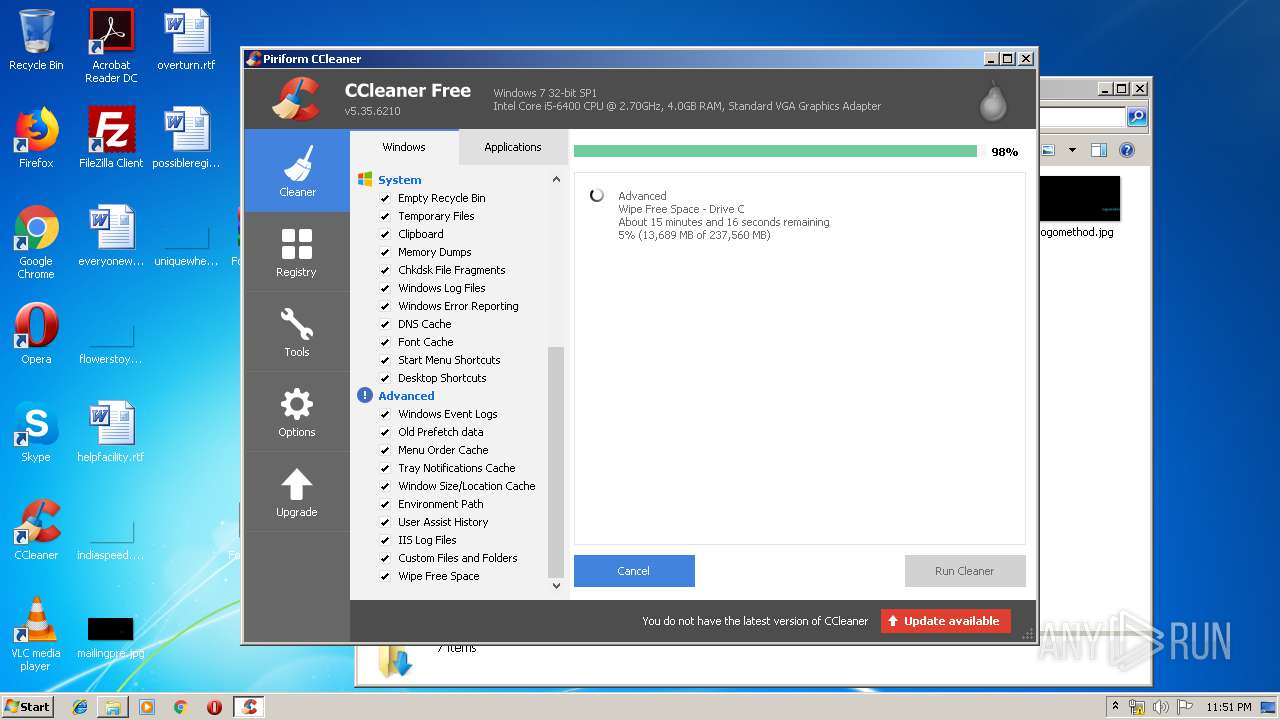
Loads the Task Scheduler COM API
- CCleaner.exe (PID: 1912)
- CCleaner.exe (PID: 3948)
Changes the autorun value in the registry
- CCleaner.exe (PID: 1912)
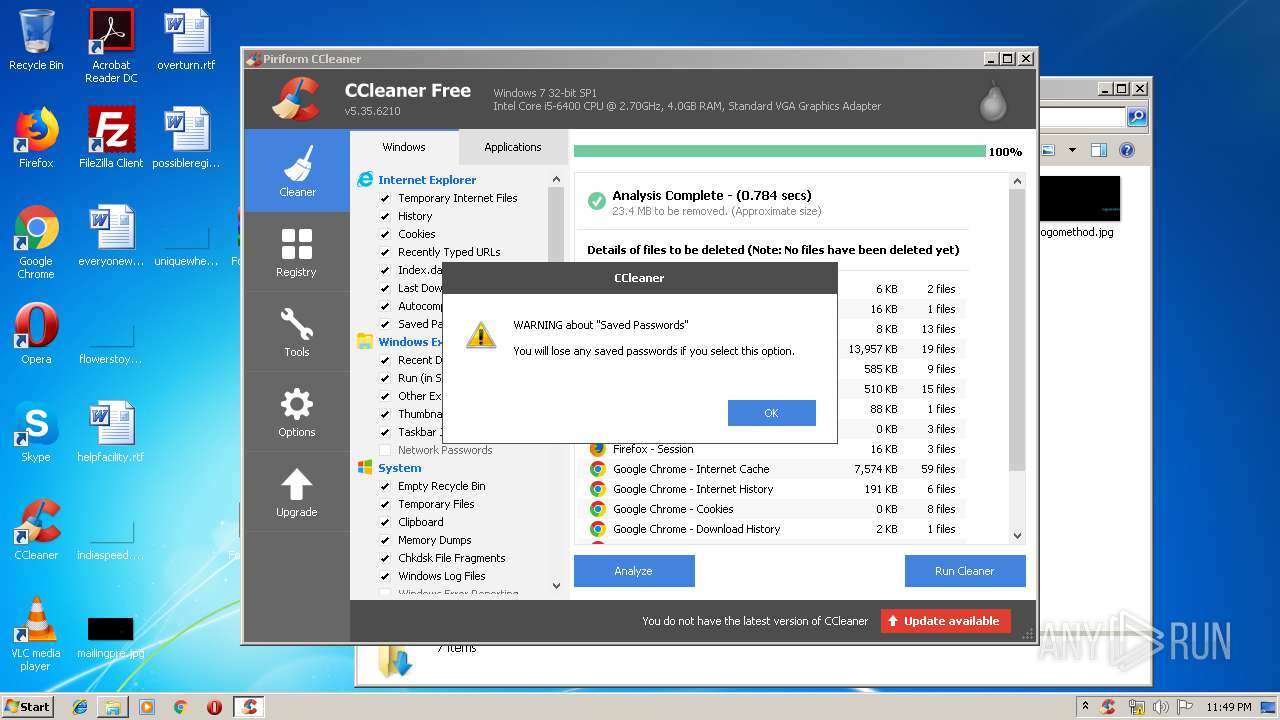
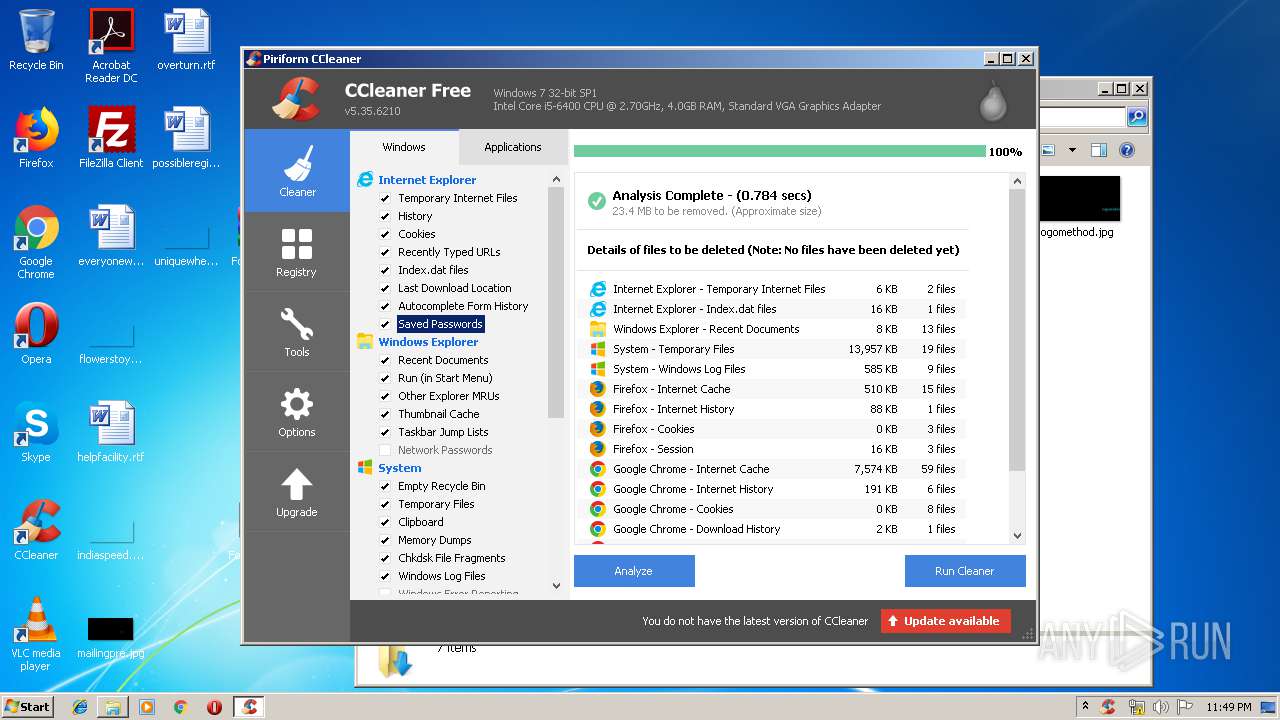
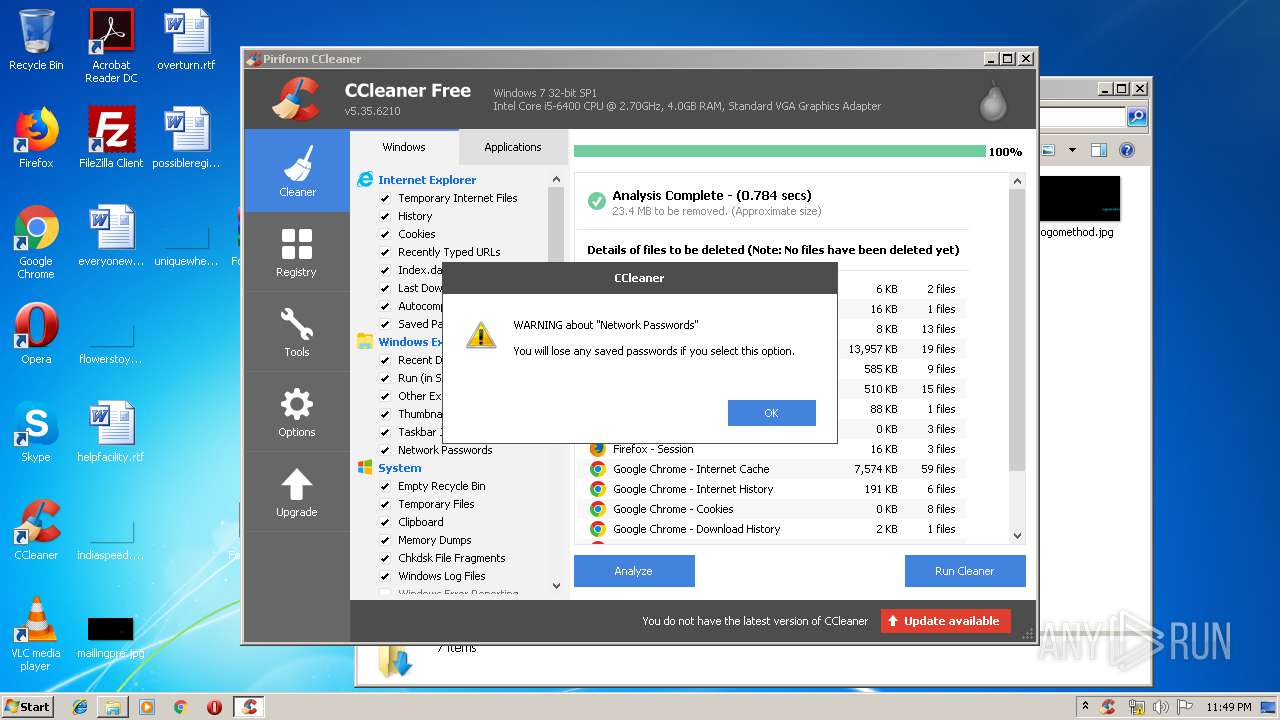
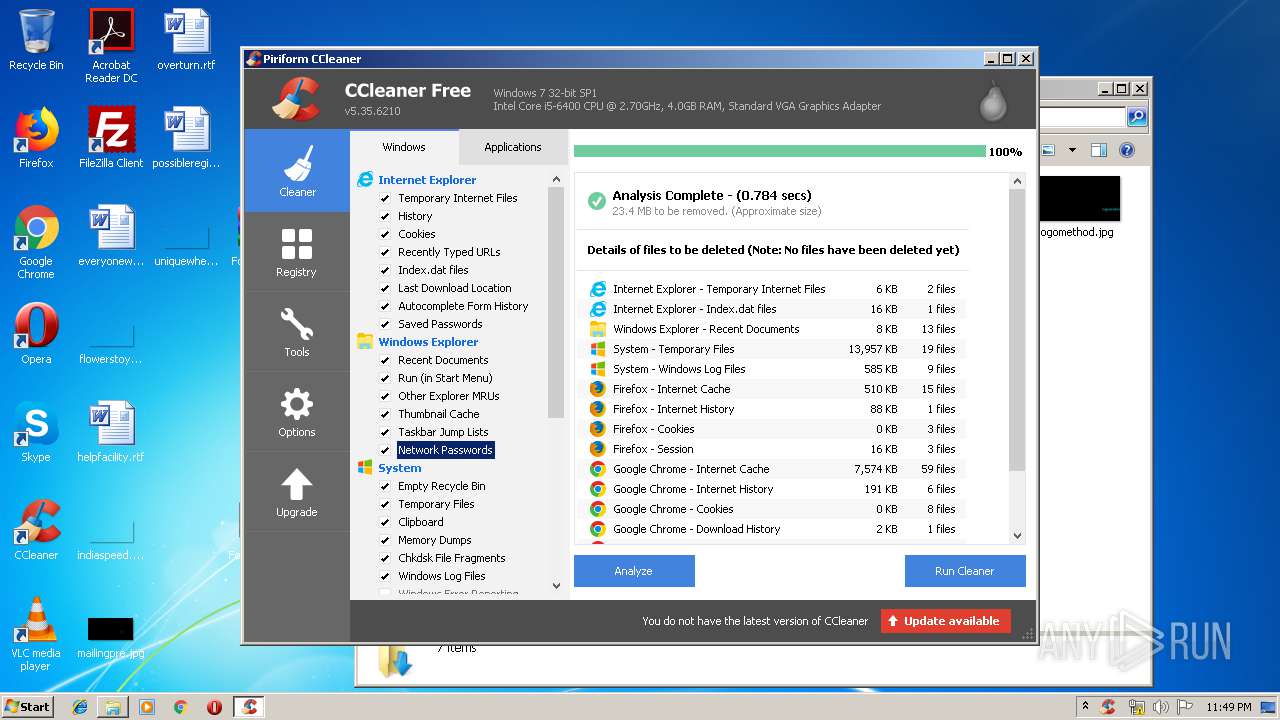
Actions looks like stealing of personal data
- CCleaner.exe (PID: 1912)
- CCleaner.exe (PID: 2064)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 3388)
Creates files in the program directory
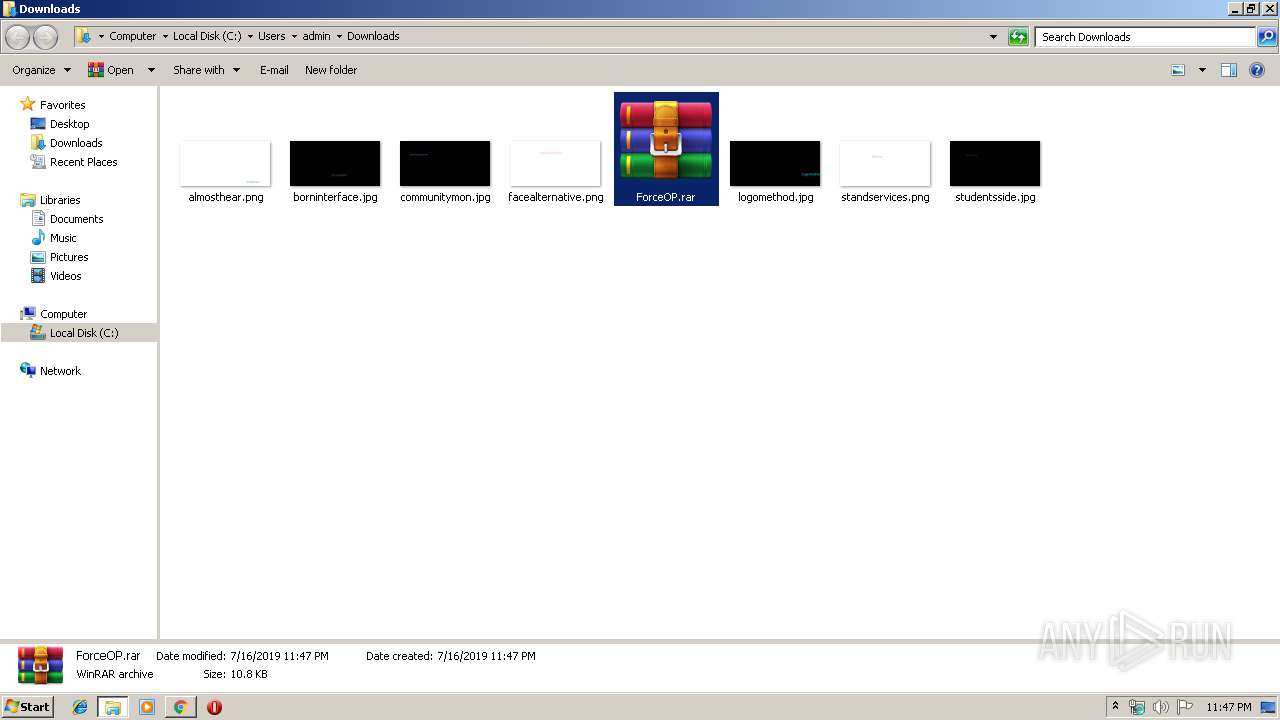
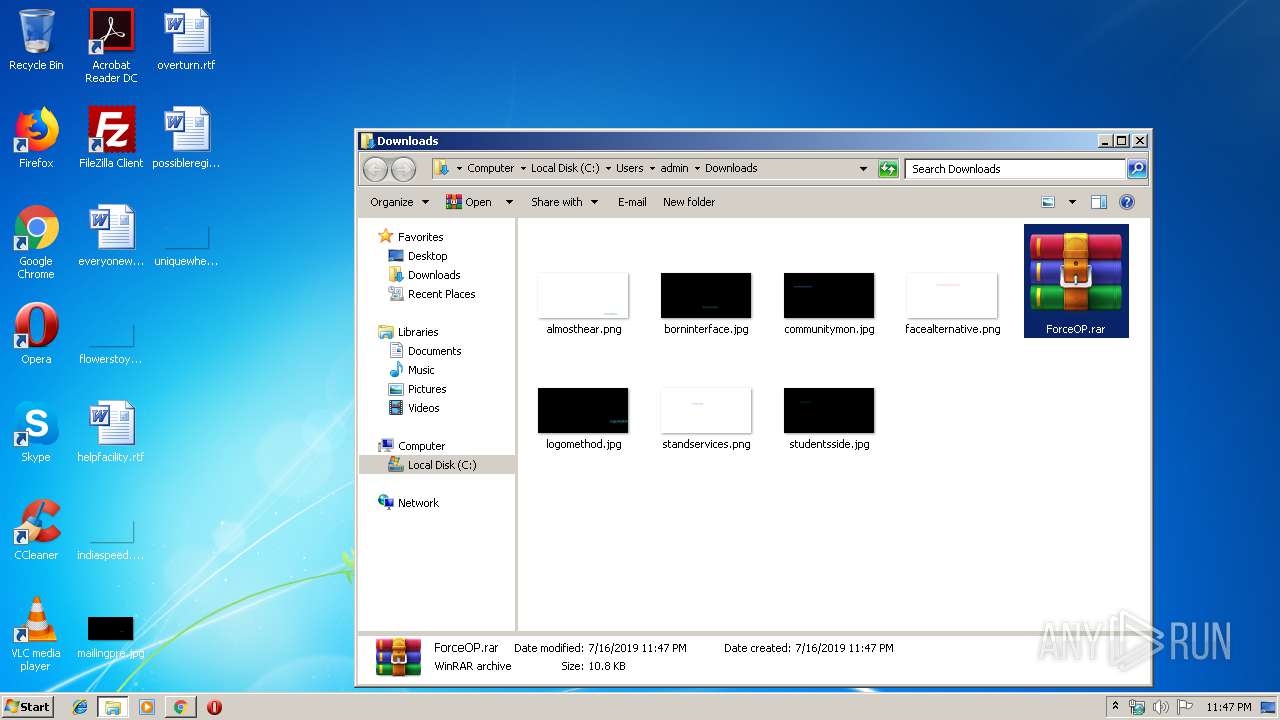
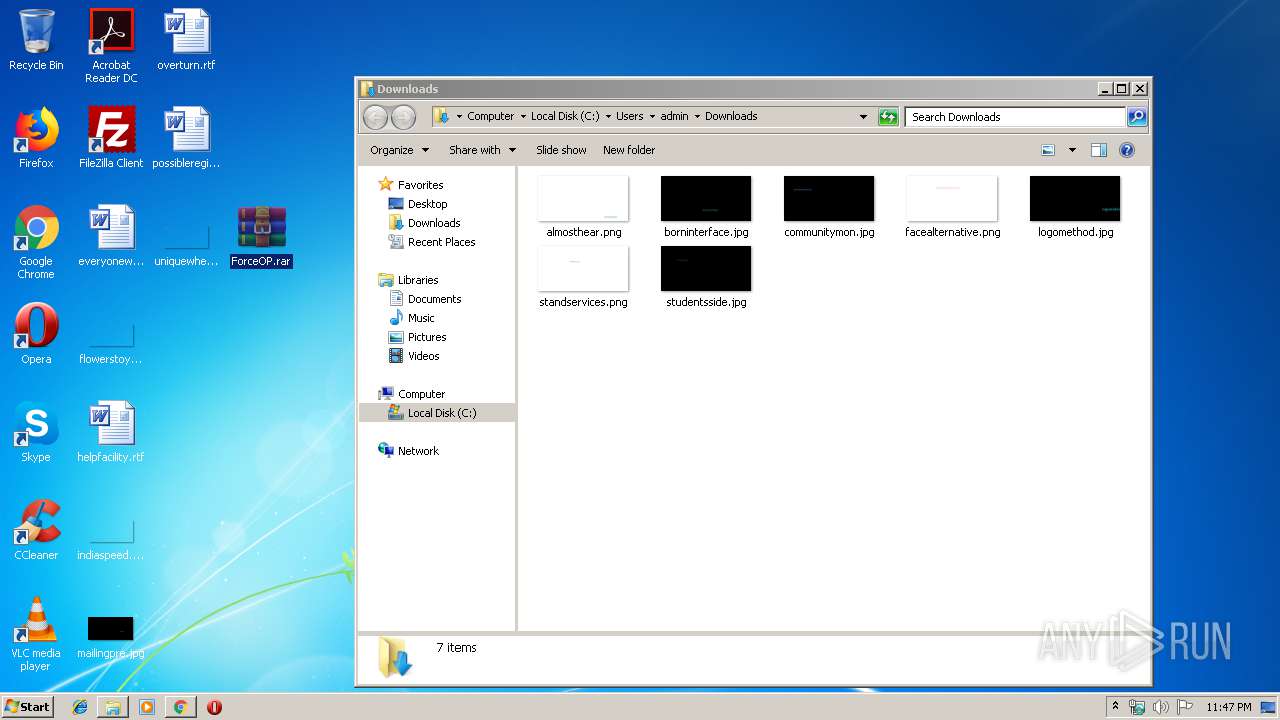
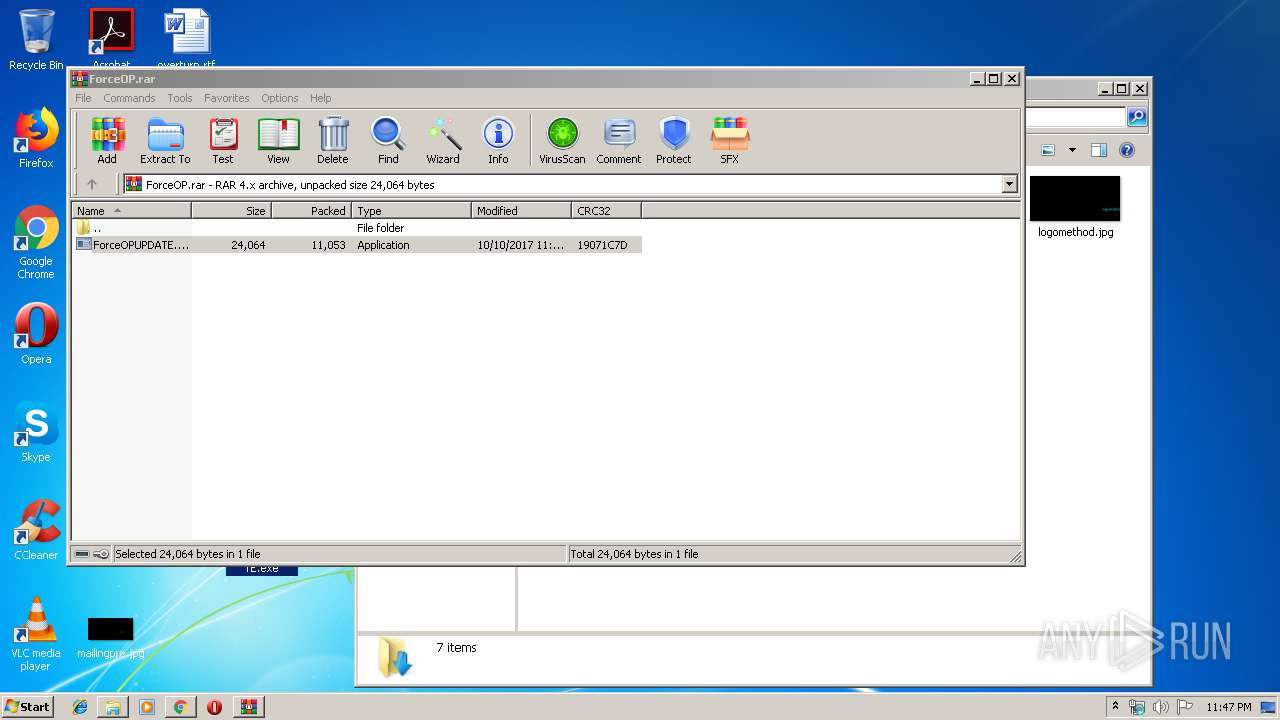
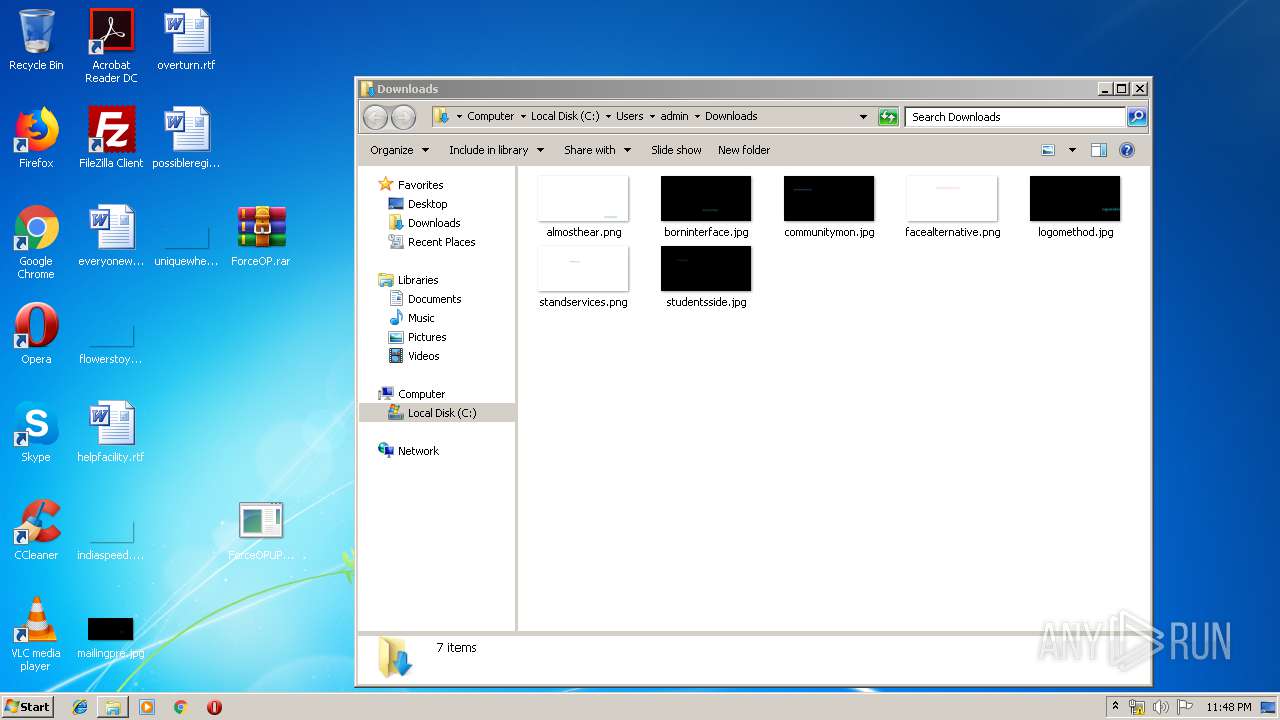
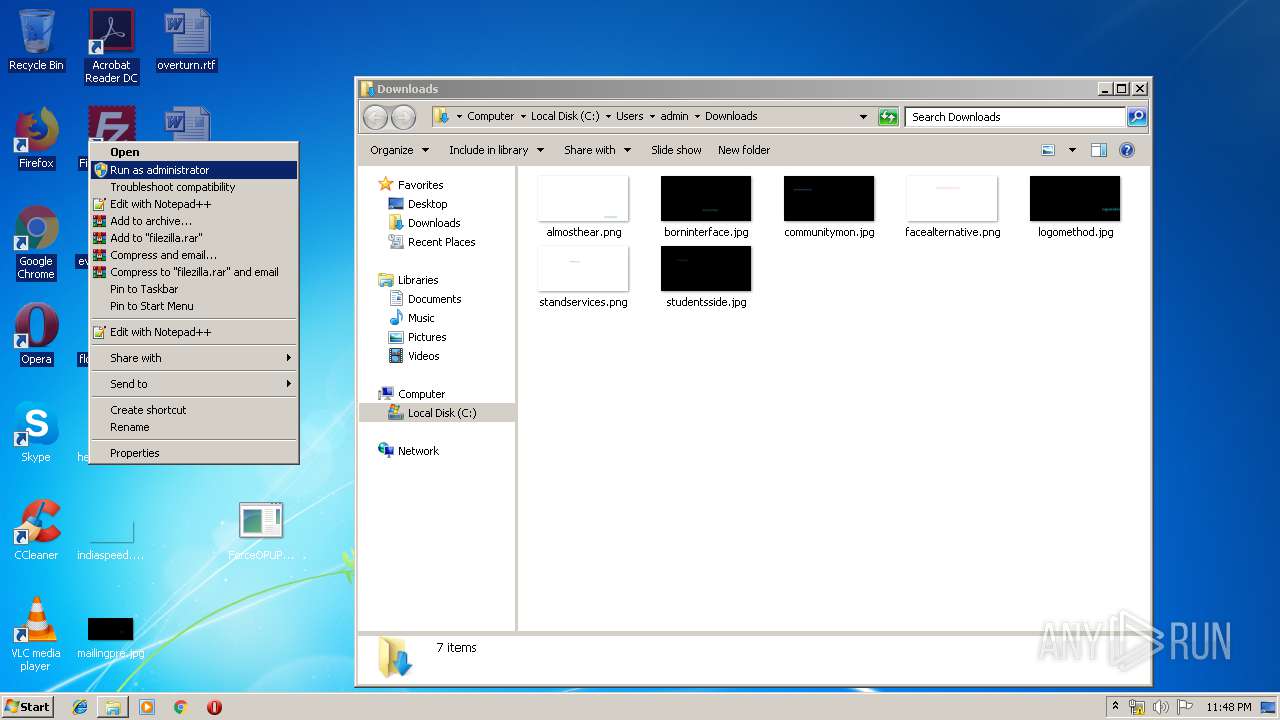
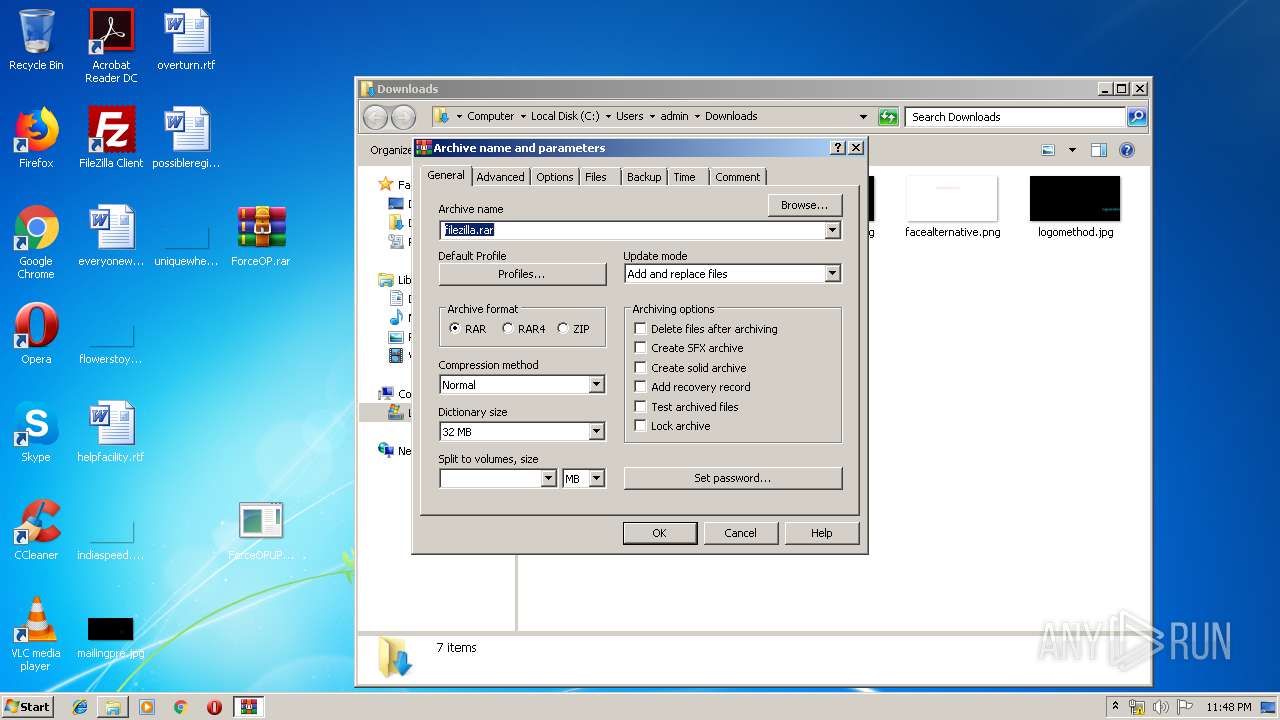
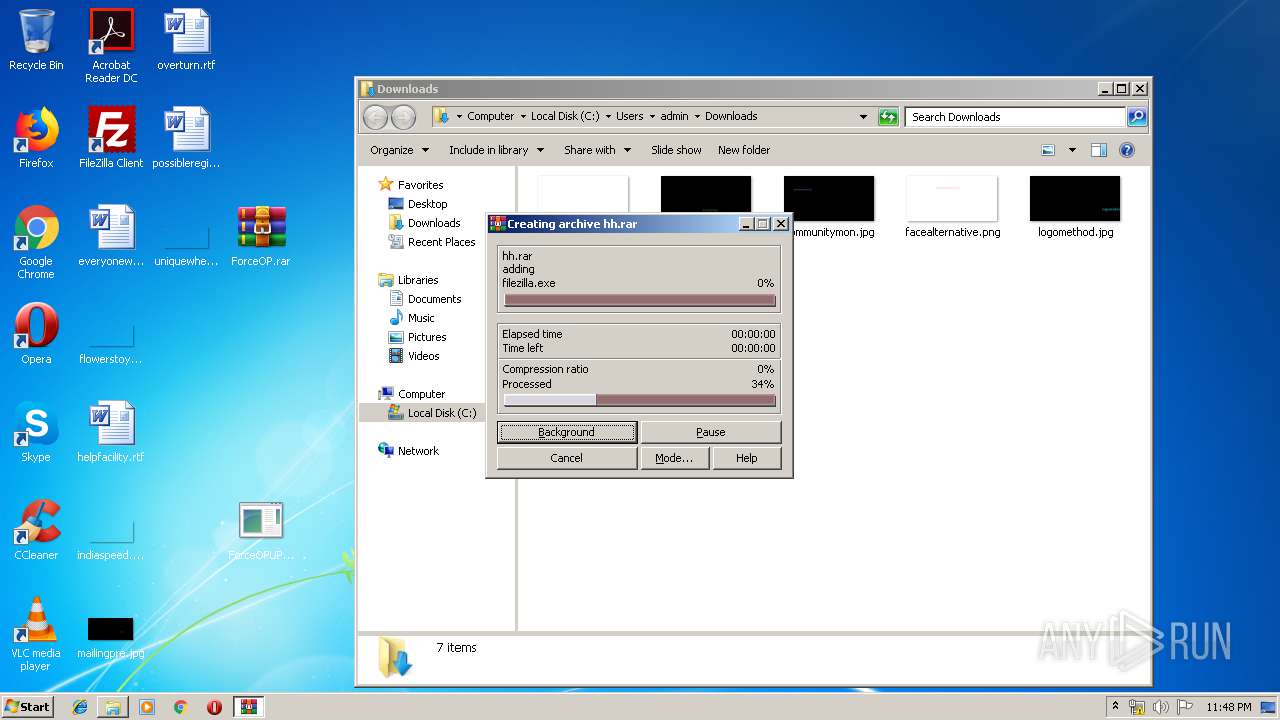
- WinRAR.exe (PID: 3448)
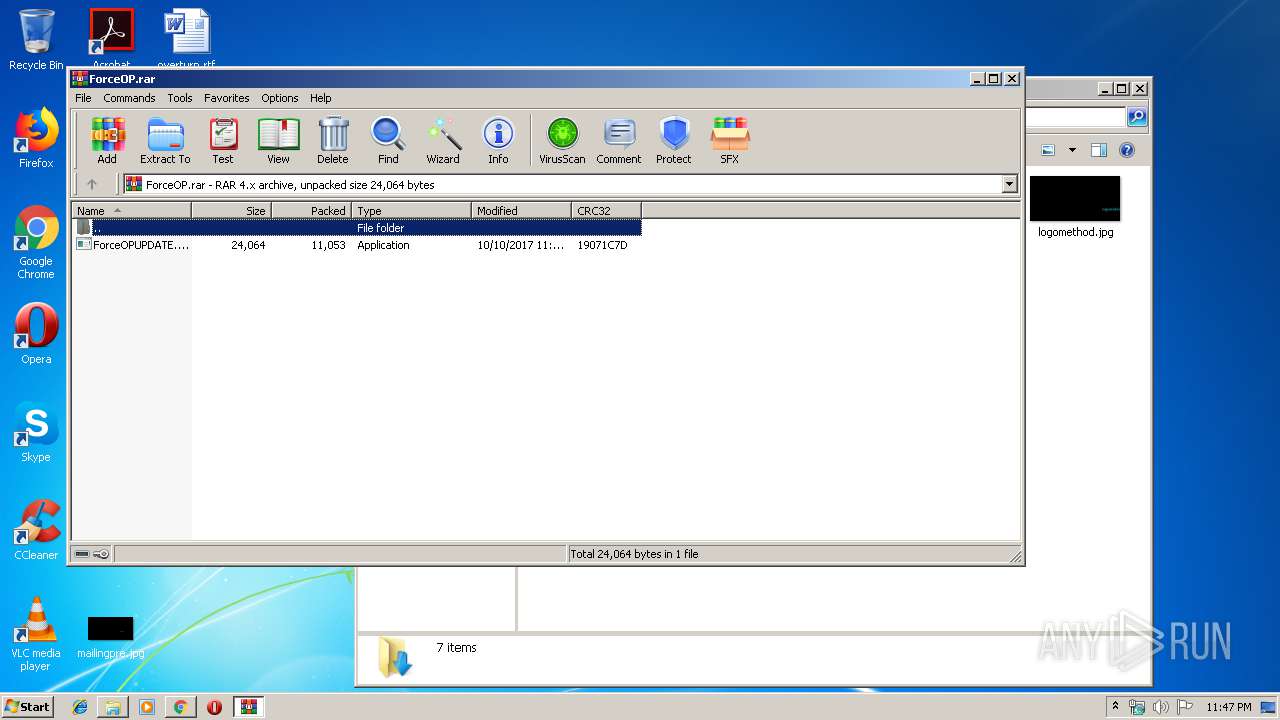
Application launched itself
- WinRAR.exe (PID: 2276)
- CCleaner.exe (PID: 2064)
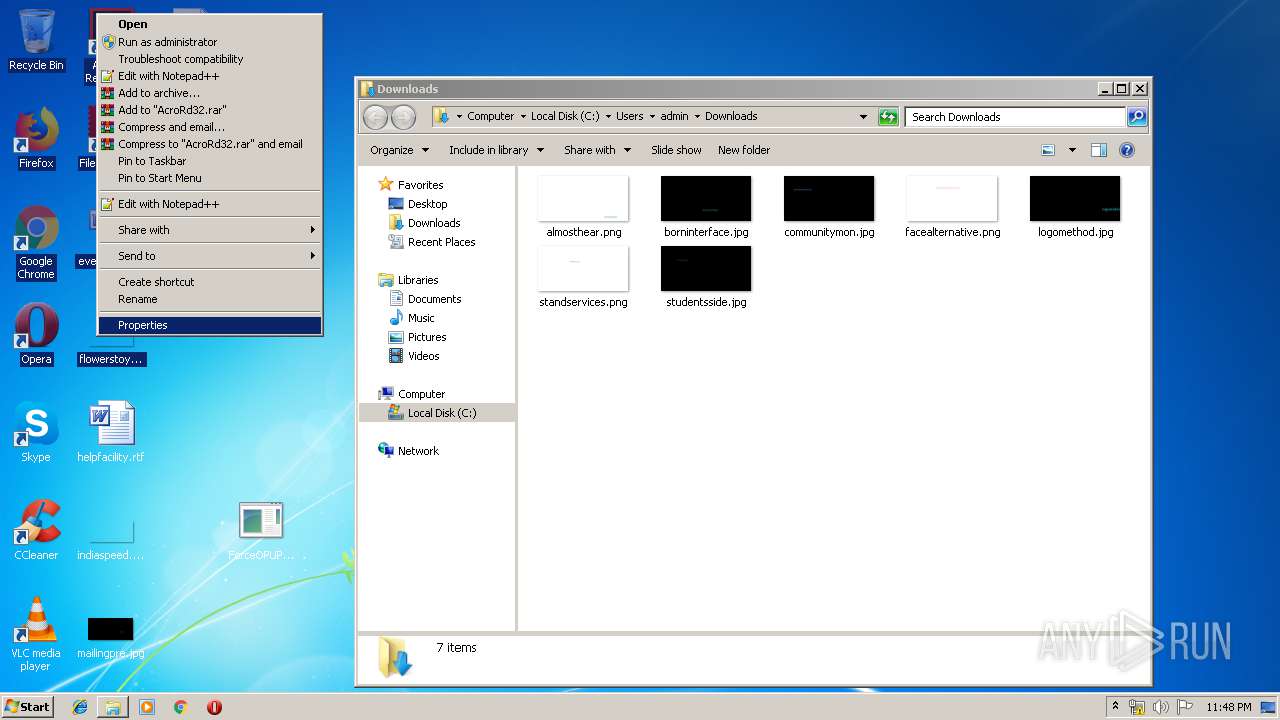
Reads internet explorer settings
- CCleaner.exe (PID: 2064)
