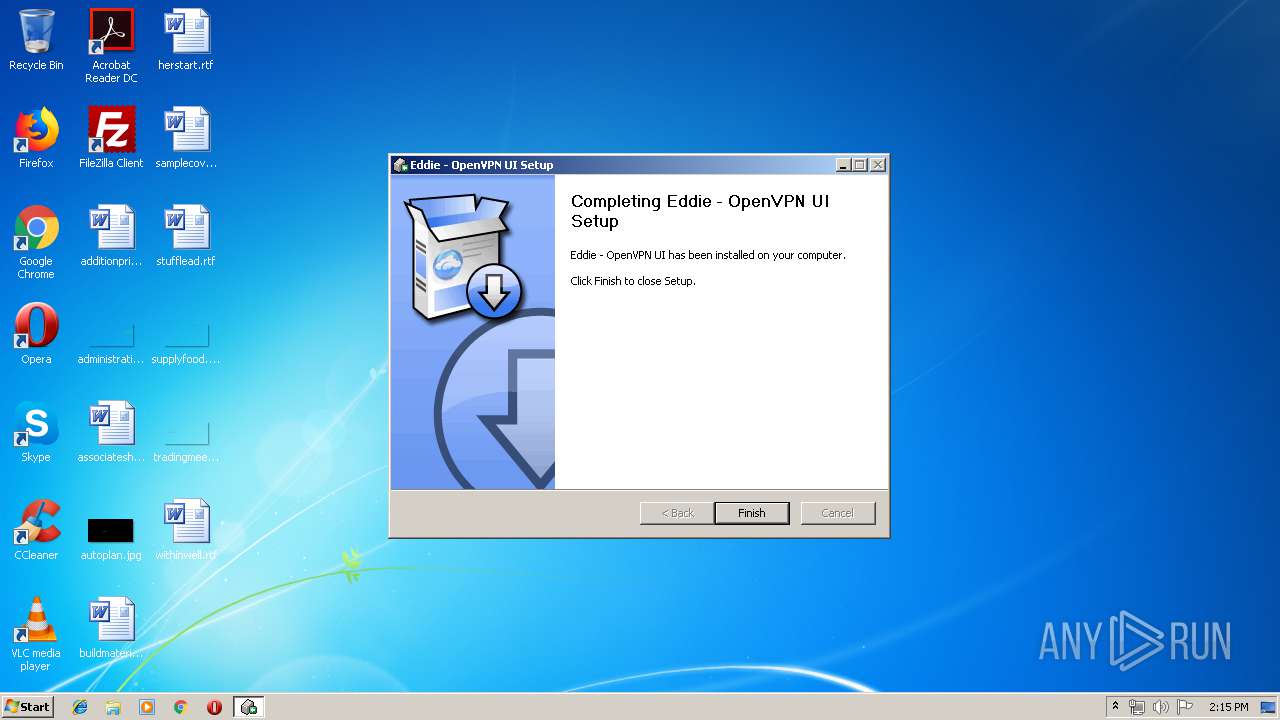
| File name: | eddie-ui_2.16.3_windows-7_x86_installer.exe |
| Full analysis: | https://app.any.run/tasks/7ded18ea-e9fc-4115-8f15-c93b2b11d7d7 |
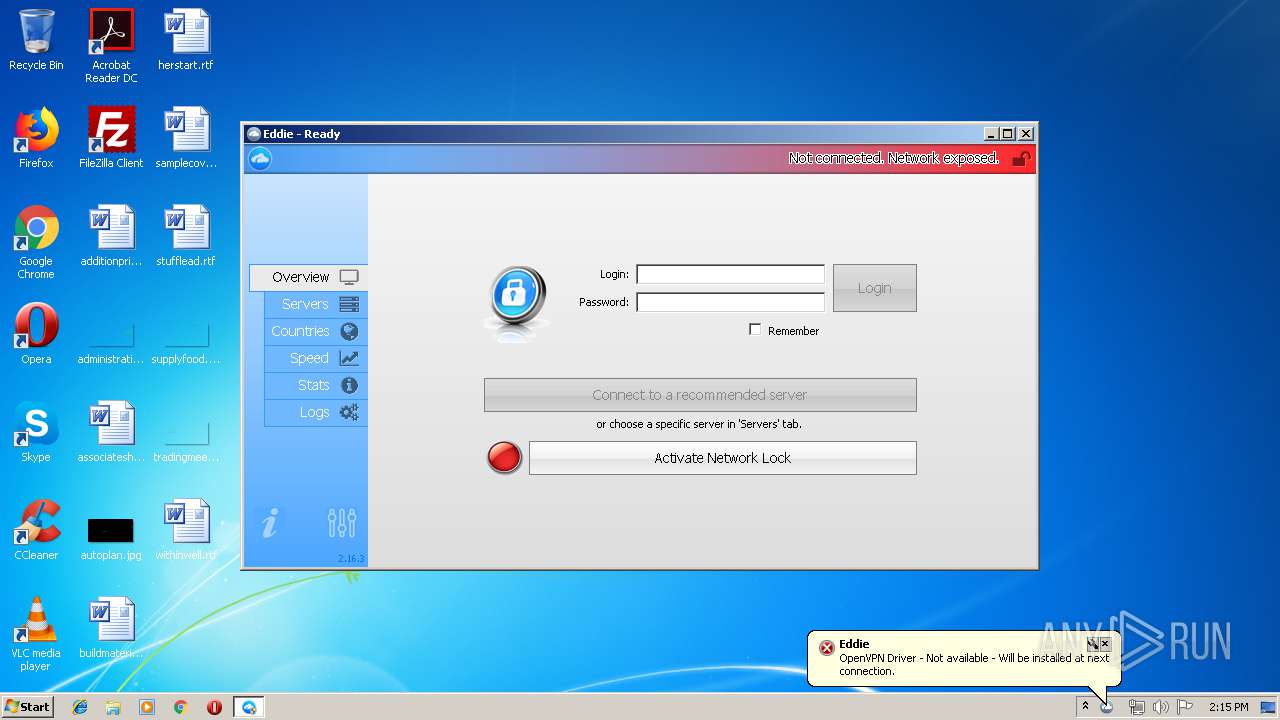
| Verdict: | Malicious activity |
| Analysis date: | June 02, 2019, 13:14:36 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 44ED74364977752BA4758B51AA35D838 |
| SHA1: | BAA3539F81AD9620DA38F870547F7BAF0C112081 |
| SHA256: | BBAD99C3EF84456780181D8F3D7FC05FD8D4EC8DFA30D95811A99C0B106A138D |
| SSDEEP: | 98304:qwHWHP3OemjsVtX2AtjXrWEd9P+MV2KE6yb5tb3MUhBBlFE66/zbbsh6pGsK4dAg:fuP3dmktX2mXrWEdJ+Mg1ltb3MABBlFW |
MALICIOUS
Loads dropped or rewritten executable
- eddie-ui_2.16.3_windows-7_x86_installer.exe (PID: 3796)
- Eddie-UI.exe (PID: 488)
- openvpn.exe (PID: 2452)
Application was dropped or rewritten from another process
- Eddie-UI.exe (PID: 3028)
- Eddie-UI.exe (PID: 488)
- openvpn.exe (PID: 2452)
- plink.exe (PID: 4000)
- stunnel.exe (PID: 2864)
- curl.exe (PID: 3804)
- curl.exe (PID: 3380)
Changes settings of System certificates
- Eddie-UI.exe (PID: 488)
SUSPICIOUS
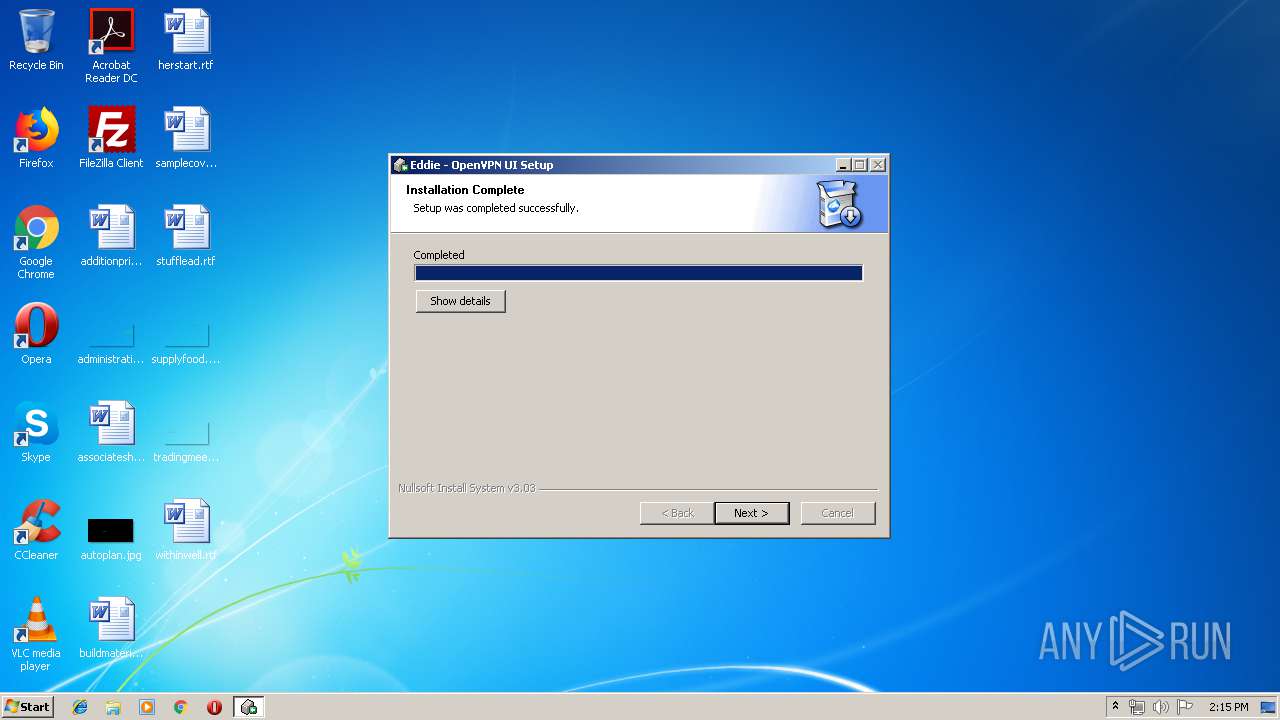
Executable content was dropped or overwritten
- eddie-ui_2.16.3_windows-7_x86_installer.exe (PID: 3796)
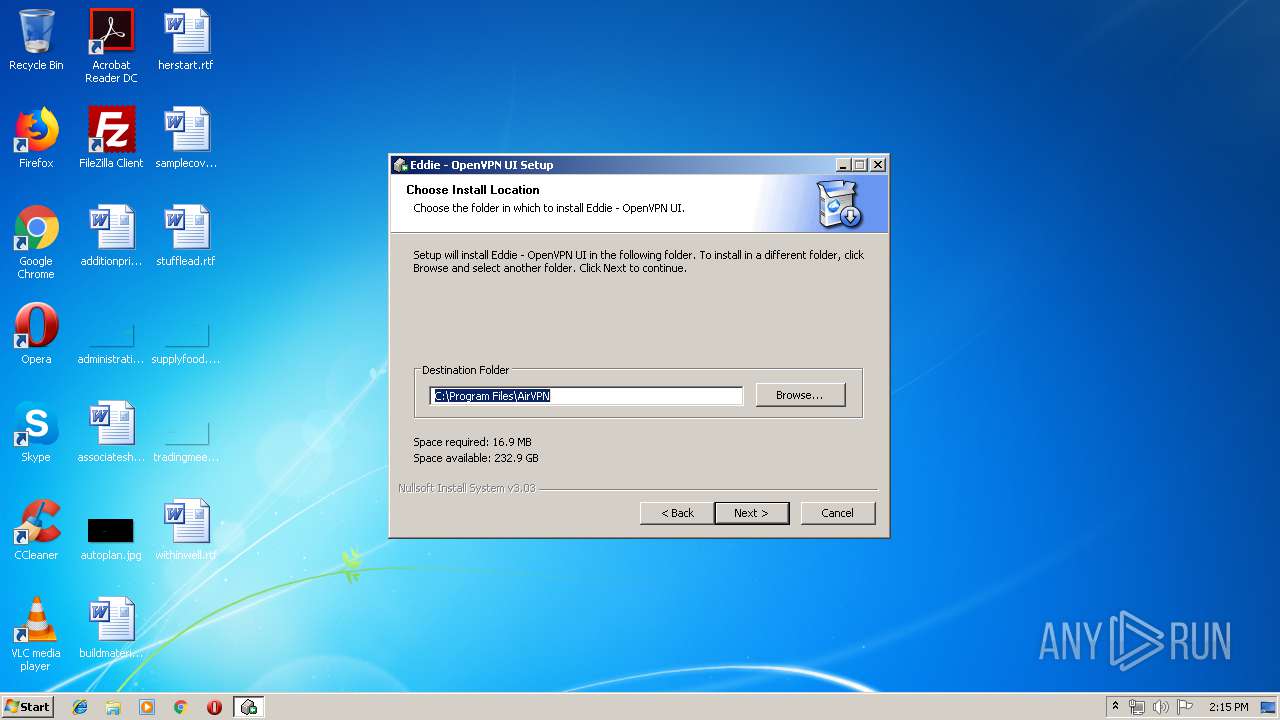
Creates files in the program directory
- eddie-ui_2.16.3_windows-7_x86_installer.exe (PID: 3796)
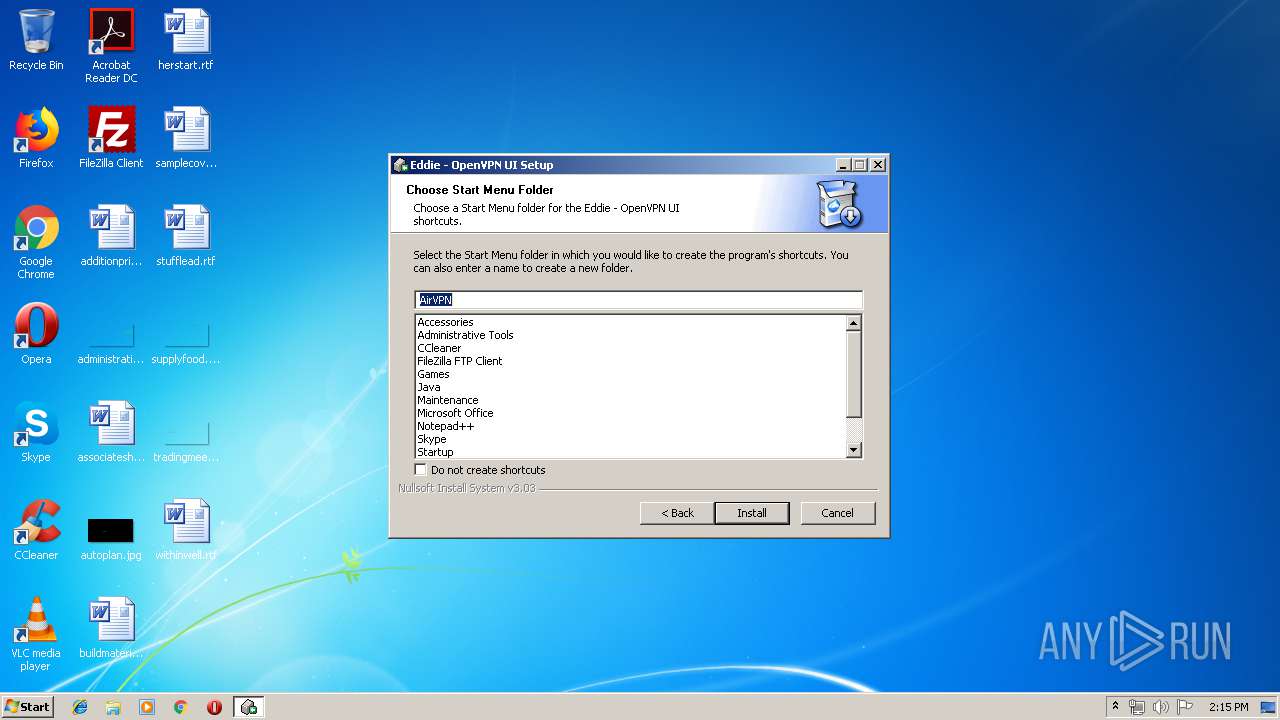
Creates a software uninstall entry
- eddie-ui_2.16.3_windows-7_x86_installer.exe (PID: 3796)
Creates files in the user directory
- eddie-ui_2.16.3_windows-7_x86_installer.exe (PID: 3796)
Adds / modifies Windows certificates
- Eddie-UI.exe (PID: 488)
Starts CMD.EXE for commands execution
- Eddie-UI.exe (PID: 488)
Uses NETSH.EXE for network configuration
- Eddie-UI.exe (PID: 488)
Connects to server without host name
- curl.exe (PID: 3380)
INFO
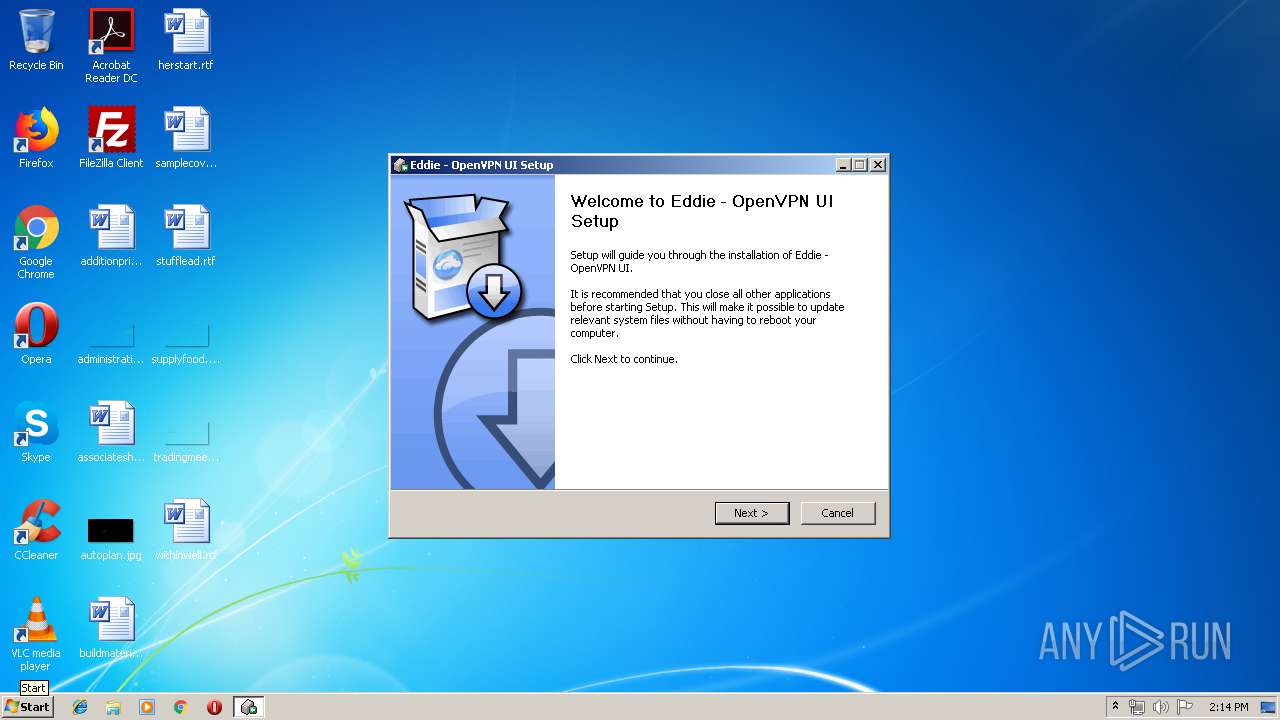
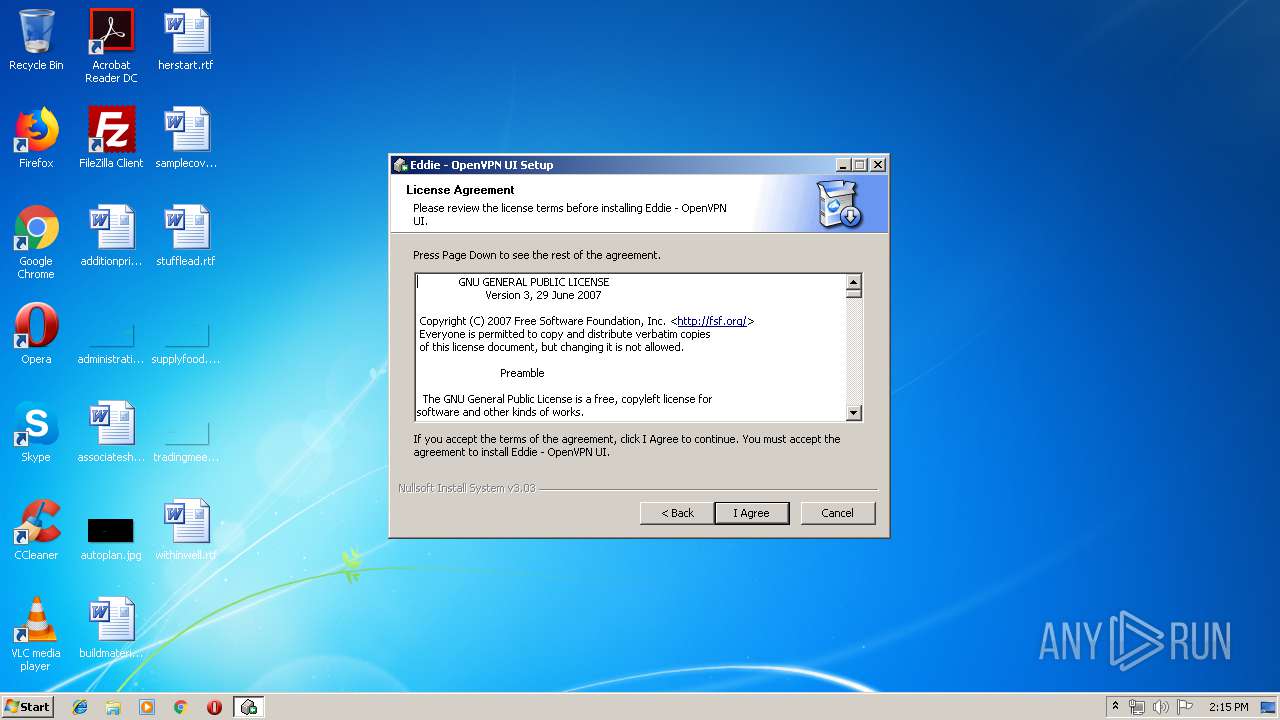
Manual execution by user
- Eddie-UI.exe (PID: 3028)
- Eddie-UI.exe (PID: 488)
Dropped object may contain Bitcoin addresses
- eddie-ui_2.16.3_windows-7_x86_installer.exe (PID: 3796)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:01:30 04:57:38+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 25088 |
| InitializedDataSize: | 118784 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x3328 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 30-Jan-2018 03:57:38 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 30-Jan-2018 03:57:38 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00006077 | 0x00006200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.40397 |
.rdata | 0x00008000 | 0x00001248 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.04426 |
.data | 0x0000A000 | 0x0001A838 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.22445 |
.ndata | 0x00025000 | 0x0000A000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0002F000 | 0x00001FA0 | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.87124 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.28813 | 1070 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 1.6733 | 1384 | UNKNOWN | English - United States | RT_ICON |
3 | 3.01183 | 744 | UNKNOWN | English - United States | RT_ICON |
4 | 2.76361 | 296 | UNKNOWN | English - United States | RT_ICON |
102 | 2.71813 | 180 | UNKNOWN | English - United States | RT_DIALOG |
103 | 2.64576 | 62 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.68372 | 512 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.91148 | 248 | UNKNOWN | English - United States | RT_DIALOG |
107 | 2.52183 | 160 | UNKNOWN | English - United States | RT_DIALOG |
111 | 2.89887 | 238 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
59
Monitored processes
14
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 488 | "C:\Program Files\AirVPN\Eddie-UI.exe" -path=home | C:\Program Files\AirVPN\Eddie-UI.exe | explorer.exe | ||||||||||||
User: admin Company: https://eddie.website Integrity Level: HIGH Description: Eddie - Windows UI Exit code: 0 Version: 2.16.0.0 Modules
| |||||||||||||||
| 1856 | route -6 PRINT | C:\Windows\system32\ROUTE.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Route Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1860 | "cmd.exe" /c route -6 PRINT | C:\Windows\system32\cmd.exe | — | Eddie-UI.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2452 | "C:\Users\admin\AppData\Local\Temp\eddie-ui_2.16.3_windows-7_x86_installer.exe" | C:\Users\admin\AppData\Local\Temp\eddie-ui_2.16.3_windows-7_x86_installer.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2452 | "C:\Program Files\AirVPN\openvpn.exe" --version | C:\Program Files\AirVPN\openvpn.exe | — | Eddie-UI.exe | |||||||||||
User: admin Company: The OpenVPN Project Integrity Level: HIGH Description: OpenVPN Daemon Exit code: 1 Version: 2.4.6.0 Modules
| |||||||||||||||
| 2480 | "cmd.exe" /c route -4 PRINT | C:\Windows\system32\cmd.exe | — | Eddie-UI.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2696 | "NetSh.exe" WFP Show Filters file="C:\Users\admin\AppData\Local\Temp\aece31da-2725-4671-878f-6425079c8ee1.xml" | C:\Windows\system32\NetSh.exe | — | Eddie-UI.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2864 | "C:\Program Files\AirVPN\stunnel.exe" -version | C:\Program Files\AirVPN\stunnel.exe | Eddie-UI.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3028 | "C:\Program Files\AirVPN\Eddie-UI.exe" -path=home | C:\Program Files\AirVPN\Eddie-UI.exe | — | explorer.exe | |||||||||||
User: admin Company: https://eddie.website Integrity Level: MEDIUM Description: Eddie - Windows UI Exit code: 3221226540 Version: 2.16.0.0 Modules
| |||||||||||||||
| 3380 | "C:\Program Files\AirVPN\curl.exe" "http://54.93.175.114" -sS --max-time 20 --cacert "C:\Program Files\AirVPN\res\cacert.pem" --data "s=LNERTCdnoe/ROB813zS4NAjwxHx/M8+EOF+XovJcKpksnJfJo1+6svVHPK2JYt+igb89H92Fy4r5Ga9edFCNmdfOVw5jLwHf502aq7/ro8wwa2HKpYENonpilEozuyGqOzk4Jq0a+BBxpG3biF3Mdy+QW08n4Ve64a1BgSUunCmP+yQp181mbyoy0ABnT+iF+ivRmxHvo61YBbkAKhCSjYy35BLRAQvE9kfa6jl6pko5b/r2qRHA2gyUspN62YKg3SiwJOhIFFWnHcBMgEBkqwuG7PgPrwNQdIFg+MU+7+HhJ1NNF4QQ8i4gohY+zH+f9IykwqTolXUg+DIh8Y+5NikJV2Za5/i05/bGet0YZcZx0dxfzBh7JAmfLoL5URbVFz03E2n1IrzRjshdmniaYhHhPmDmVGn4lmH5l4vrnBKlRT9Z9caz+Tgpcj8q+r3FnQsLCf/Yr2O66WPoE+UzNTTJtyfrJiD6EMuAvqFHWyJjqmEUu3QOtvEFAXEP8pF7jVV7qNOjeQjcDlvEBbo60IVP+2agt7dsw7sTevOEcV4TRv1E7DDc3EN/r7cmkgLj/S856jyBn20Bp2pjOh4zGhe93aETz6i8StVWD6YHXnjdIUJgRDPnNqhntJsV5jNINjEGv8Q6p6NrLsLaWmdgcEi9VgOS7ivuXkbFie9QjAA=&d=k+nYYqlDlwbtr/7zIAk5EkVWgAOIRwP0MBLaafYatESRRz6MRYyFmFfbOe+50AF5q0N30a18CYup6fq7xb0iP/ltsKMbP7YK92VgosnfgQCzVbebUUNEjsqtZq8Eskv9thGXoMFdCUEE07J4114BzQ==" -i | C:\Program Files\AirVPN\curl.exe | Eddie-UI.exe | ||||||||||||
User: admin Company: curl, https://curl.haxx.se/ Integrity Level: HIGH Description: The curl executable Exit code: 0 Version: 7.54.1 Modules
| |||||||||||||||
Total events
532
Read events
447
Write events
85
Delete events
0
Modification events
| (PID) Process: | (3796) eddie-ui_2.16.3_windows-7_x86_installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\AirVPN |
| Operation: | write | Name: | |
Value: C:\Program Files\AirVPN | |||
| (PID) Process: | (3796) eddie-ui_2.16.3_windows-7_x86_installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\AirVPN |
| Operation: | write | Name: | DisplayName |
Value: Eddie - OpenVPN UI | |||
| (PID) Process: | (3796) eddie-ui_2.16.3_windows-7_x86_installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\AirVPN |
| Operation: | write | Name: | UninstallString |
Value: "C:\Program Files\AirVPN\uninstall.exe" | |||
| (PID) Process: | (3796) eddie-ui_2.16.3_windows-7_x86_installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\AirVPN |
| Operation: | write | Name: | URLInfoAbout |
Value: https://eddie.website | |||
| (PID) Process: | (3796) eddie-ui_2.16.3_windows-7_x86_installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\AirVPN |
| Operation: | write | Name: | HelpLink |
Value: https://eddie.website | |||
| (PID) Process: | (3796) eddie-ui_2.16.3_windows-7_x86_installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\AirVPN |
| Operation: | write | Name: | Publisher |
Value: AirVPN - https://airvpn.org | |||
| (PID) Process: | (3796) eddie-ui_2.16.3_windows-7_x86_installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\AirVPN |
| Operation: | write | Name: | RegCompany |
Value: AirVPN - https://airvpn.org | |||
| (PID) Process: | (3796) eddie-ui_2.16.3_windows-7_x86_installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\AirVPN |
| Operation: | write | Name: | DisplayIcon |
Value: "C:\Program Files\AirVPN\Eddie-UI.exe" | |||
| (PID) Process: | (3796) eddie-ui_2.16.3_windows-7_x86_installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\AirVPN |
| Operation: | write | Name: | SupportUpgrade |
Value: yes | |||
| (PID) Process: | (3796) eddie-ui_2.16.3_windows-7_x86_installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\AirVPN |
| Operation: | write | Name: | NoModify |
Value: 1 | |||
Executable files
22
Suspicious files
1
Text files
33
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3796 | eddie-ui_2.16.3_windows-7_x86_installer.exe | C:\Users\admin\AppData\Local\Temp\nsl4BF3.tmp\ioSpecial.ini | text | |
MD5:— | SHA256:— | |||
| 3796 | eddie-ui_2.16.3_windows-7_x86_installer.exe | C:\Users\admin\AppData\Local\Temp\nsl4BF3.tmp\splash.bmp | image | |
MD5:— | SHA256:— | |||
| 3796 | eddie-ui_2.16.3_windows-7_x86_installer.exe | C:\Program Files\AirVPN\Eddie-CLI.exe | executable | |
MD5:— | SHA256:— | |||
| 3796 | eddie-ui_2.16.3_windows-7_x86_installer.exe | C:\Program Files\AirVPN\curl.exe | executable | |
MD5:— | SHA256:— | |||
| 3796 | eddie-ui_2.16.3_windows-7_x86_installer.exe | C:\Program Files\AirVPN\Lib.Forms.dll | executable | |
MD5:— | SHA256:— | |||
| 3796 | eddie-ui_2.16.3_windows-7_x86_installer.exe | C:\Program Files\AirVPN\Lib.Core.dll | executable | |
MD5:— | SHA256:— | |||
| 3796 | eddie-ui_2.16.3_windows-7_x86_installer.exe | C:\Program Files\AirVPN\Lib.Platform.Windows.dll | executable | |
MD5:— | SHA256:— | |||
| 3796 | eddie-ui_2.16.3_windows-7_x86_installer.exe | C:\Program Files\AirVPN\liblzo2-2.dll | executable | |
MD5:— | SHA256:— | |||
| 3796 | eddie-ui_2.16.3_windows-7_x86_installer.exe | C:\Program Files\AirVPN\Lib.Platform.Windows.Native.dll | executable | |
MD5:— | SHA256:— | |||
| 3796 | eddie-ui_2.16.3_windows-7_x86_installer.exe | C:\Program Files\AirVPN\libpkcs11-helper-1.dll | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
1
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3380 | curl.exe | POST | 200 | 54.93.175.114:80 | http://54.93.175.114/ | DE | binary | 133 Kb | suspicious |
— | — | GET | 200 | 91.199.212.52:80 | http://crt.comodoca.com/COMODORSAAddTrustCA.crt | GB | der | 1.37 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 91.199.212.52:80 | crt.comodoca.com | Comodo CA Ltd | GB | suspicious |
— | — | 54.93.175.114:80 | — | Amazon.com, Inc. | DE | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crt.comodoca.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3380 | curl.exe | Attempted Information Leak | ET POLICY curl User-Agent Outbound |