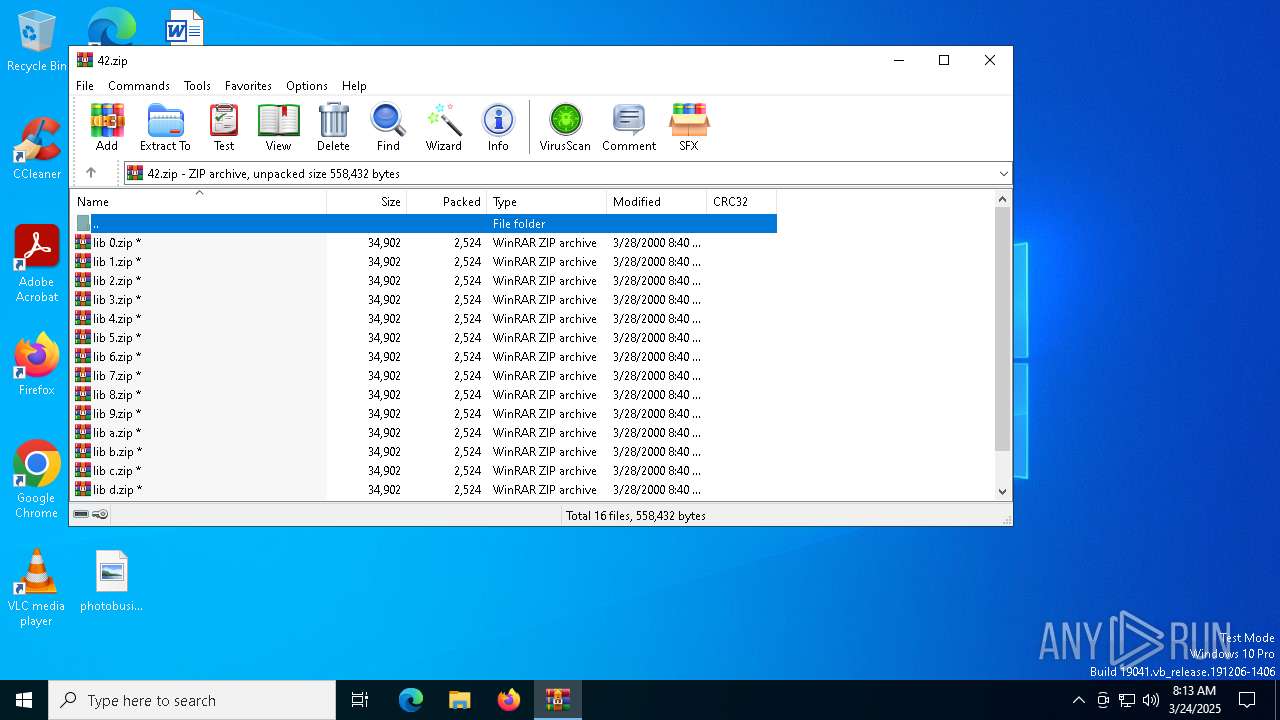
| File name: | 42.zip |
| Full analysis: | https://app.any.run/tasks/56ce8a5c-d02a-4430-aa64-c5c63f4996ce |
| Verdict: | Malicious activity |
| Analysis date: | March 24, 2025, 08:13:44 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v5.1 to extract, compression method=AES Encrypted |
| MD5: | 1DF9A18B18332F153918030B7B516615 |
| SHA1: | 6C42C62696616B72BBFC88A4BE4EAD57AA7BC503 |
| SHA256: | BBD05DE19AA2AF1455C0494639215898A15286D9B05073B6C4817FE24B2C36FA |
| SSDEEP: | 768:hzyVr8GSKL6O3QOXk/0u3wqOghrFCezL1VFJdbq2QTJTw02Q:hGx8DKXE//ZhhCirFi2cwK |
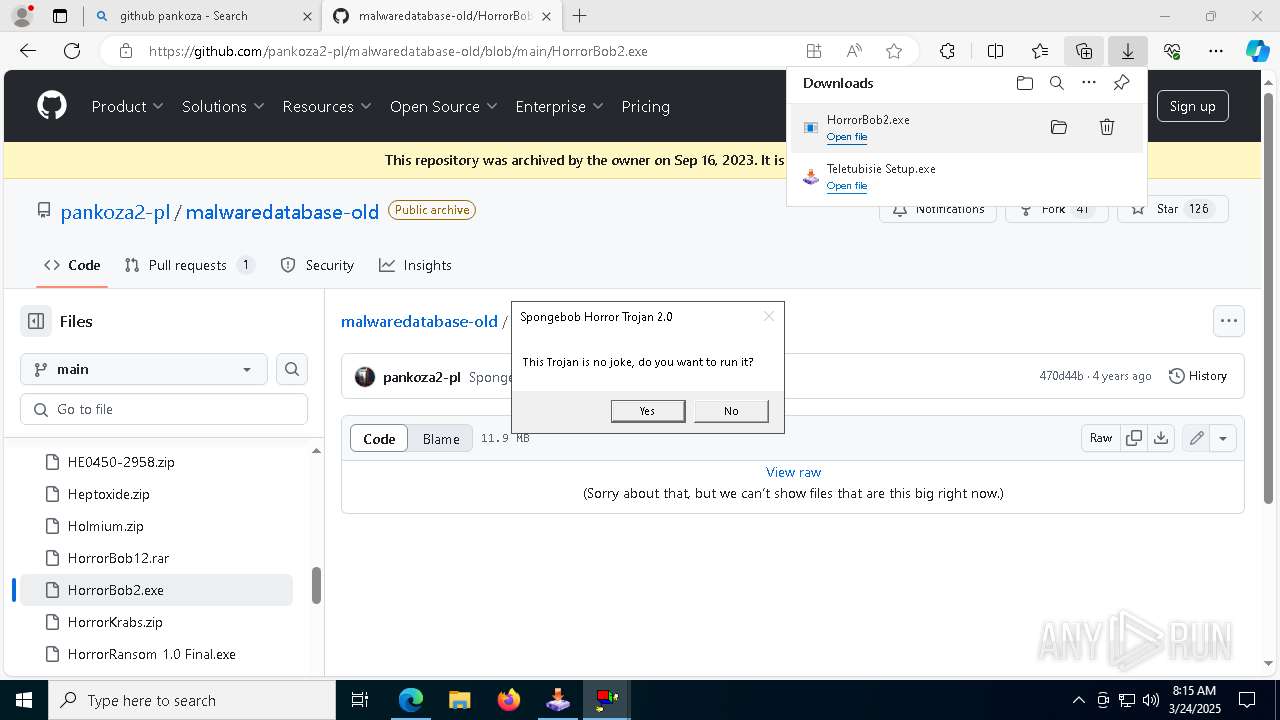
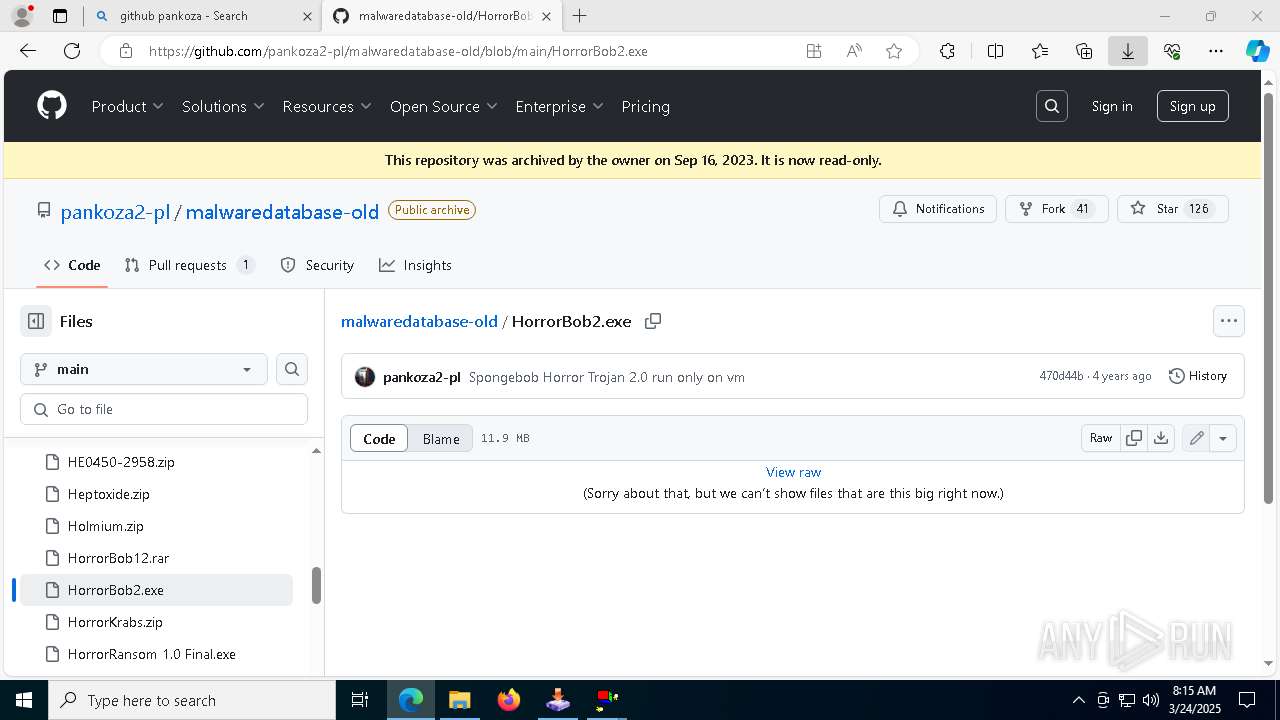
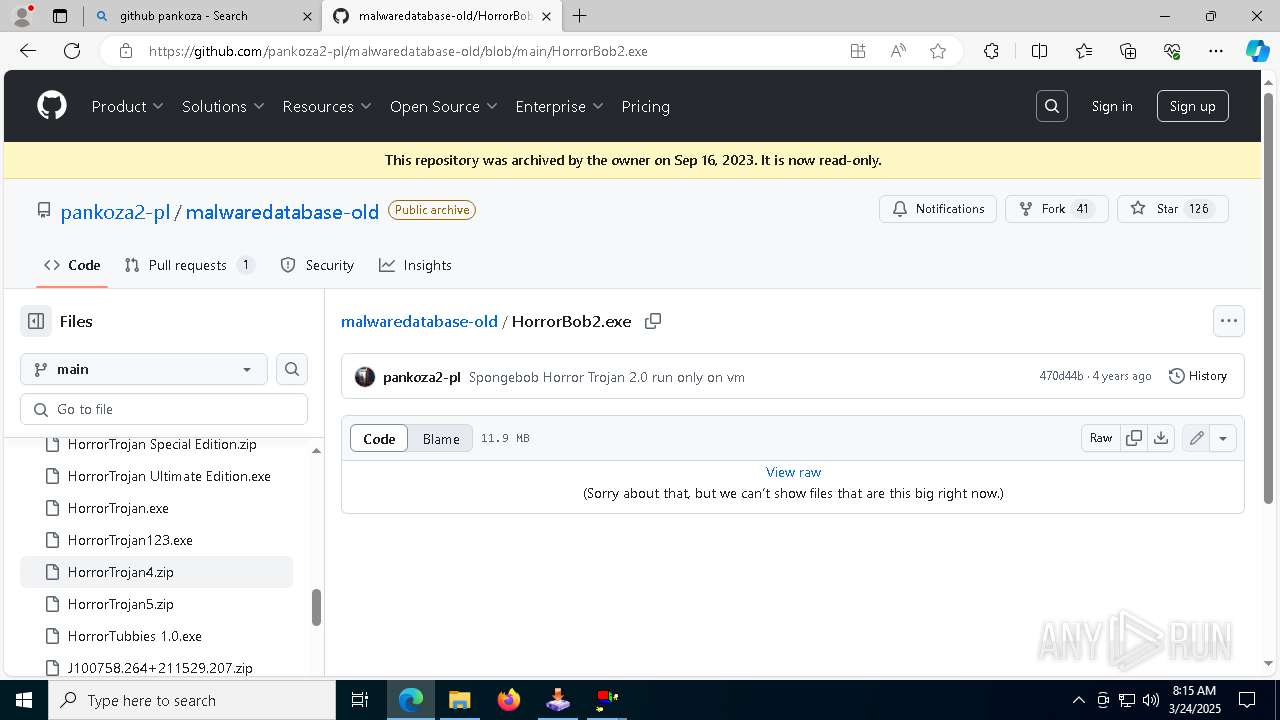
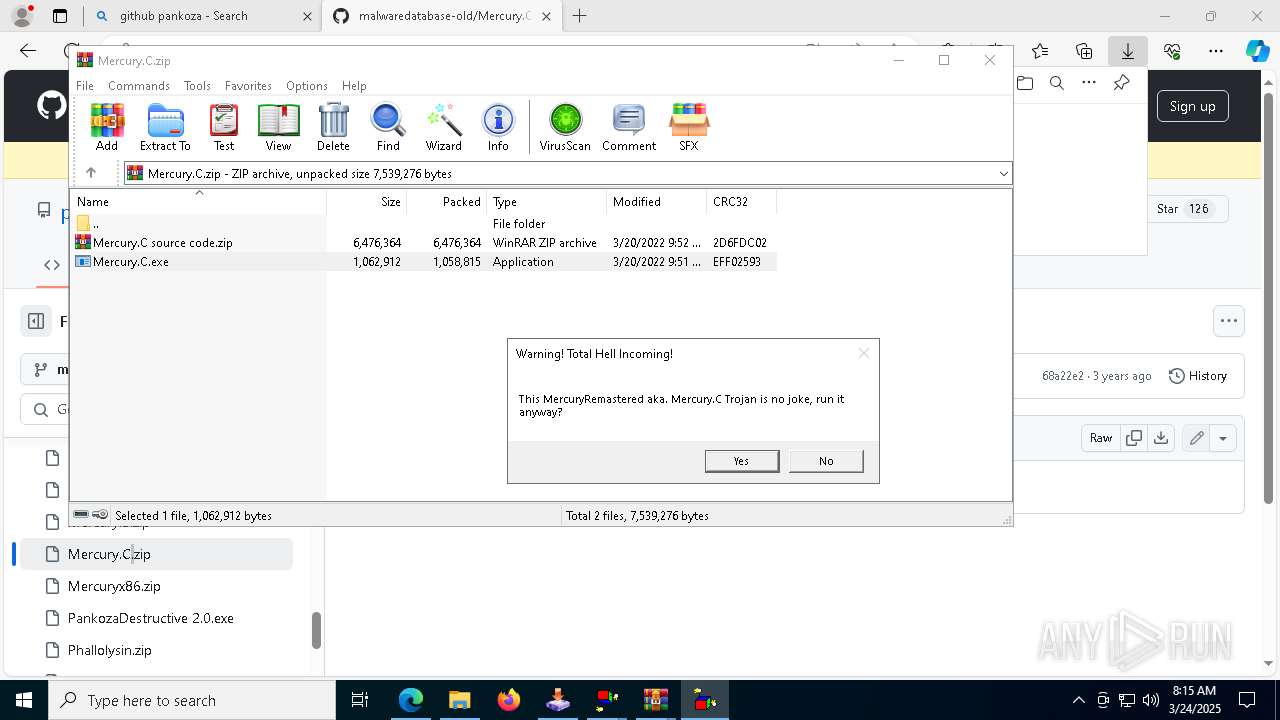
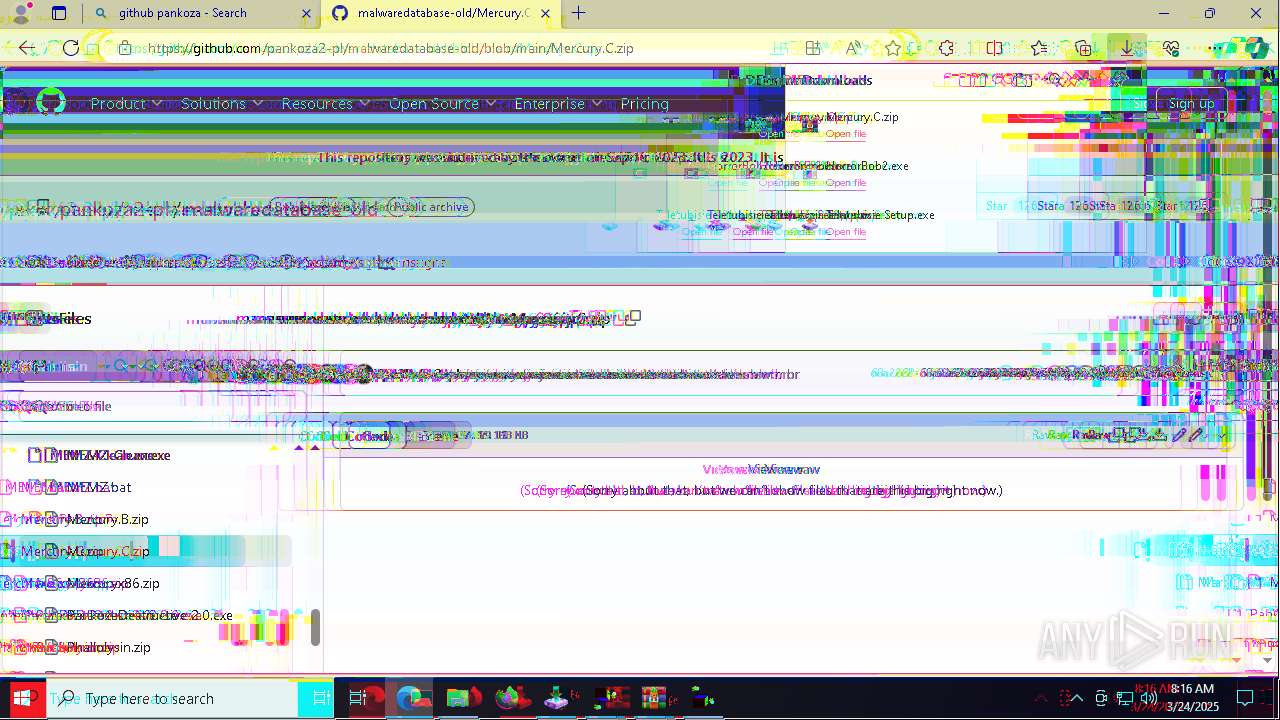
MALICIOUS
Starts NET.EXE to view/add/change user profiles
- net.exe (PID: 8600)
- cmd.exe (PID: 8280)
SUSPICIOUS
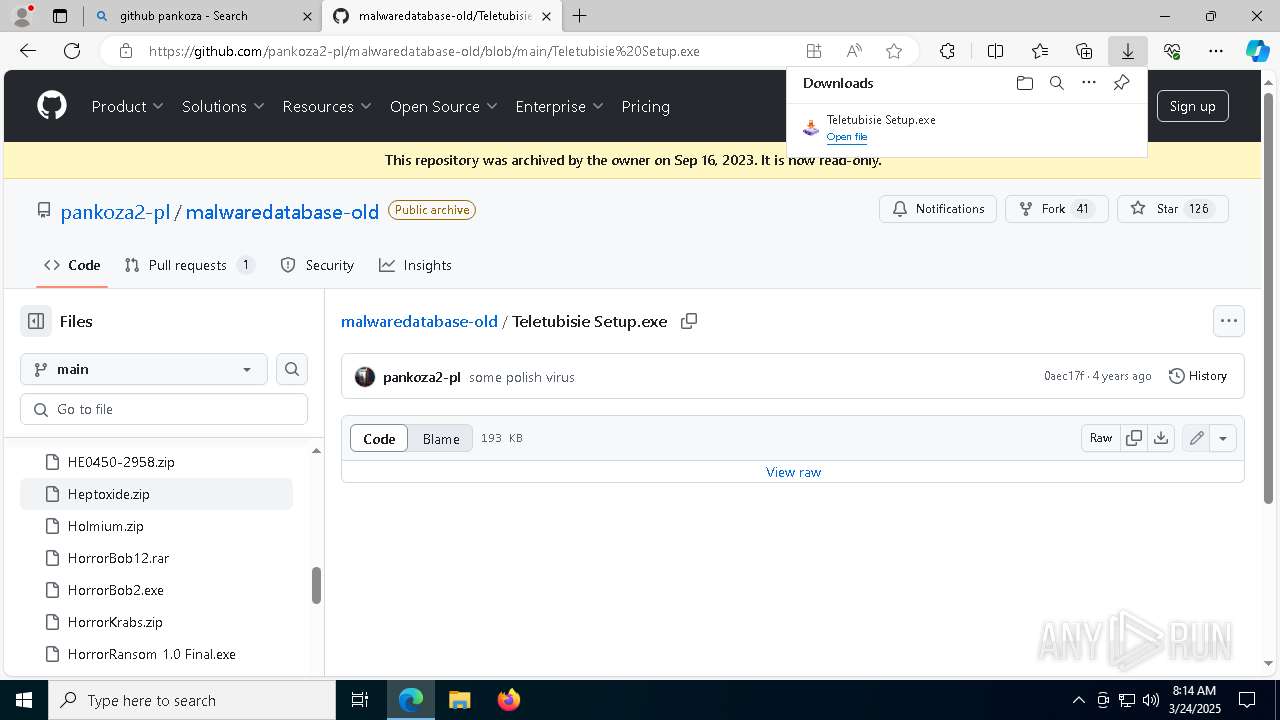
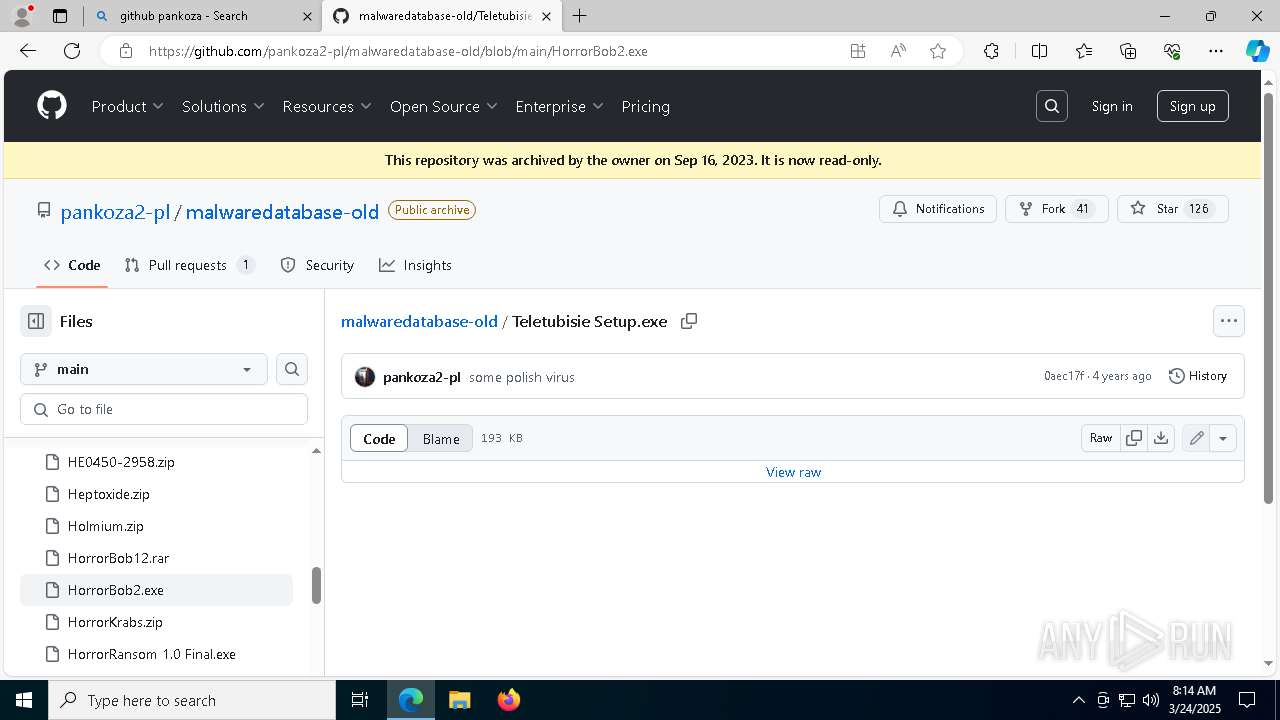
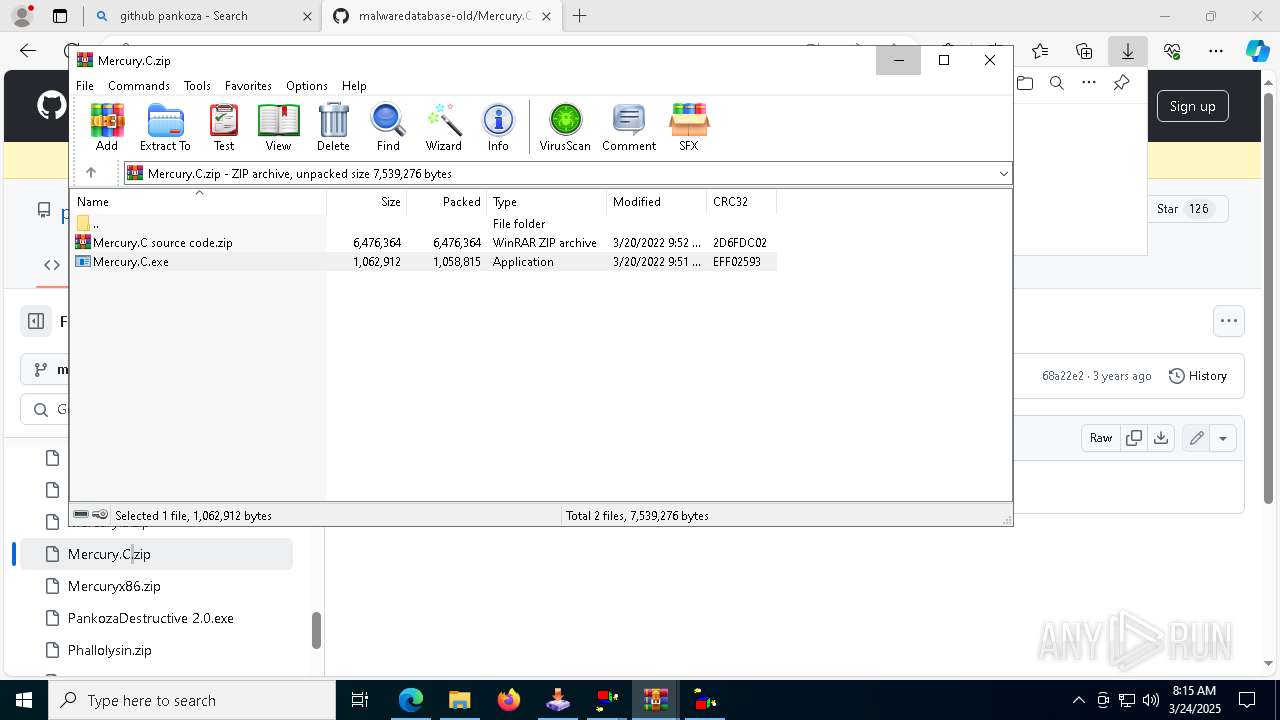
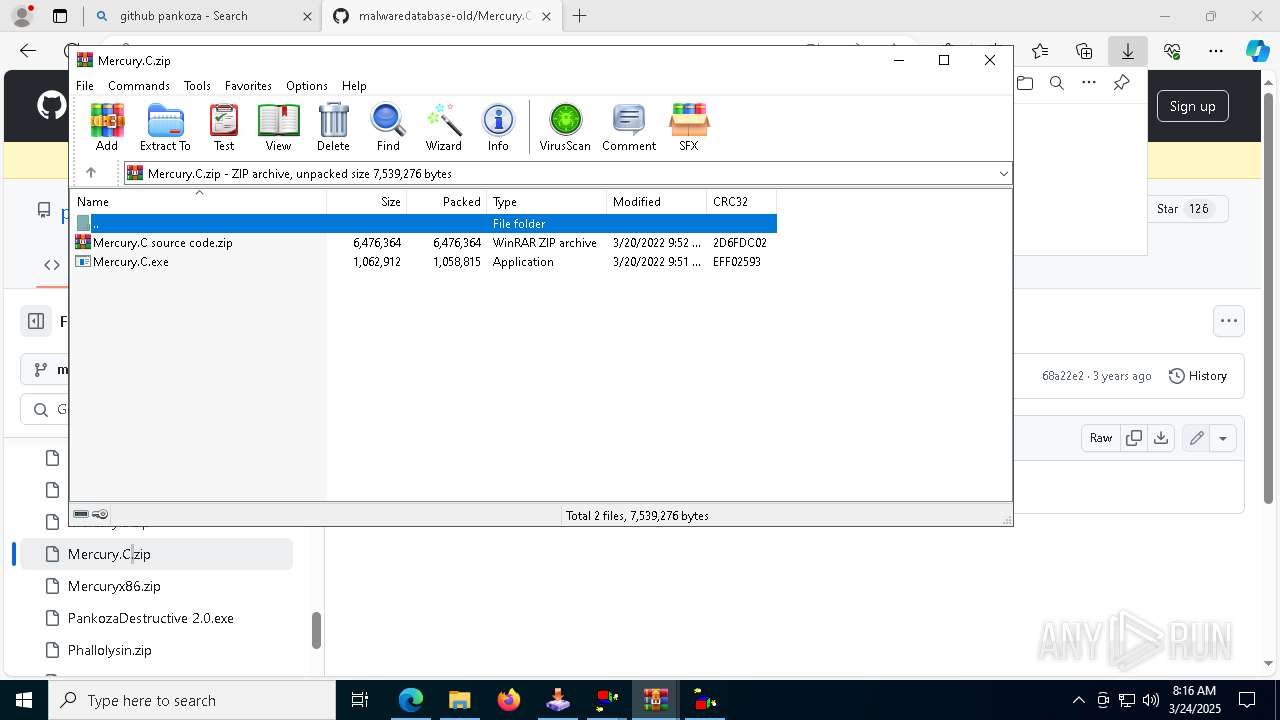
Executable content was dropped or overwritten
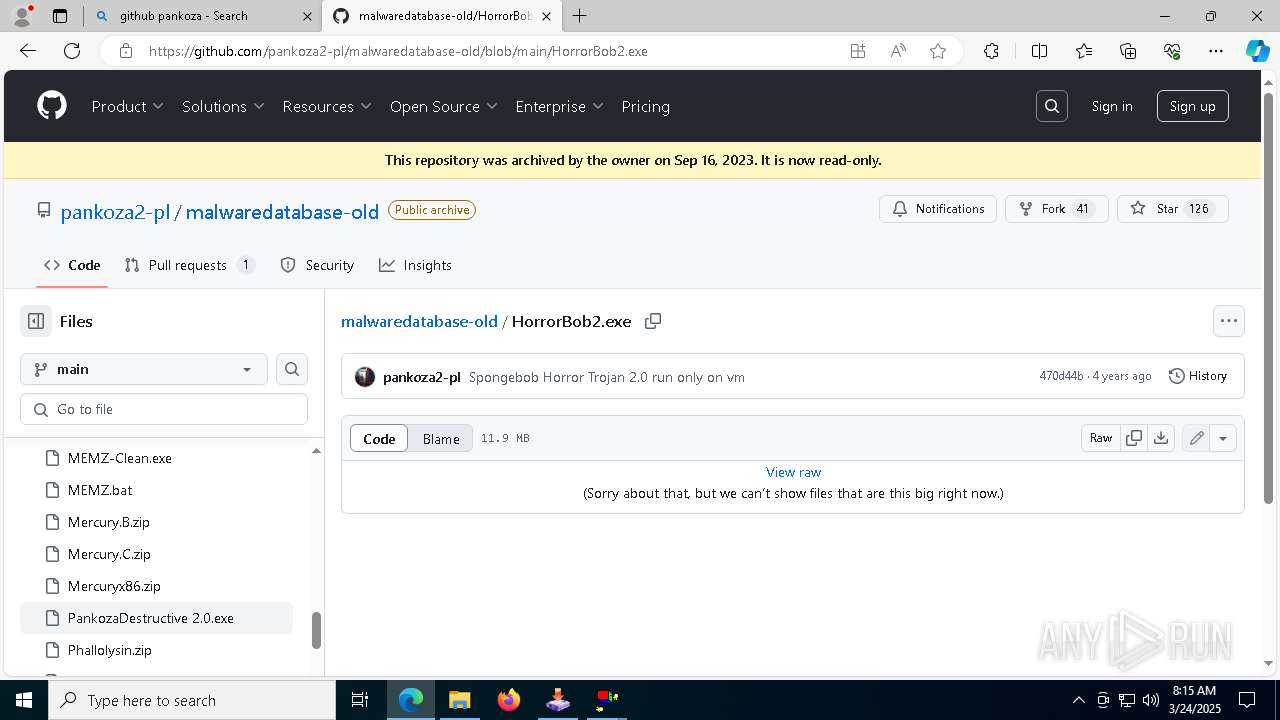
- HorrorBob2.exe (PID: 7800)
- HorrorBob2.exe (PID: 728)
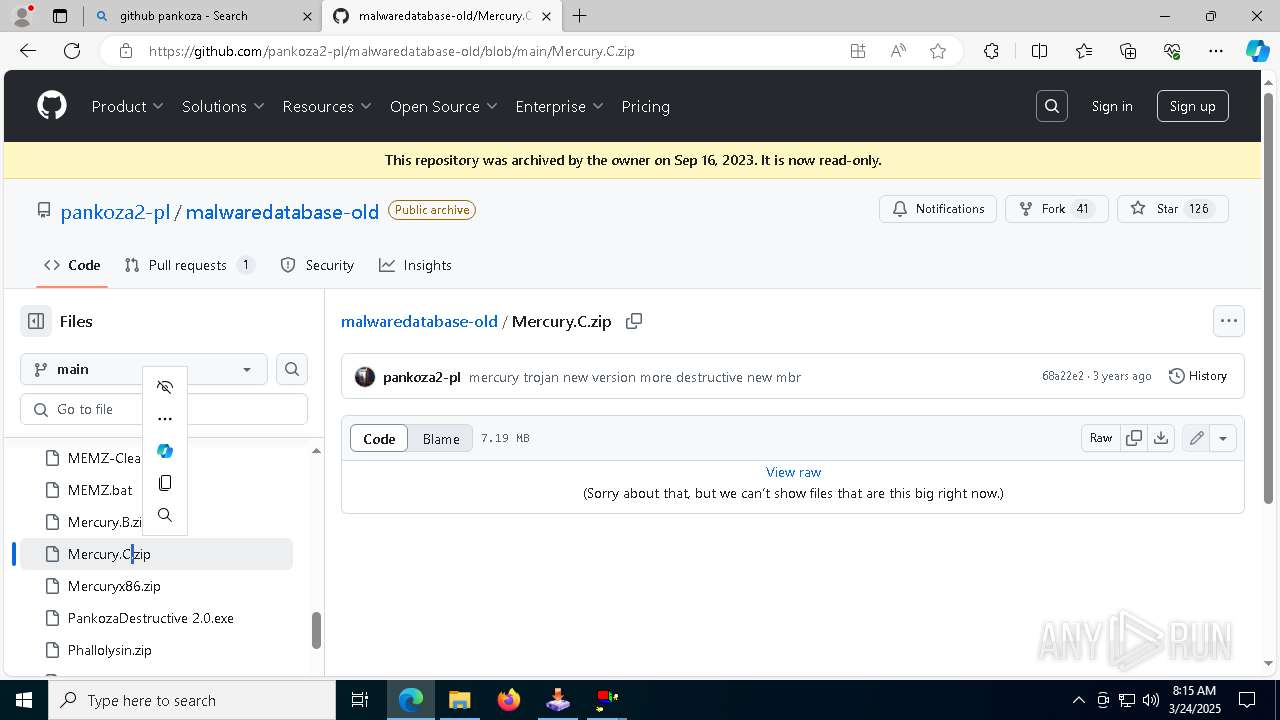
- Mercury.C.exe (PID: 1748)
- HorrorBob2.exe (PID: 6416)
- HorrorBob2.exe (PID: 4012)
- Mercury.C.exe (PID: 4452)
- HorrorBob2.exe (PID: 7596)
- HorrorBob2.exe (PID: 4304)
- HorrorBob2.exe (PID: 6080)
- cmd.exe (PID: 8280)
Reads security settings of Internet Explorer
- HorrorBob2.exe (PID: 7800)
- HorrorBob2.exe (PID: 728)
- HorrorBob2.exe (PID: 4012)
- Mercury.C.exe (PID: 4452)
- HorrorBob2.exe (PID: 4304)
- HorrorBob2.exe (PID: 6080)
Executing commands from a ".bat" file
- HorrorBob2.exe (PID: 728)
- HorrorBob2.exe (PID: 7800)
- HorrorBob2.exe (PID: 6416)
- HorrorBob2.exe (PID: 4012)
- HorrorBob2.exe (PID: 7596)
- HorrorBob2.exe (PID: 4304)
- HorrorBob2.exe (PID: 6080)
Starts CMD.EXE for commands execution
- HorrorBob2.exe (PID: 7800)
- HorrorBob2.exe (PID: 728)
- HorrorBob2.exe (PID: 6416)
- HorrorBob2.exe (PID: 4012)
- HorrorBob2.exe (PID: 7596)
- HorrorBob2.exe (PID: 4304)
- HorrorBob2.exe (PID: 6080)
The process executes VB scripts
- cmd.exe (PID: 6048)
- cmd.exe (PID: 4000)
- Mercury.C.exe (PID: 1748)
- cmd.exe (PID: 232)
- cmd.exe (PID: 3024)
- Mercury.C.exe (PID: 4452)
- wscript.exe (PID: 6892)
- cmd.exe (PID: 6876)
- cmd.exe (PID: 5640)
- cmd.exe (PID: 8280)
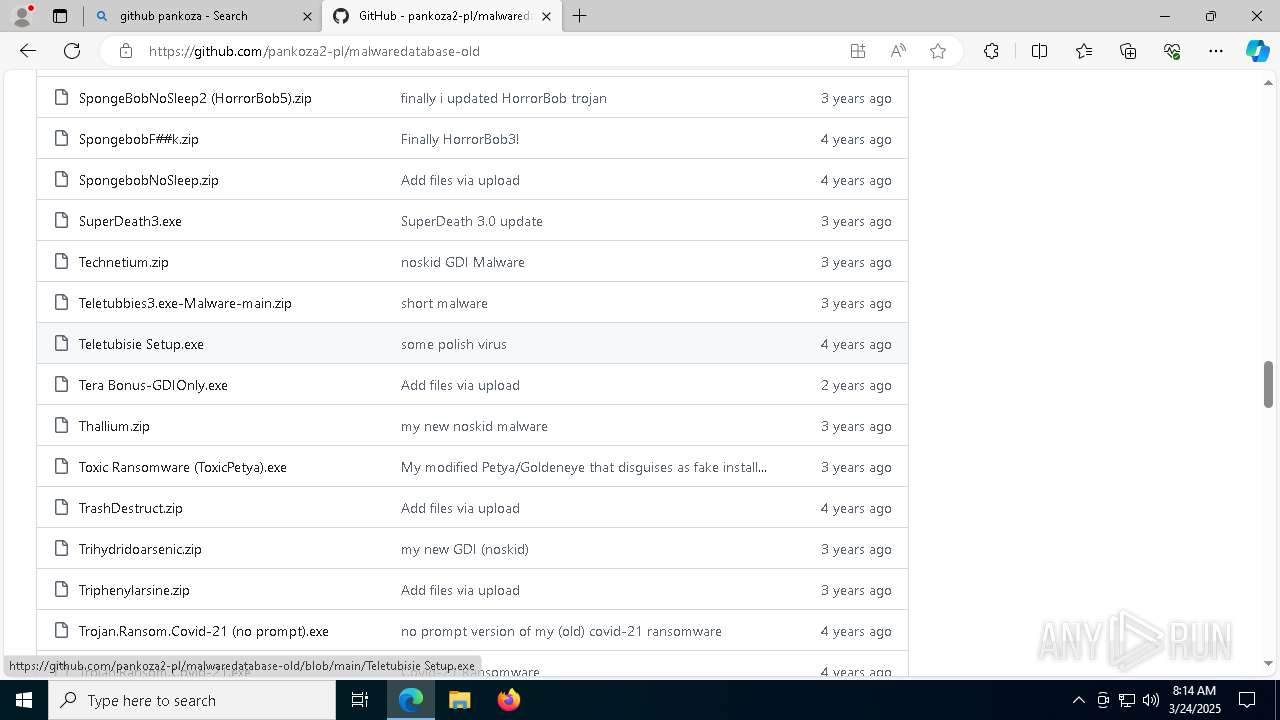
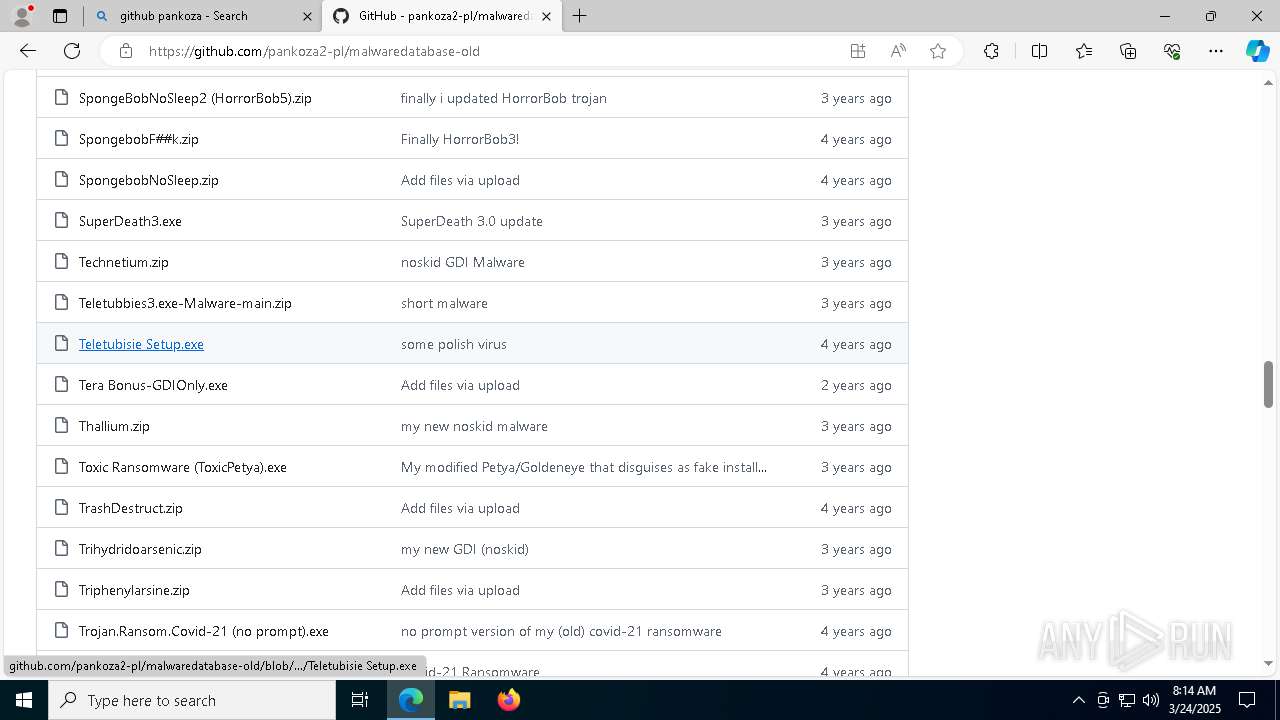
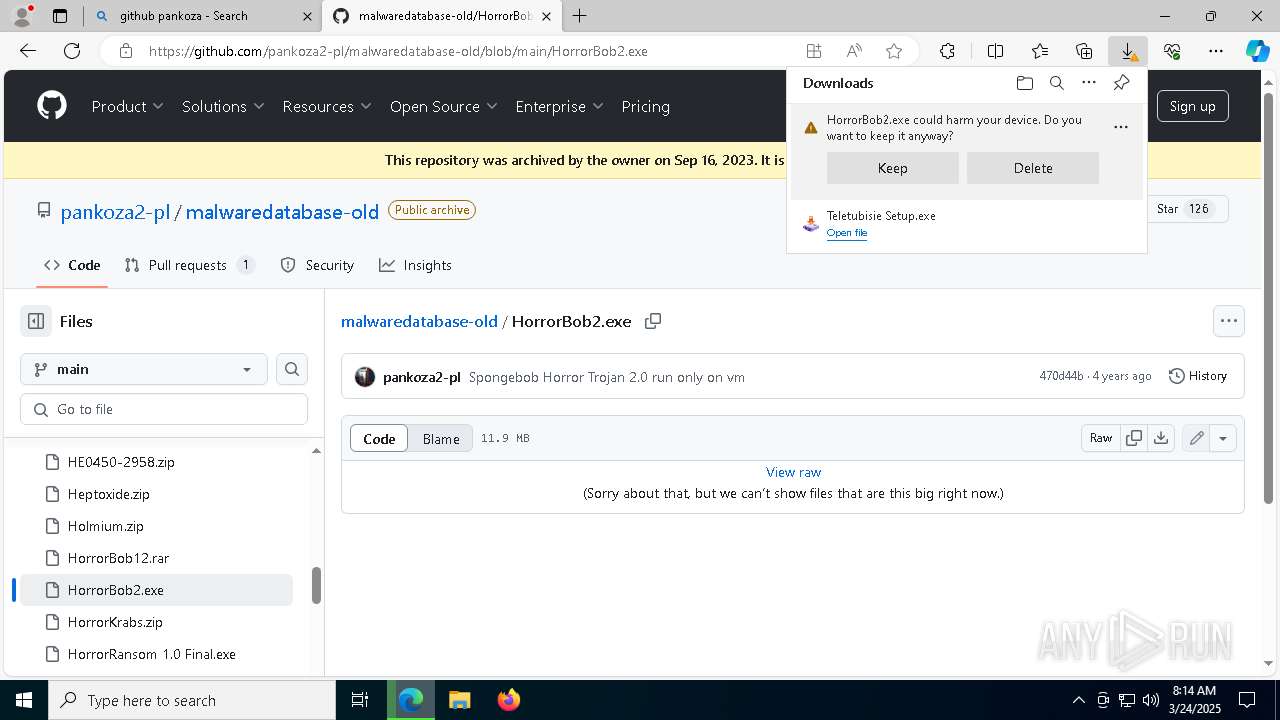
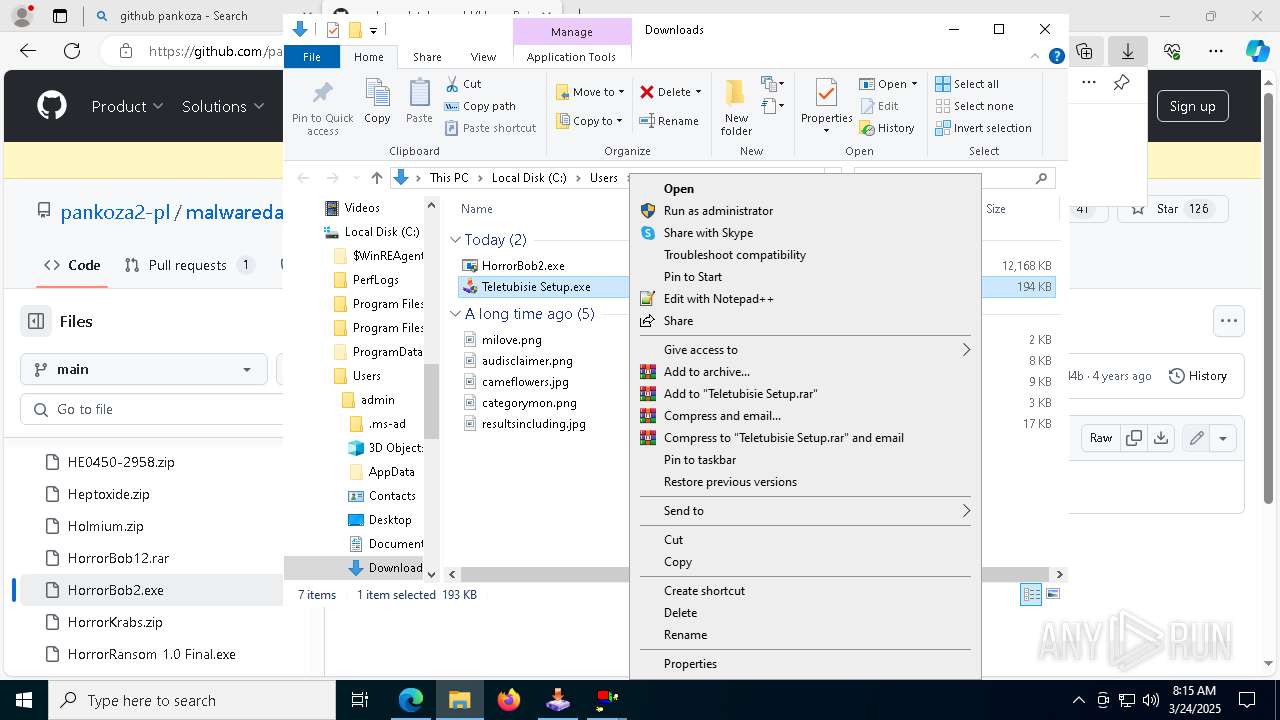
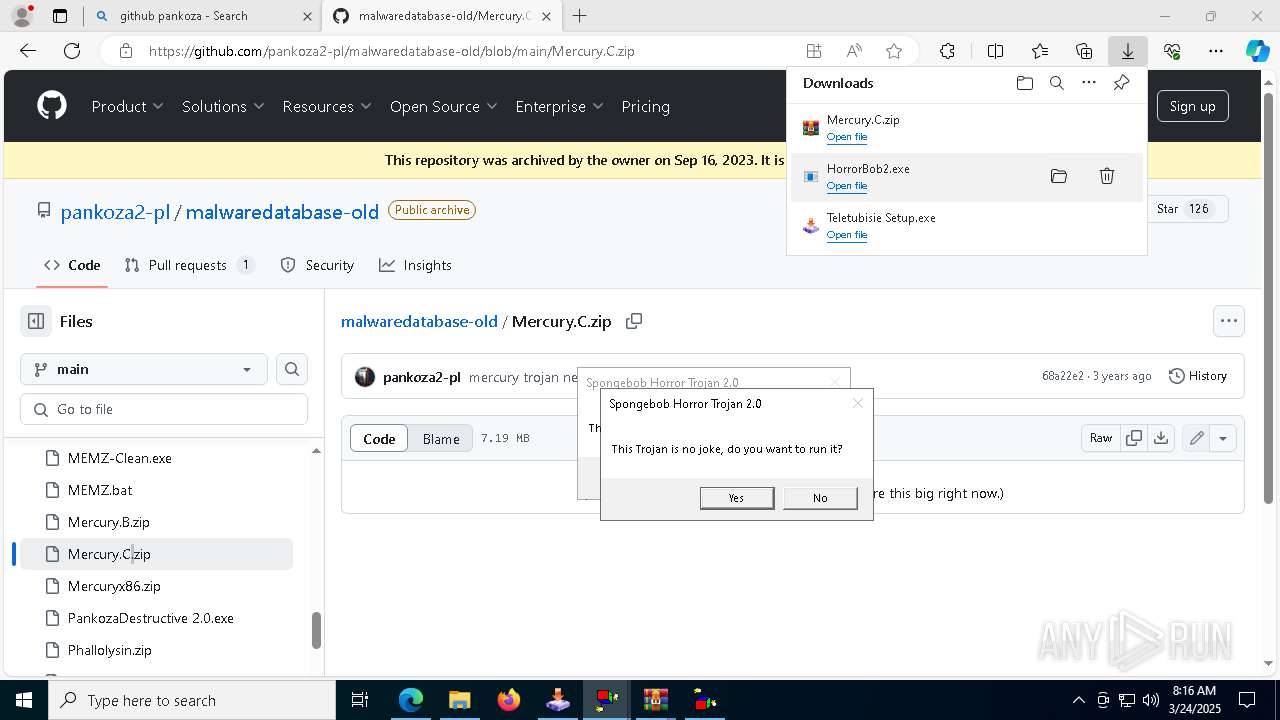
There is functionality for taking screenshot (YARA)
- Teletubisie Setup.exe (PID: 3884)
Runs WScript without displaying logo
- wscript.exe (PID: 7172)
- wscript.exe (PID: 6892)
Application launched itself
- wscript.exe (PID: 6892)
Runs shell command (SCRIPT)
- wscript.exe (PID: 2040)
- wscript.exe (PID: 6892)
Working with threads in the GNU C Compiler (GCC) libraries related mutex has been found
- mbr.exe (PID: 4628)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 2040)
Writes binary data to a Stream object (SCRIPT)
- wscript.exe (PID: 2040)
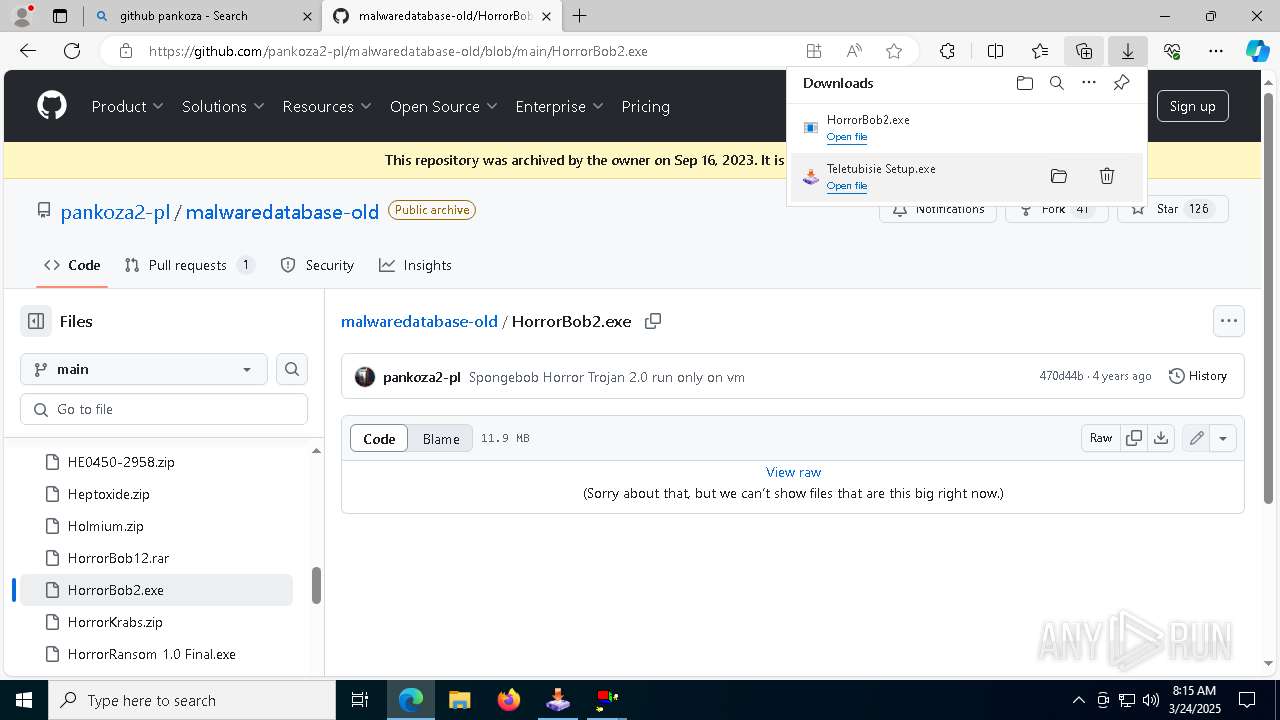
Changes the desktop background image
- reg.exe (PID: 8456)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 8280)
The system shut down or reboot
- cmd.exe (PID: 8280)
INFO
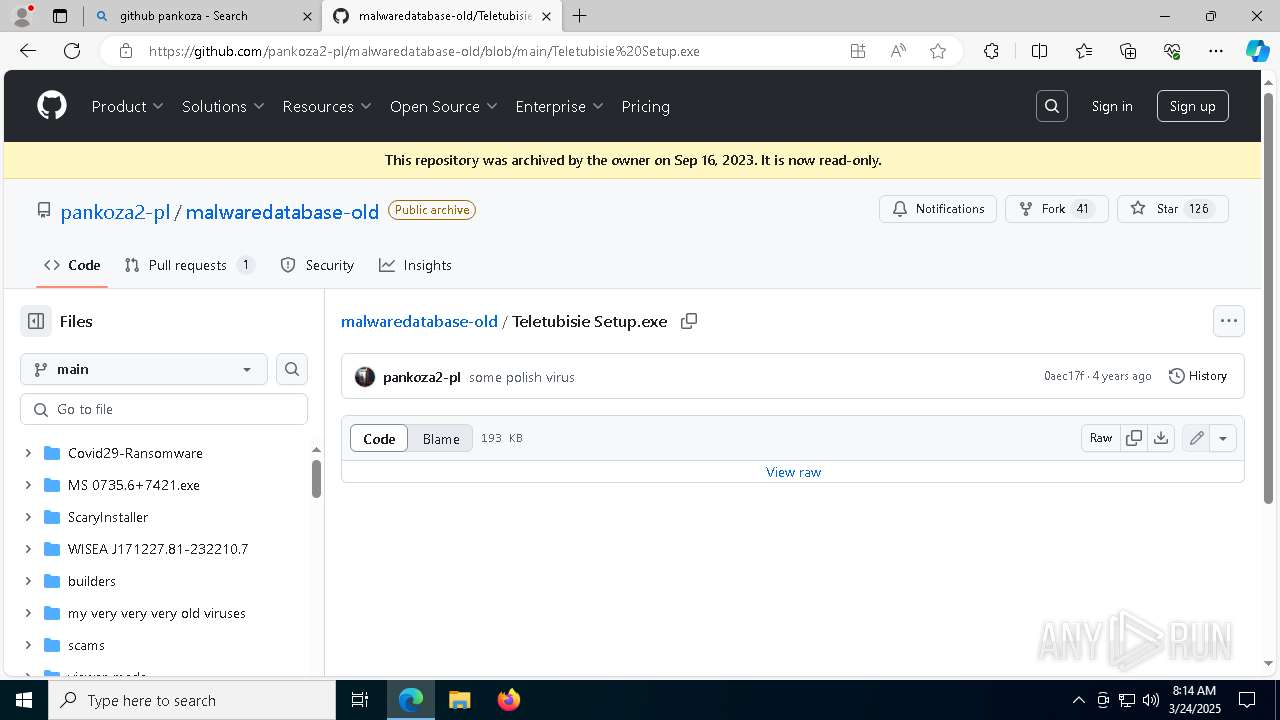
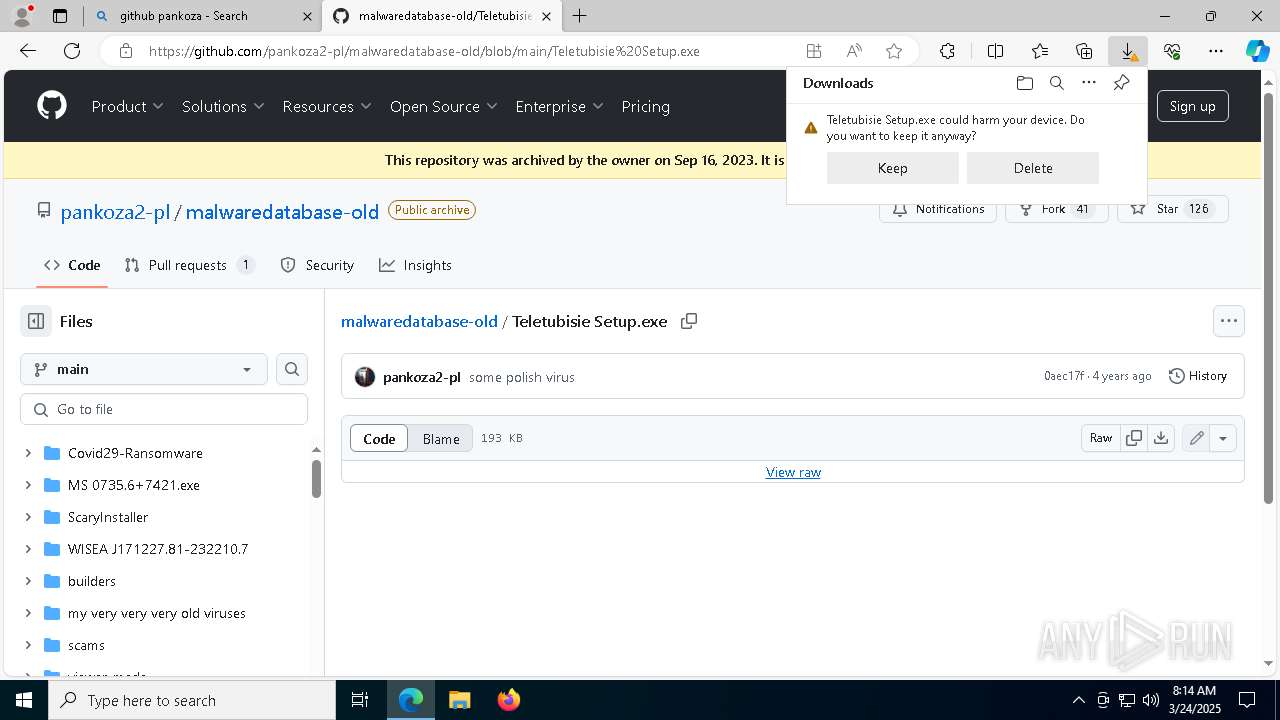
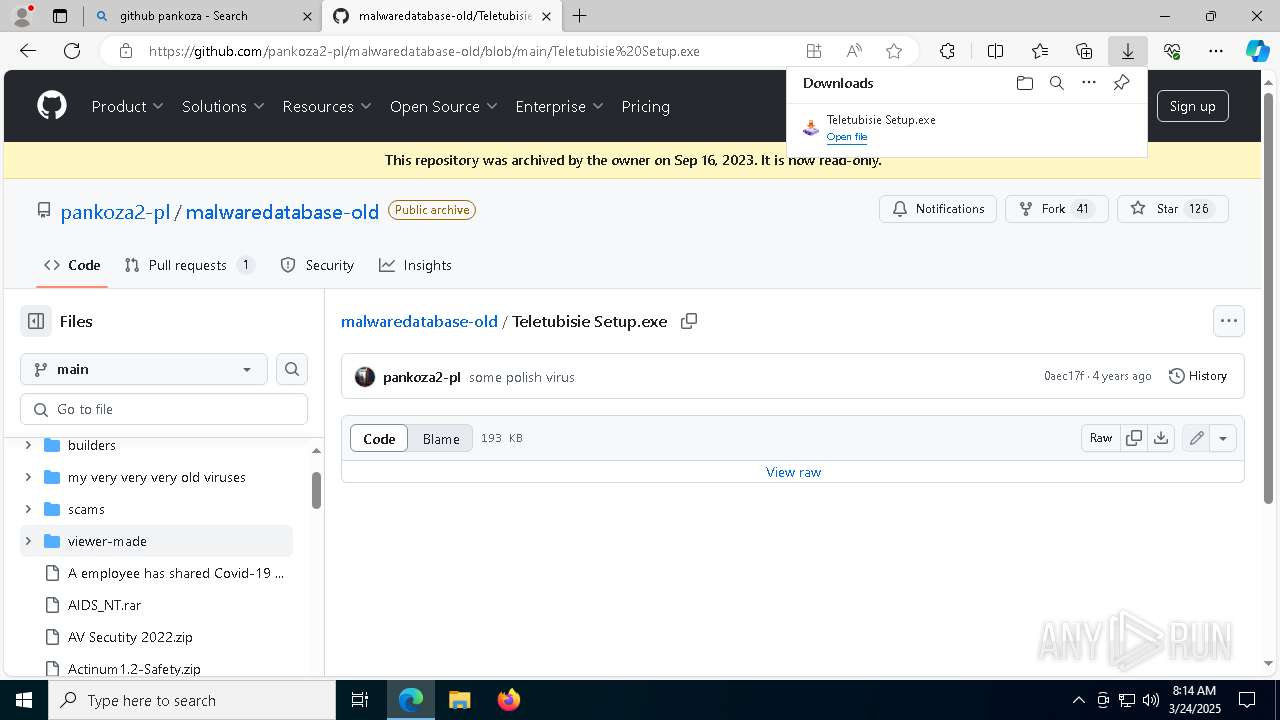
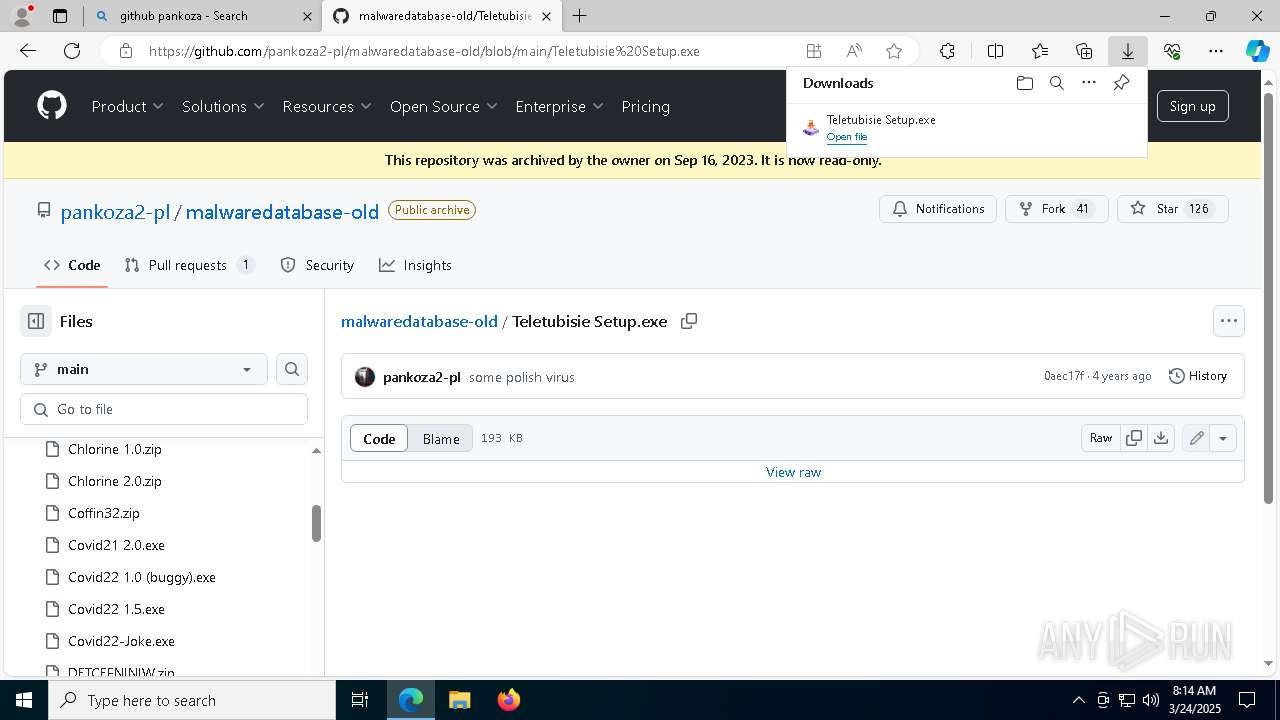
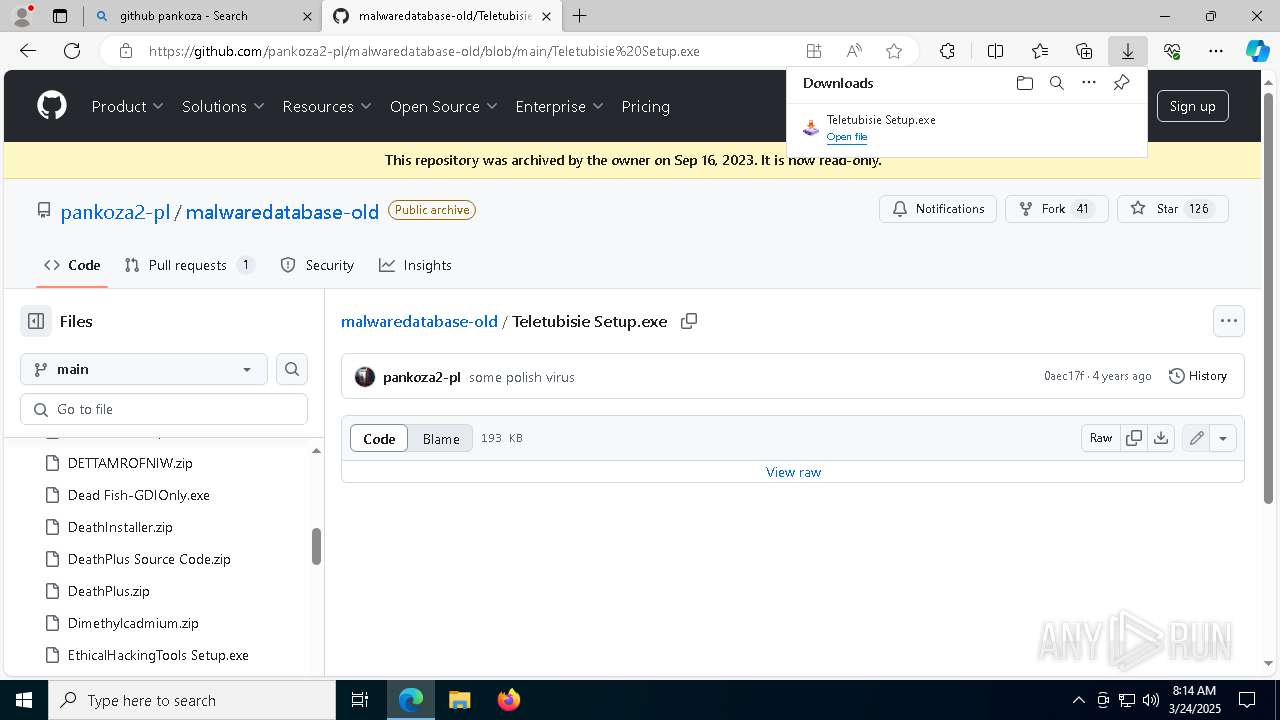
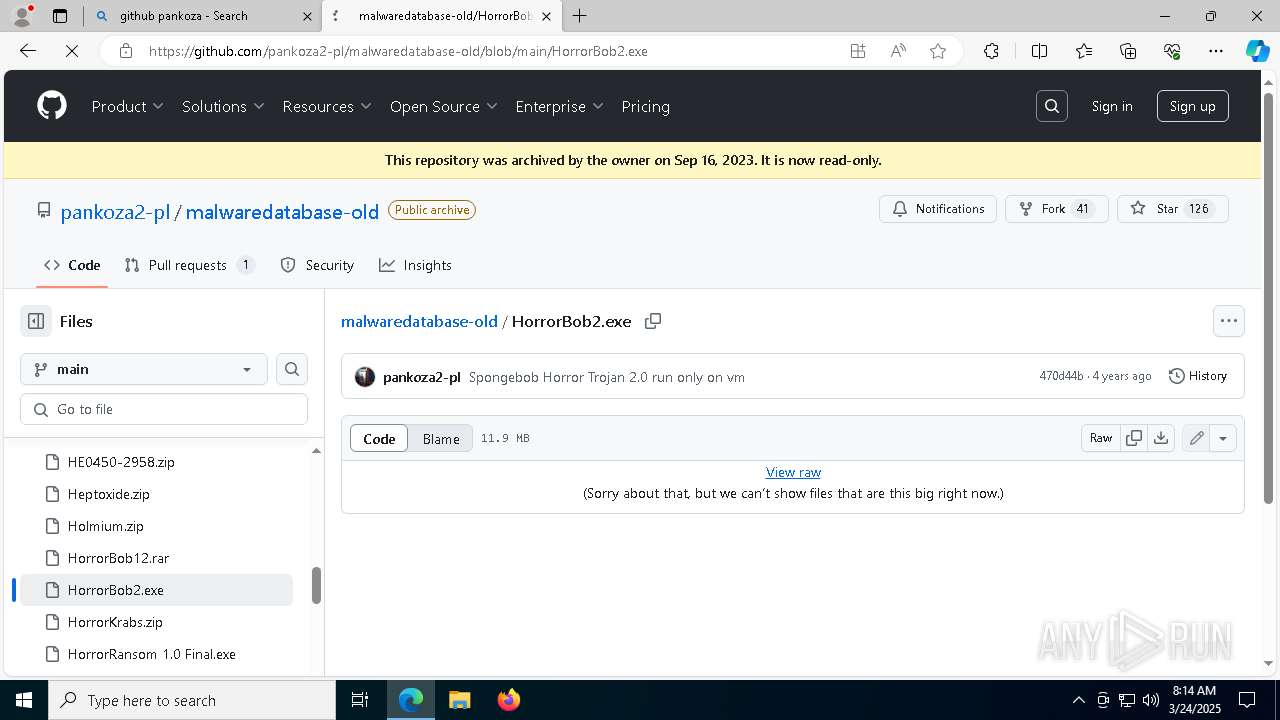
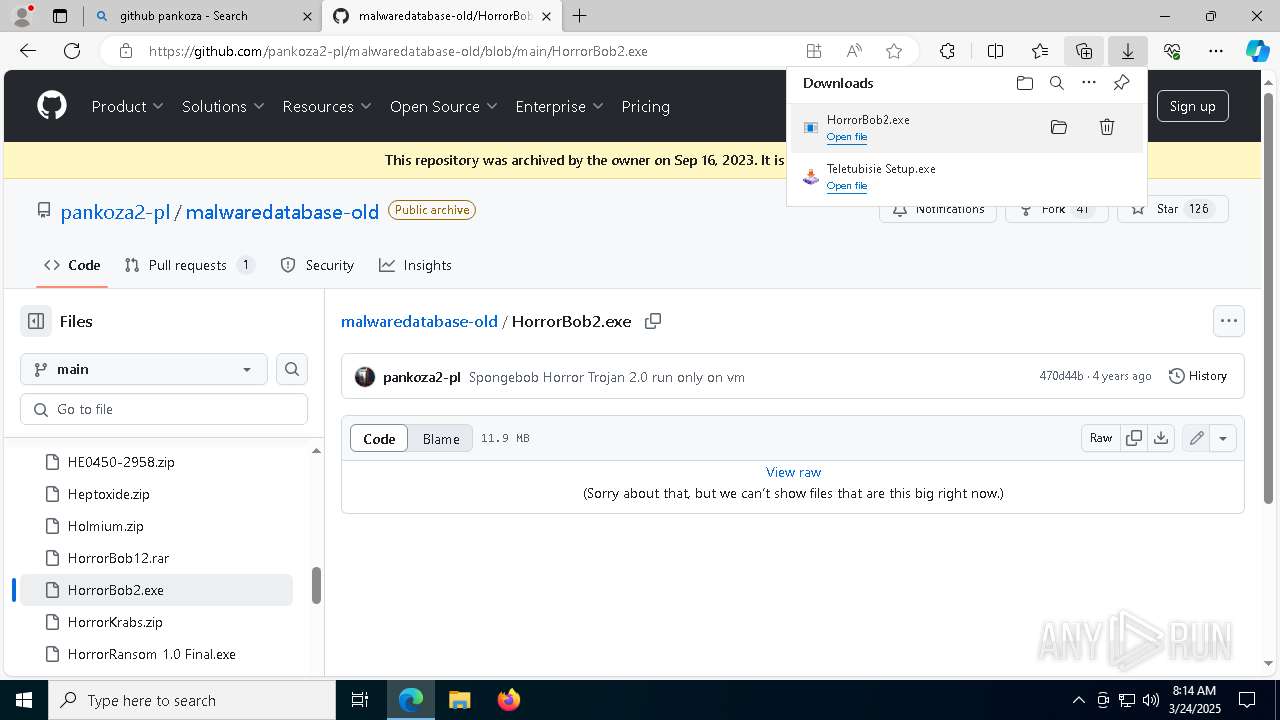
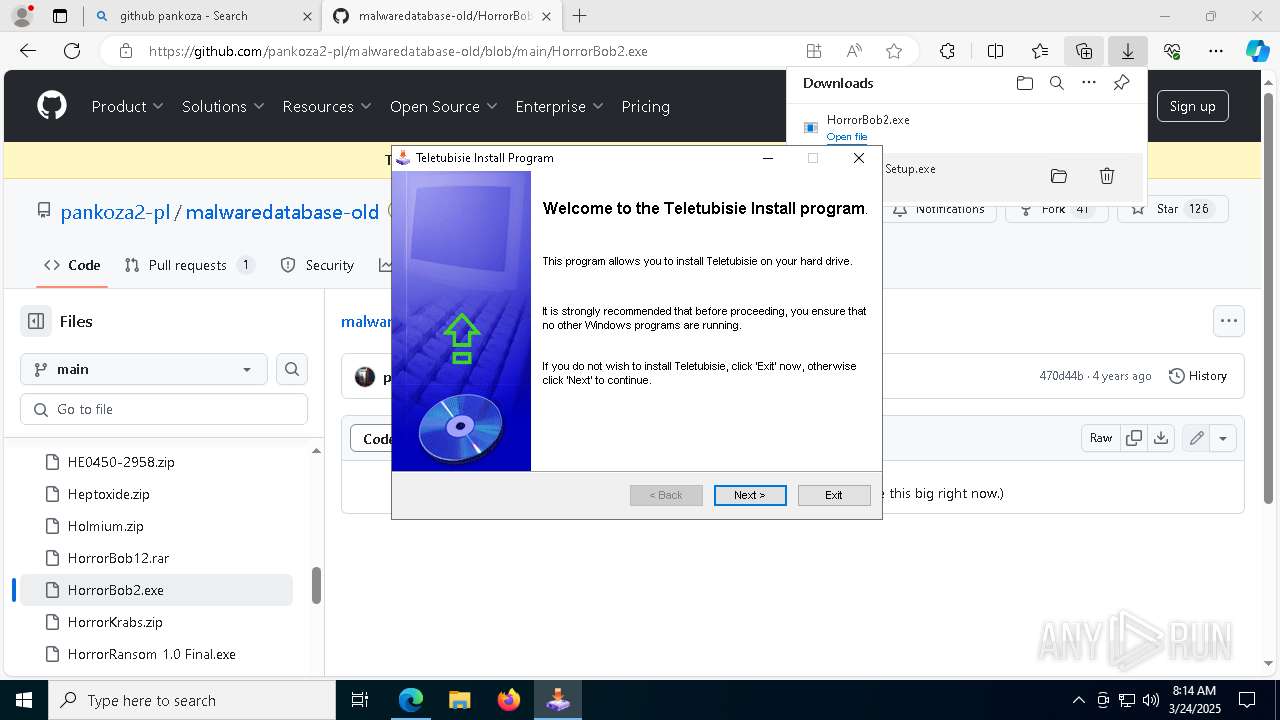
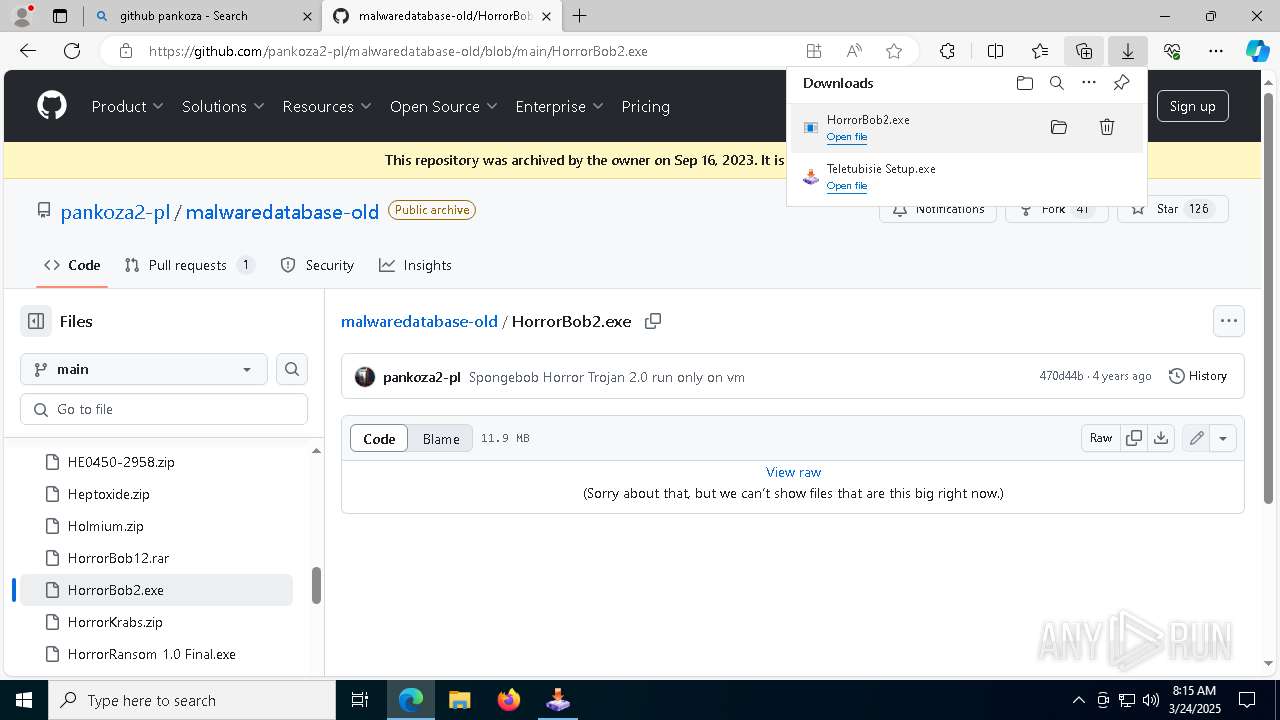
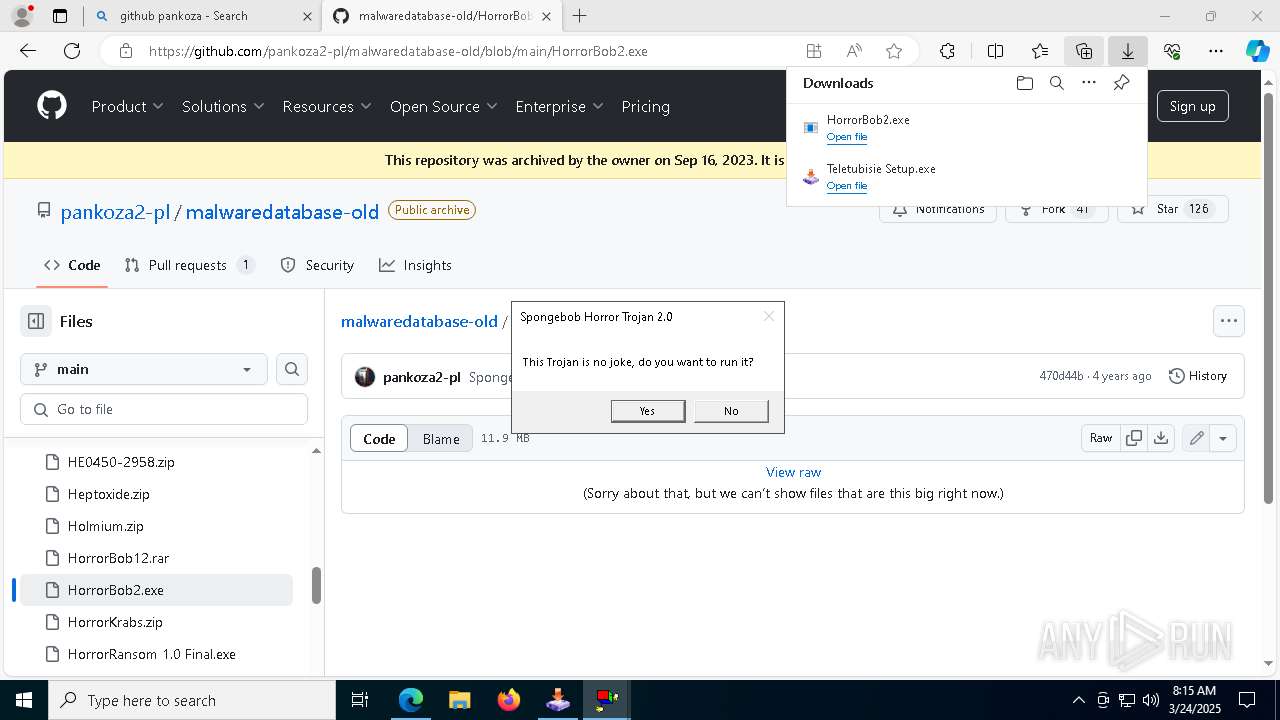
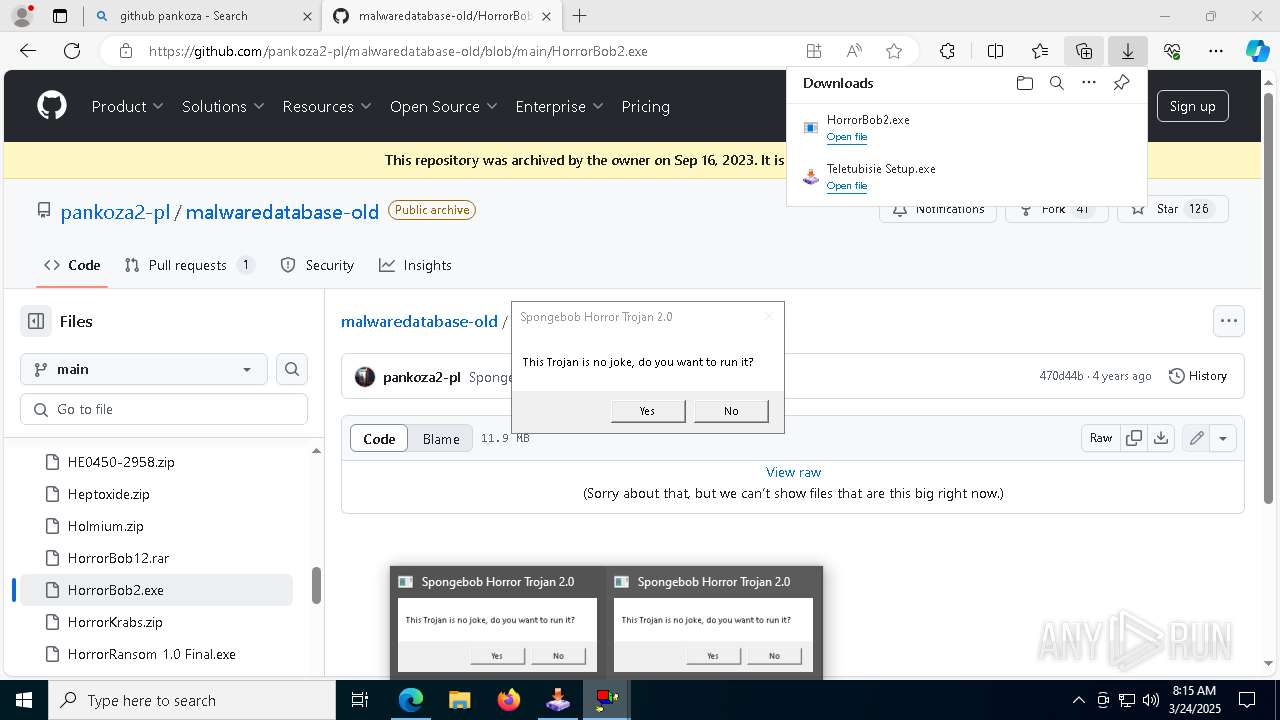
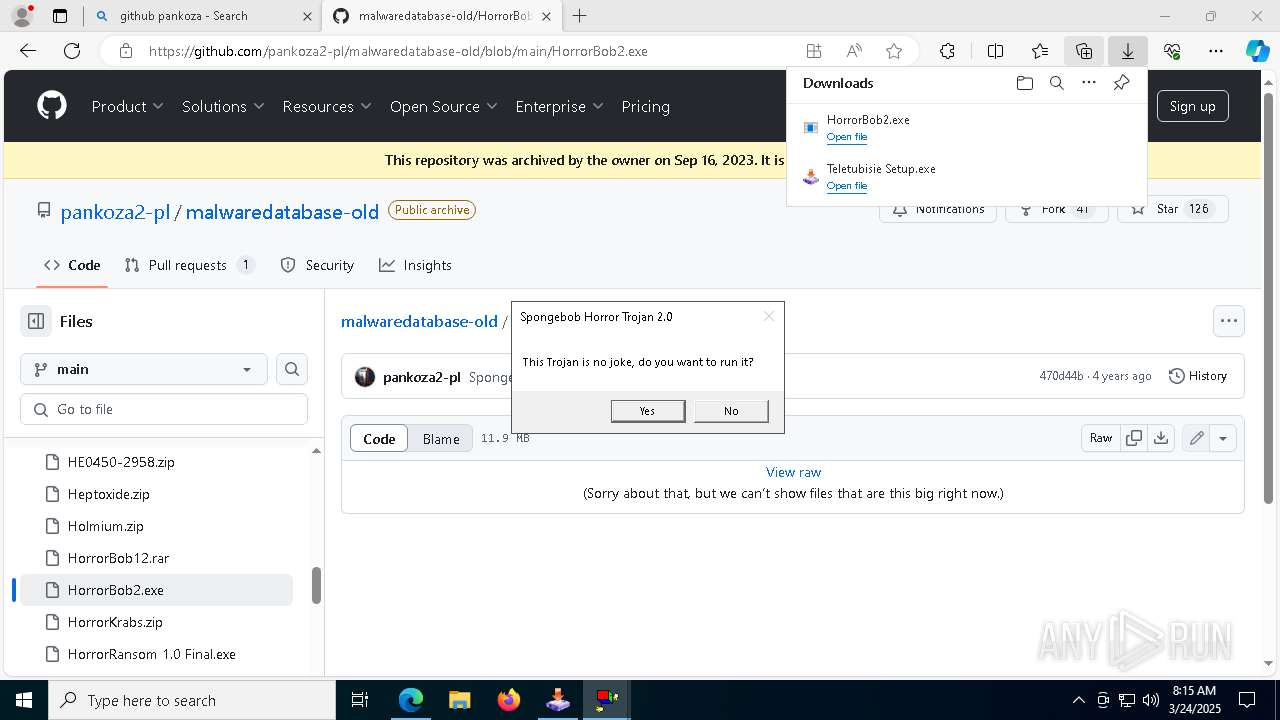
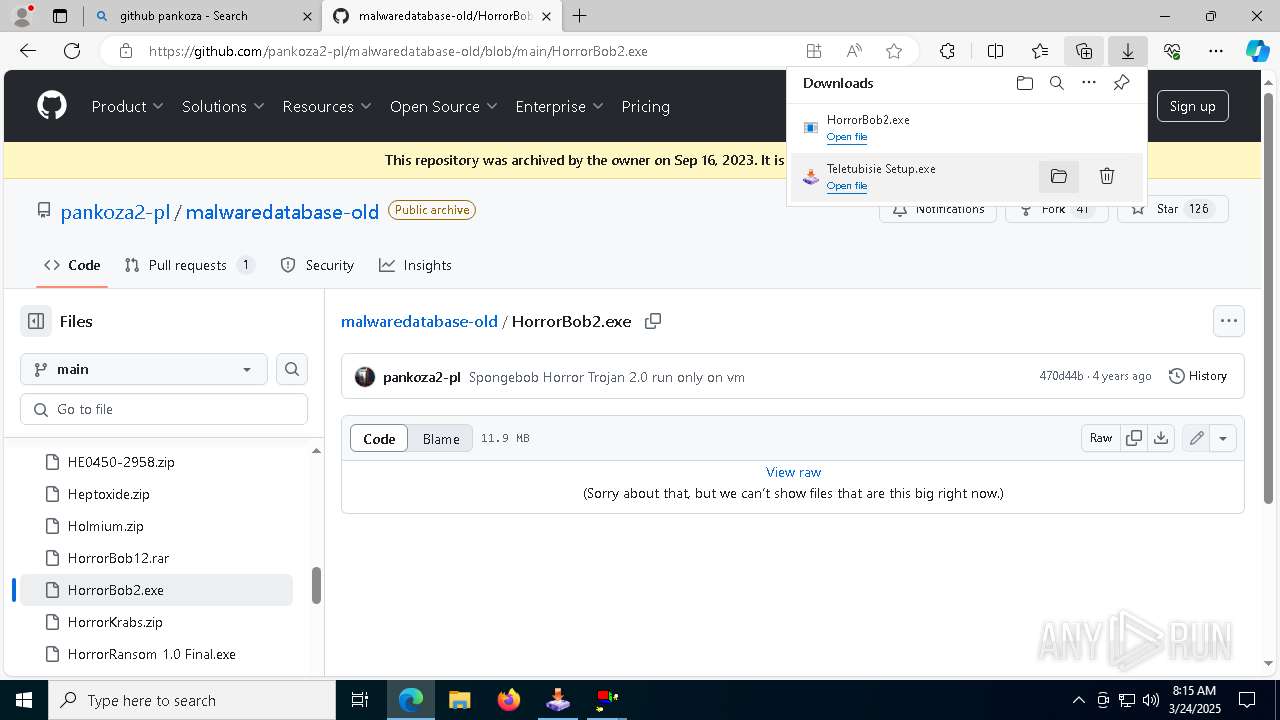
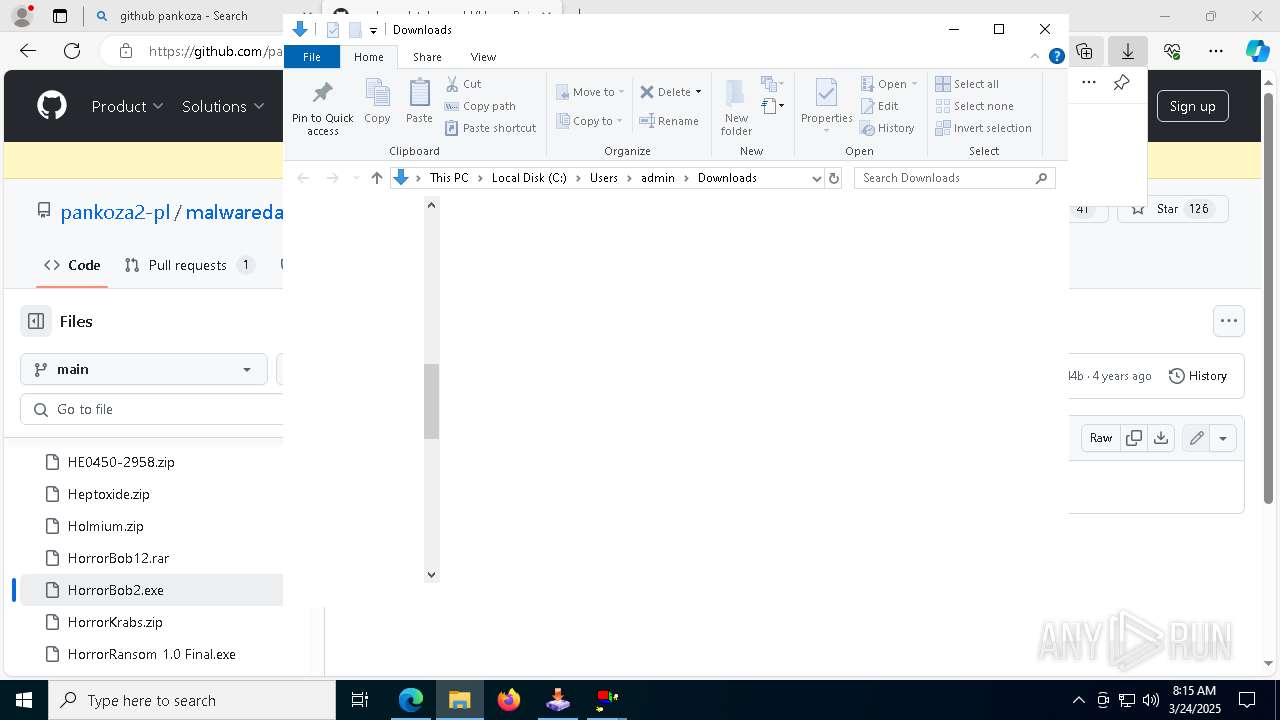
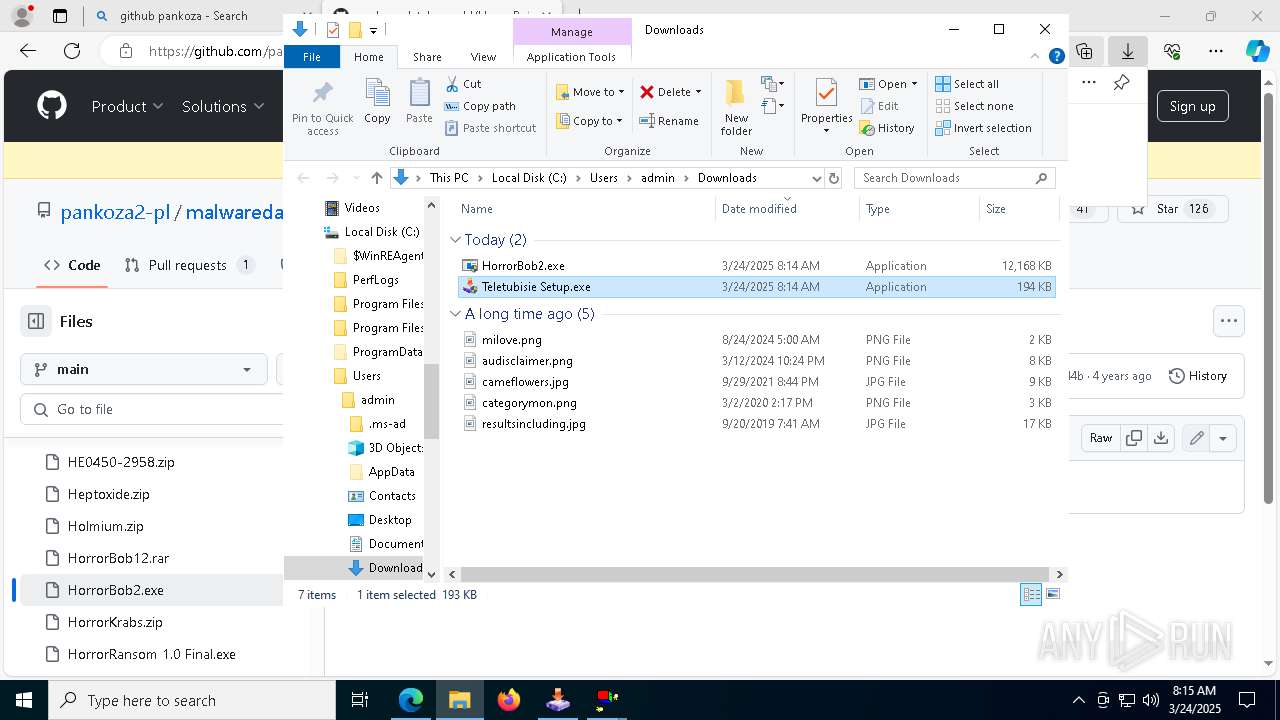
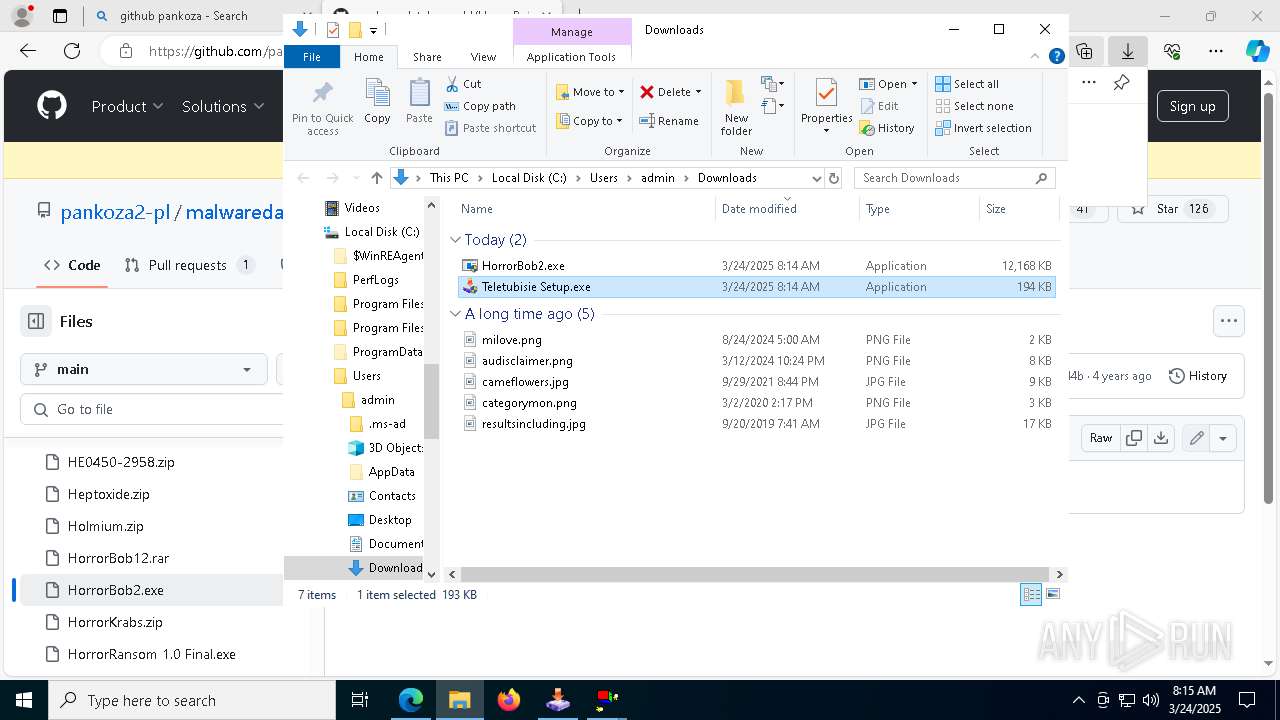
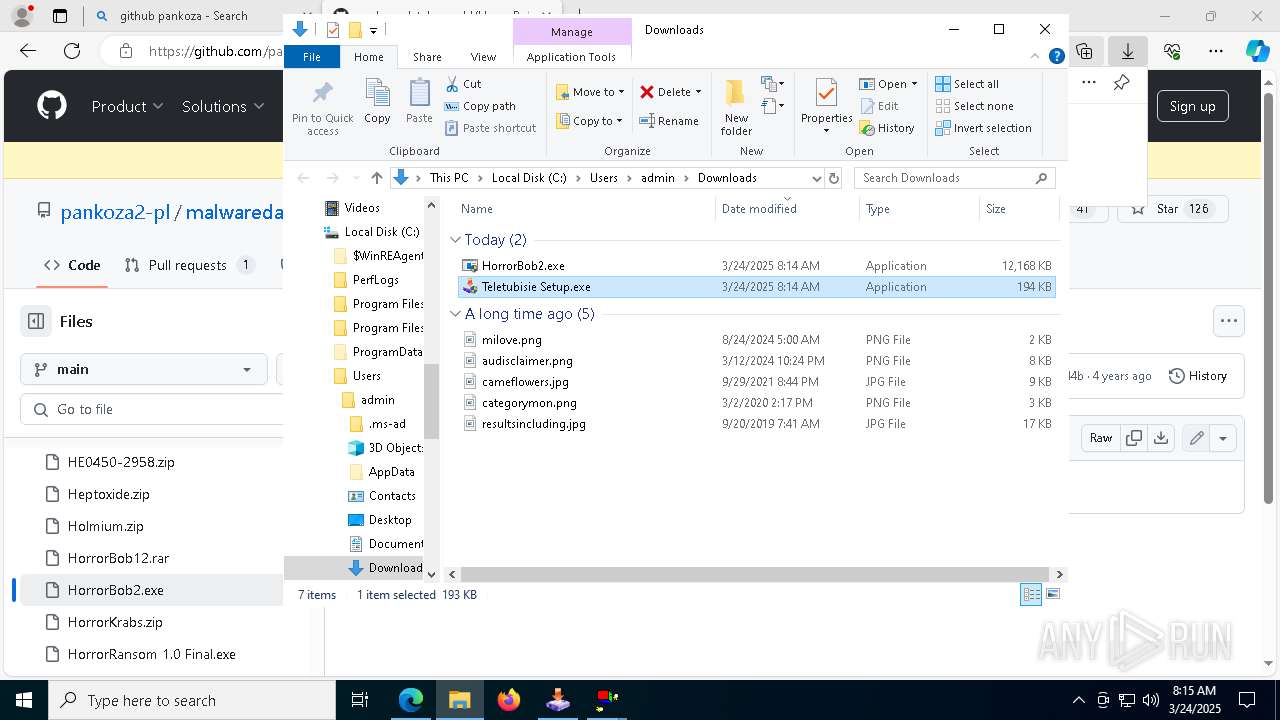
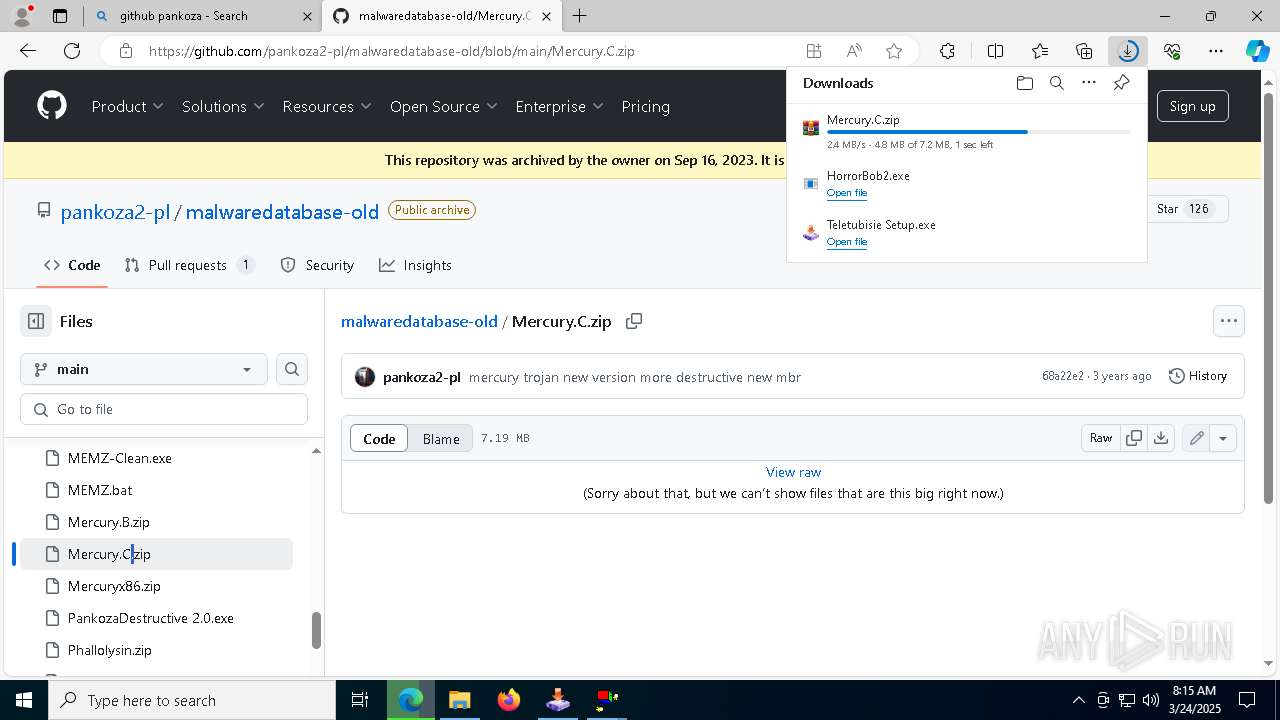
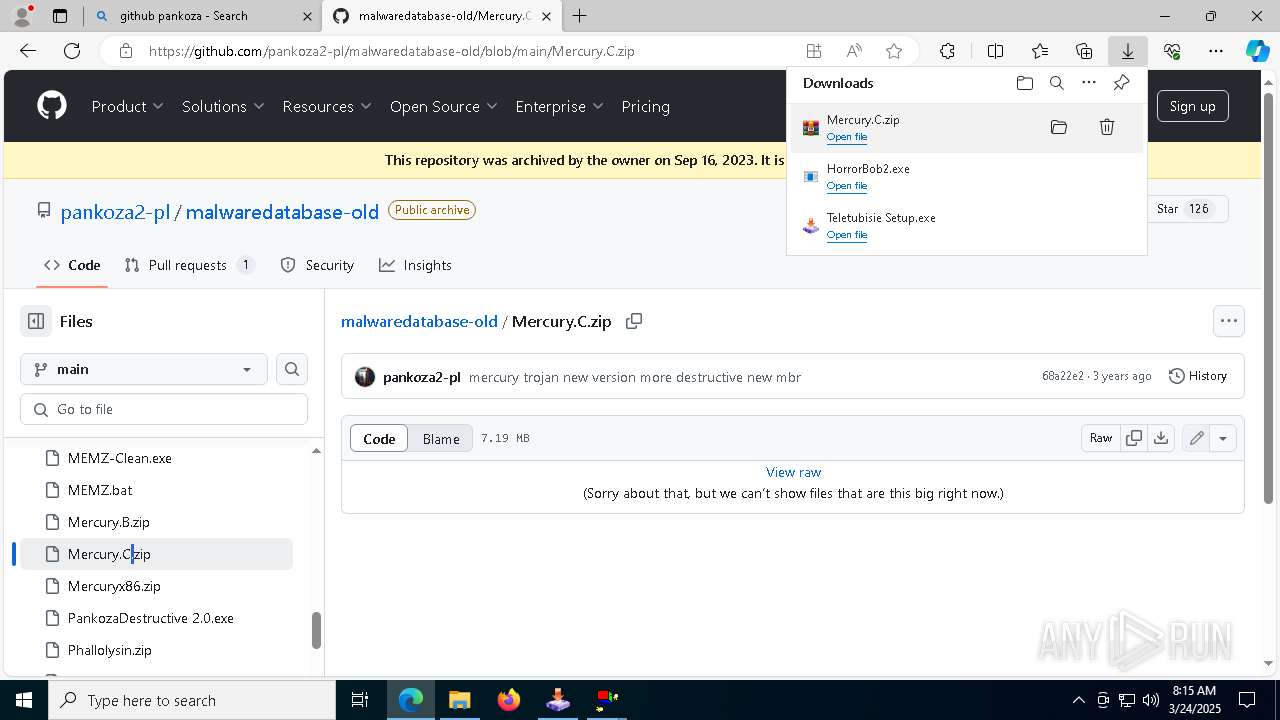
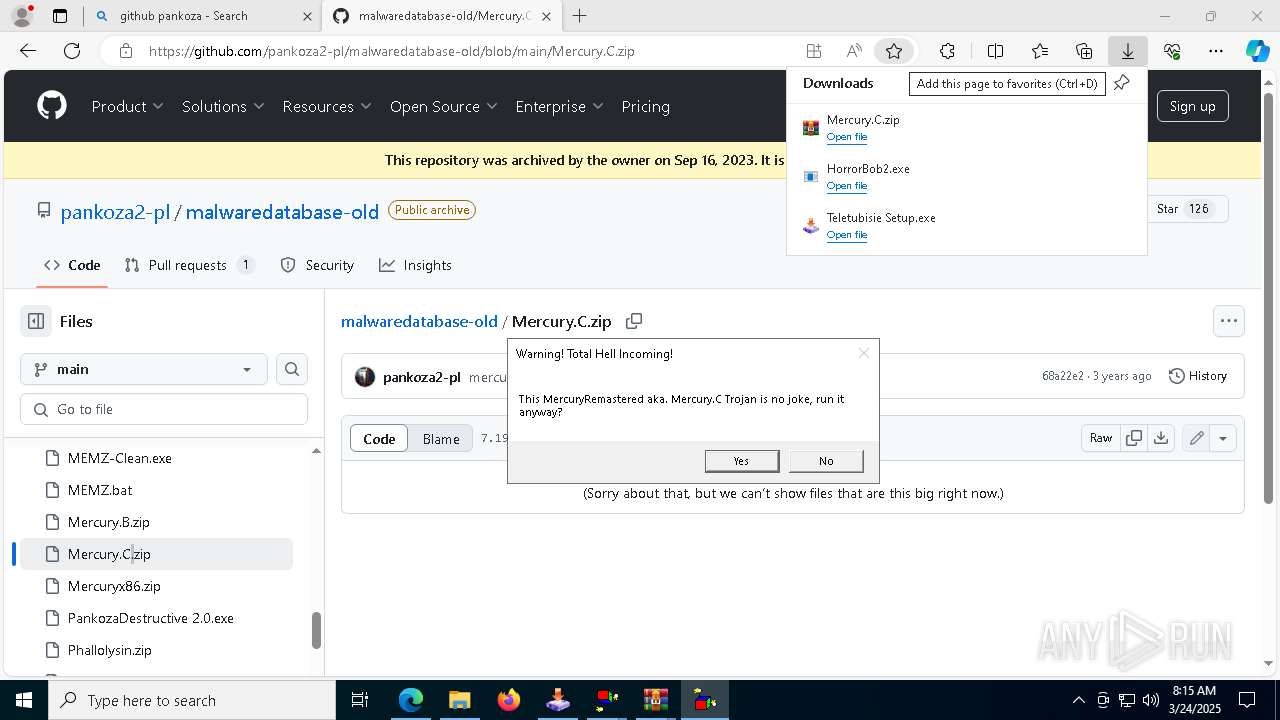
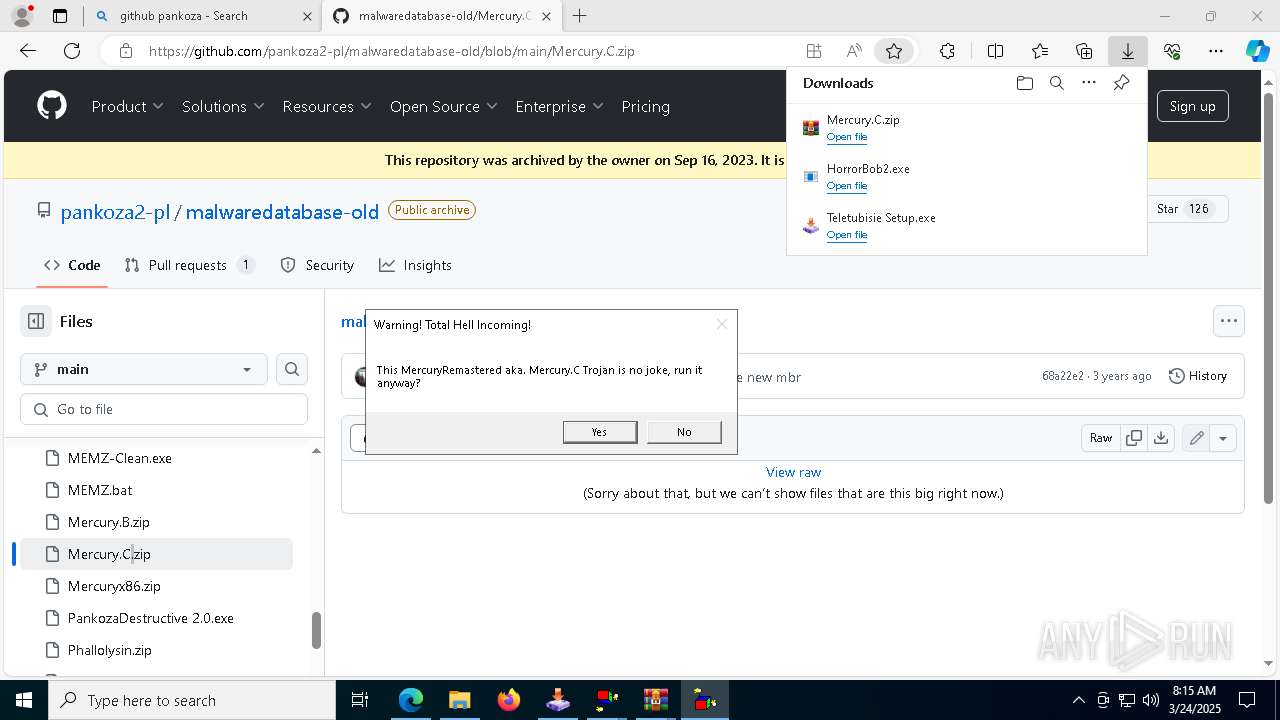
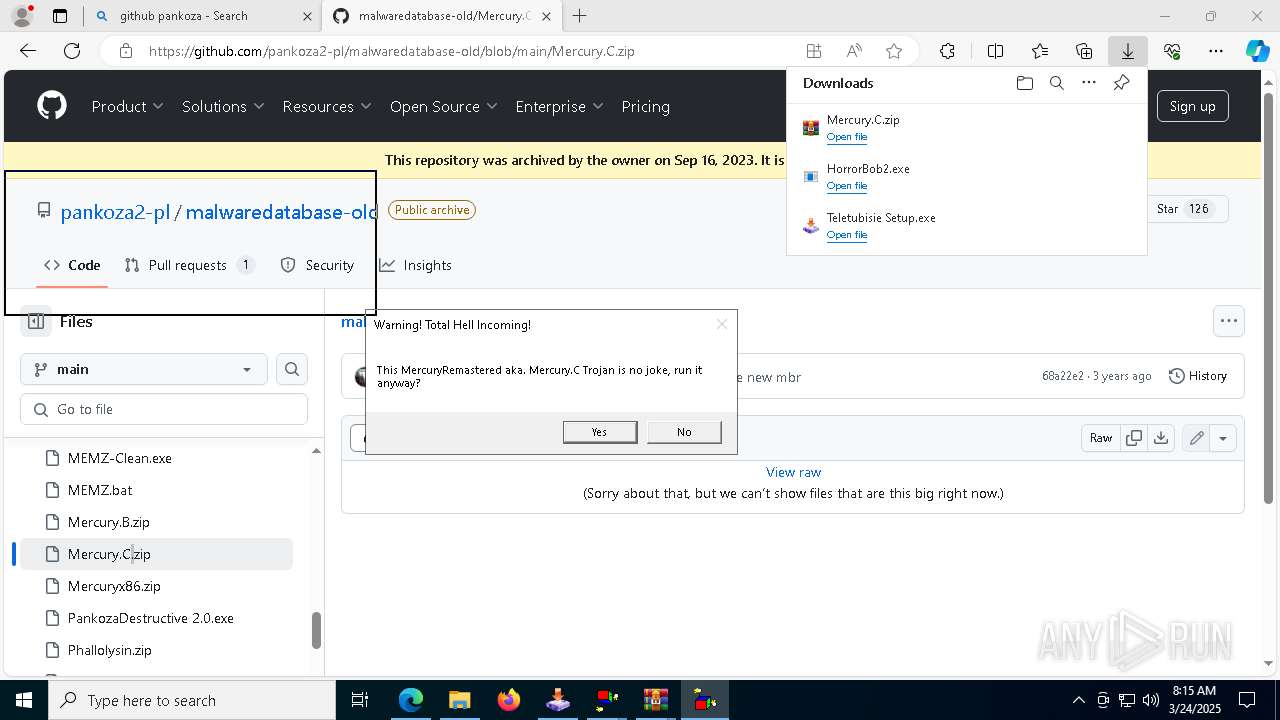
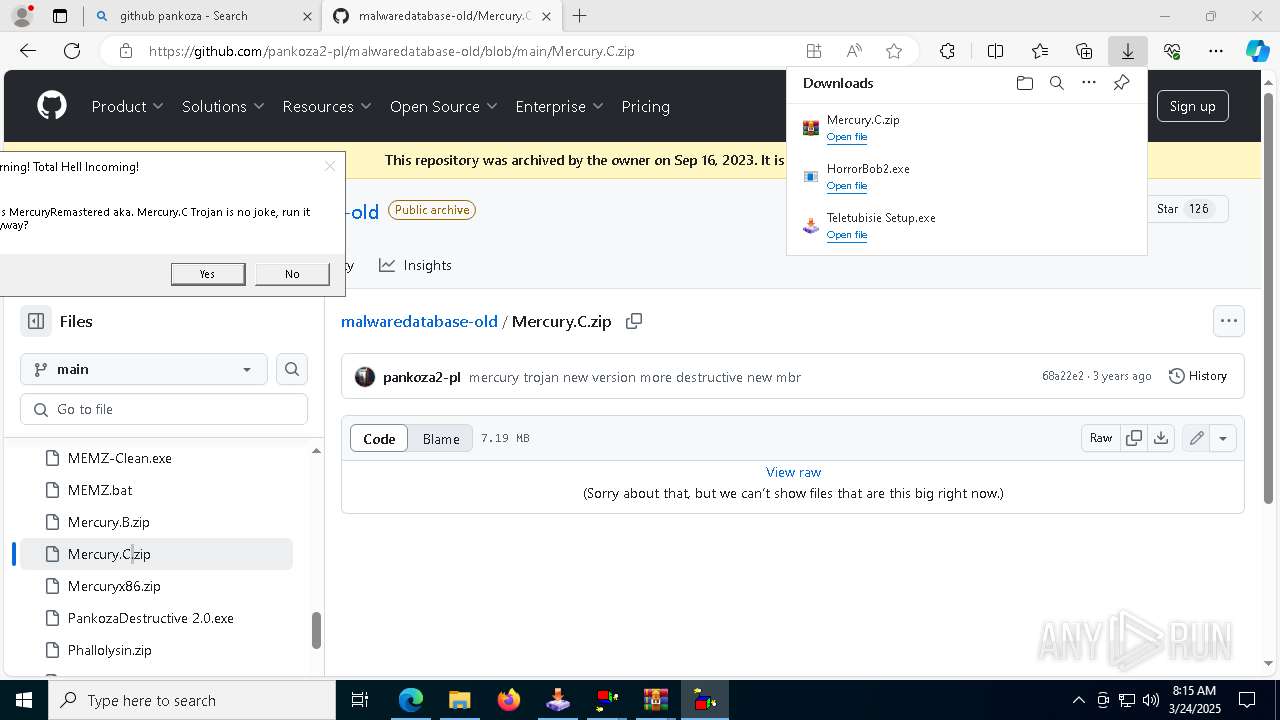
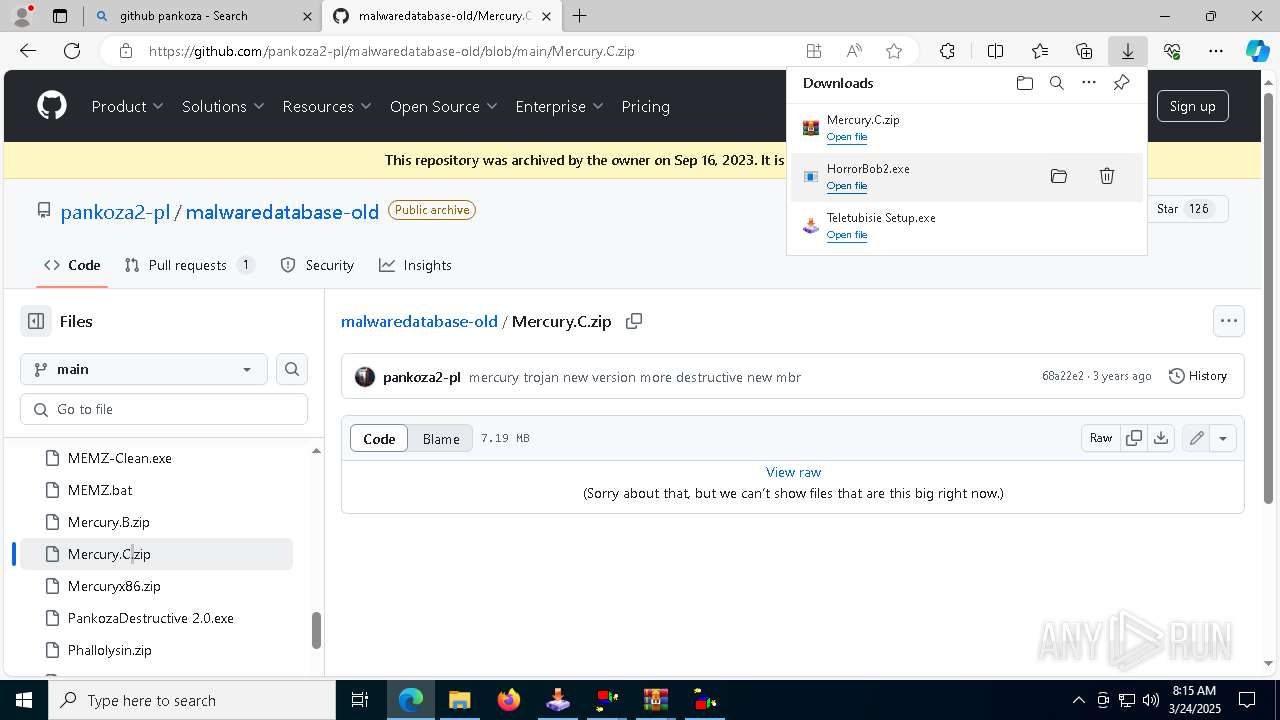
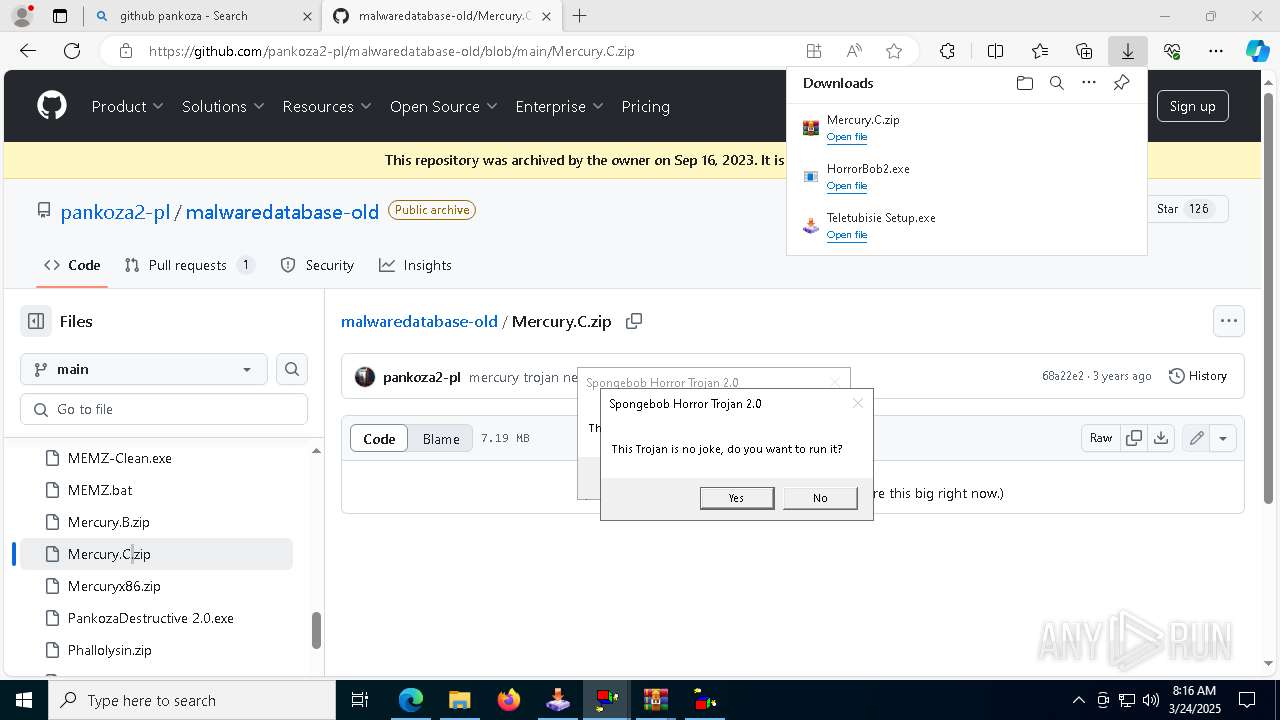
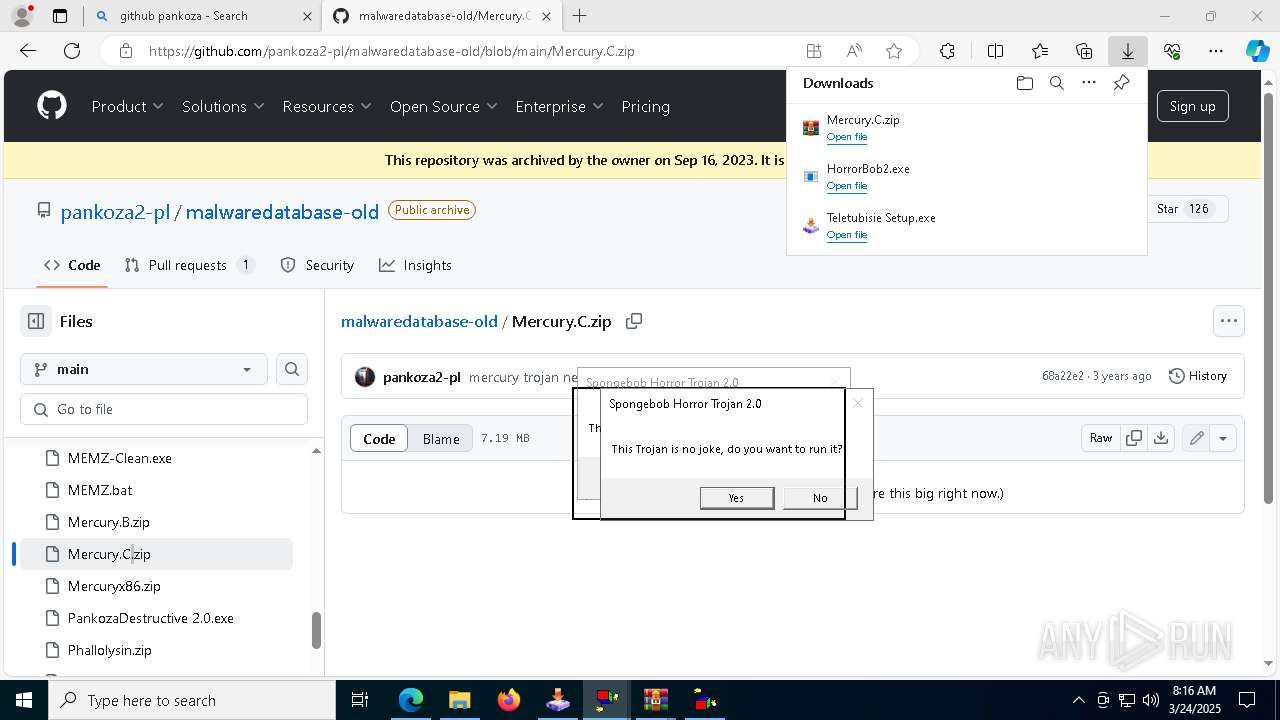
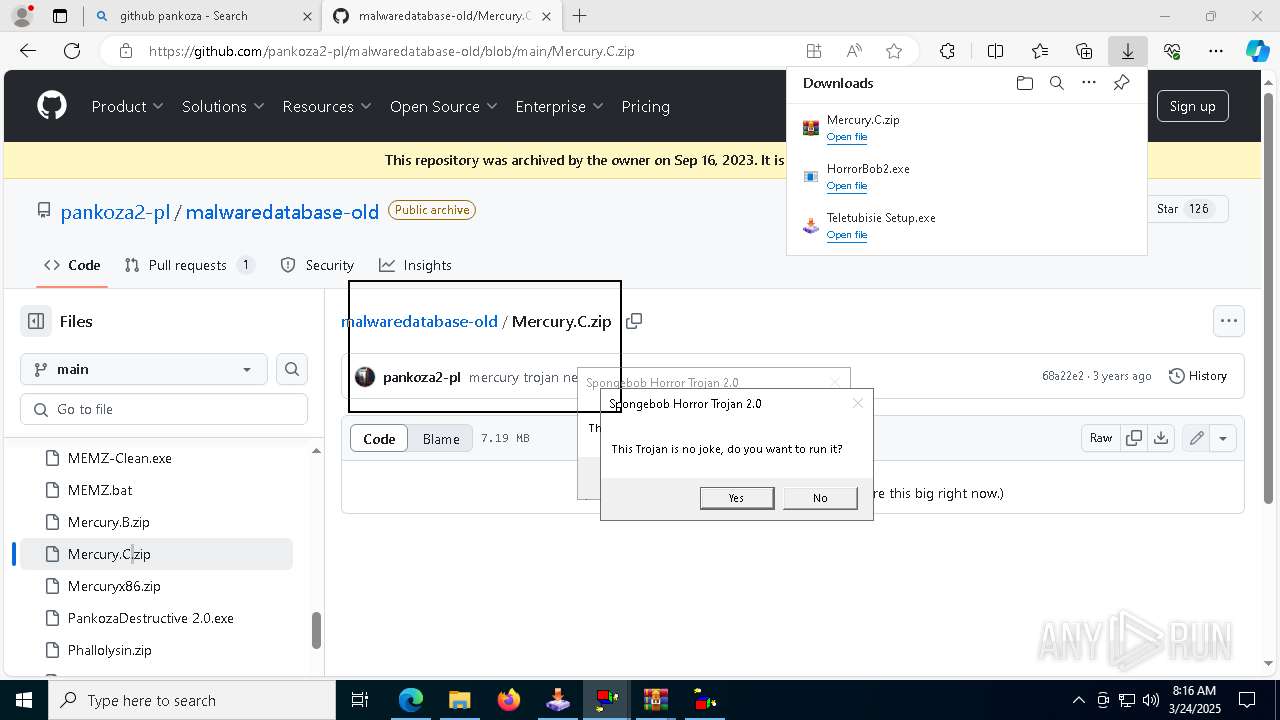
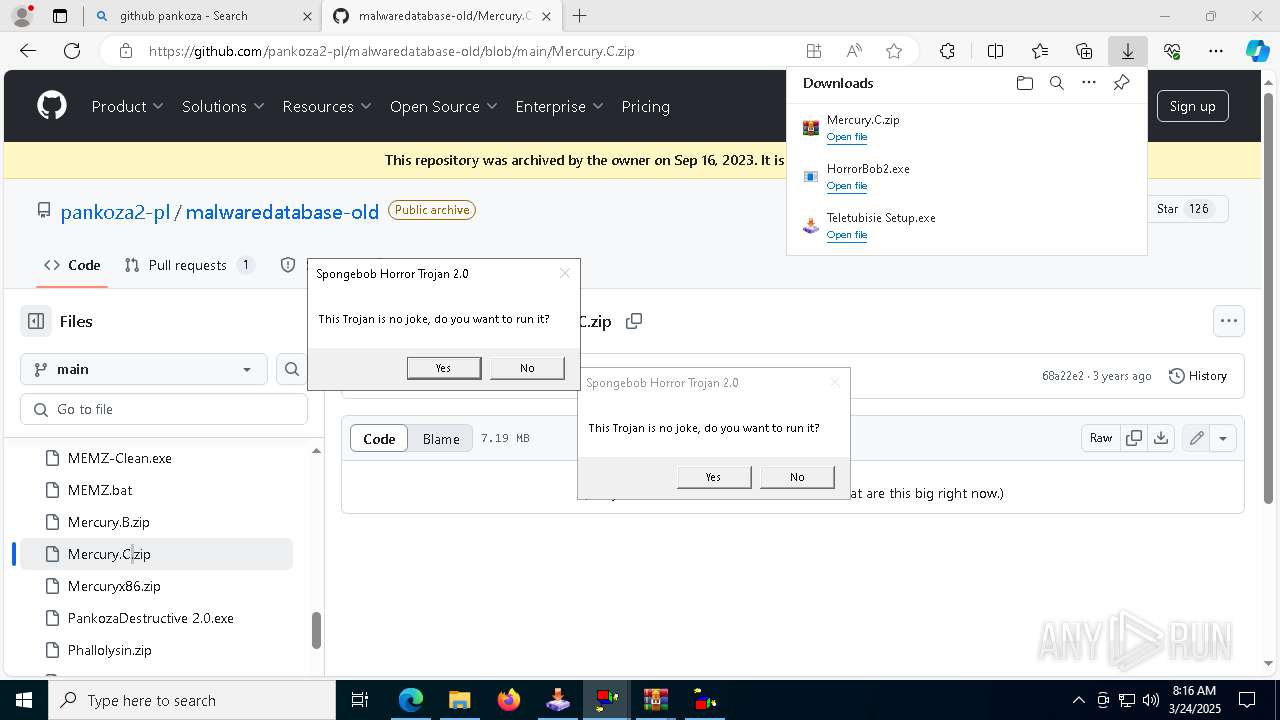
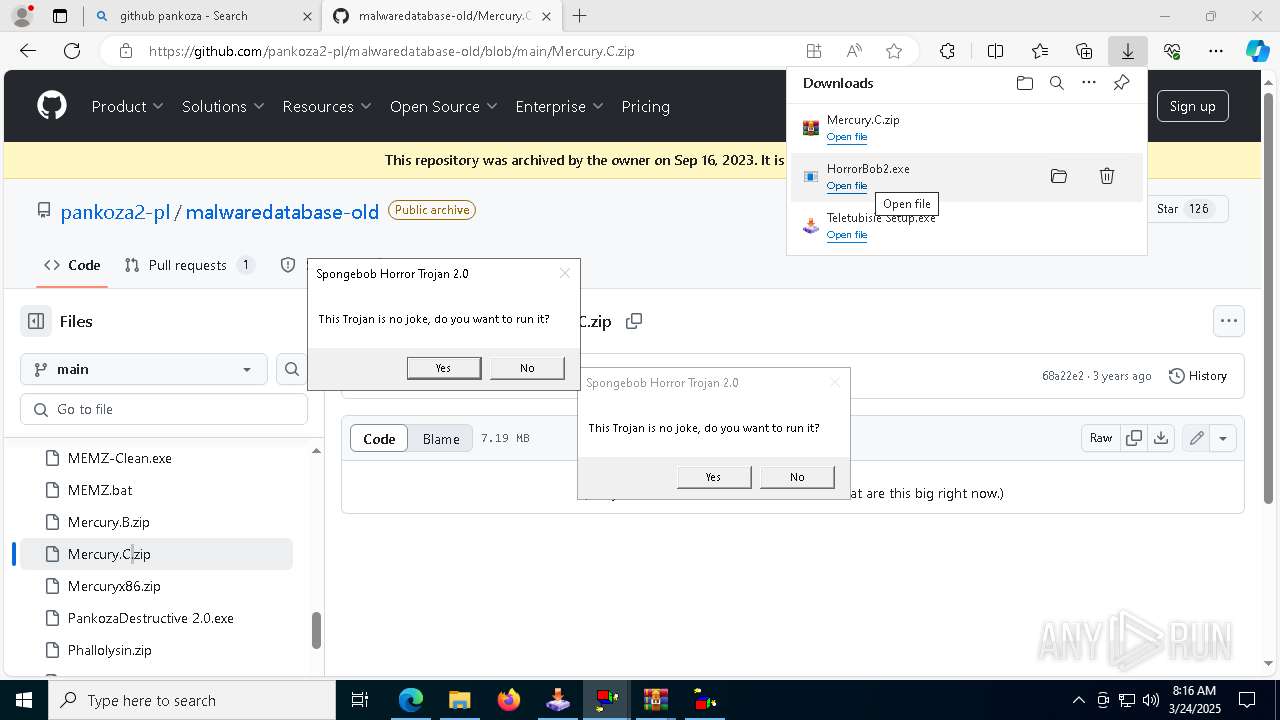
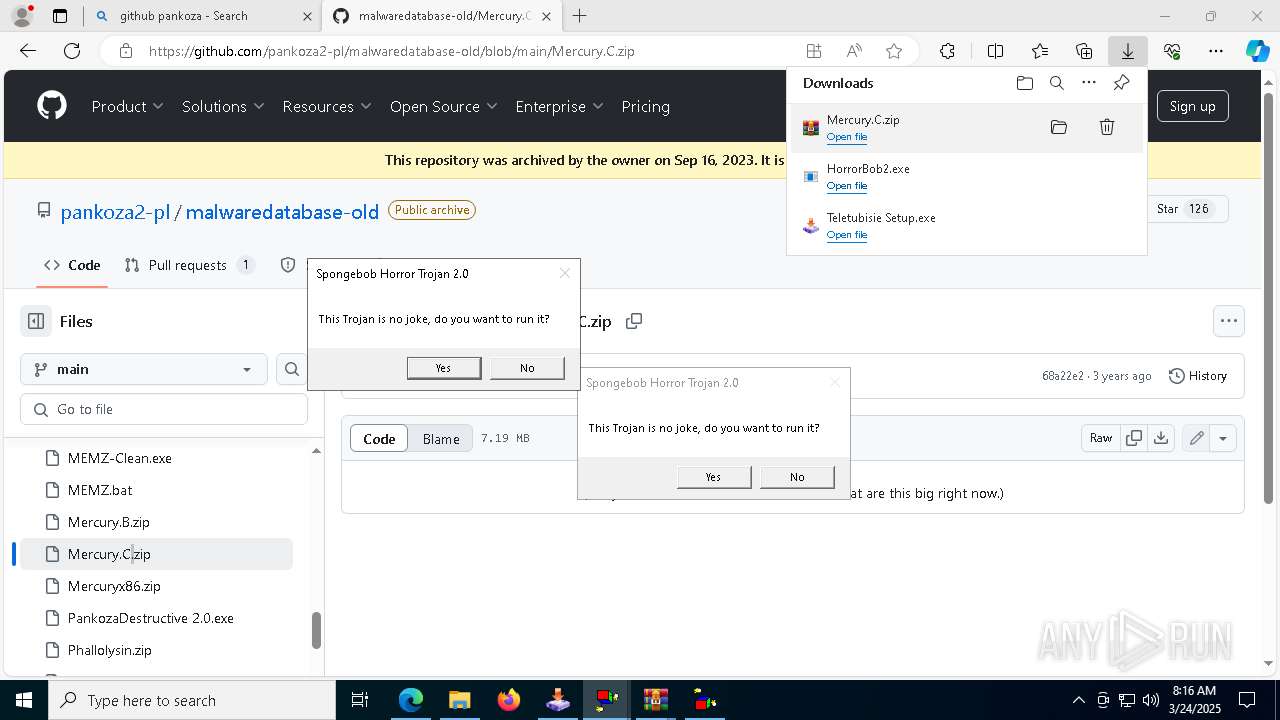
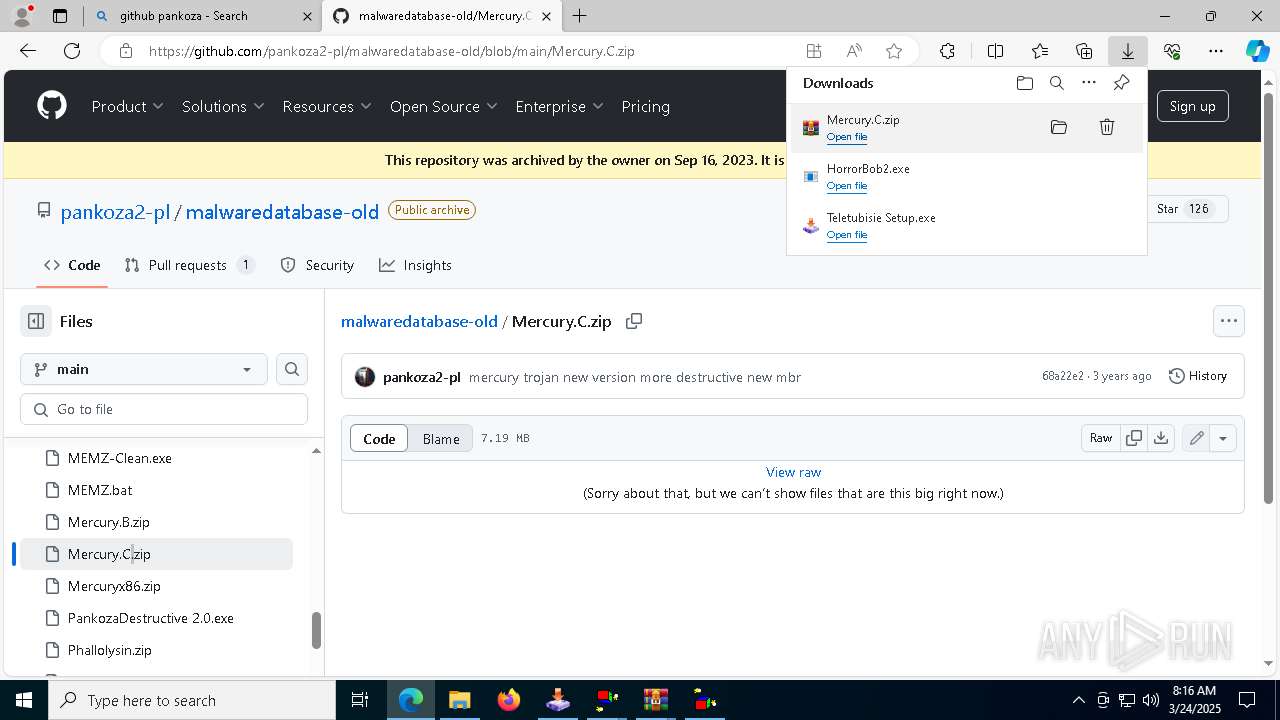
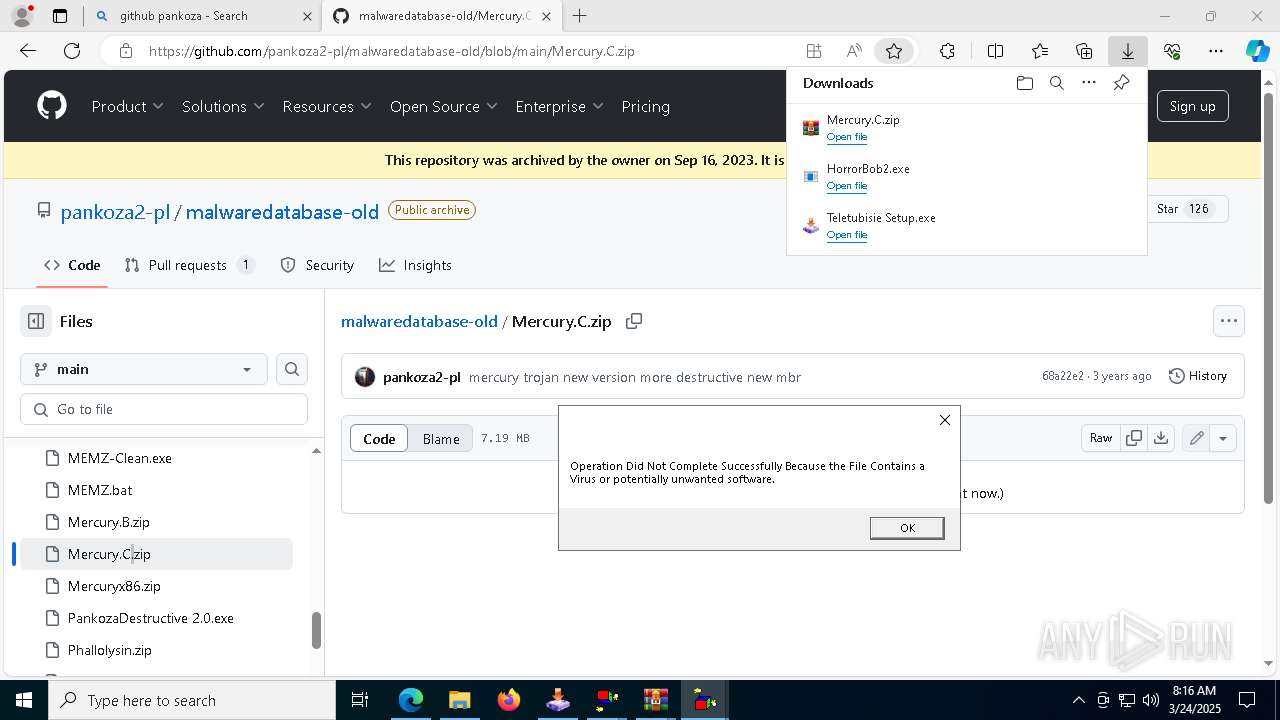
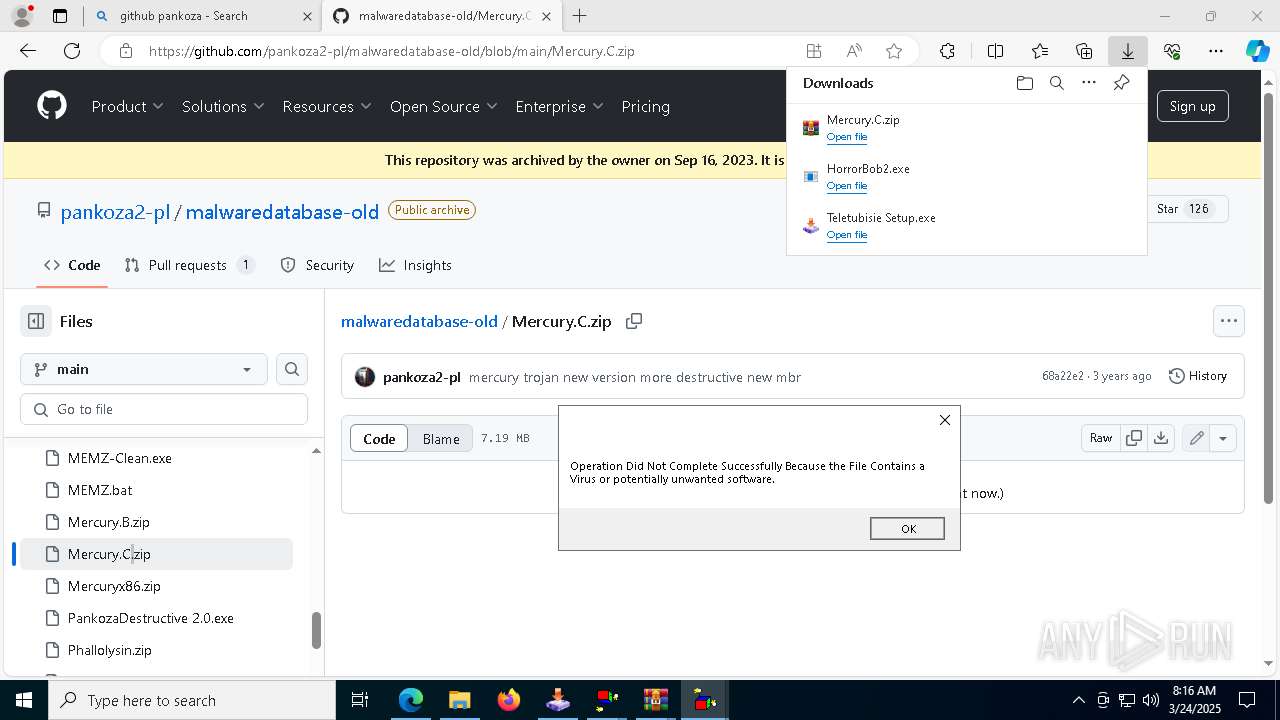
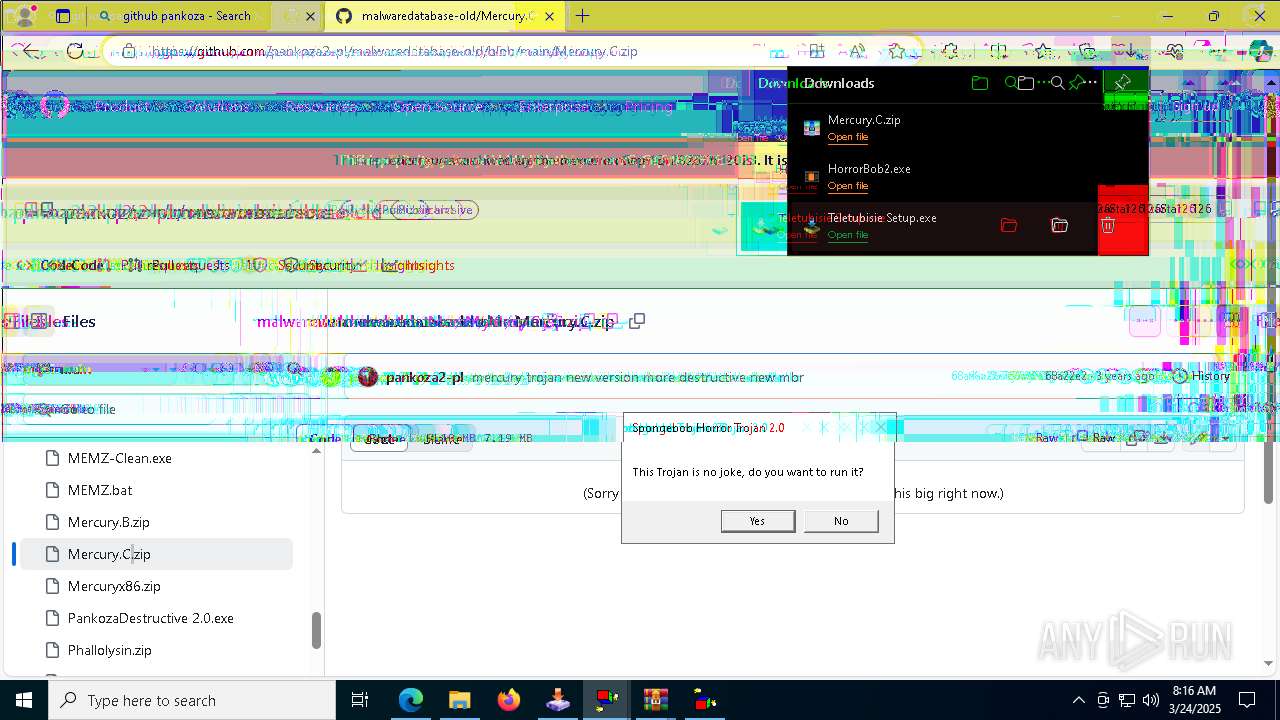
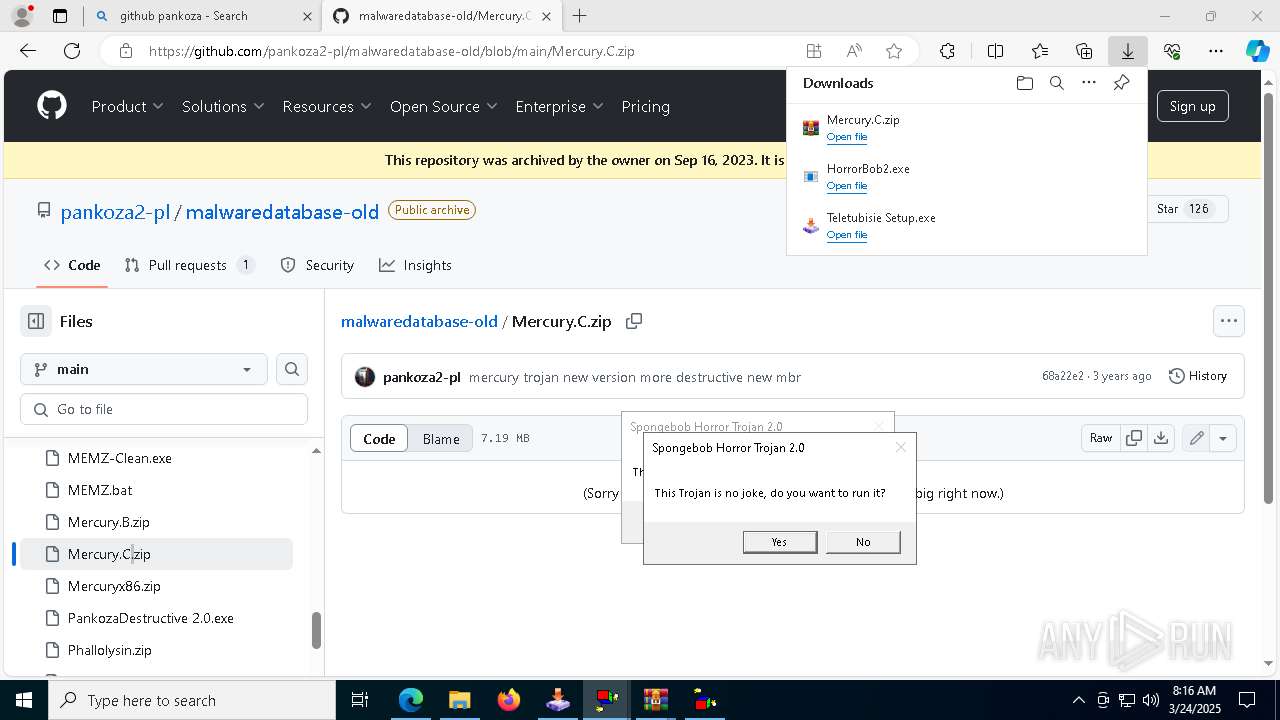
Manual execution by a user
- msedge.exe (PID: 8000)
- Teletubisie Setup.exe (PID: 7916)
- Teletubisie Setup.exe (PID: 7860)
- Teletubisie Setup.exe (PID: 7588)
- Teletubisie Setup.exe (PID: 6244)
Reads Environment values
- identity_helper.exe (PID: 7924)
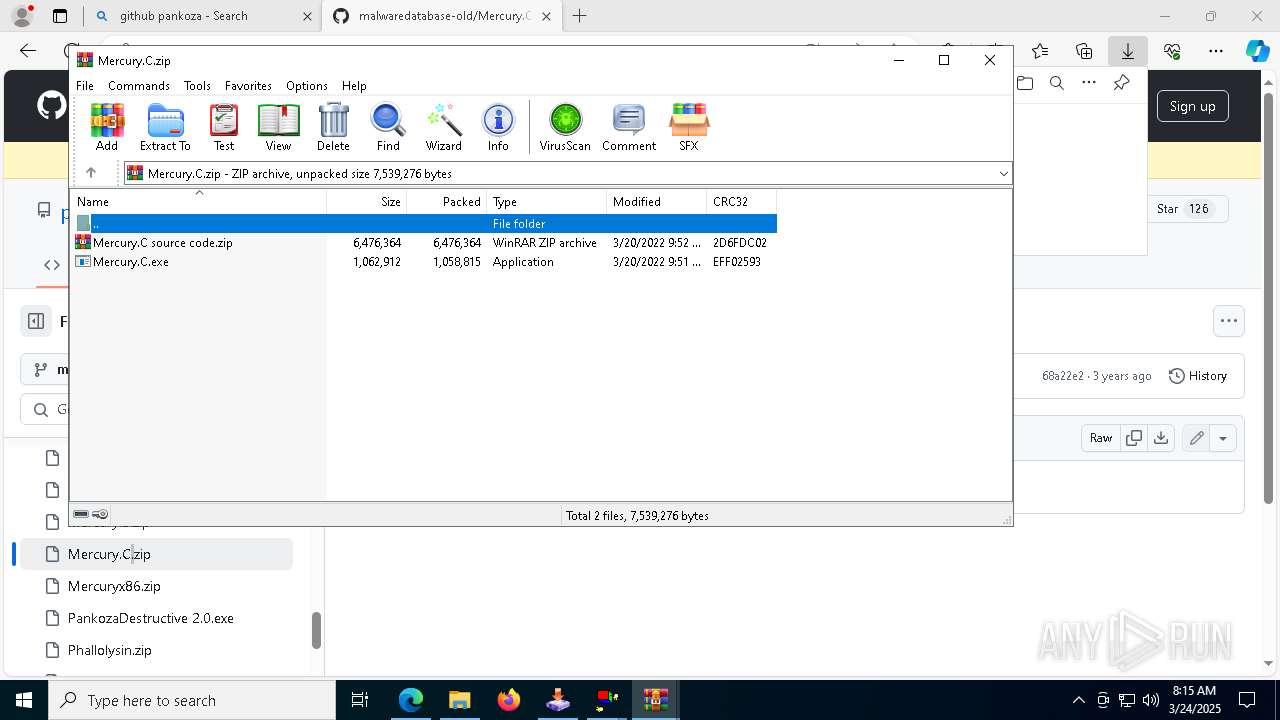
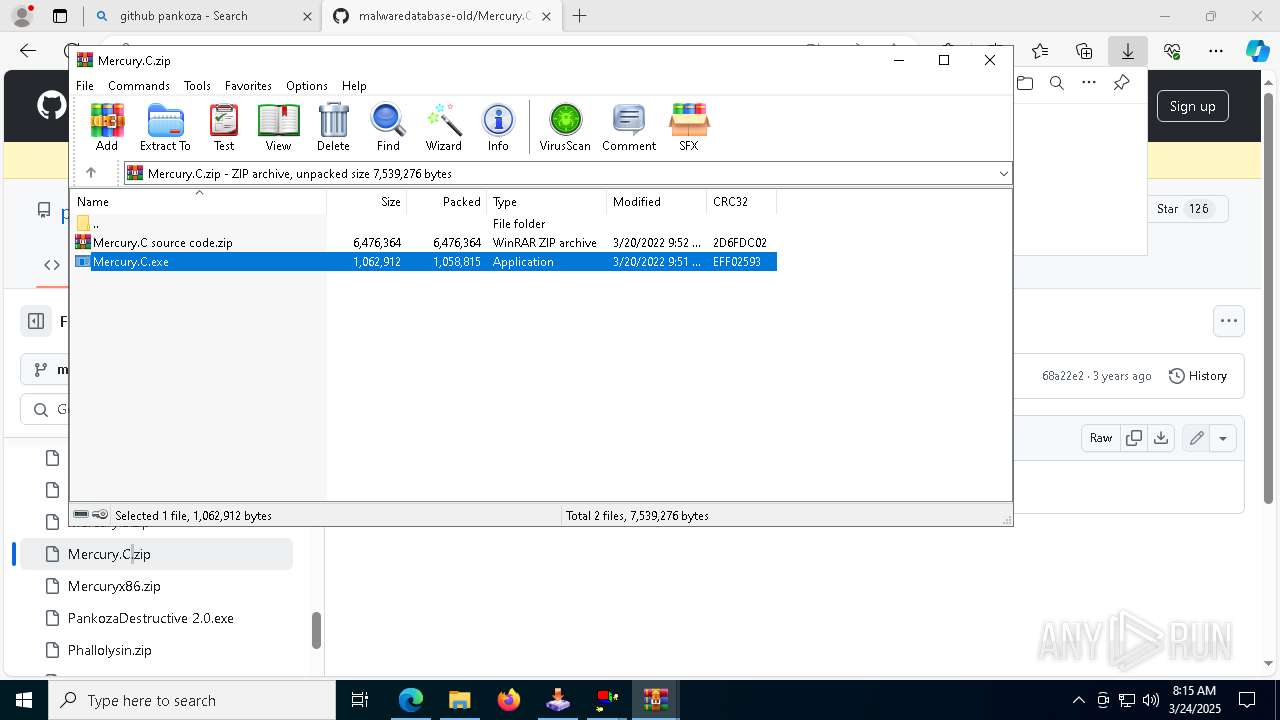
Executable content was dropped or overwritten
- msedge.exe (PID: 6036)
- msedge.exe (PID: 8000)
- WinRAR.exe (PID: 6940)
- msedge.exe (PID: 4188)
- WinRAR.exe (PID: 7356)
Checks supported languages
- identity_helper.exe (PID: 7924)
- Teletubisie Setup.exe (PID: 3884)
- HorrorBob2.exe (PID: 7800)
- HorrorBob2.exe (PID: 728)
- Teletubisie Setup.exe (PID: 4608)
- Teletubisie Setup.exe (PID: 968)
- Teletubisie Setup.exe (PID: 7740)
- HorrorBob2.exe (PID: 6416)
- Teletubisie Setup.exe (PID: 7860)
- Mercury.C.exe (PID: 4452)
- HorrorBob2.exe (PID: 4012)
- HorrorBob2.exe (PID: 7596)
- mbr.exe (PID: 4628)
Reads the computer name
- identity_helper.exe (PID: 7924)
- HorrorBob2.exe (PID: 728)
- HorrorBob2.exe (PID: 4304)
Reads the software policy settings
- slui.exe (PID: 7336)
- slui.exe (PID: 7948)
Autorun file from Downloads
- msedge.exe (PID: 8000)
- msedge.exe (PID: 1040)
- msedge.exe (PID: 2192)
- msedge.exe (PID: 5116)
The sample compiled with english language support
- msedge.exe (PID: 8000)
- msedge.exe (PID: 6036)
- WinRAR.exe (PID: 6940)
- msedge.exe (PID: 4188)
- WinRAR.exe (PID: 7356)
Create files in a temporary directory
- HorrorBob2.exe (PID: 7800)
- HorrorBob2.exe (PID: 728)
- Mercury.C.exe (PID: 1748)
- HorrorBob2.exe (PID: 6416)
- HorrorBob2.exe (PID: 4012)
- Mercury.C.exe (PID: 4452)
- HorrorBob2.exe (PID: 4304)
- HorrorBob2.exe (PID: 6080)
- HorrorBob2.exe (PID: 7596)
Application launched itself
- msedge.exe (PID: 8000)
Reads security settings of Internet Explorer
- cscript.exe (PID: 1040)
- wscript.exe (PID: 6892)
- cscript.exe (PID: 7572)
- cscript.exe (PID: 1188)
- cscript.exe (PID: 8360)
Process checks computer location settings
- HorrorBob2.exe (PID: 728)
- Mercury.C.exe (PID: 4452)
- HorrorBob2.exe (PID: 7596)
UPX packer has been detected
- HorrorBob2.exe (PID: 7800)
- HorrorBob2.exe (PID: 728)
Reads Microsoft Office registry keys
- msedge.exe (PID: 8000)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 51 |
|---|---|
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2000:03:28 21:40:54 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | 2524 |
| ZipUncompressedSize: | 34902 |
| ZipFileName: | lib 0.zip |
Total processes
293
Monitored processes
133
Malicious processes
4
Suspicious processes
8
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 232 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\B4B2.tmp\HorrorBob2.bat" " | C:\Windows\SysWOW64\cmd.exe | — | HorrorBob2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 664 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7164 --field-trial-handle=2420,i,6187170378630719756,14570524945737215652,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 728 | "C:\Users\admin\Downloads\HorrorBob2.exe" | C:\Users\admin\Downloads\HorrorBob2.exe | msedge.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 900 | "C:\Users\admin\Downloads\Teletubisie Setup.exe" | C:\Users\admin\Downloads\Teletubisie Setup.exe | — | msedge.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Version: 2,0,0,45 Modules
| |||||||||||||||
| 968 | "C:\Users\admin\Downloads\Teletubisie Setup.exe" | C:\Users\admin\Downloads\Teletubisie Setup.exe | msedge.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 2,0,0,45 Modules
| |||||||||||||||
| 1040 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6136 --field-trial-handle=2420,i,6187170378630719756,14570524945737215652,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1040 | cscript prompt.vbs | C:\Windows\SysWOW64\cscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Console Based Script Host Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 1168 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5092 --field-trial-handle=2420,i,6187170378630719756,14570524945737215652,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
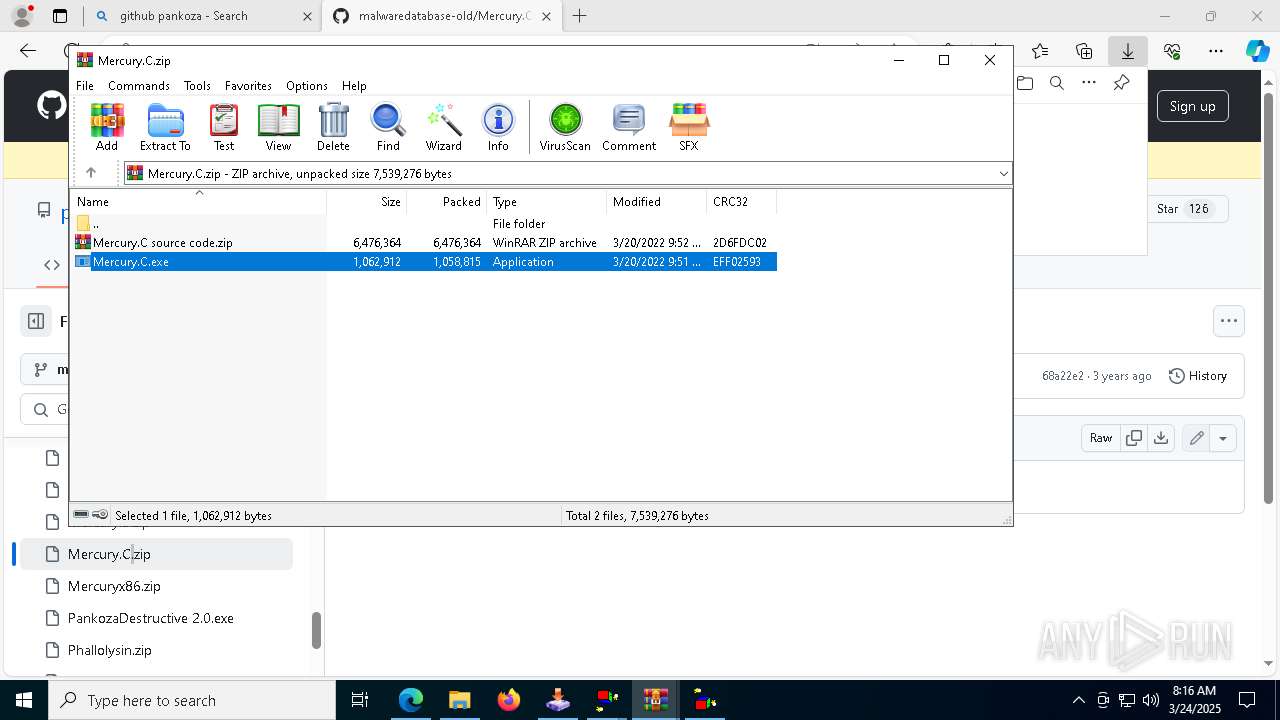
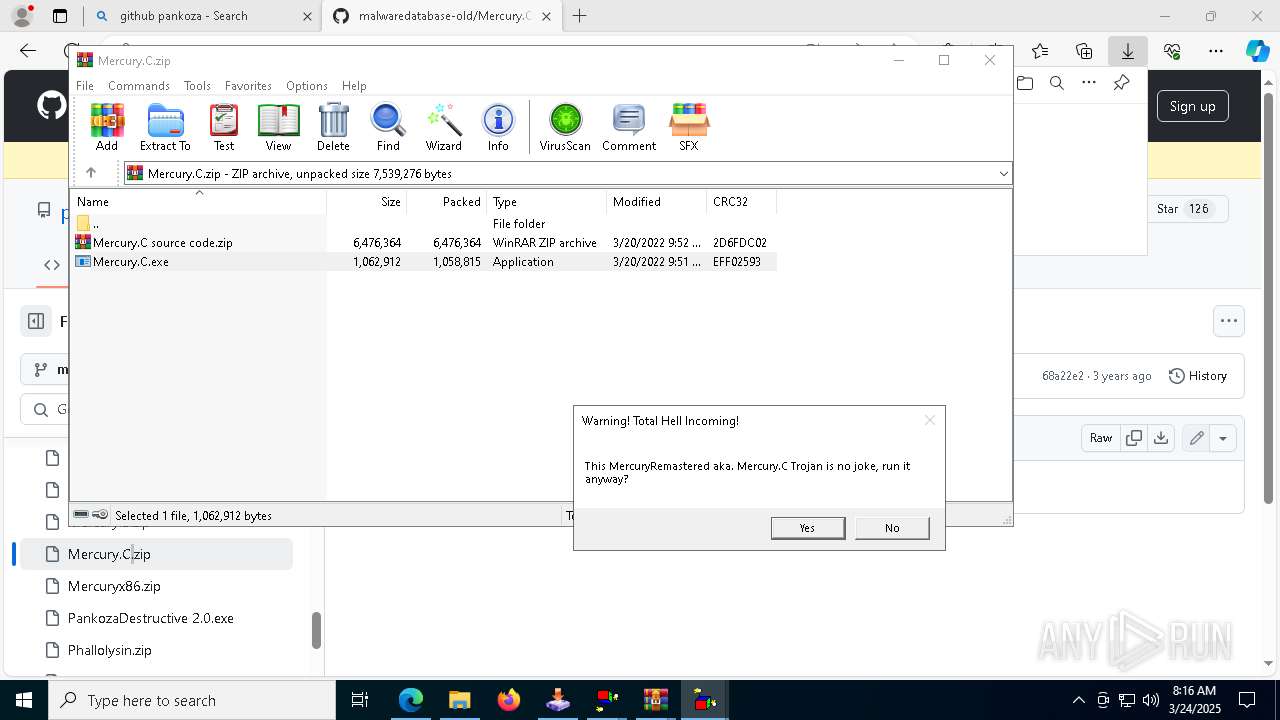
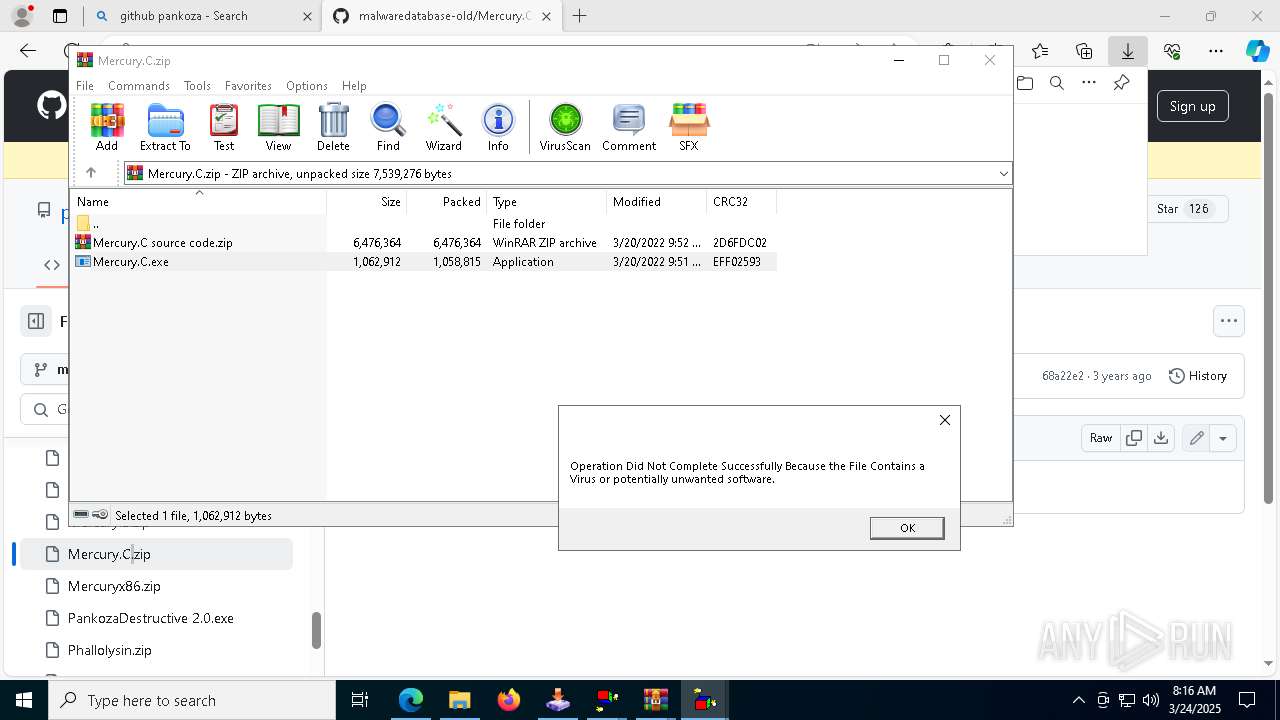
| 1188 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa6940.45848\Mercury.C.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa6940.45848\Mercury.C.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 1188 | "C:\Users\admin\Downloads\HorrorBob2.exe" | C:\Users\admin\Downloads\HorrorBob2.exe | — | msedge.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
Total events
23 935
Read events
23 837
Write events
98
Delete events
0
Modification events
| (PID) Process: | (6652) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6652) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6652) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6652) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\42.zip | |||
| (PID) Process: | (6652) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6652) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6652) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6652) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6652) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
| (PID) Process: | (6652) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
Executable files
76
Suspicious files
703
Text files
313
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 8000 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10d1e8.TMP | — | |
MD5:— | SHA256:— | |||
| 8000 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 8000 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10d1f8.TMP | — | |
MD5:— | SHA256:— | |||
| 8000 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 8000 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10d207.TMP | — | |
MD5:— | SHA256:— | |||
| 8000 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 8000 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10d1e8.TMP | — | |
MD5:— | SHA256:— | |||
| 8000 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10d1f8.TMP | — | |
MD5:— | SHA256:— | |||
| 8000 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 8000 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
29
TCP/UDP connections
130
DNS requests
140
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7420 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.32:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5936 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/84d3e481-77df-49da-bc37-0a994069ddb9?P1=1743114354&P2=404&P3=2&P4=mUNvypqSDuk32%2fc86570OLnfagfVQU6DCQqa0iOYSdZzNVXB1nQcdTFpRVJU9TGzgBhLFxeqG77jUyHt7RRk0Q%3d%3d | unknown | — | — | whitelisted |
7780 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7780 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5936 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/84d3e481-77df-49da-bc37-0a994069ddb9?P1=1743114354&P2=404&P3=2&P4=mUNvypqSDuk32%2fc86570OLnfagfVQU6DCQqa0iOYSdZzNVXB1nQcdTFpRVJU9TGzgBhLFxeqG77jUyHt7RRk0Q%3d%3d | unknown | — | — | whitelisted |
5936 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/84d3e481-77df-49da-bc37-0a994069ddb9?P1=1743114354&P2=404&P3=2&P4=mUNvypqSDuk32%2fc86570OLnfagfVQU6DCQqa0iOYSdZzNVXB1nQcdTFpRVJU9TGzgBhLFxeqG77jUyHt7RRk0Q%3d%3d | unknown | — | — | whitelisted |
5936 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/84d3e481-77df-49da-bc37-0a994069ddb9?P1=1743114354&P2=404&P3=2&P4=mUNvypqSDuk32%2fc86570OLnfagfVQU6DCQqa0iOYSdZzNVXB1nQcdTFpRVJU9TGzgBhLFxeqG77jUyHt7RRk0Q%3d%3d | unknown | — | — | whitelisted |
5936 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/84d3e481-77df-49da-bc37-0a994069ddb9?P1=1743114354&P2=404&P3=2&P4=mUNvypqSDuk32%2fc86570OLnfagfVQU6DCQqa0iOYSdZzNVXB1nQcdTFpRVJU9TGzgBhLFxeqG77jUyHt7RRk0Q%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.164.32:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4208 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 20.190.159.4:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
3216 | svchost.exe | 20.197.71.89:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | SG | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
ntp.msn.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
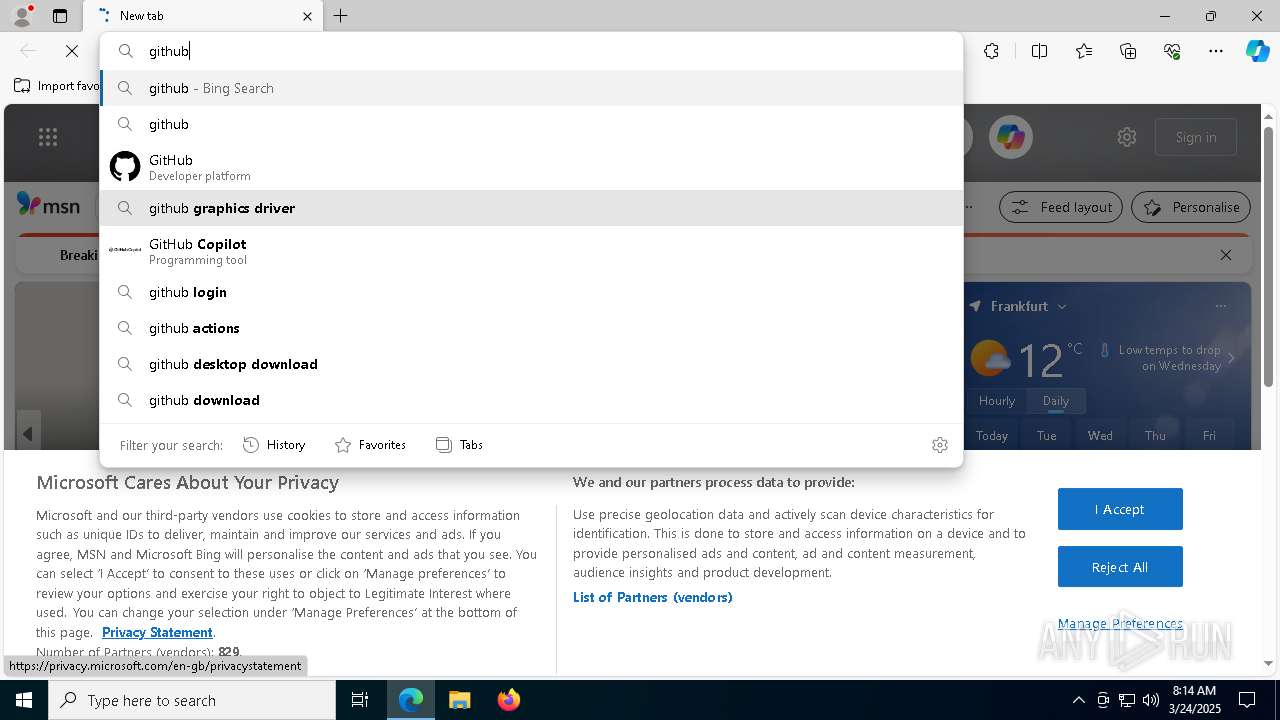
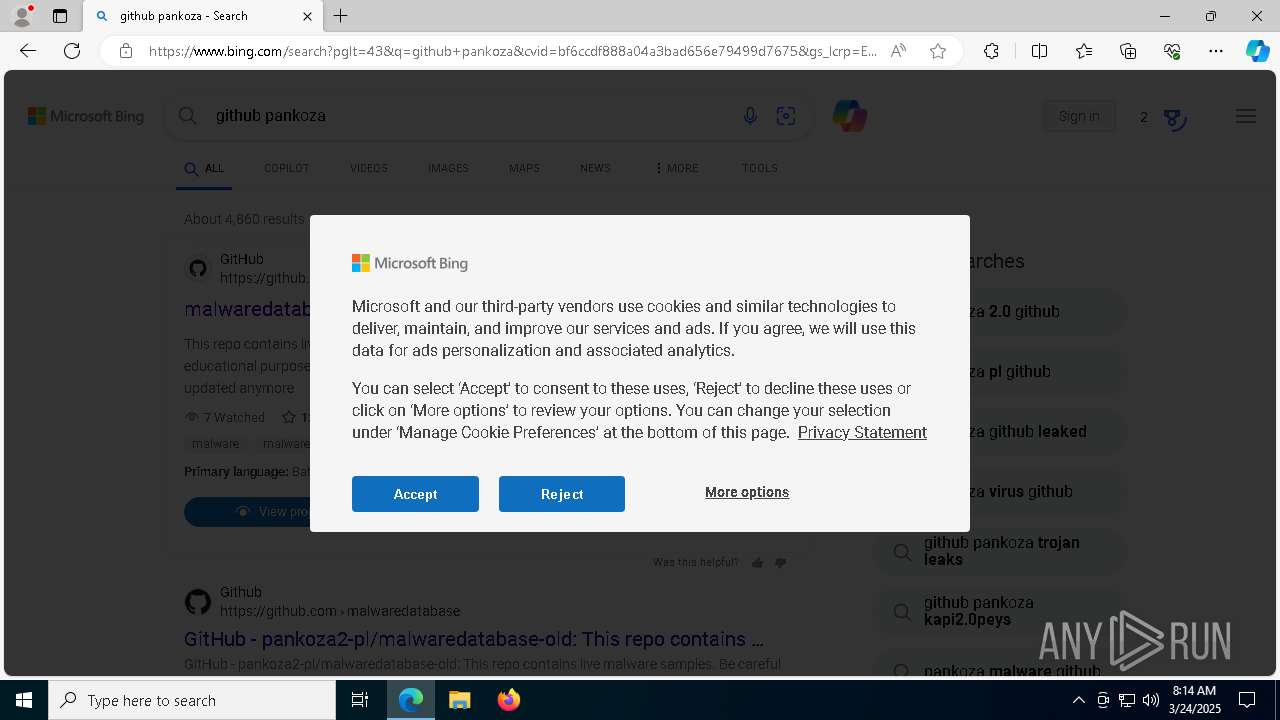
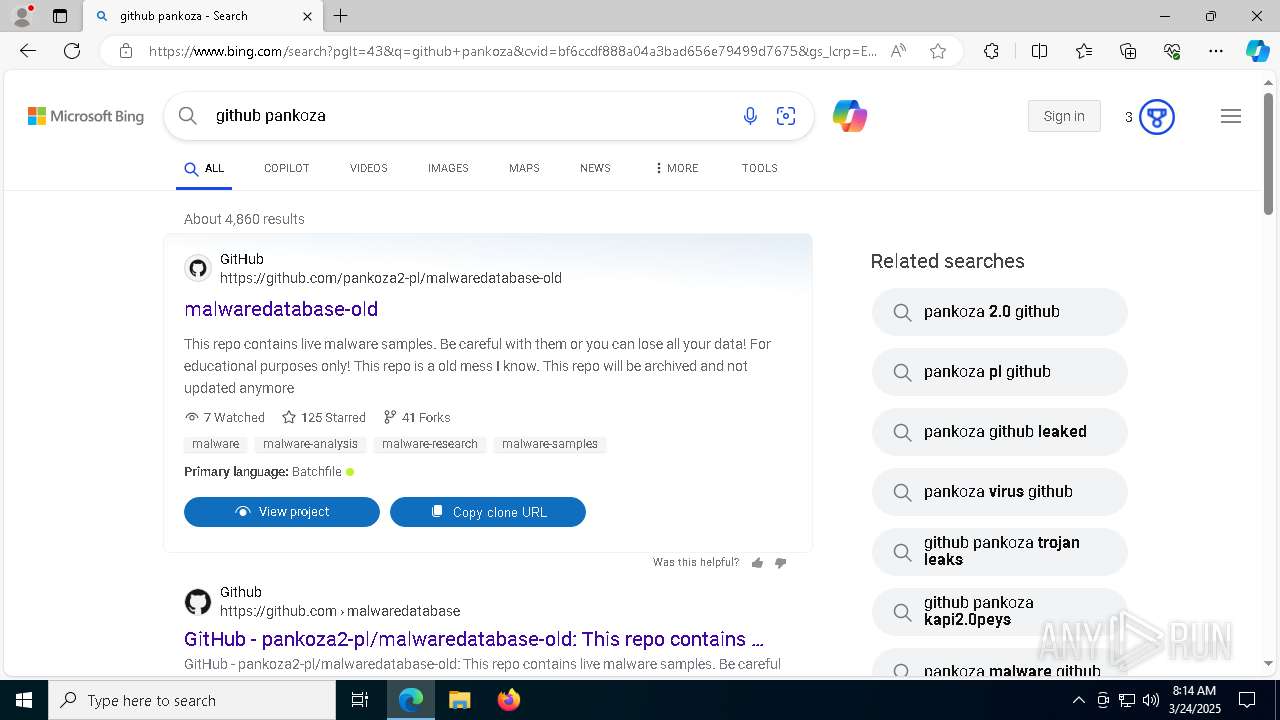
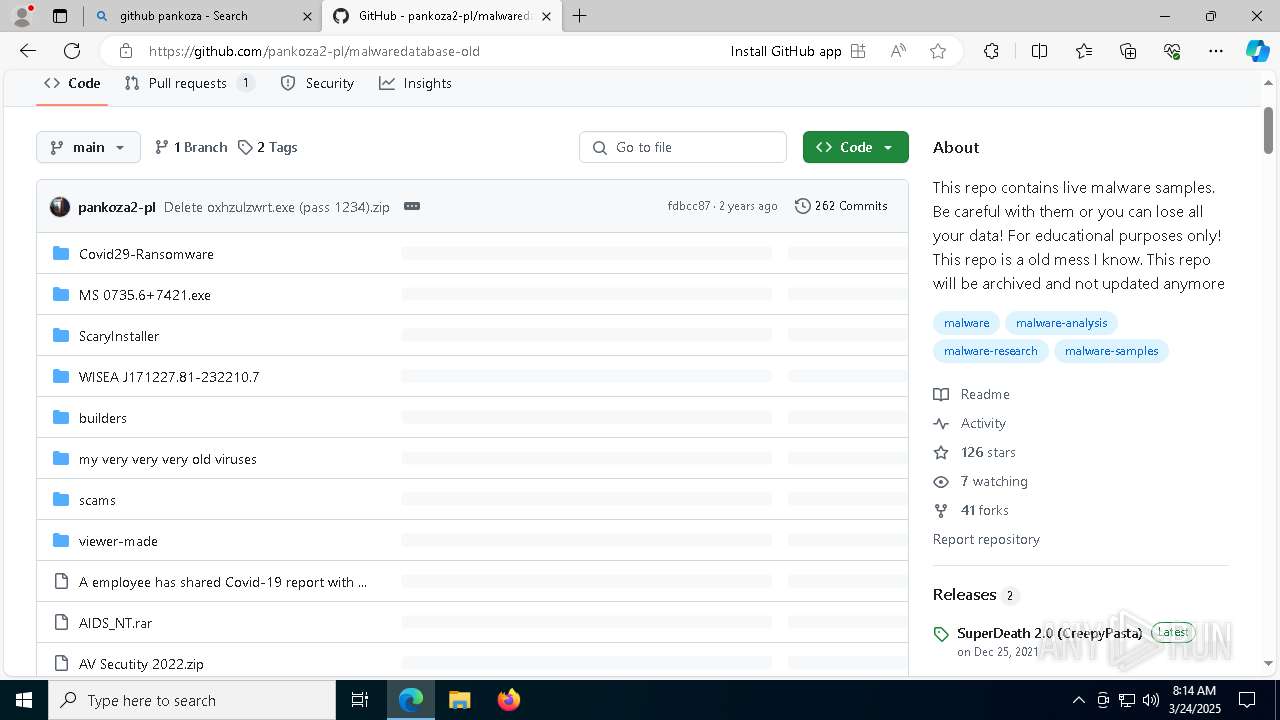
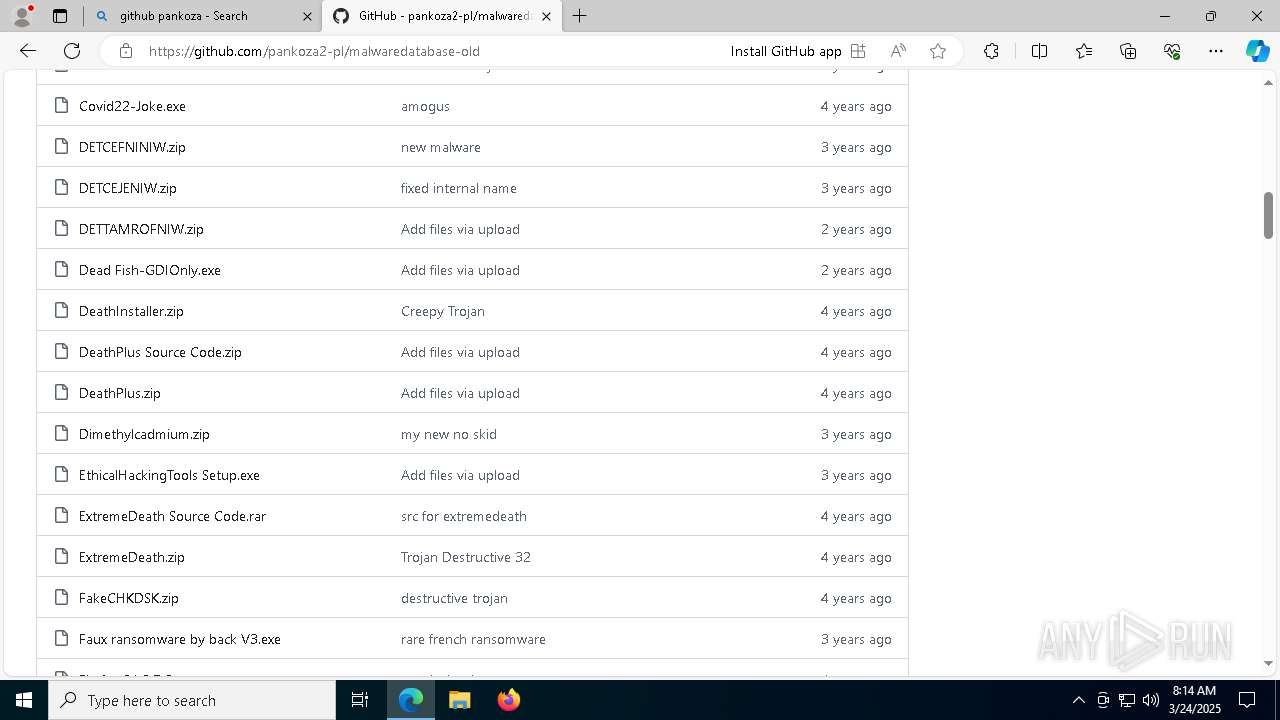
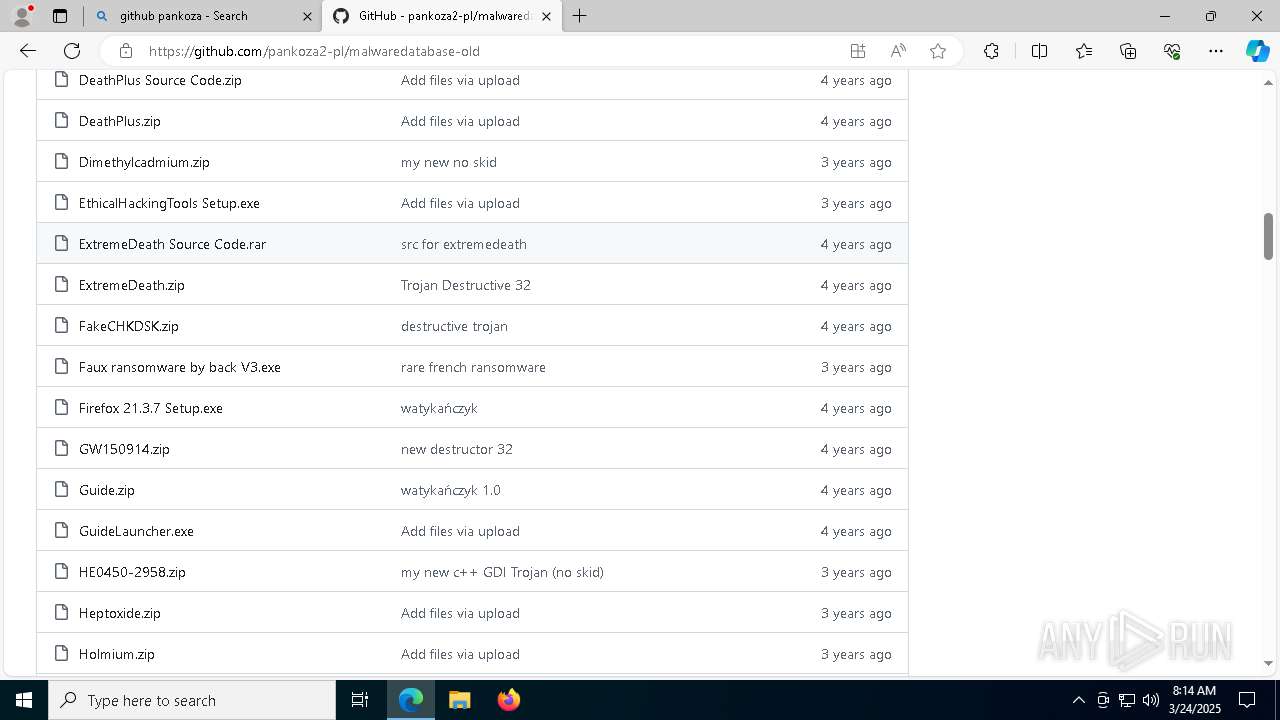
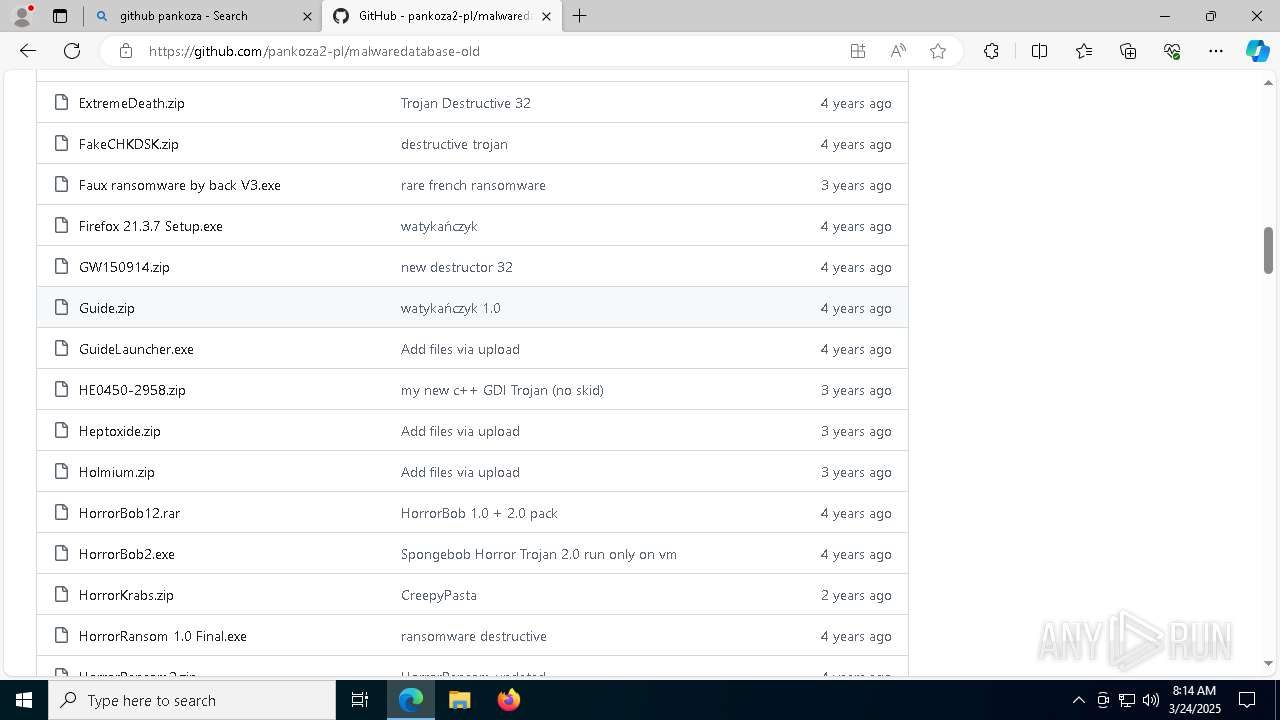
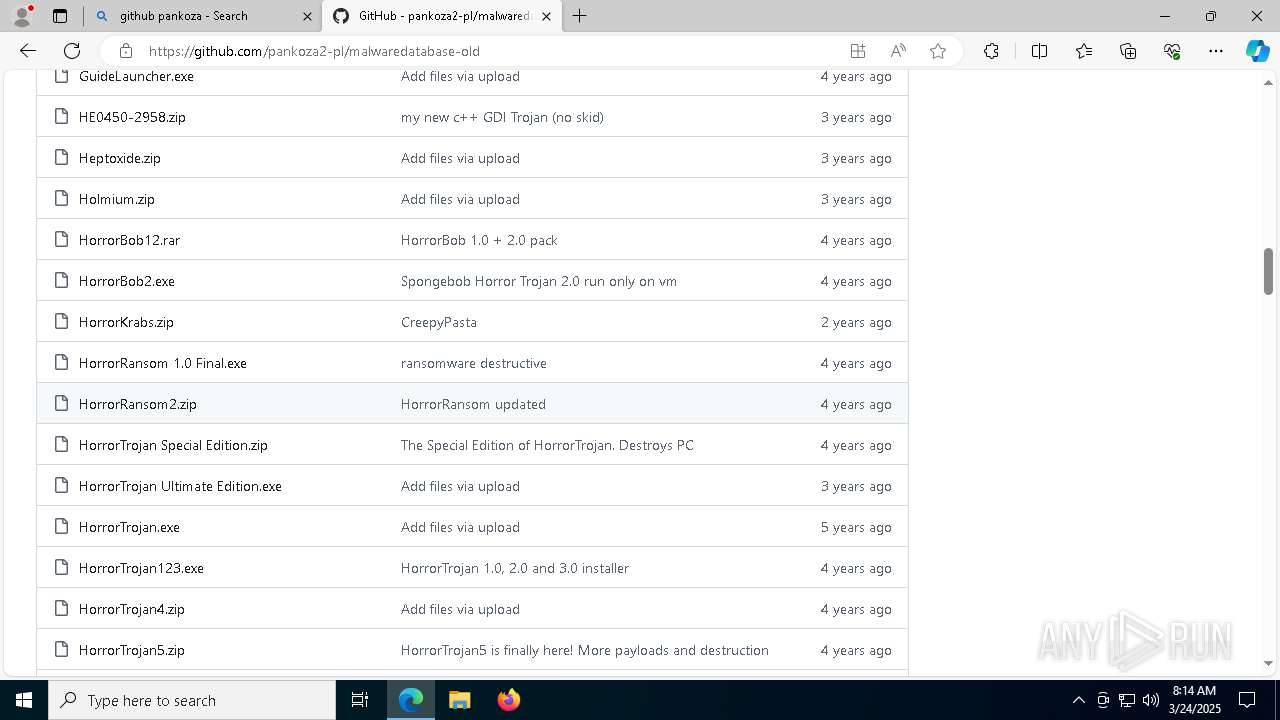
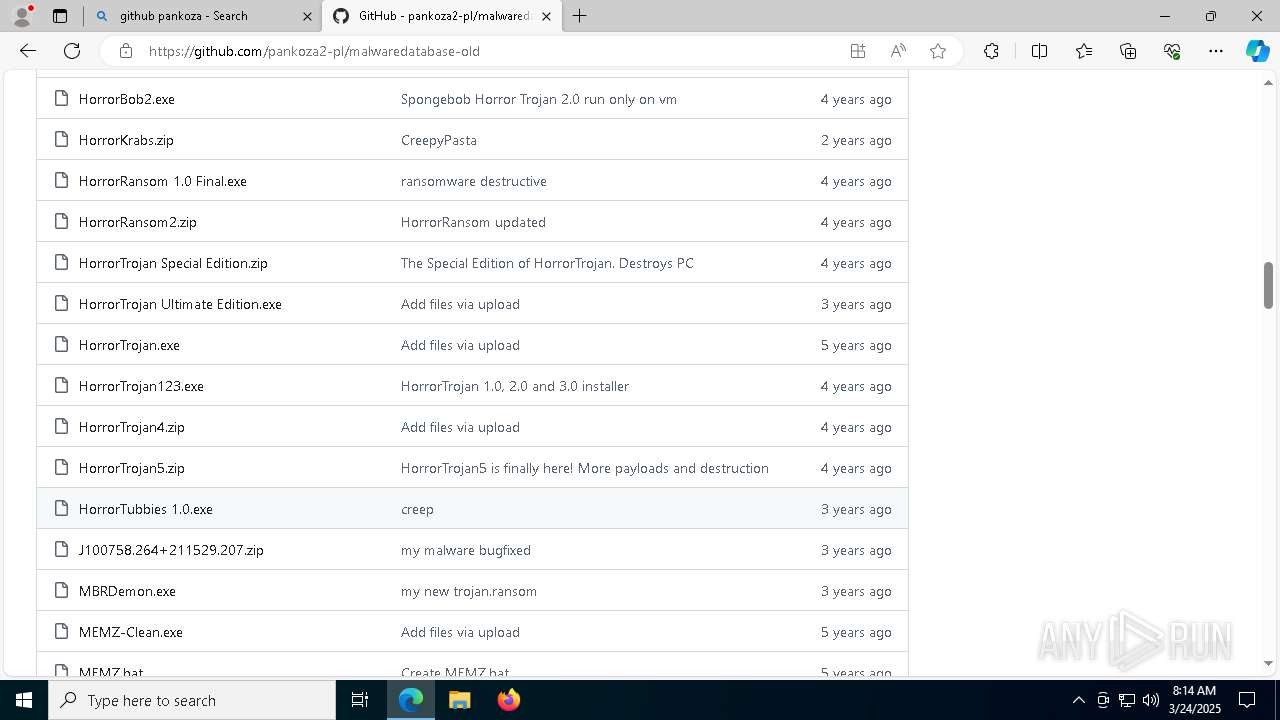
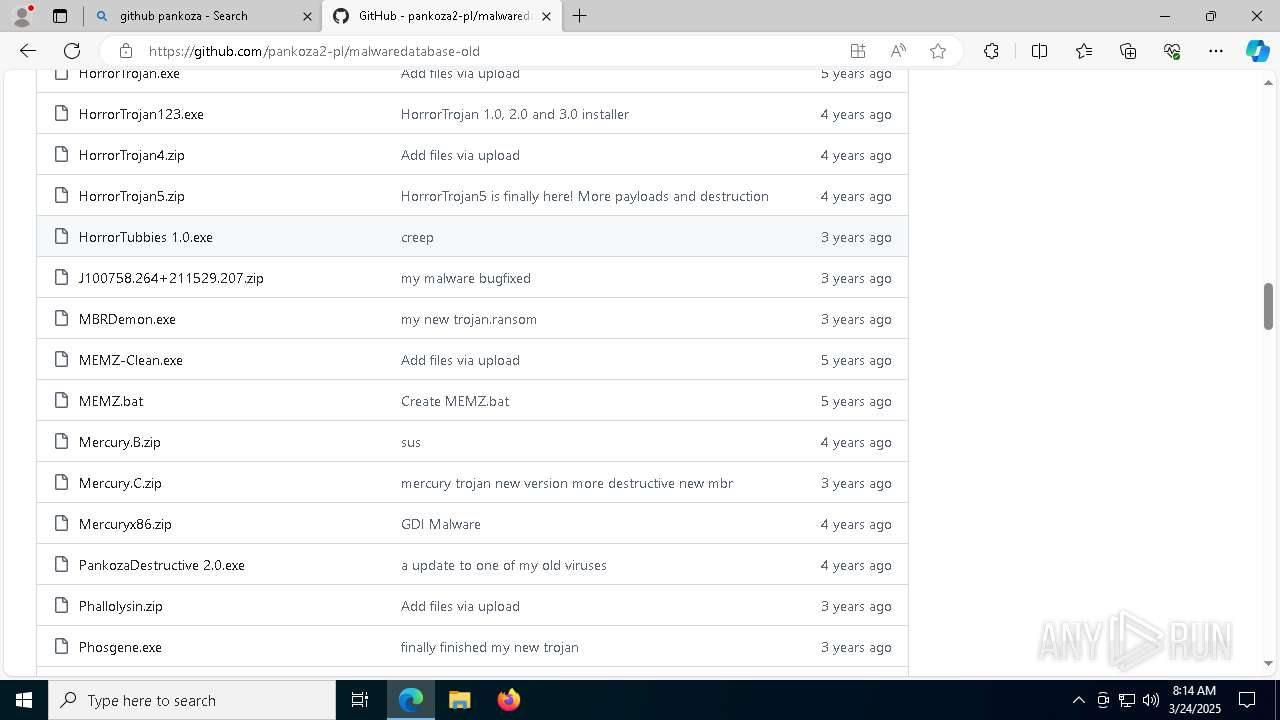
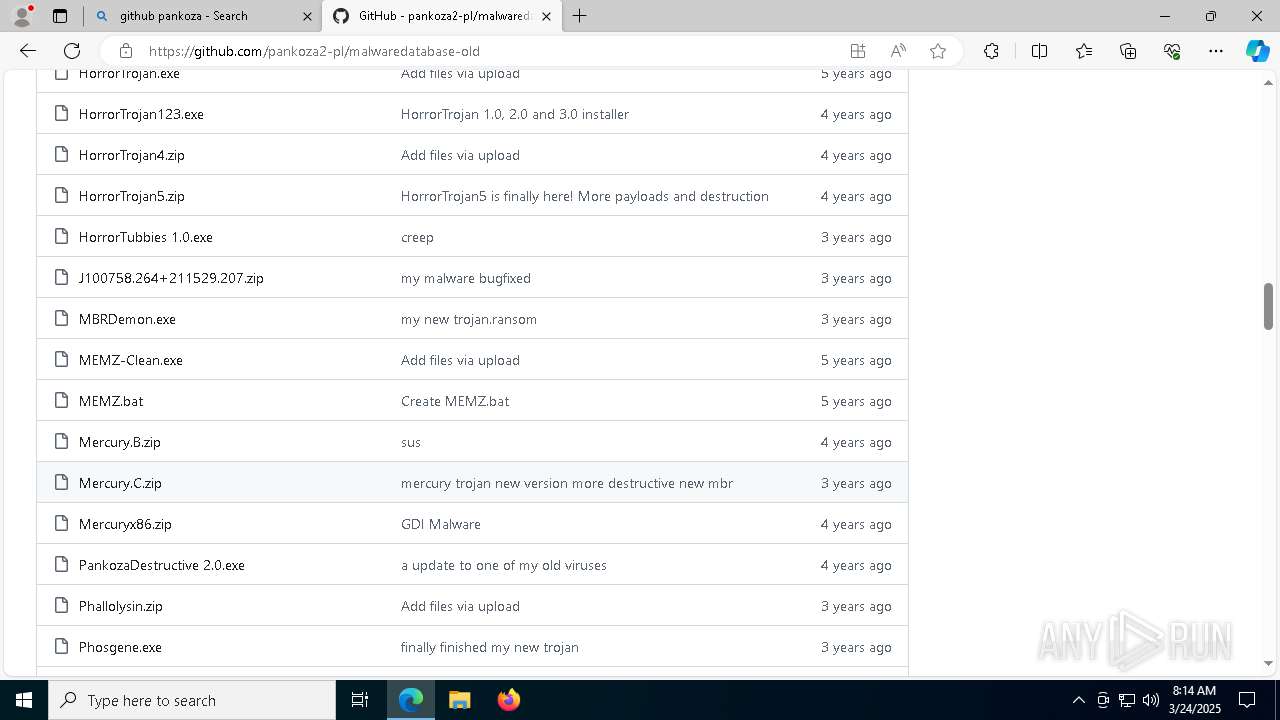
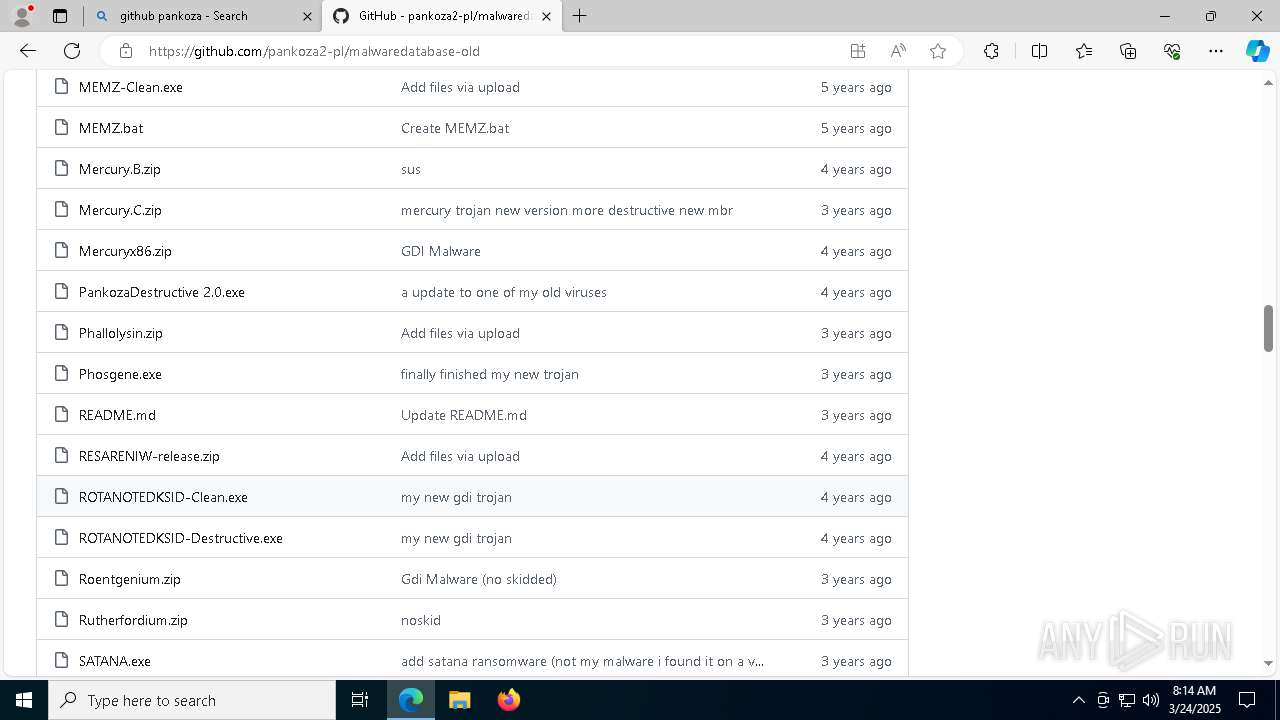
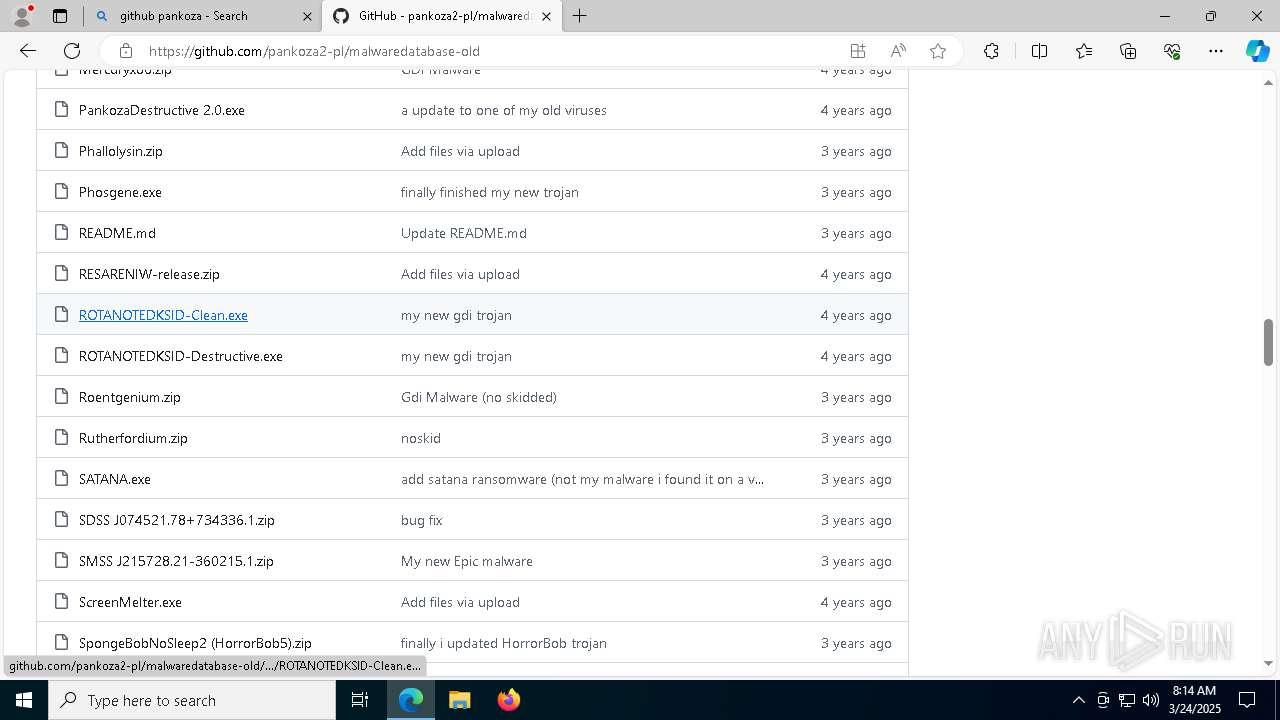
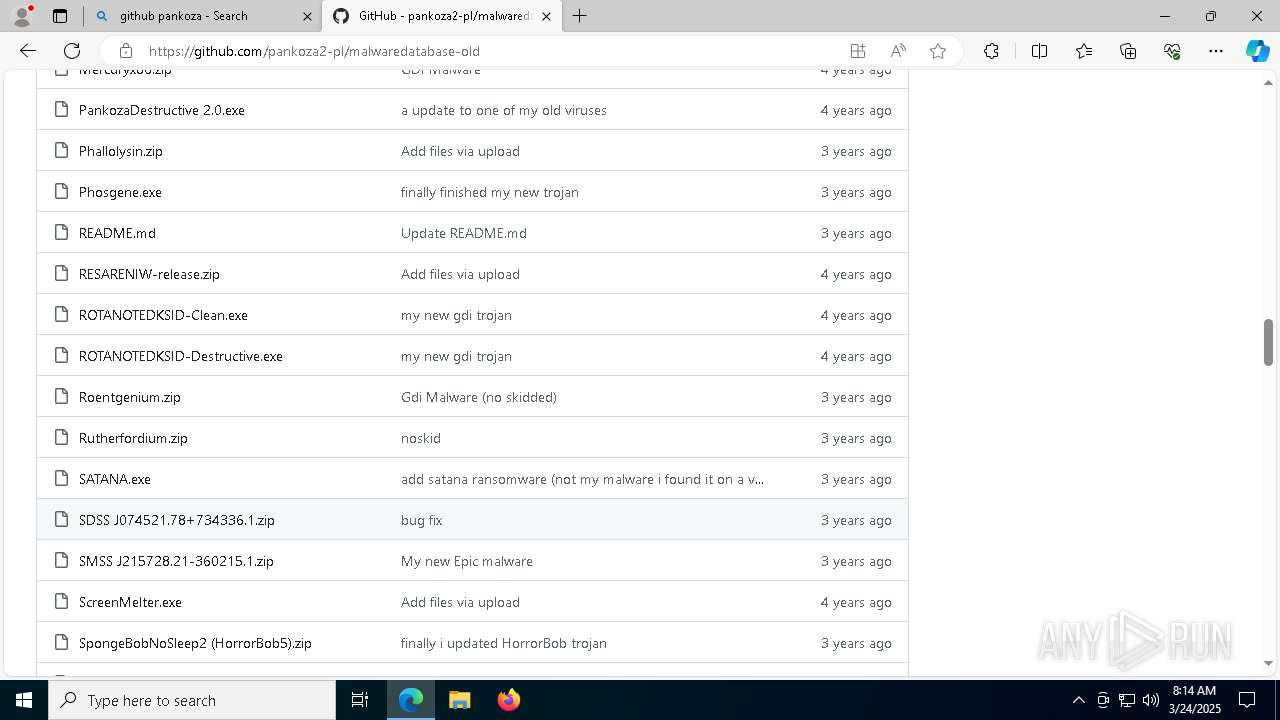
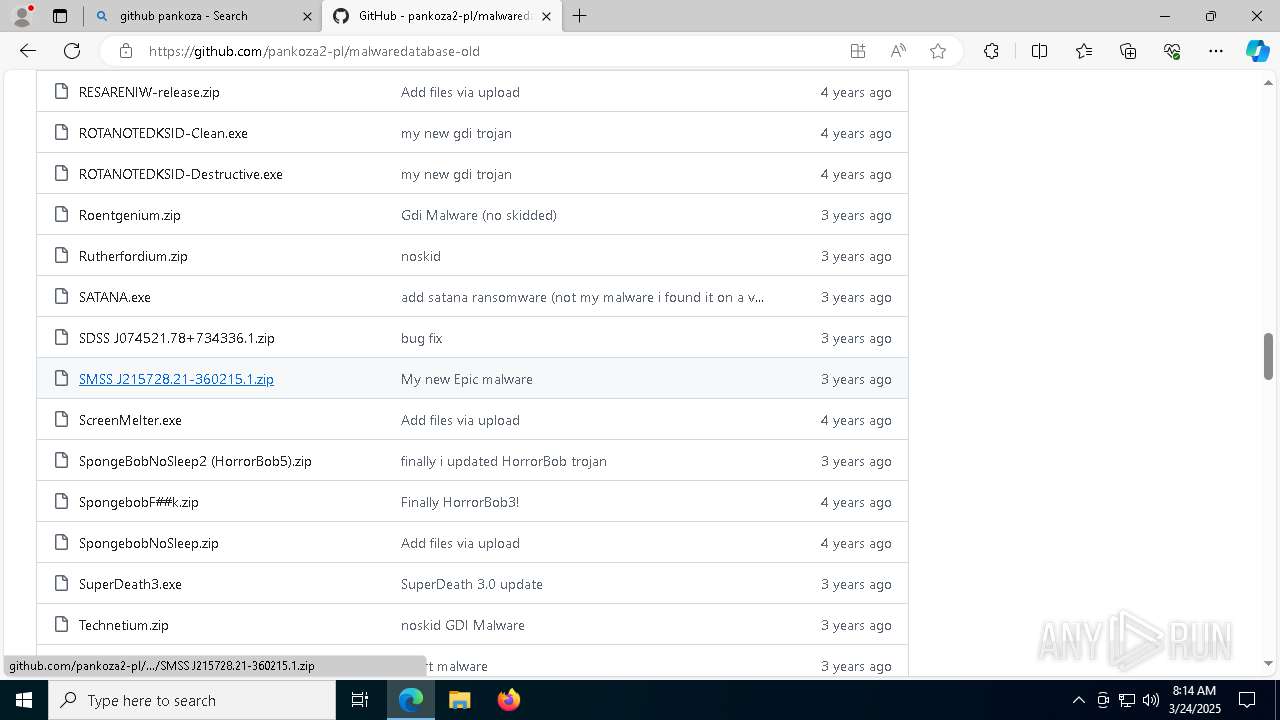
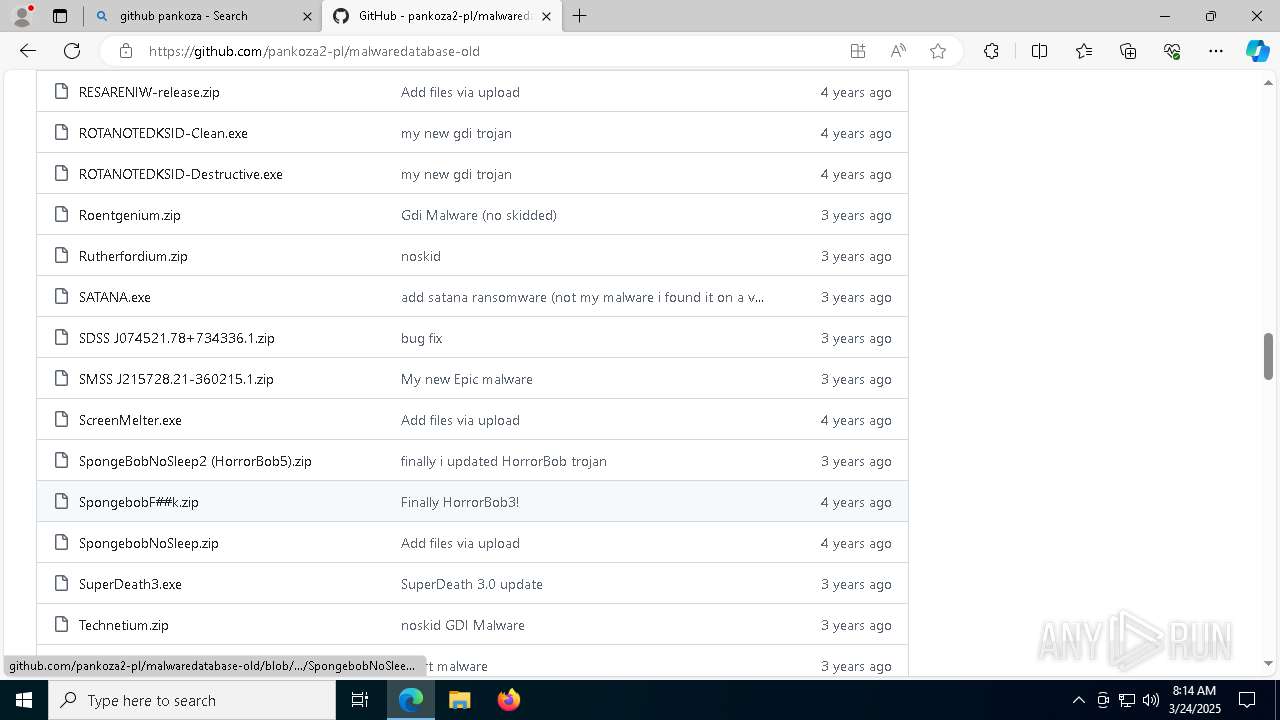
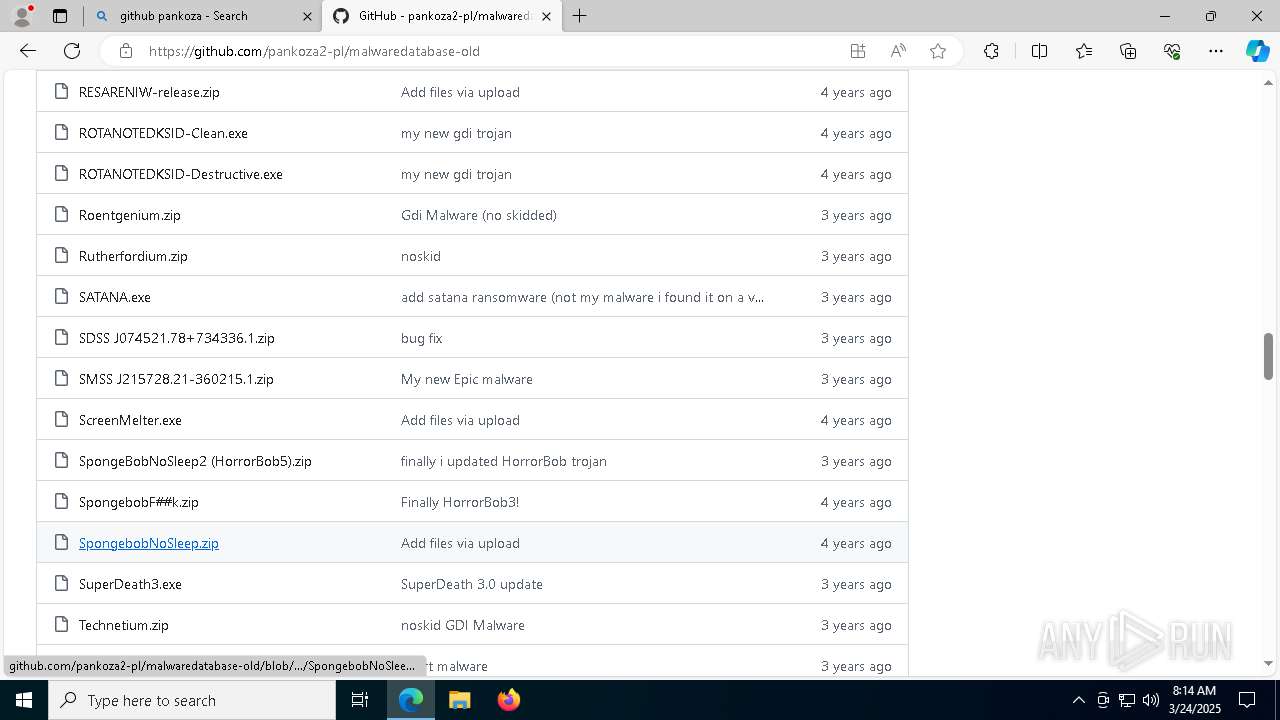
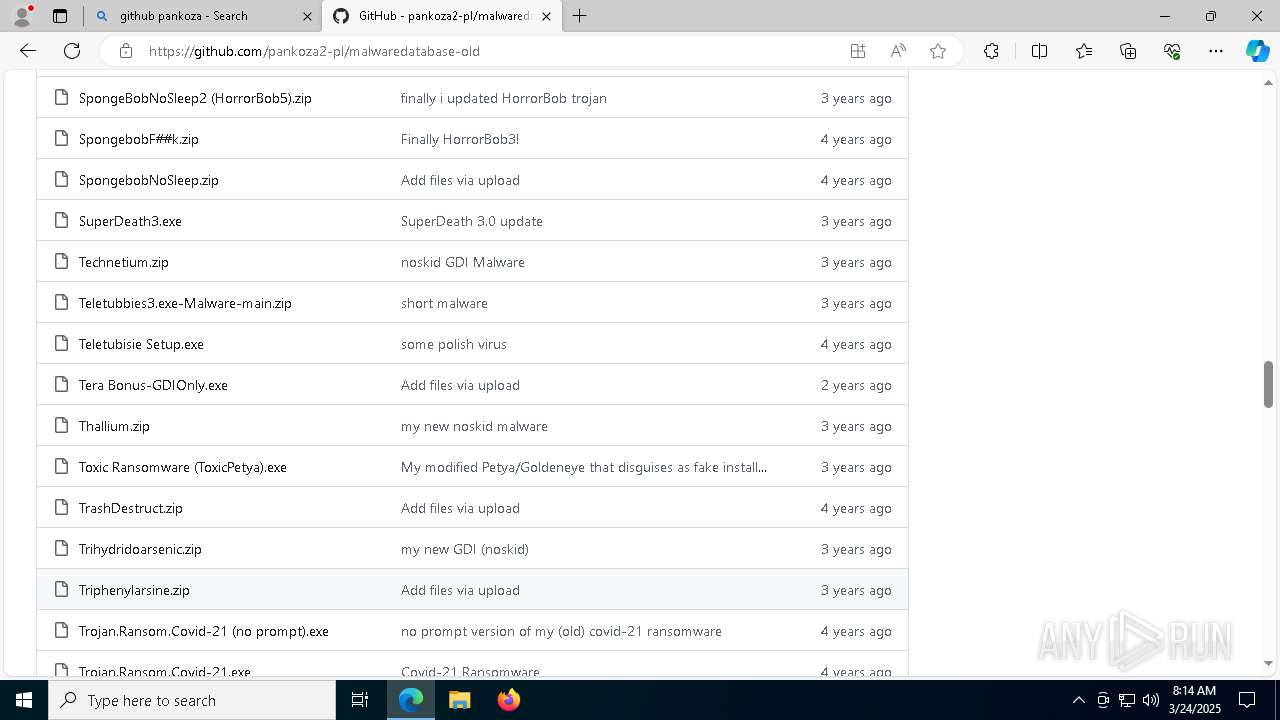
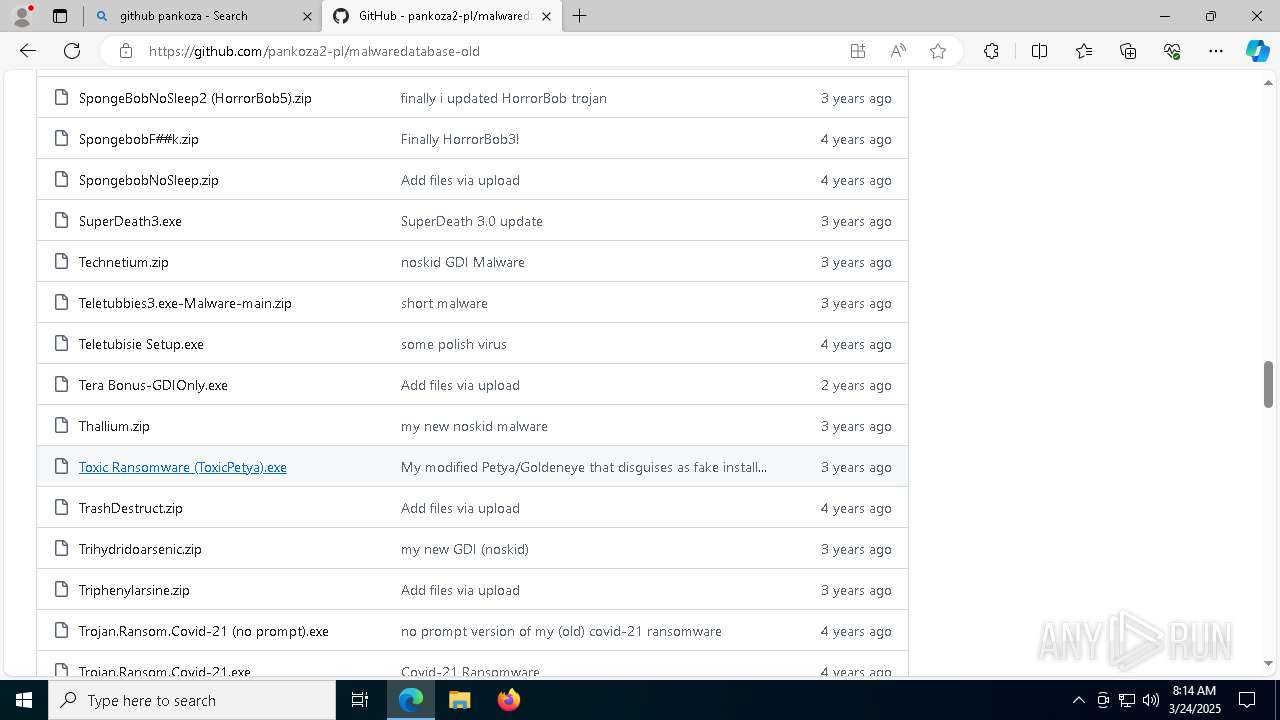
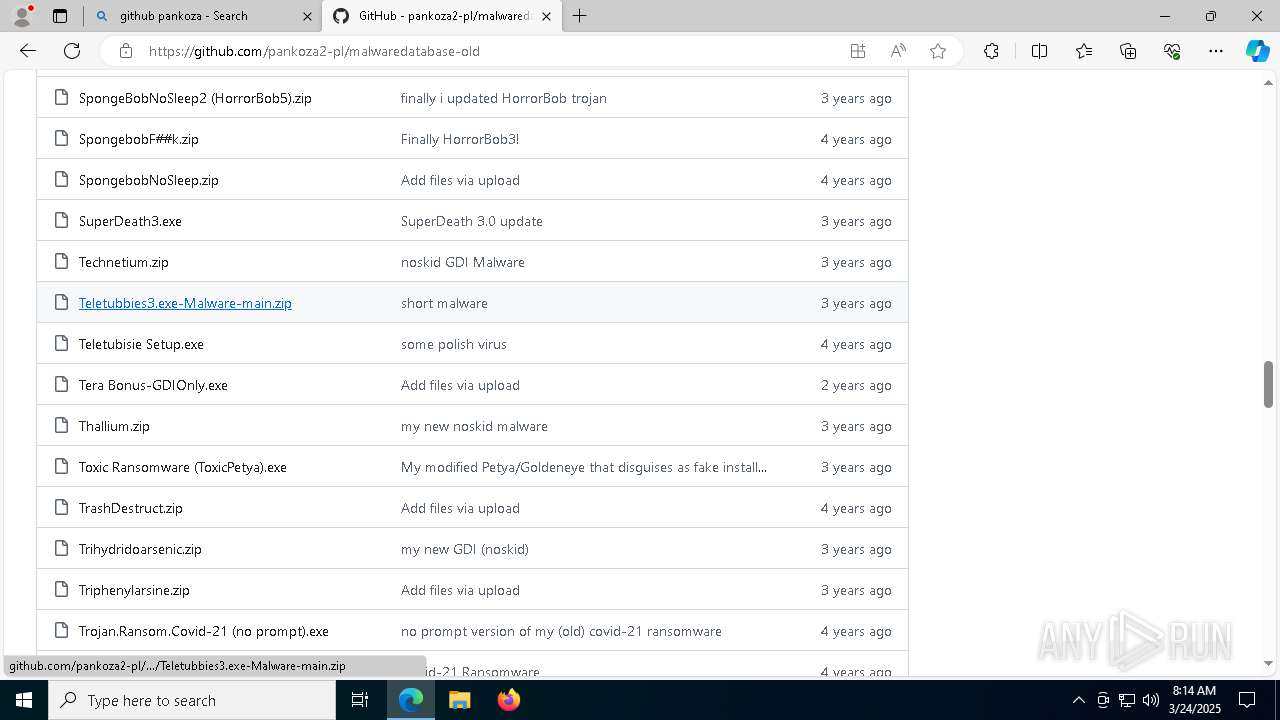
6036 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
6036 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
6036 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
6036 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |