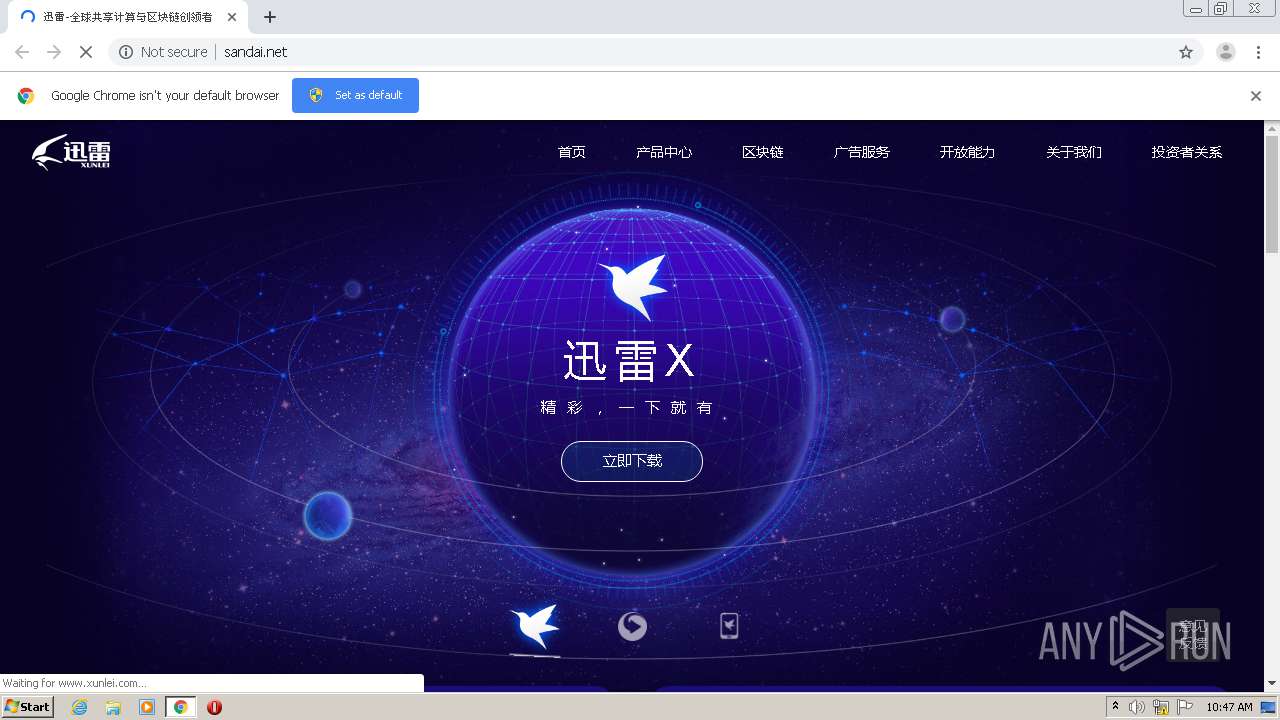
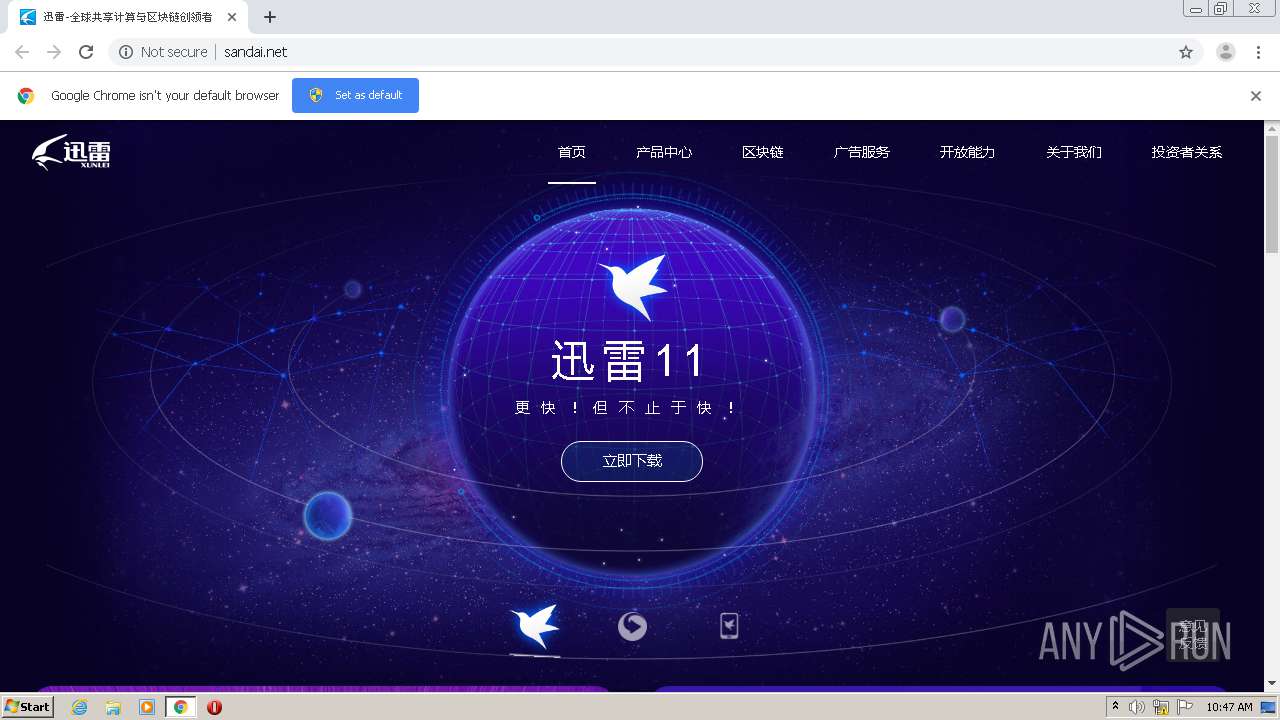
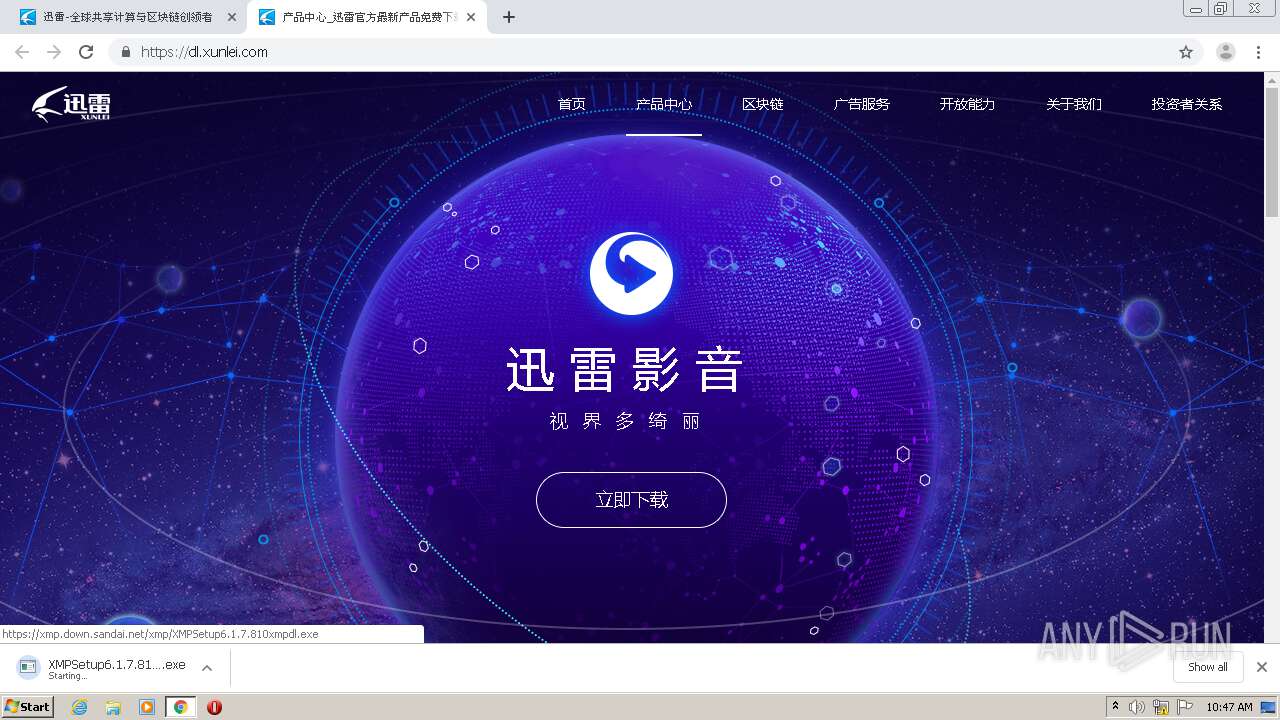
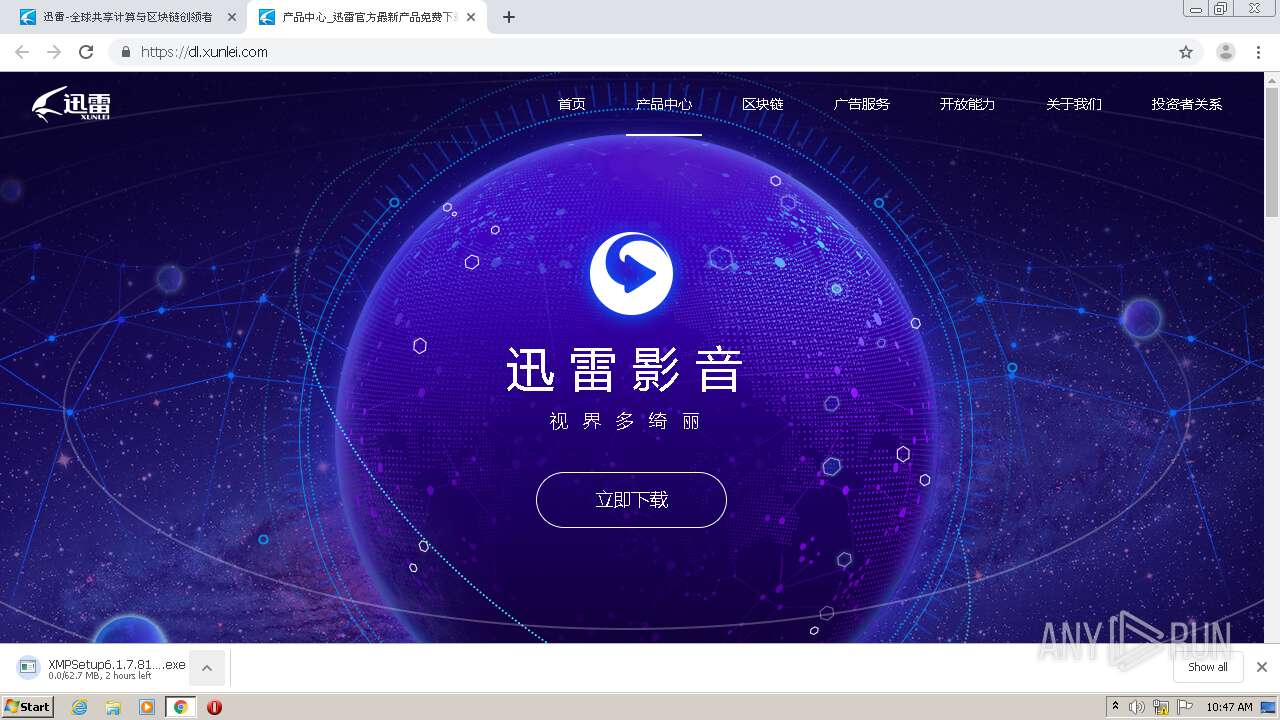
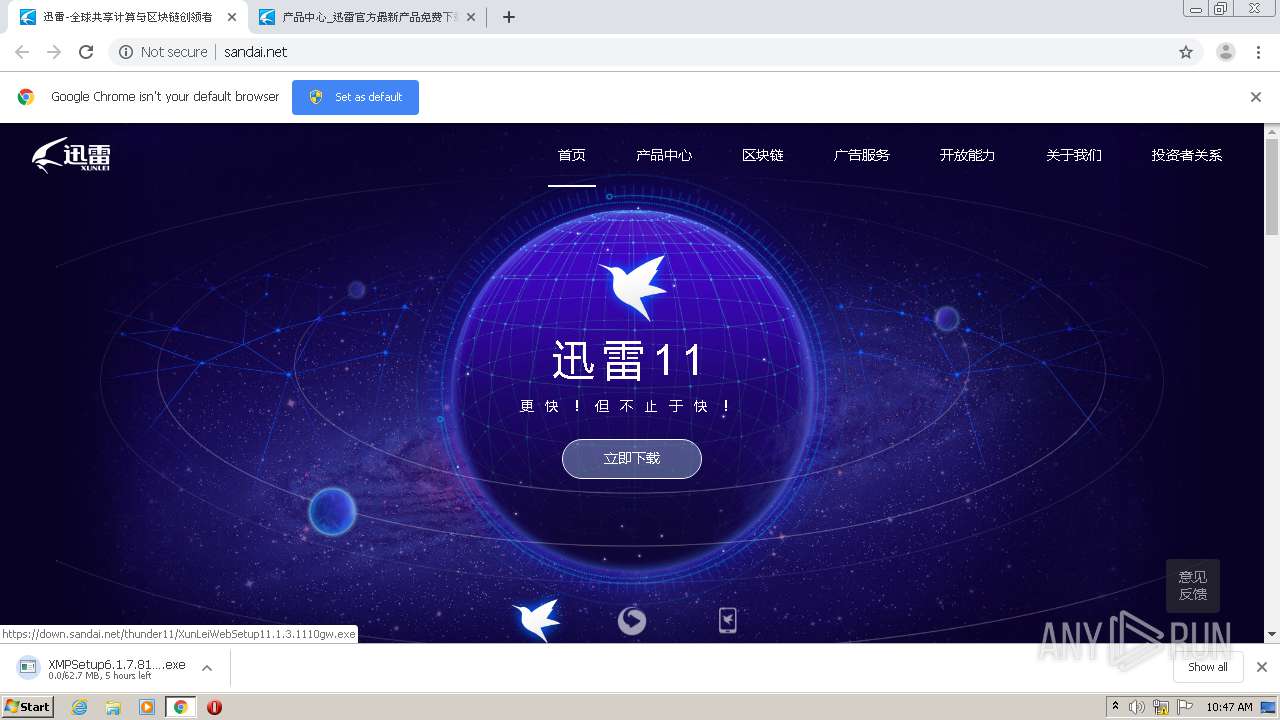
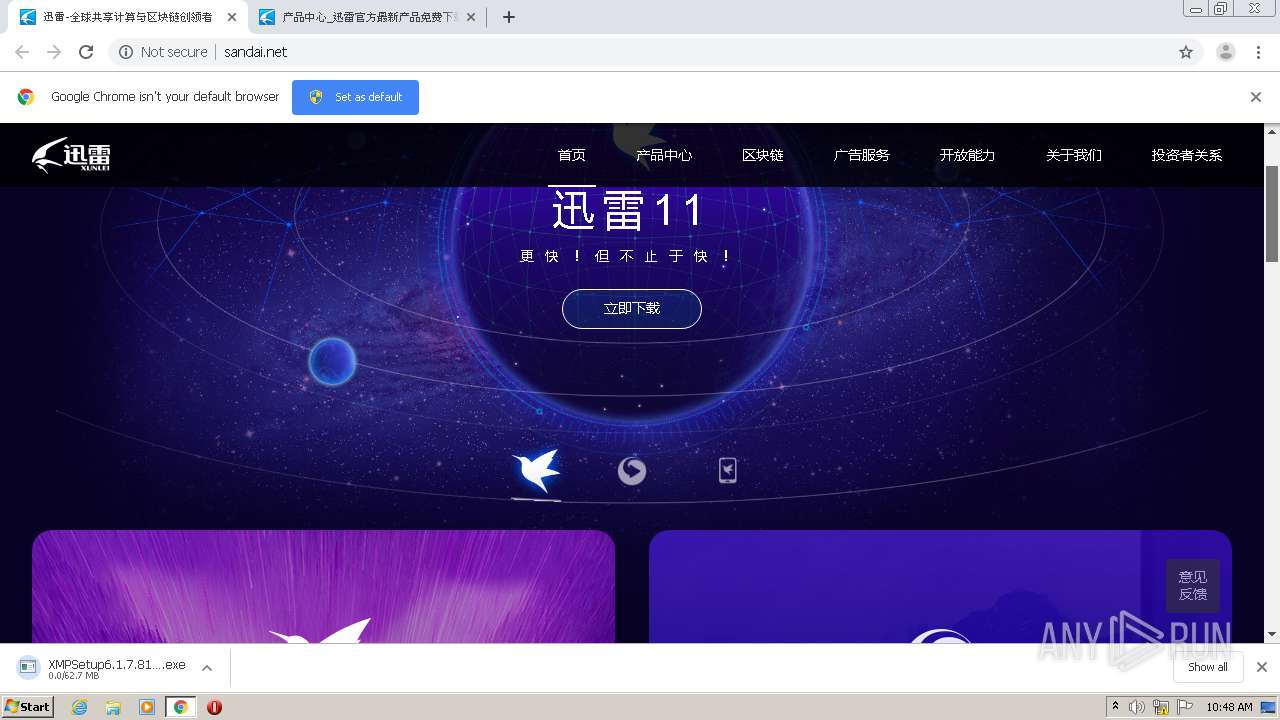
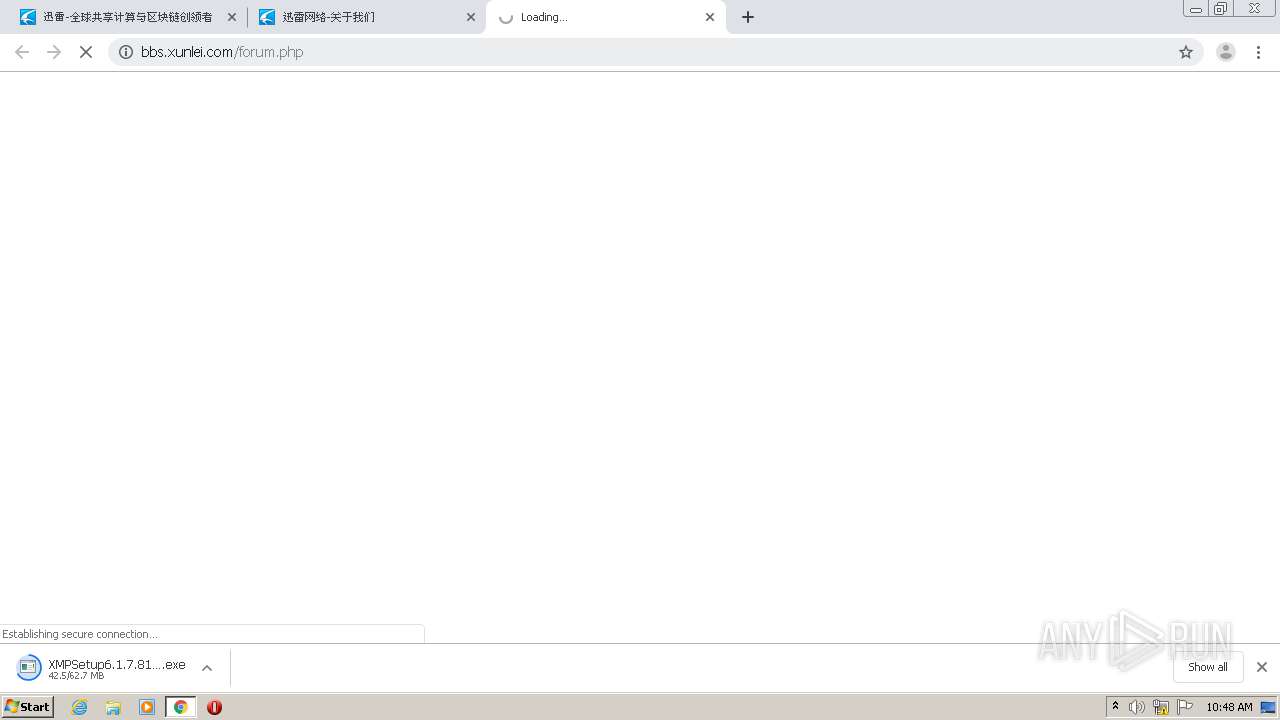
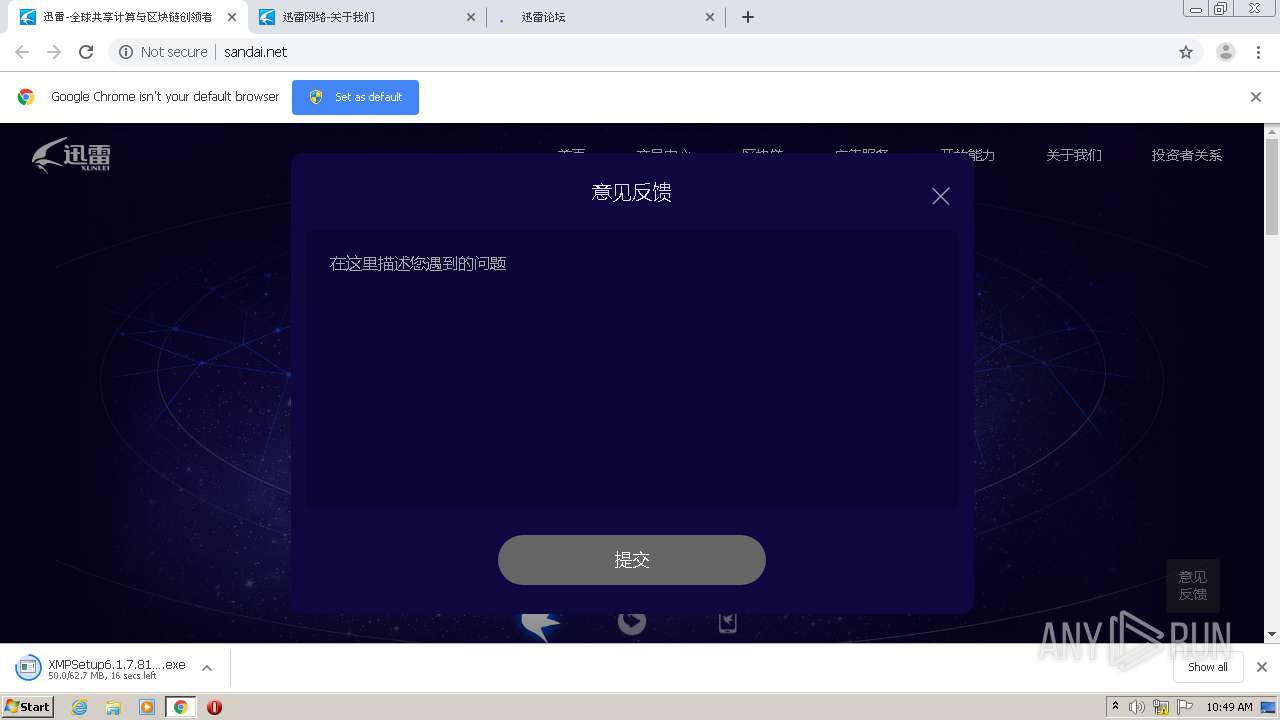
| URL: | http://sandai.net |
| Full analysis: | https://app.any.run/tasks/f2203062-7b98-473f-8514-0d0c9ec3fbf6 |
| Verdict: | Malicious activity |
| Analysis date: | November 25, 2020, 10:47:01 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | CC80E812F43F6118F32B34B856BDCB4A |
| SHA1: | 25AE762D81E246EDC386801DDE78EAD7D0317C1A |
| SHA256: | BB639465677F8D0D60979D9CAEEE651B21CE034E5E73ABEC516EA1AC5EED907B |
| SSDEEP: | 3:N1KNELjo:CW4 |
MALICIOUS
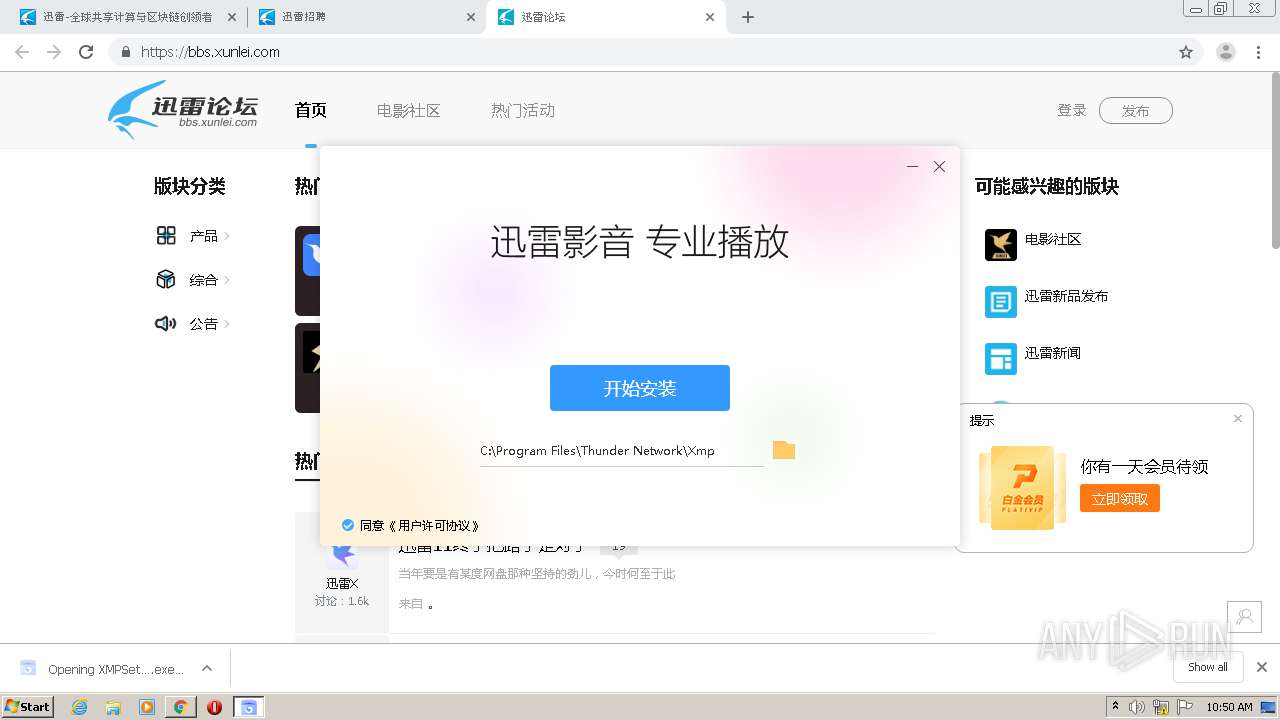
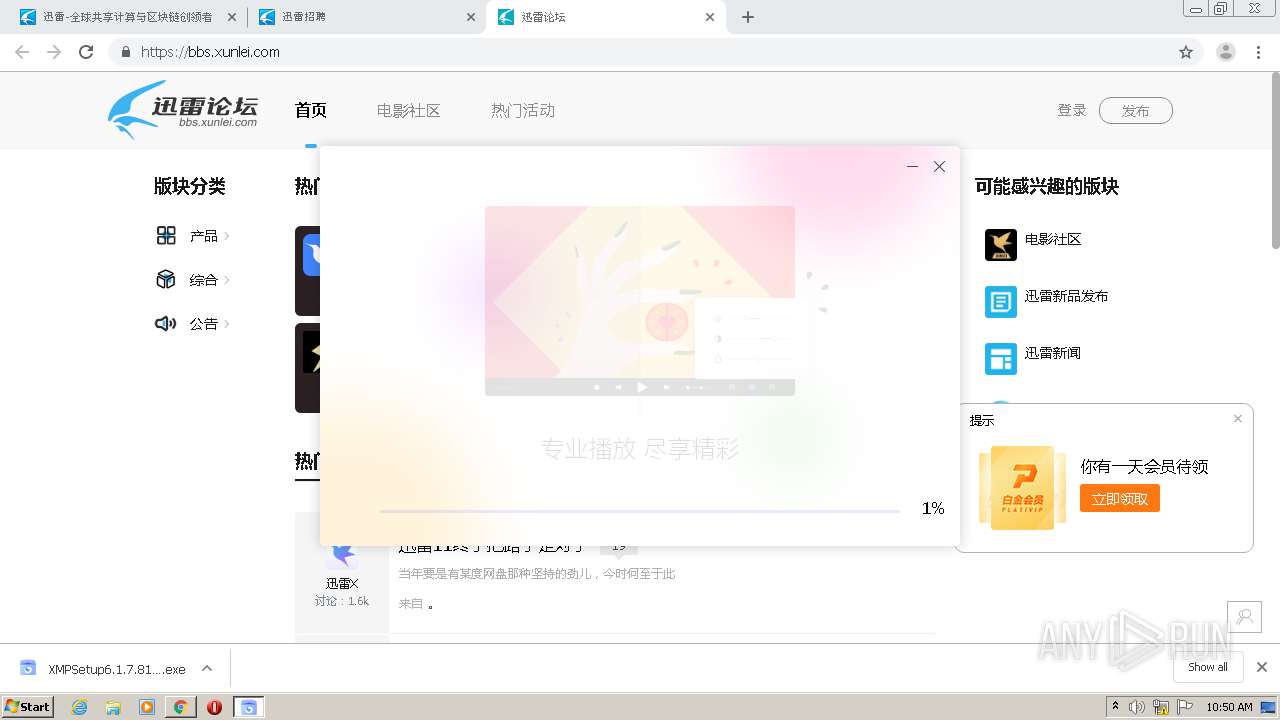
Application was dropped or rewritten from another process
- XMPSetup6.1.7.810xmpdl.exe (PID: 404)
- DownloadSDKServer.exe (PID: 2380)
- XMPSetup6.1.7.810xmpdl.exe (PID: 2788)
- Win7AppId.exe (PID: 3040)
- Win7AppId.exe (PID: 2524)
- Win7AppId.exe (PID: 2220)
- Win7AppId.exe (PID: 3304)
- XLServicePlatform.exe (PID: 396)
- XLServicePlatform.exe (PID: 3668)
- Win7AppId.exe (PID: 2144)
- Win7AppId.exe (PID: 3452)
- XLServicePlatform.exe (PID: 2940)
- AssociateHelper.exe (PID: 1080)
- Xmp.exe (PID: 2164)
- Xmp.exe (PID: 2008)
- XmpLiveUD.exe (PID: 2848)
- XmpLiveUD.exe (PID: 3360)
- DownloadSDKServer.exe (PID: 2312)
- Xmp.exe (PID: 4000)
- Xmp.exe (PID: 2792)
- AssociateHelper.exe (PID: 3676)
Drops executable file immediately after starts
- XMPSetup6.1.7.810xmpdl.exe (PID: 404)
- XLServicePlatform.exe (PID: 2940)
- XmpLiveUD.exe (PID: 2848)
Loads dropped or rewritten executable
- DownloadSDKServer.exe (PID: 2380)
- XMPSetup6.1.7.810xmpdl.exe (PID: 404)
- svchost.exe (PID: 3556)
- regsvr32.exe (PID: 2480)
- regsvr32.exe (PID: 2832)
- Xmp.exe (PID: 2164)
- Xmp.exe (PID: 2008)
- XmpLiveUD.exe (PID: 2848)
- XmpLiveUD.exe (PID: 3360)
- Xmp.exe (PID: 4000)
- DownloadSDKServer.exe (PID: 2312)
Creates or modifies windows services
- XLServicePlatform.exe (PID: 2940)
Changes settings of System certificates
- svchost.exe (PID: 3556)
- regsvr32.exe (PID: 2480)
- Xmp.exe (PID: 2164)
Registers / Runs the DLL via REGSVR32.EXE
- XMPSetup6.1.7.810xmpdl.exe (PID: 404)
Changes the autorun value in the registry
- XMPSetup6.1.7.810xmpdl.exe (PID: 404)
SUSPICIOUS
Drops a file with too old compile date
- XMPSetup6.1.7.810xmpdl.exe (PID: 404)
- XLServicePlatform.exe (PID: 2940)
- Xmp.exe (PID: 2008)
Uses NETSH.EXE for network configuration
- XMPSetup6.1.7.810xmpdl.exe (PID: 404)
Low-level read access rights to disk partition
- XMPSetup6.1.7.810xmpdl.exe (PID: 404)
- DownloadSDKServer.exe (PID: 2380)
- XLServicePlatform.exe (PID: 3668)
- XLServicePlatform.exe (PID: 2940)
- svchost.exe (PID: 3556)
- Xmp.exe (PID: 2164)
- Xmp.exe (PID: 2008)
- XmpLiveUD.exe (PID: 2848)
- XmpLiveUD.exe (PID: 3360)
- Xmp.exe (PID: 4000)
- DownloadSDKServer.exe (PID: 2312)
- Xmp.exe (PID: 2792)
Creates a directory in Program Files
- XMPSetup6.1.7.810xmpdl.exe (PID: 404)
- XLServicePlatform.exe (PID: 2940)
- regsvr32.exe (PID: 2480)
- Xmp.exe (PID: 2008)
Reads CPU info
- DownloadSDKServer.exe (PID: 2380)
- DownloadSDKServer.exe (PID: 2312)
Creates files in the user directory
- XMPSetup6.1.7.810xmpdl.exe (PID: 404)
- Xmp.exe (PID: 2164)
Creates a software uninstall entry
- XMPSetup6.1.7.810xmpdl.exe (PID: 404)
Executable content was dropped or overwritten
- chrome.exe (PID: 564)
- XLServicePlatform.exe (PID: 2940)
- XMPSetup6.1.7.810xmpdl.exe (PID: 404)
- regsvr32.exe (PID: 2480)
- regsvr32.exe (PID: 2832)
- XmpLiveUD.exe (PID: 2848)
- Xmp.exe (PID: 2008)
Creates files in the program directory
- XLServicePlatform.exe (PID: 2940)
- svchost.exe (PID: 3556)
- XMPSetup6.1.7.810xmpdl.exe (PID: 404)
- regsvr32.exe (PID: 2480)
- regsvr32.exe (PID: 2832)
- Xmp.exe (PID: 2008)
- Xmp.exe (PID: 2164)
Drops a file that was compiled in debug mode
- XLServicePlatform.exe (PID: 2940)
- regsvr32.exe (PID: 2480)
- regsvr32.exe (PID: 2832)
- XmpLiveUD.exe (PID: 2848)
- XMPSetup6.1.7.810xmpdl.exe (PID: 404)
- Xmp.exe (PID: 2008)
Creates files in the Windows directory
- svchost.exe (PID: 3556)
Removes files from Windows directory
- svchost.exe (PID: 3556)
Adds / modifies Windows certificates
- svchost.exe (PID: 3556)
- regsvr32.exe (PID: 2480)
- Xmp.exe (PID: 2164)
Modifies the open verb of a shell class
- XMPSetup6.1.7.810xmpdl.exe (PID: 404)
- Xmp.exe (PID: 2008)
Creates COM task schedule object
- regsvr32.exe (PID: 2832)
- regsvr32.exe (PID: 2480)
Application launched itself
- Xmp.exe (PID: 2164)
- Xmp.exe (PID: 2008)
Starts itself from another location
- XmpLiveUD.exe (PID: 2848)
INFO
Application launched itself
- chrome.exe (PID: 564)
Reads the hosts file
- chrome.exe (PID: 2496)
- chrome.exe (PID: 564)
- Xmp.exe (PID: 2164)
Reads settings of System Certificates
- chrome.exe (PID: 2496)
- Xmp.exe (PID: 2164)
Dropped object may contain Bitcoin addresses
- XMPSetup6.1.7.810xmpdl.exe (PID: 404)
- Xmp.exe (PID: 2008)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
107
Monitored processes
52
Malicious processes
12
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 252 | C:\Windows\system32\netsh.exe advfirewall firewall delete rule name="DownloadSDKServer" dir=in action=allow program="C:\Users\admin\AppData\Local\Temp\XmpInstall\6.1.7.810\SDK\DownloadSDKServer.exe" | C:\Windows\system32\netsh.exe | — | XMPSetup6.1.7.810xmpdl.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 292 | C:\Windows\system32\netsh.exe advfirewall firewall add rule name="APlayer" dir=in action=allow program="C:\Program Files\Thunder Network\Xmp\Program\APlayer.exe" | C:\Windows\system32\netsh.exe | — | XMPSetup6.1.7.810xmpdl.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 396 | "C:\Program Files\Thunder Network\Xmp\Program\XLServicePlatform.exe" -p | C:\Program Files\Thunder Network\Xmp\Program\XLServicePlatform.exe | — | XMPSetup6.1.7.810xmpdl.exe | |||||||||||
User: admin Company: ShenZhen Xunlei Networking Technologies,LTD Integrity Level: HIGH Description: XLServicePlatform Exit code: 0 Version: 2, 0, 0, 5 Modules
| |||||||||||||||
| 404 | "C:\Users\admin\Downloads\XMPSetup6.1.7.810xmpdl.exe" | C:\Users\admin\Downloads\XMPSetup6.1.7.810xmpdl.exe | chrome.exe | ||||||||||||
User: admin Company: ShenZhen Xunlei Networking Technologies,LTD Integrity Level: HIGH Description: XmpSetup6.1.7.810xmpdl Exit code: 0 Version: 6.1.7.810 Modules
| |||||||||||||||
