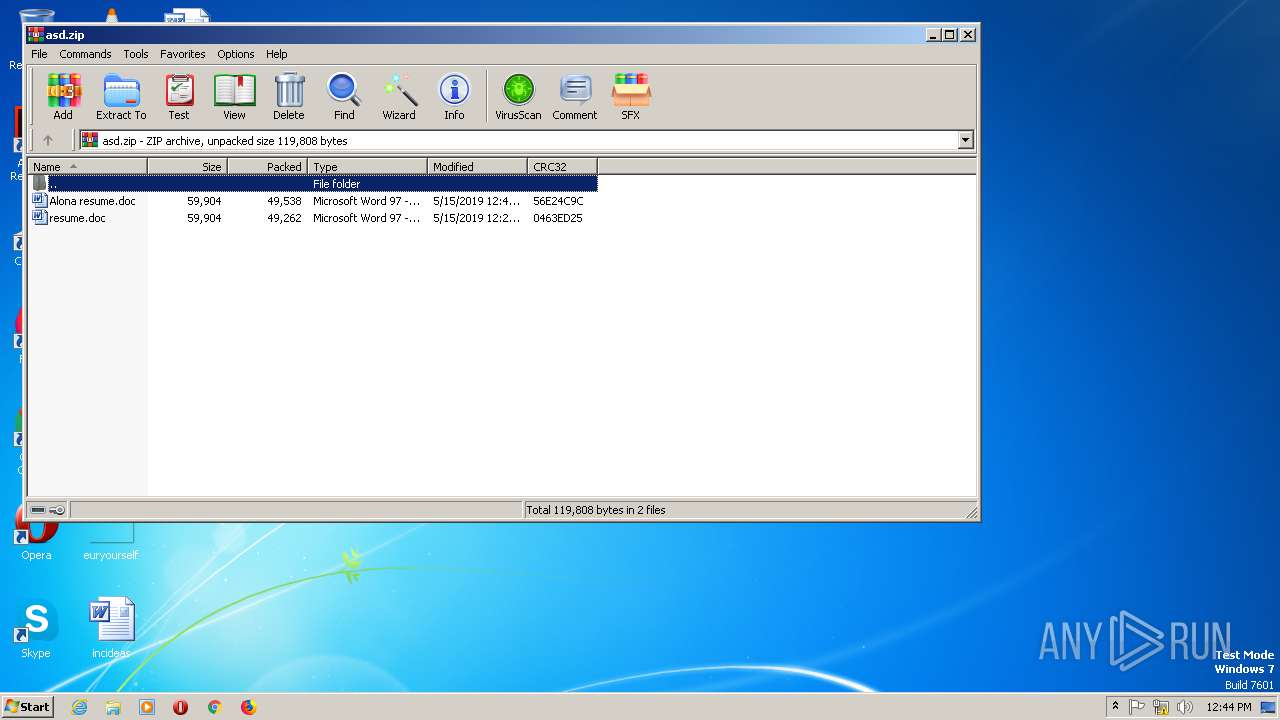
| File name: | asd.zip |
| Full analysis: | https://app.any.run/tasks/30e5e50e-0f49-4046-b2c4-48c512f9dca3 |
| Verdict: | Malicious activity |
| Analysis date: | May 15, 2019, 12:44:05 |
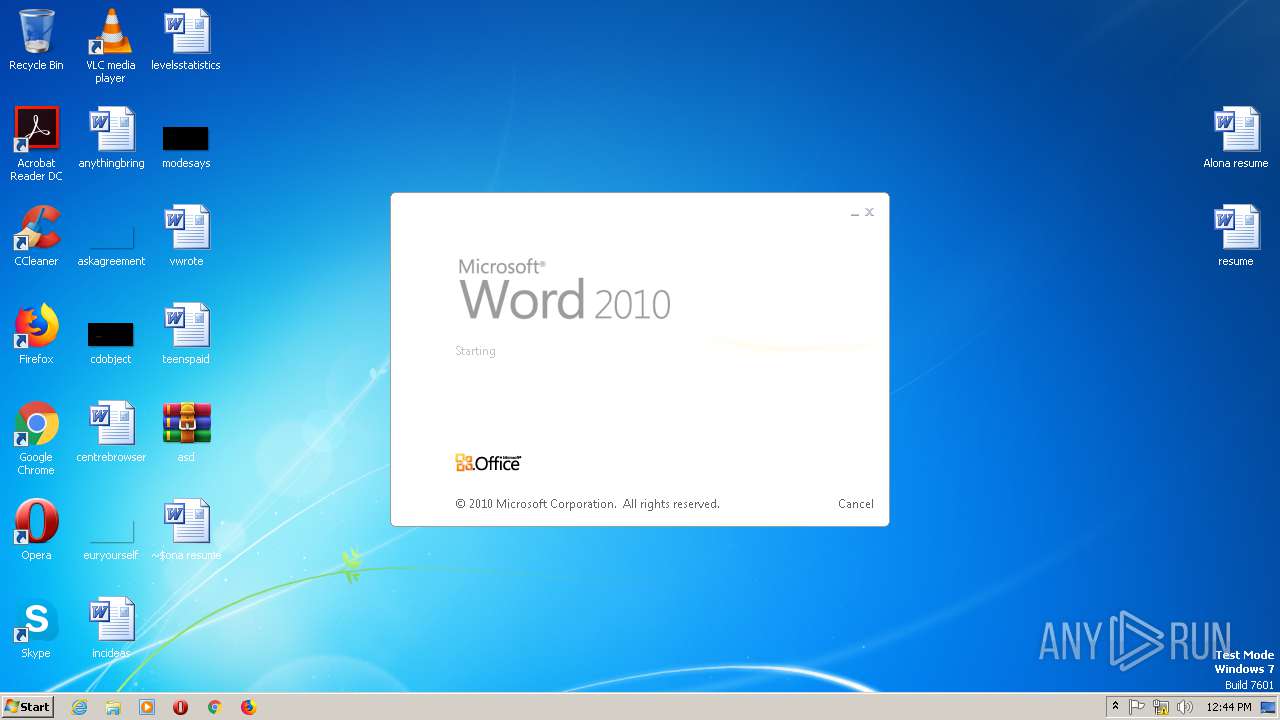
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 685AA3DA091A239473D99FCFE4D1C64D |
| SHA1: | C943EDB24A3DAC8EB85A2C9C5200FA211B67B654 |
| SHA256: | BB864A8D25B367C34AD814BC5BD404C158B668C9441A8EDFD16D6DBD58F9BB6E |
| SSDEEP: | 3072:UdosbDLuIrxliXyLnygZKqRS9IsAw+Wb1qPlP6:U7FxrZKXIsr1qPJ6 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads the machine GUID from the registry
- WinRAR.exe (PID: 2916)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2992)
- WINWORD.EXE (PID: 2636)
Reads the machine GUID from the registry
- WINWORD.EXE (PID: 2992)
- WINWORD.EXE (PID: 2636)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:05:15 14:40:02 |
| ZipCRC: | 0x56e24c9c |
| ZipCompressedSize: | 49538 |
| ZipUncompressedSize: | 59904 |
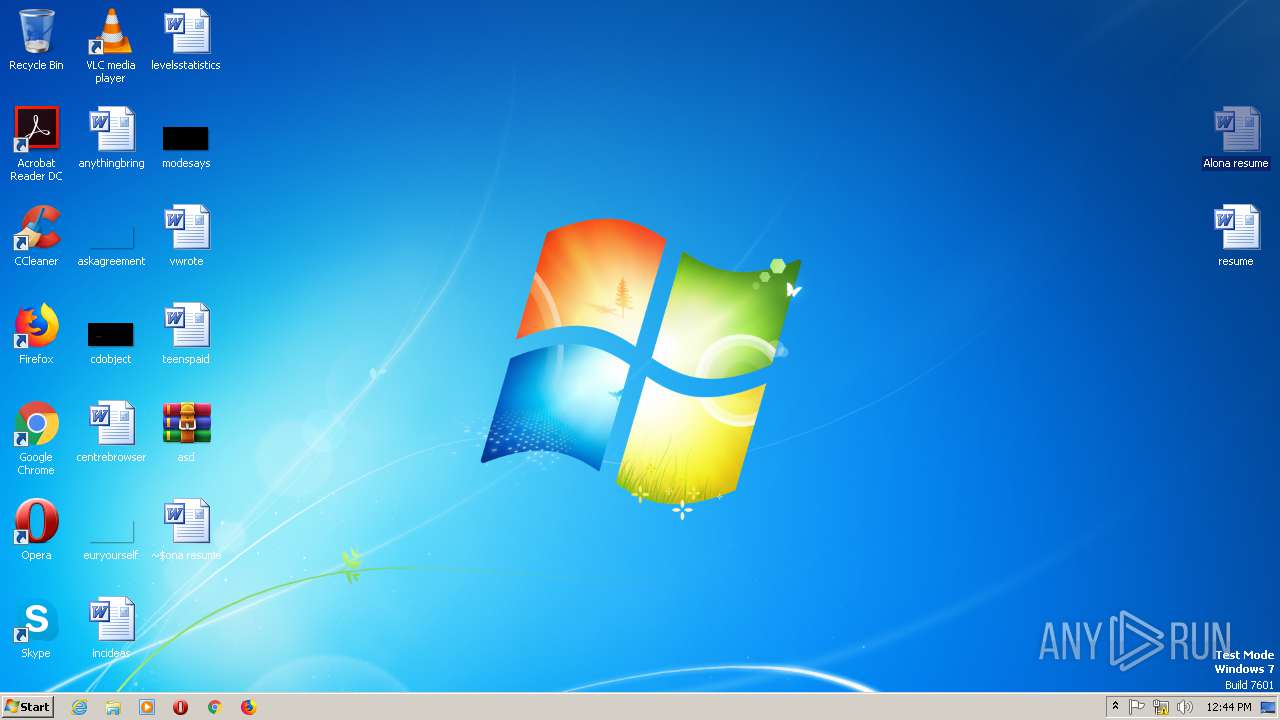
| ZipFileName: | Alona resume.doc |
Total processes
38
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
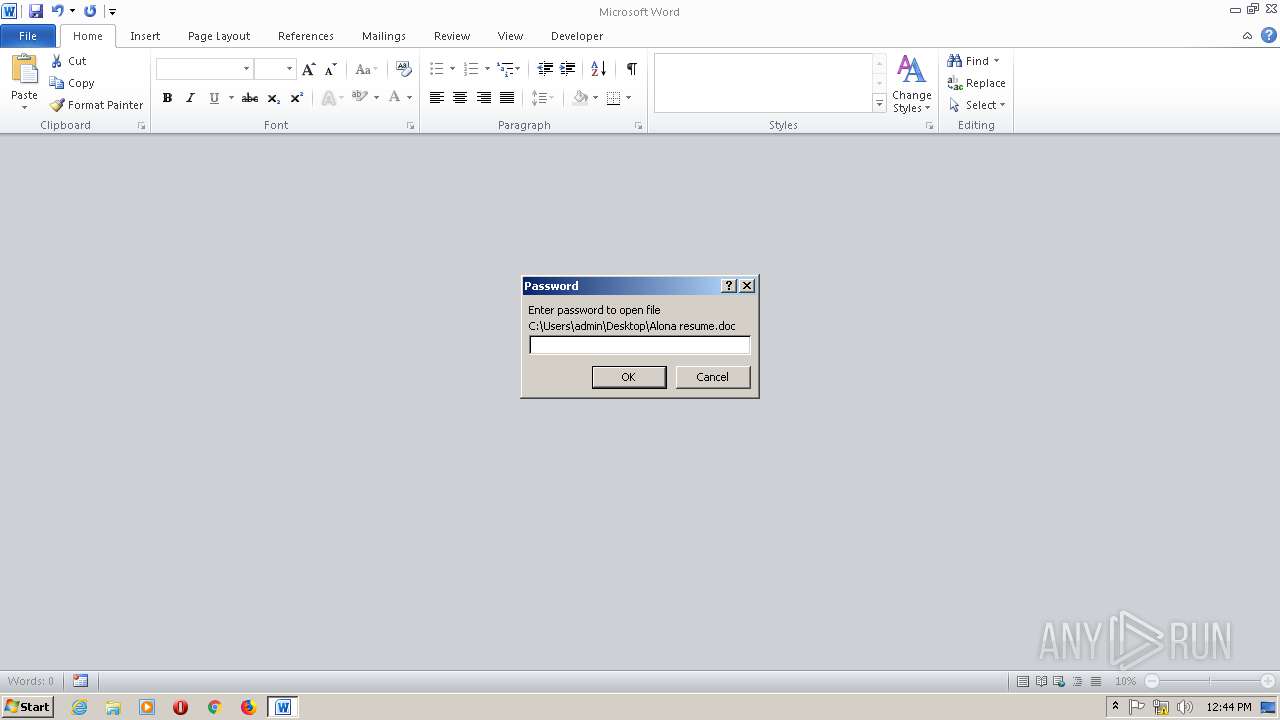
| 2636 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\Alona resume.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.5123.5000 Modules
| |||||||||||||||
| 2916 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\asd.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
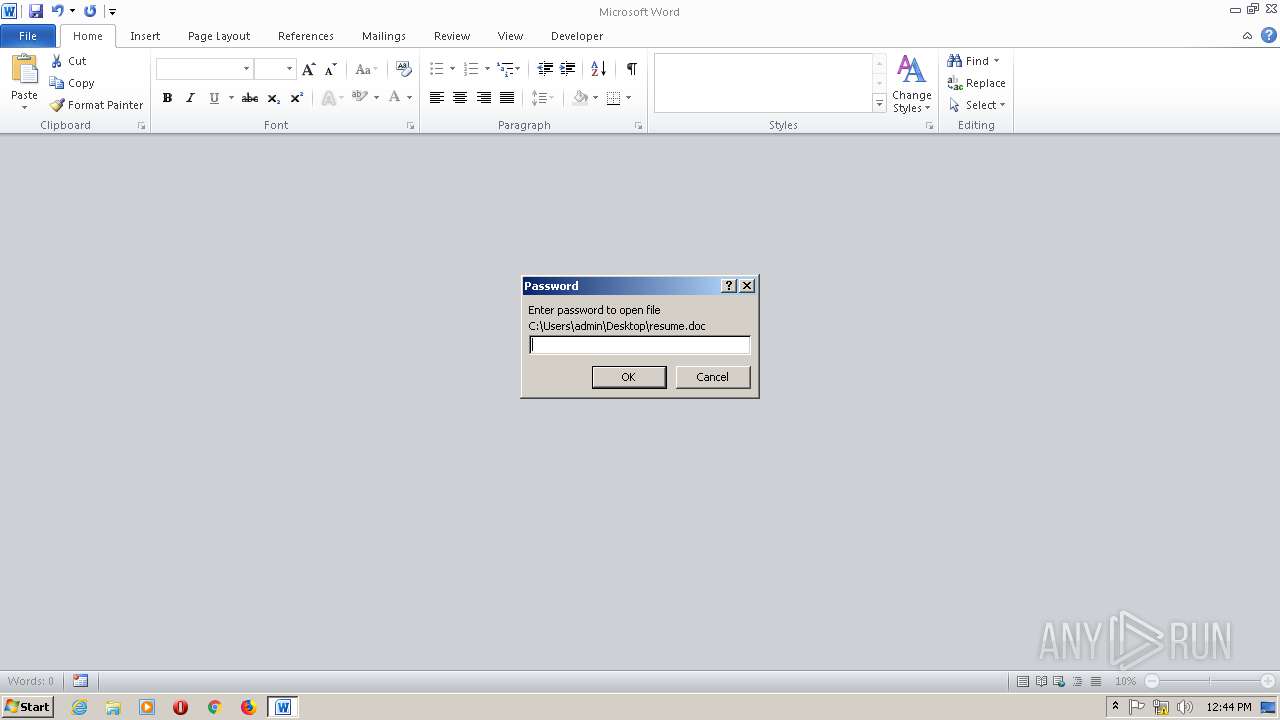
| 2992 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\resume.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.5123.5000 Modules
| |||||||||||||||
Total events
1 228
Read events
1 146
Write events
70
Delete events
12
Modification events
| (PID) Process: | (2916) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2916) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2916) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\65\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2916) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\asd.zip | |||
| (PID) Process: | (2916) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2916) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2916) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2916) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2916) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF1600000016000000D60300000B020000 | |||
| (PID) Process: | (2916) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\General |
| Operation: | write | Name: | LastFolder |
Value: C:\Users\admin\Desktop | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
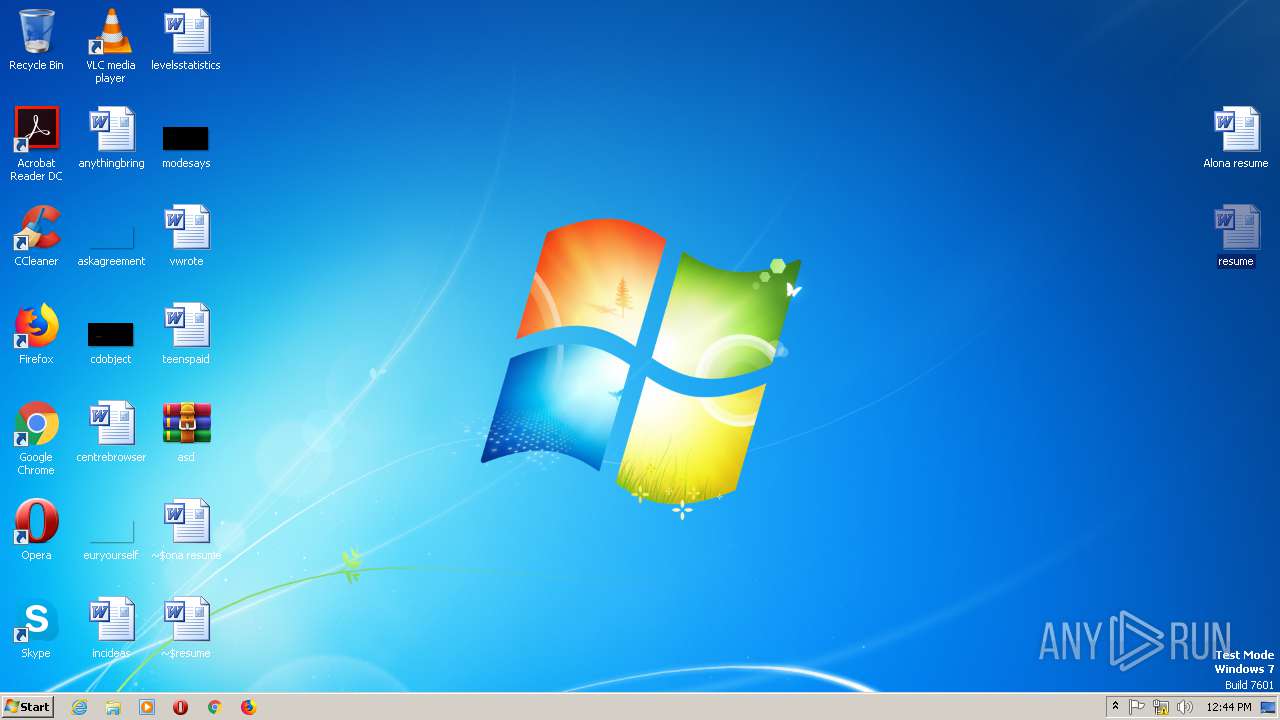
| 2916 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2916.27065\Alona resume.doc | — | |
MD5:— | SHA256:— | |||
| 2916 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2916.27065\resume.doc | — | |
MD5:— | SHA256:— | |||
| 2636 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR235E.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2636 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF81419FE062771337.TMP | — | |
MD5:— | SHA256:— | |||
| 2636 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF67B6B8B9A7A82560.TMP | — | |
MD5:— | SHA256:— | |||
| 2636 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF8A228C4EA7D3594B.TMP | — | |
MD5:— | SHA256:— | |||
| 2636 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF5641BCF8E563A2D6.TMP | — | |
MD5:— | SHA256:— | |||
| 2636 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFDE0C3AFC29B3D5A4.TMP | — | |
MD5:— | SHA256:— | |||
| 2636 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{FA779EC6-8B22-42D0-98DC-482A68513EDB}.tmp | — | |
MD5:— | SHA256:— | |||
| 2992 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR4686.tmp.cvr | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report