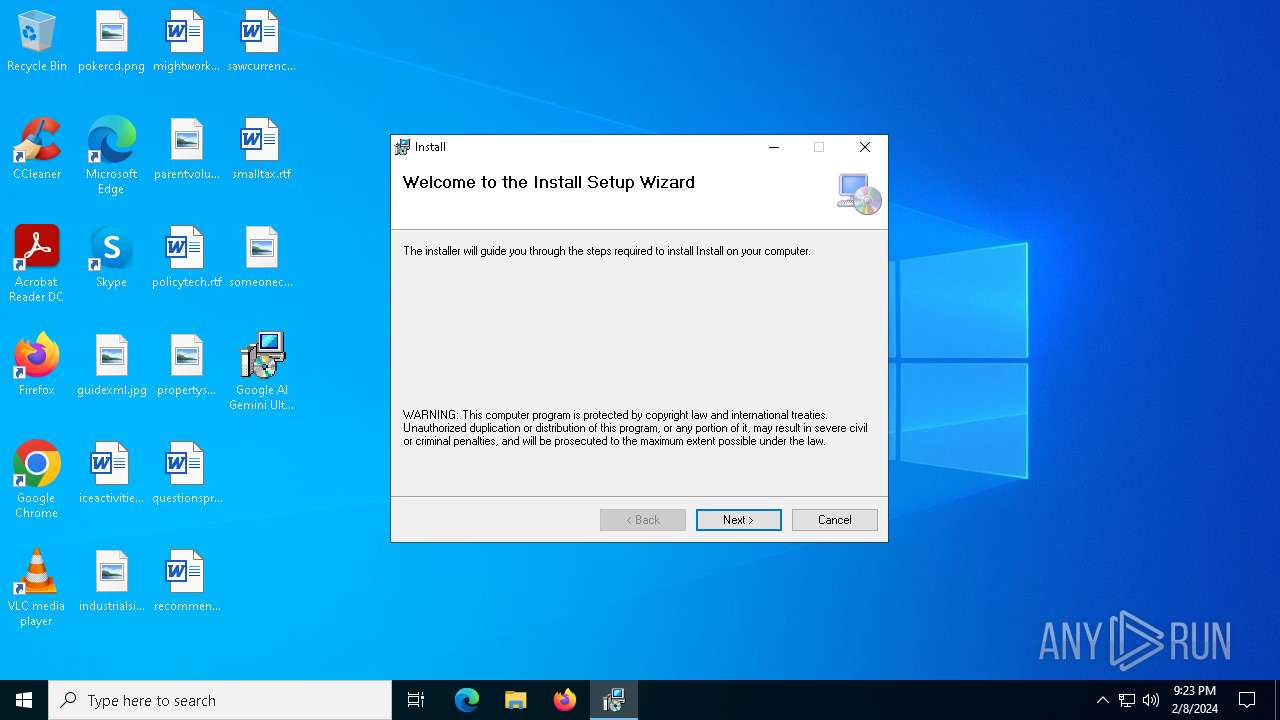
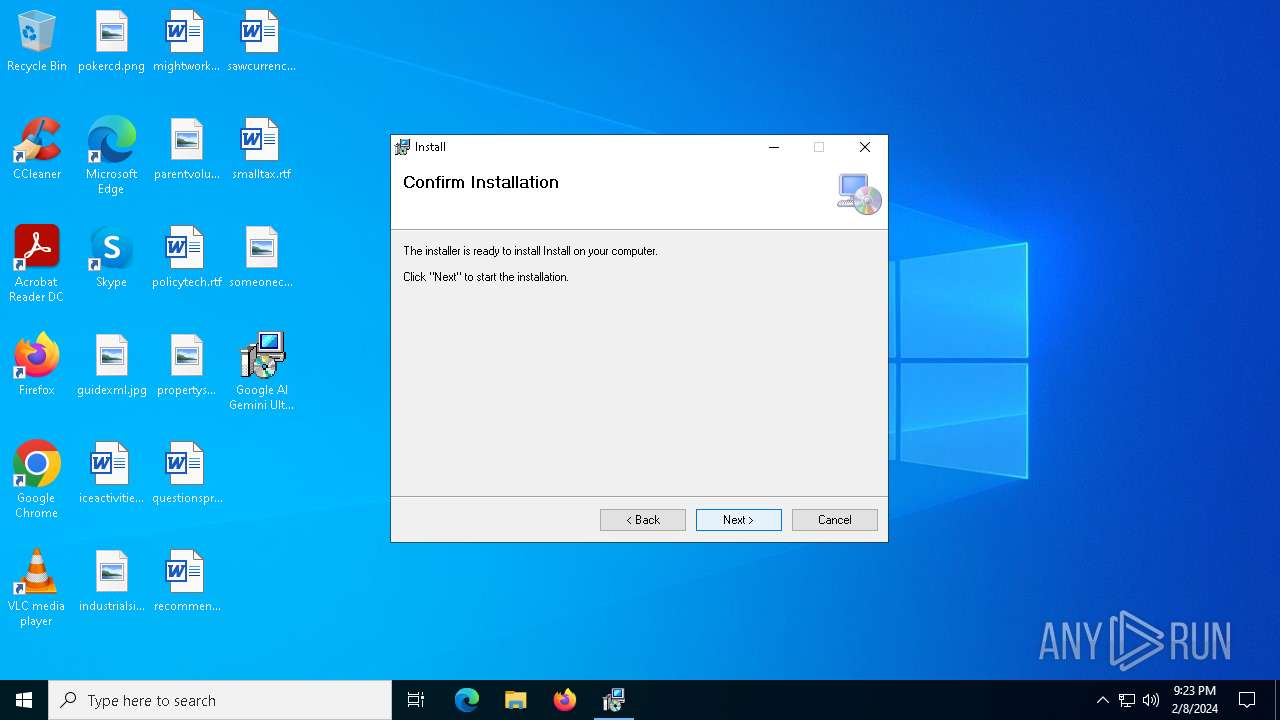
| File name: | Google AI Gemini Ultra For PC V1.0.1.msi |
| Full analysis: | https://app.any.run/tasks/edf4d2d8-e6f5-44e6-82c3-b3de6f21f83f |
| Verdict: | Malicious activity |
| Analysis date: | February 08, 2024, 21:23:33 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, MSI Installer, Create Time/Date: Mon Jun 21 08:00:00 1999, Name of Creating Application: Windows Installer, Security: 1, Code page: 1252, Template: Intel;1033, Number of Pages: 200, Revision Number: {C6C2D440-EA93-4E35-B8C6-83DD50C1613C}, Title: Install, Author: Install, Comments: Bringing the benefits of AI to everyone, Number of Words: 2, Last Saved Time/Date: Mon Jan 22 11:59:18 2024, Last Printed: Mon Jan 22 11:59:18 2024 |
| MD5: | BF17D7F8DAC7DF58B37582CEC39E609D |
| SHA1: | 0C55B3C75E5759EFC6DB20B6DB4FAD790CBCD4E7 |
| SHA256: | BB7C3B78F2784A7AC3C090331326279476C748087188AEB69F431BBD70AC6407 |
| SSDEEP: | 24576:C1ipiRvE4wbF60m3oOEZ/vTk1oQ53eYc:C1ipiRM4wbF60m3oOEZ/vTk1oQ53lc |
MALICIOUS
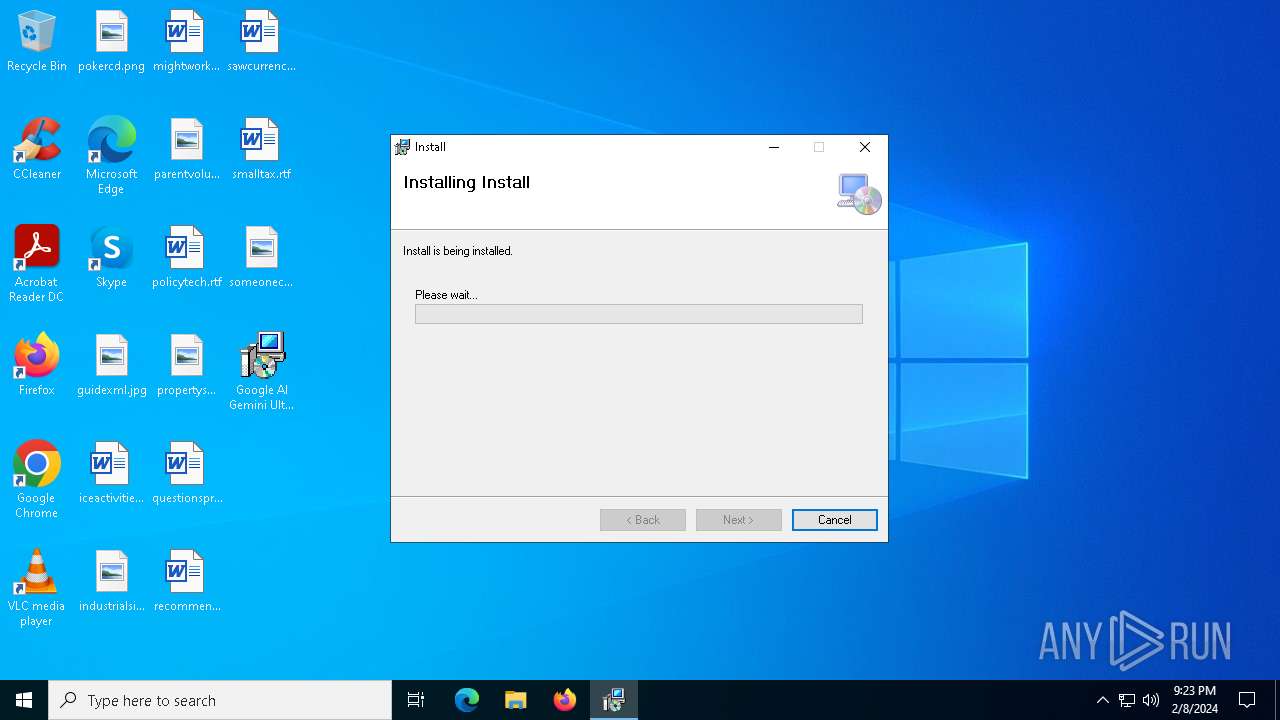
Drops the executable file immediately after the start
- msiexec.exe (PID: 5312)
Bypass execution policy to execute commands
- powershell.exe (PID: 4604)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 6092)
SUSPICIOUS
Process drops legitimate windows executable
- msiexec.exe (PID: 5996)
- msiexec.exe (PID: 5312)
Executes as Windows Service
- VSSVC.exe (PID: 3736)
Executing commands from ".cmd" file
- msiexec.exe (PID: 5312)
Starts CMD.EXE for commands execution
