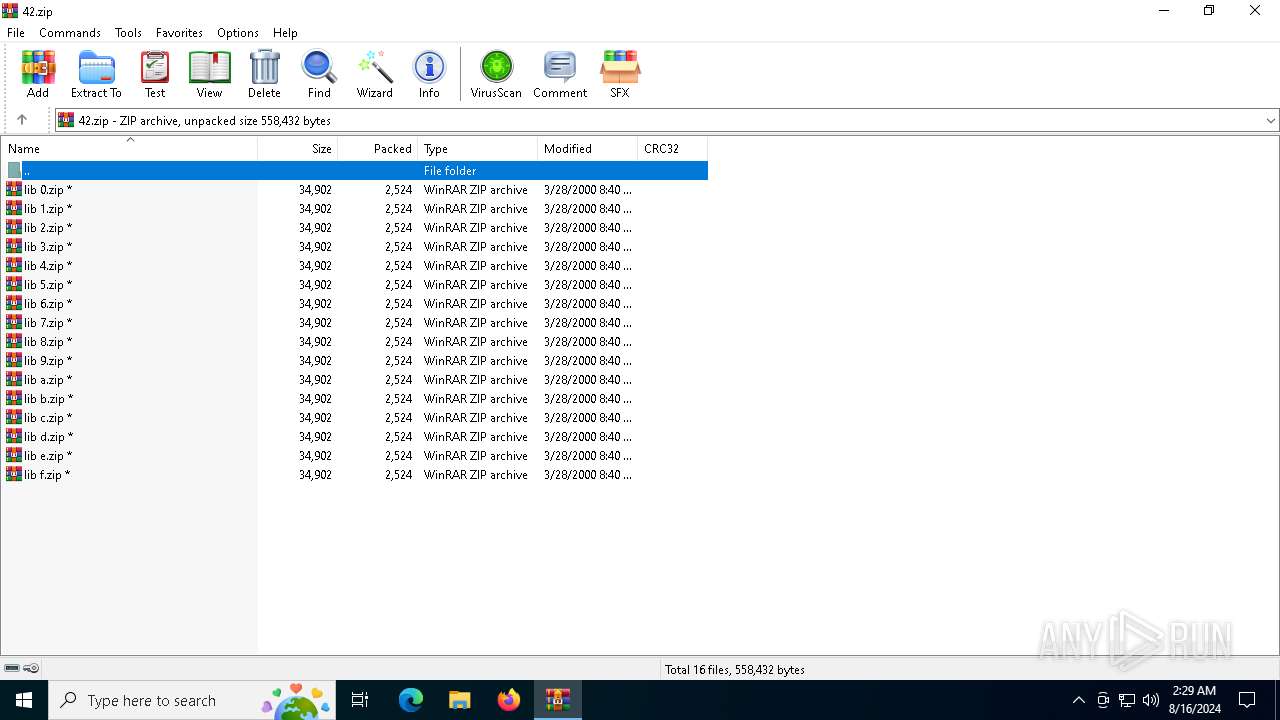
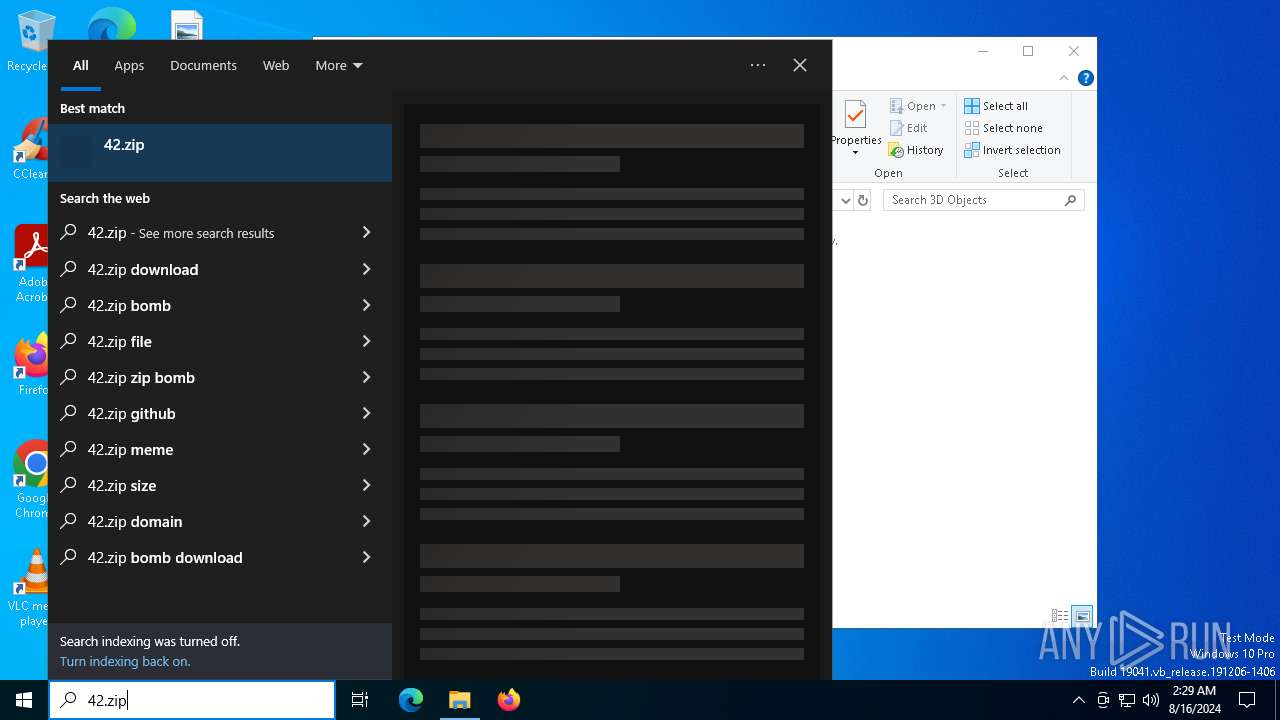
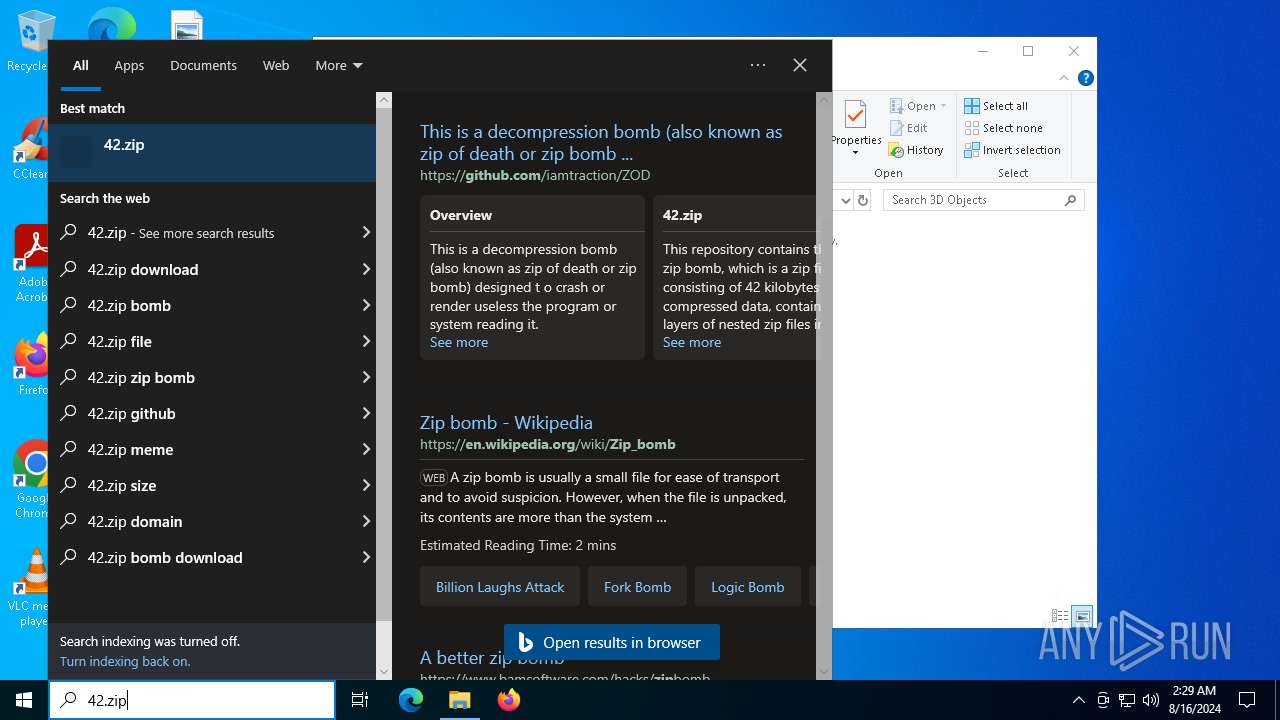
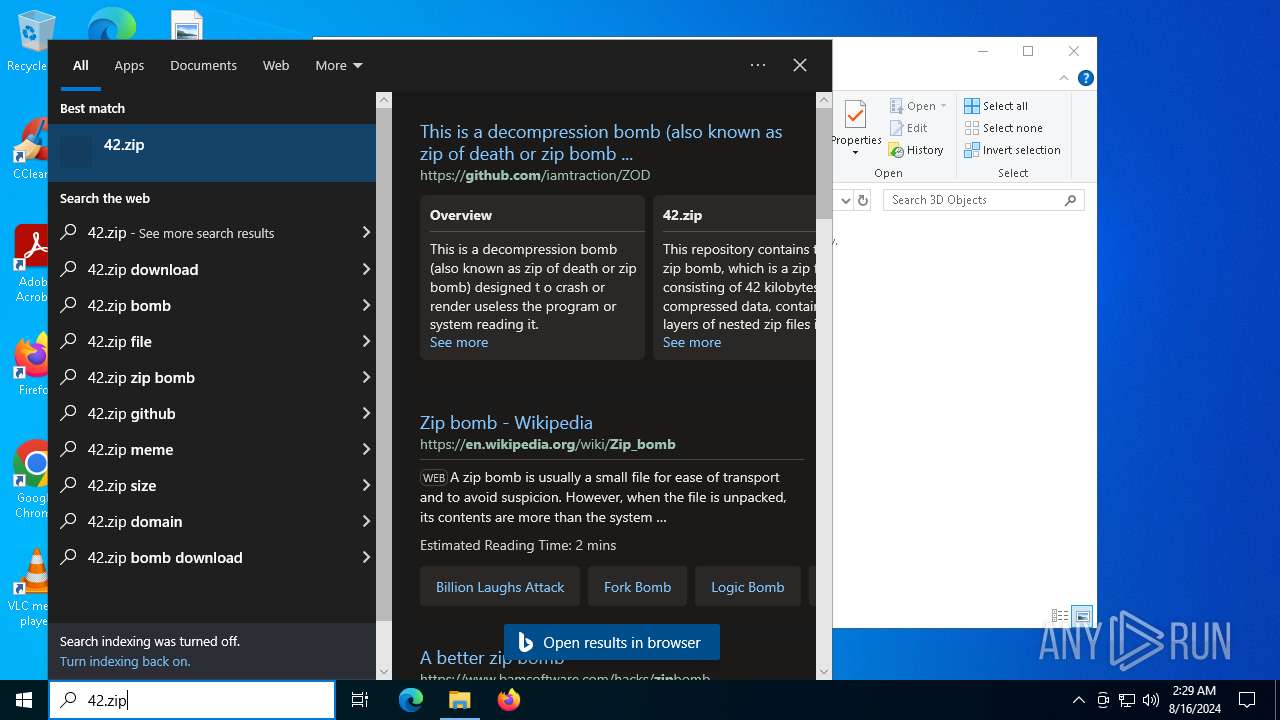
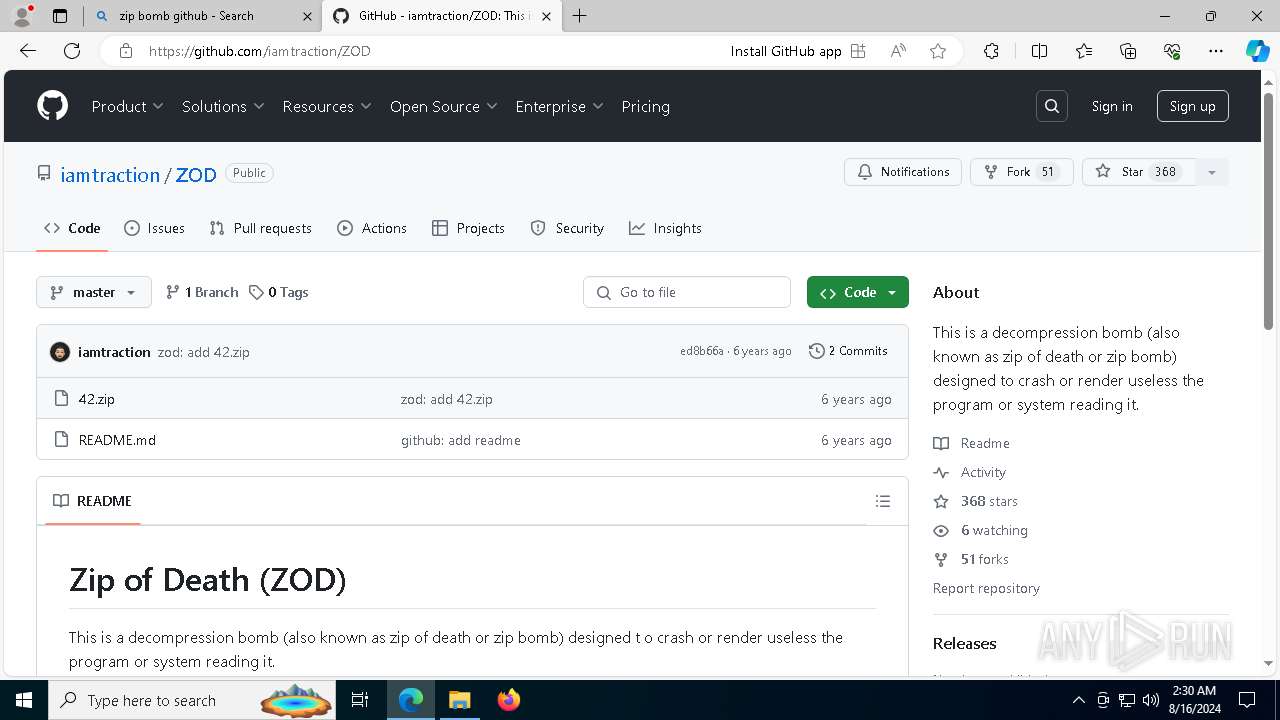
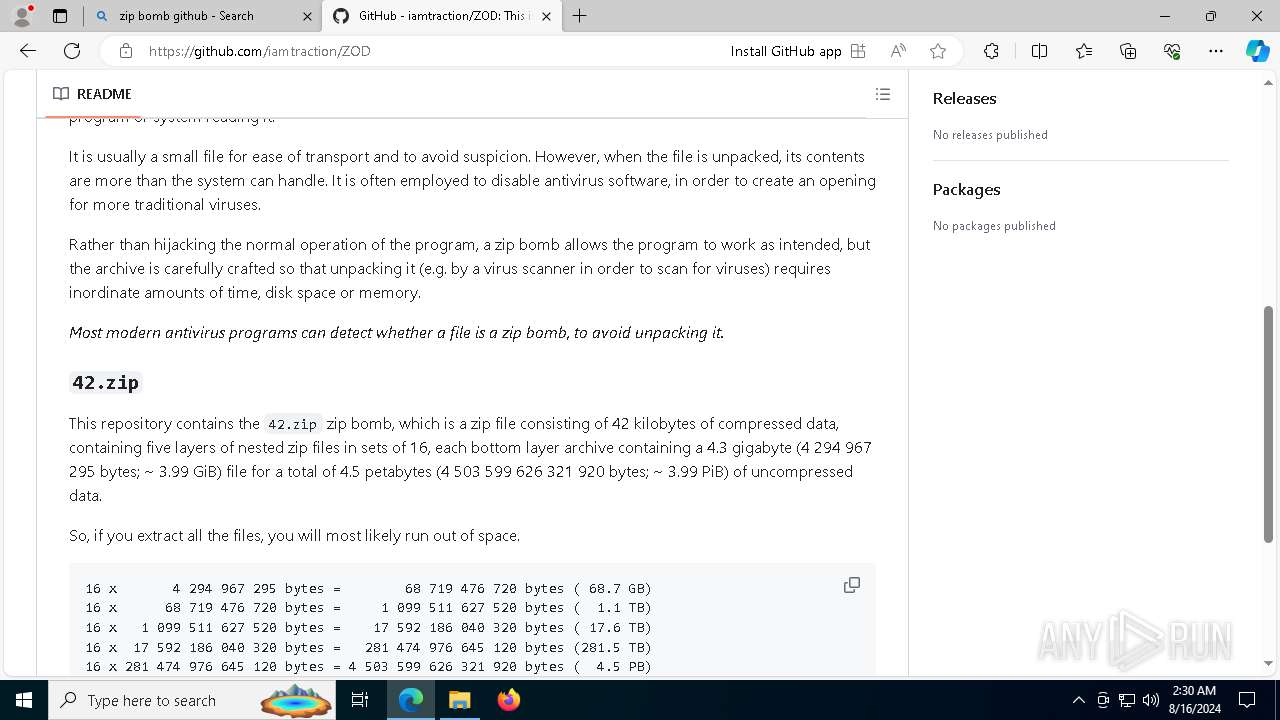
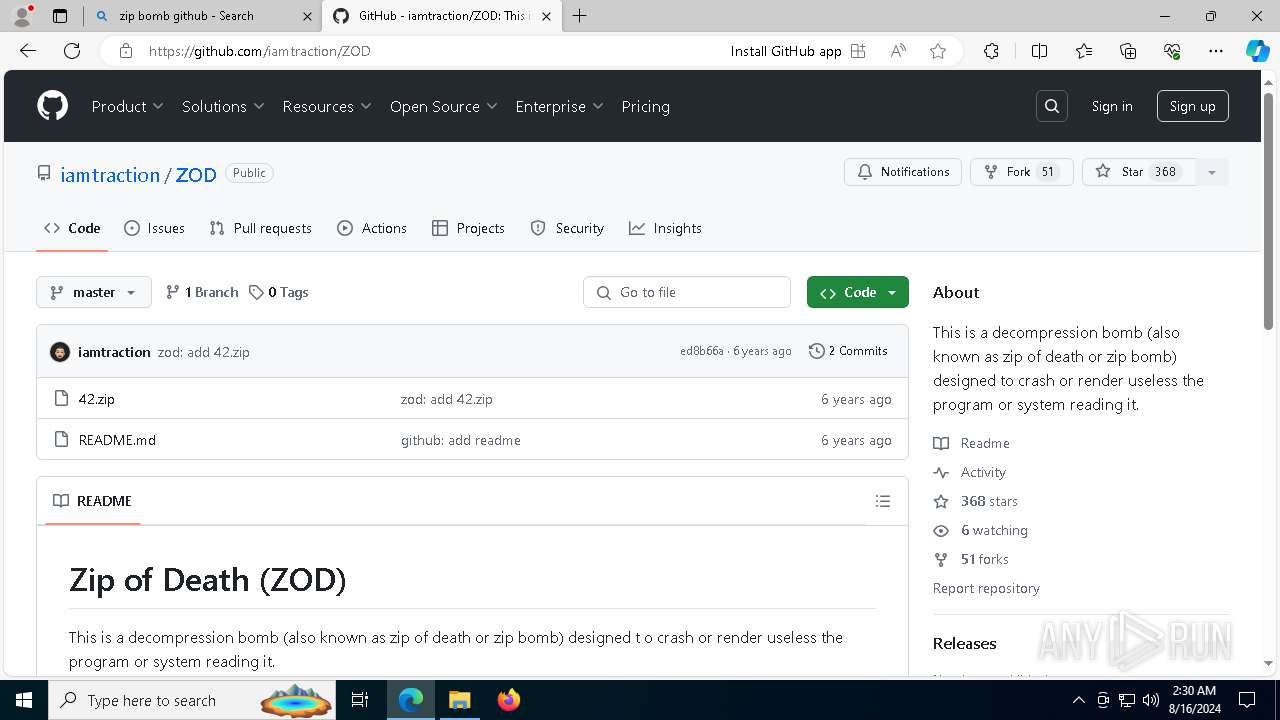
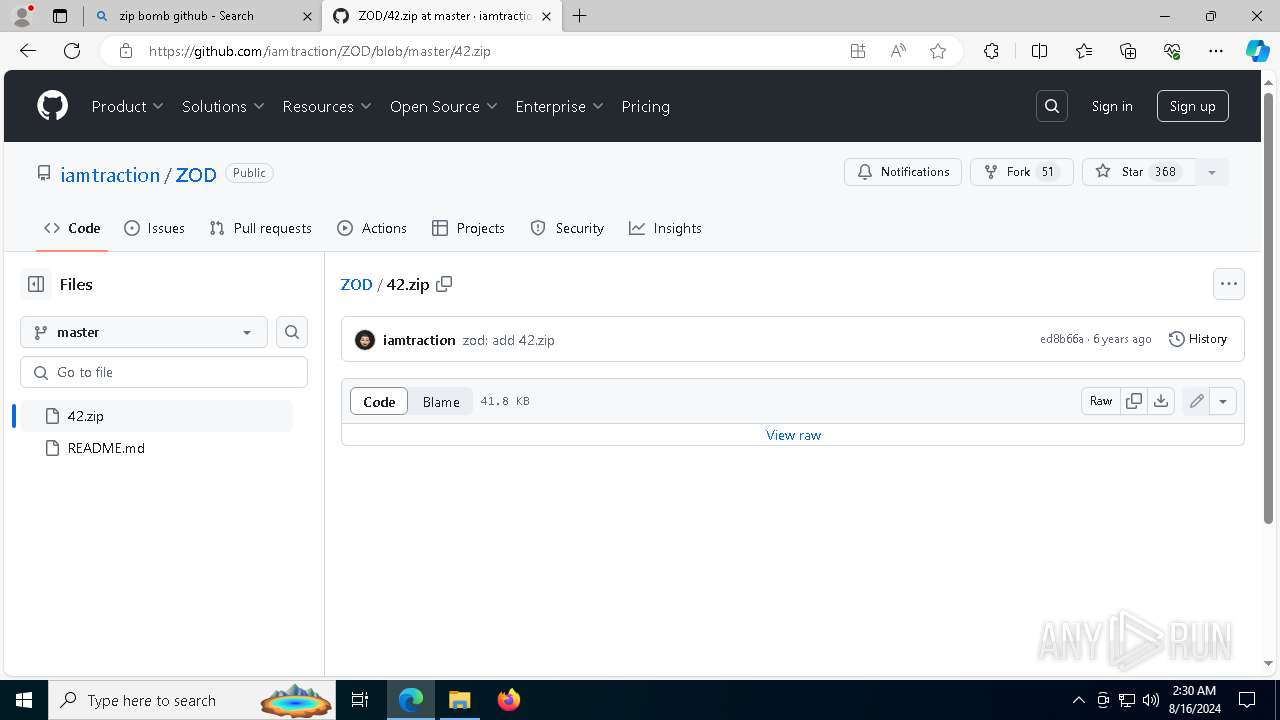
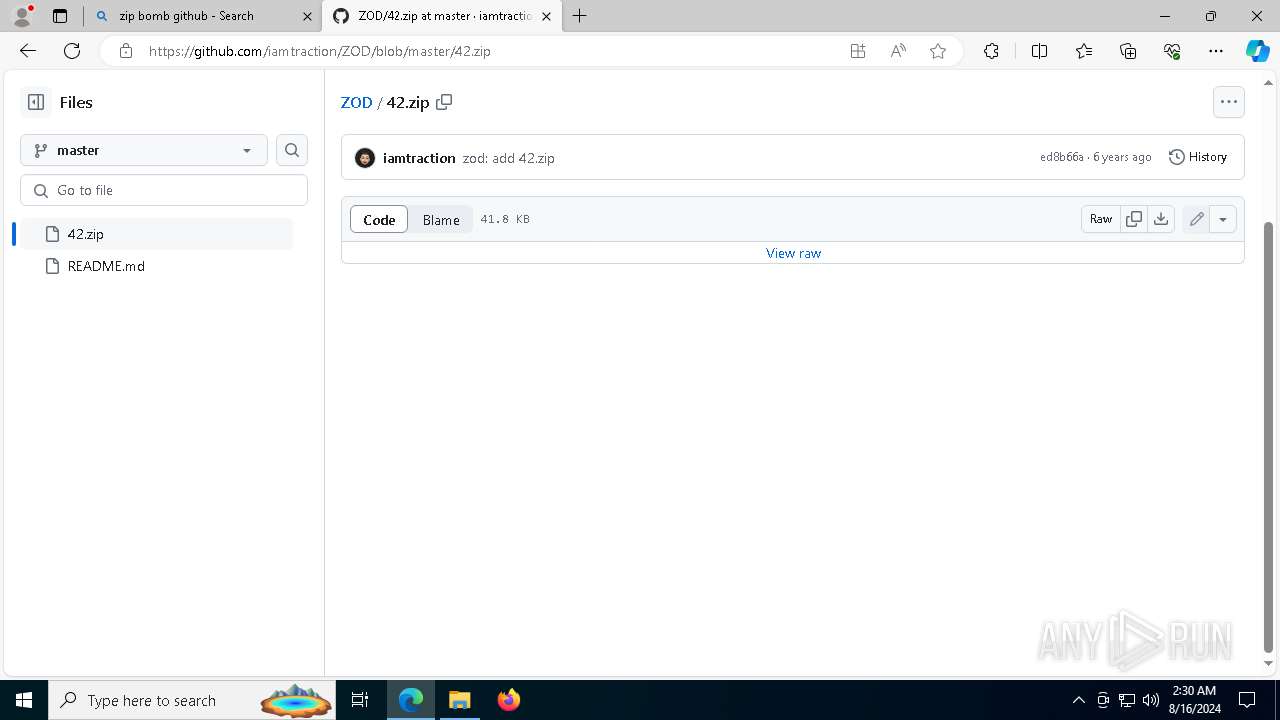
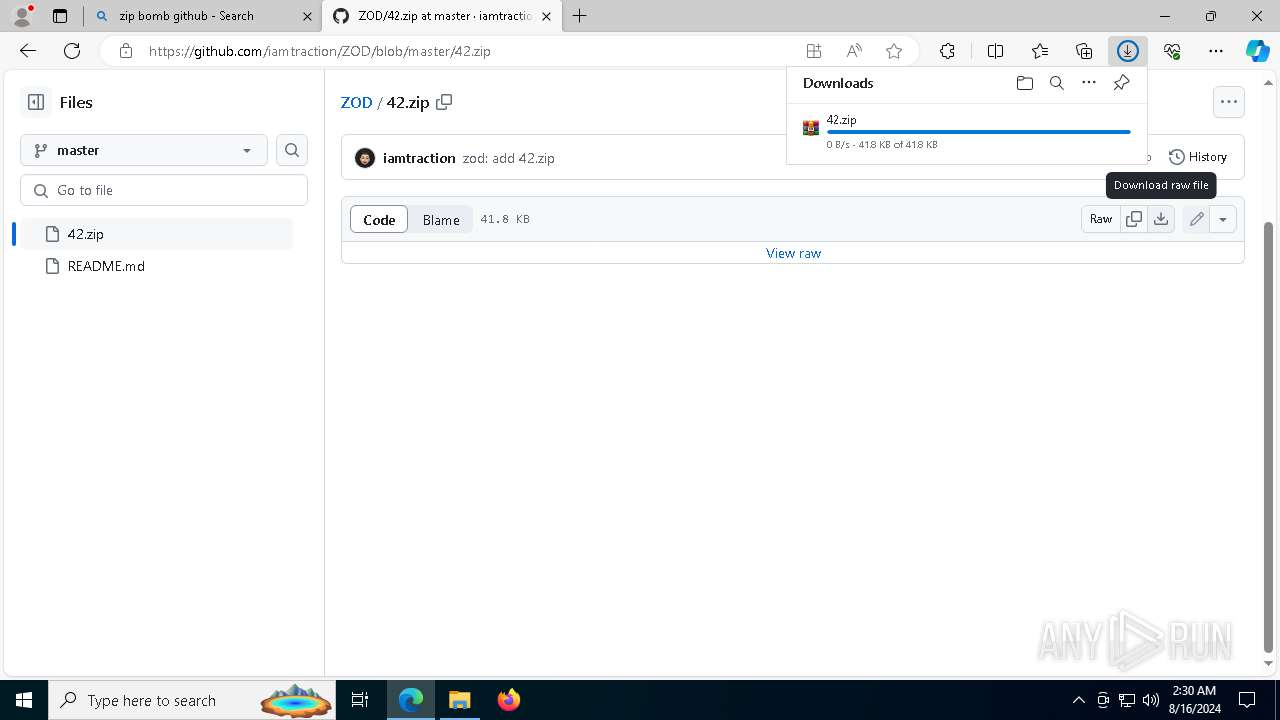
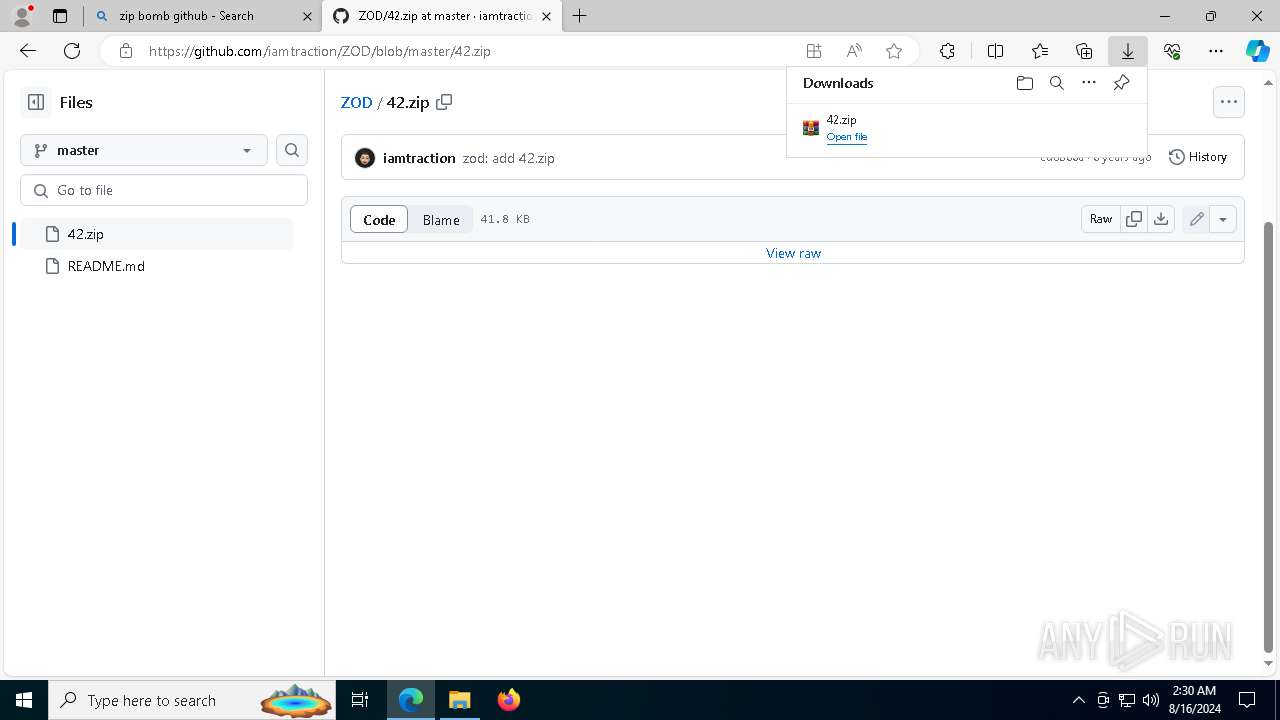
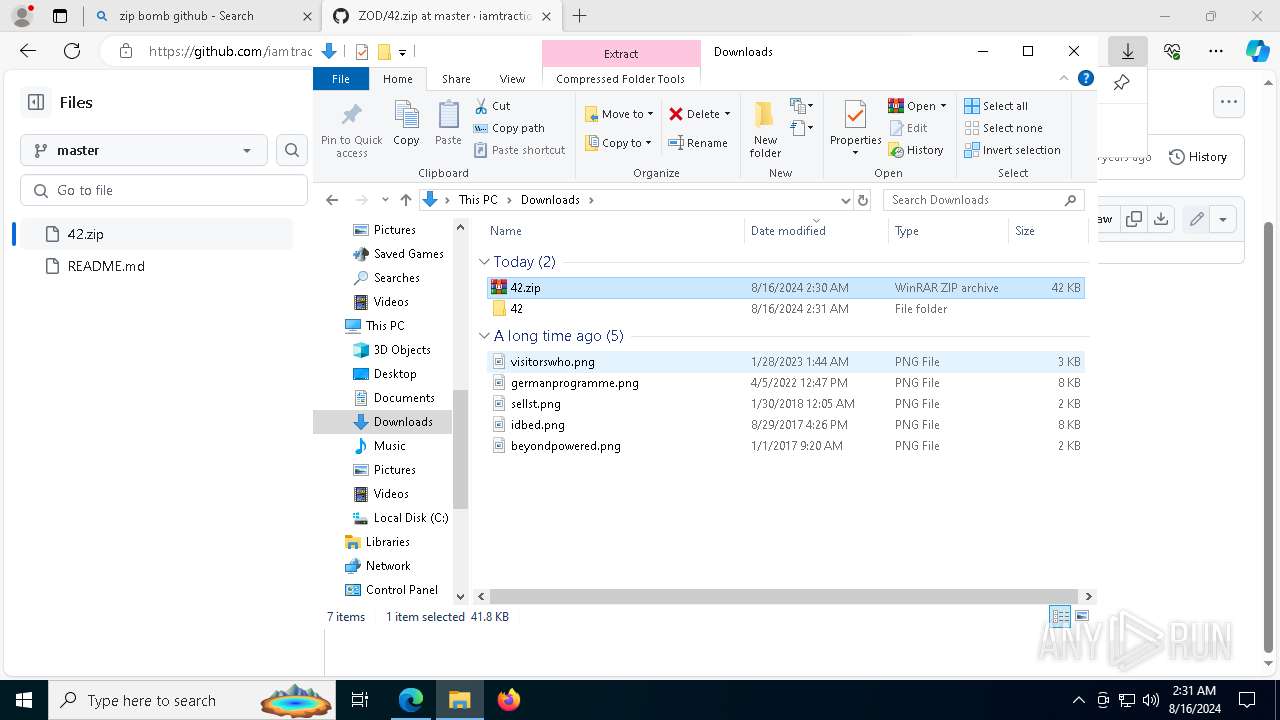
| File name: | 42.zip |
| Full analysis: | https://app.any.run/tasks/46891c25-a71b-4a3f-b1e6-775c5a7fa63e |
| Verdict: | Malicious activity |
| Analysis date: | August 16, 2024, 02:29:14 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| MIME: | application/zip |
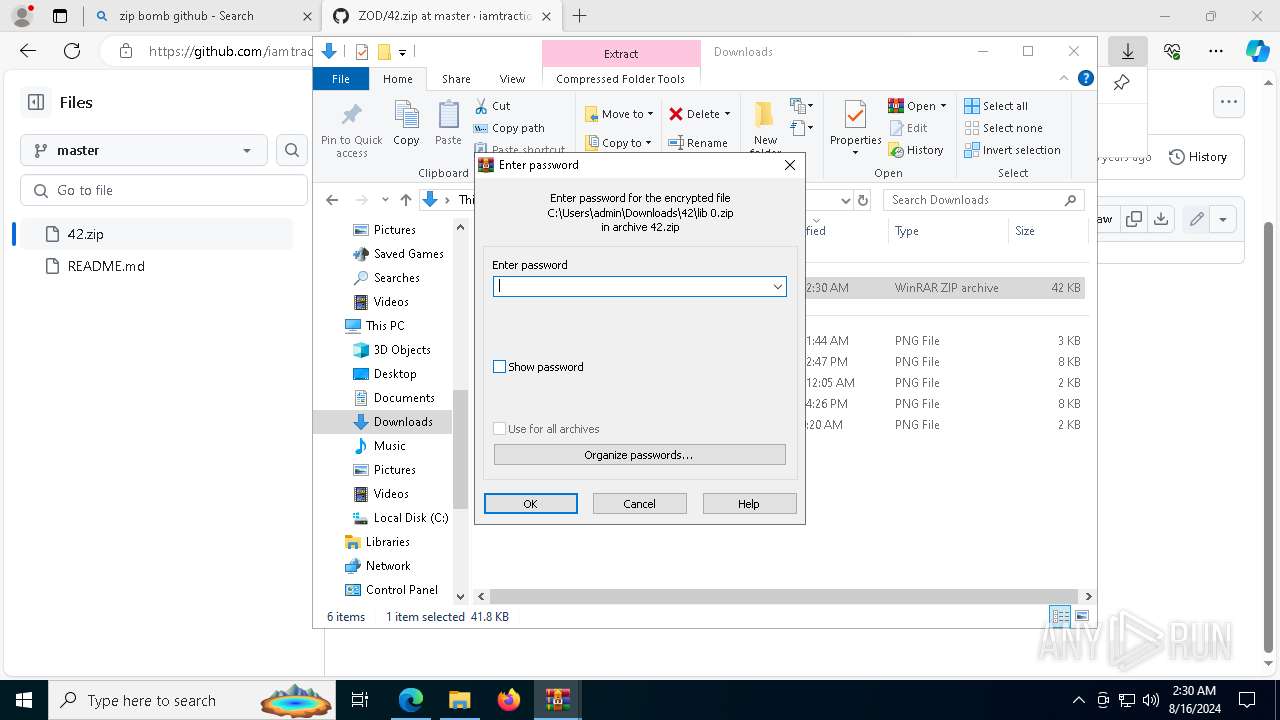
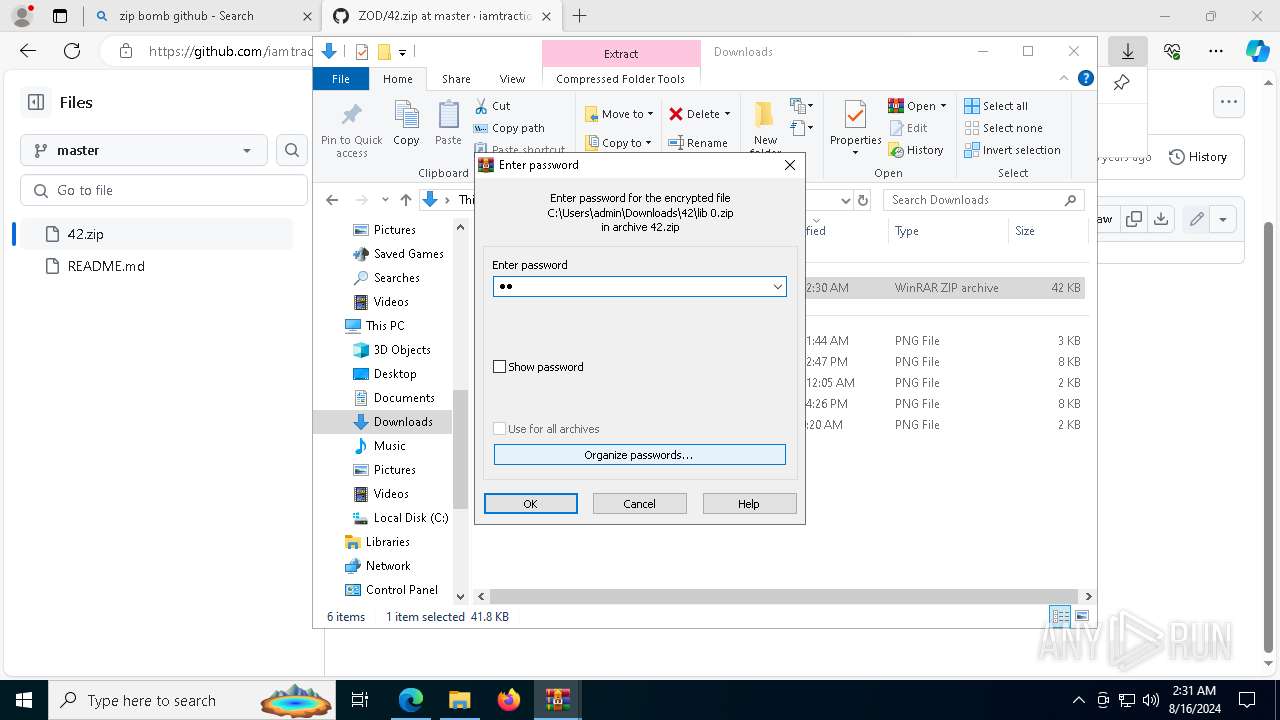
| File info: | Zip archive data, at least v5.1 to extract, compression method=AES Encrypted |
| MD5: | 1DF9A18B18332F153918030B7B516615 |
| SHA1: | 6C42C62696616B72BBFC88A4BE4EAD57AA7BC503 |
| SHA256: | BBD05DE19AA2AF1455C0494639215898A15286D9B05073B6C4817FE24B2C36FA |
