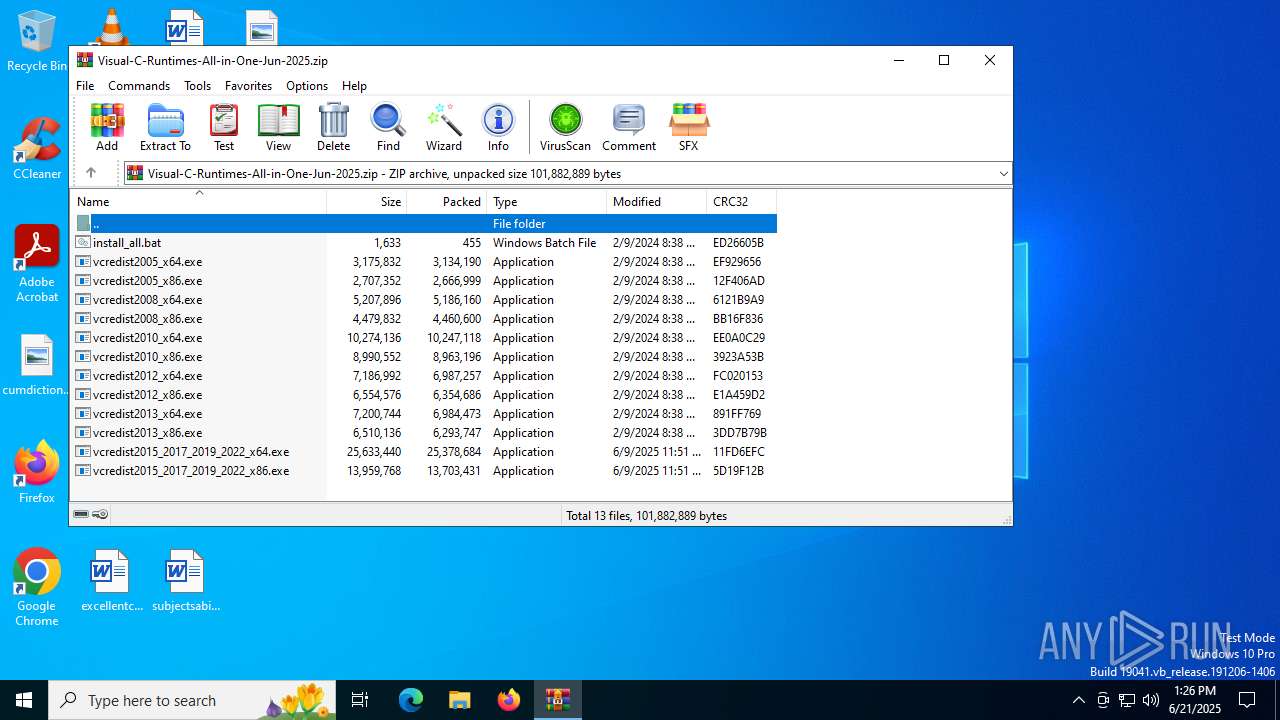
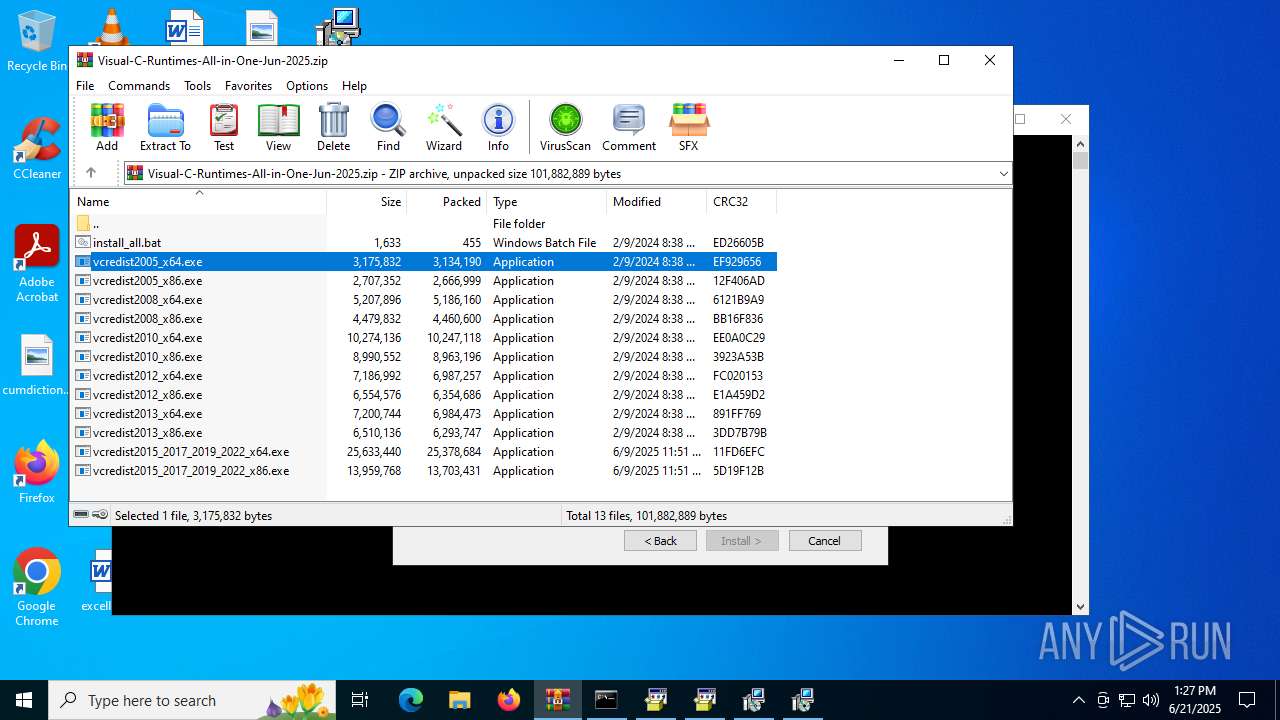
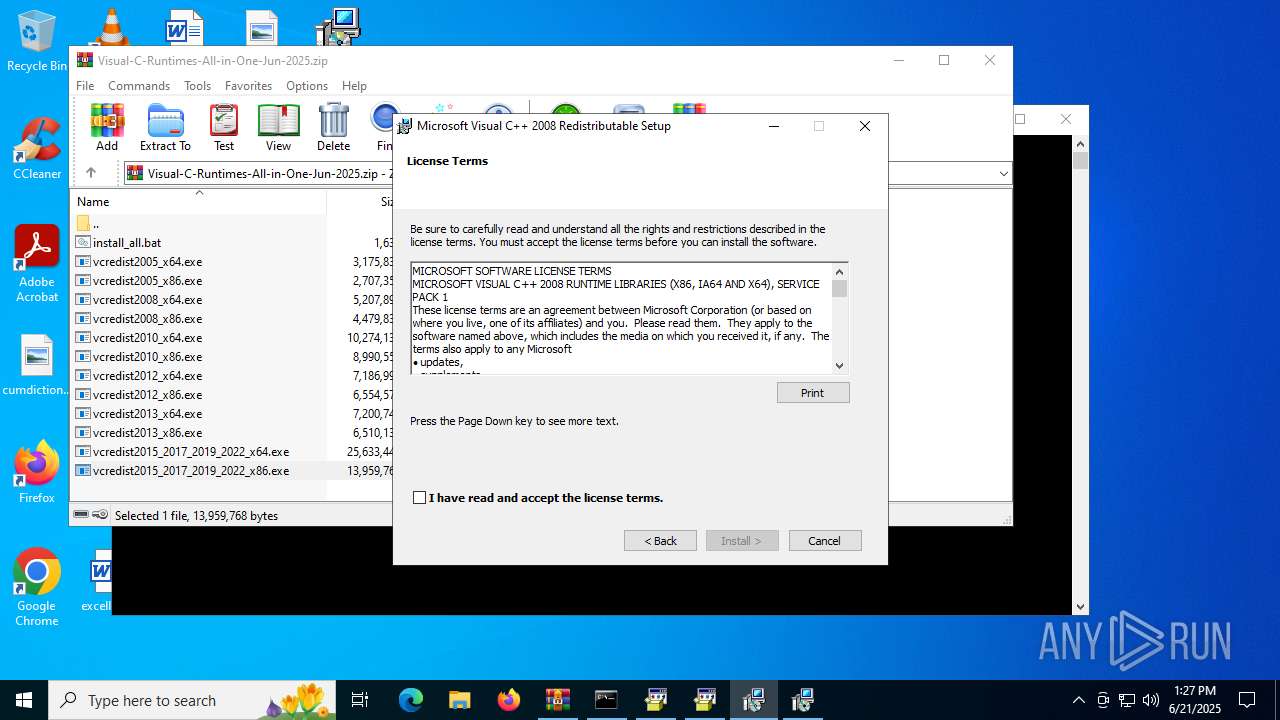
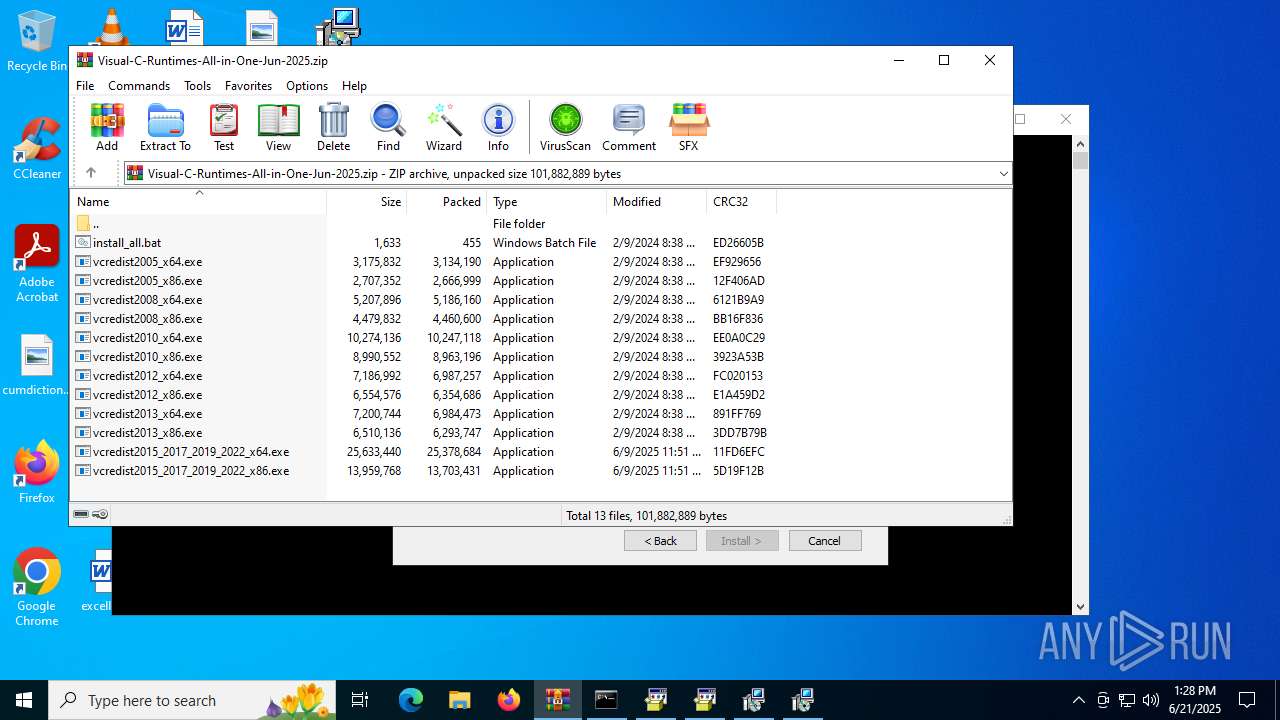
| File name: | Visual-C-Runtimes-All-in-One-Jun-2025.zip |
| Full analysis: | https://app.any.run/tasks/d16ceb3f-e30c-4d6b-b931-972fb06cd41d |
| Verdict: | Malicious activity |
| Analysis date: | June 21, 2025, 13:25:43 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | BD8B561F8AEED5DCDB15F6AB064851B9 |
| SHA1: | 278AD5E640C55489CEEFD27BE2D7995204CCAB7E |
| SHA256: | BBAF37E73518AE18B4A8AA7B4211E73A77FEC2E94582C7BFCA2A5976BEDC70B9 |
| SSDEEP: | 786432:FZpGPT1lNbpKXPfWDkNJ1LMeybTBztdbjQ98558wXI+OQHT:JGPhlNbpKXGDkv1LMeoTBz7421Y+OE |
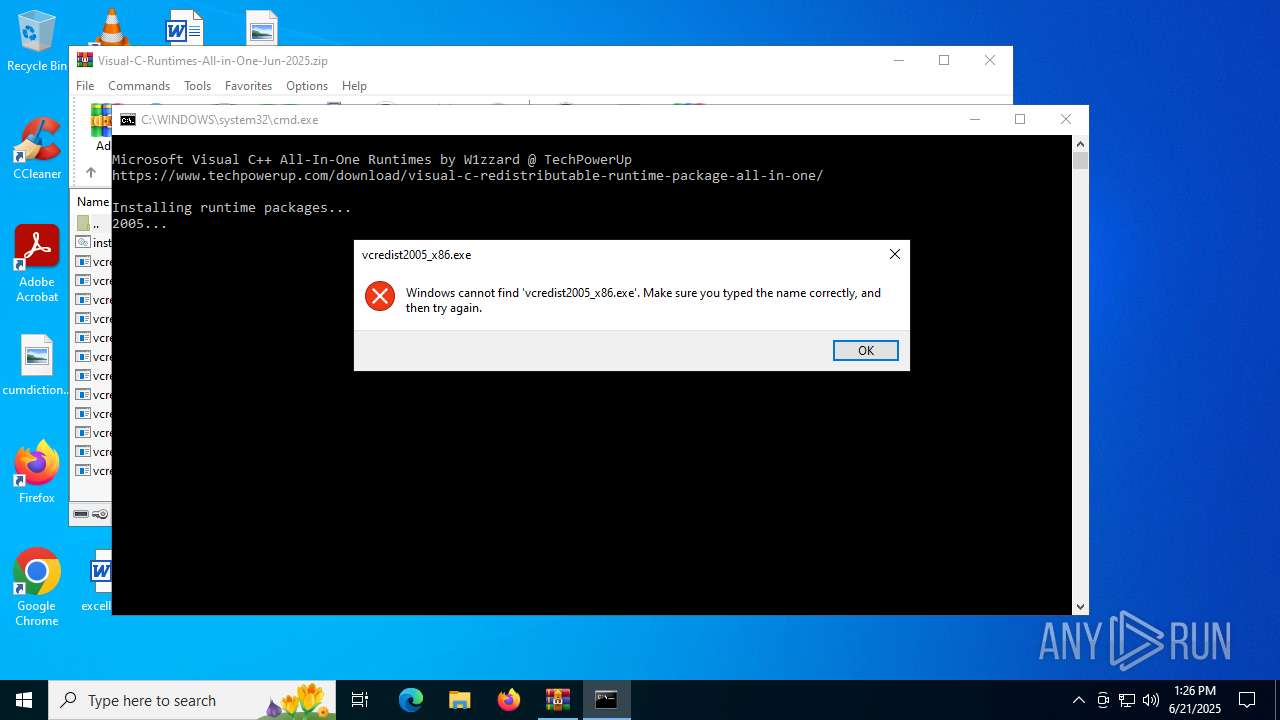
MALICIOUS
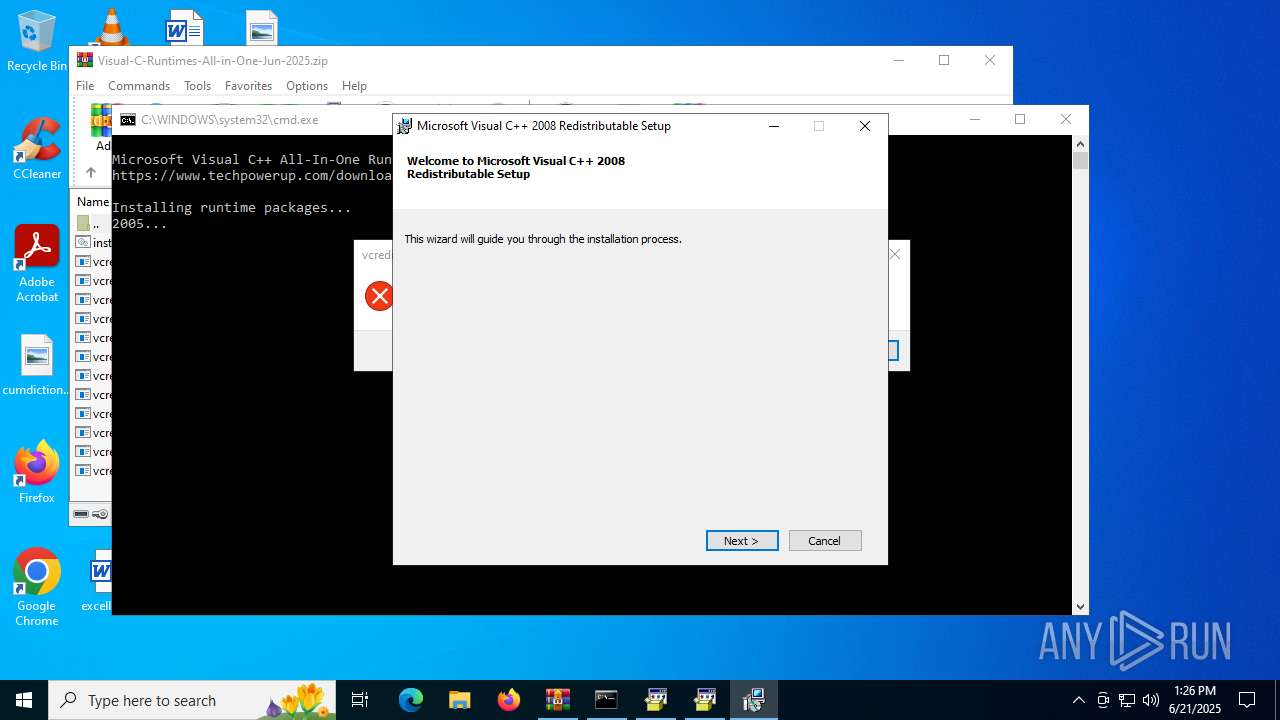
Generic archive extractor
- WinRAR.exe (PID: 5496)
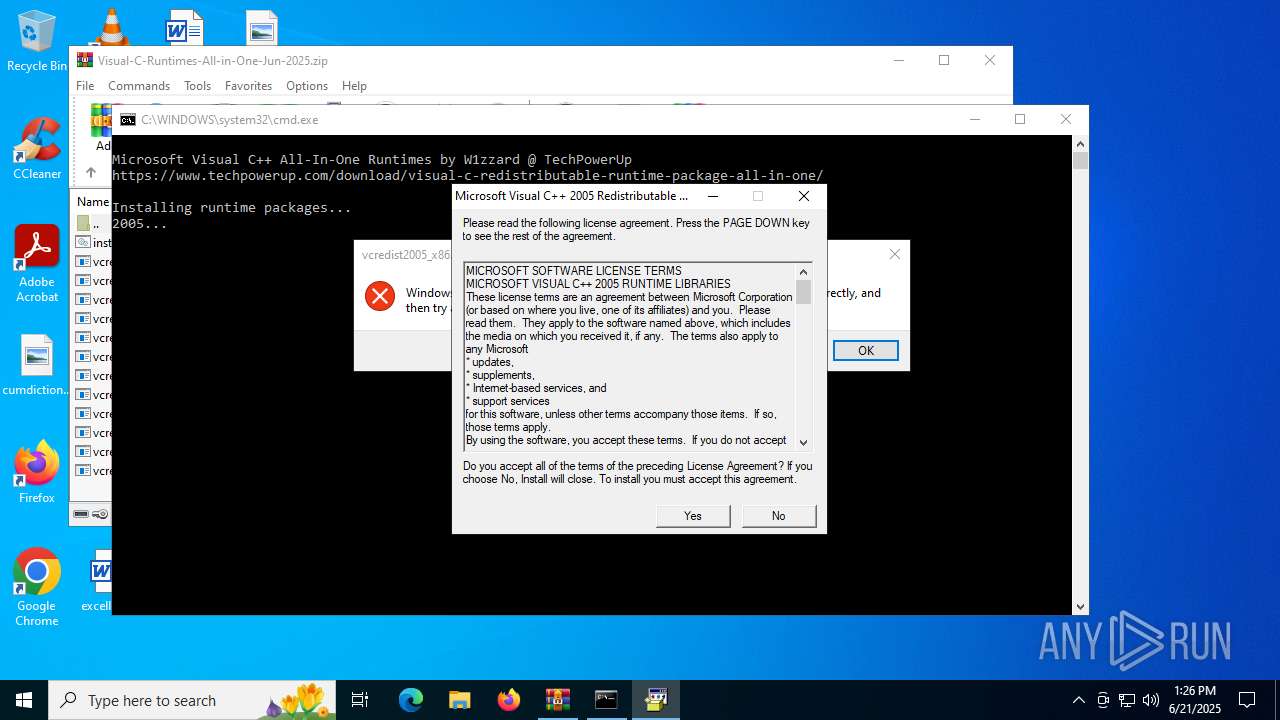
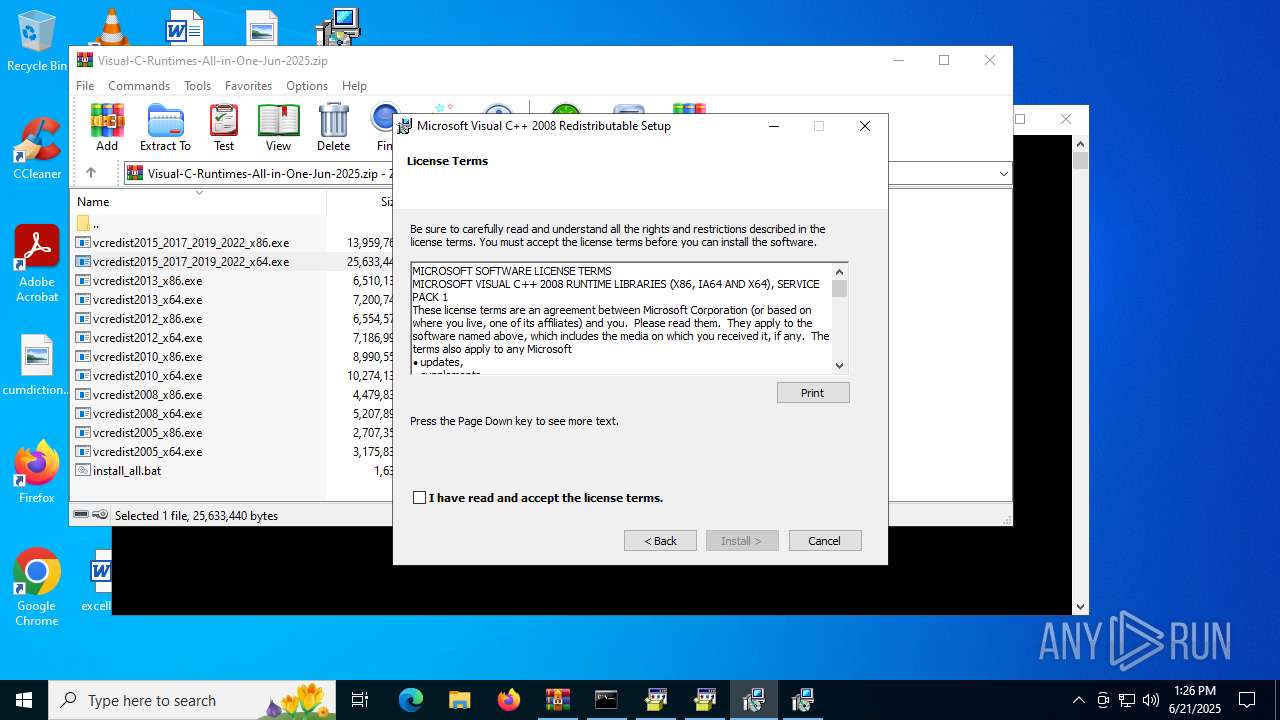
Executing a file with an untrusted certificate
- vcredist2005_x86.exe (PID: 3884)
- vcredist2005_x64.exe (PID: 2388)
- vcredist2008_x86.exe (PID: 6264)
- vcredist2008_x86.exe (PID: 3960)
- install.exe (PID: 7120)
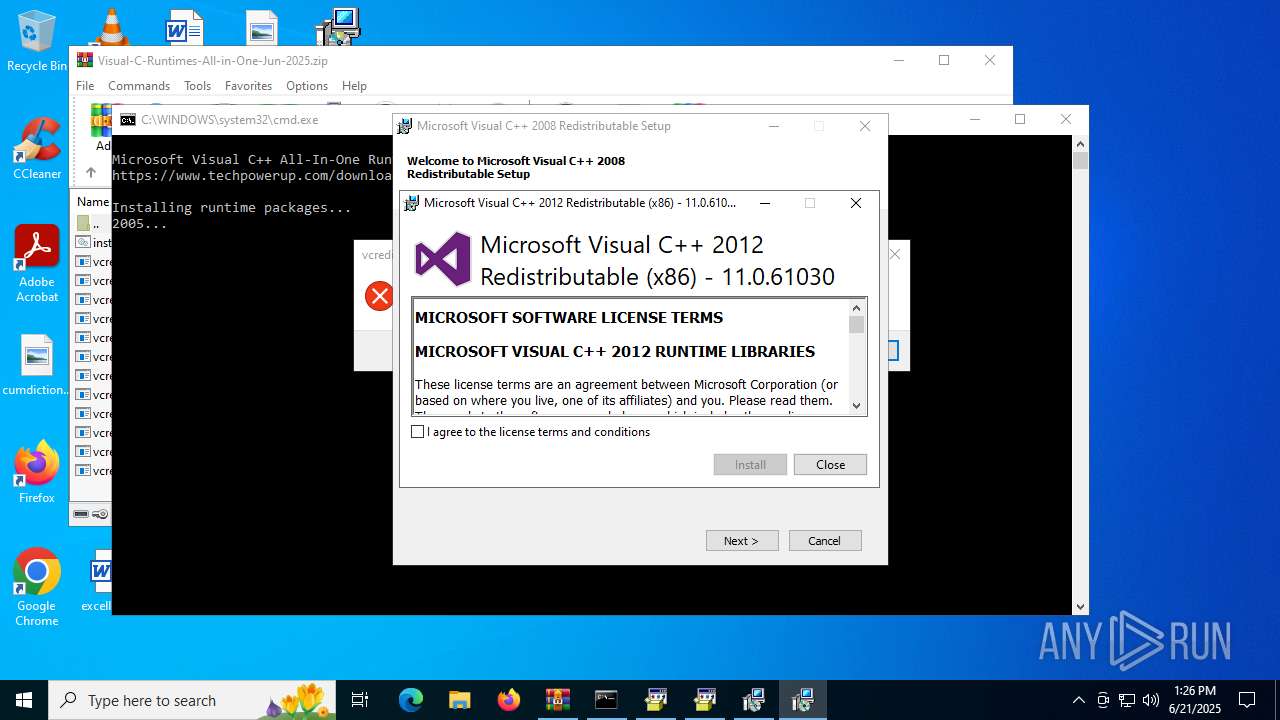
- vcredist2012_x86.exe (PID: 6868)
SUSPICIOUS
Starts a Microsoft application from unusual location
