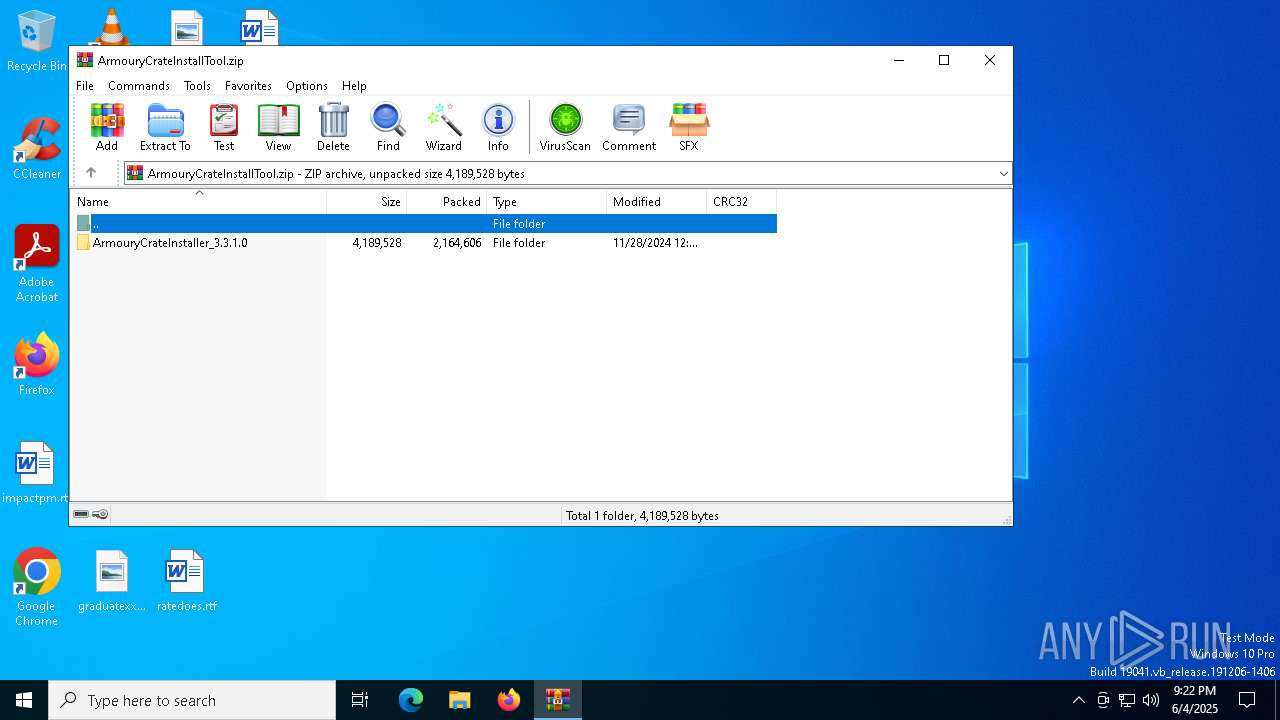
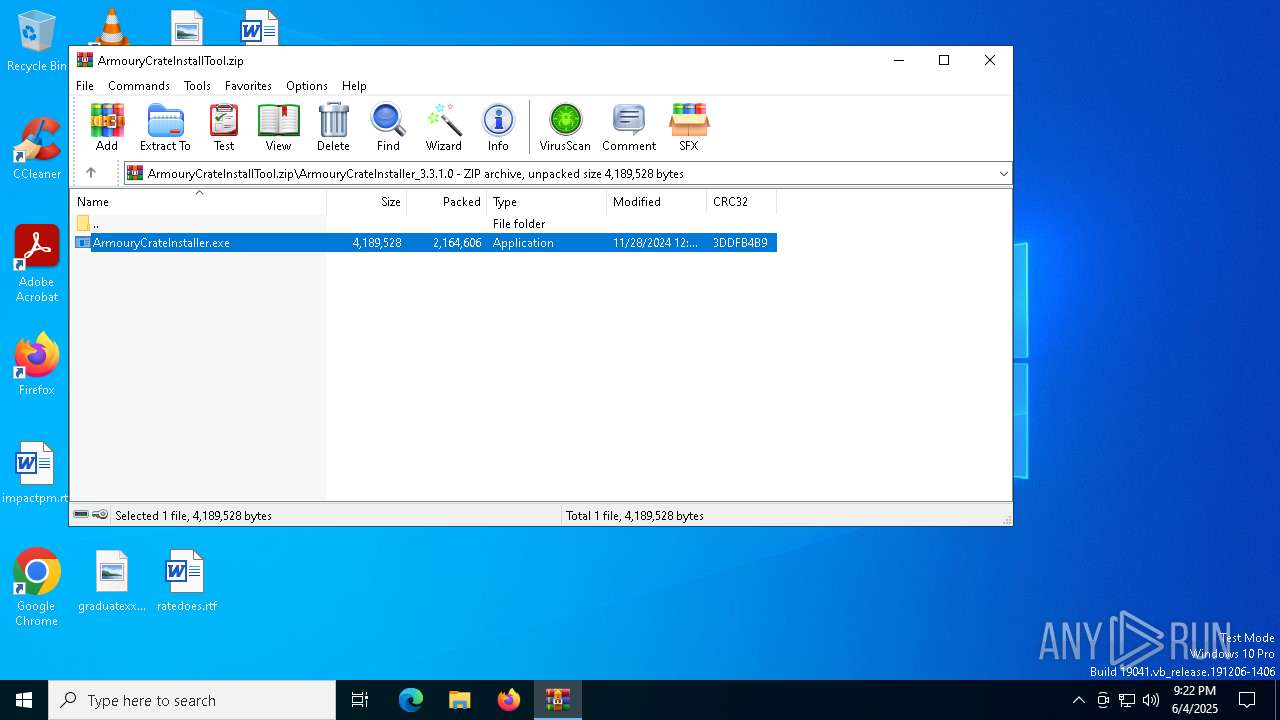
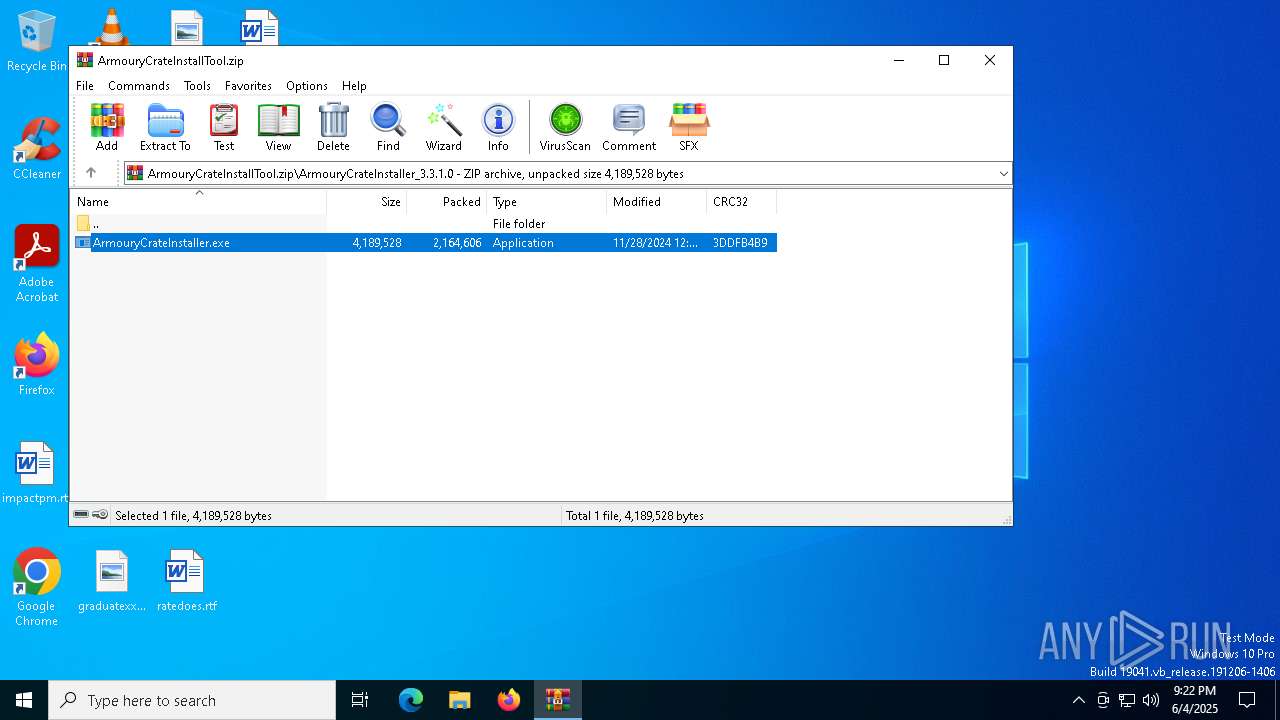
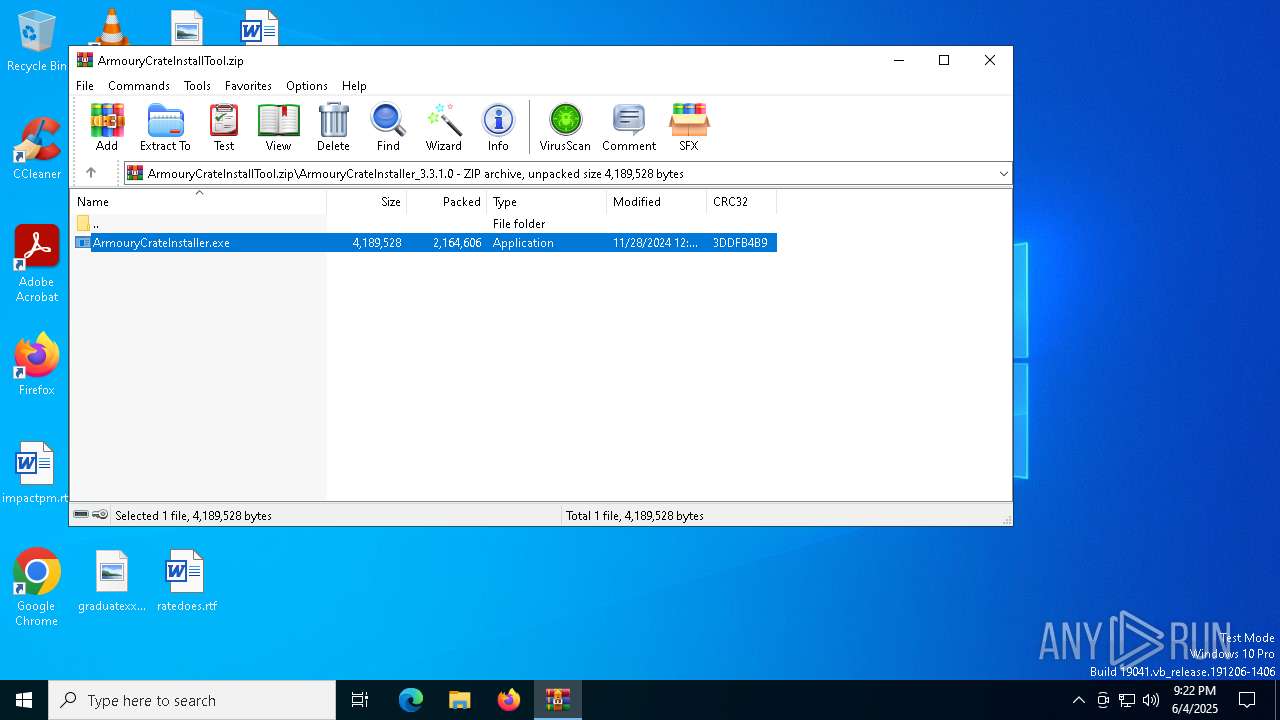
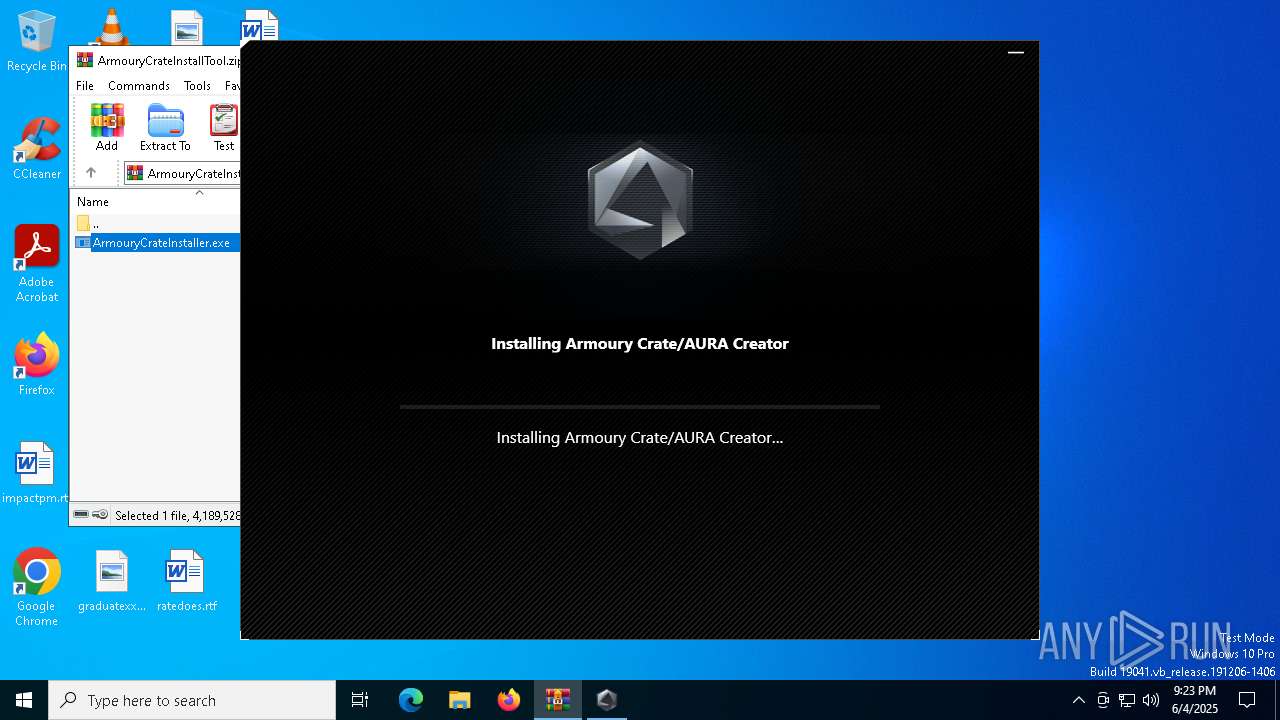
| File name: | ArmouryCrateInstallTool.zip |
| Full analysis: | https://app.any.run/tasks/39d0b0e9-8cc6-4137-8697-1fad0468ecd1 |
| Verdict: | Malicious activity |
| Analysis date: | June 04, 2025, 21:22:36 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=store |
| MD5: | 613E0D3038311E9A80FC4F1EBB7582CC |
| SHA1: | F3EBD8247451EE1C193F959695E7AB6546F3DBF1 |
| SHA256: | BBCD8B2F6DA29C43C26356502DCDE4313FC7BB2720DA1A081763AC0C426A5F6B |
| SSDEEP: | 98304:cg/GR+bNH3S1cUBS5rXV8BH9OKv/DvSh4ASVwDXnFuewhHUEZc1zmQCbq7QEeeQ6:aS |
MALICIOUS
No malicious indicators.SUSPICIOUS
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 3828)
- cmd.exe (PID: 7572)
- cmd.exe (PID: 6640)
- cmd.exe (PID: 7788)
- cmd.exe (PID: 8024)
- cmd.exe (PID: 6184)
- cmd.exe (PID: 516)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 4200)
- ArmouryCrateInstaller.exe (PID: 672)
- Armoury Crate Installer.exe (PID: 6632)
- Armoury Crate Installer.exe (PID: 5236)
- AsusROGLSLService.exe (PID: 2852)
- Armoury Crate Installer.exe (PID: 7468)
- ROGLSLoader.exe (PID: 7288)
- Armoury Crate Installer.exe (PID: 7388)
- ArmouryCrateInstaller.exe (PID: 5956)
Executable content was dropped or overwritten
- ArmouryCrateInstaller.exe (PID: 672)
- ArmouryCrateInstaller.exe (PID: 5956)
- AsZip.exe (PID: 4844)
Reads the date of Windows installation
- ArmouryCrateInstaller.exe (PID: 5956)
- ArmouryCrateInstaller.exe (PID: 672)
- AsusROGLSLService.exe (PID: 2852)
- ROGLSLoader.exe (PID: 7288)
Starts CMD.EXE for commands execution
- ArmouryCrateInstaller.exe (PID: 672)
- ArmouryCrateInstaller.exe (PID: 5956)
