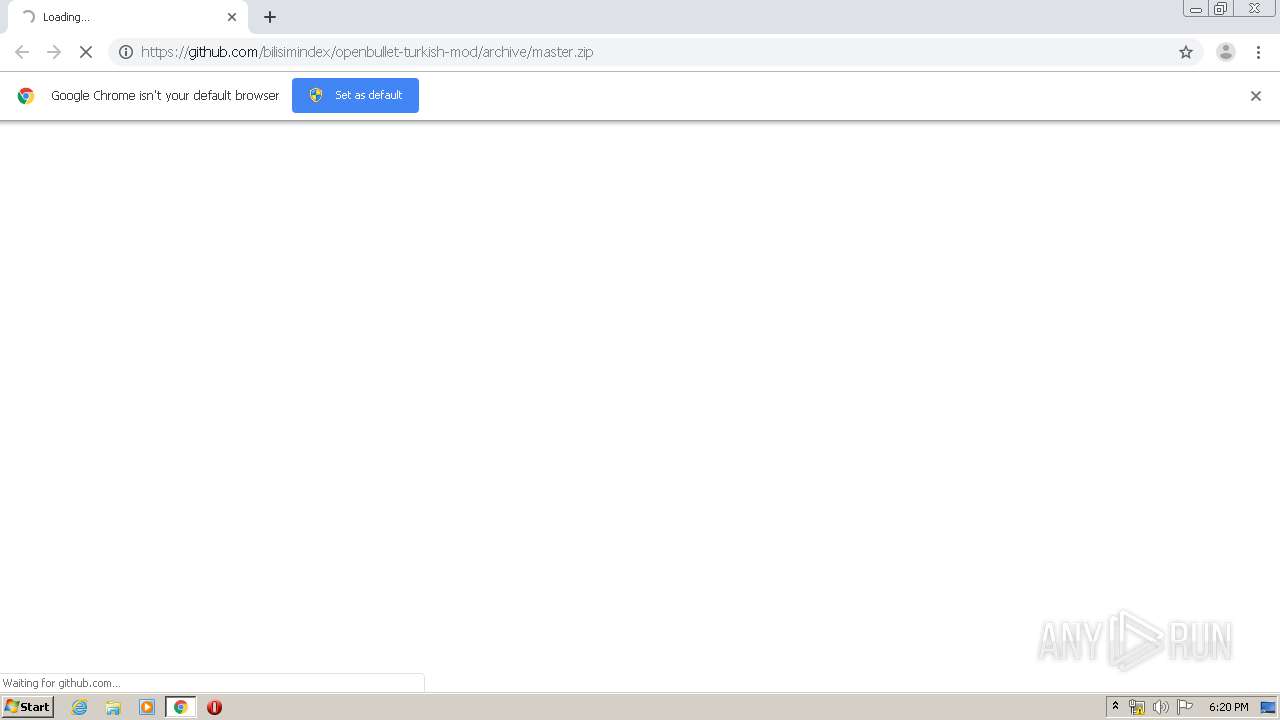
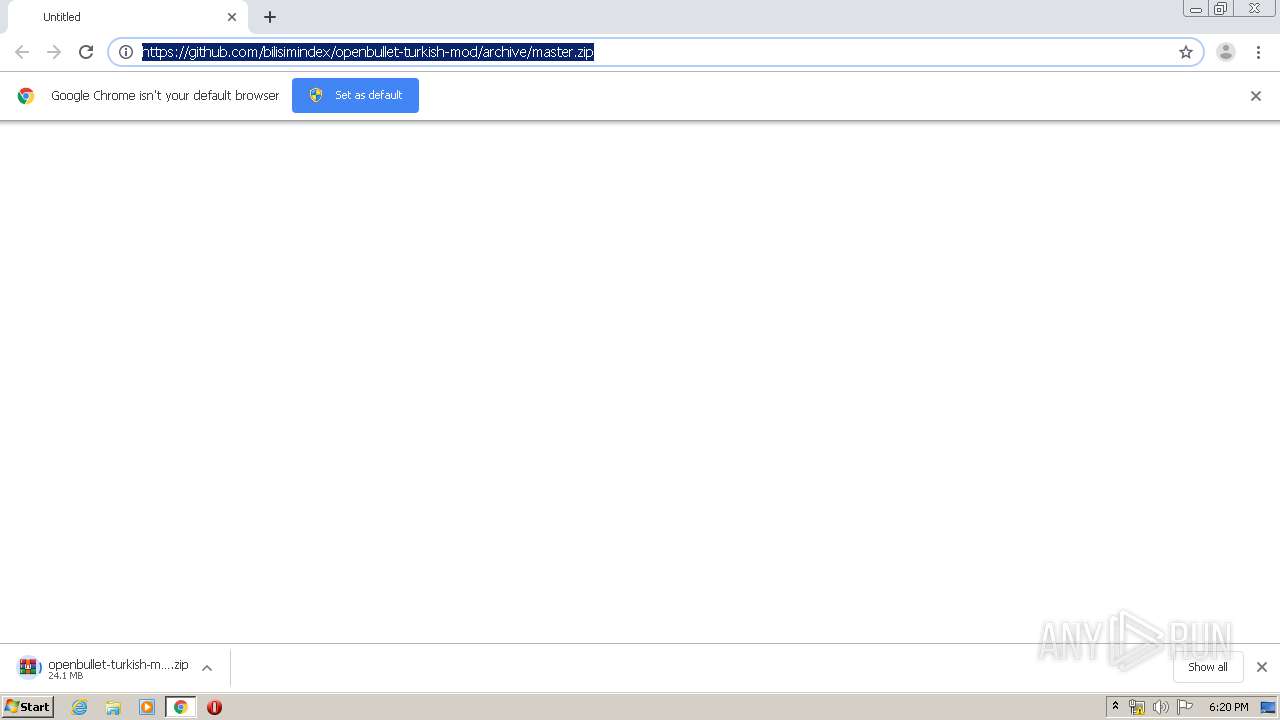
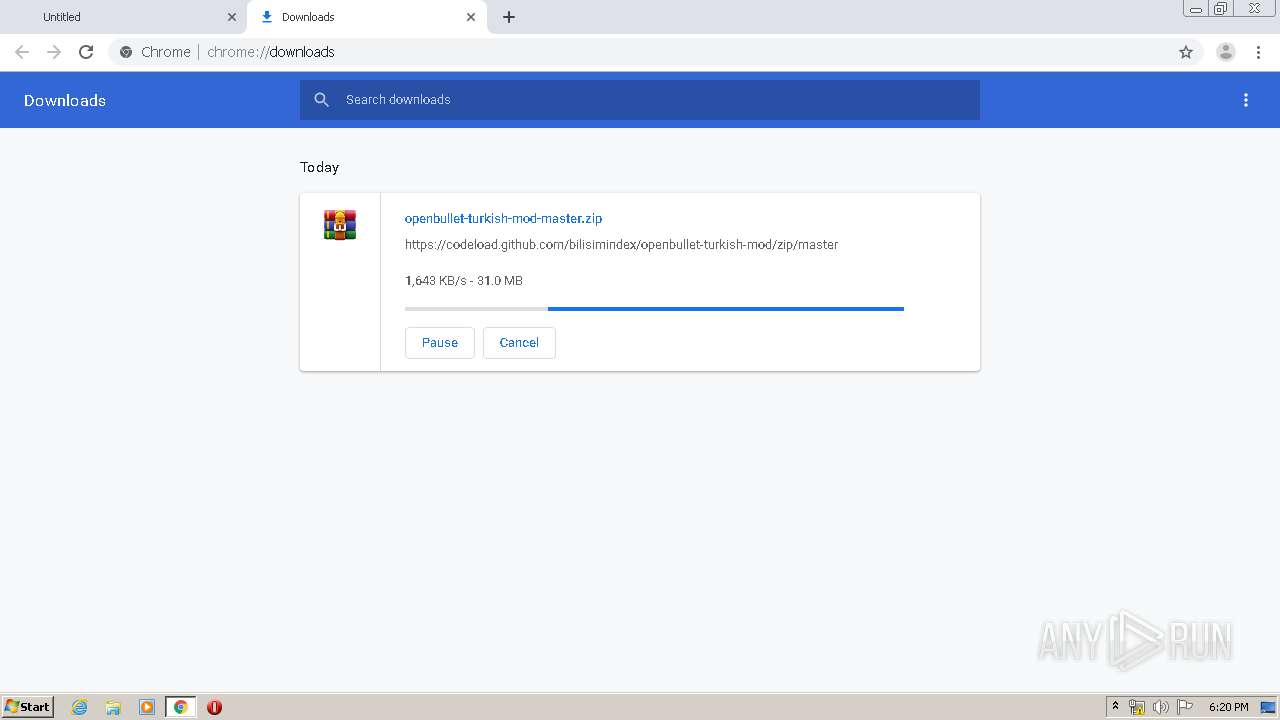
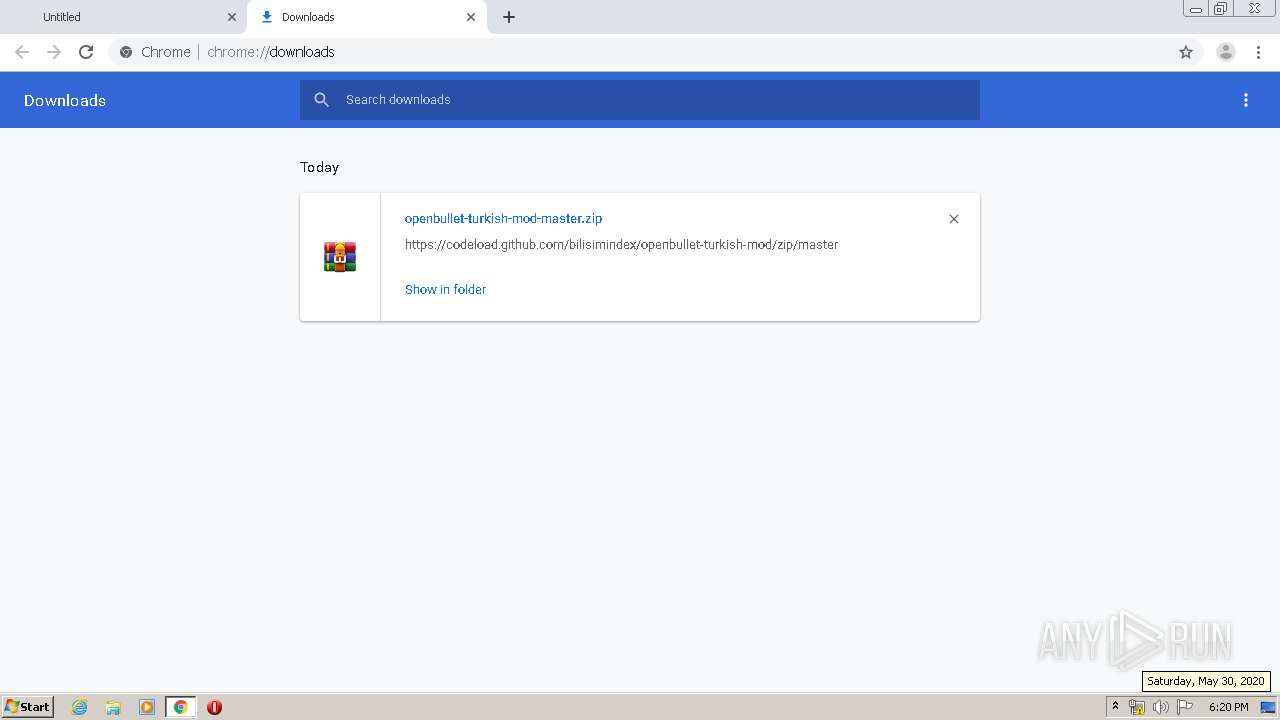
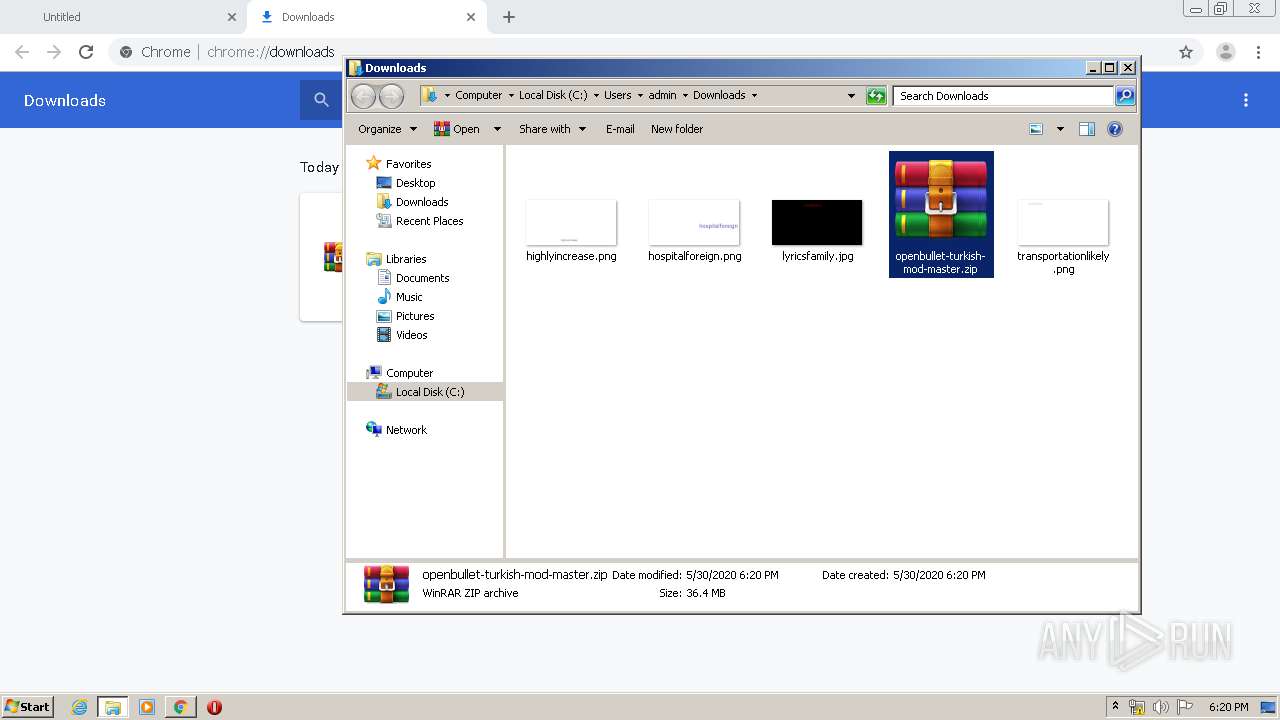
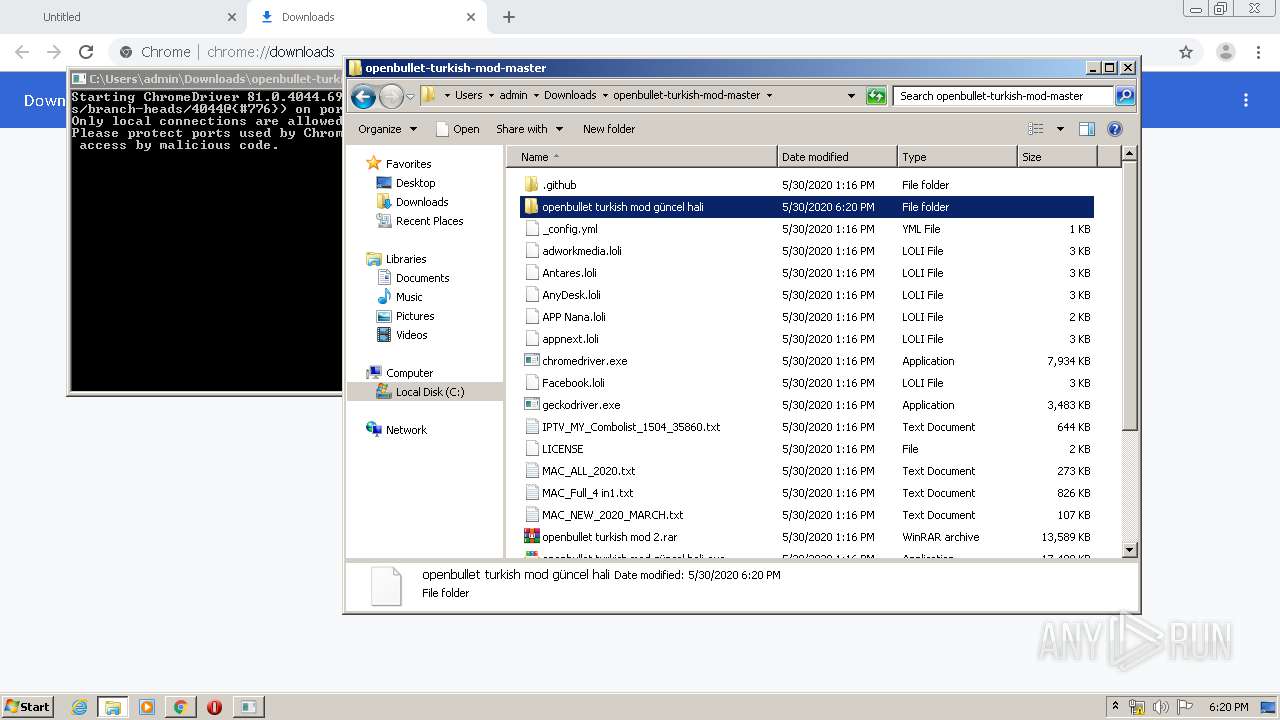
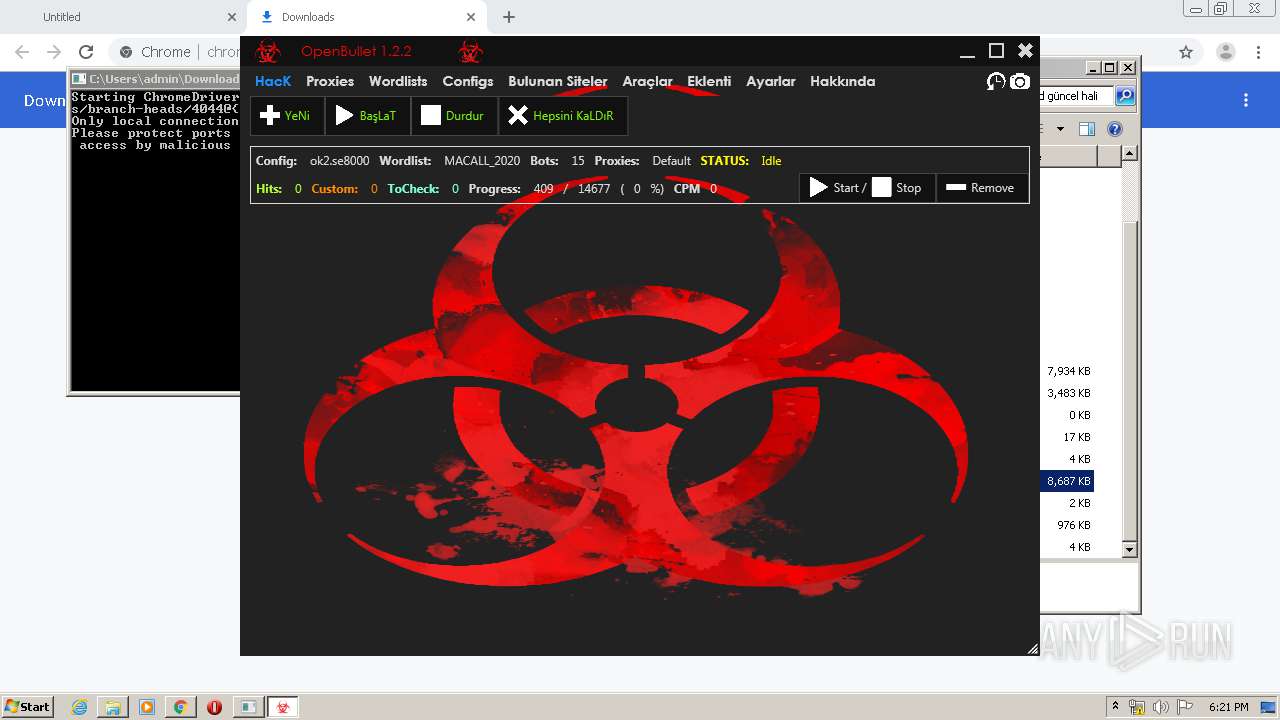
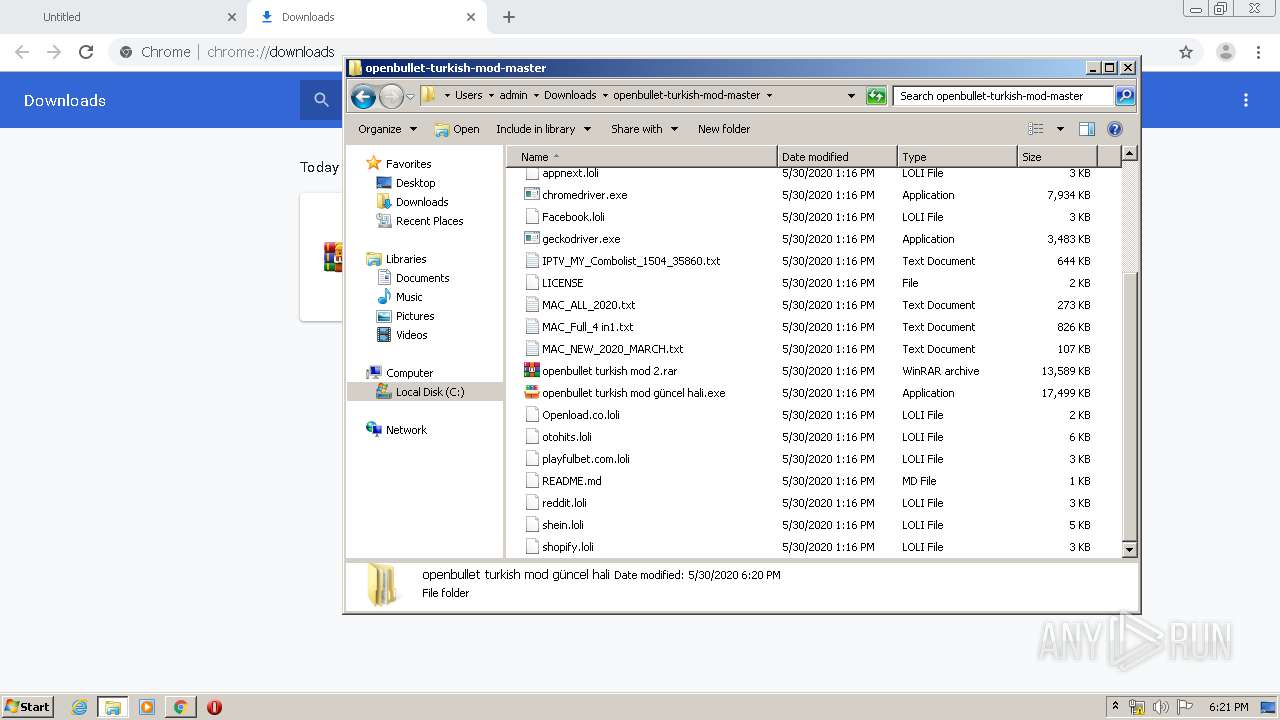
| URL: | https://github.com/bilisimindex/openbullet-turkish-mod/archive/master.zip |
| Full analysis: | https://app.any.run/tasks/397ffa83-521e-413c-a35f-09a96f76194a |
| Verdict: | Malicious activity |
| Analysis date: | May 30, 2020, 17:19:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | F2050CFE4FF4128AF4BE892677E531A3 |
| SHA1: | 844056D2AB149DB46C806ACD699653CBC8C99C20 |
| SHA256: | BBC482BECF420651D81B37409F242E642089E28C10AD49B22CA481910A53F621 |
| SSDEEP: | 3:N8tEd3Ic6qTK1EGNSJo:2uC/qGtMJo |
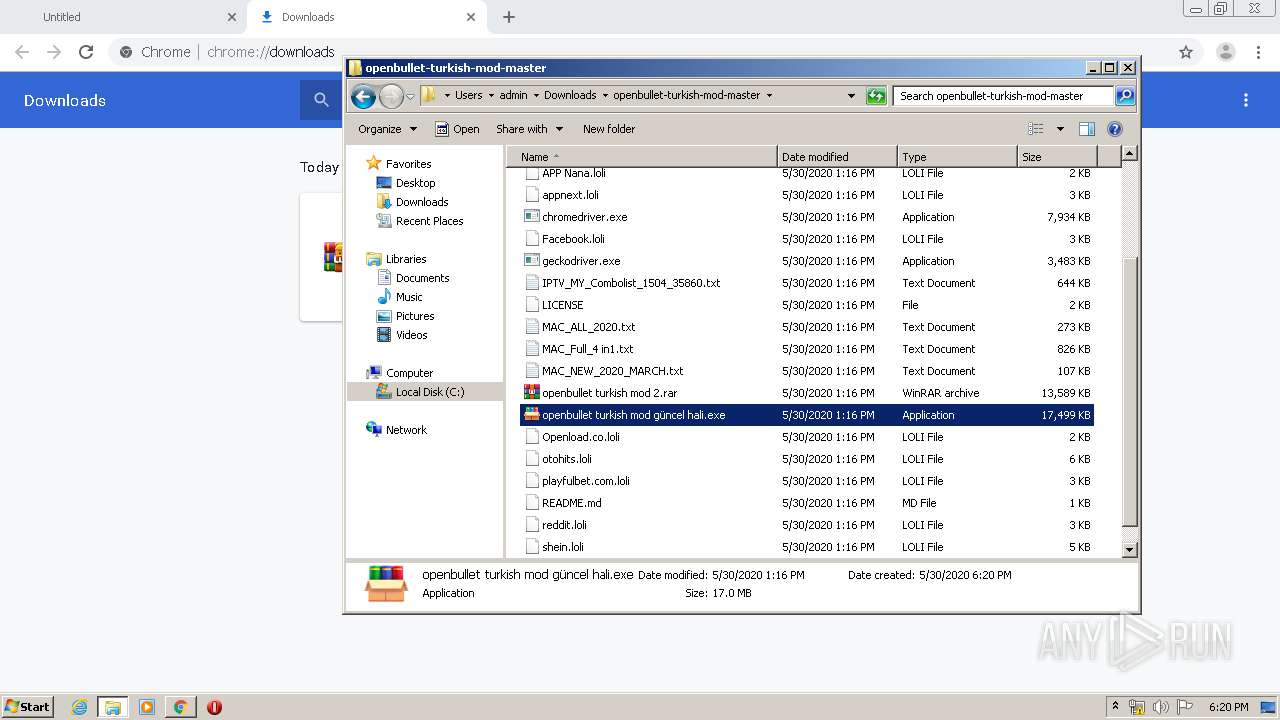
MALICIOUS
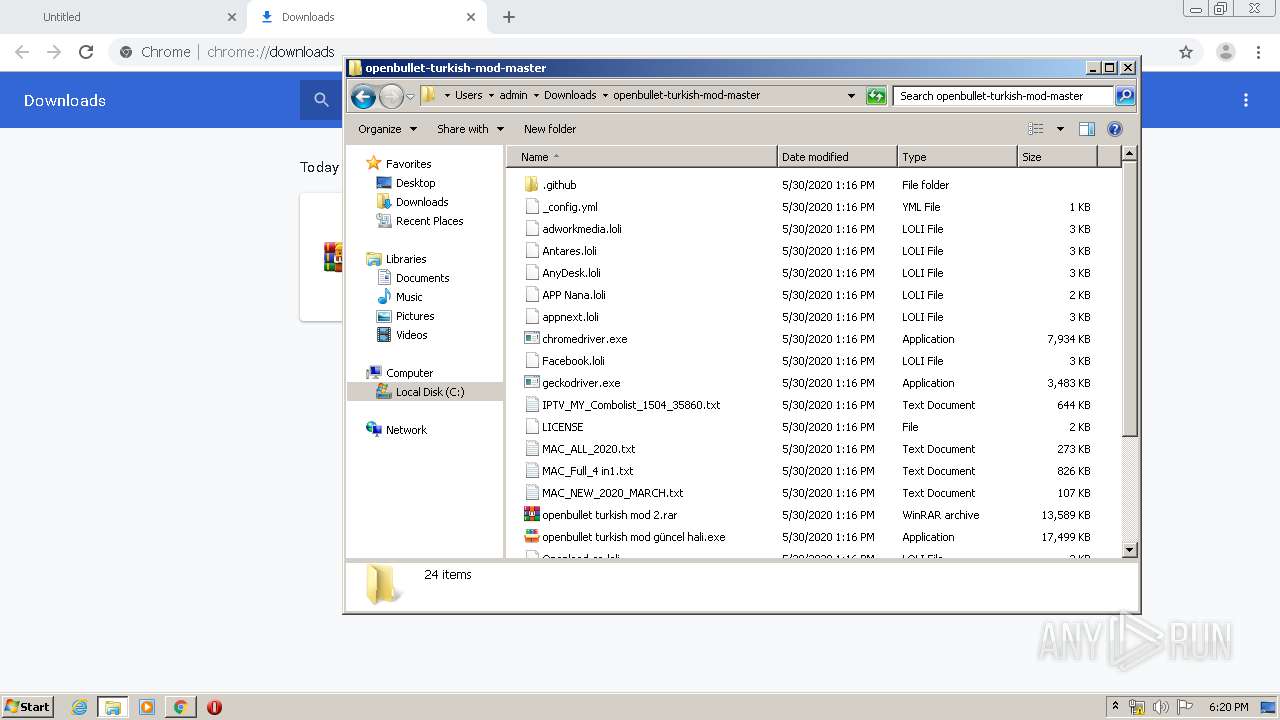
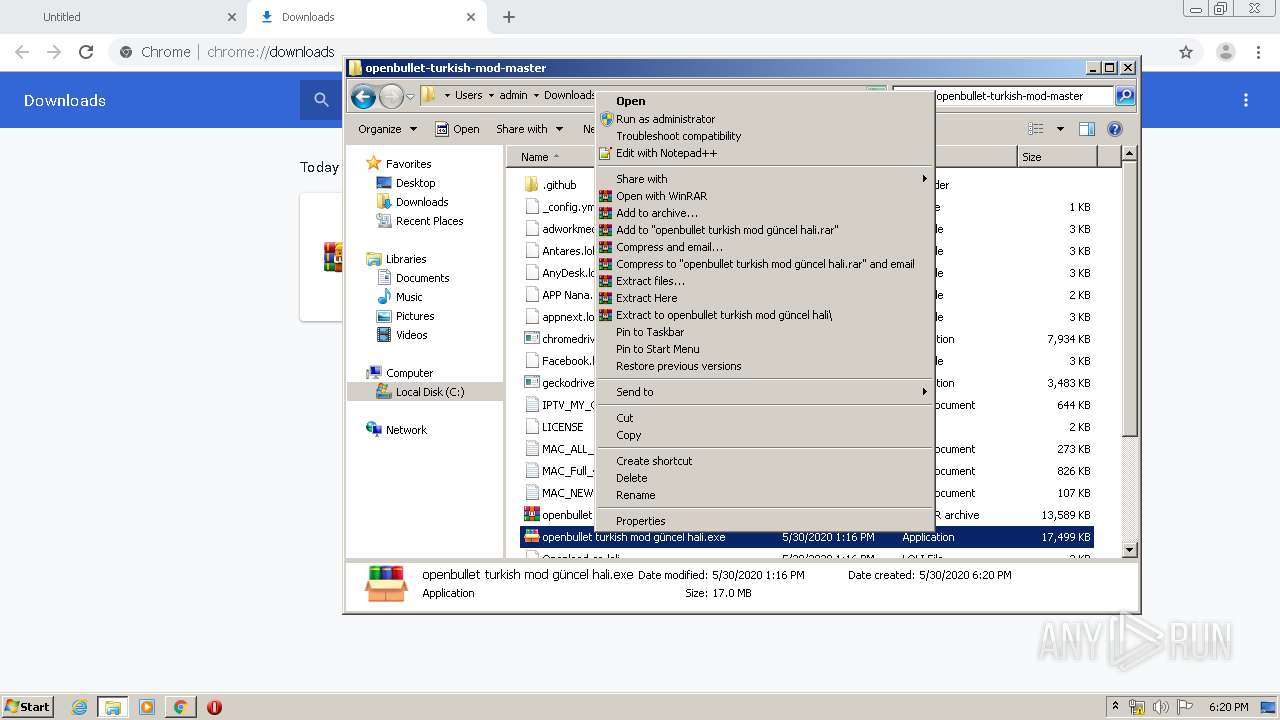
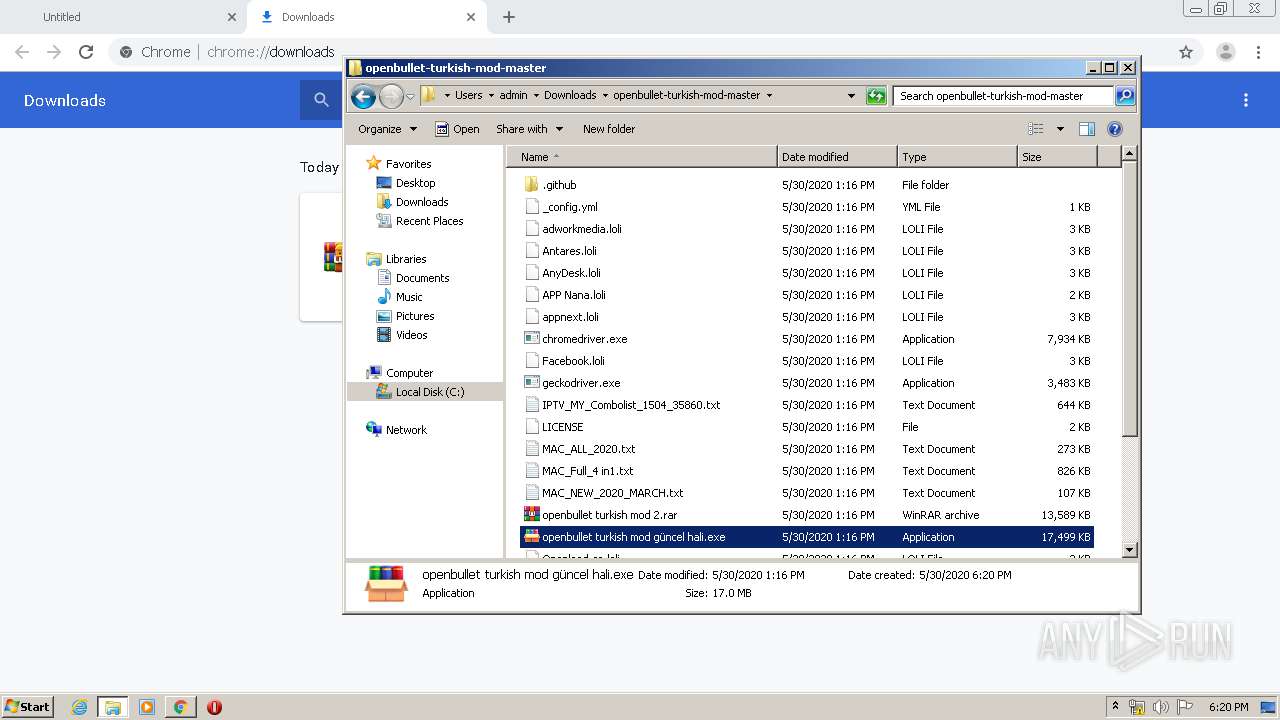