- msiexec.exe (PID: 5312)
The process executes Powershell scripts
- cmd.exe (PID: 6092)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 6092)
INFO
Checks supported languages
- msiexec.exe (PID: 5312)
- msiexec.exe (PID: 4672)
- msiexec.exe (PID: 6168)
- identity_helper.exe (PID: 8168)
Reads the computer name
- msiexec.exe (PID: 5312)
- msiexec.exe (PID: 4672)
- msiexec.exe (PID: 6168)
- identity_helper.exe (PID: 8168)
Create files in a temporary directory
- msiexec.exe (PID: 4672)
- msiexec.exe (PID: 6168)
Executable content was dropped or overwritten
- msiexec.exe (PID: 5996)
- msiexec.exe (PID: 5312)
- msedge.exe (PID: 7876)
Drops the executable file immediately after the start
- msiexec.exe (PID: 5996)
- chrome.exe (PID: 5716)
- msedge.exe (PID: 2628)
- msedge.exe (PID: 7876)
Creates files or folders in the user directory
- msiexec.exe (PID: 5312)
The process uses the downloaded file
- chrome.exe (PID: 7784)
- chrome.exe (PID: 7912)
- chrome.exe (PID: 7212)
- chrome.exe (PID: 784)
Application launched itself
- chrome.exe (PID: 5716)
- msedge.exe (PID: 640)
Reads the software policy settings
- slui.exe (PID: 7608)
- slui.exe (PID: 7956)
Checks proxy server information
- slui.exe (PID: 7608)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (90.2) |
|---|---|---|
| .msp | | | Windows Installer Patch (8.4) |
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| CreateDate: | 1999:06:21 07:00:00 |
|---|---|
| Software: | Windows Installer |
| Security: | Password protected |
| CodePage: | Windows Latin 1 (Western European) |
| Template: | Intel;1033 |
| Pages: | 200 |
| RevisionNumber: | {C6C2D440-EA93-4E35-B8C6-83DD50C1613C} |
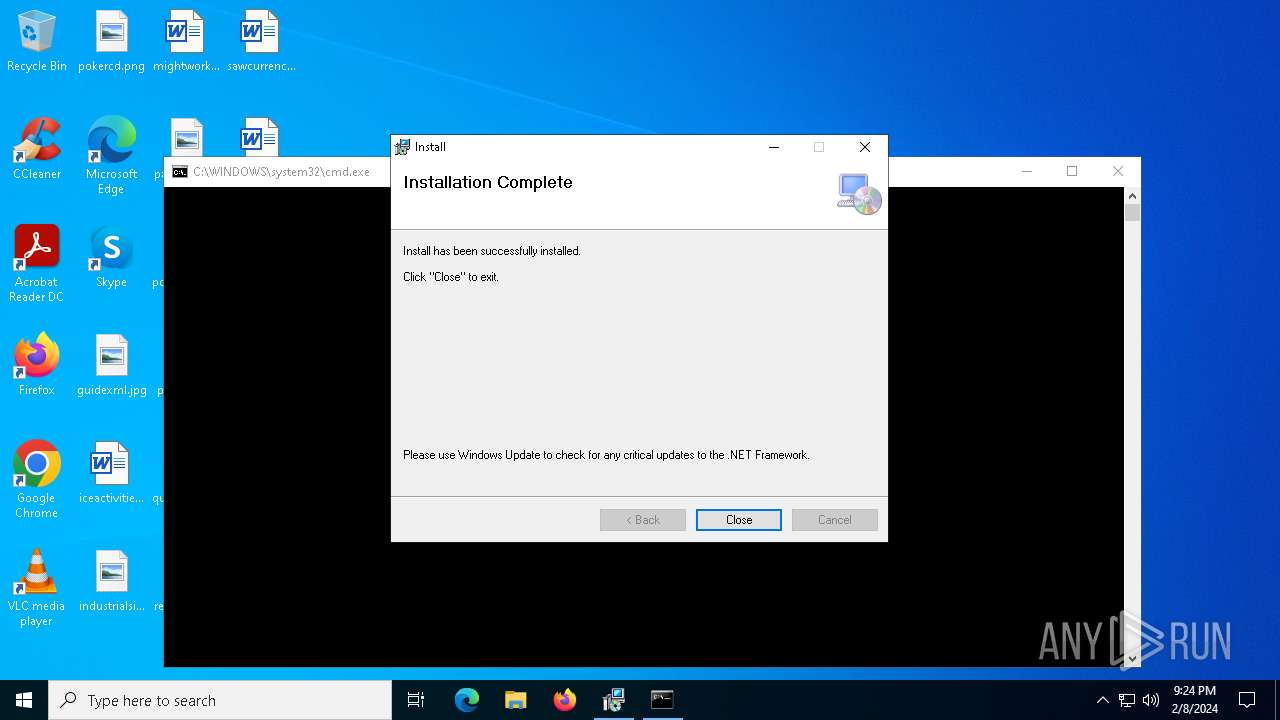
| Title: | Install |
| Subject: | - |
| Author: | Install |
| Keywords: | - |
| Comments: | Bringing the benefits of AI to everyone |
| Words: | 2 |
| ModifyDate: | 2024:01:22 11:59:18 |
| LastPrinted: | 2024:01:22 11:59:18 |
Total processes
226
Monitored processes
83
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
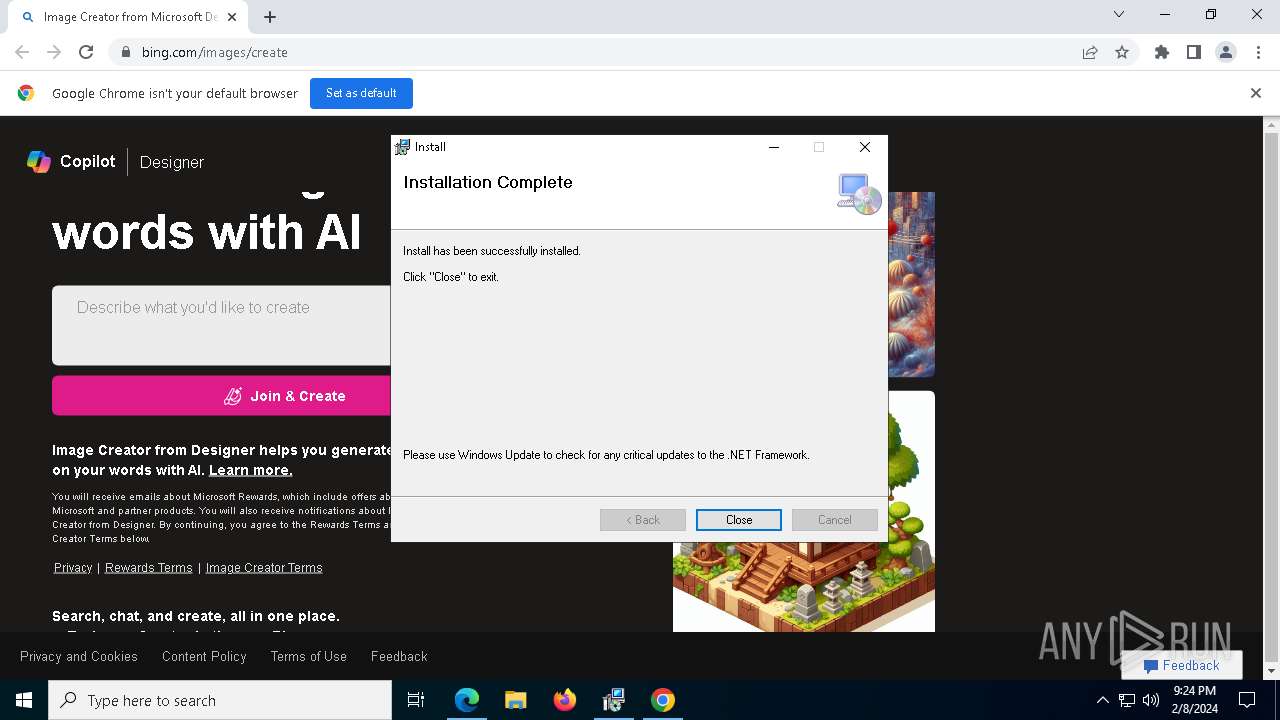
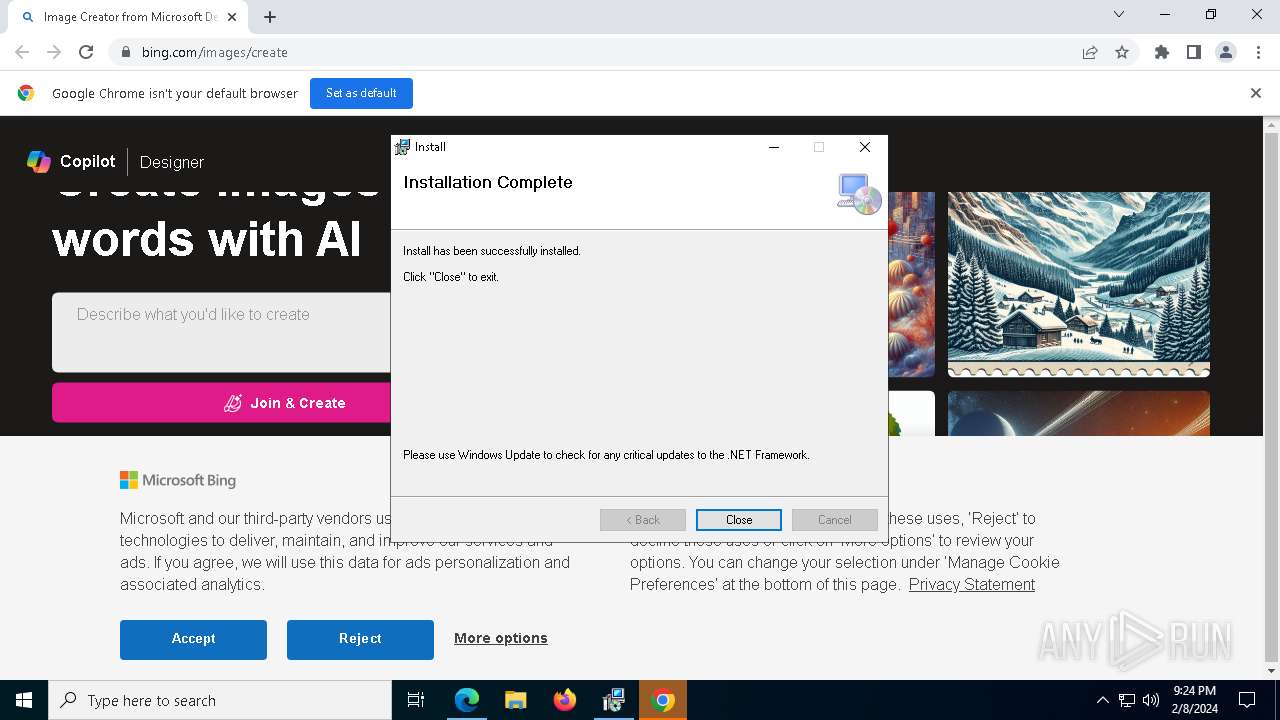
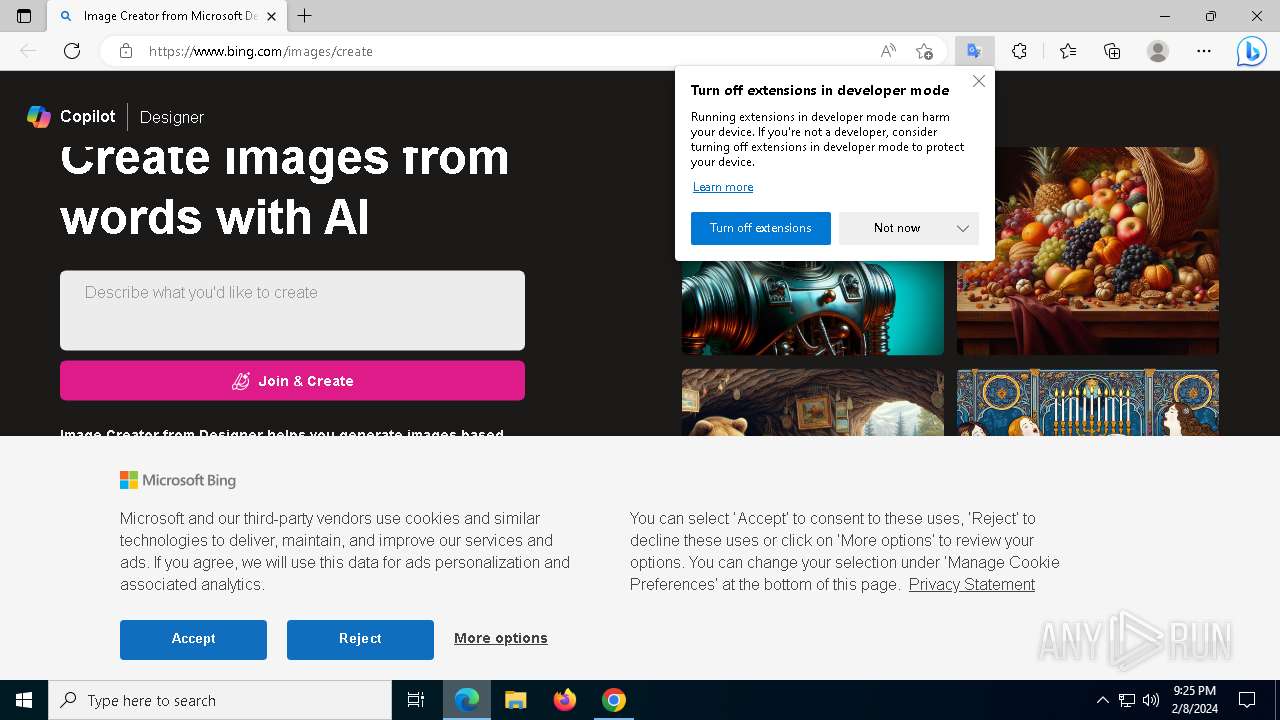
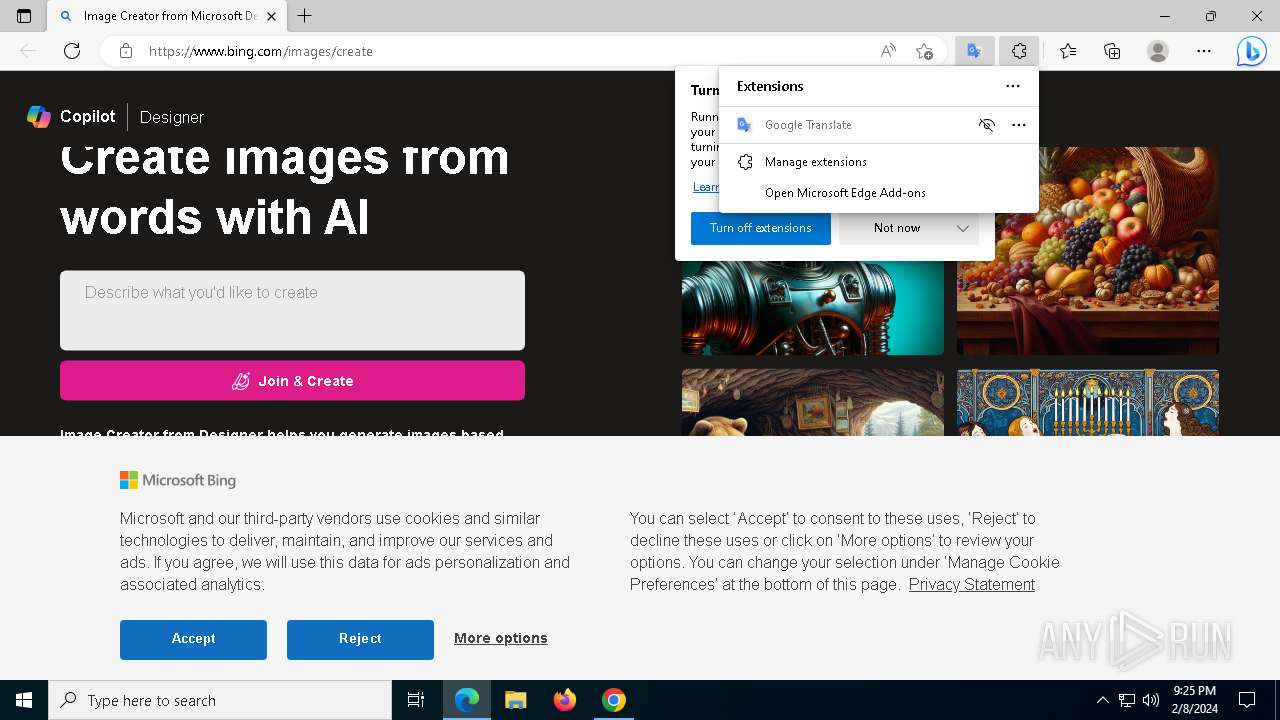
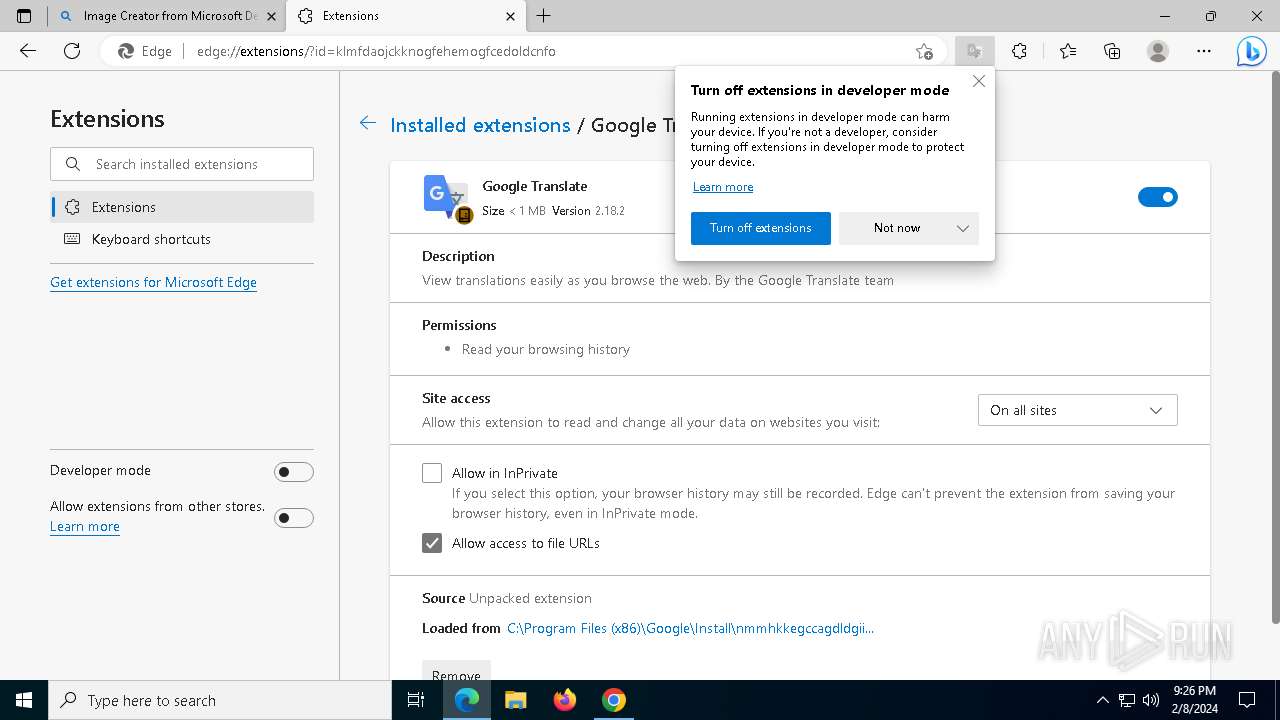
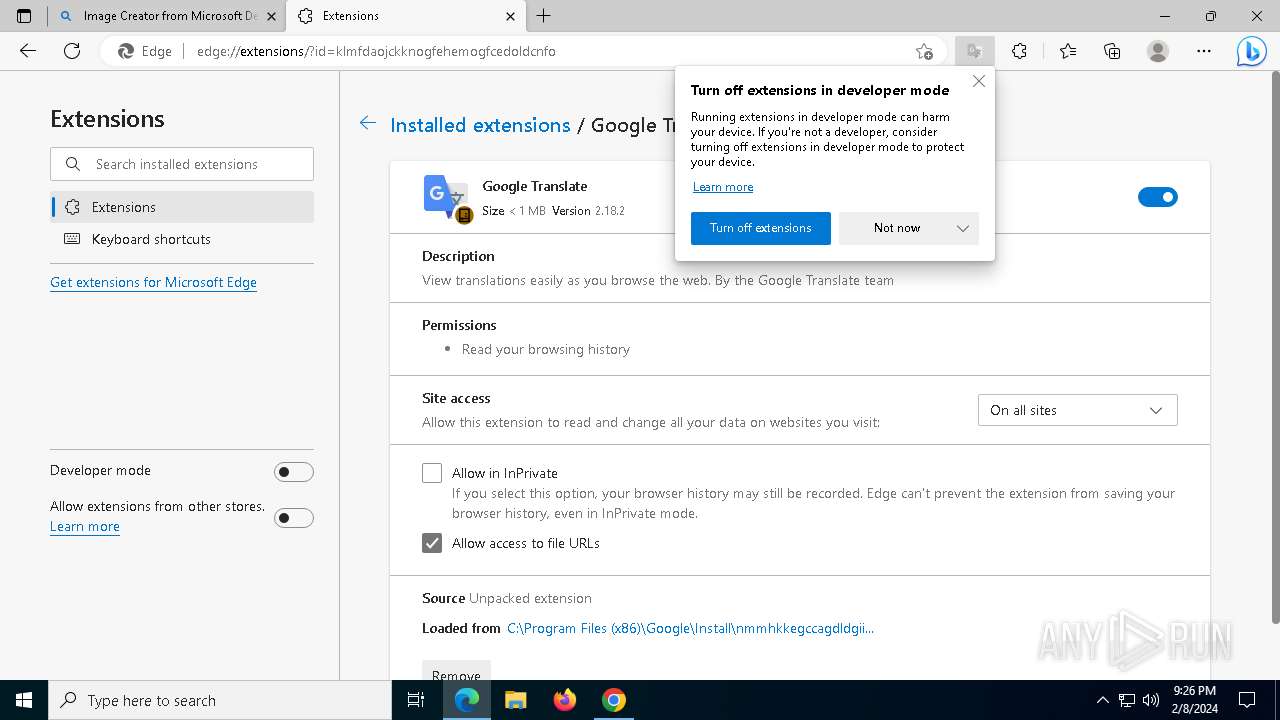
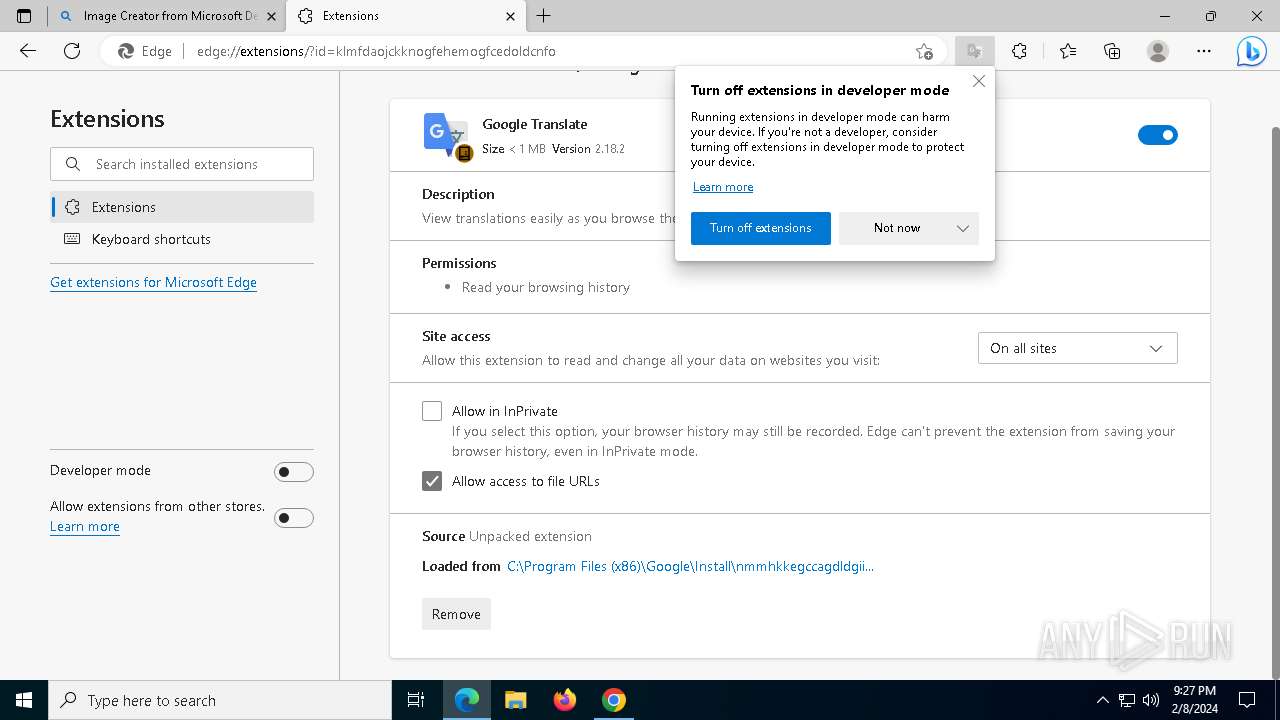
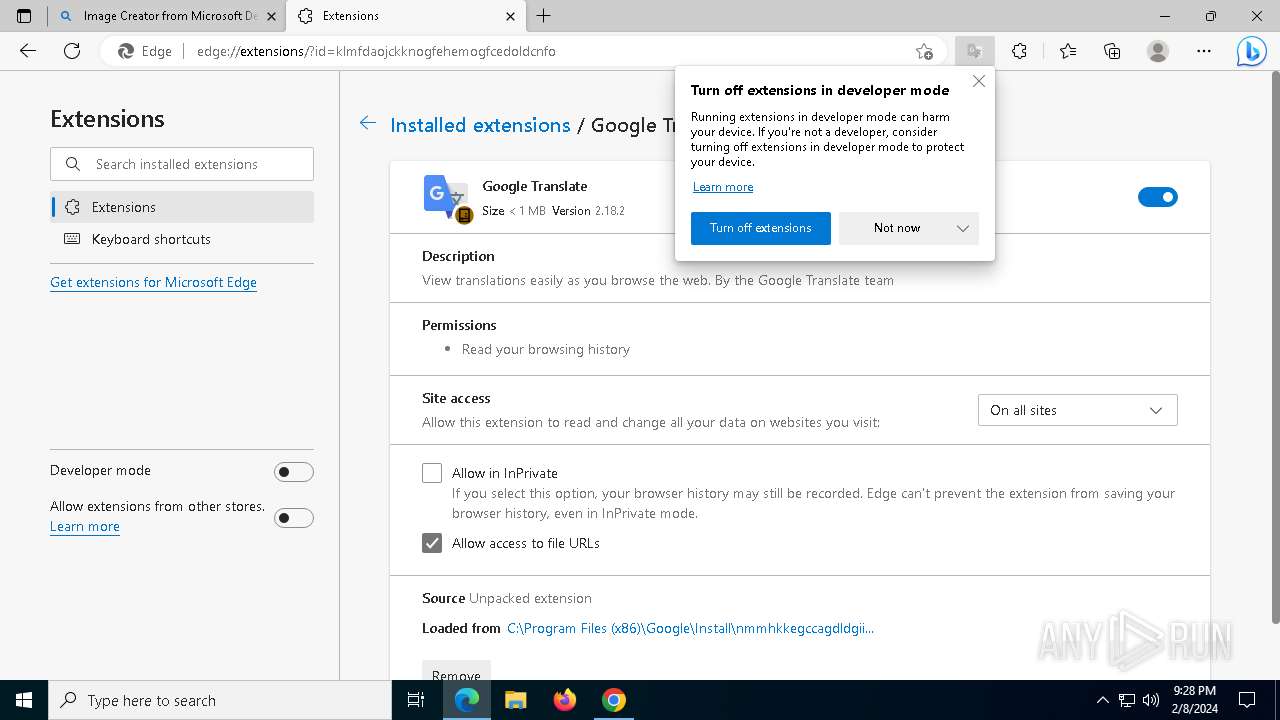
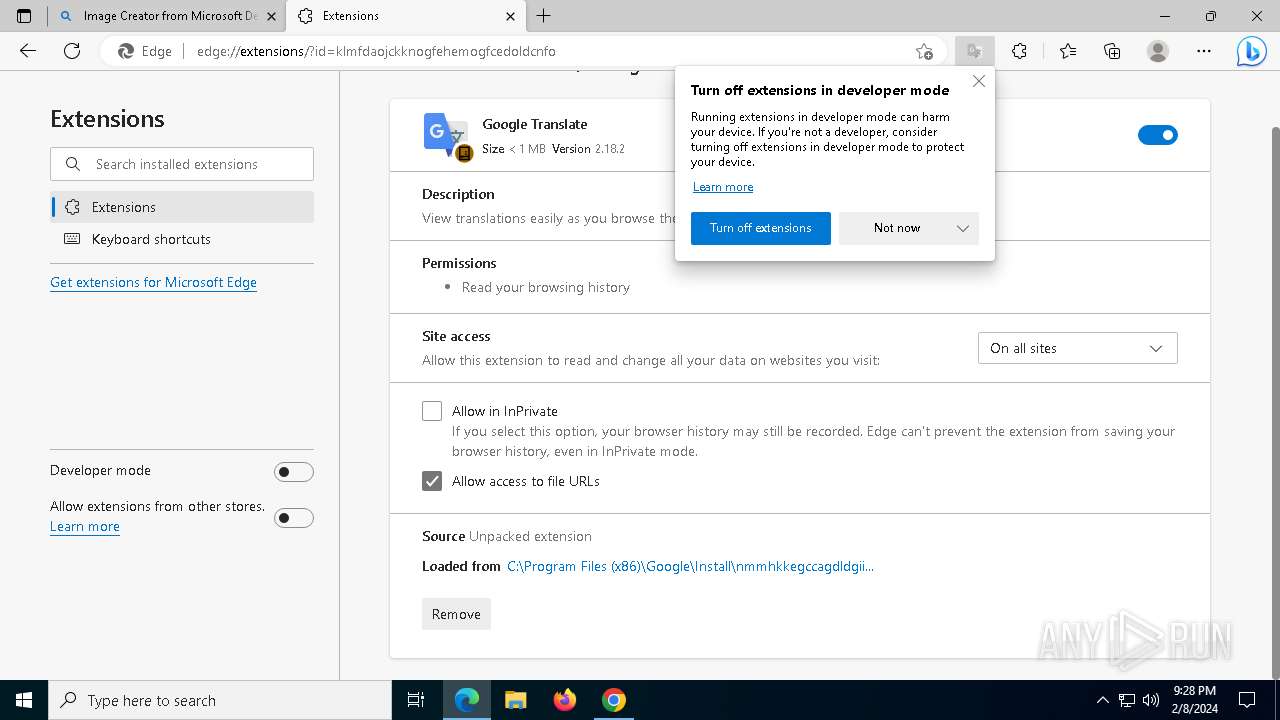
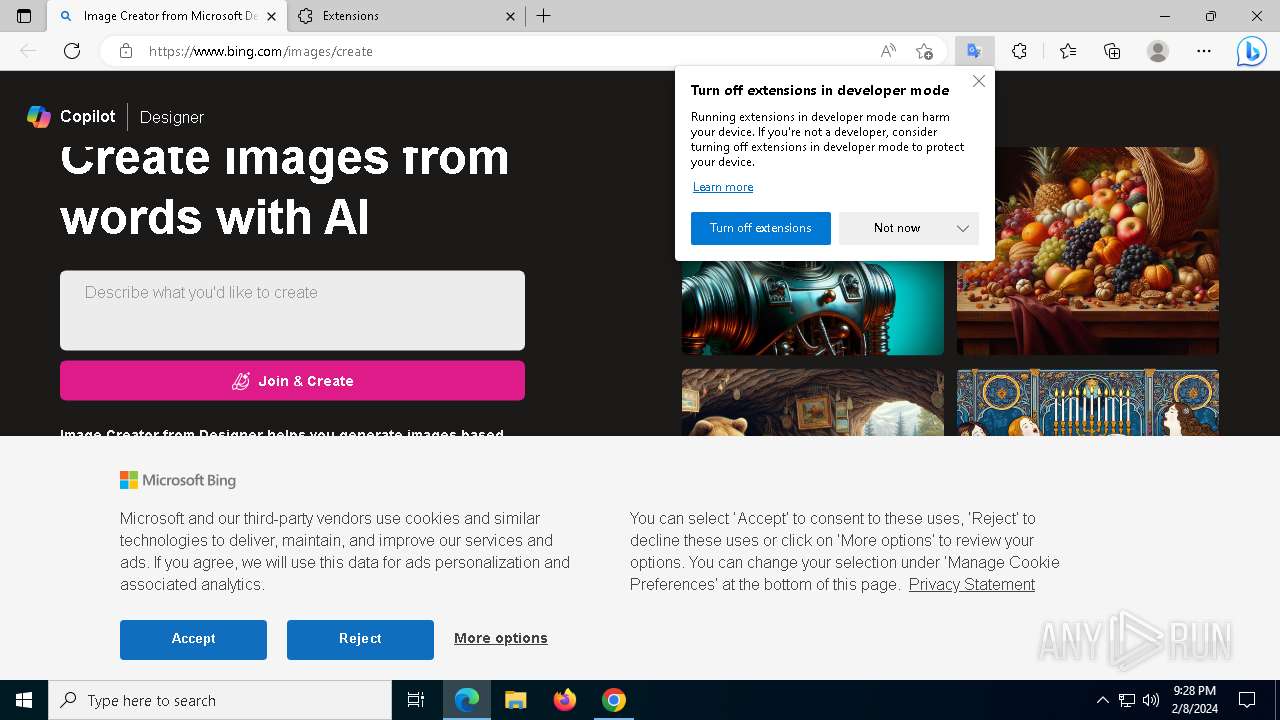
| 640 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --load-extension="C:\Program Files (x86)\Google\Install\nmmhkkegccagdldgiimedpic" --new-window https://www.bing.com/images/create | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 111.0.1661.62 Modules
| |||||||||||||||
| 784 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=2364 --field-trial-handle=1932,i,2507089187864958496,10413697378886867012,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 112.0.5615.50 Modules
| |||||||||||||||
| 892 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=24 --mojo-platform-channel-handle=6984 --field-trial-handle=2024,i,18146265825062396601,13950626187364792627,131072 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 111.0.1661.62 Modules
| |||||||||||||||
| 1540 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=1472 --field-trial-handle=1932,i,2507089187864958496,10413697378886867012,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 112.0.5615.50 Modules
| |||||||||||||||
| 1684 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=17 --mojo-platform-channel-handle=6452 --field-trial-handle=2024,i,18146265825062396601,13950626187364792627,131072 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 111.0.1661.62 Modules
| |||||||||||||||
| 2224 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --mojo-platform-channel-handle=6876 --field-trial-handle=2024,i,18146265825062396601,13950626187364792627,131072 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 111.0.1661.62 Modules
| |||||||||||||||
| 2580 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=5720 --field-trial-handle=2024,i,18146265825062396601,13950626187364792627,131072 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 111.0.1661.62 Modules
| |||||||||||||||
| 2628 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=6872 --field-trial-handle=2024,i,18146265825062396601,13950626187364792627,131072 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 111.0.1661.62 Modules
| |||||||||||||||
| 2724 | C:\Users\admin\AppData\Local\Microsoft\OneDrive\19.043.0304.0013\FileCoAuth.exe -Embedding | C:\Users\admin\AppData\Local\Microsoft\OneDrive\19.043.0304.0013\FileCoAuth.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft OneDriveFile Co-Authoring Executable Exit code: 0 Version: 19.043.0304.0013 Modules