- QueryUWP.exe (PID: 1188)
Executes as Windows Service
- AsusROGLSLService.exe (PID: 7272)
- AsusROGLSLService.exe (PID: 2852)
The process drops C-runtime libraries
- AsusROGLSLService.exe (PID: 2852)
- AsZip.exe (PID: 4844)
Process drops legitimate windows executable
- AsusROGLSLService.exe (PID: 2852)
- AsZip.exe (PID: 4844)
INFO
Creates files in the program directory
- ArmouryCrateInstaller.exe (PID: 5956)
- ArmouryCrateInstaller.exe (PID: 672)
- Armoury Crate Installer.exe (PID: 6632)
- Armoury Crate Installer.exe (PID: 5236)
- QueryUWP.exe (PID: 1188)
- Armoury Crate Installer.exe (PID: 7468)
- CheckTool.exe (PID: 4188)
- AsusROGLSLService.exe (PID: 2852)
- AsZip.exe (PID: 4844)
- AsZip.exe (PID: 3884)
- ROGLSLoader.exe (PID: 7288)
- Armoury Crate Installer.exe (PID: 7388)
- AsusROGLSLService.exe (PID: 5776)
- CheckTool.exe (PID: 2268)
Process checks computer location settings
- ArmouryCrateInstaller.exe (PID: 5956)
- ArmouryCrateInstaller.exe (PID: 672)
The sample compiled with chinese language support
- ArmouryCrateInstaller.exe (PID: 672)
- ArmouryCrateInstaller.exe (PID: 5956)
- AsZip.exe (PID: 4844)
- AsusROGLSLService.exe (PID: 2852)
Checks supported languages
- ArmouryCrateInstaller.exe (PID: 672)
- AsusROGLSLService.exe (PID: 6744)
- AsusROGLSLService.exe (PID: 7584)
- AsusROGLSLService.exe (PID: 7272)
- Armoury Crate Installer.exe (PID: 6632)
- AsusROGLSLService.exe (PID: 456)
- AsusROGLSLService.exe (PID: 2852)
- Armoury Crate Installer.exe (PID: 5236)
- QueryUWP.exe (PID: 1188)
- Armoury Crate Installer.exe (PID: 7468)
- AsZip.exe (PID: 3884)
- CheckTool.exe (PID: 4188)
- AsZip.exe (PID: 4844)
- Armoury Crate Installer.exe (PID: 7388)
- CheckTool.exe (PID: 2268)
- ArmouryCrateInstaller.exe (PID: 5956)
- AsusROGLSLService.exe (PID: 5776)
- ROGLSLoader.exe (PID: 7288)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 4200)
The sample compiled with english language support
- ArmouryCrateInstaller.exe (PID: 5956)
- ArmouryCrateInstaller.exe (PID: 672)
- AsusROGLSLService.exe (PID: 2852)
- AsZip.exe (PID: 4844)
Reads the computer name
- ArmouryCrateInstaller.exe (PID: 672)
- AsusROGLSLService.exe (PID: 6744)
- AsusROGLSLService.exe (PID: 7584)
- AsusROGLSLService.exe (PID: 7272)
- Armoury Crate Installer.exe (PID: 6632)
- AsusROGLSLService.exe (PID: 456)
- AsusROGLSLService.exe (PID: 2852)
- Armoury Crate Installer.exe (PID: 5236)
- Armoury Crate Installer.exe (PID: 7468)
- CheckTool.exe (PID: 4188)
- ROGLSLoader.exe (PID: 7288)
- Armoury Crate Installer.exe (PID: 7388)
- CheckTool.exe (PID: 2268)
- ArmouryCrateInstaller.exe (PID: 5956)
- AsusROGLSLService.exe (PID: 5776)
Reads the machine GUID from the registry
- Armoury Crate Installer.exe (PID: 6632)
- Armoury Crate Installer.exe (PID: 5236)
- Armoury Crate Installer.exe (PID: 7468)
- CheckTool.exe (PID: 4188)
- AsusROGLSLService.exe (PID: 2852)
- CheckTool.exe (PID: 2268)
- Armoury Crate Installer.exe (PID: 7388)
Disables trace logs
- CheckTool.exe (PID: 4188)
- CheckTool.exe (PID: 2268)
Reads the software policy settings
- CheckTool.exe (PID: 4188)
- AsusROGLSLService.exe (PID: 2852)
- ROGLSLoader.exe (PID: 7288)
- CheckTool.exe (PID: 2268)
- slui.exe (PID: 2084)
Reads Environment values
- CheckTool.exe (PID: 4188)
- ROGLSLoader.exe (PID: 7288)
- CheckTool.exe (PID: 2268)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2024:11:28 20:19:24 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | ArmouryCrateInstaller_3.3.1.0/ |
Total processes
177
Monitored processes
49
Malicious processes
2
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 456 | "C:\Program Files (x86)\ASUS\AsusROGLSLService\AsusROGLSLService.exe" -install | C:\Program Files (x86)\ASUS\AsusROGLSLService\AsusROGLSLService.exe | — | ArmouryCrateInstaller.exe | |||||||||||
User: admin Company: ASUS Integrity Level: HIGH Exit code: 0 Version: 3.3.0.0 Modules
| |||||||||||||||
| 516 | C:\WINDOWS\system32\cmd.exe /c PowerShell "get-appxpackage | select-string B9ECED6F.ArmouryCrate" | C:\Windows\System32\cmd.exe | — | QueryUWP.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 672 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa4200.47595\ArmouryCrateInstaller_3.3.1.0\ArmouryCrateInstaller.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa4200.47595\ArmouryCrateInstaller_3.3.1.0\ArmouryCrateInstaller.exe | WinRAR.exe | ||||||||||||
User: admin Company: ASUS Integrity Level: HIGH Description: The installer for Armoury Crate and Aura Creator. Exit code: 0 Version: 3.3.1.0 Modules
| |||||||||||||||
| 1120 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | ArmouryCrateInstaller.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1188 | "C:\Program Files (x86)\ASUS\AsusROGLSLService\QueryUWP.exe" | C:\Program Files (x86)\ASUS\AsusROGLSLService\QueryUWP.exe | — | AsusROGLSLService.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 4294967295 Version: 1.0.0.3 Modules
| |||||||||||||||
| 1228 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa4200.47595\ArmouryCrateInstaller_3.3.1.0\ArmouryCrateInstaller.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa4200.47595\ArmouryCrateInstaller_3.3.1.0\ArmouryCrateInstaller.exe | — | WinRAR.exe | |||||||||||
User: admin Company: ASUS Integrity Level: MEDIUM Description: The installer for Armoury Crate and Aura Creator. Exit code: 3221226540 Version: 3.3.1.0 Modules
| |||||||||||||||
| 1324 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa4200.47462\ArmouryCrateInstaller_3.3.1.0\ArmouryCrateInstaller.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa4200.47462\ArmouryCrateInstaller_3.3.1.0\ArmouryCrateInstaller.exe | — | WinRAR.exe | |||||||||||
User: admin Company: ASUS Integrity Level: MEDIUM Description: The installer for Armoury Crate and Aura Creator. Exit code: 3221226540 Version: 3.3.1.0 Modules
| |||||||||||||||
| 2084 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2268 | "C:\Program Files (x86)\ASUS\ROGLSLoader\CheckTool.exe" --is-china-network | C:\Program Files (x86)\ASUS\ROGLSLoader\CheckTool.exe | ROGLSLoader.exe | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Description: CheckTool Exit code: 0 Version: 1.0.2.0 Modules
| |||||||||||||||
| 2384 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | AsusROGLSLService.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
46 232
Read events
46 190
Write events
36
Delete events
6
Modification events
| (PID) Process: | (4200) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (4200) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (4200) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (4200) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (4200) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (4200) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\ArmouryCrateInstallTool.zip | |||
| (PID) Process: | (4200) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4200) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4200) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (4200) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
52
Suspicious files
11
Text files
34
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4200 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa4200.47462\ArmouryCrateInstaller_3.3.1.0\ArmouryCrateInstaller.exe | executable | |
MD5:BEB653D2CD771788B34A1AB37F854ADE | SHA256:8139B87231D99CAC36BFED7A4974C8086A9C32DD5FE15F4775F476F54F586B4C | |||
| 5956 | ArmouryCrateInstaller.exe | C:\Program Files (x86)\ASUS\AsusROGLSLService\Newtonsoft.Json.dll | executable | |
MD5:081D9558BBB7ADCE142DA153B2D5577A | SHA256:B624949DF8B0E3A6153FDFB730A7C6F4990B6592EE0D922E1788433D276610F3 | |||
| 5776 | AsusROGLSLService.exe | C:\ProgramData\ASUS\ALL\ACLoader\ArmouryCrateInstaller.log | text | |
MD5:14CF9D234BDE15A4F699207282D67439 | SHA256:965A5416C373DF977647A81D35E6F4ACE9594072648B582AF657292C6443C89B | |||
| 5956 | ArmouryCrateInstaller.exe | C:\Program Files (x86)\ASUS\AsusROGLSLService\AsusGCGridServiceSetup.exe | executable | |
MD5:242C0332DB5EBA361CC3628DFAB5CE56 | SHA256:BCC843B036C22AD4A1485E62C2ED5CA88F33688FA919C73276B93D4CDBE83347 | |||
| 5776 | AsusROGLSLService.exe | C:\ProgramData\ASUS\ALL\ACLoader\AsusROGLSLService.log | text | |
MD5:DC7A87483870EB6EFB7DBE6CE61C9BBF | SHA256:C918FE217F8B637E9E6F25F1FB20B45141E977F513F30D7032A8B6F12EF7D94A | |||
| 5956 | ArmouryCrateInstaller.exe | C:\Program Files (x86)\ASUS\AsusROGLSLService\ProductInfoLib.dll | executable | |
MD5:48CEB044F0876024635C22BB5A5B4DBA | SHA256:E0404A40233C8B4DD7731B361C6E7BD6BC22496825ABD733C26643B50BF2243F | |||
| 5956 | ArmouryCrateInstaller.exe | C:\Program Files (x86)\ASUS\AsusROGLSLService\CheckTool.exe | executable | |
MD5:DB80FF85D5B06290FDD3B4BE2F01C8FF | SHA256:669059A35C04D46176CDC39737291D27BE495766550A5E7AD7C6FCAB5901477F | |||
| 672 | ArmouryCrateInstaller.exe | C:\Program Files (x86)\ASUS\AsusROGLSLService\AsusROGLSLService.exe | executable | |
MD5:0DE7BDE67B480DA74EA735ED8CAFA36D | SHA256:996A26F8E0845A2BAC0C760B9DA65FF800C6EEFEF84CA1BB5D583994E65EEC4E | |||
| 672 | ArmouryCrateInstaller.exe | C:\Program Files (x86)\ASUS\AsusROGLSLService\AsZip.exe | executable | |
MD5:9131A40E5770D1170C3093FB0D2F6F63 | SHA256:FCF8D154E6B37985434F991B048CEF457DE123DD5A553EF3C6B28A67FB8A3987 | |||
| 4200 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa4200.47595\ArmouryCrateInstaller_3.3.1.0\ArmouryCrateInstaller.exe | executable | |
MD5:BEB653D2CD771788B34A1AB37F854ADE | SHA256:8139B87231D99CAC36BFED7A4974C8086A9C32DD5FE15F4775F476F54F586B4C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
37
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.168.114:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7512 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7512 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6544 | svchost.exe | 20.190.159.71:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.16.168.114:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
— | — | 23.219.150.101:80 | www.microsoft.com | AKAMAI-AS | CL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6544 | svchost.exe | 20.190.159.23:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 23.54.109.203:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
4188 | CheckTool.exe | 18.172.112.57:443 | www.asus.com | — | US | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
login.live.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.asus.com |
| whitelisted |
liveupdate01s.asus.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
AsusROGLSLService.exe | Failed to get baseboard manufacturer via WMI, get via registry. |
AsusROGLSLService.exe | Failed to get baseboard manufacturer via WMI, get via registry. |