| download: | index.html |
| Full analysis: | https://app.any.run/tasks/d1a25cb0-150f-4246-8cc8-f5ff3aab6dc5 |
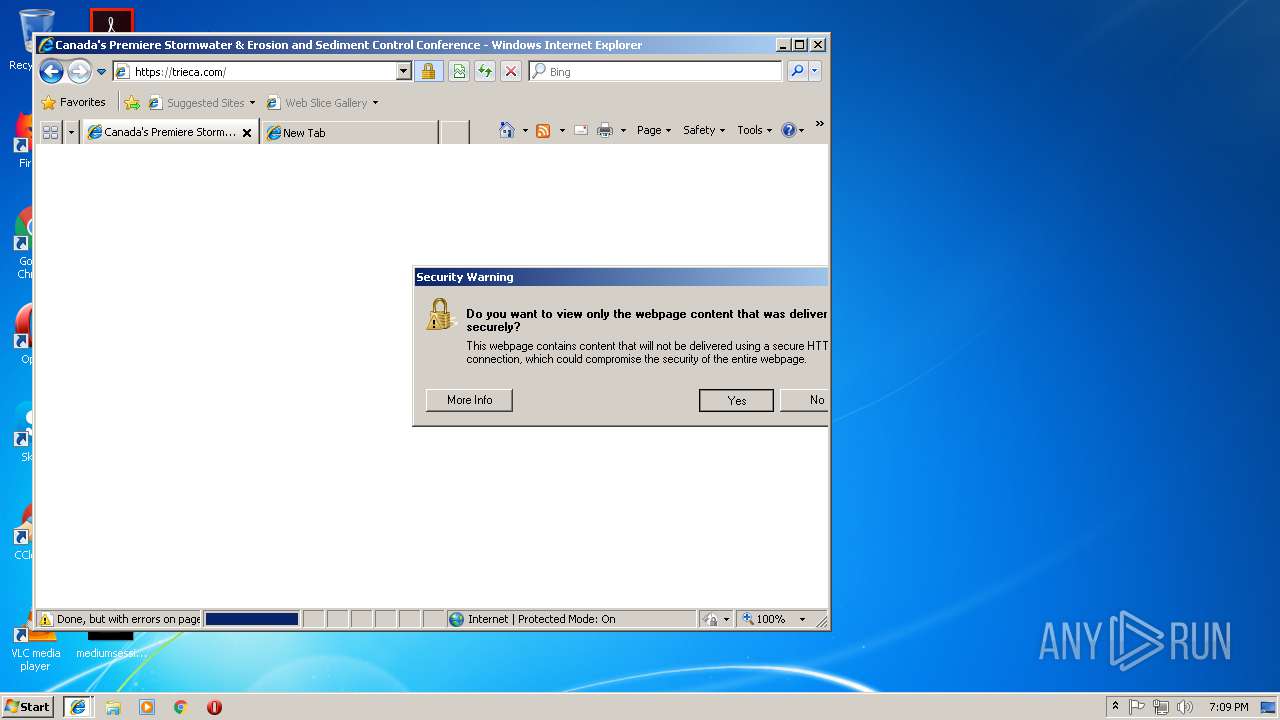
| Verdict: | Malicious activity |
| Analysis date: | January 10, 2019, 19:08:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, UTF-8 Unicode text, with very long lines, with CRLF, LF line terminators |
| MD5: | 4AECFFA9C95838CF15694958C724A2C9 |
| SHA1: | A9F3D32B73E7E48E6DFF4E3F2A1DA236C8407A4E |
| SHA256: | BBC8A0B05BA3CD29C1B087DFCDB145E9C75AFFB995DD000E3C4A175A8F171DC1 |
| SSDEEP: | 3072:4npKOkstQRWq5I8paoFia3+d9wwfLyREp+G5JMnghnVbYcd7b8UOk84:mQbP+dKwfLWEl5JMngV |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 3388)
- iexplore.exe (PID: 3012)
- iexplore.exe (PID: 2296)
- iexplore.exe (PID: 2700)
Application launched itself
- iexplore.exe (PID: 2700)
Changes settings of System certificates
- iexplore.exe (PID: 3388)
- iexplore.exe (PID: 2700)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3388)
- iexplore.exe (PID: 2700)
Creates files in the user directory
- iexplore.exe (PID: 3388)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 2448)
- iexplore.exe (PID: 2296)
Reads settings of System Certificates
- iexplore.exe (PID: 2296)
- iexplore.exe (PID: 2700)
Reads internet explorer settings
- iexplore.exe (PID: 3388)
- iexplore.exe (PID: 2296)
- iexplore.exe (PID: 3012)
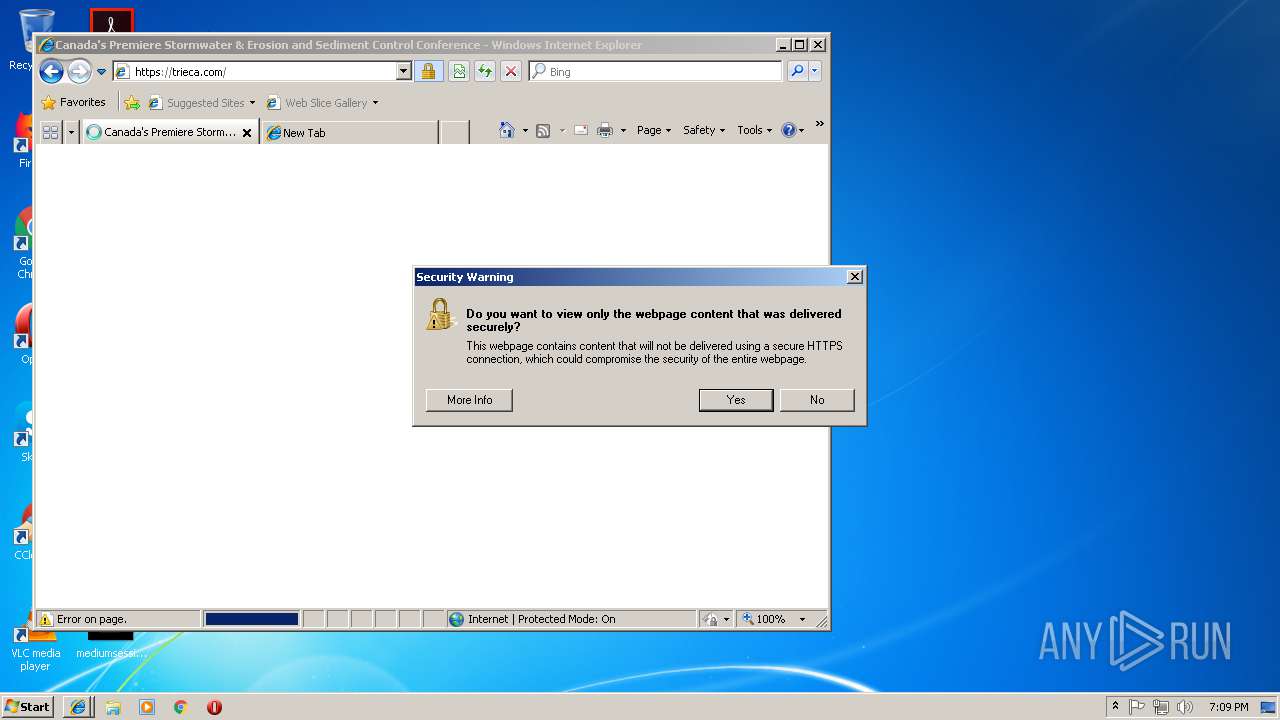
Changes internet zones settings
- iexplore.exe (PID: 2700)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .htm/html | | | HyperText Markup Language with DOCTYPE (80.6) |
|---|---|---|
| .html | | | HyperText Markup Language (19.3) |
EXIF
HTML
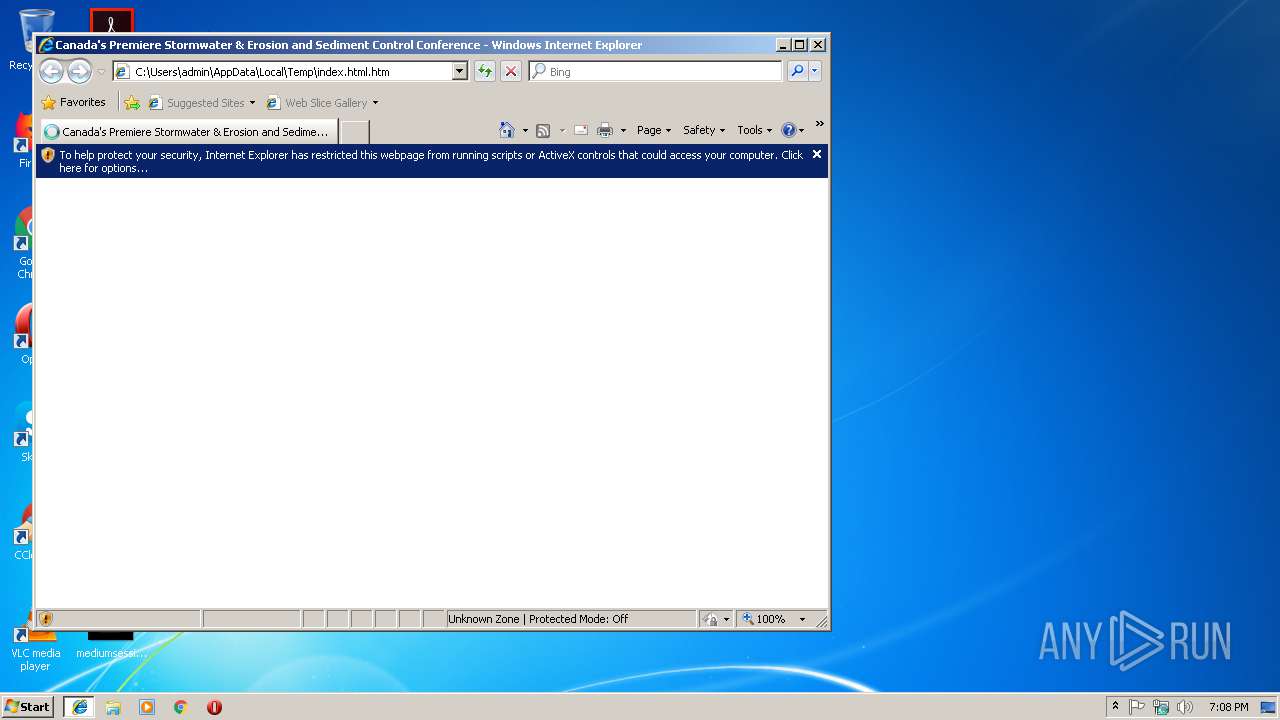
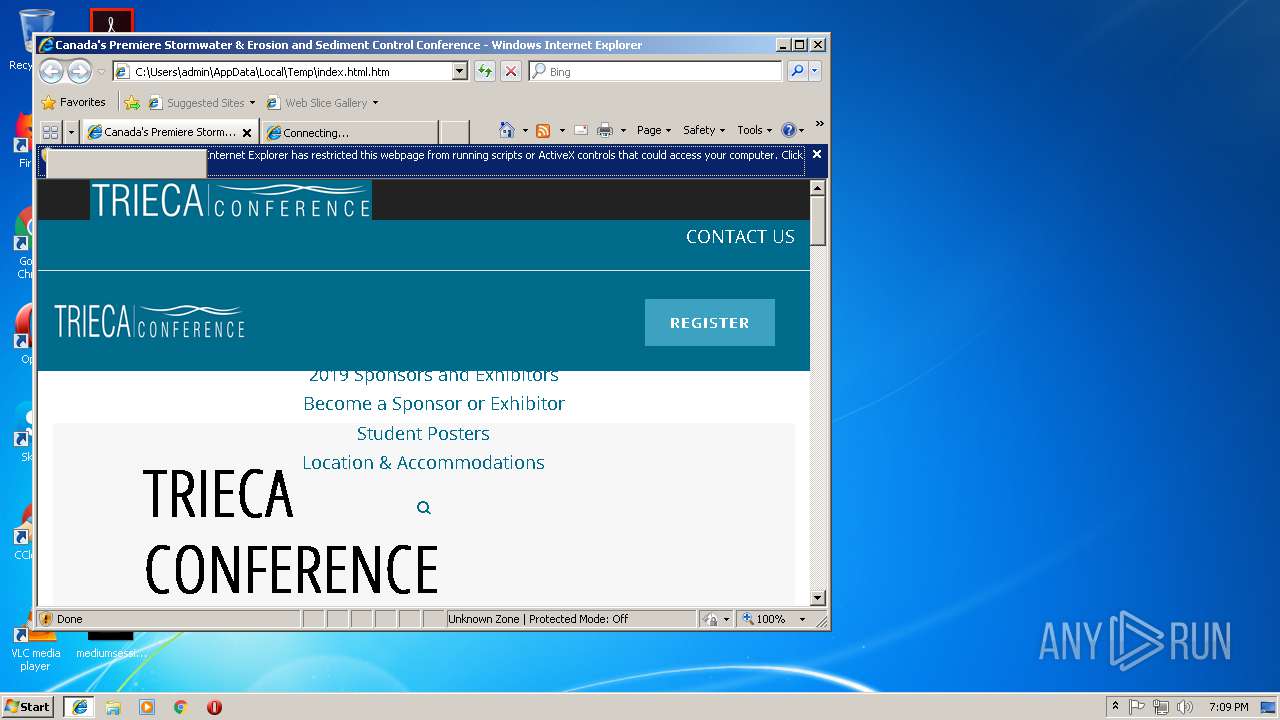
| Title: | Canada's Premiere Stormwater & Erosion and Sediment Control Conference |
|---|---|
| viewport: | width=device-width, initial-scale=1.0 |
| Description: | TRIECA is Canada’s premier stormwater and erosion and sediment control conference bringing together leading experts, influential leaders & research partners |
| twitterCard: | summary |
| twitterDescription: | TRIECA is Canada’s premier stormwater and erosion and sediment control conference bringing together leading experts, influential leaders & research partners |
| twitterTitle: | TRIECA - Canada's Premier Stormwater & Erosion and Sediment Control Conference |
| twitterSite: | @TRCA_TRIECA |
| twitterImage: | https://trieca.com/app/uploads/2018/10/DdfIlwDU8AEEVSo.png |
| twitterCreator: | @TRCA_TRIECA |
| Generator: | Powered by Slider Revolution 5.1.6 - responsive, Mobile-Friendly Slider Plugin for WordPress with comfortable drag and drop interface. |
Total processes
37
Monitored processes
5
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2296 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2700 CREDAT:203009 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2448 | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 26.0 r0 Exit code: 0 Version: 26,0,0,131 Modules
| |||||||||||||||
| 2700 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\AppData\Local\Temp\index.html.htm | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3012 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2700 CREDAT:137473 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3388 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2700 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
891
Read events
756
Write events
129
Delete events
6
Modification events
| (PID) Process: | (2700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {1F0460FB-150B-11E9-BAD8-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 3 | |||
| (PID) Process: | (2700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E307010004000A001300080021007A02 | |||
Executable files
0
Suspicious files
1
Text files
144
Unknown types
20
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2700 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2700 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3388 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\0UU90R59\swift-slider[1].css | text | |
MD5:— | SHA256:— | |||
| 3388 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\css[1].txt | text | |
MD5:— | SHA256:— | |||
| 3388 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\D2YPIJ90\style[1].css | html | |
MD5:— | SHA256:— | |||
| 3388 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\responsive[1].css | text | |
MD5:— | SHA256:— | |||
| 3388 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\0UU90R59\jquery.themepunch.revolution.min[1].js | text | |
MD5:— | SHA256:— | |||
| 3388 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\0UU90R59\spb-styles[1].css | text | |
MD5:— | SHA256:— | |||
| 3388 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\D2YPIJ90\ss-gizmo[1].css | html | |
MD5:7CBC06EC83E98CAA96E18463C00FBF1E | SHA256:BCC6B81A519AD4DB0B130ADE5EB1ACA6EA91E46BB8F682BCEDE26333911CF9EC | |||
| 2700 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[3].png | image | |
MD5:9FB559A691078558E77D6848202F6541 | SHA256:6D8A01DC7647BC218D003B58FE04049E24A9359900B7E0CEBAE76EDF85B8B914 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
45
DNS requests
14
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3388 | iexplore.exe | OPTIONS | 400 | 216.58.205.232:80 | http://www.googletagmanager.com/ | US | html | 1.52 Kb | whitelisted |
3388 | iexplore.exe | OPTIONS | 400 | 216.58.205.232:80 | http://www.googletagmanager.com/ | US | html | 1.52 Kb | whitelisted |
3388 | iexplore.exe | OPTIONS | 400 | 216.58.205.232:80 | http://www.googletagmanager.com/ | US | html | 1.52 Kb | whitelisted |
3388 | iexplore.exe | OPTIONS | 400 | 216.58.205.232:80 | http://www.googletagmanager.com/ | US | html | 1.52 Kb | whitelisted |
3388 | iexplore.exe | OPTIONS | 400 | 216.58.205.232:80 | http://www.googletagmanager.com/ | US | html | 1.52 Kb | whitelisted |
3388 | iexplore.exe | OPTIONS | 400 | 216.58.205.232:80 | http://www.googletagmanager.com/ | US | html | 1.52 Kb | whitelisted |
3388 | iexplore.exe | OPTIONS | 400 | 216.58.205.232:80 | http://www.googletagmanager.com/ | US | html | 1.52 Kb | whitelisted |
2700 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
3388 | iexplore.exe | OPTIONS | 400 | 216.58.205.232:80 | http://www.googletagmanager.com/ | US | html | 1.52 Kb | whitelisted |
3388 | iexplore.exe | OPTIONS | 400 | 216.58.205.232:80 | http://www.googletagmanager.com/ | US | html | 1.52 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3388 | iexplore.exe | 216.58.207.67:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2700 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3388 | iexplore.exe | 172.217.22.106:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
— | — | 216.58.210.14:137 | maps.google.com | Google Inc. | US | whitelisted |
2296 | iexplore.exe | 172.217.22.106:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
4 | System | 216.58.210.14:445 | maps.google.com | Google Inc. | US | whitelisted |
2296 | iexplore.exe | 216.58.205.232:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
2296 | iexplore.exe | 64.233.167.155:443 | stats.g.doubleclick.net | Google Inc. | US | whitelisted |
2296 | iexplore.exe | 216.58.207.67:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2296 | iexplore.exe | 216.58.208.46:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
trieca.com |
| unknown |
fonts.googleapis.com |
| whitelisted |
www.bing.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
maps.google.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
connect.facebook.net |
| whitelisted |
stats.g.doubleclick.net |
| whitelisted |
www.google.com |
| malicious |
Threats
10 ETPRO signatures available at the full report