| File name: | 2f93b97f-3002-4549-a641-f02157896893.mp4 |
| Full analysis: | https://app.any.run/tasks/a1067f1a-618b-468a-9da9-7f2e9d75da34 |
| Verdict: | Malicious activity |
| Analysis date: | November 29, 2020, 20:07:16 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | video/mp4 |
| File info: | ISO Media, MP4 Base Media v1 [IS0 14496-12:2003] |
| MD5: | 15E522D6F9EF3D8F0C4EAB86FA941CD5 |
| SHA1: | C90CD2519E323DB30170856AEA206FB5ACE0F73F |
| SHA256: | BB7F1752EB55F09C4C9AB6E4D6A9D435F00695A0AA80A80CB6D4351847C7124C |
| SSDEEP: | 3072:gp2qTNRhZ9mhkVASAzkMoLwB2CLL9vBCauIGSg6RUtbf3M5a91fg5oHKQb6mvUPp:gZZchQAhzkMSE2WRvEz+abf85ajuEXbM |
MALICIOUS
No malicious indicators.SUSPICIOUS
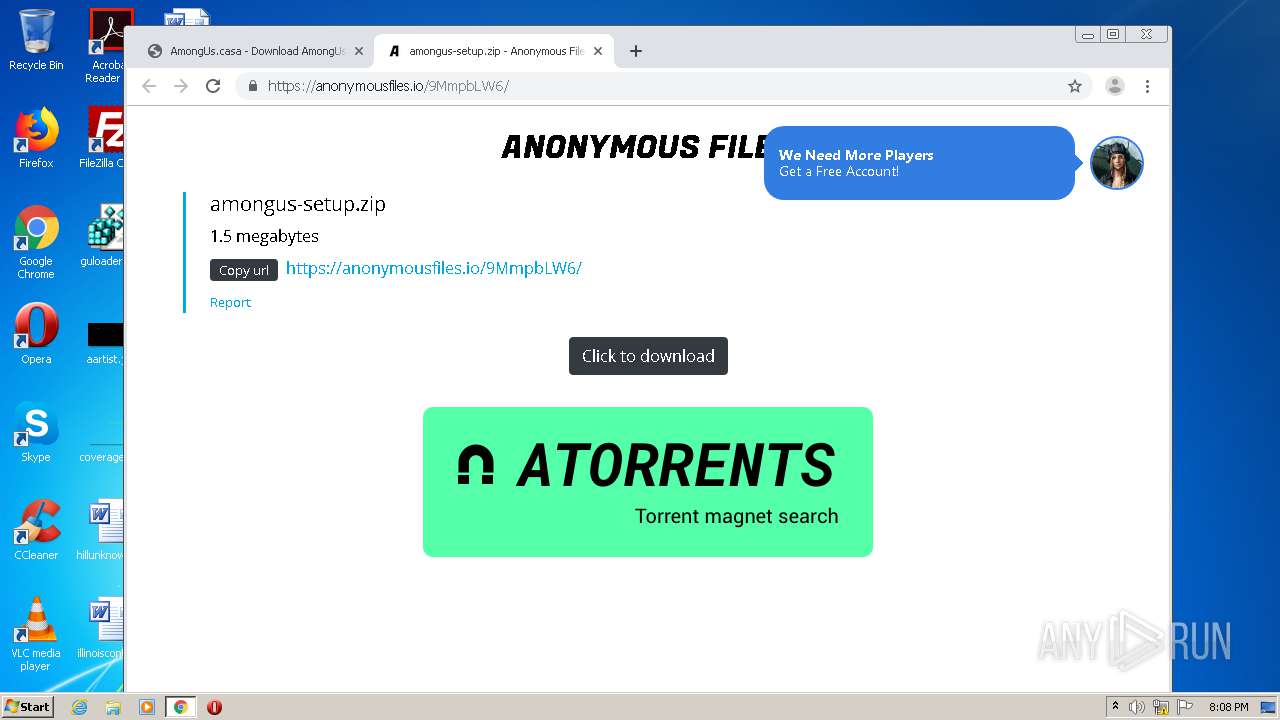
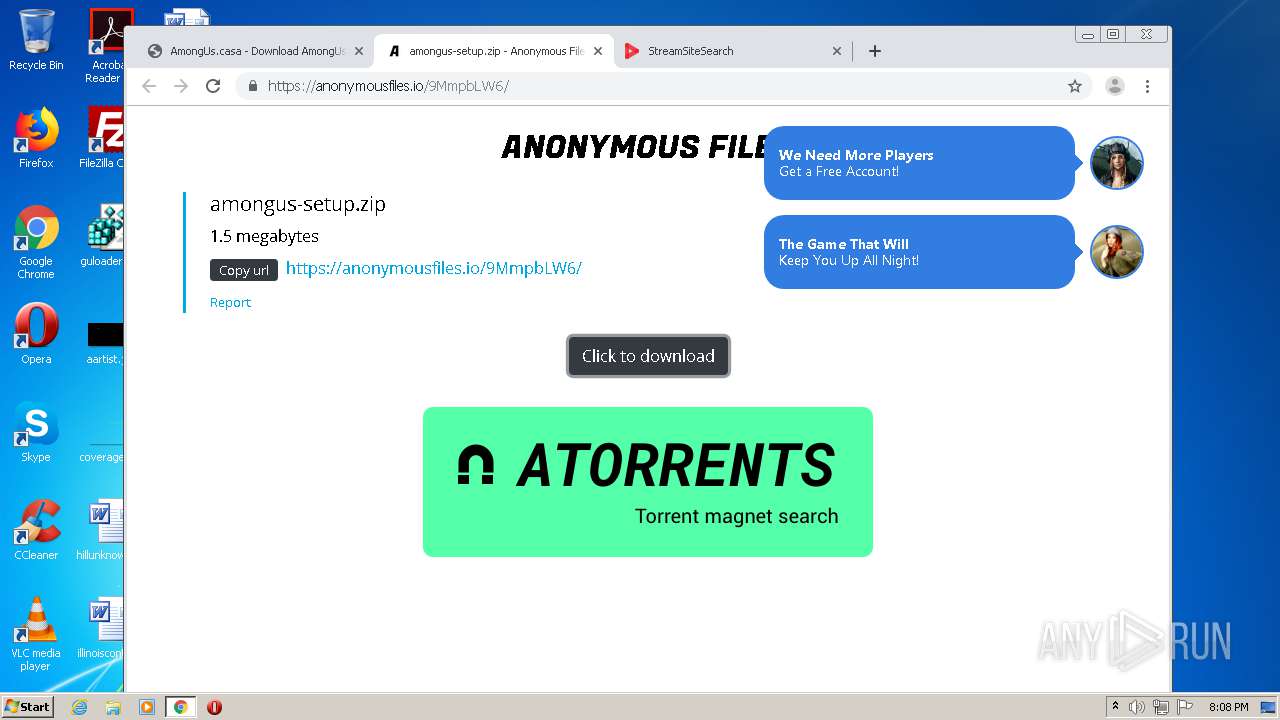
Creates files in the user directory
- vlc.exe (PID: 1904)
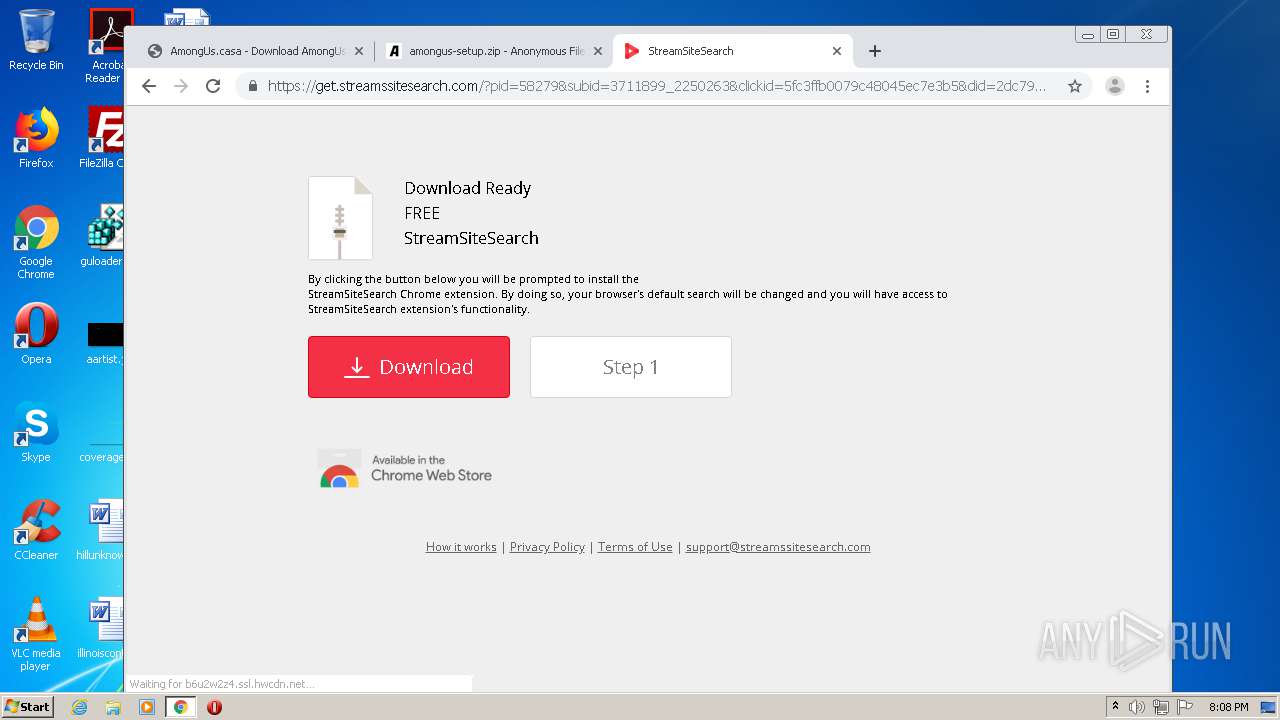
Modifies files in Chrome extension folder
- chrome.exe (PID: 1784)
INFO
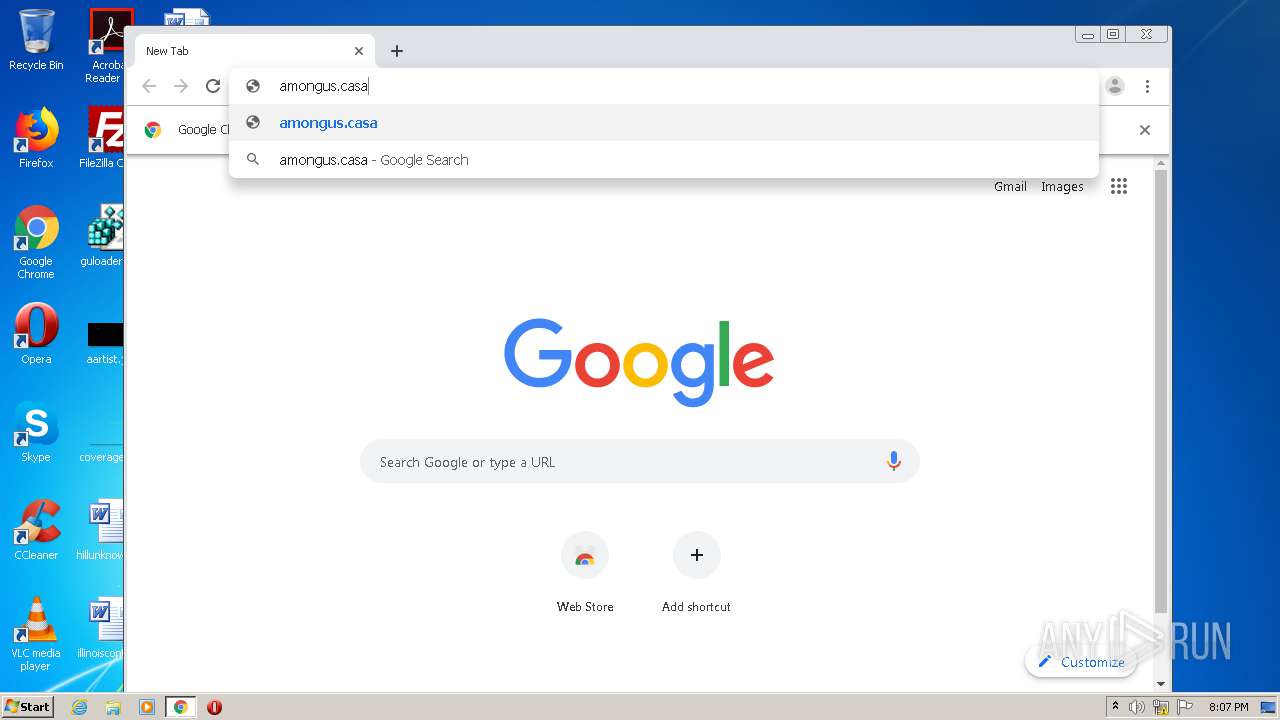
Manual execution by user
- chrome.exe (PID: 1784)
Application launched itself
- chrome.exe (PID: 1784)
Reads the hosts file
- chrome.exe (PID: 1784)
- chrome.exe (PID: 3316)
Creates files in the user directory