- CCleaner.exe (PID: 1912)
Reads Internet Cache Settings
- CCleaner.exe (PID: 2064)
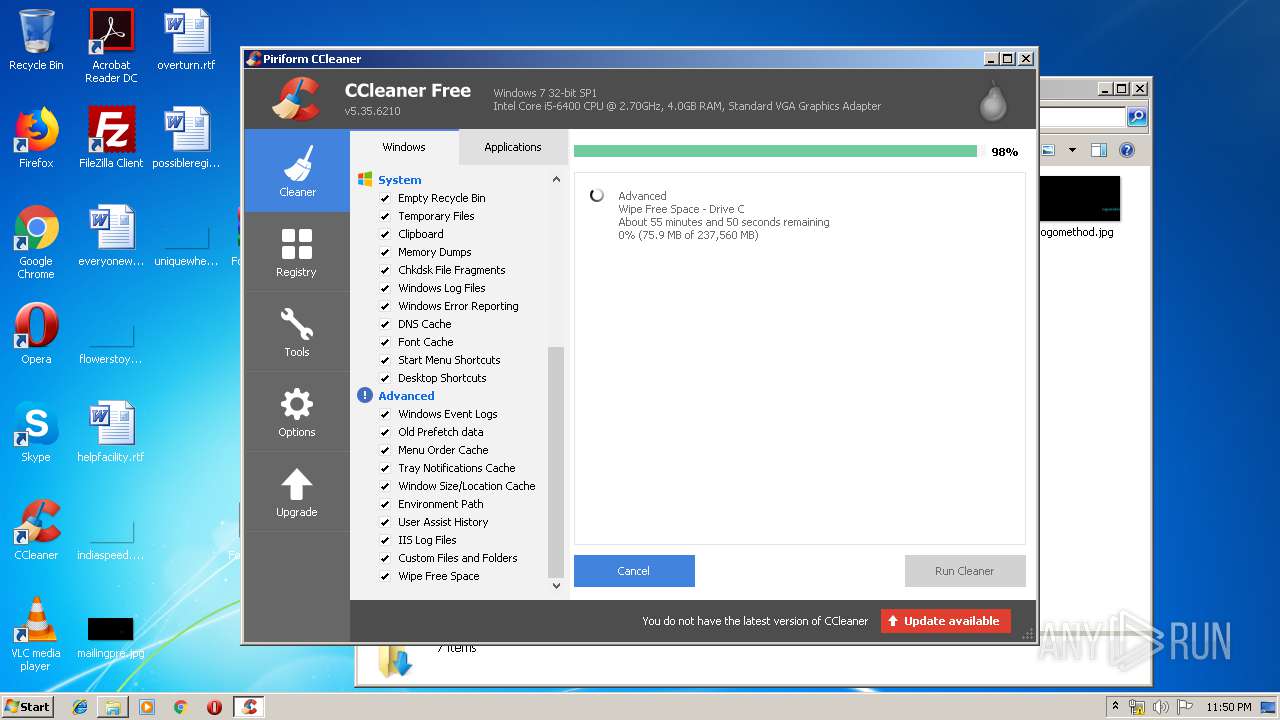
Low-level read access rights to disk partition
- CCleaner.exe (PID: 2064)
Reads the cookies of Google Chrome
- CCleaner.exe (PID: 2064)
Executed via Task Scheduler
- CCleaner.exe (PID: 2064)
Reads the cookies of Mozilla Firefox
- CCleaner.exe (PID: 2064)
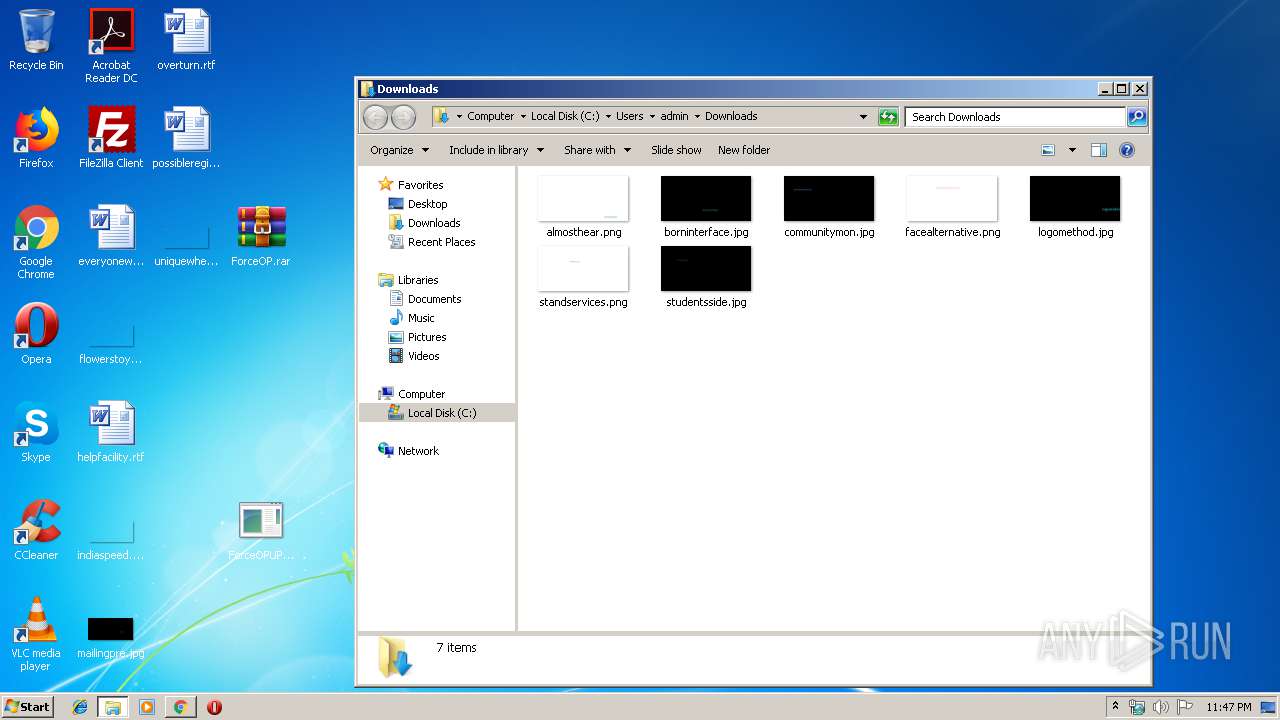
Creates files in the user directory
- CCleaner.exe (PID: 2064)
Removes files from Windows directory
- CCleaner.exe (PID: 2064)
INFO
Changes settings of System certificates
- chrome.exe (PID: 2808)
Reads Internet Cache Settings
- chrome.exe (PID: 3388)
Application launched itself
- chrome.exe (PID: 3388)
Creates files in the user directory
- chrome.exe (PID: 3388)
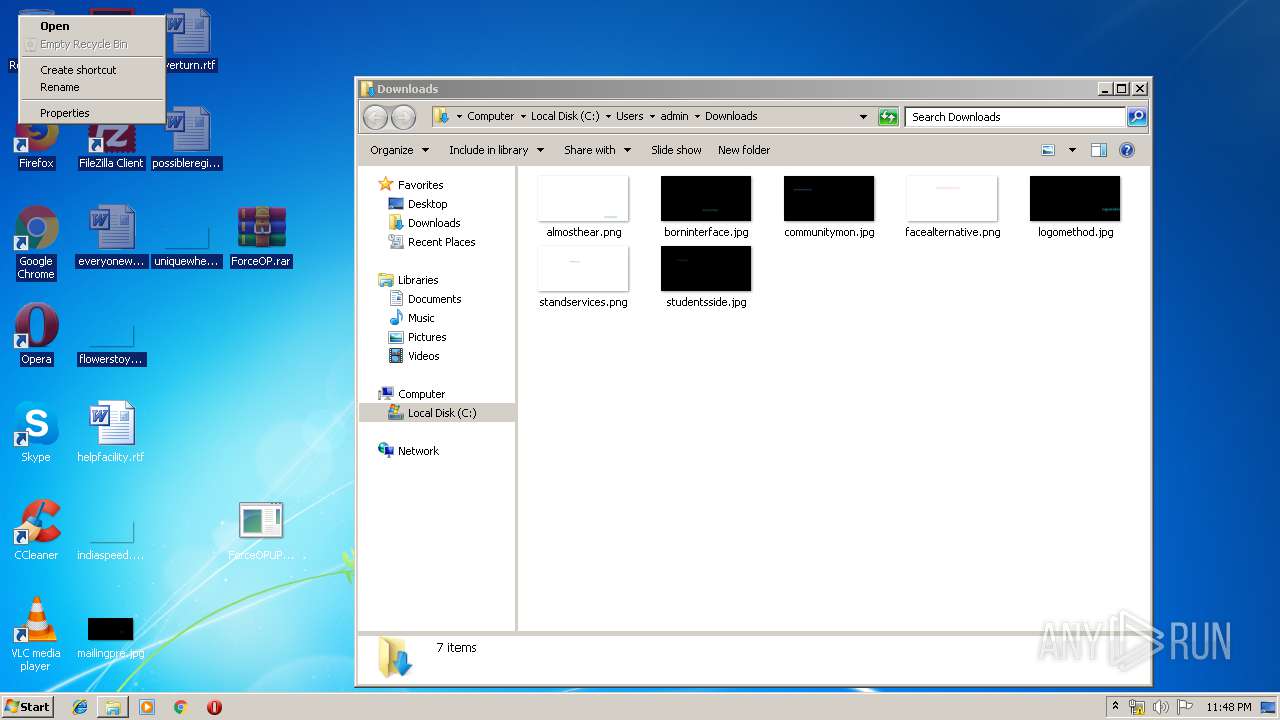
Manual execution by user
- ForceOPUPDATE.exe (PID: 2532)
- ForceOPUPDATE.exe (PID: 956)
- ForceOPUPDATE.exe (PID: 3244)
- WinRAR.exe (PID: 576)
- ForceOPUPDATE.exe (PID: 2748)
- ForceOPUPDATE.exe (PID: 2968)
- ForceOPUPDATE.exe (PID: 2604)
- ForceOPUPDATE.exe (PID: 2220)
- ForceOPUPDATE.exe (PID: 3088)
- ForceOPUPDATE.exe (PID: 564)
- ForceOPUPDATE.exe (PID: 652)
- ForceOPUPDATE.exe (PID: 4012)
- ForceOPUPDATE.exe (PID: 3464)
- WinRAR.exe (PID: 2276)
- ForceOPUPDATE.exe (PID: 2512)
- ForceOPUPDATE.exe (PID: 2408)
- ForceOPUPDATE.exe (PID: 3548)
- CCleaner.exe (PID: 3948)
Reads settings of System Certificates
- CCleaner.exe (PID: 2064)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
92
Monitored processes
48
Malicious processes
16
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 300 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,13545372789272437792,8433857143016299186,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10778879176974450230 --renderer-client-id=22 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2940 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 308 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,13545372789272437792,8433857143016299186,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16891857859369471038 --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3524 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 564 | "C:\Users\admin\Desktop\ForceOPUPDATE.exe" | C:\Users\admin\Desktop\ForceOPUPDATE.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 576 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\ForceOP.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 652 | "C:\Users\admin\Desktop\ForceOPUPDATE.exe" | C:\Users\admin\Desktop\ForceOPUPDATE.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 956 | "C:\Users\admin\Desktop\ForceOPUPDATE.exe" | C:\Users\admin\Desktop\ForceOPUPDATE.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1488 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,13545372789272437792,8433857143016299186,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4213996332522502511 --mojo-platform-channel-handle=4020 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1600 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,13545372789272437792,8433857143016299186,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8178238048516890806 --mojo-platform-channel-handle=4140 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1772 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,13545372789272437792,8433857143016299186,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=622019726420202183 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2180 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
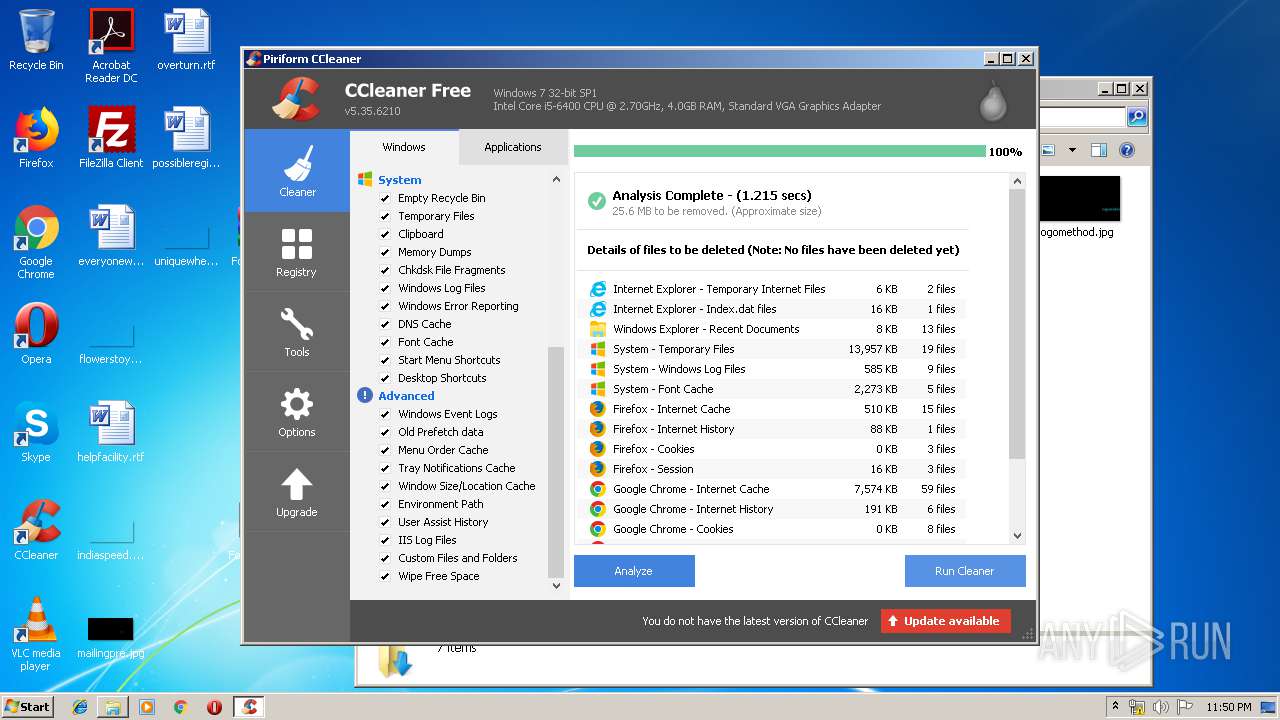
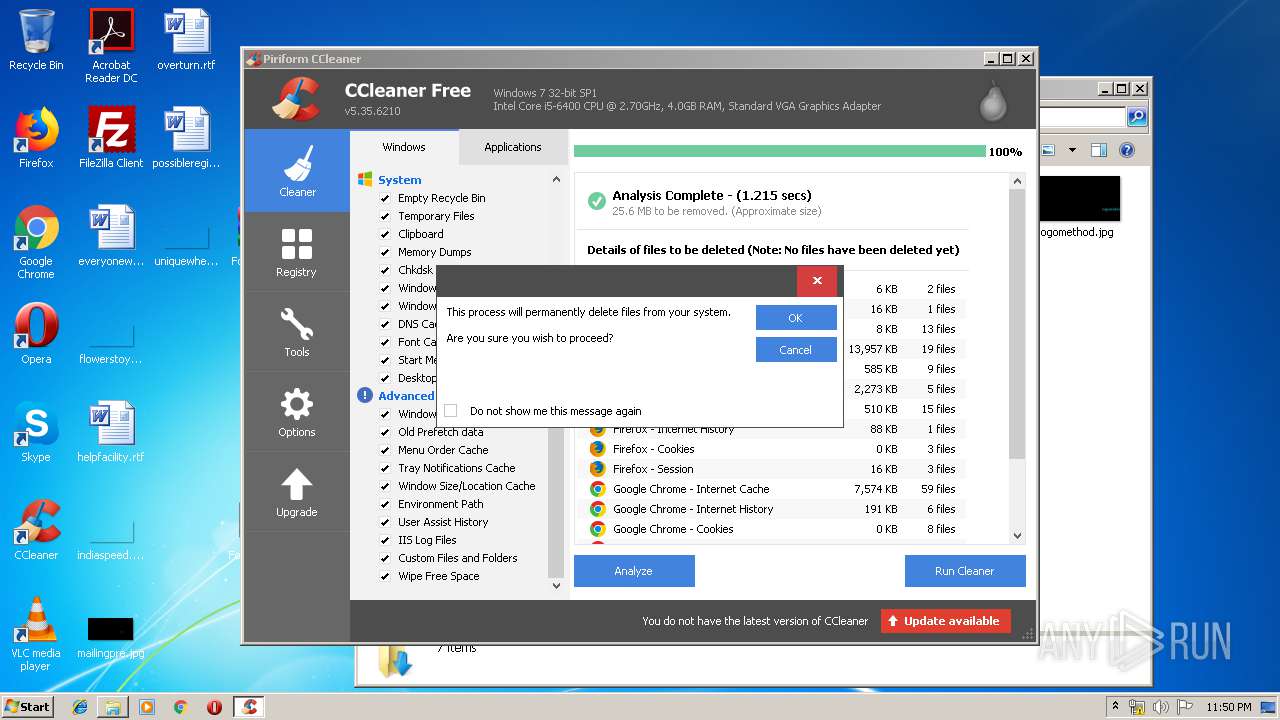
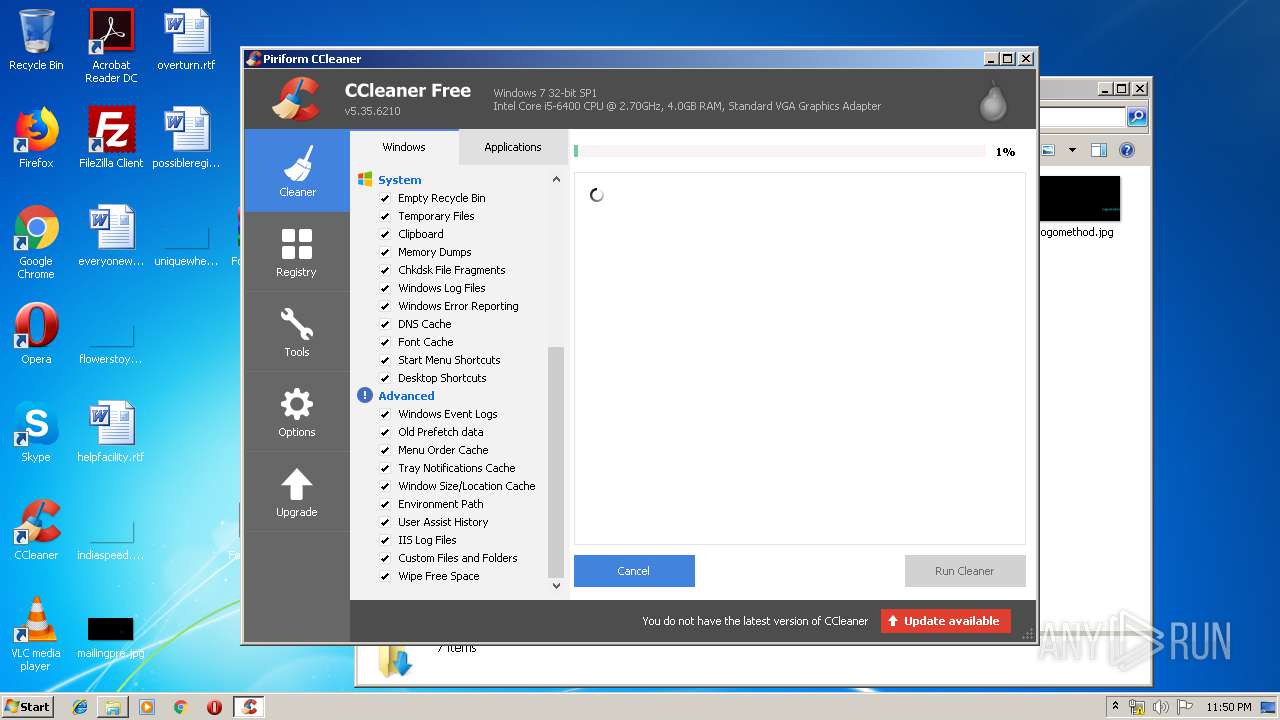
| 1912 | "C:\Program Files\CCleaner\CCleaner.exe" /monitor | C:\Program Files\CCleaner\CCleaner.exe | CCleaner.exe | ||||||||||||
User: admin Company: Piriform Ltd Integrity Level: HIGH Description: CCleaner Exit code: 0 Version: 5, 35, 0, 6210 Modules
| |||||||||||||||
Total events
2 354
Read events
1 931
Write events
392
Delete events
31
Modification events
| (PID) Process: | (3388) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3388) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3388) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3388) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3388) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3232) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3388-13207790820026125 |
Value: 259 | |||
| (PID) Process: | (3388) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3388) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3388) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (3388) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
80
Text files
209
Unknown types
2 771
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3388 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\c4597c9b-85e1-4779-b13f-fbc2e58d88de.tmp | — | |
MD5:— | SHA256:— | |||
| 3388 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3388 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3388 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3388 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3388 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old~RF17d409.TMP | text | |
MD5:— | SHA256:— | |||
| 3388 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF17d253.TMP | text | |
MD5:— | SHA256:— | |||
| 3388 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3388 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3388 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
49
DNS requests
36
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2808 | chrome.exe | GET | 302 | 172.217.16.142:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 516 b | whitelisted |
2808 | chrome.exe | GET | 200 | 91.199.212.52:80 | http://crt.comodoca.com/COMODORSAAddTrustCA.crt | GB | der | 1.37 Kb | whitelisted |
2064 | CCleaner.exe | GET | 301 | 151.101.0.64:80 | http://www.piriform.com/auto?a=0&p=cc&v=5.35.6210&l=1033&lk=&mk=IJR6-W5SV-5KYR-QBZD-6BY4-RN5Z-WAV9-RVK2-VJCA&o=6.1W3&au=1&mx=97B7721C4994E2556FF6A439510F665DB45337A341A47E15F4997584423BF714&gu=00000000-0000-4000-8000-d6f7f2be5127 | US | — | — | whitelisted |
2808 | chrome.exe | GET | 200 | 173.194.187.6:80 | http://r1---sn-4g5e6ns6.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=185.183.107.227&mm=28&mn=sn-4g5e6ns6&ms=nvh&mt=1563317128&mv=m&mvi=0&pl=24&shardbypass=yes | US | crx | 862 Kb | whitelisted |
2808 | chrome.exe | GET | 200 | 91.199.212.52:80 | http://crt.comodoca.com/COMODORSADomainValidationSecureServerCA.crt | GB | der | 1.51 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2808 | chrome.exe | 37.187.167.53:443 | www.upload.ee | OVH SAS | FR | suspicious |
2808 | chrome.exe | 172.217.22.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2808 | chrome.exe | 23.210.248.44:443 | s7.addthis.com | Akamai International B.V. | NL | whitelisted |
2808 | chrome.exe | 172.217.18.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
2808 | chrome.exe | 35.190.74.92:443 | www.tradeadexchange.com | Google Inc. | US | whitelisted |
2808 | chrome.exe | 216.58.207.66:443 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
2808 | chrome.exe | 172.217.22.2:443 | adservice.google.at | Google Inc. | US | whitelisted |
2808 | chrome.exe | 216.58.206.8:443 | ssl.google-analytics.com | Google Inc. | US | whitelisted |
2808 | chrome.exe | 104.27.147.197:443 | geniusonclick.com | Cloudflare Inc | US | shared |
2808 | chrome.exe | 216.58.207.78:443 | clients1.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.upload.ee |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
s7.addthis.com |
| whitelisted |
www.tradeadexchange.com |
| whitelisted |
crt.comodoca.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
ssl.google-analytics.com |
| whitelisted |
v1.addthisedge.com |
| shared |
v1.addthis.com |
| whitelisted |