| File name: | 32bit_matan_edit |
| Full analysis: | https://app.any.run/tasks/f3464020-df87-4fb6-ace4-623727ff37e0 |
| Verdict: | Malicious activity |
| Analysis date: | June 18, 2019, 19:26:02 |
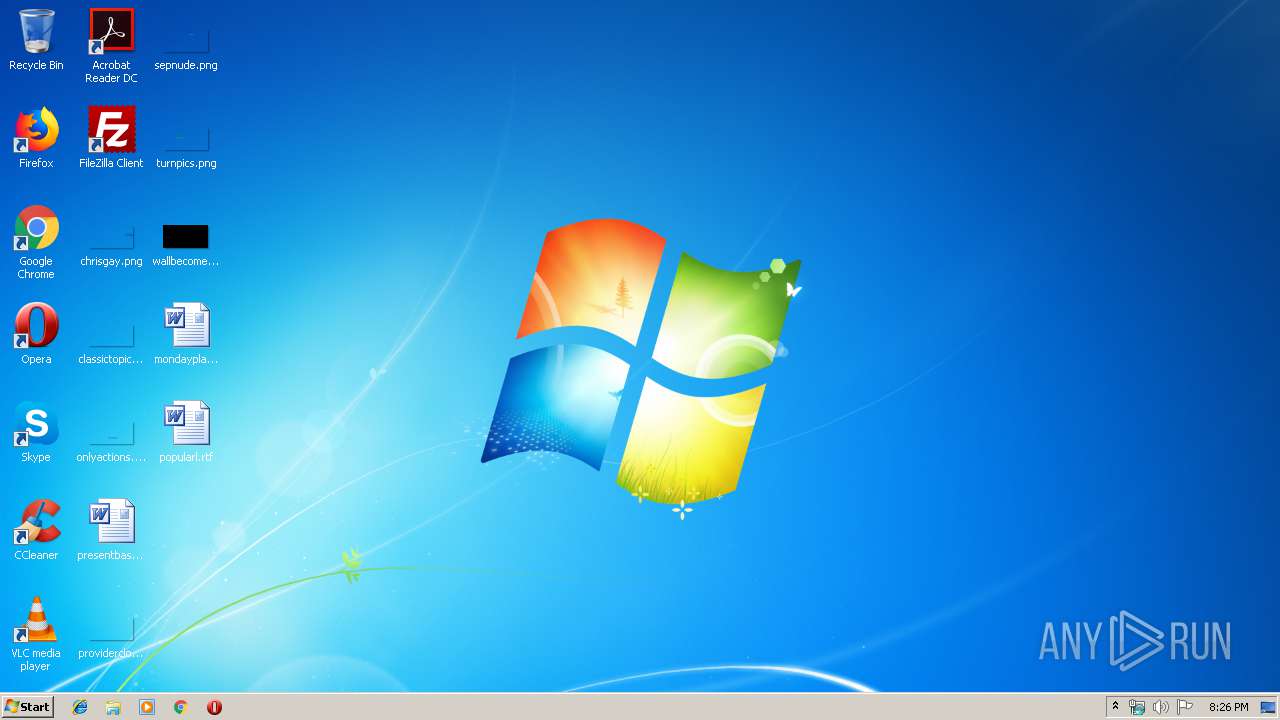
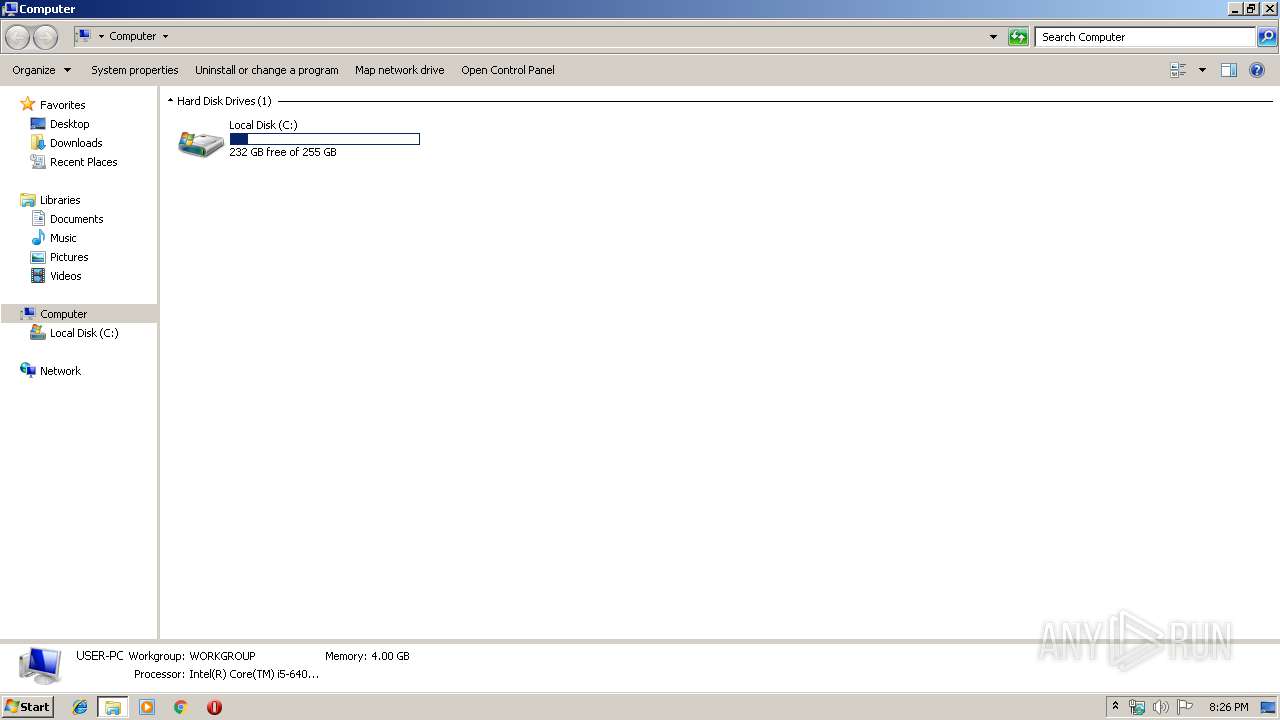
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | 9C73199CEAC47372615A4322293A9842 |
| SHA1: | AD12E3270FEE17404D97B3EB117E89B0BFD973B5 |
| SHA256: | BBA04AE2BF02BC0DD1C1219983CB8271D47F739C59A7A5897B8FE5EE0CE550F5 |
| SSDEEP: | 1536:EKPR3b59Ffvcw61YrlwKARUv1+WIp+/jNwCC71R1J5N6lwSp:EEJbPVvcw61YrWVevAWi+/jiBR1JLdSp |
MALICIOUS
Deletes shadow copies
- jtVqXv:exe (PID: 2608)
Changes the autorun value in the registry
- 32bit_matan_edit.exe (PID: 3080)
SUSPICIOUS
Starts CMD.EXE for commands execution
- 32bit_matan_edit.exe (PID: 3080)
Executable content was dropped or overwritten
- 32bit_matan_edit.exe (PID: 3080)
Starts application with an unusual extension
- 32bit_matan_edit.exe (PID: 3080)
- odvD.exe (PID: 2580)
Starts itself from another location
- 32bit_matan_edit.exe (PID: 3080)
Starts NET.EXE for network exploration
- Ekv:exe (PID: 3484)
Creates files in the program directory
- jtVqXv:exe (PID: 2608)
INFO
Dropped object may contain Bitcoin addresses
- jtVqXv:exe (PID: 2608)
Dropped object may contain TOR URL's
- jtVqXv:exe (PID: 2608)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:10:22 09:48:04+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 12 |
| CodeSize: | 12288 |
| InitializedDataSize: | 86016 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3a90 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows command line |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 22-Oct-2017 07:48:04 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 22-Oct-2017 07:48:04 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00003000 | 0x00003000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_LNK_COMDAT, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_TYPE_DSECT | 5.96467 |
.rdata | 0x00004000 | 0x00002000 | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.23944 |
.data | 0x00006000 | 0x00012000 | 0x00011000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.85157 |
.reloc | 0x00018000 | 0x00000174 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ, IMAGE_SCN_TYPE_DSECT | 0.906846 |
Imports
ADVAPI32.dll |
CFGMGR32.dll |
CLUSAPI.dll |
CRYPT32.dll |
KERNEL32.dll |
MSACM32.dll |
NETAPI32.dll |
OLEAUT32.dll |
POWRPROF.dll |
RASAPI32.dll |
Total processes
50
Monitored processes
7
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2312 | C:\Windows\system32\net.exe view | C:\Windows\system32\net.exe | — | Ekv:exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2580 | C:\Users\admin\AppData\Local\13XF\odvD.exe 1 C:\Users\admin\AppData\Local\Temp\32BIT_~1.EXE | C:\Users\admin\AppData\Local\13XF\odvD.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
| 2608 | C:\Users\admin\AppData\Local\jtVqXv:exe 3 C:\Users\admin\AppData\Local\13XF\odvD.exe | C:\Users\admin\AppData\Local\jtVqXv:exe | — | odvD.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2744 | C:\Windows\system32\vssadmin.exe Delete Shadows /All /Quiet | C:\Windows\system32\vssadmin.exe | — | jtVqXv:exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Command Line Interface for Microsoft® Volume Shadow Copy Service Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3080 | "C:\Users\admin\AppData\Local\Temp\32bit_matan_edit.exe" | C:\Users\admin\AppData\Local\Temp\32bit_matan_edit.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 3328 | "C:\Windows\System32\cmd.exe" /c C:\Users\admin\AppData\Local\13XF\odvD.exe 1 C:\Users\admin\AppData\Local\Temp\32BIT_~1.EXE | C:\Windows\System32\cmd.exe | 32bit_matan_edit.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3484 | C:\Users\admin\AppData\Local\Ekv:exe 2 | C:\Users\admin\AppData\Local\Ekv:exe | — | 32bit_matan_edit.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
Total events
75
Read events
70
Write events
5
Delete events
0
Modification events
| (PID) Process: | (3080) 32bit_matan_edit.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | FrZxujS5jwzDN |
Value: C:\Users\admin\AppData\Local\uS6Ch\oat5.exe | |||
