| File name: | _bba07e615664530a55d45151d2ddb194d85d165eff17f723b2ca7fd0ae350c9d.fpx |
| Full analysis: | https://app.any.run/tasks/5c89ae31-c787-4013-b02a-efdd1f6b063a |
| Verdict: | Malicious activity |
| Analysis date: | March 13, 2026, 18:23:20 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
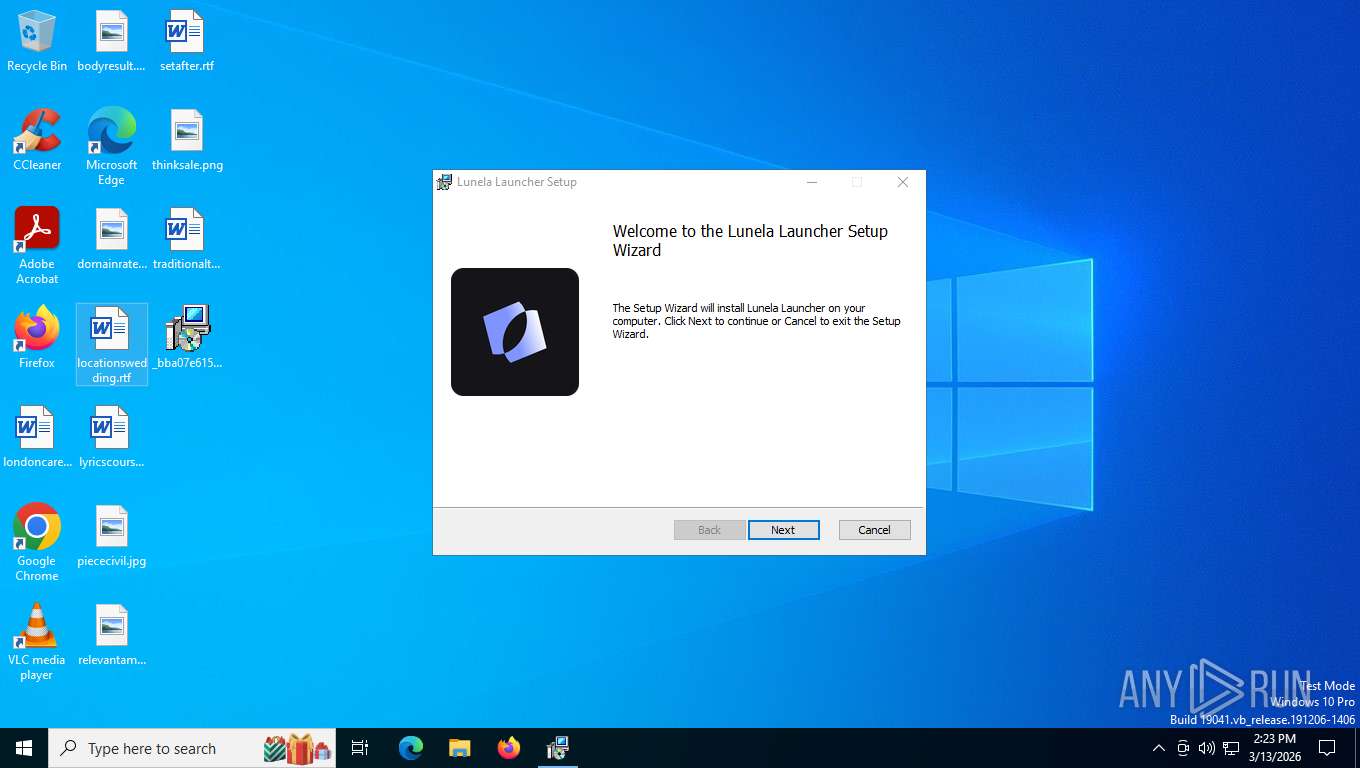
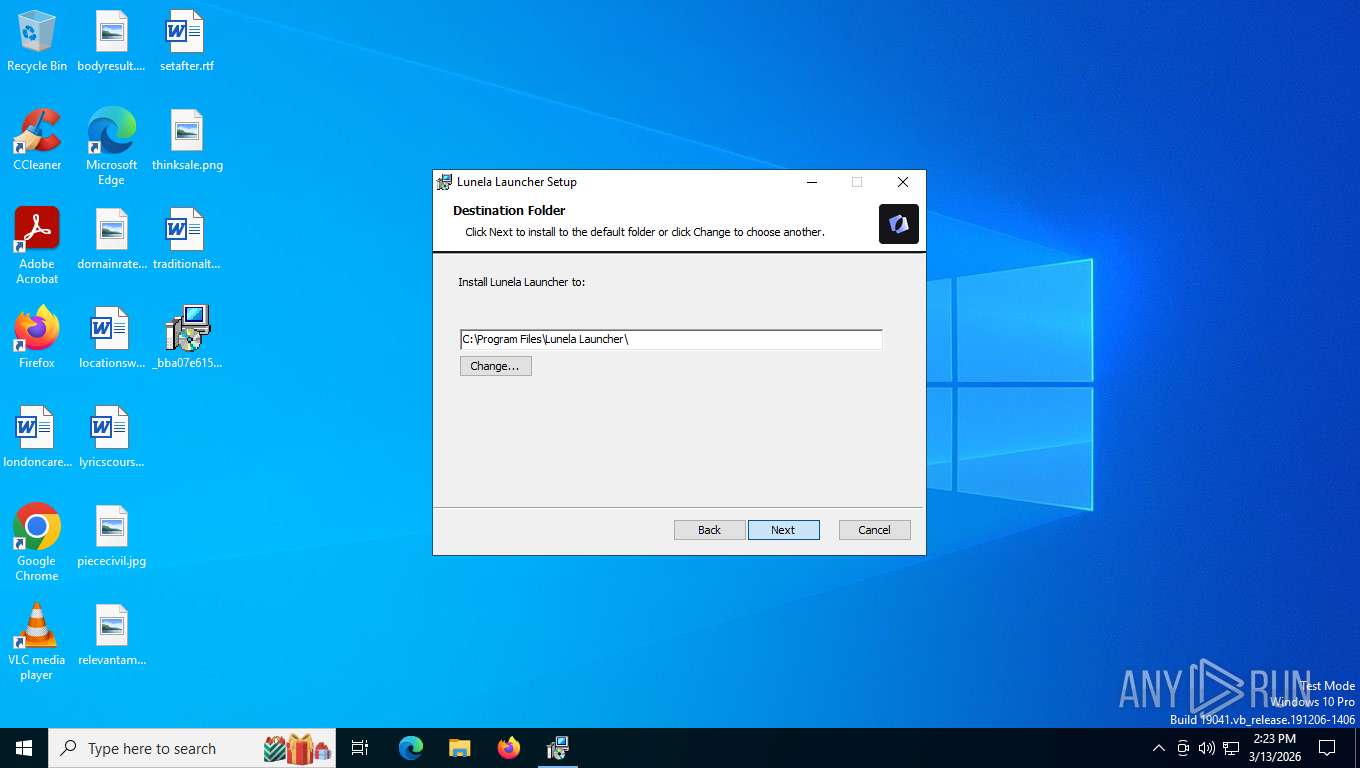
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, MSI Installer, Code page: 1252, Template: x64;0, Revision Number: {691B9E35-02DE-4F1F-A723-398319705217}, Number of Pages: 450, Number of Words: 2, Name of Creating Application: Windows Installer XML Toolset (3.14.1.8722), Security: 2, Title: Lunela Windows Installer, Subject: Lunela Windows Installer, Author: Lunela Company, Create Time/Date: Mon Dec 19 07:37:13 2022, Last Saved Time/Date: Mon Dec 19 07:37:13 2022 |
| MD5: | BACD436B177A7976A1276CEAAFCE39EA |
| SHA1: | 433F7EE53BE8ECC96B5C489229C6400C10F35B81 |
| SHA256: | BBA07E615664530A55D45151D2DDB194D85D165EFF17F723B2CA7FD0AE350C9D |
| SSDEEP: | 98304:1RFtp/Xisd6pMw/oo8dLQgQf8yakIMHugpg+KO2BH/KDJFaH89VHrbSlsZ4AYcrO:nM2Bfs |
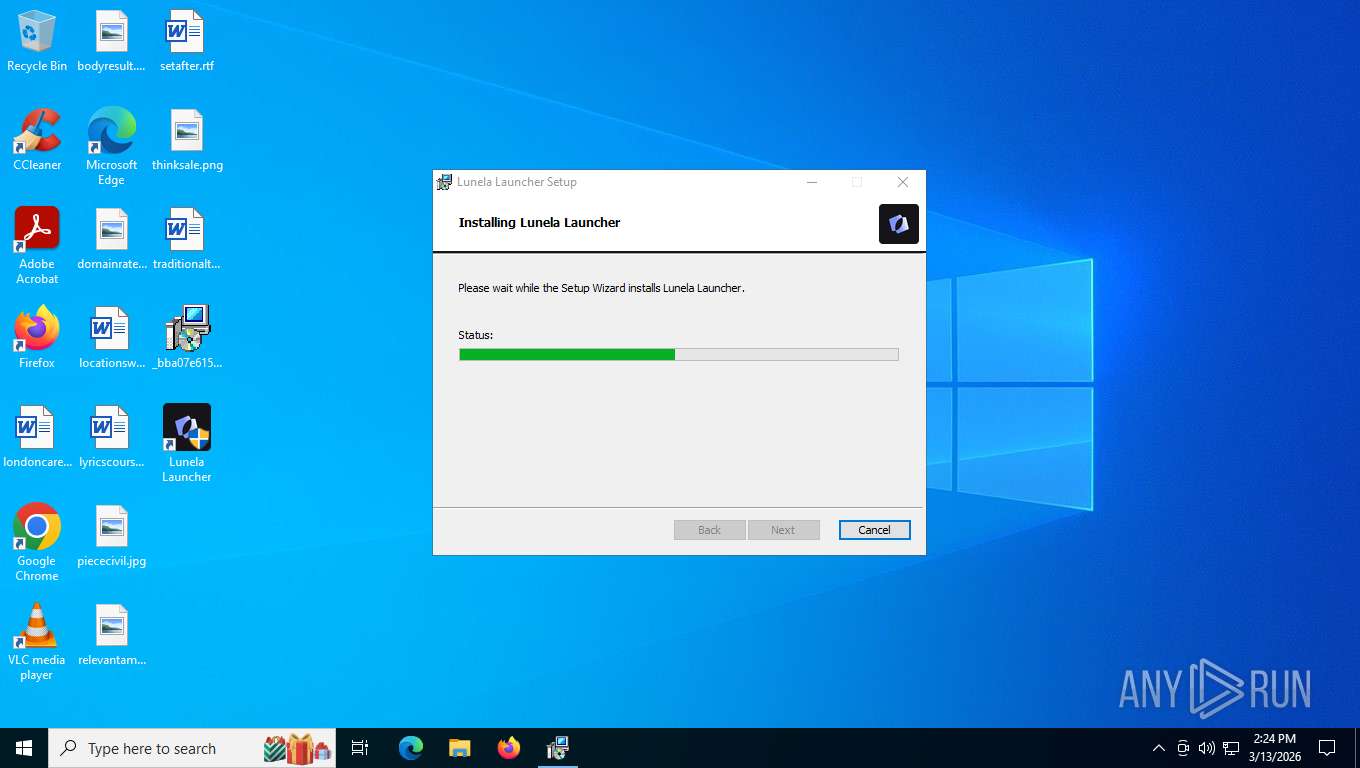
MALICIOUS
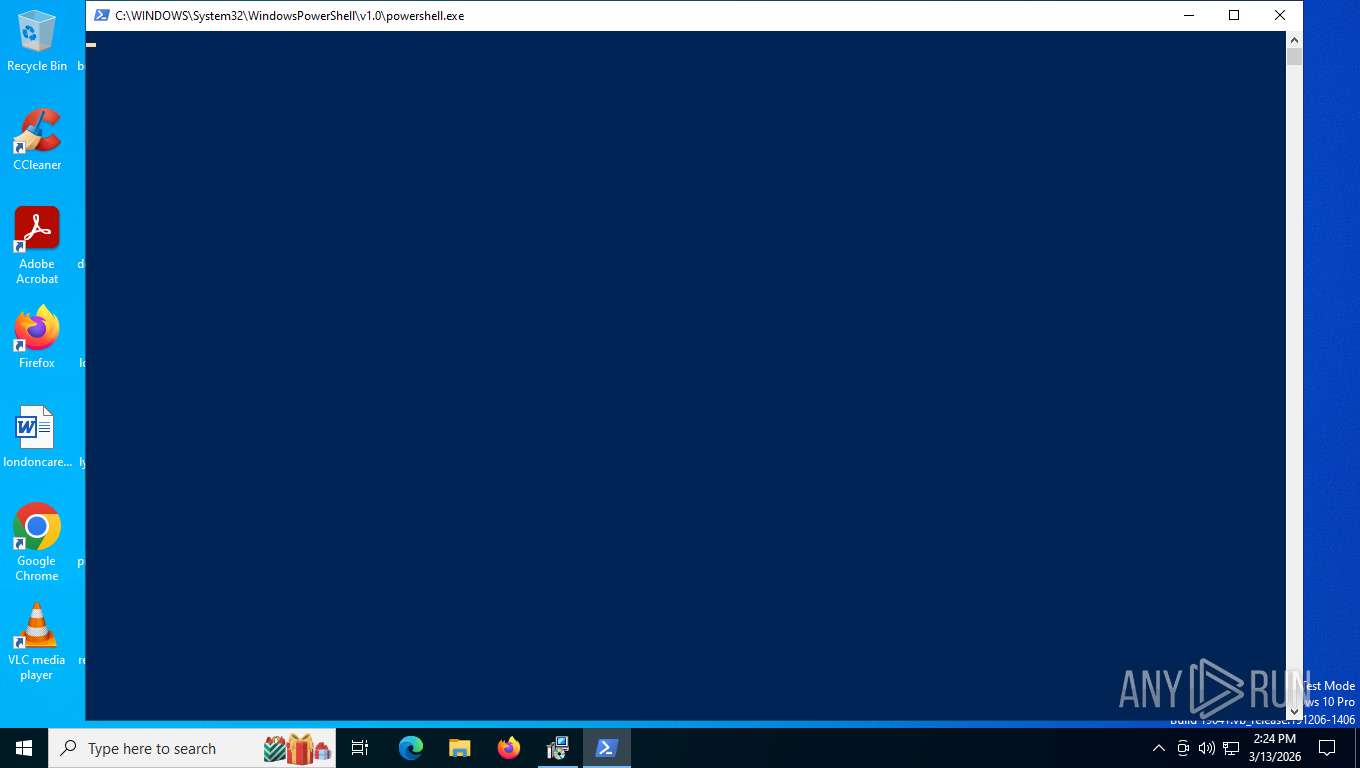
Run PowerShell with an invisible window
- powershell.exe (PID: 5512)
Changes the autorun value in the registry
- MicrosoftEdgeUpdate.exe (PID: 1432)
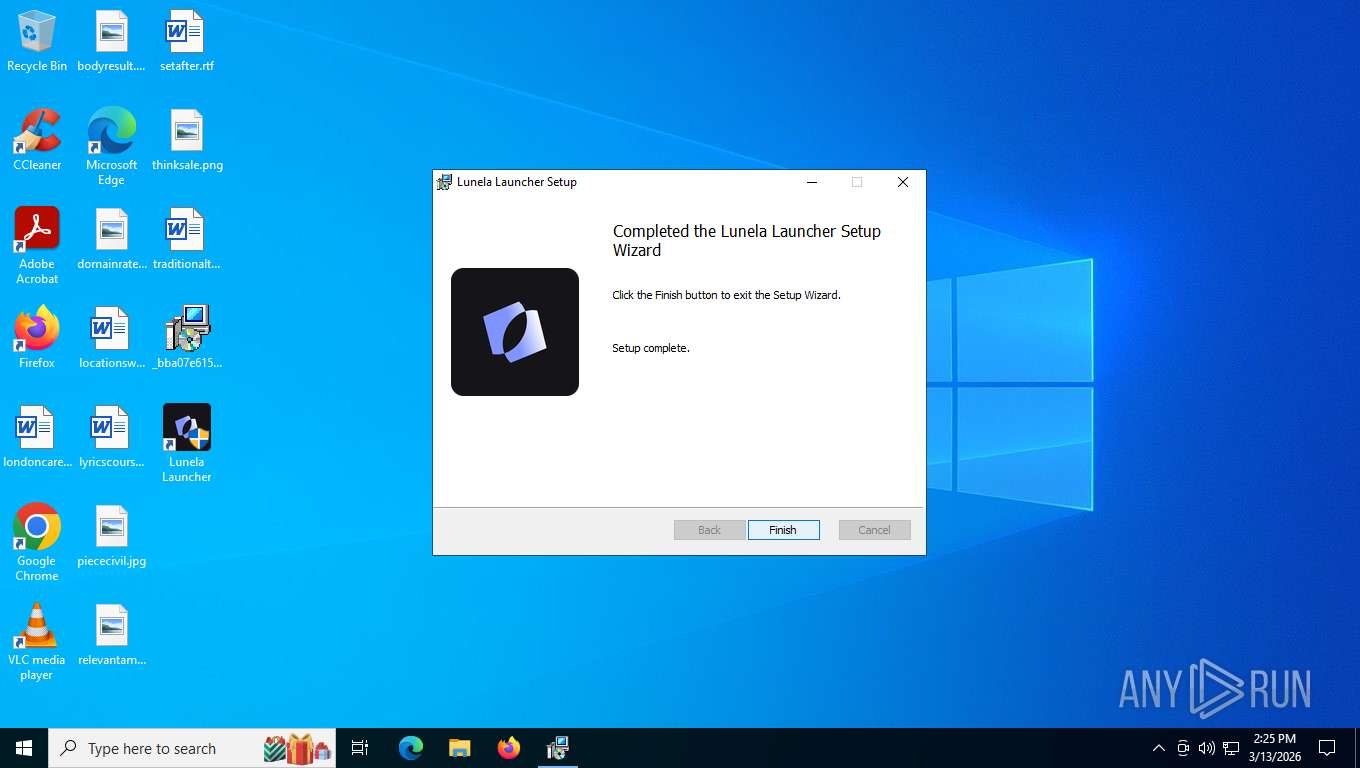
Executing a file with an untrusted certificate
- lunela-launcher.exe (PID: 3092)
- lunela-launcher.exe (PID: 8176)
Potential DLL hijacking behavior detected
- msedgewebview2.exe (PID: 1656)
Scans artifacts that could help determine the target
- msedgewebview2.exe (PID: 4552)
SUSPICIOUS
Executes as Windows Service
- VSSVC.exe (PID: 8228)
Downloads file from URI via Powershell
- powershell.exe (PID: 5512)
Manipulates environment variables
- powershell.exe (PID: 5512)
Starts POWERSHELL.EXE for commands execution
- msiexec.exe (PID: 8368)
The process bypasses the loading of PowerShell profile settings
- msiexec.exe (PID: 8368)
Starts process via Powershell
- powershell.exe (PID: 5512)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 5512)
Starts a Microsoft application from unusual location
- MicrosoftEdgeWebview2Setup.exe (PID: 8020)
- MicrosoftEdgeUpdate.exe (PID: 1432)
Executable content was dropped or overwritten
- MicrosoftEdgeWebview2Setup.exe (PID: 8020)
- MicrosoftEdgeUpdate.exe (PID: 1432)
- MicrosoftEdge_X64_146.0.3856.59.exe (PID: 4300)
- setup.exe (PID: 2148)
Starts itself from another location
- MicrosoftEdgeUpdate.exe (PID: 1432)
Creates/Modifies COM task schedule object
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 2764)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 2548)
- MicrosoftEdgeUpdate.exe (PID: 6108)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 8436)
Application launched itself
- msedgewebview2.exe (PID: 4552)
- MicrosoftEdgeUpdate.exe (PID: 8180)
Searches for installed software
- setup.exe (PID: 2148)
Uses WMIC.EXE to obtain a list of video controllers
- lunela-launcher.exe (PID: 8176)
INFO
An automatically generated document
- msiexec.exe (PID: 7424)
Creates files or folders in the user directory
- msiexec.exe (PID: 7424)
- MicrosoftEdgeUpdate.exe (PID: 1432)
- MicrosoftEdgeUpdate.exe (PID: 8180)
- MicrosoftEdge_X64_146.0.3856.59.exe (PID: 4300)
- setup.exe (PID: 2148)
- msedgewebview2.exe (PID: 2944)
- msedgewebview2.exe (PID: 4552)
- msedgewebview2.exe (PID: 8492)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 7424)
- MicrosoftEdgeUpdate.exe (PID: 1432)
- msiexec.exe (PID: 132)
- MicrosoftEdgeUpdate.exe (PID: 8180)
- msedgewebview2.exe (PID: 4552)
- WMIC.exe (PID: 1872)
Reads the computer name
- msiexec.exe (PID: 8368)
- msiexec.exe (PID: 132)
- MicrosoftEdgeUpdate.exe (PID: 1432)
- MicrosoftEdgeUpdate.exe (PID: 6108)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 2764)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 8436)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 2548)
- MicrosoftEdgeUpdate.exe (PID: 7340)
- MicrosoftEdgeUpdate.exe (PID: 8180)
- MicrosoftEdgeUpdate.exe (PID: 9064)
- MicrosoftEdgeUpdate.exe (PID: 824)
- MicrosoftEdge_X64_146.0.3856.59.exe (PID: 4300)
- setup.exe (PID: 2148)
- MicrosoftEdgeUpdateCore.exe (PID: 7392)
- MicrosoftEdgeUpdate.exe (PID: 7544)
- lunela-launcher.exe (PID: 8176)
- msedgewebview2.exe (PID: 4552)
- msedgewebview2.exe (PID: 1656)
- msedgewebview2.exe (PID: 8492)
Checks supported languages
- msiexec.exe (PID: 8368)
- msiexec.exe (PID: 132)
- MicrosoftEdgeWebview2Setup.exe (PID: 8020)
- MicrosoftEdgeUpdate.exe (PID: 1432)
- MicrosoftEdgeUpdate.exe (PID: 6108)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 2764)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 2548)
- MicrosoftEdgeUpdate.exe (PID: 7340)
- MicrosoftEdgeUpdate.exe (PID: 9064)
- MicrosoftEdgeUpdate.exe (PID: 8180)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 8436)