| 564 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "http://sandai.net" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 784 | C:\Windows\system32\netsh.exe advfirewall firewall add rule name="DownloadSDKServer" dir=in action=allow program="C:\Program Files\Thunder Network\Xmp\Program\resources\bin\SDK\DownloadSDKServer.exe" | C:\Windows\system32\netsh.exe | — | XMPSetup6.1.7.810xmpdl.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 860 | C:\Windows\system32\netsh.exe advfirewall firewall delete rule name="APlayer" dir=in action=allow program="C:\Program Files\Thunder Network\Xmp\Program\APlayer.exe" | C:\Windows\system32\netsh.exe | — | XMPSetup6.1.7.810xmpdl.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 896 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2268 --on-initialized-event-handle=316 --parent-handle=320 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 984 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,6668019728418415023,4073725586304577716,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9794691009315178700 --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3748 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
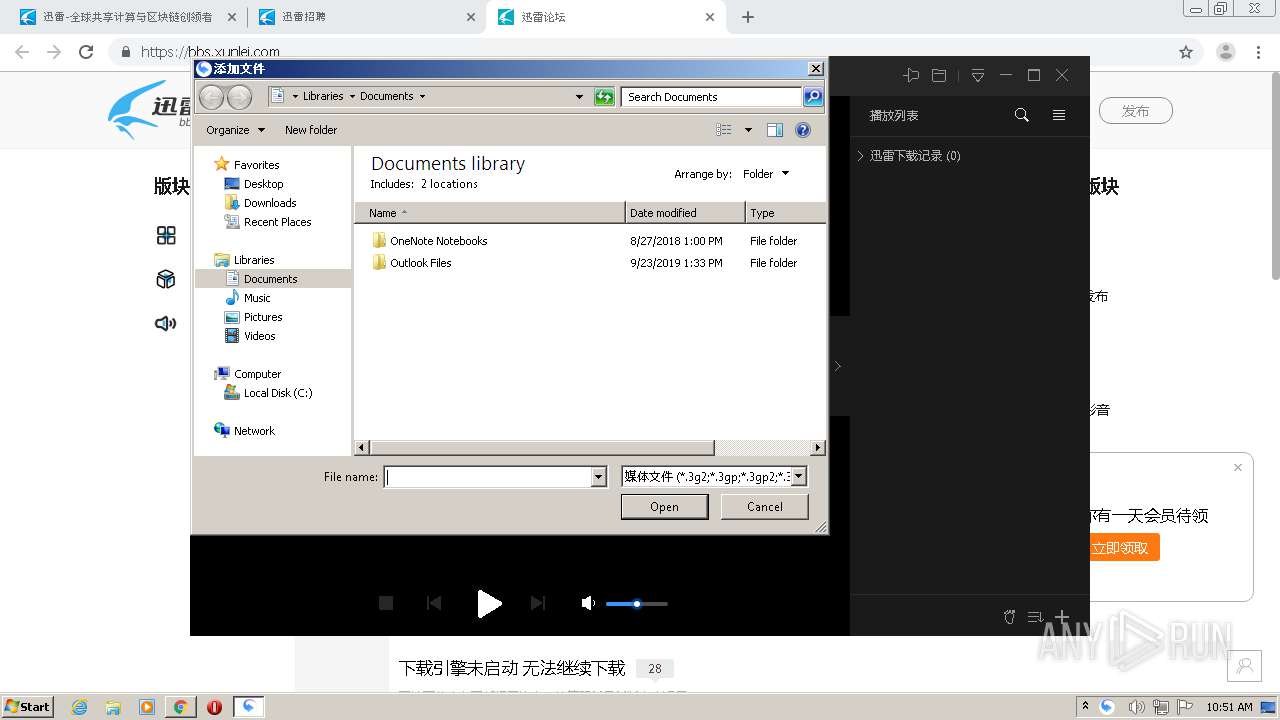
| 1080 | "C:\Program Files\Thunder Network\Xmp\Program\AssociateHelper.exe" --associate=.3g2;.3gp;.3gp2;.3gpp;.aac;.ac3;.acc;.aiff;.amr;.amv;.ape;.asf;.ass;.au;.avi;.bik;.cda;.csf;.divx;.dts;.dvd;.evo;.f4v;.flac;.flv;.hlv;.letv;.m1a;.m1v;.m2a;.m2p;.m2ts;.m2v;.m4a;.m4b;.m4p;.m4r;.m4v;.mid;.midi;.mka;.mkv;.mod;.mov;.mp2;.mp2v;.mp3;.mp4;.mpa;.mpc;.mpe;.mpeg;.mpeg1;.mpeg2;.mpeg4;.mpg;.mpv2;.mts;.oga;.ogg;.ogm;.ogv;.ogx;.psb;.pmp;.pva;.qt;.ra;.ram;.rm;.rmvb;.rpm;.rt;.scm;.smi;.smil;.srt;.ssa;.sub;.sup;.swf;.tp;.tpr;.ts;.tta;.usf;.vob;.vp6;.wav;.wm;.wma;.wmp;.wmv;.wv;.xlmv;.hflv;.f5v;.hmp4;.mp5;.hmkv;.mk5; | C:\Program Files\Thunder Network\Xmp\Program\AssociateHelper.exe | — | XMPSetup6.1.7.810xmpdl.exe | |||||||||||
User: admin Company: ShenZhen Xunlei Networking Technologies,LTD Integrity Level: HIGH Description: AssociateHelper Exit code: 0 Version: 1.0.0.3 Modules
| |||||||||||||||
Total events
6 868
Read events
2 528
Write events
4 335
Delete events
5
Modification events
| (PID) Process: | (564) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (564) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (564) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (564) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (564) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (896) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 564-13250774836917000 |
Value: 259 | |||
| (PID) Process: | (564) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (564) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (564) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (564) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
358
Suspicious files
132
Text files
1 114
Unknown types
87
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5FBE3635-234.pma | — | |
MD5:— | SHA256:— | |||
| 564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\29b0dbfd-9839-4ff4-a104-6b4a4f02cb85.tmp | — | |
MD5:— | SHA256:— | |||
| 564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF1541a6.TMP | text | |
MD5:— | SHA256:— | |||
| 564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | text | |
MD5:— | SHA256:— | |||
| 564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF154213.TMP | text | |
MD5:— | SHA256:— | |||
| 564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF15437b.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
216
TCP/UDP connections
225
DNS requests
278
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
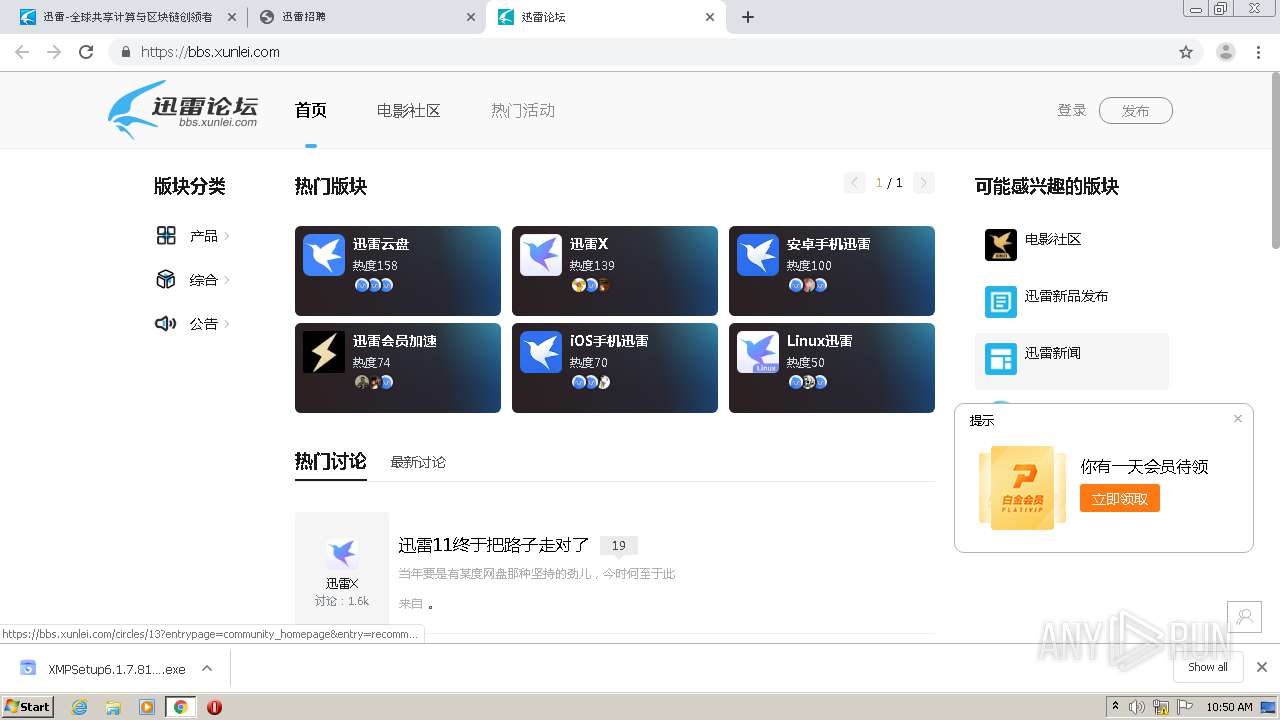
2496 | chrome.exe | GET | 200 | 39.104.39.191:80 | http://sandai.net/ | CN | html | 7.10 Kb | whitelisted |
2496 | chrome.exe | GET | 200 | 39.104.39.191:80 | http://sandai.net/v2018/dist/homepage.css?h=33931c | CN | text | 9.54 Kb | whitelisted |
2496 | chrome.exe | GET | 200 | 103.235.46.191:80 | http://hm.baidu.com/hm.js?eff9bb8c1851f3f4e2fb515943970a1d | HK | text | 14.9 Kb | whitelisted |
2496 | chrome.exe | GET | 200 | 39.104.39.191:80 | http://sandai.net/v2018/dist/earth02.png?h=10e885 | CN | image | 111 Kb | whitelisted |
2496 | chrome.exe | GET | 200 | 39.104.39.191:80 | http://sandai.net/v2018/dist/ios.png?h=a403f6 | CN | image | 7.10 Kb | whitelisted |
2496 | chrome.exe | GET | 200 | 39.104.39.191:80 | http://sandai.net/v2018/dist/banner_bgmask.png?h=11c08a | CN | image | 44.9 Kb | whitelisted |
2496 | chrome.exe | GET | 200 | 39.104.39.191:80 | http://sandai.net/v2018/dist/earth01.png?h=9bbded | CN | image | 102 Kb | whitelisted |
2496 | chrome.exe | GET | 200 | 39.104.39.191:80 | http://sandai.net/v2018/dist/banner_bg.jpg?h=b150bd | CN | image | 231 Kb | whitelisted |
2496 | chrome.exe | GET | 200 | 39.104.39.191:80 | http://sandai.net/v2018/dist/earth03.png?h=ab2f78 | CN | image | 106 Kb | whitelisted |
2496 | chrome.exe | GET | 200 | 39.104.39.191:80 | http://sandai.net/v2018/dist/common.css?h=fa7ada | CN | text | 4.64 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
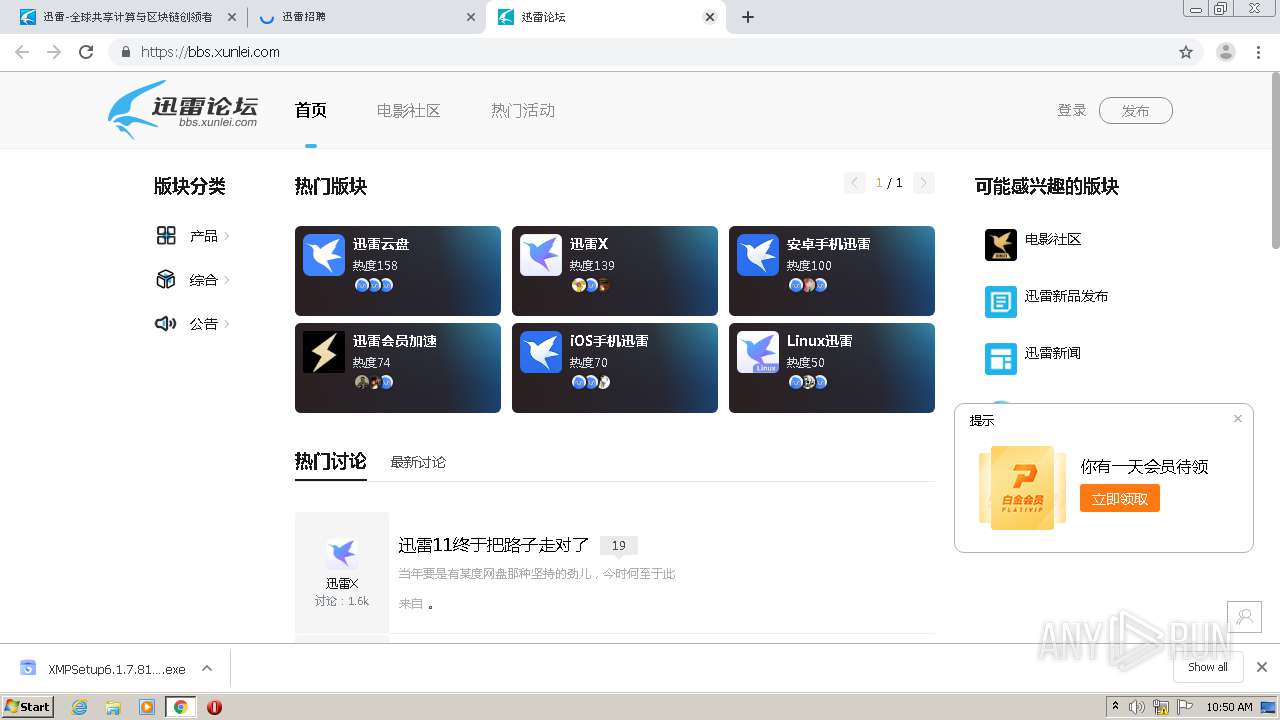
2496 | chrome.exe | 47.101.181.191:443 | etl-xlmc-ssl.xunlei.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
2496 | chrome.exe | 115.231.155.197:443 | xmp.down.sandai.net | No.31,Jin-rong Street | CN | suspicious |
2496 | chrome.exe | 122.224.49.210:80 | x.xunlei.com | No.288,Fu-chun Road | CN | unknown |
2496 | chrome.exe | 101.133.209.97:443 | bbs.xunlei.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
2496 | chrome.exe | 101.133.209.97:80 | bbs.xunlei.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
2496 | chrome.exe | 39.104.39.191:80 | sandai.net | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
2496 | chrome.exe | 172.217.18.109:443 | accounts.google.com | Google Inc. | US | suspicious |
2496 | chrome.exe | 27.148.149.248:443 | www.xunlei.com | Fuzhou | CN | suspicious |
2496 | chrome.exe | 120.39.202.103:443 | img-vip-ssl.a.88cdn.com | No.31,Jin-rong Street | CN | unknown |
2496 | chrome.exe | 172.217.21.206:443 | clients1.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
sandai.net |
| whitelisted |
accounts.google.com |
| shared |
www.xunlei.com |
| malicious |
img-vip-ssl.a.88cdn.com |
| malicious |
safebrowsing.googleapis.com |
| whitelisted |
bbs.xunlei.com |
| unknown |
beian.miit.gov.cn |
| whitelisted |
biz.xunlei.com |
| malicious |
box.onethingpcs.com |
| unknown |
dl.xunlei.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2380 | DownloadSDKServer.exe | Potential Corporate Privacy Violation | ET P2P BitTorrent DHT ping request |