| (PID) Process: | (3080) 32bit_matan_edit.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3080) 32bit_matan_edit.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
7
Suspicious files
1 719
Text files
1 804
Unknown types
46
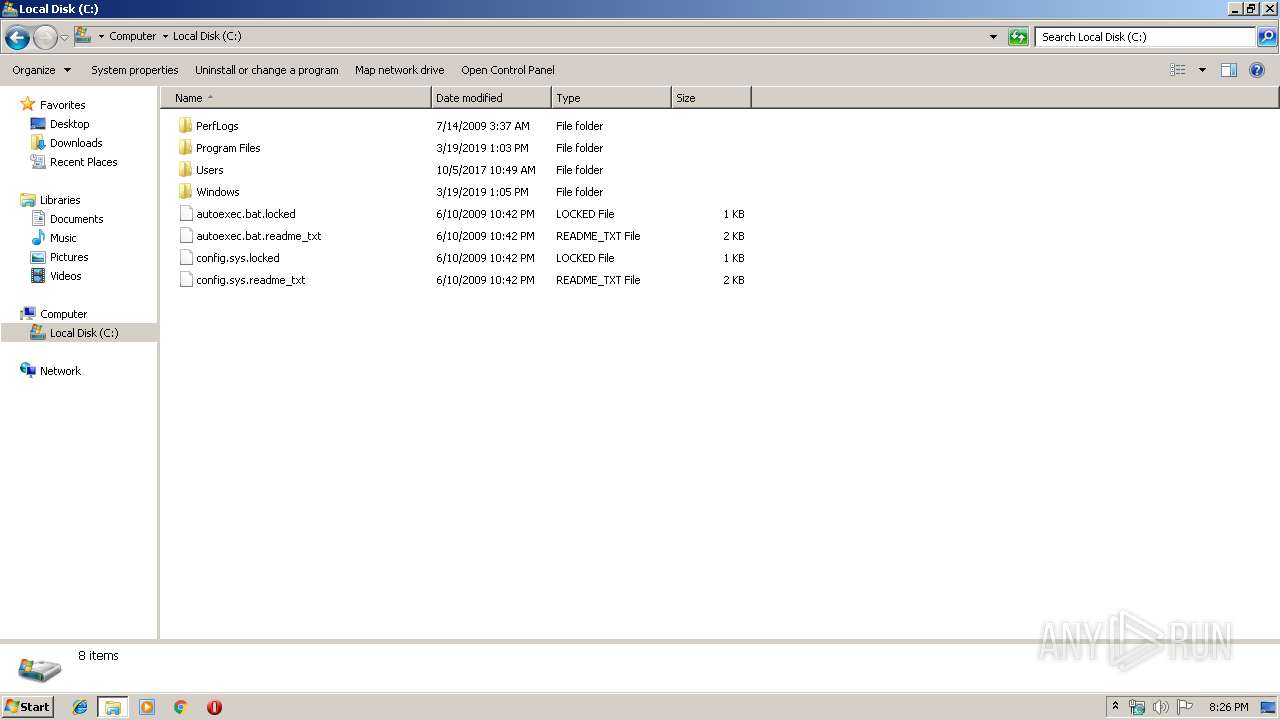
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2580 | odvD.exe | C:\Users\admin\AppData\Local\jtVqXv:exe | — | |
MD5:— | SHA256:— | |||
| 2608 | jtVqXv:exe | C:\autoexec.bat | — | |
MD5:— | SHA256:— | |||
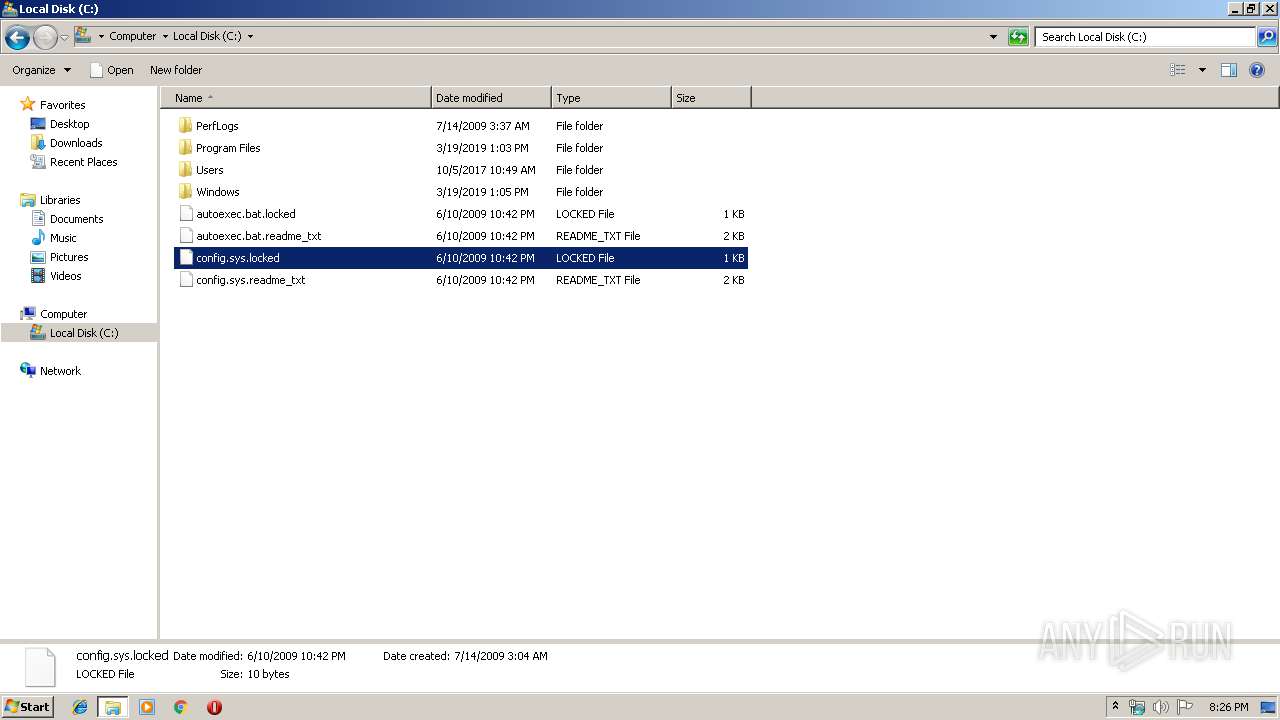
| 2608 | jtVqXv:exe | C:\config.sys | — | |
MD5:— | SHA256:— | |||
| 2608 | jtVqXv:exe | C:\config.sys.locked | — | |
MD5:— | SHA256:— | |||
| 2608 | jtVqXv:exe | C:\MSOCache\All Users\{90140000-0016-0409-0000-0000000FF1CE}-C\ExcelLR.cab | — | |
MD5:— | SHA256:— | |||
| 2608 | jtVqXv:exe | C:\MSOCache\All Users\{90140000-0016-0409-0000-0000000FF1CE}-C\ExcelLR.cab.locked | — | |
MD5:— | SHA256:— | |||
| 2608 | jtVqXv:exe | C:\MSOCache\All Users\{90140000-0016-0409-0000-0000000FF1CE}-C\ExcelMUI.msi | — | |
MD5:— | SHA256:— | |||
| 2608 | jtVqXv:exe | C:\MSOCache\All Users\{90140000-0016-0409-0000-0000000FF1CE}-C\ExcelMUI.xml | — | |
MD5:— | SHA256:— | |||
| 2608 | jtVqXv:exe | C:\MSOCache\All Users\{90140000-0016-0409-0000-0000000FF1CE}-C\Setup.xml | — | |
MD5:— | SHA256:— | |||
| 2608 | jtVqXv:exe | C:\MSOCache\All Users\{90140000-0018-0409-0000-0000000FF1CE}-C\PowerPointMUI.msi | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report