- MicrosoftEdgeUpdate.exe (PID: 824)
- MicrosoftEdge_X64_146.0.3856.59.exe (PID: 4300)
- setup.exe (PID: 2148)
- MicrosoftEdgeUpdateCore.exe (PID: 7392)
- MicrosoftEdgeUpdate.exe (PID: 7544)
- msedgewebview2.exe (PID: 4552)
- msedgewebview2.exe (PID: 2944)
- msedgewebview2.exe (PID: 1656)
- msedgewebview2.exe (PID: 8492)
- msedgewebview2.exe (PID: 7340)
- lunela-launcher.exe (PID: 8176)
- msedgewebview2.exe (PID: 1128)
- msedgewebview2.exe (PID: 6340)
- msedgewebview2.exe (PID: 6336)
- msedgewebview2.exe (PID: 8108)
Executable content was dropped or overwritten
- msiexec.exe (PID: 7424)
Manages system restore points
- SrTasks.exe (PID: 6036)
Disables trace logs
- powershell.exe (PID: 5512)
The executable file from the user directory is run by the Powershell process
- MicrosoftEdgeWebview2Setup.exe (PID: 8020)
The sample compiled with english language support
- MicrosoftEdgeWebview2Setup.exe (PID: 8020)
- MicrosoftEdgeUpdate.exe (PID: 1432)
- MicrosoftEdge_X64_146.0.3856.59.exe (PID: 4300)
- setup.exe (PID: 2148)
Launching a file from a Registry key
- MicrosoftEdgeUpdate.exe (PID: 1432)
Create files in a temporary directory
- MicrosoftEdgeWebview2Setup.exe (PID: 8020)
- msedgewebview2.exe (PID: 4552)
Reads the machine GUID from the registry
- MicrosoftEdgeUpdate.exe (PID: 7340)
- MicrosoftEdgeUpdate.exe (PID: 8180)
- MicrosoftEdgeUpdate.exe (PID: 7544)
- msedgewebview2.exe (PID: 4552)
- lunela-launcher.exe (PID: 8176)
Process checks computer location settings
- MicrosoftEdgeUpdate.exe (PID: 1432)
- setup.exe (PID: 2148)
- msiexec.exe (PID: 132)
- msedgewebview2.exe (PID: 4552)
- msedgewebview2.exe (PID: 1128)
- msedgewebview2.exe (PID: 6340)
- msedgewebview2.exe (PID: 6336)
Manual execution by a user
- MicrosoftEdgeUpdateCore.exe (PID: 7392)
Reads Environment values
- MicrosoftEdgeUpdate.exe (PID: 7340)
- MicrosoftEdgeUpdate.exe (PID: 7544)
- msedgewebview2.exe (PID: 4552)
- msedgewebview2.exe (PID: 1656)
- lunela-launcher.exe (PID: 8176)
Creates a software uninstall entry
- setup.exe (PID: 2148)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (93.3) |
|---|---|---|
| .pps/ppt | | | Microsoft PowerPoint document (5.2) |
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| CodePage: | Windows Latin 1 (Western European) |
|---|---|
| Template: | x64;0 |
| RevisionNumber: | {691B9E35-02DE-4F1F-A723-398319705217} |
| Pages: | 450 |
| Words: | 2 |
| Software: | Windows Installer XML Toolset (3.14.1.8722) |
| Security: | Read-only recommended |
