| File name: | OneLaunch - Package Finder_13rc4.exe |
| Full analysis: | https://app.any.run/tasks/a00e01ae-bc16-4d70-8b9b-e84bc2be4563 |
| Verdict: | Malicious activity |
| Analysis date: | March 06, 2023, 16:18:26 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 996A7F5176FD6CBAC571E22DE6424BA6 |
| SHA1: | 9EA35D9944AAD80424973CE685D10E50304B09D0 |
| SHA256: | BBDD1FF124CE1A7FA5DAD768DF8AB2C7C262E439259F5F45F6B32D9C1E6C3CD7 |
| SSDEEP: | 49152:cqe3f6Rz+VAoYpCpk42zP4jqVX5rIJwI2J5PiH7nBGtg:pSiRzjZpW2D4jgJLTiH7BUg |
MALICIOUS
Drops the executable file immediately after the start
- OneLaunch - Package Finder_13rc4.exe (PID: 3492)
- OneLaunch - Package Finder_13rc4.tmp (PID: 3384)
- OneLaunch - Package Finder_uqyj4.exe (PID: 3052)
- OneLaunch - Package Finder_uqyj4.tmp (PID: 3436)
Loads dropped or rewritten executable
- OneLaunch - Package Finder_13rc4.tmp (PID: 3384)
- OneLaunch - Package Finder_uqyj4.tmp (PID: 3436)
SUSPICIOUS
Executable content was dropped or overwritten
- OneLaunch - Package Finder_13rc4.exe (PID: 3492)
- OneLaunch - Package Finder_13rc4.tmp (PID: 3384)
- OneLaunch - Package Finder_uqyj4.exe (PID: 3052)
- OneLaunch - Package Finder_uqyj4.tmp (PID: 3436)
Reads the Windows owner or organization settings
- OneLaunch - Package Finder_13rc4.tmp (PID: 3384)
- OneLaunch - Package Finder_uqyj4.tmp (PID: 3436)
INFO
Checks supported languages
- OneLaunch - Package Finder_13rc4.exe (PID: 3492)
- OneLaunch - Package Finder_13rc4.tmp (PID: 3384)
- OneLaunch - Package Finder_uqyj4.exe (PID: 3052)
- OneLaunch - Package Finder_uqyj4.tmp (PID: 3436)
Reads the computer name
- OneLaunch - Package Finder_13rc4.tmp (PID: 3384)
- OneLaunch - Package Finder_uqyj4.tmp (PID: 3436)
The process checks LSA protection
- OneLaunch - Package Finder_13rc4.tmp (PID: 3384)
- OneLaunch - Package Finder_uqyj4.tmp (PID: 3436)
Create files in a temporary directory
- OneLaunch - Package Finder_13rc4.exe (PID: 3492)
- OneLaunch - Package Finder_13rc4.tmp (PID: 3384)
- chrome.exe (PID: 3092)
- OneLaunch - Package Finder_uqyj4.exe (PID: 3052)
- OneLaunch - Package Finder_uqyj4.tmp (PID: 3436)
- chrome.exe (PID: 3900)
Application was dropped or rewritten from another process
- OneLaunch - Package Finder_13rc4.tmp (PID: 3384)
- OneLaunch - Package Finder_uqyj4.tmp (PID: 3436)
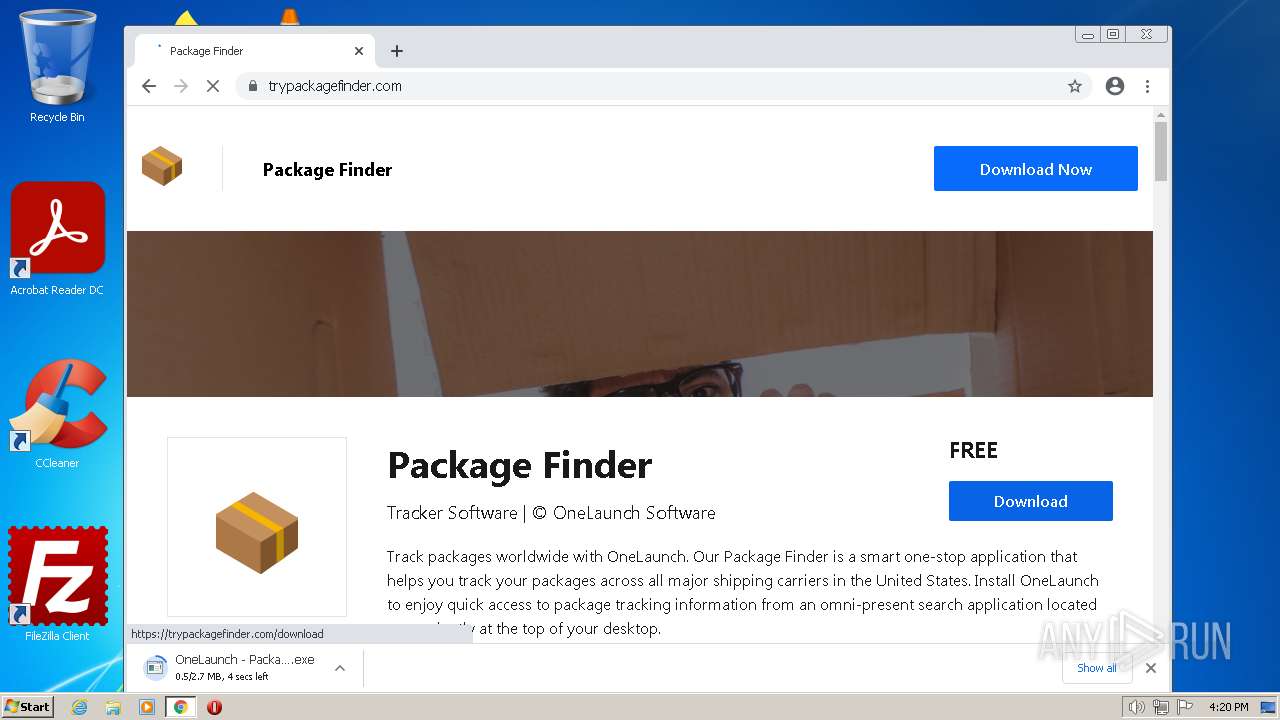
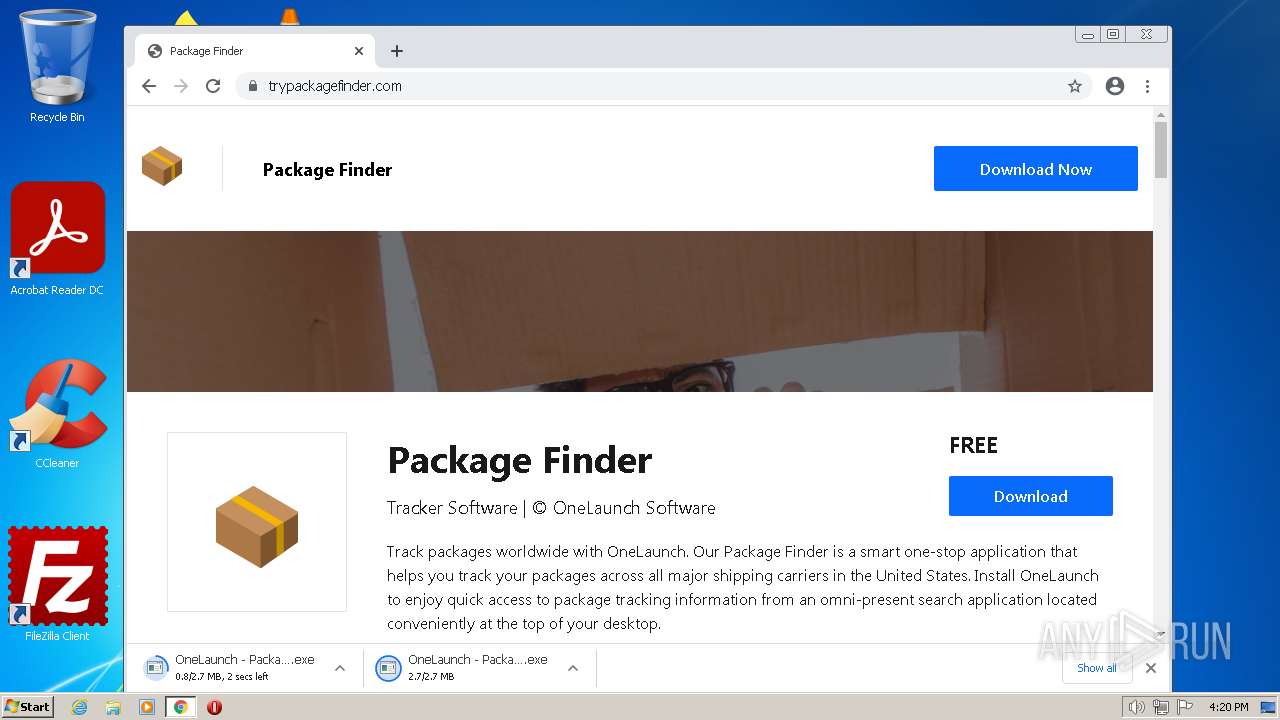
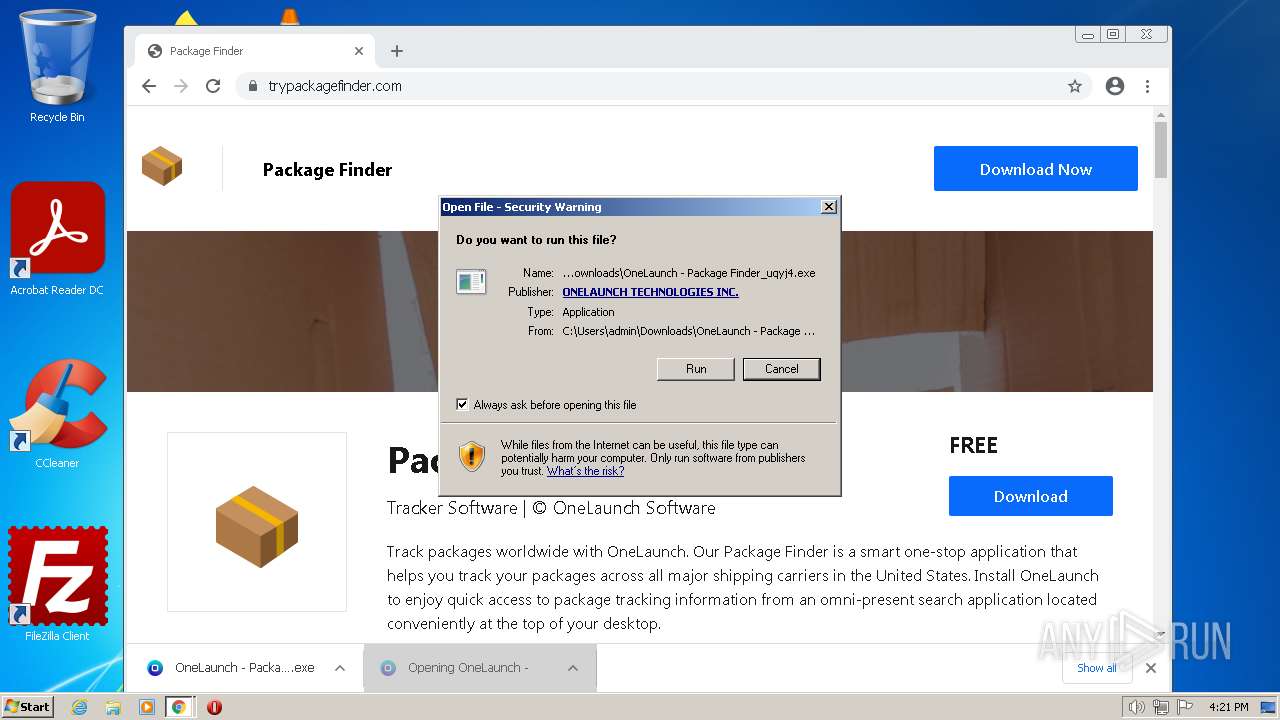
Manual execution by a user
- chrome.exe (PID: 3900)
Drops the executable file immediately after the start
- chrome.exe (PID: 3900)
- chrome.exe (PID: 3092)
Executable content was dropped or overwritten
- chrome.exe (PID: 3900)
- chrome.exe (PID: 3092)
Application launched itself
- chrome.exe (PID: 3900)
The process uses the downloaded file
- chrome.exe (PID: 3900)
- chrome.exe (PID: 3208)
- chrome.exe (PID: 1800)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (67.7) |
|---|---|---|
| .exe | | | Win32 EXE PECompact compressed (generic) (25.6) |
| .exe | | | Win32 Executable (generic) (2.7) |
| .exe | | | Win16/32 Executable Delphi generic (1.2) |
| .exe | | | Generic Win/DOS Executable (1.2) |
EXIF
EXE
| ProductVersion: | 5.12.1 |
|---|---|
| ProductName: | OneLaunch |
| OriginalFileName: | |
| LegalCopyright: | Copyright OneLaunch. All rights reserved. |
| FileVersion: | 5.12.1 |
| FileDescription: | OneLaunch Setup |
| CompanyName: | OneLaunch |
| Comments: | This installation was built with Inno Setup. |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 5.12.1.0 |
| FileVersionNumber: | 5.12.1.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 6.1 |
| ImageVersion: | 6 |
| OSVersion: | 6.1 |
| EntryPoint: | 0xb5eec |
| UninitializedDataSize: | - |
| InitializedDataSize: | 151552 |
| CodeSize: | 741376 |
| LinkerVersion: | 2.25 |
| PEType: | PE32 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| TimeStamp: | 2020:11:15 09:48:30+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 15-Nov-2020 09:48:30 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | OneLaunch |
| FileDescription: | OneLaunch Setup |
| FileVersion: | 5.12.1 |
| LegalCopyright: | Copyright OneLaunch. All rights reserved. |
| OriginalFileName: | - |
| ProductName: | OneLaunch |
| ProductVersion: | 5.12.1 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 10 |
| Time date stamp: | 15-Nov-2020 09:48:30 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000B361C | 0x000B3800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.35606 |
.itext | 0x000B5000 | 0x00001688 | 0x00001800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.97275 |
.data | 0x000B7000 | 0x000037A4 | 0x00003800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.0444 |
.bss | 0x000BB000 | 0x00006DE8 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x000C2000 | 0x00000F36 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.8987 |
.didata | 0x000C3000 | 0x000001A4 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.75636 |
.edata | 0x000C4000 | 0x0000009A | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.87222 |
.tls | 0x000C5000 | 0x00000018 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x000C6000 | 0x0000005D | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.38389 |
