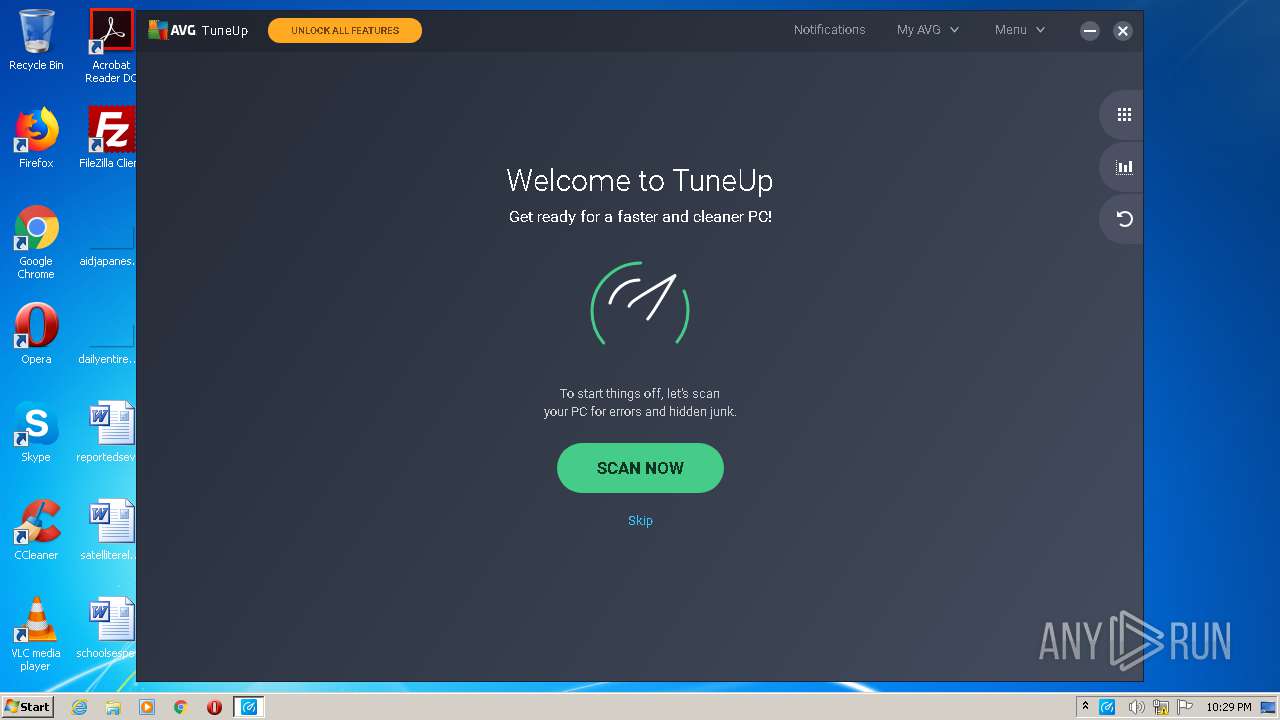
| File name: | avg_tuneup_online_setup.exe |
| Full analysis: | https://app.any.run/tasks/81905263-220e-4764-8b7f-75ed0dffb005 |
| Verdict: | Malicious activity |
| Analysis date: | September 20, 2020, 21:27:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | FAC5F8104508DDD82F5508E79E976F47 |
| SHA1: | E0976A161B0F4D2F9D148AED8B41BEB664494055 |
| SHA256: | BBD8080AC627486637DF068D8FCC2014A2740369DFDFBBDF4CC3BDFDB5D8B43D |
| SSDEEP: | 24576:rqFfPexQMBsUKMBKiSagggg8xqkVQQkmEZVYhVuPoU6ZV8grqH4Y0ODN:UOxjaYgggg8YQzjugUo8Kq4Y0yN |
MALICIOUS
Application was dropped or rewritten from another process
- icarus.exe (PID: 2916)
- icarus.exe (PID: 2420)
- icarus_ui.exe (PID: 3948)
- InstallCrt.exe (PID: 2428)
- pdfix.exe (PID: 4068)
- TuneupSvc.exe (PID: 1556)
- TuneupUI.exe (PID: 3720)
- TuneupUI.exe (PID: 2196)
- TuneupUI.exe (PID: 992)
- gf2hlp.exe (PID: 1712)
- TuneupUI.exe (PID: 2576)
Changes settings of System certificates
- avg_tuneup_online_setup.exe (PID: 3736)
- TuneupSvc.exe (PID: 1556)
Loads dropped or rewritten executable
- icarus.exe (PID: 2420)
- TuneupSvc.exe (PID: 1556)
- TuneupUI.exe (PID: 992)
- TuneupUI.exe (PID: 3720)
- TuneupUI.exe (PID: 2196)
- gf2hlp.exe (PID: 1712)
- TuneupUI.exe (PID: 2576)
Loads the Task Scheduler COM API
- icarus.exe (PID: 2420)
- TuneupSvc.exe (PID: 1556)
Changes the autorun value in the registry
- icarus.exe (PID: 2420)
Actions looks like stealing of personal data
- TuneupSvc.exe (PID: 1556)
SUSPICIOUS
Creates files in the program directory
- avg_tuneup_online_setup.exe (PID: 3736)
- icarus.exe (PID: 2916)
- icarus_ui.exe (PID: 3948)
- TuneupSvc.exe (PID: 1556)
- icarus.exe (PID: 2420)
- TuneupUI.exe (PID: 3720)
- gf2hlp.exe (PID: 1712)
Low-level read access rights to disk partition
- avg_tuneup_online_setup.exe (PID: 3736)
- icarus.exe (PID: 2916)
- icarus.exe (PID: 2420)
- TuneupSvc.exe (PID: 1556)
Adds / modifies Windows certificates
- avg_tuneup_online_setup.exe (PID: 3736)
- TuneupSvc.exe (PID: 1556)
Creates or modifies windows services
- icarus.exe (PID: 2916)
- icarus.exe (PID: 2420)
- icarus_ui.exe (PID: 3948)
- TuneupSvc.exe (PID: 1556)
- gf2hlp.exe (PID: 1712)
Executable content was dropped or overwritten
- avg_tuneup_online_setup.exe (PID: 3736)
- icarus.exe (PID: 2916)
- InstallCrt.exe (PID: 2428)
- icarus.exe (PID: 2420)
- TuneupSvc.exe (PID: 1556)
Creates files in the Windows directory
- avg_tuneup_online_setup.exe (PID: 3736)
- icarus.exe (PID: 2916)
- InstallCrt.exe (PID: 2428)
- TuneupSvc.exe (PID: 1556)
Starts itself from another location
- icarus.exe (PID: 2916)
Creates a software uninstall entry
- icarus.exe (PID: 2420)
Executed as Windows Service
- TuneupSvc.exe (PID: 1556)
- vssvc.exe (PID: 2804)
Application launched itself
- TuneupUI.exe (PID: 3720)
Creates files in the user directory
- TuneupUI.exe (PID: 3720)
Removes files from Windows directory
- icarus.exe (PID: 2916)
- avg_tuneup_online_setup.exe (PID: 3736)
- TuneupSvc.exe (PID: 1556)
Reads the cookies of Google Chrome
- TuneupSvc.exe (PID: 1556)
Reads the cookies of Mozilla Firefox
- TuneupSvc.exe (PID: 1556)
Searches for installed software
- TuneupSvc.exe (PID: 1556)
Executed via COM
- DllHost.exe (PID: 3592)
- unsecapp.exe (PID: 876)
INFO
Reads the hosts file
- icarus.exe (PID: 2916)
- icarus.exe (PID: 2420)
- TuneupSvc.exe (PID: 1556)
- TuneupUI.exe (PID: 3720)
Dropped object may contain Bitcoin addresses
- icarus.exe (PID: 2420)
- TuneupSvc.exe (PID: 1556)
Reads settings of System Certificates
- TuneupSvc.exe (PID: 1556)
Manual execution by user
- TuneupUI.exe (PID: 3720)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (43.5) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (29.8) |
| .exe | | | Generic Win/DOS Executable (13.2) |
| .exe | | | DOS Executable Generic (13.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:06:04 14:38:15+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.24 |
| CodeSize: | 770560 |
| InitializedDataSize: | 300544 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x271f0 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 20.4.757.0 |
| ProductVersionNumber: | 20.1.1906.150 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | AVG Technologies |
| FileDescription: | AVG Self-Extract Package |
| FileVersion: | 20.4.757.0 |
| InternalName: | icarus_sfx |
| LegalCopyright: | © 2020 AVG Technologies |
| OriginalFileName: | icarus_sfx.exe |
| ProductId: | avg-icarus |
| ProductName: | AVG Installer |
| ProductVersion: | 20.1.1906.150 |
| tuincluded: | 20.1.1906.150 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 04-Jun-2020 12:38:15 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | AVG Technologies |
| FileDescription: | AVG Self-Extract Package |
| FileVersion: | 20.4.757.0 |
| InternalName: | icarus_sfx |
| LegalCopyright: | © 2020 AVG Technologies |
| OriginalFilename: | icarus_sfx.exe |
| ProductId: | avg-icarus |
| ProductName: | AVG Installer |
| ProductVersion: | 20.1.1906.150 |
| tu included: | 20.1.1906.150 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000148 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 04-Jun-2020 12:38:15 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000BC024 | 0x000BC200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.64904 |
.rdata | 0x000BE000 | 0x00028812 | 0x00028A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.06842 |
.data | 0x000E7000 | 0x00008E0C | 0x00006800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.94066 |
.rsrc | 0x000F0000 | 0x0001CBB8 | 0x0001CC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.22876 |
.reloc | 0x0010D000 | 0x0000998C | 0x00009A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.60177 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.16939 | 2016 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 6.39469 | 1384 | UNKNOWN | English - United States | RT_ICON |
3 | 7.905 | 44458 | UNKNOWN | English - United States | RT_ICON |
4 | 6.35147 | 9640 | UNKNOWN | English - United States | RT_ICON |
5 | 6.53793 | 4264 | UNKNOWN | English - United States | RT_ICON |
6 | 5.7454 | 1128 | UNKNOWN | English - United States | RT_ICON |
7 | 7.96429 | 14654 | UNKNOWN | English - United States | RT_ICON |
8 | 2.79026 | 9640 | UNKNOWN | English - United States | RT_ICON |
9 | 2.98046 | 5220 | UNKNOWN | English - United States | RT_ICON |
10 | 2.74561 | 4264 | UNKNOWN | English - United States | RT_ICON |
Imports
ADVAPI32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll (delay-loaded) |
gdiplus.dll |
ntdll.dll |
ole32.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
asw_process_storage_allocate_connector | 1 | 0x00025790 |
asw_process_storage_deallocate_connector | 2 | 0x000257B0 |
on_avast_dll_unload | 3 | 0x000251C0 |
onexit_register_connector_avast_2 | 4 | 0x00025650 |
Total processes
58
Monitored processes
16
Malicious processes
11
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 876 | C:\Windows\system32\wbem\unsecapp.exe -Embedding | C:\Windows\system32\wbem\unsecapp.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Sink to receive asynchronous callbacks for WMI client application Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 992 | "C:\Program Files\AVG\TuneUp\TuneupUI.exe" --type=renderer --no-sandbox --autoplay-policy=no-user-gesture-required --field-trial-handle=2748,5806596222133412939,12565764498748329080,131072 --disable-gpu-compositing --service-pipe-token=1331049359968362853 --lang=en-US --log-file="C:\Users\admin\AppData\Roaming\AVG\TuneUp\log\cef_log.txt" --log-severity=disable --user-agent="Mozilla/5.0 AppleWebKit/537.36 (KHTML, like Gecko) Chrome/72.3.3626.1895 Safari/537.36 Avastium" --proxy-auto-detect --disable-webaudio --force-wave-audio --disable-software-rasterizer --no-sandbox --blacklist-accelerated-compositing --disable-accelerated-2d-canvas --disable-accelerated-compositing --disable-accelerated-layers --disable-accelerated-video-decode --blacklist-webgl --disable-bundled-ppapi-flash --disable-flash-3d --enable-aggressive-domstorage-flushing --enable-media-stream --allow-file-access-from-files=1 --pack_loading_disabled=1 --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1331049359968362853 --renderer-client-id=2 --mojo-platform-channel-handle=2676 /prefetch:1 | C:\Program Files\AVG\TuneUp\TuneupUI.exe | — | TuneupUI.exe | |||||||||||
User: admin Company: AVG Technologies CZ, s.r.o. Integrity Level: MEDIUM Description: AVG Cleanup UI Exit code: 0 Version: 20.1.2071.0 Modules
| |||||||||||||||
| 1556 | "C:\Program Files\AVG\TuneUp\TuneupSvc.exe" | C:\Program Files\AVG\TuneUp\TuneupSvc.exe | services.exe | ||||||||||||
User: SYSTEM Company: AVG Technologies CZ, s.r.o. Integrity Level: SYSTEM Description: AVG Cleanup Service Exit code: 0 Version: 20.1.2071.0 Modules
| |||||||||||||||
| 1712 | "C:\Program Files\AVG\TuneUp\gf2hlp.exe" /analyze recycleBin | C:\Program Files\AVG\TuneUp\gf2hlp.exe | — | TuneupSvc.exe | |||||||||||
User: admin Company: AVG Technologies CZ, s.r.o. Integrity Level: HIGH Description: AVG Cleanup Helper Application Exit code: 1 Version: 20.1.2071.0 Modules
| |||||||||||||||
| 2196 | "C:\Program Files\AVG\TuneUp\TuneupUI.exe" --type=gpu-process --field-trial-handle=2748,5806596222133412939,12565764498748329080,131072 --no-sandbox --log-file="C:\Users\admin\AppData\Roaming\AVG\TuneUp\log\cef_log.txt" --log-severity=disable --user-agent="Mozilla/5.0 AppleWebKit/537.36 (KHTML, like Gecko) Chrome/72.3.3626.1895 Safari/537.36 Avastium" --lang=en-US --proxy-auto-detect --disable-webaudio --force-wave-audio --disable-software-rasterizer --no-sandbox --blacklist-accelerated-compositing --disable-accelerated-2d-canvas --disable-accelerated-compositing --disable-accelerated-layers --disable-accelerated-video-decode --blacklist-webgl --disable-bundled-ppapi-flash --disable-flash-3d --enable-aggressive-domstorage-flushing --enable-media-stream --allow-file-access-from-files=1 --pack_loading_disabled=1 --gpu-preferences=KAAAAAAAAACAAwCAAQAAAAAAAAAAAGAAAAAAAAMAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --use-gl=swiftshader-webgl --service-request-channel-token=10257199303931883804 --mojo-platform-channel-handle=2652 /prefetch:2 | C:\Program Files\AVG\TuneUp\TuneupUI.exe | — | TuneupUI.exe | |||||||||||
User: admin Company: AVG Technologies CZ, s.r.o. Integrity Level: MEDIUM Description: AVG Cleanup UI Exit code: 0 Version: 20.1.2071.0 Modules
| |||||||||||||||
| 2420 | C:\Windows\Temp\asw-66dbd362-4c10-41c9-9463-84e32b422dda\avg-tu\icarus.exe /er_master:master_ep_d8cb2668-81b8-428a-a66e-f7cd5cb88e83 /er_ui:ui_ep_06e69318-0ae0-41e1-93ad-f3a4dffd2362 /er_slave:avg-tu_slave_ep_4ef8a274-e6b5-435c-93e6-2964579e1ba8 /slave:avg-tu | C:\Windows\Temp\asw-66dbd362-4c10-41c9-9463-84e32b422dda\avg-tu\icarus.exe | icarus.exe | ||||||||||||
User: admin Company: AVG Technologies Integrity Level: HIGH Description: AVG Installer Exit code: 0 Version: 20.4.1269.0 Modules
| |||||||||||||||
| 2428 | "C:\Program Files\AVG\TuneUp\CRT\InstallCrt.exe" /avg /v140 /debug /release | C:\Program Files\AVG\TuneUp\CRT\InstallCrt.exe | icarus.exe | ||||||||||||
User: admin Company: AVG Technologies CZ, s.r.o. Integrity Level: HIGH Description: AVG Internet Security System Installer Exit code: 0 Version: 20.1.5034.0 Modules
| |||||||||||||||
| 2576 | "C:\Program Files\AVG\TuneUp\TuneupUI.exe" --type=gpu-process --field-trial-handle=2748,5806596222133412939,12565764498748329080,131072 --disable-gpu-sandbox --use-gl=disabled --no-sandbox --log-file="C:\Users\admin\AppData\Roaming\AVG\TuneUp\log\cef_log.txt" --log-severity=disable --user-agent="Mozilla/5.0 AppleWebKit/537.36 (KHTML, like Gecko) Chrome/72.3.3626.1895 Safari/537.36 Avastium" --lang=en-US --proxy-auto-detect --disable-webaudio --force-wave-audio --disable-software-rasterizer --no-sandbox --blacklist-accelerated-compositing --disable-accelerated-2d-canvas --disable-accelerated-compositing --disable-accelerated-layers --disable-accelerated-video-decode --blacklist-webgl --disable-bundled-ppapi-flash --disable-flash-3d --enable-aggressive-domstorage-flushing --enable-media-stream --allow-file-access-from-files=1 --pack_loading_disabled=1 --gpu-preferences=KAAAAAAAAACAAwCAAQAAAAAAAAAAAGAAAAAAAAMAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --use-gl=swiftshader-webgl --service-request-channel-token=5979180332344827878 --mojo-platform-channel-handle=3076 /prefetch:2 | C:\Program Files\AVG\TuneUp\TuneupUI.exe | — | TuneupUI.exe | |||||||||||
User: admin Company: AVG Technologies CZ, s.r.o. Integrity Level: MEDIUM Description: AVG Cleanup UI Exit code: 0 Version: 20.1.2071.0 Modules
| |||||||||||||||
| 2716 | "C:\Users\admin\AppData\Local\Temp\avg_tuneup_online_setup.exe" | C:\Users\admin\AppData\Local\Temp\avg_tuneup_online_setup.exe | — | explorer.exe | |||||||||||
User: admin Company: AVG Technologies Integrity Level: MEDIUM Description: AVG Self-Extract Package Exit code: 3221226540 Version: 20.4.757.0 Modules
| |||||||||||||||
| 2804 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
4 977
Read events
4 793
Write events
182
Delete events
2
Modification events
| (PID) Process: | (3736) avg_tuneup_online_setup.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3736) avg_tuneup_online_setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\5FB7EE0633E259DBAD0C4C9AE6D38F1A61C7DC25 |
| Operation: | write | Name: | Blob |
Value: 040000000100000010000000D474DE575C39B2D39C8583C5C065498A0F0000000100000014000000E35EF08D884F0A0ADE2F75E96301CE6230F213A80300000001000000140000005FB7EE0633E259DBAD0C4C9AE6D38F1A61C7DC251D00000001000000100000008F76B981D528AD4770088245E2031B630B0000000100000012000000440069006700690043006500720074000000140000000100000014000000B13EC36903F8BF4701D498261A0802EF63642BC36200000001000000200000007431E5F4C3C1CE4690774F0B61E05440883BA9A01ED00BA6ABD7806ED3B118CF5300000001000000230000003021301F06096086480186FD6C020130123010060A2B0601040182373C0101030200C0090000000100000034000000303206082B0601050507030106082B0601050507030206082B0601050507030406082B0601050507030306082B06010505070308190000000100000010000000BA4F3972E7AED9DCCDC210DB59DA13C92000000001000000C9030000308203C5308202ADA003020102021002AC5C266A0B409B8F0B79F2AE462577300D06092A864886F70D0101050500306C310B300906035504061302555331153013060355040A130C446967694365727420496E6331193017060355040B13107777772E64696769636572742E636F6D312B30290603550403132244696769436572742048696768204173737572616E636520455620526F6F74204341301E170D3036313131303030303030305A170D3331313131303030303030305A306C310B300906035504061302555331153013060355040A130C446967694365727420496E6331193017060355040B13107777772E64696769636572742E636F6D312B30290603550403132244696769436572742048696768204173737572616E636520455620526F6F7420434130820122300D06092A864886F70D01010105000382010F003082010A0282010100C6CCE573E6FBD4BBE52D2D32A6DFE5813FC9CD2549B6712AC3D5943467A20A1CB05F69A640B1C4B7B28FD098A4A941593AD3DC94D63CDB7438A44ACC4D2582F74AA5531238EEF3496D71917E63B6ABA65FC3A484F84F6251BEF8C5ECDB3892E306E508910CC4284155FBCB5A89157E71E835BF4D72093DBE3A38505B77311B8DB3C724459AA7AC6D00145A04B7BA13EB510A984141224E656187814150A6795C89DE194A57D52EE65D1C532C7E98CD1A0616A46873D03404135CA171D35A7C55DB5E64E13787305604E511B4298012F1793988A202117C2766B788B778F2CA0AA838AB0A64C2BF665D9584C1A1251E875D1A500B2012CC41BB6E0B5138B84BCB0203010001A3633061300E0603551D0F0101FF040403020186300F0603551D130101FF040530030101FF301D0603551D0E04160414B13EC36903F8BF4701D498261A0802EF63642BC3301F0603551D23041830168014B13EC36903F8BF4701D498261A0802EF63642BC3300D06092A864886F70D010105050003820101001C1A0697DCD79C9F3C886606085721DB2147F82A67AABF183276401057C18AF37AD911658E35FA9EFC45B59ED94C314BB891E8432C8EB378CEDBE3537971D6E5219401DA55879A2464F68A66CCDE9C37CDA834B1699B23C89E78222B7043E35547316119EF58C5852F4E30F6A0311623C8E7E2651633CBBF1A1BA03DF8CA5E8B318B6008892D0C065C52B7C4F90A98D1155F9F12BE7C366338BD44A47FE4262B0AC497690DE98CE2C01057B8C876129155F24869D8BC2A025B0F44D42031DBF4BA70265D90609EBC4B17092FB4CB1E4368C90727C1D25CF7EA21B968129C3C9CBF9EFC805C9B63CDEC47AA252767A037F300827D54D7A9F8E92E13A377E81F4A | |||
| (PID) Process: | (2916) icarus.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\partmgr |
| Operation: | write | Name: | EnableCounterForIoctl |
Value: 1 | |||
| (PID) Process: | (2916) icarus.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Session Manager |
| Operation: | write | Name: | BootExecute |
Value: autocheck autochk * | |||
| (PID) Process: | (2916) icarus.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\Software\AVG\Icarus |
| Operation: | write | Name: | DataFolder |
Value: C:\ProgramData\AVG\Icarus | |||
| (PID) Process: | (2420) icarus.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\partmgr |
| Operation: | write | Name: | EnableCounterForIoctl |
Value: 1 | |||
| (PID) Process: | (3948) icarus_ui.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\partmgr |
| Operation: | write | Name: | EnableCounterForIoctl |
Value: 1 | |||
| (PID) Process: | (2428) InstallCrt.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\SideBySide\Winners\x86_avg.vc140.crt_f92d94485545da78_none_4494295e9dc491b0 |
| Operation: | write | Name: | (default) |
Value: 14.0 | |||
| (PID) Process: | (2428) InstallCrt.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\SideBySide\Winners\x86_avg.vc140.crt_f92d94485545da78_none_4494295e9dc491b0\14.0 |
| Operation: | write | Name: | 14.0.28127.0 |
Value: 01 | |||
| (PID) Process: | (2428) InstallCrt.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\SideBySide\Winners\x86_avg.vc140.crt_f92d94485545da78_none_4494295e9dc491b0\14.0 |
| Operation: | write | Name: | (default) |
Value: 14.0.28127.0 | |||
Executable files
229
Suspicious files
73
Text files
264
Unknown types
148
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3736 | avg_tuneup_online_setup.exe | C:\ProgramData\AVG\Icarus\Logs\sfx.log | — | |
MD5:— | SHA256:— | |||
| 3736 | avg_tuneup_online_setup.exe | C:\Windows\Temp\asw-66dbd362-4c10-41c9-9463-84e32b422dda\common\388876c1-a80c-4961-a4ca-b31035a5073e | — | |
MD5:— | SHA256:— | |||
| 3736 | avg_tuneup_online_setup.exe | C:\Windows\Temp\asw-66dbd362-4c10-41c9-9463-84e32b422dda\common\13b63799-537e-452f-a646-9d18051d53c8 | — | |
MD5:— | SHA256:— | |||
| 3736 | avg_tuneup_online_setup.exe | C:\Windows\Temp\asw-66dbd362-4c10-41c9-9463-84e32b422dda\common\0b0c02c5-06f2-4cf6-bfb0-d0dc691c9bde | — | |
MD5:— | SHA256:— | |||
| 3736 | avg_tuneup_online_setup.exe | C:\Windows\Temp\asw-66dbd362-4c10-41c9-9463-84e32b422dda\common\254298dd-9a57-4d5c-a346-d59cb2a1902e | — | |
MD5:— | SHA256:— | |||
| 3736 | avg_tuneup_online_setup.exe | C:\Windows\Temp\asw-66dbd362-4c10-41c9-9463-84e32b422dda\common\92f0286f-9f35-4974-8321-2348c259d59f | — | |
MD5:— | SHA256:— | |||
| 3736 | avg_tuneup_online_setup.exe | C:\Windows\Temp\asw-66dbd362-4c10-41c9-9463-84e32b422dda\common\a13fa5d6-3057-4444-96f2-a75b5ecad15f | — | |
MD5:— | SHA256:— | |||
| 3736 | avg_tuneup_online_setup.exe | C:\Windows\Temp\asw-66dbd362-4c10-41c9-9463-84e32b422dda\common\6b28ea1c-2e86-417c-91b7-c600d97e5da5 | — | |
MD5:— | SHA256:— | |||
| 3736 | avg_tuneup_online_setup.exe | C:\Windows\Temp\asw-66dbd362-4c10-41c9-9463-84e32b422dda\common\5d843cea-71b1-4ed4-9c55-1606de6c5384 | — | |
MD5:— | SHA256:— | |||
| 3736 | avg_tuneup_online_setup.exe | C:\Windows\Temp\asw-66dbd362-4c10-41c9-9463-84e32b422dda\common\bbc13f48-8dab-4d98-92ba-5c7ee1e04941 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
50
DNS requests
38
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | US | der | 471 b | whitelisted |
— | — | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEAJVTZToyhkouZlB2YFfERY%3D | US | der | 471 b | whitelisted |
1556 | TuneupSvc.exe | POST | 200 | 69.94.69.211:80 | http://software-cleanup.ff.avast.com/scan | US | binary | 1.83 Kb | unknown |
— | — | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | US | der | 471 b | whitelisted |
3736 | avg_tuneup_online_setup.exe | GET | 404 | 104.111.215.183:80 | http://honzik.avcdn.net/dll/avg-tu/x86/icarus_mod.dll.lzma | NL | html | 232 b | whitelisted |
— | — | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEAJVTZToyhkouZlB2YFfERY%3D | US | der | 471 b | whitelisted |
1556 | TuneupSvc.exe | GET | 200 | 2.16.177.50:80 | http://ncc.avast.com/ncc.txt | unknown | text | 26 b | whitelisted |
1556 | TuneupSvc.exe | GET | 200 | 2.16.177.120:80 | http://ncc.avast.com/ncc.txt | unknown | text | 26 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3736 | avg_tuneup_online_setup.exe | 5.62.40.211:443 | analytics.ff.avast.com | AVAST Software s.r.o. | DE | unknown |
3736 | avg_tuneup_online_setup.exe | 104.111.215.183:443 | honzik.avcdn.net | Akamai International B.V. | NL | whitelisted |
3736 | avg_tuneup_online_setup.exe | 104.111.215.183:80 | honzik.avcdn.net | Akamai International B.V. | NL | whitelisted |
2916 | icarus.exe | 5.62.40.213:443 | analytics.ff.avast.com | AVAST Software s.r.o. | DE | unknown |
2916 | icarus.exe | 5.62.44.66:443 | shepherd.ff.avast.com | AVAST Software s.r.o. | US | suspicious |
2420 | icarus.exe | 104.111.215.183:443 | honzik.avcdn.net | Akamai International B.V. | NL | whitelisted |
2916 | icarus.exe | 5.62.40.211:443 | analytics.ff.avast.com | AVAST Software s.r.o. | DE | unknown |
1556 | TuneupSvc.exe | 2.16.177.120:80 | ncc.avast.com | Akamai International B.V. | — | unknown |
1556 | TuneupSvc.exe | 2.16.177.50:80 | ncc.avast.com | Akamai International B.V. | — | unknown |
1556 | TuneupSvc.exe | 5.62.40.213:443 | analytics.ff.avast.com | AVAST Software s.r.o. | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
analytics.ff.avast.com |
| whitelisted |
honzik.avcdn.net |
| unknown |
shepherd.ff.avast.com |
| whitelisted |
ssl.google-analytics.com |
| whitelisted |
ncc.avast.com |
| whitelisted |
alpha-license-dealer.ff.avast.com |
| whitelisted |
aus5.mozilla.org |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
auth.ff.avast.com |
| whitelisted |
software-cleanup.ff.avast.com |
| unknown |
Threats
Process | Message |
|---|---|
icarus_ui.exe | SAPI.request (setup.get.product.name), data(null)
|
icarus_ui.exe | SAPI request:(setup.get.os_supported) failed (-1)
|
icarus_ui.exe | SAPI.request (setup.get.language), data(null)
|
icarus_ui.exe | SAPI.request (setup.get.os_supported), data(null)
|
icarus_ui.exe | SAPI.request (setup.get.path), data(null)
|
icarus_ui.exe | SAPI.request (setup.get.mode), data(null)
|
icarus_ui.exe | SAPI.request (setup.get.cmdline), data(null)
|
icarus_ui.exe | SAPI.request (product.get.blocking.apps), data({"product-id":"avg-tu"})
|
icarus_ui.exe | SAPI.request (setup.get.versions), data(null)
|
icarus_ui.exe | SAPI.response (setup.get.language) data=({"lng_id":"en-us"})
|