| Title: | Lunela Windows Installer |
| Subject: | Lunela Windows Installer |
| Author: | Lunela Company |
| Keywords: | - |
| Comments: | - |
| CreateDate: | 2022:12:19 07:37:13 |
| ModifyDate: | 2022:12:19 07:37:13 |
Total processes
184
Monitored processes
36
Malicious processes
7
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | C:\Windows\syswow64\MsiExec.exe -Embedding EE85E71BB5893B1A316D3DED61A1D38E C | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 824 | "C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe" /c | C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe | — | MicrosoftEdgeUpdateCore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update Exit code: 0 Version: 1.3.225.7 Modules
| |||||||||||||||
| 1128 | "C:\Users\admin\AppData\Local\Microsoft\EdgeWebView\Application\146.0.3856.59\msedgewebview2.exe" --type=renderer --noerrdialogs --user-data-dir="C:\Users\admin\AppData\Local\com.applauncher.desktop\EBWebView" --webview-exe-name=lunela-launcher.exe --webview-exe-version=25.16.4779.18068 --embedded-browser-webview=1 --embedded-browser-webview-dpi-awareness=2 --autoplay-policy=no-user-gesture-required --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--expose-gc --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=5 --ram-no-pressure-read-main-dll --metrics-shmem-handle=3684,i,8227165013455735078,163886100723167407,2097152 --field-trial-handle=1920,i,8729661157579333874,16724243557387991949,262144 --disable-features=msPdfOOUI,msSmartScreenProtection,msWebOOUI --variations-seed-version --pseudonymization-salt-handle=1924,i,17054463620771204064,16556782427357980503,4 --trace-process-track-uuid=3190708990997080739 --mojo-platform-channel-handle=3688 /prefetch:1 | C:\Users\admin\AppData\Local\Microsoft\EdgeWebView\Application\146.0.3856.59\msedgewebview2.exe | — | msedgewebview2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge WebView2 Version: 146.0.3856.59 Modules
| |||||||||||||||
| 1432 | C:\Users\admin\AppData\Local\Temp\EUF3D4.tmp\MicrosoftEdgeUpdate.exe /silent /install "appguid={F3017226-FE2A-4295-8BDF-00C3A9A7E4C5}&appname=Microsoft%20Edge%20Webview2%20Runtime&needsadmin=prefers" | C:\Users\admin\AppData\Local\Temp\EUF3D4.tmp\MicrosoftEdgeUpdate.exe | MicrosoftEdgeWebview2Setup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update Exit code: 0 Version: 1.3.225.7 Modules
| |||||||||||||||
| 1656 | "C:\Users\admin\AppData\Local\Microsoft\EdgeWebView\Application\146.0.3856.59\msedgewebview2.exe" --type=gpu-process --noerrdialogs --user-data-dir="C:\Users\admin\AppData\Local\com.applauncher.desktop\EBWebView" --webview-exe-name=lunela-launcher.exe --webview-exe-version=25.16.4779.18068 --embedded-browser-webview=1 --embedded-browser-webview-dpi-awareness=2 --gpu-preferences=SAAAAAAAAADgAAAEAAAAAAAAAAAAAGAAAQAAAAAAAAAAAAAAAAAAAAIAAAAAAAAAAAAAAAAAAAAQAAAAAAAAABAAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --startup-read-main-dll --metrics-shmem-handle=1716,i,15070462335431854352,13596586088690571462,262144 --field-trial-handle=1920,i,8729661157579333874,16724243557387991949,262144 --disable-features=msPdfOOUI,msSmartScreenProtection,msWebOOUI --variations-seed-version --pseudonymization-salt-handle=1924,i,17054463620771204064,16556782427357980503,4 --trace-process-track-uuid=3190708988185955192 --mojo-platform-channel-handle=1916 /prefetch:2 | C:\Users\admin\AppData\Local\Microsoft\EdgeWebView\Application\146.0.3856.59\msedgewebview2.exe | — | msedgewebview2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge WebView2 Version: 146.0.3856.59 Modules
| |||||||||||||||
| 1872 | "wmic" path win32_videocontroller get name,AdapterCompatibility /format:csv | C:\Windows\System32\wbem\WMIC.exe | — | lunela-launcher.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2148 | "C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\Install\{9C2B49F8-FF65-4B5D-A7A8-D1B0DE041364}\EDGEMITMP_89358.tmp\setup.exe" --install-archive="C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\Install\{9C2B49F8-FF65-4B5D-A7A8-D1B0DE041364}\MicrosoftEdge_X64_146.0.3856.59.exe" --msedgewebview --verbose-logging --do-not-launch-msedge --user-level | C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\Install\{9C2B49F8-FF65-4B5D-A7A8-D1B0DE041364}\EDGEMITMP_89358.tmp\setup.exe | MicrosoftEdge_X64_146.0.3856.59.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Installer Exit code: 0 Version: 146.0.3856.59 Modules
| |||||||||||||||
| 2548 | "C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\1.3.225.7\MicrosoftEdgeUpdateComRegisterShell64.exe" /user | C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\1.3.225.7\MicrosoftEdgeUpdateComRegisterShell64.exe | — | MicrosoftEdgeUpdate.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update COM Registration Helper Exit code: 0 Version: 1.3.225.7 Modules
| |||||||||||||||
| 2764 | "C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\1.3.225.7\MicrosoftEdgeUpdateComRegisterShell64.exe" /user | C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\1.3.225.7\MicrosoftEdgeUpdateComRegisterShell64.exe | — | MicrosoftEdgeUpdate.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update COM Registration Helper Exit code: 0 Version: 1.3.225.7 Modules
| |||||||||||||||
| 2944 | C:\Users\admin\AppData\Local\Microsoft\EdgeWebView\Application\146.0.3856.59\msedgewebview2.exe --type=crashpad-handler --user-data-dir=C:\Users\admin\AppData\Local\com.applauncher.desktop\EBWebView /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler --database=C:\Users\admin\AppData\Local\com.applauncher.desktop\EBWebView\Crashpad --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=146.0.7680.76 --annotation=exe=C:\Users\admin\AppData\Local\Microsoft\EdgeWebView\Application\146.0.3856.59\msedgewebview2.exe --annotation=plat=Win64 "--annotation=prod=Edge WebView2" --annotation=ver=146.0.3856.59 --initial-client-data=0x184,0x188,0x18c,0x160,0x194,0x7ffd6ea324d8,0x7ffd6ea324e4,0x7ffd6ea324f0 | C:\Users\admin\AppData\Local\Microsoft\EdgeWebView\Application\146.0.3856.59\msedgewebview2.exe | — | msedgewebview2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge WebView2 Version: 146.0.3856.59 Modules
| |||||||||||||||
Total events
33 337
Read events
30 444
Write events
2 816
Delete events
77
Modification events
| (PID) Process: | (8368) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4800000000000000792AF98816B3DC01B0200000E40A0000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (8368) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 4800000000000000792AF98816B3DC01B0200000E40A0000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (8368) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 480000000000000007AF5F8916B3DC01B0200000E40A0000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (8368) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 480000000000000007AF5F8916B3DC01B0200000E40A0000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (8368) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 48000000000000006511628916B3DC01B0200000E40A0000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (8368) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4800000000000000FBD5668916B3DC01B0200000E40A0000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (8368) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 48000000000000004A72838916B3DC01B0200000E40A0000D30700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (8228) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000AE22948916B3DC012420000074120000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (8228) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000AE22948916B3DC0124200000EC100000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (8228) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Leave) |
Value: 48000000000000001285968916B3DC012420000074120000E80300000000000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
206
Suspicious files
109
Text files
73
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 8368 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 8368 | msiexec.exe | C:\Windows\Installer\1ecf63.msi | — | |
MD5:— | SHA256:— | |||
| 8368 | msiexec.exe | C:\Program Files\Lunela Launcher\lunela-launcher.exe | — | |
MD5:— | SHA256:— | |||
| 8368 | msiexec.exe | C:\Windows\Installer\1ecf65.msi | — | |
MD5:— | SHA256:— | |||
| 7424 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\C8E534EE129F27D55460CE17FD628216_1130D9B25898B0DB0D4F04DC5B93F141 | binary | |
MD5:CC0C4FBD540C5BD30F6D1A2AB922702A | SHA256:F689862B5FA4FC8F0E95BCFA259D36A37ADC82DB54F227CD1E5D7296F9FABED1 | |||
| 7424 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\698460A0B6E60F2F602361424D832905_8BB23D43DE574E82F2BEE0DF0EC47EEB | binary | |
MD5:0D623BE078FE295310613425B6556278 | SHA256:0E74B0C5C5374C1185E83AB1995D20B9D39C48B9CCF4BB8109CB7164E25F1620 | |||
| 7424 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\C8E534EE129F27D55460CE17FD628216_1130D9B25898B0DB0D4F04DC5B93F141 | binary | |
MD5:956B94B4091BD9D418575D8E7D287675 | SHA256:A1AFCA0B284F933FB41529A32BA84E39A6AF09CC1692AC880EF4348505209957 | |||
| 7424 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\8EC9B1D0ABBD7F98B401D425828828CE_C6BEFFBBCAA7B5B9D27EF4403AA033DE | binary | |
MD5:C06A716E035E28E8C35778D92114C637 | SHA256:25990F8A2E4FBA98545D23EA32AD97F991E74FF6C417FEFF8EBEDF0F504829B9 | |||
| 7424 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI98E2.tmp | executable | |
MD5:CFBB8568BD3711A97E6124C56FCFA8D9 | SHA256:7F47D98AB25CFEA9B3A2E898C3376CC9BA1CD893B4948B0C27CAA530FD0E34CC | |||
| 7424 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\698460A0B6E60F2F602361424D832905_8BB23D43DE574E82F2BEE0DF0EC47EEB | binary | |
MD5:87EF9108CD68491C5F71D6356D41B265 | SHA256:11C1A18E8DF39F6C740EBAB49D48CEE8AA6346A0E8588944408BC3F91B21190D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