- chrome.exe (PID: 1784)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .m4v | | | MPEG-4 Video (36.7) |
|---|---|---|
| .m4r | | | iPhone Ringtone (33) |
| .3g2 | | | 3GPP2 multimedia audio/video (25.4) |
| .mov | | | QuickTime Movie (2.6) |
| .mp4 | | | Generic MP4 container (1.5) |
EXIF
QuickTime
| MajorBrand: | MP4 Base Media v1 [IS0 14496-12:2003] |
|---|---|
| MinorVersion: | 0.2.0 |
| CompatibleBrands: |
|
| MovieDataSize: | 159128 |
| MovieDataOffset: | 48 |
| MovieHeaderVersion: | - |
| CreateDate: | 0000:00:00 00:00:00 |
| ModifyDate: | 0000:00:00 00:00:00 |
| TimeScale: | 1000 |
| Duration: | 1.17 s |
| PreferredRate: | 1 |
| PreferredVolume: | 100.00% |
| PreviewTime: | 0 s |
| PreviewDuration: | 0 s |
| PosterTime: | 0 s |
| SelectionTime: | 0 s |
| SelectionDuration: | 0 s |
| CurrentTime: | 0 s |
| NextTrackID: | 3 |
| TrackHeaderVersion: | - |
| TrackCreateDate: | 0000:00:00 00:00:00 |
| TrackModifyDate: | 0000:00:00 00:00:00 |
| TrackID: | 1 |
| TrackDuration: | 1.17 s |
| TrackLayer: | - |
| TrackVolume: | 0.00% |
| ImageWidth: | 1136 |
| ImageHeight: | 480 |
| GraphicsMode: | srcCopy |
| OpColor: | 0 0 0 |
| CompressorID: | avc1 |
| SourceImageWidth: | 1136 |
| SourceImageHeight: | 480 |
| XResolution: | 72 |
| YResolution: | 72 |
| BitDepth: | 24 |
| PixelAspectRatio: | 1350:1349 |
| VideoFrameRate: | 30 |
| MatrixStructure: | 1 0 0 0 1 0 0 0 1 |
| MediaHeaderVersion: | - |
| MediaCreateDate: | 0000:00:00 00:00:00 |
| MediaModifyDate: | 0000:00:00 00:00:00 |
| MediaTimeScale: | 48000 |
| MediaDuration: | 1.17 s |
| MediaLanguageCode: | und |
| HandlerDescription: | SoundHandler |
| Balance: | - |
| AudioFormat: | mp4a |
| AudioChannels: | 2 |
| AudioBitsPerSample: | 16 |
| AudioSampleRate: | 48000 |
| HandlerType: | Metadata |
| HandlerVendorID: | Apple |
| Encoder: | Lavf57.56.100 |
Composite
| AvgBitrate: | 1.08 Mbps |
|---|---|
| ImageSize: | 1136x480 |
| Megapixels: | 0.545 |
| Rotation: | - |
Total processes
79
Monitored processes
43
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 464 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,9541674257820138779,5657722152658878465,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11572729275462645593 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2508 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 736 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,9541674257820138779,5657722152658878465,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4327974431903796549 --mojo-platform-channel-handle=3844 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 752 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,9541674257820138779,5657722152658878465,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16775989379074818731 --mojo-platform-channel-handle=4436 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 780 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,9541674257820138779,5657722152658878465,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4403723451774826932 --mojo-platform-channel-handle=3456 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1132 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,9541674257820138779,5657722152658878465,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17091298892685787418 --mojo-platform-channel-handle=3544 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1248 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,9541674257820138779,5657722152658878465,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15858311006617107640 --mojo-platform-channel-handle=4136 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1500 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=1152 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1784 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1828 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,9541674257820138779,5657722152658878465,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17059439871658472834 --renderer-client-id=35 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1972 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
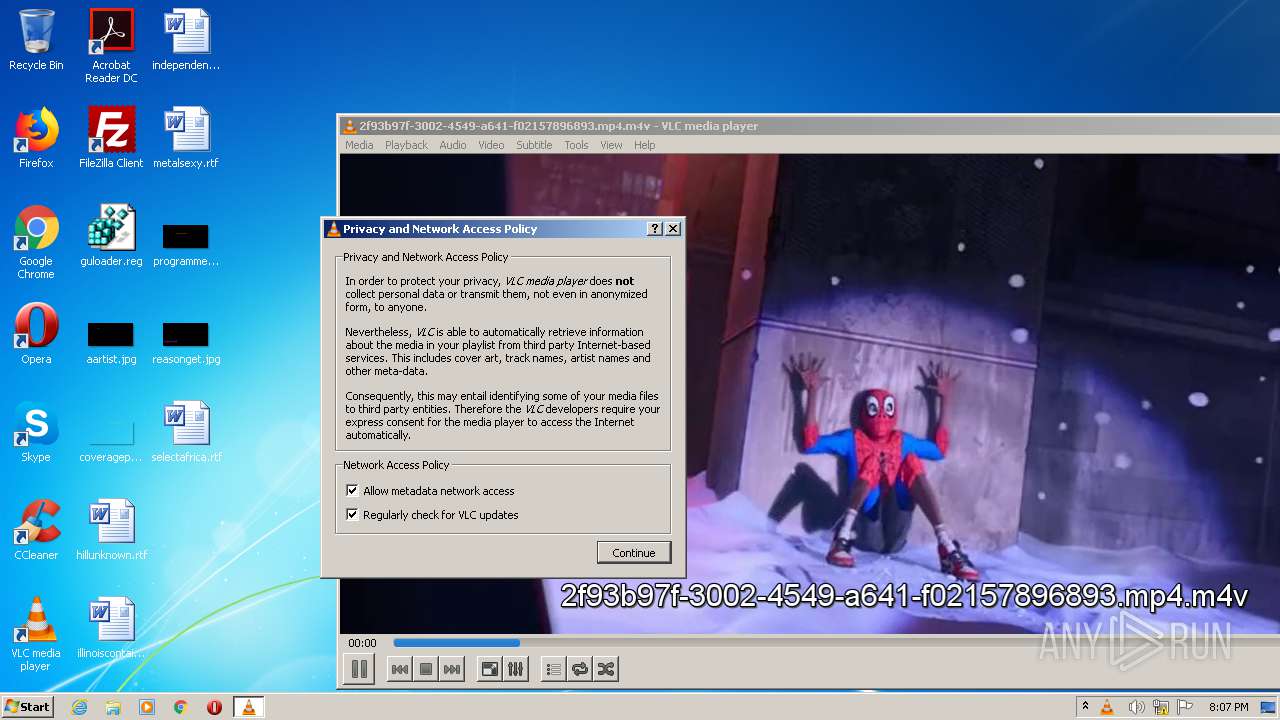
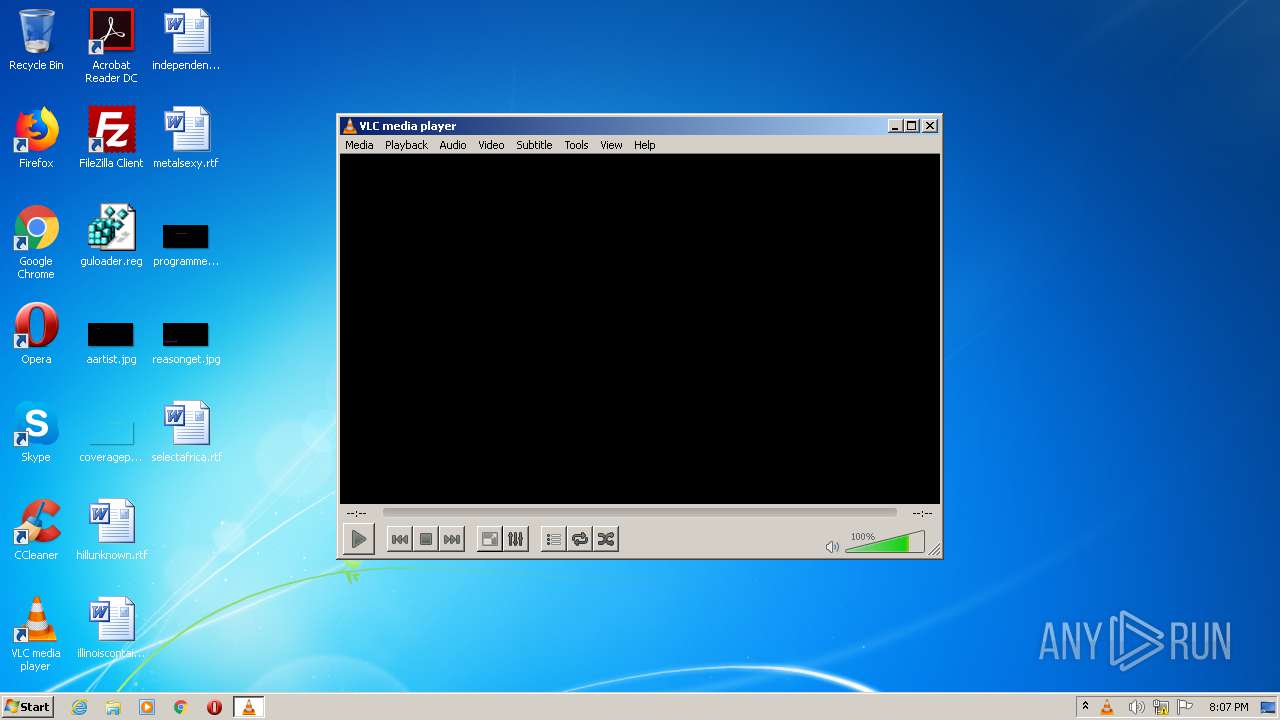
| 1904 | "C:\Program Files\VideoLAN\VLC\vlc.exe" --started-from-file "C:\Users\admin\AppData\Local\Temp\2f93b97f-3002-4549-a641-f02157896893.mp4.m4v" | C:\Program Files\VideoLAN\VLC\vlc.exe | explorer.exe | ||||||||||||
User: admin Company: VideoLAN Integrity Level: MEDIUM Description: VLC media player Exit code: 0 Version: 2.2.6 Modules
| |||||||||||||||
Total events
1 006
Read events
921
Write events
81
Delete events
4
Modification events
| (PID) Process: | (1904) vlc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: vlc.exe | |||
| (PID) Process: | (1784) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1784) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1784) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1784) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1784) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1500) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1784-13251154058155890 |
Value: 259 | |||
| (PID) Process: | (1784) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1784) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1784) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
Executable files
0
Suspicious files
169
Text files
262
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1904 | vlc.exe | C:\Users\admin\AppData\Local\Temp\VLCF38B.tmp | — | |
MD5:— | SHA256:— | |||
| 1904 | vlc.exe | C:\Users\admin\AppData\Local\Temp\VLCF467.tmp | — | |
MD5:— | SHA256:— | |||
| 1904 | vlc.exe | C:\Users\admin\AppData\Local\Temp\VLCF468.tmp | — | |
MD5:— | SHA256:— | |||
| 1904 | vlc.exe | C:\Users\admin\AppData\Local\Temp\VLCF469.tmp | — | |
MD5:— | SHA256:— | |||
| 1904 | vlc.exe | C:\Users\admin\AppData\Local\Temp\VLCF46A.tmp | — | |
MD5:— | SHA256:— | |||
| 1904 | vlc.exe | C:\Users\admin\AppData\Local\Temp\VLCF46B.tmp | — | |
MD5:— | SHA256:— | |||
| 1904 | vlc.exe | C:\Users\admin\AppData\Local\Temp\VLCF46C.tmp | — | |
MD5:— | SHA256:— | |||