- vcredist2005_x86.exe (PID: 3884)
- vcredist2005_x64.exe (PID: 2388)
- vcredist2008_x86.exe (PID: 6264)
- vcredist2008_x86.exe (PID: 3960)
- vcredist2012_x86.exe (PID: 6868)
Process drops legitimate windows executable
- vcredist2008_x86.exe (PID: 3960)
- vcredist2012_x86.exe (PID: 6868)
Creates file in the systems drive root
- vcredist2008_x86.exe (PID: 3960)
Executable content was dropped or overwritten
- vcredist2008_x86.exe (PID: 3960)
- vcredist2012_x86.exe (PID: 6868)
Searches for installed software
- vcredist2012_x86.exe (PID: 6868)
Reads security settings of Internet Explorer
- install.exe (PID: 7120)
Reads the Windows owner or organization settings
- install.exe (PID: 7120)
INFO
Manual execution by a user
- cmd.exe (PID: 5904)
- vcredist2005_x86.exe (PID: 3884)
- vcredist2005_x64.exe (PID: 2388)
- vcredist2008_x86.exe (PID: 6264)
- vcredist2008_x86.exe (PID: 3960)
- vcredist2012_x86.exe (PID: 6868)
Reads the computer name
- vcredist2005_x86.exe (PID: 3884)
- vcredist2005_x64.exe (PID: 2388)
- vcredist2008_x86.exe (PID: 3960)
- install.exe (PID: 7120)
- vcredist2012_x86.exe (PID: 6868)
- msiexec.exe (PID: 1148)
Checks supported languages
- vcredist2005_x86.exe (PID: 3884)
- vcredist2005_x64.exe (PID: 2388)
- vcredist2008_x86.exe (PID: 3960)
- install.exe (PID: 7120)
- vcredist2012_x86.exe (PID: 6868)
- msiexec.exe (PID: 1148)
Reads the machine GUID from the registry
- vcredist2008_x86.exe (PID: 3960)
- install.exe (PID: 7120)
The sample compiled with korean language support
- vcredist2008_x86.exe (PID: 3960)
The sample compiled with japanese language support
- vcredist2008_x86.exe (PID: 3960)
The sample compiled with english language support
- vcredist2008_x86.exe (PID: 3960)
- vcredist2012_x86.exe (PID: 6868)
The sample compiled with russian language support
- vcredist2008_x86.exe (PID: 3960)
The sample compiled with Italian language support
- vcredist2008_x86.exe (PID: 3960)
The sample compiled with spanish language support
- vcredist2008_x86.exe (PID: 3960)
The sample compiled with german language support
- vcredist2008_x86.exe (PID: 3960)
The sample compiled with french language support
- vcredist2008_x86.exe (PID: 3960)
The sample compiled with chinese language support
- vcredist2008_x86.exe (PID: 3960)
Create files in a temporary directory
- install.exe (PID: 7120)
- vcredist2012_x86.exe (PID: 6868)
Checks proxy server information
- install.exe (PID: 7120)
- slui.exe (PID: 316)
Reads the software policy settings
- install.exe (PID: 7120)