| |||||||||||||||
| 3736 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
29 356
Read events
29 183
Write events
145
Delete events
28
Modification events
| (PID) Process: | (5312) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4800000000000000F8A26F1E28C7D901181500003C120000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5312) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 4800000000000000616E762828C7D9010812000010140000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5312) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 4800000000000000616E762828C7D9010812000010140000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5312) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 4800000000000000616E762828C7D9010812000010140000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5312) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 4800000000000000616E762828C7D9010812000010140000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5312) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 48000000000000009984A61E28C7D901181500003C120000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5312) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 3 | |||
| (PID) Process: | (5312) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4800000000000000F6C6B41E28C7D901181500003C120000D30700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3736) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{9dea862c-5cdd-4e70-acc1-f32b344d4795}\Elements\11000001 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (3736) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Description |
| Operation: | write | Name: | FirmwareModified |
Value: 1 | |||
Executable files
17
Suspicious files
587
Text files
215
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5312 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 5996 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSIC25C.tmp | executable | |
MD5:B77A2A2768B9CC78A71BBFFB9812B978 | SHA256:F74C97B1A53541B059D3BFAFE41A79005CE5065F8210D7DE9F1B600DC4E28AA0 | |||
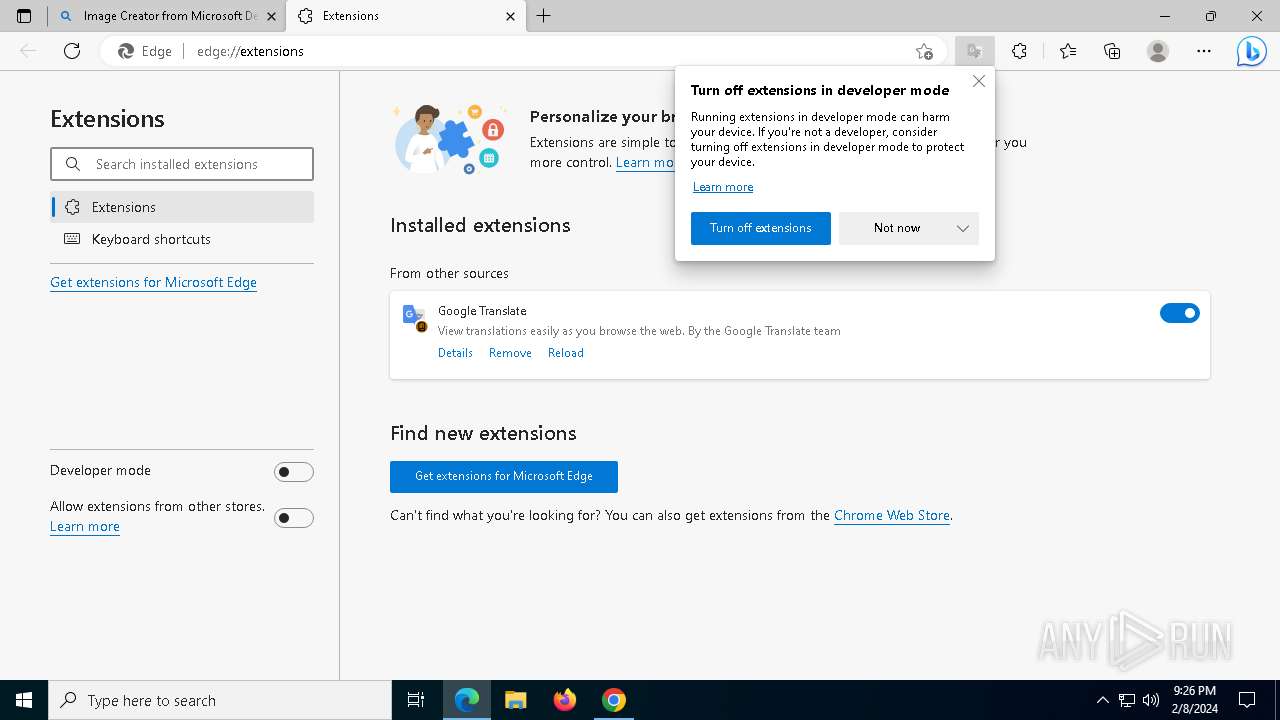
| 5312 | msiexec.exe | C:\Program Files (x86)\Google\Install\System.Deployment.dll | executable | |
MD5:A3866C0523804E20005AB9CCDC1DC8B8 | SHA256:D1F155CBC36C0032382A39DEDAAB9D3CEB681ECE6DCFA988E34A3116B7CC5549 | |||
| 6168 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\CFG12FD.tmp | xml | |
MD5:68675E0D405C8C76102802FA624EB895 | SHA256:B839CDD1C3F55651CD4D0E54A679BCE5AC60ED7618A7B74BFC8EF8CA311E53ED | |||
| 5312 | msiexec.exe | C:\WINDOWS\TEMP\~DFA753CC9ADD3E74FD.TMP | binary | |
MD5:BF619EAC0CDF3F68D496EA9344137E8B | SHA256:076A27C79E5ACE2A3D47F9DD2E83E4FF6EA8872B3C2218F66C92B89B55F36560 | |||
| 5312 | msiexec.exe | C:\WINDOWS\Installer\MSI137C.tmp | binary | |
MD5:C02231E1287C387F0D2E9C88543A7E4D | SHA256:8A2F833B3A916664F0459C6DB0F4AB0EFF5770BBD2DDE09052DF4A3BA20CC61F | |||
| 5312 | msiexec.exe | C:\Program Files (x86)\Google\Install\nmmhkkegccagdldgiimedpic\favicon.png | image | |
MD5:8BE1FACB79791A064862A61399B6DFEA | SHA256:89FF11A2237F9EC798ED4493738B14BE76F11F282C5AB755847779FE241EF857 | |||
| 5312 | msiexec.exe | C:\WINDOWS\Installer\inprogressinstallinfo.ipi | binary | |
MD5:44720ED5CF4B6D736347CF229E13DBFE | SHA256:47326284F7E7AF123460C5A496737420EBA1A8D8E2EBB0B6126ACCDD81D326C3 | |||
| 5312 | msiexec.exe | C:\Program Files (x86)\Google\Install\New Folder #%d2\account_manager (22).xls | html | |
MD5:6C5641DC874A47886100A16B2CCC91D9 | SHA256:CA63E6F0579499AC87F9AC73D0EF0403022D5474A250D1BD2650288BB0C39BB9 | |||
| 5312 | msiexec.exe | C:\Program Files (x86)\Google\Install\Microsoft.VisualC.Dll | executable | |
MD5:8DF8C5146490DC4E469DDD31CED8A705 | SHA256:14F2E8D64BDB5B4FAD83B9D550FE1A39539CAEC3C66B8A6AB5A7995BBDA1A296 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
157
TCP/UDP connections
109
DNS requests
124
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1612 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | binary | 814 b | unknown |
1612 | svchost.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | binary | 1.01 Kb | unknown |
1092 | svchost.exe | POST | 302 | 23.35.238.131:80 | http://go.microsoft.com/fwlink/?LinkID=252669&clcid=0x409 | unknown | — | — | unknown |
6164 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | binary | 471 b | unknown |
1092 | svchost.exe | POST | 502 | 20.231.121.79:80 | http://dmd.metaservices.microsoft.com/metadata.svc | unknown | html | 183 b | unknown |
1092 | svchost.exe | POST | 302 | 23.35.238.131:80 | http://go.microsoft.com/fwlink/?LinkID=252669&clcid=0x409 | unknown | — | — | unknown |
1092 | svchost.exe | POST | 502 | 20.231.121.79:80 | http://dmd.metaservices.microsoft.com/metadata.svc | unknown | html | 183 b | unknown |
1092 | svchost.exe | POST | 302 | 23.35.238.131:80 | http://go.microsoft.com/fwlink/?LinkID=252669&clcid=0x409 | unknown | — | — | unknown |
1092 | svchost.exe | POST | 502 | 20.231.121.79:80 | http://dmd.metaservices.microsoft.com/metadata.svc | unknown | html | 183 b | unknown |
1092 | svchost.exe | POST | 502 | 20.231.121.79:80 | http://dmd.metaservices.microsoft.com/metadata.svc | unknown | html | 183 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3720 | svchost.exe | 239.255.255.250:1900 | — | — | — | unknown |
6492 | msedge.exe | 52.123.243.83:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | DE | unknown |
5612 | MoUsoCoreWorker.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1612 | svchost.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1612 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1612 | svchost.exe | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1612 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
6164 | svchost.exe | 40.126.31.73:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
6164 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1092 | svchost.exe | 23.35.238.131:80 | go.microsoft.com | AKAMAI-AS | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.edge.skype.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
dmd.metaservices.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.googleapis.com |
| whitelisted |