| 1904 | vlc.exe | C:\Users\admin\AppData\Local\Temp\VLCF46D.tmp | — | |
MD5:— | SHA256:— | |||
| 1904 | vlc.exe | C:\Users\admin\AppData\Local\Temp\VLCF46E.tmp | — | |
MD5:— | SHA256:— | |||
| 1904 | vlc.exe | C:\Users\admin\AppData\Local\Temp\VLCF47E.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
103
DNS requests
59
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
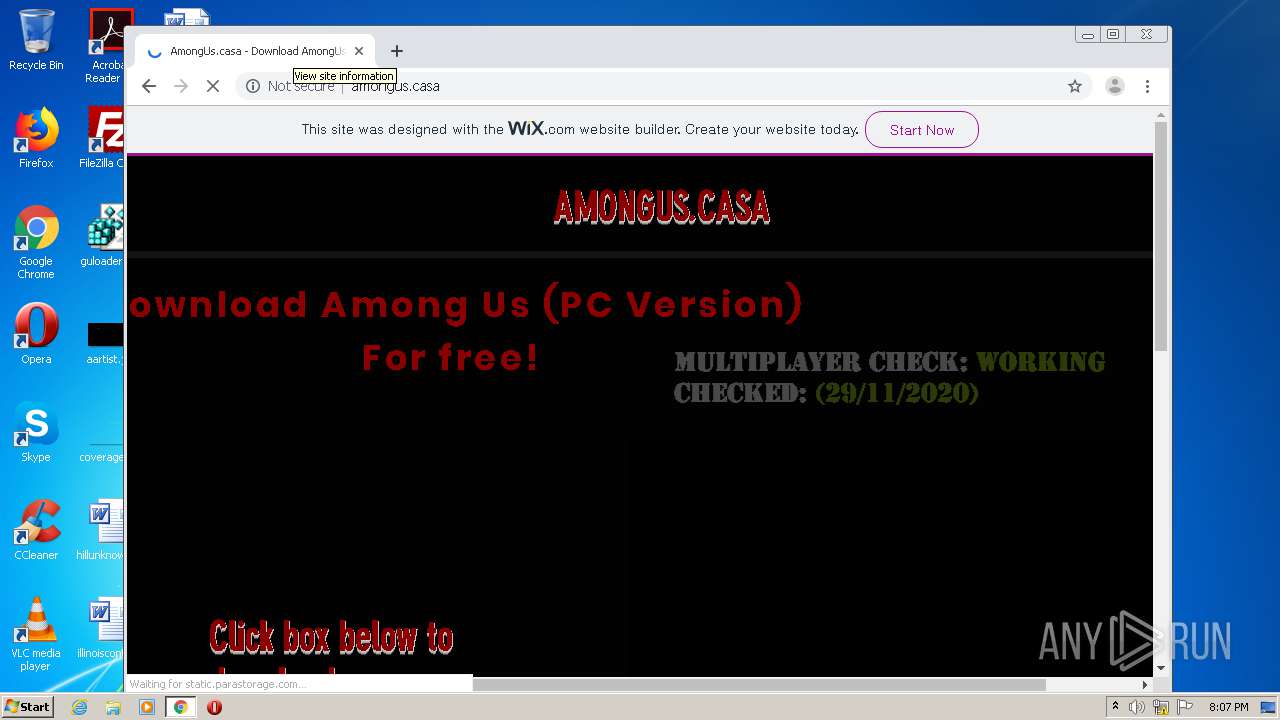
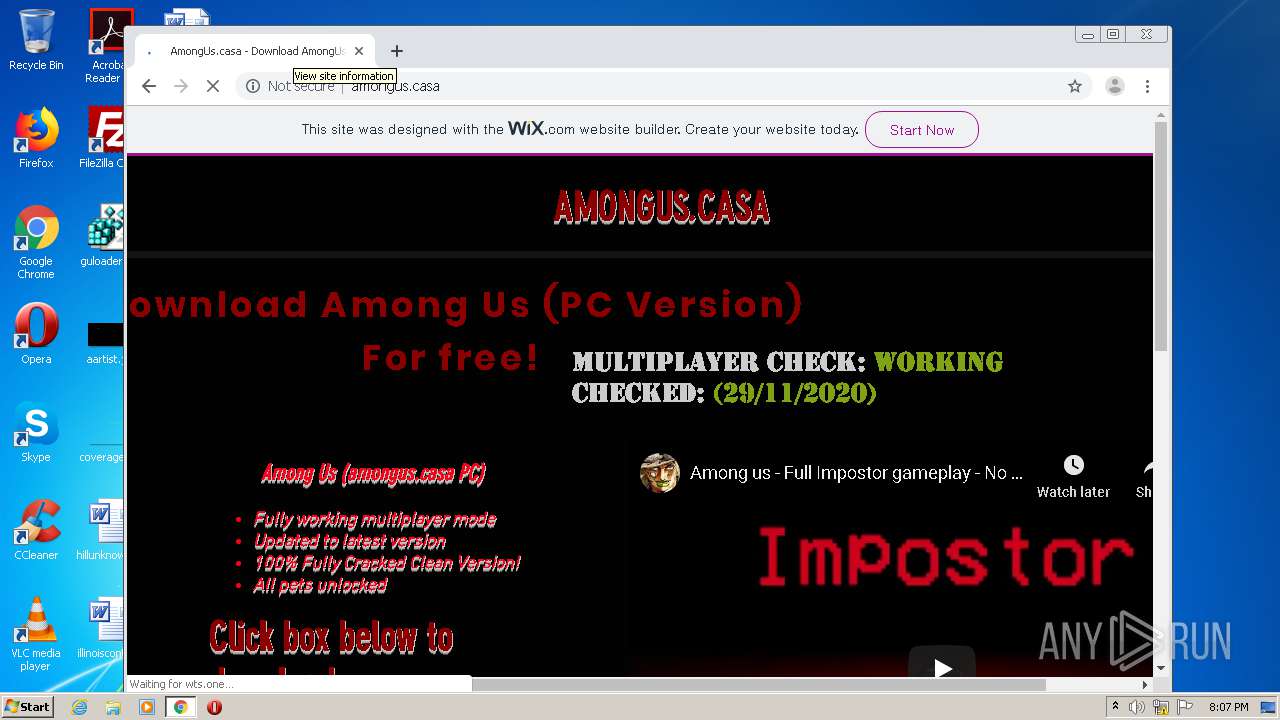
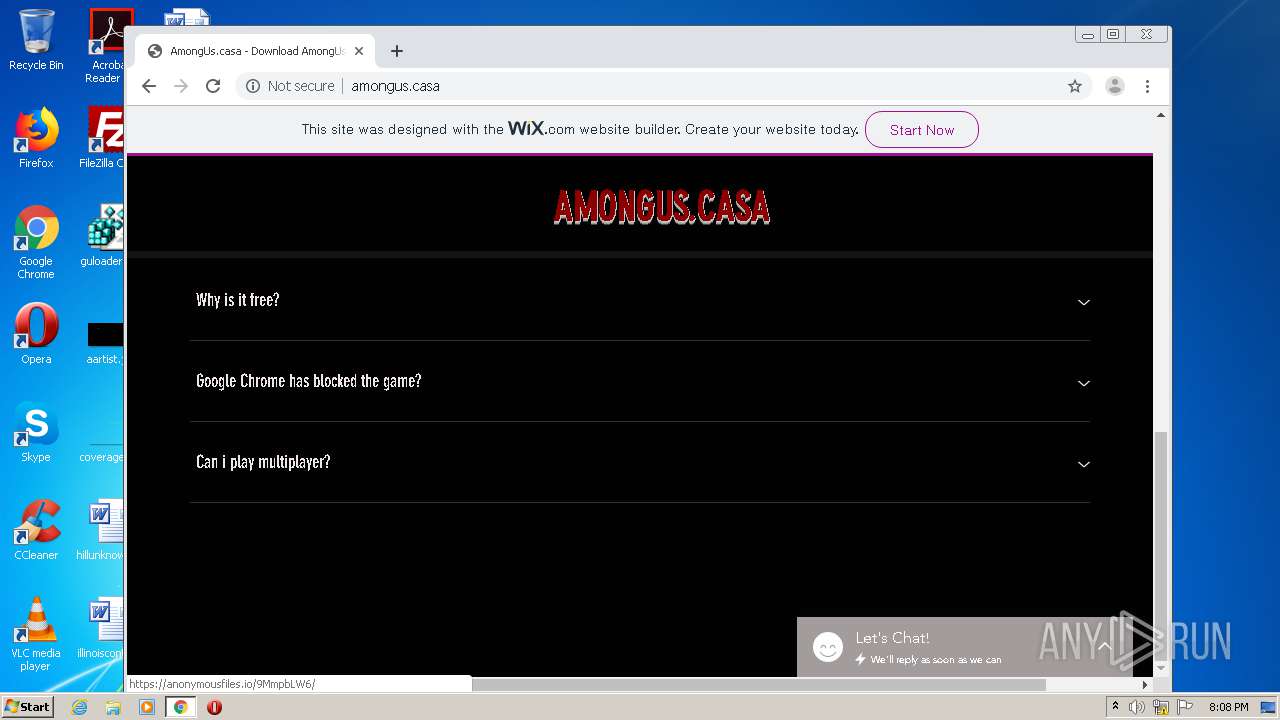
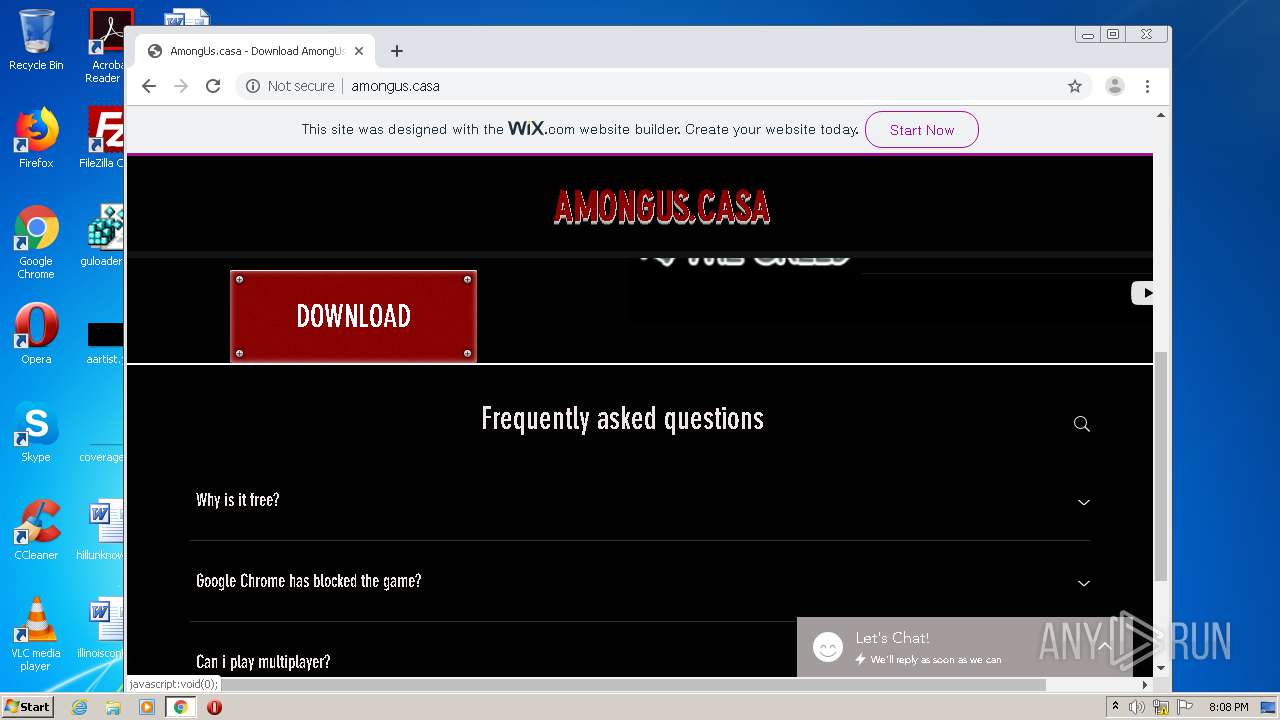
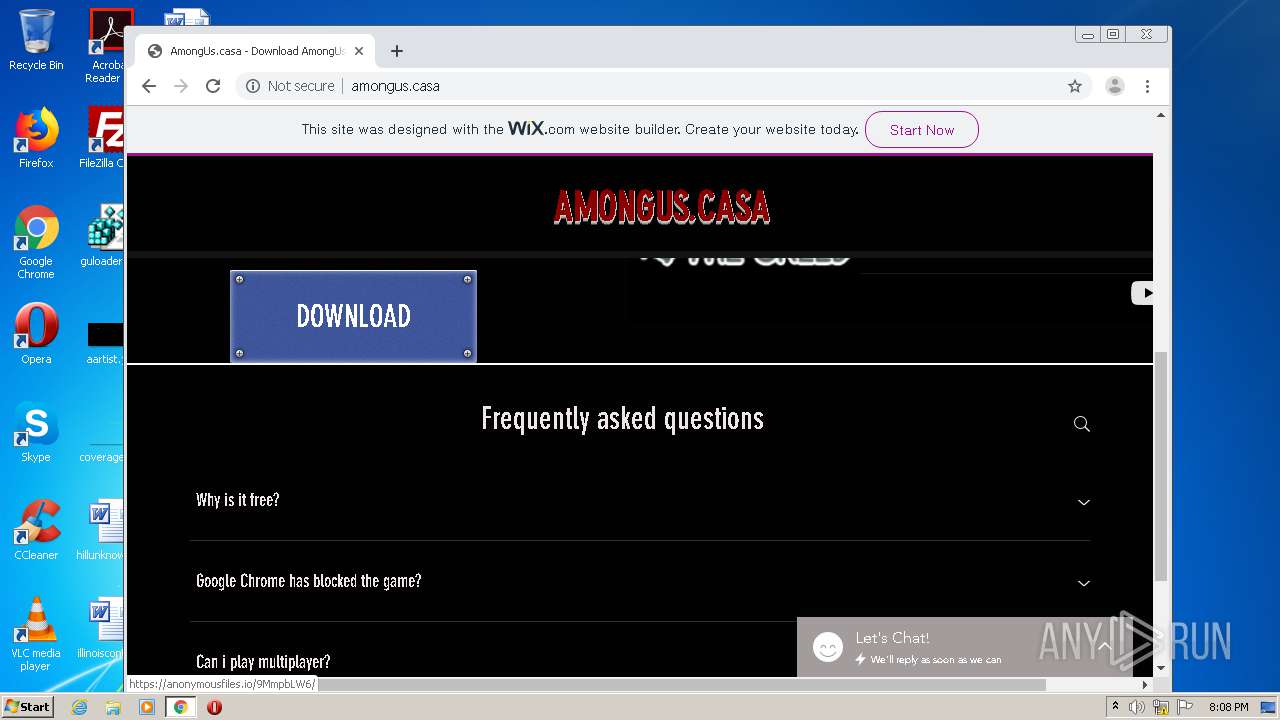
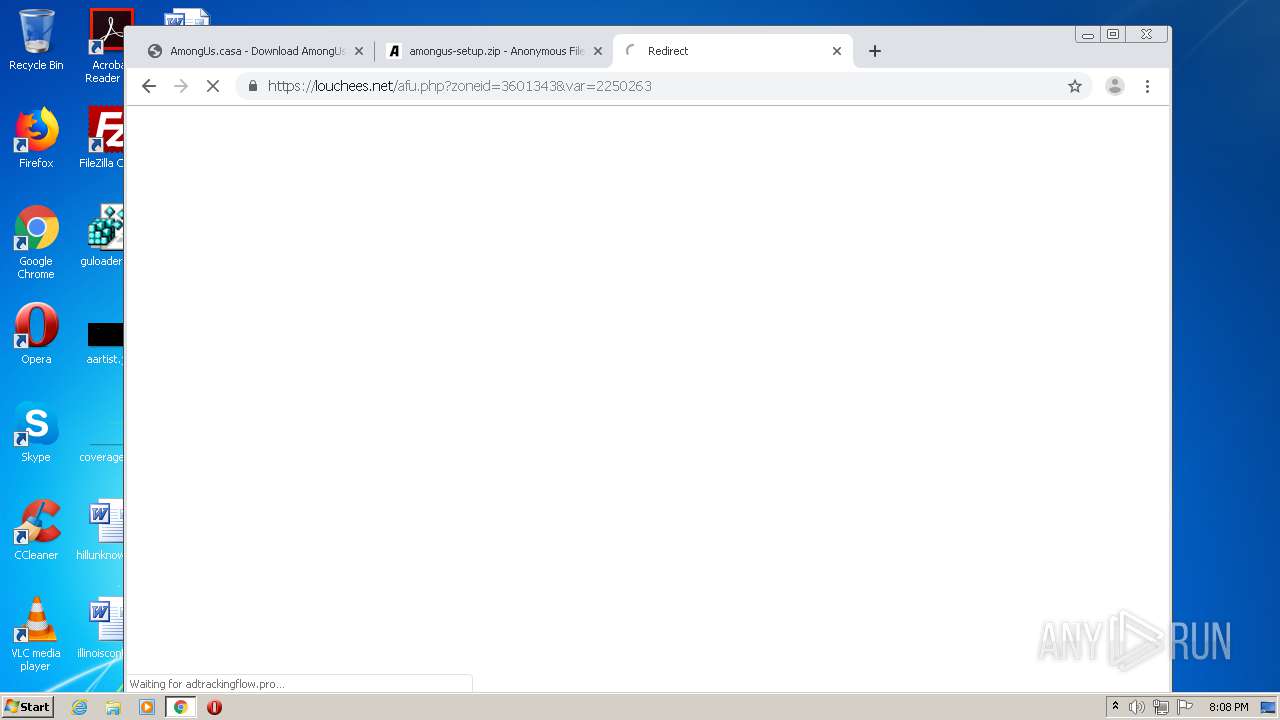
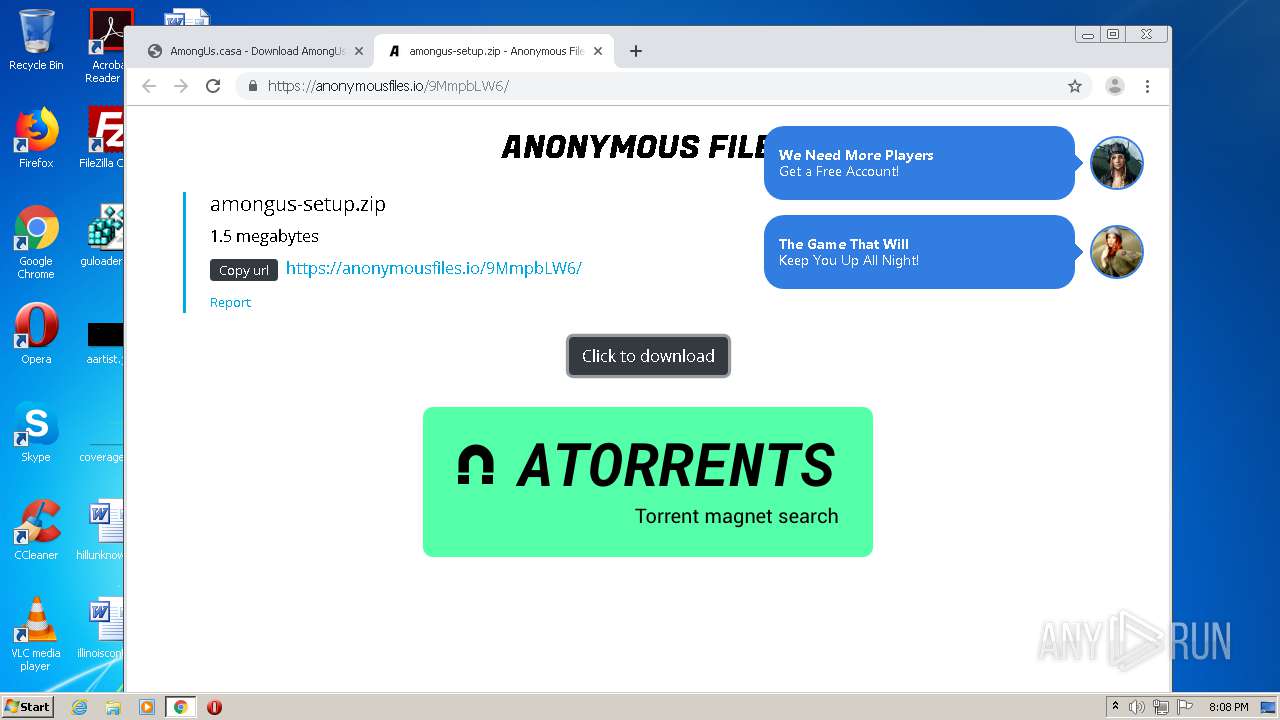
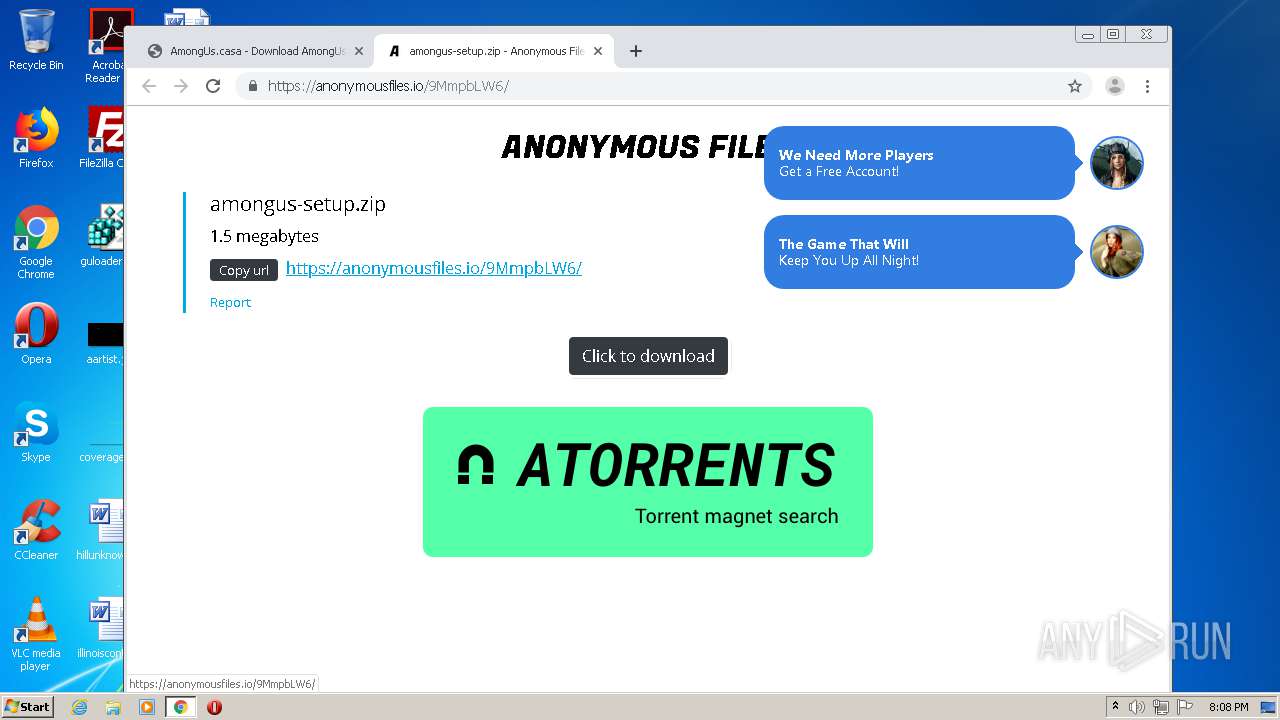
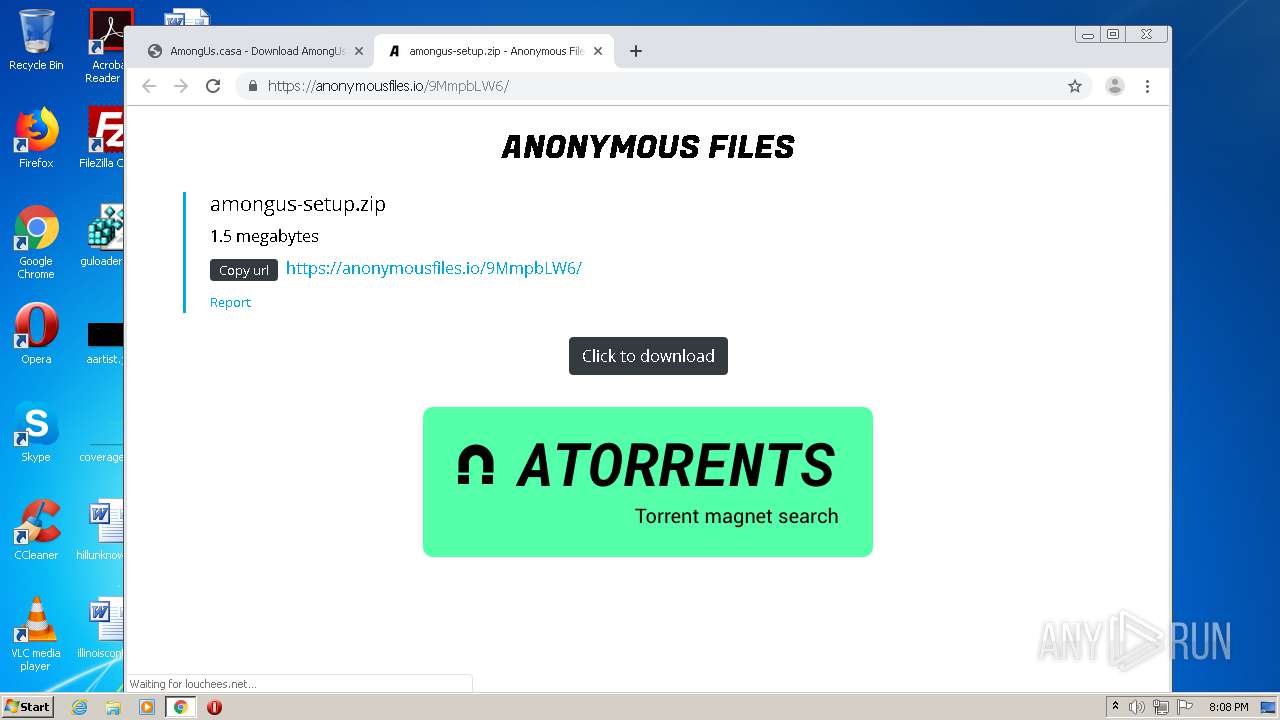
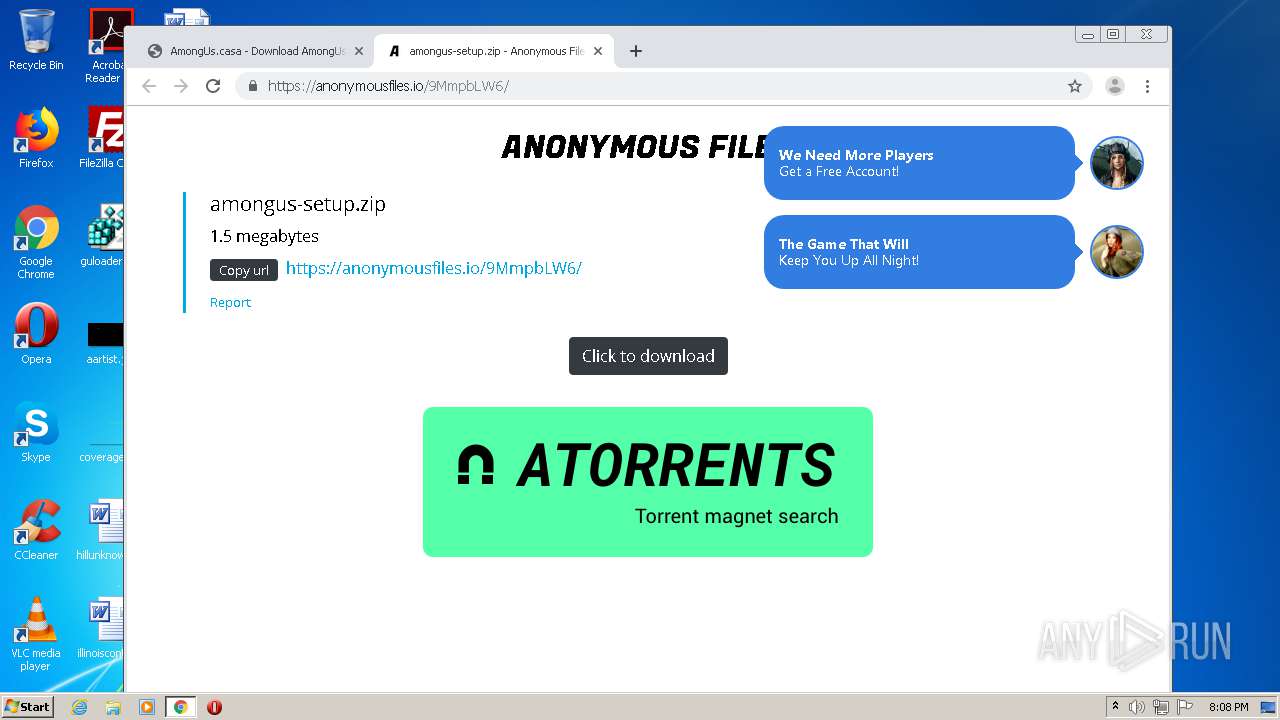
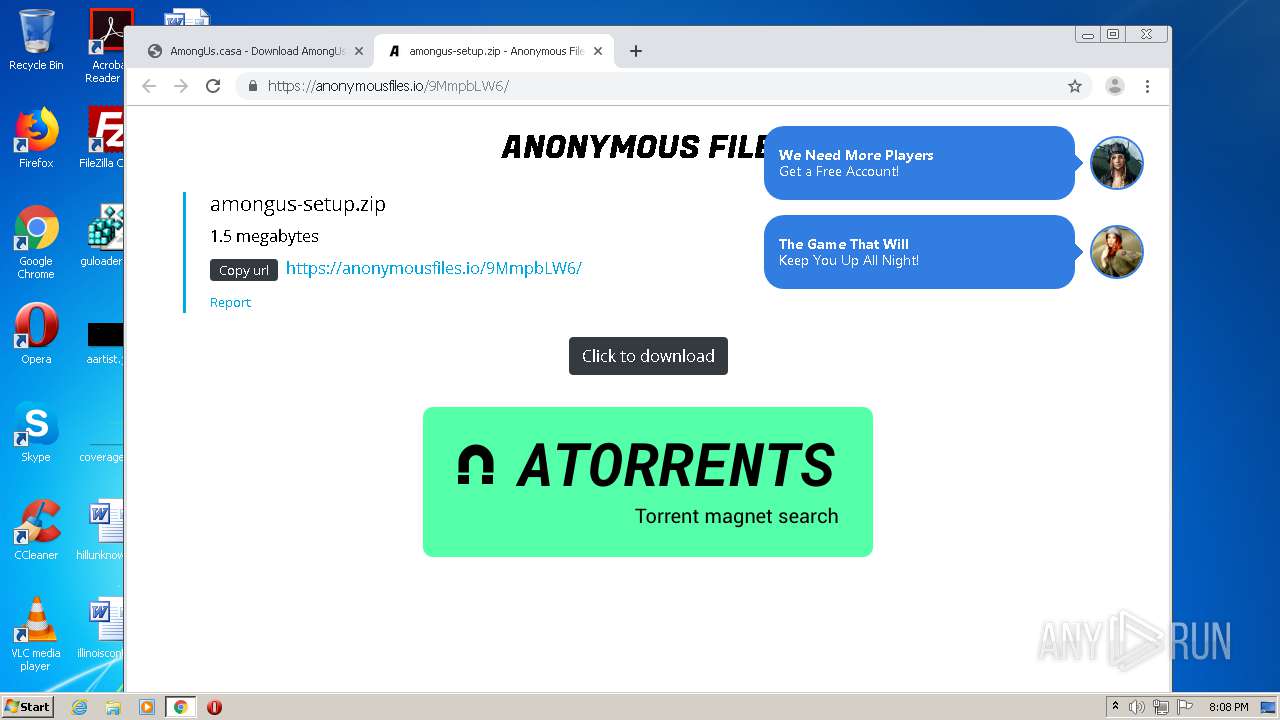
3316 | chrome.exe | GET | 200 | 192.64.119.227:80 | http://amongus.casa/favicon.ico | US | html | 981 b | suspicious |
3316 | chrome.exe | GET | 200 | 192.64.119.227:80 | http://amongus.casa/ | US | html | 957 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3316 | chrome.exe | 192.64.119.227:80 | amongus.casa | Namecheap, Inc. | US | suspicious |
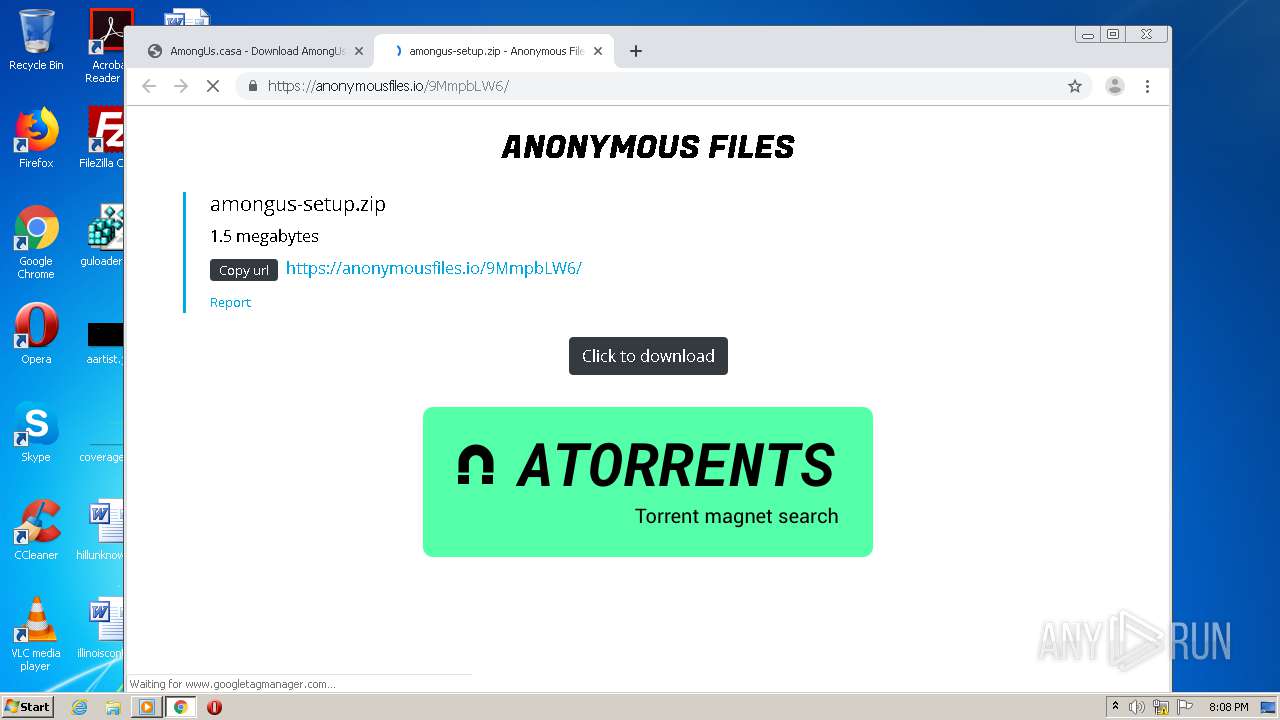
3316 | chrome.exe | 35.242.251.130:443 | cashhazard7.wixsite.com | — | US | malicious |
3316 | chrome.exe | 151.101.2.49:443 | static.parastorage.com | Fastly | US | malicious |
3316 | chrome.exe | 172.217.21.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3316 | chrome.exe | 216.58.212.163:443 | www.google.com.ua | Google Inc. | US | whitelisted |
3316 | chrome.exe | 172.217.18.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3316 | chrome.exe | 216.58.206.3:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3316 | chrome.exe | 172.217.22.14:443 | apis.google.com | Google Inc. | US | whitelisted |
3316 | chrome.exe | 216.58.207.78:443 | ogs.google.com.ua | Google Inc. | US | whitelisted |
3316 | chrome.exe | 172.217.18.3:443 | www.google.se | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com.ua |
| whitelisted |
www.google.com |
| malicious |
www.google.se |
| whitelisted |
Threats
Process | Message |
|---|---|
vlc.exe | core libvlc: one instance mode ENABLED
|
vlc.exe | core libvlc: Running vlc with the default interface. Use 'cvlc' to use vlc without interface.
|
vlc.exe | direct3d vout display error: Direct3D could not be initialized
|
vlc.exe | direct3d vout display error: Direct3D could not be initialized
|