- slui.exe (PID: 316)
Creates files or folders in the user directory
- install.exe (PID: 7120)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2024:02:09 09:38:48 |
| ZipCRC: | 0x12f406ad |
| ZipCompressedSize: | 2666999 |
| ZipUncompressedSize: | 2707352 |
| ZipFileName: | vcredist2005_x86.exe |
Total processes
129
Monitored processes
11
Malicious processes
3
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 316 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1148 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2388 | "C:\Users\admin\Desktop\vcredist2005_x64.exe" | C:\Users\admin\Desktop\vcredist2005_x64.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Win32 Cabinet Self-Extractor Version: 6.00.2900.2180 (xpsp_sp2_rtm.040803-2158) Modules
| |||||||||||||||
| 3884 | "C:\Users\admin\Desktop\vcredist2005_x86.exe" | C:\Users\admin\Desktop\vcredist2005_x86.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Win32 Cabinet Self-Extractor Version: 6.00.2900.2180 (xpsp_sp2_rtm.040803-2158) Modules
| |||||||||||||||
| 3960 | "C:\Users\admin\Desktop\vcredist2008_x86.exe" | C:\Users\admin\Desktop\vcredist2008_x86.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2008 Redistributable Setup Version: 9.0.30729.5677 Modules
| |||||||||||||||
| 5496 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\Visual-C-Runtimes-All-in-One-Jun-2025.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 5612 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5904 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\Desktop\install_all.bat" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6264 | "C:\Users\admin\Desktop\vcredist2008_x86.exe" | C:\Users\admin\Desktop\vcredist2008_x86.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Visual C++ 2008 Redistributable Setup Exit code: 3221226540 Version: 9.0.30729.5677 Modules
| |||||||||||||||
| 6868 | "C:\Users\admin\Desktop\vcredist2012_x86.exe" | C:\Users\admin\Desktop\vcredist2012_x86.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Visual C++ 2012 Redistributable (x86) - 11.0.61030 Version: 11.0.61030.0 Modules
| |||||||||||||||
Total events
8 715
Read events
8 701
Write events
14
Delete events
0
Modification events
| (PID) Process: | (5496) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (5496) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (5496) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (5496) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\Visual-C-Runtimes-All-in-One-Jun-2025.zip | |||
| (PID) Process: | (5496) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (5496) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (5496) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (5496) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (5496) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList |
| Operation: | write | Name: | ArcSort |
Value: 32 | |||
| (PID) Process: | (5496) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList |
| Operation: | write | Name: | ArcSort |
Value: 0 | |||
Executable files
14
Suspicious files
3
Text files
17
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3960 | vcredist2008_x86.exe | C:\4d6ed4480b28944e5bd25d59f1a4\install.res.1031.dll | executable | |
MD5:6F22A8ECC5A917C61F1478EF4AD53949 | SHA256:2C5FA53E6EB07BDDC22C7C5203FF7BBE707C4CF8803F144CEB031384B59831AA | |||
| 3960 | vcredist2008_x86.exe | C:\4d6ed4480b28944e5bd25d59f1a4\install.res.1028.dll | executable | |
MD5:8C2C1DF03574E935277ADDC6E151BDBE | SHA256:1074252F76E72E59A9DA9D7E109C80AB131D53554C49CB3D69A180729BFFC18E | |||
| 3960 | vcredist2008_x86.exe | C:\4d6ed4480b28944e5bd25d59f1a4\install.res.1033.dll | executable | |
MD5:FF6003014EEFC9C30ABE20E3E1F5FBE8 | SHA256:A522C5EA3250CDD538A9CE7B4A06DFD5123E7EB05EEF67509F2B975A8E1D3067 | |||
| 3960 | vcredist2008_x86.exe | C:\4d6ed4480b28944e5bd25d59f1a4\install.res.1042.dll | executable | |
MD5:BA91E387D54B94689644EBD23FF264BA | SHA256:16FED8F279B0240F63DD90925150CD37782E9395AF32A2693BDC0533C0809767 | |||
| 3960 | vcredist2008_x86.exe | C:\4d6ed4480b28944e5bd25d59f1a4\install.res.1041.dll | executable | |
MD5:6BFB58958D58BF38E9242B2056392B8C | SHA256:F74006AAA2A19777FB0C3B81321AABF00D87107DC23BA0D2282092502E5CD332 | |||
| 3960 | vcredist2008_x86.exe | C:\4d6ed4480b28944e5bd25d59f1a4\install.res.1040.dll | executable | |
MD5:EF1CCFE8572CDAAEFB1940EFBBFF6D80 | SHA256:709AB0139C643B78C2DACE7A35B9801E1A4B4E4C4E176C0D00F1B55A2A71D7A8 | |||
| 3960 | vcredist2008_x86.exe | C:\4d6ed4480b28944e5bd25d59f1a4\install.res.1049.dll | executable | |
MD5:9AAC6CE2AD6C7AEE5481E46DDB0AD0DD | SHA256:3DE25F7B3FD91A8D5B7F7DD8ECCF44E24B33B66133FC89519D21A426B489374E | |||
| 3960 | vcredist2008_x86.exe | C:\4d6ed4480b28944e5bd25d59f1a4\vc_red.msi | executable | |
MD5:7E641E6A0B456271745C20C3BB8A18F9 | SHA256:34C5E7D7EA270EE67F92D34843D89603D6D3B6D9EF5247B43AE3C59C909D380D | |||
| 3960 | vcredist2008_x86.exe | C:\4d6ed4480b28944e5bd25d59f1a4\install.res.1036.dll | executable | |
MD5:4D431F94A7D0945F4A7F13B7988632AA | SHA256:CB38381C0AFDCB3465F71699ADDAD7534FFD72702907B017708EBA463DBC68B6 | |||
| 3960 | vcredist2008_x86.exe | C:\4d6ed4480b28944e5bd25d59f1a4\install.exe | executable | |
MD5:4138C31964FBCB3B7418E086933324C3 | SHA256:B72056FC3DF6F46069294C243FE5006879BF4A9D8EEF388369A590CA41745F29 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
23
DNS requests
10
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 184.24.77.43:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7120 | install.exe | GET | 200 | 23.55.104.190:80 | http://crl.microsoft.com/pki/crl/products/CSPCA.crl | unknown | — | — | whitelisted |
— | — | POST | 500 | 20.83.72.98:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
2940 | svchost.exe | GET | 200 | 69.192.161.44:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
— | — | POST | 500 | 20.83.72.98:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 184.24.77.43:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 184.24.77.43:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.24.77.43:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
7120 | install.exe | 23.55.104.190:80 | crl.microsoft.com | Akamai International B.V. | US | whitelisted |
4800 | slui.exe | 40.91.76.224:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |