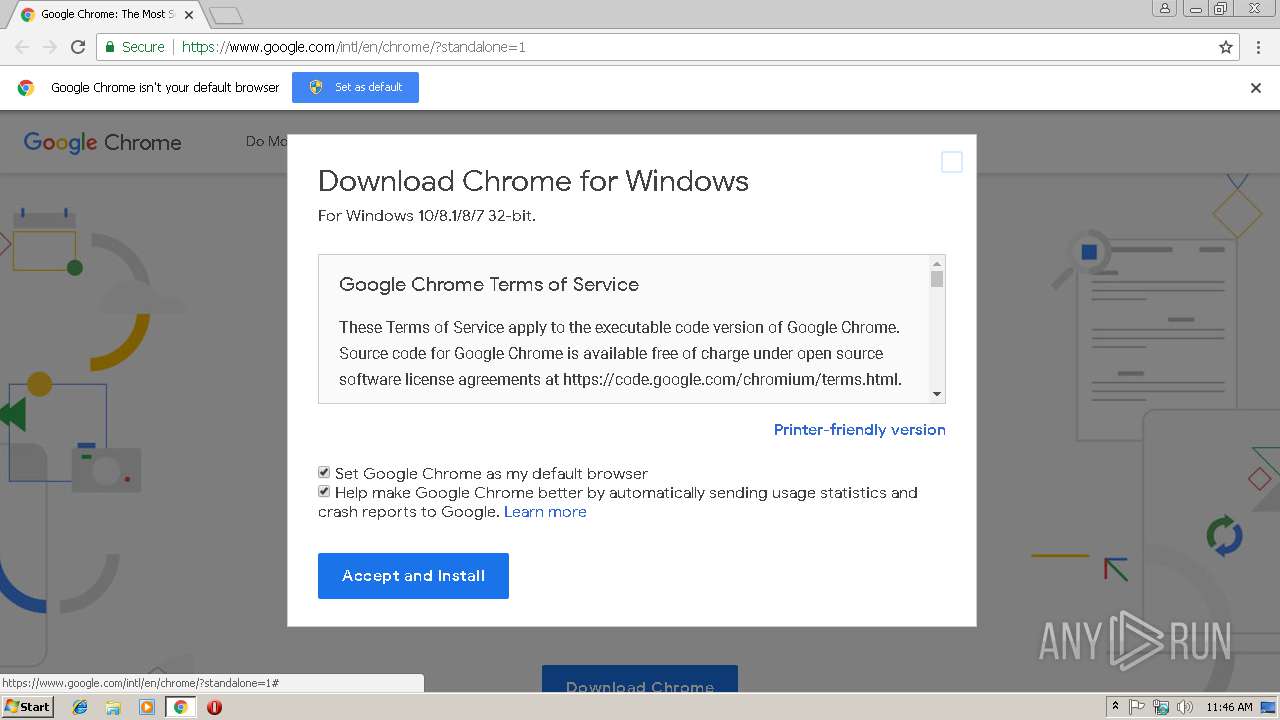
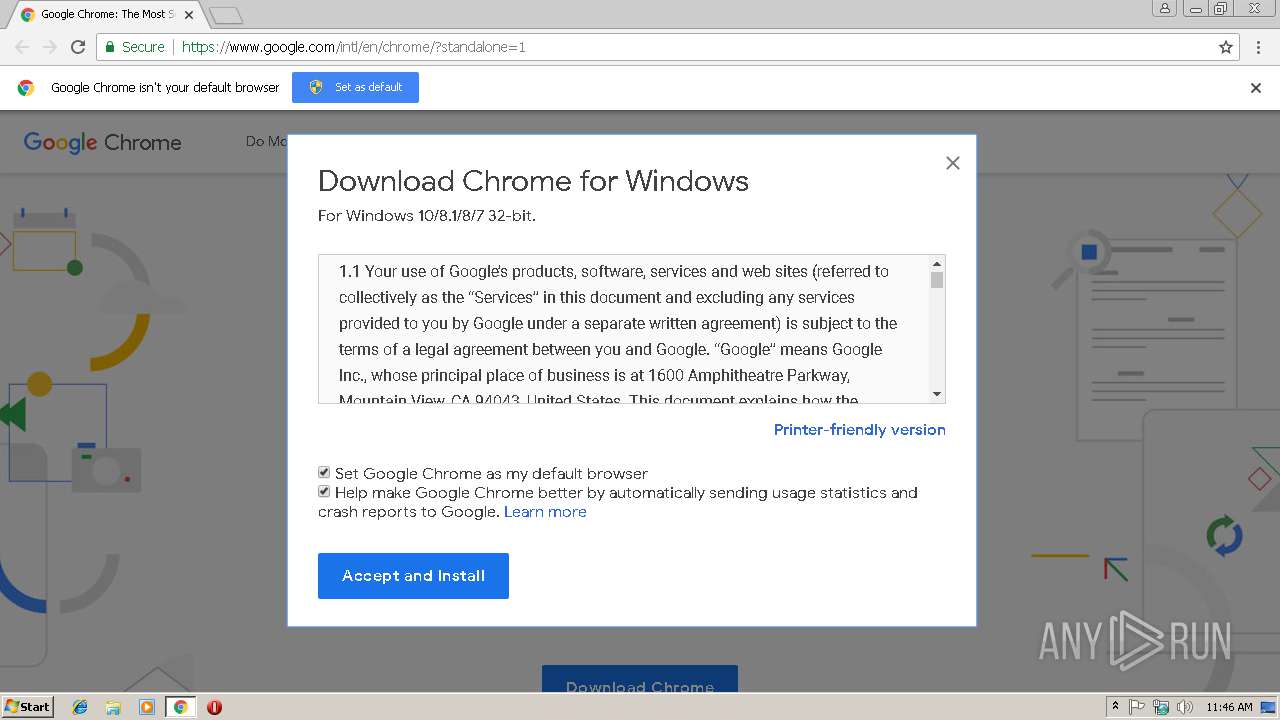
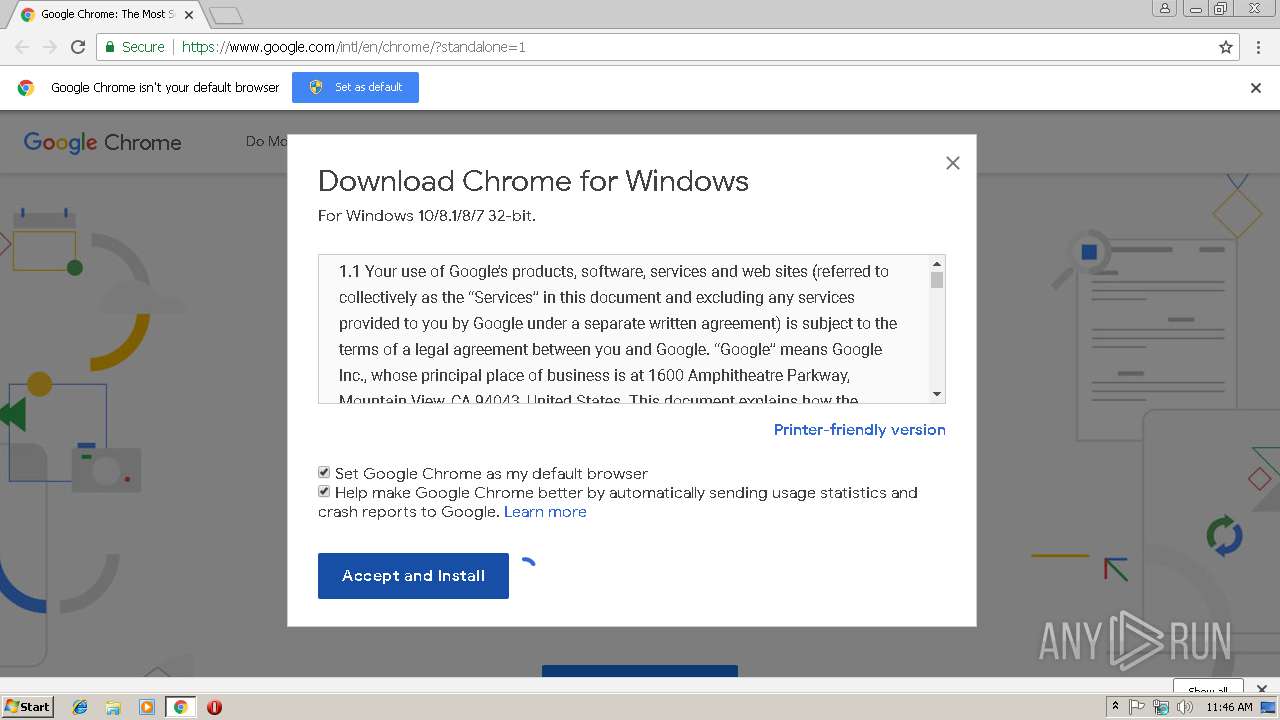
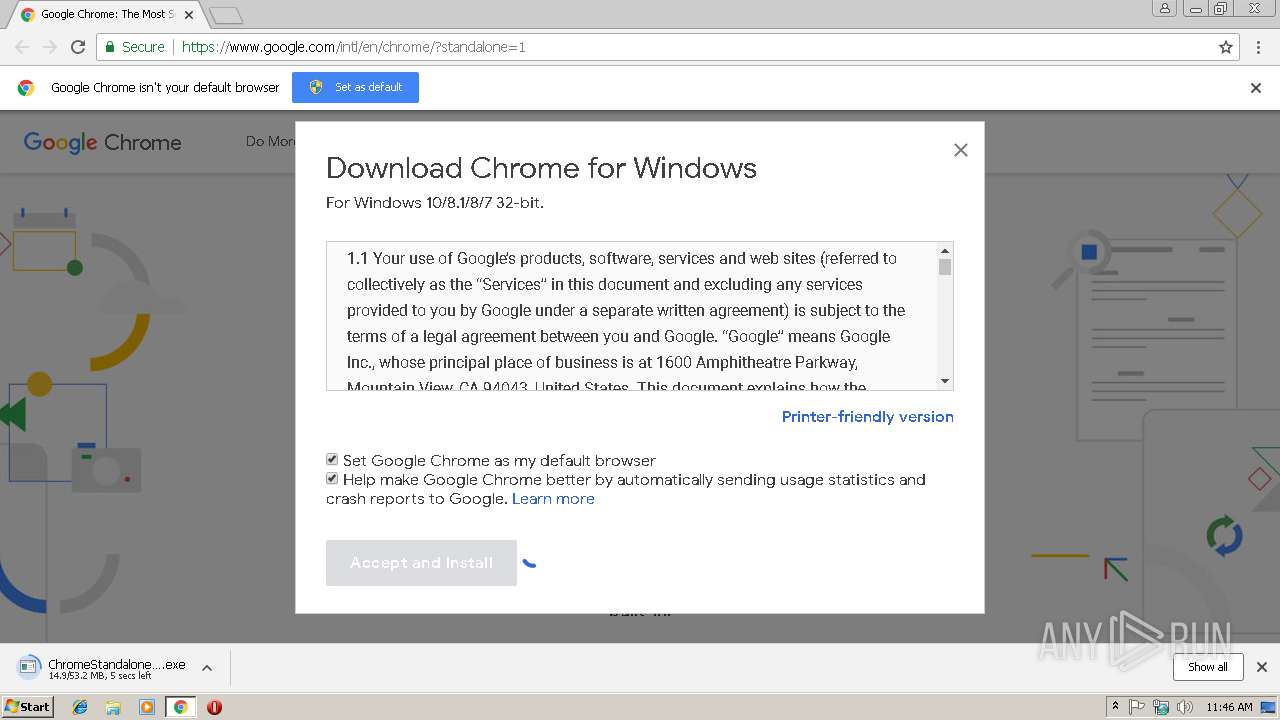
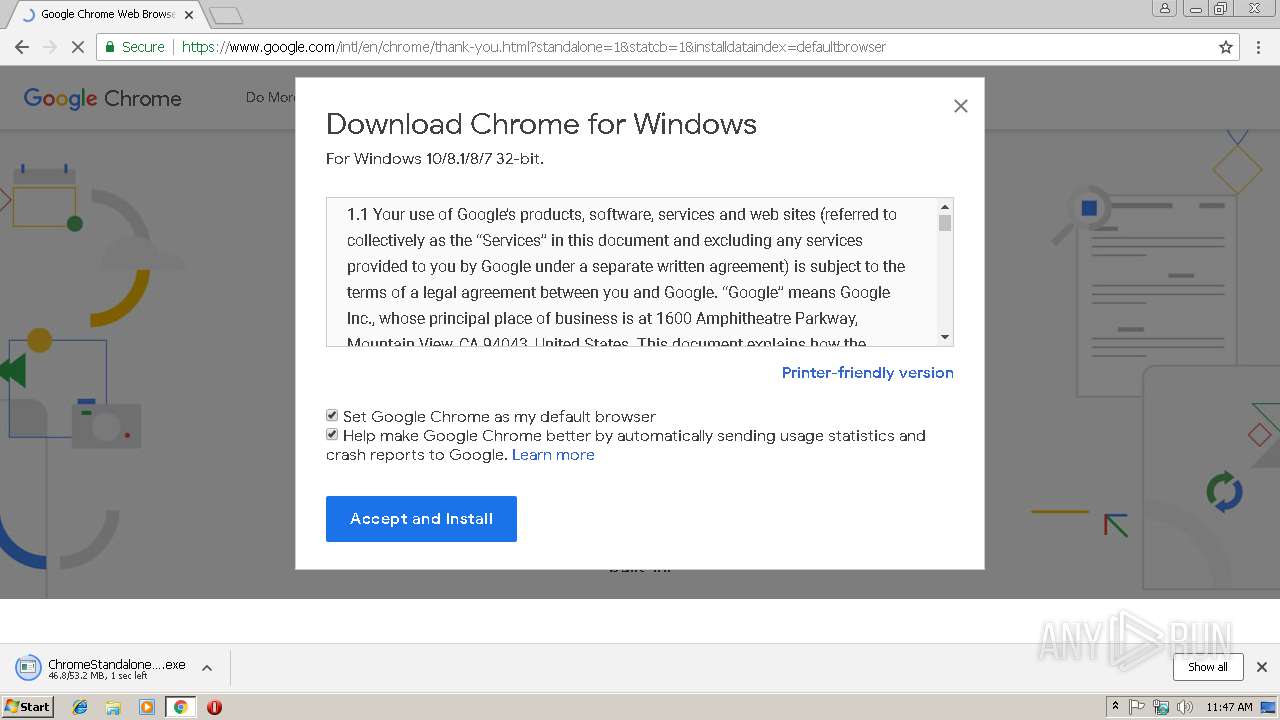
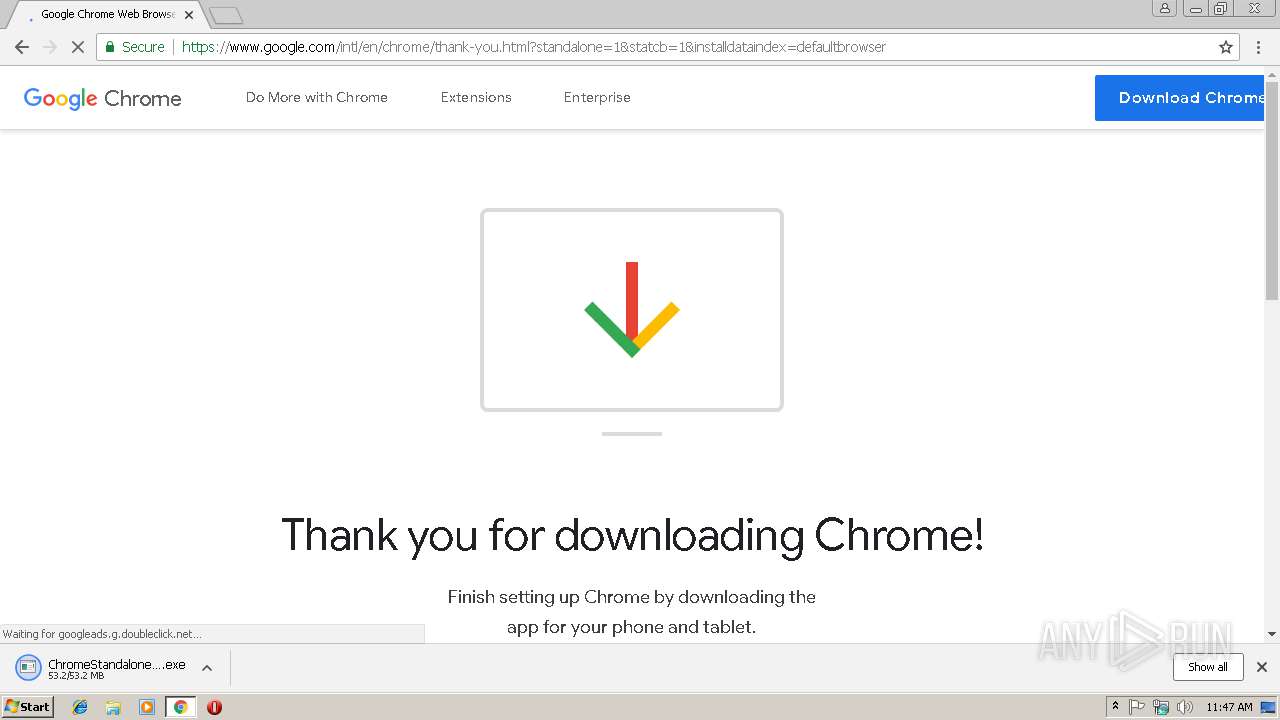
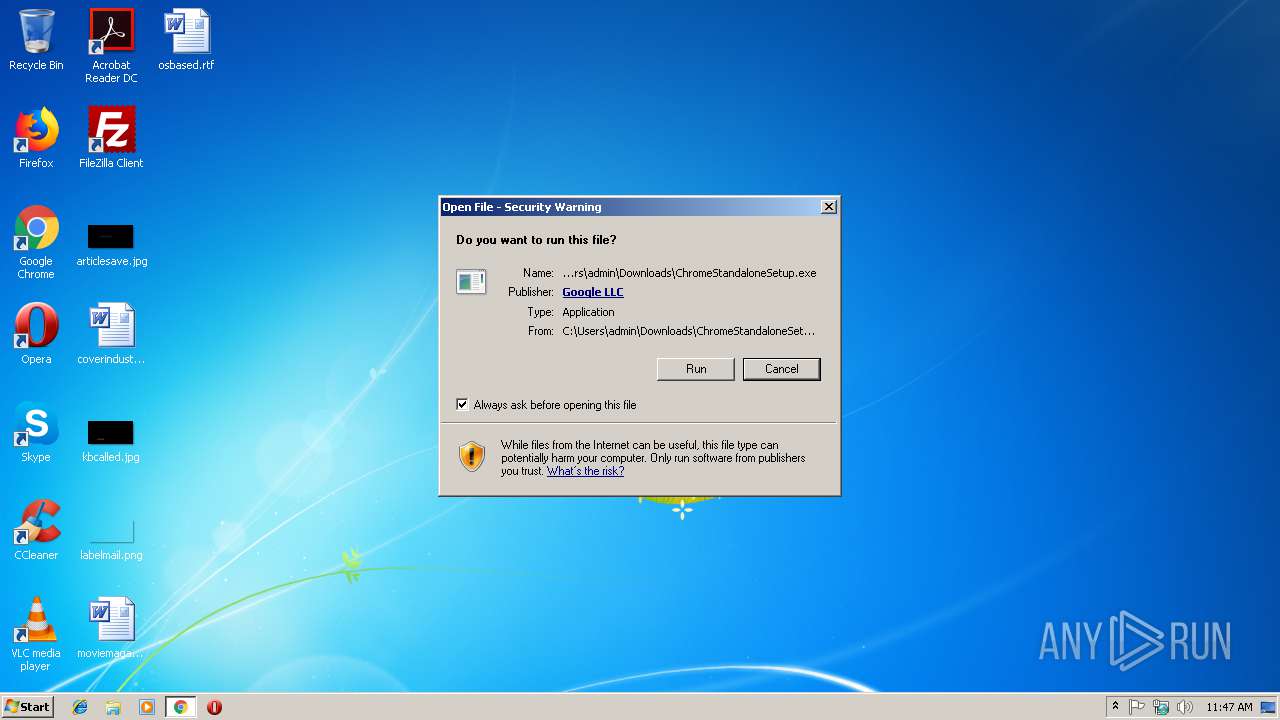
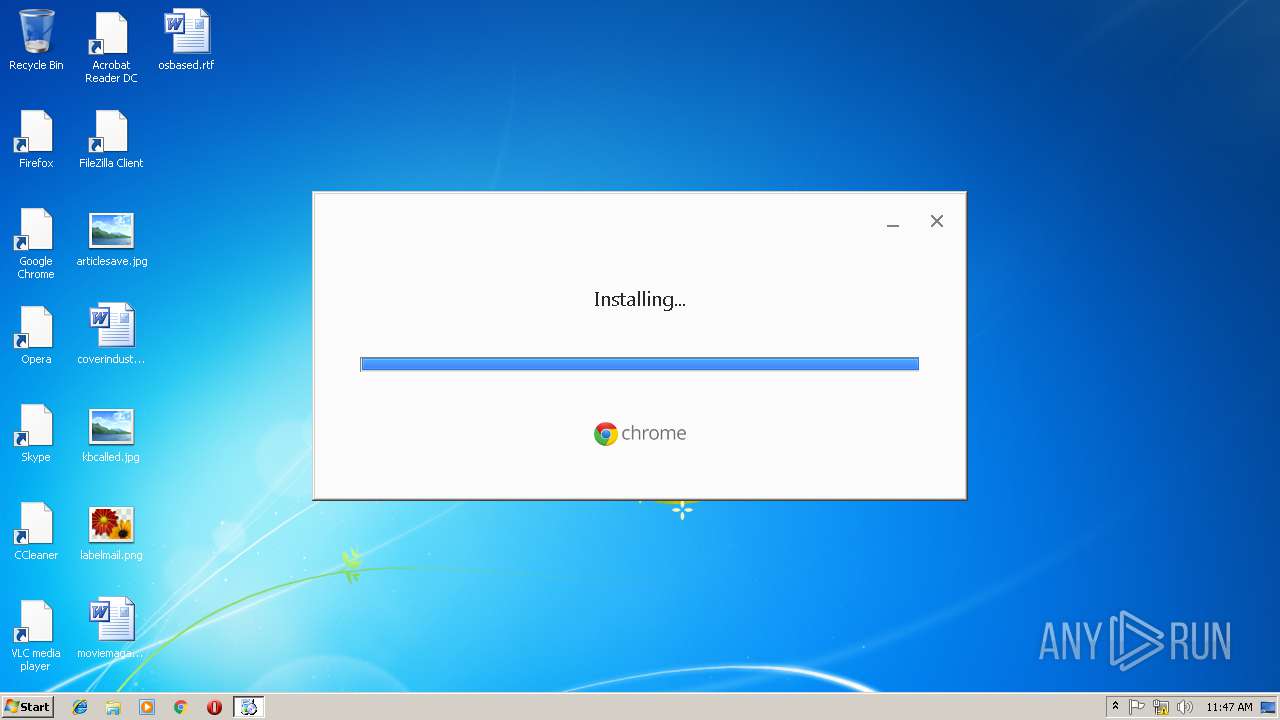
| URL: | https://www.google.com/intl/en/chrome/?standalone=1 |
| Full analysis: | https://app.any.run/tasks/4c057862-323a-4101-b5a5-b00c7b5f32e4 |
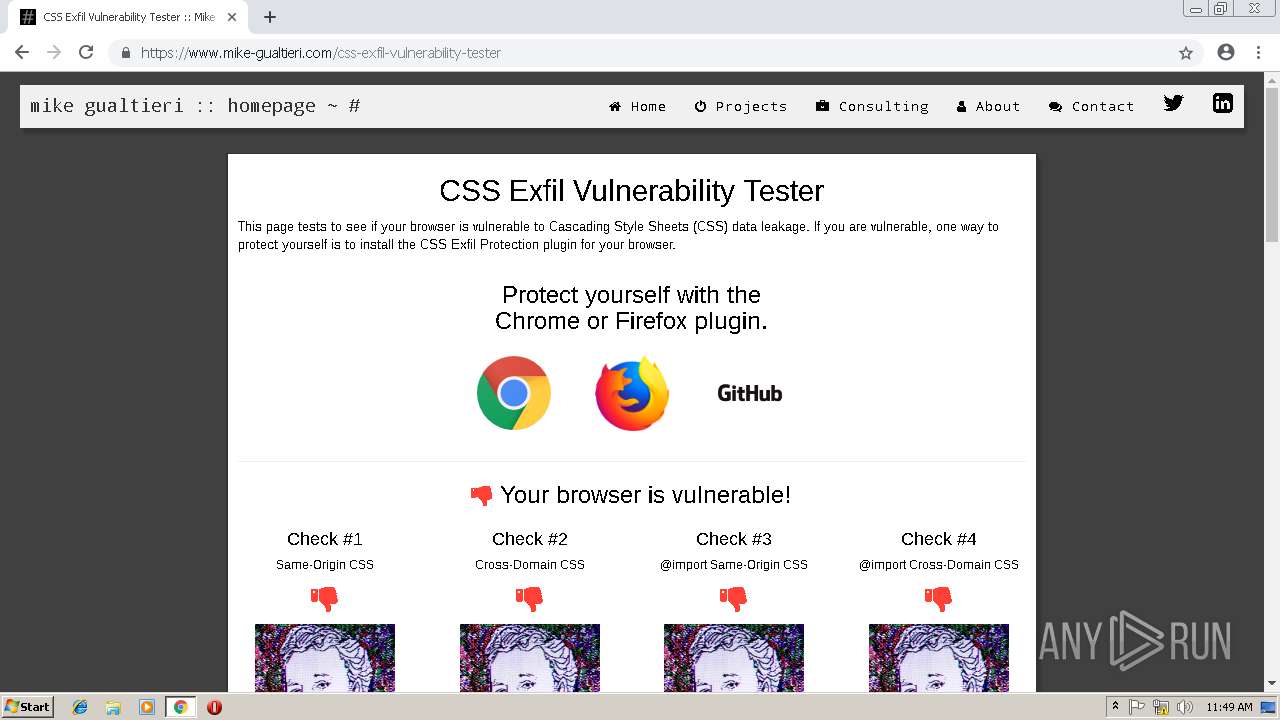
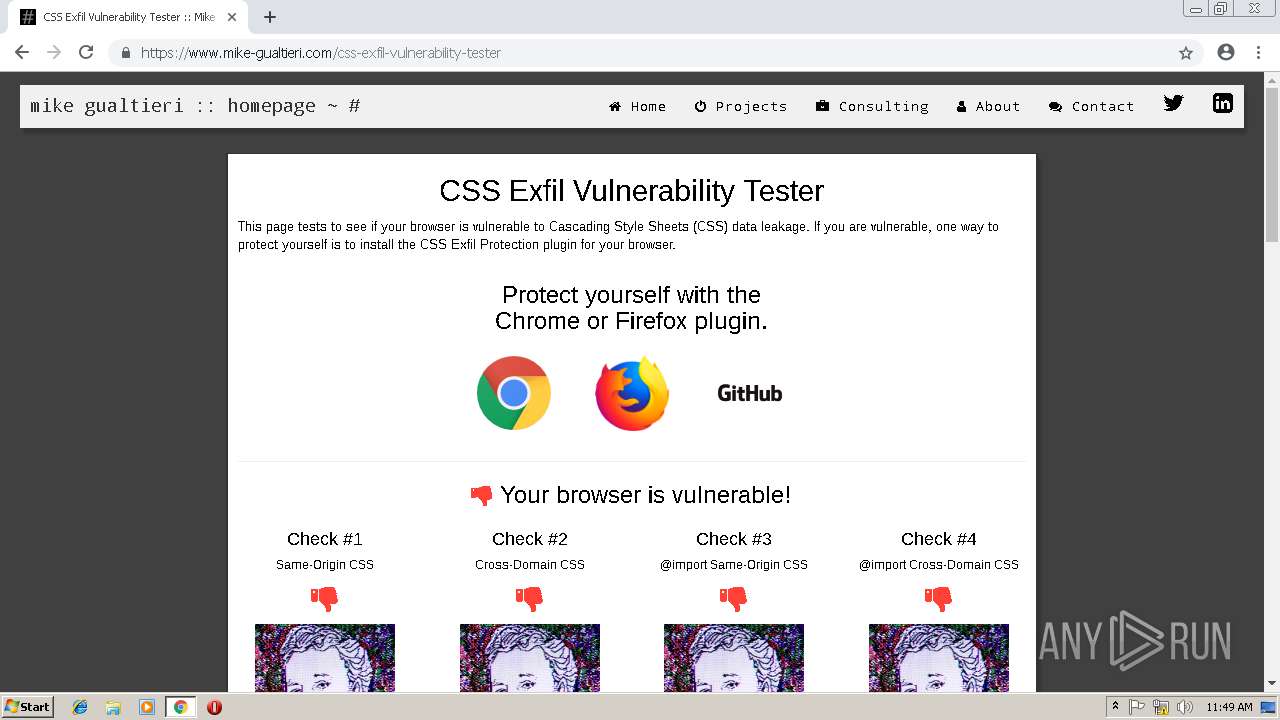
| Verdict: | Malicious activity |
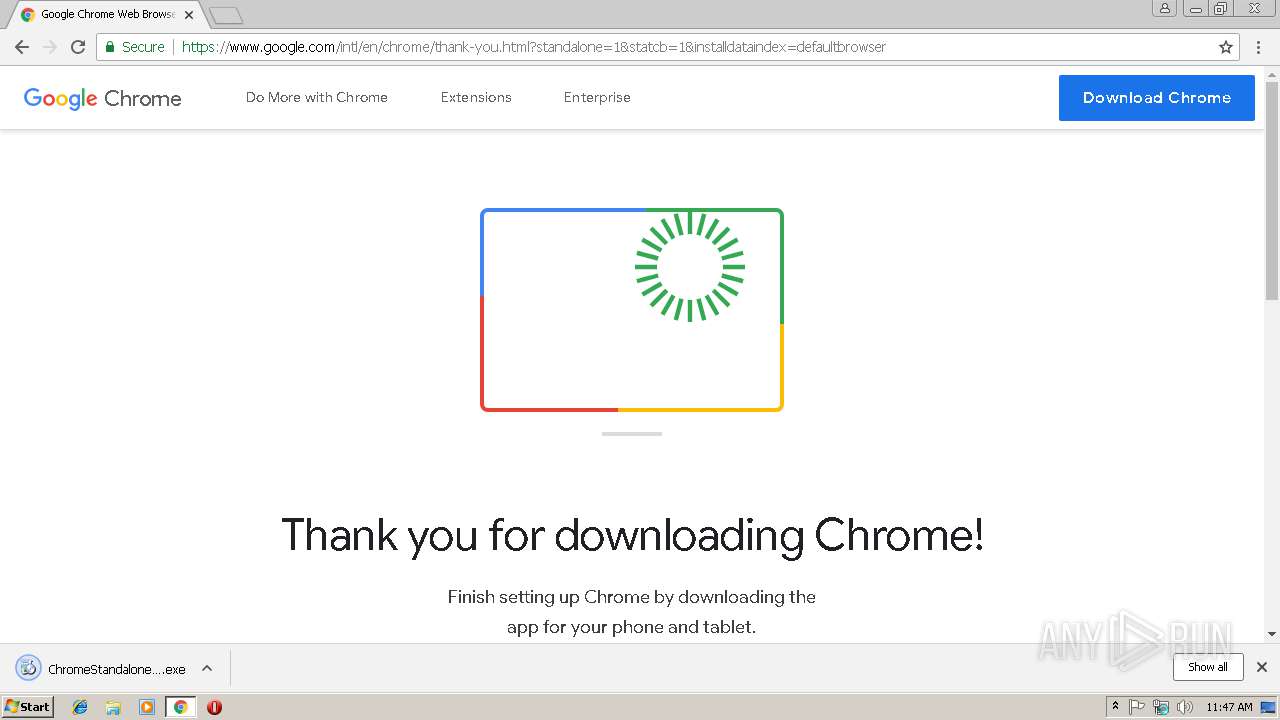
| Analysis date: | February 19, 2019, 11:46:18 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | F39D04EFC57AED0BDBF73F122E7F392F |
| SHA1: | D1E606108D2E2B9D4CA13B144B96D5F61CB494CF |
| SHA256: | BBD5669462BBCC71C272EEBA70709E620767D2A984C7A556F3F20FB77D87FA5B |
| SSDEEP: | 3:N8DSLIqTKA+GwIAgoBLA5:2OLIqX59AJi5 |
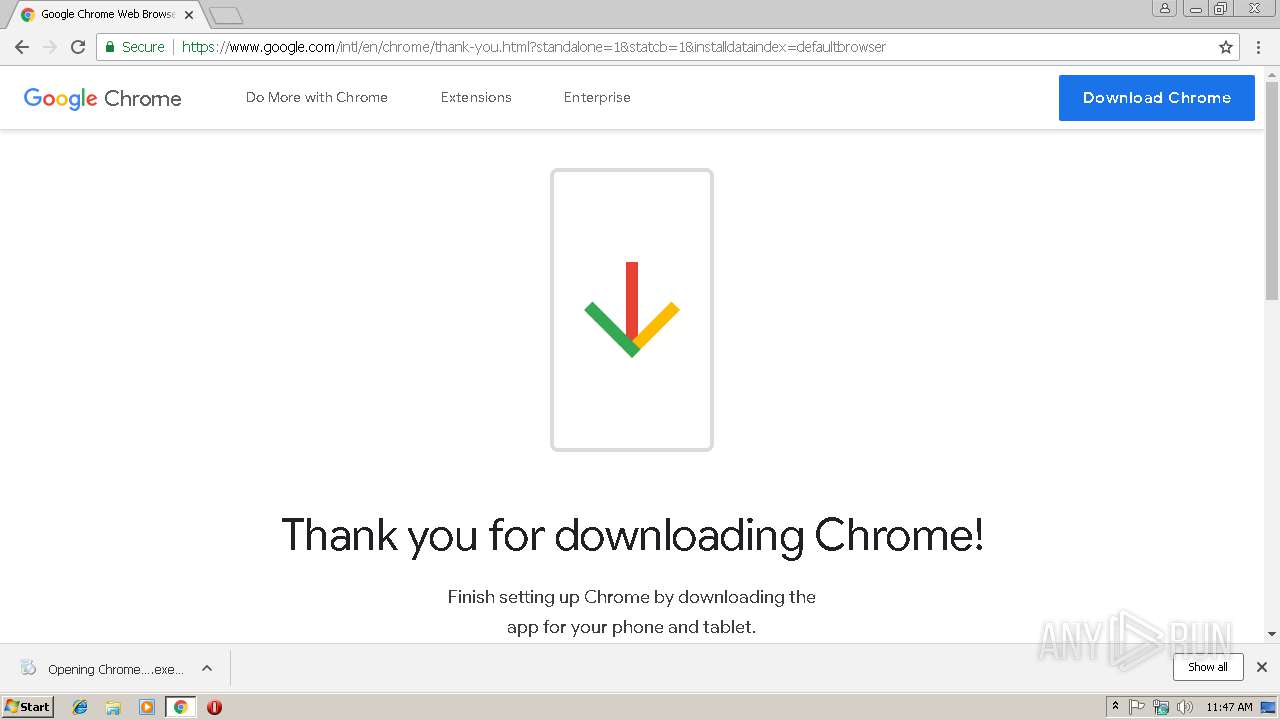
MALICIOUS
Application was dropped or rewritten from another process
- ChromeStandaloneSetup.exe (PID: 3232)
- GoogleUpdate.exe (PID: 3608)
- GoogleUpdateSetup.exe (PID: 2116)
- GoogleUpdate.exe (PID: 3100)
- GoogleUpdate.exe (PID: 3836)
- GoogleUpdate.exe (PID: 3760)
- GoogleUpdate.exe (PID: 2808)
- GoogleUpdate.exe (PID: 3980)
- GoogleUpdate.exe (PID: 3672)
- GoogleCrashHandler.exe (PID: 2468)
- setup.exe (PID: 2480)
- GoogleUpdateOnDemand.exe (PID: 3056)
- GoogleUpdate.exe (PID: 3964)
- GoogleUpdate.exe (PID: 3116)
- chrome.exe (PID: 3356)
- chrome.exe (PID: 1316)
- chrome.exe (PID: 3324)
- chrome.exe (PID: 2428)
- chrome.exe (PID: 2936)
- chrome.exe (PID: 3384)
- chrome.exe (PID: 2304)
- chrome.exe (PID: 3236)
- chrome.exe (PID: 3228)
- chrome.exe (PID: 3764)
- setup.exe (PID: 3656)
- chrome.exe (PID: 3552)
- chrome.exe (PID: 128)
- chrome.exe (PID: 1764)
- chrome.exe (PID: 3140)
- chrome.exe (PID: 2992)
- chrome.exe (PID: 3968)
- chrome.exe (PID: 1832)
- chrome.exe (PID: 3396)
- chrome.exe (PID: 3048)
- chrome.exe (PID: 2200)
- chrome.exe (PID: 3372)
- chrome.exe (PID: 2440)
- chrome.exe (PID: 1268)
- chrome.exe (PID: 2568)
- chrome.exe (PID: 560)
- GoogleUpdateBroker.exe (PID: 2896)
- chrome.exe (PID: 3476)
- chrome.exe (PID: 2932)
- GoogleUpdate.exe (PID: 2376)
- GoogleUpdate.exe (PID: 4056)
- GoogleUpdate.exe (PID: 3504)
- chrome.exe (PID: 2324)
- chrome.exe (PID: 2176)
- chrome.exe (PID: 3612)
- chrome.exe (PID: 2380)
- chrome.exe (PID: 560)
- chrome.exe (PID: 2656)
- chrome.exe (PID: 588)
- chrome.exe (PID: 1932)
- chrome.exe (PID: 2712)
- chrome.exe (PID: 1928)
- chrome.exe (PID: 3588)
- chrome.exe (PID: 2372)
- chrome.exe (PID: 4088)
- chrome.exe (PID: 1836)
- chrome.exe (PID: 3600)
- chrome.exe (PID: 1324)
- chrome.exe (PID: 2604)
- chrome.exe (PID: 3252)
Loads dropped or rewritten executable
- GoogleUpdate.exe (PID: 3608)
- GoogleUpdate.exe (PID: 3836)
- GoogleUpdate.exe (PID: 3100)
- GoogleUpdate.exe (PID: 3760)
- GoogleUpdate.exe (PID: 3980)
- GoogleUpdate.exe (PID: 3672)
- GoogleUpdate.exe (PID: 2808)
- chrome.exe (PID: 2428)
- chrome.exe (PID: 2324)
- GoogleUpdate.exe (PID: 3964)
- svchost.exe (PID: 688)
- GoogleUpdate.exe (PID: 3116)
- chrome.exe (PID: 3764)
- GoogleUpdate.exe (PID: 4056)
- GoogleUpdate.exe (PID: 3504)
- chrome.exe (PID: 2304)
- GoogleUpdate.exe (PID: 2376)
Loads the Task Scheduler COM API
- GoogleUpdate.exe (PID: 3100)
Changes settings of System certificates
- GoogleUpdate.exe (PID: 2808)
Changes the autorun value in the registry
- setup.exe (PID: 3656)
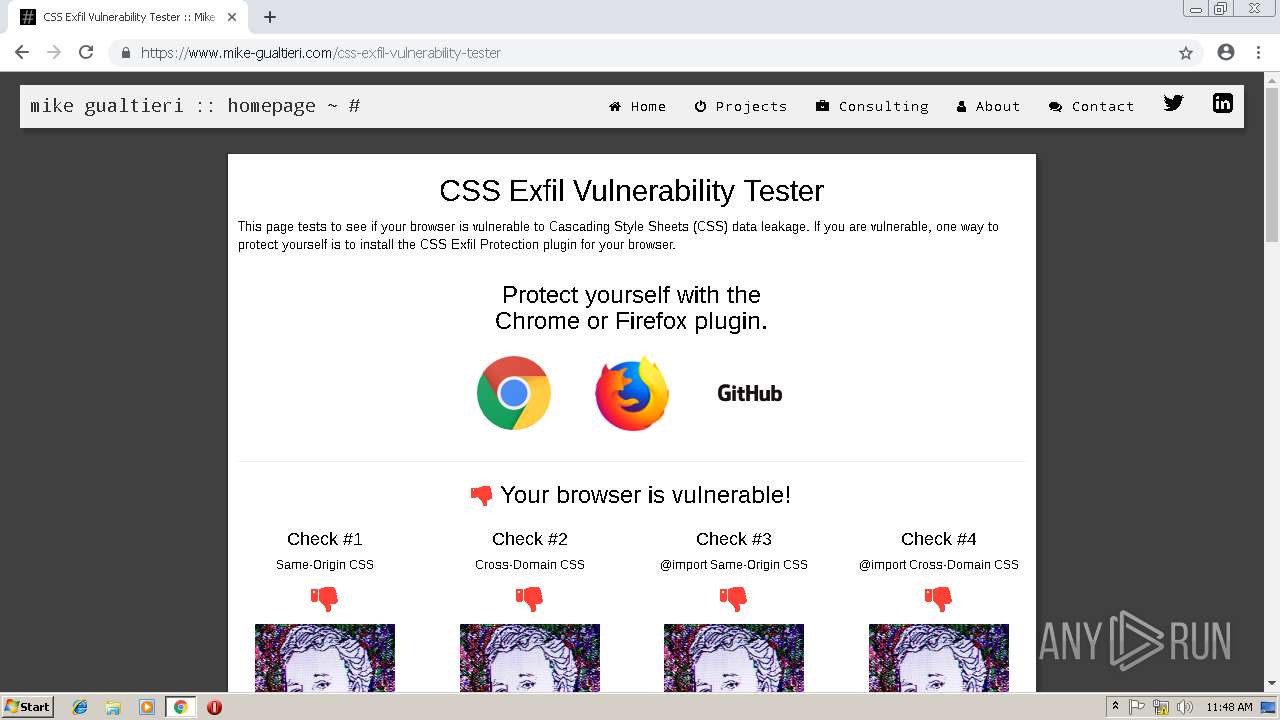
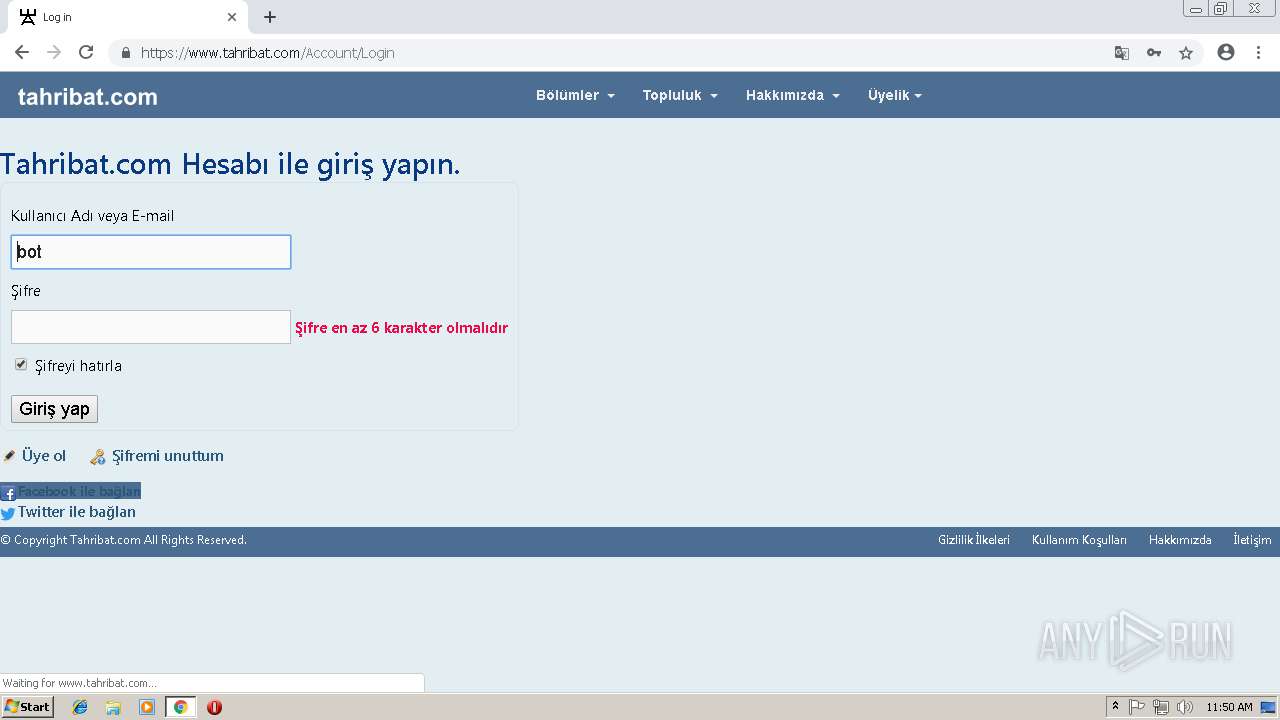
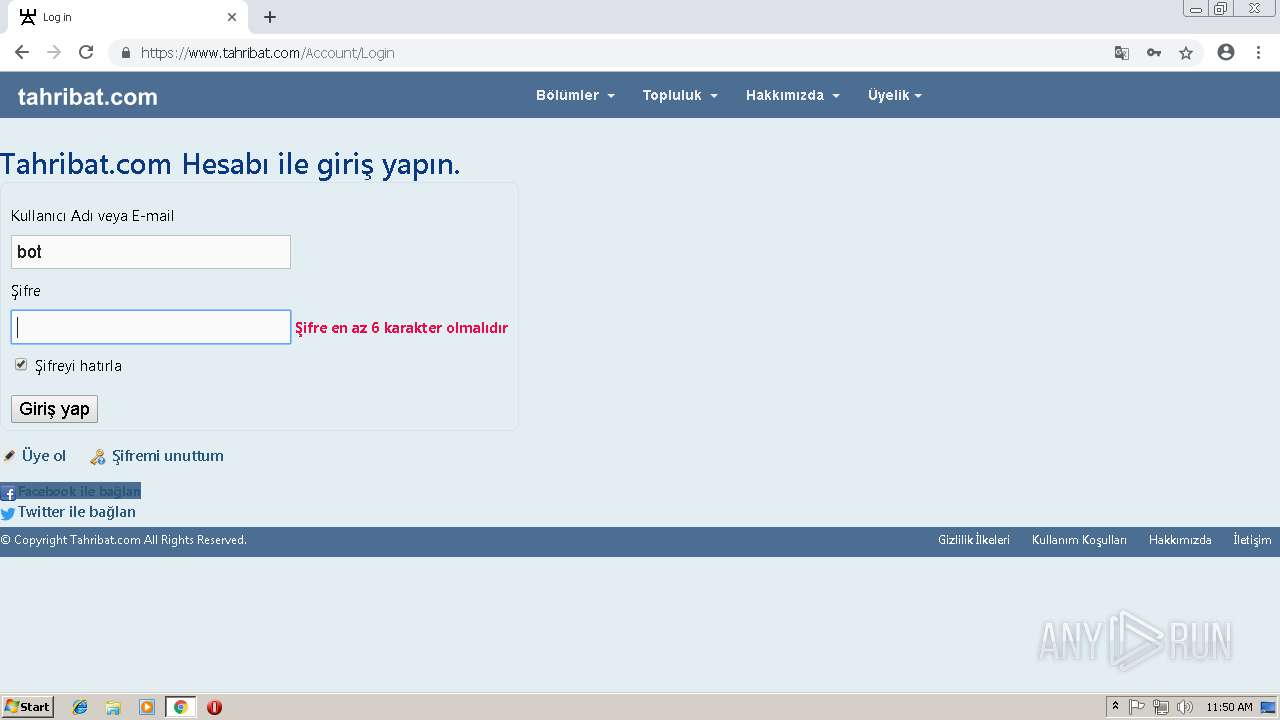
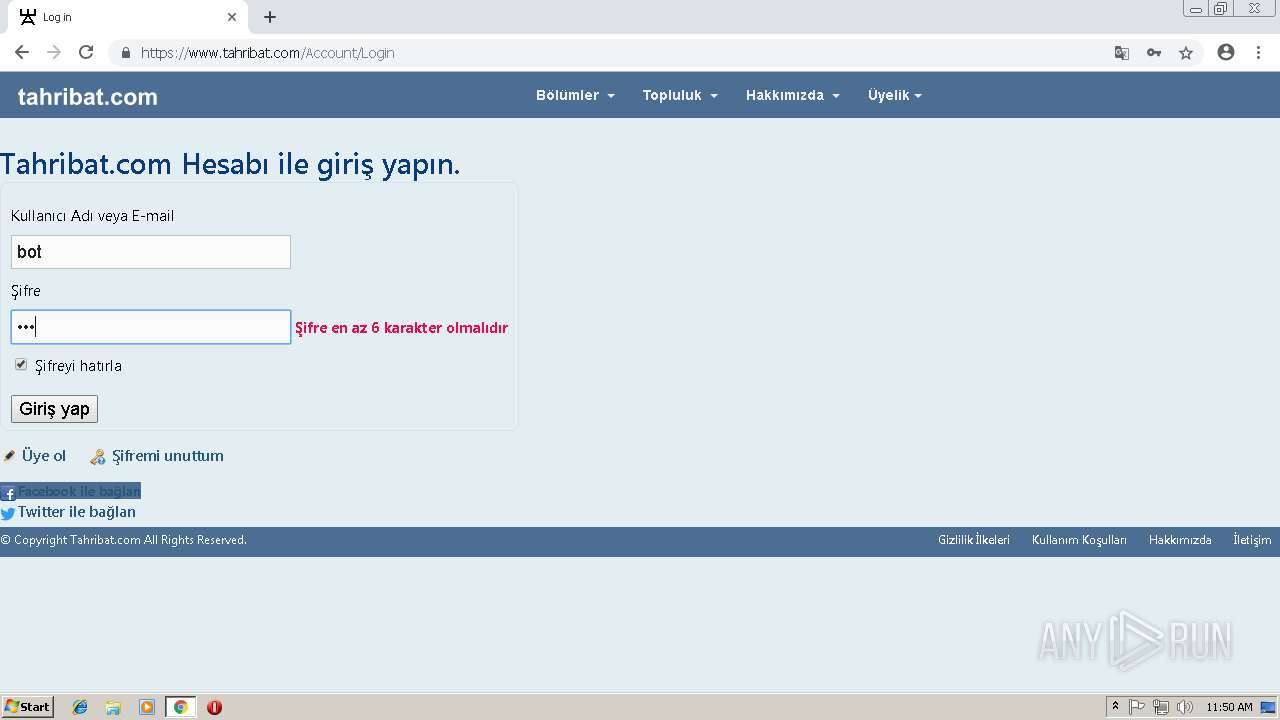
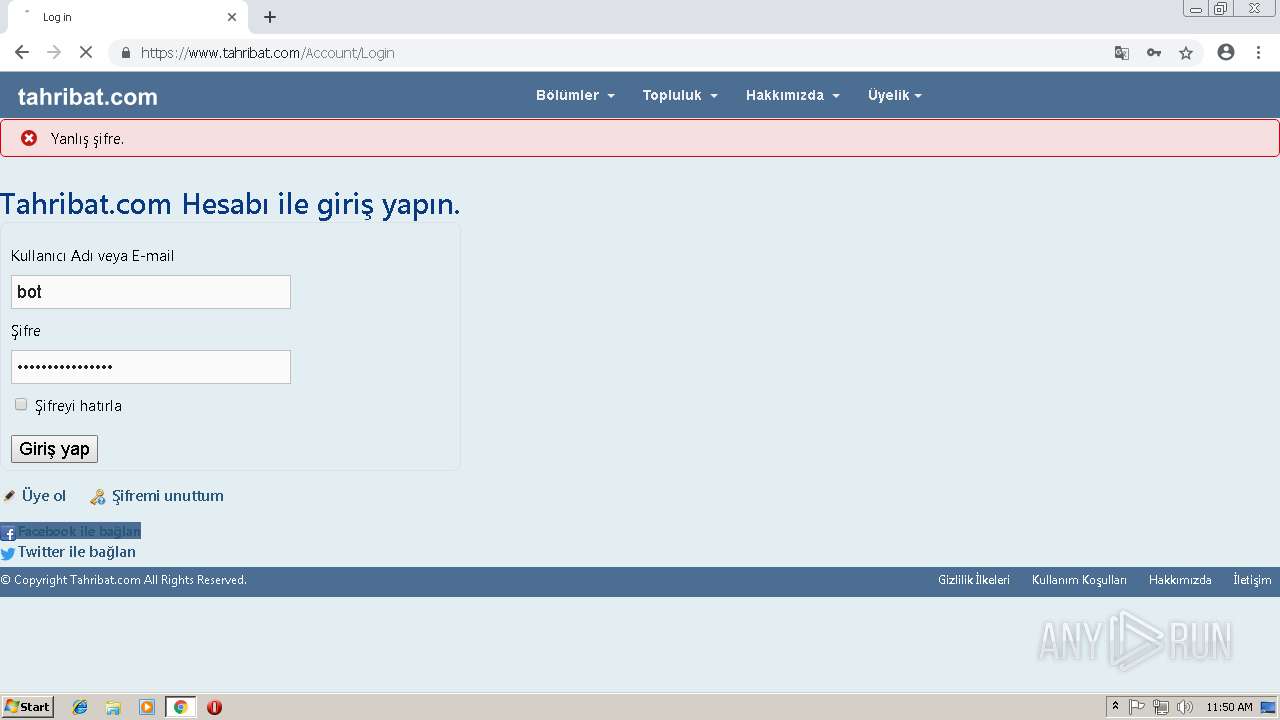
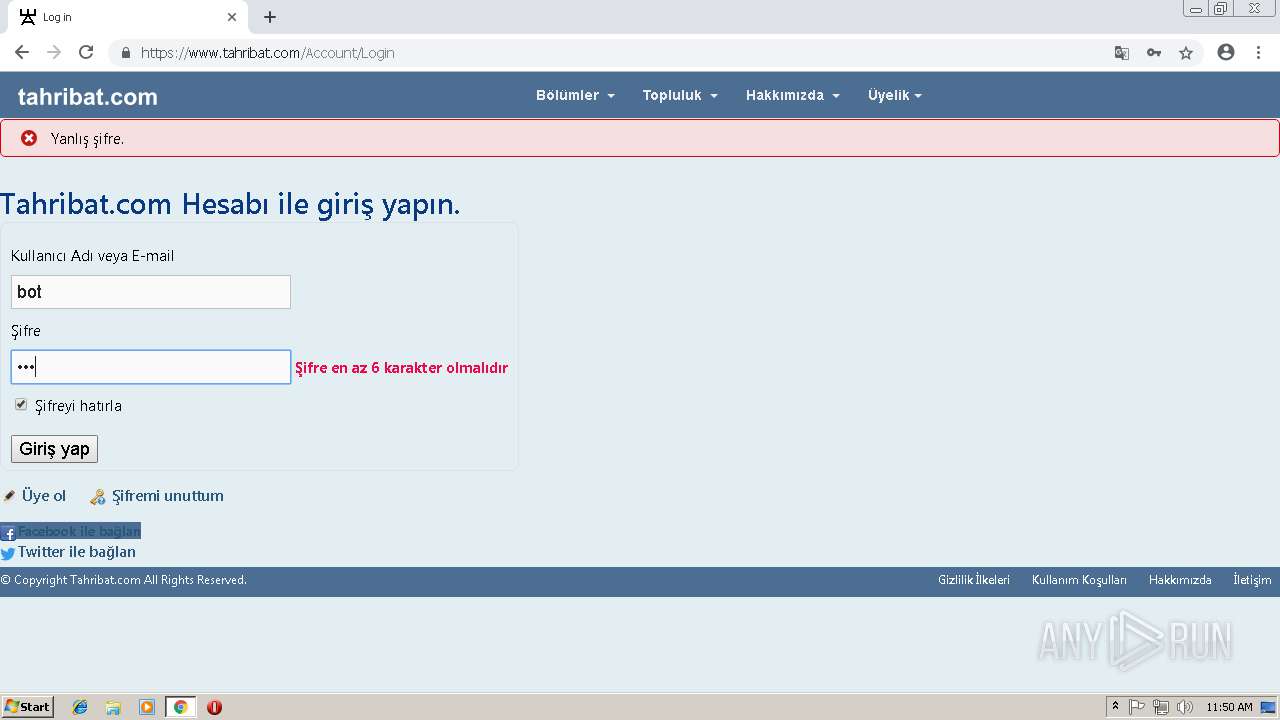
Connects to CnC server
- chrome.exe (PID: 128)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 3356)
- ChromeStandaloneSetup.exe (PID: 3232)
- GoogleUpdateSetup.exe (PID: 2116)
- GoogleUpdate.exe (PID: 3100)
- chrome_installer.exe (PID: 3020)
- setup.exe (PID: 3656)
Cleans NTFS data-stream (Zone Identifier)
- chrome.exe (PID: 3356)
Creates files in the program directory
- GoogleUpdateSetup.exe (PID: 2116)
- GoogleUpdate.exe (PID: 3100)
- GoogleUpdate.exe (PID: 3672)
- setup.exe (PID: 3656)
Starts itself from another location
- GoogleUpdate.exe (PID: 3100)
Disables SEHOP
- GoogleUpdate.exe (PID: 3100)
Creates COM task schedule object
- GoogleUpdate.exe (PID: 3760)
- GoogleUpdate.exe (PID: 3100)
Adds / modifies Windows certificates
- GoogleUpdate.exe (PID: 2808)
Creates files in the Windows directory
- setup.exe (PID: 2480)
- GoogleUpdate.exe (PID: 3672)
Creates a software uninstall entry
- setup.exe (PID: 3656)
Removes files from Windows directory
- setup.exe (PID: 3656)
Modifies the open verb of a shell class
- setup.exe (PID: 3656)
Application launched itself
- GoogleUpdate.exe (PID: 3672)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2304)
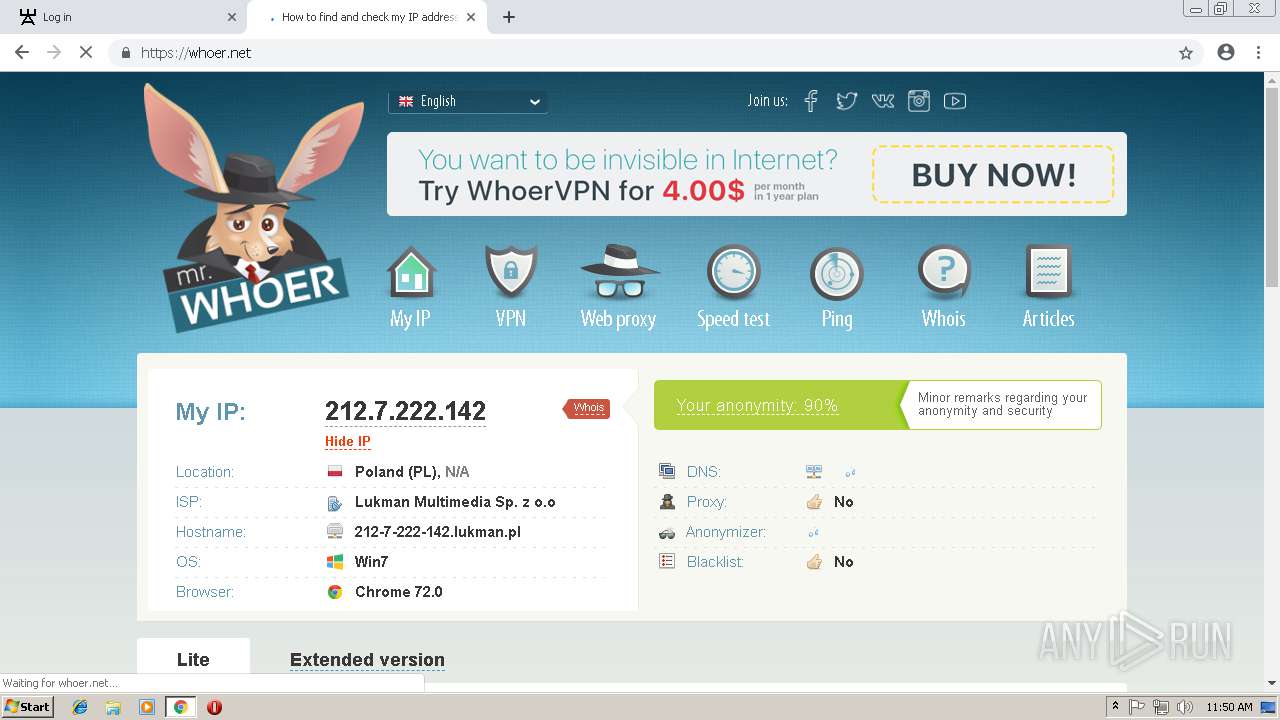
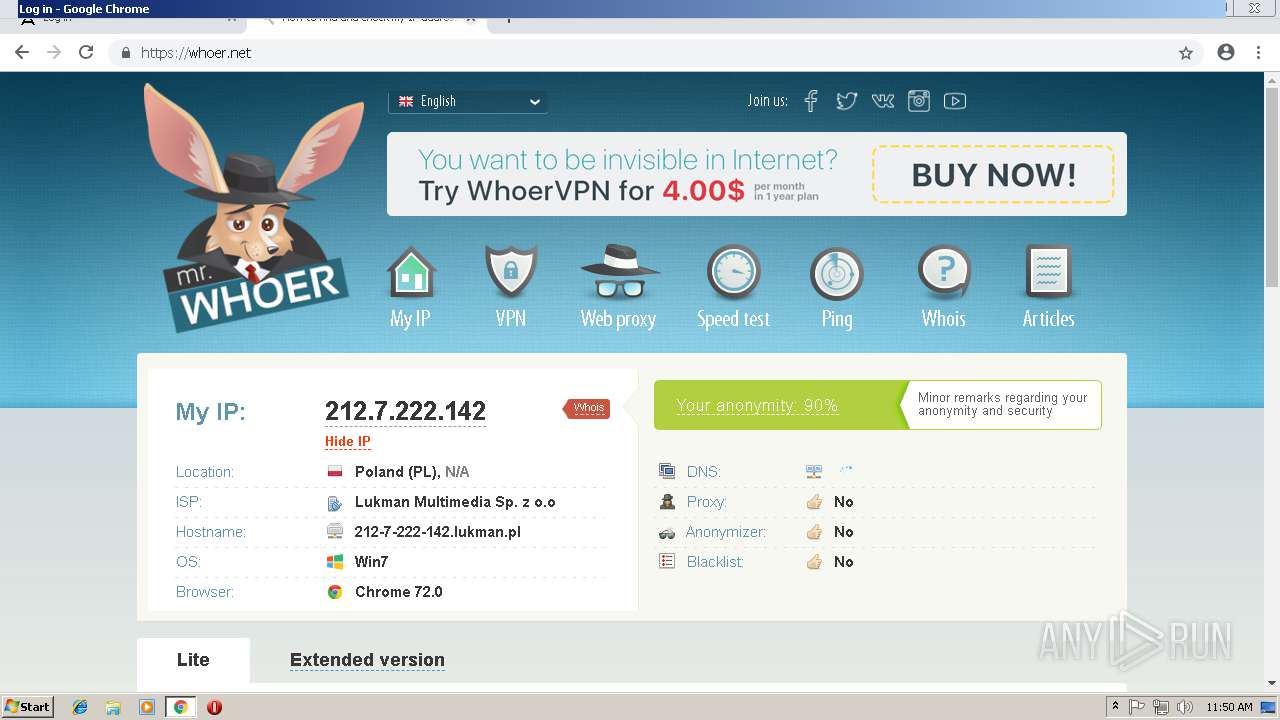
Checks for external IP
- chrome.exe (PID: 128)
INFO
Application launched itself
- chrome.exe (PID: 3356)
- chrome.exe (PID: 2304)
Reads settings of System Certificates
- chrome.exe (PID: 3356)
- chrome.exe (PID: 128)
Reads Internet Cache Settings
- chrome.exe (PID: 3356)
Dropped object may contain Bitcoin addresses
- setup.exe (PID: 3656)
Creates files in the user directory
- chrome.exe (PID: 2304)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
97
Monitored processes
66
Malicious processes
16
Suspicious processes
8
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 128 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=916,6852933028605827601,7182201538678818842,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=11195303425143735034 --mojo-platform-channel-handle=1496 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
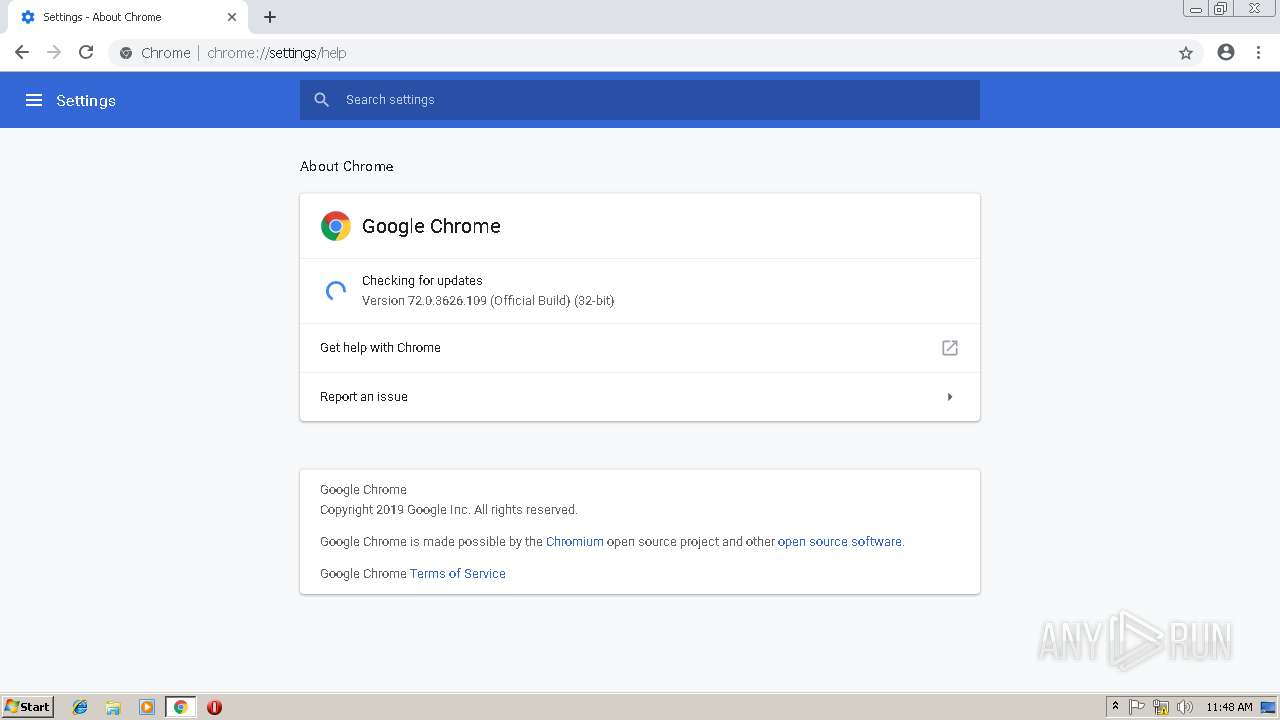
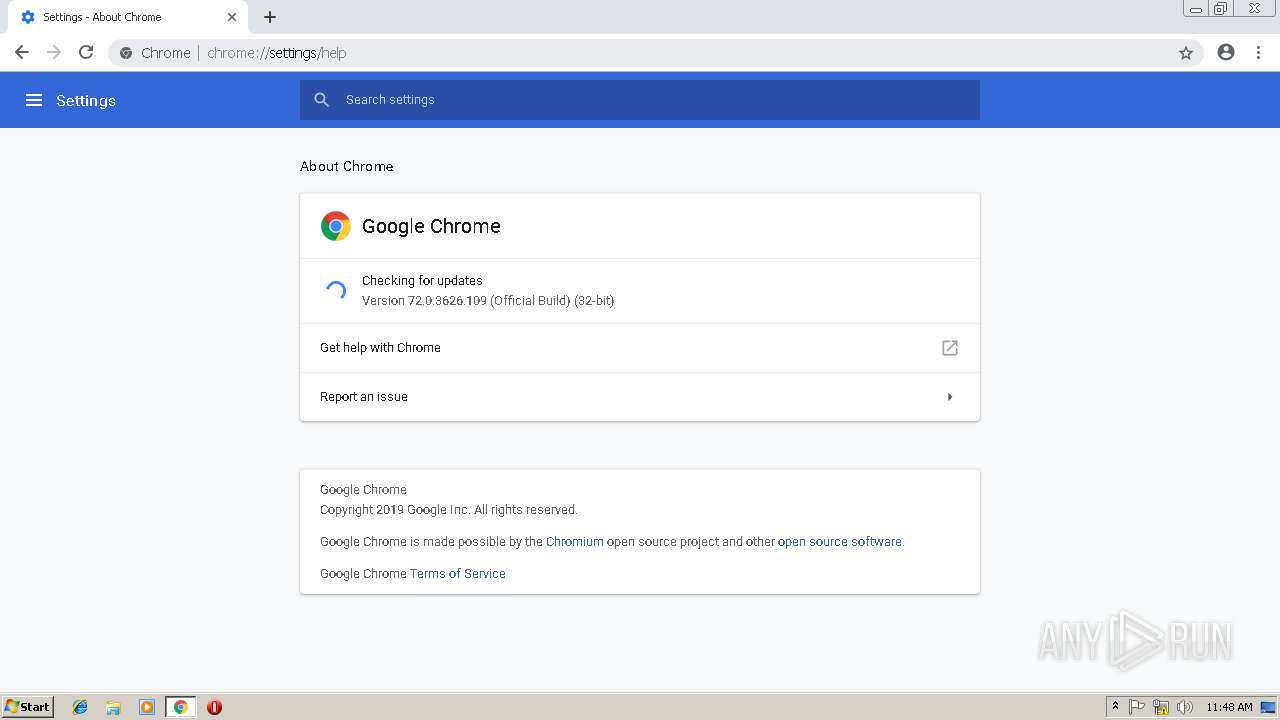
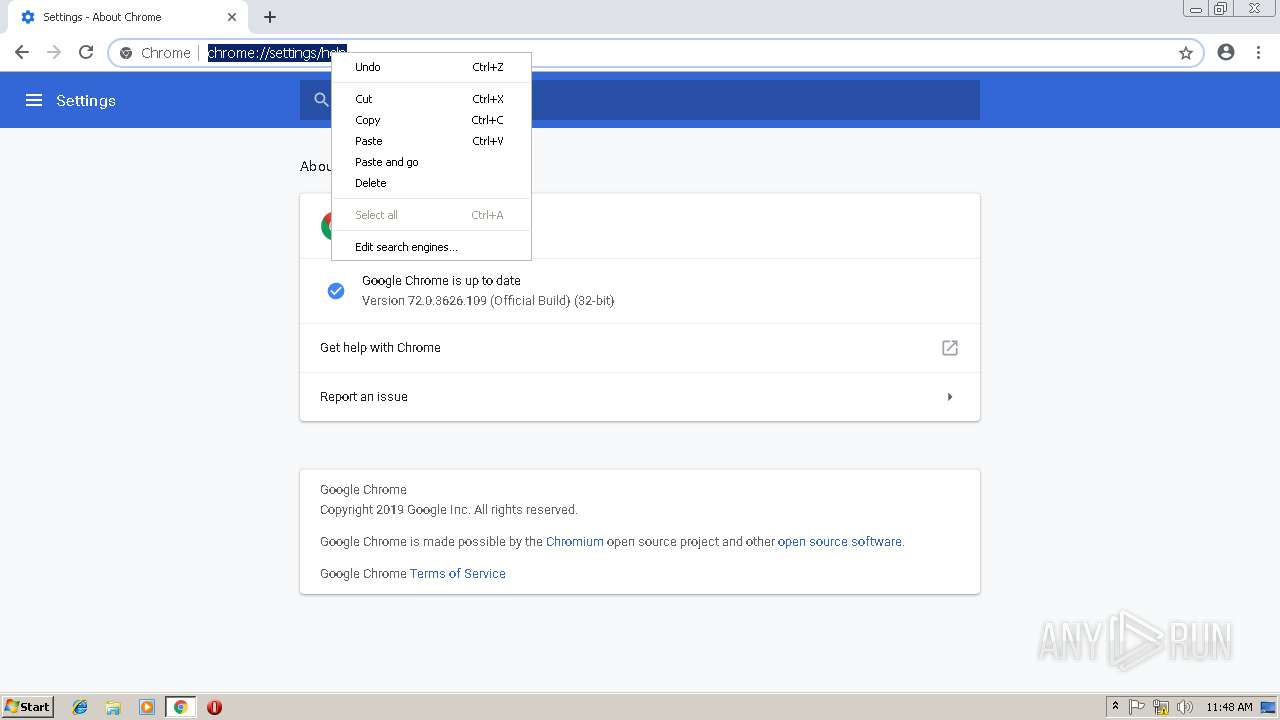
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 72.0.3626.109 Modules
| |||||||||||||||
| 560 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=916,6852933028605827601,7182201538678818842,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAACAAwCAAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=6066845329005535841 --mojo-platform-channel-handle=3804 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 72.0.3626.109 Modules
| |||||||||||||||
| 560 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=916,6852933028605827601,7182201538678818842,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5843137149099274760 --mojo-platform-channel-handle=472 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 72.0.3626.109 Modules
| |||||||||||||||
| 588 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=916,6852933028605827601,7182201538678818842,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=15062489550522430606 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15062489550522430606 --renderer-client-id=33 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3432 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 72.0.3626.109 Modules
| |||||||||||||||
| 688 | C:\Windows\system32\svchost.exe -k RPCSS | C:\Windows\System32\svchost.exe | — | services.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1268 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=916,6852933028605827601,7182201538678818842,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=13482711254455342573 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13482711254455342573 --renderer-client-id=19 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3372 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 72.0.3626.109 Modules
| |||||||||||||||
| 1316 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=68.0.3440.106 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x6f5d00b0,0x6f5d00c0,0x6f5d00cc | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1324 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=916,6852933028605827601,7182201538678818842,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=6476397044144410700 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6476397044144410700 --renderer-client-id=37 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2624 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 72.0.3626.109 Modules
| |||||||||||||||
| 1764 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=916,6852933028605827601,7182201538678818842,131072 --enable-features=PasswordImport --service-pipe-token=9066239813408317992 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9066239813408317992 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2392 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 72.0.3626.109 Modules
| |||||||||||||||
| 1832 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=916,6852933028605827601,7182201538678818842,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9822462579784500247 --mojo-platform-channel-handle=3124 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 72.0.3626.109 Modules
| |||||||||||||||
Total events
3 511
Read events
1 962
Write events
1 392
Delete events
157
Modification events
| (PID) Process: | (3356) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3356) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3356) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3324) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3356-13195050398860000 |
Value: 259 | |||
| (PID) Process: | (3356) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3356) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3356) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (3356) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3356) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3356-13195050398860000 |
Value: 259 | |||
| (PID) Process: | (3356) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
222
Suspicious files
290
Text files
411
Unknown types
94
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3356 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\a8a4b488-92a5-4f65-87c2-56d31da089fa.tmp | — | |
MD5:— | SHA256:— | |||
| 3356 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3356 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3356 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\91dec5fe-b18c-40b2-b8cd-9337532901d0.tmp | — | |
MD5:— | SHA256:— | |||
| 3356 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF198ea9.TMP | text | |
MD5:— | SHA256:— | |||
| 3356 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3356 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old~RF198ed8.TMP | text | |
MD5:— | SHA256:— | |||
| 3356 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Cache\f_00000c | compressed | |
MD5:— | SHA256:— | |||
| 3356 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Thumbnails\LOG.old~RF198fb3.TMP | text | |
MD5:— | SHA256:— | |||
| 3356 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Thumbnails\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
29
TCP/UDP connections
138
DNS requests
60
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
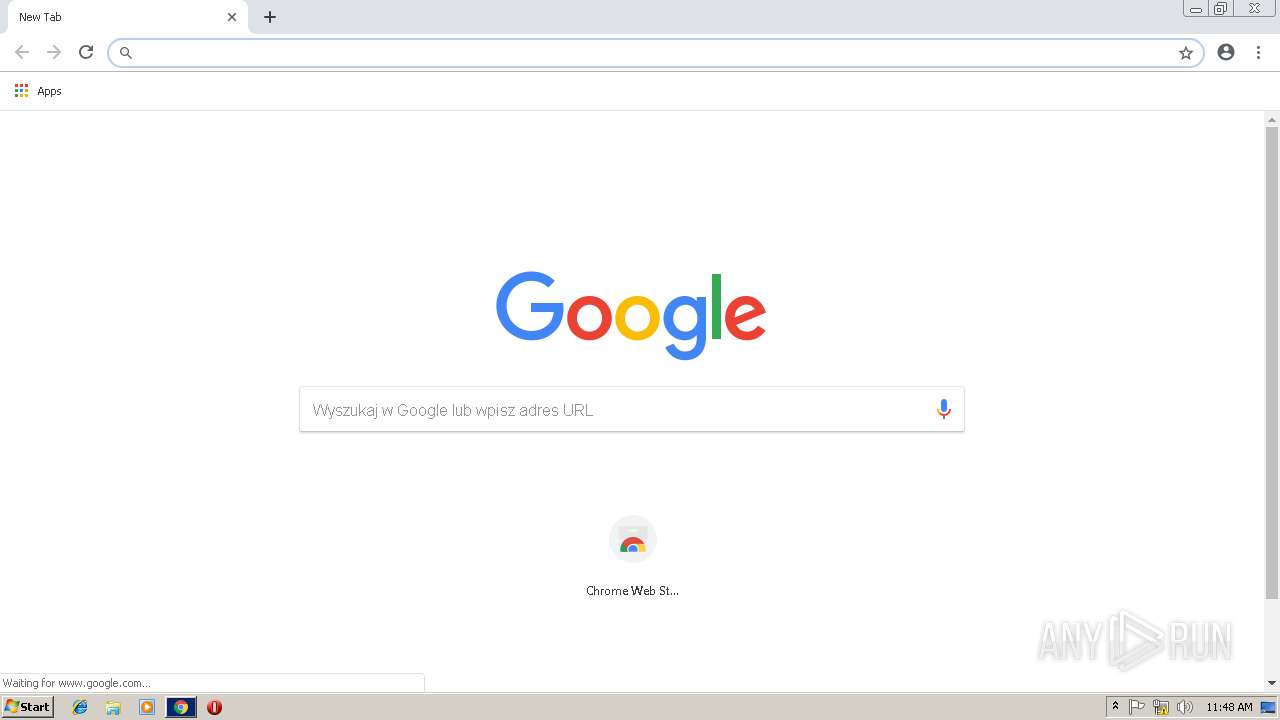
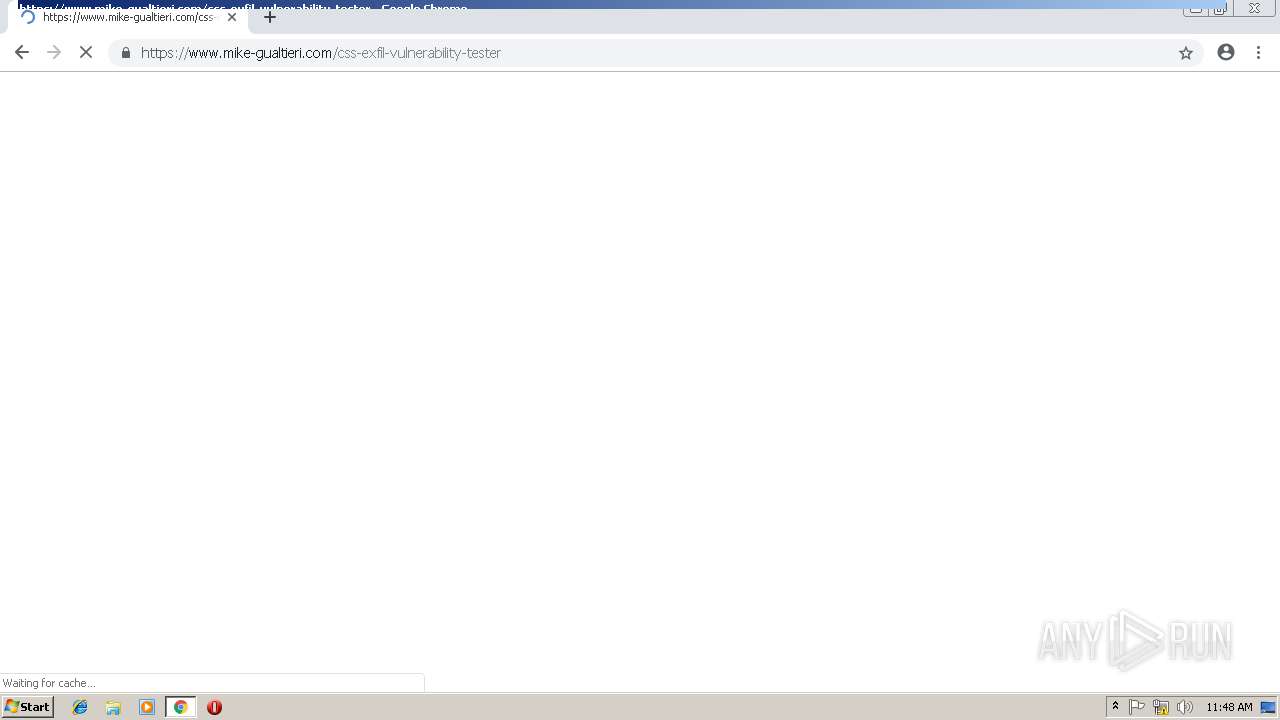
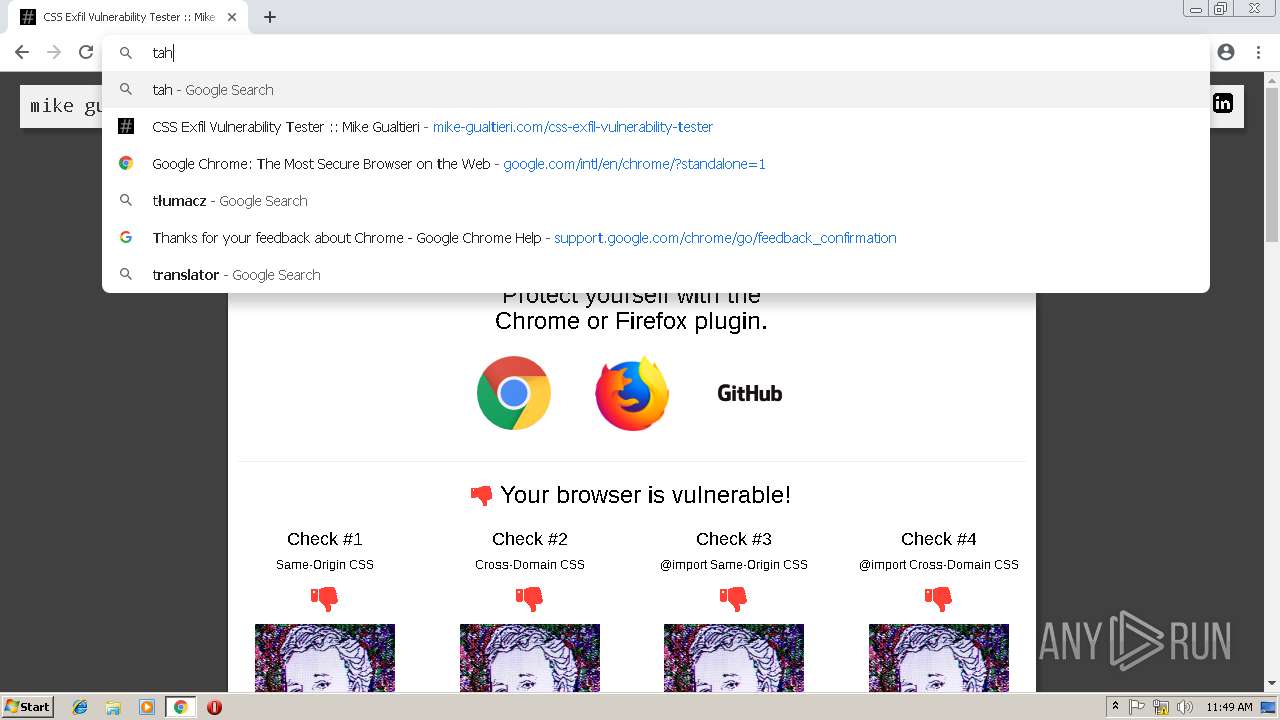
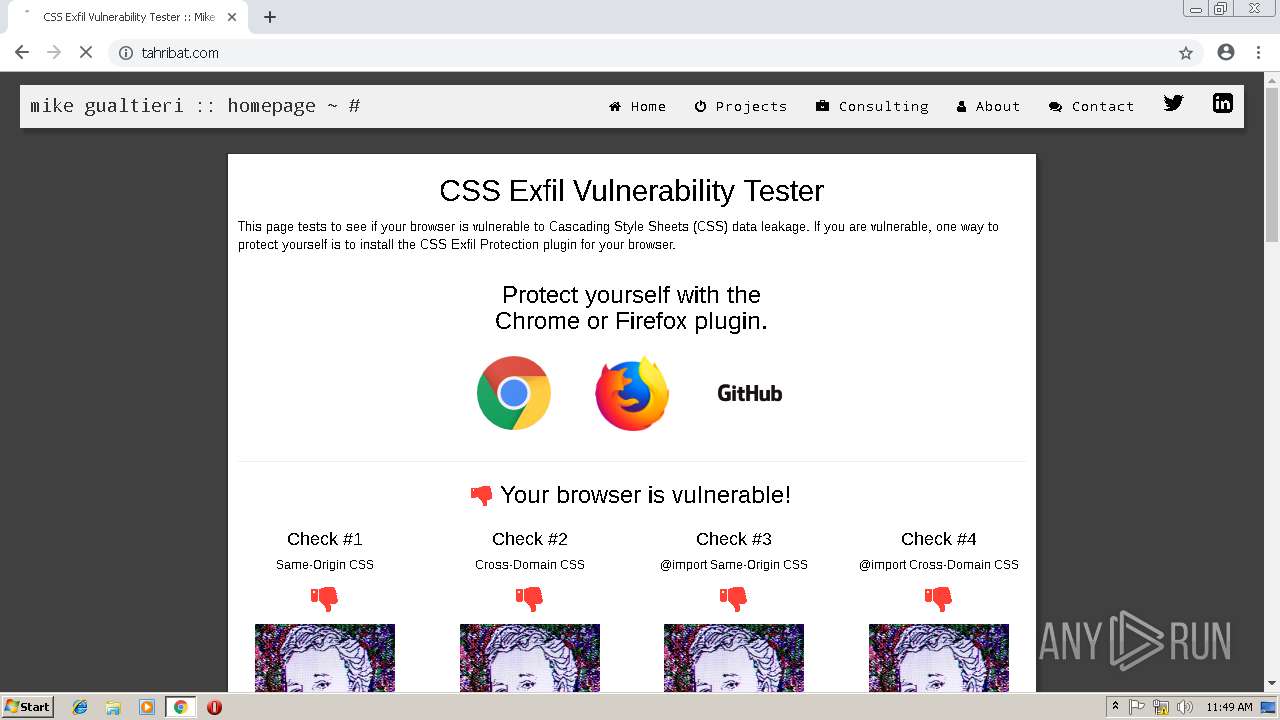
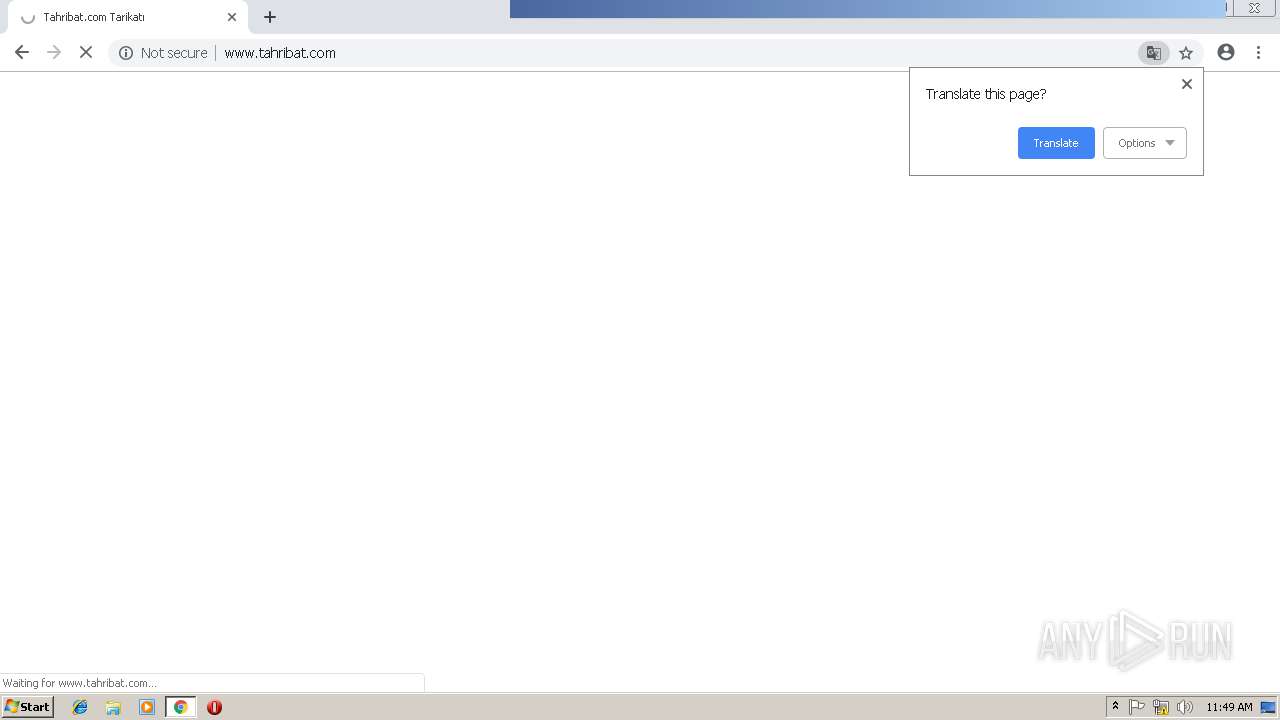
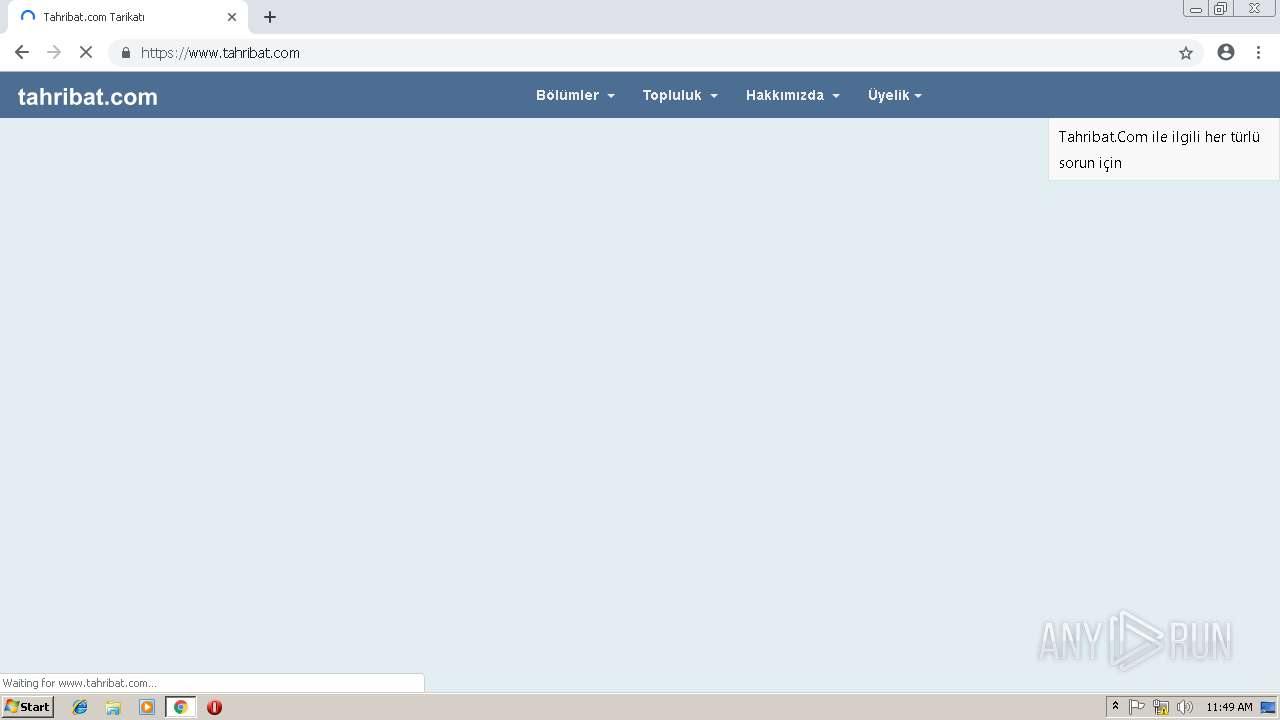
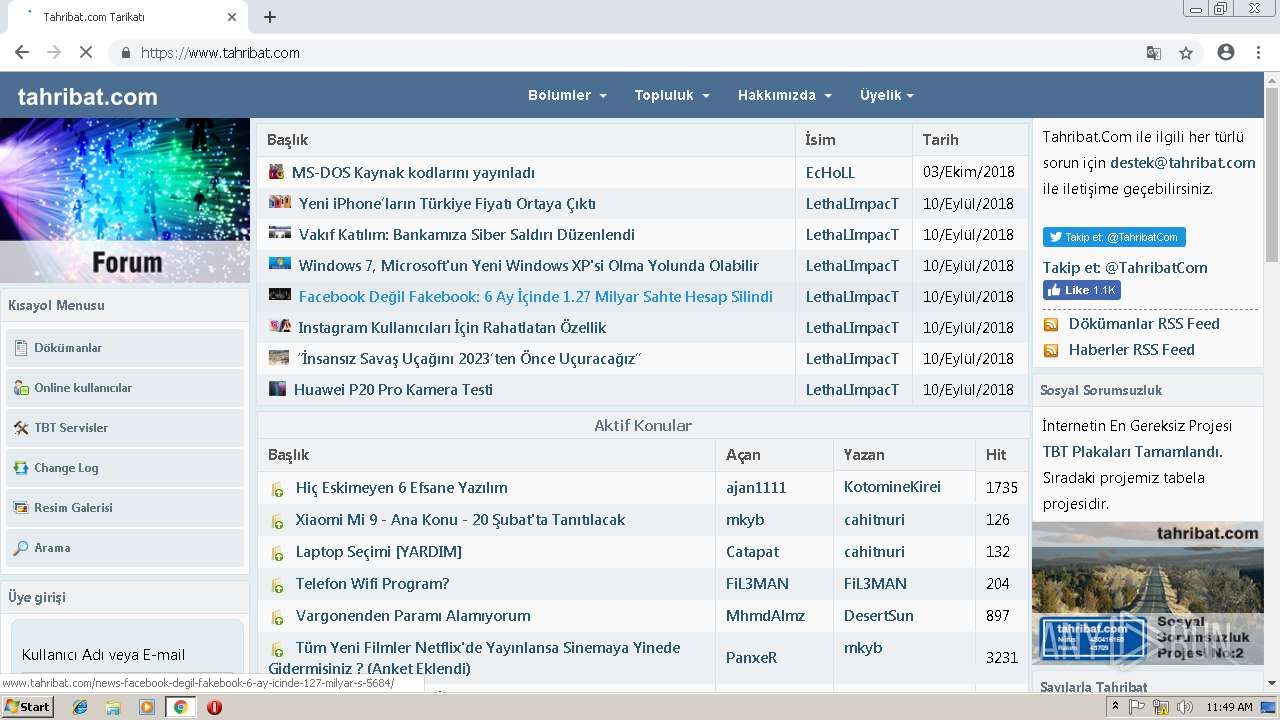
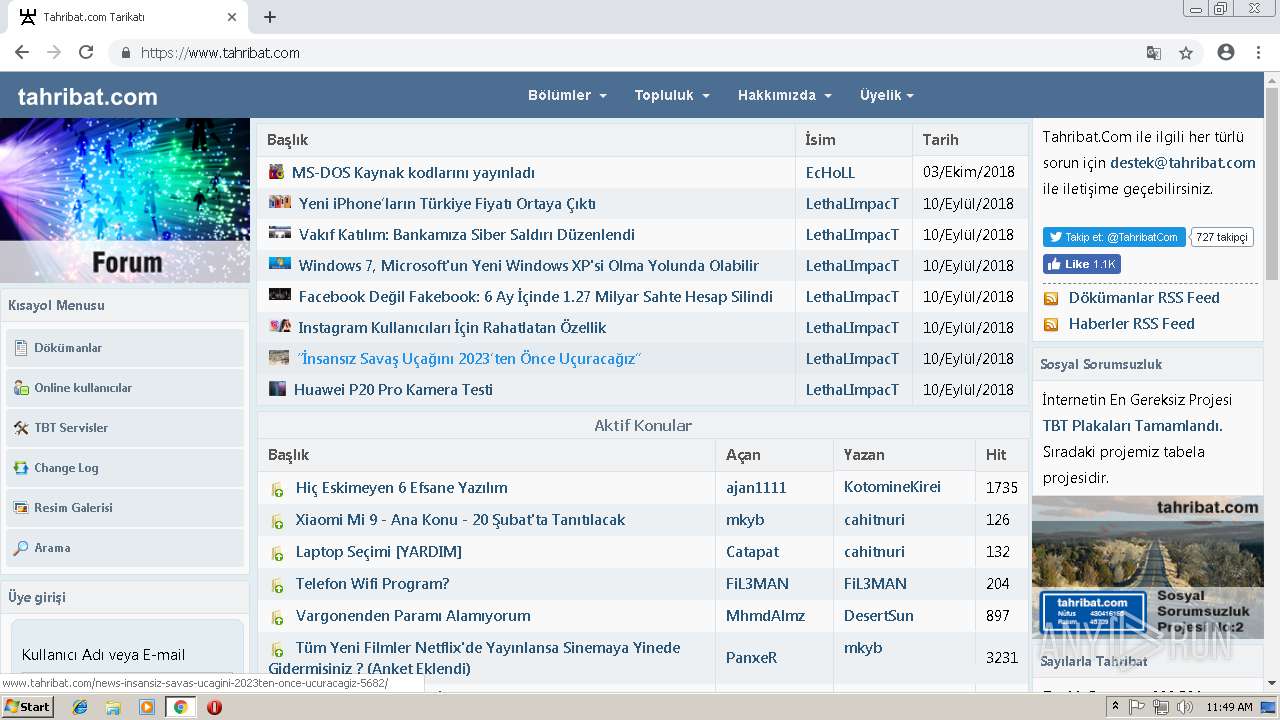
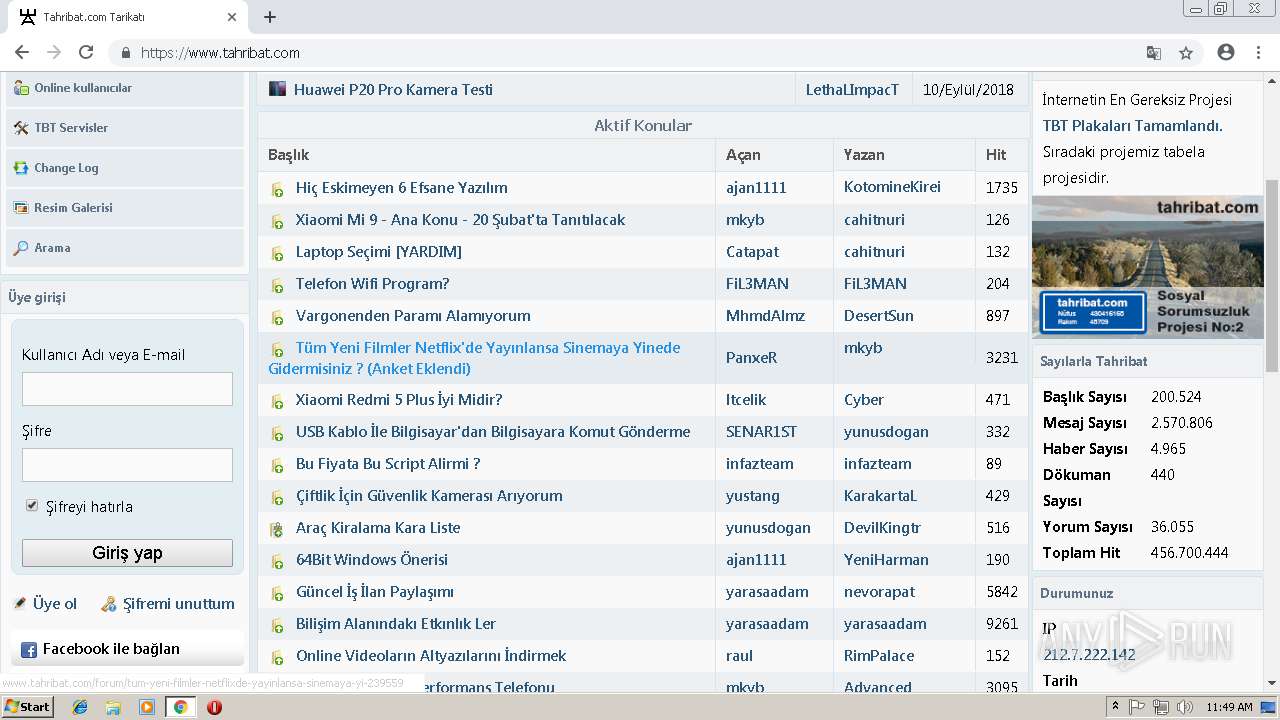
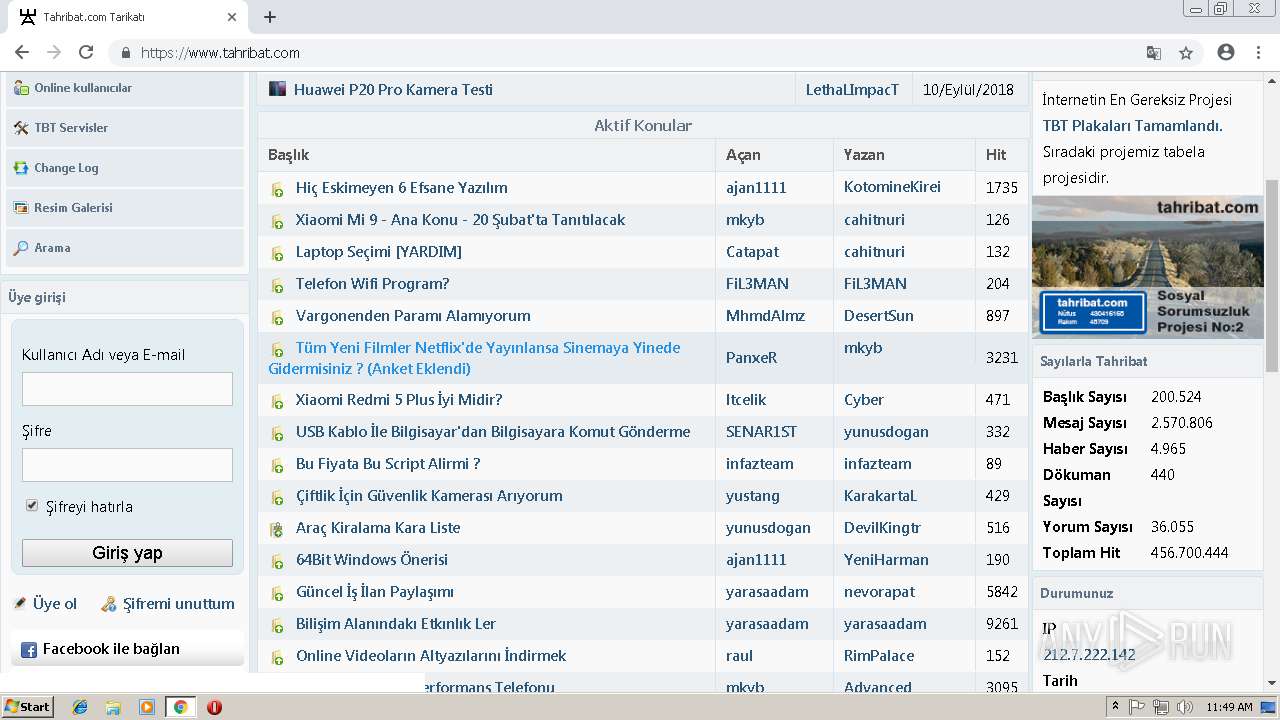
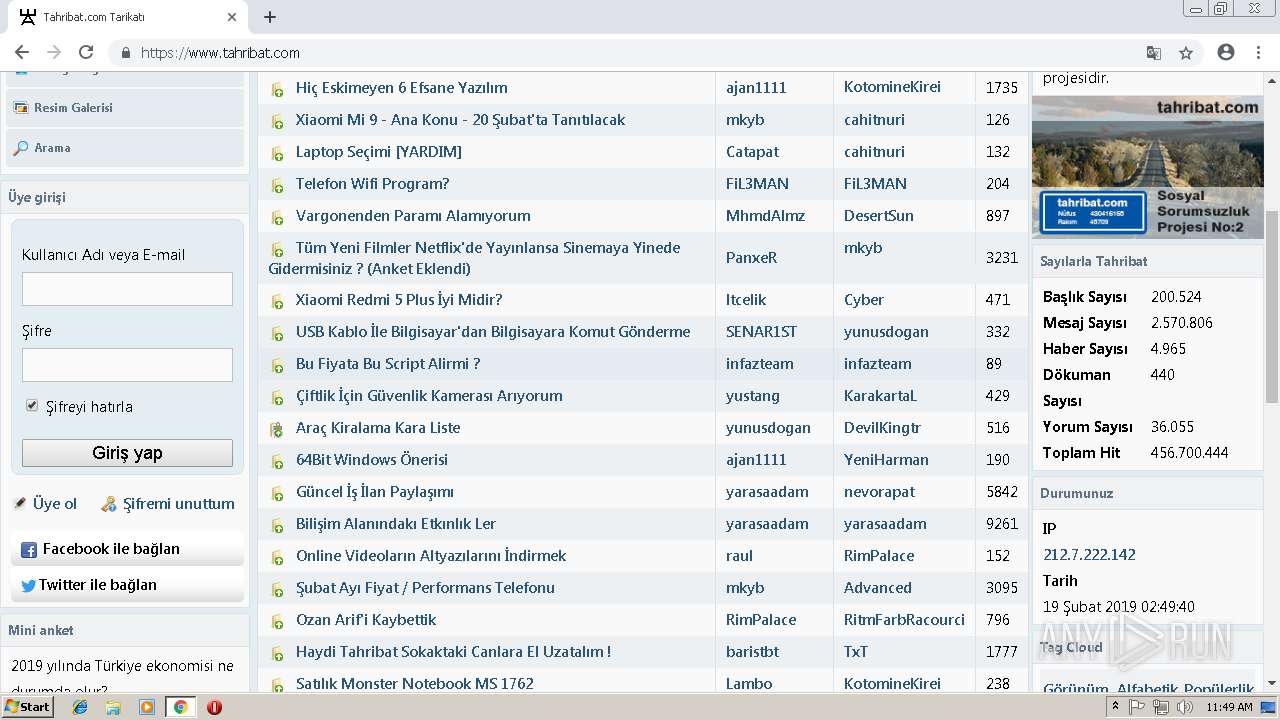
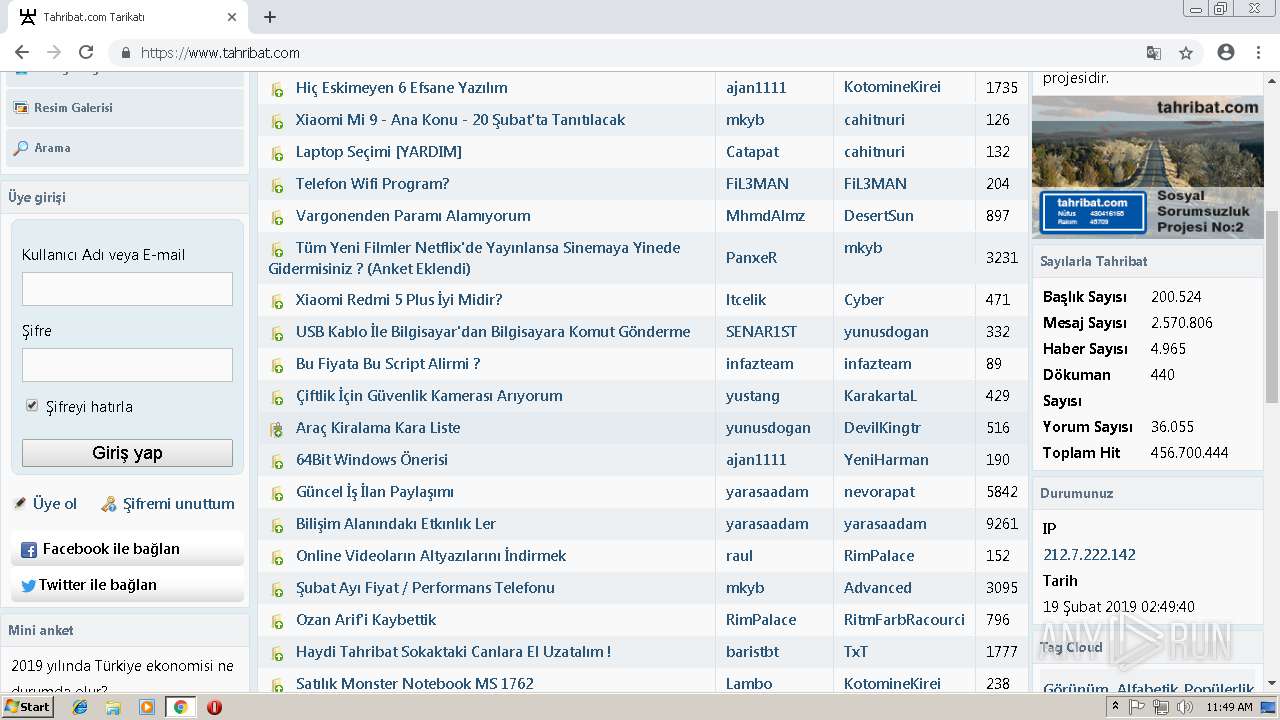
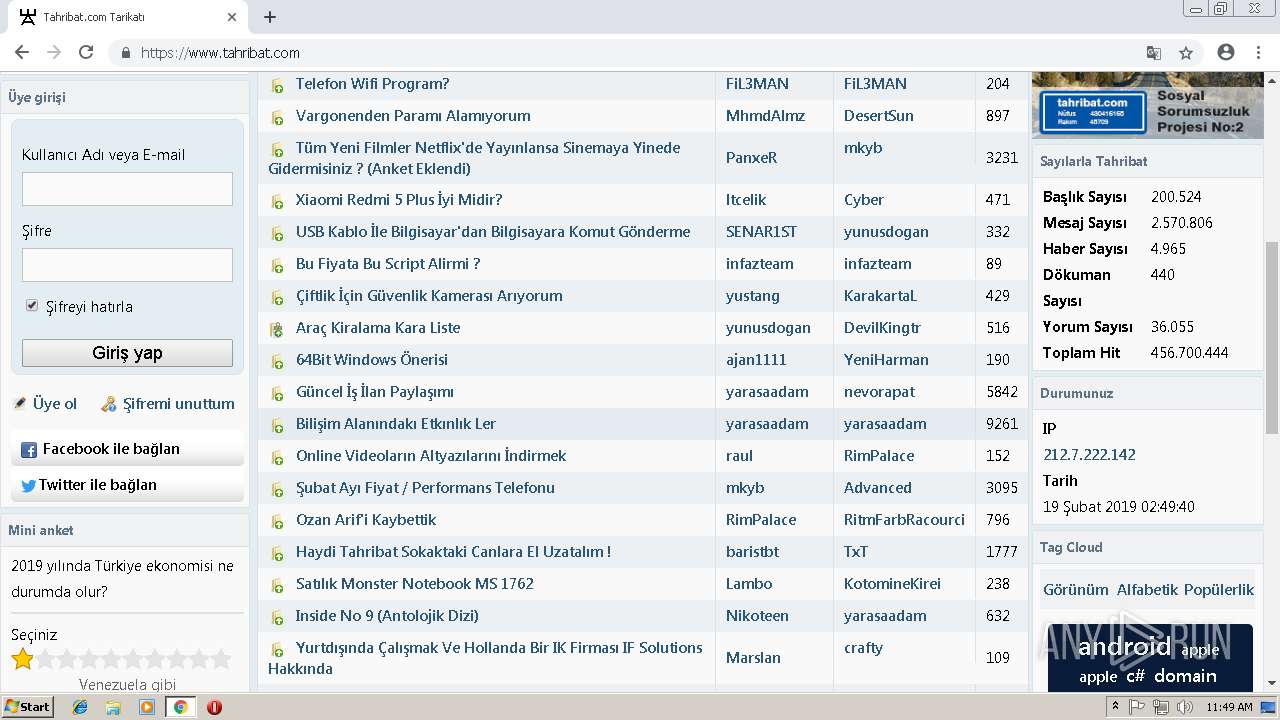
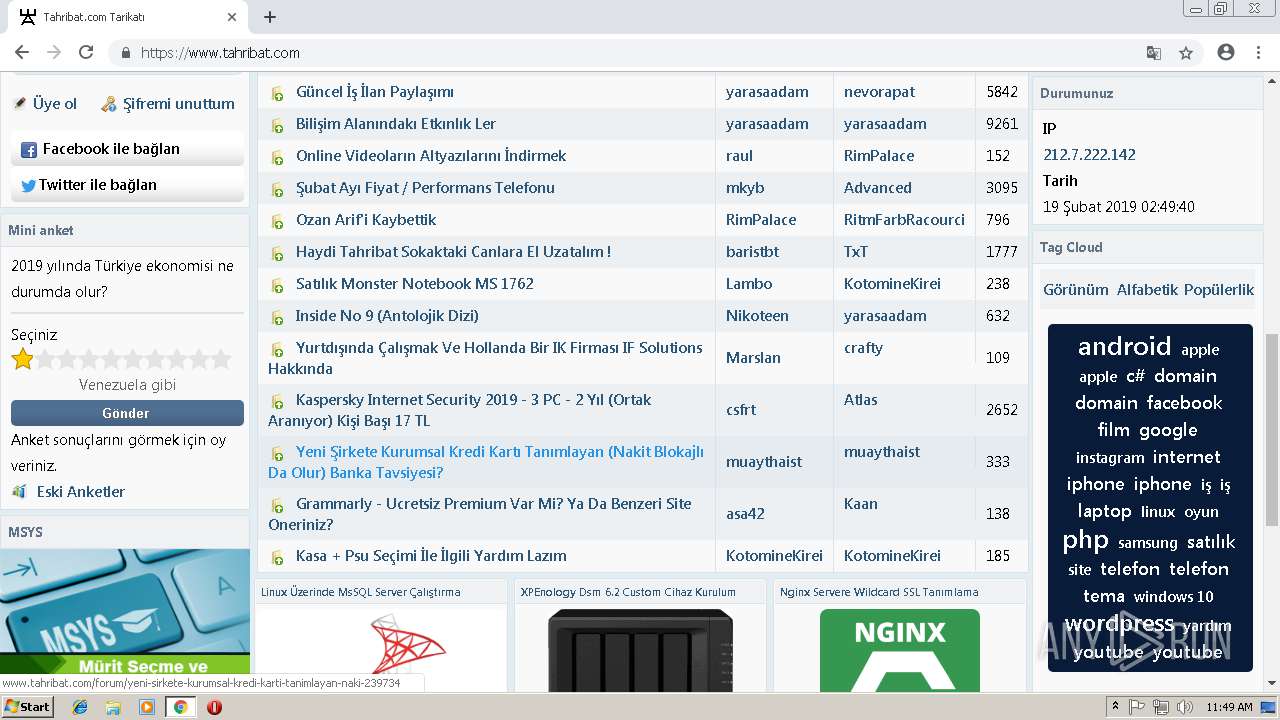
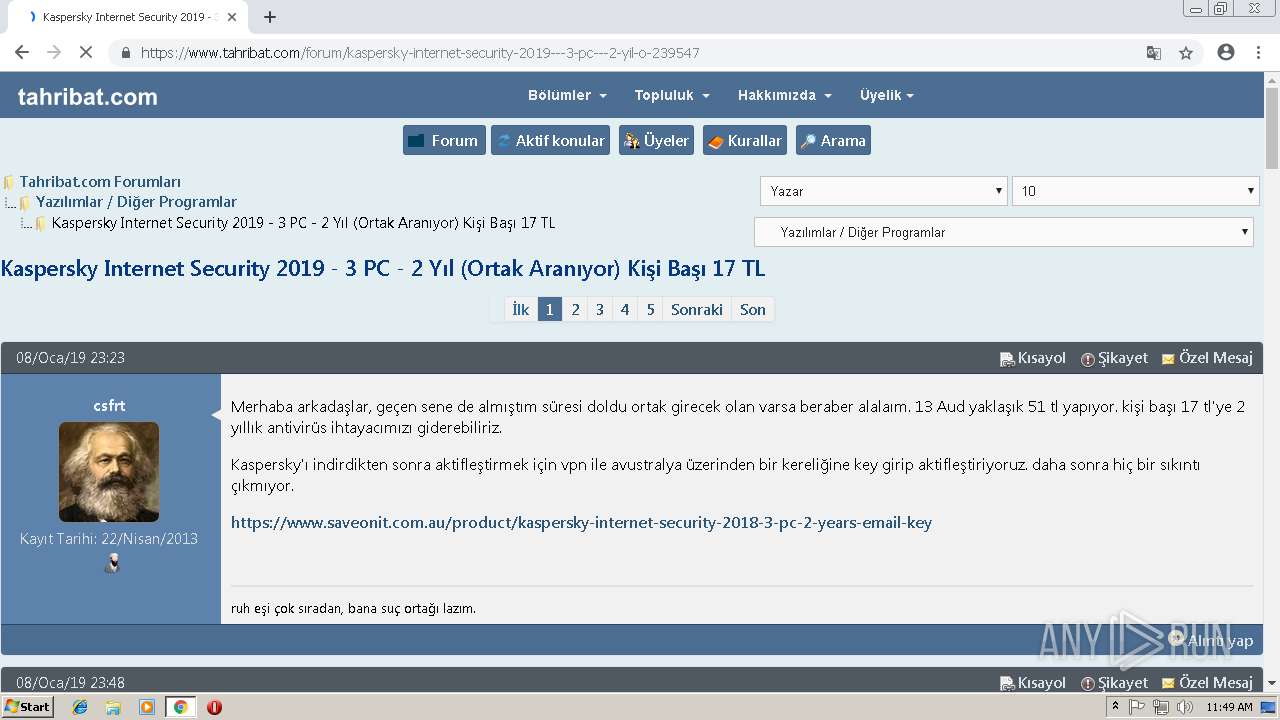
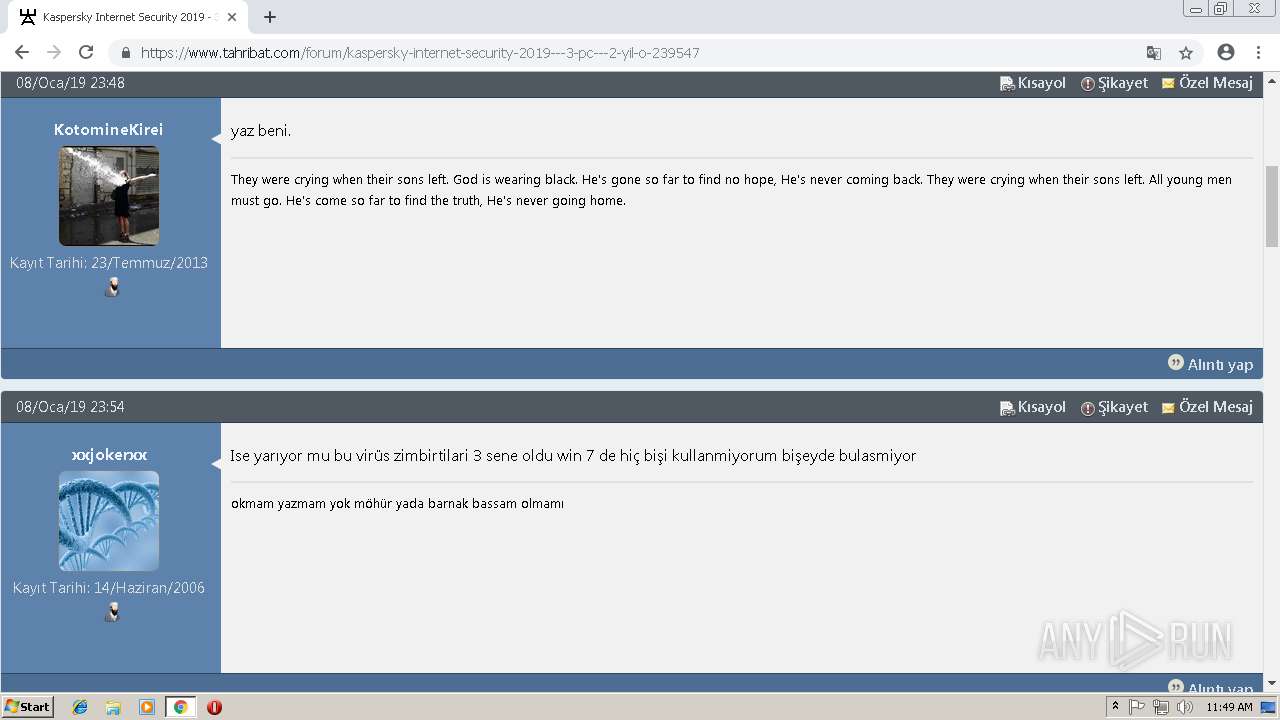
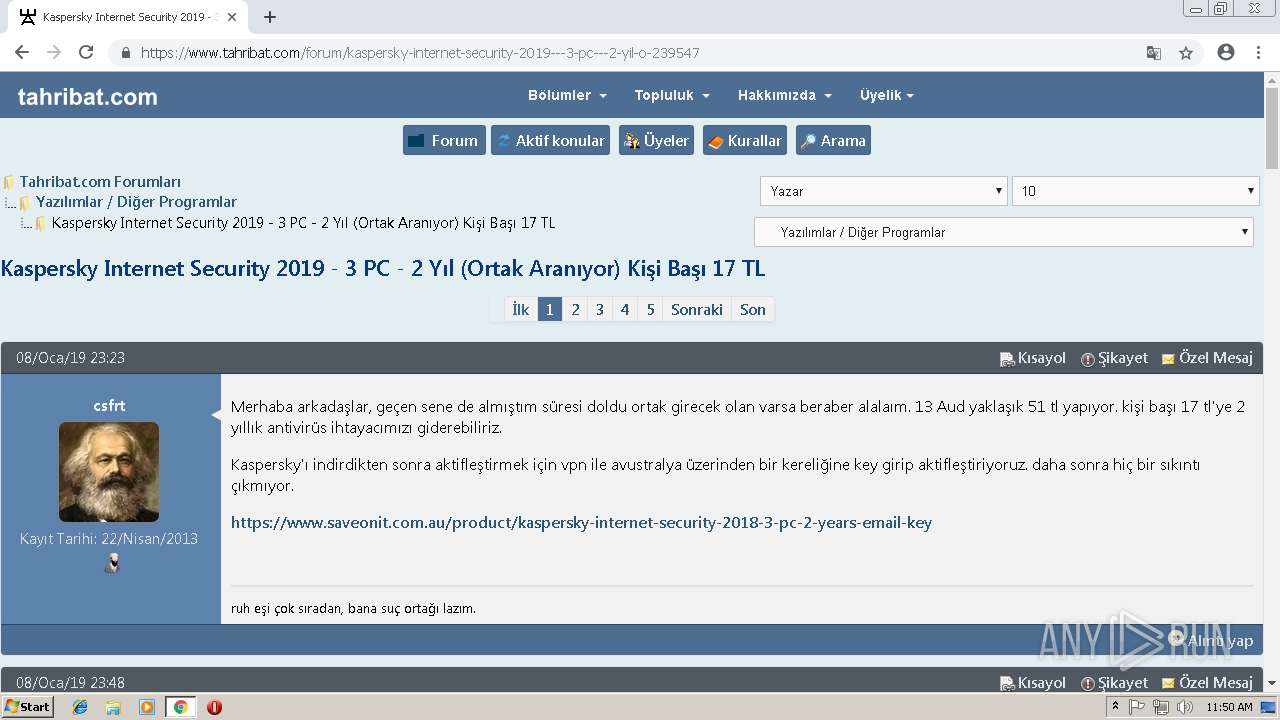
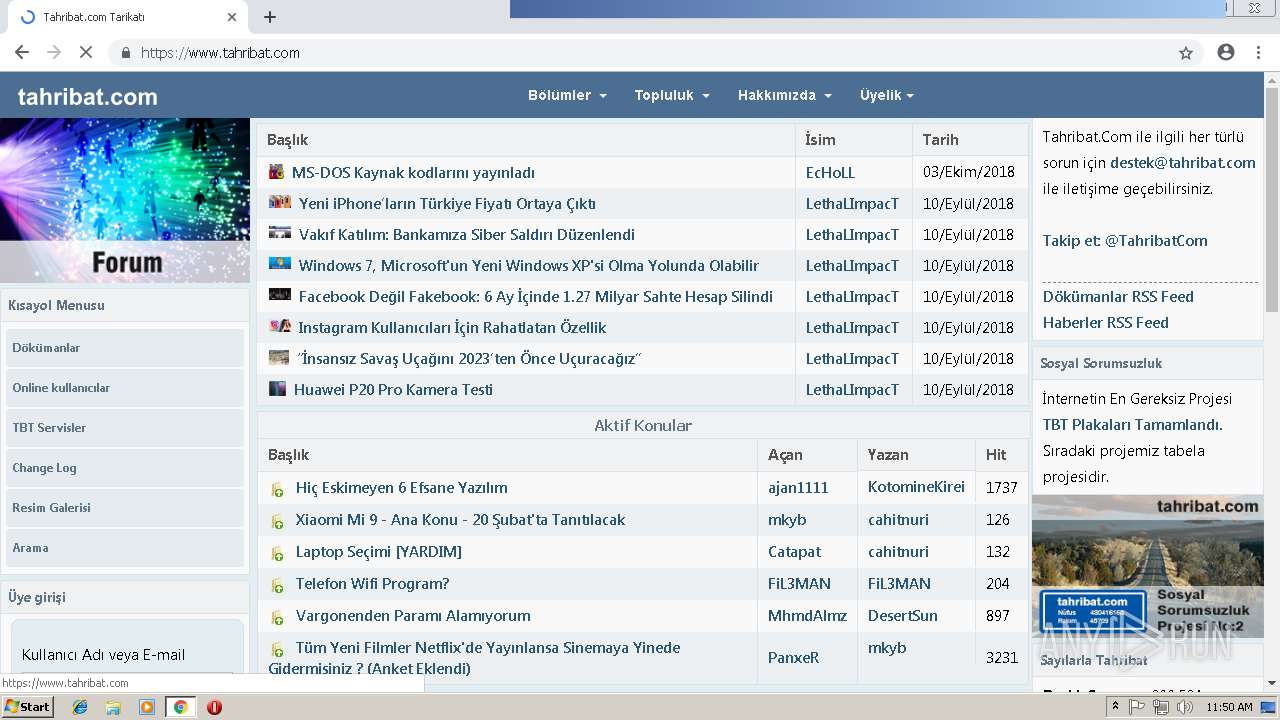
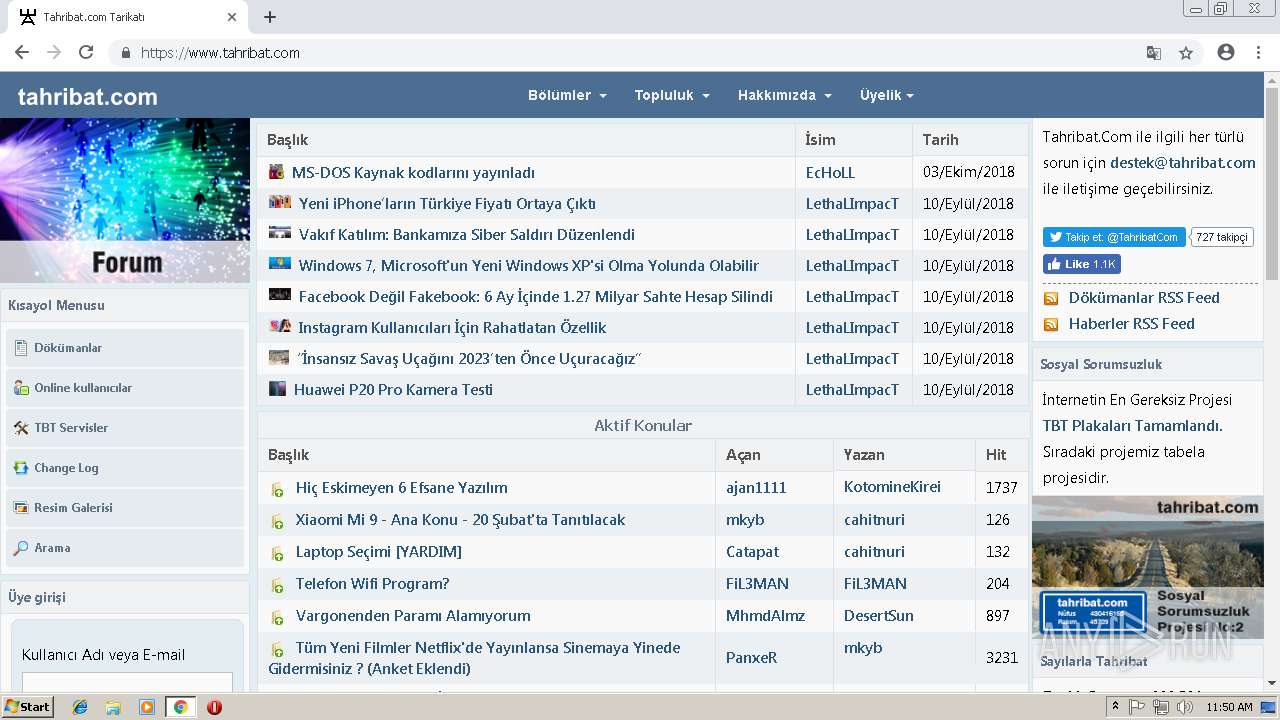
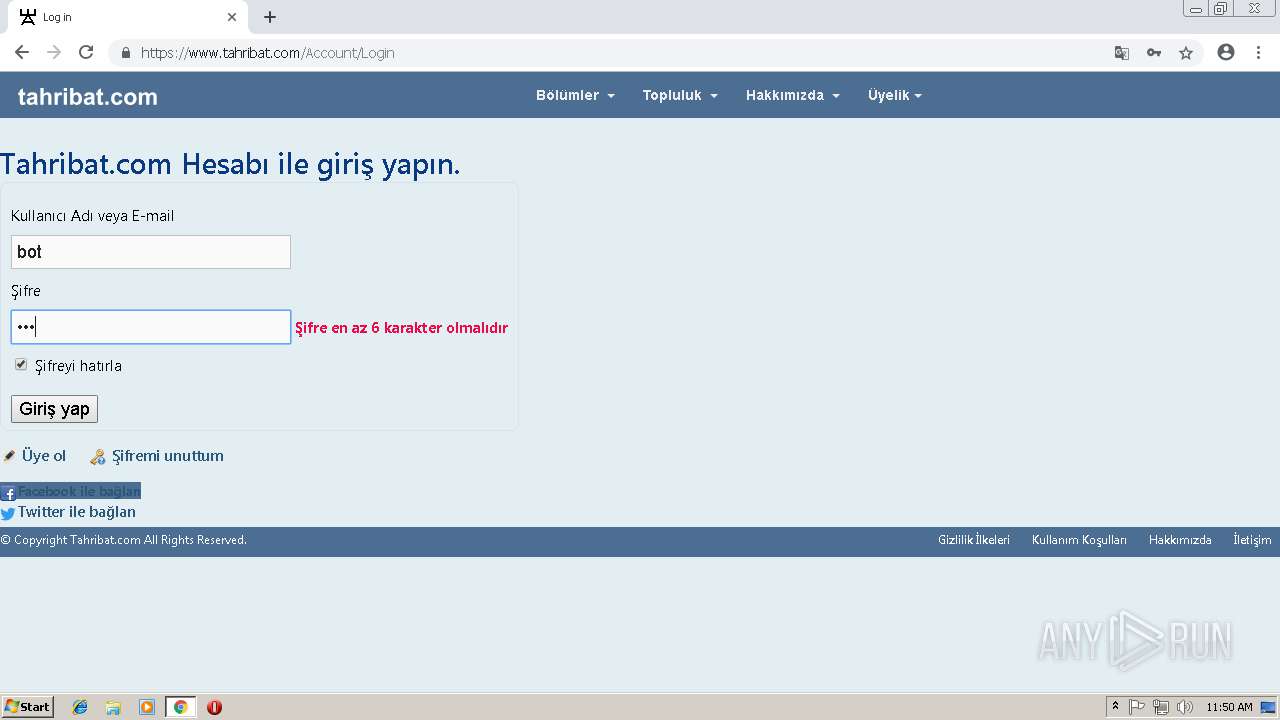
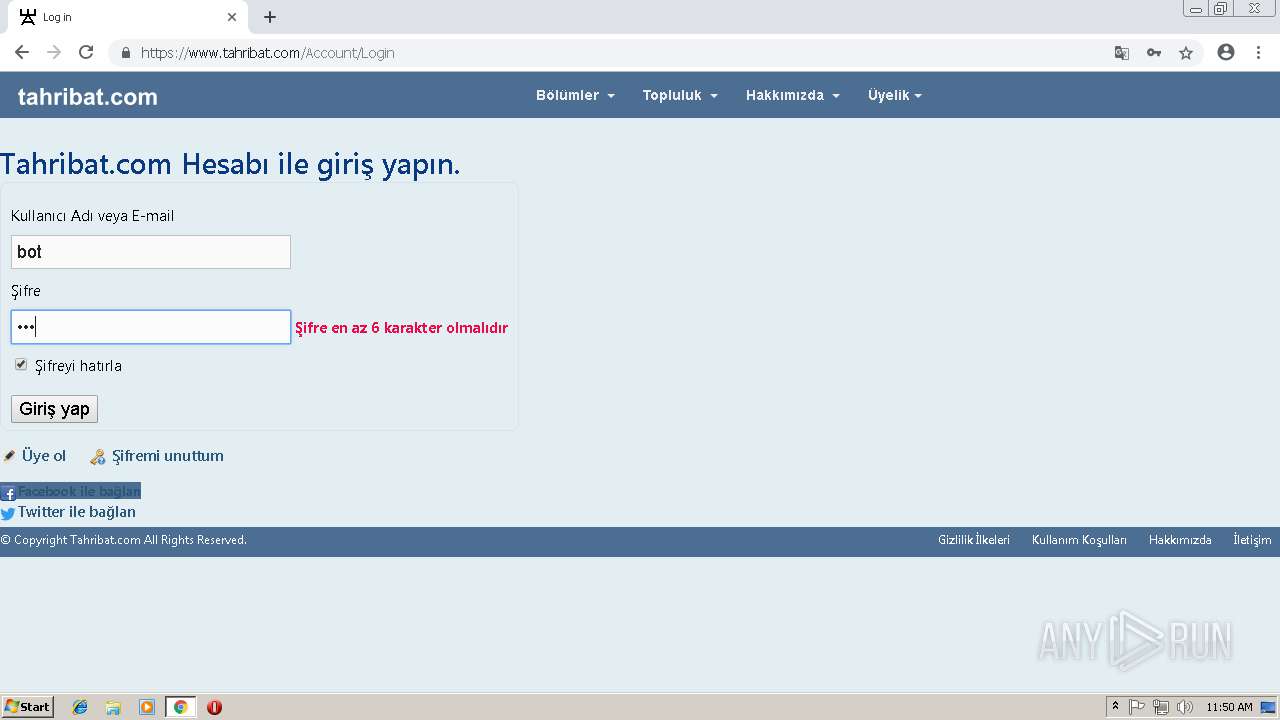
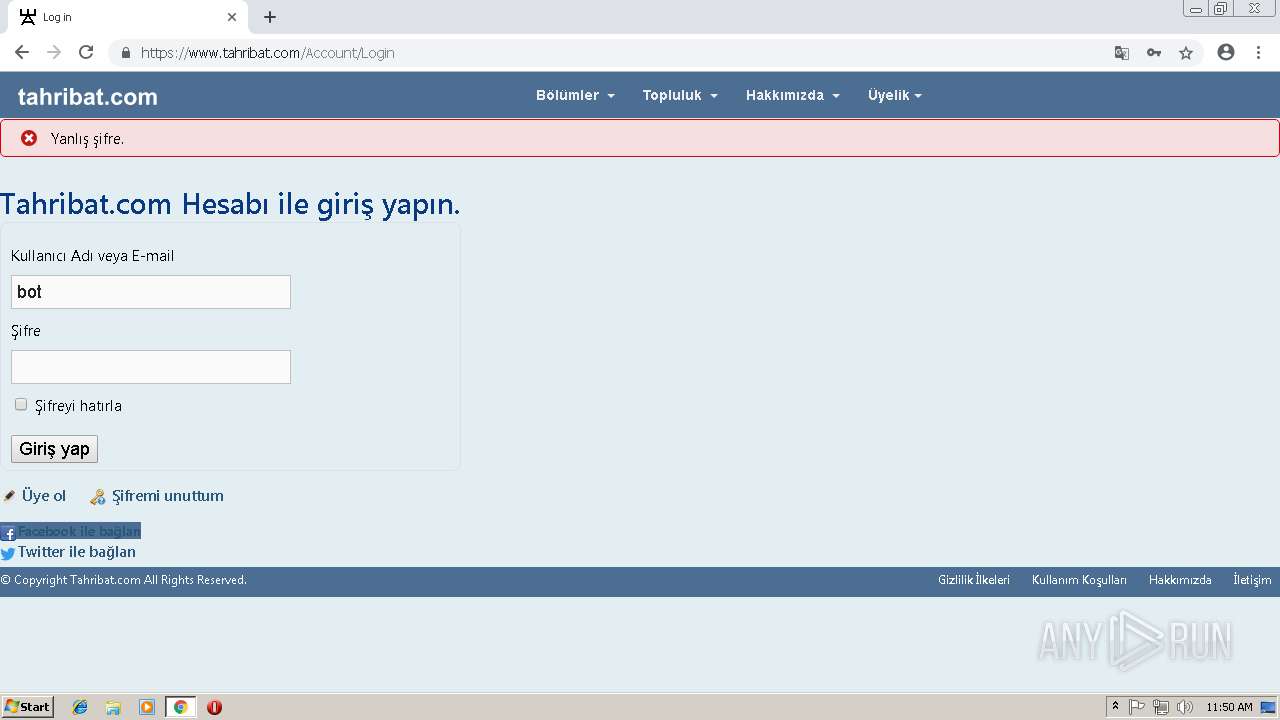
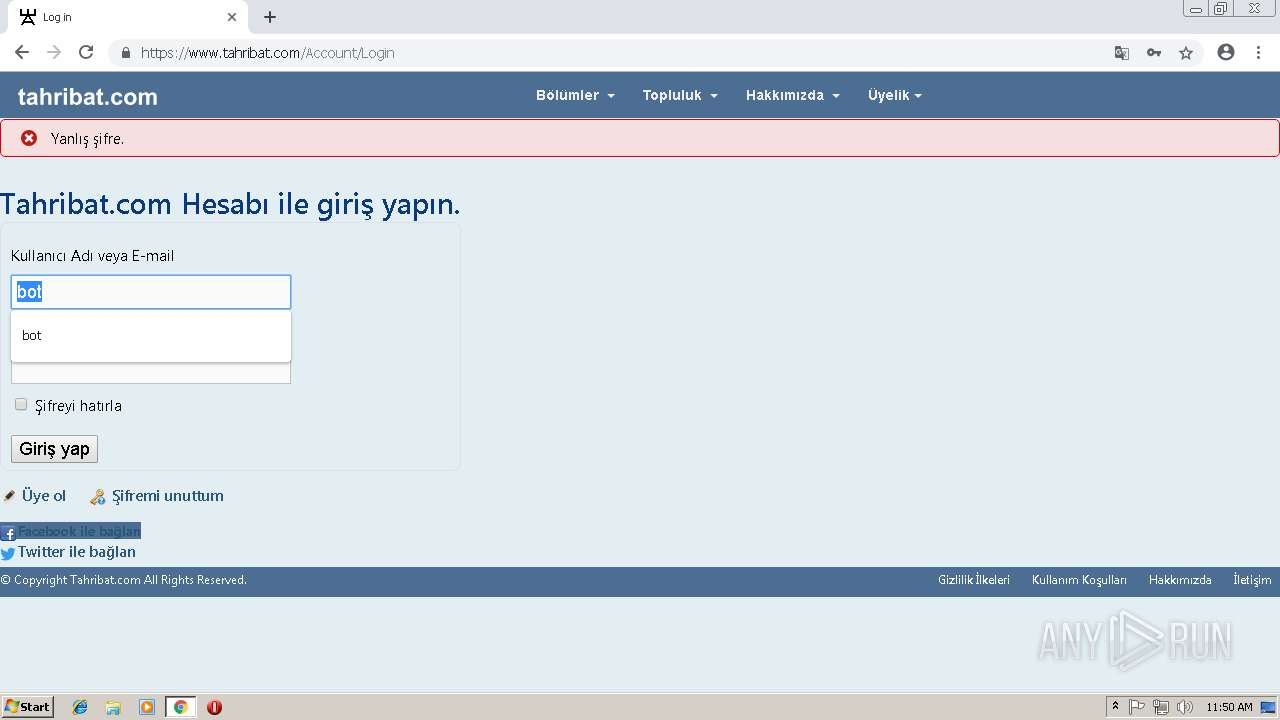
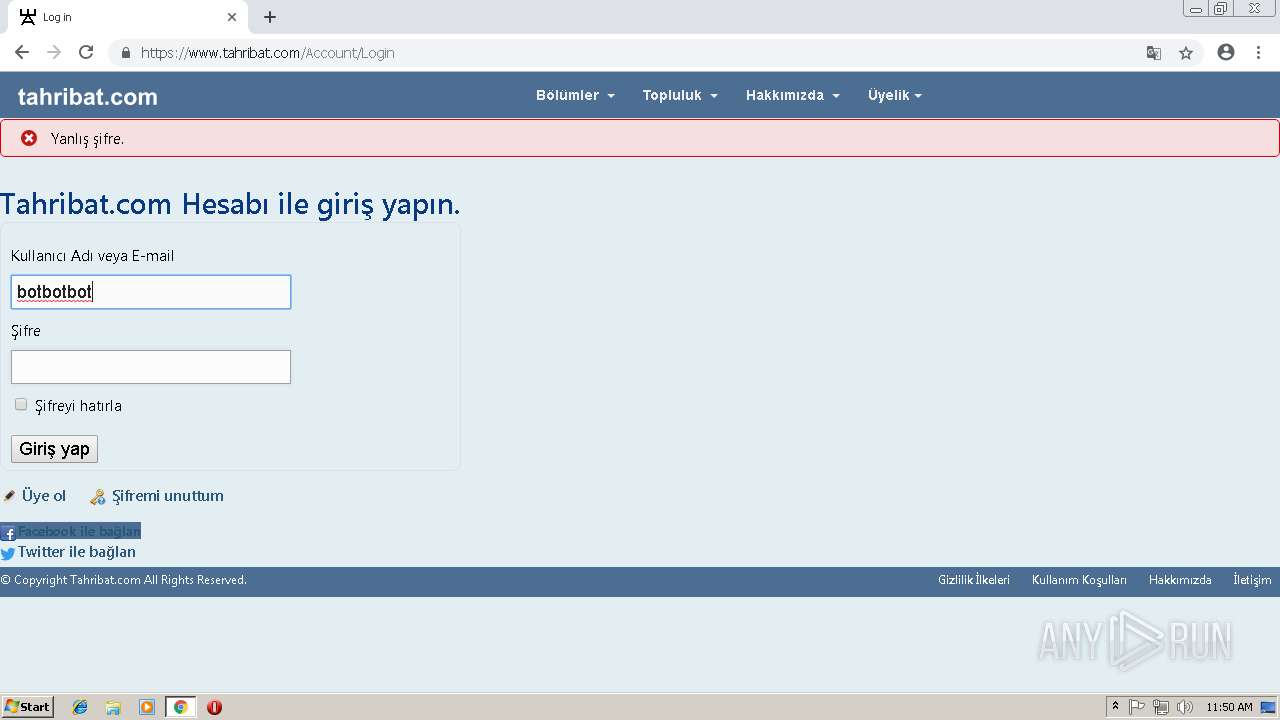
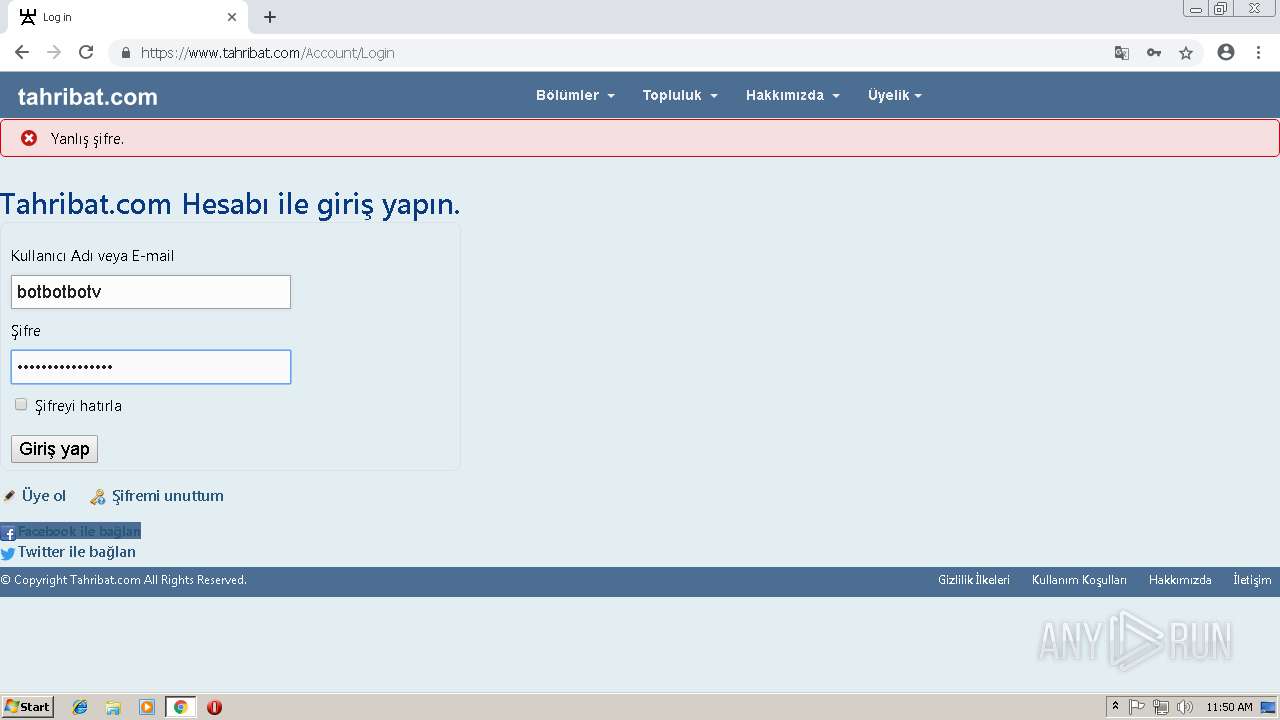
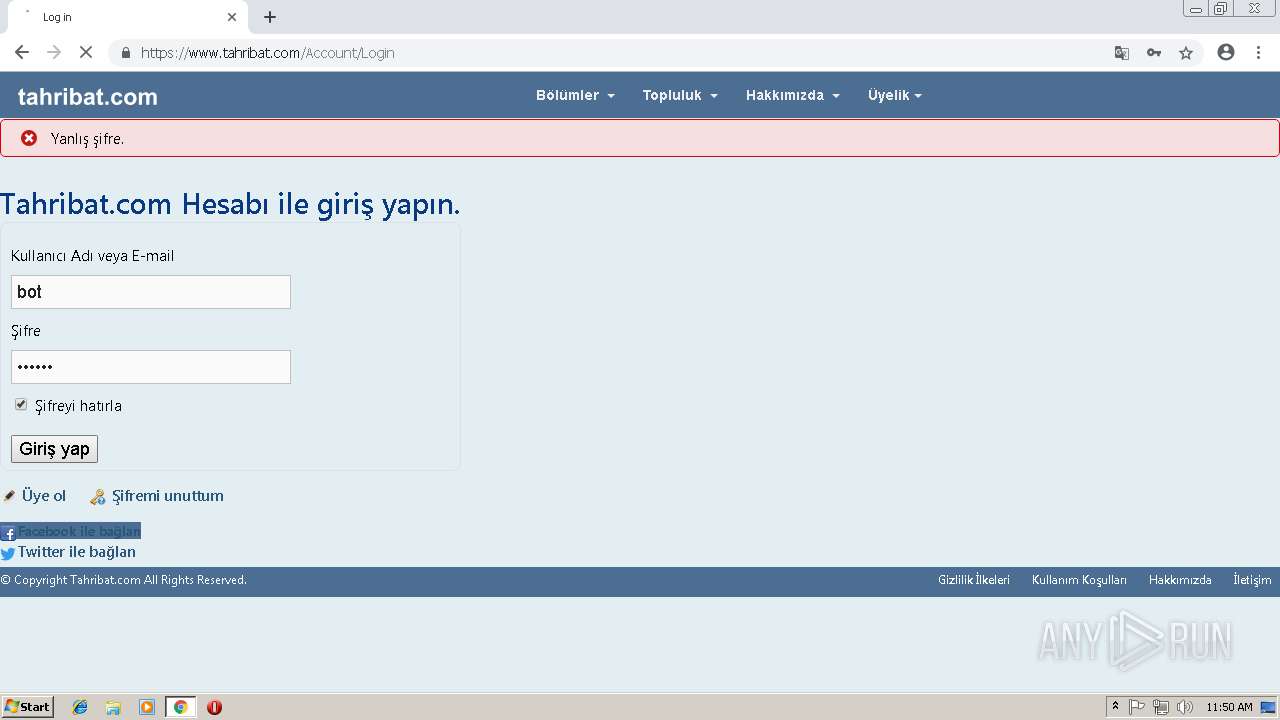
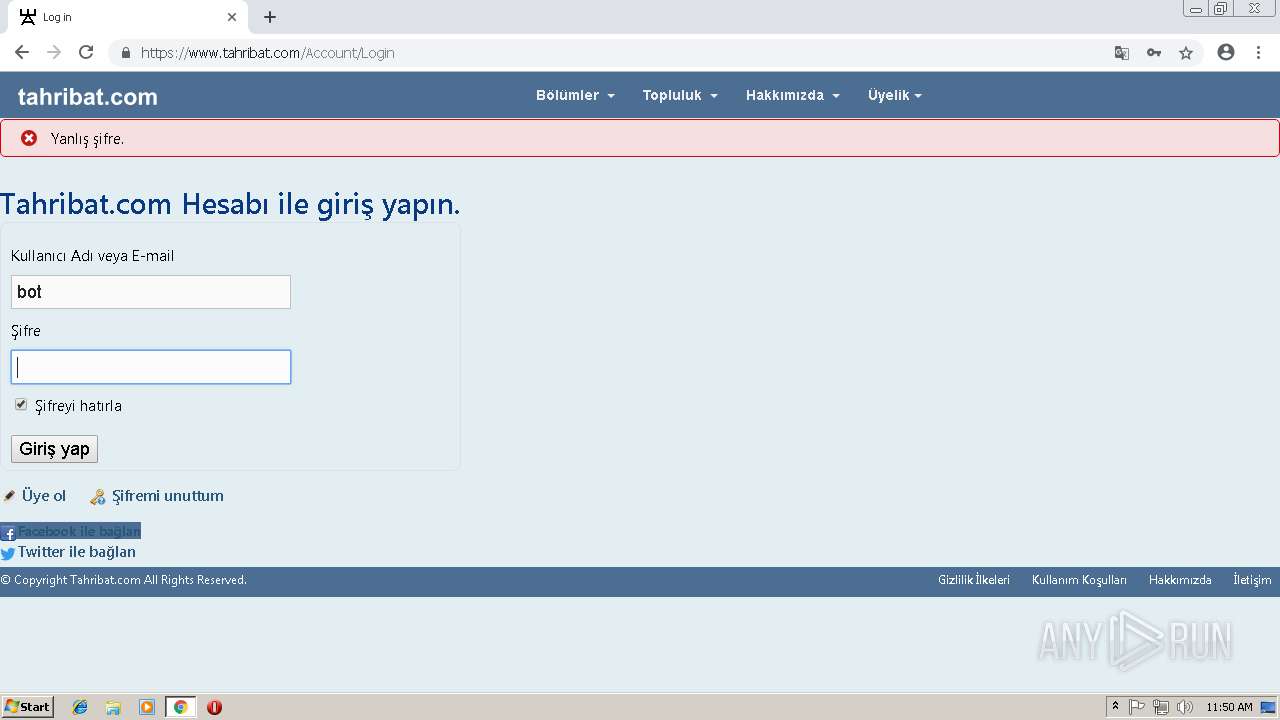
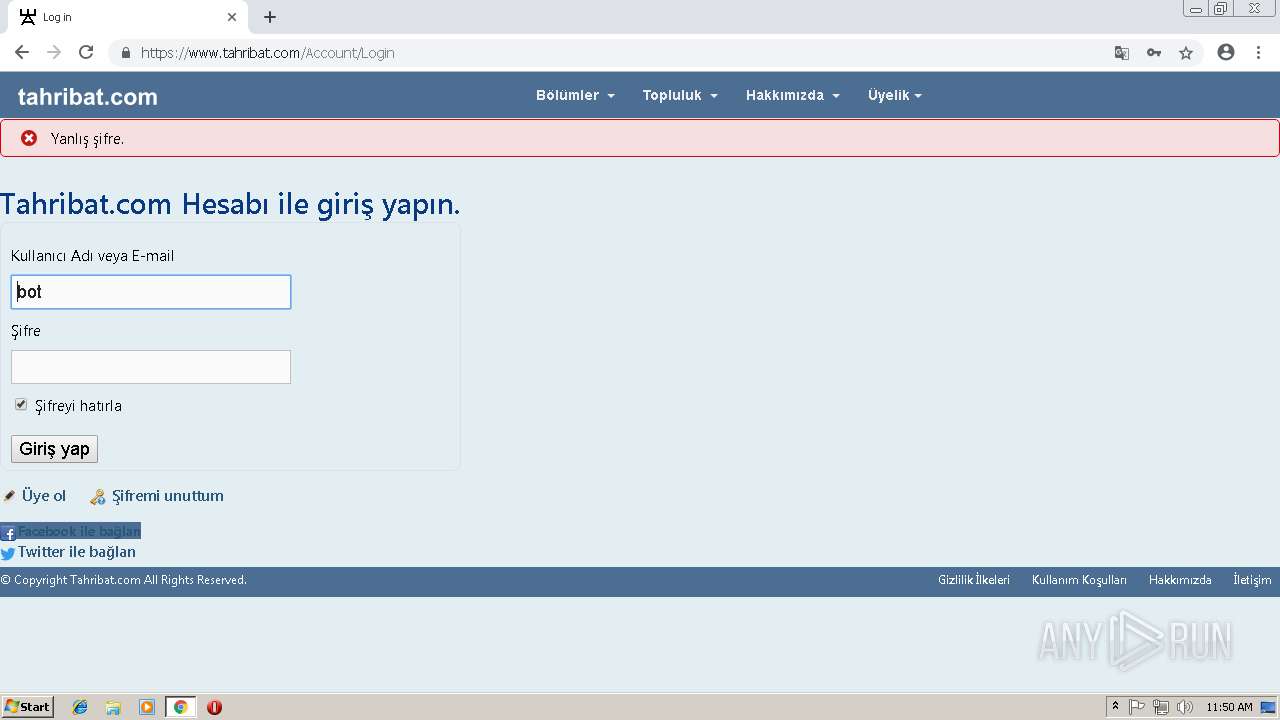
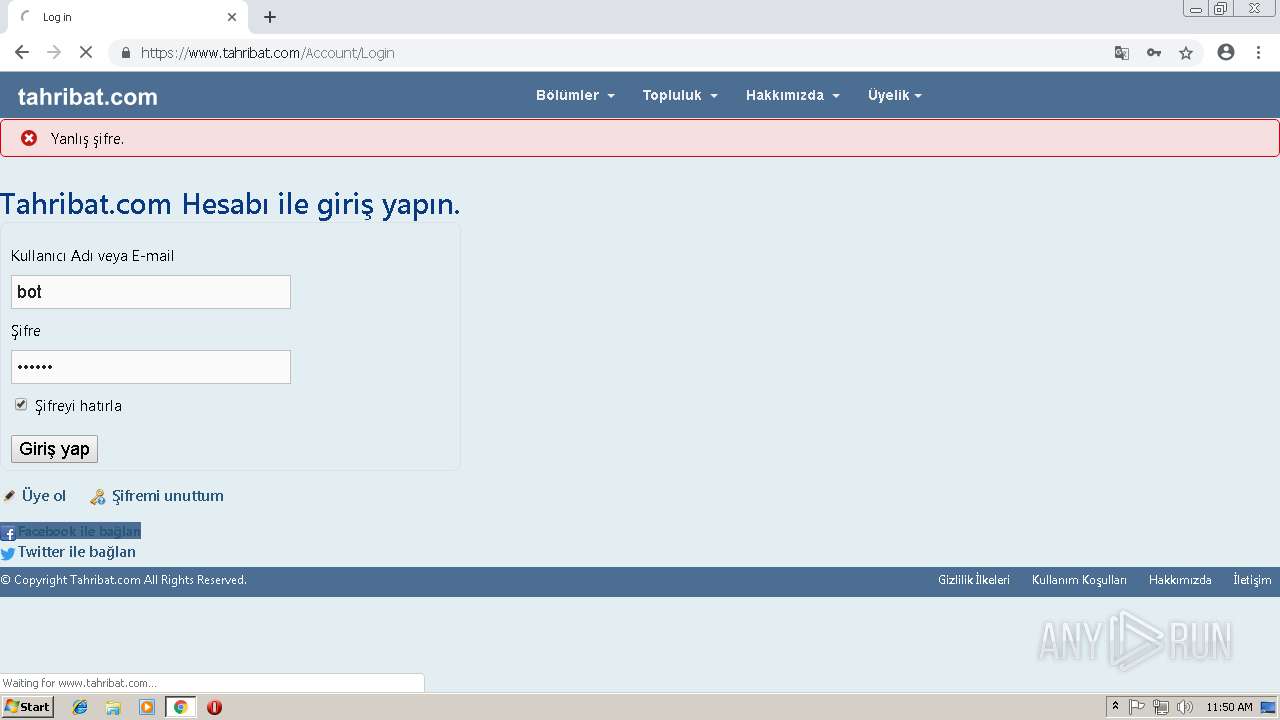
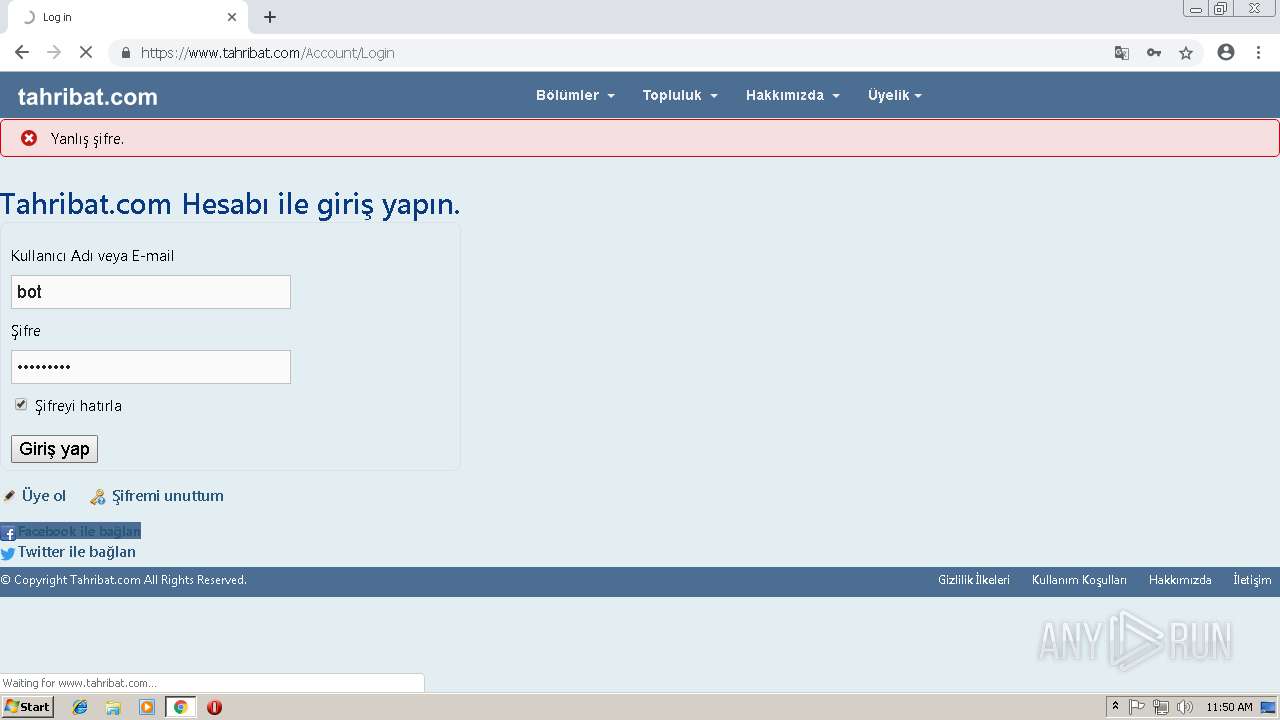
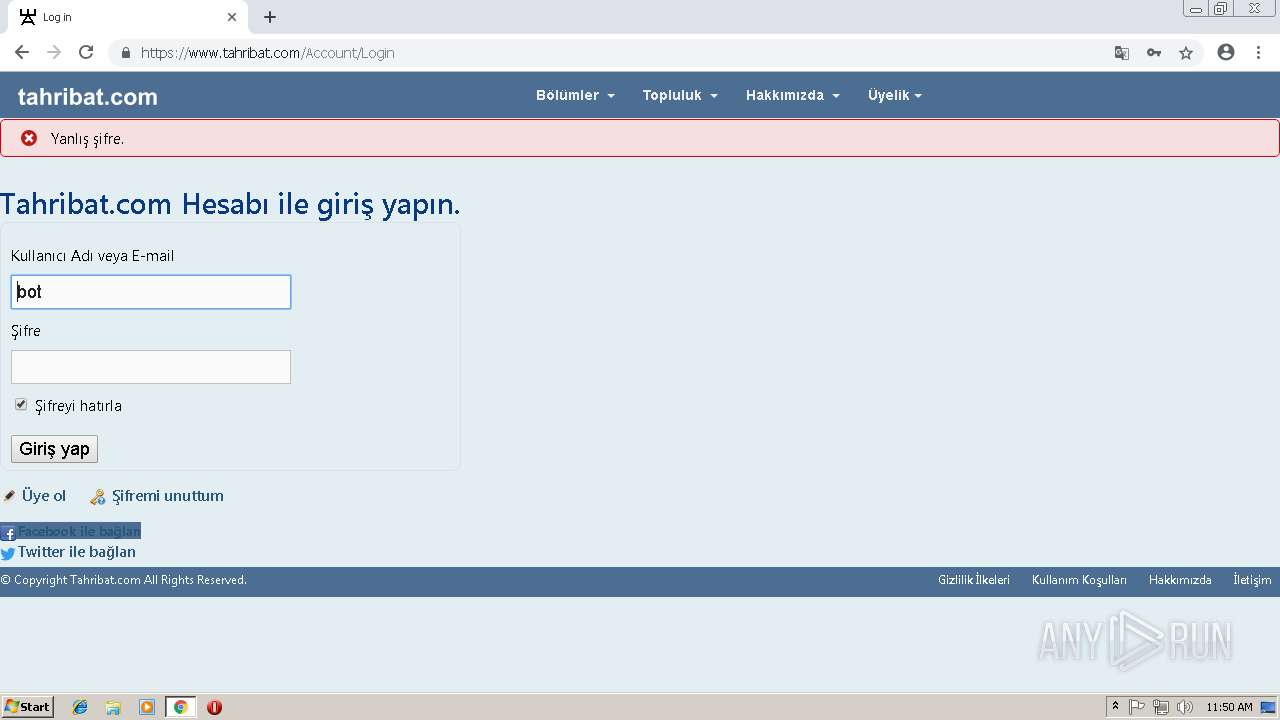
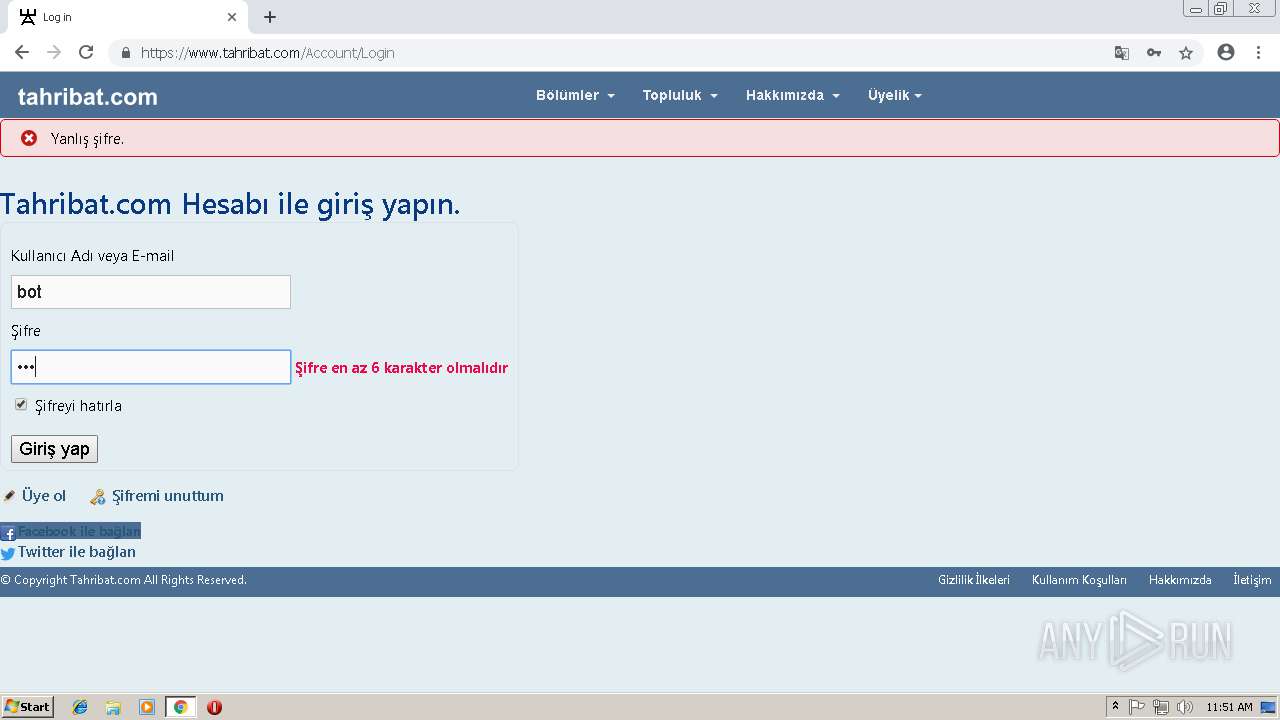
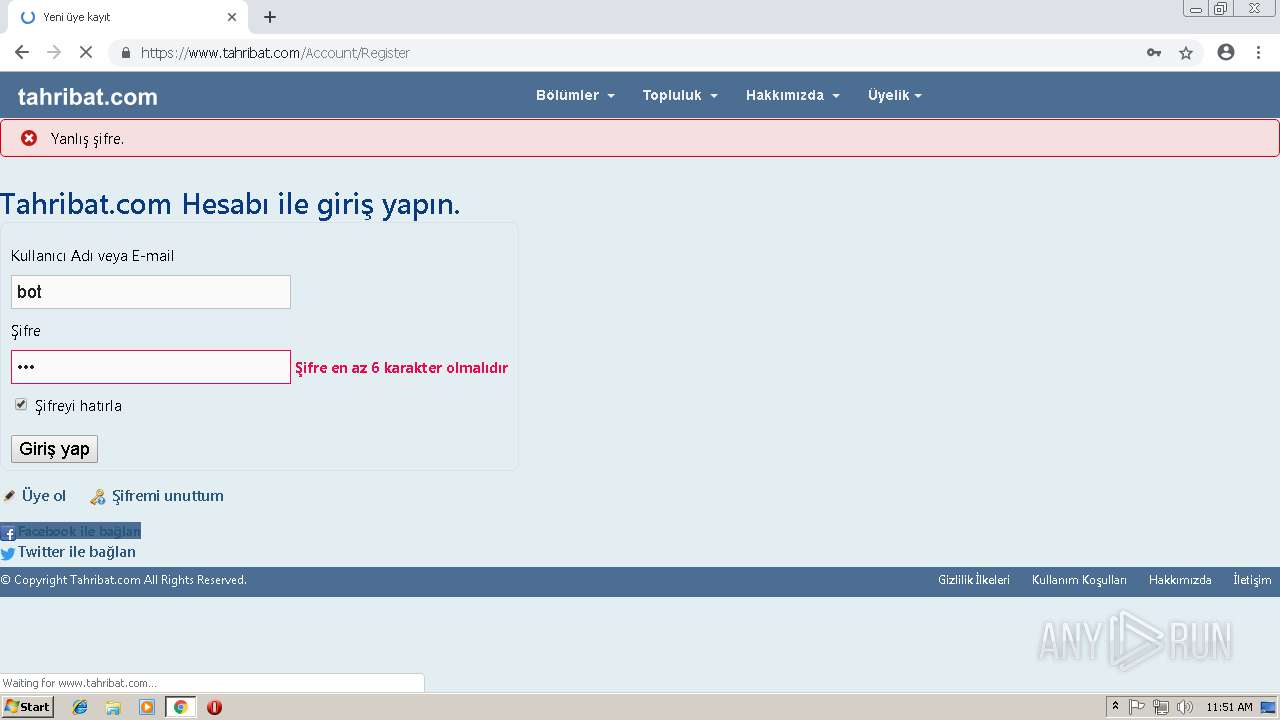
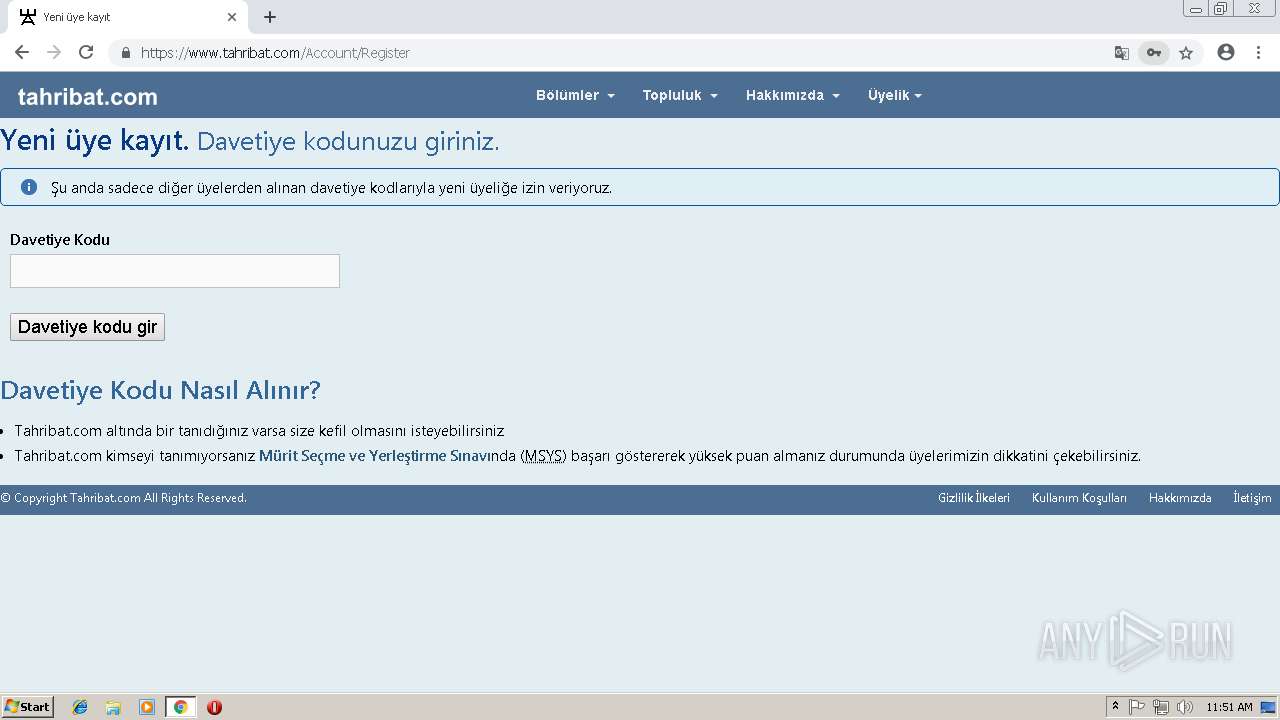
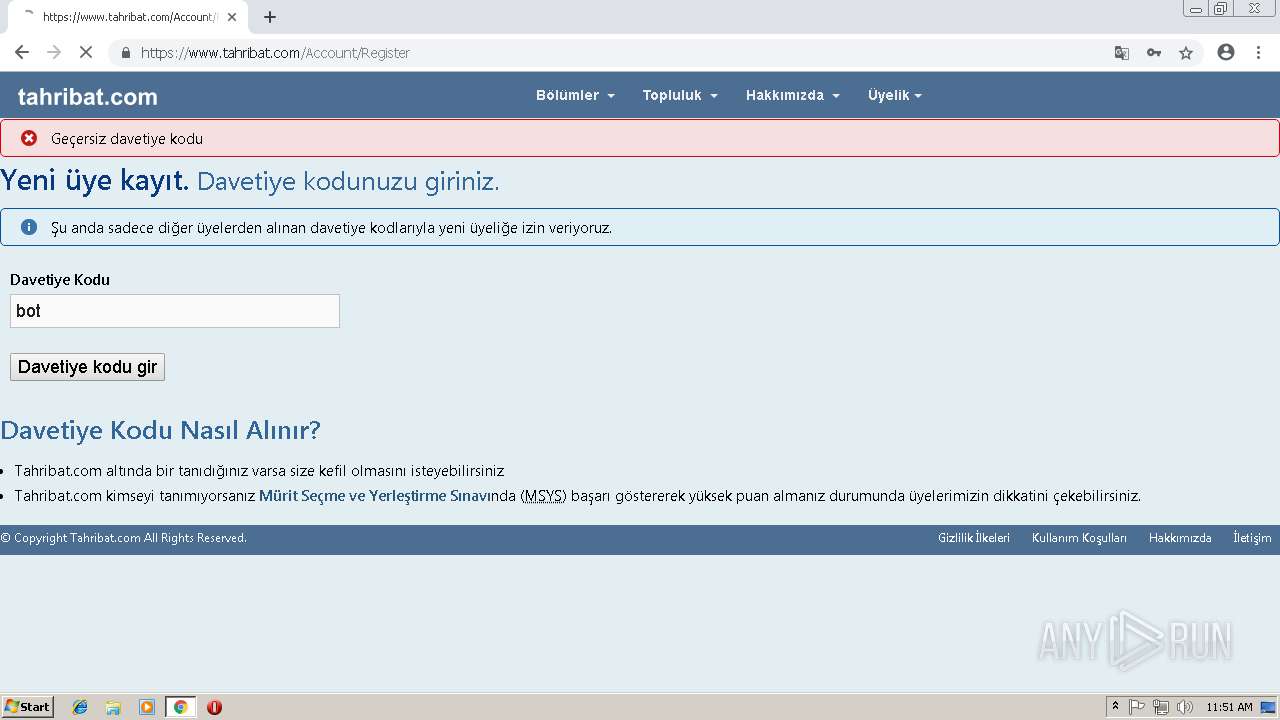
128 | chrome.exe | GET | 302 | 104.31.9.176:80 | http://tahribat.com/ | US | — | — | whitelisted |
128 | chrome.exe | GET | 200 | 104.31.8.176:80 | http://www.tahribat.com/css/Themes/mavimsi/main.css | US | text | 7.32 Kb | suspicious |
128 | chrome.exe | GET | 200 | 104.31.8.176:80 | http://www.tahribat.com/Scripts/jquery.barrating.min.js | US | text | 1.28 Kb | suspicious |
128 | chrome.exe | GET | 200 | 104.31.8.176:80 | http://www.tahribat.com/css/jquery.barrating.css | US | text | 797 b | suspicious |
128 | chrome.exe | GET | 302 | 172.217.16.142:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYzUyQUFWOFljLTZ0SFk5N2hiaHlUc1haQQ/7218.1203.0.0_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 509 b | whitelisted |
128 | chrome.exe | GET | 200 | 104.31.8.176:80 | http://www.tahribat.com/Modules/Menu/tahribatcom.svg | US | image | 3.71 Kb | suspicious |
128 | chrome.exe | GET | 200 | 194.9.24.115:80 | http://r8---sn-5uh5o-f5fd.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYzUyQUFWOFljLTZ0SFk5N2hiaHlUc1haQQ/7218.1203.0.0_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=212.7.222.142&mm=28&mn=sn-5uh5o-f5fd&ms=nvh&mt=1550576839&mv=m&pl=22&shardbypass=yes | PL | crx | 840 Kb | whitelisted |
128 | chrome.exe | GET | 200 | 104.31.8.176:80 | http://www.tahribat.com/css/Themes/mavimsi/tbtmenu2.css | US | text | 2.36 Kb | suspicious |
128 | chrome.exe | GET | 200 | 104.31.8.176:80 | http://www.tahribat.com/ | US | html | 12.9 Kb | suspicious |
128 | chrome.exe | GET | 200 | 104.31.8.176:80 | http://www.tahribat.com/img/Asset/forum2.png | US | image | 64.4 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3356 | chrome.exe | 172.217.16.164:443 | www.google.com | Google Inc. | US | whitelisted |
3356 | chrome.exe | 216.58.207.67:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3356 | chrome.exe | 172.217.21.205:443 | accounts.google.com | Google Inc. | US | whitelisted |
3356 | chrome.exe | 172.217.22.99:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3356 | chrome.exe | 216.58.206.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3356 | chrome.exe | 216.58.207.38:443 | 2542116.fls.doubleclick.net | Google Inc. | US | whitelisted |
3356 | chrome.exe | 172.217.16.168:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
3356 | chrome.exe | 216.58.207.70:443 | static.doubleclick.net | Google Inc. | US | whitelisted |
3356 | chrome.exe | 172.217.22.14:443 | www.youtube.com | Google Inc. | US | whitelisted |
3356 | chrome.exe | 216.58.205.226:443 | googleads.g.doubleclick.net | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.google.com |
| malicious |
www.gstatic.com |
| whitelisted |
accounts.google.com |
| shared |
fonts.gstatic.com |
| whitelisted |
tools.google.com |
| whitelisted |
www.youtube.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
googleads.g.doubleclick.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
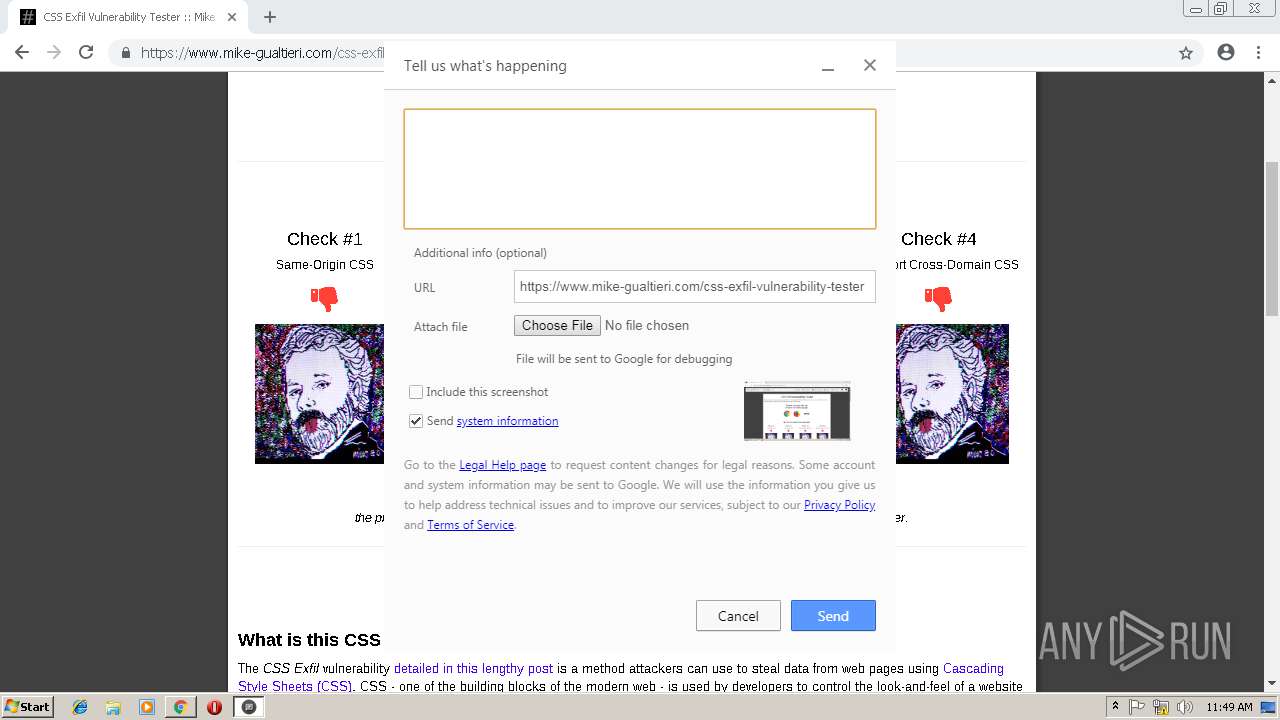
128 | chrome.exe | A Network Trojan was detected | ET CNC Ransomware Tracker Reported CnC Server group 1 |
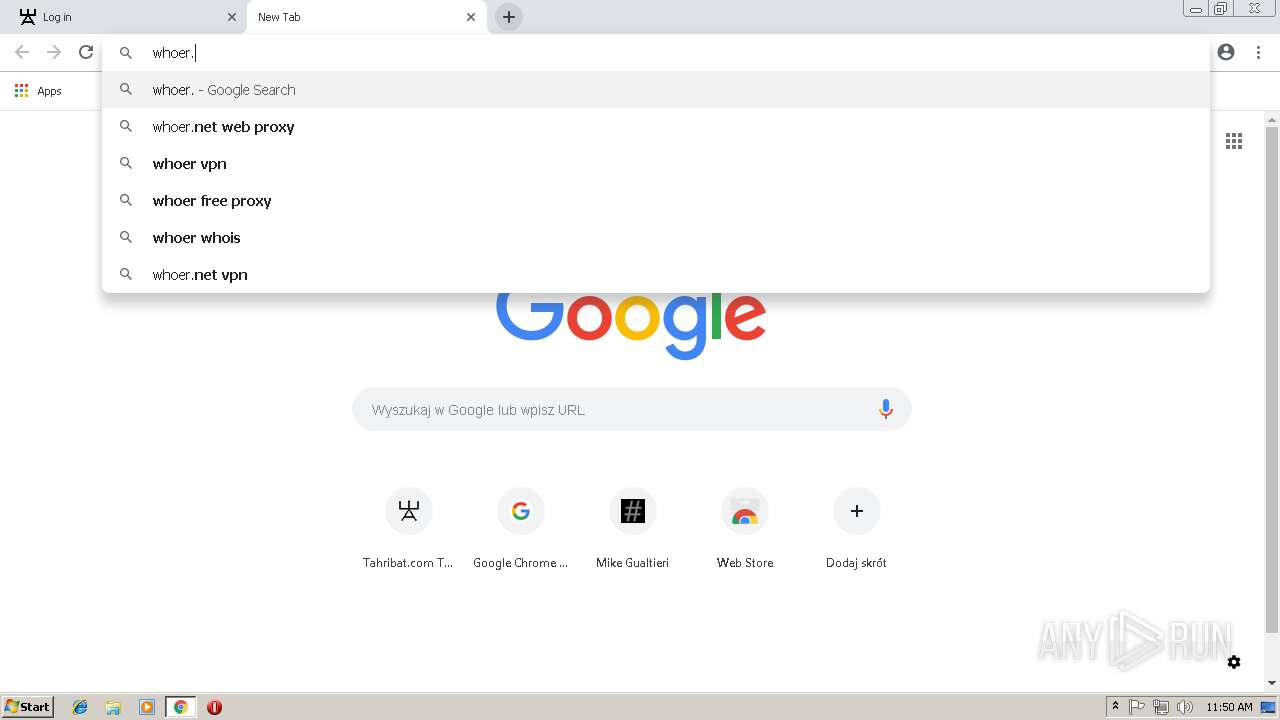
128 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Possible External IP Lookup whoer.net |