.rsrc | 0x000C7000 | 0x00020194 | 0x00020200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.05967 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.18295 | 1830 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 5.42918 | 67624 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 5.59133 | 16936 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 5.70399 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 5.79345 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 5.89179 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
4086 | 3.16547 | 864 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4087 | 3.40938 | 608 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4088 | 3.31153 | 1116 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4089 | 3.33977 | 1036 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
kernel32.dll (delay-loaded) |
netapi32.dll |
oleaut32.dll |
user32.dll |
version.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
dbkFCallWrapperAddr | 1 | 0x000BE63C |
__dbk_fcall_wrapper | 2 | 0x0000D0A0 |
TMethodImplementationIntercept | 3 | 0x00054060 |
Total processes
96
Monitored processes
56
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1028,6851494879864175916,10514771213575818009,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2400 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 996 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1028,6851494879864175916,10514771213575818009,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=2352 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1180 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1028,6851494879864175916,10514771213575818009,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3684 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1412 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --field-trial-handle=1028,6851494879864175916,10514771213575818009,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=icon_reader --mojo-platform-channel-handle=3036 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1668 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1028,6851494879864175916,10514771213575818009,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3408 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1684 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,6851494879864175916,10514771213575818009,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=36 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2784 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1772 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --field-trial-handle=1028,6851494879864175916,10514771213575818009,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=icon_reader --mojo-platform-channel-handle=2624 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1800 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --field-trial-handle=1028,6851494879864175916,10514771213575818009,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1776 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1856 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1028,6851494879864175916,10514771213575818009,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3372 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2032 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1028,6851494879864175916,10514771213575818009,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3216 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
42 064
Read events
41 684
Write events
360
Delete events
20
Modification events
| (PID) Process: | (3384) OneLaunch - Package Finder_13rc4.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 380D0000D230584B4750D901 | |||
| (PID) Process: | (3384) OneLaunch - Package Finder_13rc4.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: C97387C9BD913EBBB9B3E264CBAA1102C6A4F4448237F90F00B571BEB9050D37 | |||
| (PID) Process: | (3384) OneLaunch - Package Finder_13rc4.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (3384) OneLaunch - Package Finder_13rc4.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (3384) OneLaunch - Package Finder_13rc4.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | SessionHash |
Value: C97387C9BD913EBBB9B3E264CBAA1102C6A4F4448237F90F00B571BEB9050D37 | |||
| (PID) Process: | (3384) OneLaunch - Package Finder_13rc4.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | Owner |
Value: 380D0000D230584B4750D901 | |||
| (PID) Process: | (3384) OneLaunch - Package Finder_13rc4.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (3900) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3900) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3900) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
Executable files
24
Suspicious files
314
Text files
256
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-640612B1-F3C.pma | — | |
MD5:— | SHA256:— | |||
| 3384 | OneLaunch - Package Finder_13rc4.tmp | C:\Users\admin\AppData\Local\Temp\is-0KCMB.tmp\Win32Library.dll | executable | |
MD5:— | SHA256:— | |||
| 3492 | OneLaunch - Package Finder_13rc4.exe | C:\Users\admin\AppData\Local\Temp\is-8F9VK.tmp\OneLaunch - Package Finder_13rc4.tmp | executable | |
MD5:— | SHA256:— | |||
| 3092 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Cache\index | binary | |
MD5:— | SHA256:— | |||
| 3384 | OneLaunch - Package Finder_13rc4.tmp | C:\Users\admin\AppData\Local\Temp\is-0KCMB.tmp\split_tests.json | ini | |
MD5:— | SHA256:— | |||
| 3900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 3900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 3400 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 3900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF10d6d73.TMP | text | |
MD5:64AD8ED3E666540337BA541C549F72F7 | SHA256:BECBDB08B5B37D203A85F2E974407334053BB1D2270F0B3C9A4DB963896F2206 | |||
| 3900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF10d6d63.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
32
DNS requests
23
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
868 | svchost.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvODJiQUFYYVJaZ0k5di1hUFlXS1prX2xDZw/1.0.0.13_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | US | crx | 2.81 Kb | whitelisted |
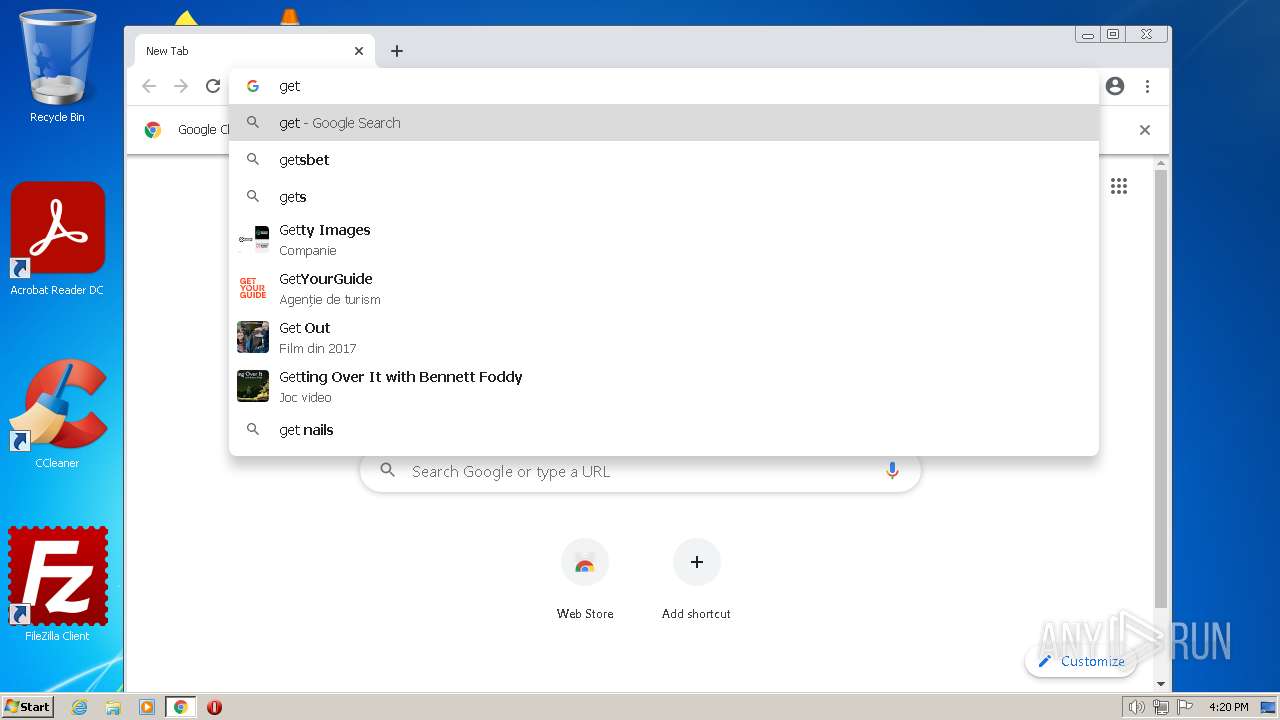
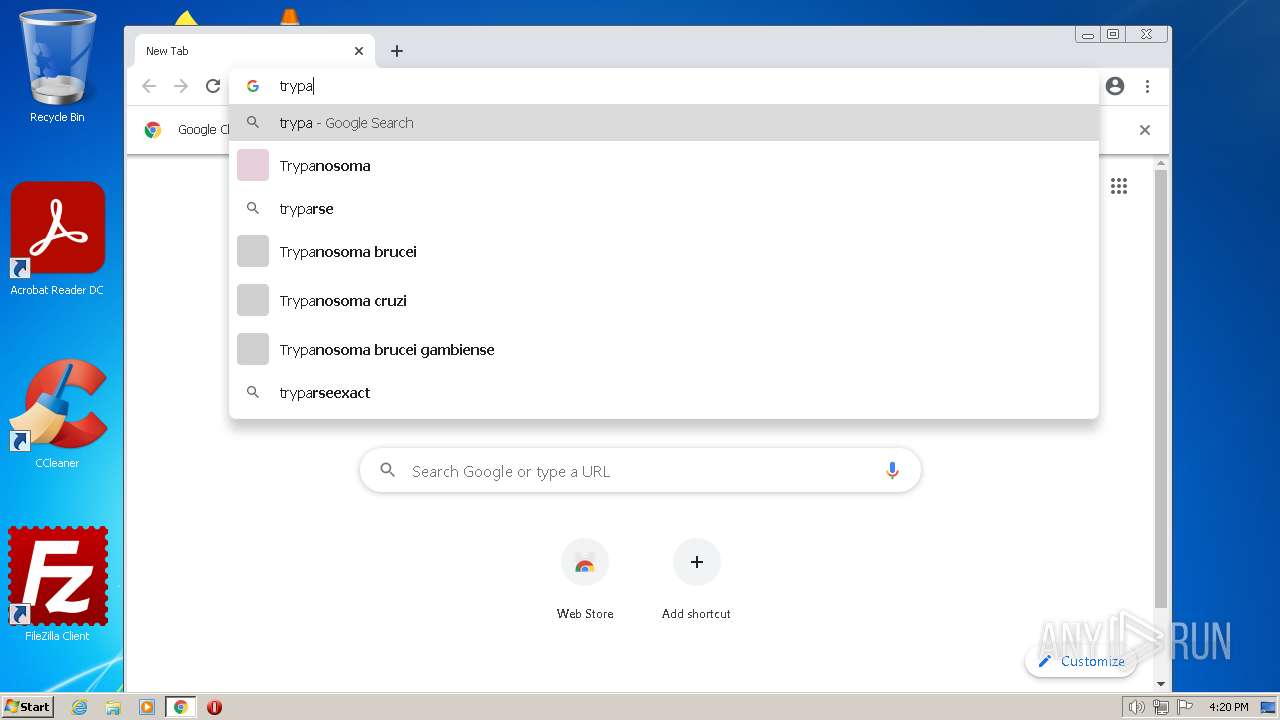
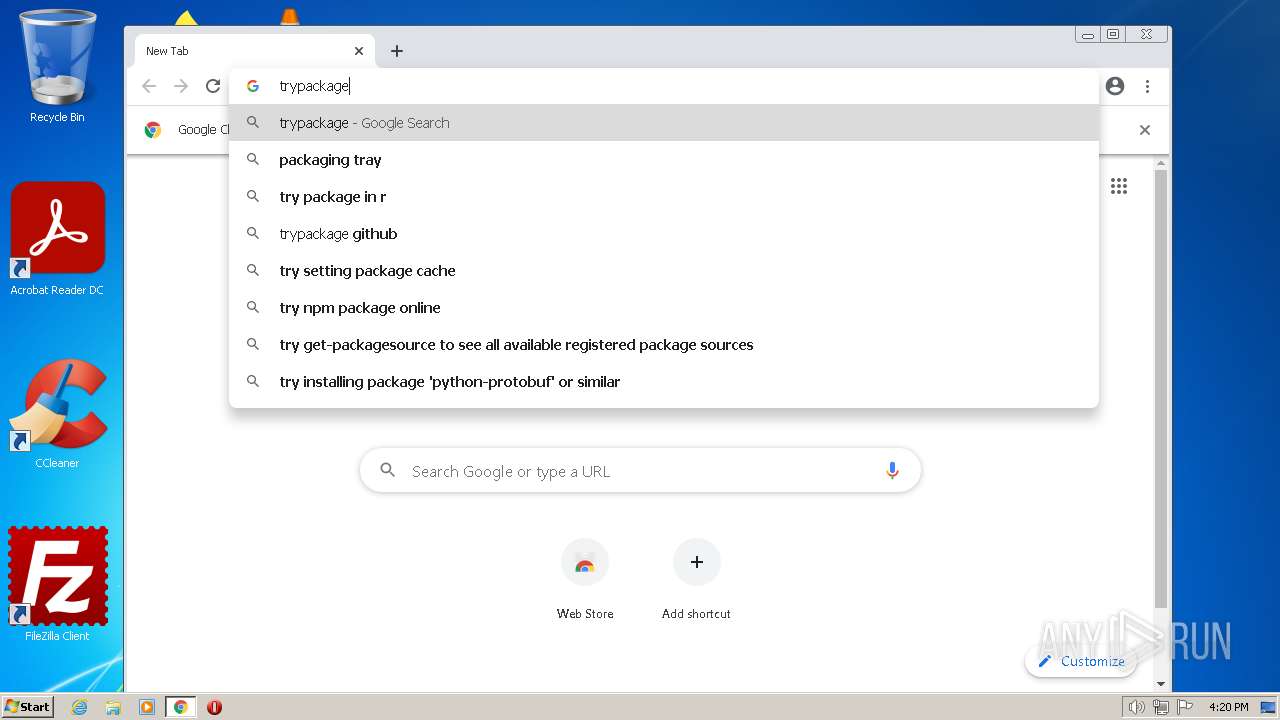
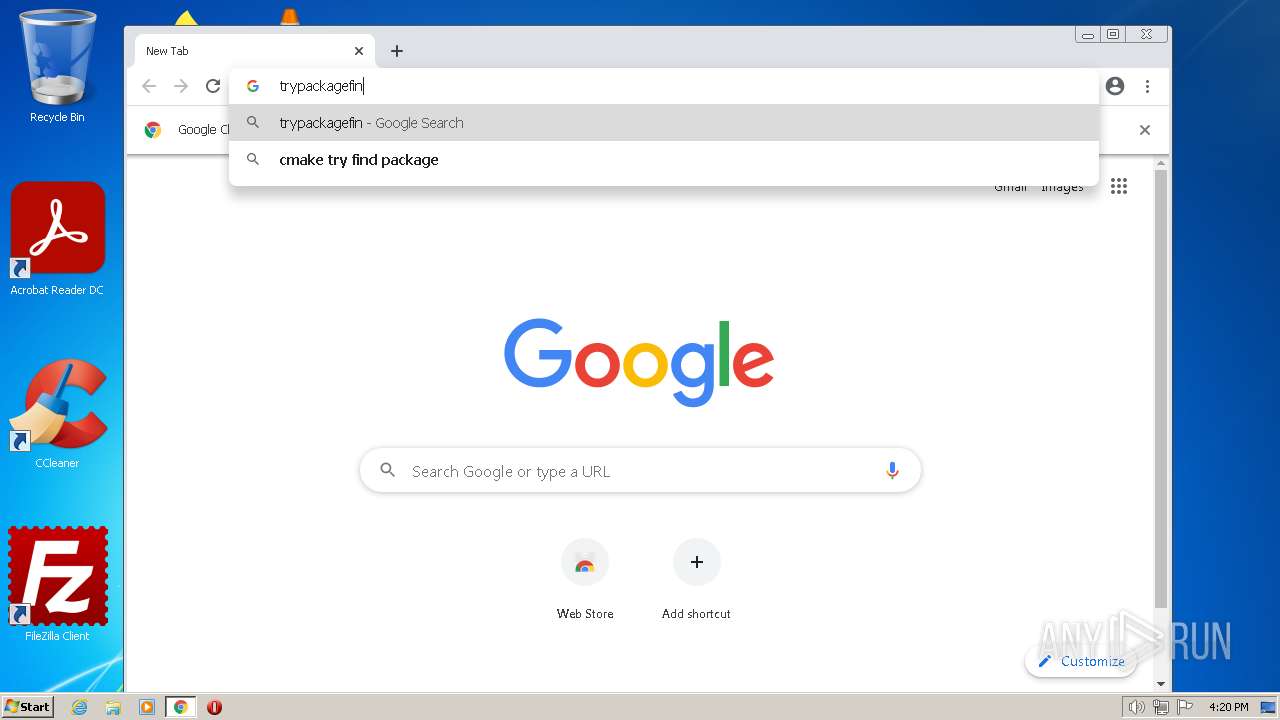
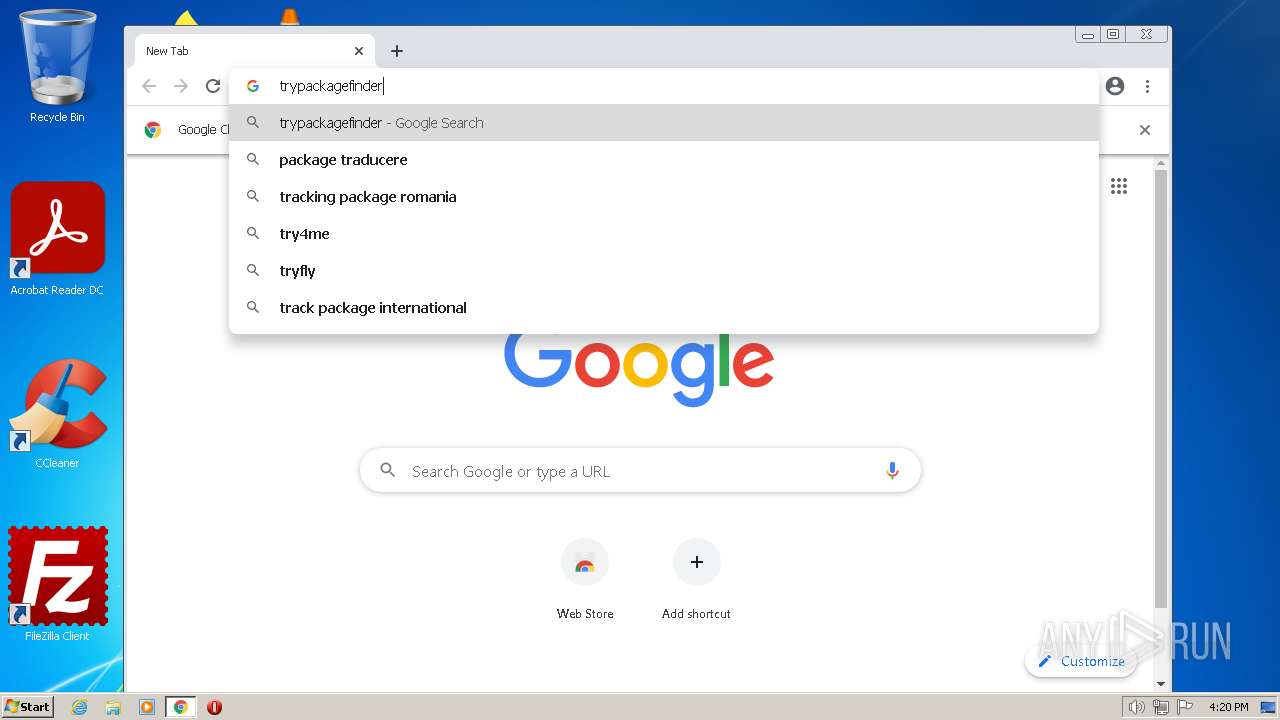
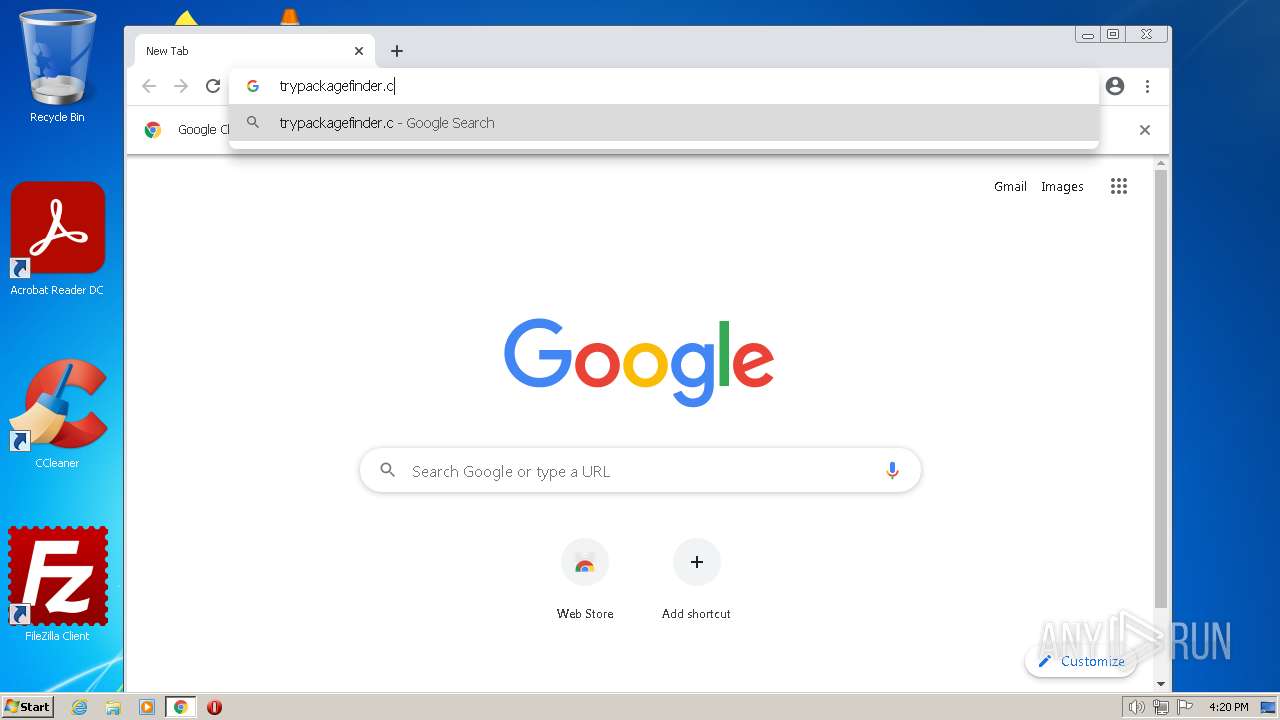
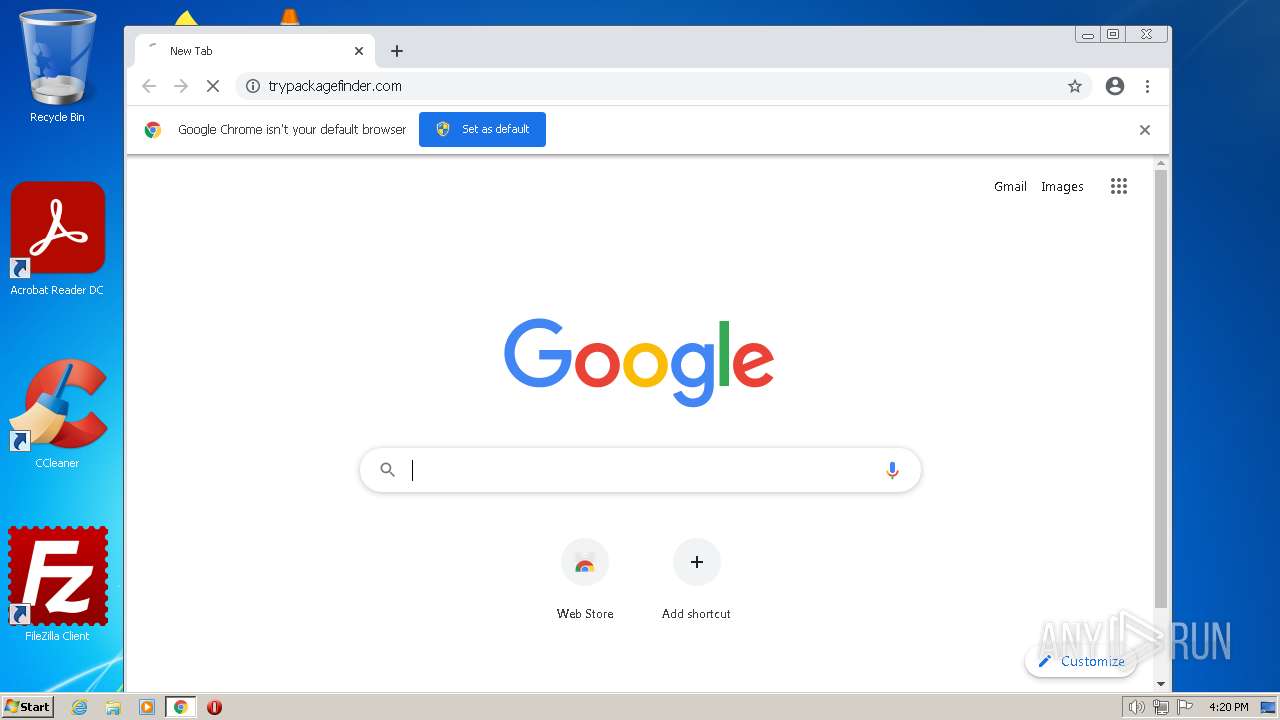
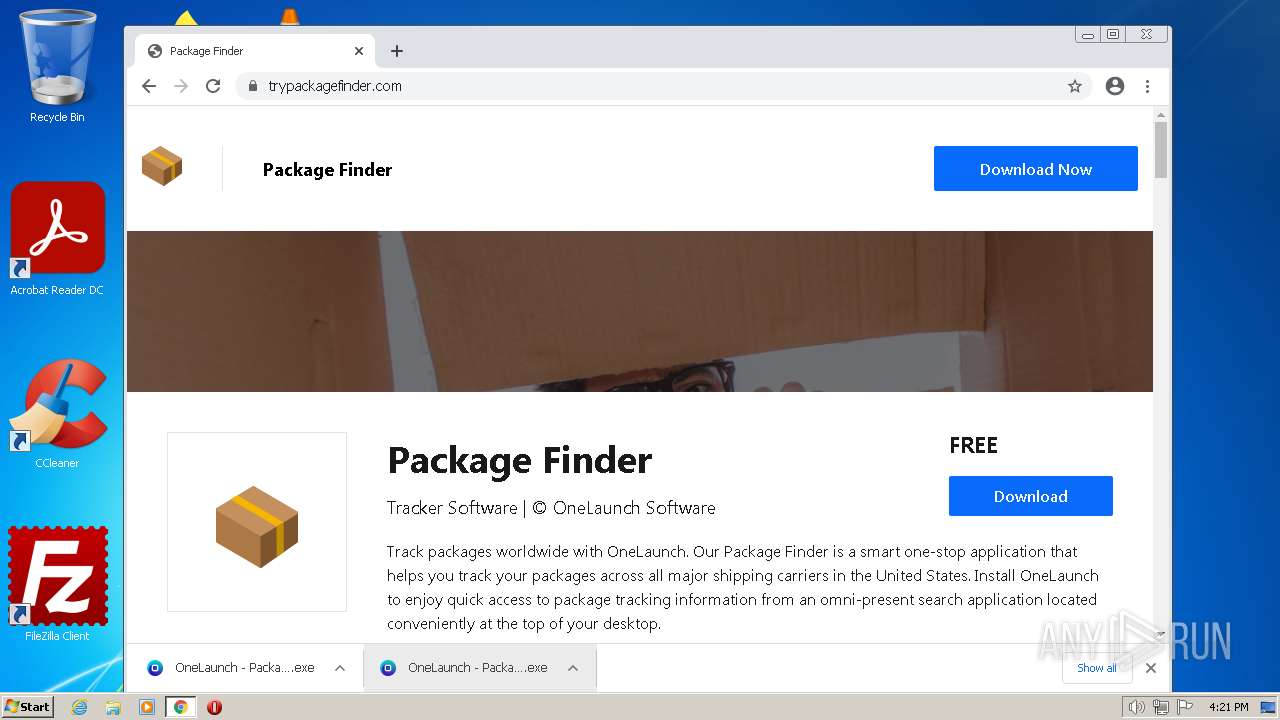
3092 | chrome.exe | GET | 301 | 188.114.97.3:80 | http://trypackagefinder.com/ | US | — | — | malicious |
868 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvODJiQUFYYVJaZ0k5di1hUFlXS1prX2xDZw/1.0.0.13_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | US | — | — | whitelisted |
3092 | chrome.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | crx | 242 Kb | whitelisted |
3092 | chrome.exe | GET | 200 | 95.140.236.0:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?9514aaef7093cb59 | GB | compressed | 61.1 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3384 | OneLaunch - Package Finder_13rc4.tmp | 13.224.189.45:443 | attribution.onelaunch.com | AMAZON-02 | US | suspicious |
3092 | chrome.exe | 172.217.18.109:443 | accounts.google.com | GOOGLE | US | suspicious |
3092 | chrome.exe | 142.250.186.110:443 | clients2.google.com | GOOGLE | US | whitelisted |
3092 | chrome.exe | 142.250.186.131:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
3092 | chrome.exe | 142.250.185.100:443 | www.google.com | GOOGLE | US | whitelisted |
3092 | chrome.exe | 142.251.208.129:443 | clients2.googleusercontent.com | GOOGLE | US | unknown |
3092 | chrome.exe | 142.250.186.163:443 | www.gstatic.com | GOOGLE | US | whitelisted |
3092 | chrome.exe | 142.250.186.99:443 | fonts.gstatic.com | GOOGLE | US | whitelisted |
3092 | chrome.exe | 172.217.16.206:443 | encrypted-tbn0.gstatic.com | GOOGLE | US | whitelisted |
3092 | chrome.exe | 172.217.18.99:443 | update.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
attribution.onelaunch.com |
| whitelisted |
accounts.google.com |
| shared |
clients2.google.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
www.google.com |
| malicious |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3384 | OneLaunch - Package Finder_13rc4.tmp | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3384 | OneLaunch - Package Finder_13rc4.tmp | Generic Protocol Command Decode | SURICATA TLS invalid record version |
3384 | OneLaunch - Package Finder_13rc4.tmp | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
3384 | OneLaunch - Package Finder_13rc4.tmp | Generic Protocol Command Decode | SURICATA TLS invalid record version |
3436 | OneLaunch - Package Finder_uqyj4.tmp | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3436 | OneLaunch - Package Finder_uqyj4.tmp | Generic Protocol Command Decode | SURICATA TLS invalid record version |
3436 | OneLaunch - Package Finder_uqyj4.tmp | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |