| File name: | test_theme[1].theme |
| Full analysis: | https://app.any.run/tasks/d1caaa62-82ee-49aa-8bce-8b120c85612f |
| Verdict: | Malicious activity |
| Analysis date: | September 16, 2024, 16:28:52 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| MIME: | text/plain |
| File info: | Unicode text, UTF-8 text |
| MD5: | 53B9081226612CC924AB4D5BC178A11B |
| SHA1: | FA55186B64B764F080FBC2574A747C3A7C2D453B |
| SHA256: | BBE82603FC304FFEC485BDA991C84A23E7F11B6DA4A5D49777AB637FF34A1A31 |
| SSDEEP: | 12:YcZ+BFbRSfCh5PRtvMnL3kcveG+3oEmhhB+mn/oNK8V:Yg+DVSfYpGnL3VY3oTvB+mn/qV |
MALICIOUS
Attempt to connect to SMB server
- System (PID: 4)
SUSPICIOUS
Potential Corporate Privacy Violation
- System (PID: 4)
INFO
Creates files or folders in the user directory
- rundll32.exe (PID: 2080)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
131
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 4 | System | [System Process] | |||||||||||||
User: SYSTEM Integrity Level: SYSTEM | |||||||||||||||
| 2080 | "C:\WINDOWS\system32\rundll32.exe" C:\WINDOWS\system32\themecpl.dll,OpenThemeAction C:\Users\admin\AppData\Local\Temp\test_theme[1].theme | C:\Windows\System32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
472
Read events
439
Write events
17
Delete events
16
Modification events
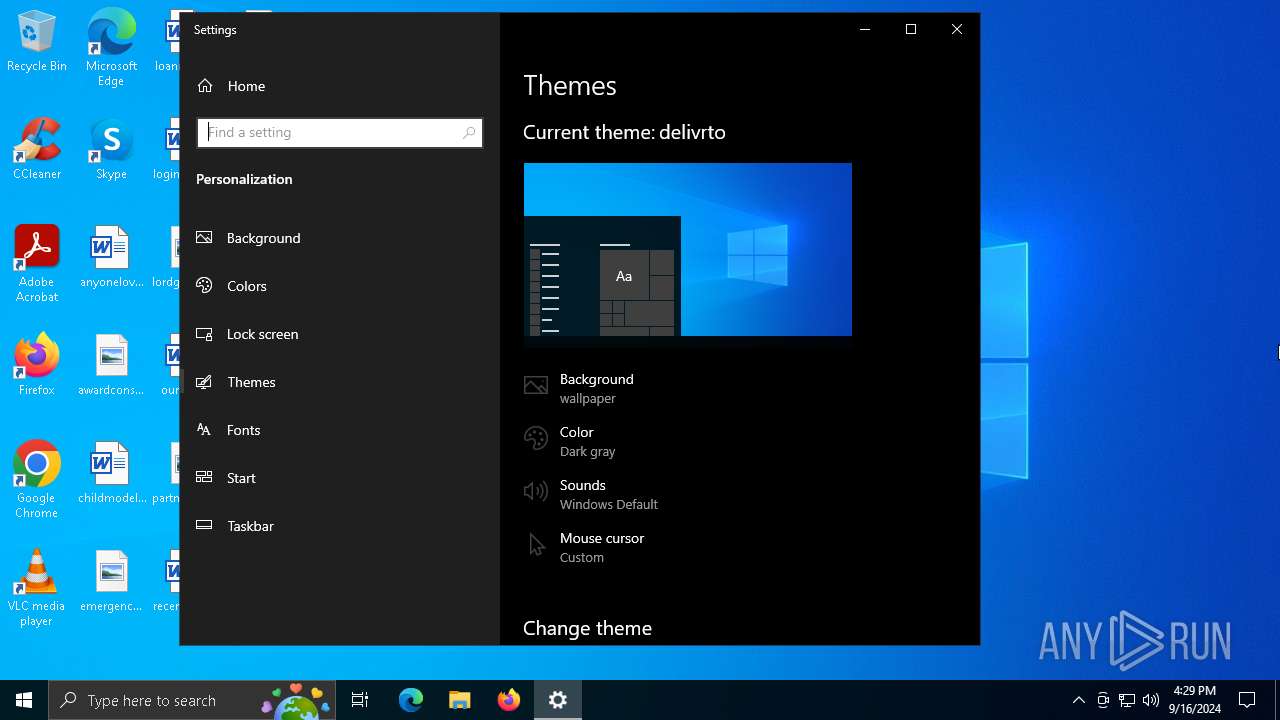
| (PID) Process: | (2080) rundll32.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Themes |
| Operation: | write | Name: | CurrentTheme |
Value: C:\Users\admin\AppData\Local\Microsoft\Windows\Themes\Custom.theme | |||
| (PID) Process: | (2080) rundll32.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Themes\HighContrast |
| Operation: | write | Name: | Pre-High Contrast Scheme |
Value: C:\Users\admin\AppData\Local\Microsoft\Windows\Themes\Custom.theme | |||
| (PID) Process: | (2080) rundll32.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Themes |
| Operation: | write | Name: | CurrentTheme |
Value: C:\Users\admin\AppData\Local\Microsoft\Windows\Themes\test_theme[1].theme | |||
| (PID) Process: | (2080) rundll32.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Themes\HighContrast |
| Operation: | write | Name: | Pre-High Contrast Scheme |
Value: C:\Users\admin\AppData\Local\Microsoft\Windows\Themes\test_theme[1].theme | |||
| (PID) Process: | (2080) rundll32.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Accent |
| Operation: | write | Name: | AccentPalette |
Value: 6B6B6BFF595959FF4C4C4CFF3F3F3FFF333333FF262626FF141414FF88179800 | |||
| (PID) Process: | (2080) rundll32.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Themes\History |
| Operation: | write | Name: | AutoColor |
Value: 0 | |||
| (PID) Process: | (2080) rundll32.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Themes\History\Colors |
| Operation: | write | Name: | ColorHistory0 |
Value: | |||
| (PID) Process: | (2080) rundll32.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Themes\History\Colors |
| Operation: | write | Name: | ColorHistory1 |
Value: 12826368 | |||
| (PID) Process: | (2080) rundll32.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Themes\History\Colors |
| Operation: | write | Name: | ColorHistory2 |
Value: 4737612 | |||
| (PID) Process: | (2080) rundll32.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Themes\History\Colors |
| Operation: | write | Name: | ColorHistory3 |
Value: 2298344 | |||
Executable files
0
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2080 | rundll32.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Themes\Custom.theme | text | |
MD5:1348E4E8FC451E8021F935F4B1376C95 | SHA256:CDF0440A375C4D4A180A358EA3C87448482622FBC71833BC797EC1410E54BB01 | |||
| 2080 | rundll32.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Themes\test_theme[1].theme | text | |
MD5:53B9081226612CC924AB4D5BC178A11B | SHA256:BBE82603FC304FFEC485BDA991C84A23E7F11B6DA4A5D49777AB637FF34A1A31 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
37
DNS requests
16
Threats
82
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1028 | SystemSettings.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1028 | SystemSettings.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
1744 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1356 | svchost.exe | GET | 200 | 23.218.209.163:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
3908 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
3908 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6424 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2120 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1356 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 35.177.186.252:445 | serve.files.delivrto.me | AMAZON-02 | GB | suspicious |
3260 | svchost.exe | 40.113.103.199:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1028 | SystemSettings.exe | 104.126.37.146:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
1028 | SystemSettings.exe | 104.64.113.235:443 | cxcs.microsoft.net | AKAMAI-AS | CZ | whitelisted |
1028 | SystemSettings.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1744 | svchost.exe | 20.190.159.0:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
serve.files.delivrto.me |
| unknown |
client.wns.windows.com |
| whitelisted |
cxcs.microsoft.net |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4 | System | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Attempt to connect to an external SMB server |
4 | System | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Attempt to connect to an external SMB server |
4 | System | Potential Corporate Privacy Violation | POLICY [ANY.RUN] NTLM Over SMB (NTLMSSP_NEGOTIATE) |
4 | System | Potential Corporate Privacy Violation | POLICY [ANY.RUN] NTLM Over SMB (NTLMSSP_NEGOTIATE) |
4 | System | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Possible NTLM Hash leak over SMB (NTLMSSP_AUTH) |
4 | System | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Attempt to connect to an external SMB server |
4 | System | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Attempt to connect to an external SMB server |
4 | System | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Attempt to connect to an external SMB server |
4 | System | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Attempt to connect to an external SMB server |
4 | System | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Attempt to connect to an external SMB server |