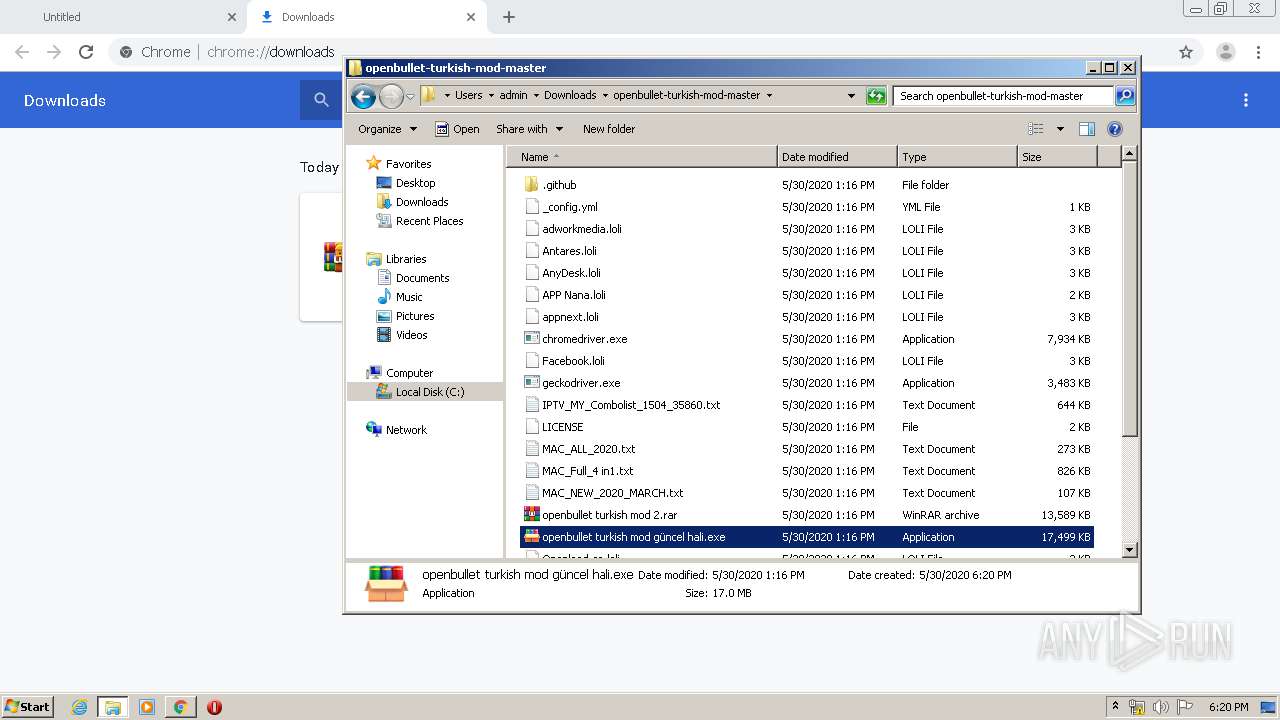
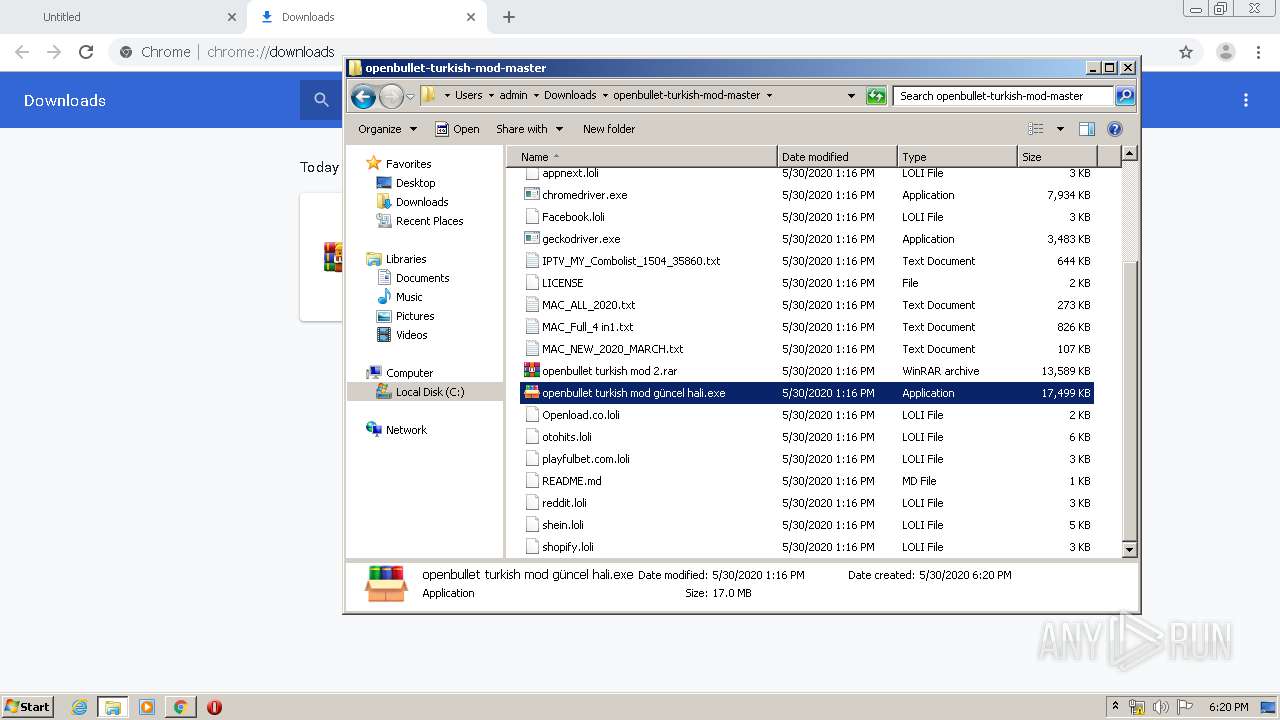
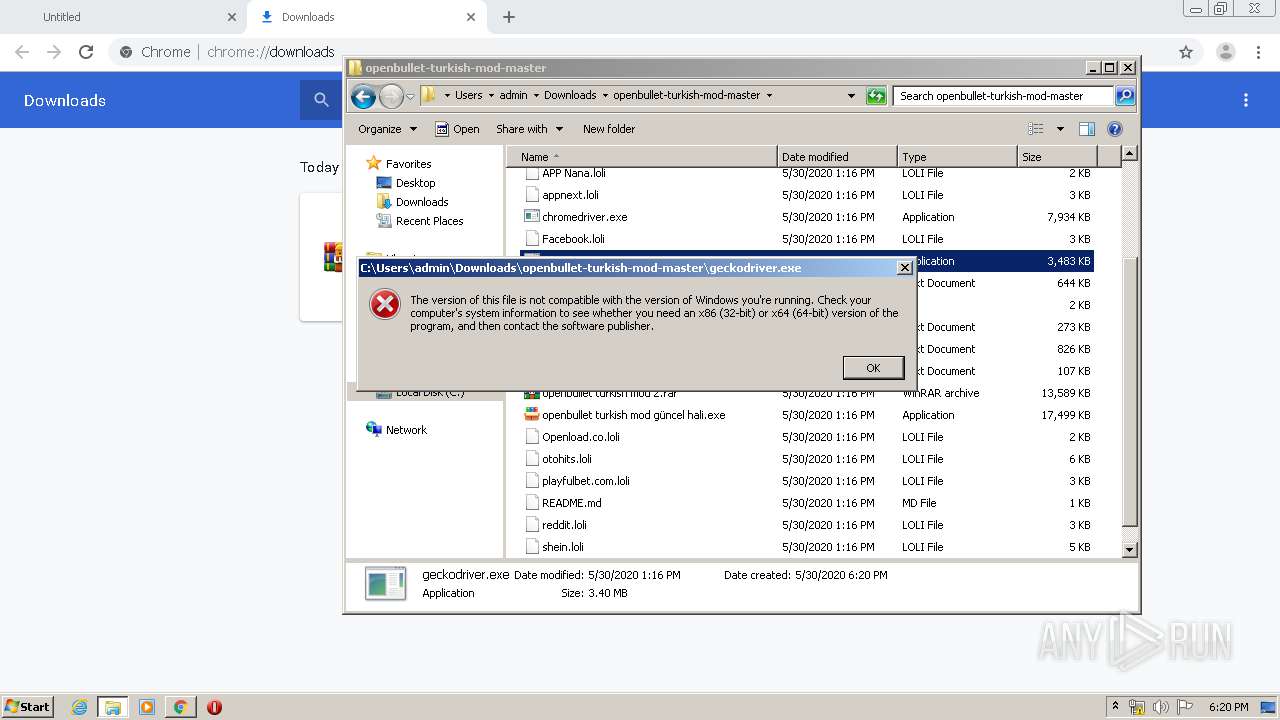
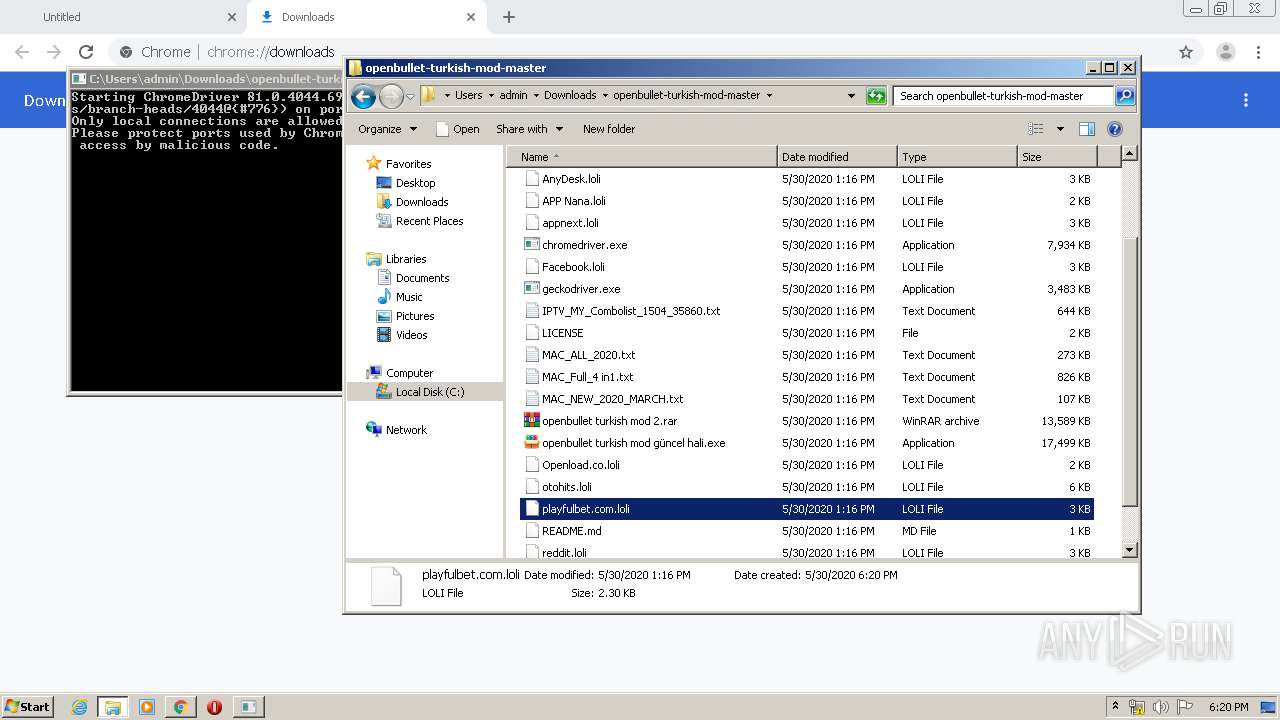
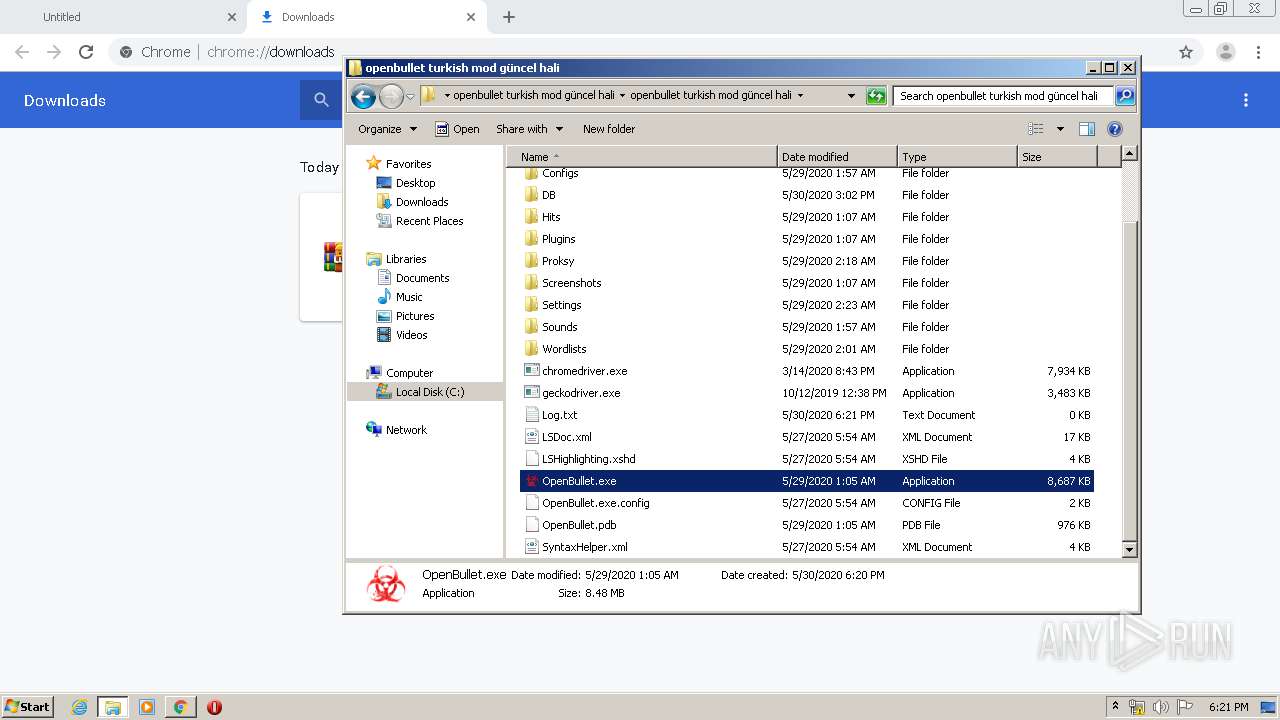
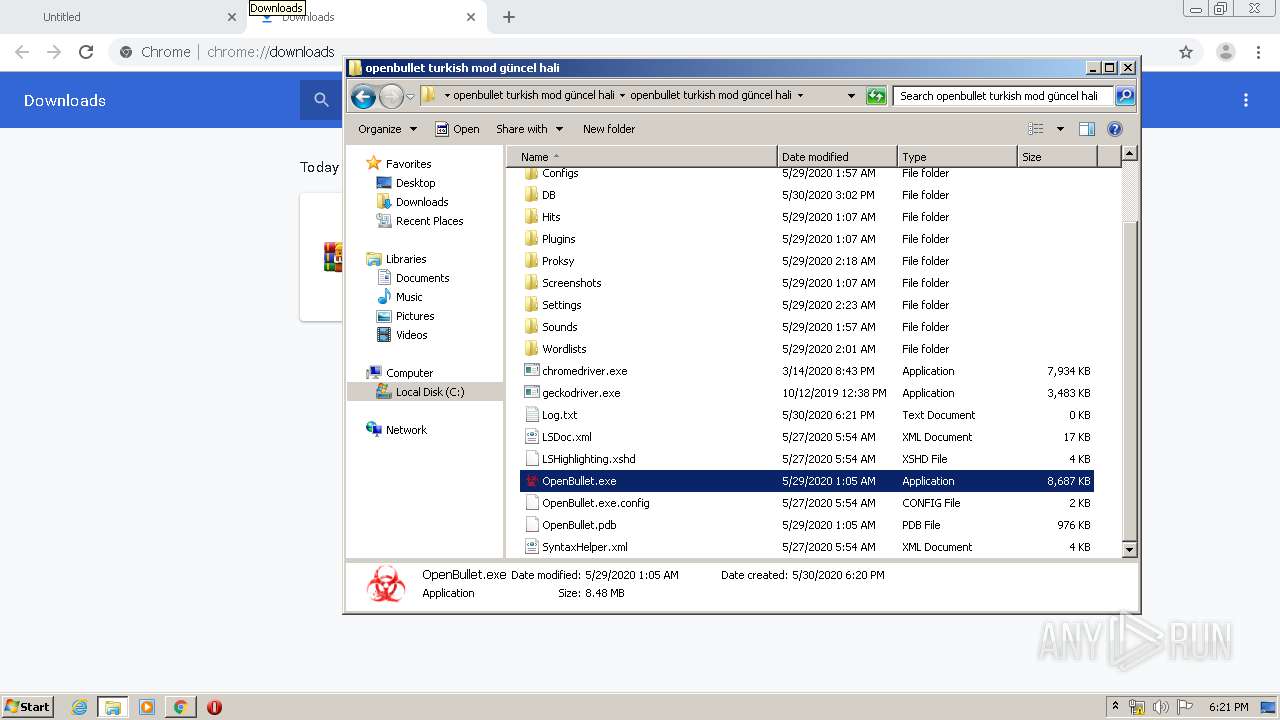
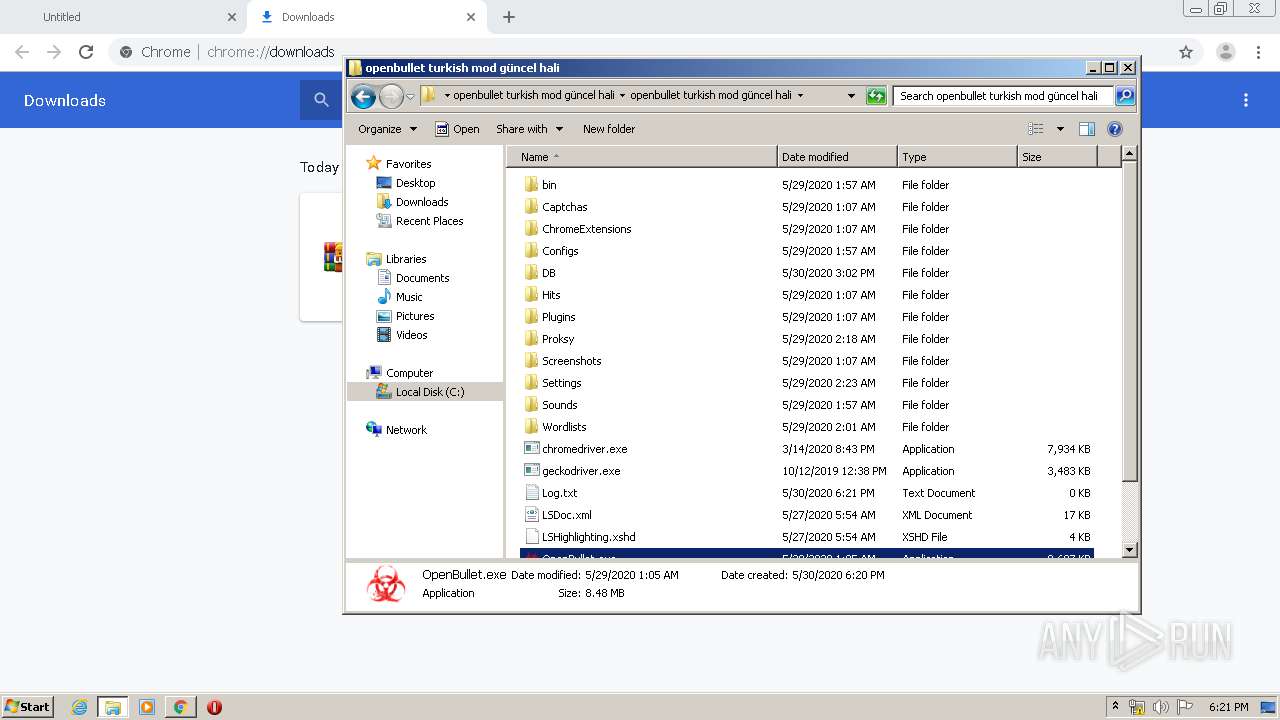
Application was dropped or rewritten from another process
- openbullet turkish mod güncel hali.exe (PID: 2384)
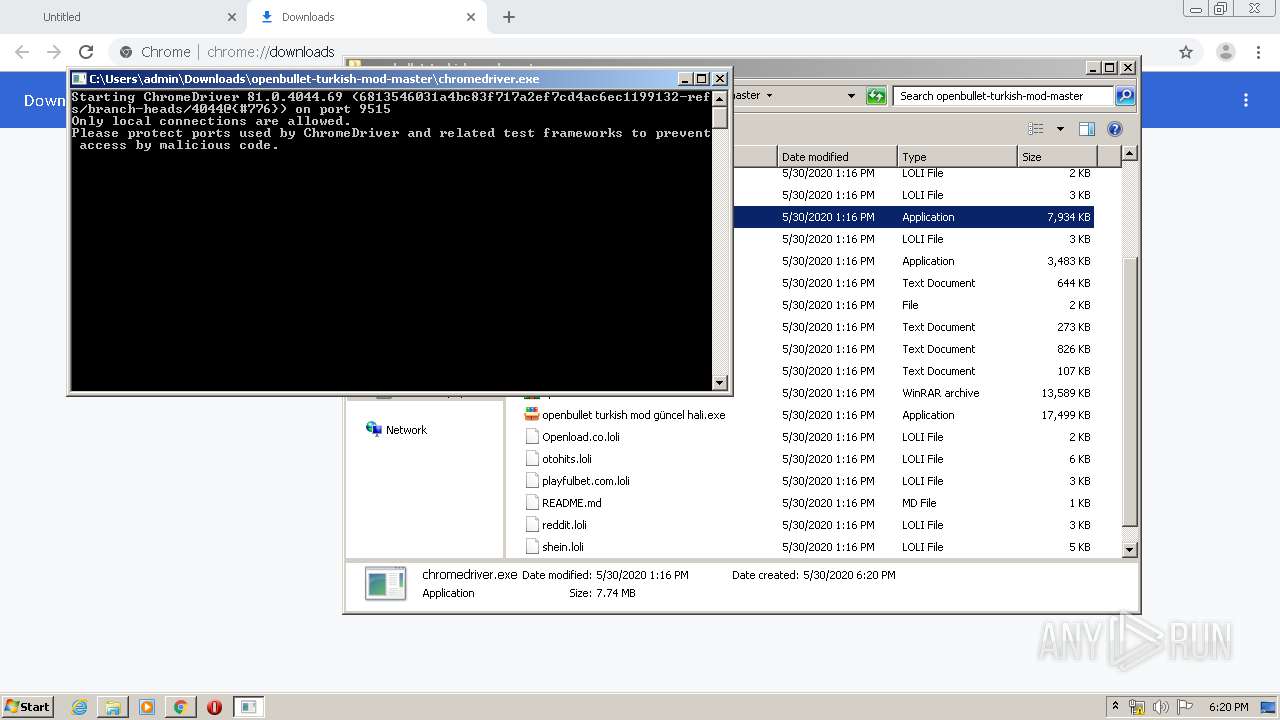
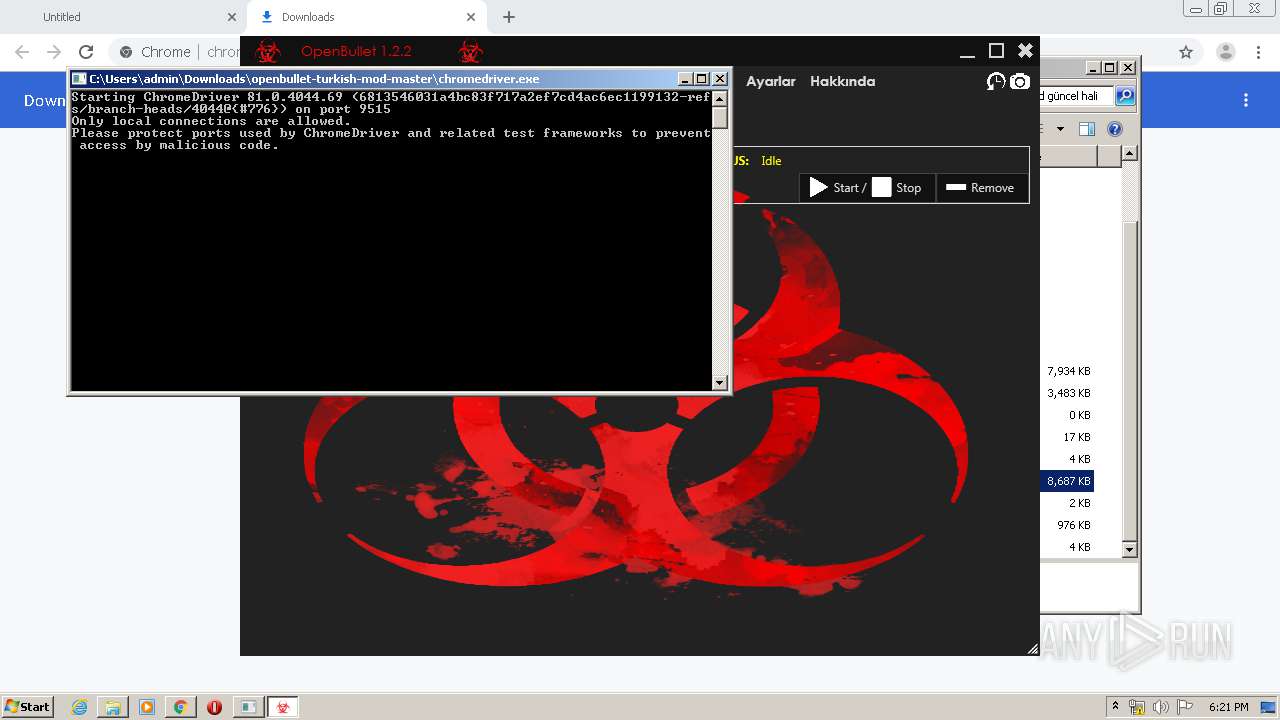
- chromedriver.exe (PID: 3708)
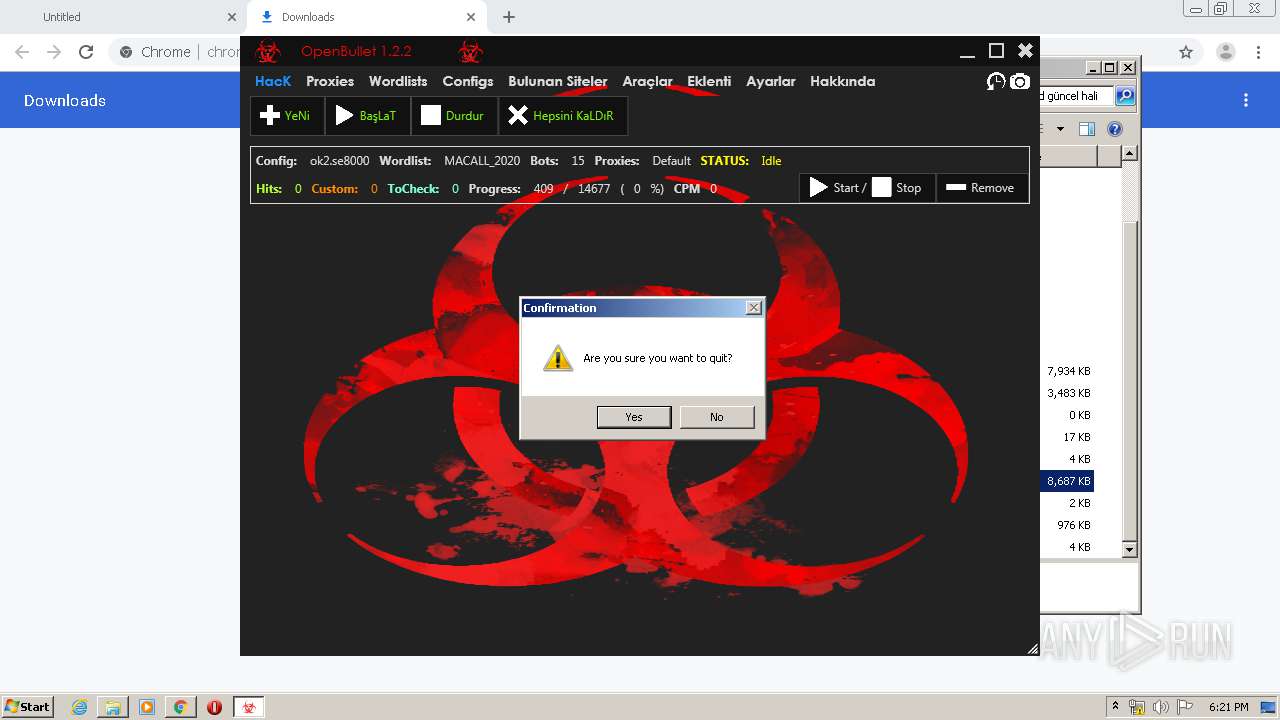
- OpenBullet.exe (PID: 1828)
Actions looks like stealing of personal data
- WinRAR.exe (PID: 2668)
- SearchProtocolHost.exe (PID: 3504)
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3504)
- OpenBullet.exe (PID: 1828)
SUSPICIOUS
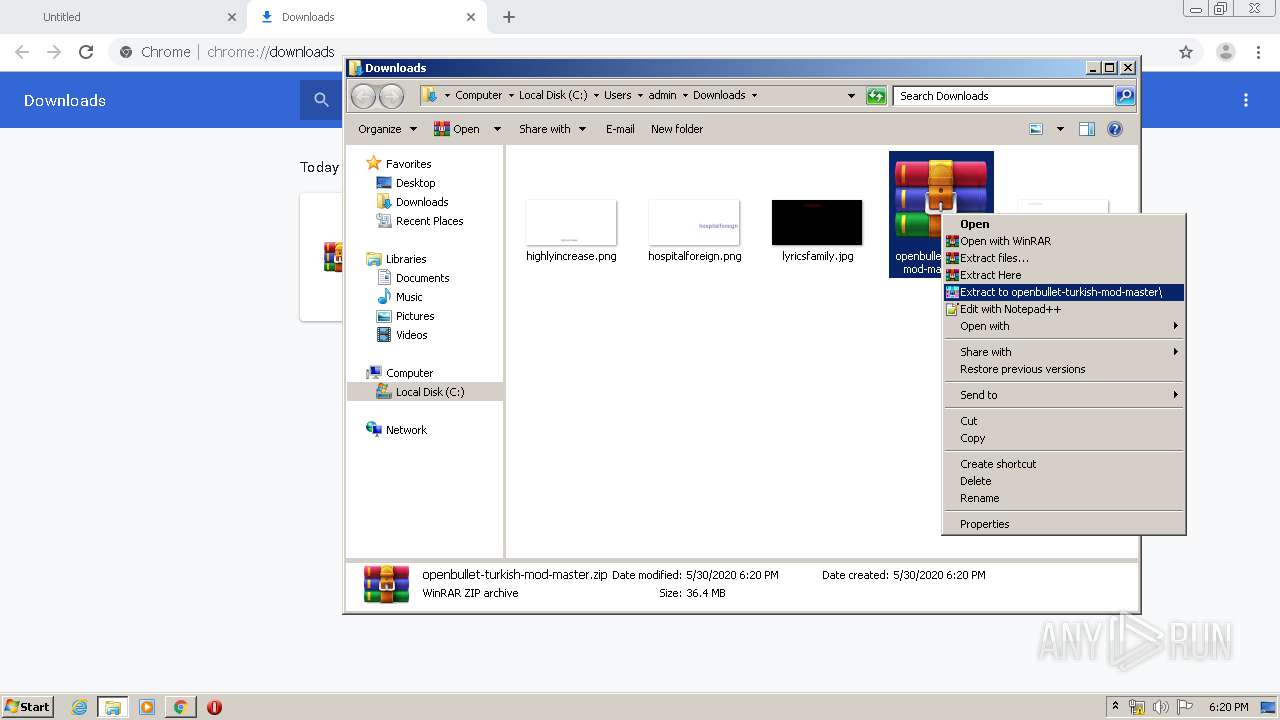
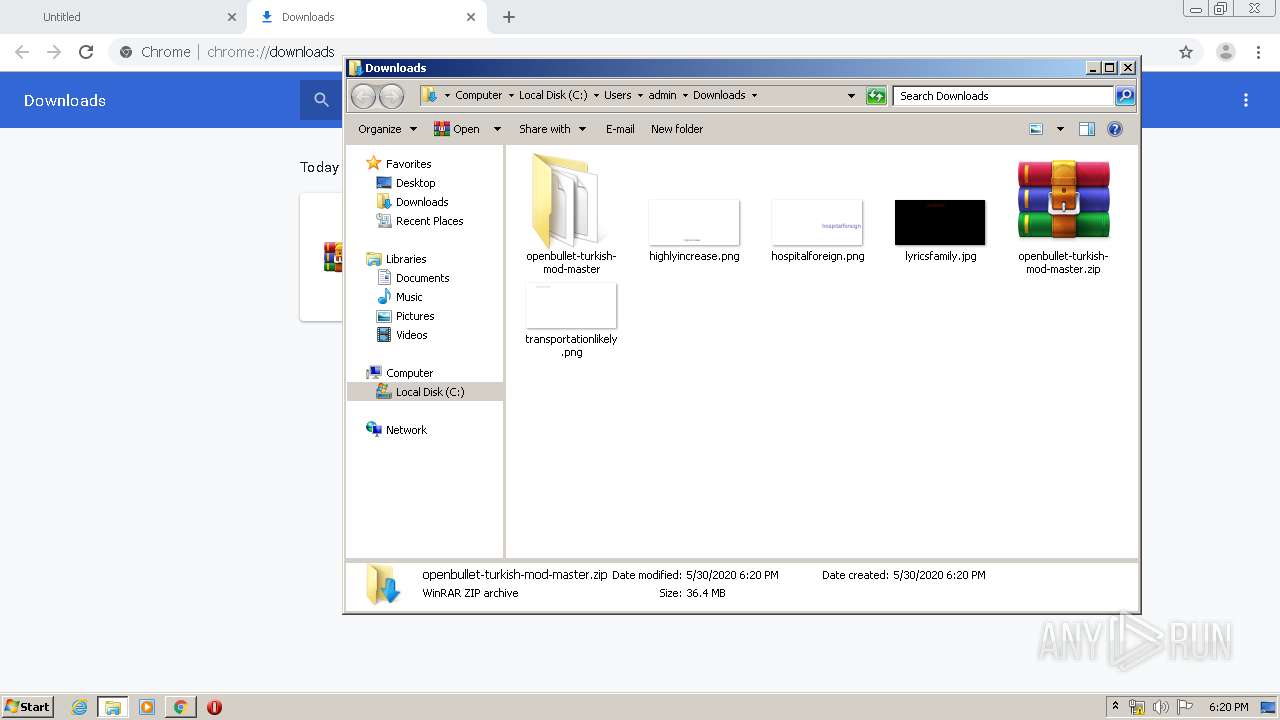
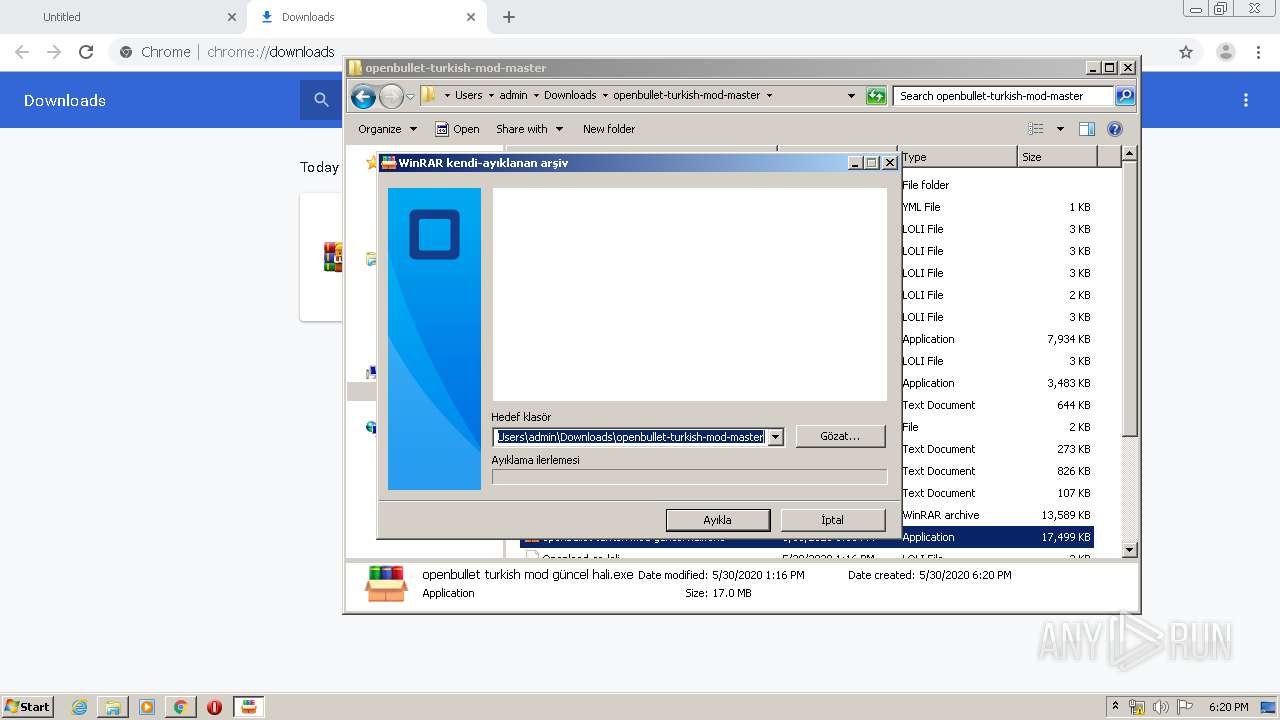
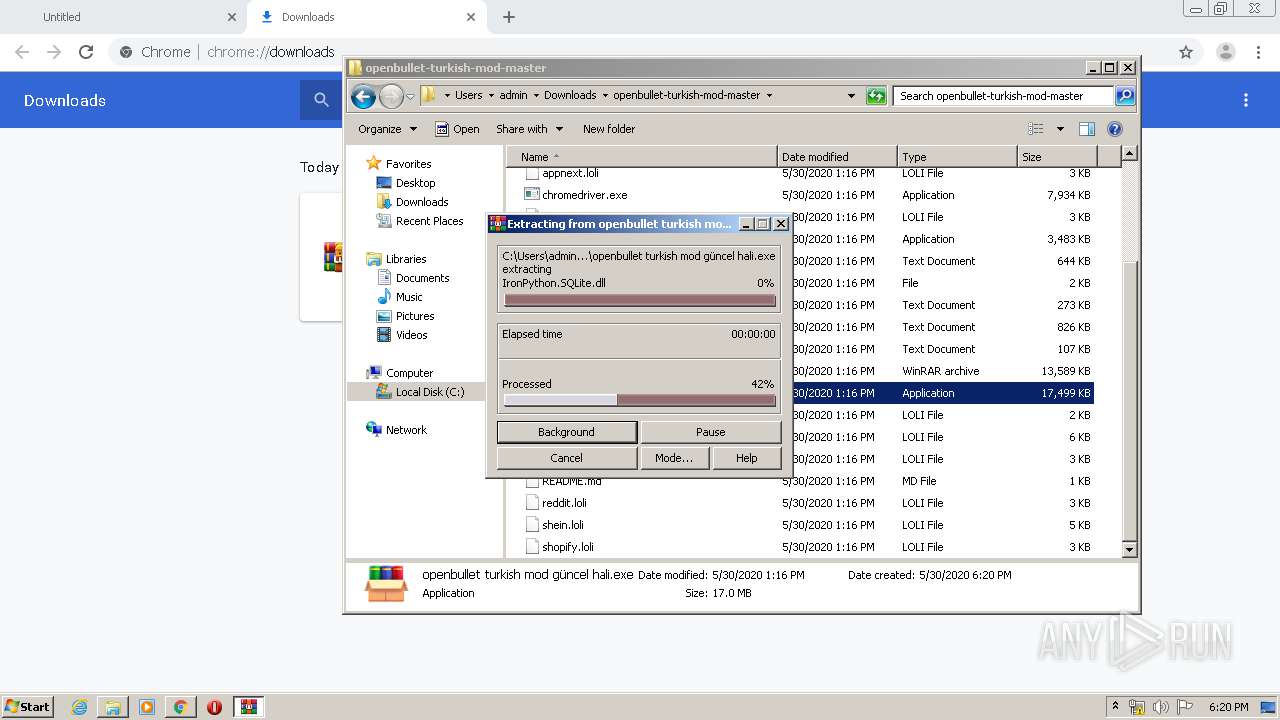
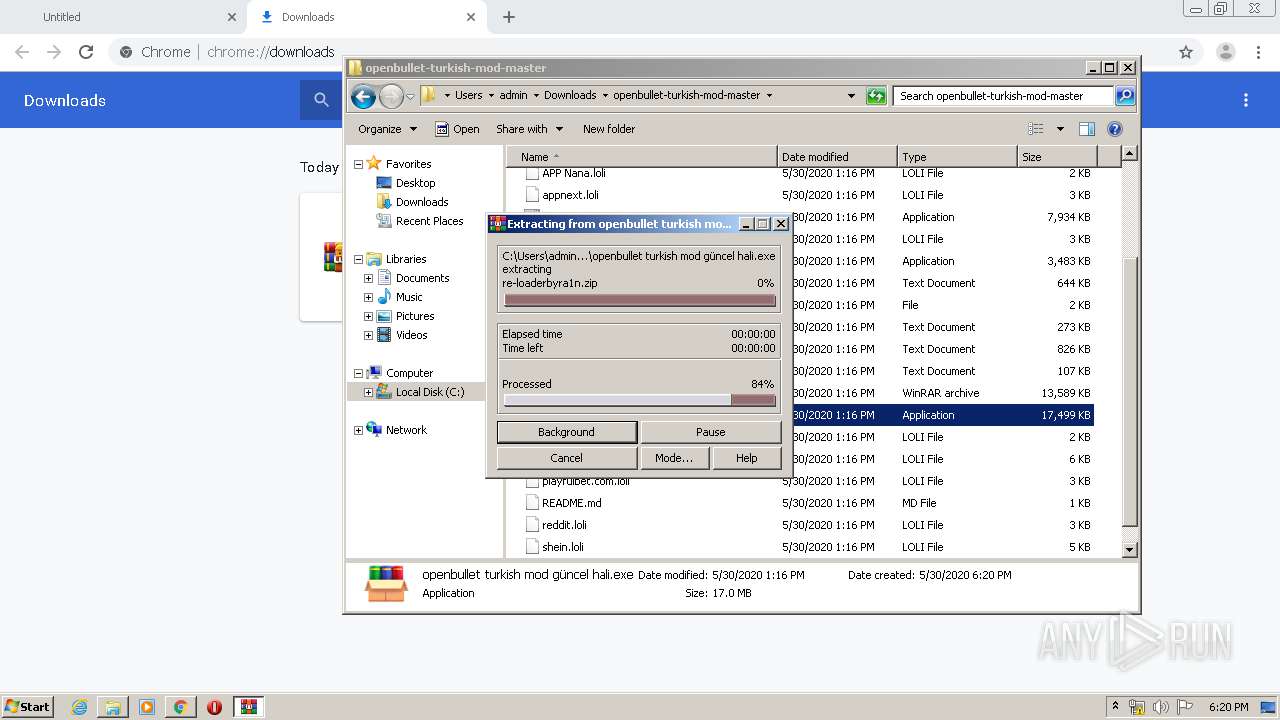
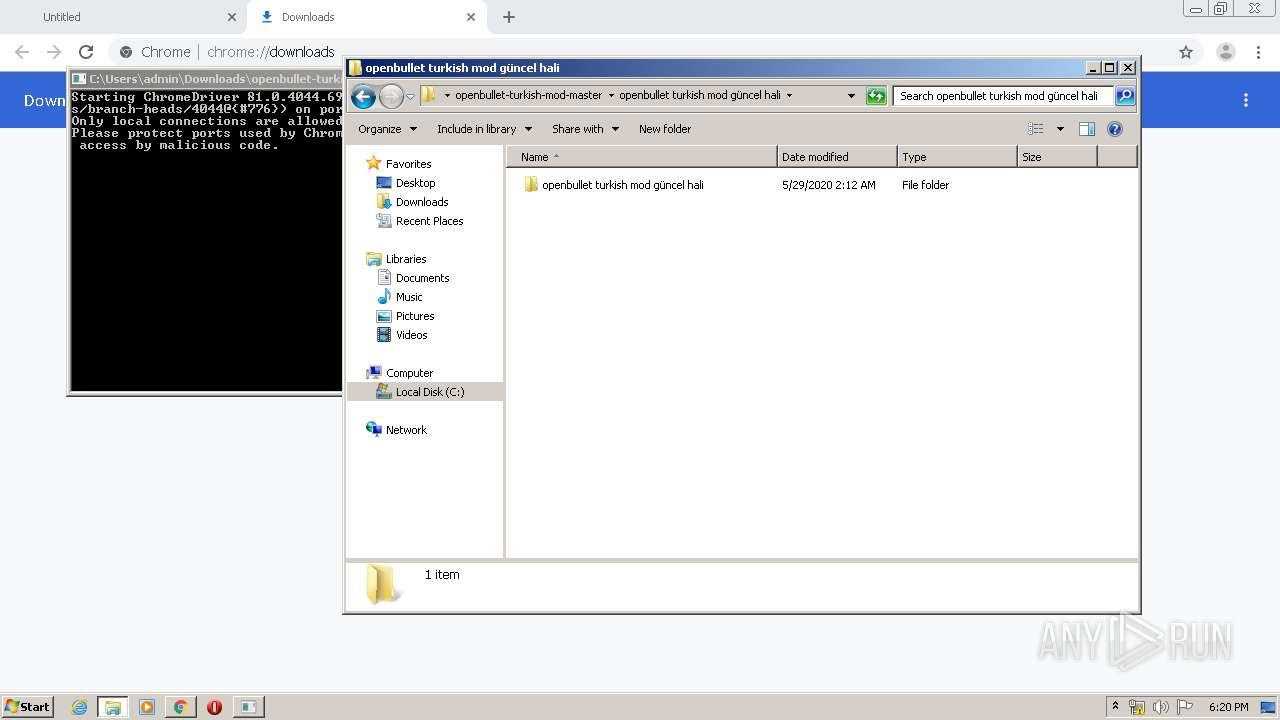
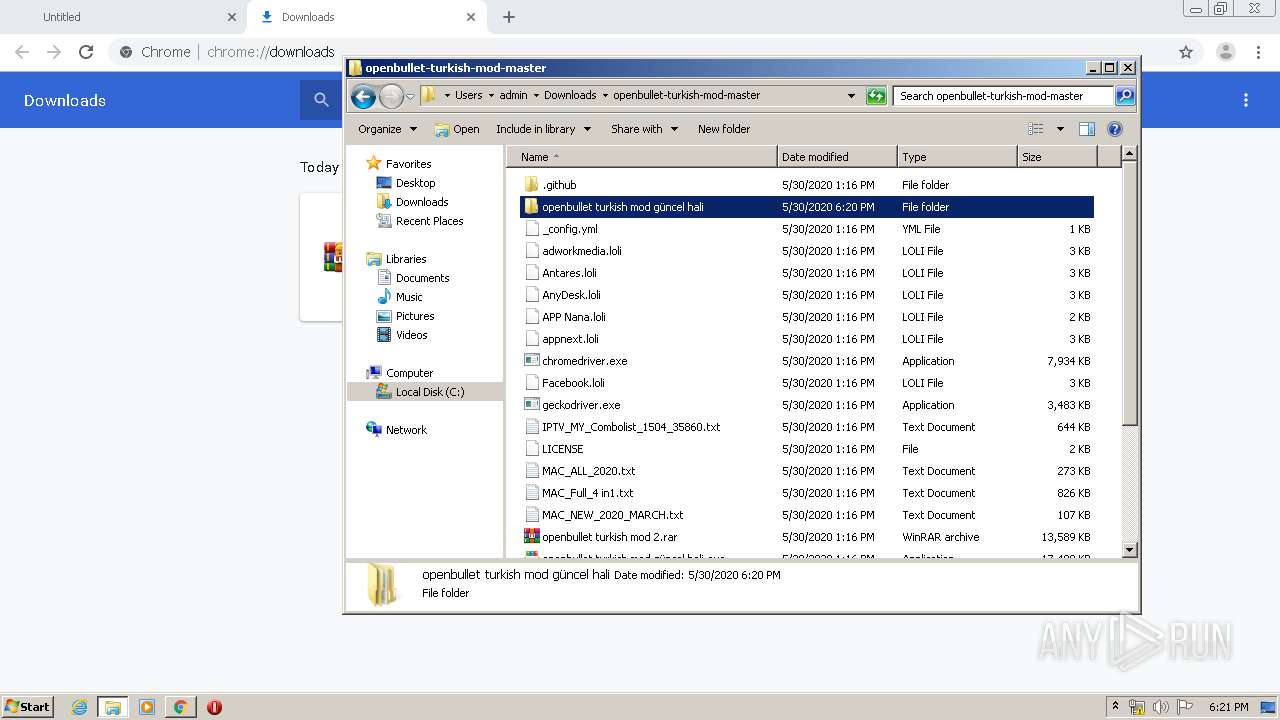
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2668)
- WinRAR.exe (PID: 2460)
Reads Internet Cache Settings
- openbullet turkish mod güncel hali.exe (PID: 2384)
Reads internet explorer settings
- openbullet turkish mod güncel hali.exe (PID: 2384)
INFO
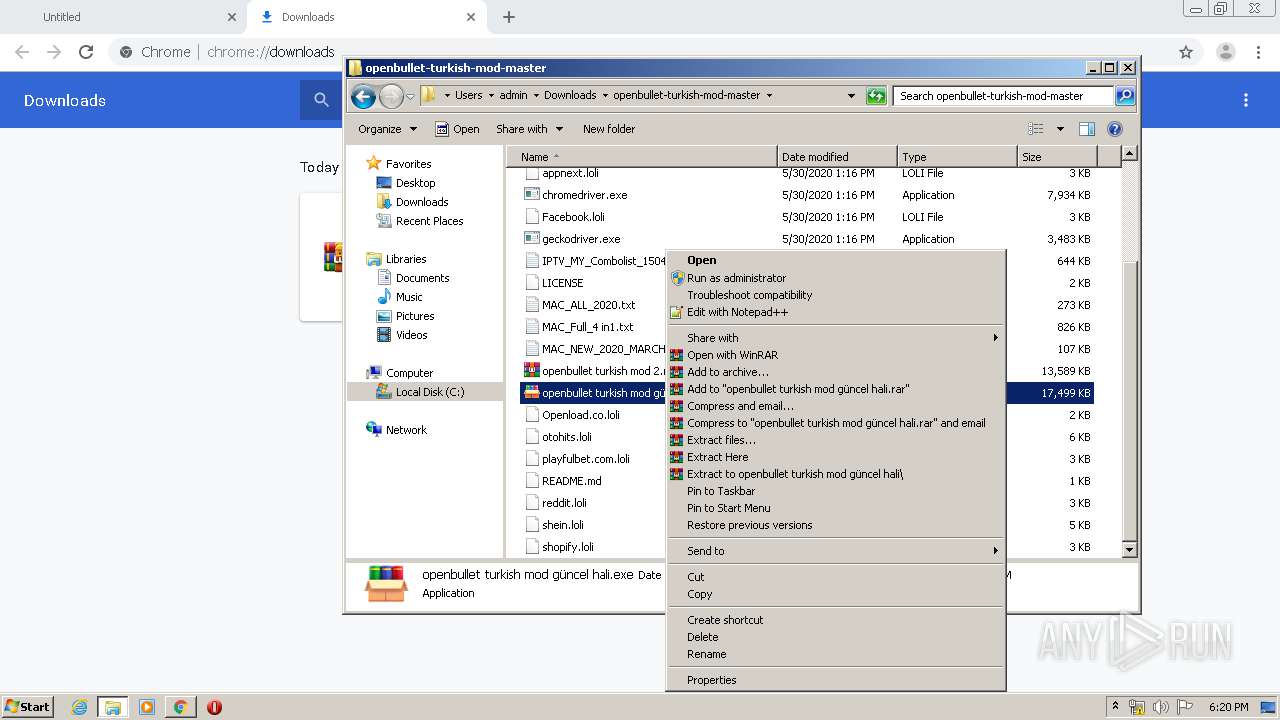
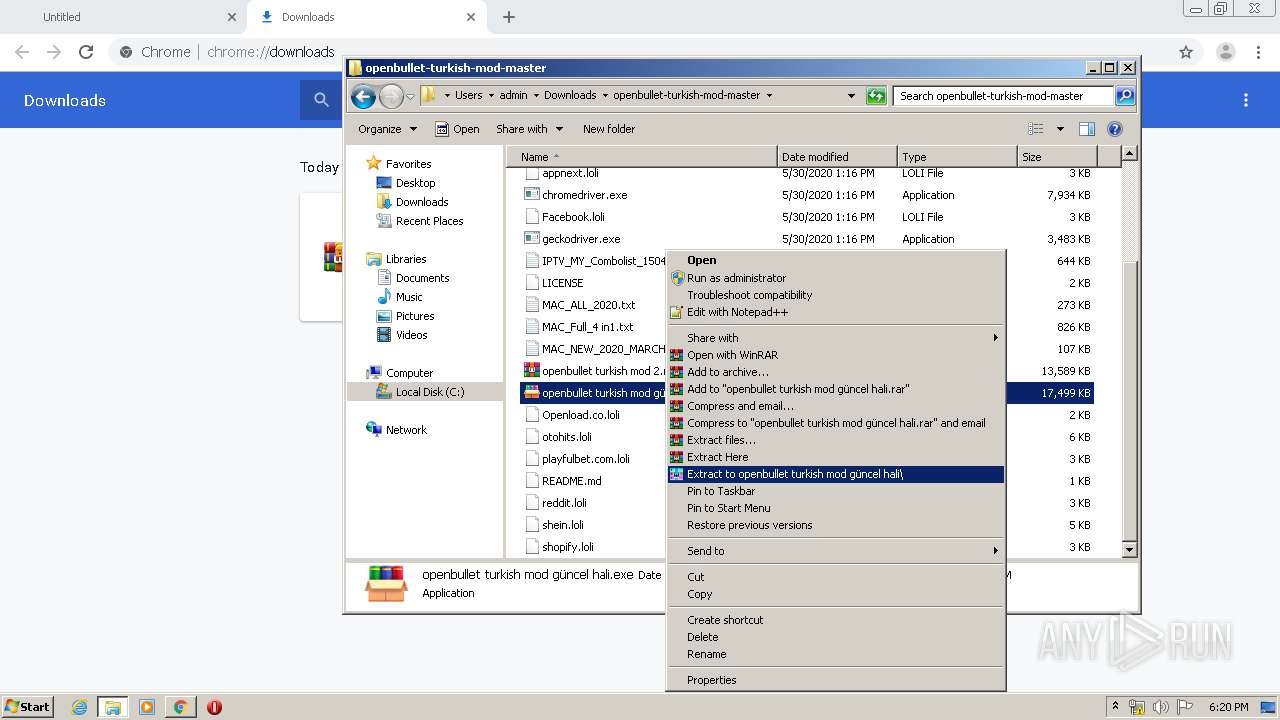
Manual execution by user
- openbullet turkish mod güncel hali.exe (PID: 2384)
- WinRAR.exe (PID: 2668)
- chromedriver.exe (PID: 3708)
- OpenBullet.exe (PID: 1828)
- WinRAR.exe (PID: 2460)
- WinRAR.exe (PID: 4000)
Reads Internet Cache Settings
- chrome.exe (PID: 2144)
Application launched itself
- chrome.exe (PID: 2144)
Reads the hosts file
- chrome.exe (PID: 2160)
- chrome.exe (PID: 2144)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
64
Monitored processes
20
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1196 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,104184781007503682,12396572969605735612,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13670821128619470314 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2288 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
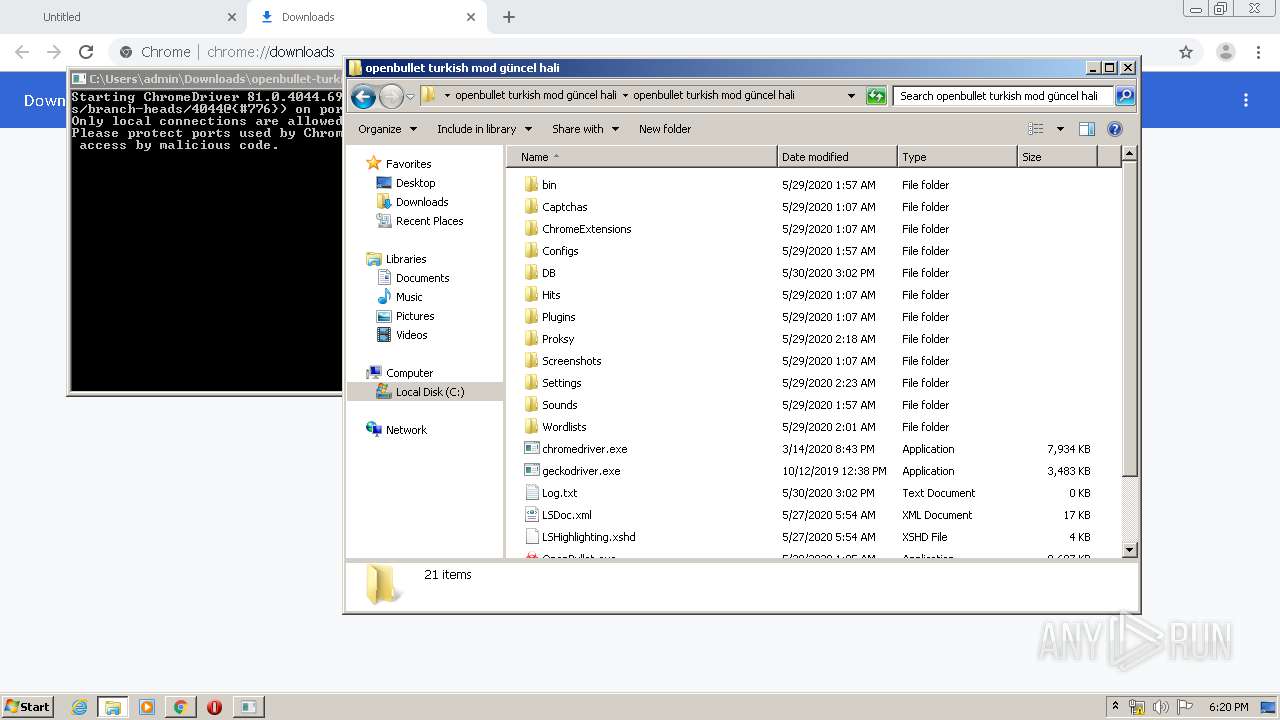
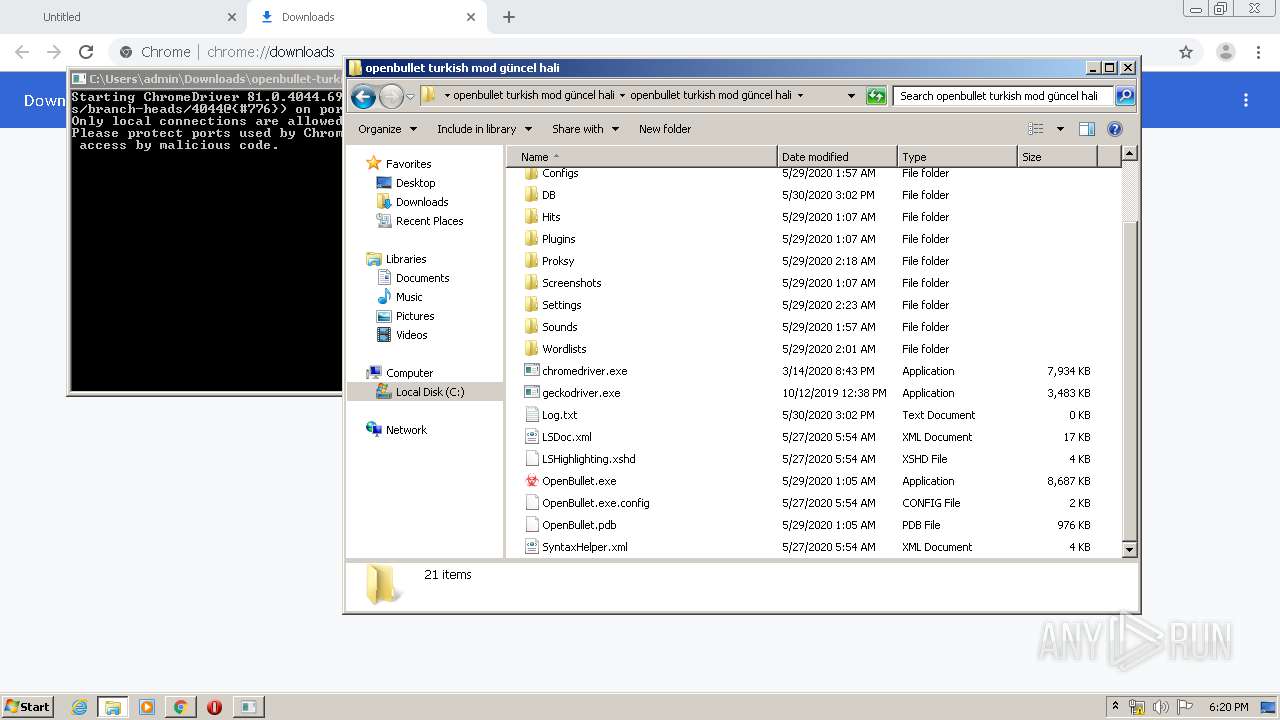
| 1828 | "C:\Users\admin\Downloads\openbullet-turkish-mod-master\openbullet turkish mod güncel hali\openbullet turkish mod güncel hali\OpenBullet.exe" | C:\Users\admin\Downloads\openbullet-turkish-mod-master\openbullet turkish mod güncel hali\openbullet turkish mod güncel hali\OpenBullet.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: OpenBullet Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2088 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,104184781007503682,12396572969605735612,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1013291010584447724 --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3620 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2144 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "https://github.com/bilisimindex/openbullet-turkish-mod/archive/master.zip" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2160 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,104184781007503682,12396572969605735612,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=11692563547845956885 --mojo-platform-channel-handle=1660 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2200 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1040,104184781007503682,12396572969605735612,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=4556839219279061097 --mojo-platform-channel-handle=1012 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2384 | "C:\Users\admin\Downloads\openbullet-turkish-mod-master\openbullet turkish mod güncel hali.exe" | C:\Users\admin\Downloads\openbullet-turkish-mod-master\openbullet turkish mod güncel hali.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 255 Modules
| |||||||||||||||
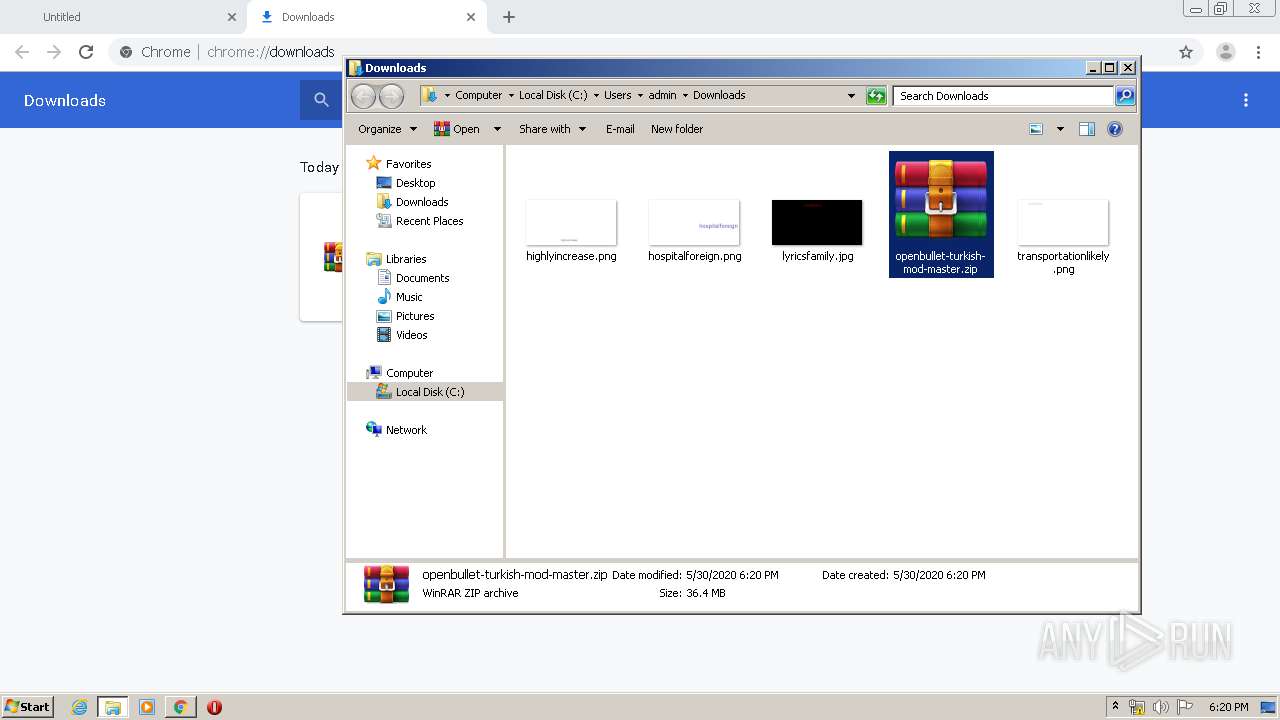
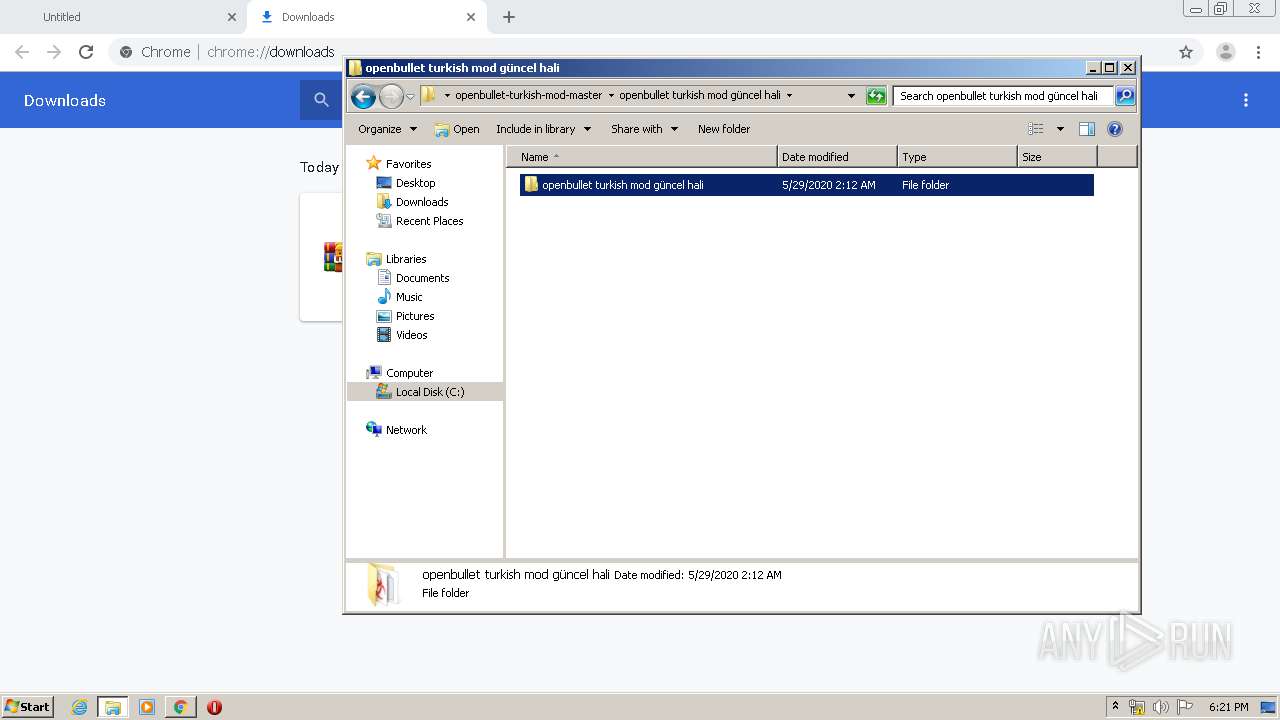
| 2460 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Downloads\openbullet-turkish-mod-master.zip" C:\Users\admin\Downloads\ | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2620 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1040,104184781007503682,12396572969605735612,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=5227459715083252909 --mojo-platform-channel-handle=3484 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2640 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2132 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 468
Read events
1 383
Write events
82
Delete events
3
Modification events
| (PID) Process: | (2144) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2144) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2144) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2144) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2144) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2640) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2144-13235332799011375 |
Value: 259 | |||
| (PID) Process: | (2144) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2144) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2144) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (2144) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
37
Suspicious files
10
Text files
394
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2144 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5ED295BF-860.pma | — | |
MD5:— | SHA256:— | |||
| 2144 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ea132d14-a715-4ed8-beca-923fe7c8136d.tmp | — | |
MD5:— | SHA256:— | |||
| 2144 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2144 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF129841.TMP | text | |
MD5:— | SHA256:— | |||
| 2144 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2144 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2144 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2144 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2144 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2144 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF129a25.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
13
DNS requests
8
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2160 | chrome.exe | 172.217.21.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2160 | chrome.exe | 140.82.118.3:443 | github.com | — | US | malicious |
2160 | chrome.exe | 172.217.23.163:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2160 | chrome.exe | 172.217.18.164:443 | www.google.com | Google Inc. | US | whitelisted |
2160 | chrome.exe | 140.82.114.9:443 | codeload.github.com | — | US | unknown |
2160 | chrome.exe | 216.58.212.141:443 | accounts.google.com | Google Inc. | US | whitelisted |
2160 | chrome.exe | 172.217.18.174:443 | clients1.google.com | Google Inc. | US | whitelisted |
2160 | chrome.exe | 216.58.207.35:443 | www.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
github.com |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
codeload.github.com |
| whitelisted |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
clients1.google.com |
| whitelisted |