122
TCP/UDP connections
91
DNS requests
39
Threats
14
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6768 | MoUsoCoreWorker.exe | GET | 200 | 23.32.238.107:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7228 | svchost.exe | GET | 200 | 23.32.238.107:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.32.238.107:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7228 | svchost.exe | GET | 200 | 23.59.18.102:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6768 | MoUsoCoreWorker.exe | GET | 200 | 23.59.18.102:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.59.18.102:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | POST | 200 | 40.126.31.3:443 | https://login.live.com/RST2.srf | unknown | text | 1.24 Kb | whitelisted |
— | — | POST | 400 | 20.190.159.75:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | binary | 203 b | whitelisted |
— | — | POST | 400 | 40.126.31.131:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | binary | 203 b | whitelisted |
— | — | POST | 400 | 20.190.159.68:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | text | 203 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 2.16.204.151:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
7228 | svchost.exe | 23.32.238.107:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
6768 | MoUsoCoreWorker.exe | 23.32.238.107:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 23.32.238.107:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
7228 | svchost.exe | 23.59.18.102:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 23.59.18.102:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5512 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
— | — | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
— | — | Misc activity | ET INFO Request for EXE via Powershell |
— | — | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
— | — | Misc activity | ET INFO Packed Executable Download |
5512 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
5512 | powershell.exe | Misc activity | ET INFO Request for EXE via Powershell |
5512 | powershell.exe | Misc activity | ET INFO Packed Executable Download |
5080 | svchost.exe | Misc activity | ET INFO Packed Executable Download |
8492 | msedgewebview2.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
Process | Message |
|---|---|
msedgewebview2.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\com.applauncher.desktop directory exists )
|