| SSDEEP: | 768:hzyVr8GSKL6O3QOXk/0u3wqOghrFCezL1VFJdbq2QTJTw02Q:hGx8DKXE//ZhhCirFi2cwK |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Checks supported languages
- TextInputHost.exe (PID: 6200)
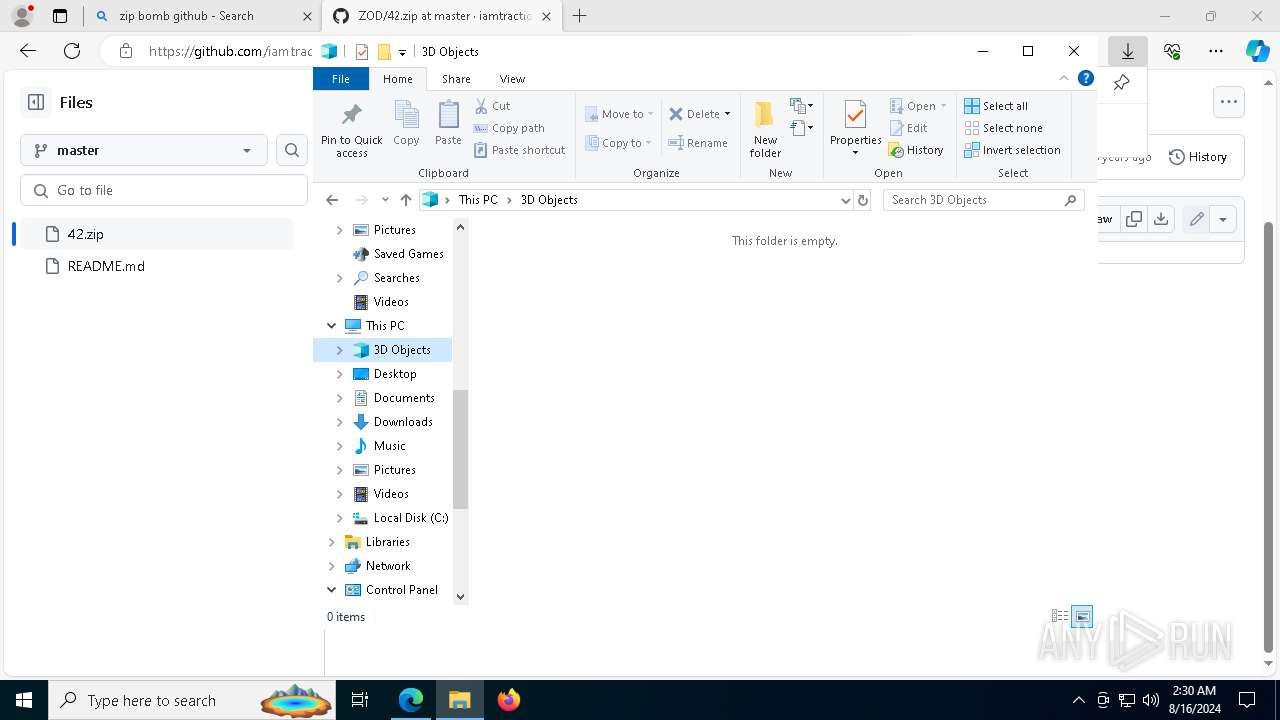
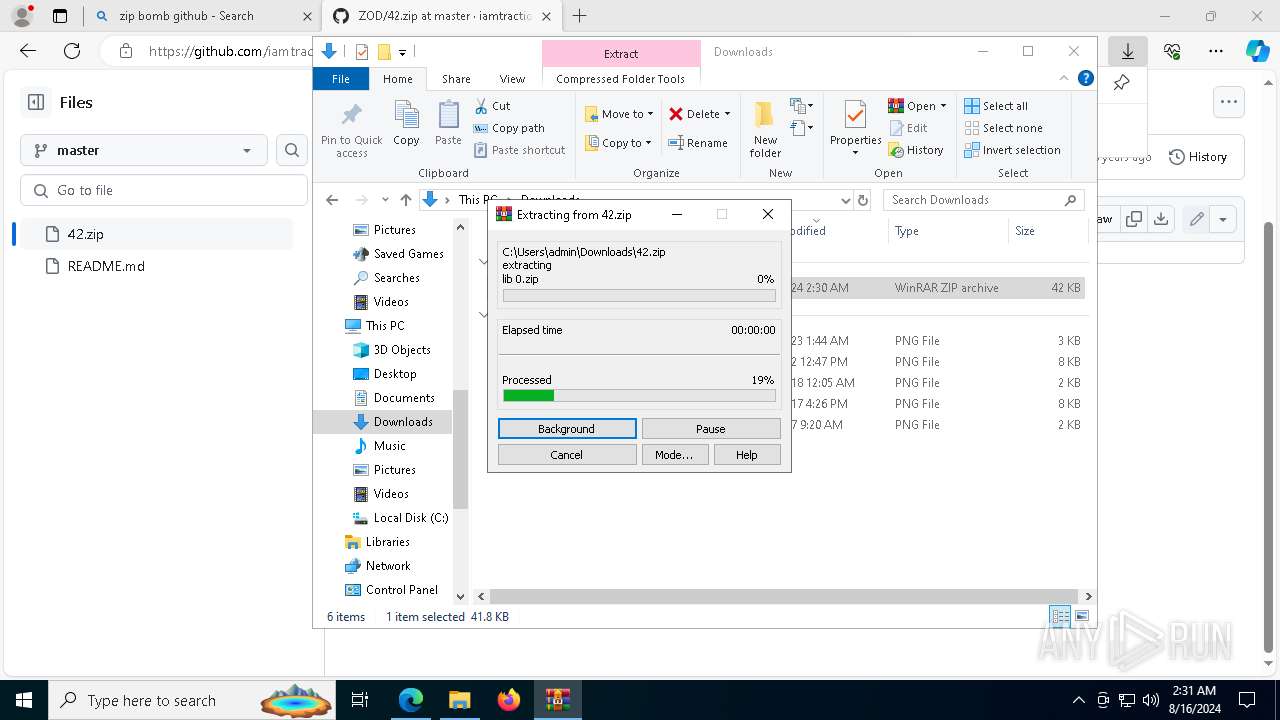
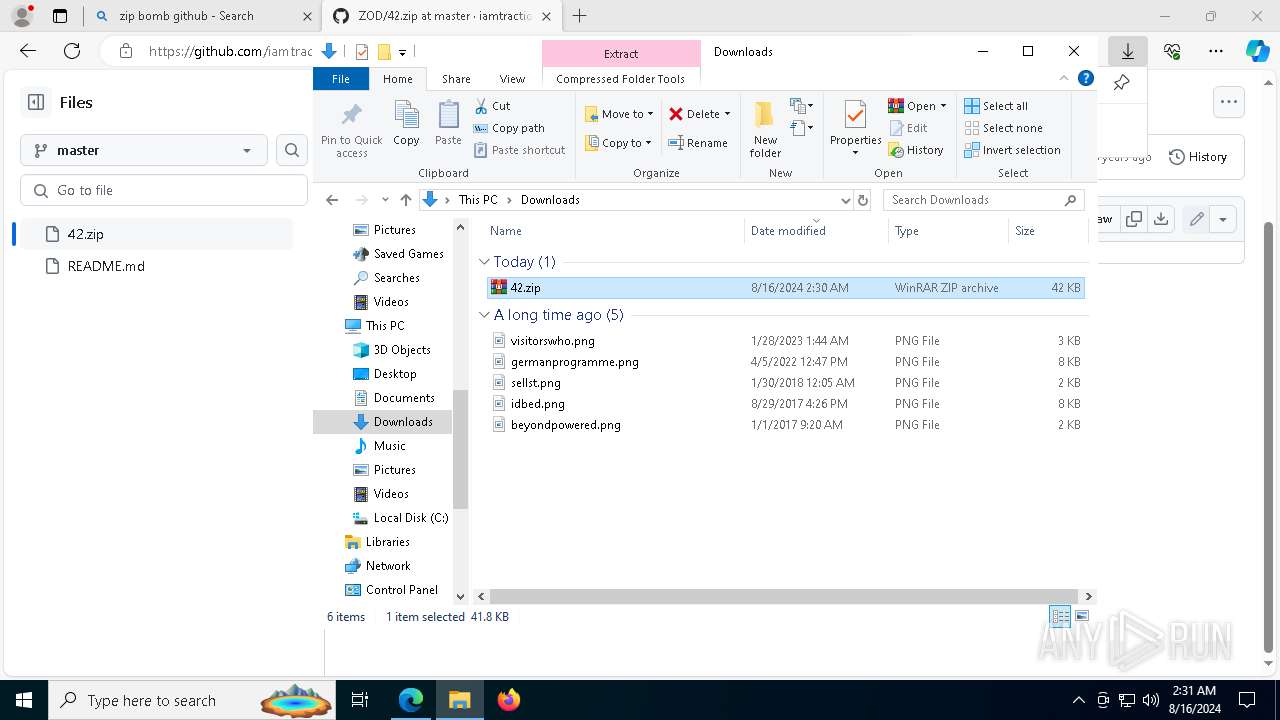
Manual execution by a user
- WinRAR.exe (PID: 7304)
- WinRAR.exe (PID: 8088)
Reads the computer name
- TextInputHost.exe (PID: 6200)
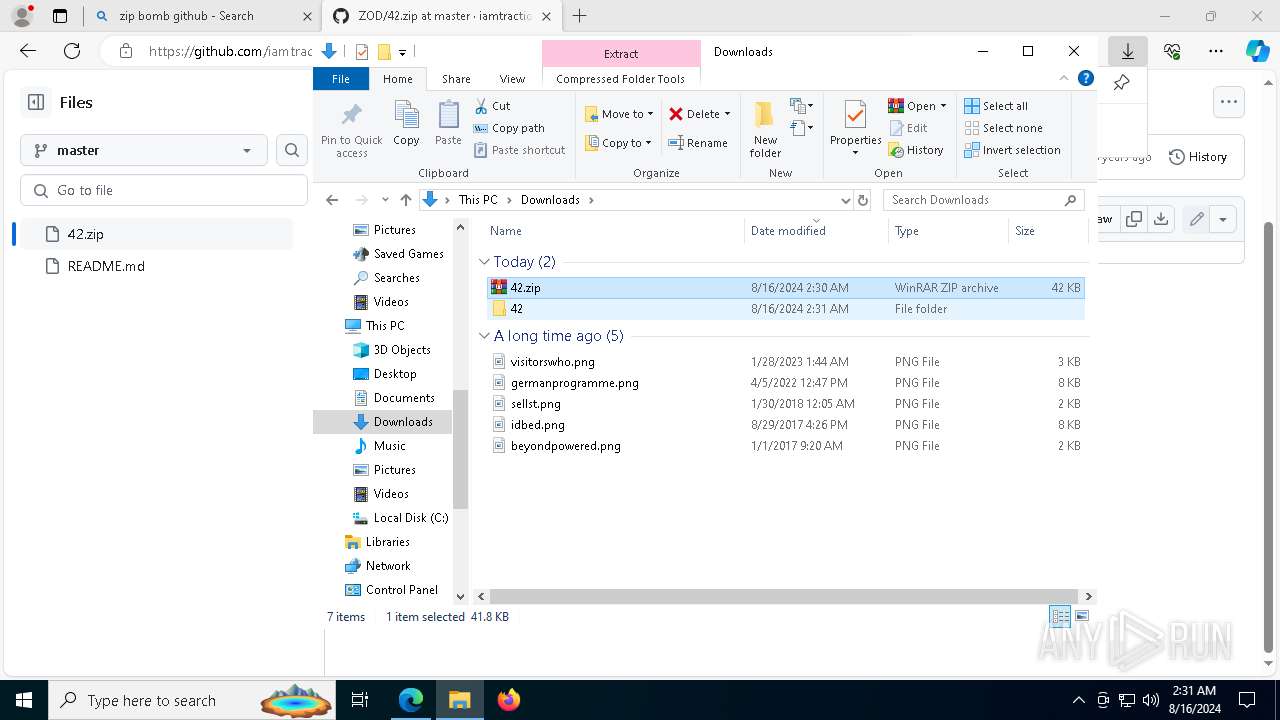
The process uses the downloaded file
- WinRAR.exe (PID: 7304)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
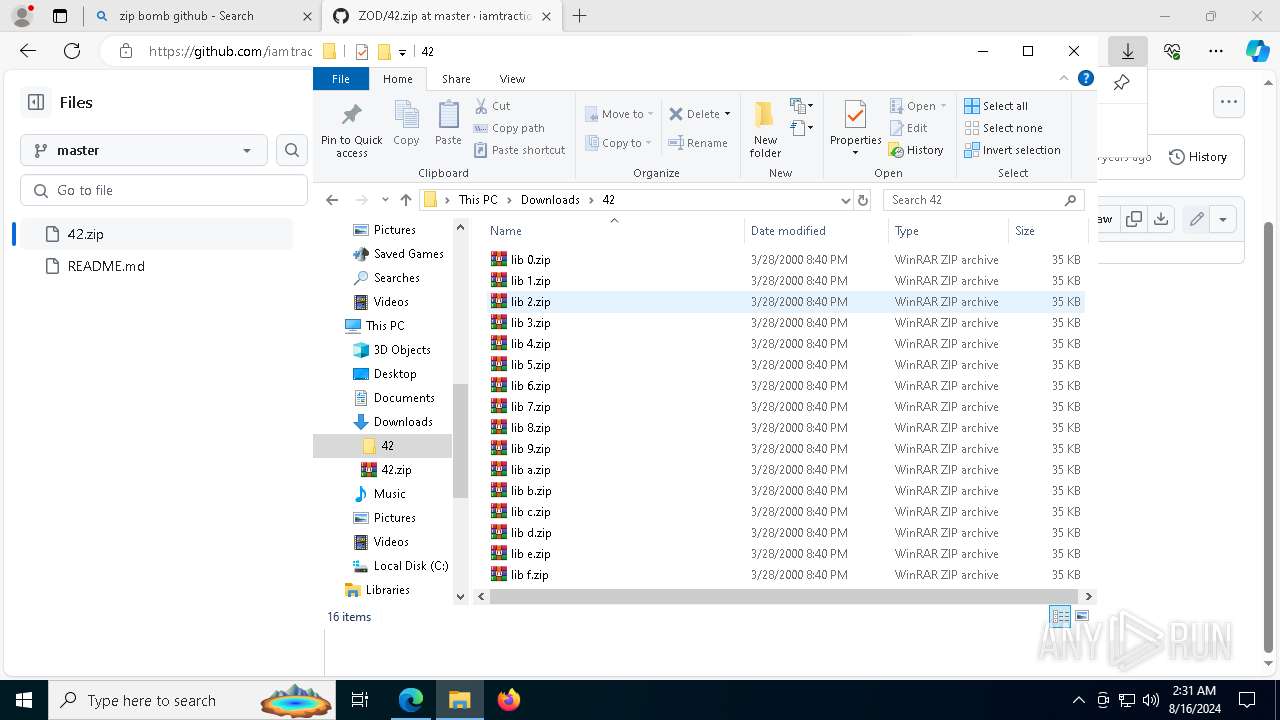
| ZipRequiredVersion: | 51 |
|---|---|
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2000:03:28 21:40:54 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | 2524 |
| ZipUncompressedSize: | 34902 |
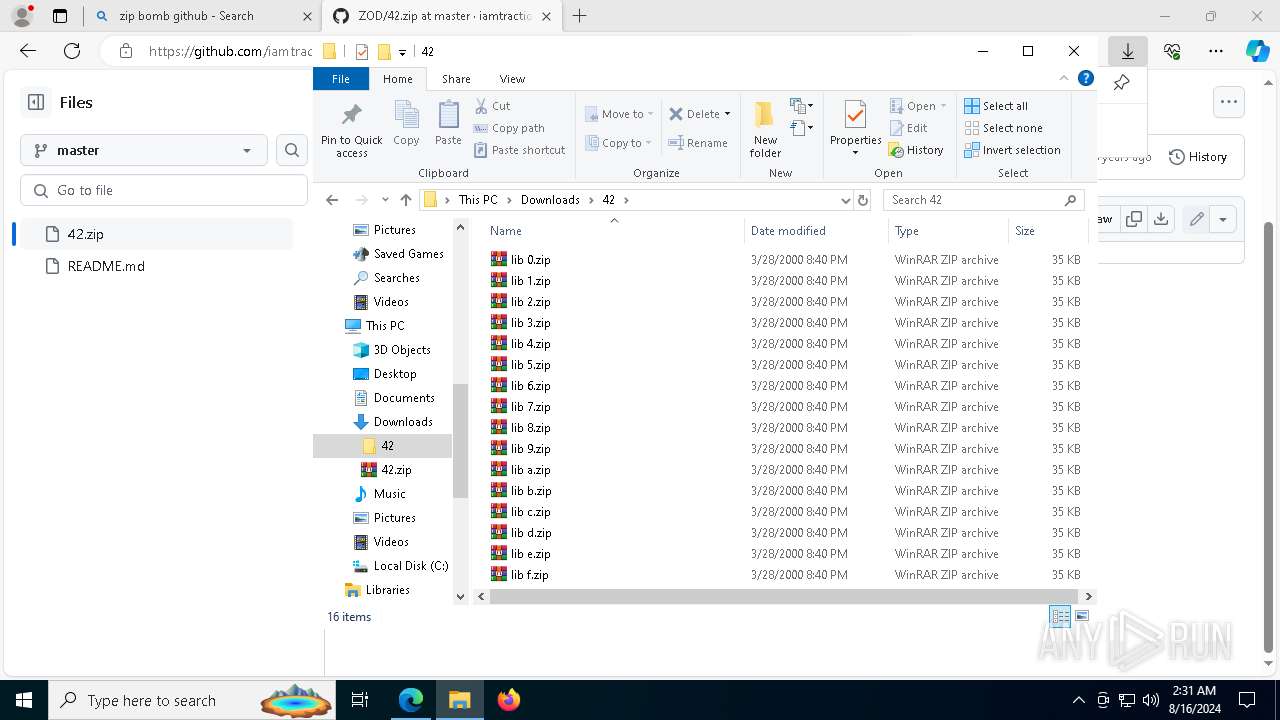
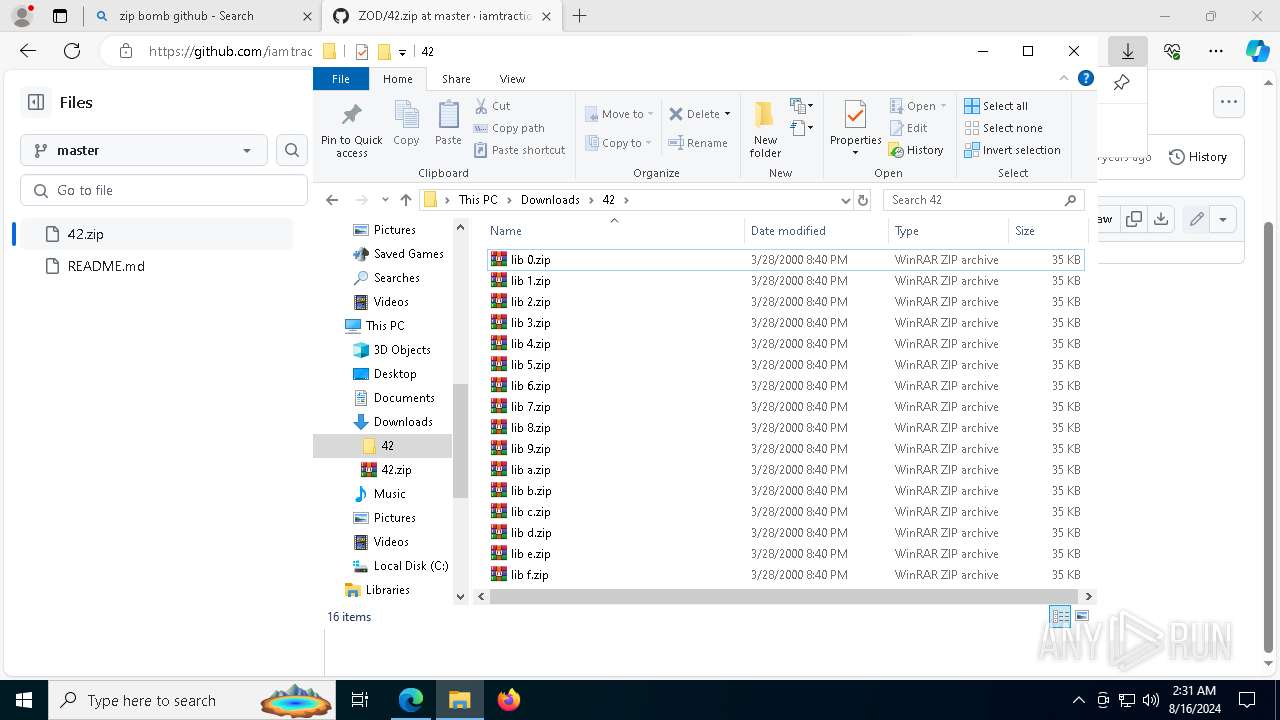
| ZipFileName: | lib 0.zip |
Total processes
197
Monitored processes
5
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 6200 | "C:\WINDOWS\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe" -ServerName:InputApp.AppXjd5de1g66v206tj52m9d0dtpppx4cgpn.mca | C:\Windows\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Version: 123.26505.0.0 Modules
| |||||||||||||||
| 6384 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\42.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 6712 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
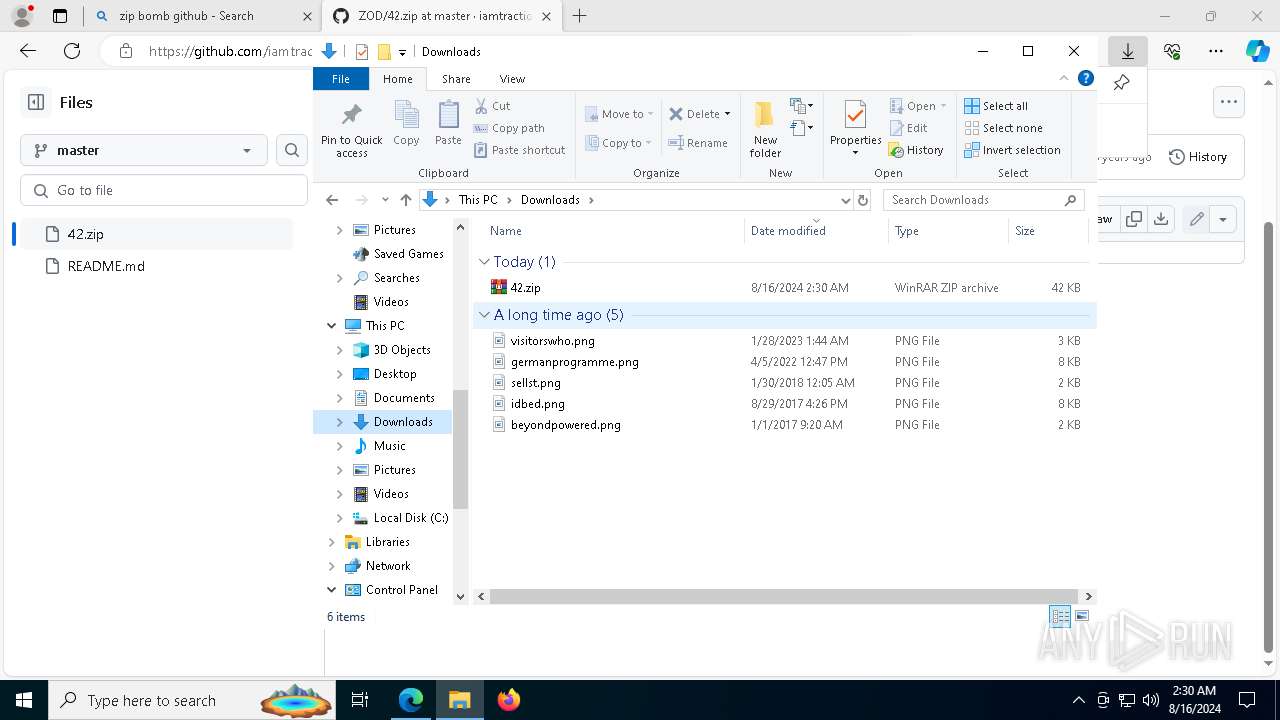
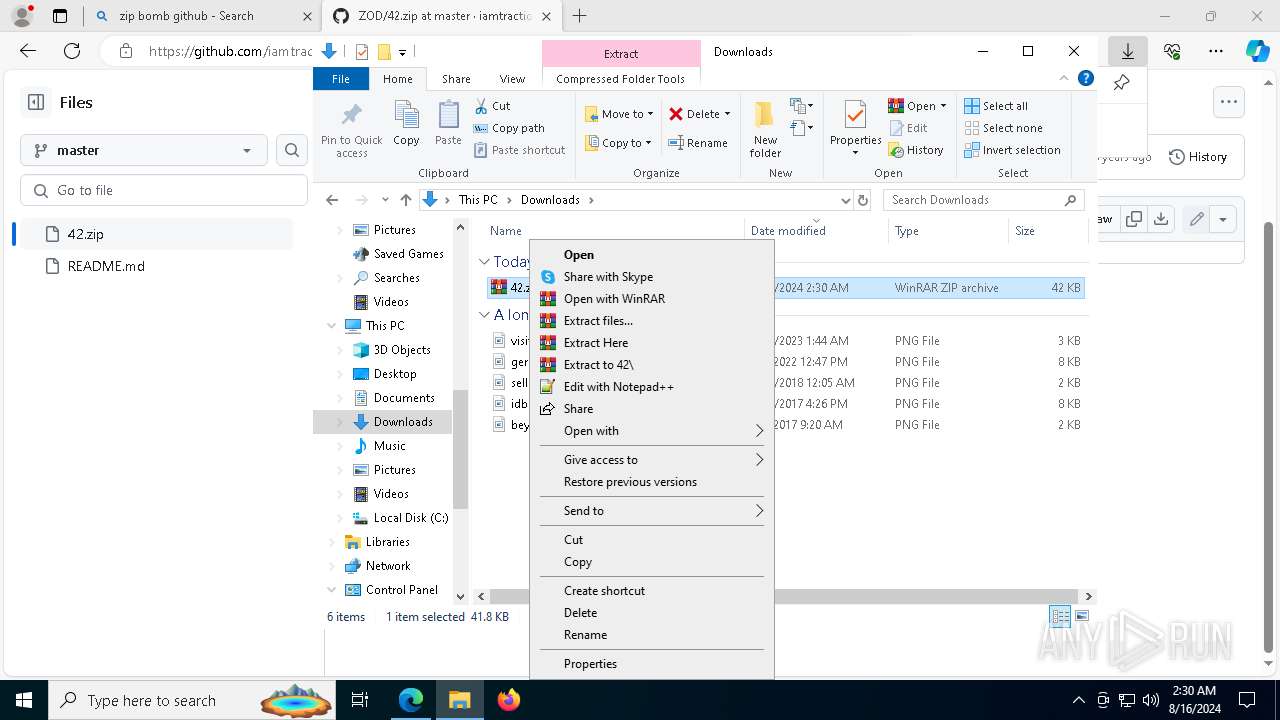
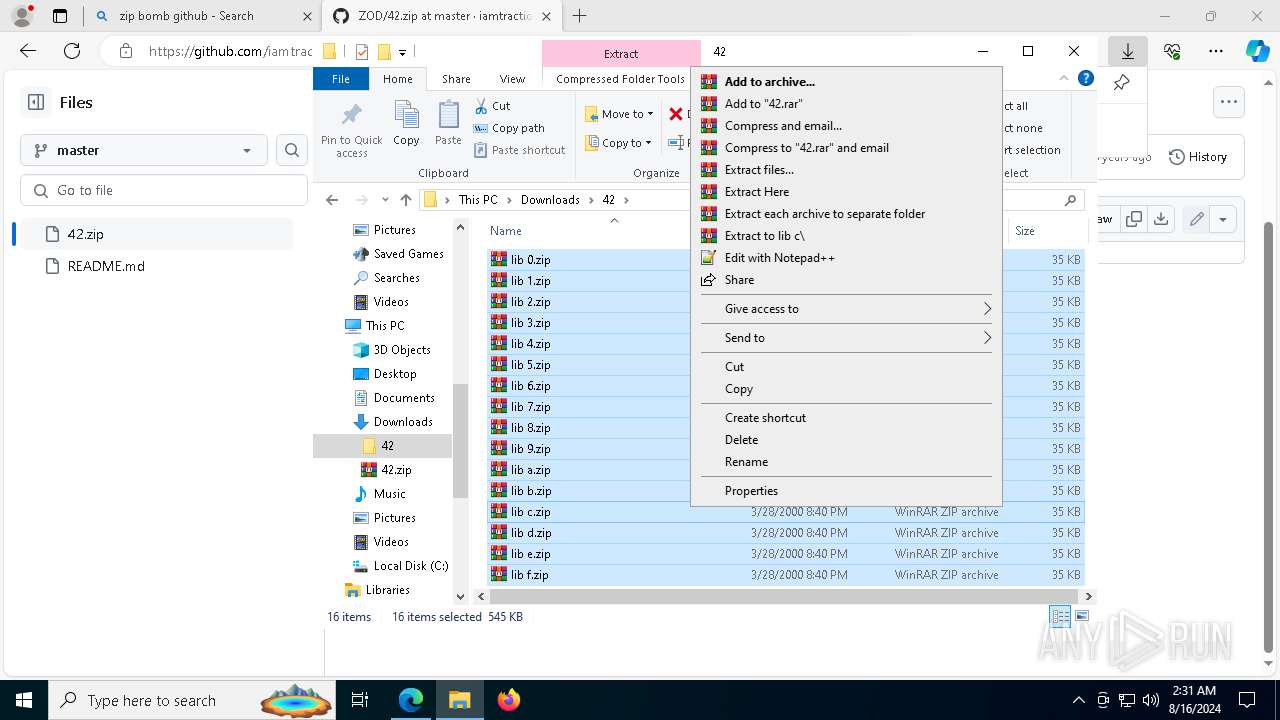
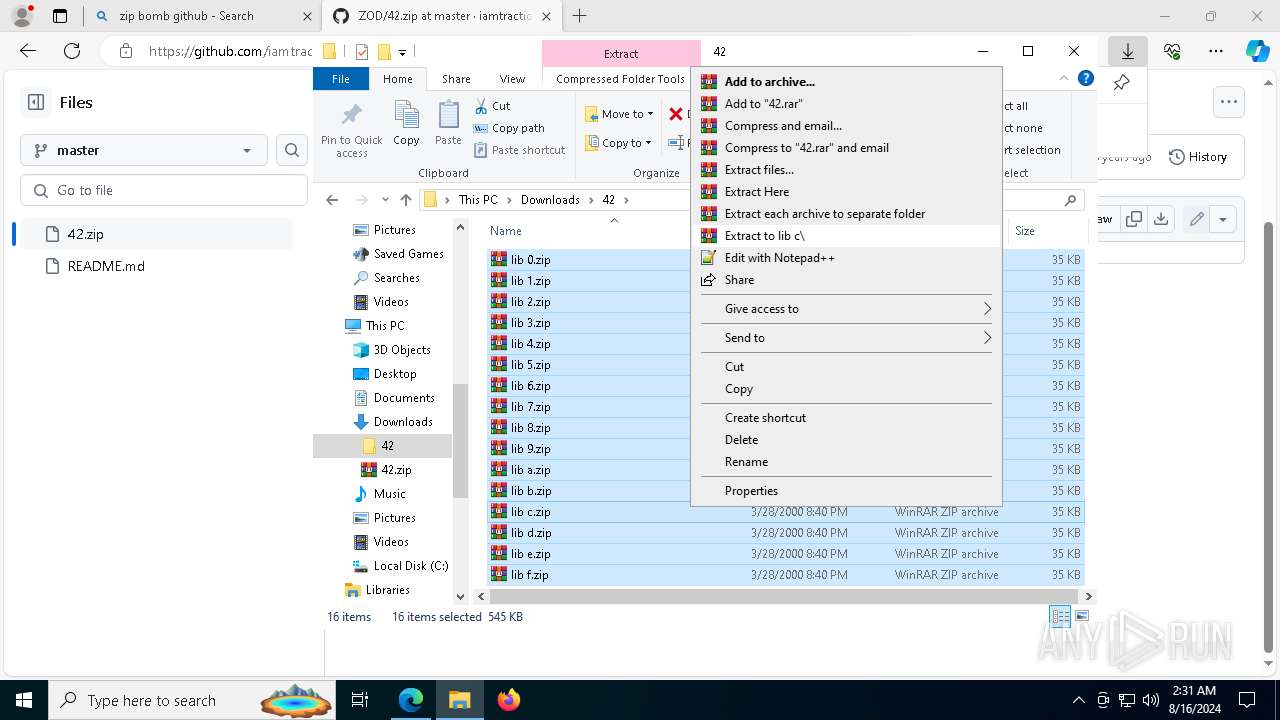
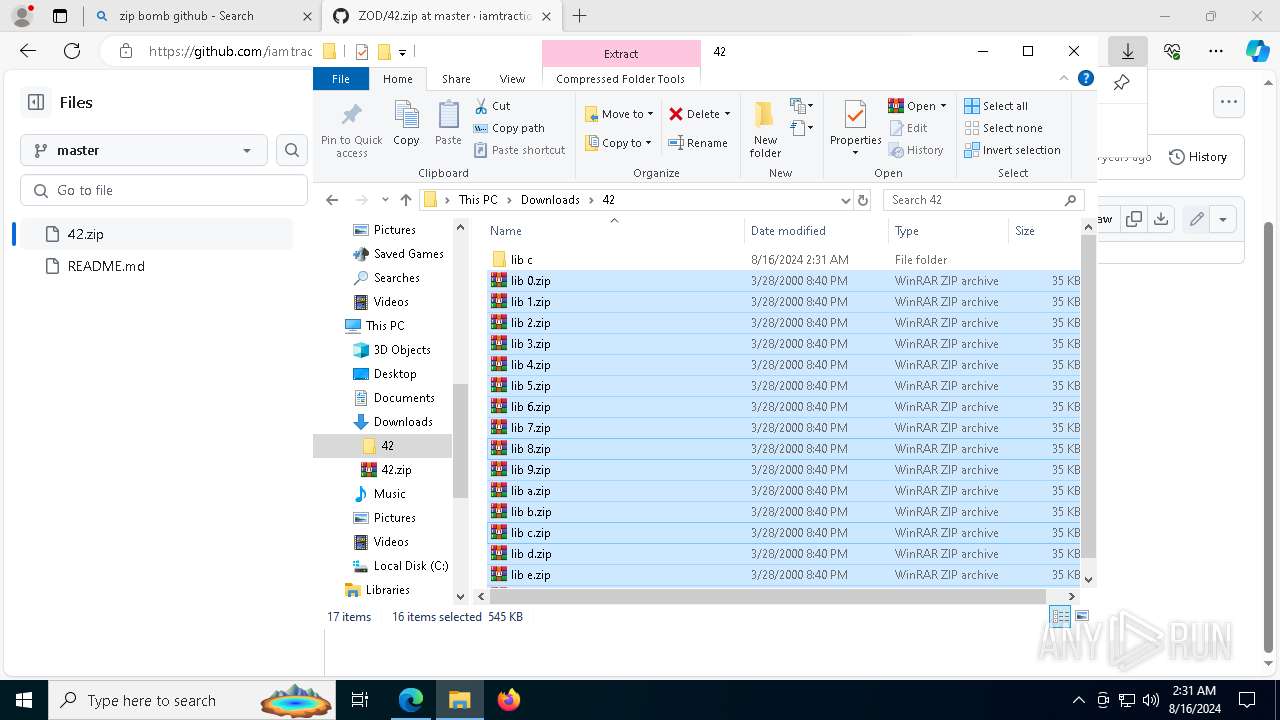
| 7304 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Downloads\42.zip" C:\Users\admin\Downloads\42\ | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
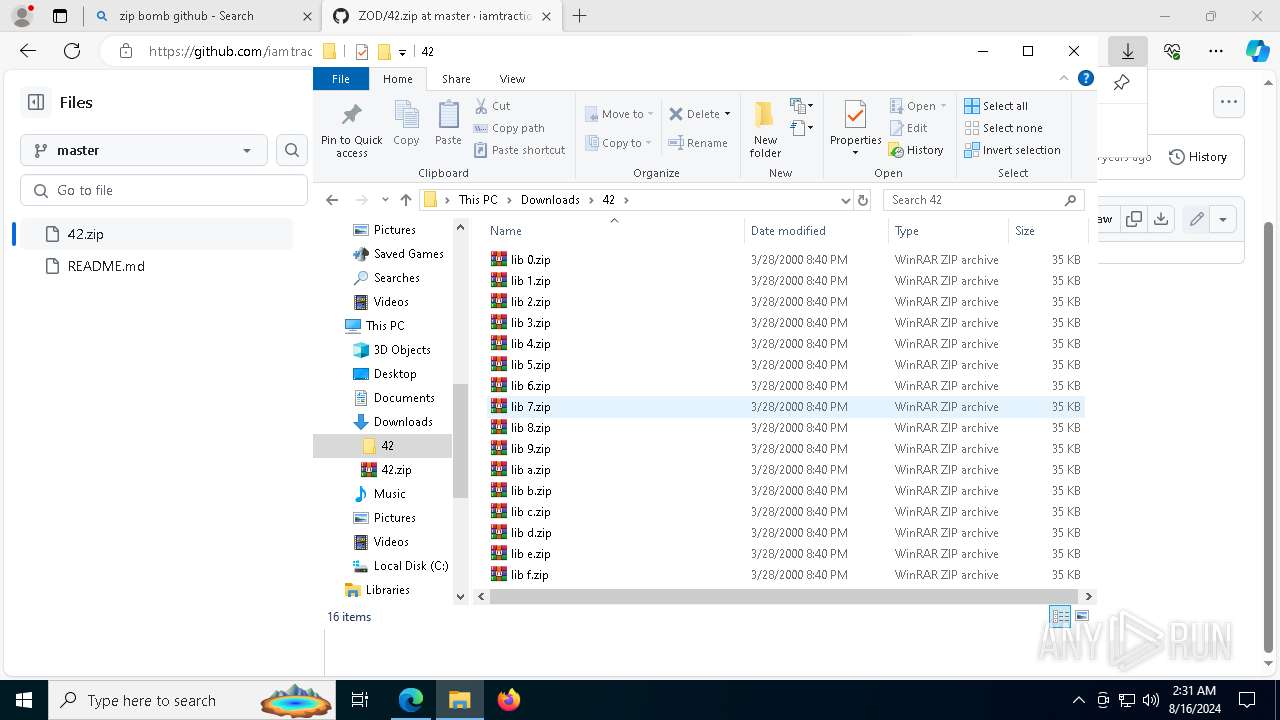
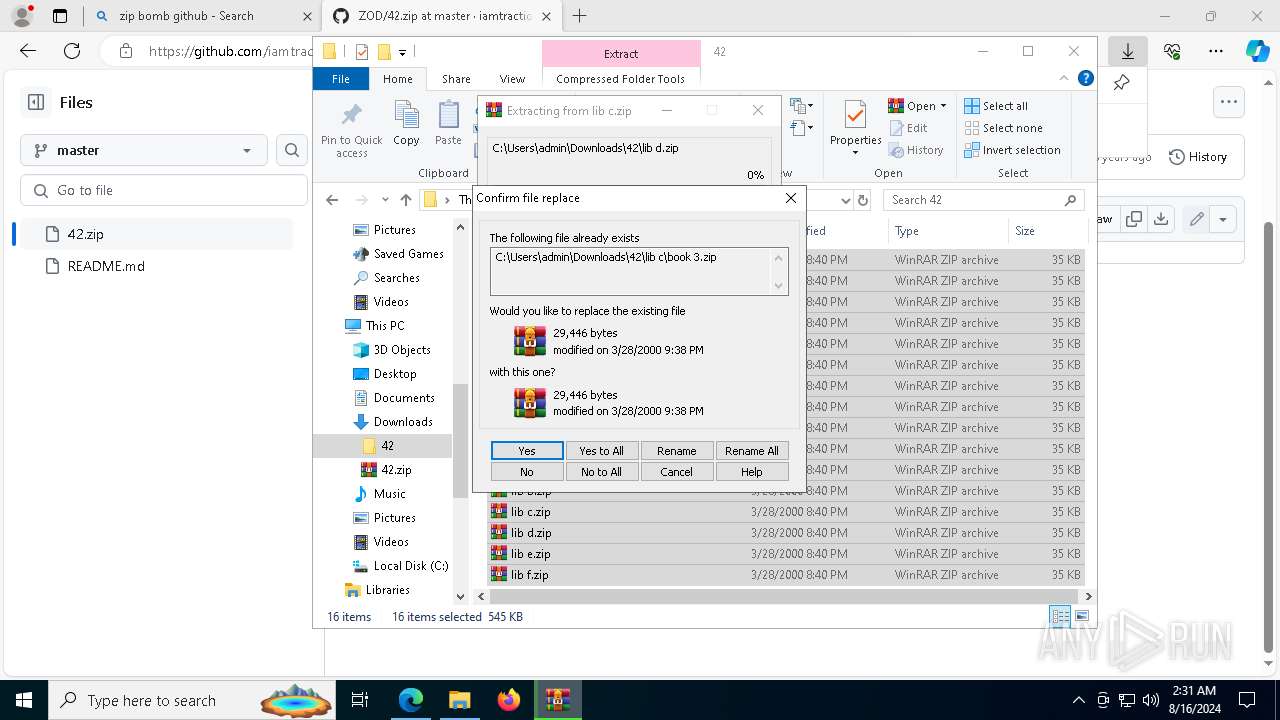
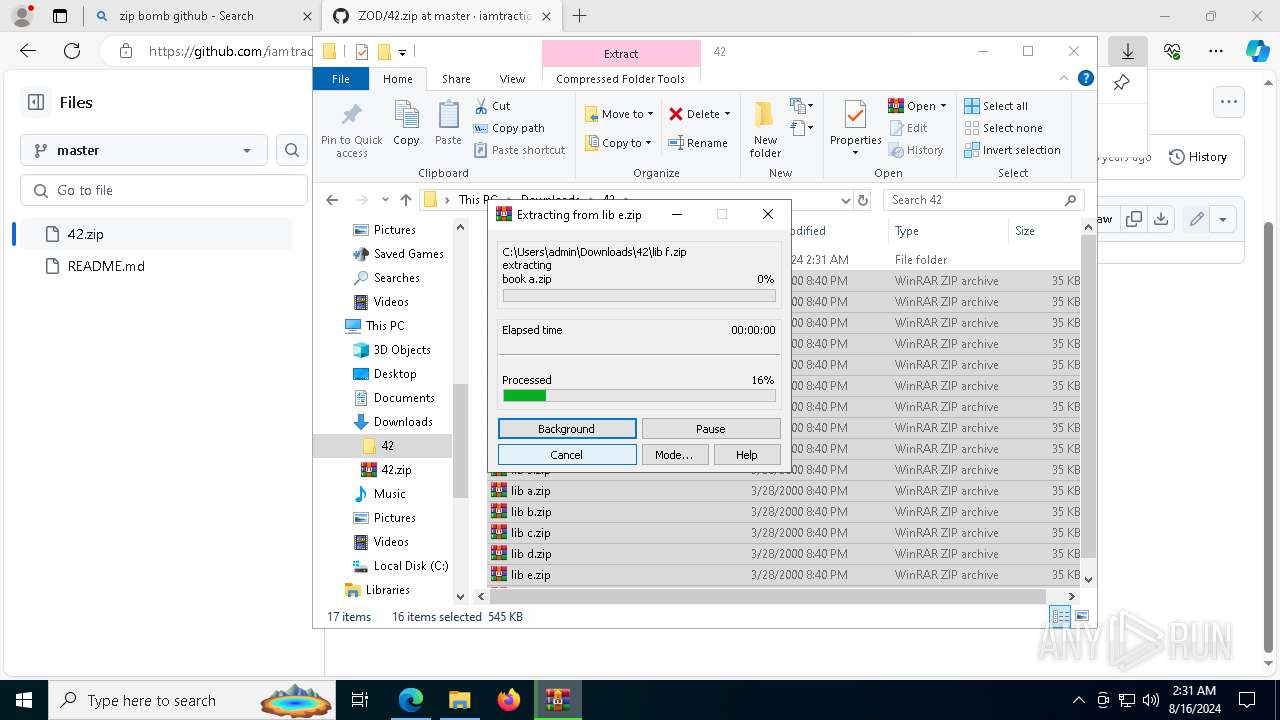
| 8088 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver "-anf=C:\Users\admin\AppData\Local\Temp\Rar$LS4552.31474" -scul -- "C:\Users\admin\Downloads\42\lib b.zip" "C:\Users\admin\Downloads\42\lib c\" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
Total events
7 458
Read events
7 426
Write events
32
Delete events
0
Modification events
| (PID) Process: | (6384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (6384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (6384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (6384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\42.zip | |||
| (PID) Process: | (6384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000200000003000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
| (PID) Process: | (6384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\General |
| Operation: | write | Name: | LastFolder |
Value: C:\Users\admin\AppData\Local\Temp | |||
Executable files
0
Suspicious files
32
Text files
0
Unknown types
0
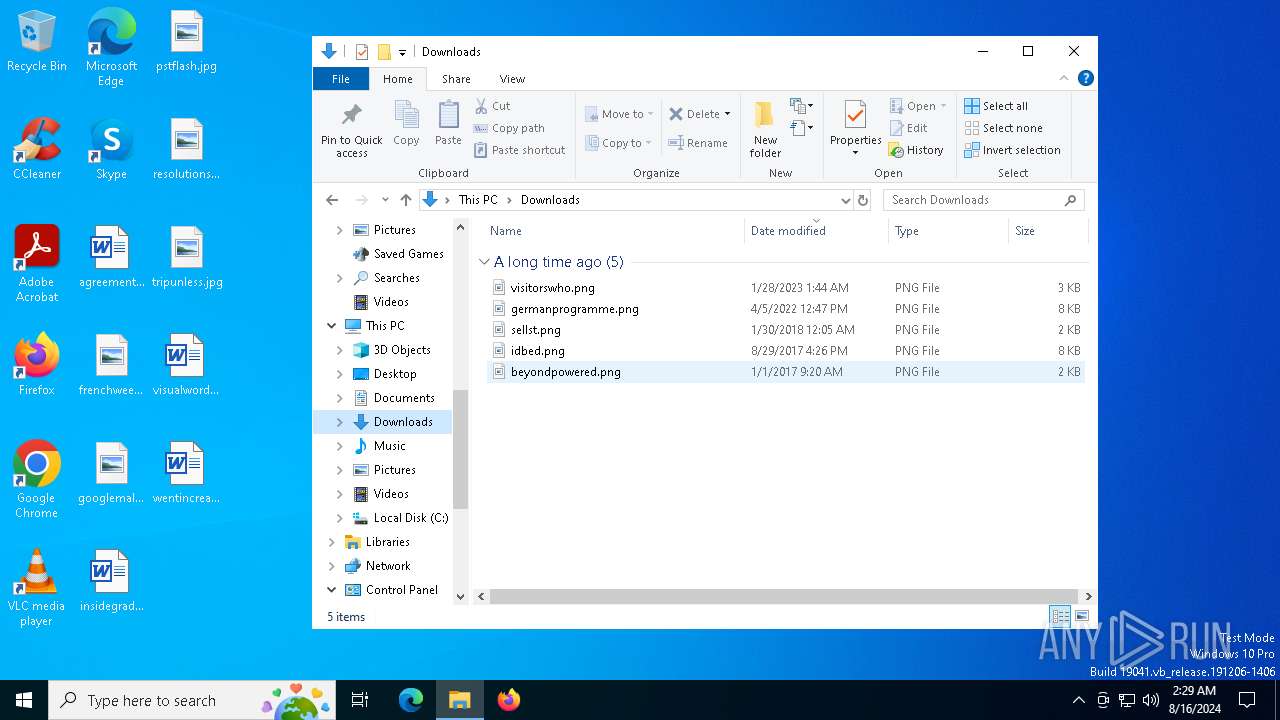
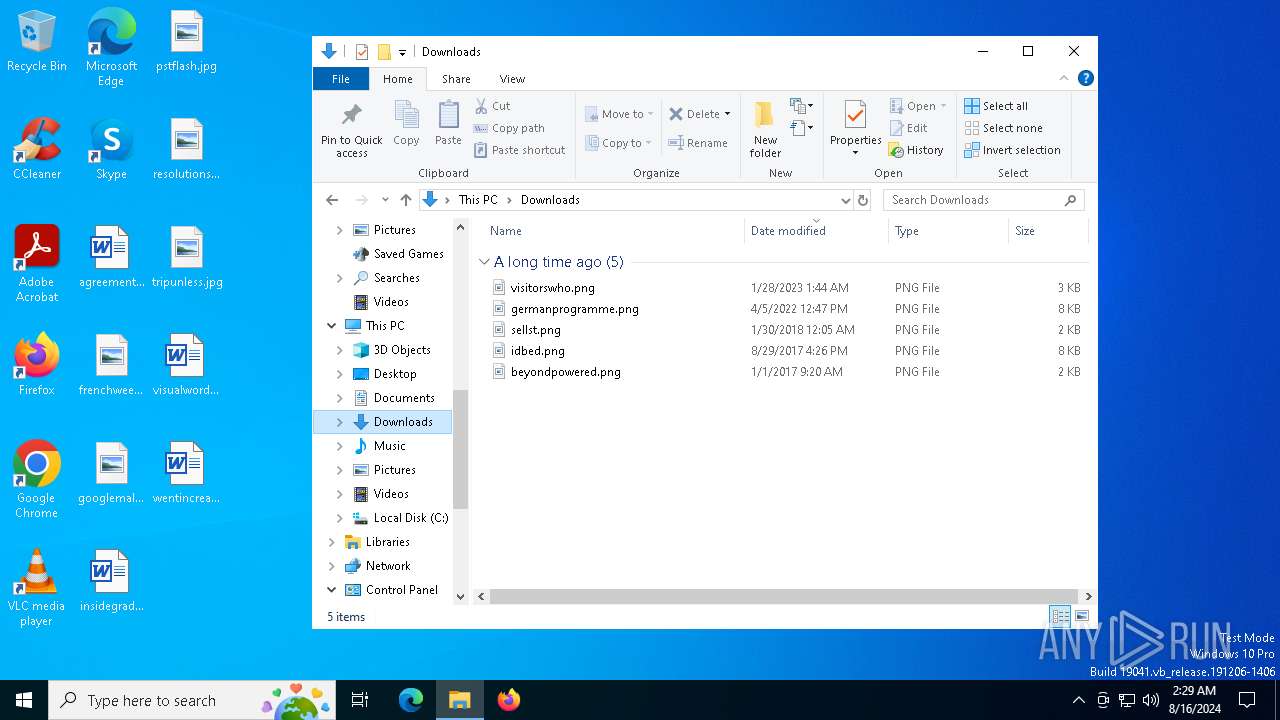
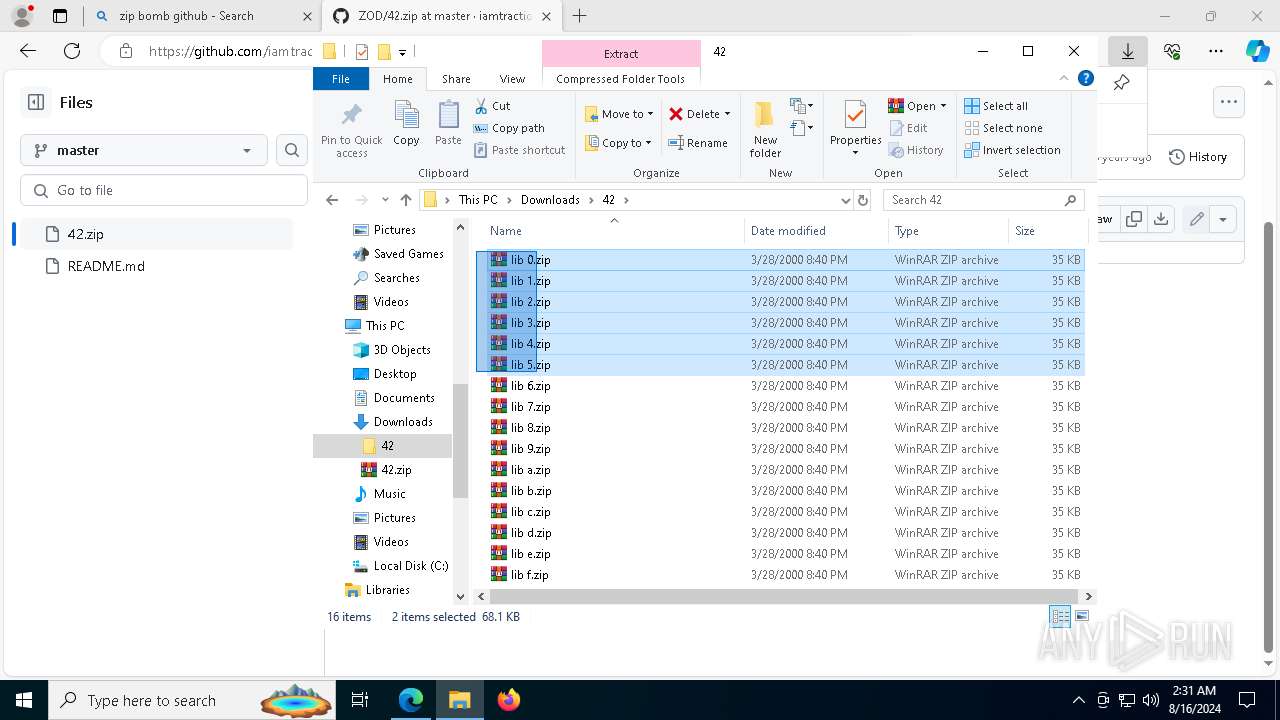
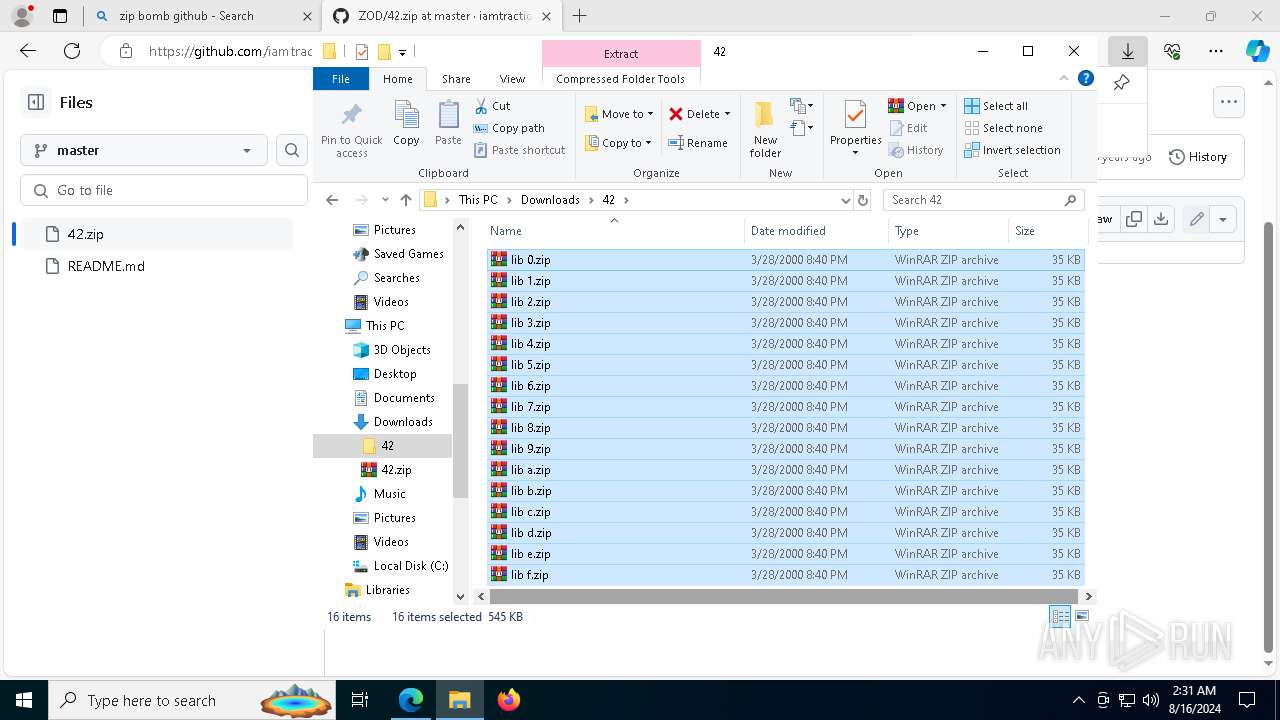
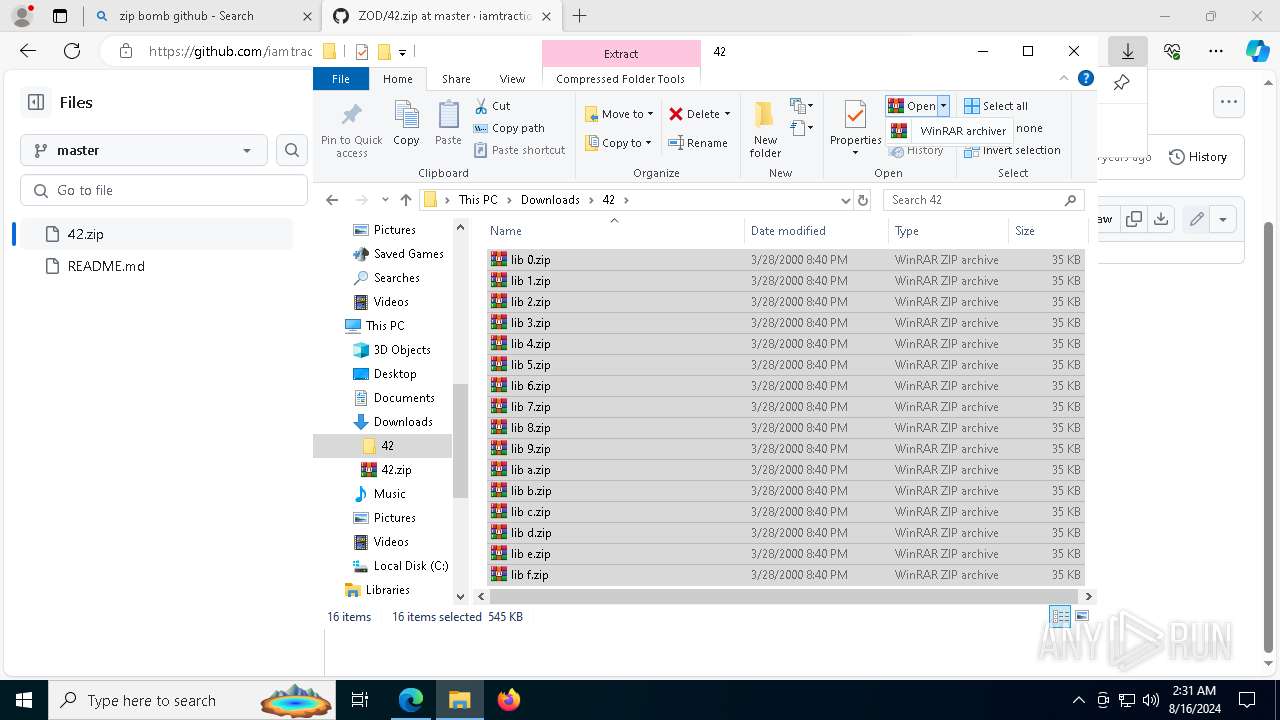
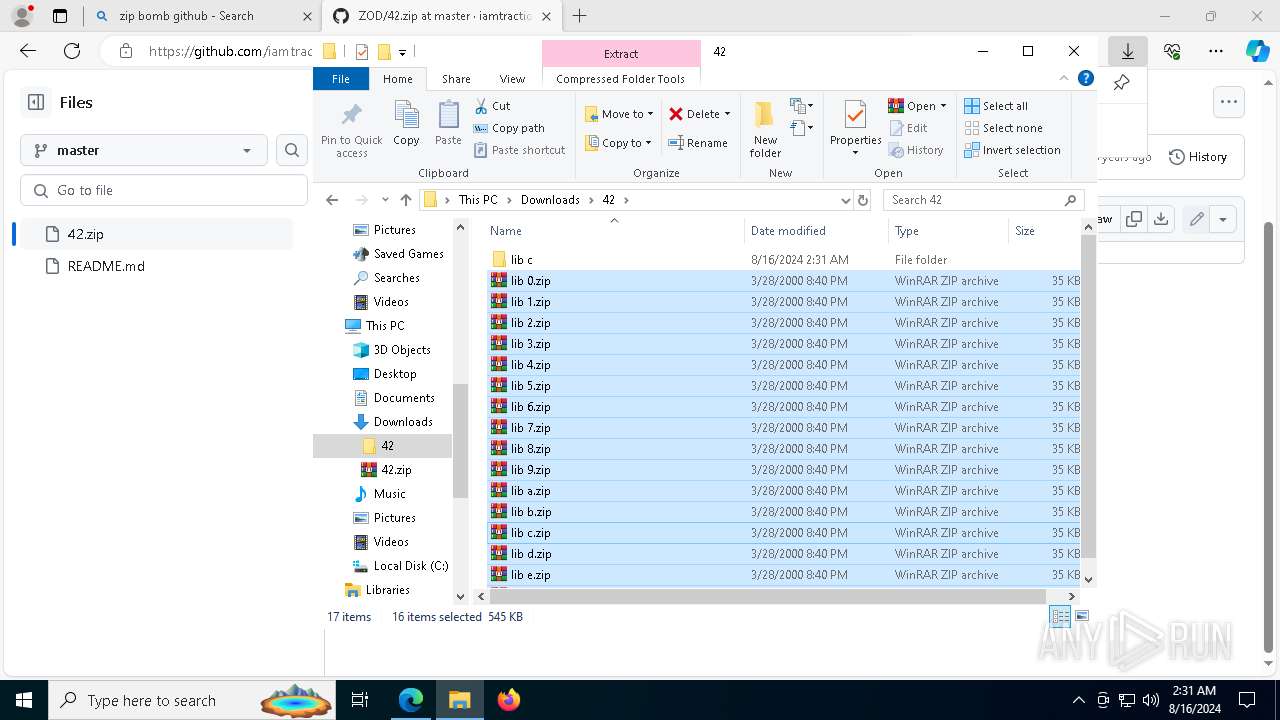
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
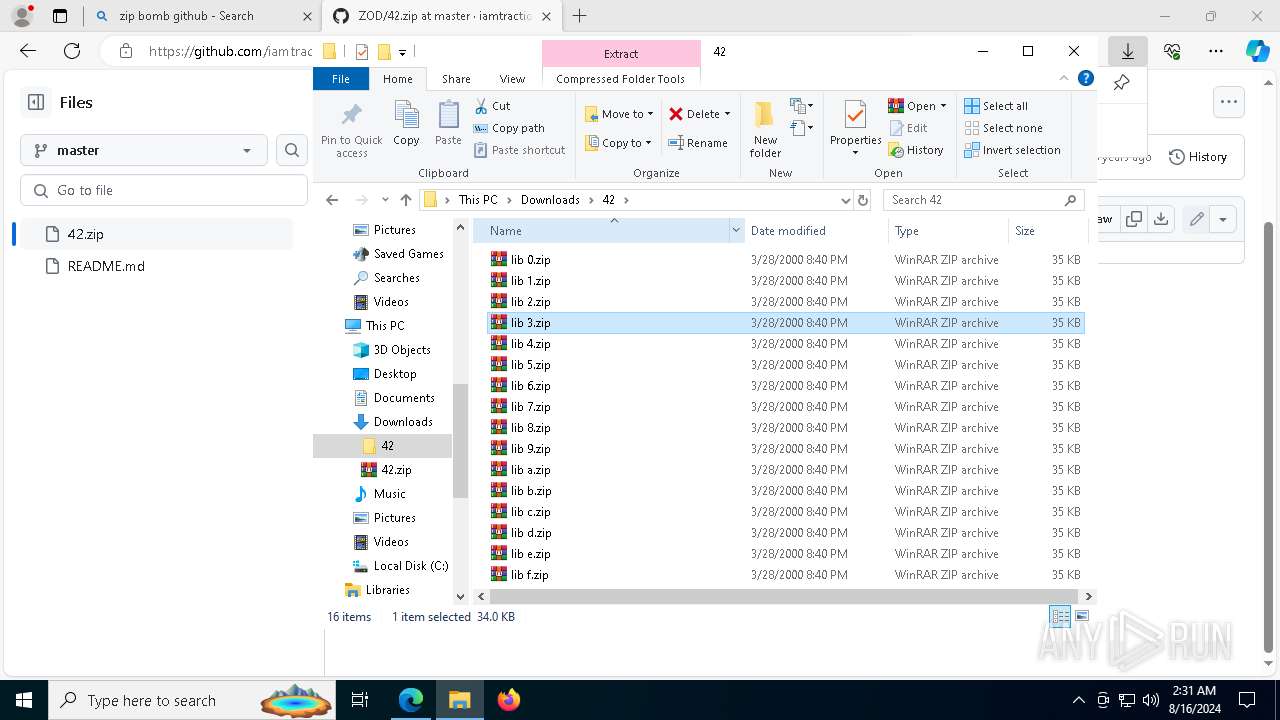
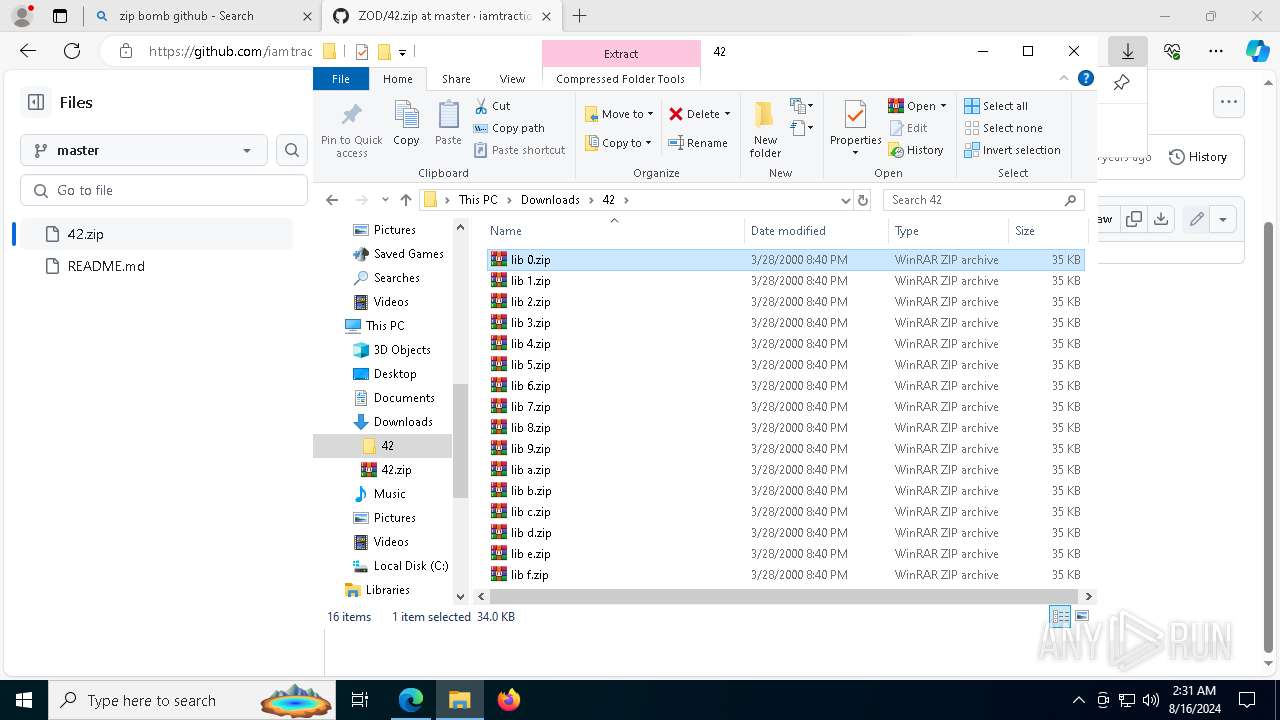
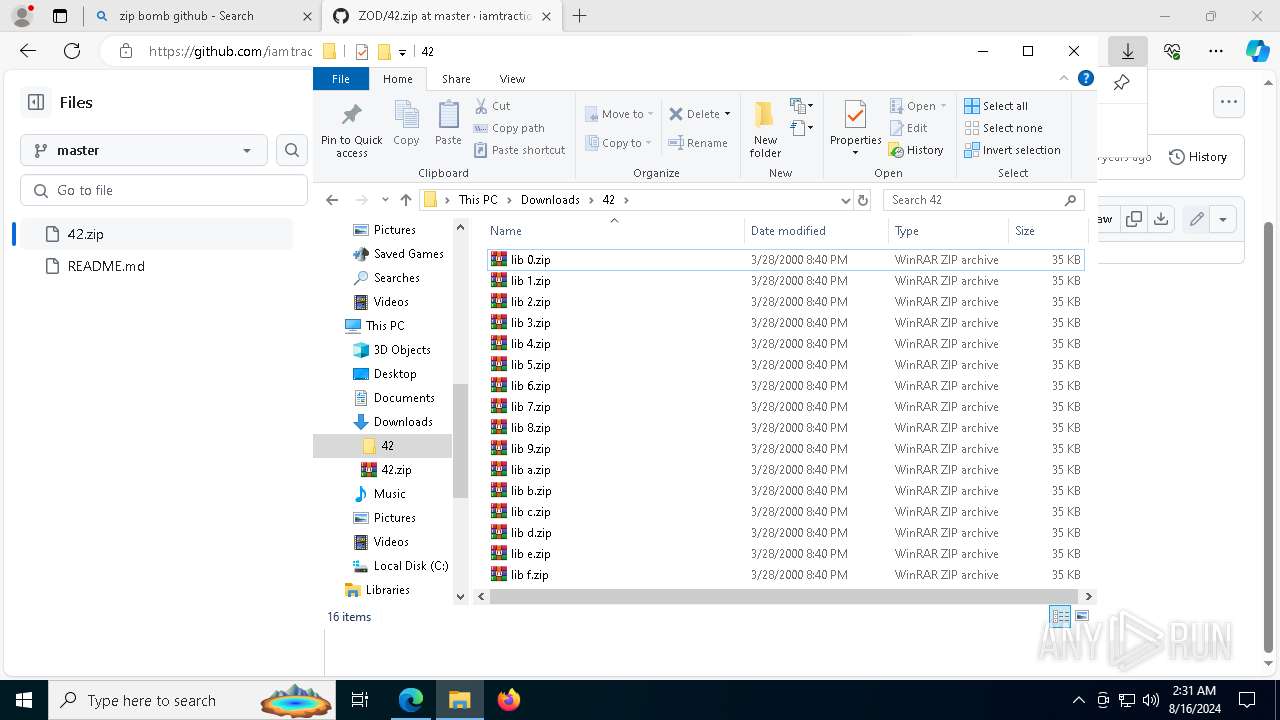
| 7304 | WinRAR.exe | C:\Users\admin\Downloads\42\lib 6.zip | compressed | |
MD5:0A76BD3E26768BBA68ACA3D210997069 | SHA256:9056B87F079861D1B0F041317D6415927D9FFB6498CE2530FF90FDA69FA64E78 | |||
| 7304 | WinRAR.exe | C:\Users\admin\Downloads\42\lib 9.zip | compressed | |
MD5:0A76BD3E26768BBA68ACA3D210997069 | SHA256:9056B87F079861D1B0F041317D6415927D9FFB6498CE2530FF90FDA69FA64E78 | |||
| 7304 | WinRAR.exe | C:\Users\admin\Downloads\42\lib a.zip | compressed | |
MD5:0A76BD3E26768BBA68ACA3D210997069 | SHA256:9056B87F079861D1B0F041317D6415927D9FFB6498CE2530FF90FDA69FA64E78 | |||
| 7304 | WinRAR.exe | C:\Users\admin\Downloads\42\lib b.zip | compressed | |
MD5:0A76BD3E26768BBA68ACA3D210997069 | SHA256:9056B87F079861D1B0F041317D6415927D9FFB6498CE2530FF90FDA69FA64E78 | |||
| 7304 | WinRAR.exe | C:\Users\admin\Downloads\42\lib f.zip | compressed | |
MD5:0A76BD3E26768BBA68ACA3D210997069 | SHA256:9056B87F079861D1B0F041317D6415927D9FFB6498CE2530FF90FDA69FA64E78 | |||
| 7304 | WinRAR.exe | C:\Users\admin\Downloads\42\lib c.zip | compressed | |
MD5:0A76BD3E26768BBA68ACA3D210997069 | SHA256:9056B87F079861D1B0F041317D6415927D9FFB6498CE2530FF90FDA69FA64E78 | |||
| 7304 | WinRAR.exe | C:\Users\admin\Downloads\42\lib 4.zip | compressed | |
MD5:0A76BD3E26768BBA68ACA3D210997069 | SHA256:9056B87F079861D1B0F041317D6415927D9FFB6498CE2530FF90FDA69FA64E78 | |||
| 7304 | WinRAR.exe | C:\Users\admin\Downloads\42\lib d.zip | compressed | |
MD5:0A76BD3E26768BBA68ACA3D210997069 | SHA256:9056B87F079861D1B0F041317D6415927D9FFB6498CE2530FF90FDA69FA64E78 | |||
| 7304 | WinRAR.exe | C:\Users\admin\Downloads\42\lib 2.zip | compressed | |
MD5:0A76BD3E26768BBA68ACA3D210997069 | SHA256:9056B87F079861D1B0F041317D6415927D9FFB6498CE2530FF90FDA69FA64E78 | |||
| 8088 | WinRAR.exe | C:\Users\admin\Downloads\42\lib c\book 0.zip | compressed | |
MD5:38605A41EDA691B378C8304BF914C777 | SHA256:F791BEA6D653EDDCAF8BE57E45B698E75F105E28A20C50F519AD43A2B2E27B2A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
35
TCP/UDP connections
176
DNS requests
124
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5540 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6804 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6864 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
4576 | svchost.exe | HEAD | 200 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/3b6aa6cb-e9f5-4799-9d73-5c5c48582465?P1=1724313425&P2=404&P3=2&P4=DXphRbtmTo1C1TIL9r%2fysiL1OQAE4v4WobVpYYtLXpoJkJ%2bcROG0Od5whQsZdtE6nq1ccaaLNpxHAcqNxk6HLw%3d%3d | unknown | — | — | whitelisted |
4576 | svchost.exe | GET | 206 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/3b6aa6cb-e9f5-4799-9d73-5c5c48582465?P1=1724313425&P2=404&P3=2&P4=DXphRbtmTo1C1TIL9r%2fysiL1OQAE4v4WobVpYYtLXpoJkJ%2bcROG0Od5whQsZdtE6nq1ccaaLNpxHAcqNxk6HLw%3d%3d | unknown | — | — | whitelisted |
4576 | svchost.exe | GET | 206 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/3b6aa6cb-e9f5-4799-9d73-5c5c48582465?P1=1724313425&P2=404&P3=2&P4=DXphRbtmTo1C1TIL9r%2fysiL1OQAE4v4WobVpYYtLXpoJkJ%2bcROG0Od5whQsZdtE6nq1ccaaLNpxHAcqNxk6HLw%3d%3d | unknown | — | — | whitelisted |
4576 | svchost.exe | GET | 206 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/3b6aa6cb-e9f5-4799-9d73-5c5c48582465?P1=1724313425&P2=404&P3=2&P4=DXphRbtmTo1C1TIL9r%2fysiL1OQAE4v4WobVpYYtLXpoJkJ%2bcROG0Od5whQsZdtE6nq1ccaaLNpxHAcqNxk6HLw%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4484 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5244 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4484 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
5336 | SearchApp.exe | 2.23.209.182:443 | www.bing.com | Akamai International B.V. | GB | unknown |
5336 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
5540 | svchost.exe | 20.190.159.23:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
th.bing.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
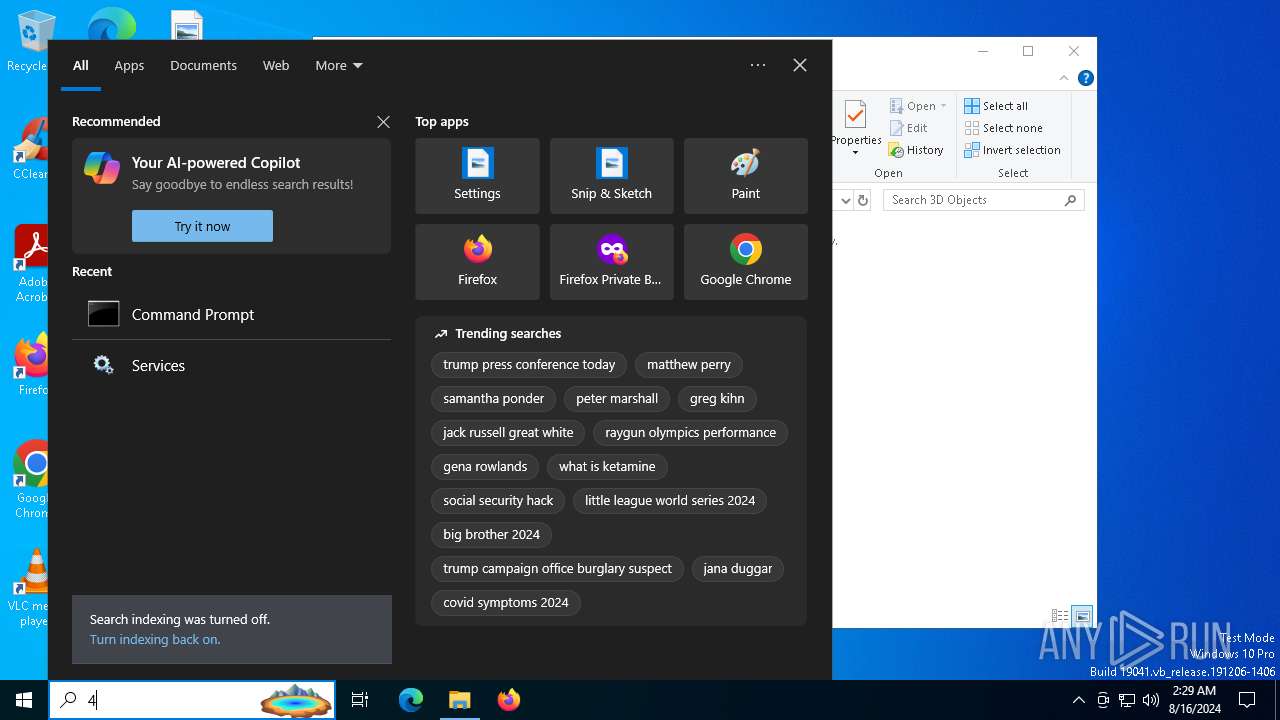
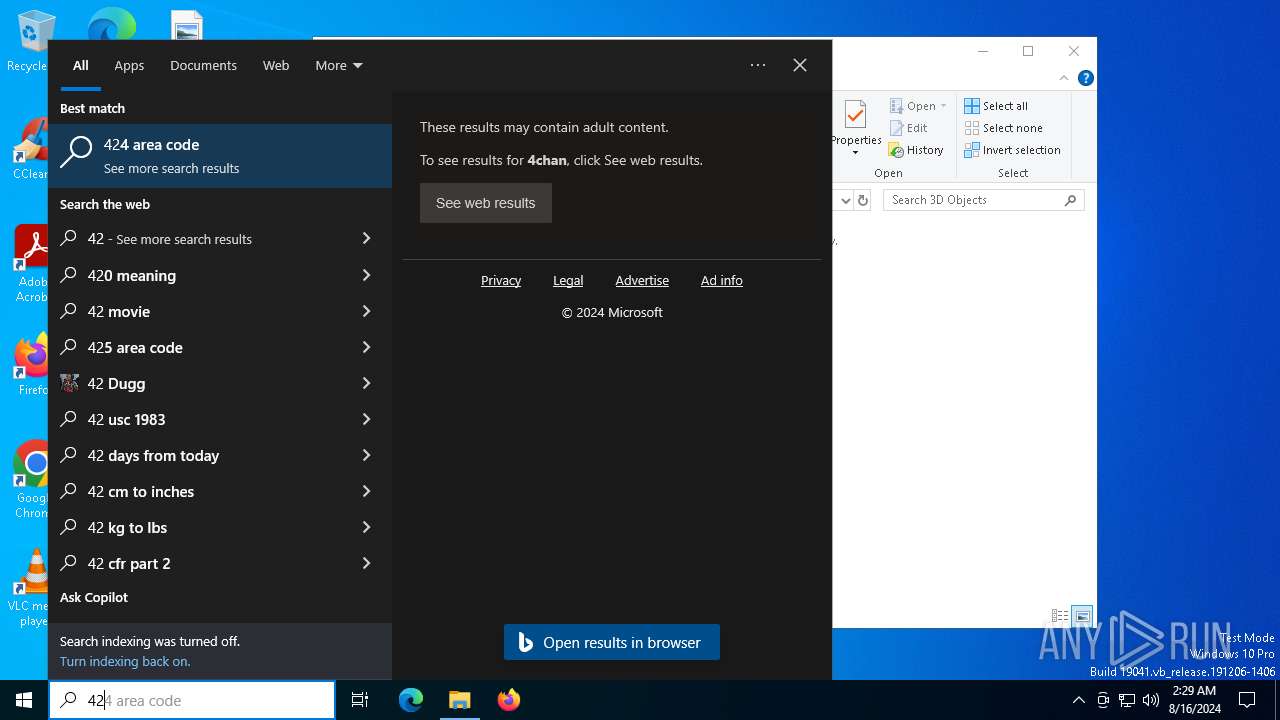
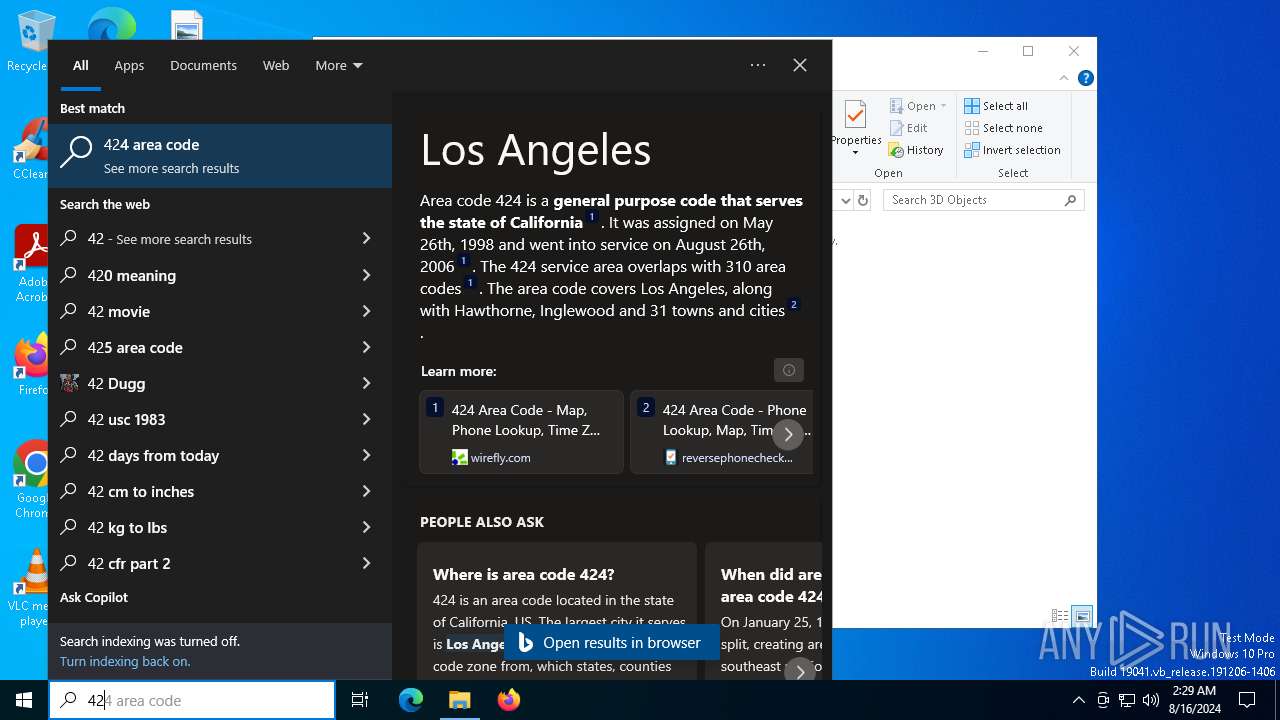
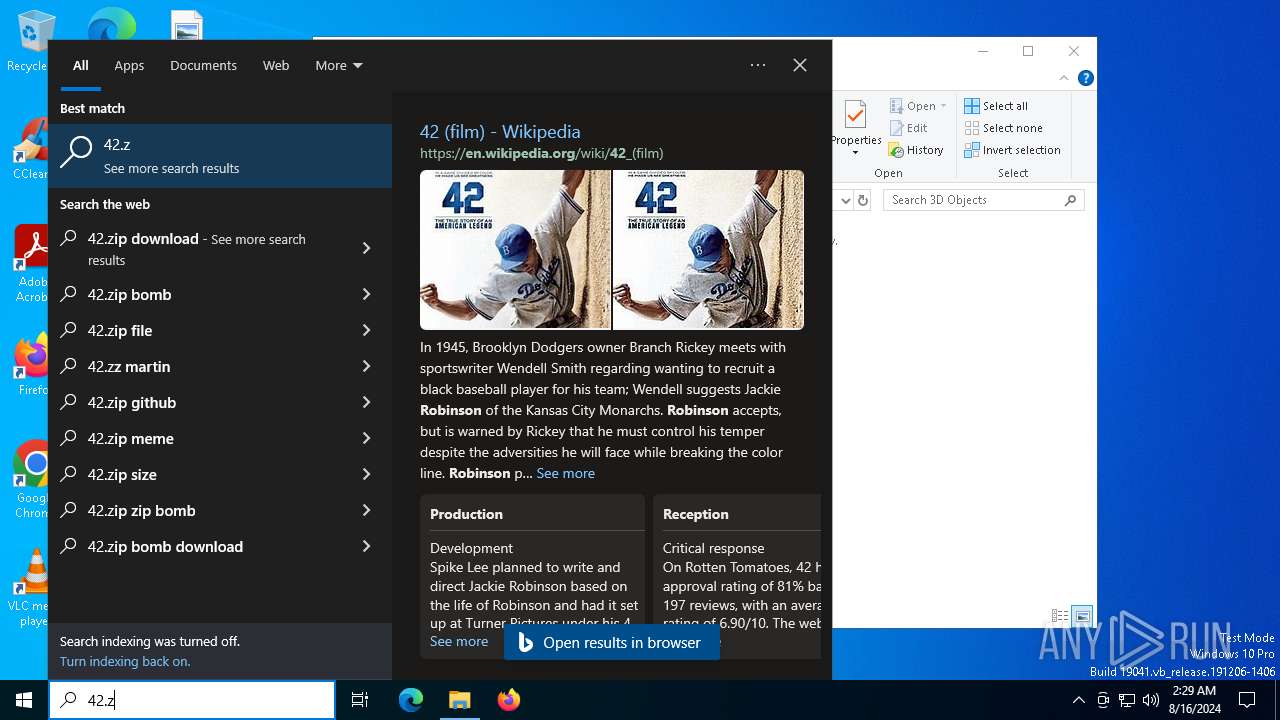
Threats
PID | Process | Class | Message |
|---|---|---|---|
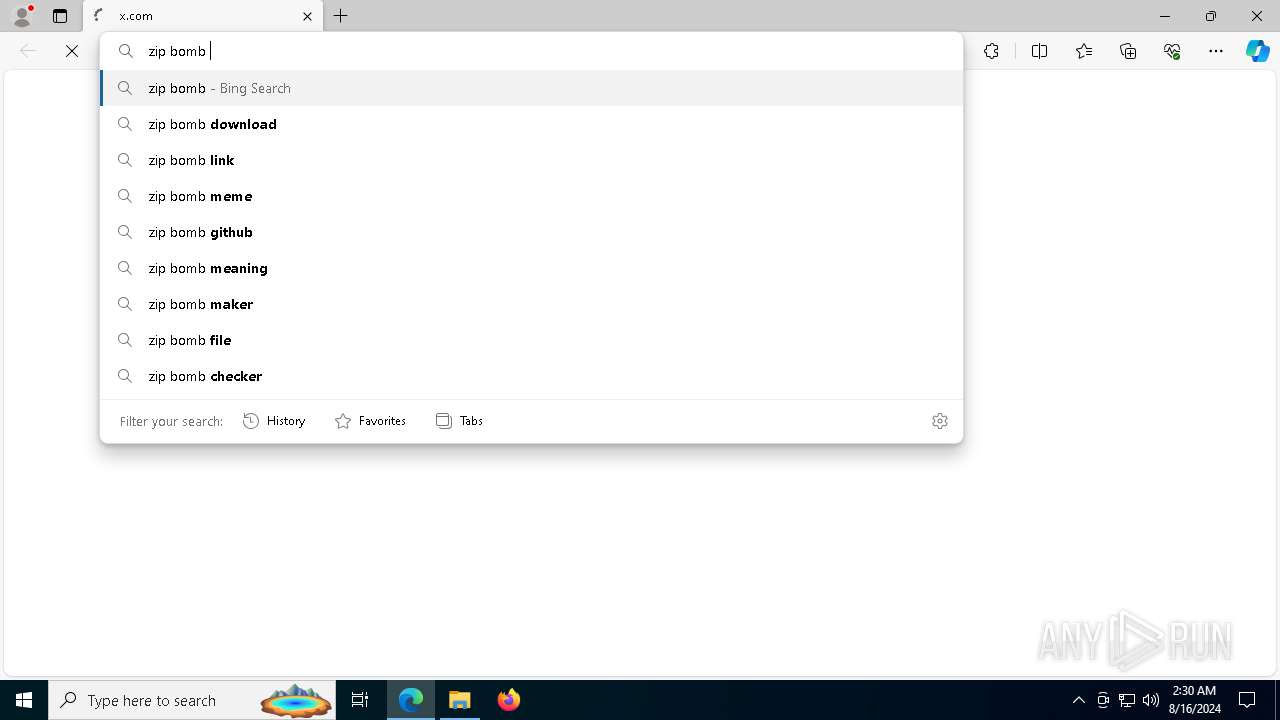
1452 | msedge.exe | Misc activity | ET INFO Observed DNS Query to .zip TLD |
1452 | msedge.exe | Misc activity | ET INFO Observed DNS Query to .zip TLD |
1452 | msedge.exe | Misc activity | ET INFO Observed DNS Query to .zip TLD |
1452 | msedge.exe | Misc activity | ET INFO Observed DNS Query to .zip TLD |
1452 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
1452 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |